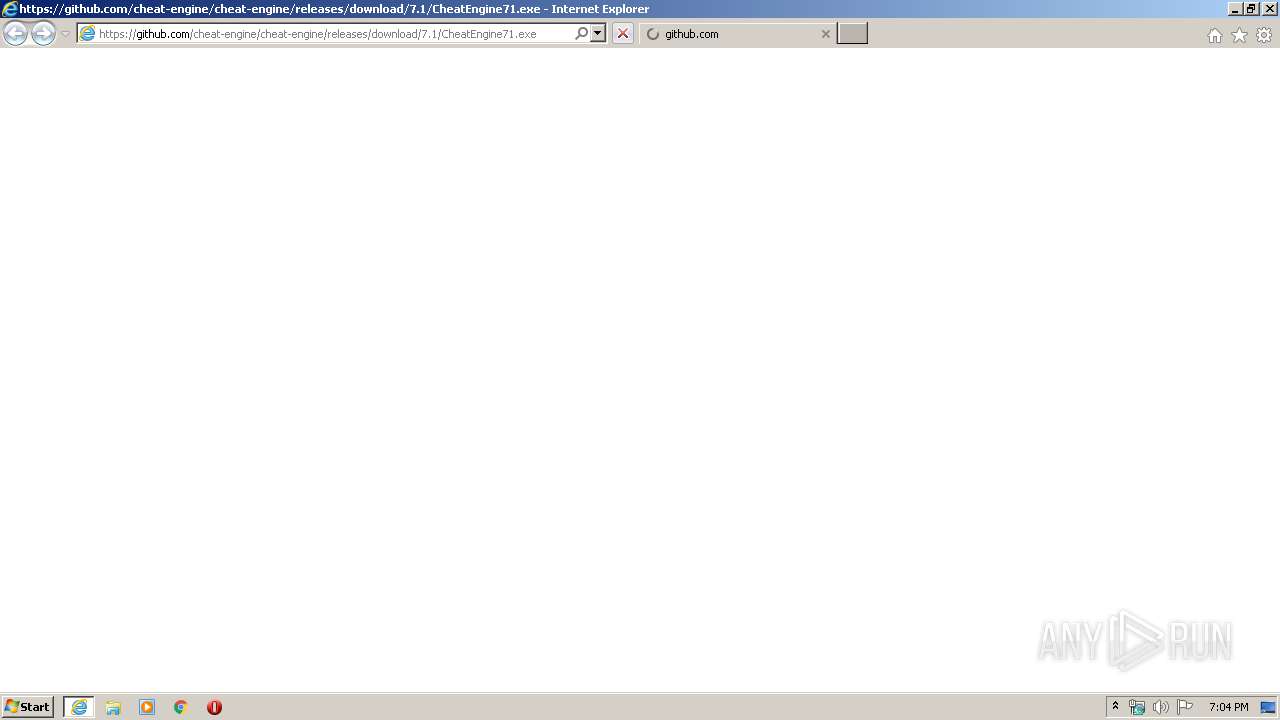
| URL: | https://github.com/cheat-engine/cheat-engine/releases/download/7.1/CheatEngine71.exe |
| Full analysis: | https://app.any.run/tasks/5a8fad01-581c-4948-b774-9cbbbfef1eaa |
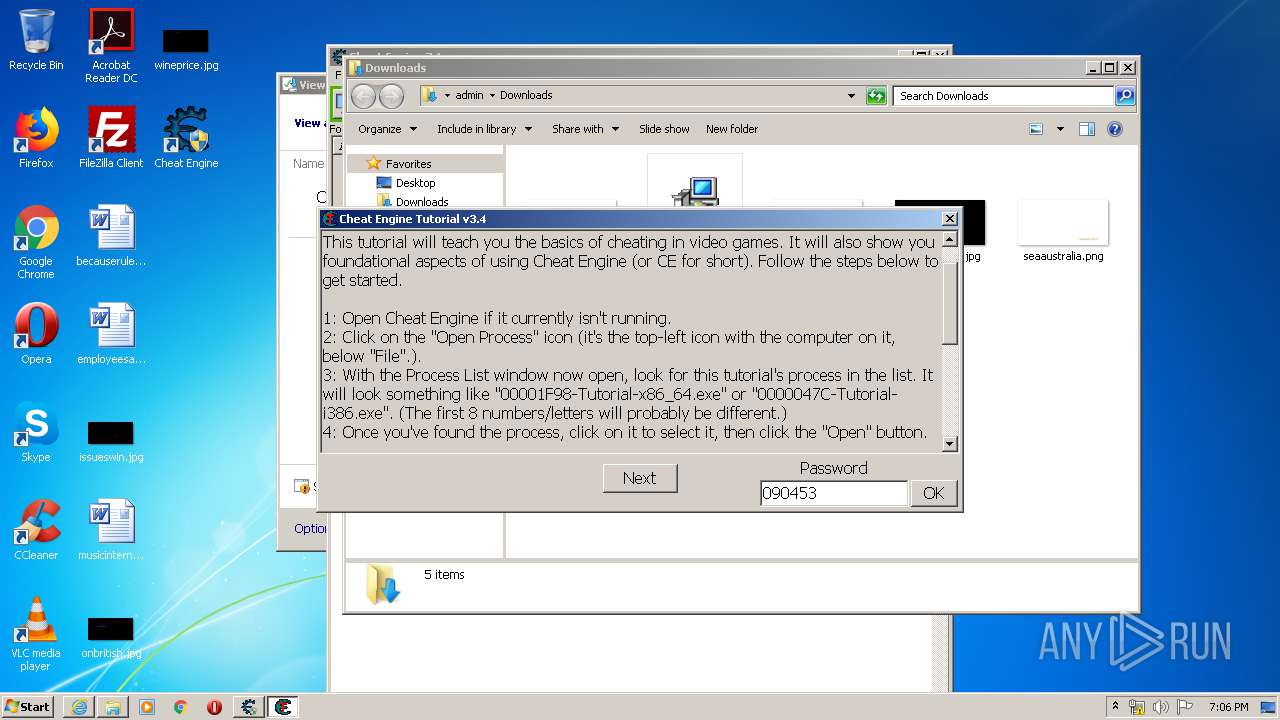
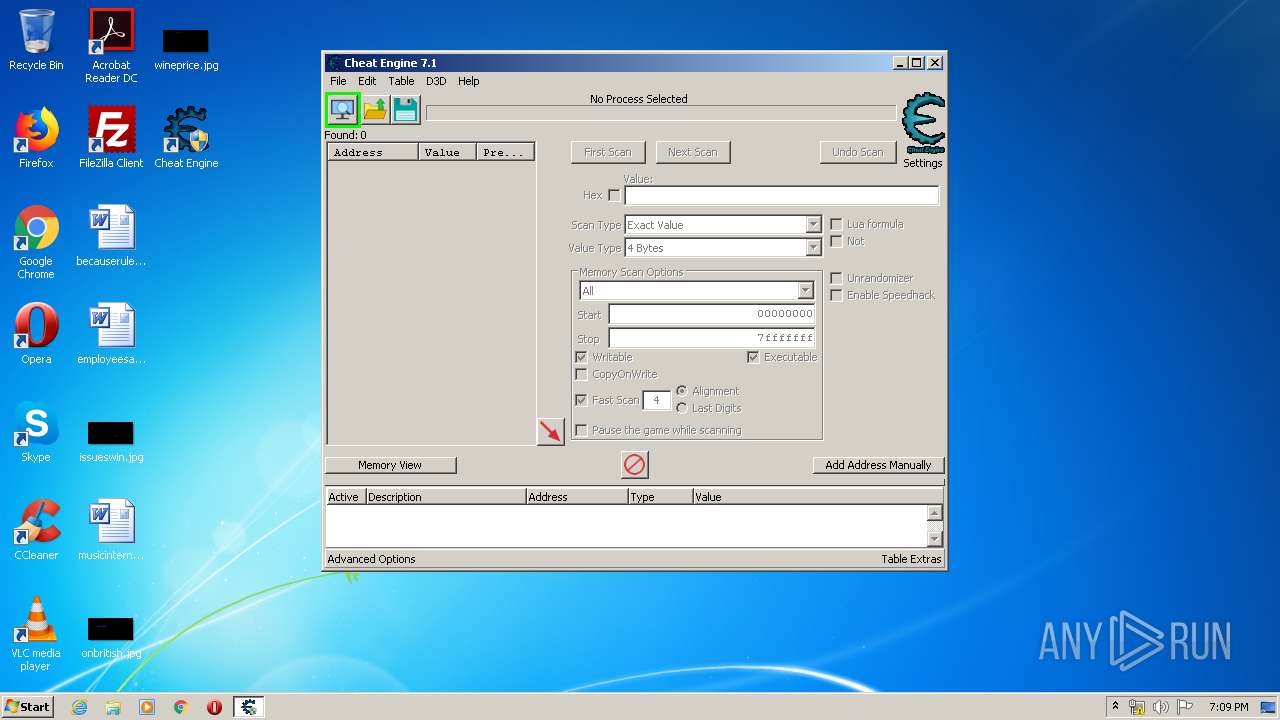
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2020, 18:04:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 03A9D5E350889F6BCB2D1B68B0E07A1C |
| SHA1: | 545893C0FD8199BFE0ACD1A2D5DFFBEFA9457421 |
| SHA256: | 0DF95CEBC46397DEF080A4D1FE4FD900AD1517A673E4870F139F4C305A4766D0 |
| SSDEEP: | 3:N8tEd2NAFNMLAdS4INMLAMAKkCSP4MrG:2ugNAFNM0deNM0BK8PxG |
MALICIOUS
Application was dropped or rewritten from another process
- CheatEngine71.exe (PID: 2172)
- Kernelmoduleunloader.exe (PID: 2352)
- windowsrepair.exe (PID: 2596)
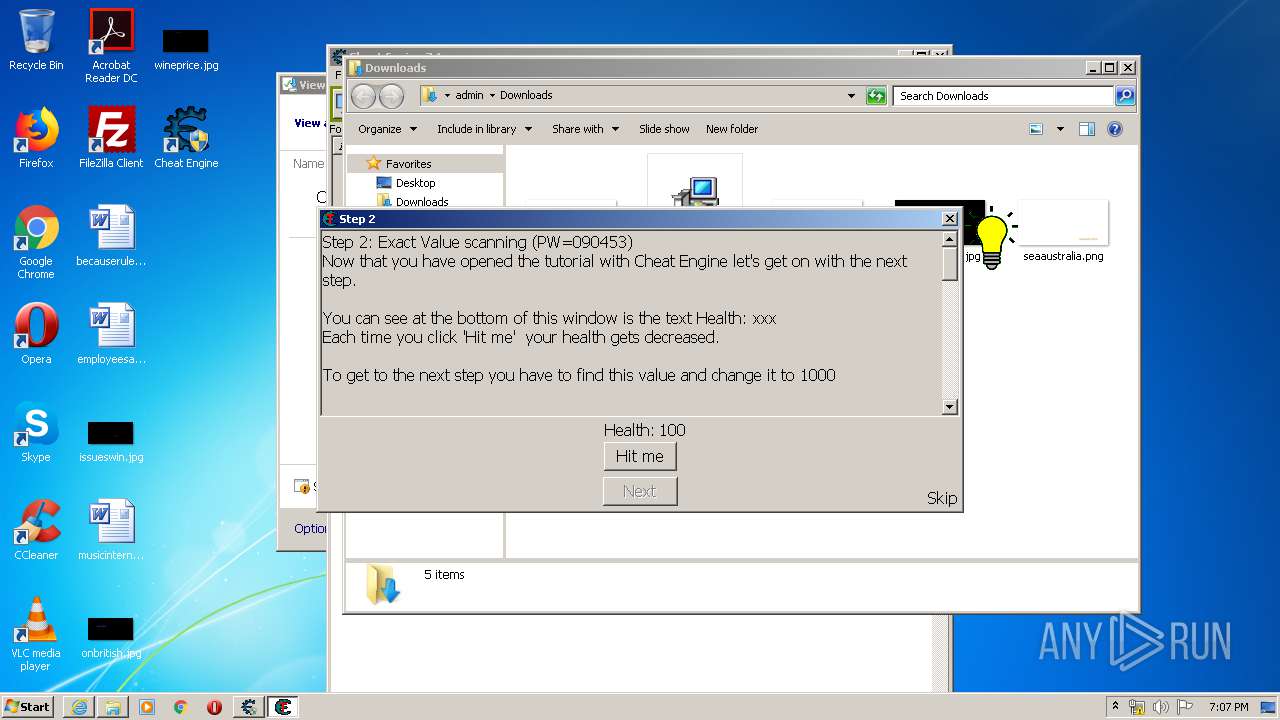
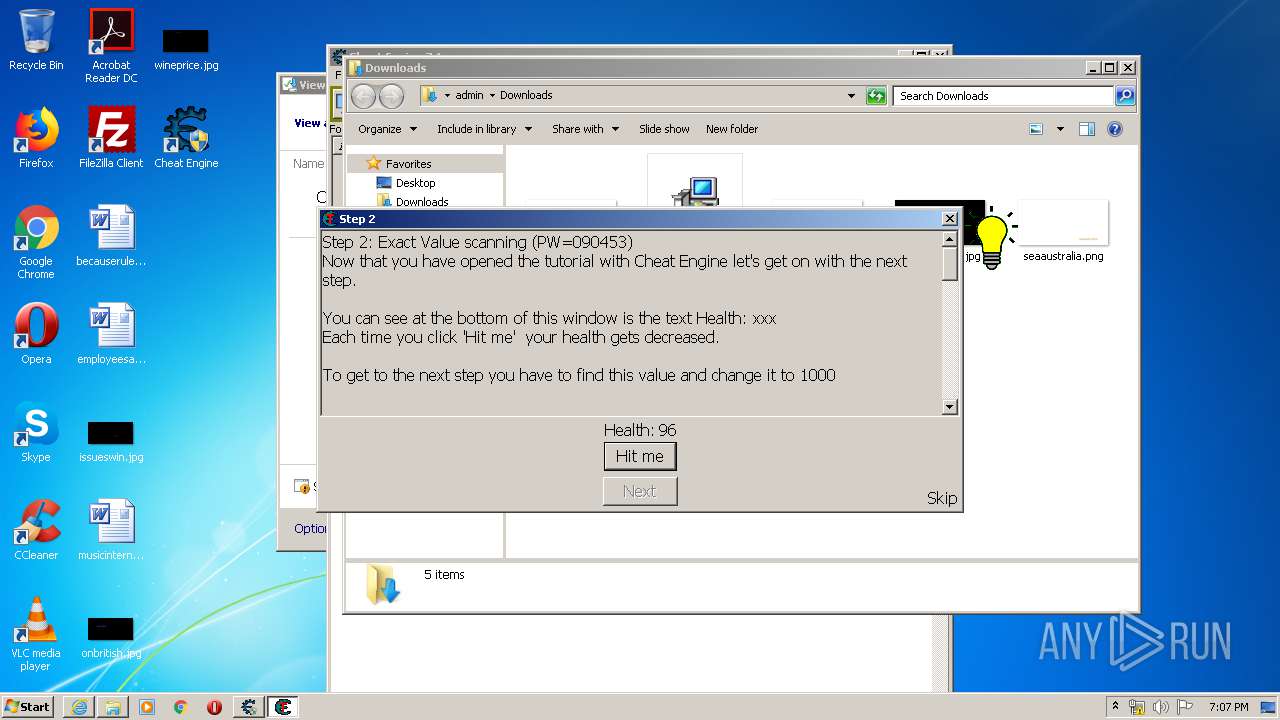
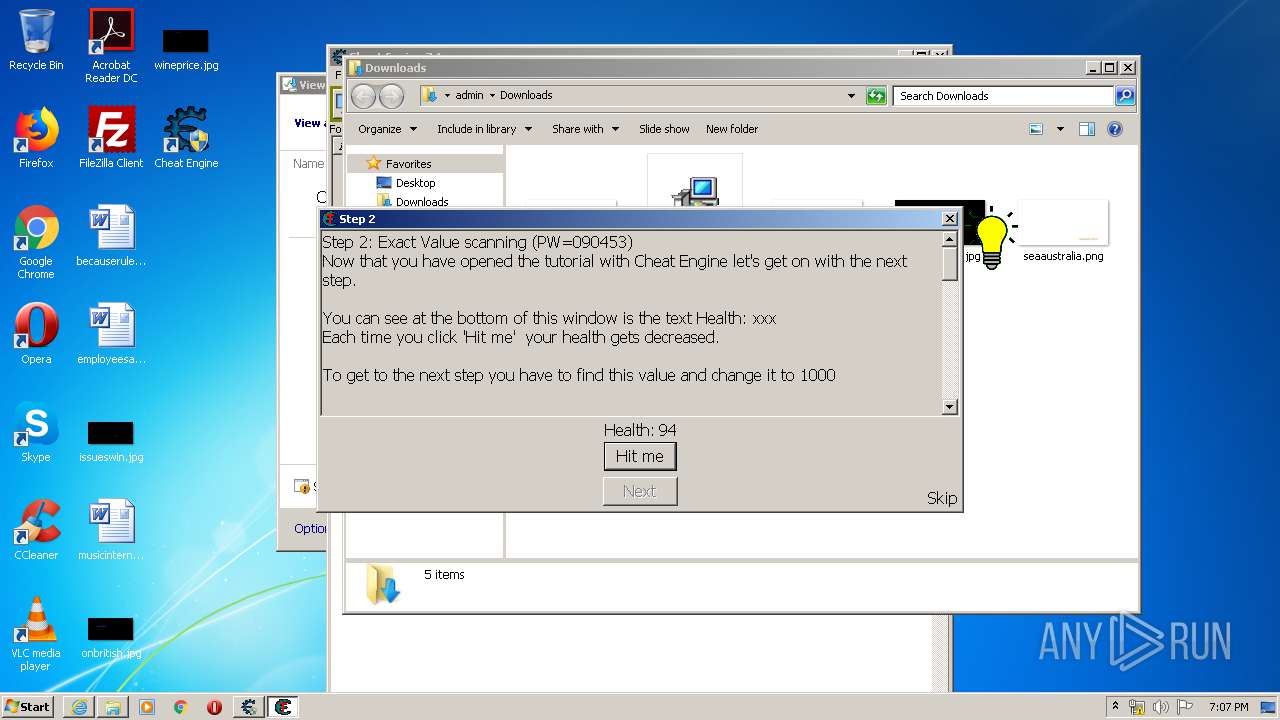
- Cheat Engine.exe (PID: 2872)
- ceregreset.exe (PID: 3928)
- cheatengine-i386.exe (PID: 2668)
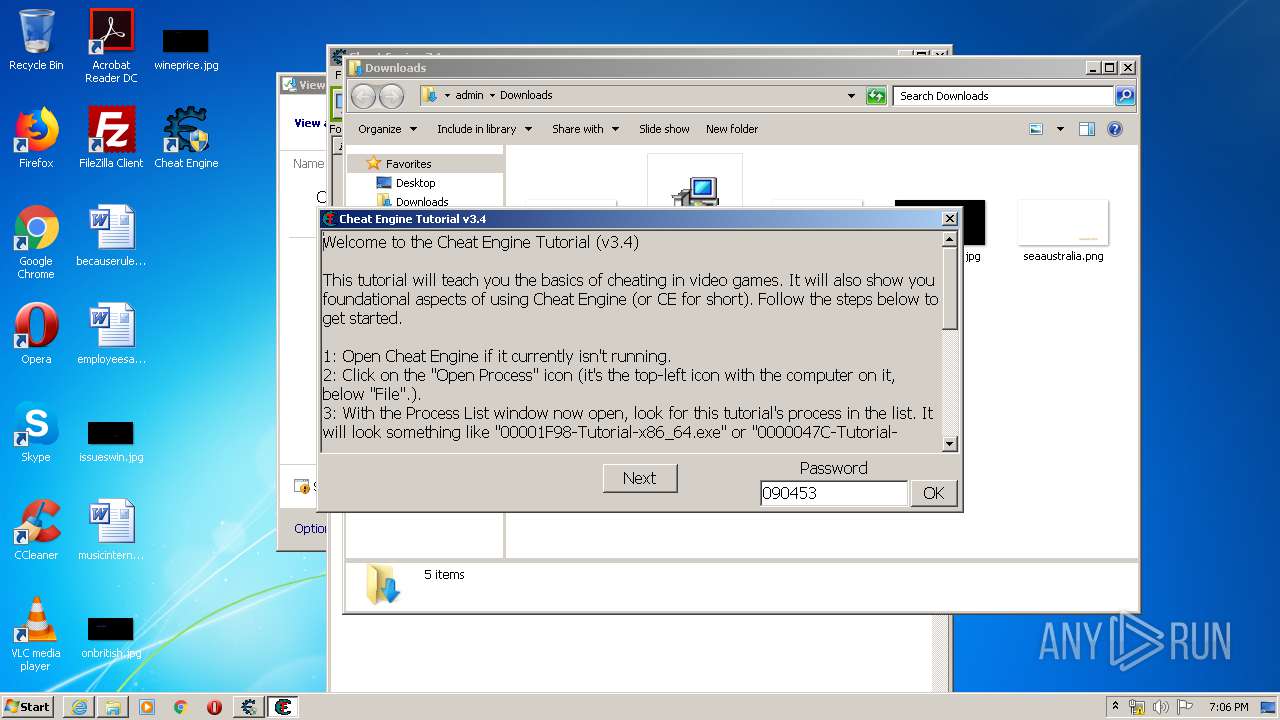
- Tutorial-i386.exe (PID: 2752)
- gtutorial-i386.exe (PID: 4088)
Actions looks like stealing of personal data
- CheatEngine71.tmp (PID: 3152)
Loads dropped or rewritten executable
- cheatengine-i386.exe (PID: 2668)
Changes settings of System certificates
- cheatengine-i386.exe (PID: 2668)
SUSPICIOUS
Reads internet explorer settings
- CheatEngine71.tmp (PID: 3152)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2964)
- CheatEngine71.exe (PID: 2172)
- iexplore.exe (PID: 3168)
- CheatEngine71.tmp (PID: 3152)
Reads Windows owner or organization settings
- CheatEngine71.tmp (PID: 3152)
Reads the Windows organization settings
- CheatEngine71.tmp (PID: 3152)
Reads Internet Cache Settings
- CheatEngine71.tmp (PID: 3152)
- cheatengine-i386.exe (PID: 2668)
Reads Environment values
- CheatEngine71.tmp (PID: 3152)
Modifies the open verb of a shell class
- CheatEngine71.tmp (PID: 3152)
Uses ICACLS.EXE to modify access control list
- CheatEngine71.tmp (PID: 3152)
Creates files in the program directory
- cheatengine-i386.exe (PID: 2668)
Creates files in the user directory
- cheatengine-i386.exe (PID: 2668)
Adds / modifies Windows certificates
- cheatengine-i386.exe (PID: 2668)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3168)
- iexplore.exe (PID: 2964)
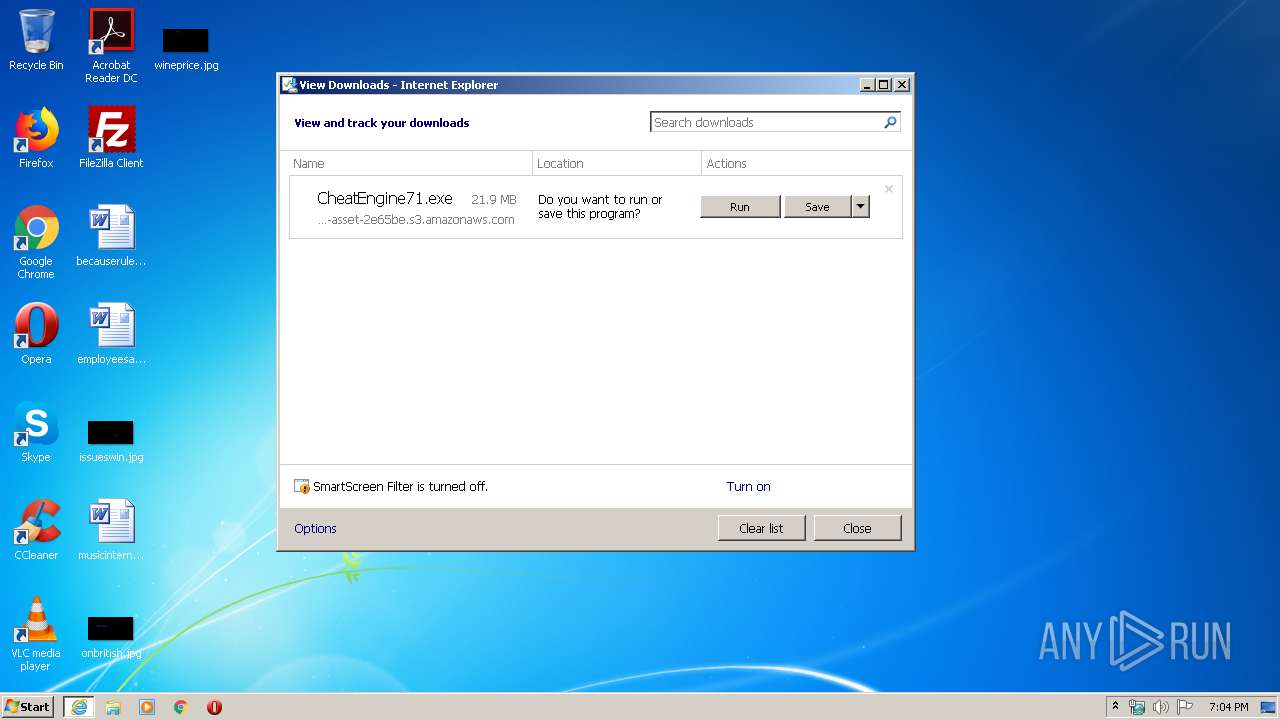
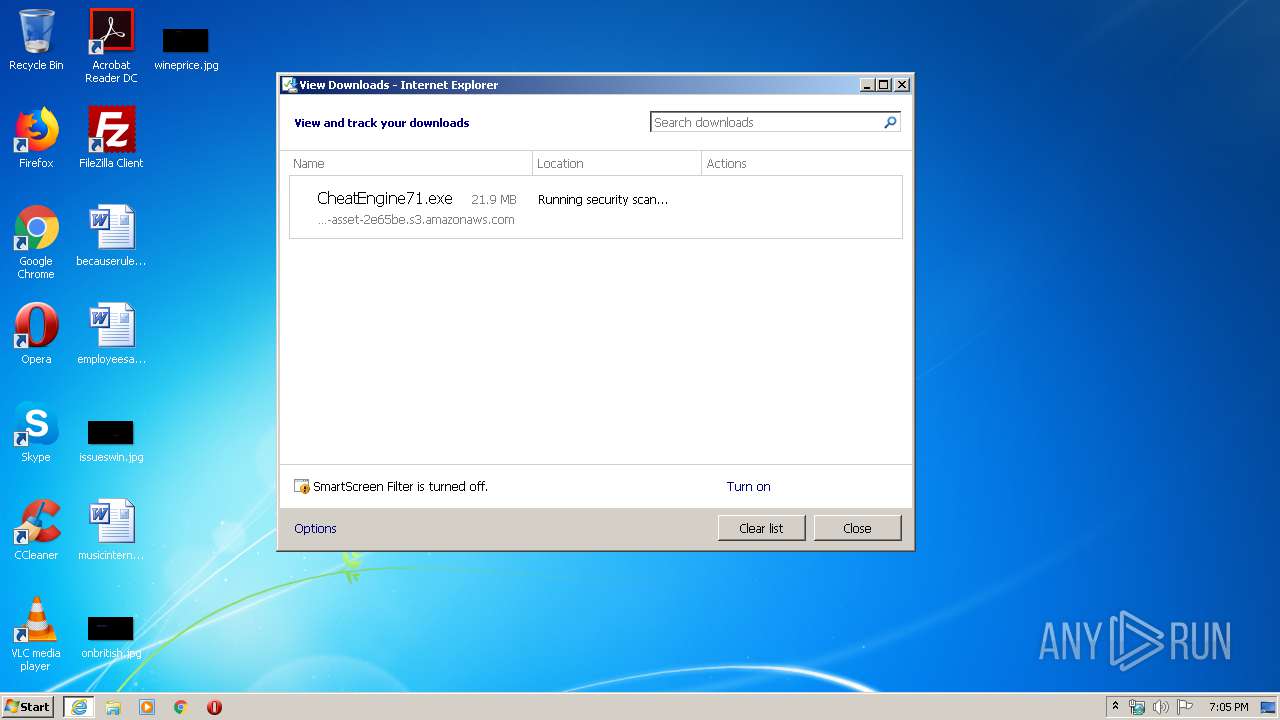
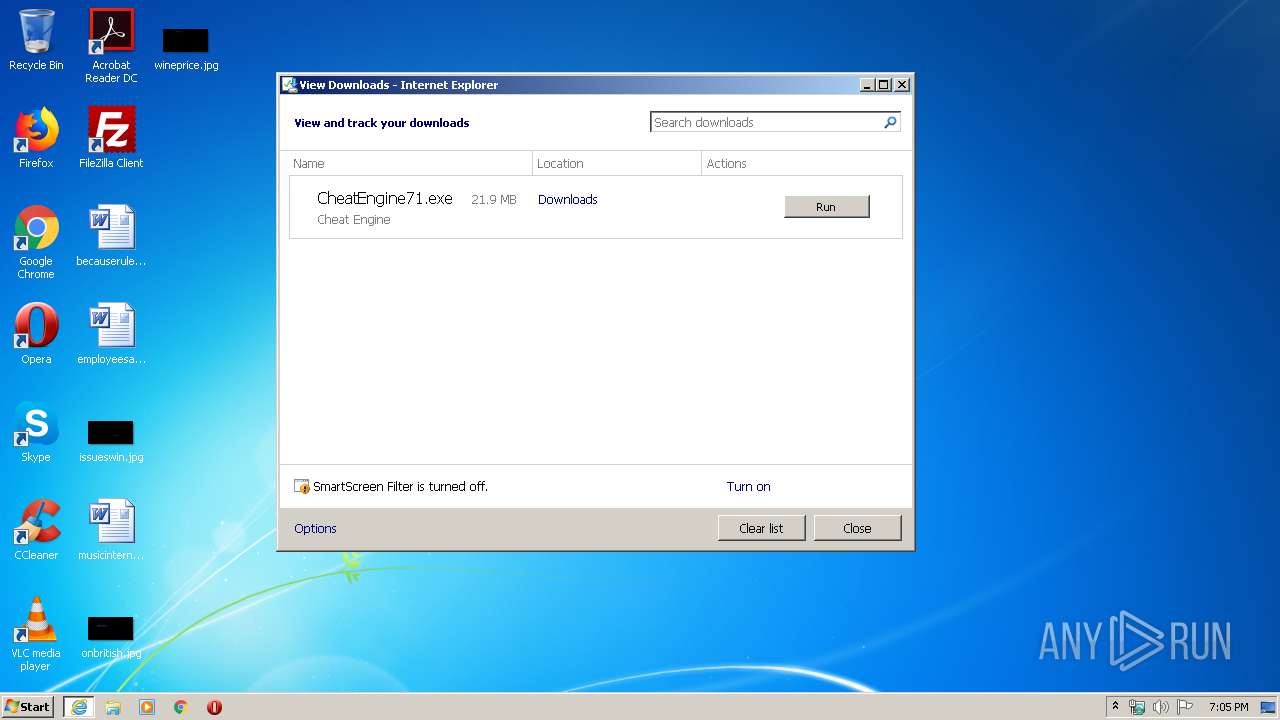
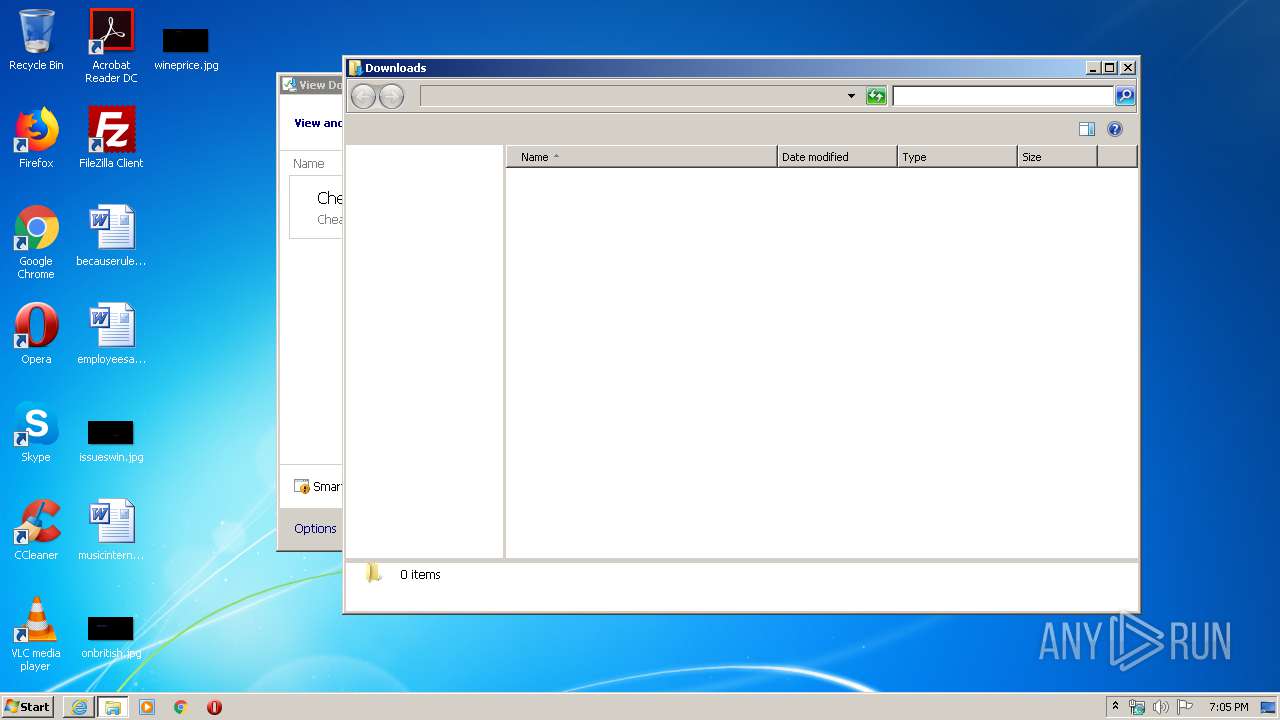
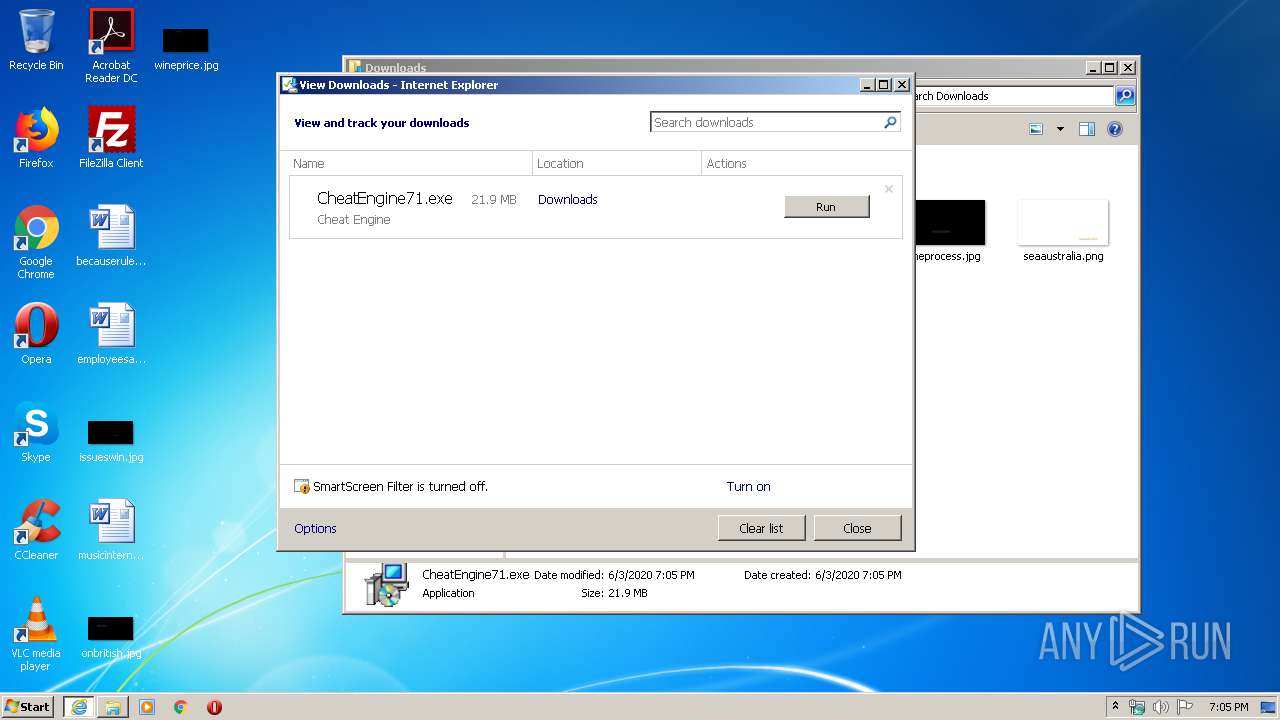
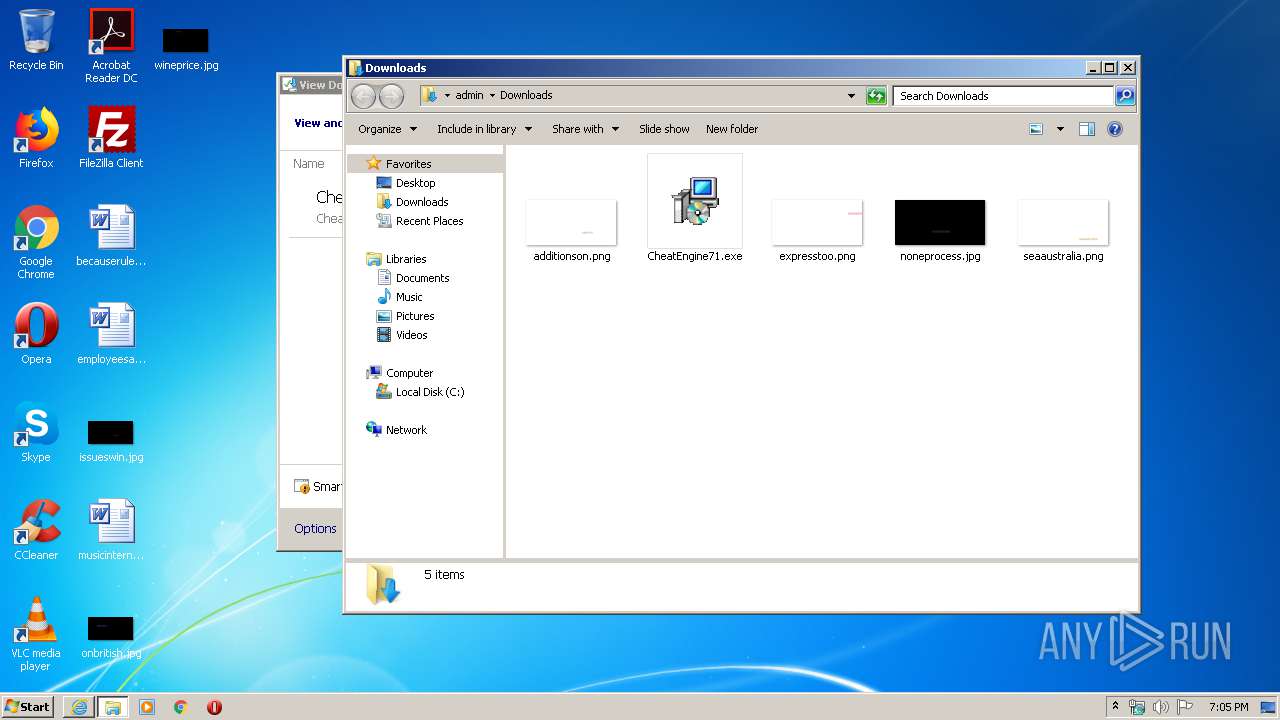
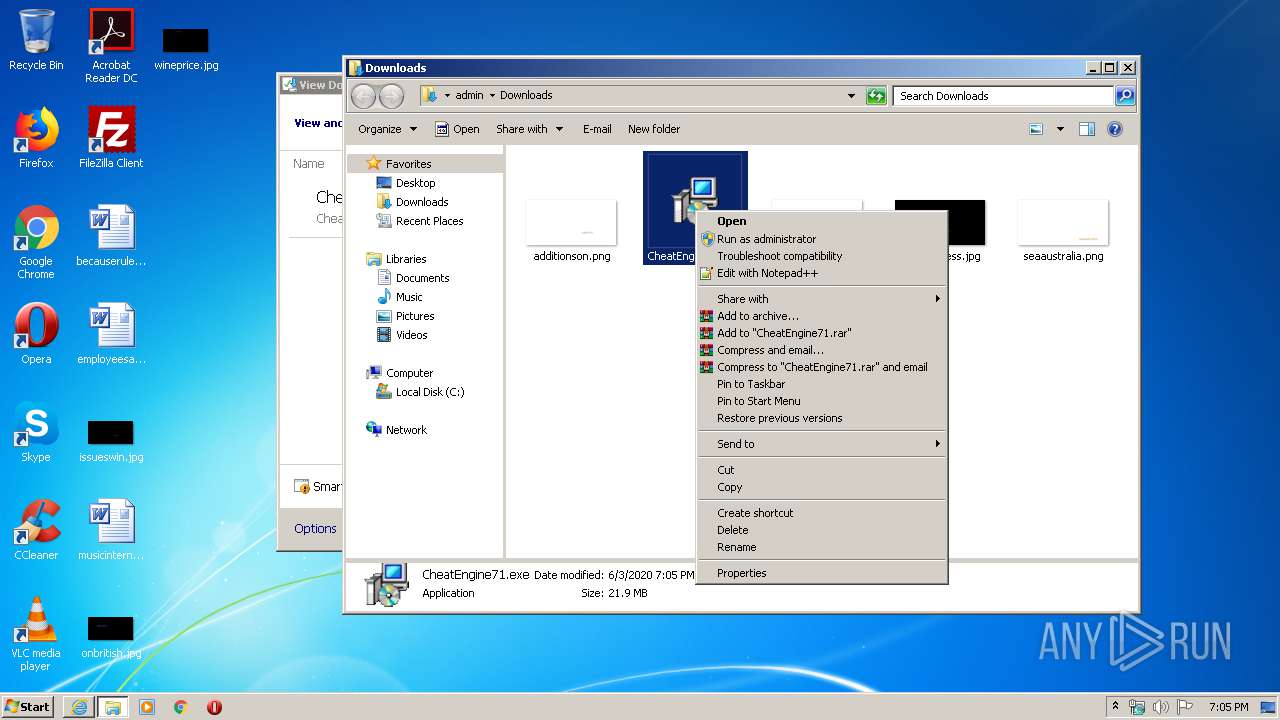
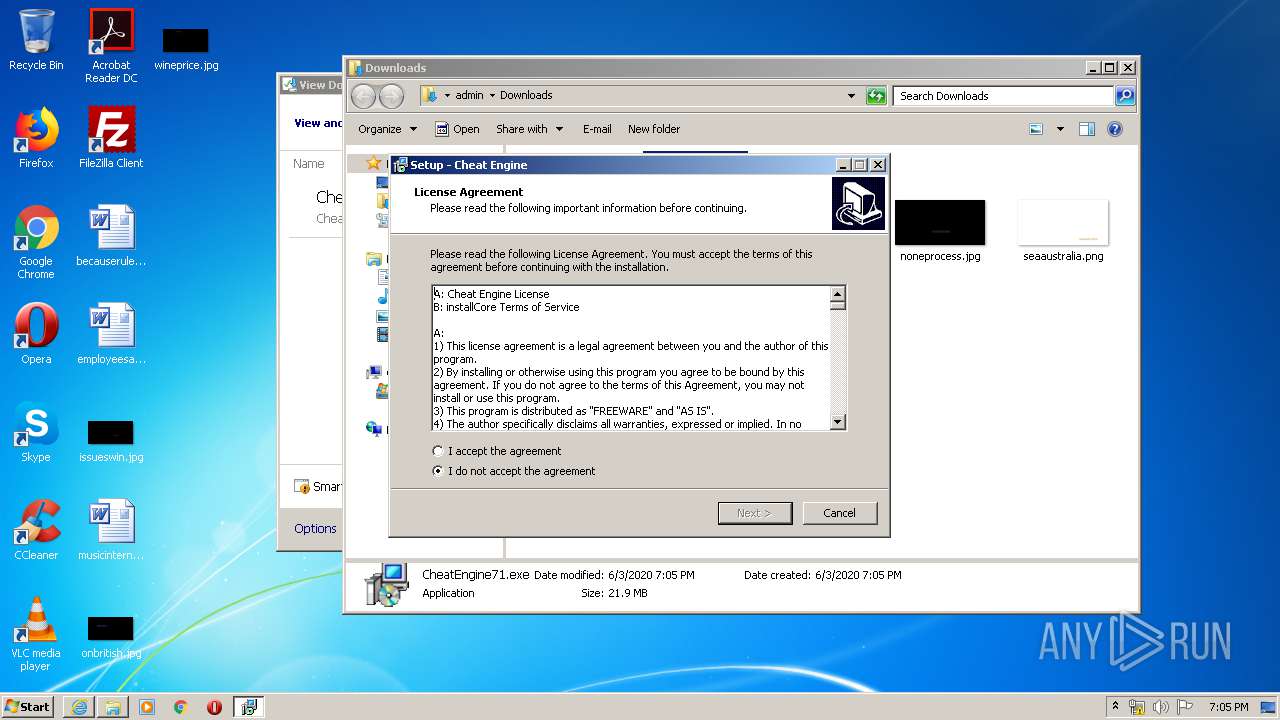
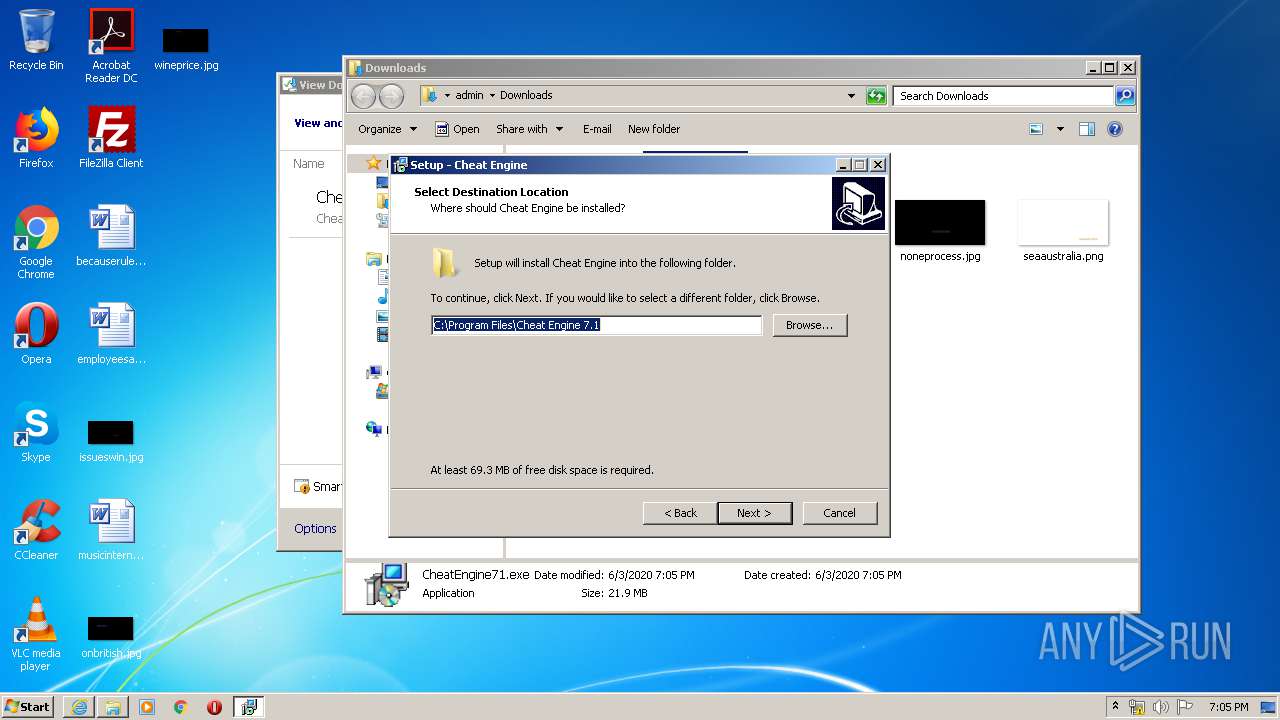
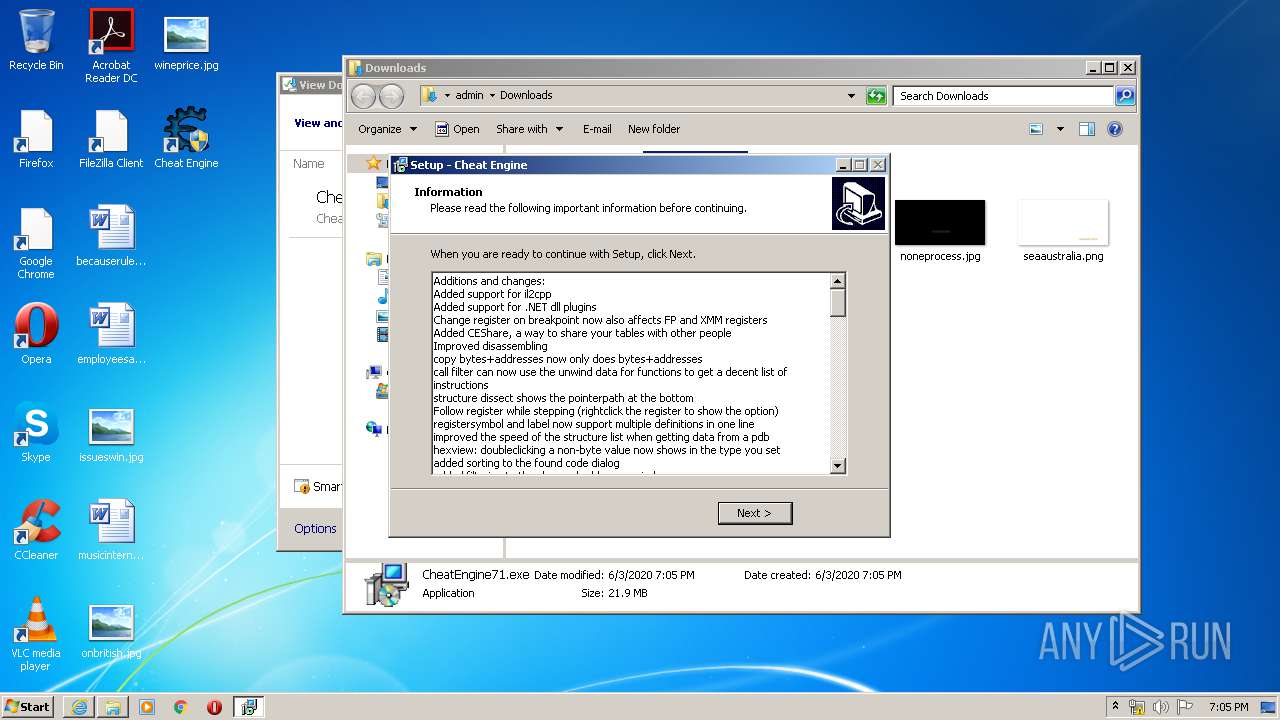
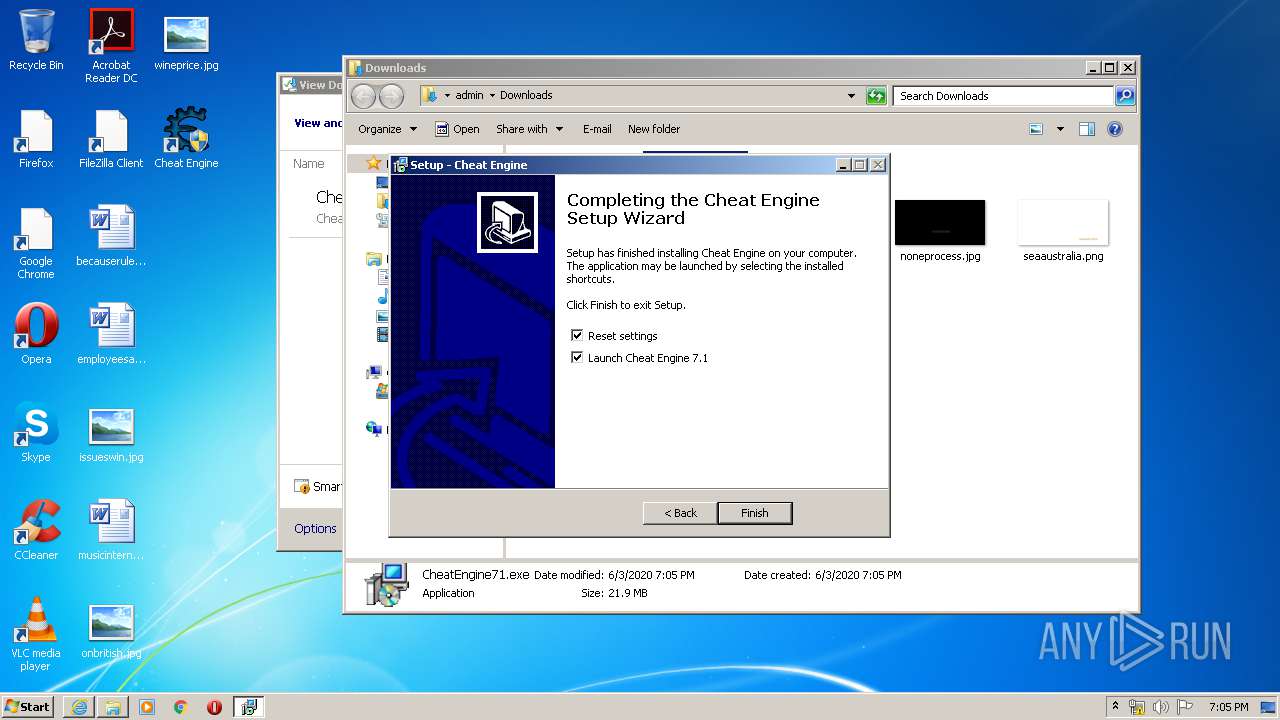
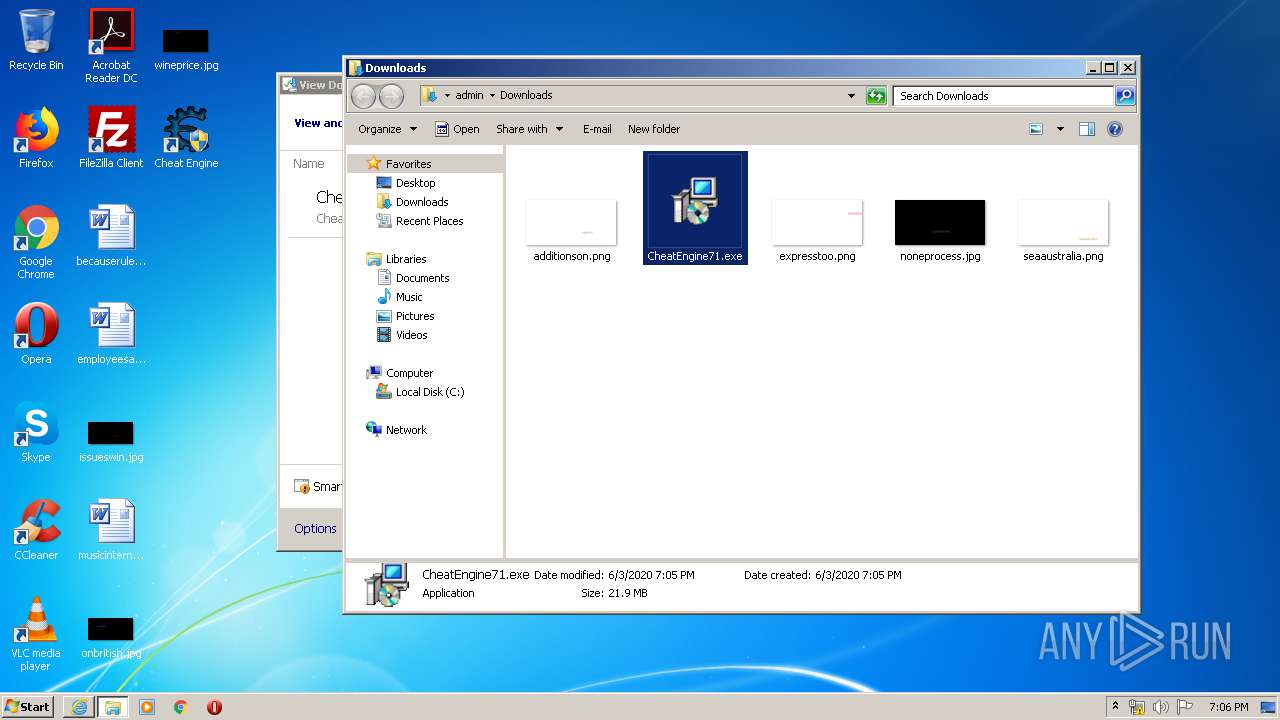
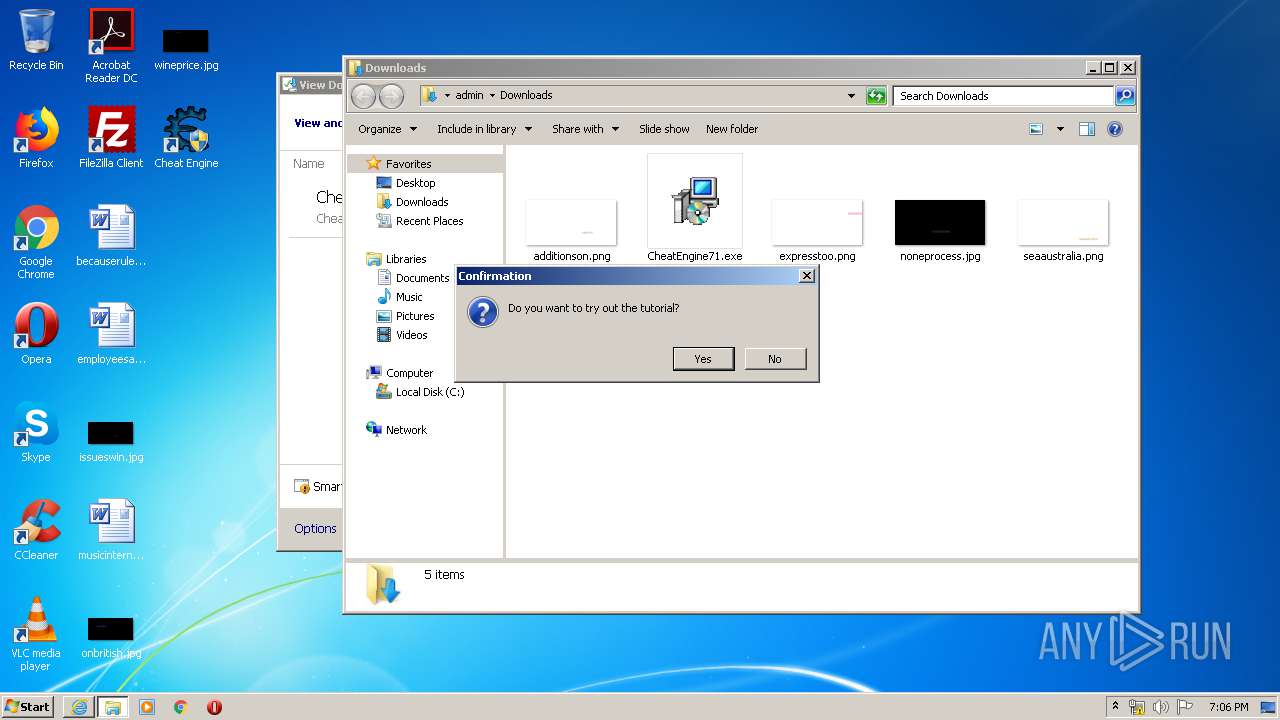
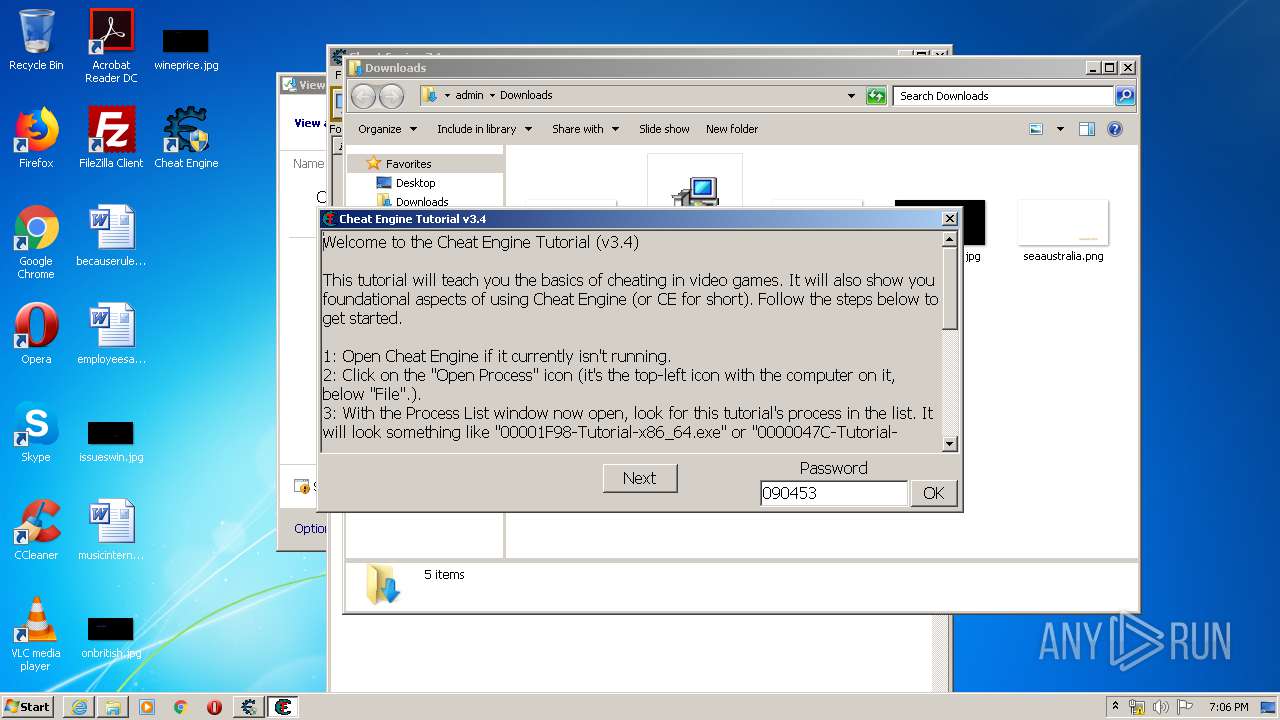
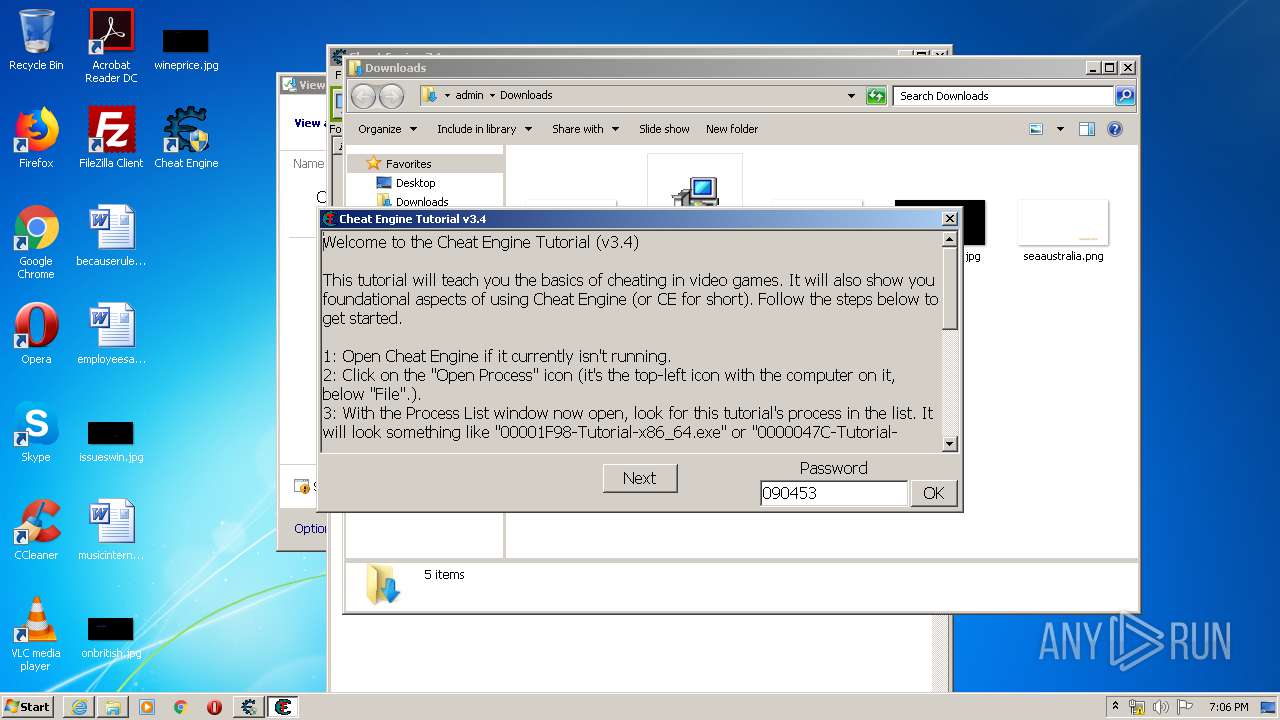
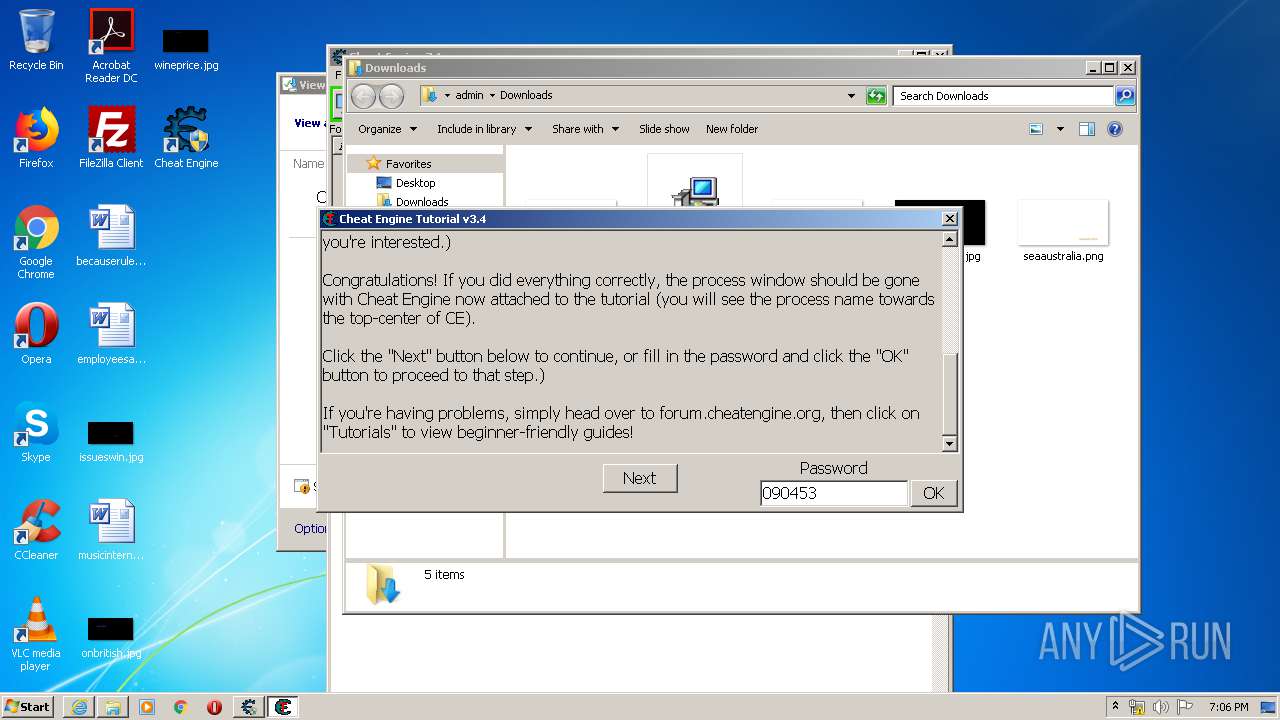
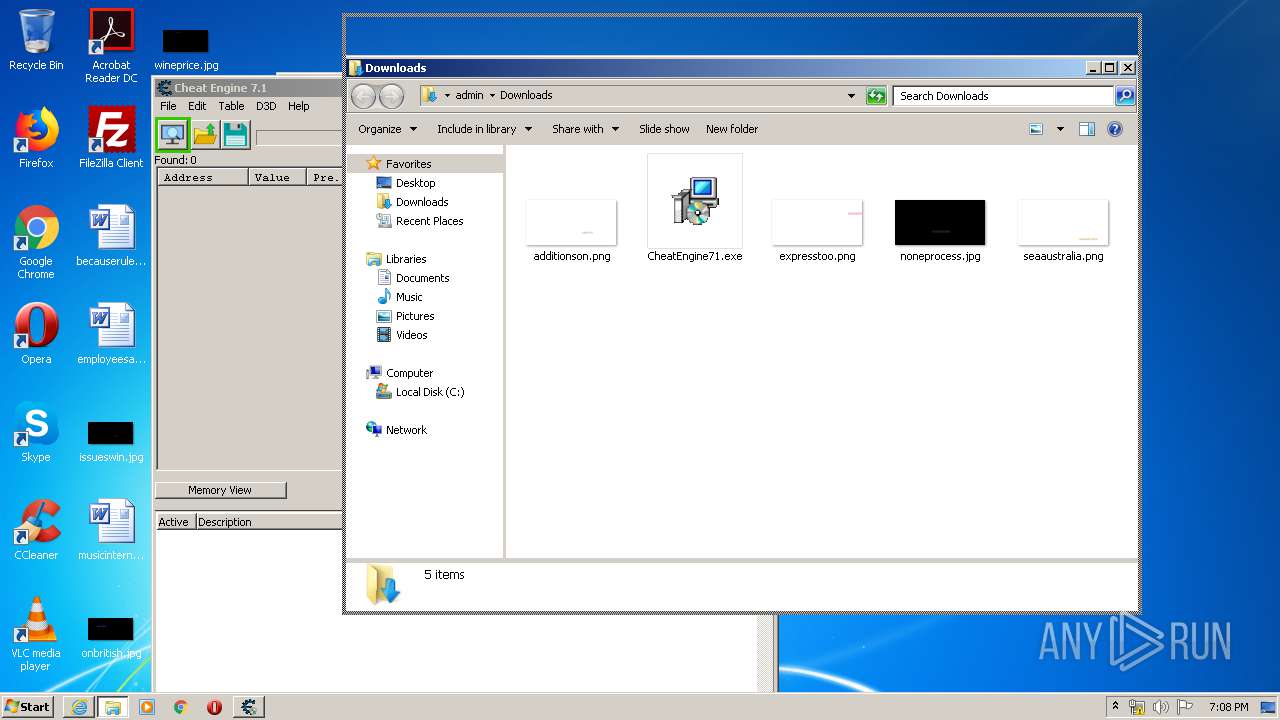
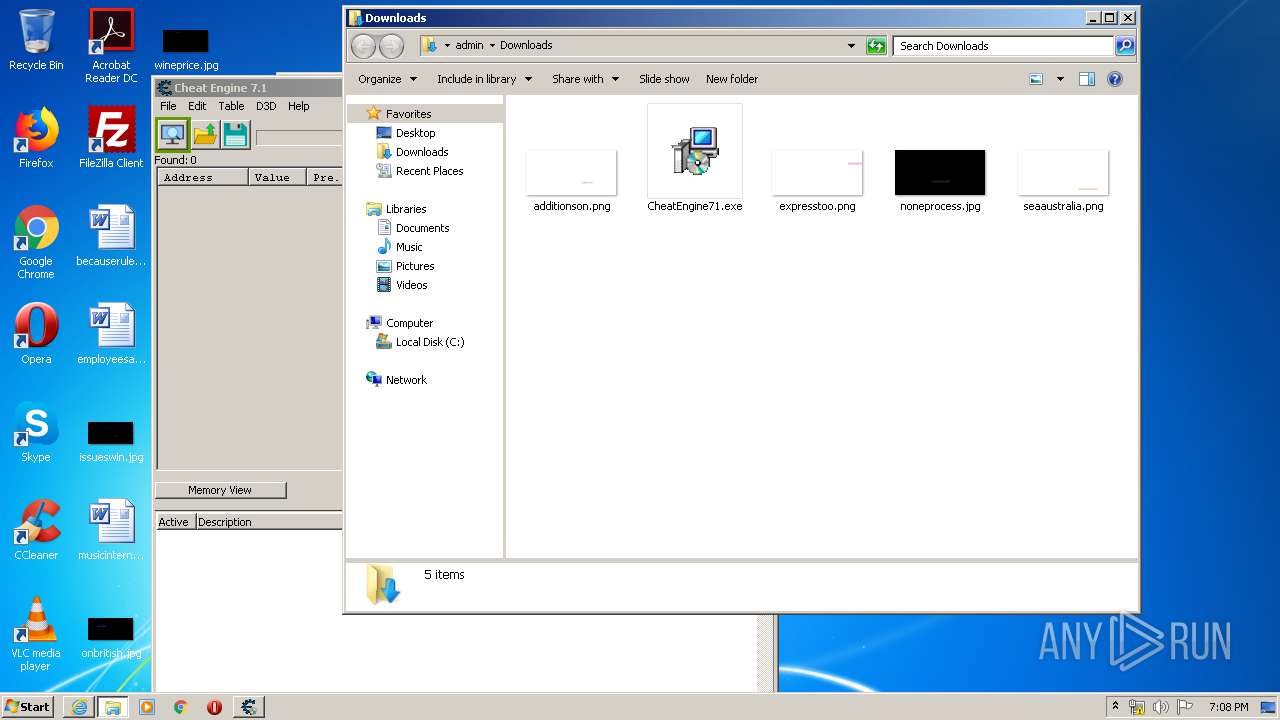
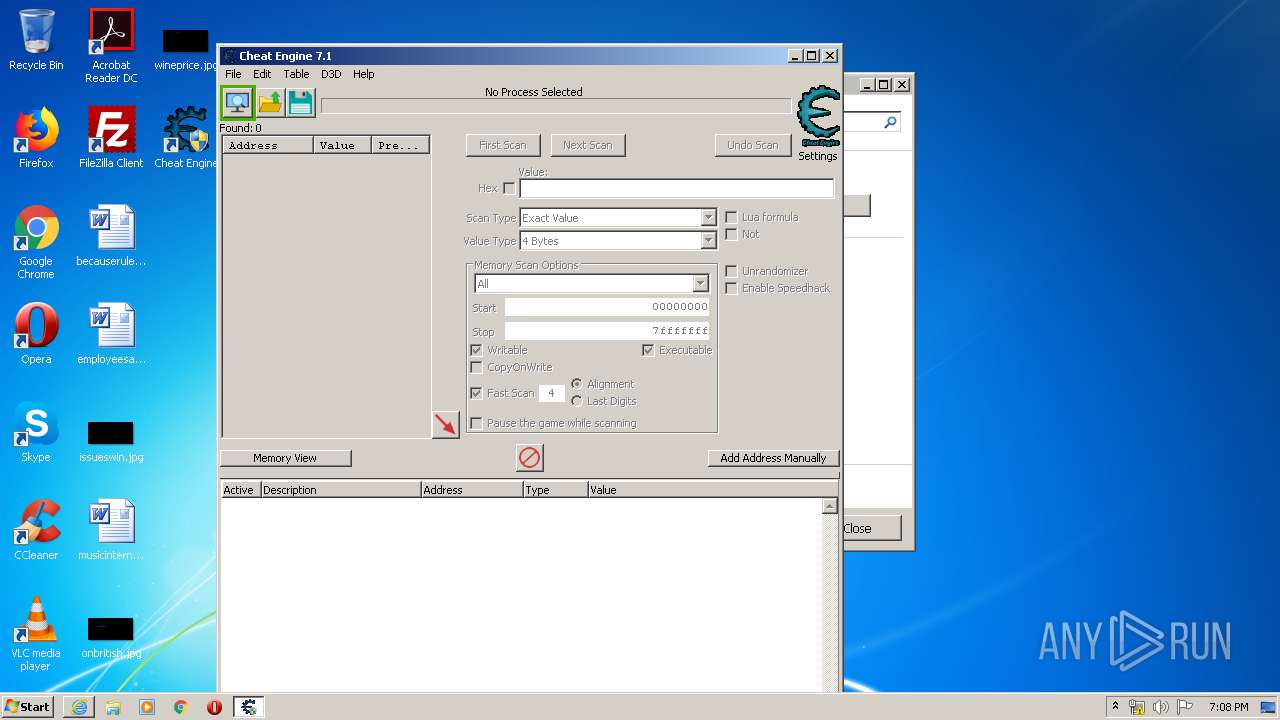
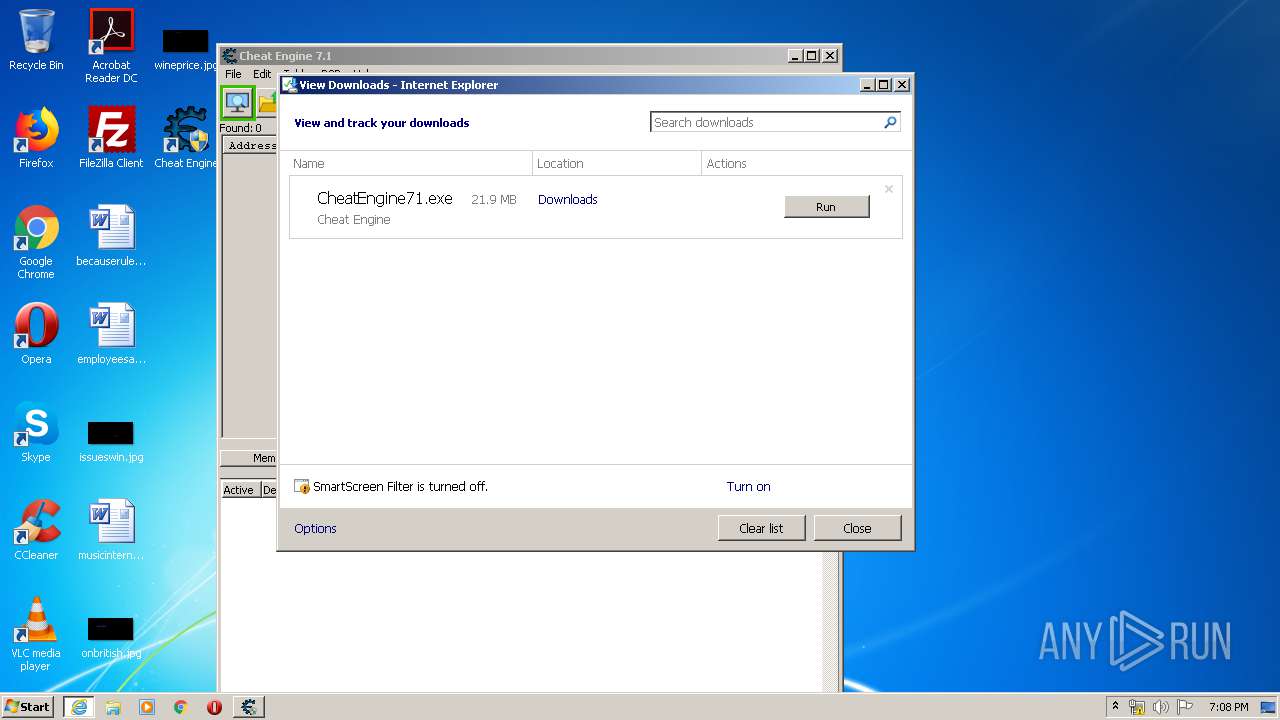
Manual execution by user
- CheatEngine71.exe (PID: 2172)
Changes internet zones settings
- iexplore.exe (PID: 3168)
Creates files in the user directory
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 3168)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3168)
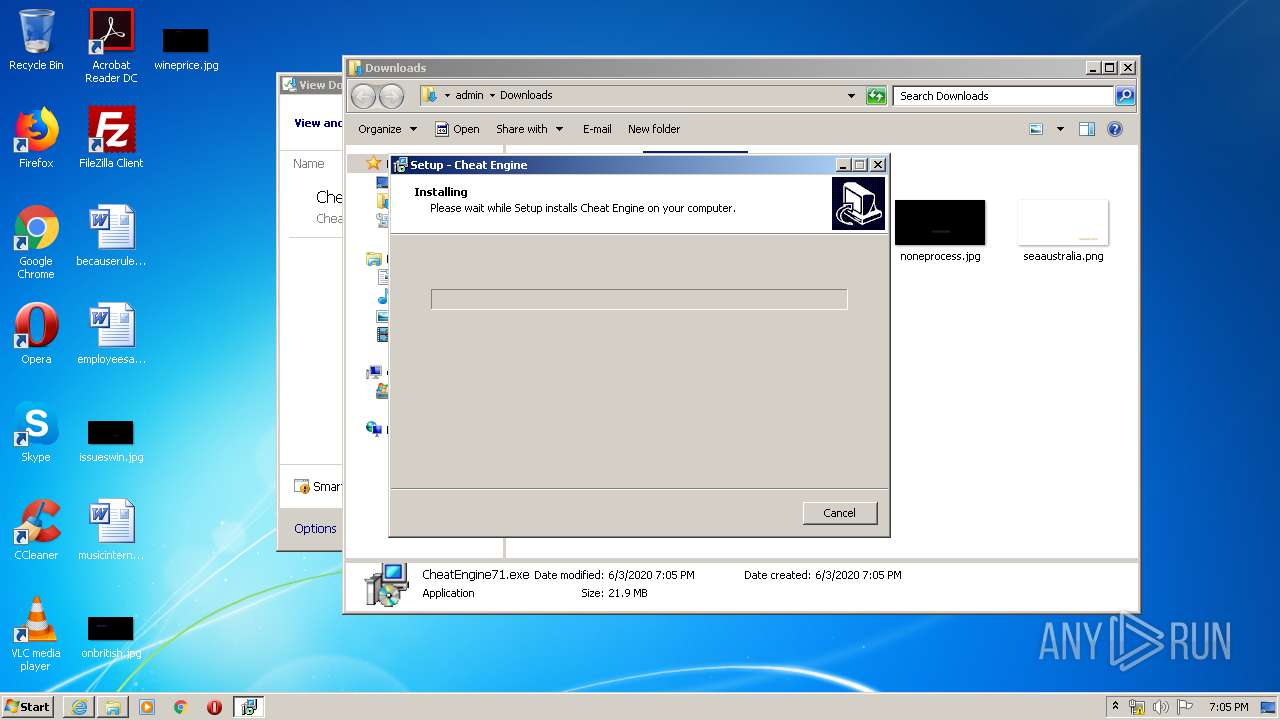
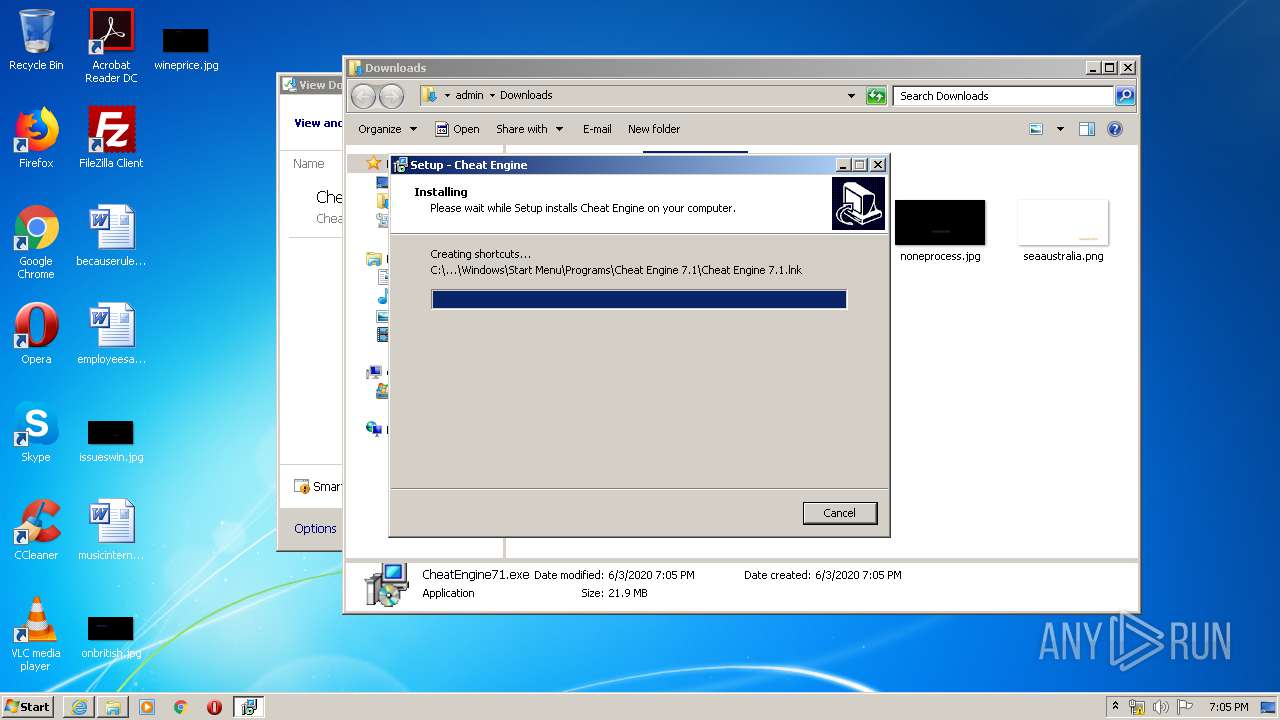
Application was dropped or rewritten from another process
- CheatEngine71.tmp (PID: 3152)
Loads dropped or rewritten executable
- CheatEngine71.tmp (PID: 3152)
Creates a software uninstall entry
- CheatEngine71.tmp (PID: 3152)
Reads settings of System Certificates
- cheatengine-i386.exe (PID: 2668)
- iexplore.exe (PID: 2964)
Creates files in the program directory
- CheatEngine71.tmp (PID: 3152)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3168)
Changes settings of System certificates
- iexplore.exe (PID: 3168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
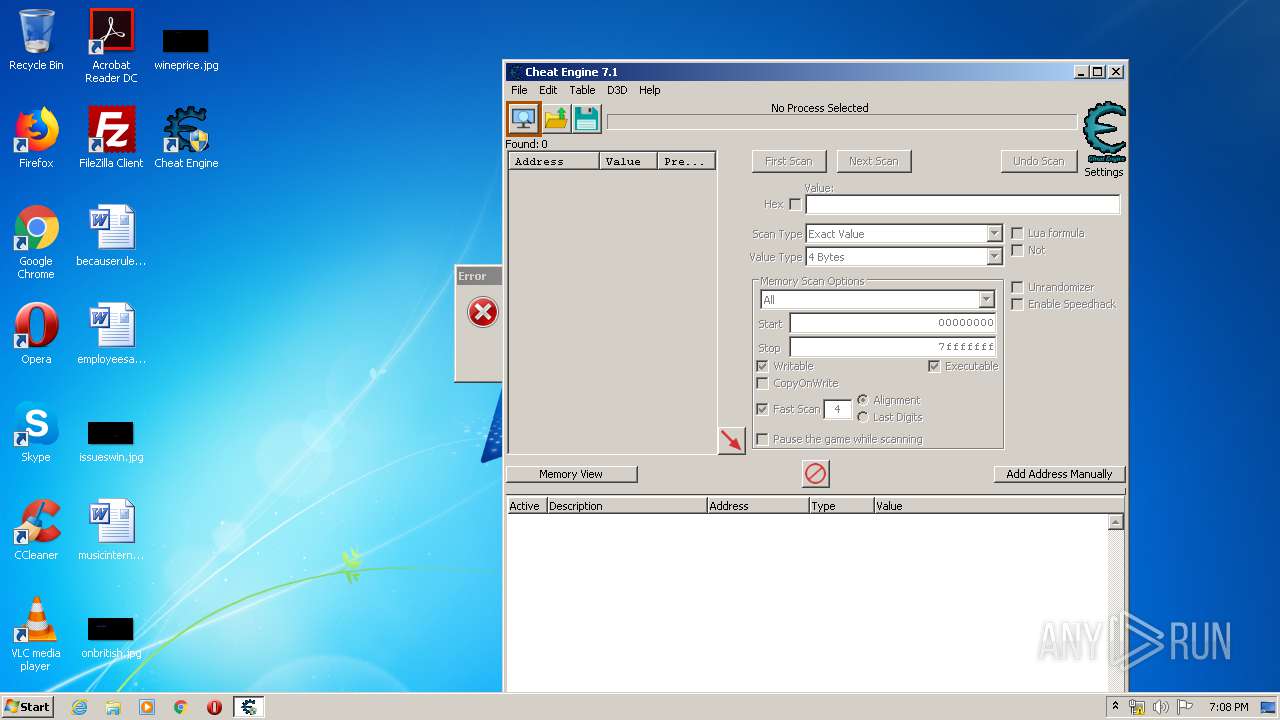
Total processes
53
Monitored processes
12
Malicious processes
5
Suspicious processes
1
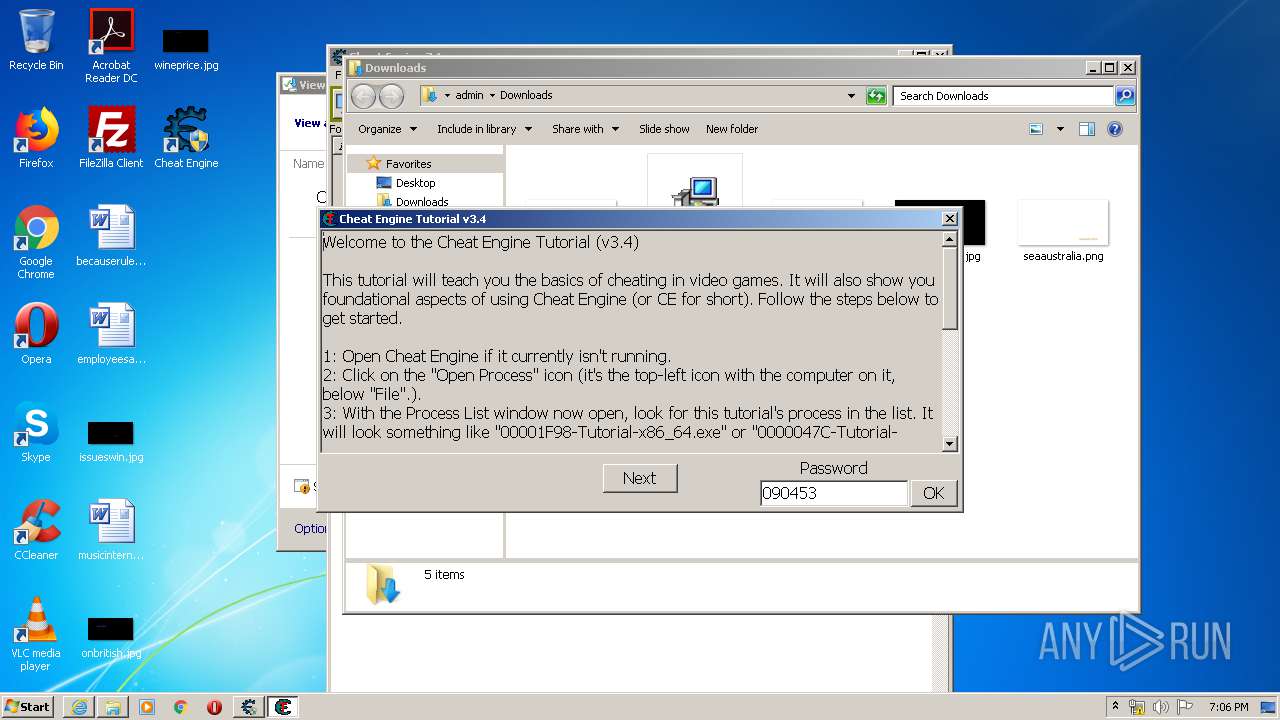
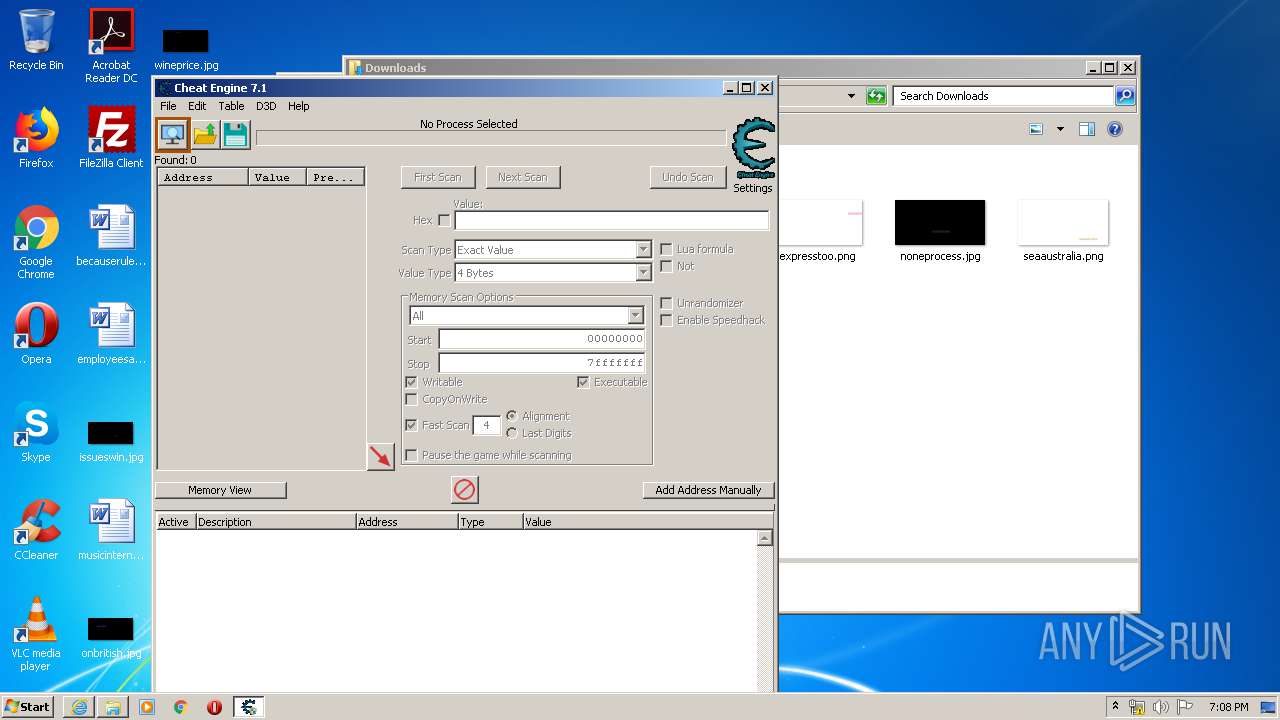
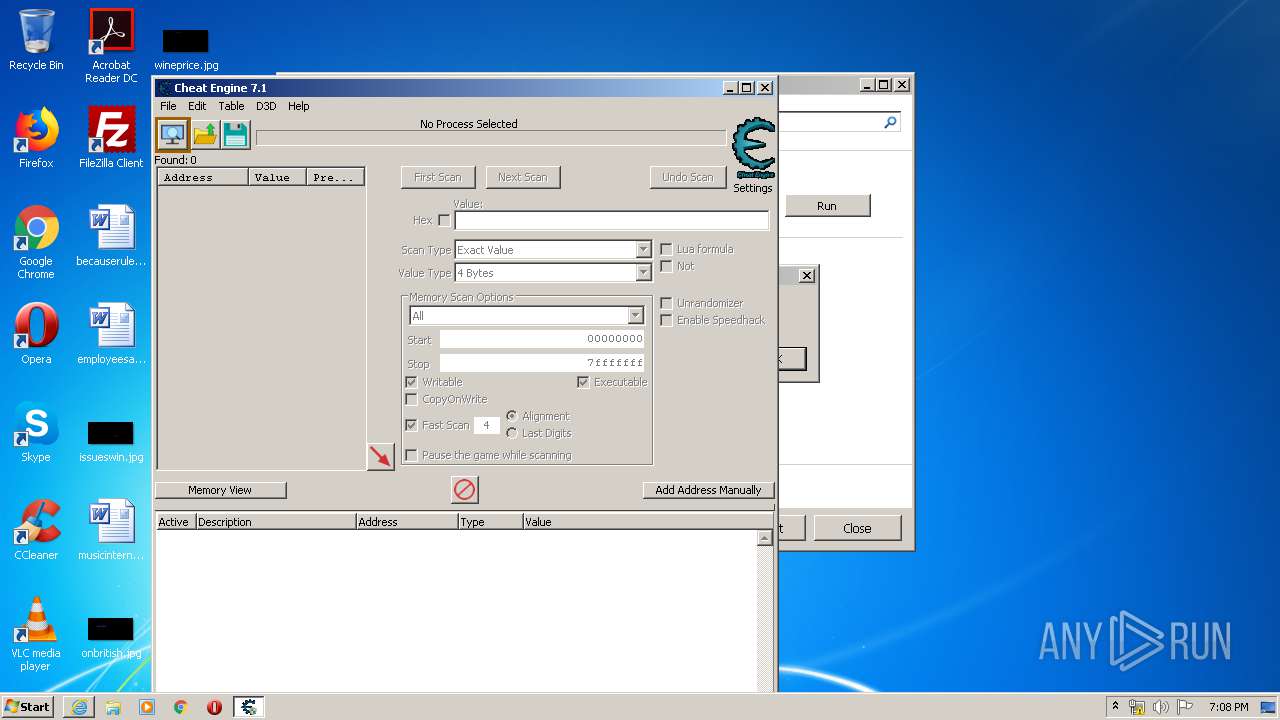
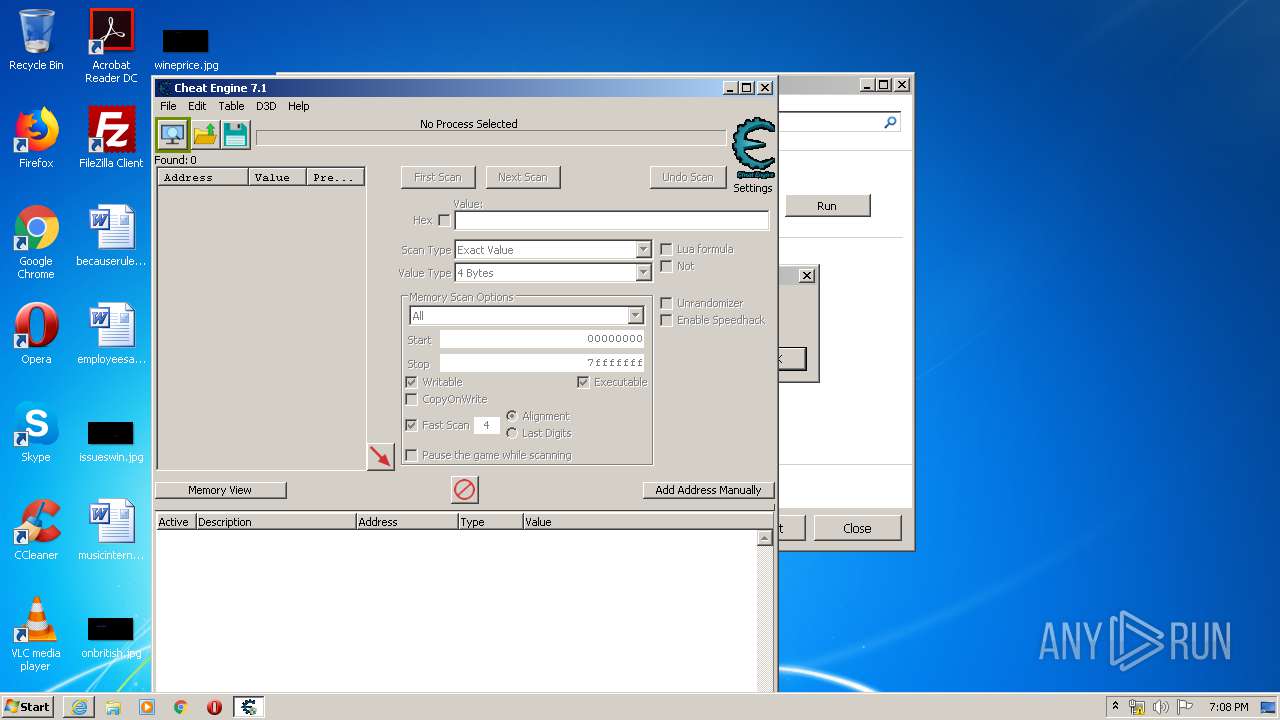
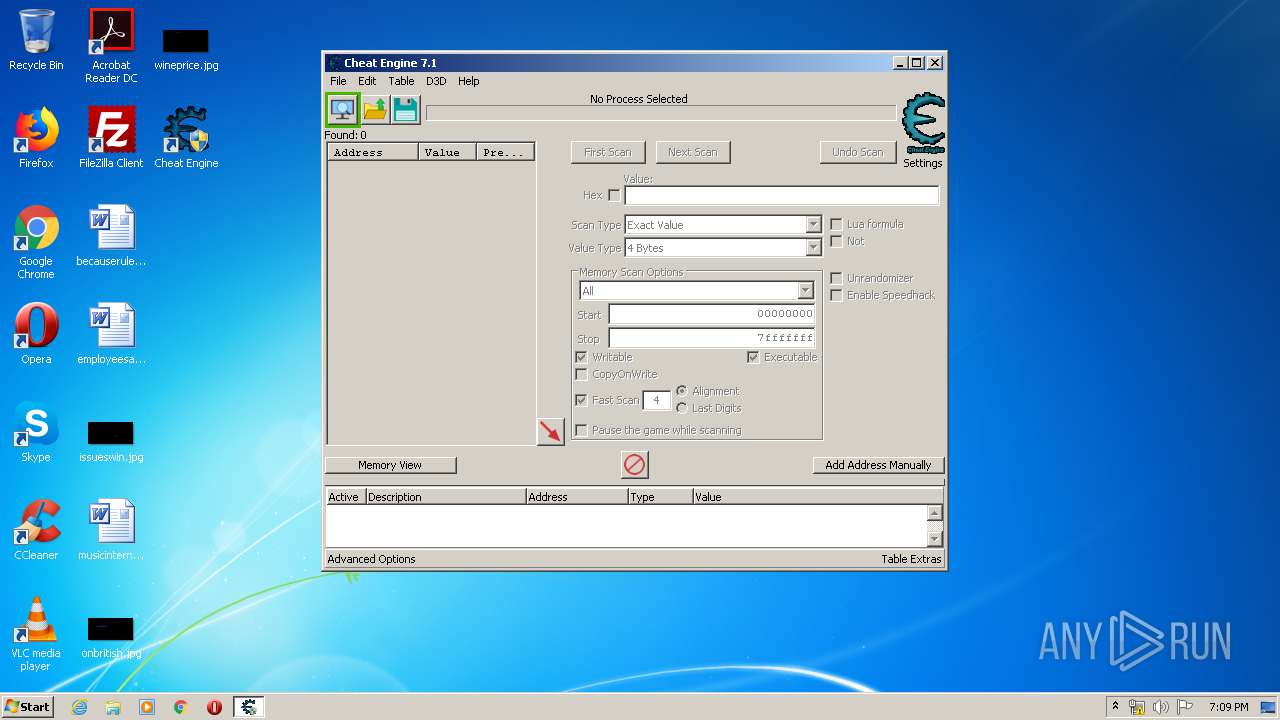
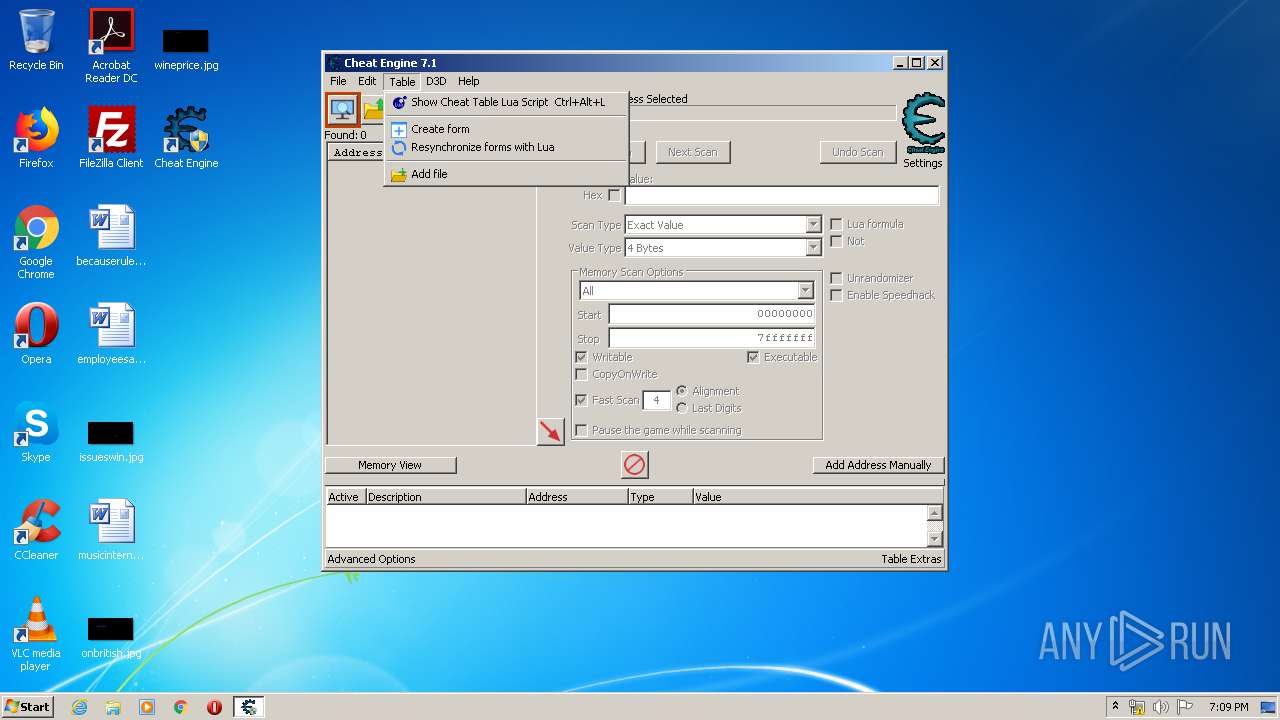
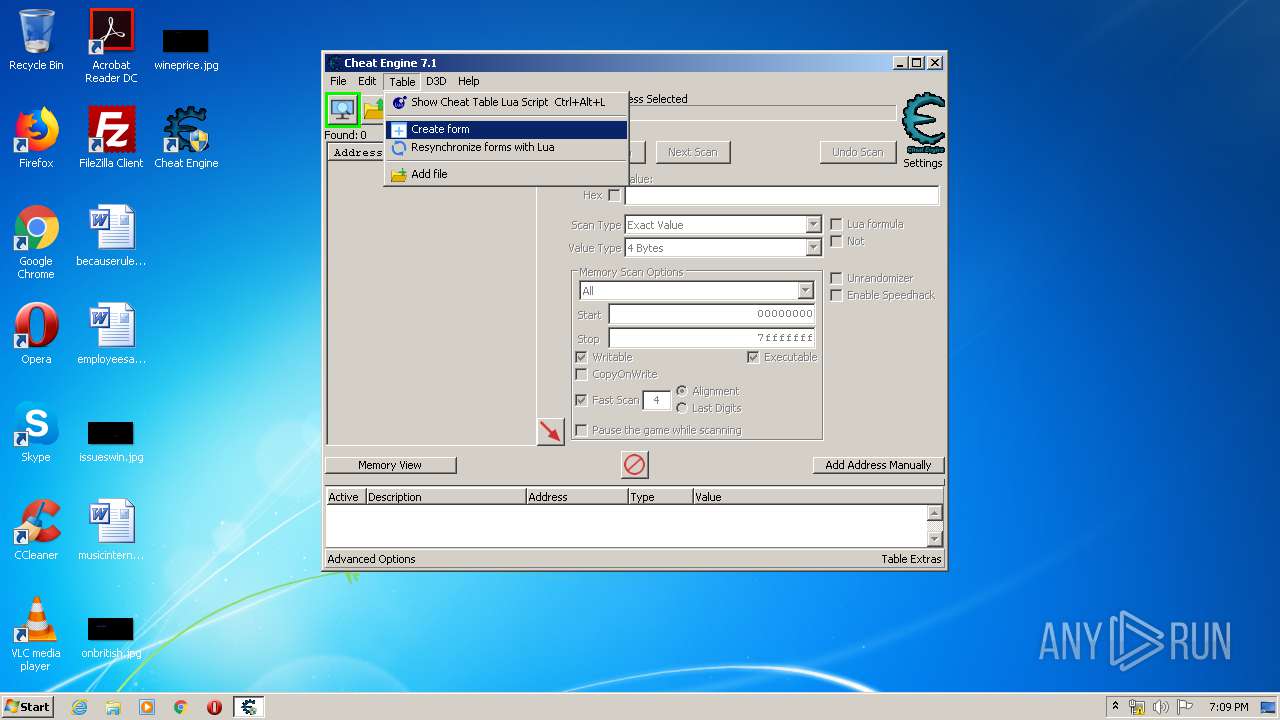
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2172 | "C:\Users\admin\Downloads\CheatEngine71.exe" | C:\Users\admin\Downloads\CheatEngine71.exe | explorer.exe | ||||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Cheat Engine Setup Exit code: 0 Version: 7.1.0.9 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Cheat Engine 7.1\Kernelmoduleunloader.exe" /SETUP | C:\Program Files\Cheat Engine 7.1\Kernelmoduleunloader.exe | CheatEngine71.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Cheat Engine 7.1\windowsrepair.exe" /s | C:\Program Files\Cheat Engine 7.1\windowsrepair.exe | — | CheatEngine71.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
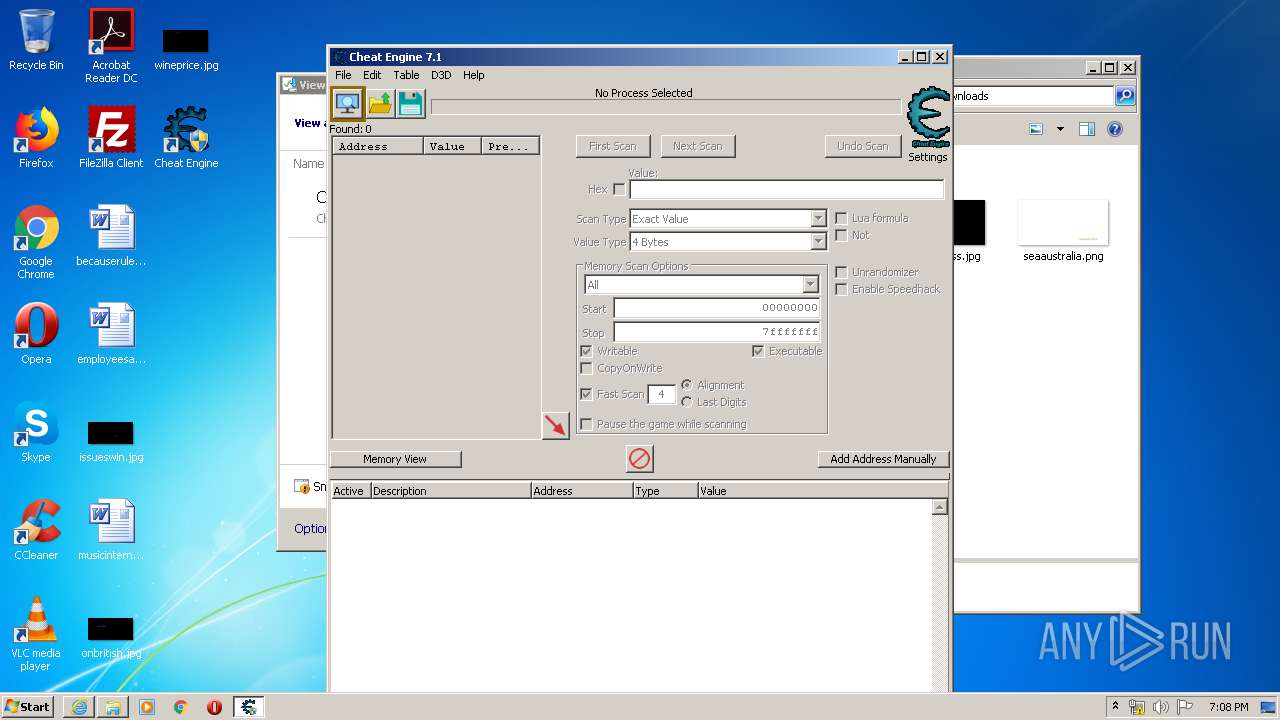
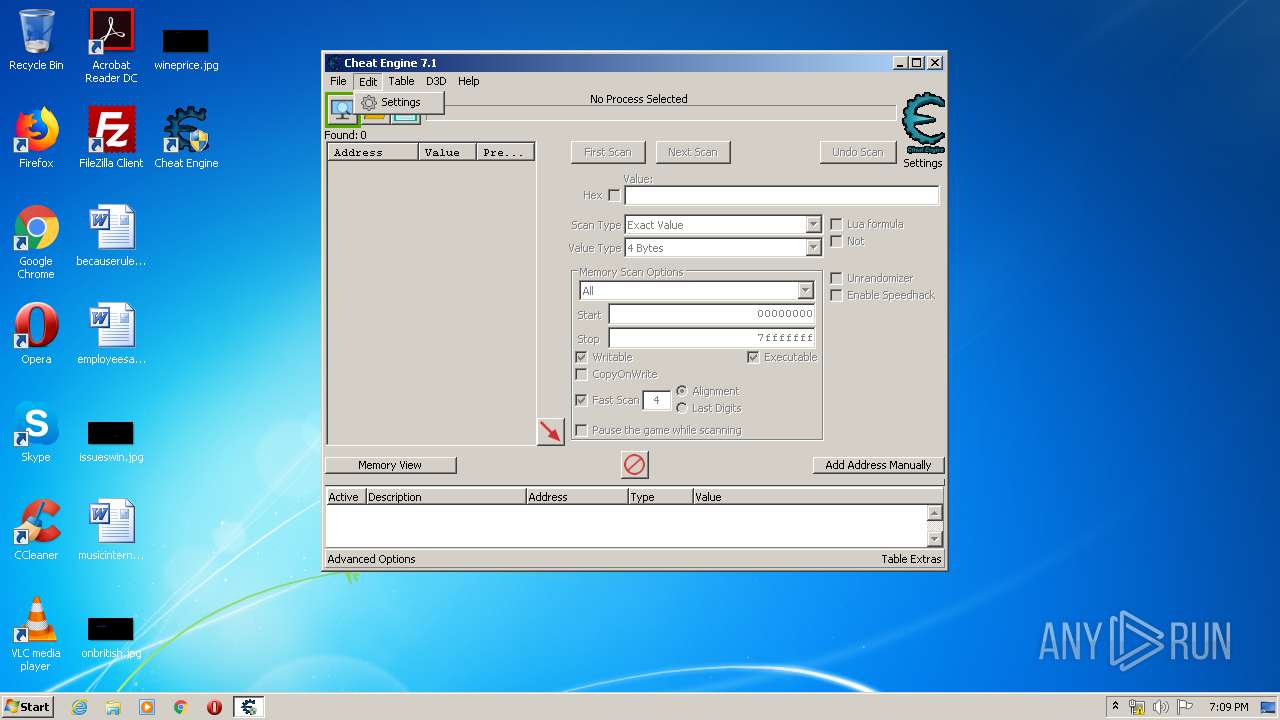
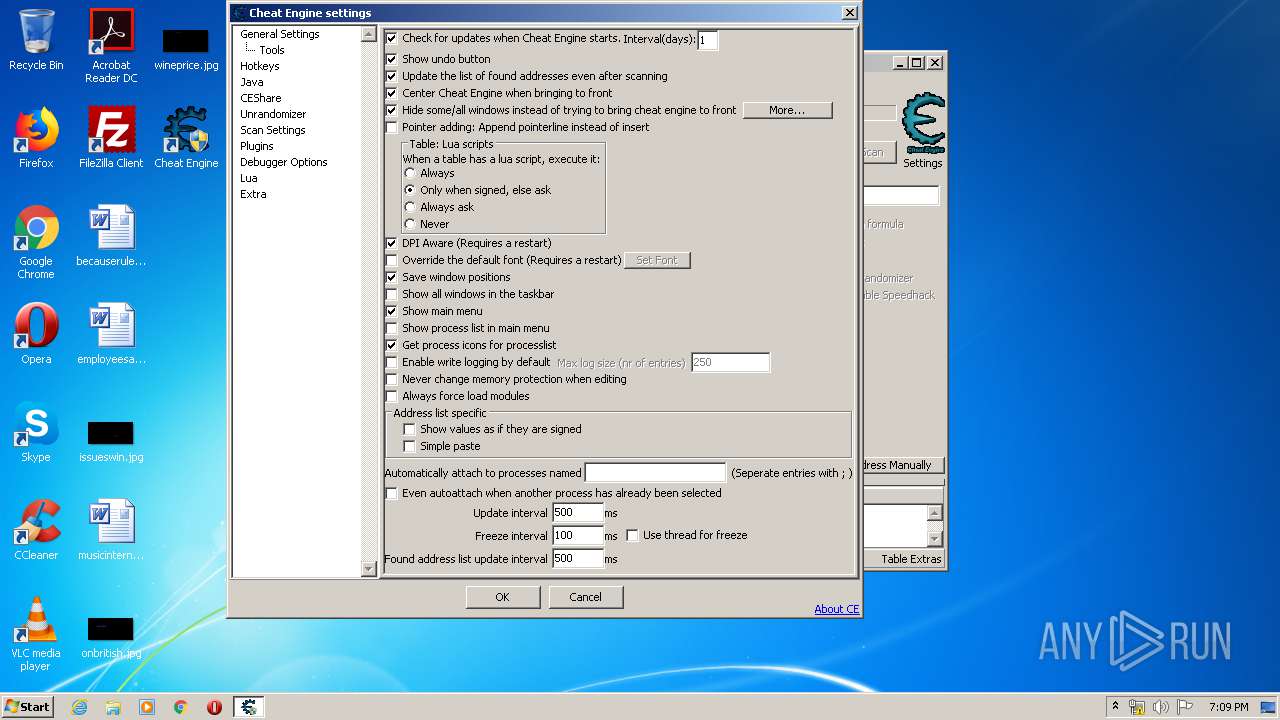
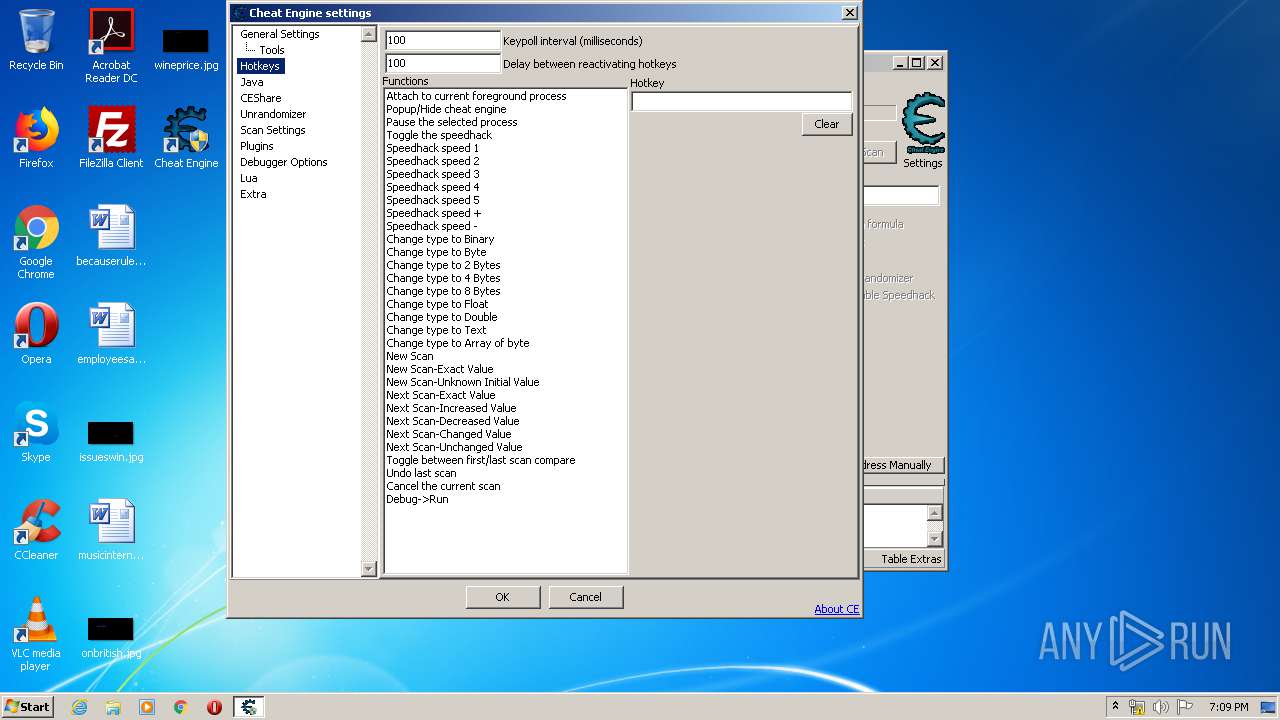
| 2668 | "C:\Program Files\Cheat Engine 7.1\cheatengine-i386.exe" | C:\Program Files\Cheat Engine 7.1\cheatengine-i386.exe | Cheat Engine.exe | ||||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Cheat Engine Exit code: 0 Version: 7.1.0.6341 Modules
| |||||||||||||||
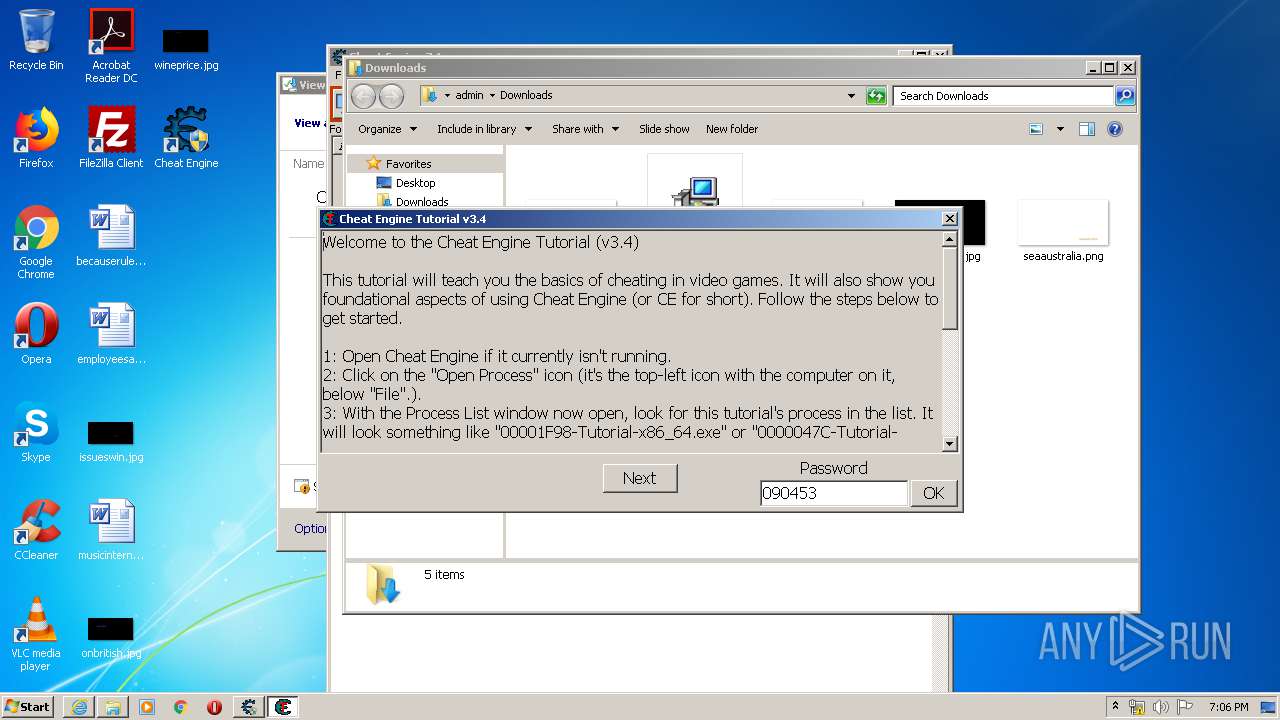
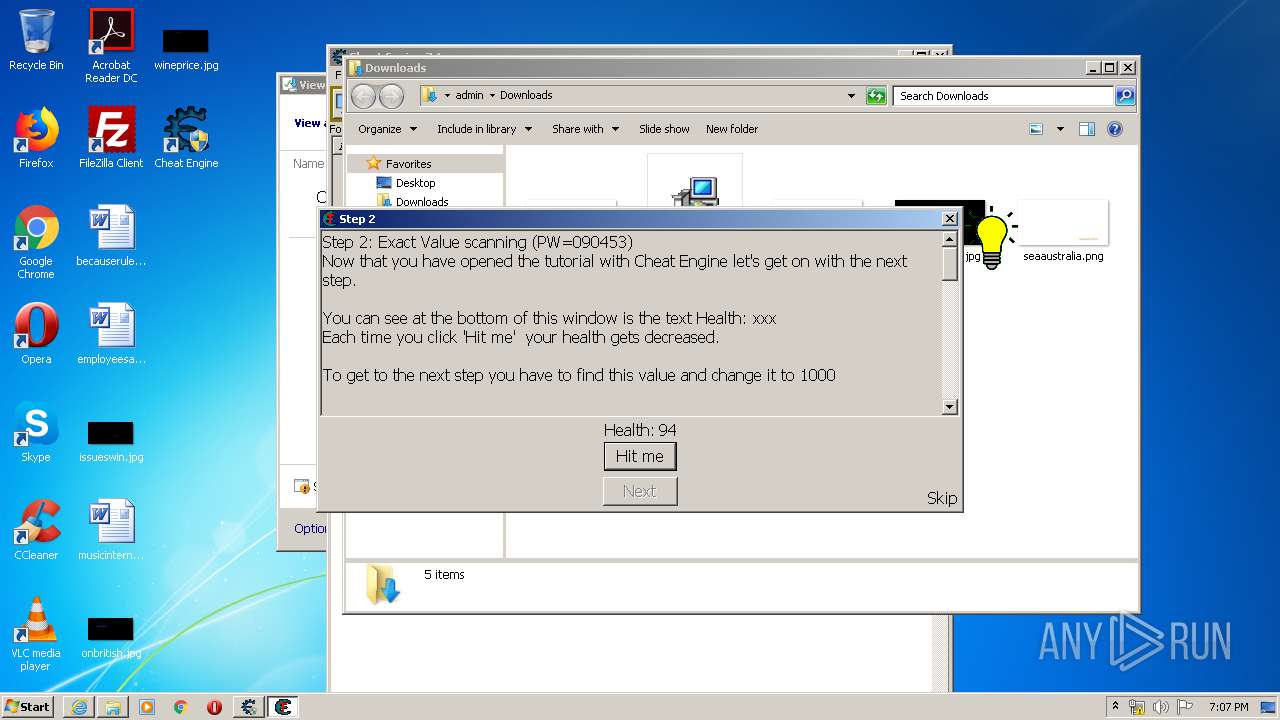
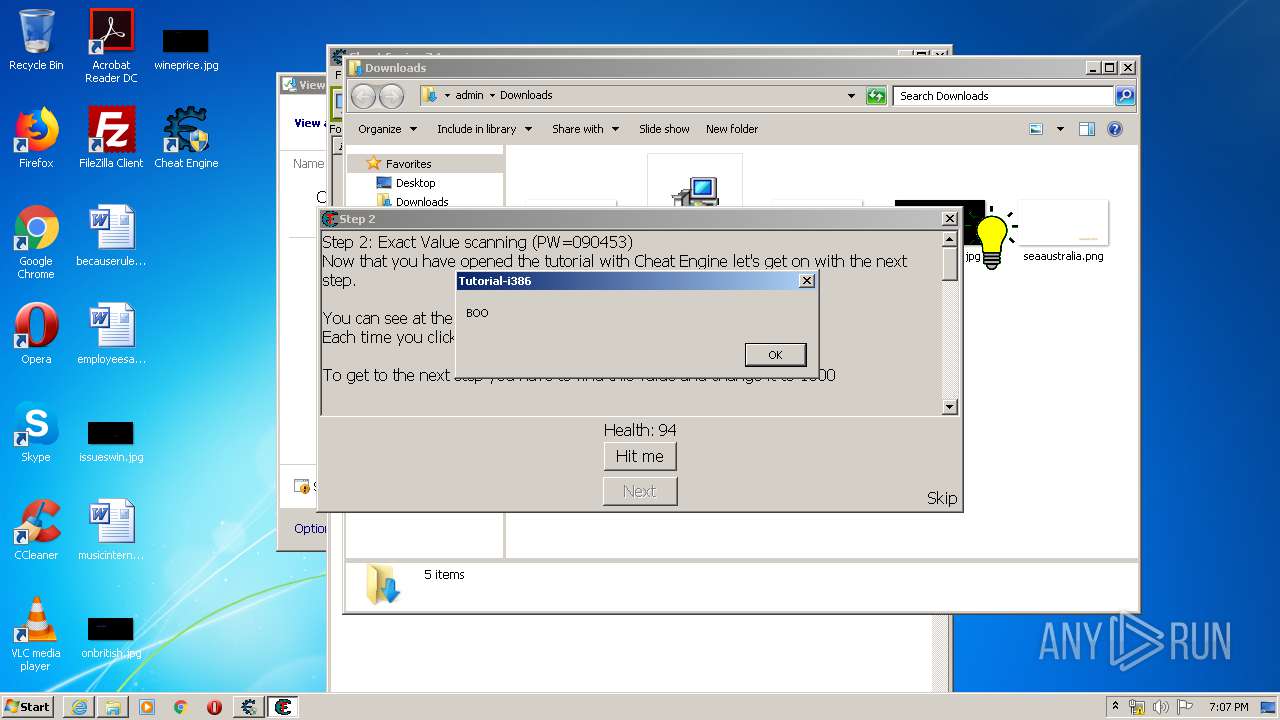
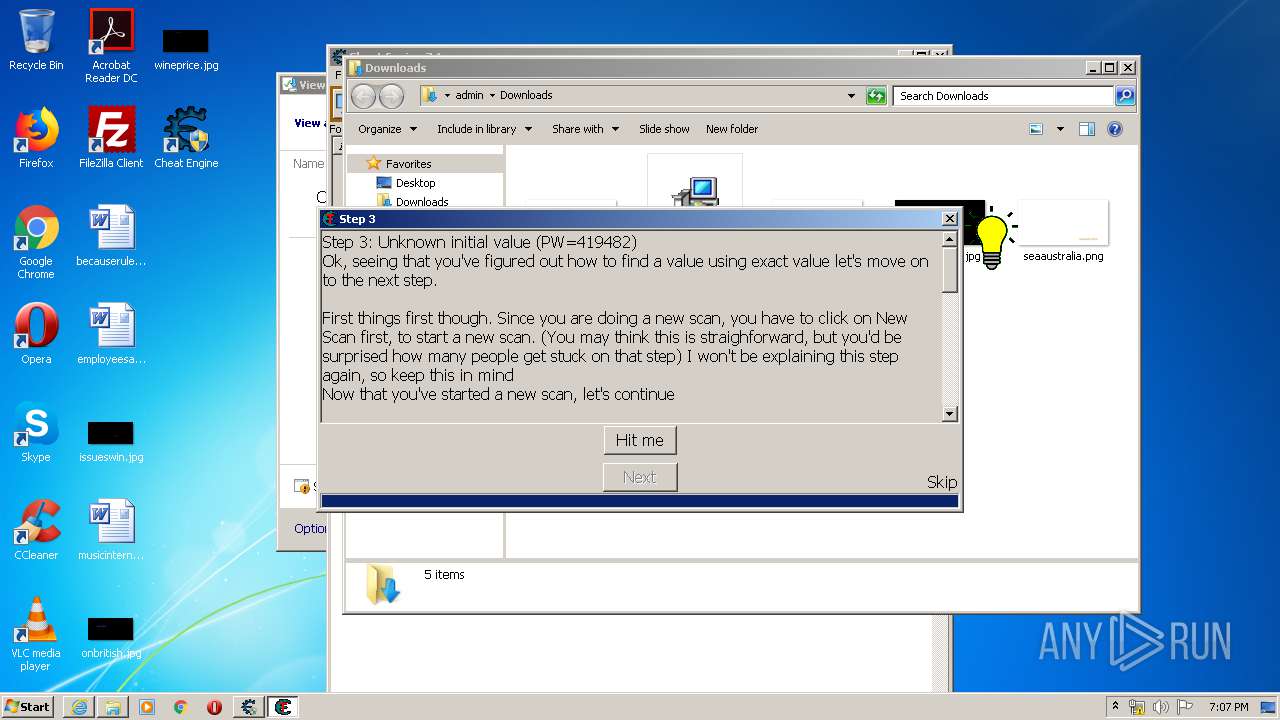
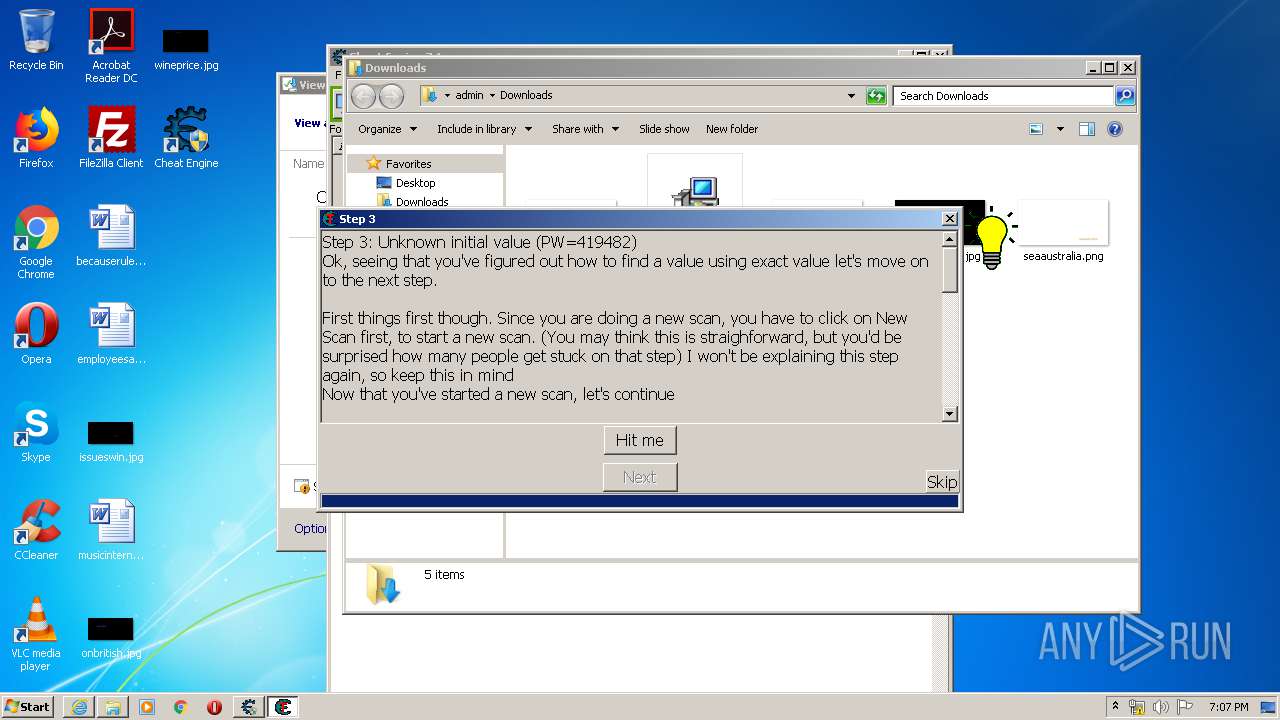
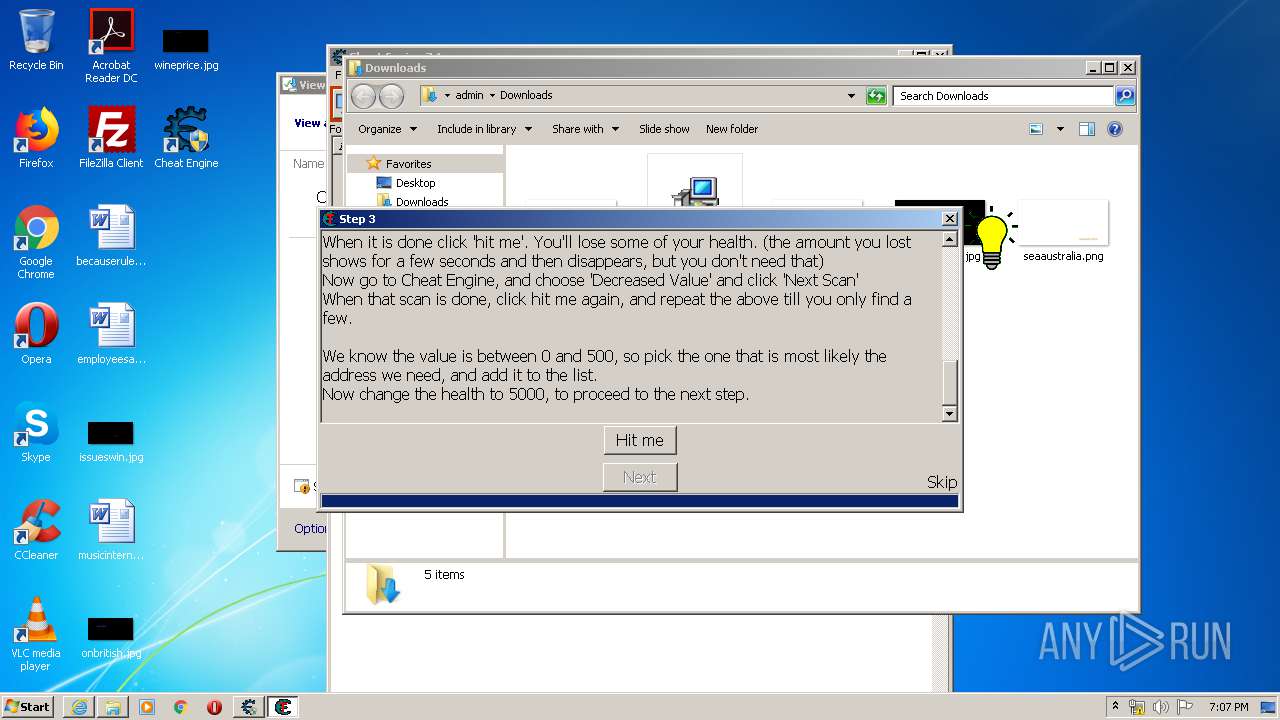
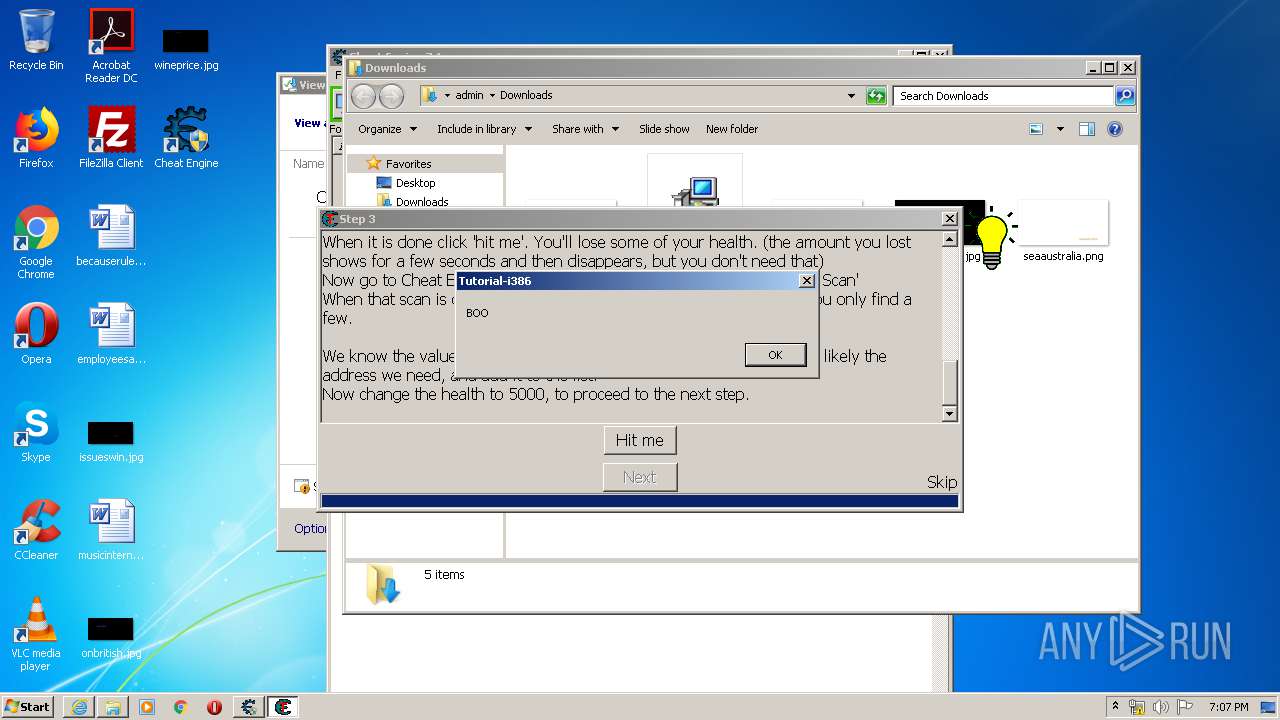
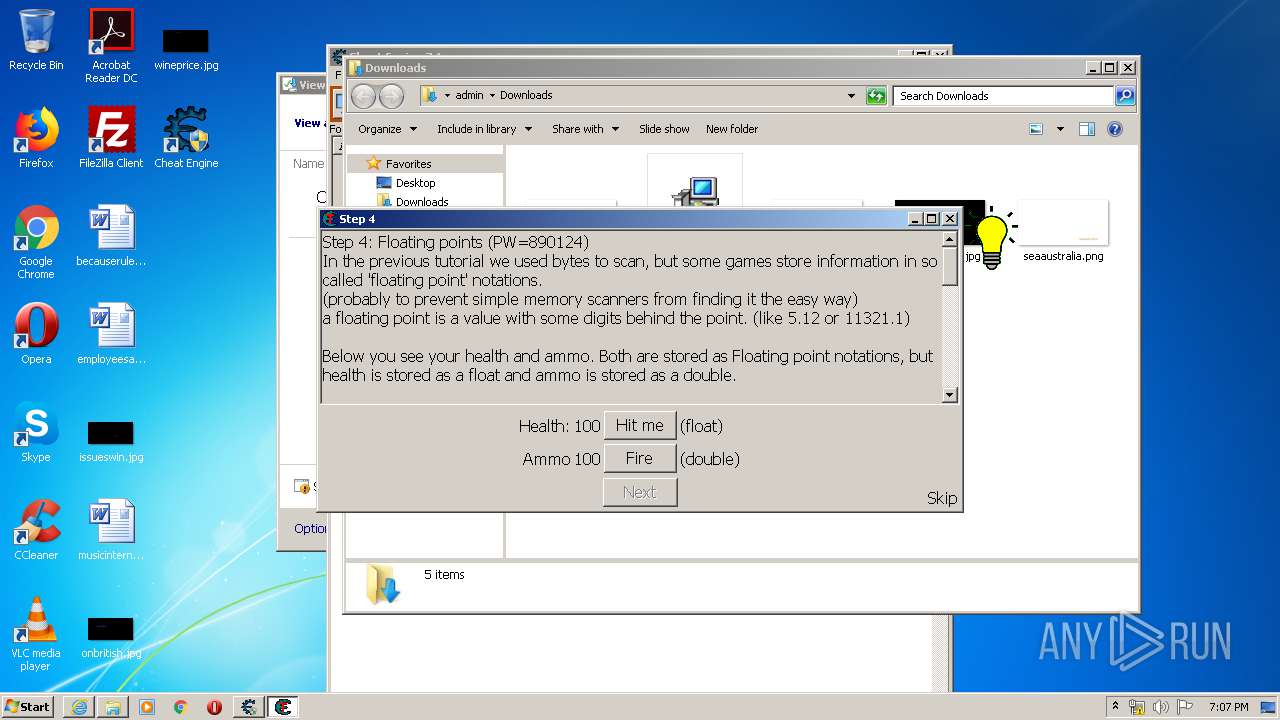
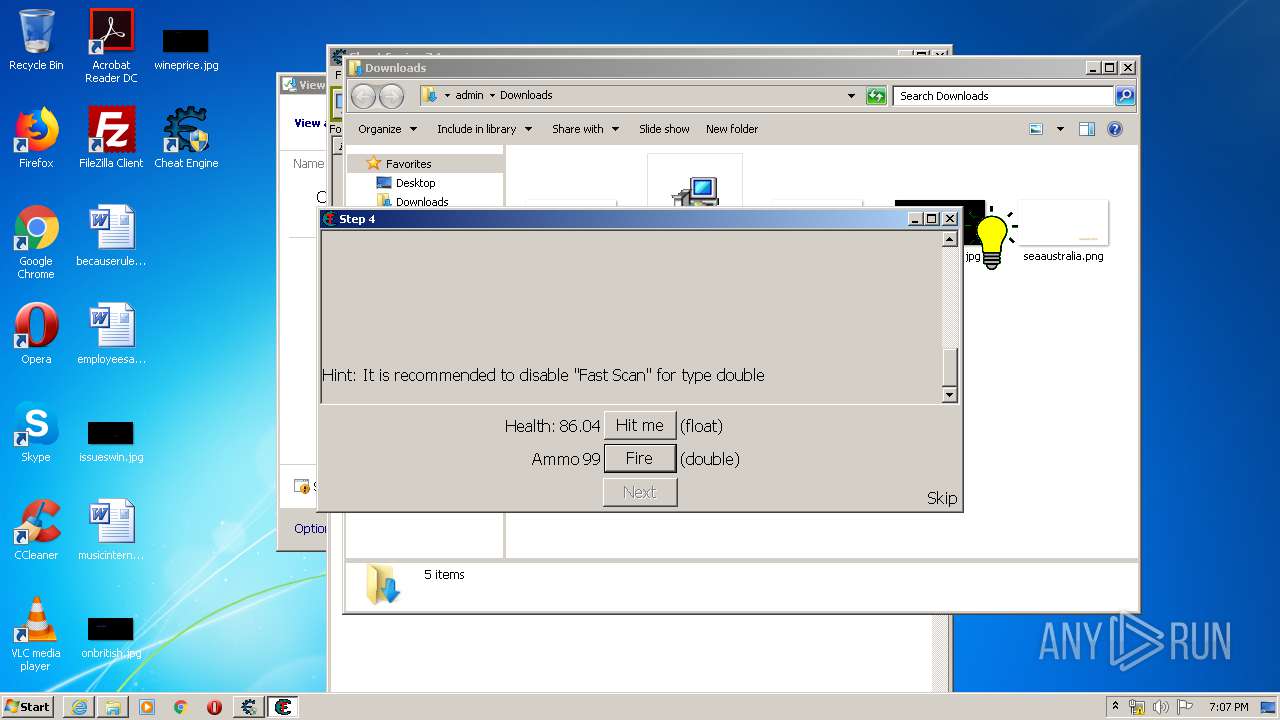
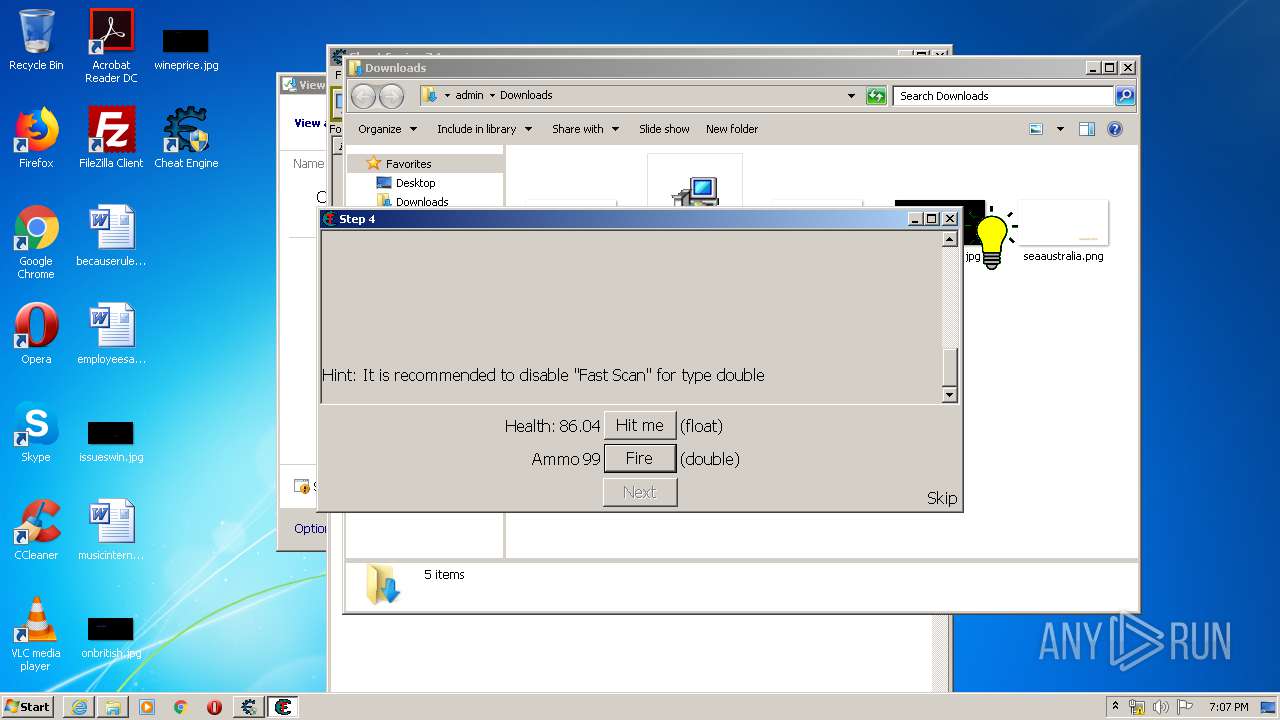
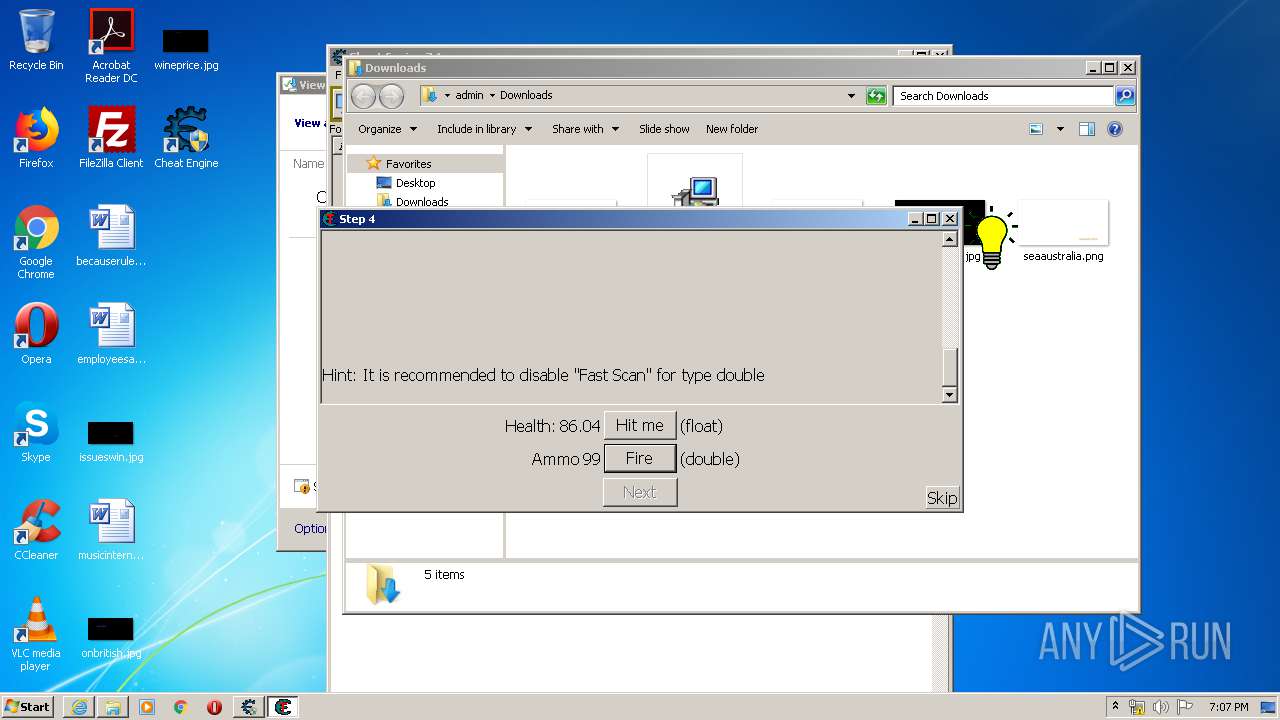
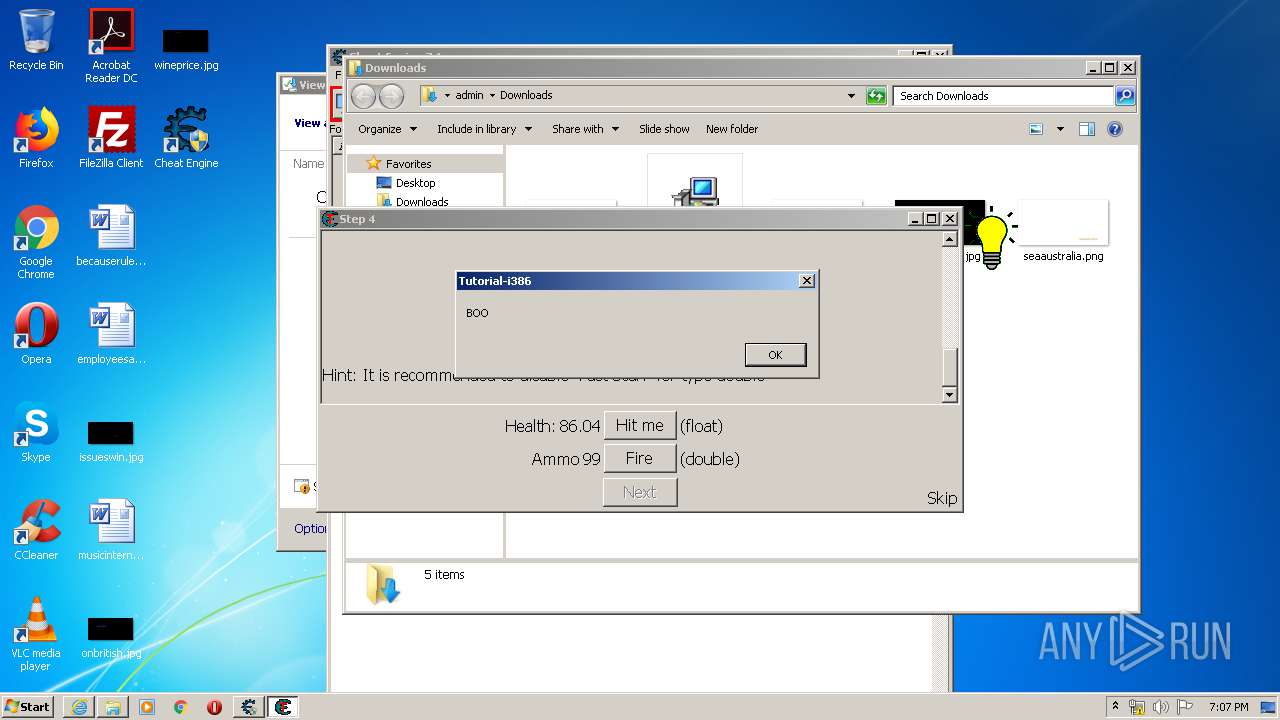
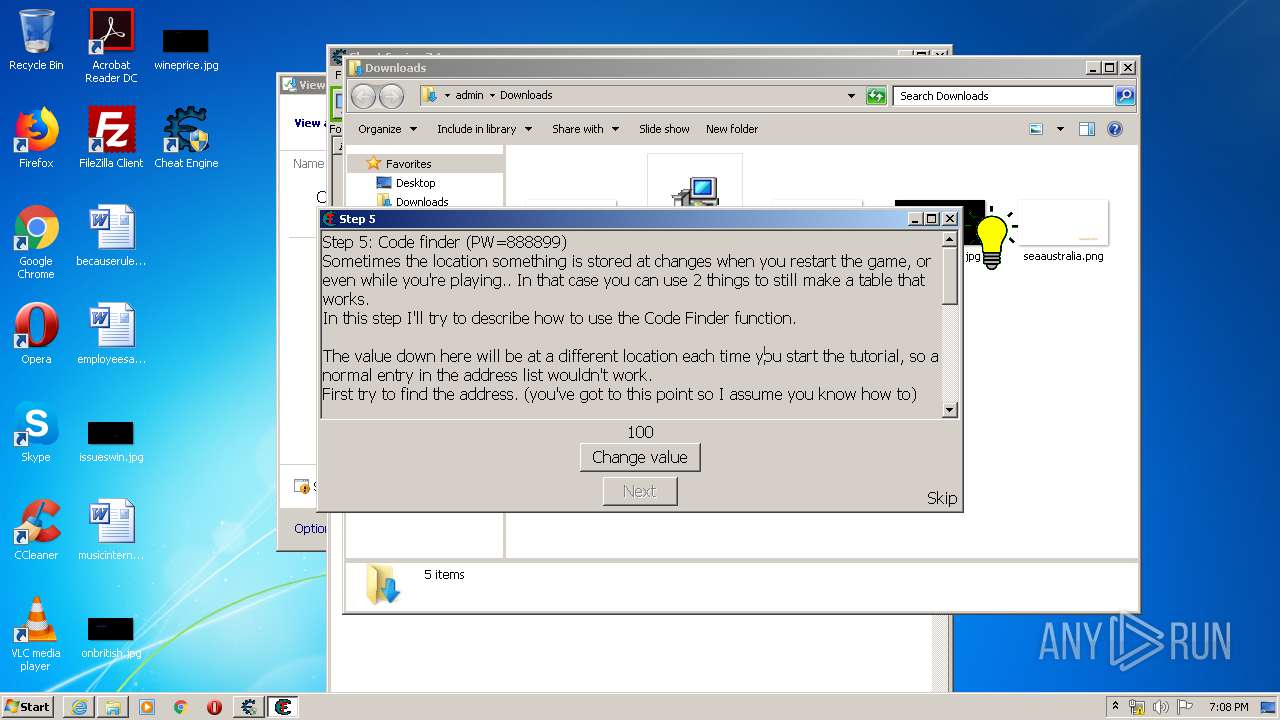
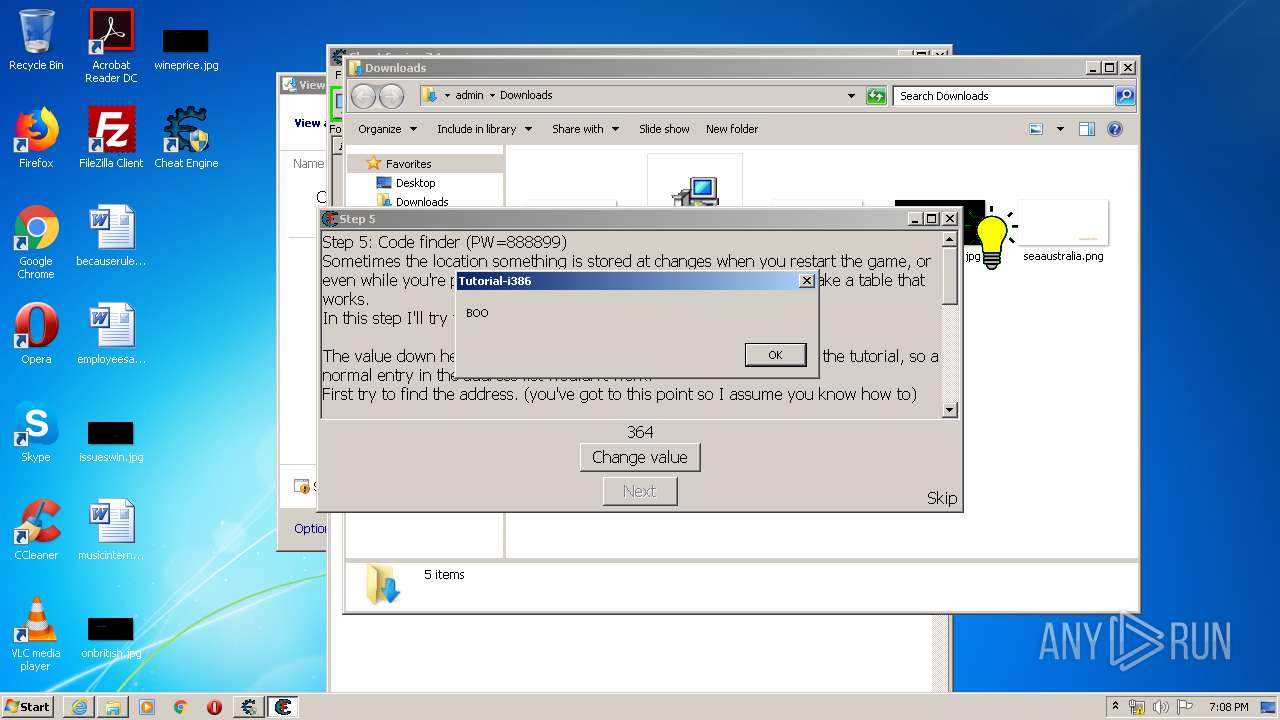
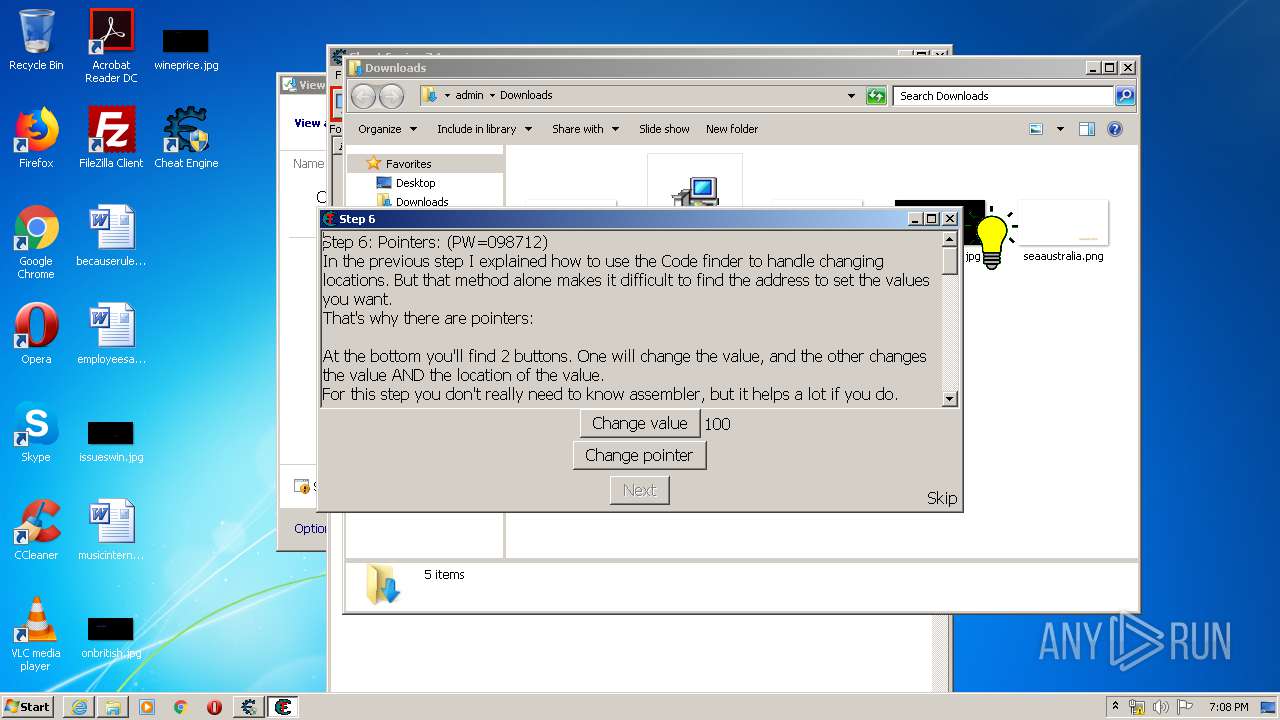
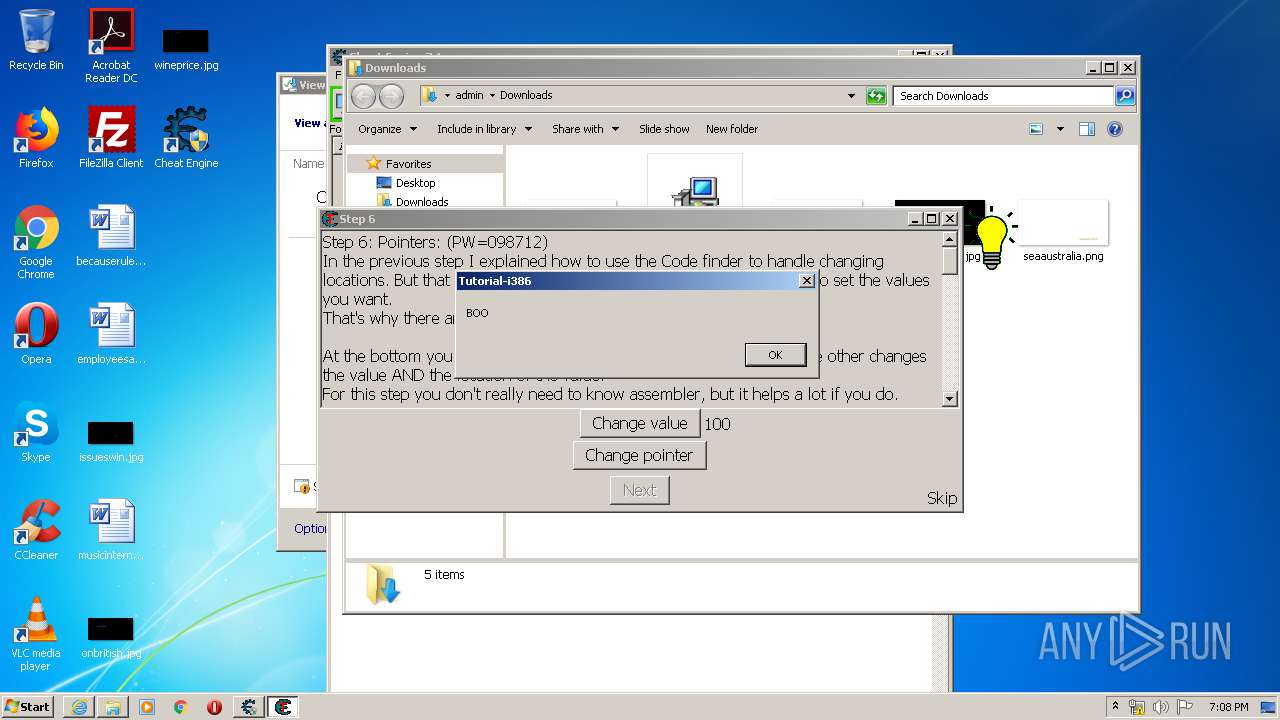
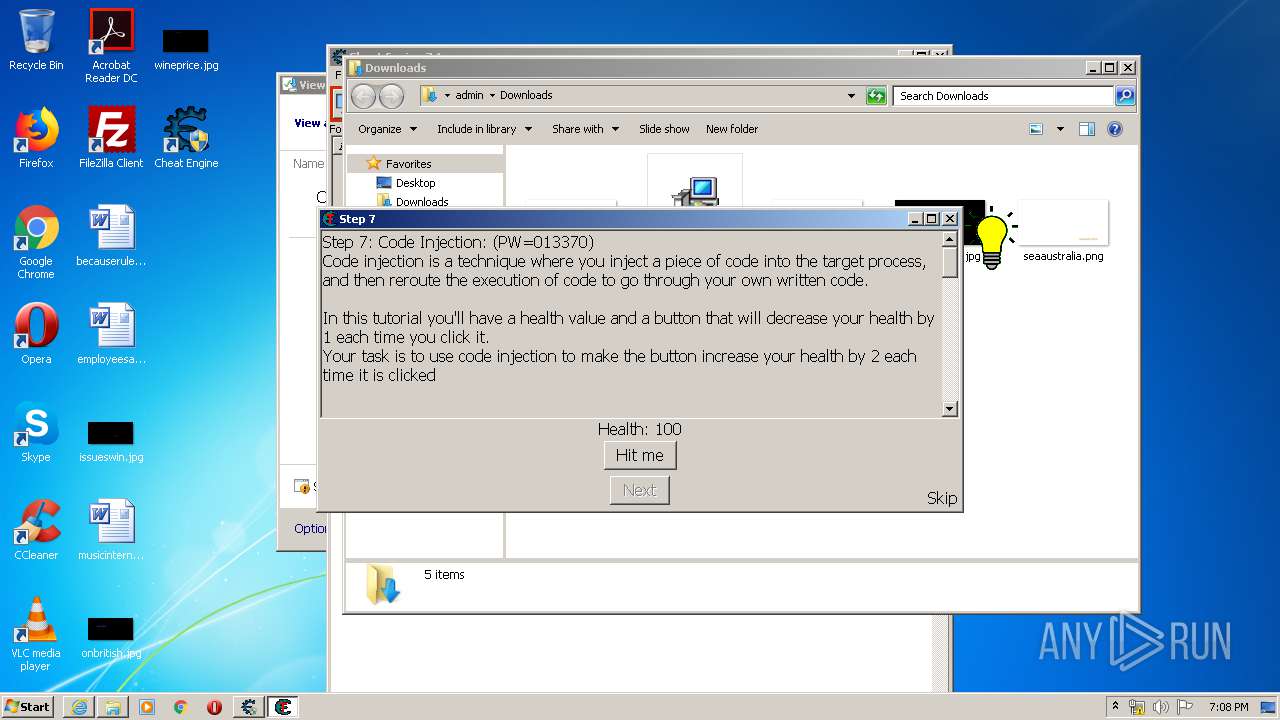
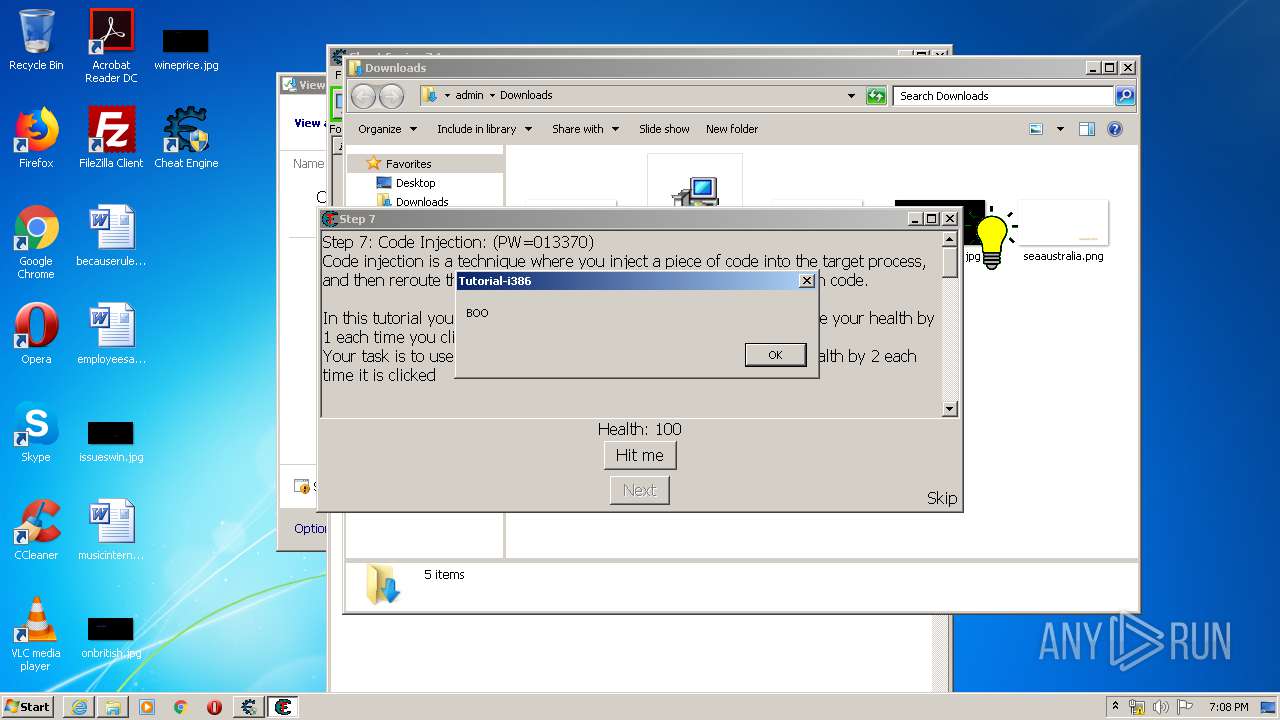
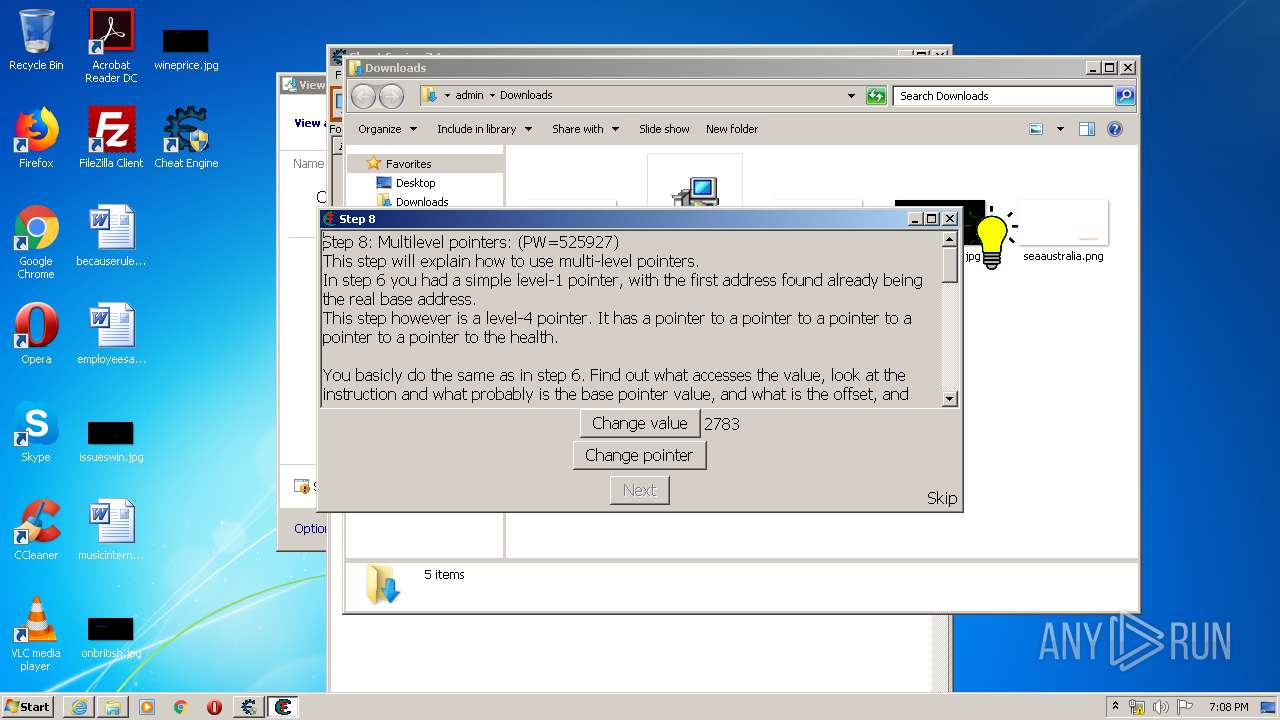
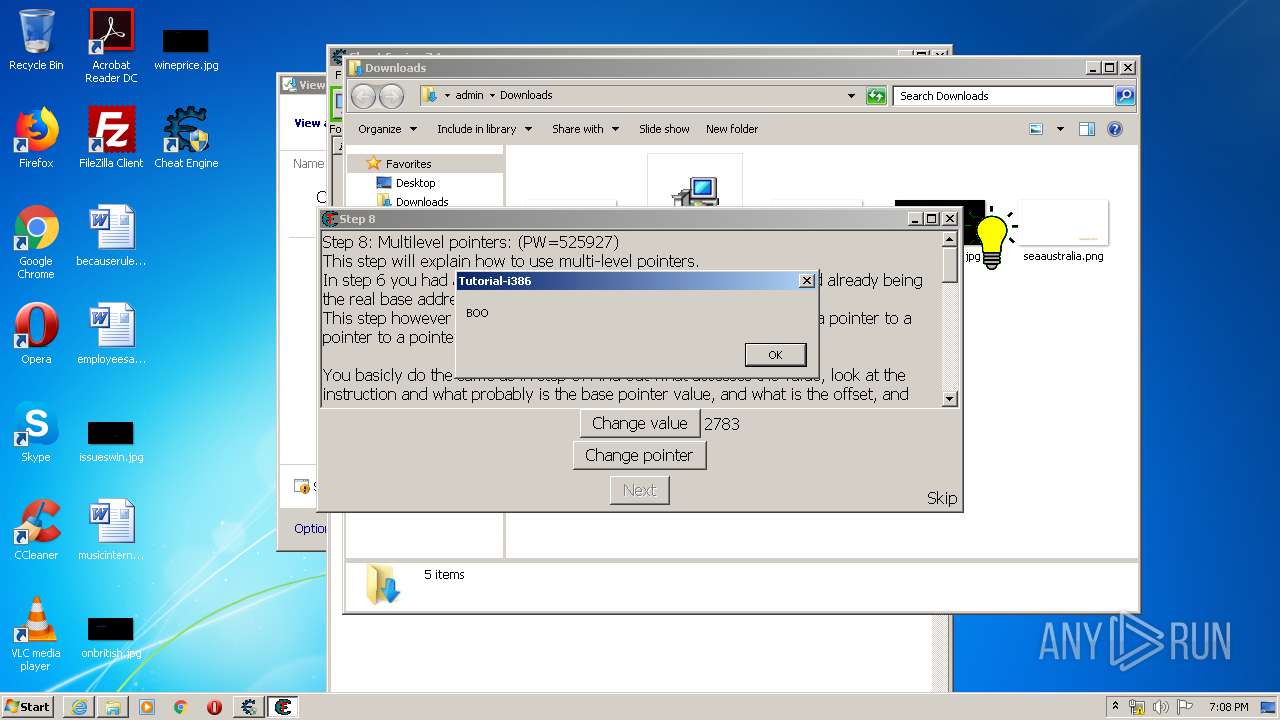
| 2752 | "C:\Program Files\Cheat Engine 7.1\Tutorial-i386.exe" | C:\Program Files\Cheat Engine 7.1\Tutorial-i386.exe | — | cheatengine-i386.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\Cheat Engine 7.1\Cheat Engine.exe" | C:\Program Files\Cheat Engine 7.1\Cheat Engine.exe | — | CheatEngine71.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 6.3.0.0 Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3168 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3152 | "C:\Users\admin\AppData\Local\Temp\is-M7TBC.tmp\CheatEngine71.tmp" /SL5="$401DA,22591019,121344,C:\Users\admin\Downloads\CheatEngine71.exe" | C:\Users\admin\AppData\Local\Temp\is-M7TBC.tmp\CheatEngine71.tmp | CheatEngine71.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3168 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/cheat-engine/cheat-engine/releases/download/7.1/CheatEngine71.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3928 | "C:\Program Files\Cheat Engine 7.1\ceregreset.exe" -silent -dontdeletecustomtypes -dontdeleteversioncheck | C:\Program Files\Cheat Engine 7.1\ceregreset.exe | — | CheatEngine71.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
6 122
Read events
1 193
Write events
3 717
Delete events
1 212
Modification events
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2271586084 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30816721 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
62
Suspicious files
32
Text files
194
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabD981.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarD982.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\YBH7GO31.txt | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\Downloads\CheatEngine71.exe.jby9r2u.partial | — | |
MD5:— | SHA256:— | |||
| 3168 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5A88EC9B89D02E0C.TMP | — | |
MD5:— | SHA256:— | |||
| 3168 | iexplore.exe | C:\Users\admin\Downloads\CheatEngine71.exe.jby9r2u.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3152 | CheatEngine71.tmp | C:\Users\admin\AppData\Local\Temp\0016AD2D.log | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_EE9DB89C3D6A328B5FEAFF0ED3C77874 | der | |
MD5:— | SHA256:— | |||
| 3168 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{B32241E5-A5C4-11EA-A1F6-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
21
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
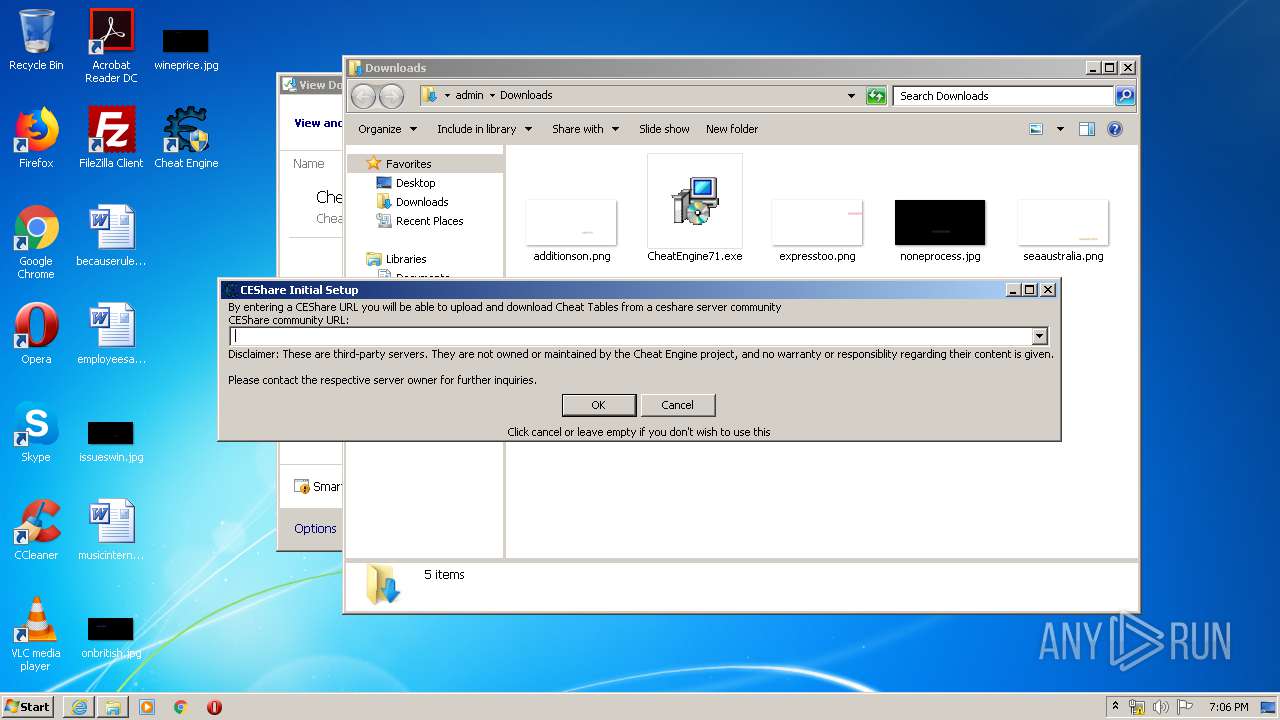
3152 | CheatEngine71.tmp | GET | 200 | 34.252.94.12:80 | http://rp.ginihehen.com/ | IE | — | — | malicious |
2964 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3152 | CheatEngine71.tmp | POST | 200 | 52.212.91.170:80 | http://rp.ginihehen.com/ | IE | — | — | malicious |
3152 | CheatEngine71.tmp | POST | 200 | 54.229.112.10:80 | http://os.ginihehen.com/ | IE | binary | 962 Kb | whitelisted |
2964 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuqL92L3tjkN67RNFF%2FEdvT6NEzAQUwBKyKHRoRmfpcCV0GgBFWwZ9XEQCEAgt9o7pxpMVvr9yB5s4EP0%3D | US | der | 471 b | whitelisted |
2964 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAVXyAsoJoOhewoRRJMpa3k%3D | US | der | 471 b | whitelisted |
3152 | CheatEngine71.tmp | POST | 200 | 52.212.91.170:80 | http://rp.ginihehen.com/ | IE | — | — | malicious |
3168 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3168 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2668 | cheatengine-i386.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | iexplore.exe | 52.216.251.132:443 | github-production-release-asset-2e65be.s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
2964 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3152 | CheatEngine71.tmp | 34.252.94.12:80 | rp.ginihehen.com | Amazon.com, Inc. | IE | malicious |
3152 | CheatEngine71.tmp | 52.212.91.170:80 | rp.ginihehen.com | Amazon.com, Inc. | IE | malicious |
3152 | CheatEngine71.tmp | 54.229.112.10:80 | os.ginihehen.com | Amazon.com, Inc. | IE | malicious |
3168 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3168 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
2668 | cheatengine-i386.exe | 104.20.174.30:443 | cheatengine.org | Cloudflare Inc | US | shared |
2668 | cheatengine-i386.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3168 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
github-production-release-asset-2e65be.s3.amazonaws.com |
| shared |
rp.ginihehen.com |
| malicious |
os.ginihehen.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
cheatengine.org |
| whitelisted |
Threats
Process | Message |
|---|---|
Kernelmoduleunloader.exe | count=0 |
Kernelmoduleunloader.exe | Kernelmodule unloader |
Kernelmoduleunloader.exe | attempting to unload |
Kernelmoduleunloader.exe | setup=true |
Kernelmoduleunloader.exe | Setup. So do not show messages |
Kernelmoduleunloader.exe | SCManager opened |
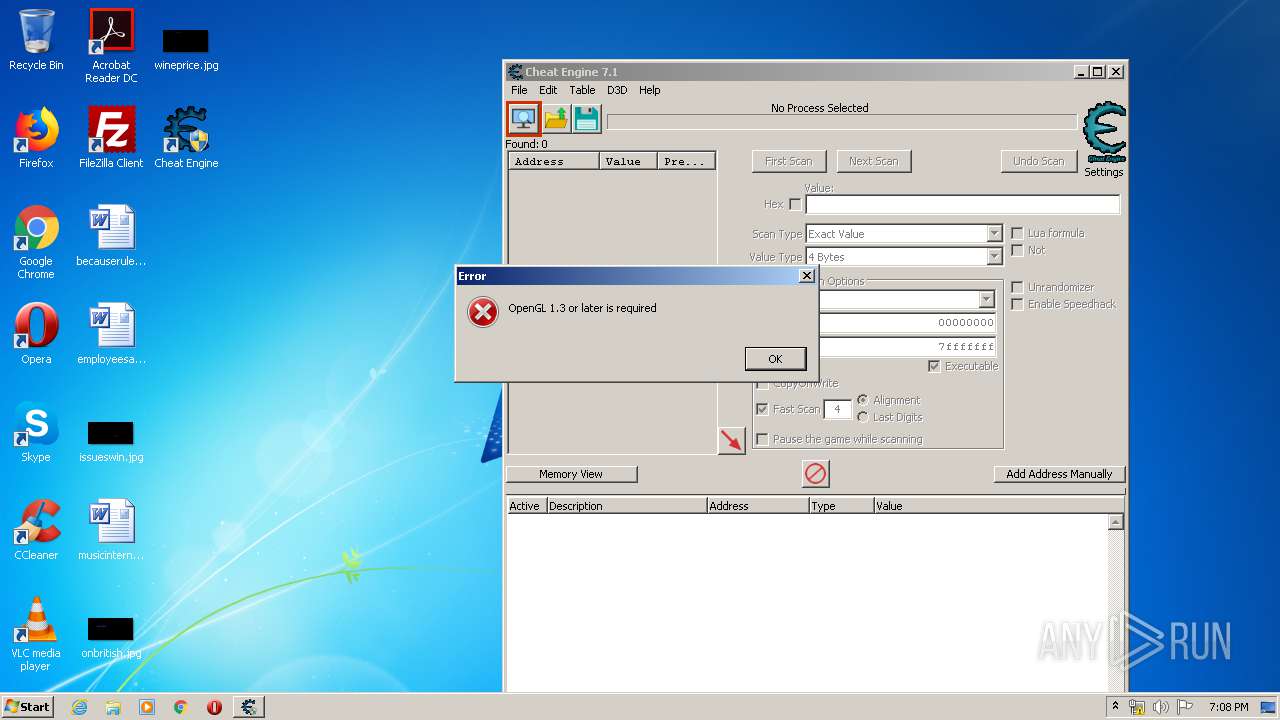
cheatengine-i386.exe | setDPIAware |
cheatengine-i386.exe | p3 |
cheatengine-i386.exe | DisassemblerThumb init |
cheatengine-i386.exe | arm disassembler |