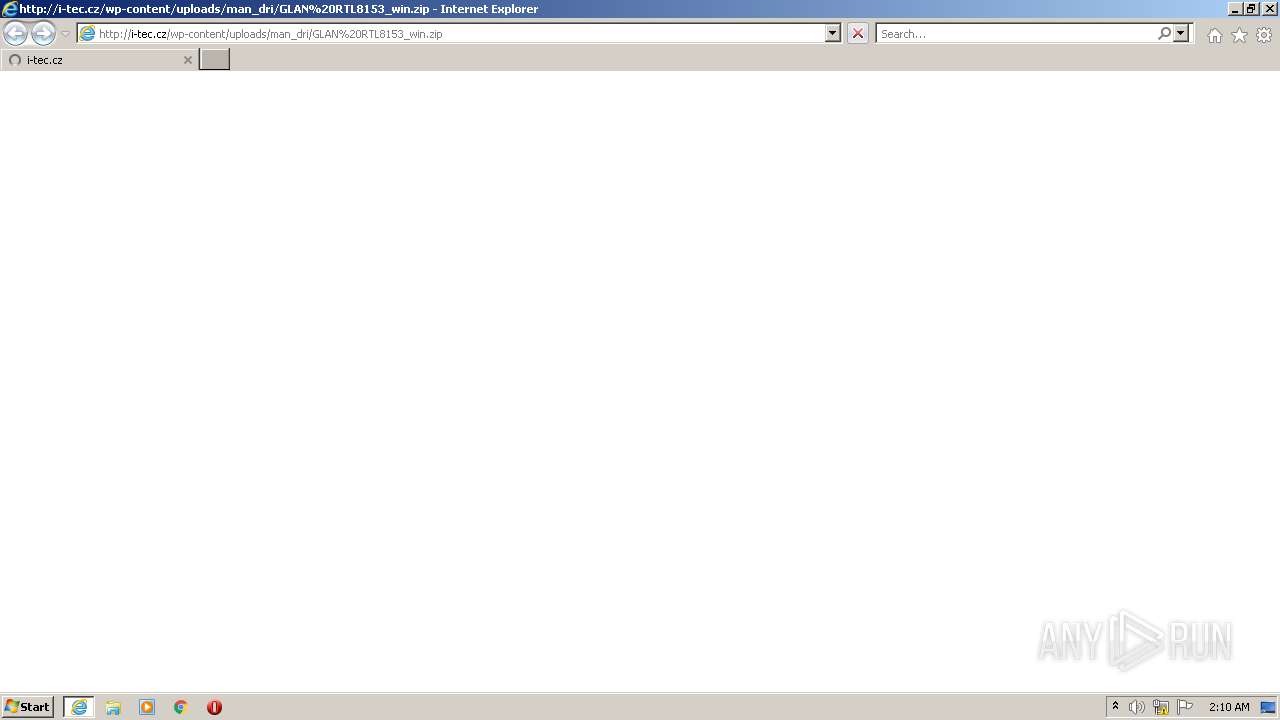
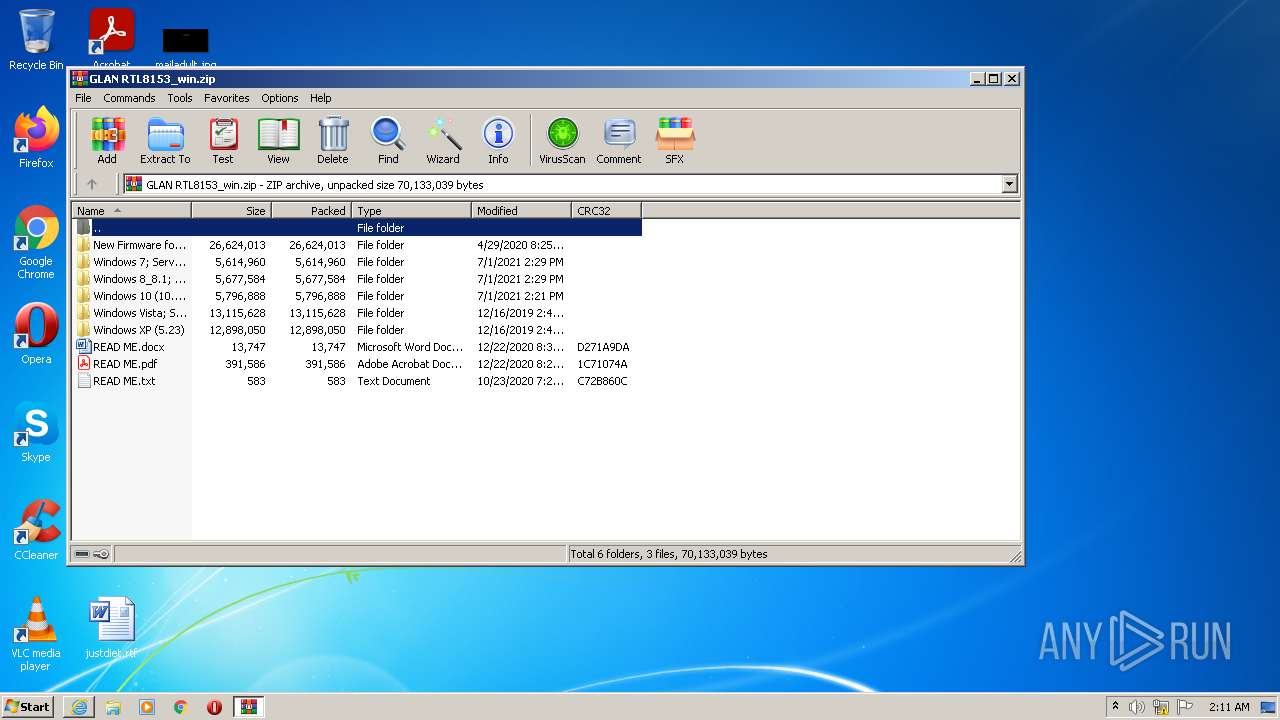
| URL: | http://i-tec.cz/wp-content/uploads/man_dri/GLAN%20RTL8153_win.zip |
| Full analysis: | https://app.any.run/tasks/be83dd87-059a-471f-9668-6d9fb2813680 |
| Verdict: | Malicious activity |
| Analysis date: | July 20, 2021, 01:10:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 09AF1825BAA8145905F13081B7826F06 |
| SHA1: | 366E75573878668EAA5F7AF4DBB82318B5C34040 |
| SHA256: | 0DF455AAF31D75E046DDAE437B63D40B450F2DEF12E5F72004F8E40B836D87CE |
| SSDEEP: | 3:N1KXsAcGxVIfAQyUmKOV3x4QWGc:CR3TIfAZUmdUP |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3512)
- setup.exe (PID: 2768)
Detects Cygwin installation
- WinRAR.exe (PID: 1232)
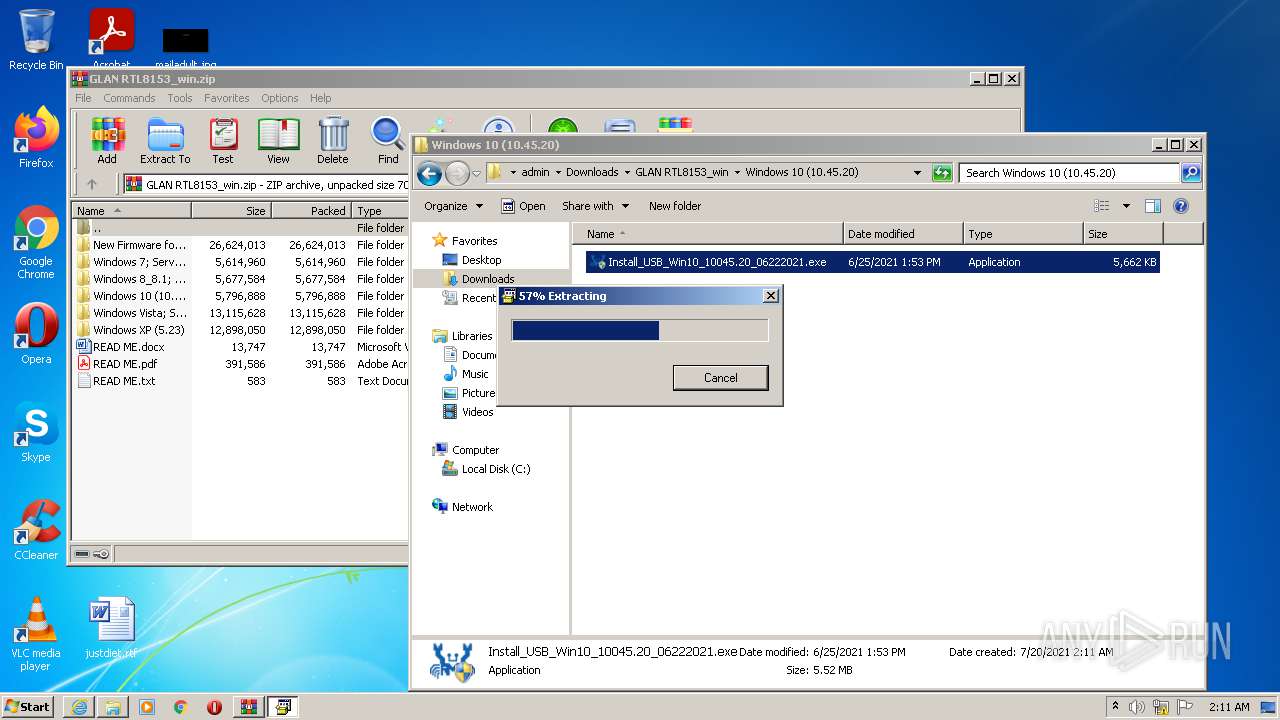
Drops executable file immediately after starts
- Install_USB_Win10_10045.20_06222021.exe (PID: 3856)
Application was dropped or rewritten from another process
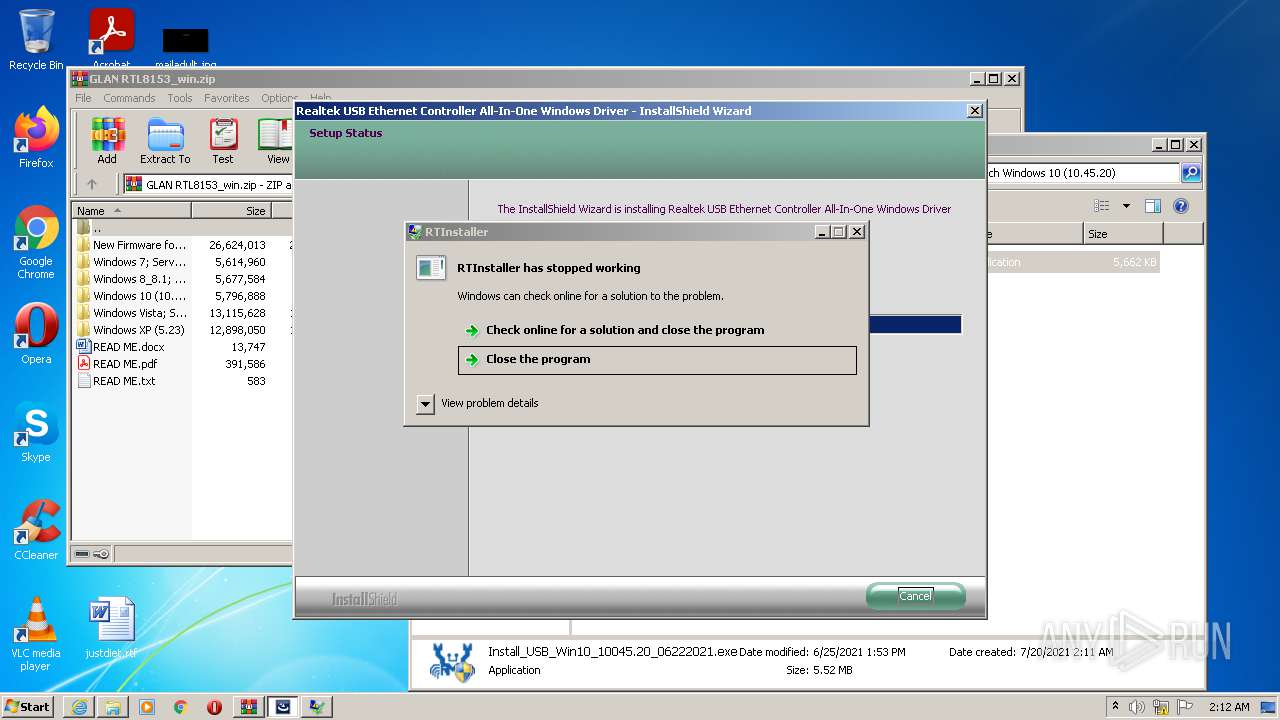
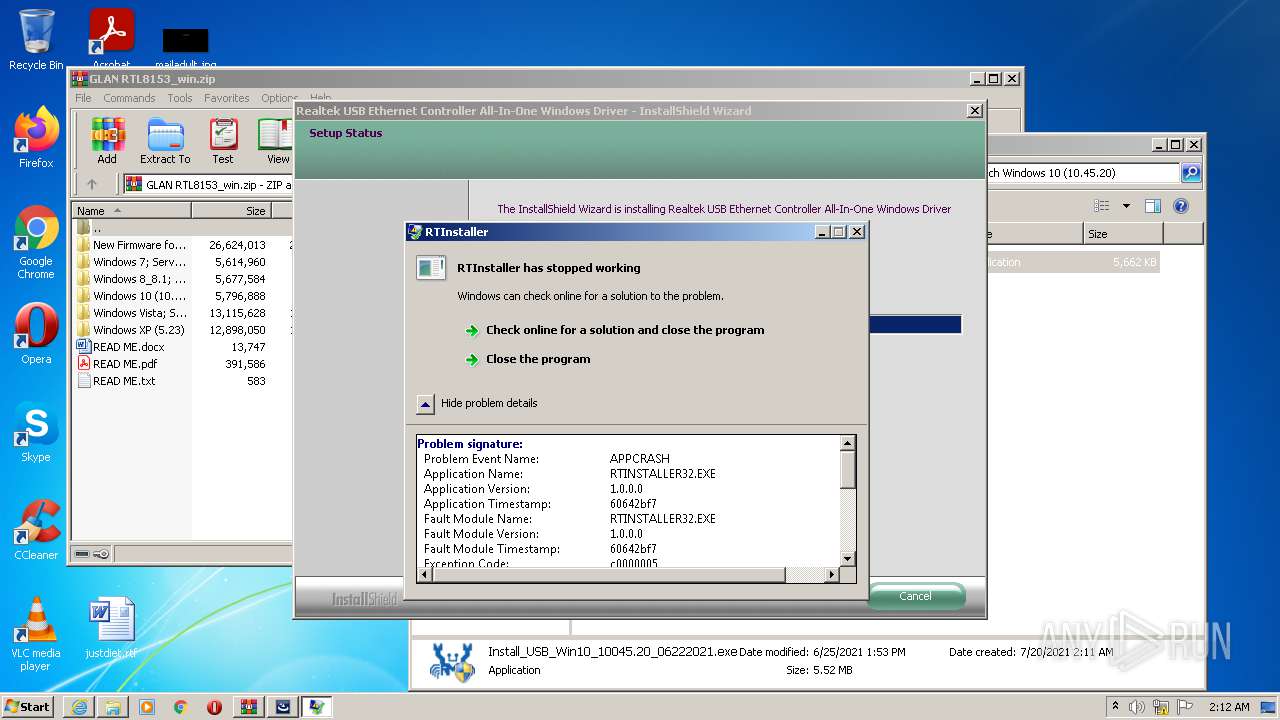
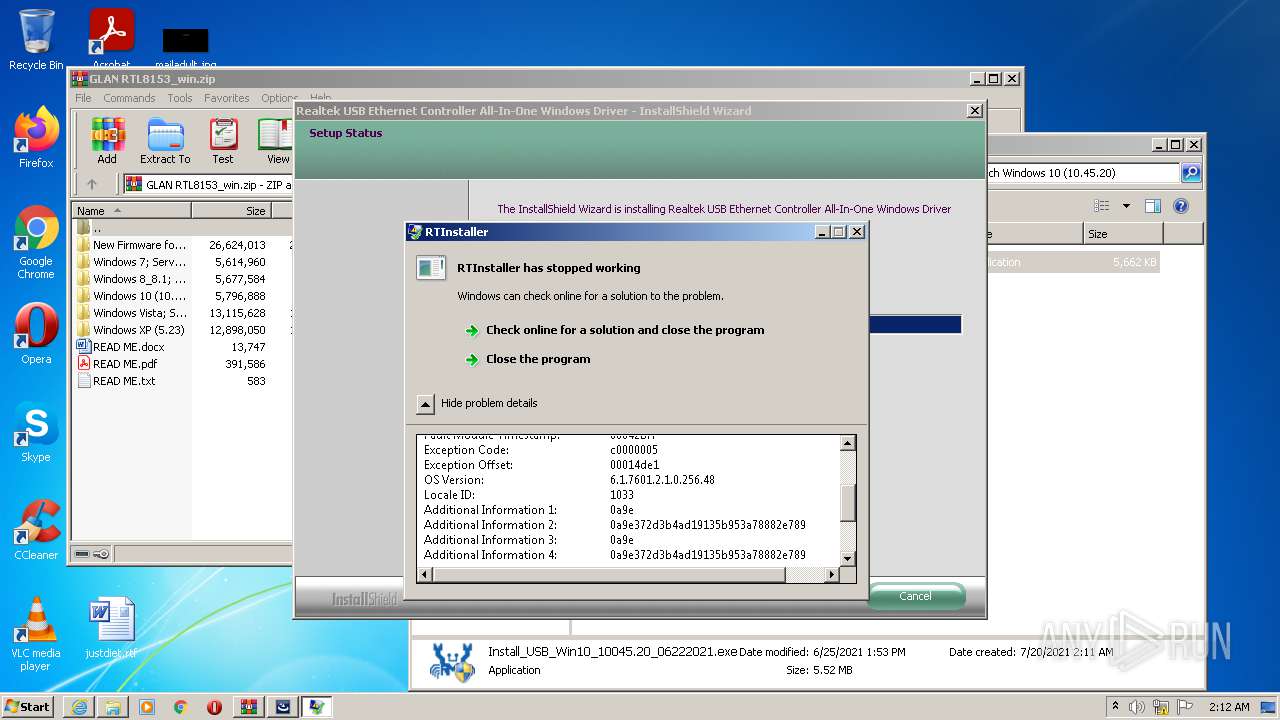
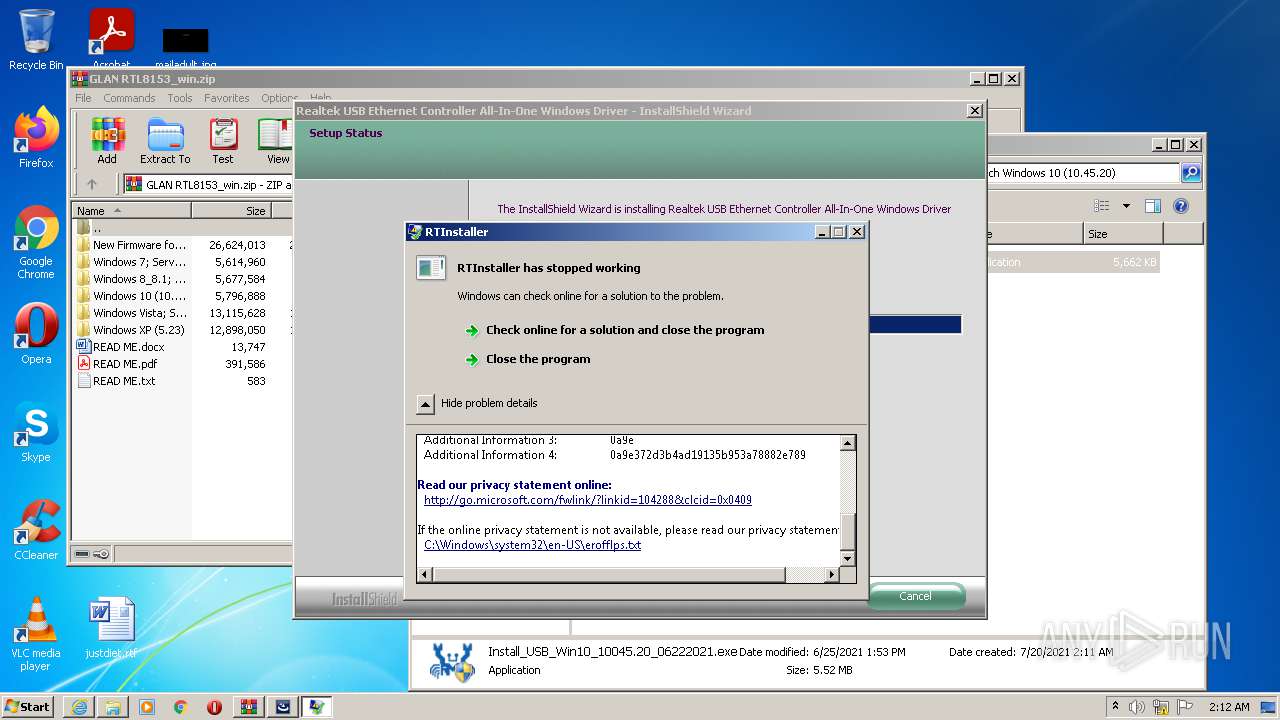
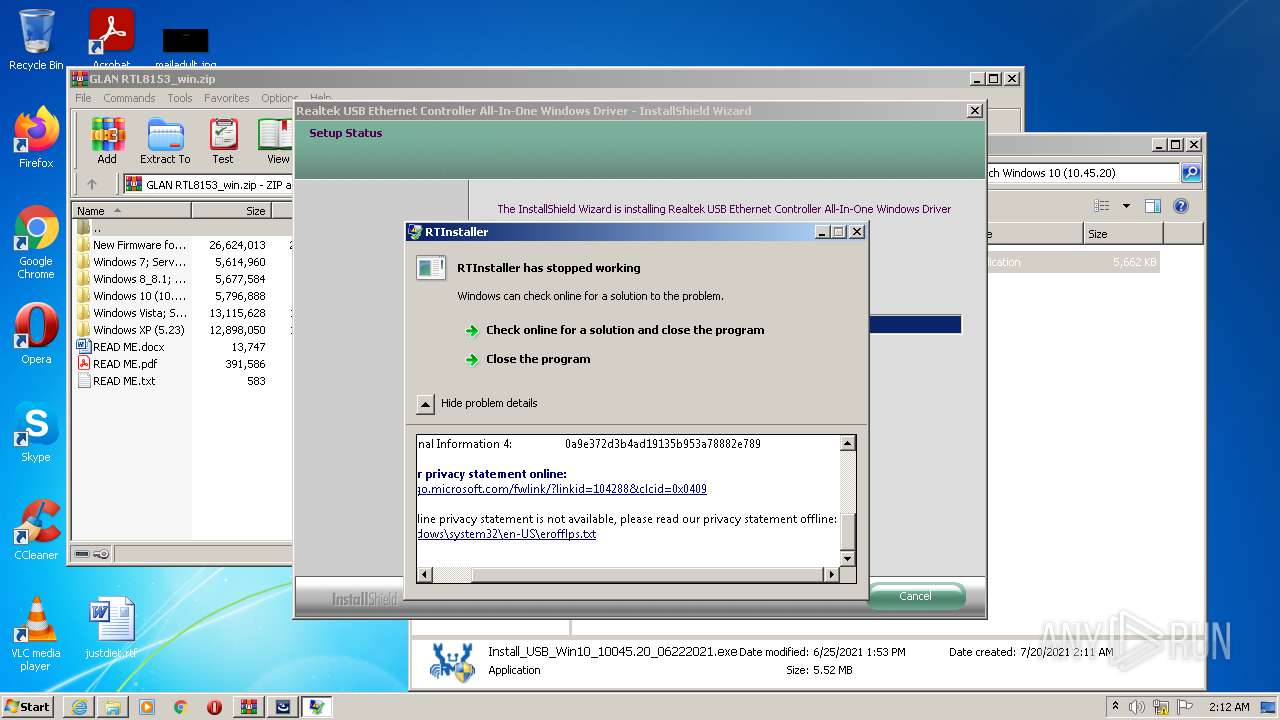
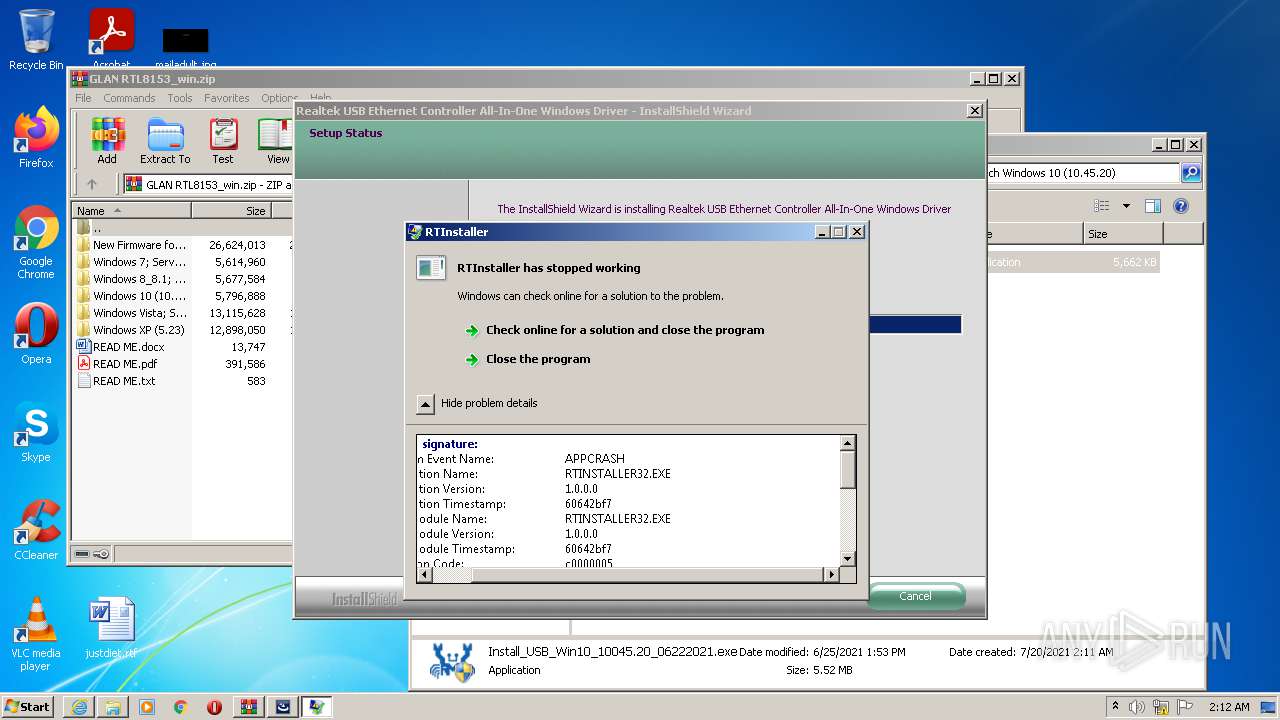
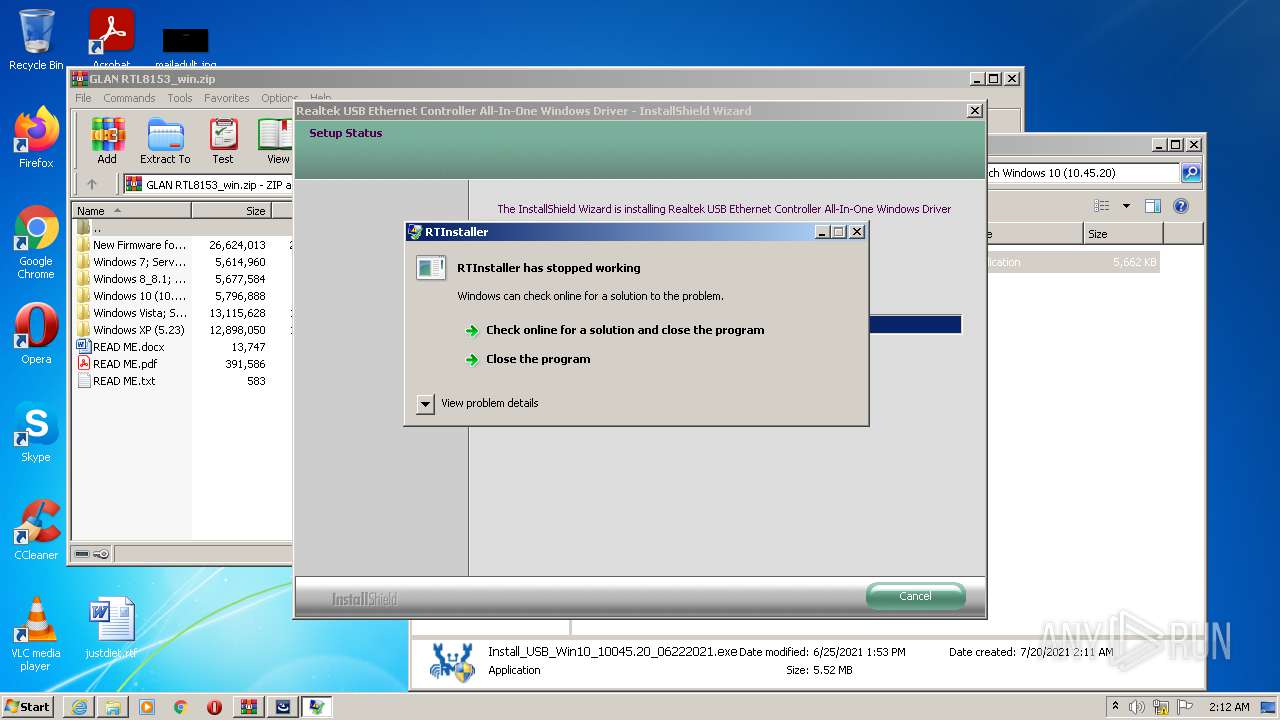
- RTINSTALLER32.EXE (PID: 2772)
- Install_USB_Win10_10045.20_06222021.exe (PID: 3956)
- Install_USB_Win10_10045.20_06222021.exe (PID: 3856)
- setup.exe (PID: 2768)
Actions looks like stealing of personal data
- Install_USB_Win10_10045.20_06222021.exe (PID: 3856)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1528)
Reads the computer name
- WinRAR.exe (PID: 1232)
- setup.exe (PID: 2768)
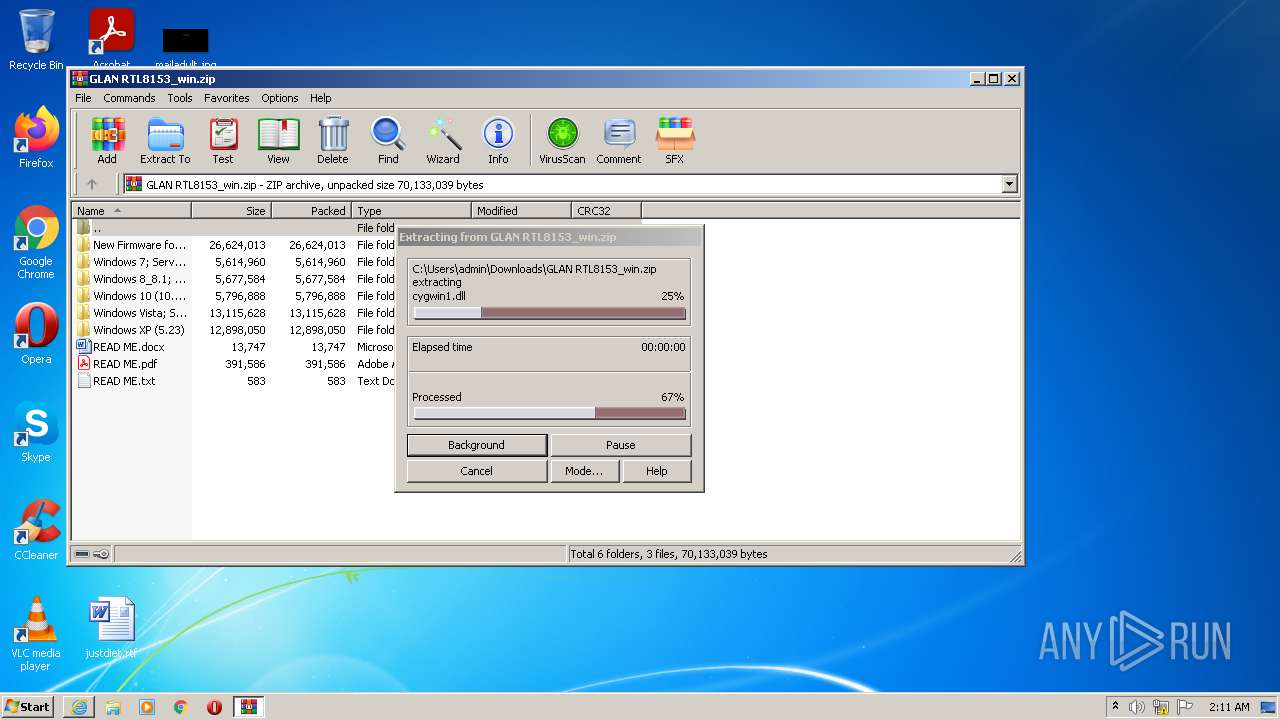
Executable content was dropped or overwritten
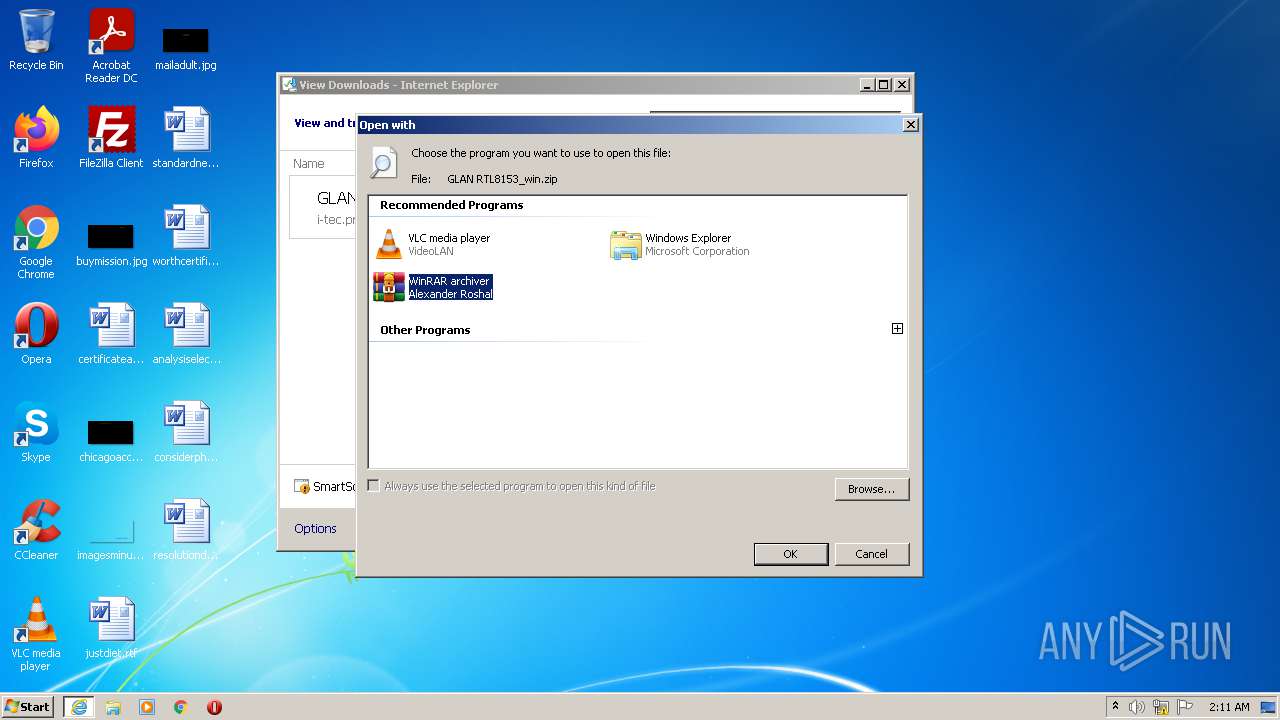
- WinRAR.exe (PID: 1232)
- setup.exe (PID: 2768)
- Install_USB_Win10_10045.20_06222021.exe (PID: 3856)
Checks supported languages
- WinRAR.exe (PID: 1232)
- Install_USB_Win10_10045.20_06222021.exe (PID: 3856)
- setup.exe (PID: 2768)
- RTINSTALLER32.EXE (PID: 2772)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1232)
- Install_USB_Win10_10045.20_06222021.exe (PID: 3856)
- setup.exe (PID: 2768)
Reads Windows owner or organization settings
- setup.exe (PID: 2768)
Executed as Windows Service
- vssvc.exe (PID: 3928)
Reads Environment values
- vssvc.exe (PID: 3928)
Reads the Windows organization settings
- setup.exe (PID: 2768)
Creates files in the program directory
- setup.exe (PID: 2768)
- RTINSTALLER32.EXE (PID: 2772)
Creates a directory in Program Files
- setup.exe (PID: 2768)
Reads default file associations for system extensions
- SearchProtocolHost.exe (PID: 3512)
Searches for installed software
- setup.exe (PID: 2768)
INFO
Reads the computer name
- iexplore.exe (PID: 1048)
- iexplore.exe (PID: 1528)
- explorer.exe (PID: 992)
- vssvc.exe (PID: 3928)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1048)
Checks supported languages
- iexplore.exe (PID: 1048)
- iexplore.exe (PID: 1528)
- explorer.exe (PID: 992)
- vssvc.exe (PID: 3928)
Changes internet zones settings
- iexplore.exe (PID: 1048)
Reads settings of System Certificates
- iexplore.exe (PID: 1528)
- iexplore.exe (PID: 1048)
Reads the date of Windows installation
- iexplore.exe (PID: 1048)
Application launched itself
- iexplore.exe (PID: 1048)
Checks Windows Trust Settings
- iexplore.exe (PID: 1528)
- iexplore.exe (PID: 1048)
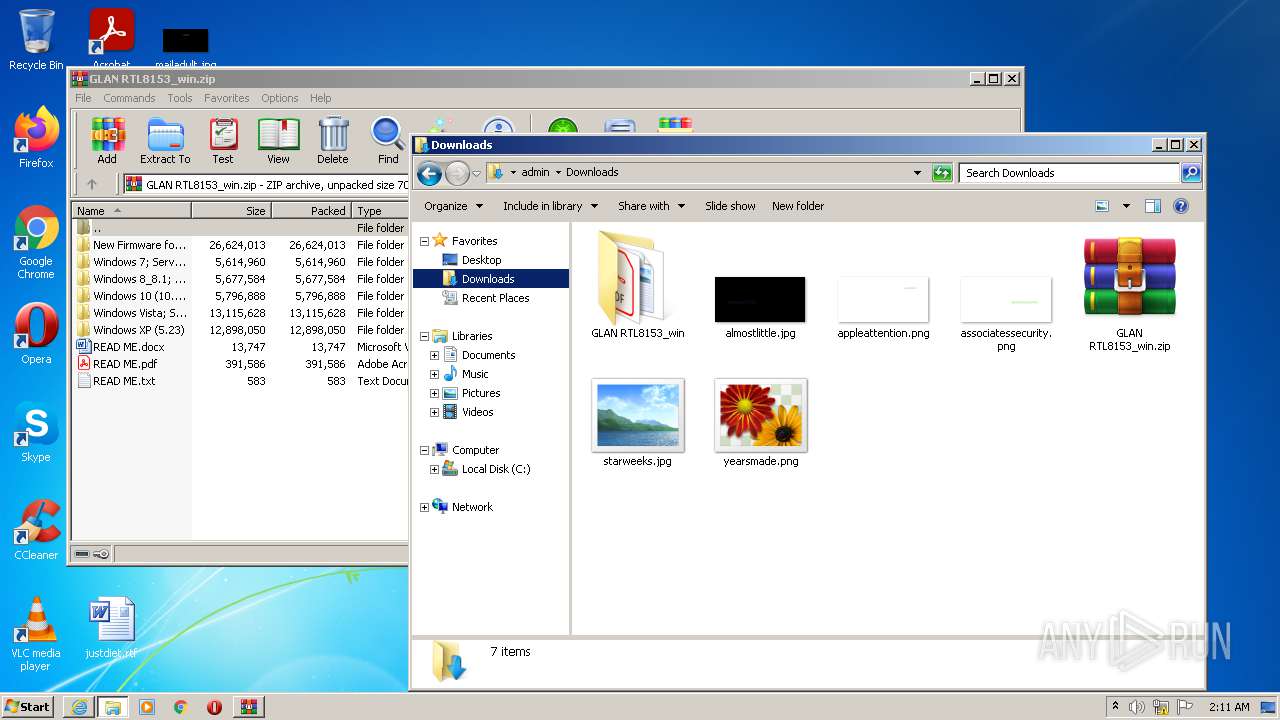
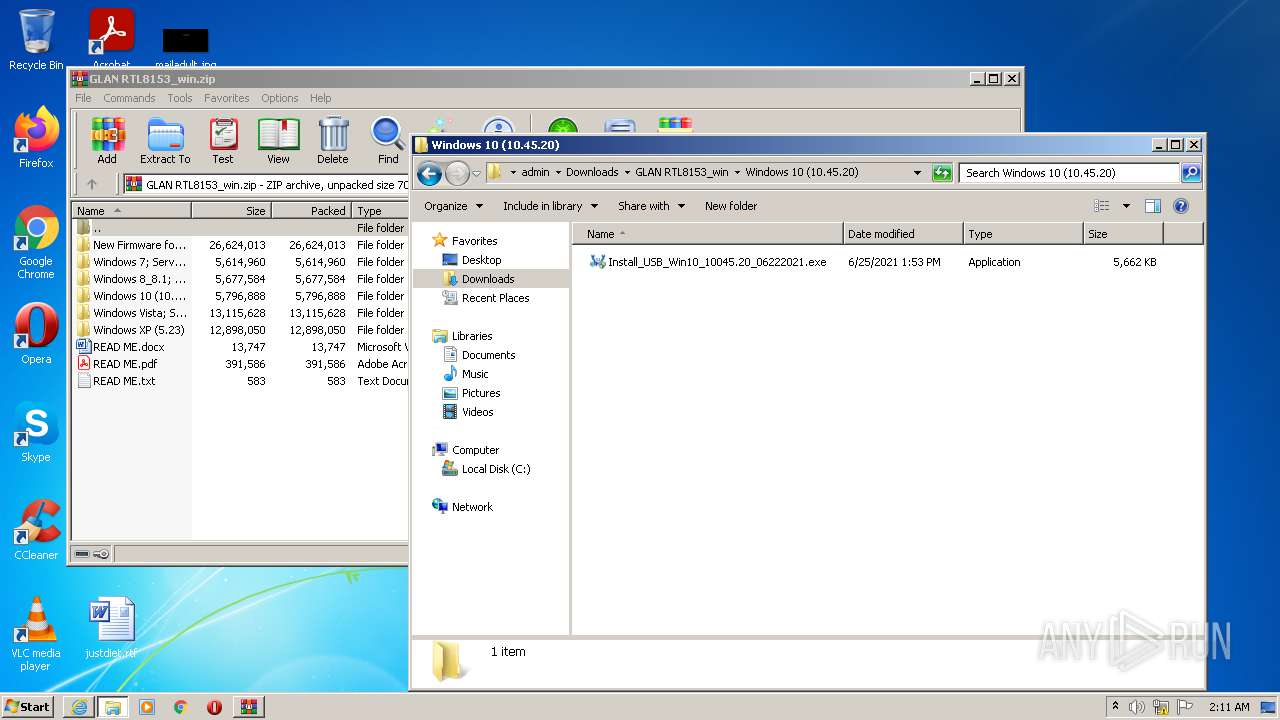
Manual execution by user
- explorer.exe (PID: 992)
- Install_USB_Win10_10045.20_06222021.exe (PID: 3956)
- Install_USB_Win10_10045.20_06222021.exe (PID: 3856)
Creates files in the user directory
- iexplore.exe (PID: 1048)
Changes settings of System certificates
- iexplore.exe (PID: 1048)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
10
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
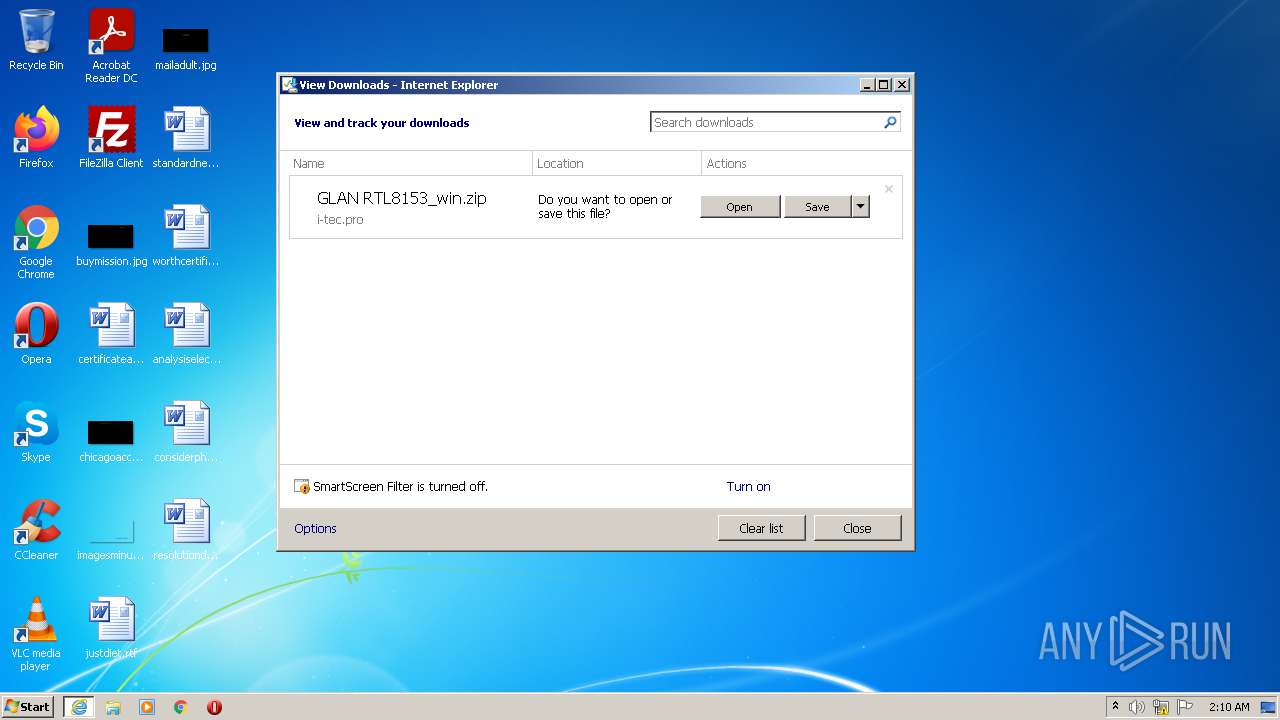
| 1048 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://i-tec.cz/wp-content/uploads/man_dri/GLAN%20RTL8153_win.zip" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
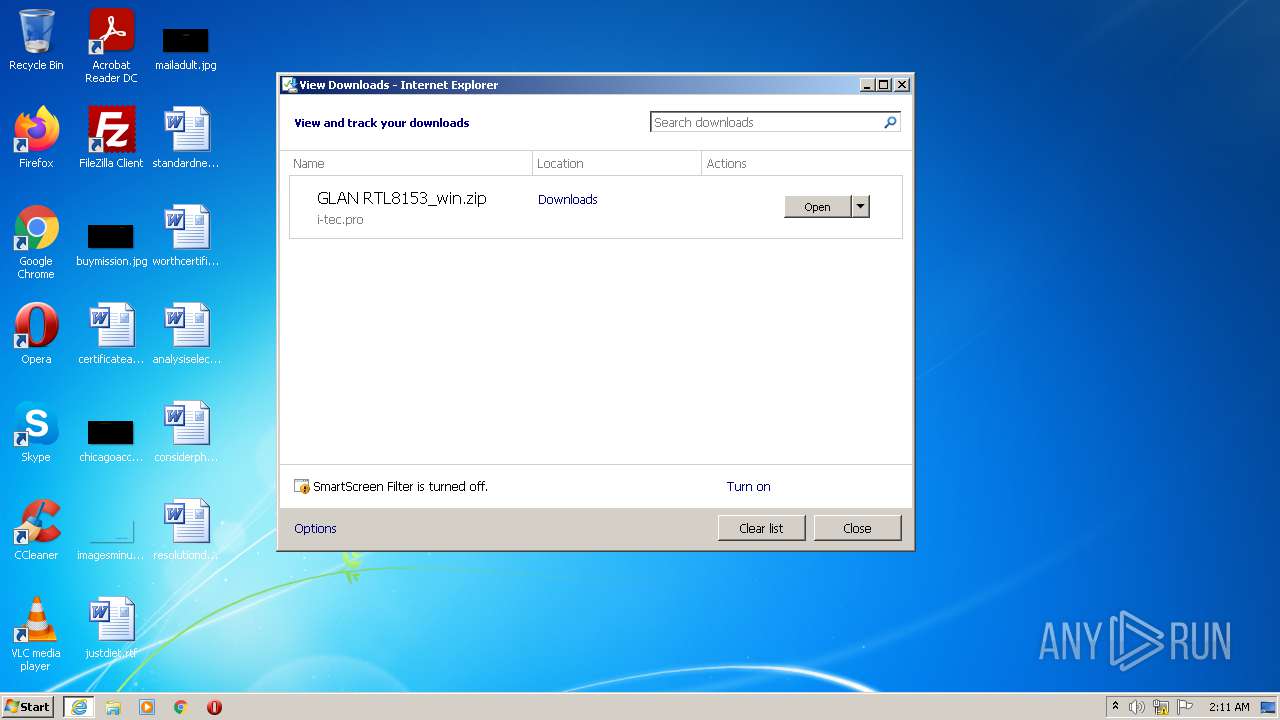
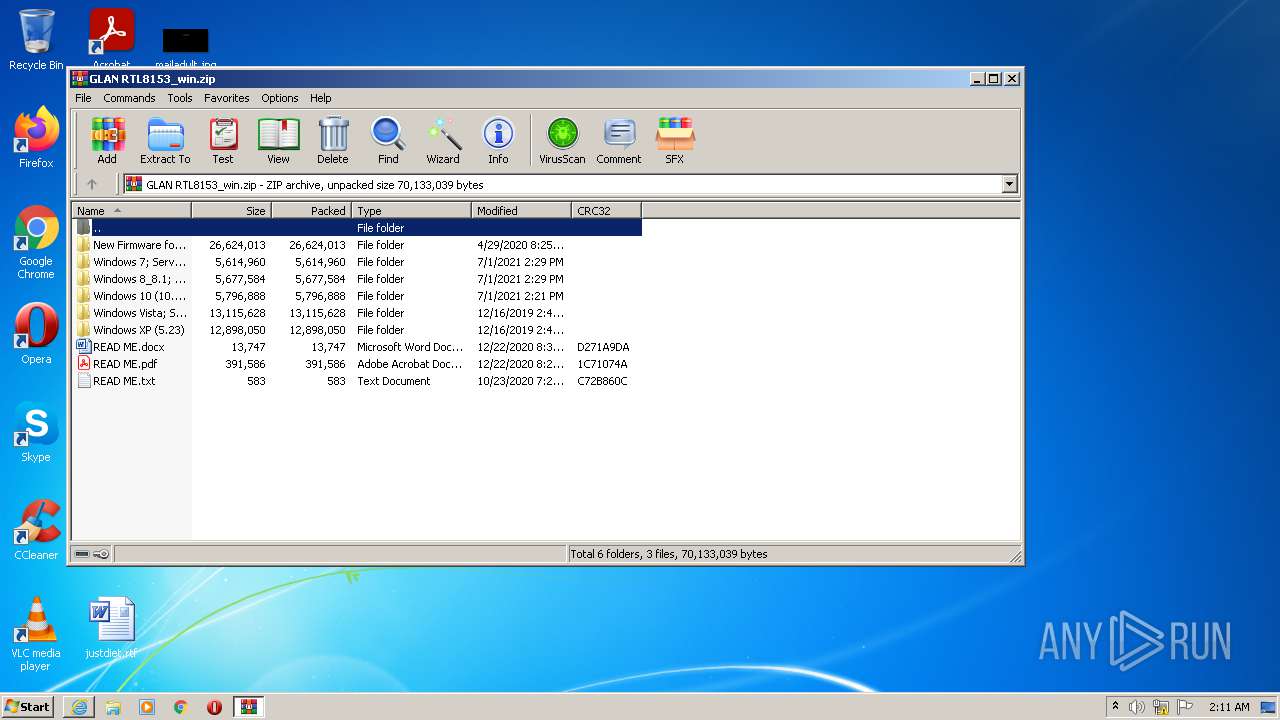
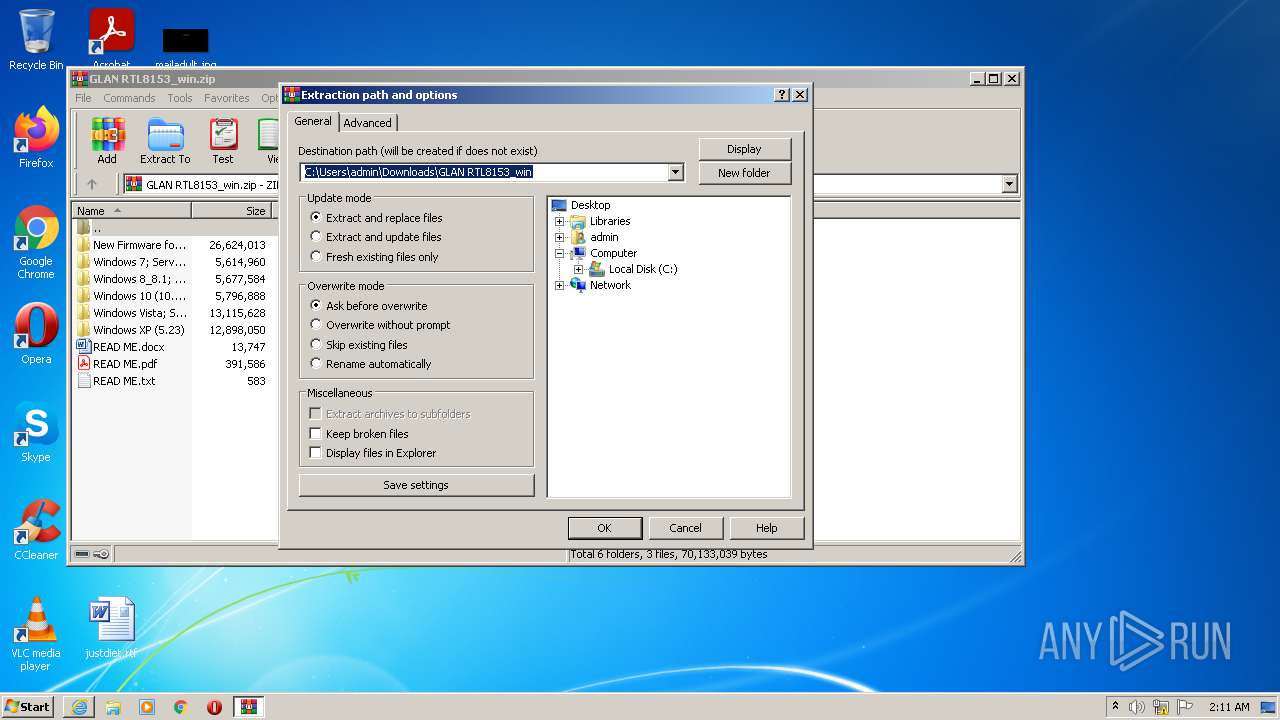
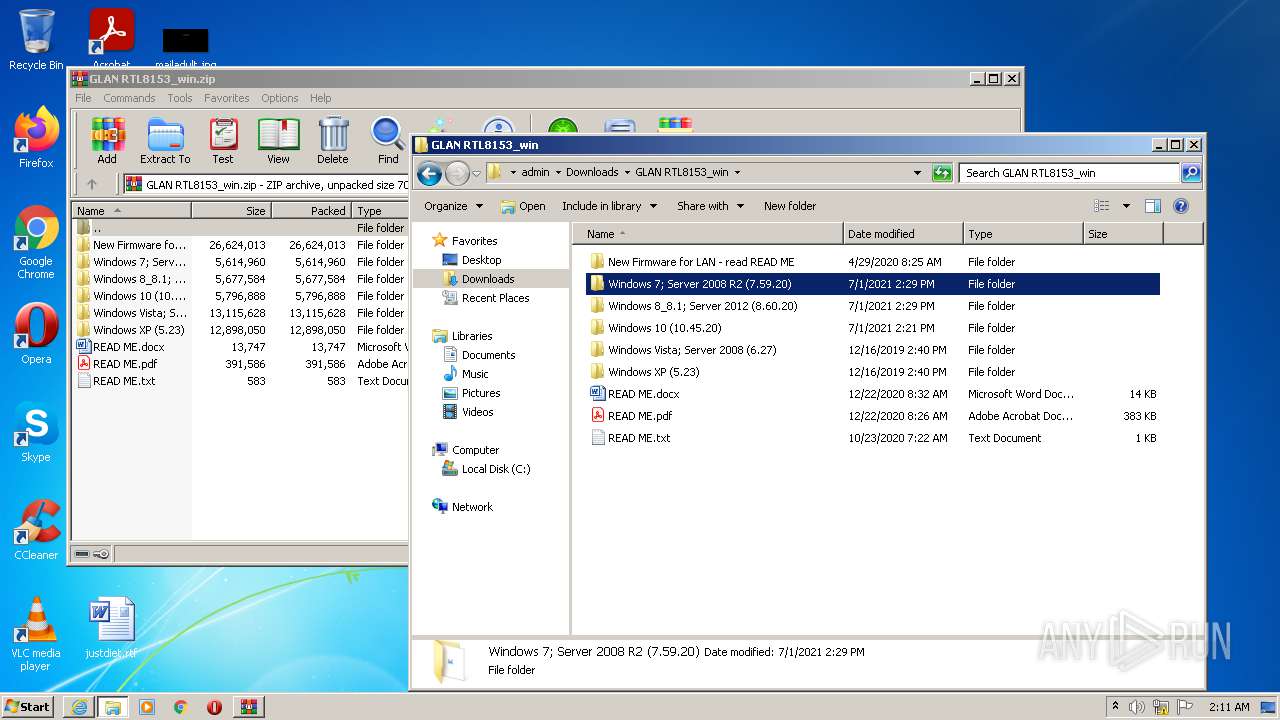
| 1232 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\GLAN RTL8153_win.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1048 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
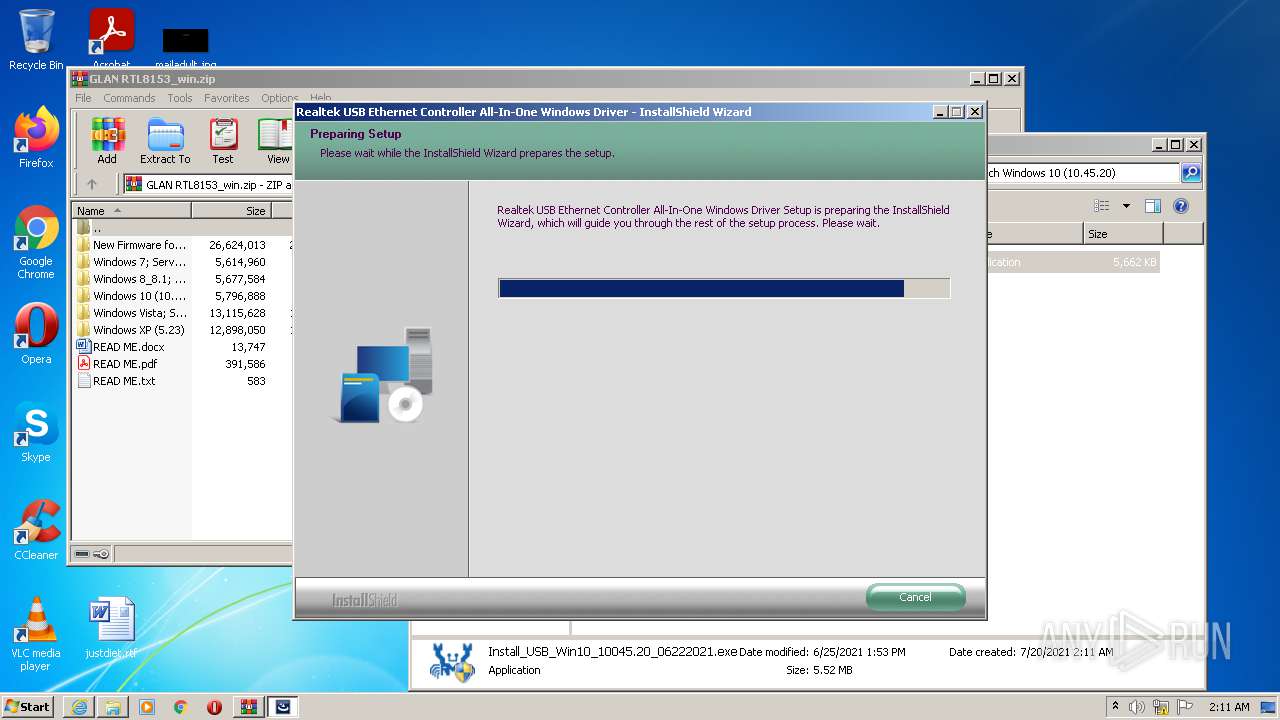
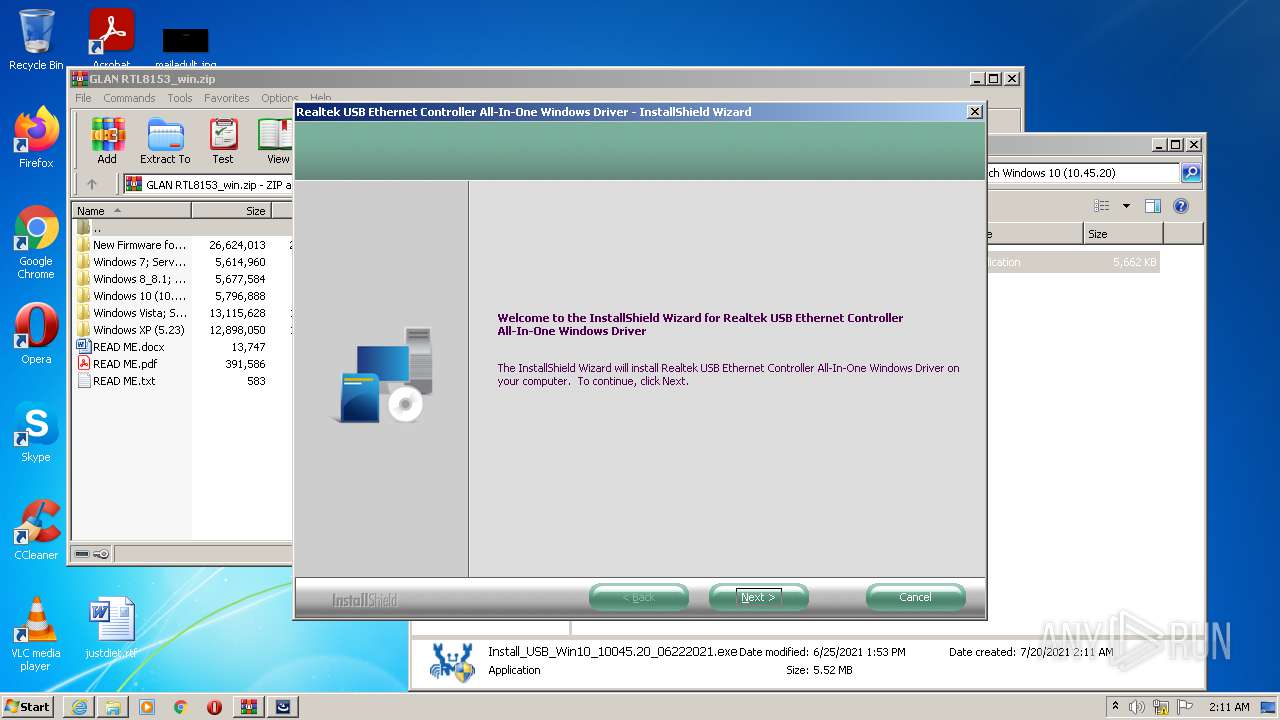
| 2768 | .\setup.exe | C:\Users\admin\AppData\Local\Temp\7zS5A5E.tmp\setup.exe | Install_USB_Win10_10045.20_06222021.exe | ||||||||||||
User: admin Company: Realtek Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Exit code: 2147753984 Version: 1.00.0001 Modules
| |||||||||||||||
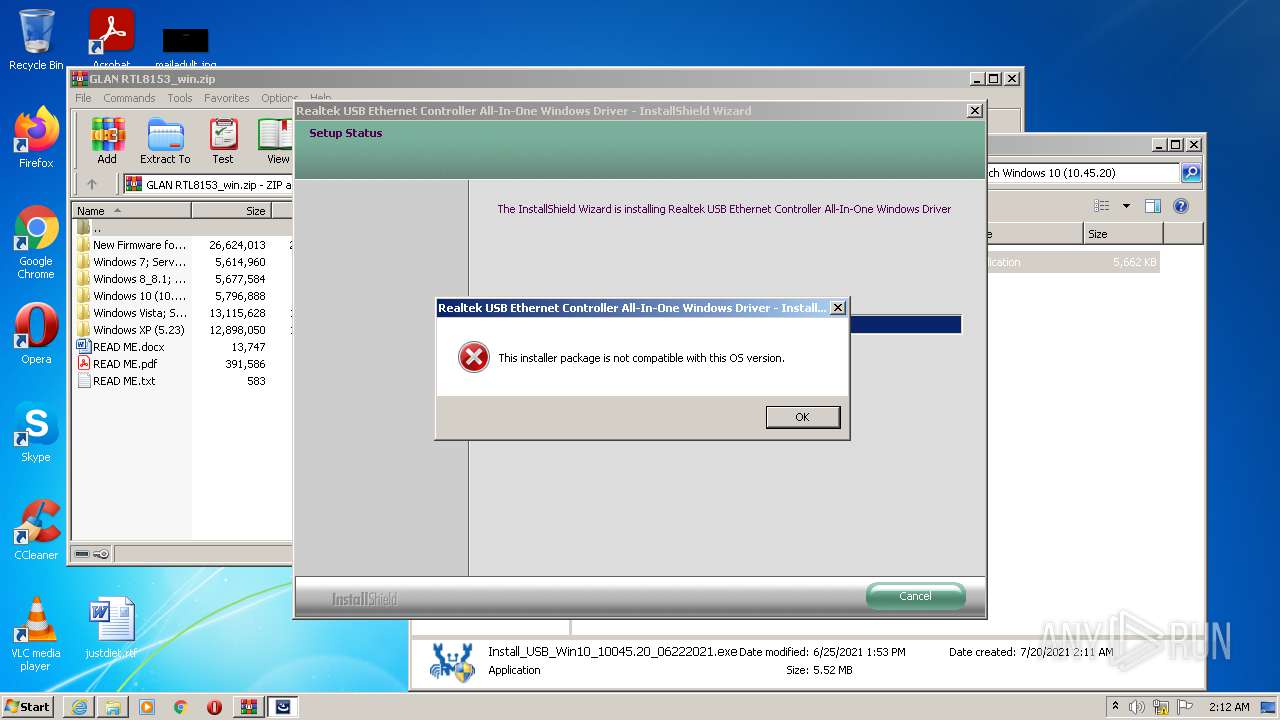
| 2772 | "C:\Program Files\Realtek\Realtek USB Ethernet Controller All-In-One Windows Driver\RTINSTALLER32.EXE" /mi /q /VISTA815x /X86 | C:\Program Files\Realtek\Realtek USB Ethernet Controller All-In-One Windows Driver\RTINSTALLER32.EXE | setup.exe | ||||||||||||
User: admin Company: Realtek Semiconductor Corp. Integrity Level: HIGH Description: RTInstaller Exit code: 3221225477 Version: 1.0.0.86 Modules
| |||||||||||||||
| 3512 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
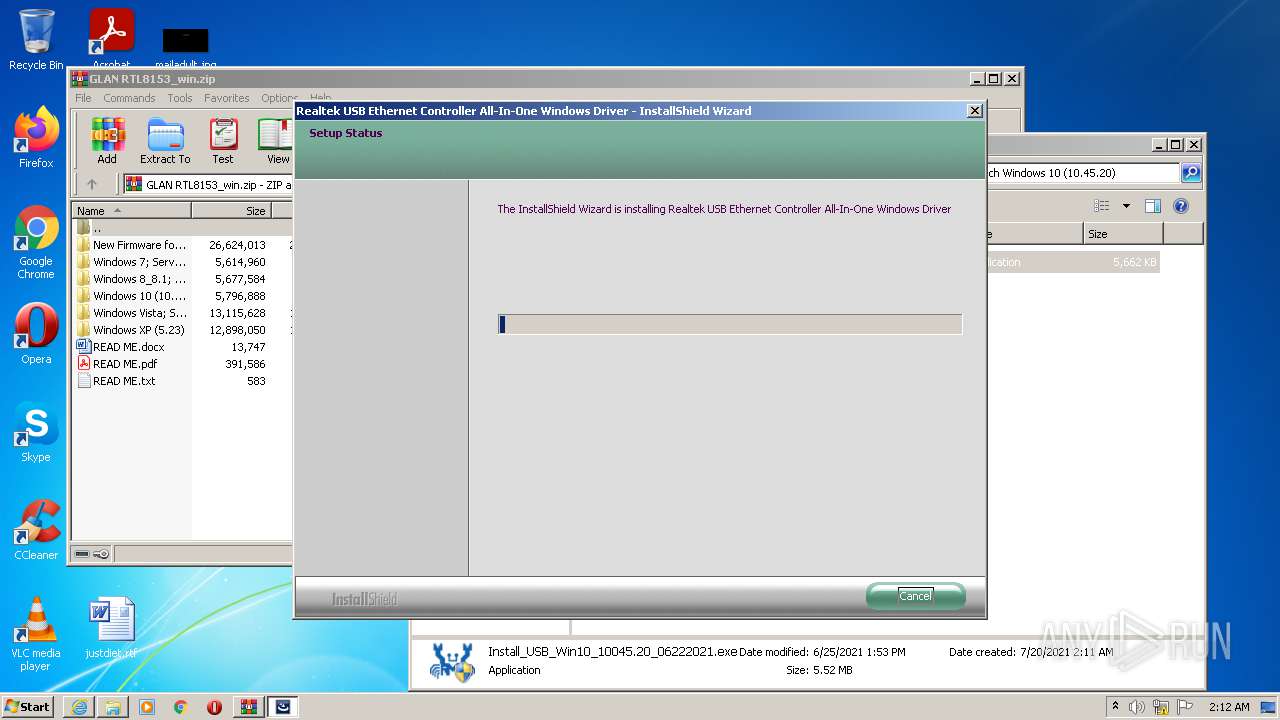
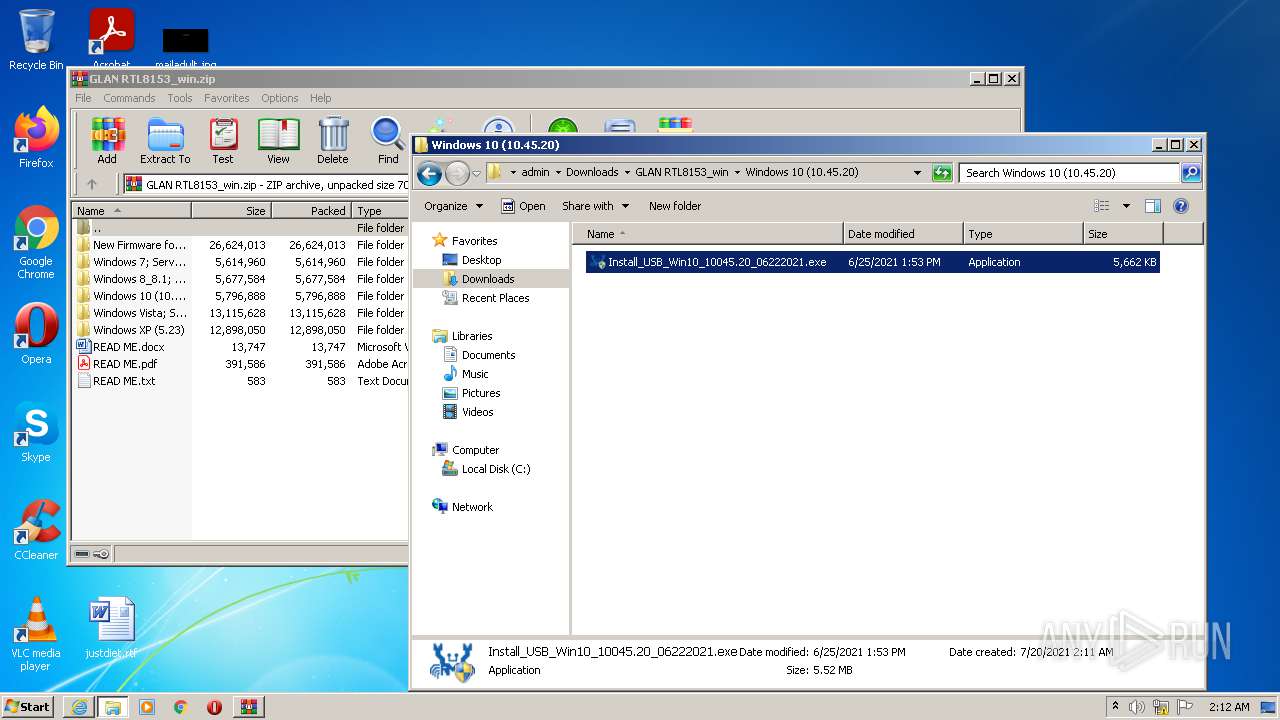
| 3856 | "C:\Users\admin\Downloads\GLAN RTL8153_win\Windows 10 (10.45.20)\Install_USB_Win10_10045.20_06222021.exe" | C:\Users\admin\Downloads\GLAN RTL8153_win\Windows 10 (10.45.20)\Install_USB_Win10_10045.20_06222021.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3928 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3956 | "C:\Users\admin\Downloads\GLAN RTL8153_win\Windows 10 (10.45.20)\Install_USB_Win10_10045.20_06222021.exe" | C:\Users\admin\Downloads\GLAN RTL8153_win\Windows 10 (10.45.20)\Install_USB_Win10_10045.20_06222021.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
21 425
Read events
21 070
Write events
349
Delete events
6
Modification events
| (PID) Process: | (1048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 214879840 | |||
| (PID) Process: | (1048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30899460 | |||
| (PID) Process: | (1048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 515037262 | |||
| (PID) Process: | (1048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30899460 | |||
| (PID) Process: | (1048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
61
Suspicious files
87
Text files
335
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
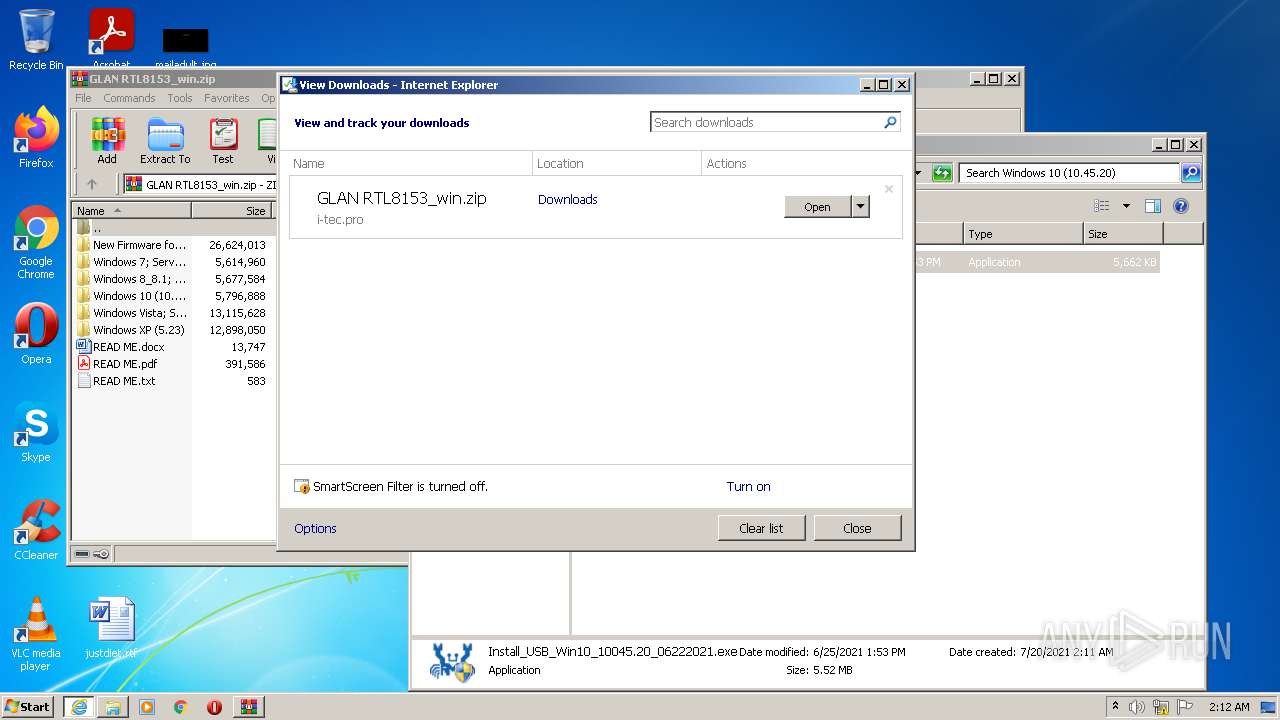
| 1048 | iexplore.exe | C:\Users\admin\Downloads\GLAN RTL8153_win.zip | — | |
MD5:— | SHA256:— | |||
| 1528 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\GLAN%20RTL8153_win[1].htm | html | |
MD5:— | SHA256:— | |||
| 1528 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 1528 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EDB09E4F3991F66C88FAAEA64859808 | binary | |
MD5:— | SHA256:— | |||
| 3512 | SearchProtocolHost.exe | C:\Users\admin\Downloads\GLAN RTL8153_win.zip.a34nbgn.partial | compressed | |
MD5:— | SHA256:— | |||
| 1528 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1048 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{4A71D569-E8F7-11EB-AD6C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1528 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:— | SHA256:— | |||
| 1528 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EDB09E4F3991F66C88FAAEA64859808 | der | |
MD5:— | SHA256:— | |||
| 1528 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\644B8874112055B5E195ECB0E8F243A4 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
22
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1528 | iexplore.exe | GET | 301 | 81.91.86.14:80 | http://i-tec.cz/wp-content/uploads/man_dri/GLAN%20RTL8153_win.zip | CZ | html | 374 b | malicious |
1528 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
1528 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRYaLDECQsWwh55pxTFhad7fw%3D%3D | unknown | der | 503 b | shared |
1528 | iexplore.exe | GET | 200 | 2.16.186.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3d5916ad58157347 | unknown | compressed | 4.70 Kb | whitelisted |
1048 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1528 | iexplore.exe | GET | 200 | 23.45.105.185:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
1048 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1048 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1048 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
1528 | iexplore.exe | GET | 200 | 2.16.186.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8d072969fcd9eebf | unknown | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1528 | iexplore.exe | 81.91.86.14:80 | i-tec.cz | Web4U s.r.o. | CZ | malicious |
1528 | iexplore.exe | 81.91.86.14:443 | i-tec.cz | Web4U s.r.o. | CZ | malicious |
1528 | iexplore.exe | 2.16.186.10:80 | crl.identrust.com | Akamai International B.V. | — | whitelisted |
1528 | iexplore.exe | 2.16.186.11:80 | r3.o.lencr.org | Akamai International B.V. | — | whitelisted |
1048 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1048 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1048 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1048 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
1528 | iexplore.exe | 23.45.105.185:80 | x1.c.lencr.org | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
i-tec.cz |
| malicious |
i-tec.pro |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
crl.identrust.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |