| URL: | https://siasky.net/PAHzB-9QA_CZsKZqFQ2oV2rgKCBk7j0bl5rb7Sr24PoNdQ |
| Full analysis: | https://app.any.run/tasks/e8ed524b-e248-447e-bacd-ed1782abf87c |
| Verdict: | Malicious activity |
| Analysis date: | October 24, 2020, 02:07:20 |
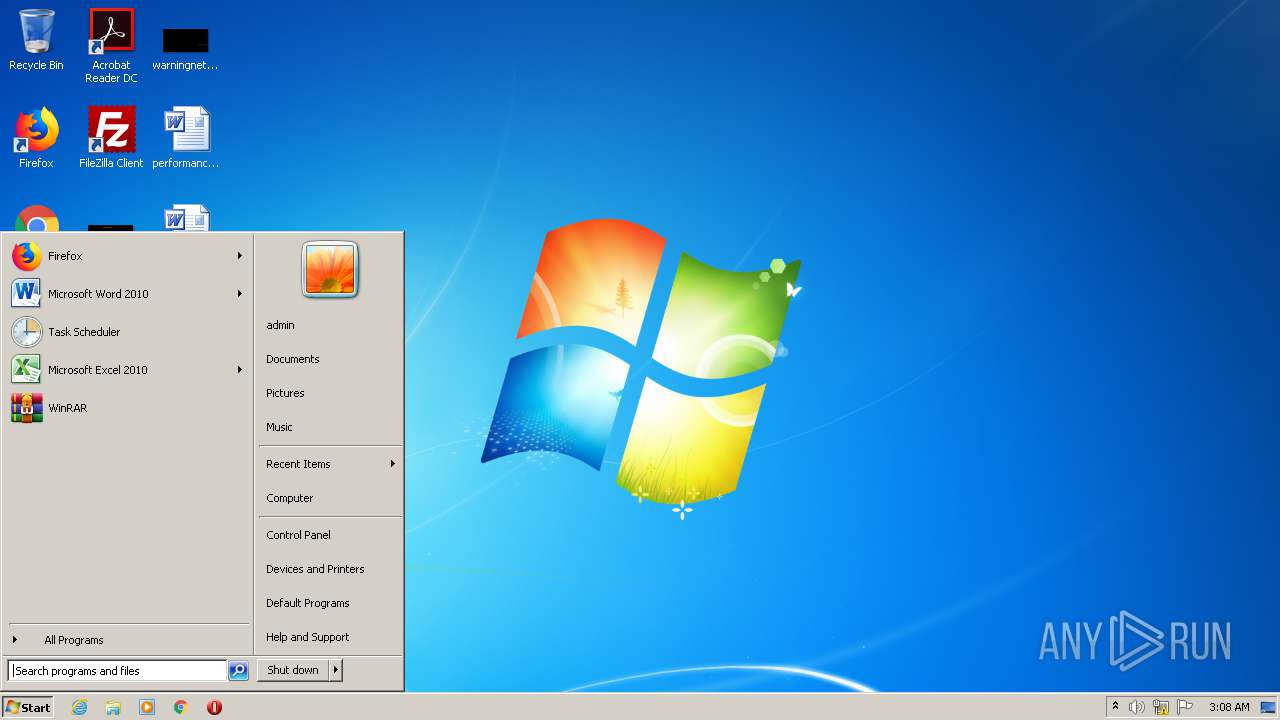
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9739ADD29F1702CCAF4860F3FDD8EBF7 |
| SHA1: | D73296CED3E7F27AEAB14C074D96256853A4A603 |
| SHA256: | 0DE6FCBE79BD692E6B56B57B8B7DA26BB6CFC79FA5D91E6C21CBE85882671713 |
| SSDEEP: | 3:N8BLIRukfXK7kpES2xAe:2yPfKku7 |
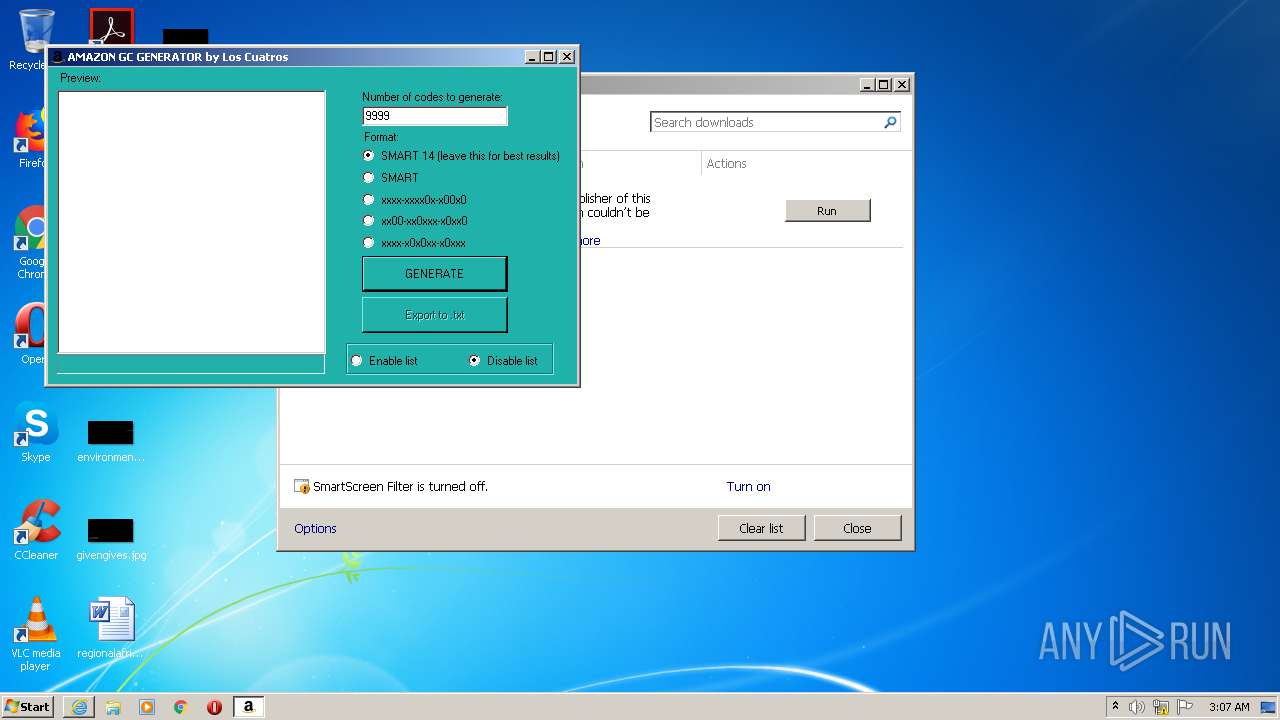
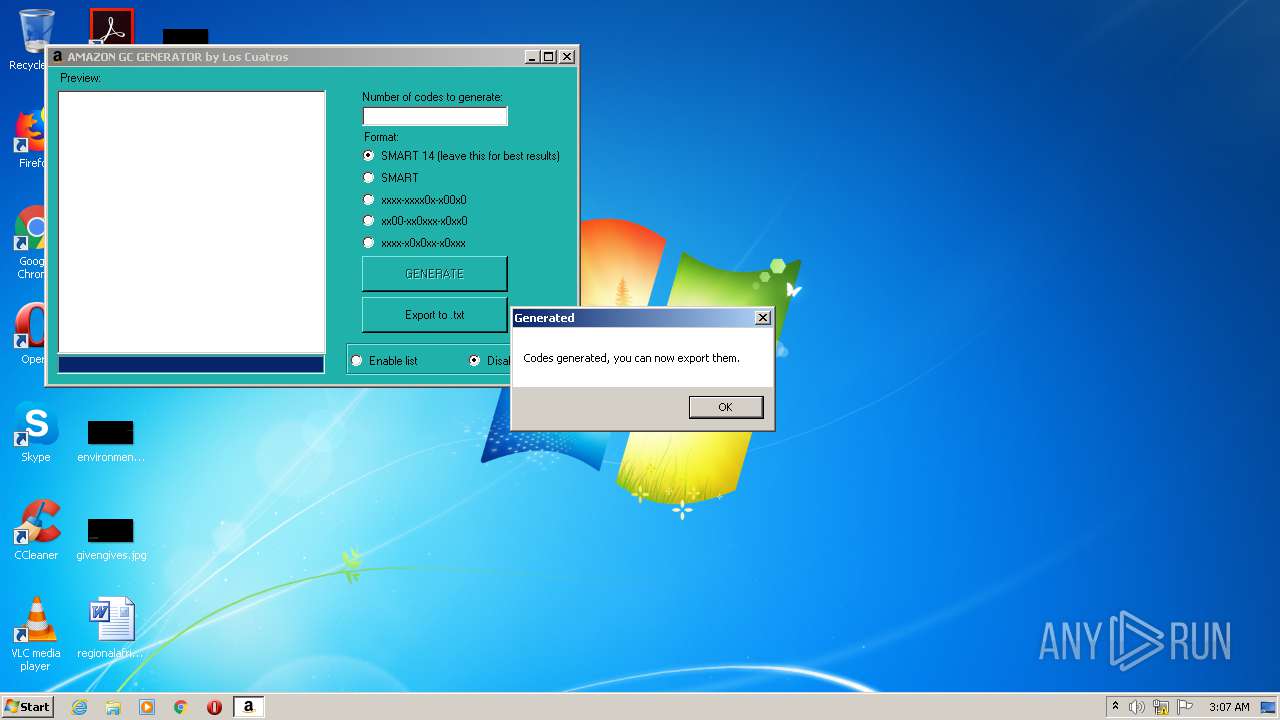
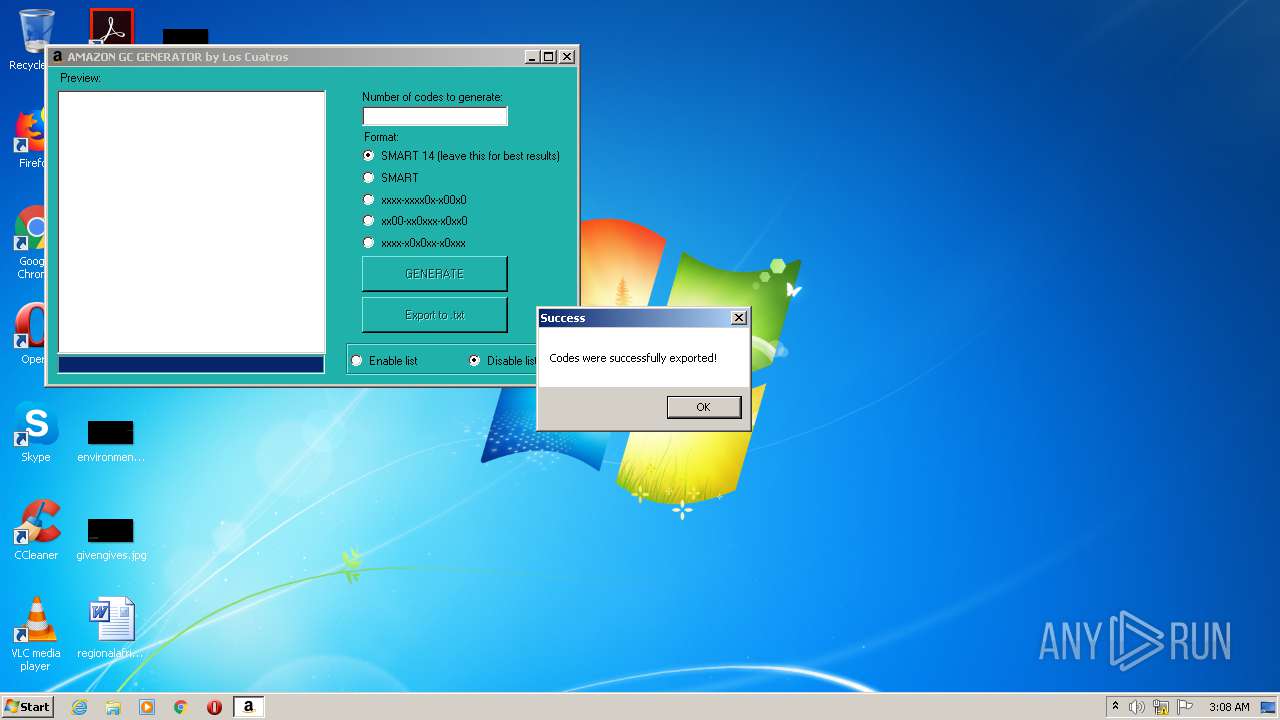
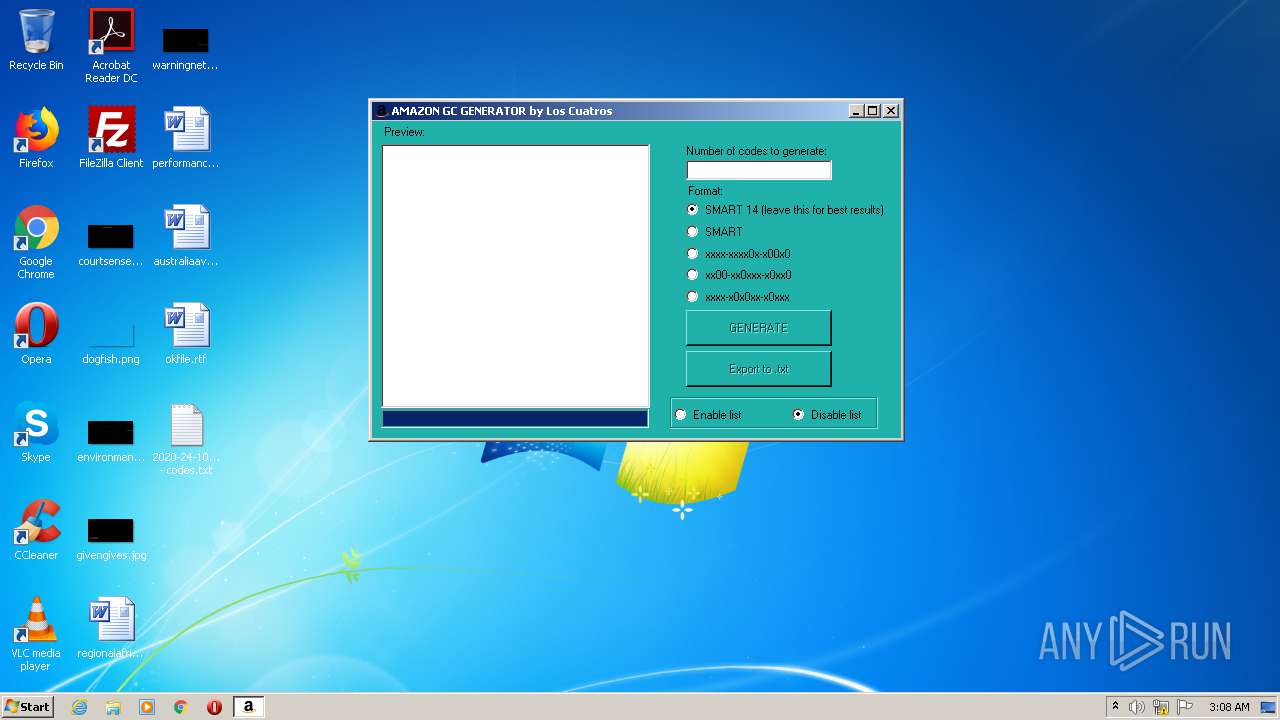
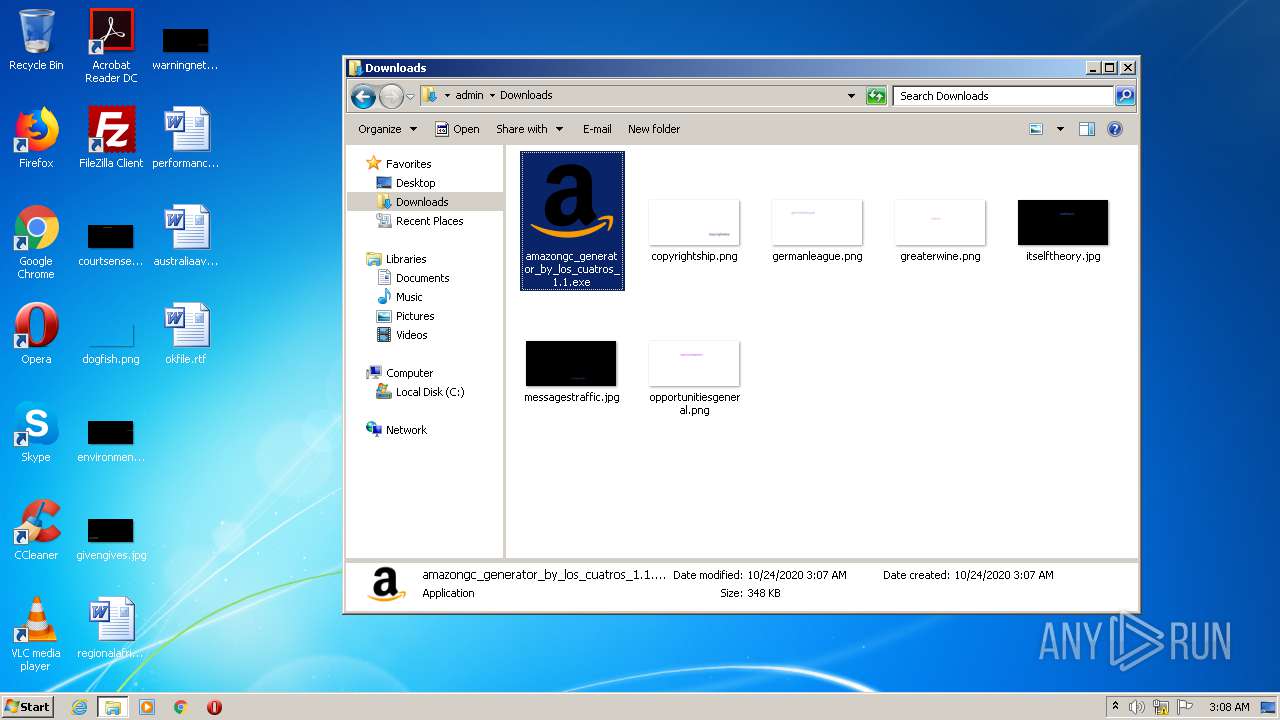
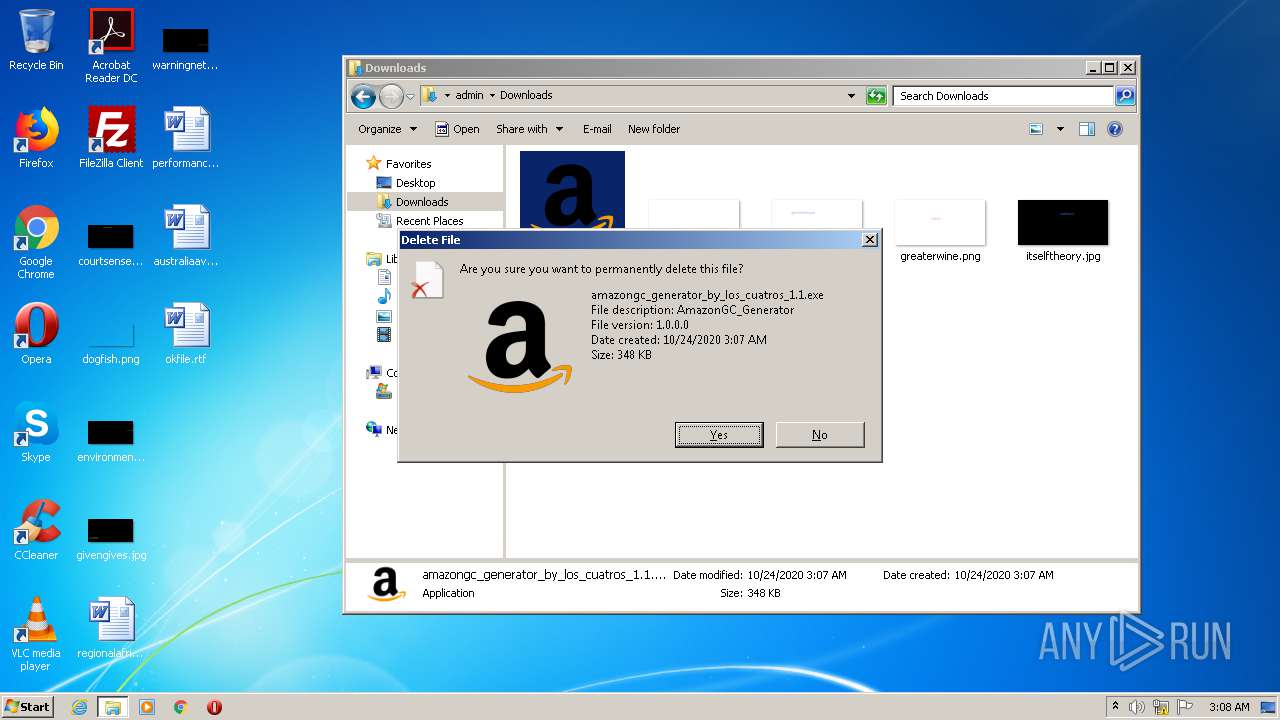
MALICIOUS
Application was dropped or rewritten from another process
- amazongc_generator_by_los_cuatros_1.1.exe (PID: 3508)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 1136)
- iexplore.exe (PID: 3564)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1136)
Reads Internet Cache Settings
- iexplore.exe (PID: 1136)
- iexplore.exe (PID: 3564)
Reads settings of System Certificates
- iexplore.exe (PID: 3564)
Application launched itself
- iexplore.exe (PID: 1136)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1136)
Manual execution by user
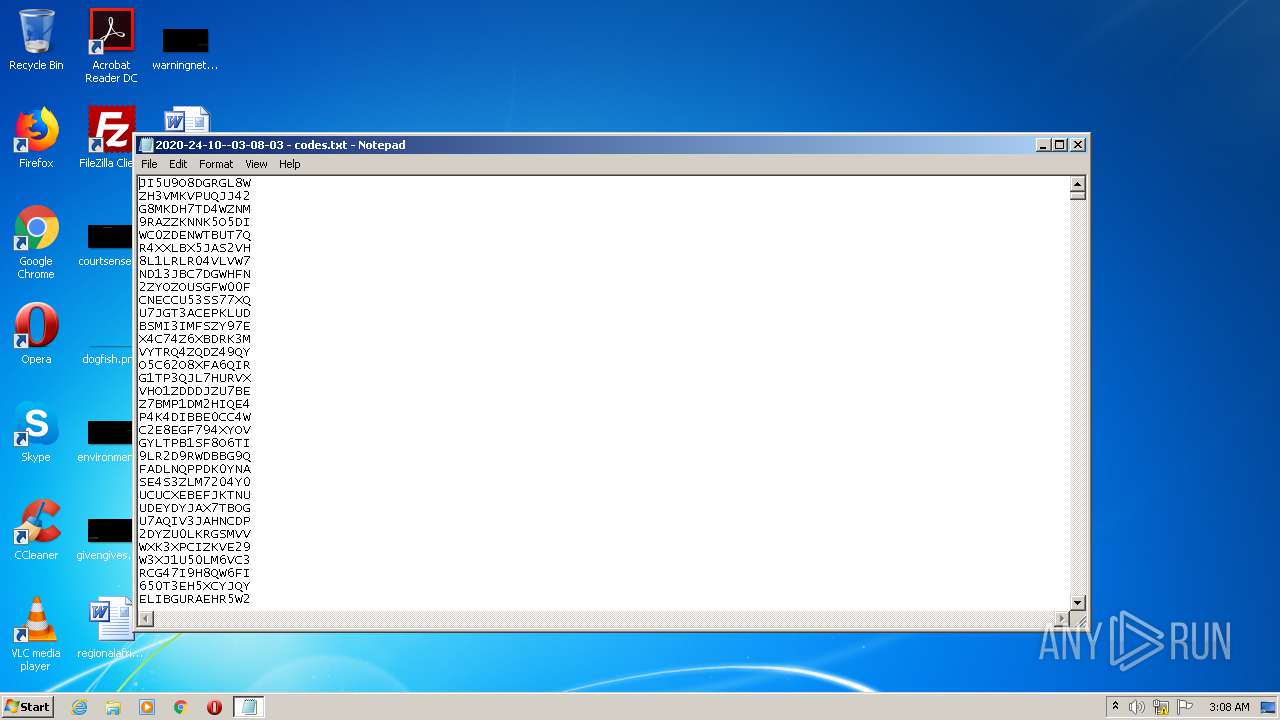
- NOTEPAD.EXE (PID: 3256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1136 | "C:\Program Files\Internet Explorer\iexplore.exe" https://siasky.net/PAHzB-9QA_CZsKZqFQ2oV2rgKCBk7j0bl5rb7Sr24PoNdQ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3256 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\2020-24-10--03-08-03 - codes.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
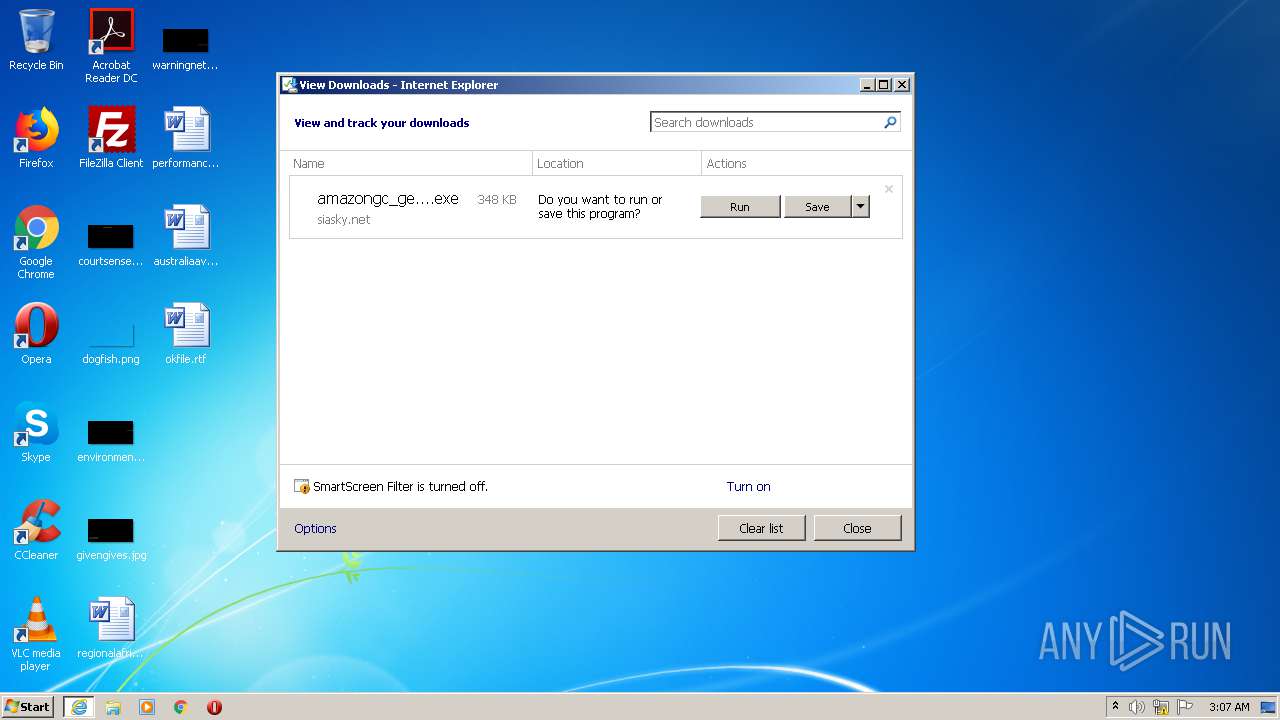
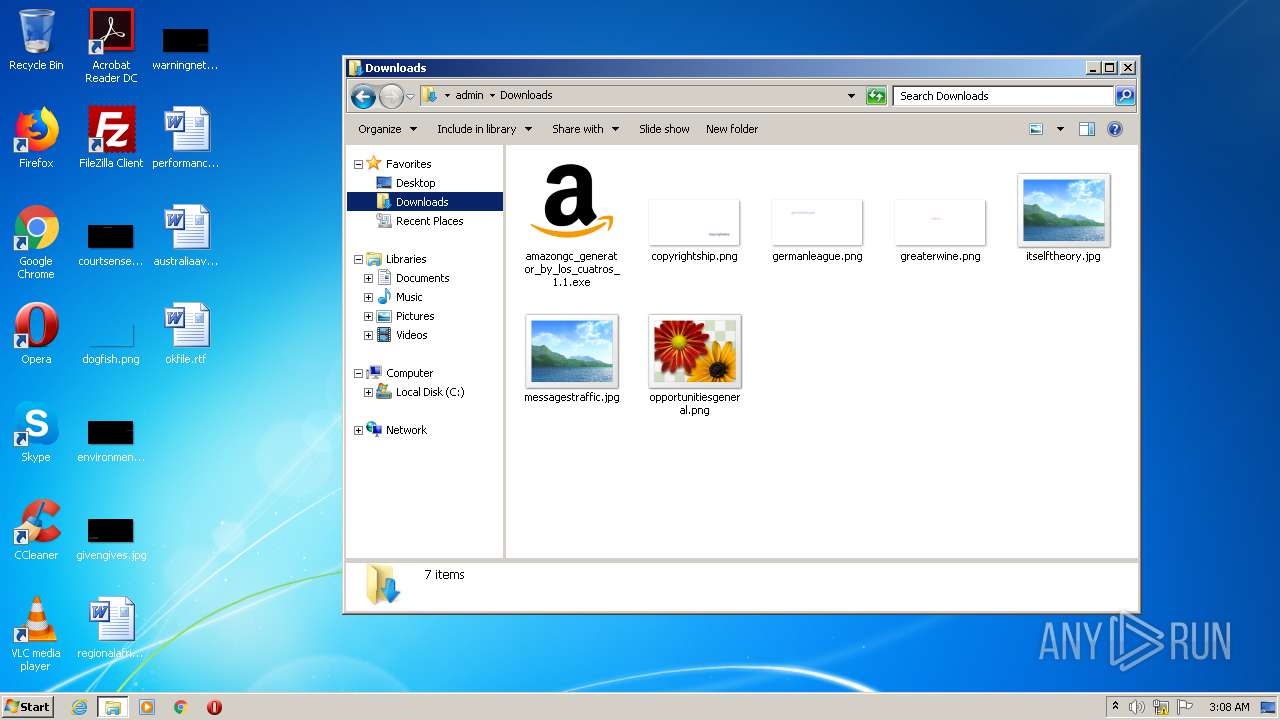
| 3508 | "C:\Users\admin\Downloads\amazongc_generator_by_los_cuatros_1.1.exe" | C:\Users\admin\Downloads\amazongc_generator_by_los_cuatros_1.1.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AmazonGC_Generator Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3564 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1136 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
754
Read events
708
Write events
45
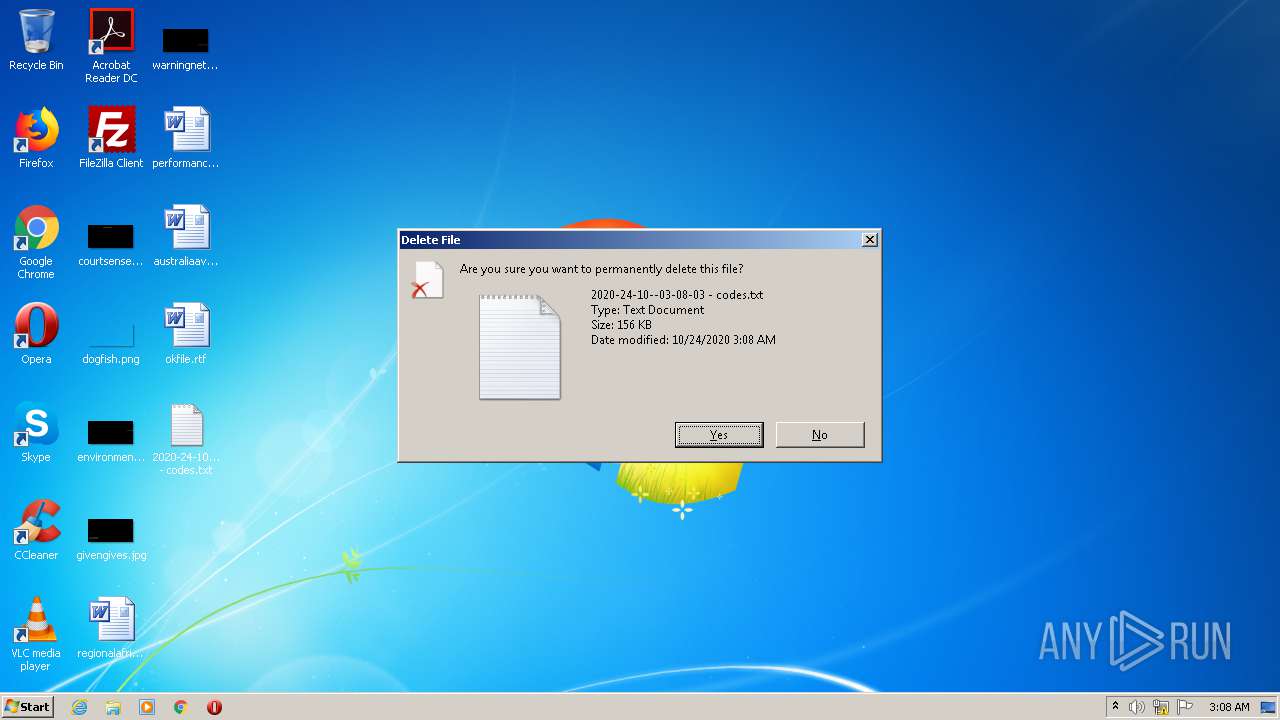
Delete events
1
Modification events
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2203533466 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30845354 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
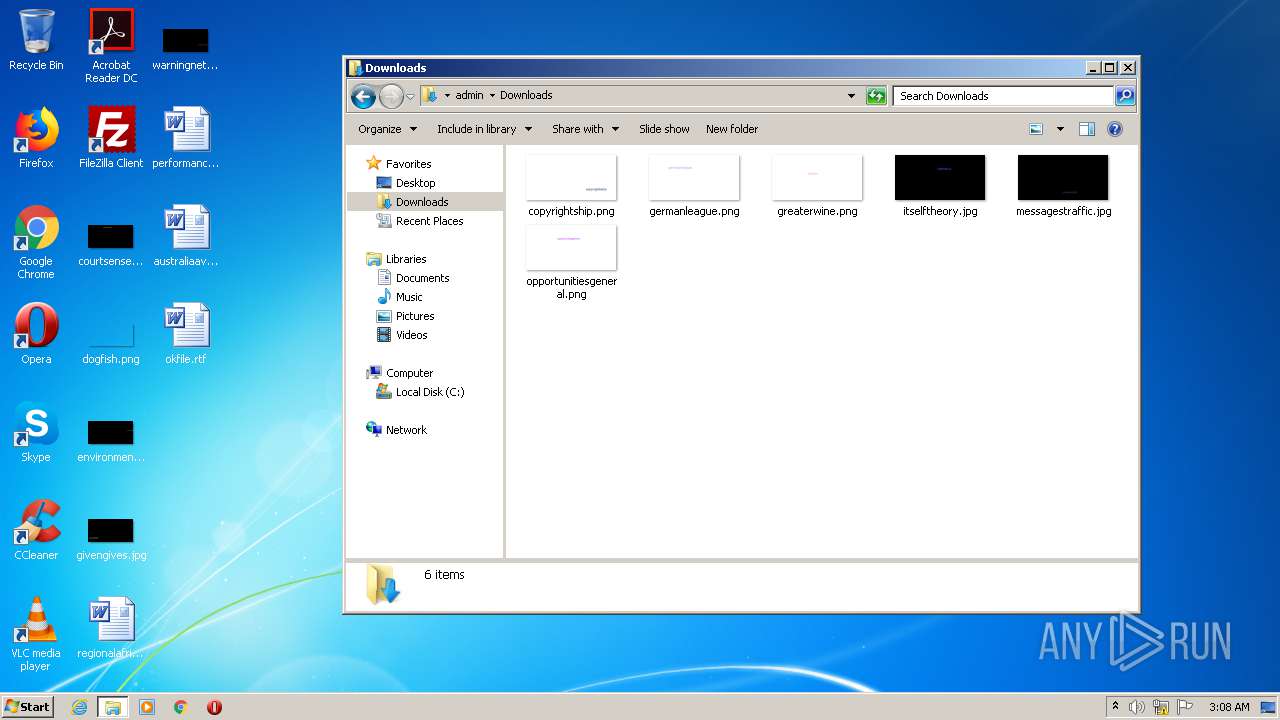
Executable files
3
Suspicious files
5
Text files
2
Unknown types
2
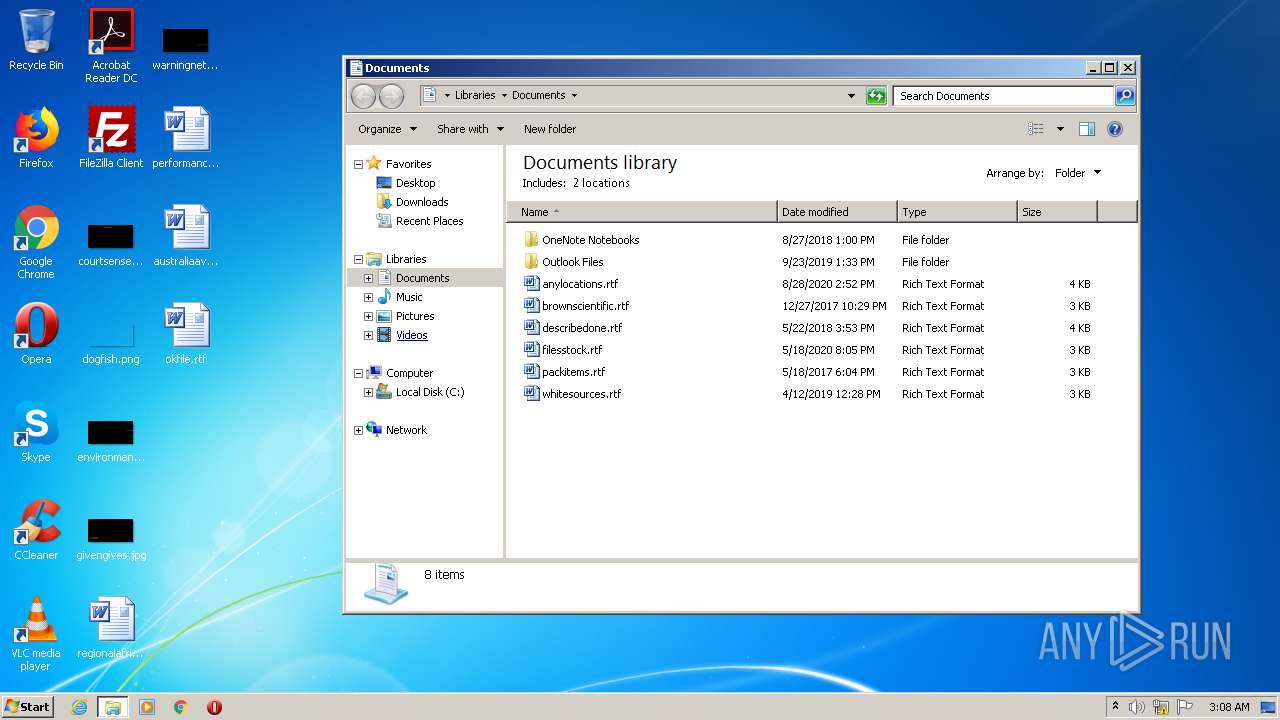
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab4F6D.tmp | — | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar4F6E.tmp | — | |
MD5:— | SHA256:— | |||
| 1136 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC716CB1CC47FBA8A.TMP | — | |
MD5:— | SHA256:— | |||
| 1136 | iexplore.exe | C:\Users\admin\Downloads\amazongc_generator_by_los_cuatros_1.1.exe.m7id5d5.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 1136 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB90ECA3A8DC96A51.TMP | — | |
MD5:— | SHA256:— | |||
| 1136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{AF13DB59-159D-11EB-85AF-12A9866C77DE}.dat | — | |
MD5:— | SHA256:— | |||
| 1136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{AF13DB5B-159D-11EB-85AF-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 3508 | amazongc_generator_by_los_cuatros_1.1.exe | C:\Users\admin\Desktop\2020-24-10--03-08-03 - codes.txt | text | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3564 | iexplore.exe | GET | 200 | 2.16.177.195:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3564 | iexplore.exe | GET | 200 | 2.16.177.195:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3564 | iexplore.exe | 144.76.198.38:443 | siasky.net | Hetzner Online GmbH | DE | unknown |
3564 | iexplore.exe | 2.16.177.195:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
siasky.net |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |