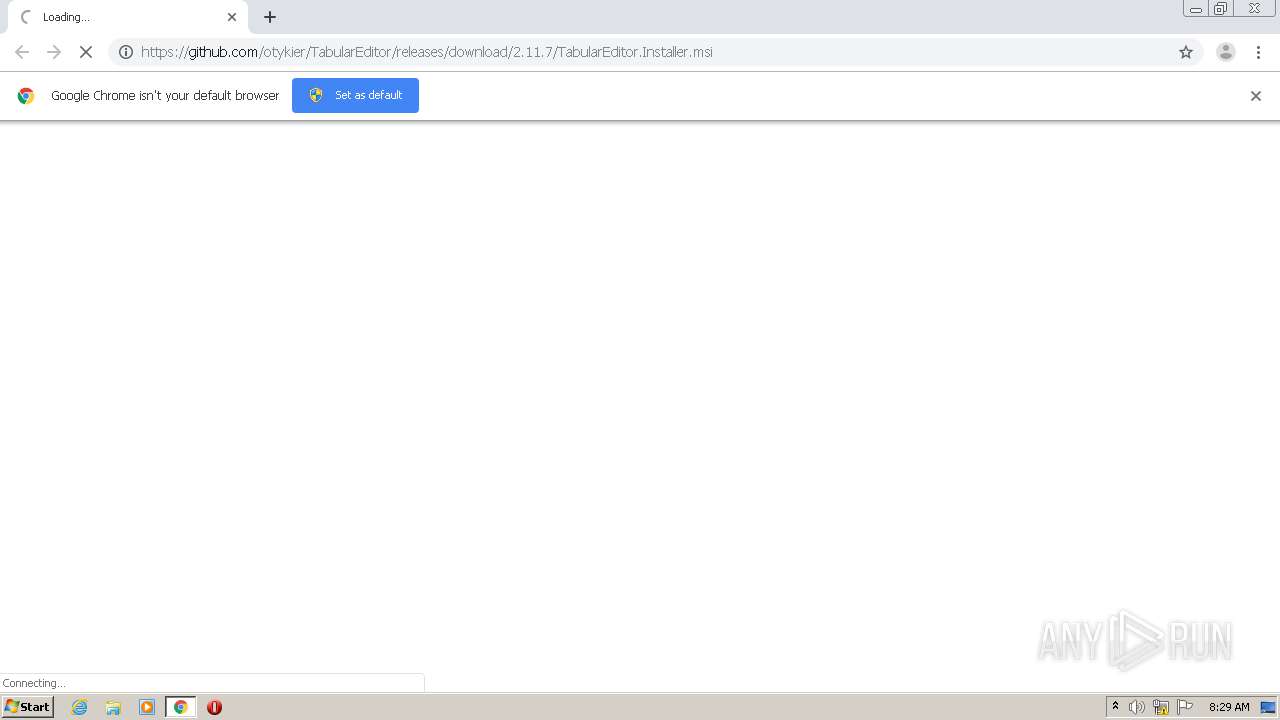
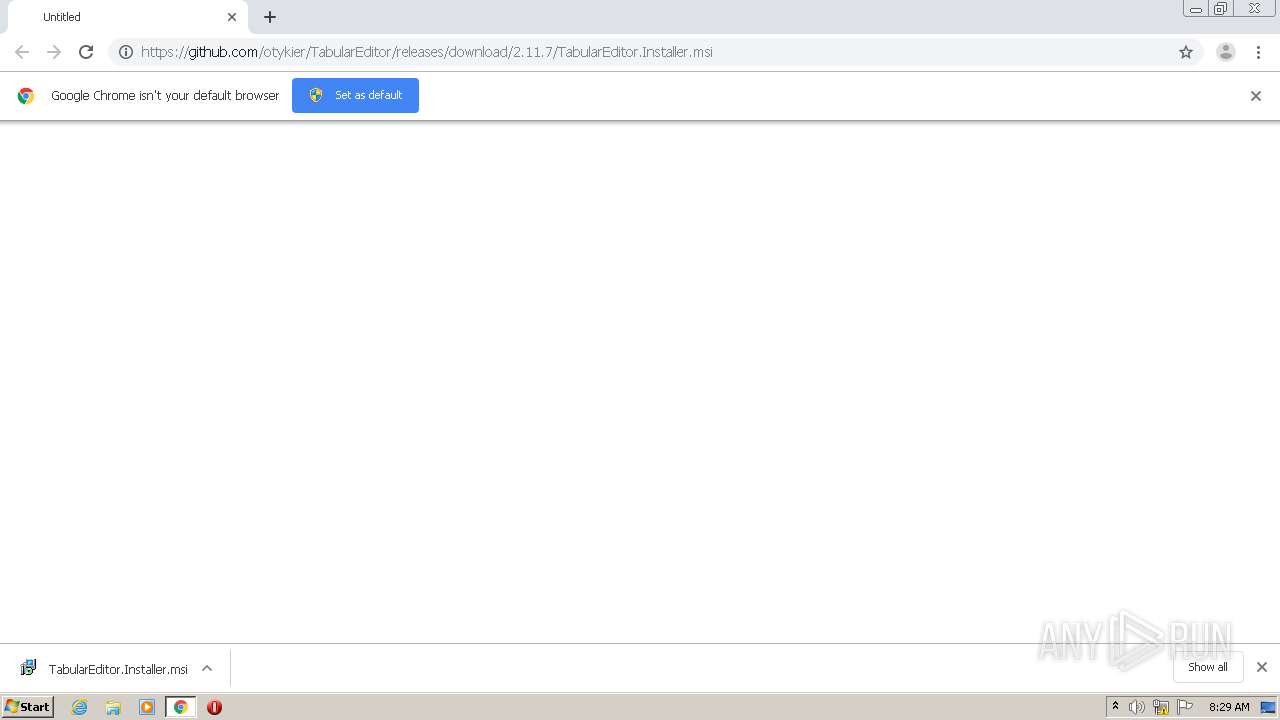
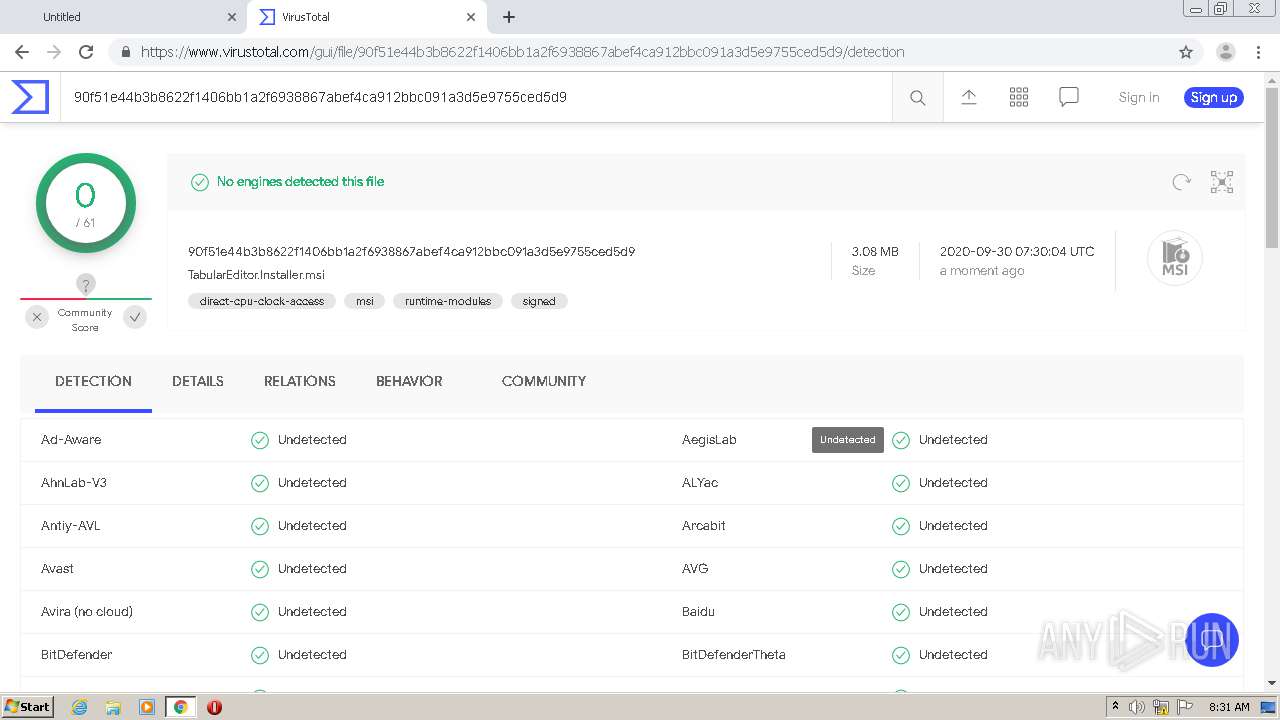
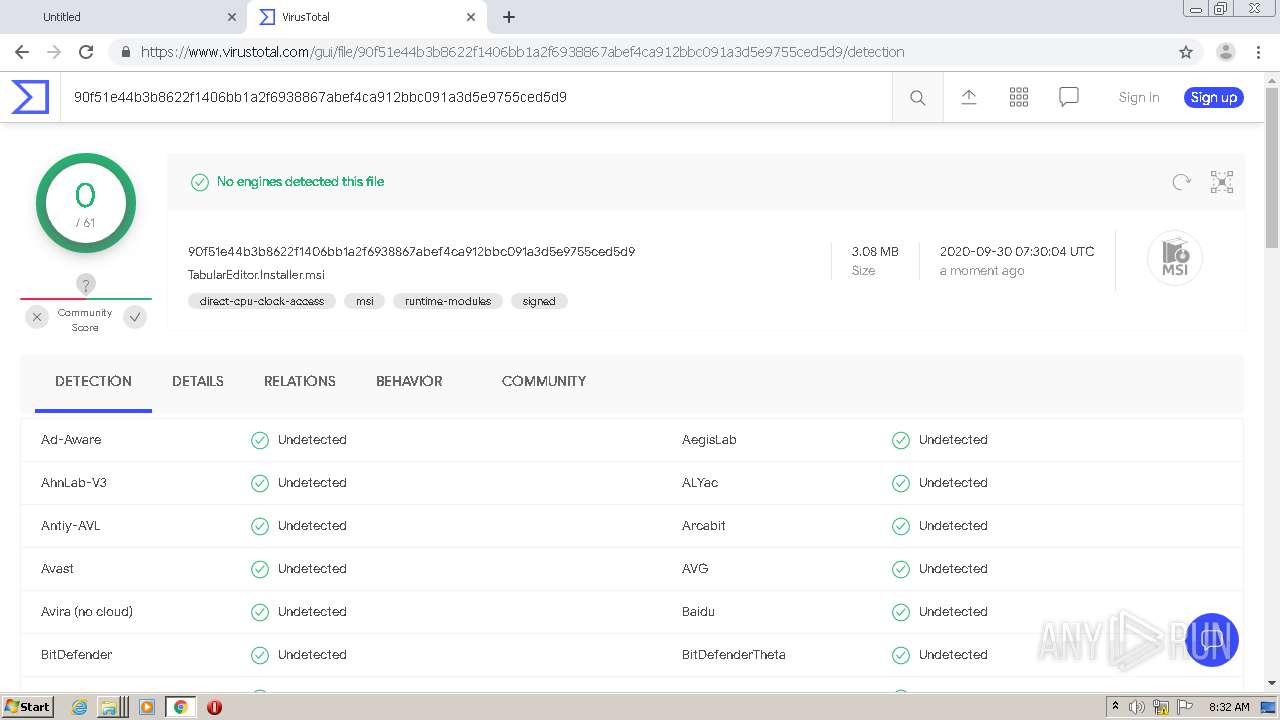
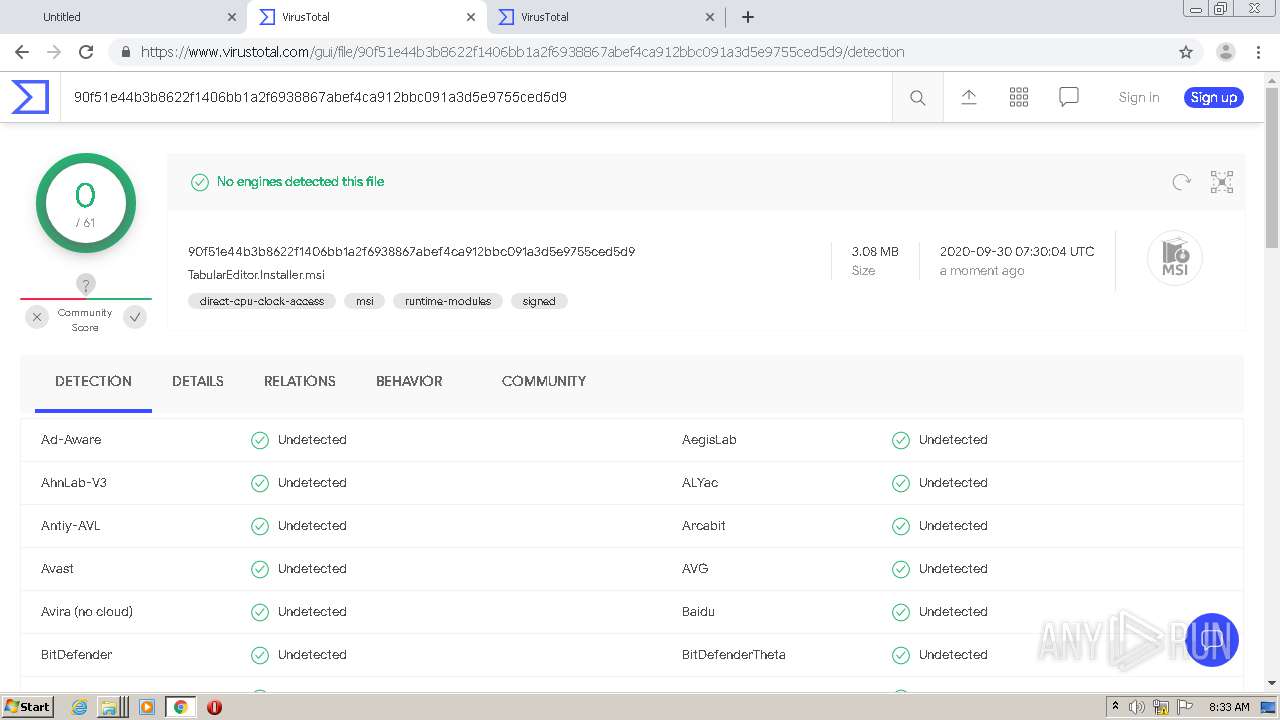
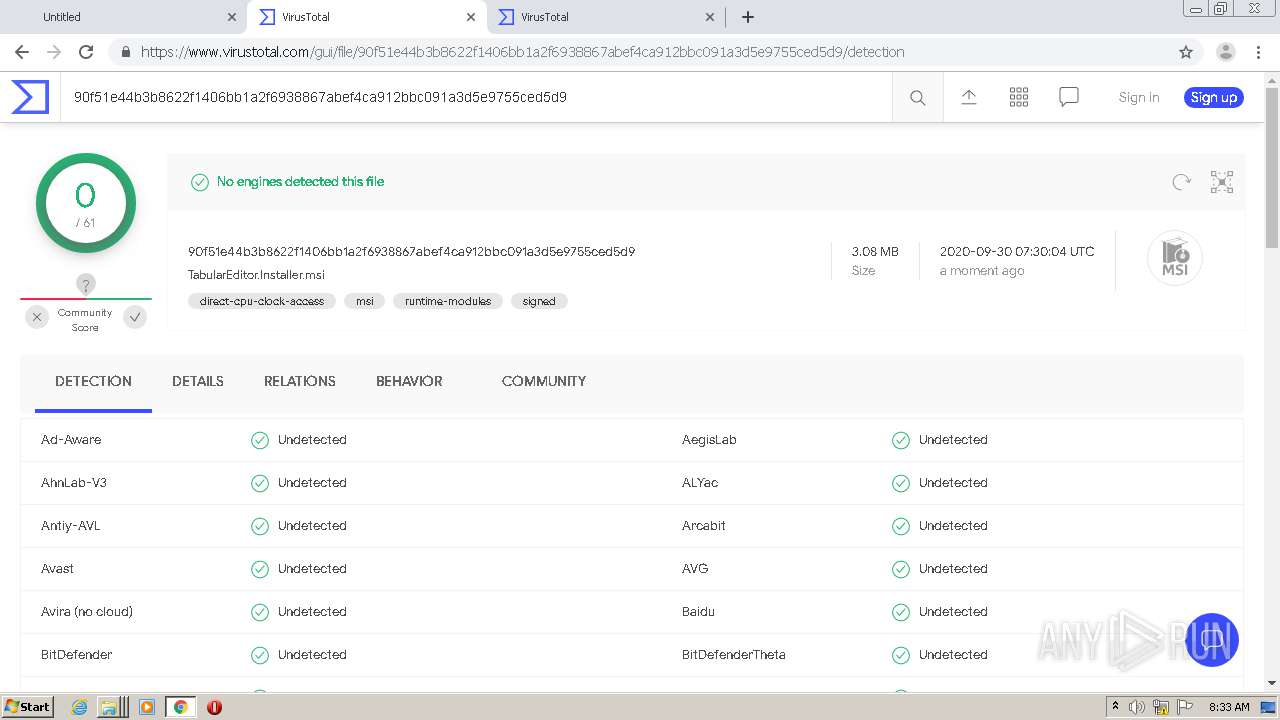
| URL: | https://github.com/otykier/TabularEditor/releases/download/2.11.7/TabularEditor.Installer.msi |
| Full analysis: | https://app.any.run/tasks/b4c6e842-c9b3-481d-a0d0-ca0d7848ad8f |
| Verdict: | Malicious activity |
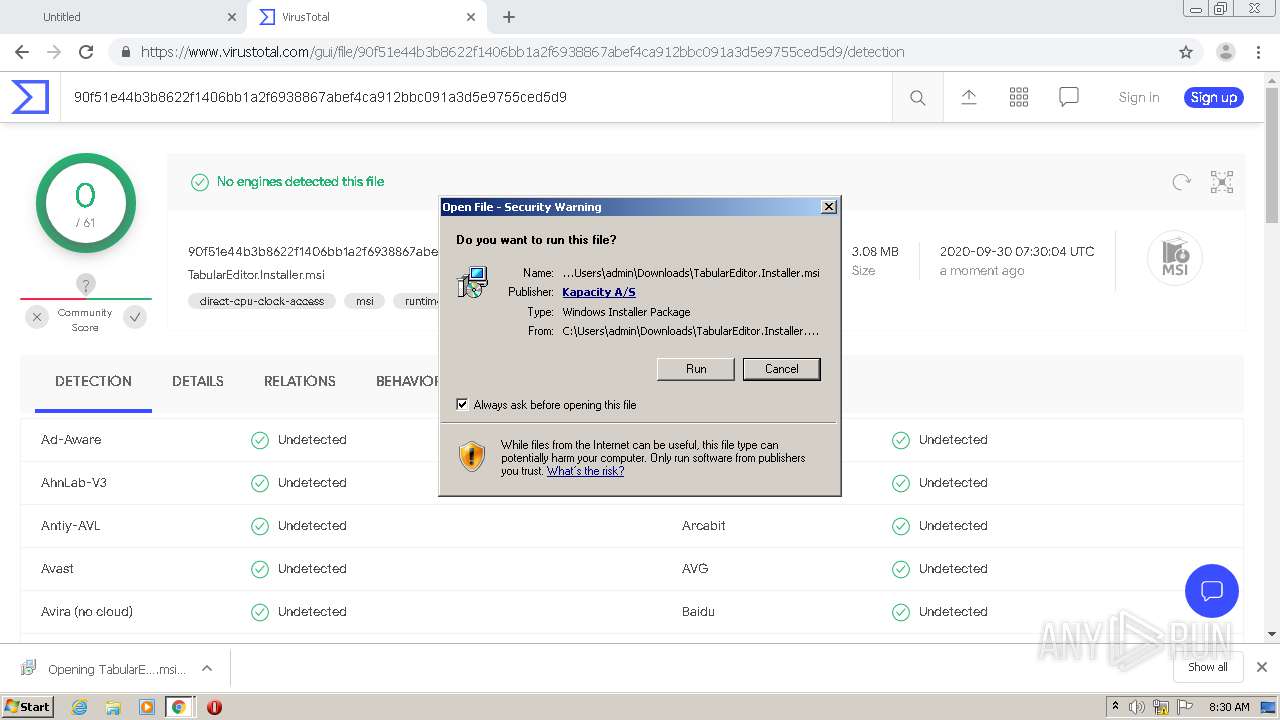
| Analysis date: | September 30, 2020, 07:29:03 |
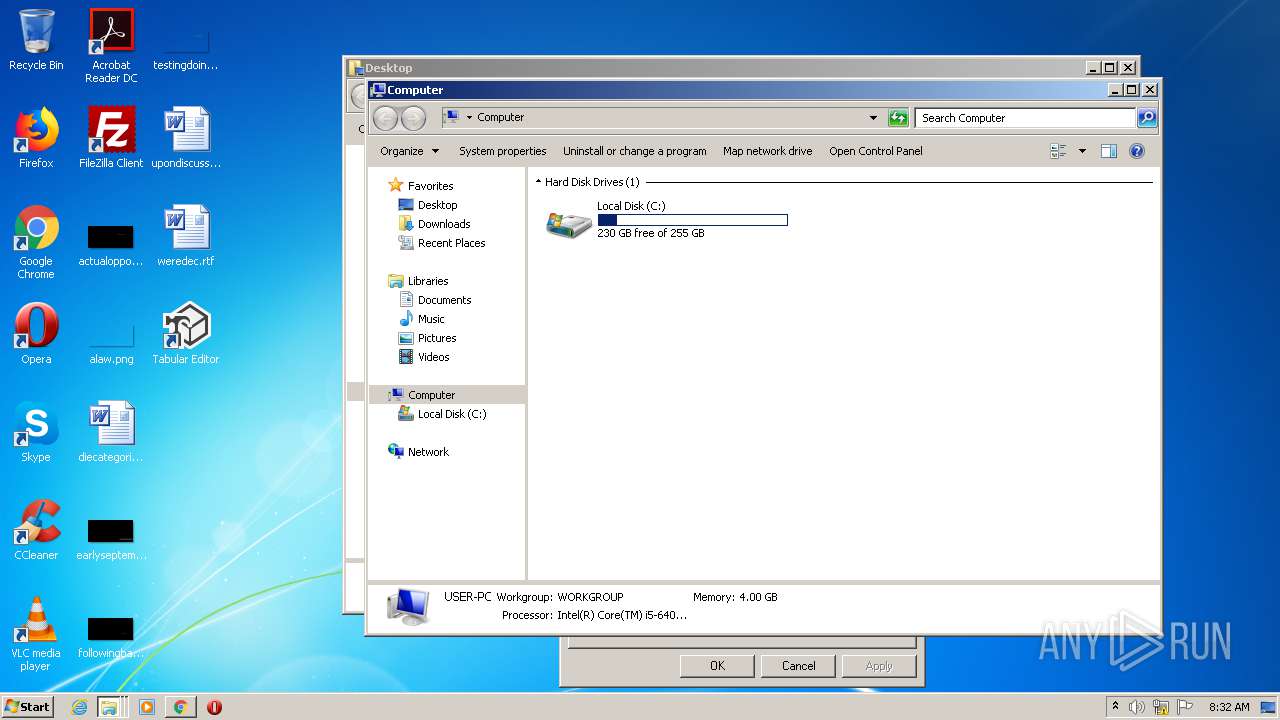
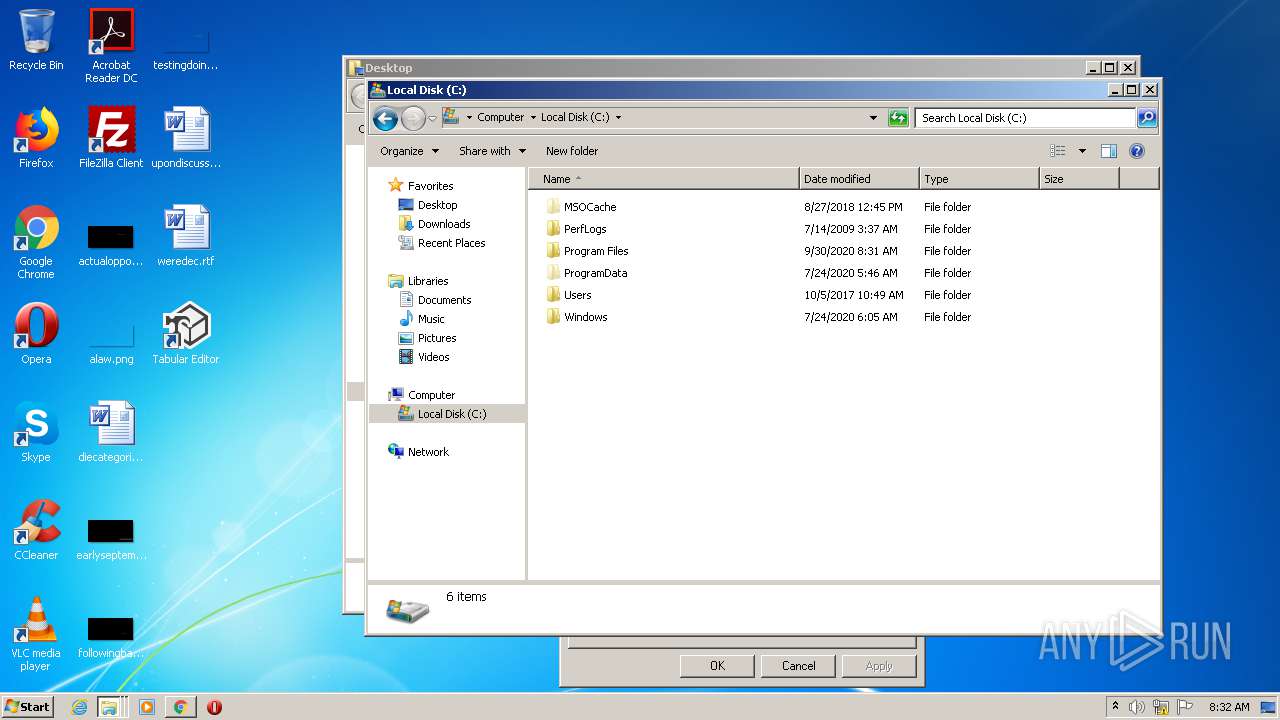
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
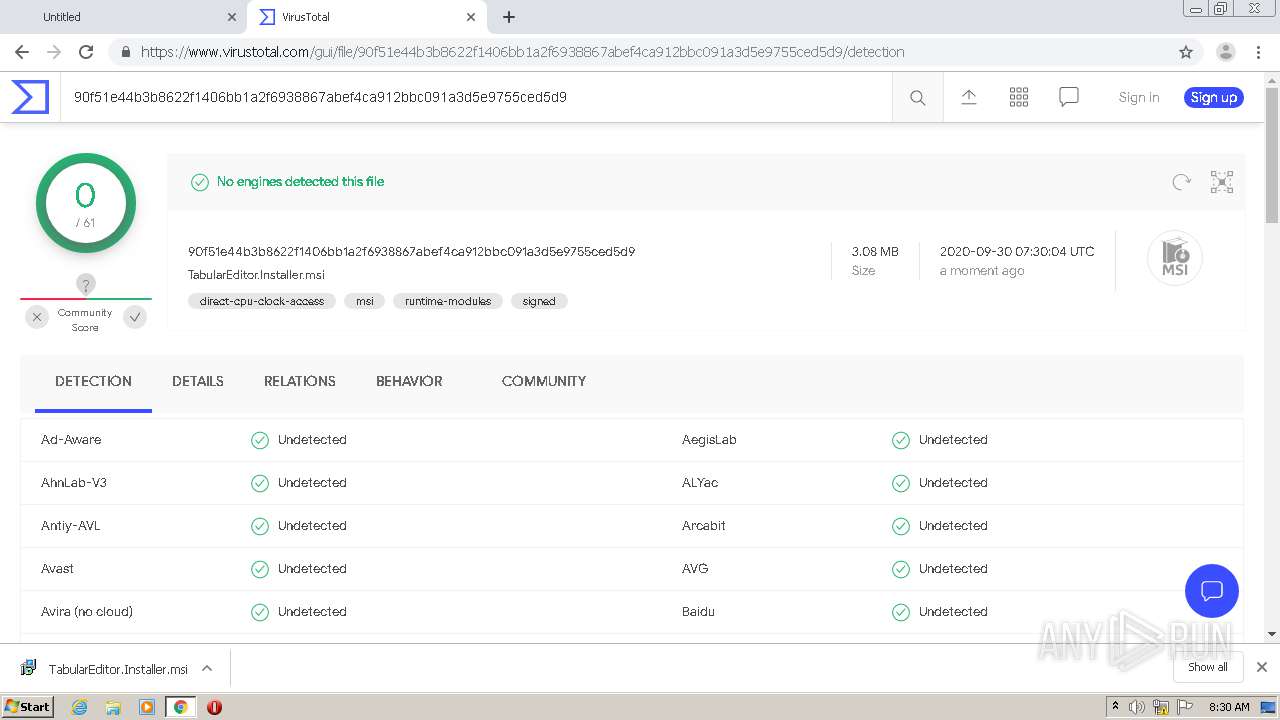
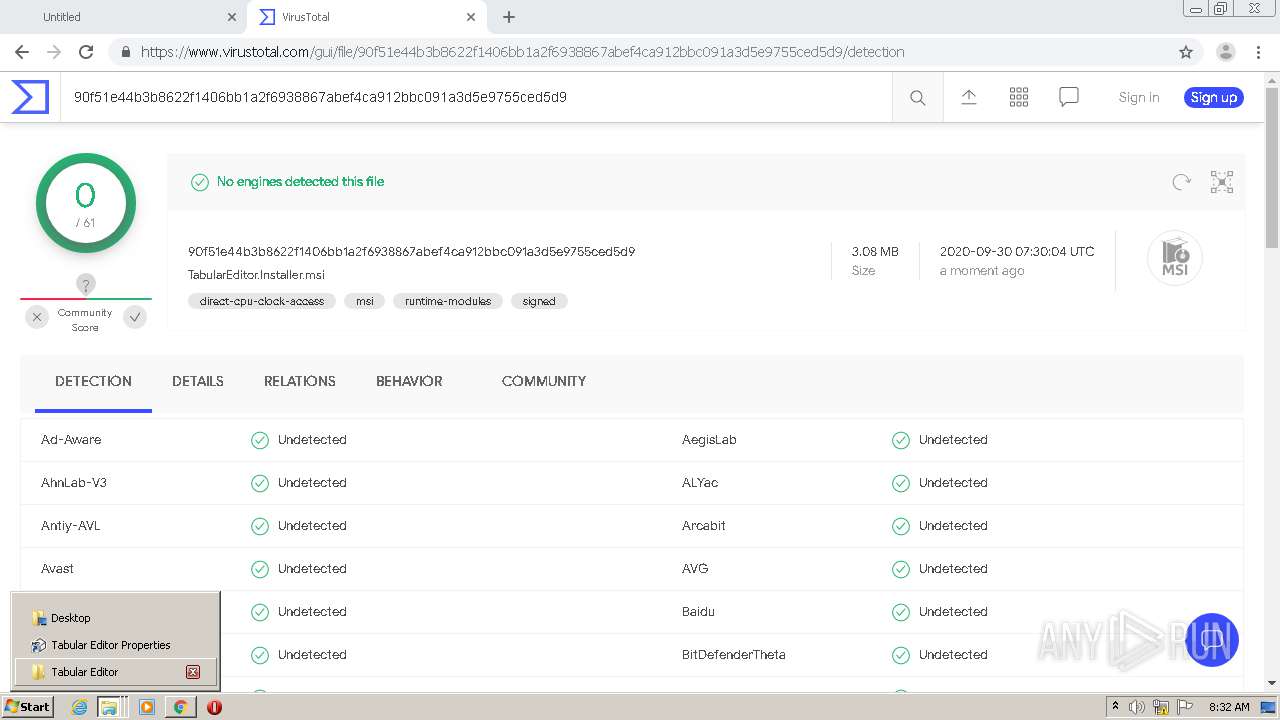
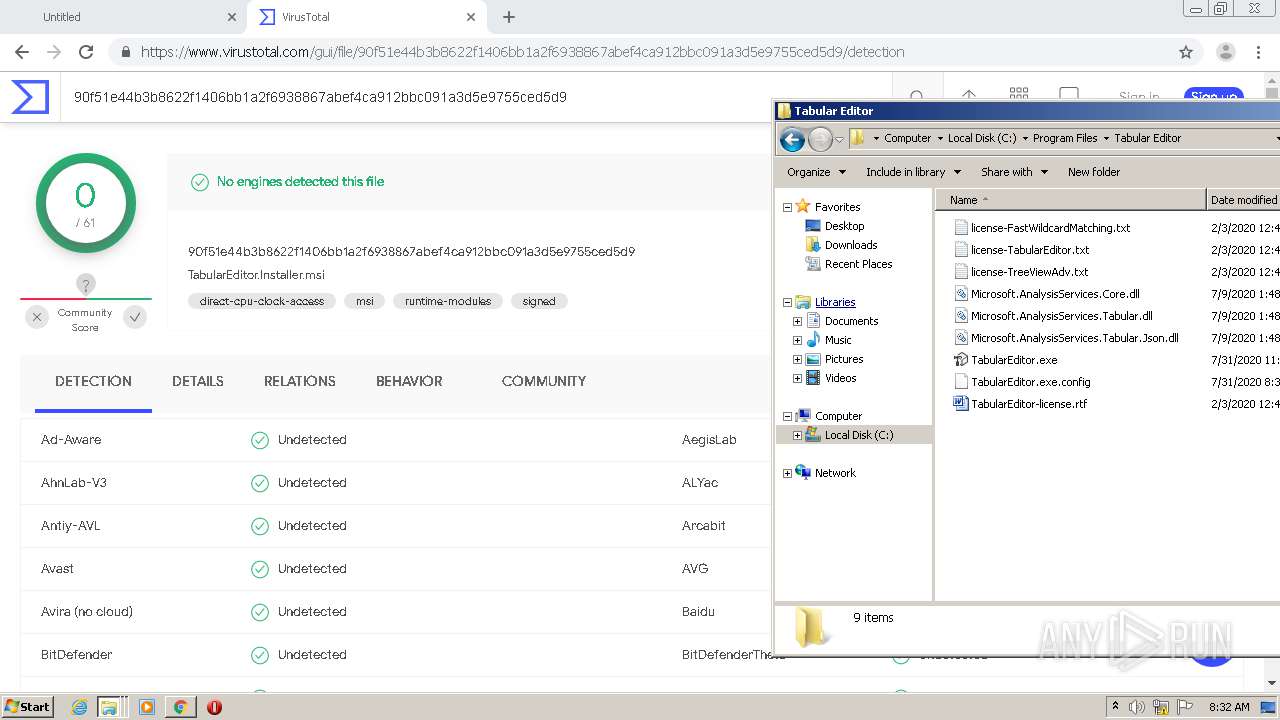
| MD5: | 6CA5A6CF2D7AA53F7C41D2CA9DF1A299 |
| SHA1: | 96F796CFC36006F40B37C4DB00F2AF77414E5067 |
| SHA256: | 0DE10C3736B843658F39CE1607D6407760D3A3293E45C17C6E5CE042C1F4ADAF |
| SSDEEP: | 3:N8tEd6RcdxkEQKchE2kCXt5CHQJ+EQK2WBXLY:2usRcdxkEQKchrhC8+EQK28XLY |
MALICIOUS
Application was dropped or rewritten from another process
- TabularEditor.exe (PID: 1860)
- TabularEditor.exe (PID: 1260)
Loads dropped or rewritten executable
- TabularEditor.exe (PID: 1860)
- TabularEditor.exe (PID: 1260)
SUSPICIOUS
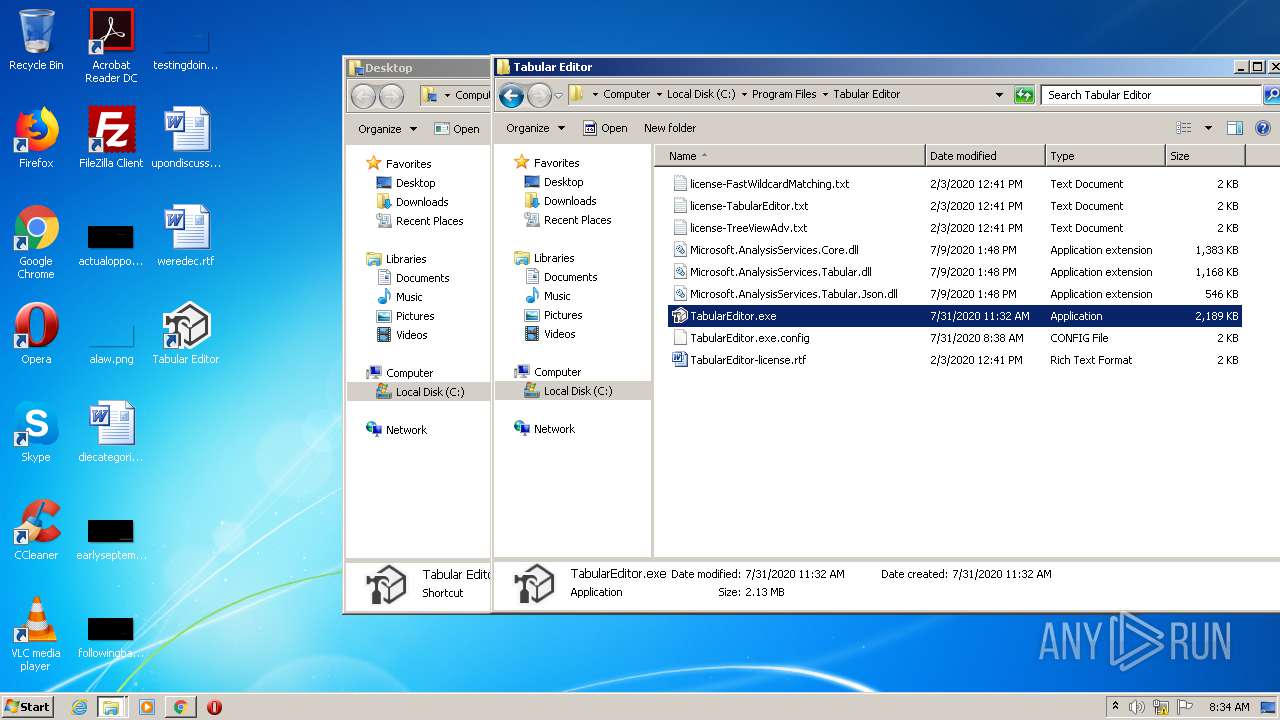
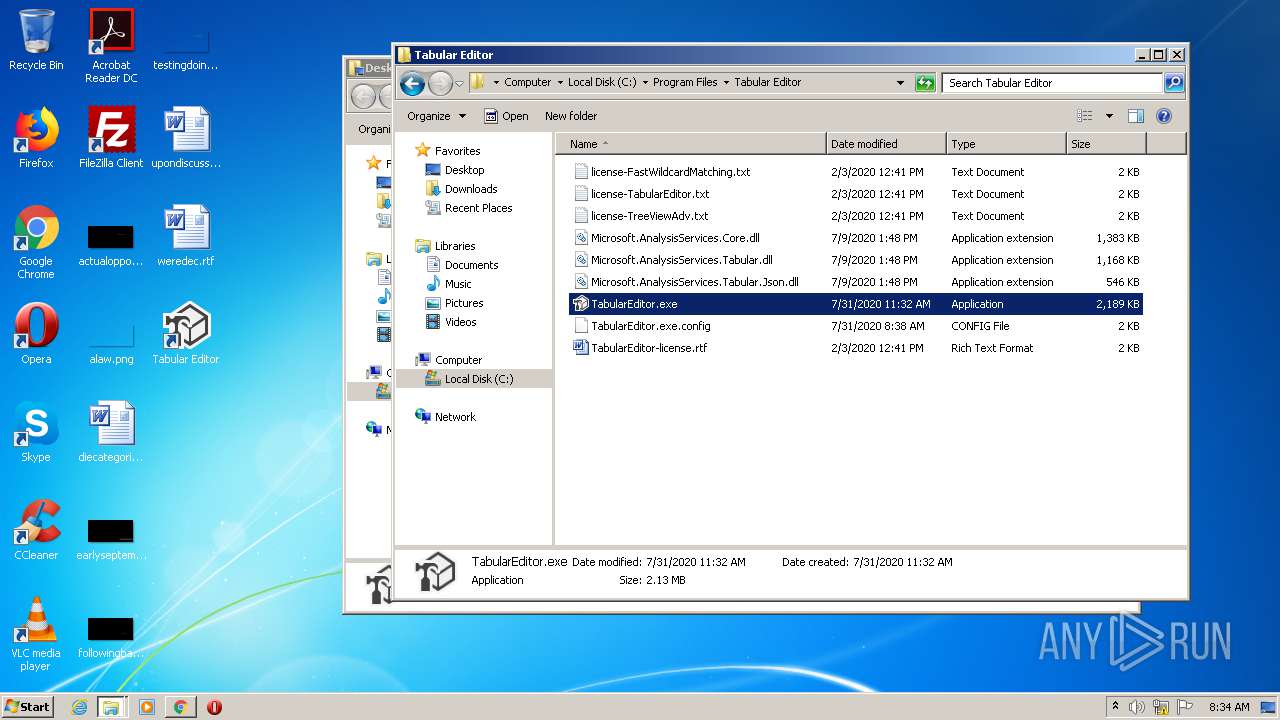
Executable content was dropped or overwritten
- chrome.exe (PID: 316)
- TabularEditor.exe (PID: 1860)
- msiexec.exe (PID: 2100)
- chrome.exe (PID: 2932)
- TabularEditor.exe (PID: 1260)
Executed as Windows Service
- vssvc.exe (PID: 2480)
Creates files in the user directory
- msiexec.exe (PID: 2100)
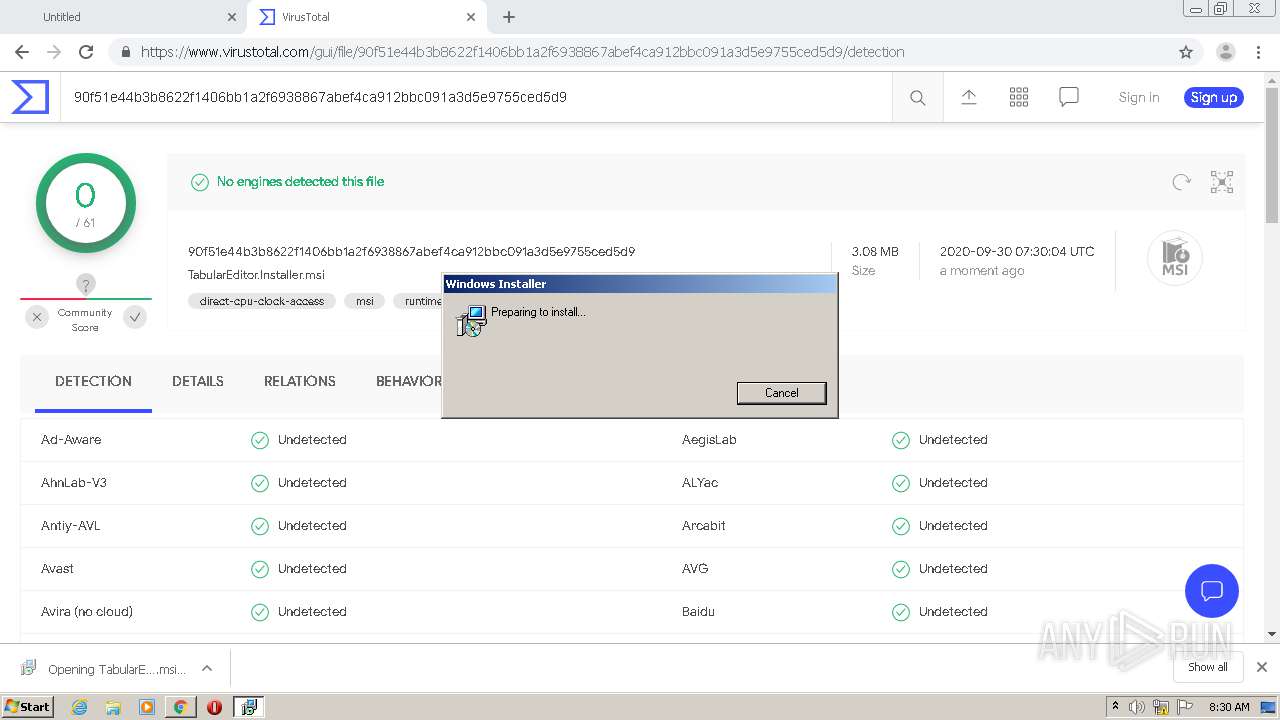
Starts Microsoft Installer
- chrome.exe (PID: 316)
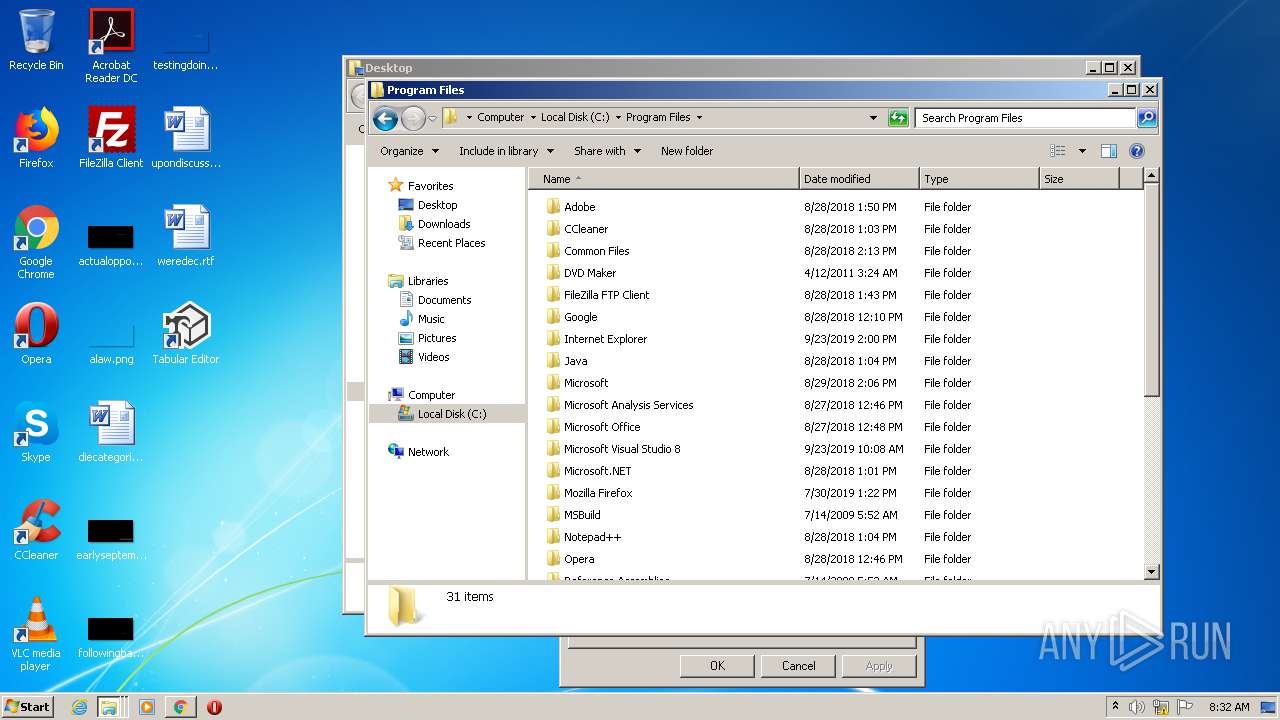
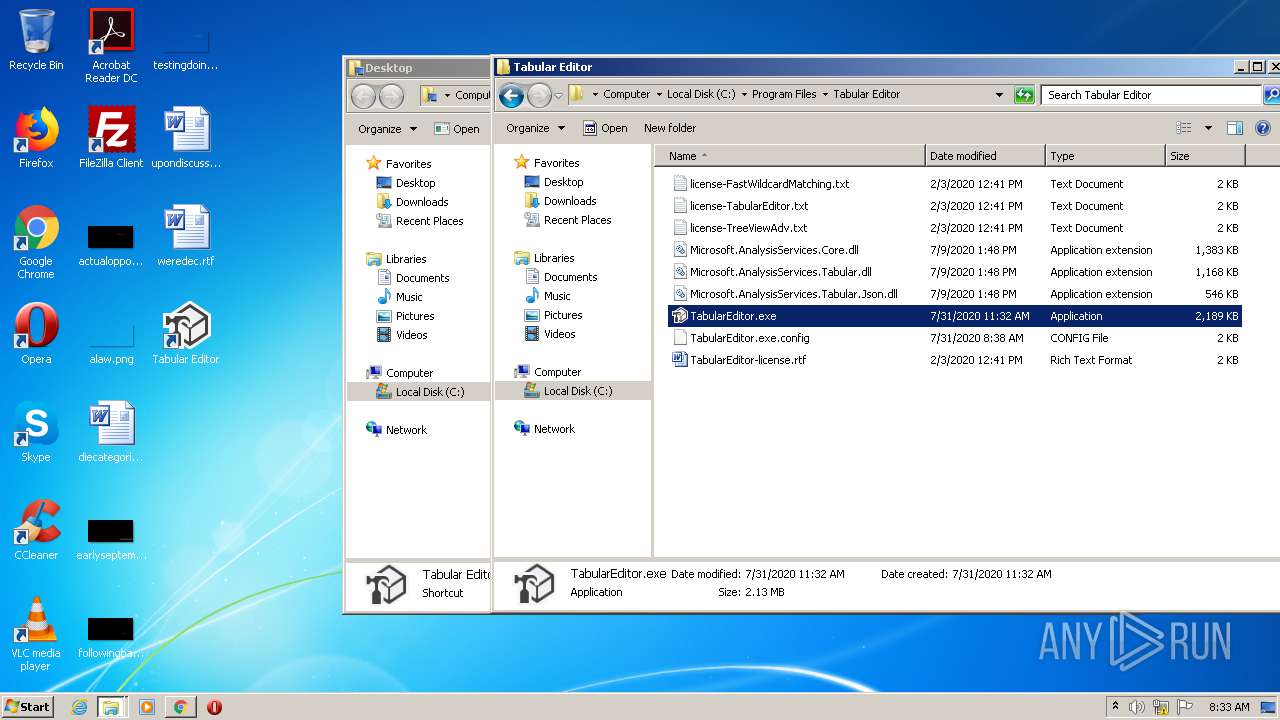
Creates files in the program directory
- TabularEditor.exe (PID: 1860)
Reads internet explorer settings
- TabularEditor.exe (PID: 1860)
INFO
Reads the hosts file
- chrome.exe (PID: 316)
- chrome.exe (PID: 2932)
Application launched itself
- msiexec.exe (PID: 2100)
- chrome.exe (PID: 316)
Searches for installed software
- msiexec.exe (PID: 2100)
Reads Internet Cache Settings
- chrome.exe (PID: 316)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2480)
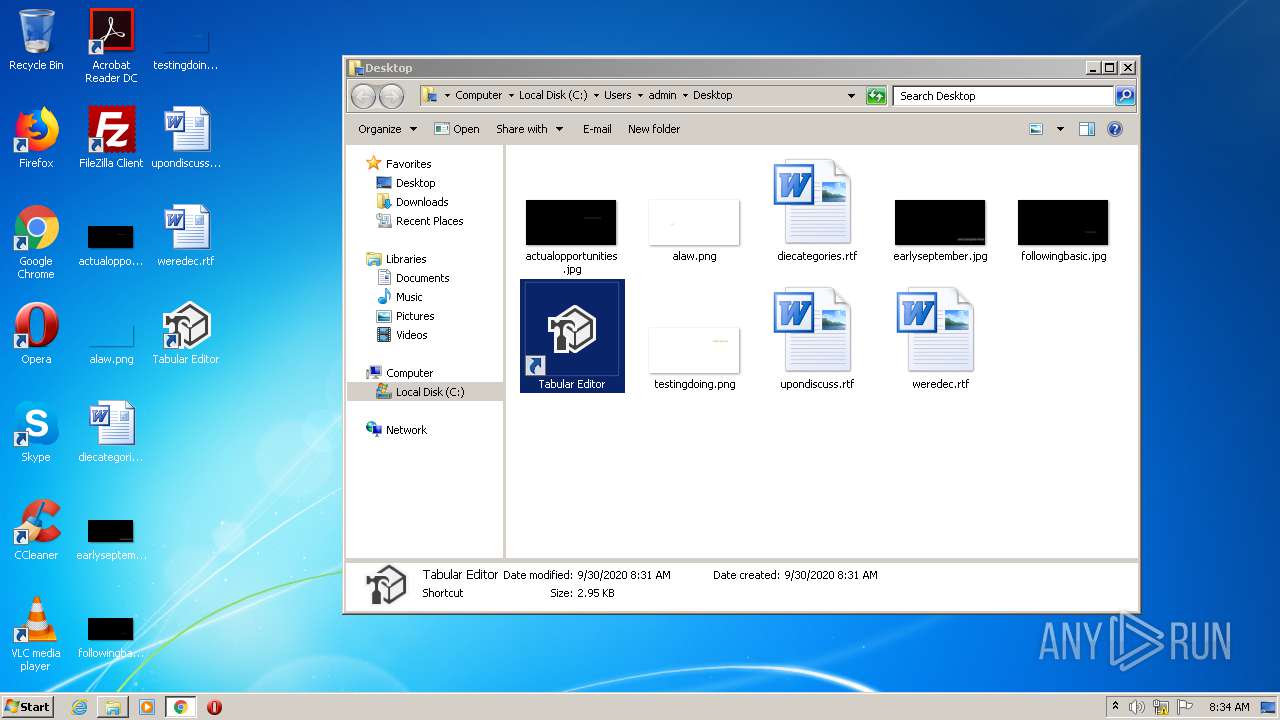
Creates a software uninstall entry
- msiexec.exe (PID: 2100)
Creates files in the program directory
- msiexec.exe (PID: 2100)
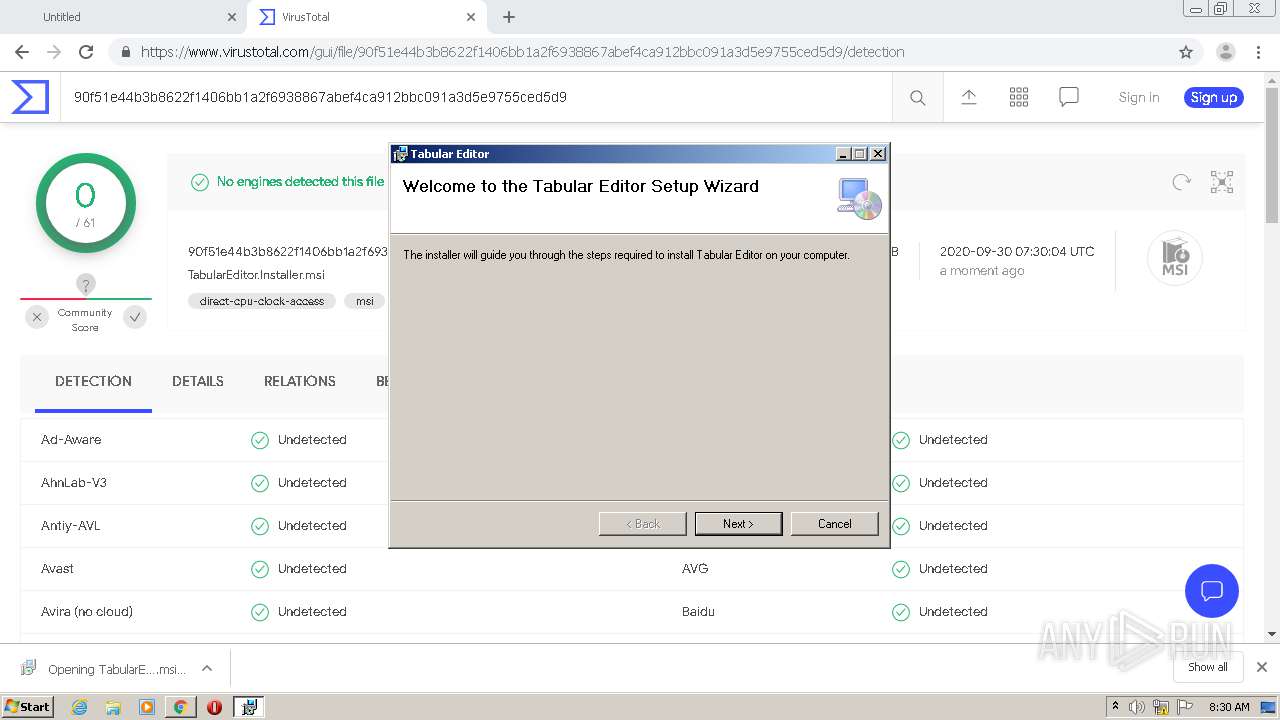
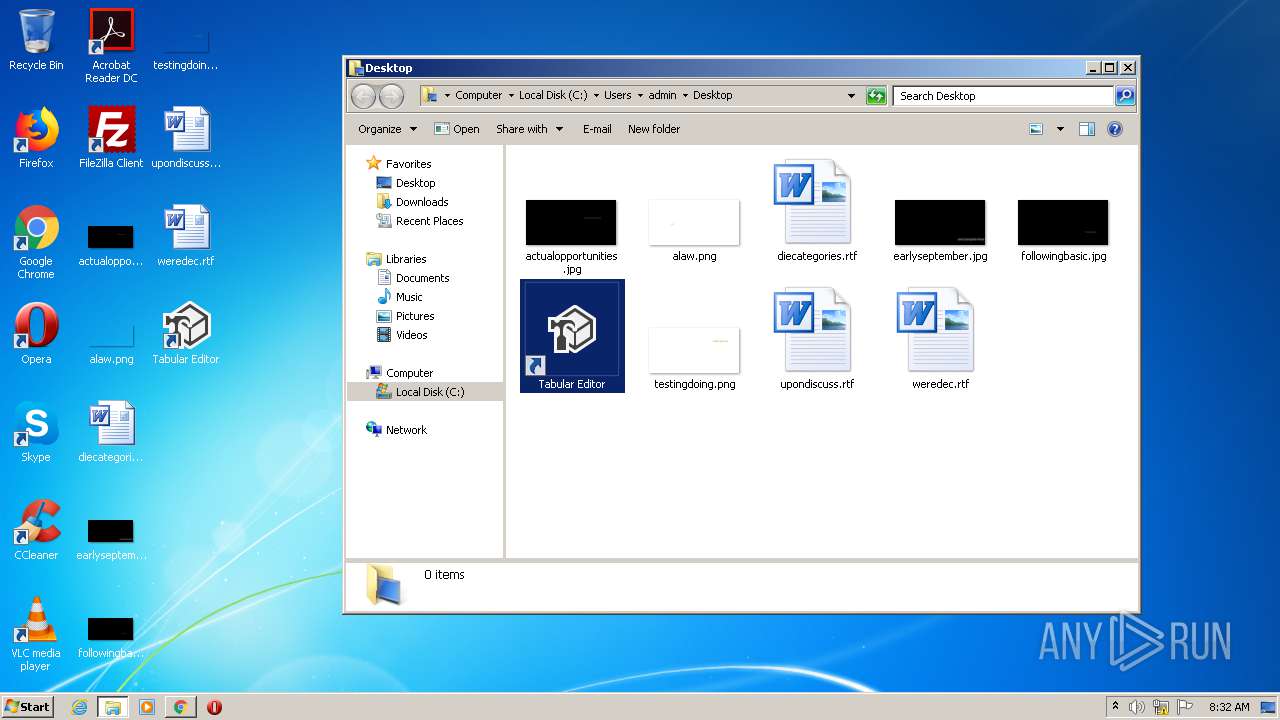
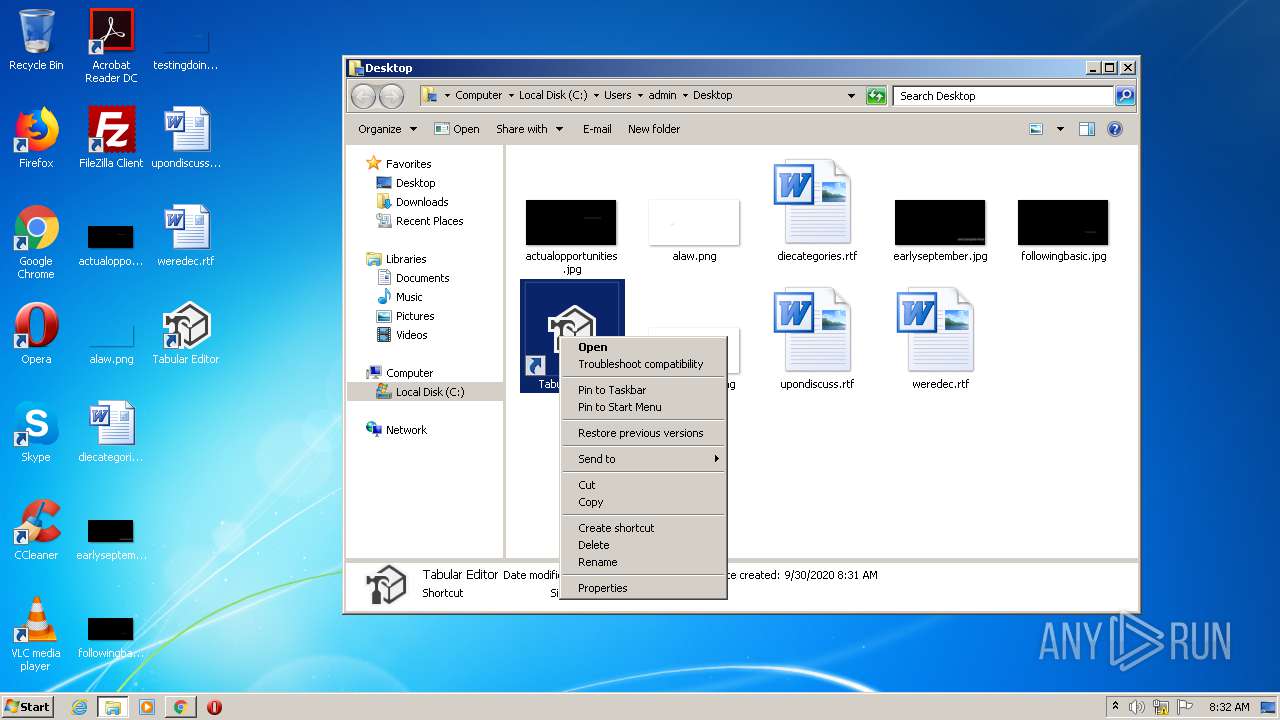
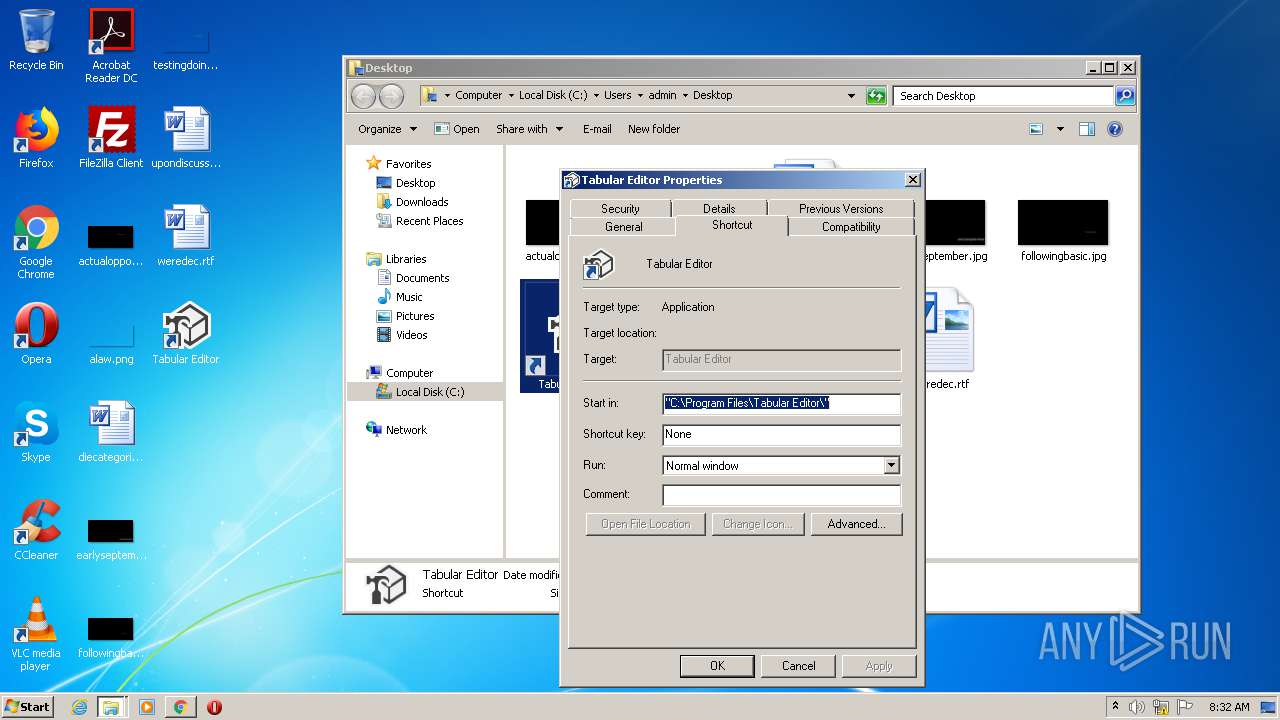
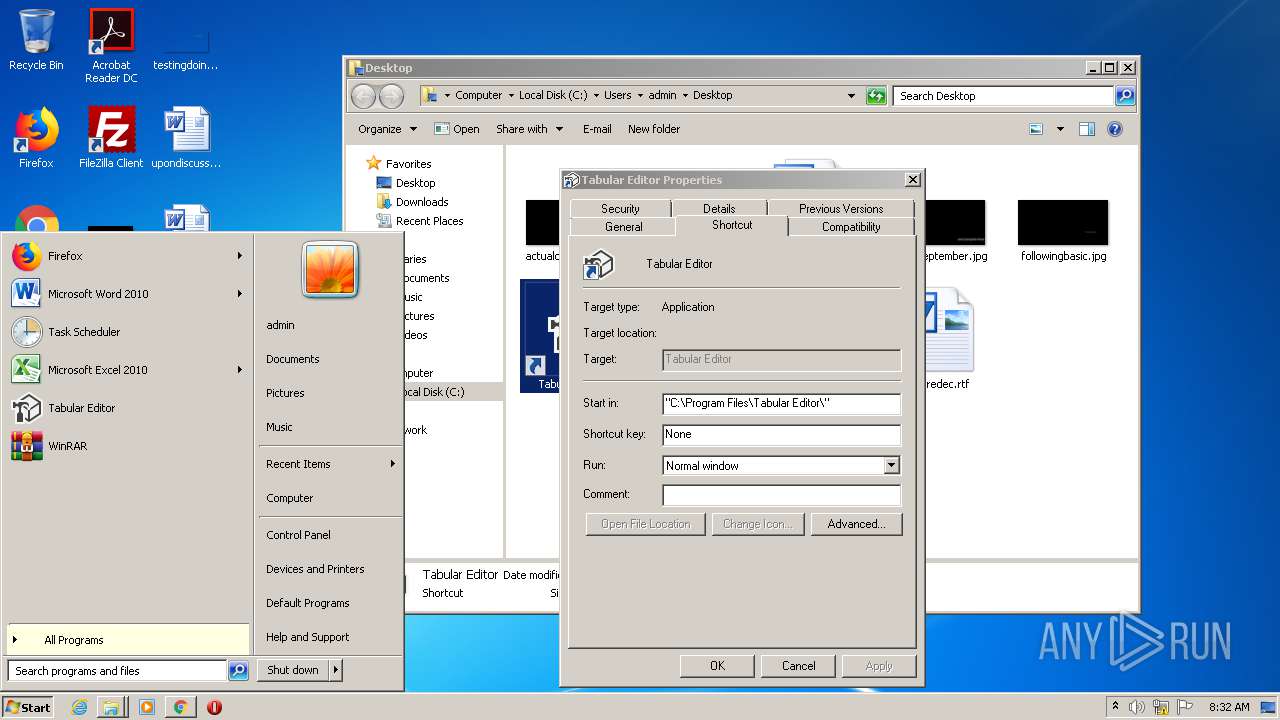
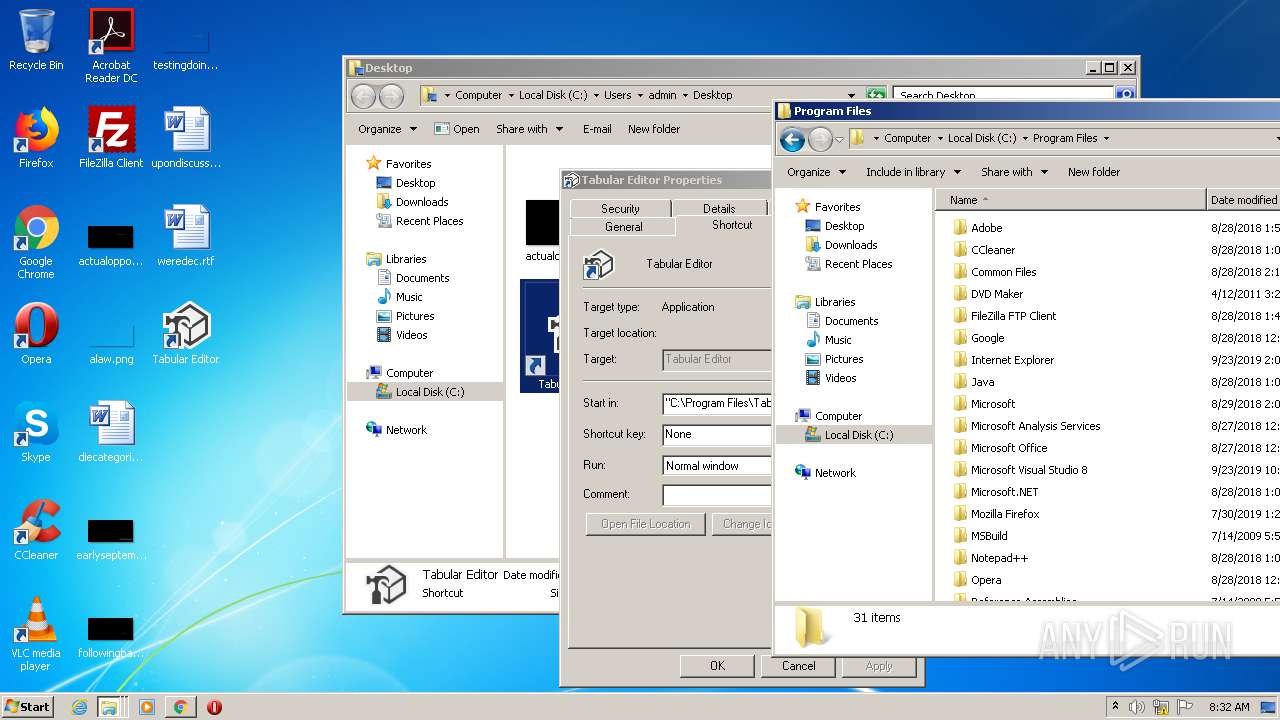
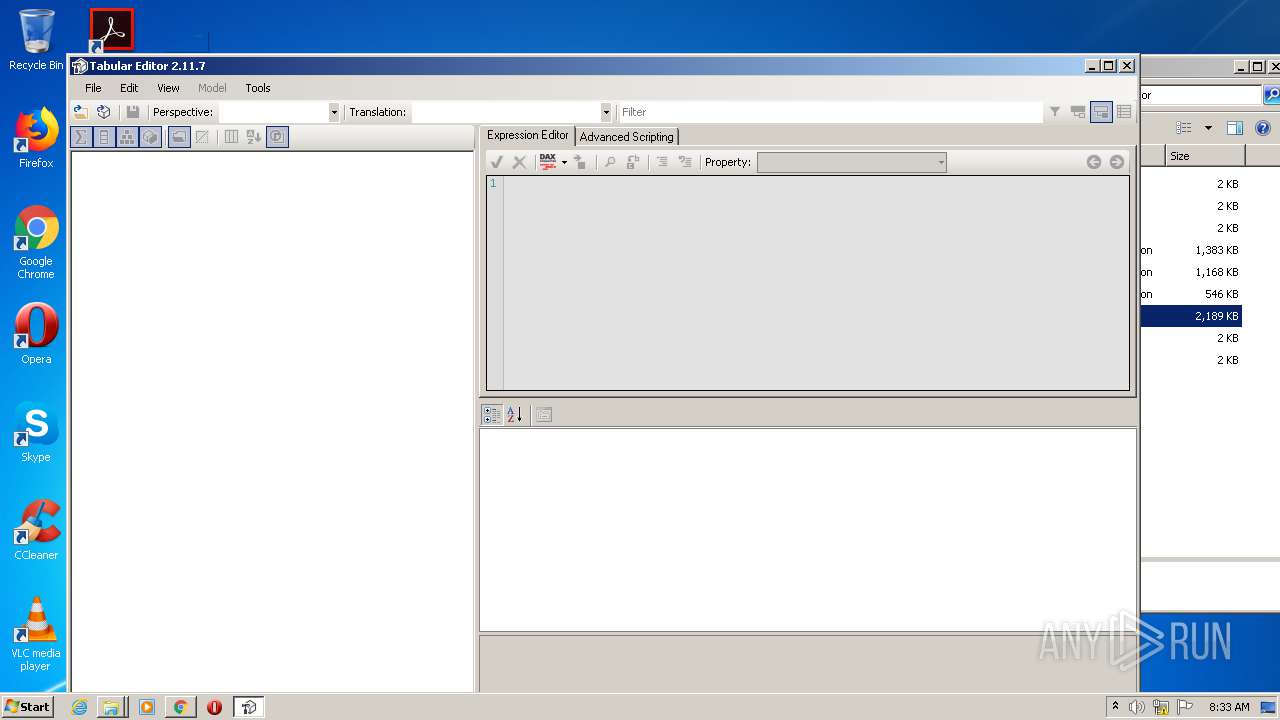
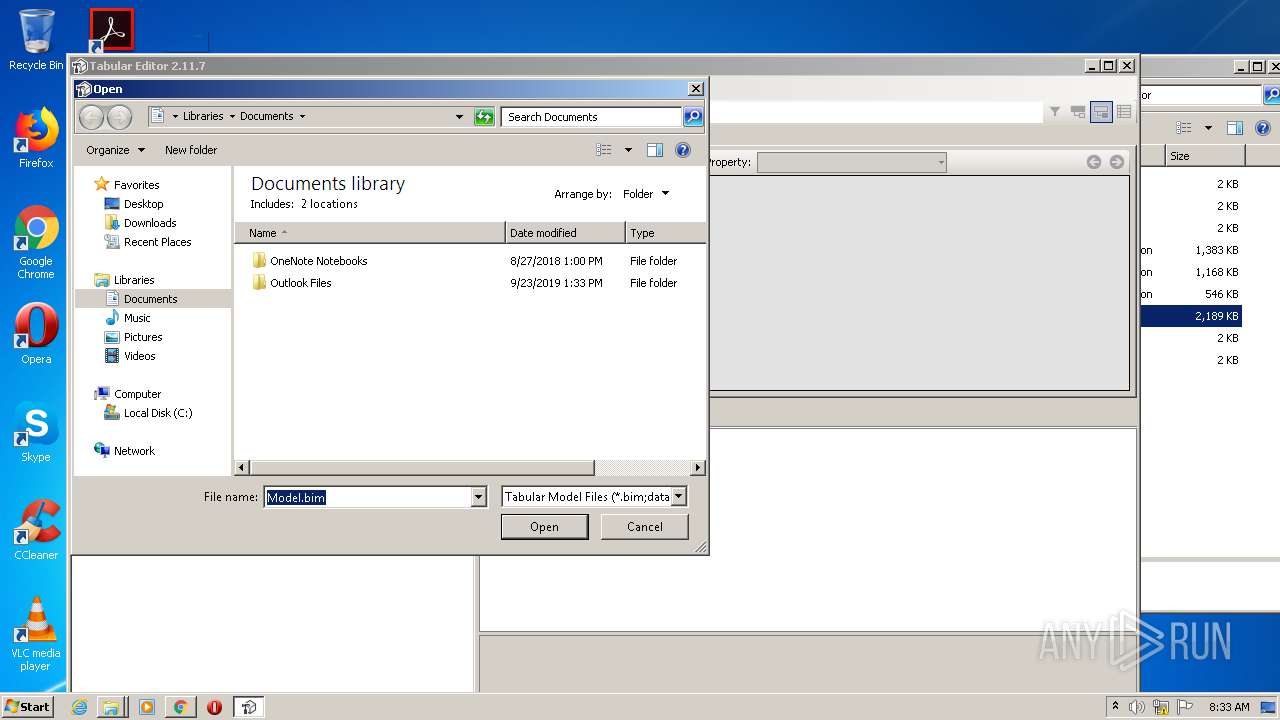
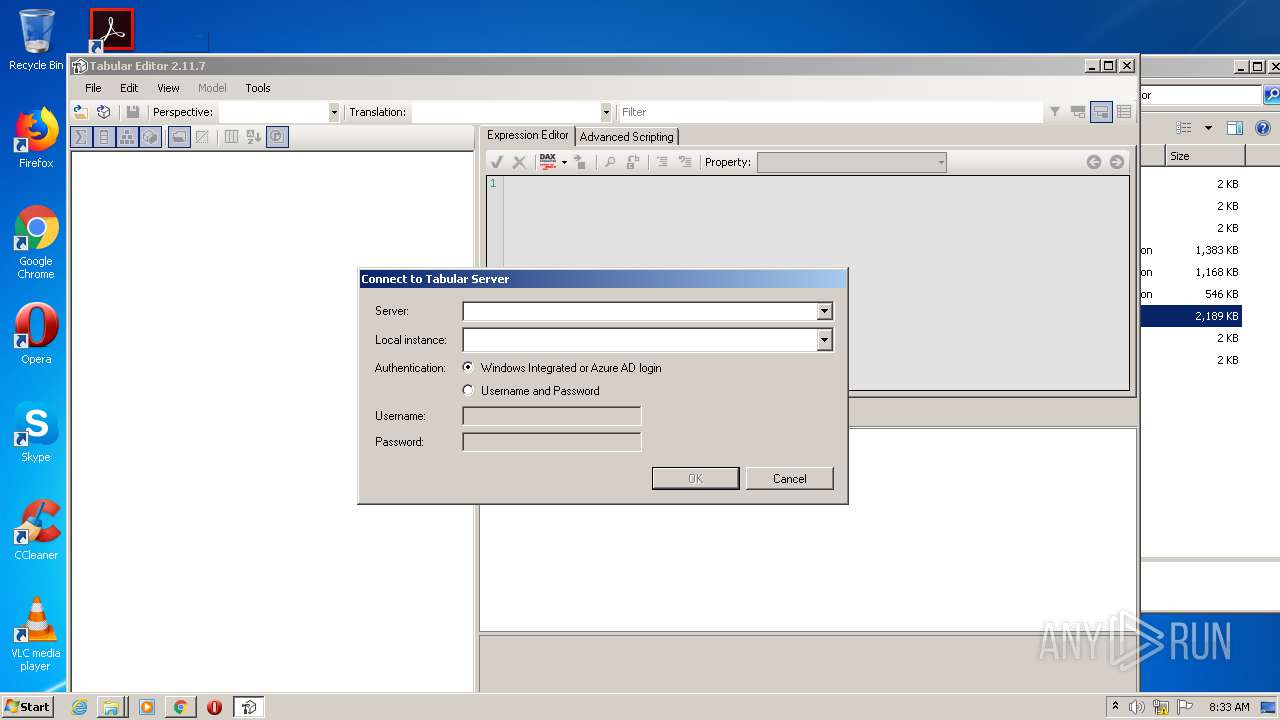
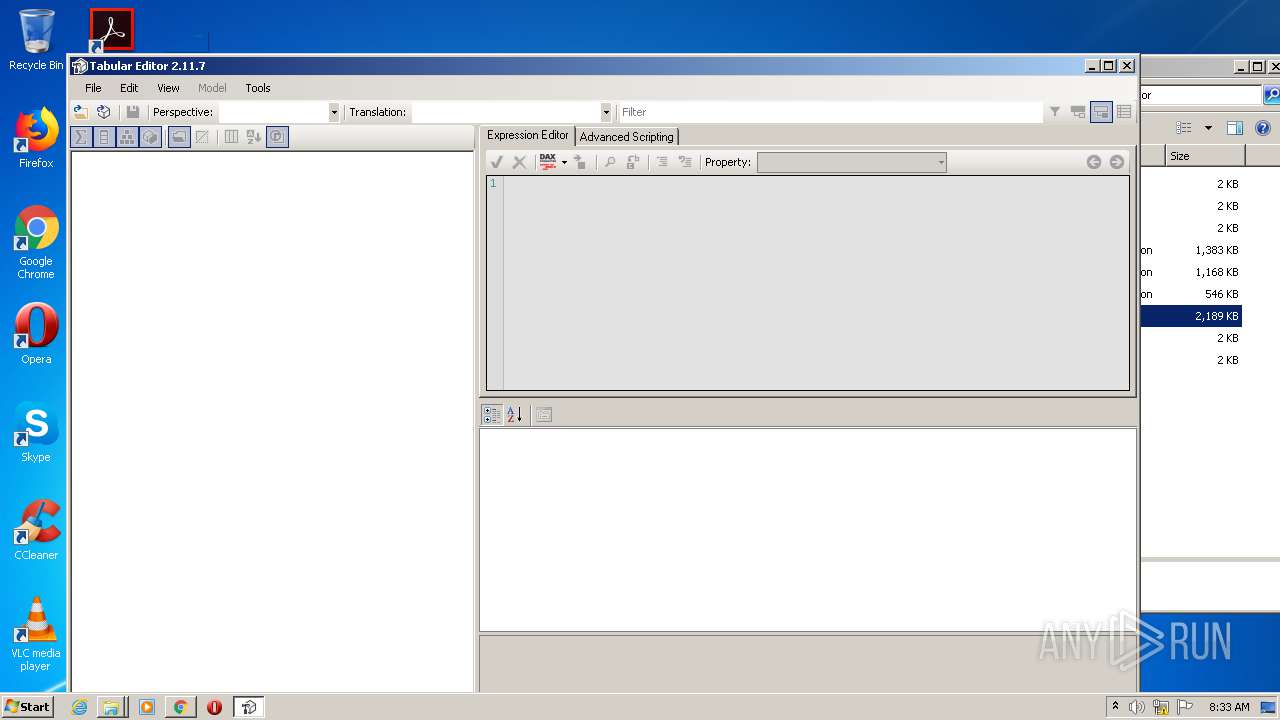
Manual execution by user
- TabularEditor.exe (PID: 1860)
- TabularEditor.exe (PID: 1260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
36
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://github.com/otykier/TabularEditor/releases/download/2.11.7/TabularEditor.Installer.msi" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,10903456473927019878,2919690766676501142,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2542161060681332165 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,10903456473927019878,2919690766676501142,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7287366697239551542 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,10903456473927019878,2919690766676501142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12308062042706631622 --mojo-platform-channel-handle=1892 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
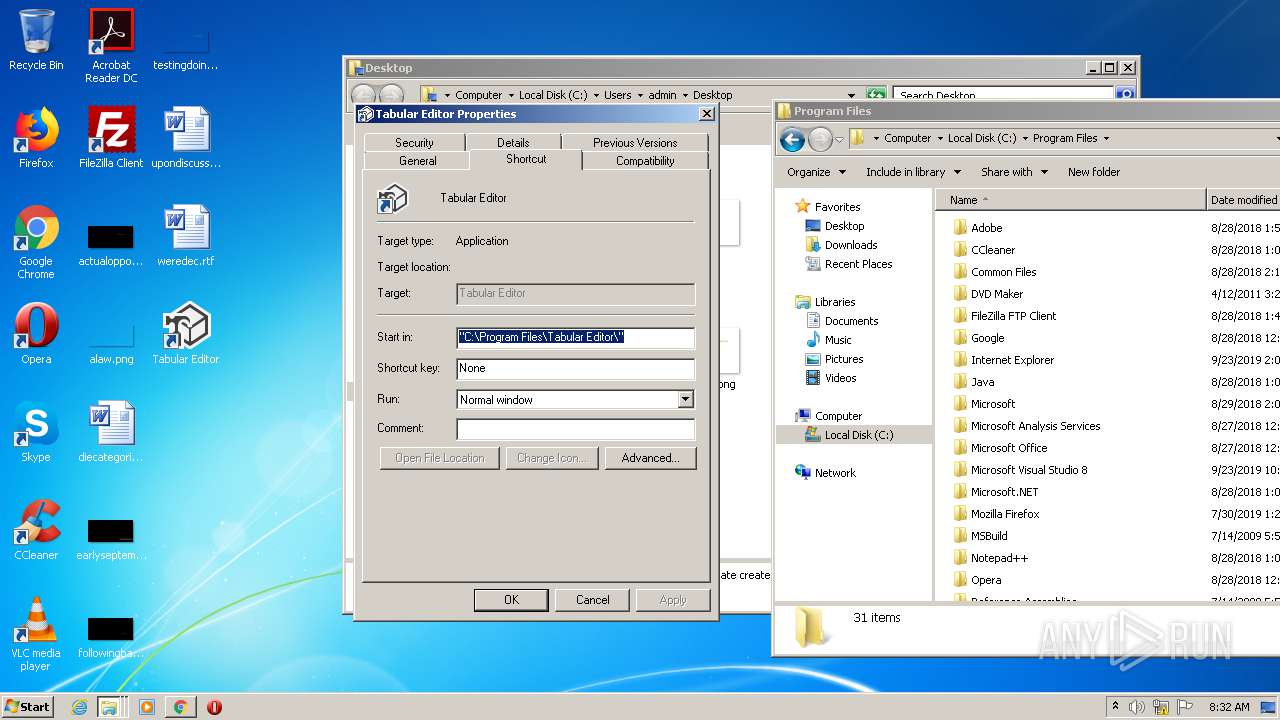
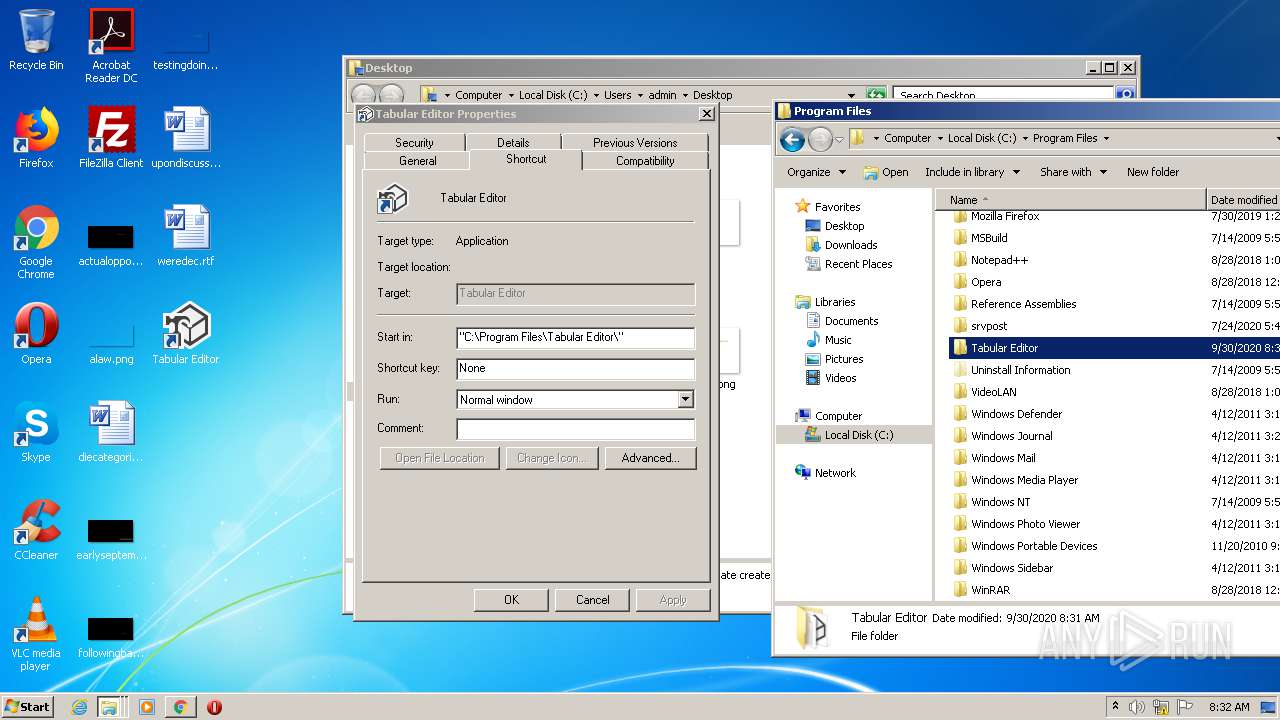
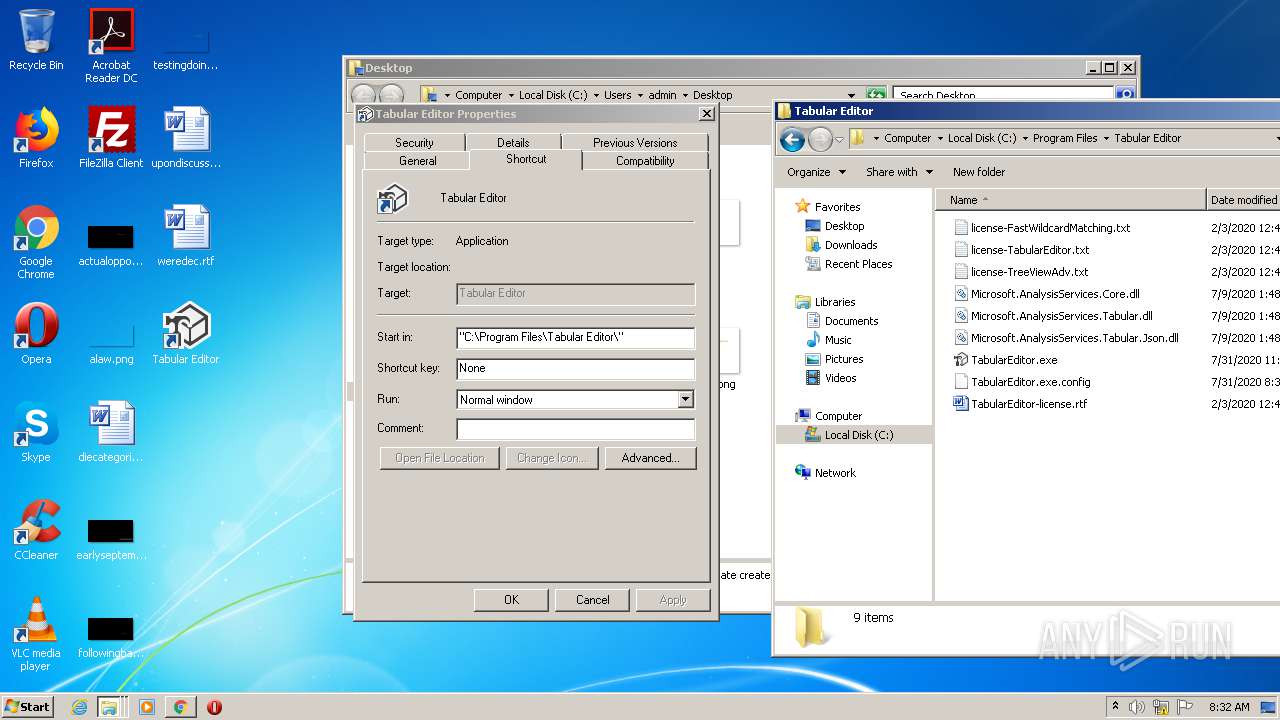
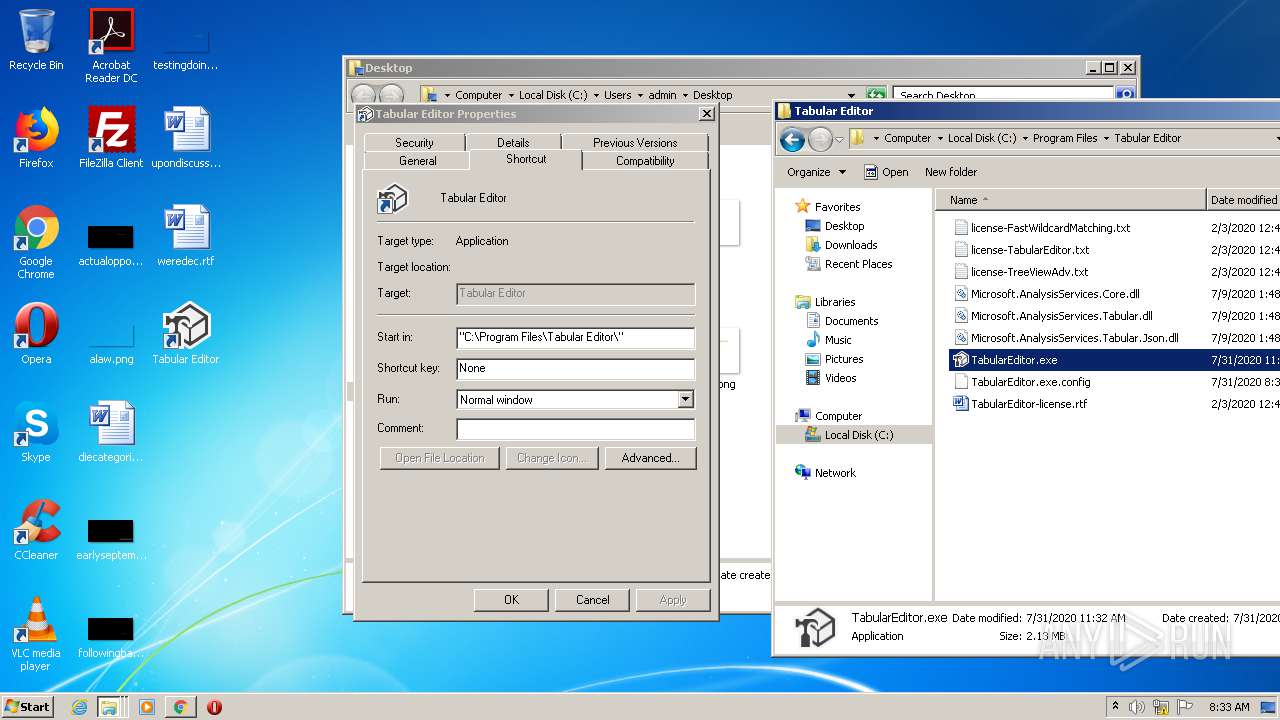
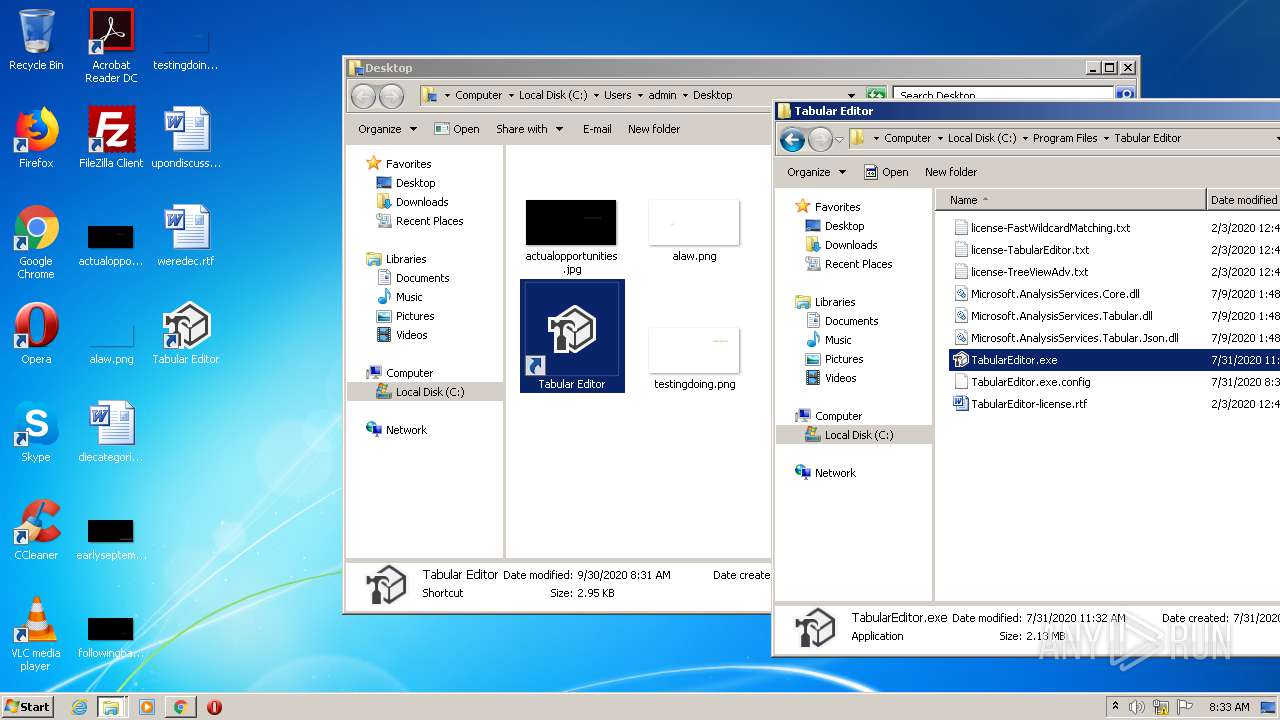
| 1260 | "C:\Program Files\Tabular Editor\TabularEditor.exe" | C:\Program Files\Tabular Editor\TabularEditor.exe | explorer.exe | ||||||||||||
User: admin Company: Kapacity A/S Integrity Level: MEDIUM Description: Tabular Editor Exit code: 0 Version: 2.11.7517.20764 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,10903456473927019878,2919690766676501142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10047593013967258558 --mojo-platform-channel-handle=1412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,10903456473927019878,2919690766676501142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18113288630216656201 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,10903456473927019878,2919690766676501142,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=753704356406779059 --mojo-platform-channel-handle=4512 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,10903456473927019878,2919690766676501142,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=839450036482932046 --mojo-platform-channel-handle=4576 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,10903456473927019878,2919690766676501142,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1404954970021195655 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 393
Read events
1 992
Write events
384
Delete events
17
Modification events
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 316-13245924559708250 |
Value: 259 | |||
| (PID) Process: | (316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (316) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
13
Suspicious files
85
Text files
139
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F7433CF-13C.pma | — | |
MD5:— | SHA256:— | |||
| 316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7f840a8c-db3a-474c-be11-d2bcc13375a5.tmp | — | |
MD5:— | SHA256:— | |||
| 316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3bbac5.TMP | text | |
MD5:— | SHA256:— | |||
| 316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3bbaa6.TMP | text | |
MD5:— | SHA256:— | |||
| 316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
42
DNS requests
28
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
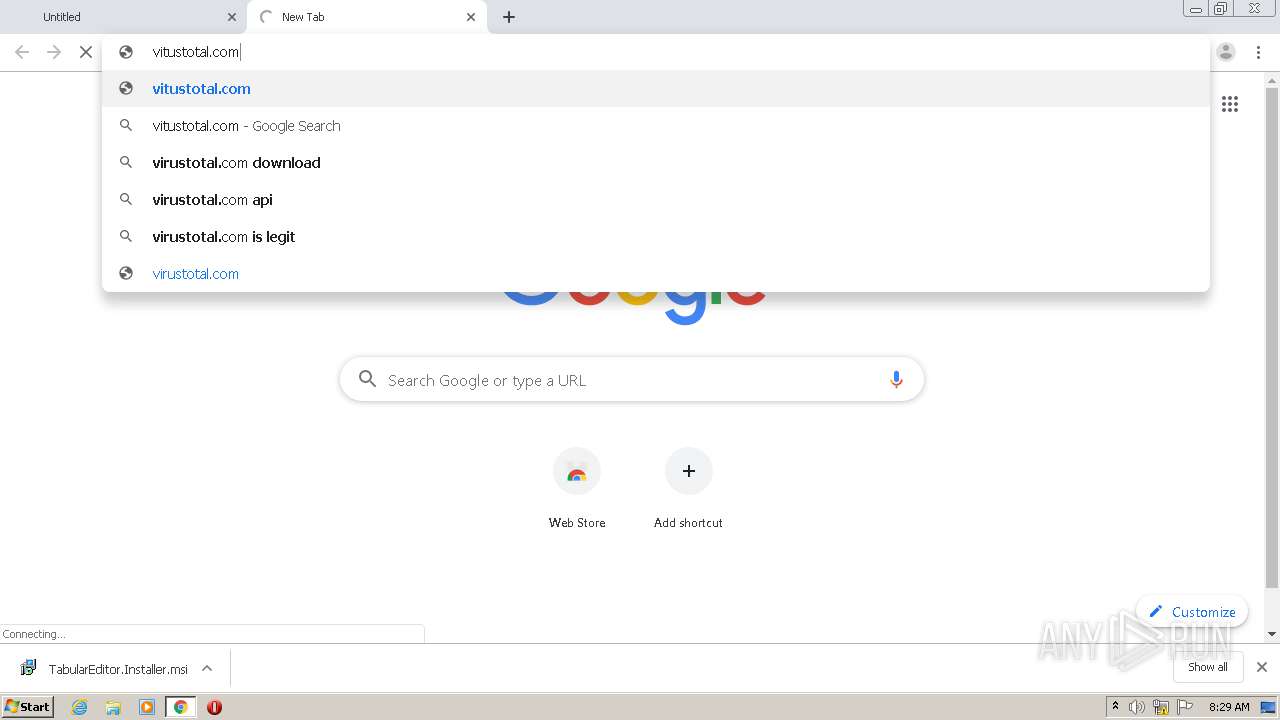
2932 | chrome.exe | GET | 302 | 69.16.230.42:80 | http://vitustotal.com/ | US | — | — | shared |
2932 | chrome.exe | GET | 302 | 69.16.230.42:80 | http://vitustotal.com./ | US | — | — | malicious |
2932 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://infopicked.com/aS/feedclick?s=wNN0tAWXi0wjCKrxWKmdqK3dDnCBF-q5pjcTajzqm_Rdm5knBh4RKoLUfaDR__NeVVH-ImtJpPaG_Nh80WMmwiN5ECptO-enhpGA25KNrvmyBQfBllbqoEcw5wDg_8fmHWVUL2gXgUyatsBFMaSTc1RQ5RxkQPBqyyTn3ctXNy-WJqJi_IFnBJtzBG5jnKS4FgGz6Ry5gzq6kiHp-m7ozZQzYcUDcOc53PCoKwFy3jNIMEBmyEjPCSYeKvmi2Q8OdutgW9r1qjlA33lLLzyrVJGXiCynBjmU4mGioCwDy6h6yFdZTfyjJ-VUs-N3LmXyKzImPT5EA9PZ6uIfeiyU8NFwzQOcZLksV_NWZhVa1PgdBFww8YJEygHA8xdlsadEZcQzcSdo7yhBJNxmTjUJHAIX9kd7VeH95wXk0BcoRF5K7-162uLFAGACoN2g3SXCD430Rbxi9J2fvMWWuec0pvLCKkzFOgztrOK6j_izNtqisqiJo3zJVGhk_mYWFW-gdutgW9r1qjkpTG-IT6Whevm8AYVGEwm6K6whdFjDKHV4elCxSt0c7OERiRlRVmugMXgbI2p9mTgZyhFBVvDOZ9Gp3QEL_nt59XICFTAVHhLTsr3EFVtQh2e-KHPZxv4Il30aiowHlvlbza5jbqDmnvmhjBkC8ThQQRYmkxaSqM5mlp6jpy8vOPhXFMyeSlT69y1aCWSxrj7JFIhOFKOWjGowr2hBjpqkVk7mHSzlDR7uXWEjzkR4-abPCjfvRaDkdAR0vuFuddCPV_YUMPLrXwobTmQwhYUQBcAesuztGpnXqKpZsjYriw_5e83ckDpSondZSoxxzESWVzb-nYzRM0G7HKLfzDOpvV7Me2ukdzcUkiyGJr58YYrNGf4gBfXpYMVr7KoCacbE-iH-PGp4KwvlduOrQ3OcFusU1-ZPuvAchsZ4f2UTZ7QupZCLAgPIPGV5T4EAApQJU7fKCS0XMm0FlsYMX66vao-4z9Ka7IUTfq_yudmXRWCDxEh_t9Tdvr1CFfjbdFZ0yNGLZz_T4Fch03DWF4JUqB6NUit6FEYLRbLirBn0pRRqtuLepC4vhHmygXHPBeQRrXJTolstn_FFzqKDcsZ5UvbsSA4KO3tu3Gm2w-lp7KCeAD1IvhNaP8sUppB90IhXvMYORdOEXp_FHNfEhKoo64-6rCXROMKuYis_aU2FVdzVMktjmOCxgauK-ugy1wxyqc2-EZ2HDFqFKw-W-fq-5dpQ5HX23ATW5LiMj9SZdQzP5FSLycBmeqLyed15_QiGFGCXXWTRhBR5kHBtJAU6WbA-g4Kzi7F8m_FKCzkL_R0-Jhiqn_bZTB7pj60yelhU_hk6kZcokFaeWwx3o9jxN74kPNgtbcUjhdErEskwOPi16mlyaXIaBQTtb1Vp_iwWeS4fc-137E-XqOAxKQ8glCsiQH0B_x_Atz7rRs-iD4ralBTN3MSmj1XppY5NBGNl7ks6_1qga_UcEBN8FFAyGW2M-edZHsATd60q3kAE_gUlFK9dzNrpeCCoSPPPjbS7KaGBjmXzMW3nWMGo8srLgcfrPL53JL_gcm6cqkr2If1cyOlCLNhTmnzCVc7kG2FlkkLEB146pQ | US | — | — | whitelisted |
2932 | chrome.exe | GET | 302 | 173.192.101.24:80 | http://p237996.infopicked.com/adServe/domainClick?ai=ydWaOHrdYTsBMXayeSj0uFmwPoOCs4uxw1aqhSMuWebhH2lrXnMnkm7WURdh_-BAuymhgY5l8zEyKdXunCDWAzltJN1ZxhVk1SLrFK8x1FSsWvdh7vYlLB_XlX_mJMDj5tPE6XOo8hwD83GajpfLng92Eaff8LU-fMzFNJbfcT6WWmDgWFl_FI0PZh-lEizEI3kQKm0756fW-ZvOYKnsYOFQ1sZSjlM4sXt8PLNnJ083ZpGUKqgW1HggqEjzz420uymhgY5l8zFQgES41liI2inXrZH2vXVxk-V6deFDbkgXEH9JUgUnCMIXtYgzGVRavsB0iuJvaA4l_jIE1GWrF0-cSEhrDbOxEkcnN0O_o7n7N9RLydVTTh8VzEnRK1KGnazT_fgIBNS4dnN5JBOCTIW_9plALkDivgUM53Dzny0iZs55fPbhlcWl6v-ux2Cq1aOuLzwF6DpmidZ79W2X0a0UsLykwuxQDlFQO5HpzDxlIvSi9Ex6ouIqupiDgyg5yrTKqtHLgCQvppZJ5ESpEQ&ui=wNN0tAWXi0wjCKrxWKmdqFY37AsT2Aewikj_BmESayBjLJqURx2el4T2H_9HEo4nXyhdQJbCzXlT257CQNB6henLYdFq2Dzzf1HfgbiLC8h6Cl42S2D67g&si=1&oref=388240a24257061ea361bc29dadf2e6c&rb=1Q6mD28z45k&rr=1&isco=t | US | — | — | suspicious |
2932 | chrome.exe | GET | 302 | 216.239.32.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
2932 | chrome.exe | 52.216.168.147:443 | github-production-release-asset-2e65be.s3.amazonaws.com | Amazon.com, Inc. | US | shared |
2932 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 216.58.212.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.16.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 142.250.74.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 173.192.101.24:80 | infopicked.com | SoftLayer Technologies Inc. | US | suspicious |
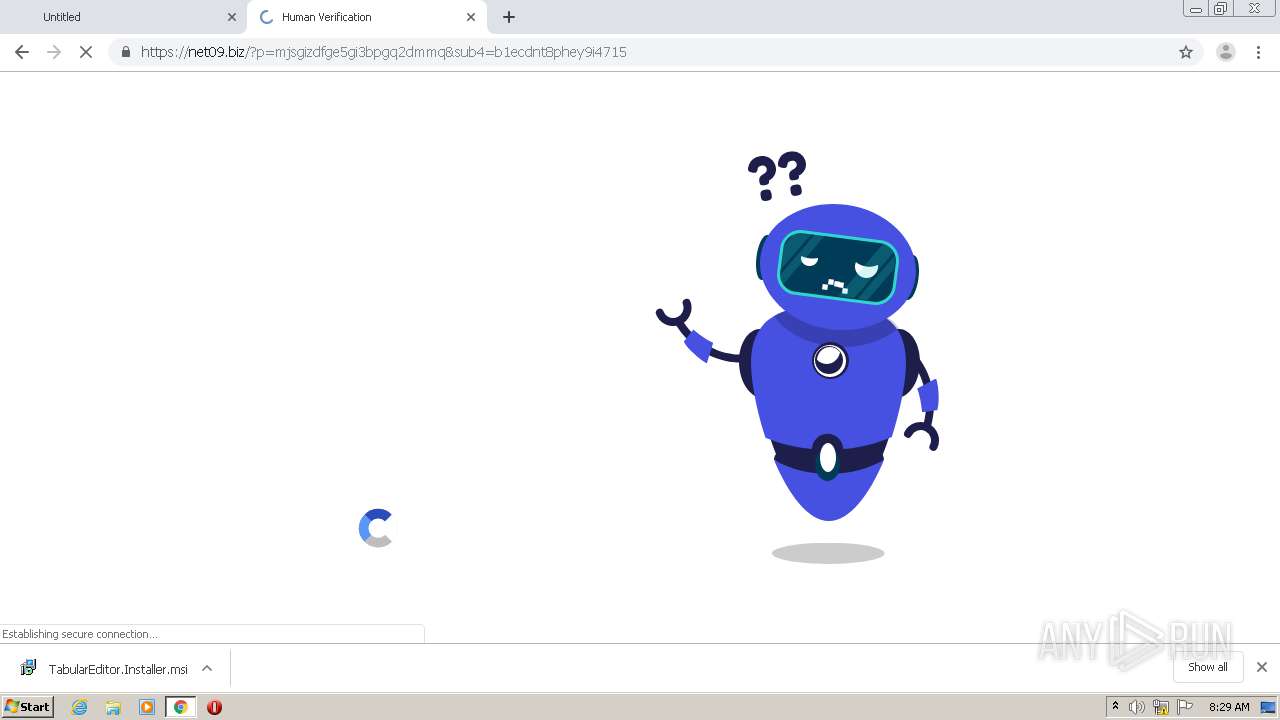
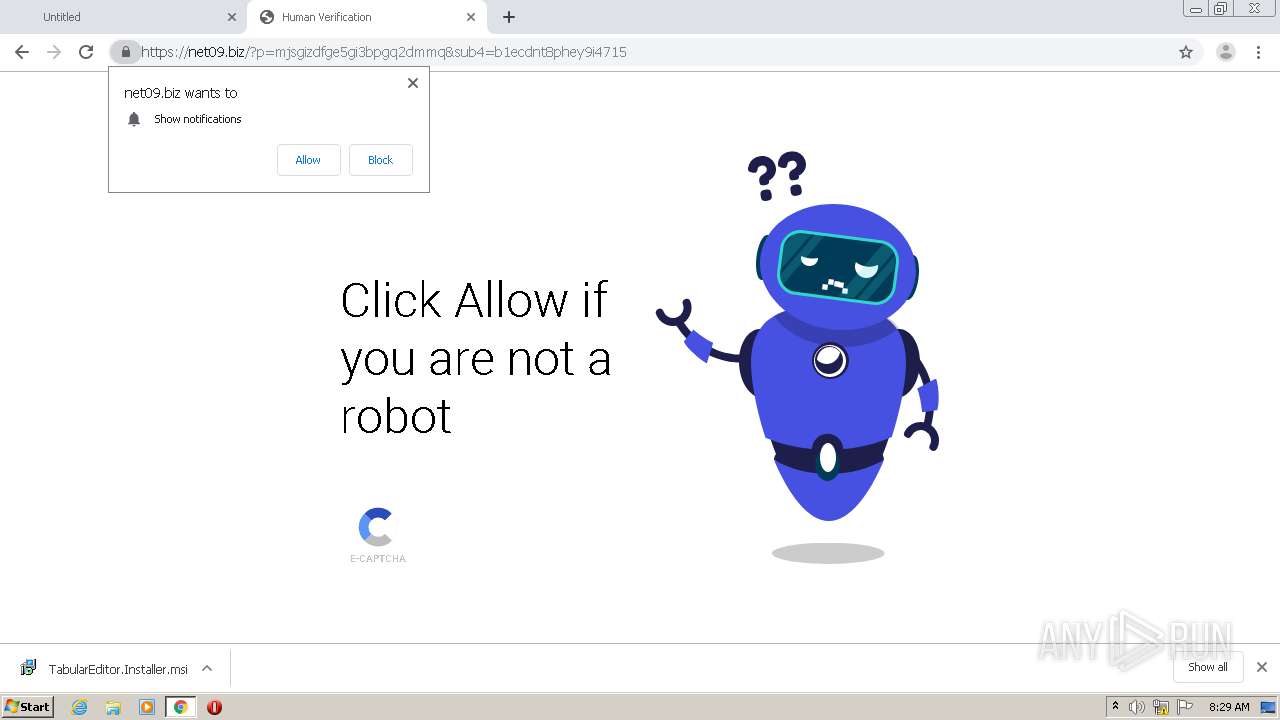
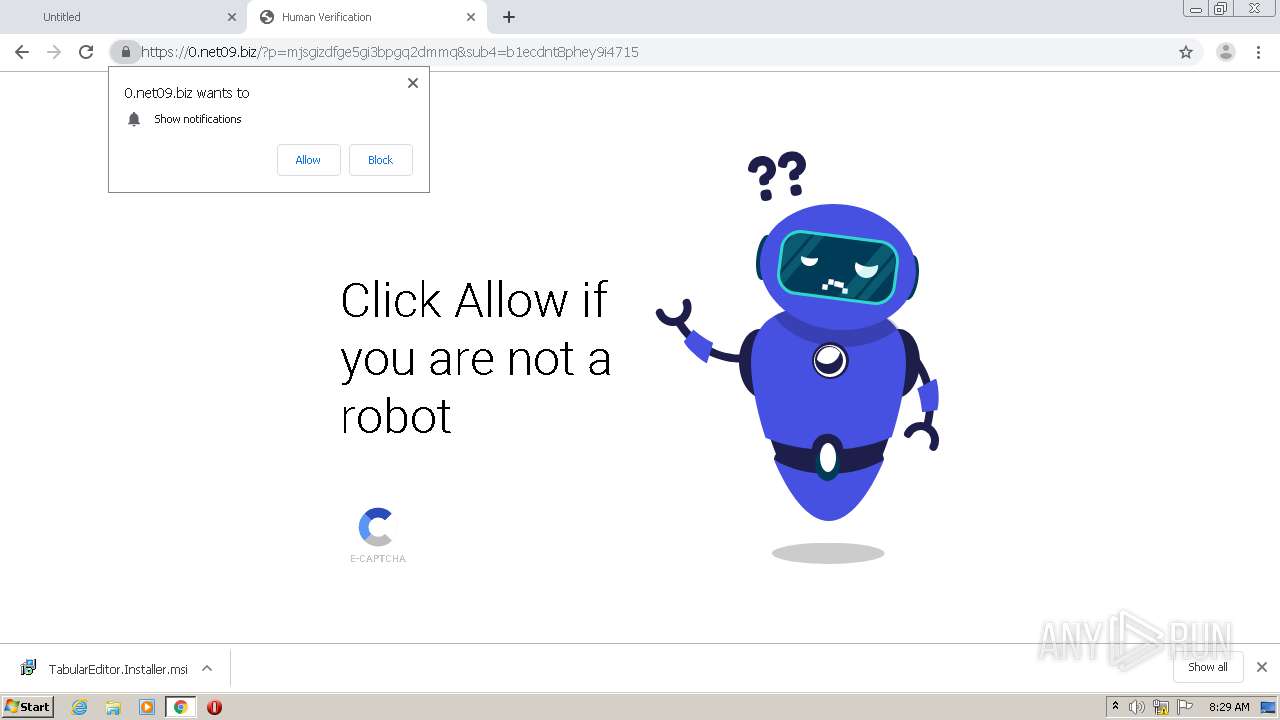
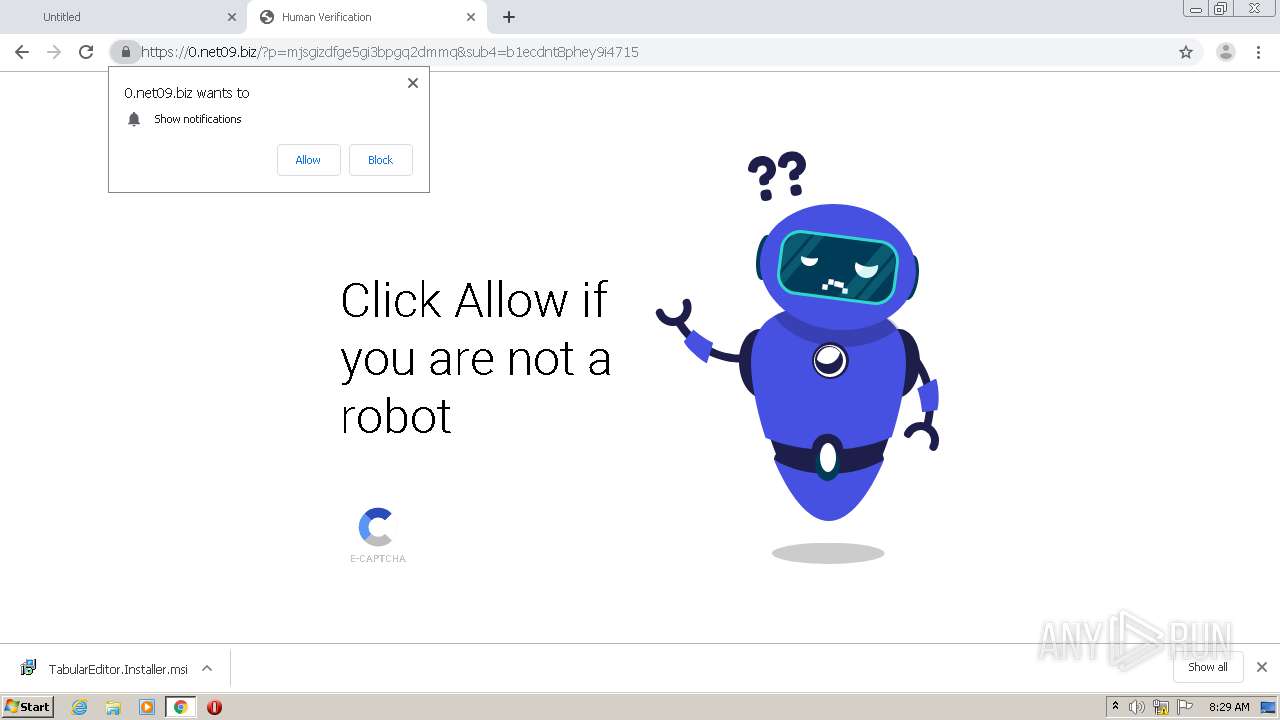
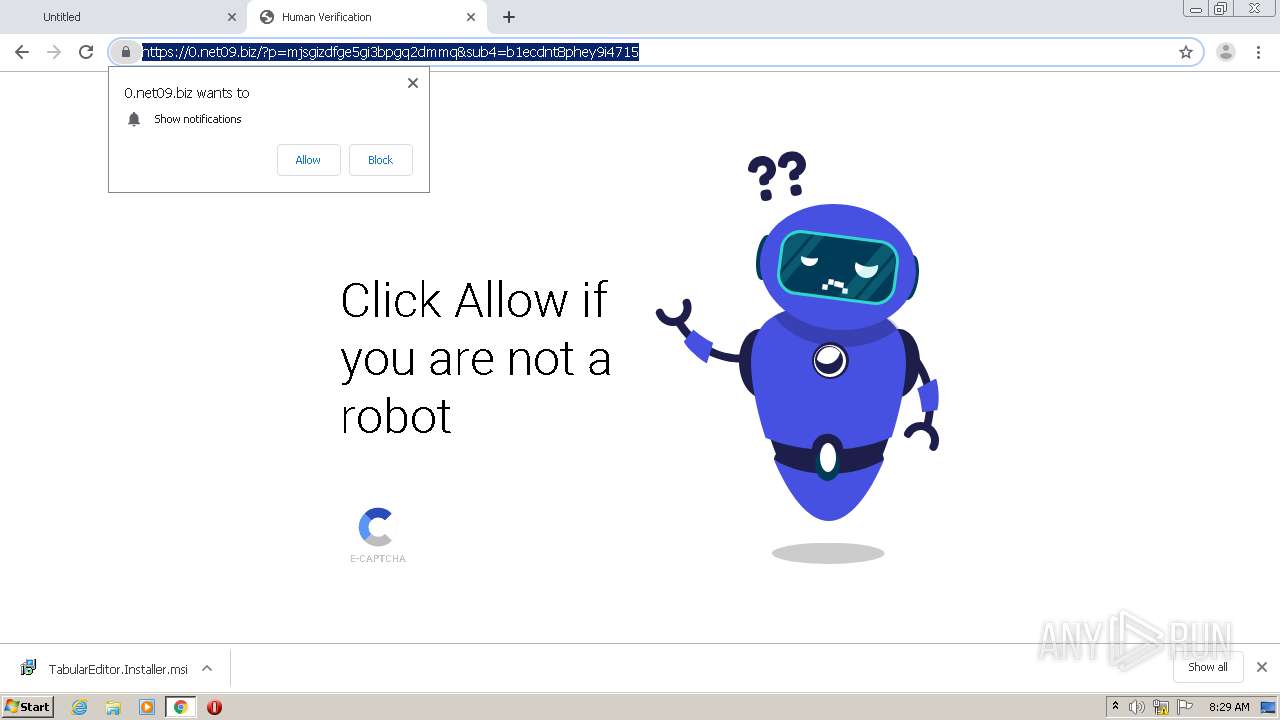
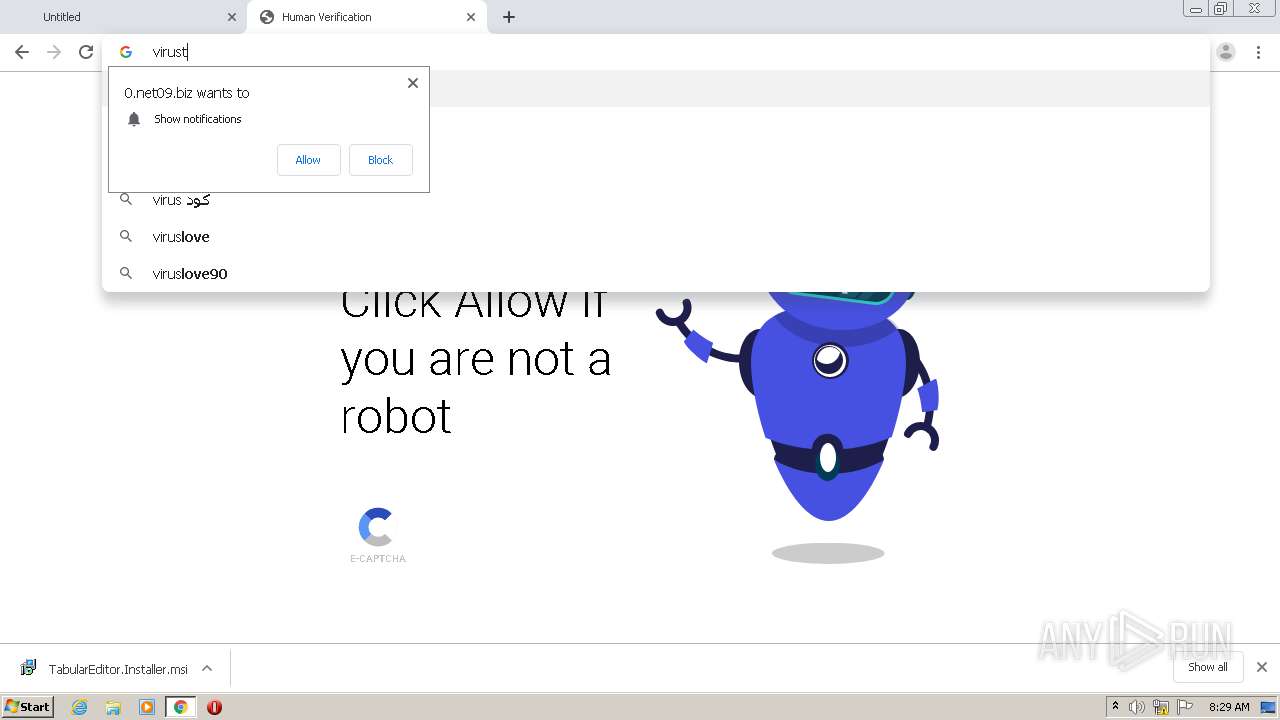
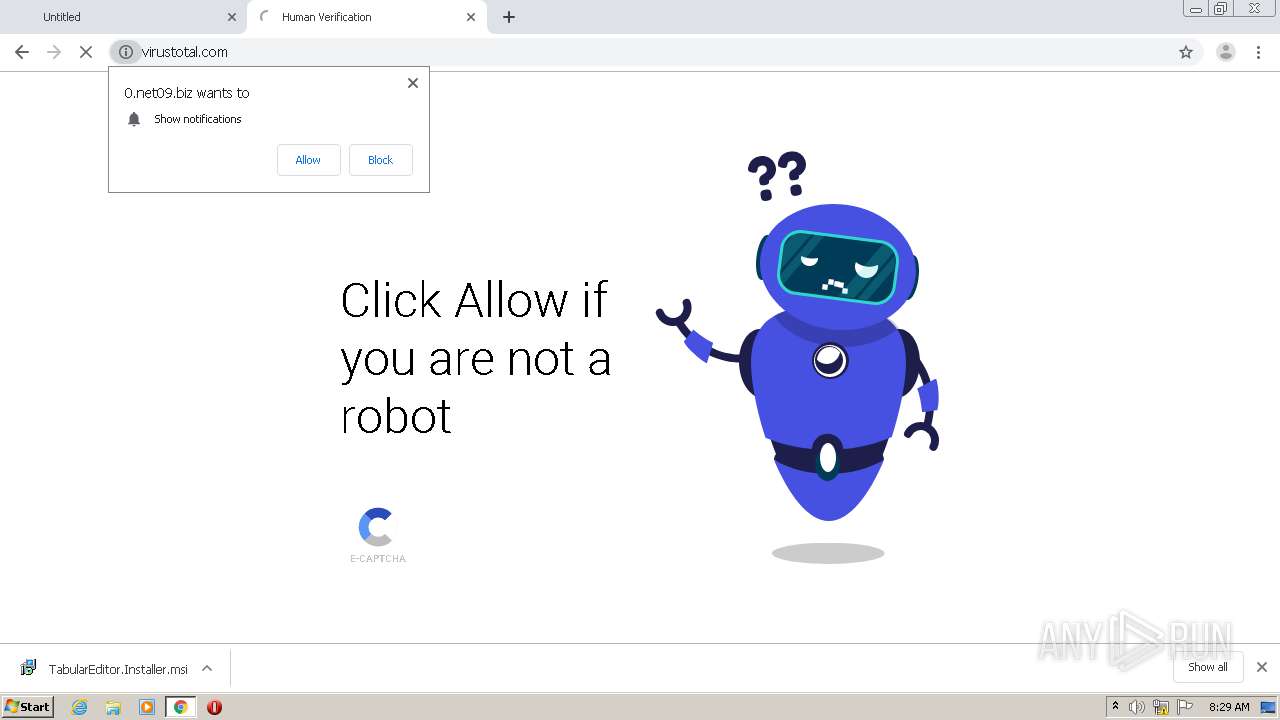
2932 | chrome.exe | 134.209.136.68:443 | net09.biz | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
github.com |
| malicious |
accounts.google.com |
| shared |
github-production-release-asset-2e65be.s3.amazonaws.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
vitustotal.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2932 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2932 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |