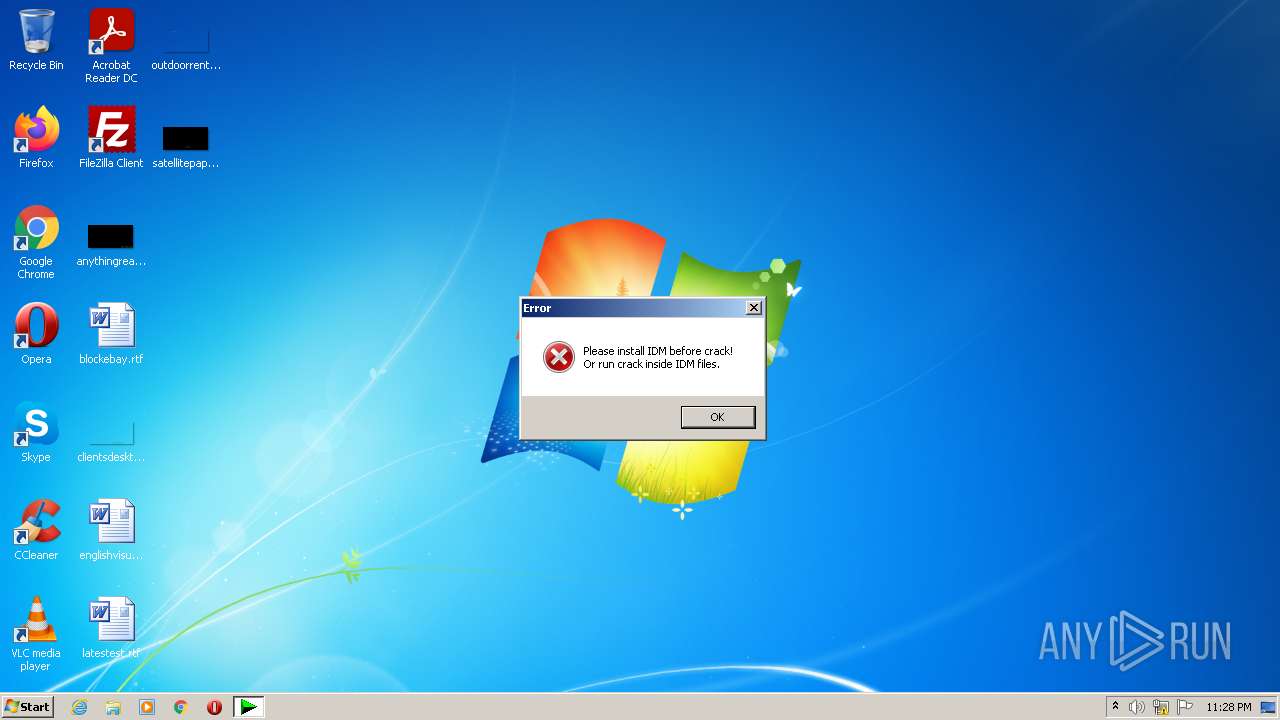
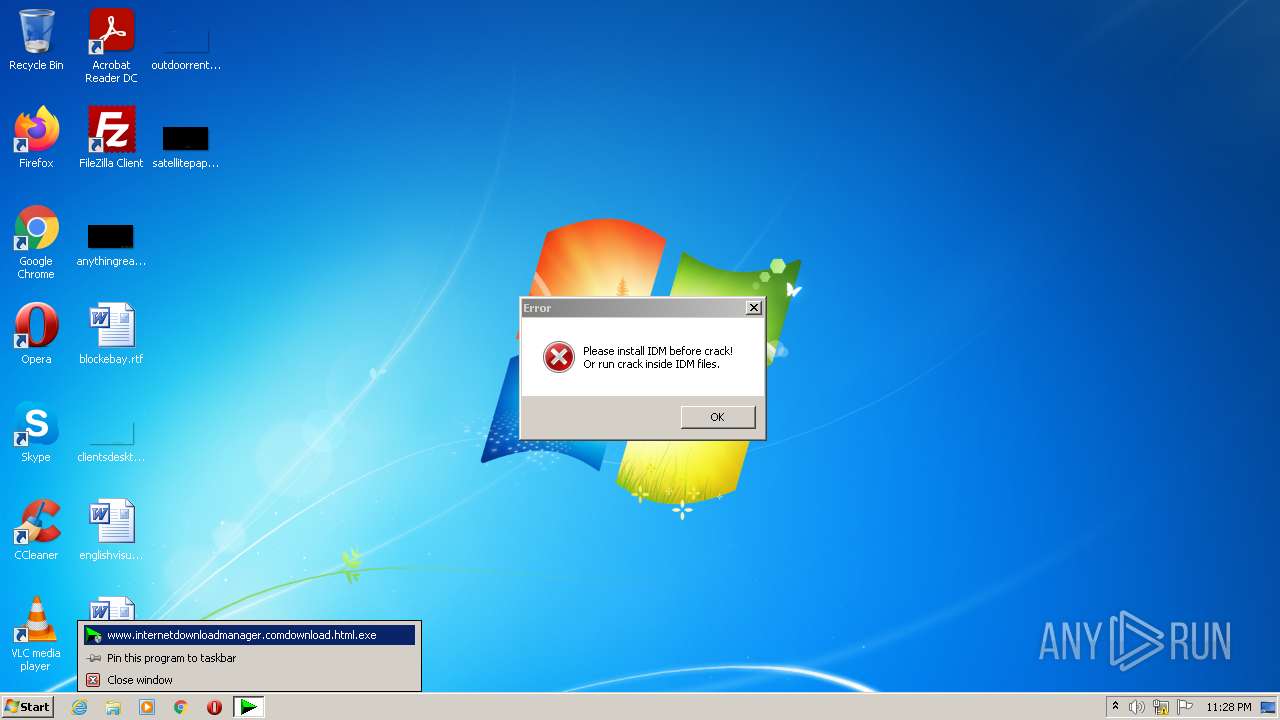
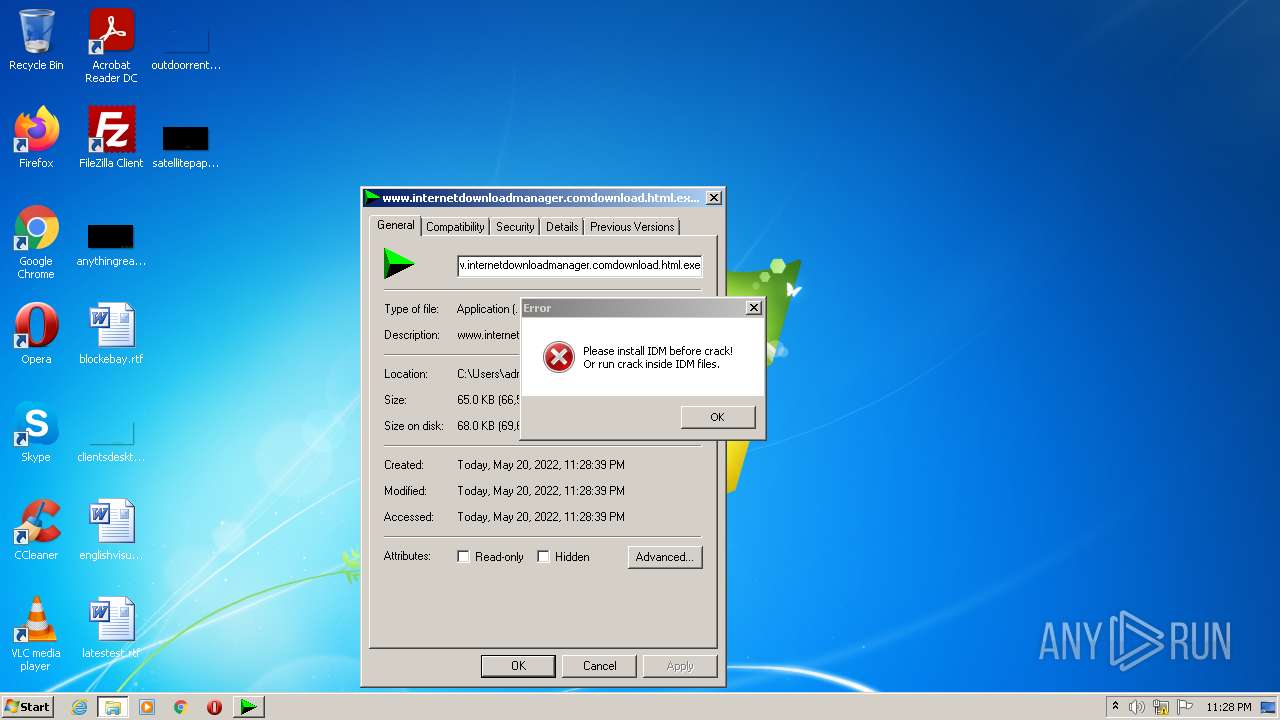
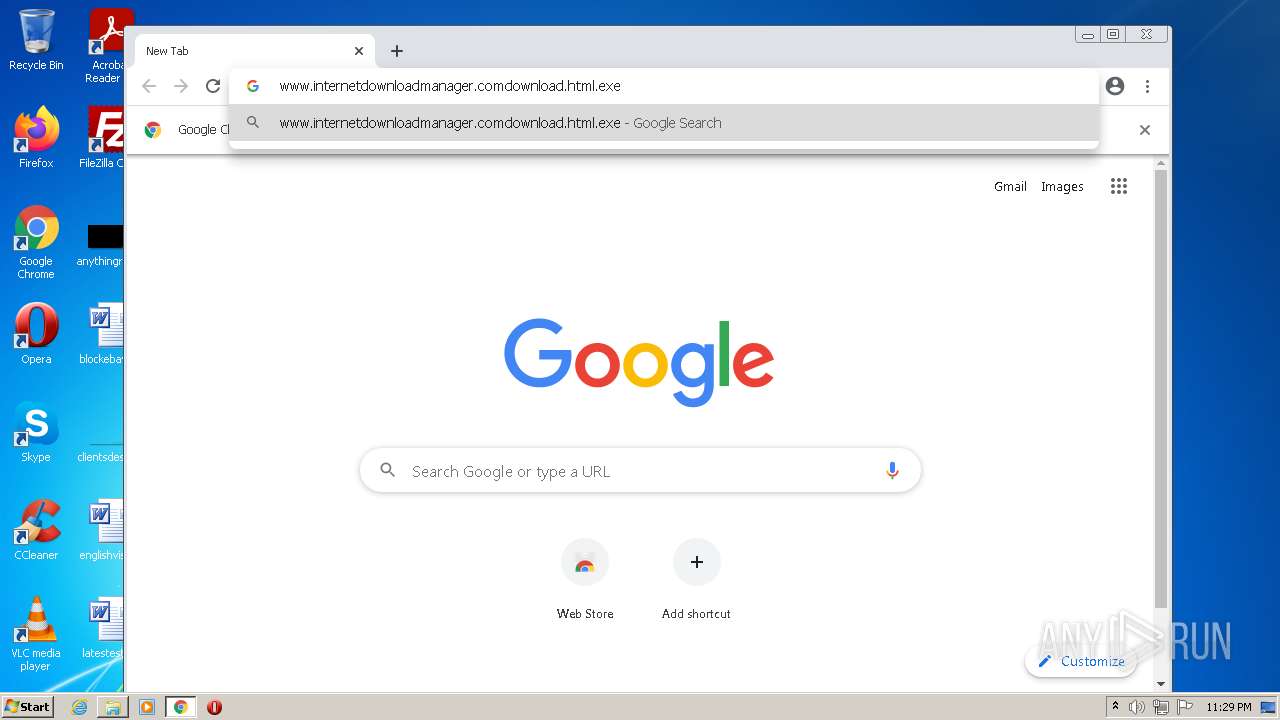
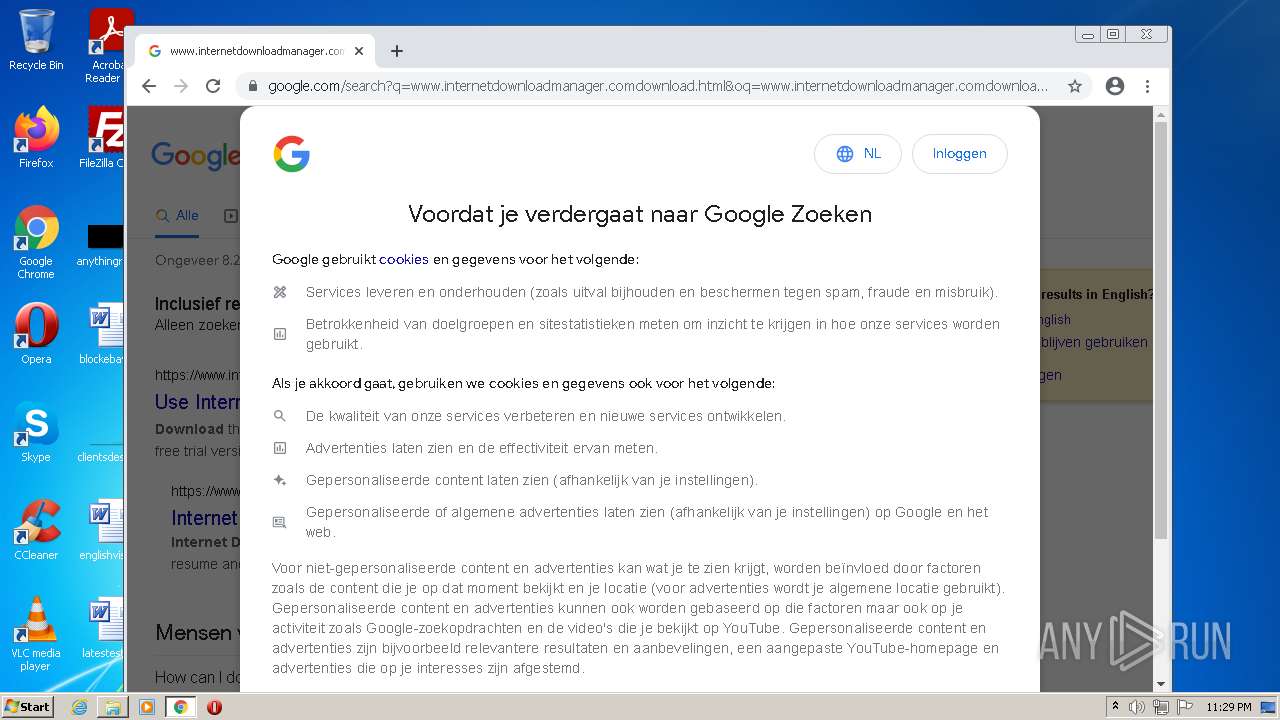
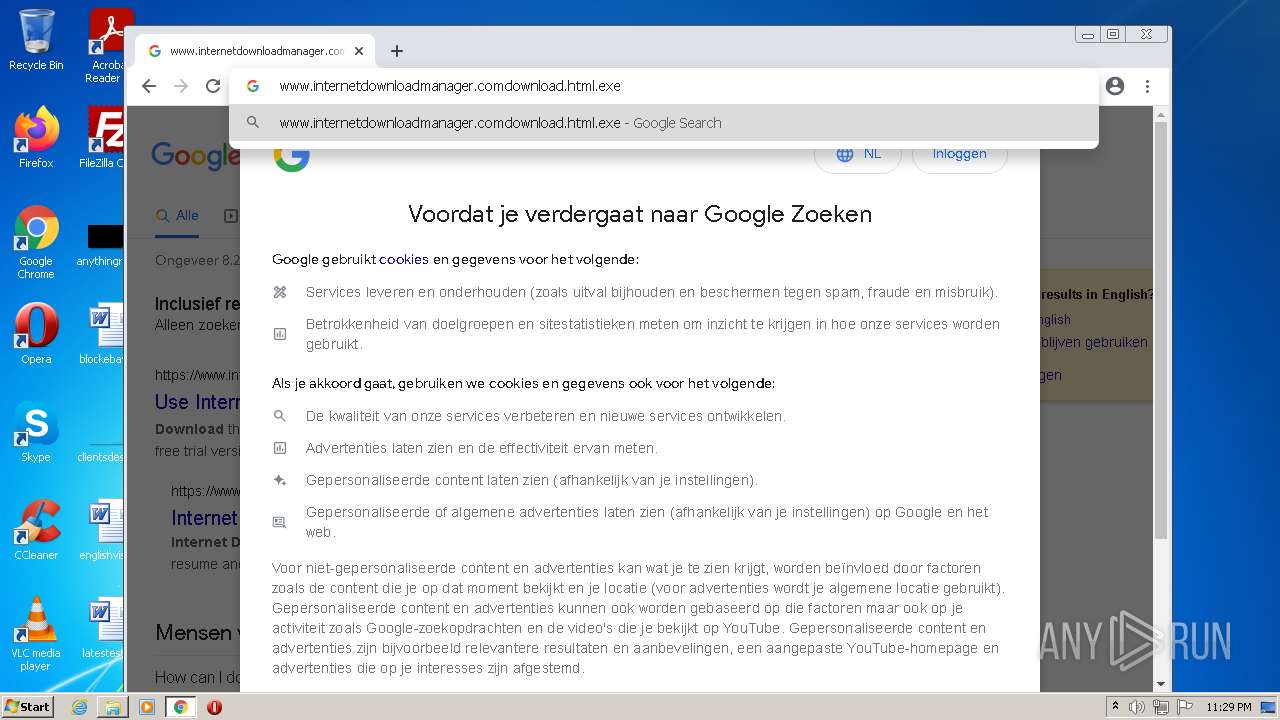
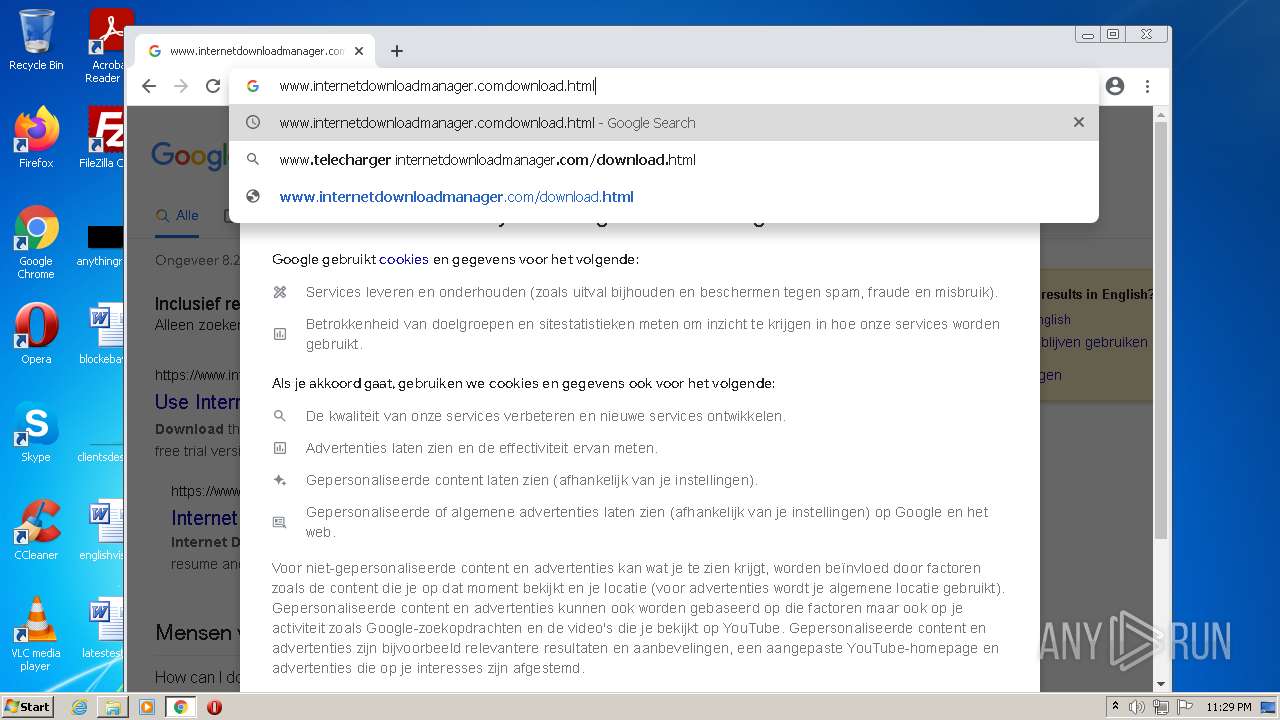
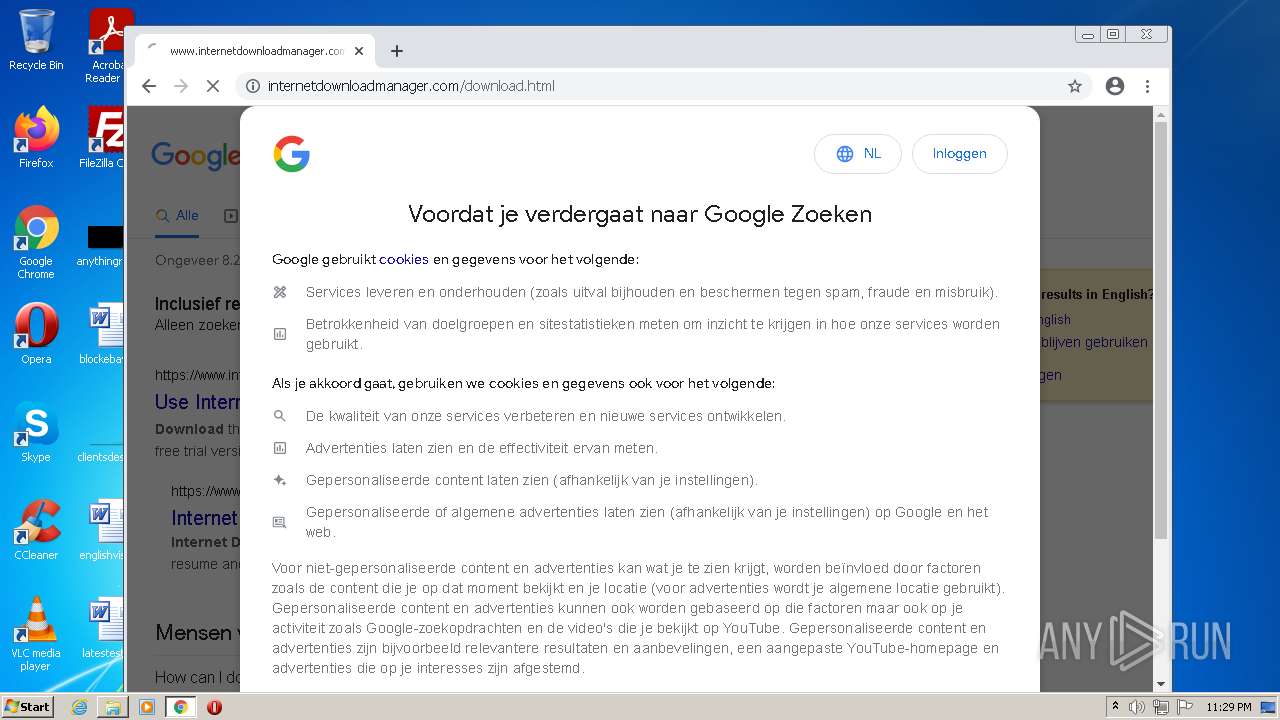
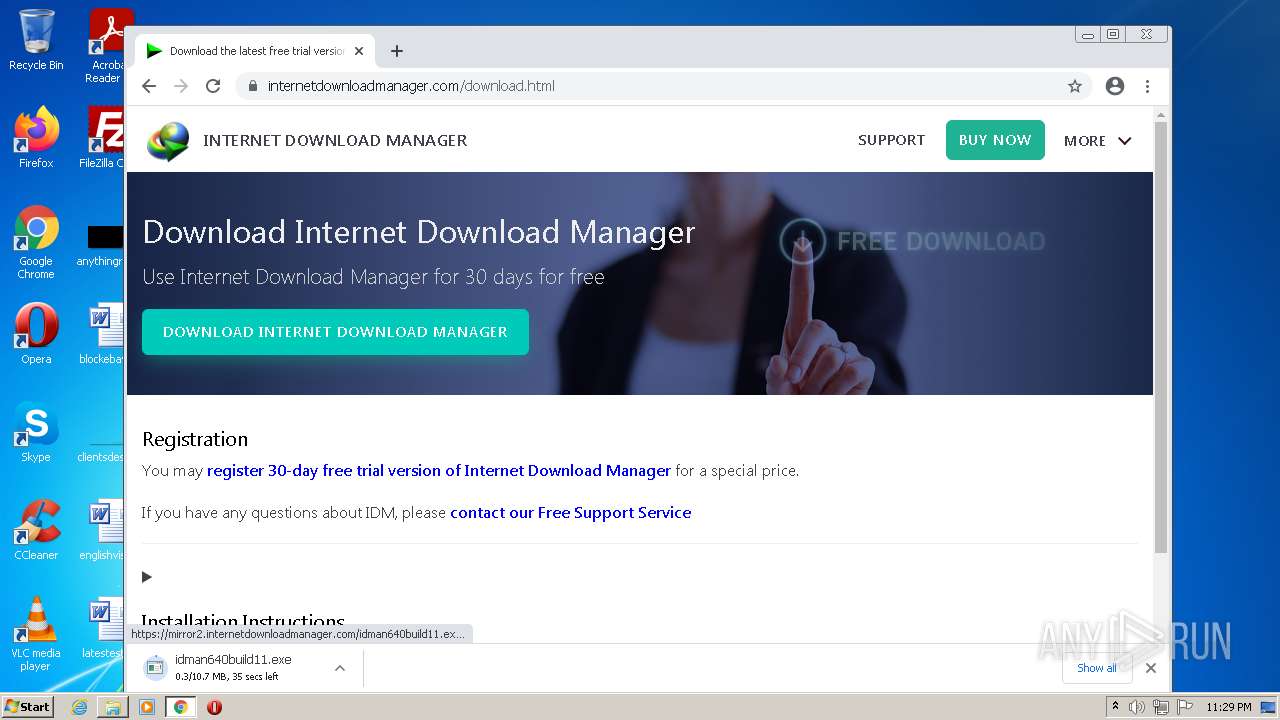
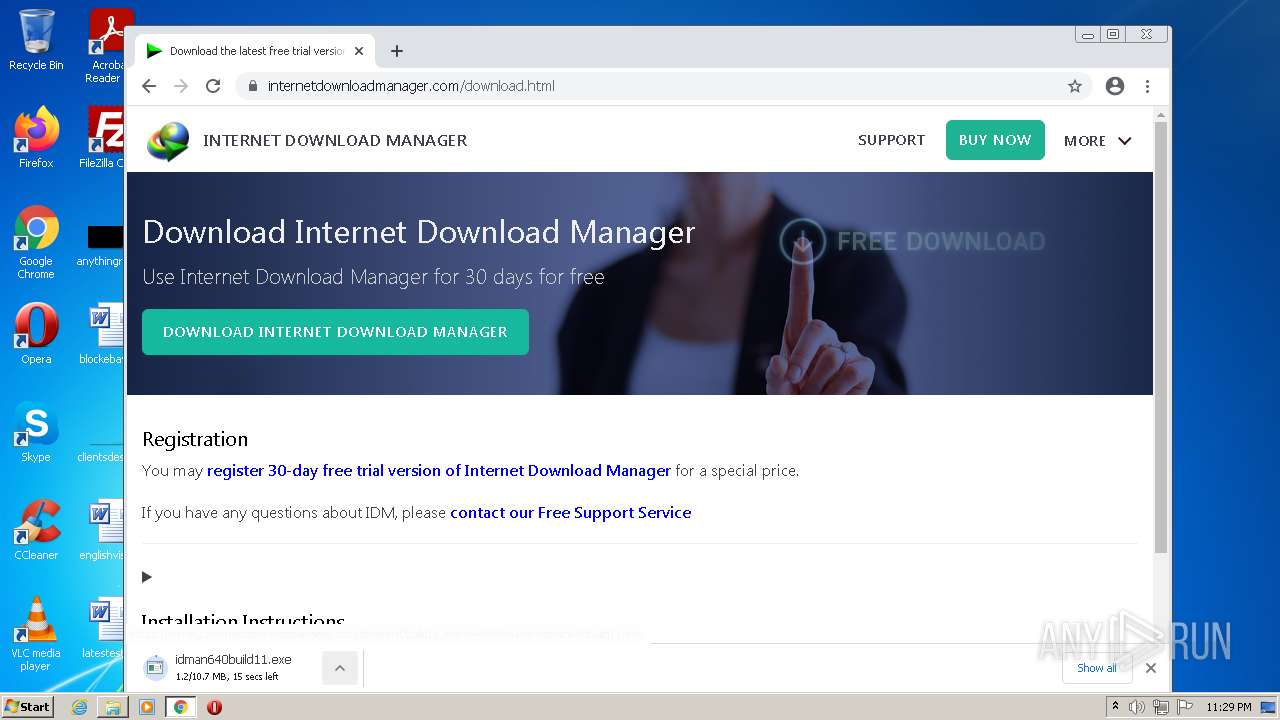
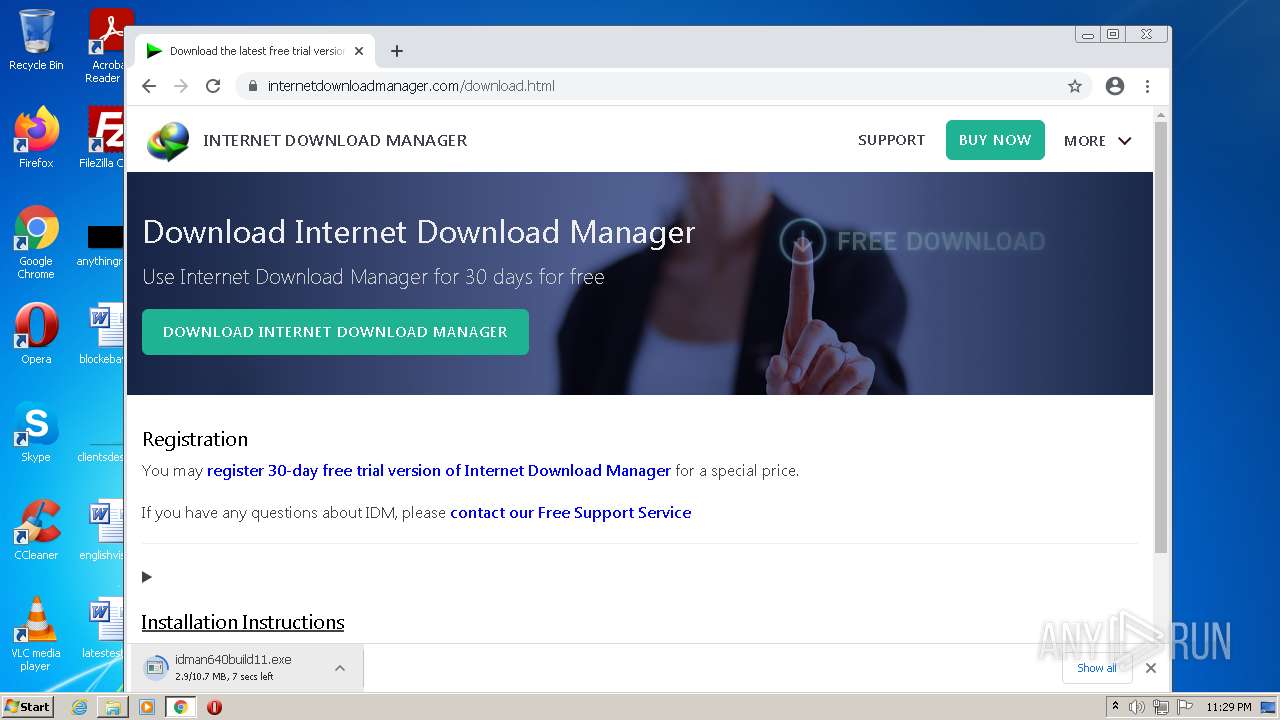
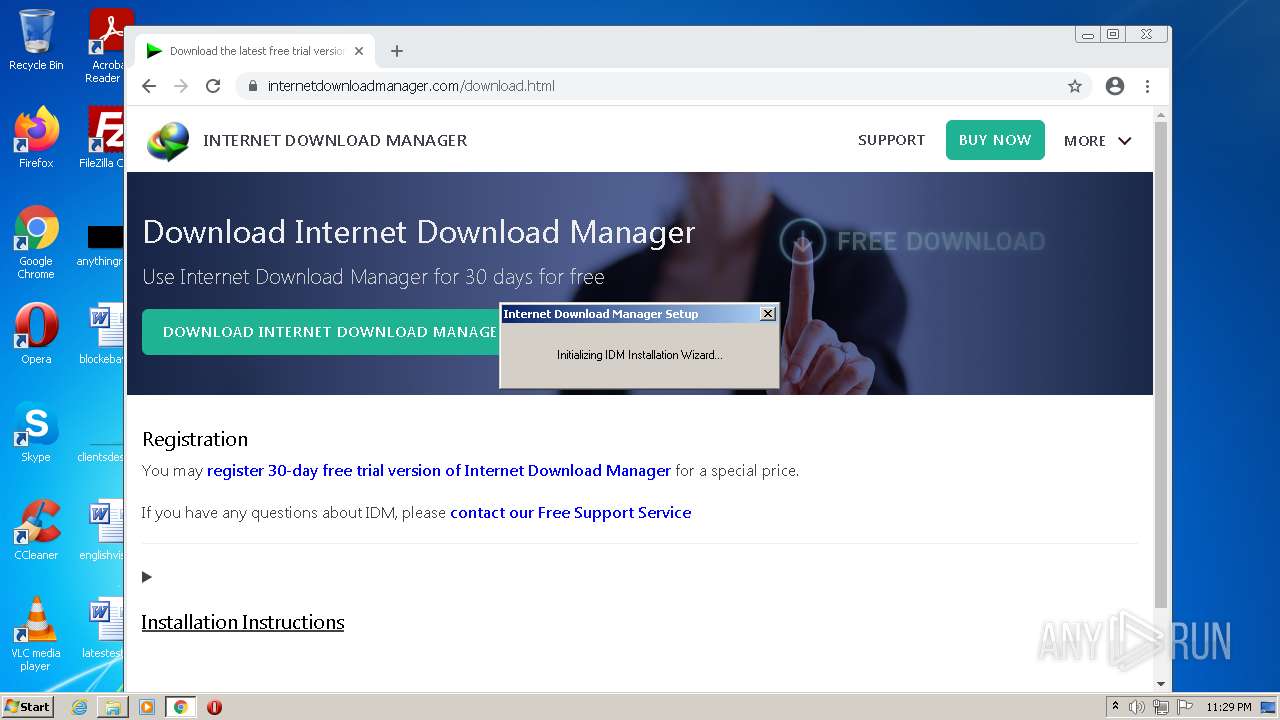
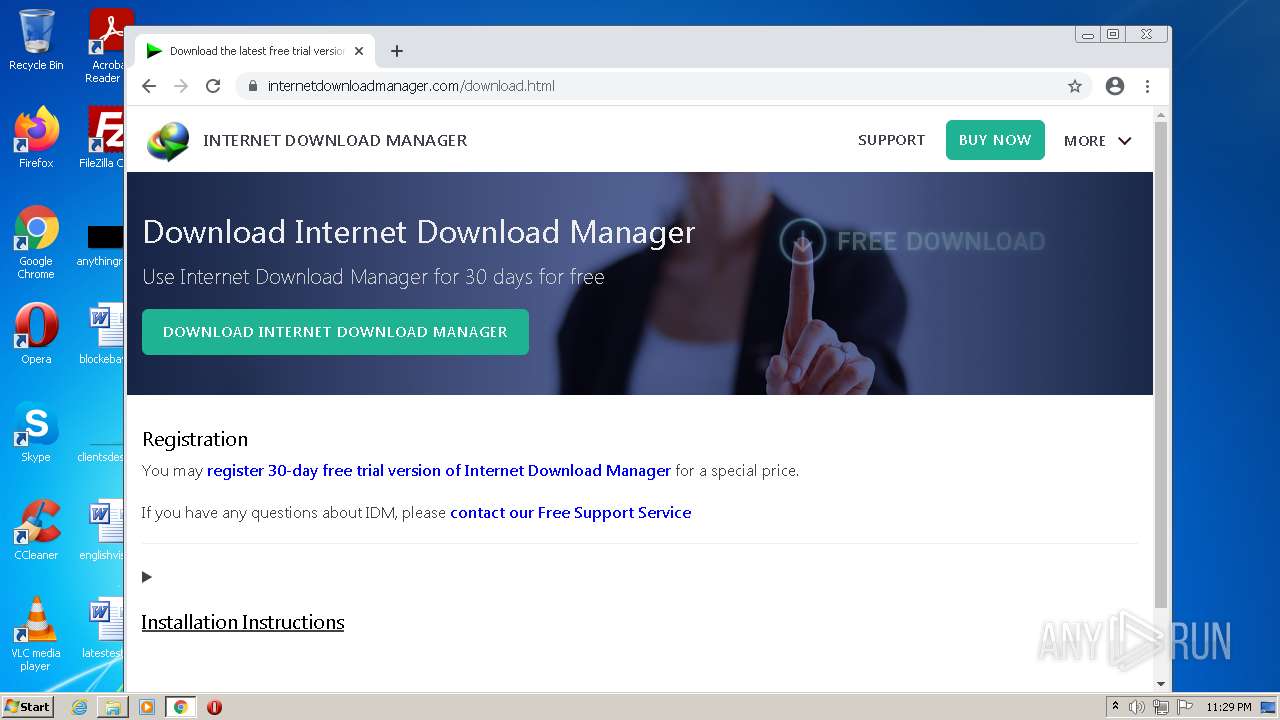
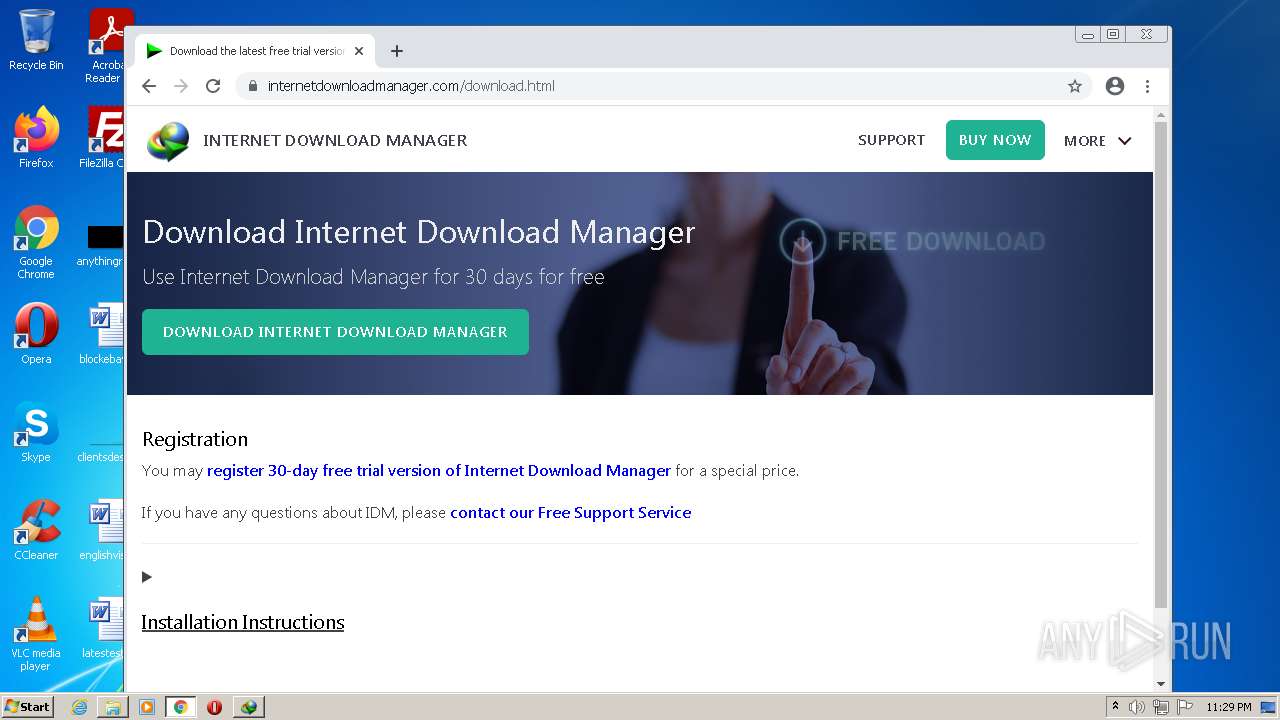
| File name: | www.internetdownloadmanager.comdownload.html |
| Full analysis: | https://app.any.run/tasks/6d16cb19-fd32-4881-bc3d-7661a92ca4ae |
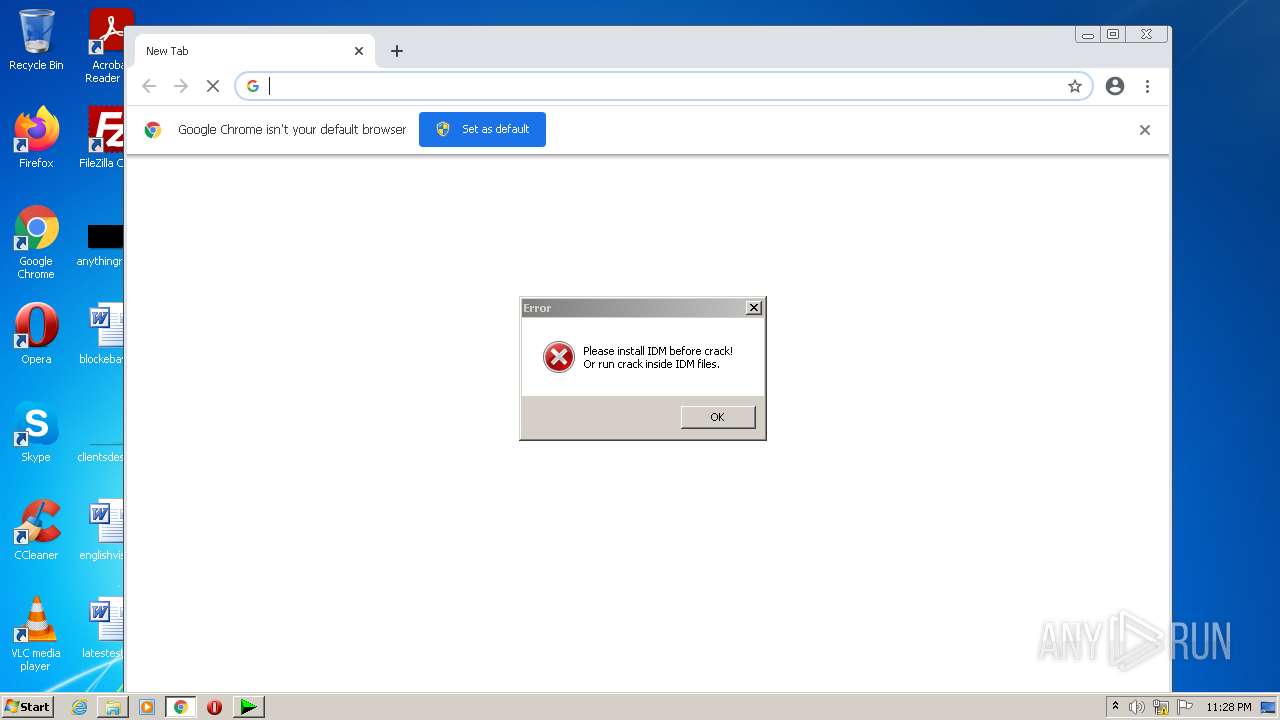
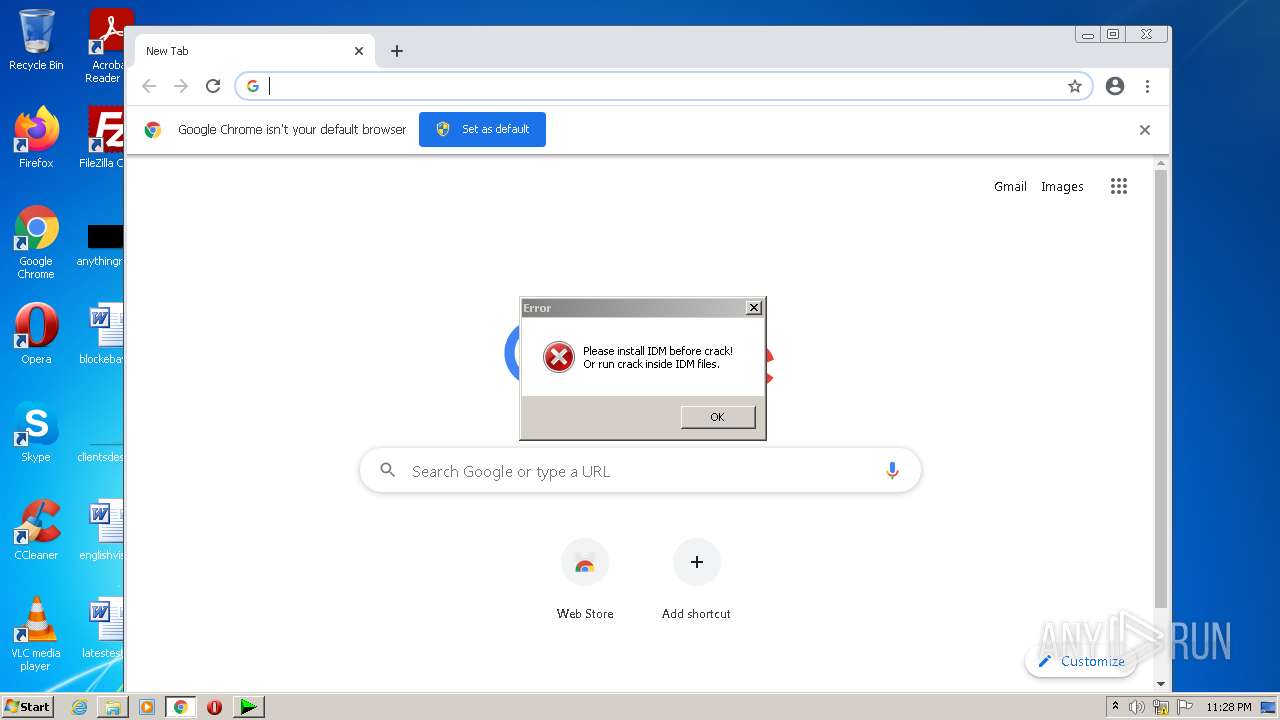
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 22:28:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2BBE2BC49BF01A9AE762DC1784AD160B |
| SHA1: | E06F7295E2CAABA5AE4AA233697048962C4D689F |
| SHA256: | 0DE10B79E2BE68626052ED191E83416446C47F26785AA4A80DFB5F778AA1F400 |
| SSDEEP: | 1536:dXD7myubjnvtiKrkh7+kue5f4sMM0Cpcy:VC7bLAKre+kfhrlWy |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 1648)
- chrome.exe (PID: 3852)
Application was dropped or rewritten from another process
- idman640build11.exe (PID: 2976)
- idman640build11.exe (PID: 372)
SUSPICIOUS
Checks supported languages
- www.internetdownloadmanager.comdownload.html.exe (PID: 3596)
- idman640build11.exe (PID: 2976)
- IDM1.tmp (PID: 3784)
- idmBroker.exe (PID: 2352)
- IDMan.exe (PID: 3536)
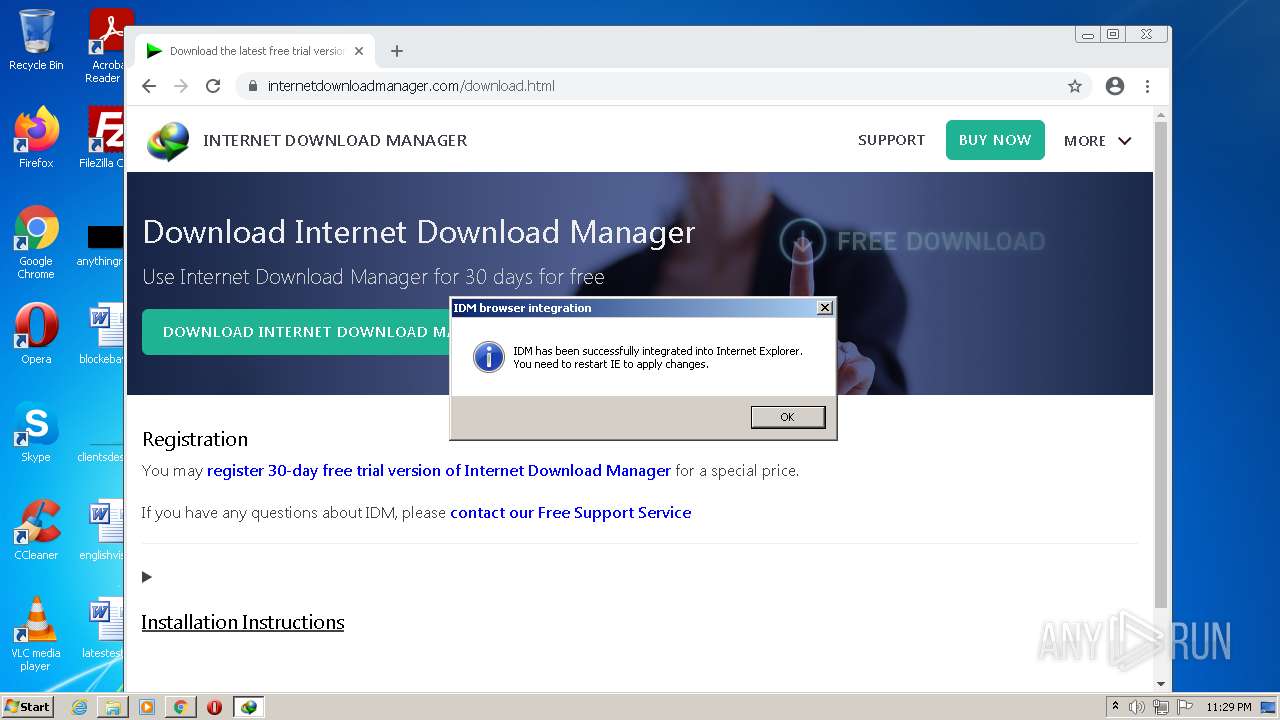
Modifies files in Chrome extension folder
- chrome.exe (PID: 1648)
Drops a file with a compile date too recent
- chrome.exe (PID: 1648)
- chrome.exe (PID: 3852)
Executable content was dropped or overwritten
- chrome.exe (PID: 1648)
- chrome.exe (PID: 3852)
Creates a directory in Program Files
- IDM1.tmp (PID: 3784)
Creates/Modifies COM task schedule object
- IDM1.tmp (PID: 3784)
- IDMan.exe (PID: 3536)
Starts application with an unusual extension
- idman640build11.exe (PID: 2976)
Creates a software uninstall entry
- IDM1.tmp (PID: 3784)
Reads the computer name
- IDM1.tmp (PID: 3784)
- IDMan.exe (PID: 3536)
Creates files in the user directory
- IDM1.tmp (PID: 3784)
- IDMan.exe (PID: 3536)
Creates files in the program directory
- IDM1.tmp (PID: 3784)
INFO
Manual execution by user
- chrome.exe (PID: 1648)
Checks supported languages
- chrome.exe (PID: 1648)
- chrome.exe (PID: 2764)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3608)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 1056)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 1004)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 2716)
- chrome.exe (PID: 2388)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 128)
- chrome.exe (PID: 3848)
- chrome.exe (PID: 2900)
- chrome.exe (PID: 3420)
Application launched itself
- chrome.exe (PID: 1648)
Reads the computer name
- chrome.exe (PID: 1648)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 3608)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 2388)
- chrome.exe (PID: 128)
- chrome.exe (PID: 2900)
Reads the hosts file
- chrome.exe (PID: 1648)
- chrome.exe (PID: 3852)
Reads settings of System Certificates
- chrome.exe (PID: 3852)
- chrome.exe (PID: 1648)
- IDMan.exe (PID: 3536)
Checks Windows Trust Settings
- chrome.exe (PID: 1648)
- IDMan.exe (PID: 3536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (58.6) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (39.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.5) |
| .exe | | | Win32 Executable (generic) (0.3) |
| .exe | | | Win16/32 Executable Delphi generic (0.1) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x929c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 31232 |
| CodeSize: | 34304 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00008564 | 0x00008600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40806 |
DATA | 0x0000A000 | 0x000004F0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.17188 |
BSS | 0x0000B000 | 0x00000691 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000C000 | 0x00000A66 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.23513 |
.tls | 0x0000D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0000F000 | 0x00000790 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.4939 |
.rsrc | 0x00010000 | 0x00005E00 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.94939 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.03348 | 1681 | UNKNOWN | UNKNOWN | RT_MANIFEST |
101 | 3.23595 | 376 | UNKNOWN | UNKNOWN | RT_DIALOG |
BATCLEN | 1 | 2 | UNKNOWN | English - United States | BINRES |
CLEAN | 5.42843 | 6339 | UNKNOWN | English - United States | BINRES |
CRKRST | 5.02225 | 274 | UNKNOWN | UNKNOWN | BINRES |
HEAD | 5.36471 | 798 | UNKNOWN | UNKNOWN | BINRES |
IDMBAK | 4.898 | 323 | UNKNOWN | UNKNOWN | BINRES |
IDMREG | 5.16471 | 640 | UNKNOWN | UNKNOWN | BINRES |
IDMSPD | 5.07133 | 934 | UNKNOWN | UNKNOWN | BINRES |
SELFDEL | 4.48118 | 55 | UNKNOWN | UNKNOWN | BINRES |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
72
Monitored processes
31
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,6254979527832970538,8292486452232911815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2156 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 372 | "C:\Users\admin\Downloads\idman640build11.exe" | C:\Users\admin\Downloads\idman640build11.exe | — | chrome.exe | |||||||||||
User: admin Company: Tonec Inc. Integrity Level: MEDIUM Description: Internet Download Manager installer Exit code: 3221226540 Version: 6, 40, 11, 1 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,6254979527832970538,8292486452232911815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2980 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,6254979527832970538,8292486452232911815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,6254979527832970538,8292486452232911815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3056 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,6254979527832970538,8292486452232911815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2080 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | |||||||||||||||
| 2352 | "C:\Program Files\Internet Download Manager\idmBroker.exe" -RegServer | C:\Program Files\Internet Download Manager\idmBroker.exe | — | IDM1.tmp | |||||||||||
User: admin Company: Internet Download Manager, Tonec Inc. Integrity Level: HIGH Description: Broker for reading of IDM settings Exit code: 0 Version: 6, 35, 9, 1 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,6254979527832970538,8292486452232911815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2744 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,6254979527832970538,8292486452232911815,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3384 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
21 558
Read events
20 912
Write events
586
Delete events
60
Modification events
| (PID) Process: | (3596) www.internetdownloadmanager.comdownload.html.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (1648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1648) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
4
Suspicious files
118
Text files
99
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62881628-670.pma | — | |
MD5:— | SHA256:— | |||
| 1648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9d13e059-8ded-475c-a6b3-f82dd772feb8.tmp | text | |
MD5:— | SHA256:— | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 1648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 1648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 1648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFfd49c.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 1648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
28
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3852 | chrome.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 591 b | whitelisted |
3536 | IDMan.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?6d1b3374de723ae2 | US | compressed | 60.0 Kb | whitelisted |
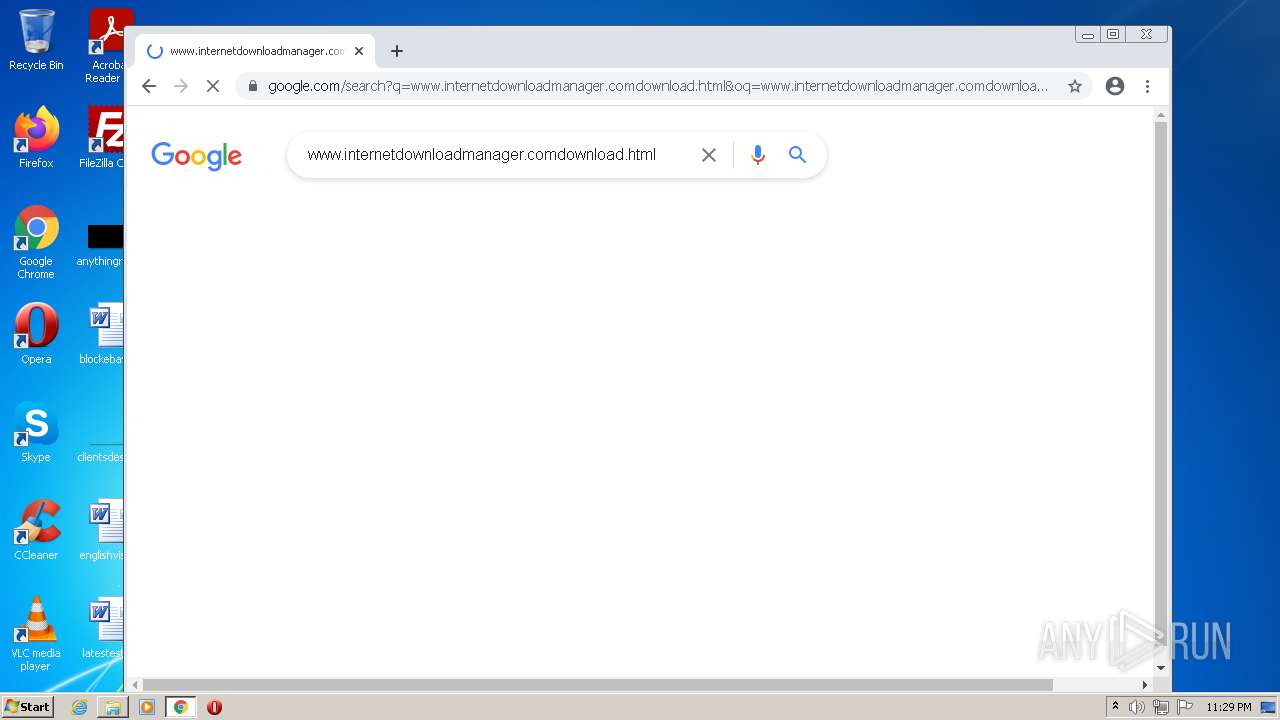
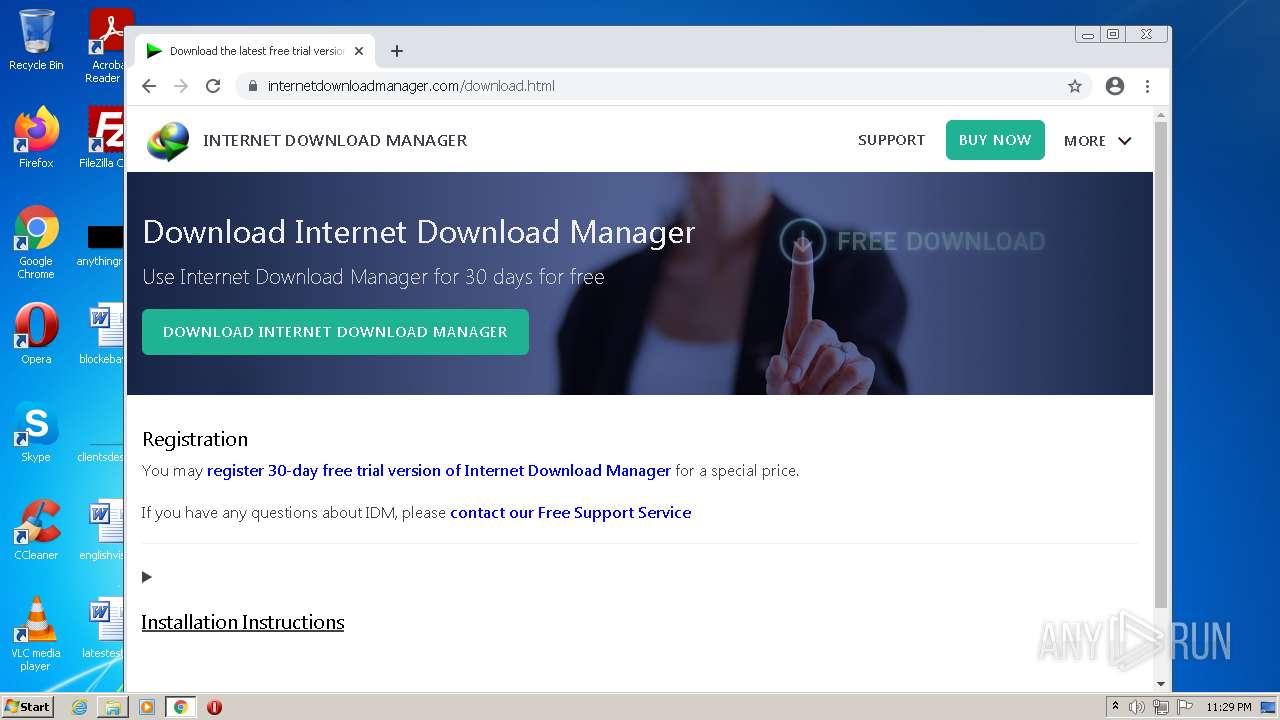
3852 | chrome.exe | GET | 301 | 169.61.27.133:80 | http://www.internetdownloadmanager.com/download.html | US | html | 261 b | whitelisted |
3852 | chrome.exe | GET | 200 | 74.125.8.104:80 | http://r3---sn-5hne6nzs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=157.97.122.7&mm=28&mn=sn-5hne6nzs&ms=nvh&mt=1653085697&mv=m&mvi=3&pl=24&rmhost=r1---sn-5hne6nzs.gvt1.com&shardbypass=sd&smhost=r1---sn-5hne6nsd.gvt1.com | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3852 | chrome.exe | 142.250.185.132:443 | www.google.com | Google Inc. | US | whitelisted |
3852 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3852 | chrome.exe | 216.58.212.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3852 | chrome.exe | 142.250.185.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3852 | chrome.exe | 142.250.184.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3852 | chrome.exe | 142.250.186.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3852 | chrome.exe | 142.250.185.206:443 | apis.google.com | Google Inc. | US | whitelisted |
3852 | chrome.exe | 142.250.186.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 142.250.186.35:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3852 | chrome.exe | 142.250.185.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |