| File name: | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe |
| Full analysis: | https://app.any.run/tasks/dfc2a3f5-8b8f-4e33-85e5-c8e4189ba433 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 19:35:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 8 sections |
| MD5: | 6F32C72517FD6D42B5BF91A783F6AC5C |
| SHA1: | 6592AF7B52E4F4E3066DE667DCC27EC195BB2843 |
| SHA256: | 0DC160127748145FB0F0C6A60C2BDFC686C89A52C96482F7E2DDF68FE177FB5F |
| SSDEEP: | 98304:7q69dyxpSd9ptUgSFRbfr+8VpyJftDT6LoERRKlKJqGt0RNs8rJ6POMD2drS8J/p:0GsOwbH54BX |
MALICIOUS
Executing a file with an untrusted certificate
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 2728)
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
SUSPICIOUS
Reads security settings of Internet Explorer
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
- Uninstall.exe (PID: 3488)
Reads Microsoft Outlook installation path
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
Executable content was dropped or overwritten
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
Drops 7-zip archiver for unpacking
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
Reads Internet Explorer settings
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
Reads the date of Windows installation
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
- Uninstall.exe (PID: 3488)
Creates/Modifies COM task schedule object
- Uninstall.exe (PID: 3488)
Creates a software uninstall entry
- Uninstall.exe (PID: 3488)
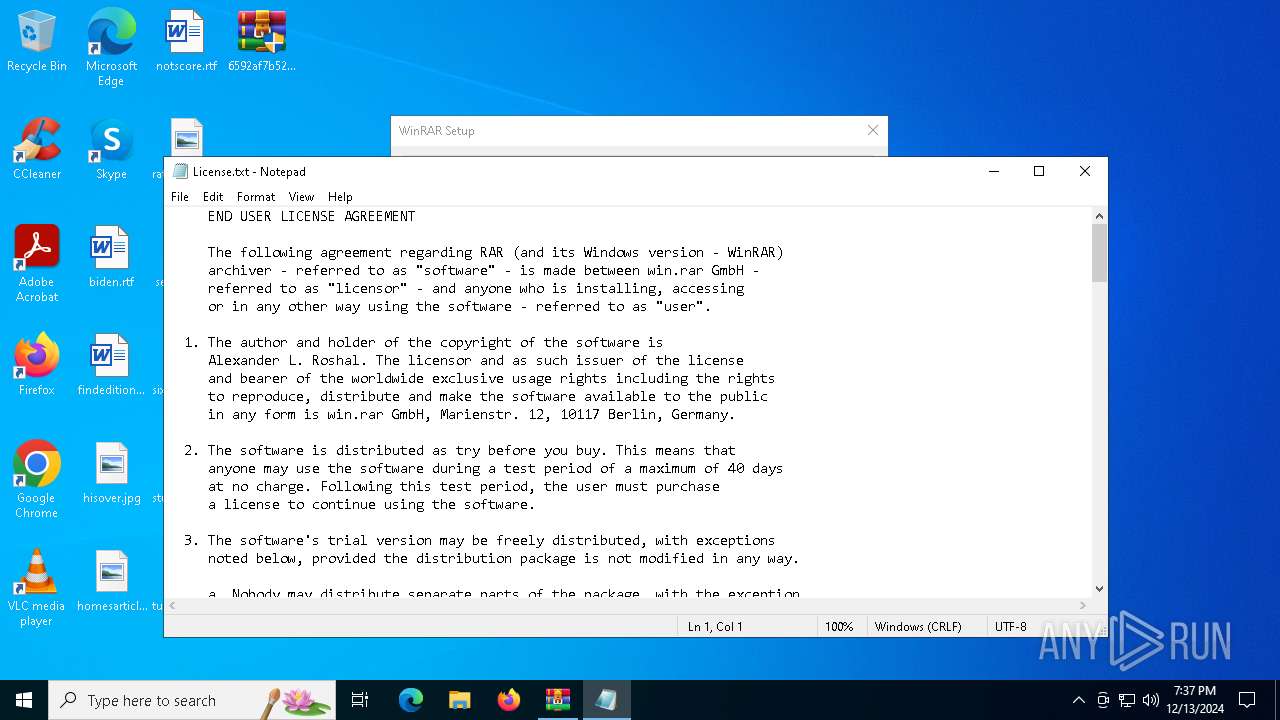
Start notepad (likely ransomware note)
- Uninstall.exe (PID: 3488)
Searches for installed software
- Uninstall.exe (PID: 3488)
INFO
The sample compiled with english language support
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
Reads the computer name
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
- Uninstall.exe (PID: 3488)
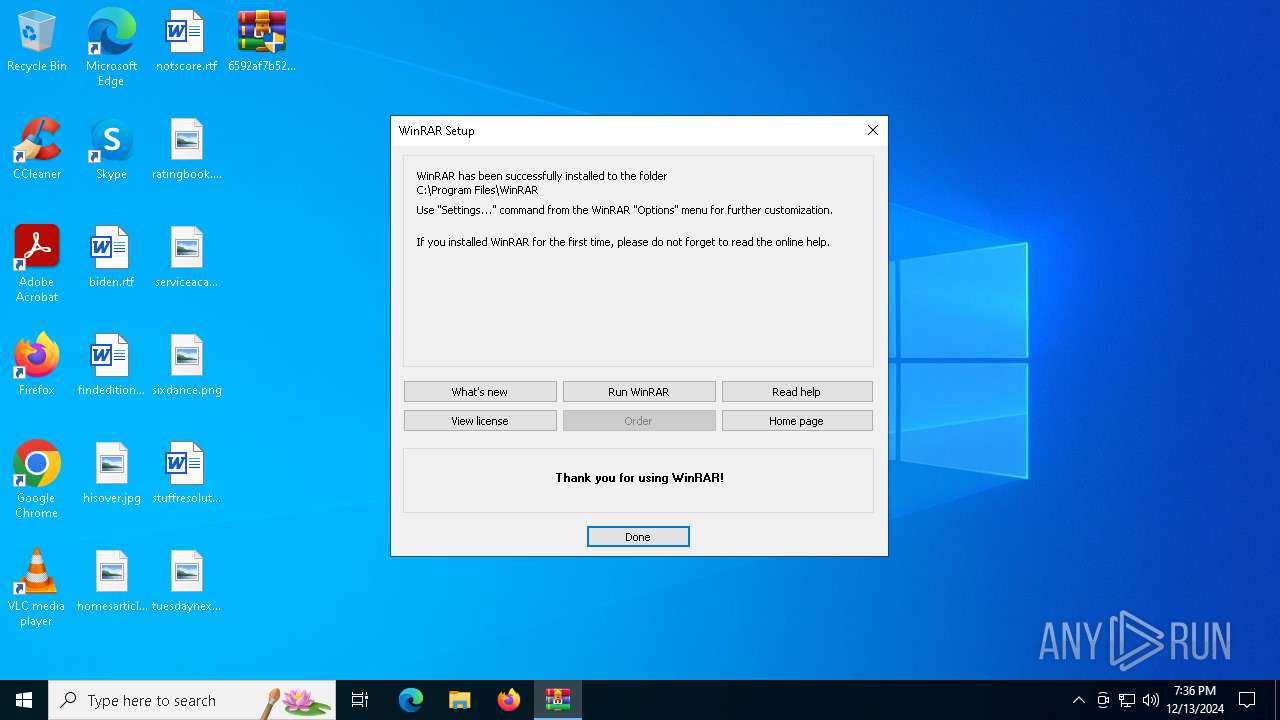
Creates files in the program directory
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
- Uninstall.exe (PID: 3488)
The process uses the downloaded file
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
- Uninstall.exe (PID: 3488)
Checks proxy server information
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
Checks supported languages
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
- Uninstall.exe (PID: 3488)
Process checks computer location settings
- 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe (PID: 4548)
- Uninstall.exe (PID: 3488)
Creates files or folders in the user directory
- Uninstall.exe (PID: 3488)
Reads Microsoft Office registry keys
- Uninstall.exe (PID: 3488)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:05:12 10:17:26+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.33 |
| CodeSize: | 270848 |
| InitializedDataSize: | 309760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29e90 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.1.0.0 |
| ProductVersionNumber: | 7.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
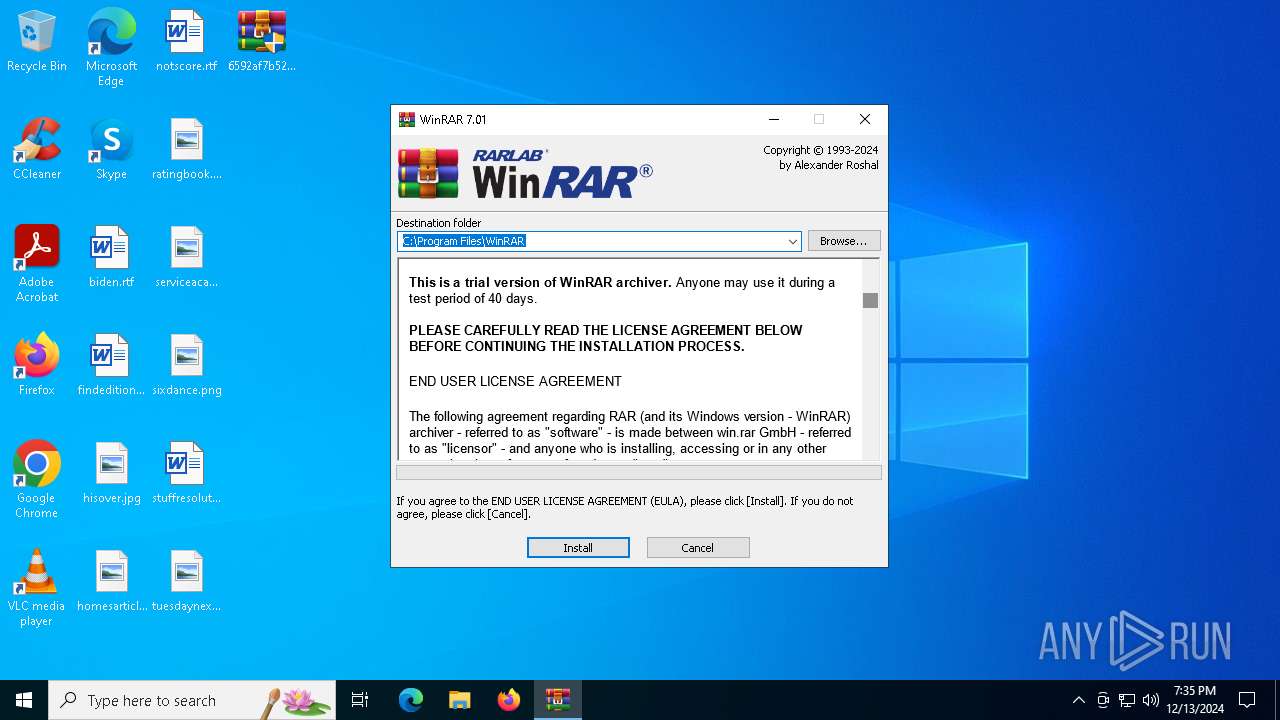
| ProductName: | WinRAR |
| CompanyName: | Alexander Roshal |
| FileDescription: | WinRAR |
| FileVersion: | 7.1.0 |
| ProductVersion: | 7.1.0 |
| InternalName: | WinRAR |
| LegalCopyright: | Copyright © Alexander Roshal 1993-2024 |
| OriginalFileName: | WinRAR.exe |
Total processes
113
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2728 | "C:\Users\admin\Desktop\6592af7b52e4f4e3066de667dcc27ec195bb2843.exe" | C:\Users\admin\Desktop\6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR Exit code: 3221226540 Version: 7.1.0 Modules
| |||||||||||||||
| 2928 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Program Files\WinRAR\License.txt | C:\Windows\System32\notepad.exe | — | Uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3488 | "C:\Program Files\WinRAR\uninstall.exe" /setup | C:\Program Files\WinRAR\Uninstall.exe | — | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Uninstall WinRAR Version: 7.1.0 Modules
| |||||||||||||||
| 4548 | "C:\Users\admin\Desktop\6592af7b52e4f4e3066de667dcc27ec195bb2843.exe" | C:\Users\admin\Desktop\6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR Exit code: 0 Version: 7.1.0 Modules
| |||||||||||||||
Total events
1 650
Read events
1 563
Write events
83
Delete events
4
Modification events
| (PID) Process: | (4548) 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4548) 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4548) 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4548) 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Program Files%WinRAR |
Value: C:\Program Files\WinRAR | |||
| (PID) Process: | (4548) 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (4548) 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
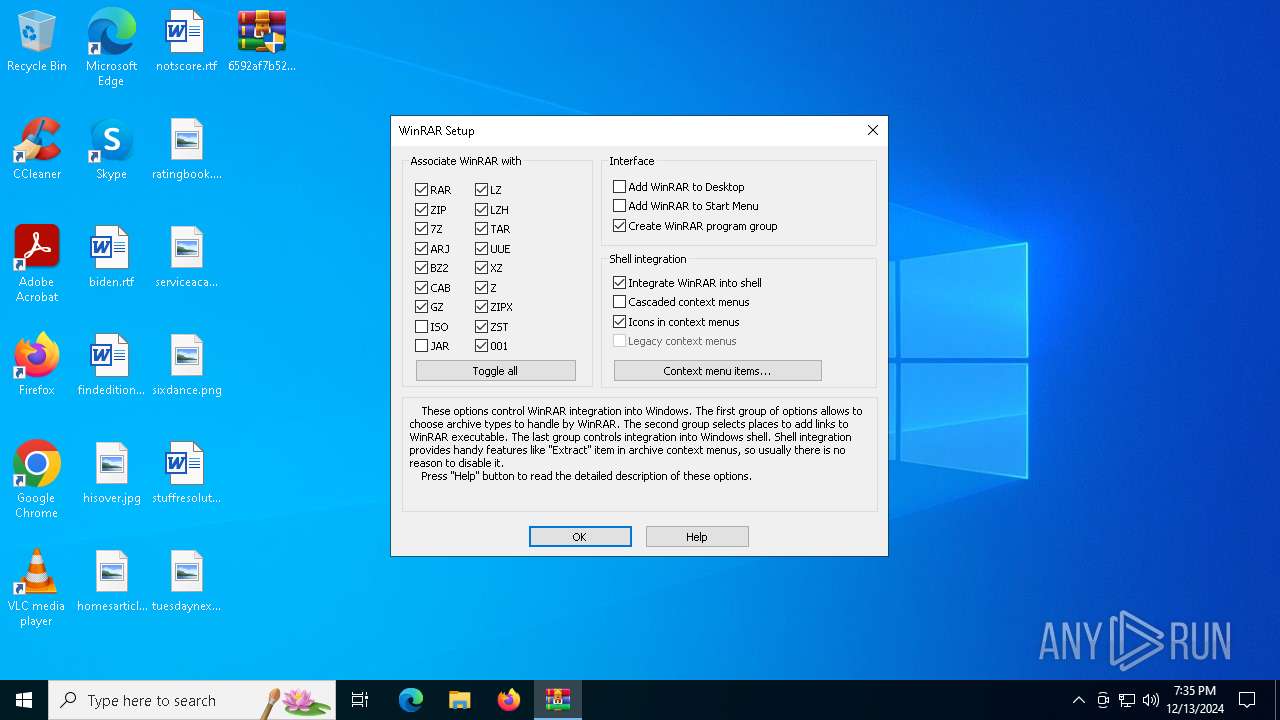
| (PID) Process: | (3488) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.rar |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (3488) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.zip |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (3488) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.cab |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (3488) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.arj |
| Operation: | write | Name: | Set |
Value: 1 | |||
Executable files
13
Suspicious files
1
Text files
11
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4548 | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | — | ||
MD5:— | SHA256:— | |||
| 4548 | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | C:\Program Files\WinRAR\Rar.txt | text | |
MD5:B954981A253F5E1EE25585037A0C5FEE | SHA256:59E40B34B09BE2654B793576035639C459AD6E962F9F9CD000D556FA21B1C7CD | |||
| 4548 | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | C:\Program Files\WinRAR\ReadMe.txt | text | |
MD5:00D0A57A6D64EE3DE8F4D5529D6C6447 | SHA256:FCD13E1B97AF47B8B923BA97AE15E9731C66093609667C3171D5DD24A6F7F2E6 | |||
| 4548 | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | C:\Program Files\WinRAR\License.txt | text | |
MD5:672064CF19DB0B083B981CF0BE7662B0 | SHA256:9FC8AA33CCAFA04C1CE4C0A61047B341297D720ADAB1B77F67B5FE59F43BB59F | |||
| 4548 | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | C:\Program Files\WinRAR\RarExtInstaller.exe | executable | |
MD5:F5B54D16610A819BBC6099BDC92ADD2C | SHA256:46F533007FB231D0B0AF058A0997AB5E6B44A1B02AE327621F04FDC4B2E18964 | |||
| 4548 | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | C:\Program Files\WinRAR\RarFiles.lst | text | |
MD5:E70E22D45ECB35217D66A4CE30F081FA | SHA256:9EB1099D7231CD24D8740609D3AC6985139F2334730356DF983AB01D7896AD6F | |||
| 4548 | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | C:\Program Files\WinRAR\Rar.exe | executable | |
MD5:16659AE52CE03889AD19DB1F5710C6AA | SHA256:0B1866B627D8078D296E7D39583C9F856117BE79C1D226B8C9378FE075369118 | |||
| 4548 | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | C:\Program Files\WinRAR\Descript.ion | text | |
MD5:84846ABC52DC17020E4E934D3C94B4E6 | SHA256:3449FD40D054C96285FAB92011E732174C7CD000EDA67470376F26F0D431F1F2 | |||
| 4548 | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | C:\Program Files\WinRAR\Default32.SFX | executable | |
MD5:C5BCFD921F209366B9CFED632B174A3B | SHA256:476E3F779D2638238EA185DF6019E4FCB54B3704AD12DBD051399FCF26E6E1BF | |||
| 4548 | 6592af7b52e4f4e3066de667dcc27ec195bb2843.exe | C:\Program Files\WinRAR\Resources.pri | pri | |
MD5:43CB15C1F1CC705305AEBA33B0A9EE73 | SHA256:A7BB097441D9F06DD7A8D08874D70E7495626760C05284CA1AE3A208C11B52F0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
21
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3296 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3296 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.209.189:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3296 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3296 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |