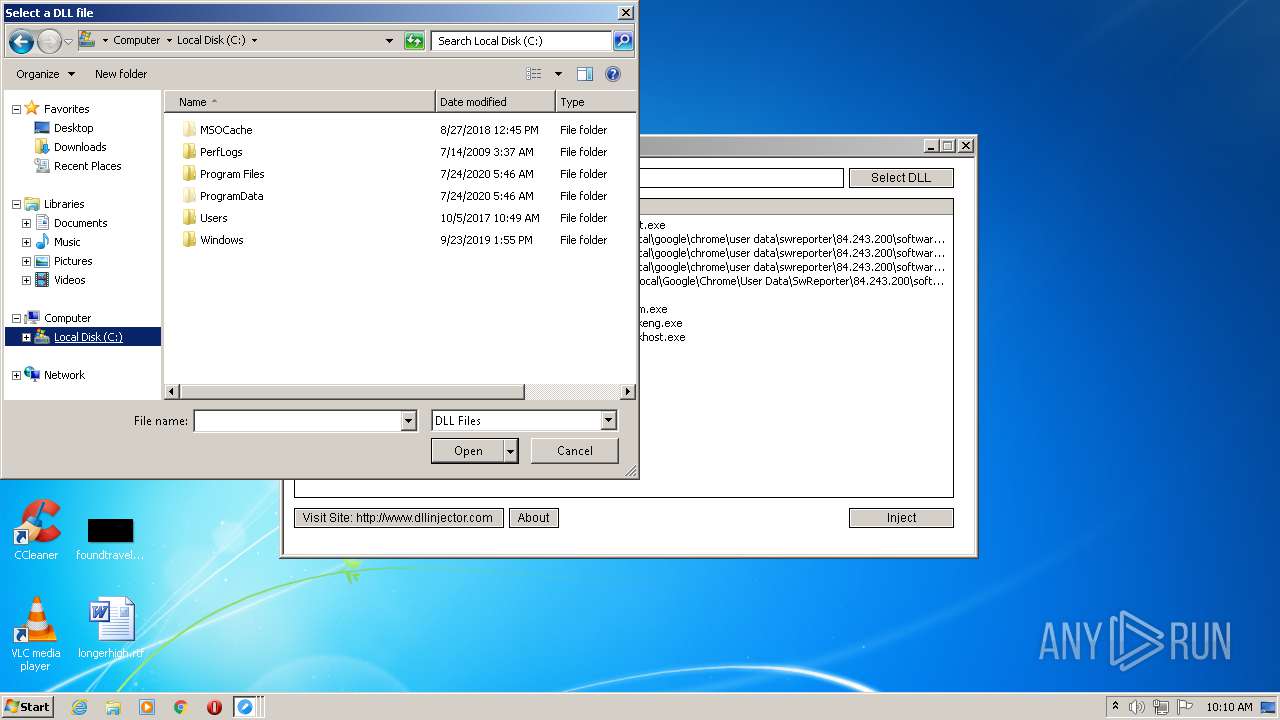
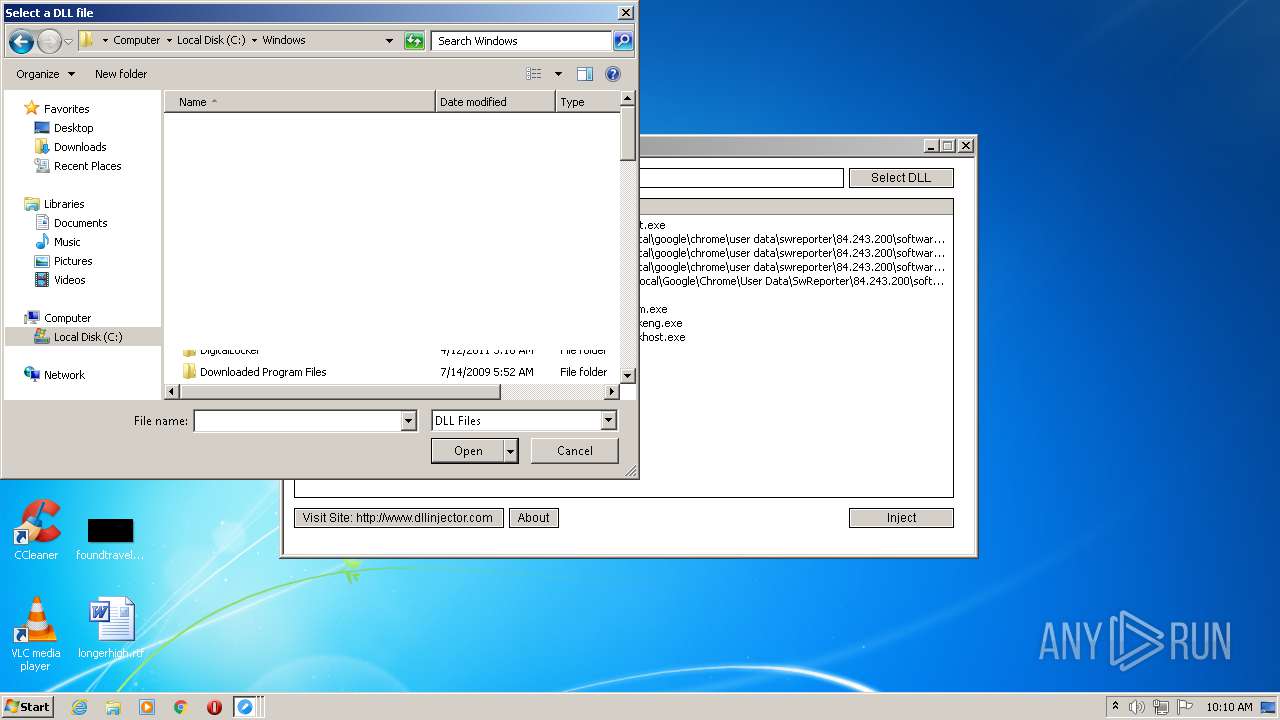
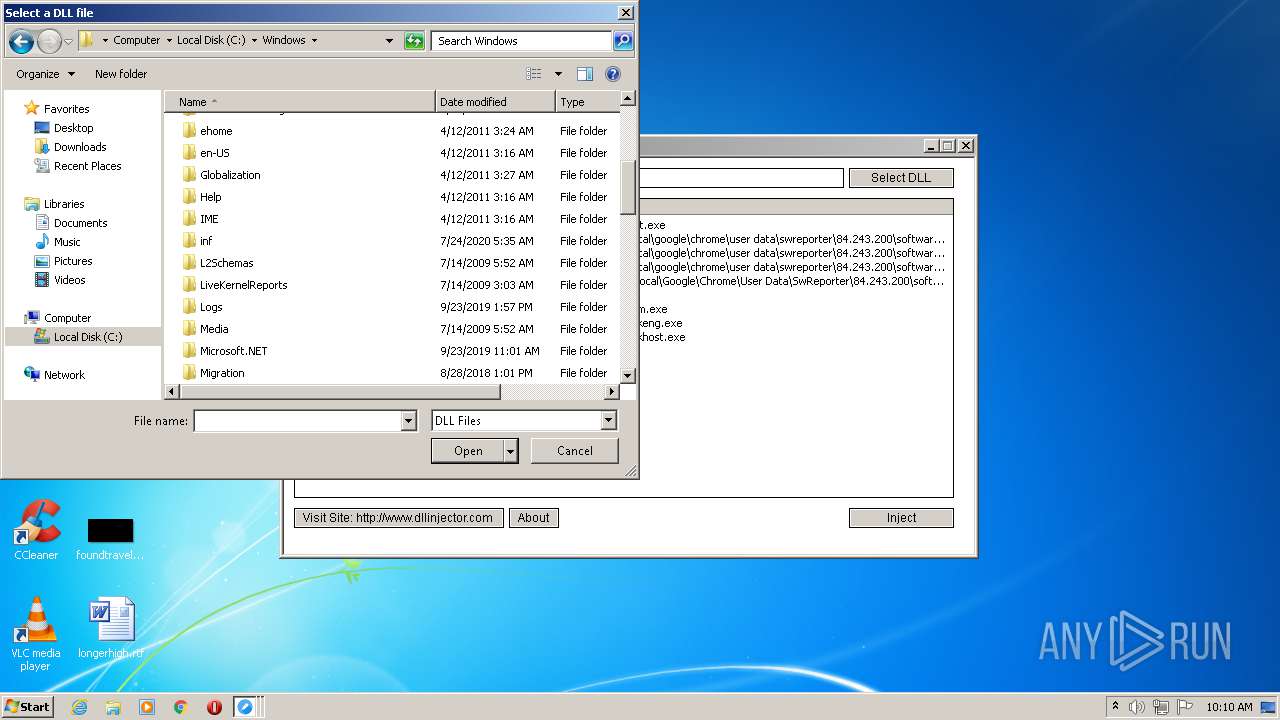
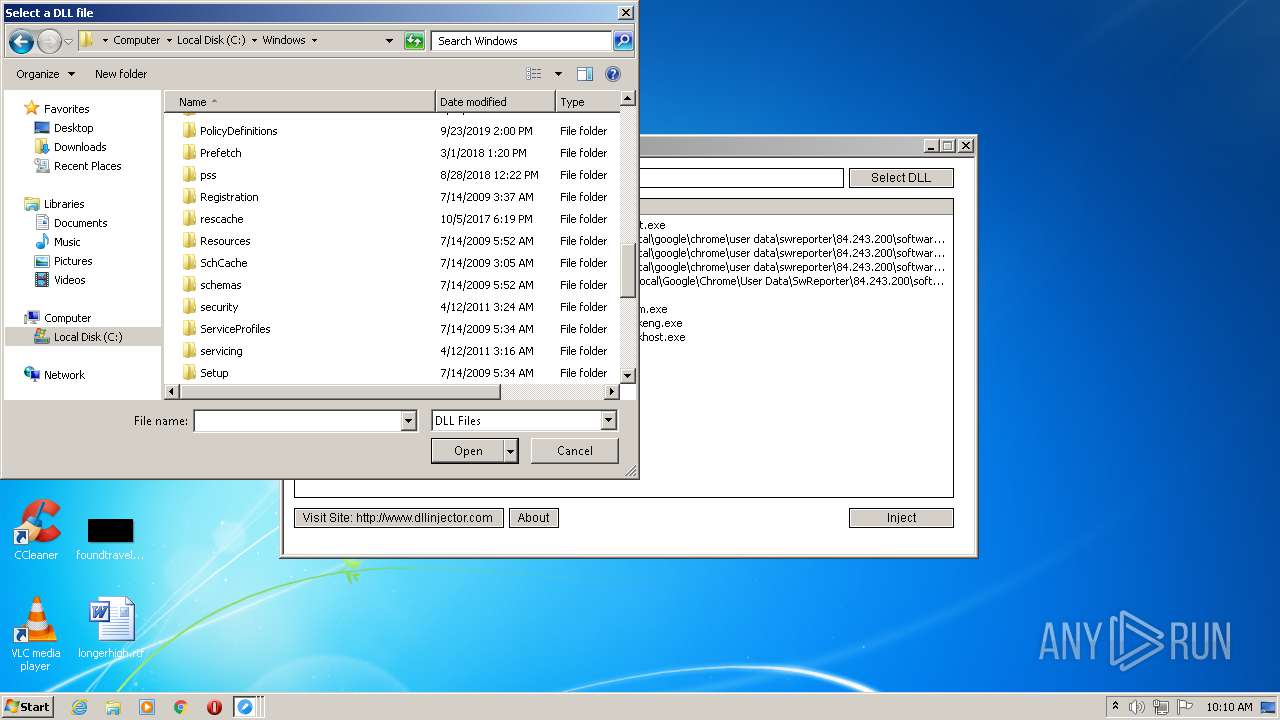
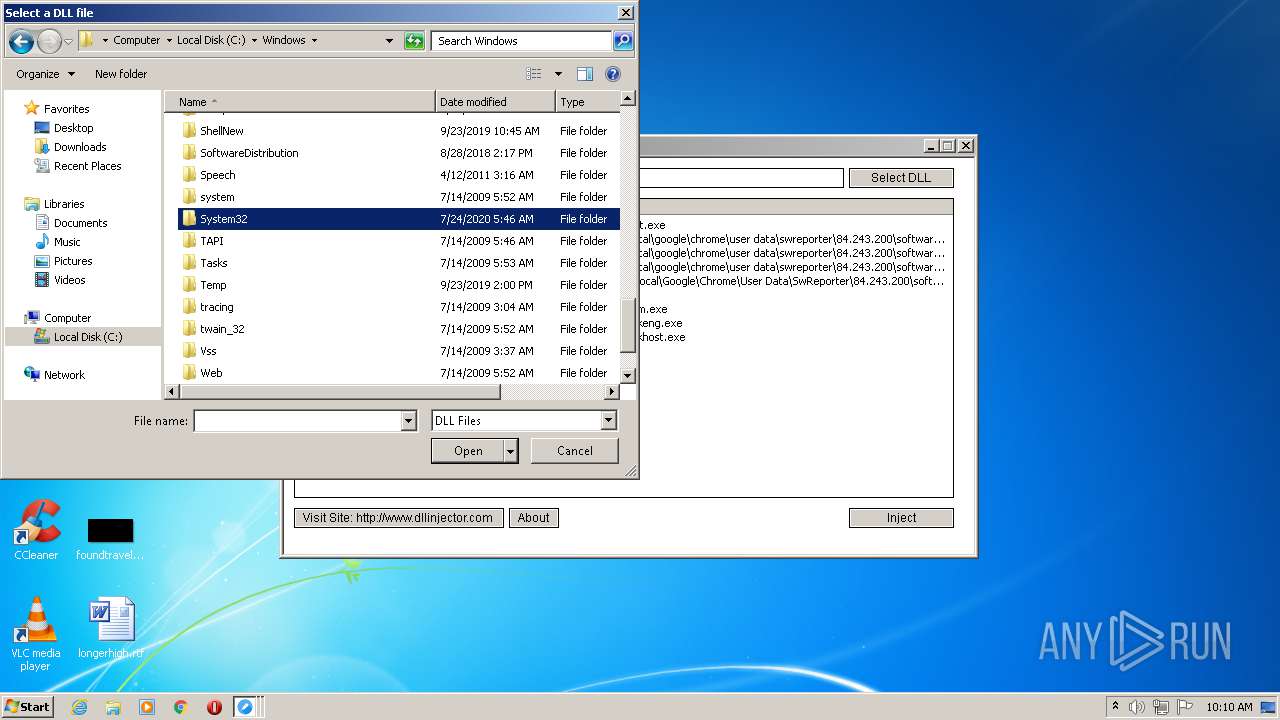
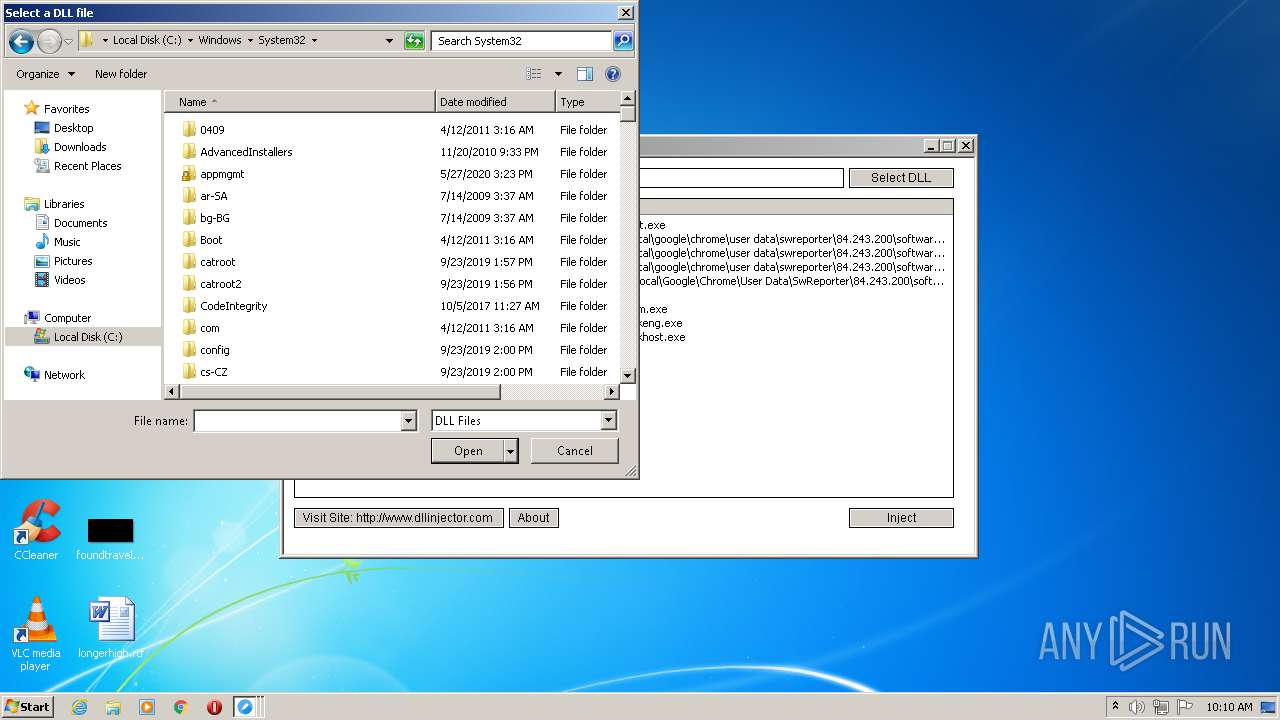
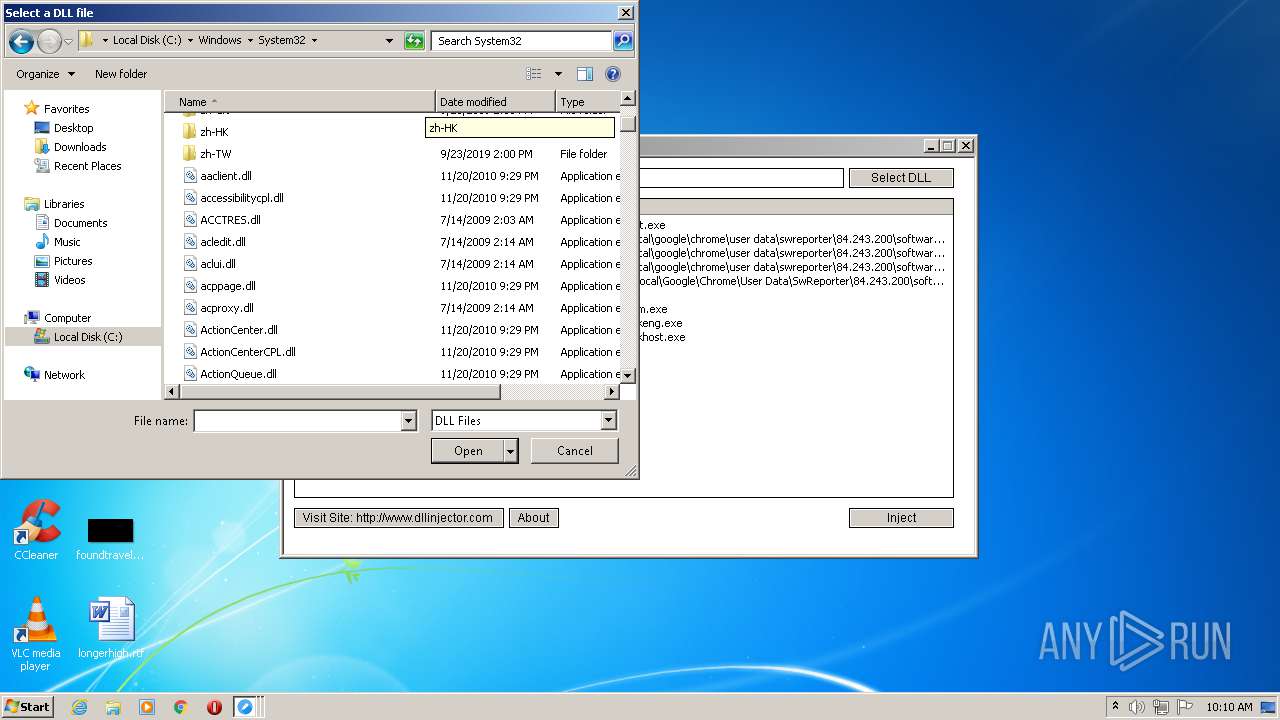
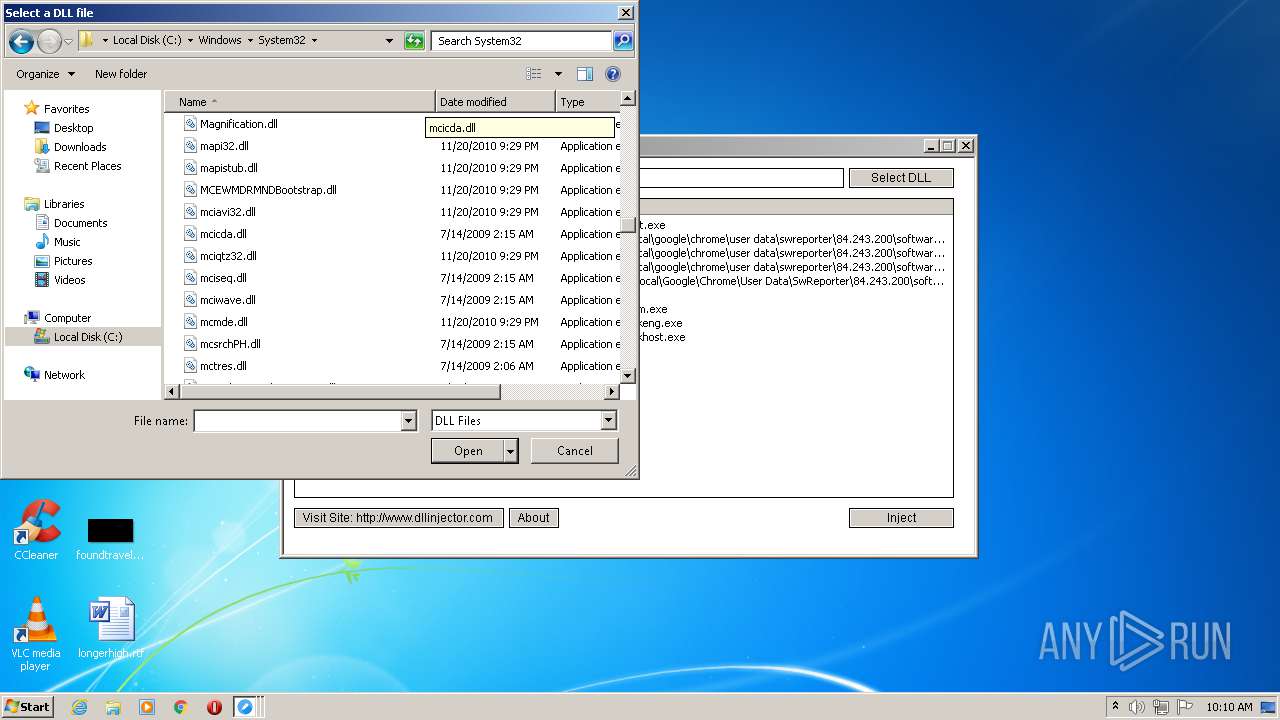
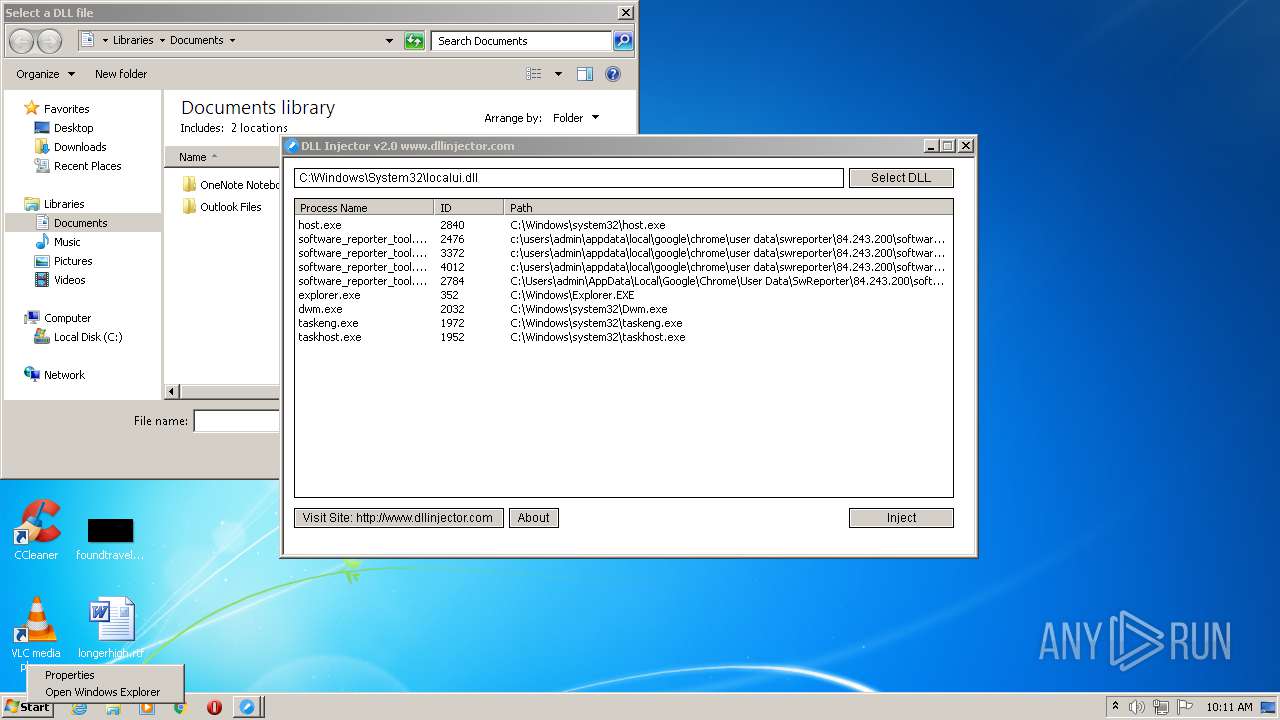
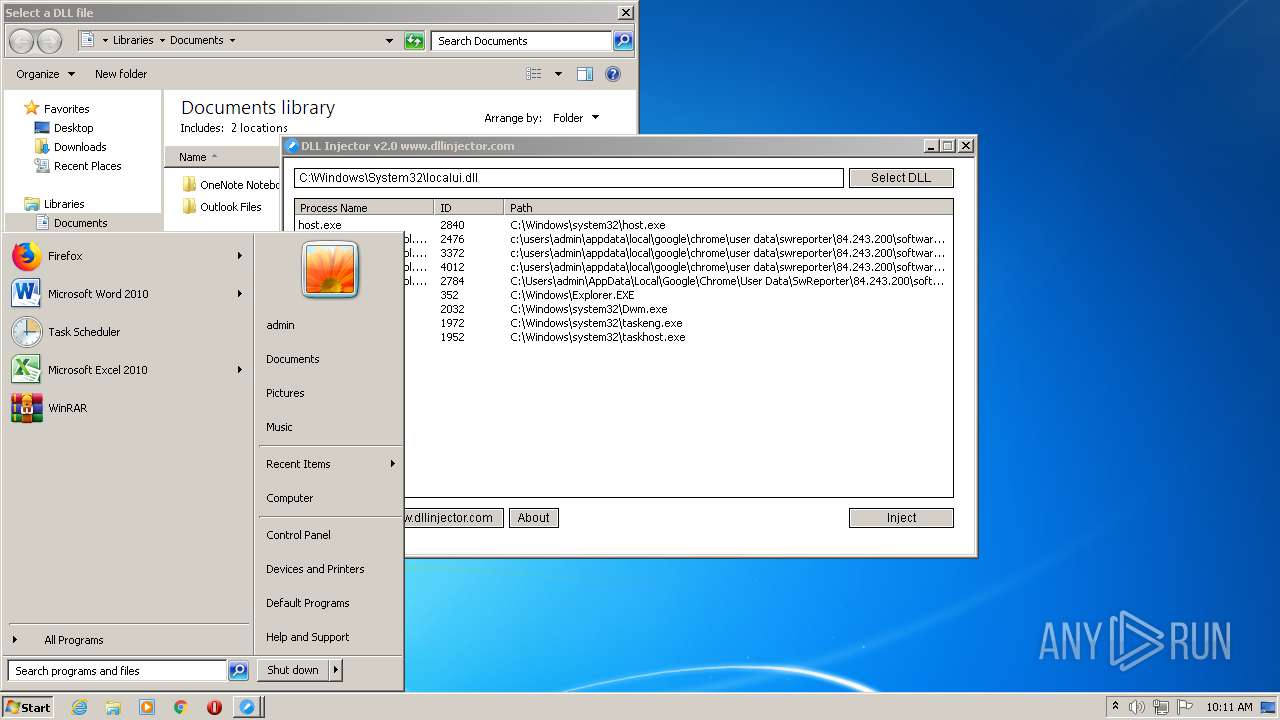
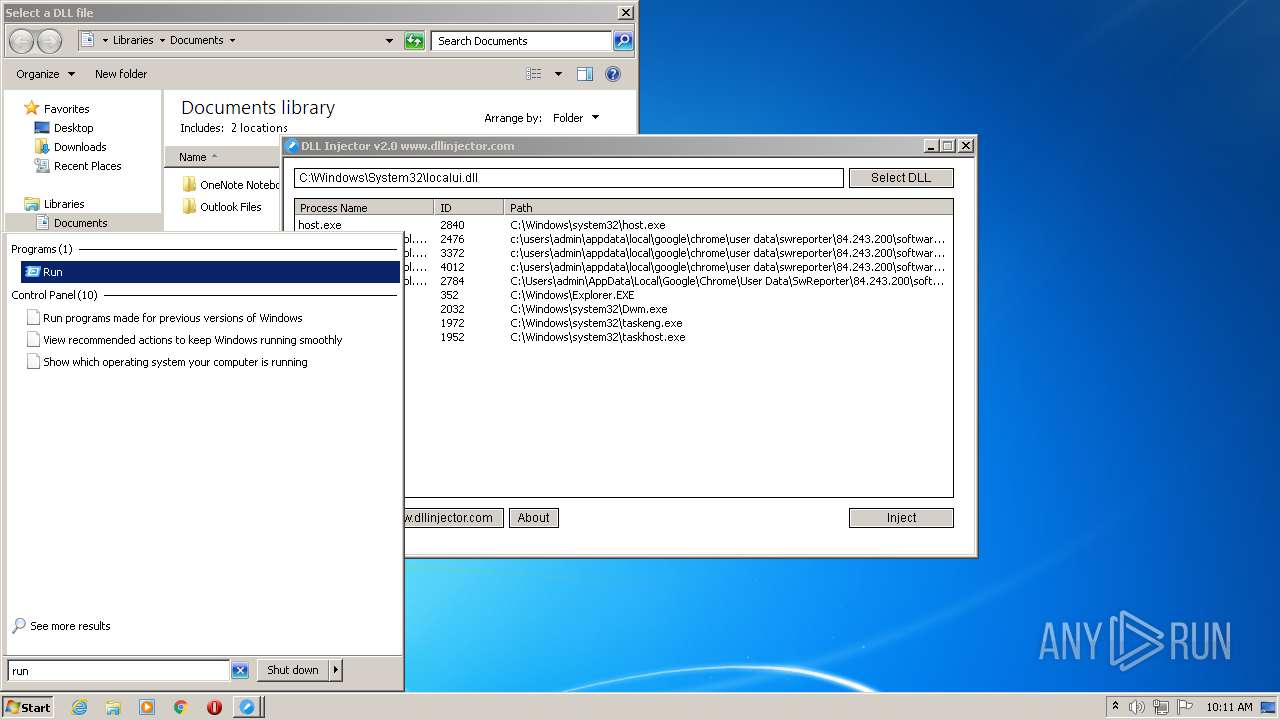
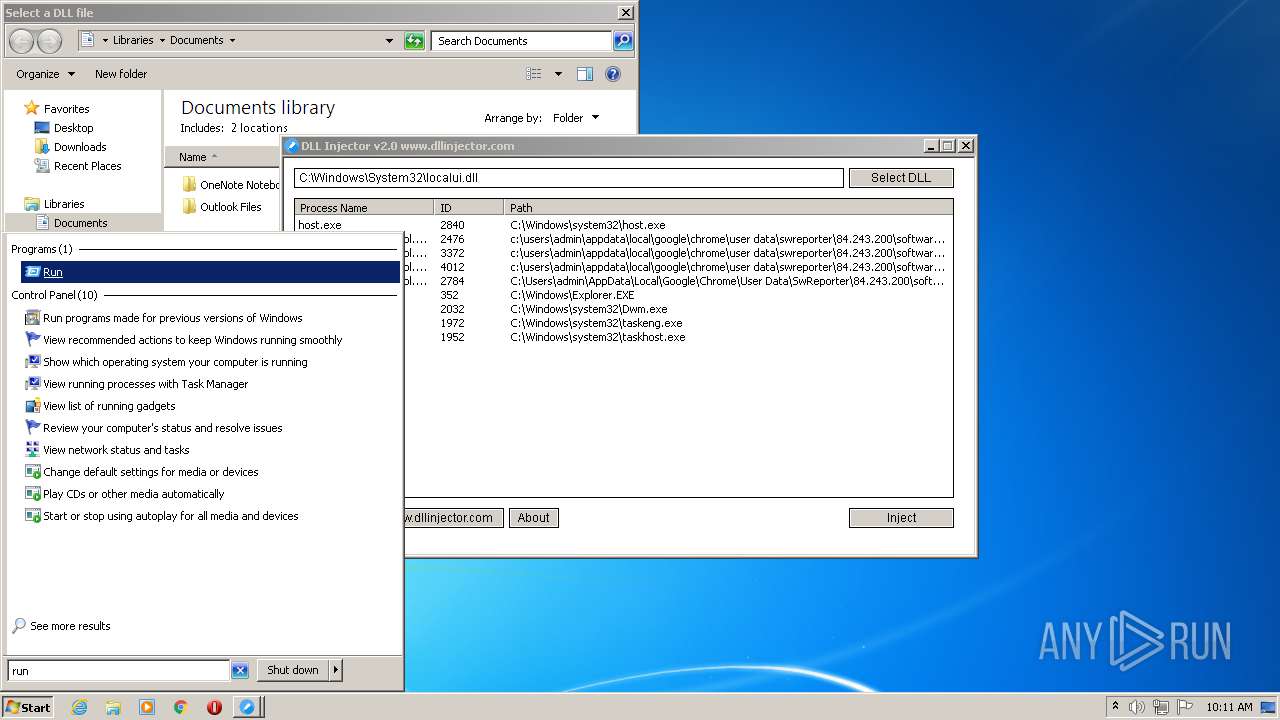
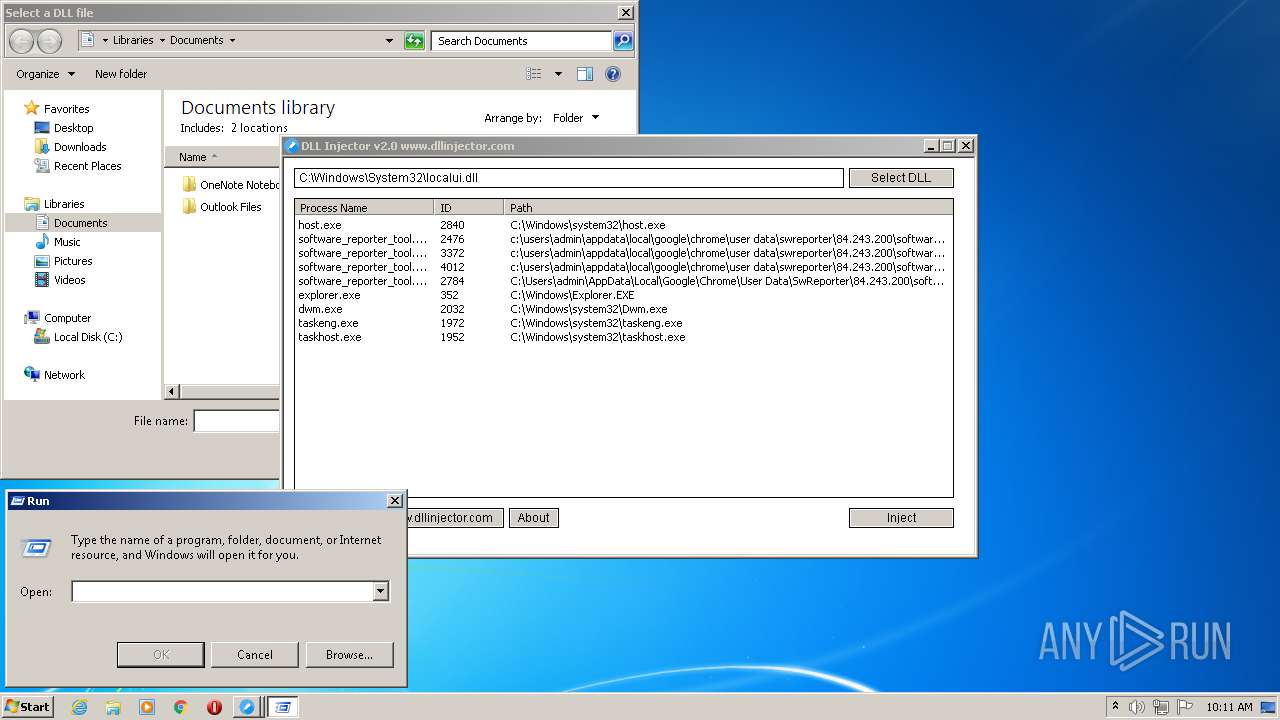
| File name: | dllinjector.exe |
| Full analysis: | https://app.any.run/tasks/f2b5c78a-ff87-4063-bcb4-72b77fe24e0b |
| Verdict: | Malicious activity |
| Analysis date: | September 21, 2020, 09:09:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0A5A1030BEBA8CBA4F283A0636231EE1 |
| SHA1: | EFCD77F4FEA4D5CFEC707F9EE936E027B92BB696 |
| SHA256: | 0DB7DDDD89FC145AB250C69C543A0B0CCC5BCE53D017F2FAF63D9A115A011D26 |
| SSDEEP: | 12288:fGDVJ1jU/DhZDkadDoDVMzQZxa4ioGYRWeyc9u/WC/Wd/5A4LGdHnHp9SdpADUk:fgZWuxa4xGdeyc9VC/Wd5LGhnHmdpADR |
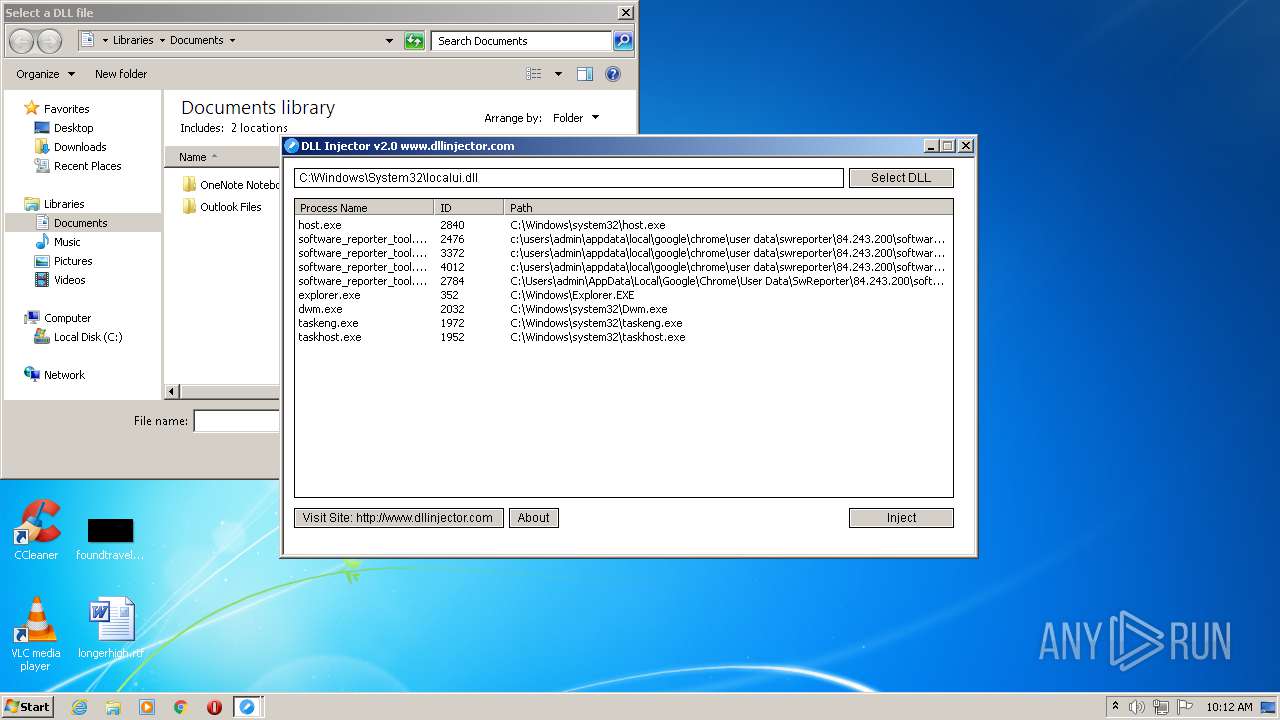
MALICIOUS
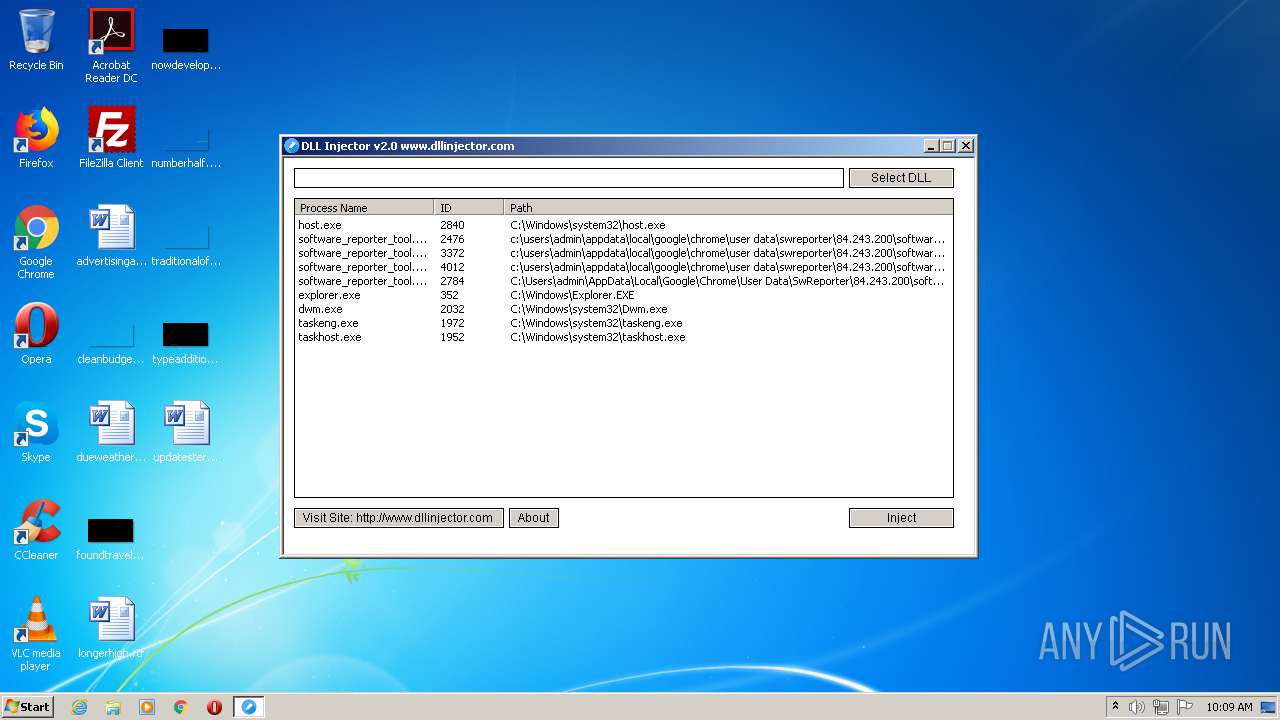
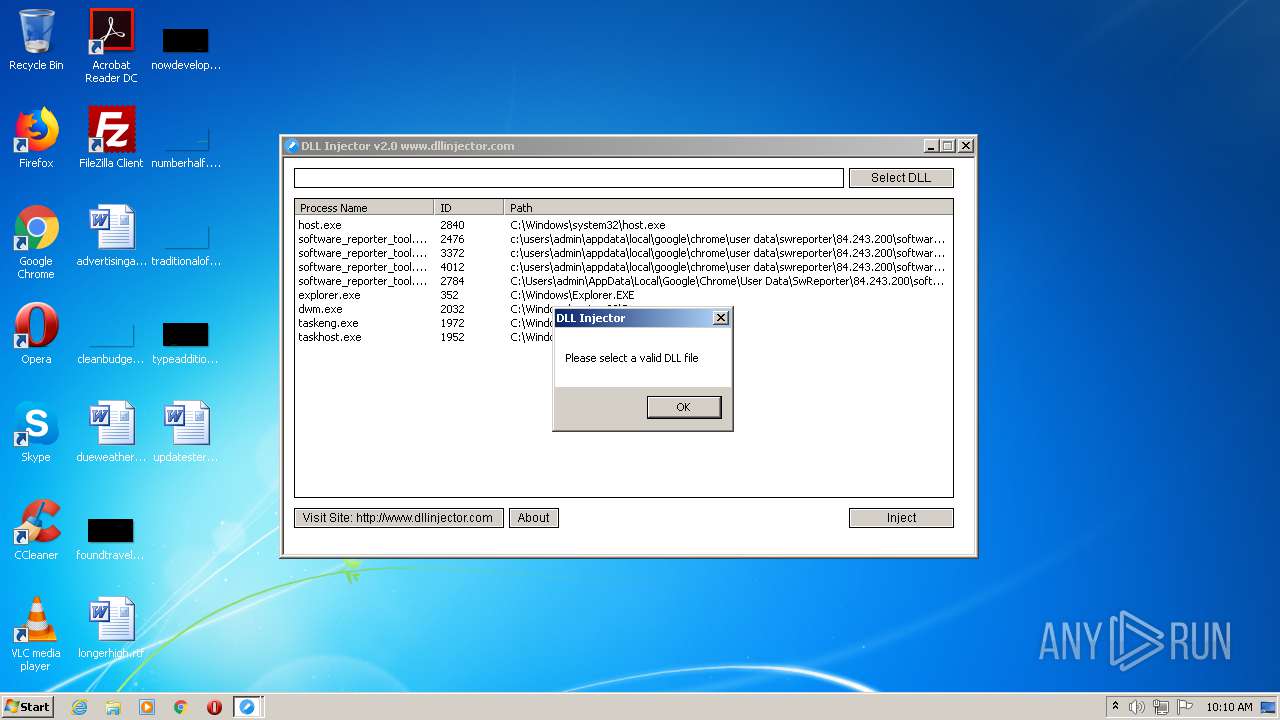
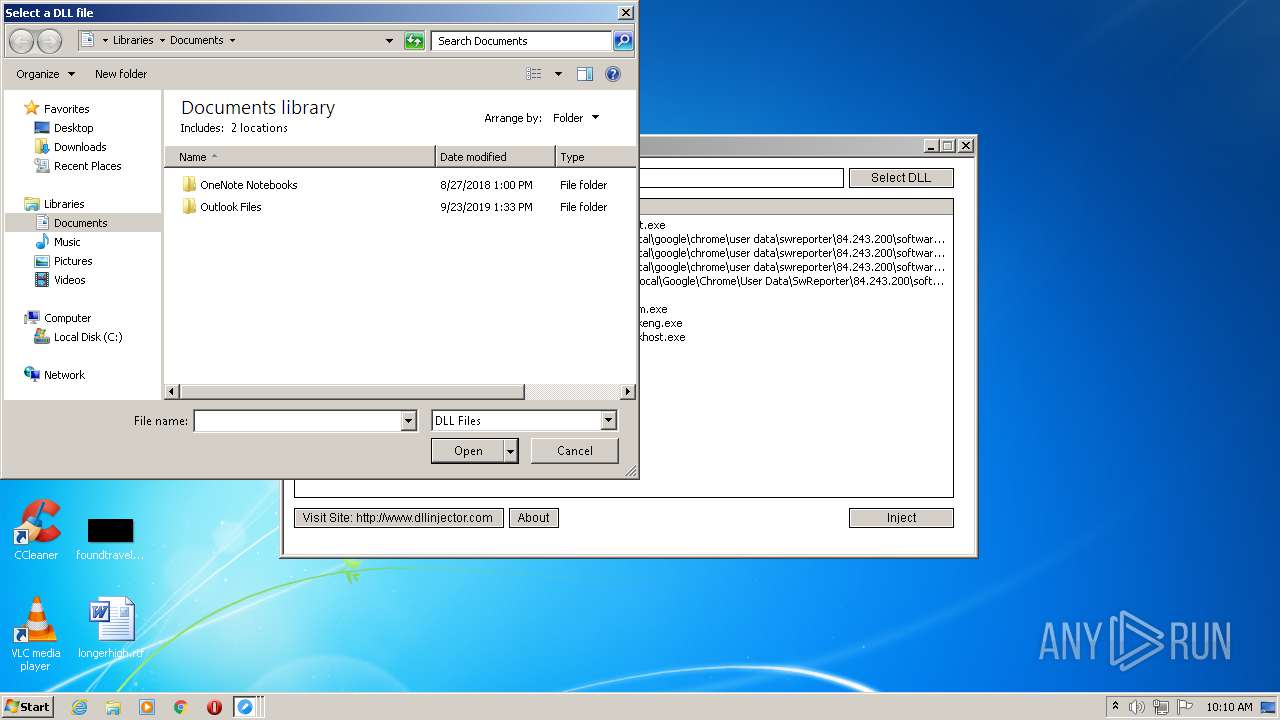
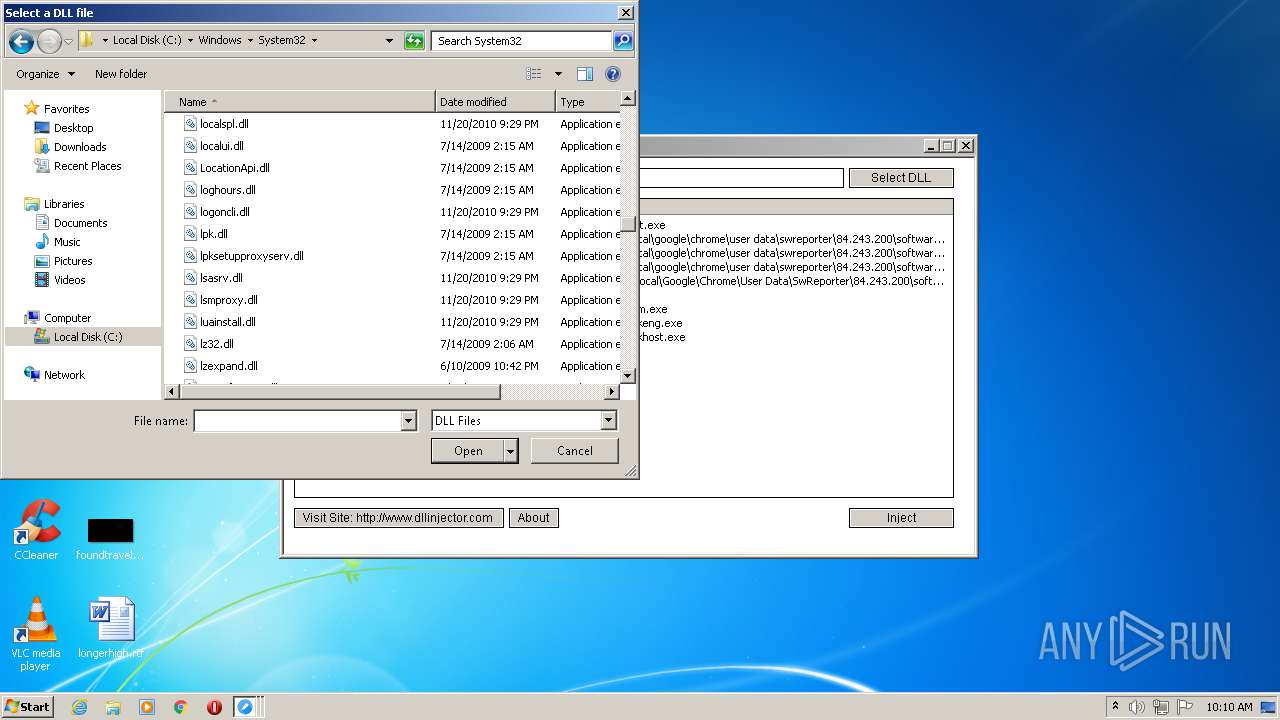
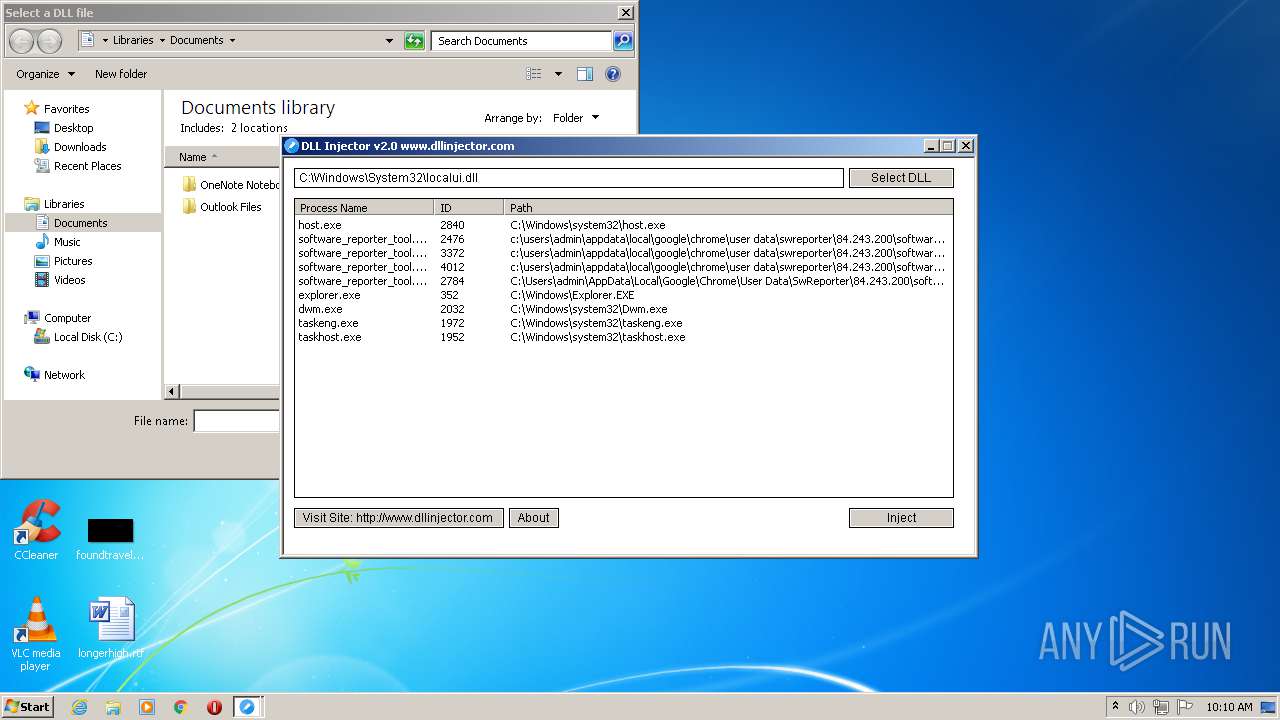
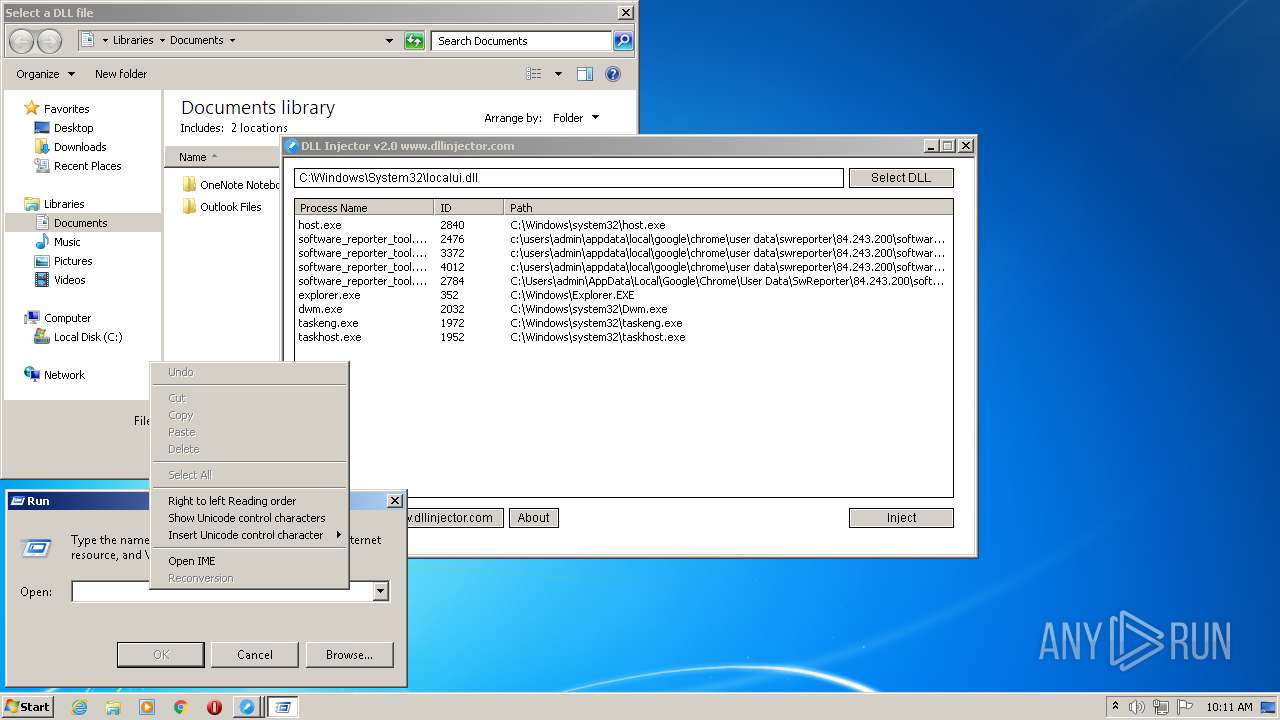
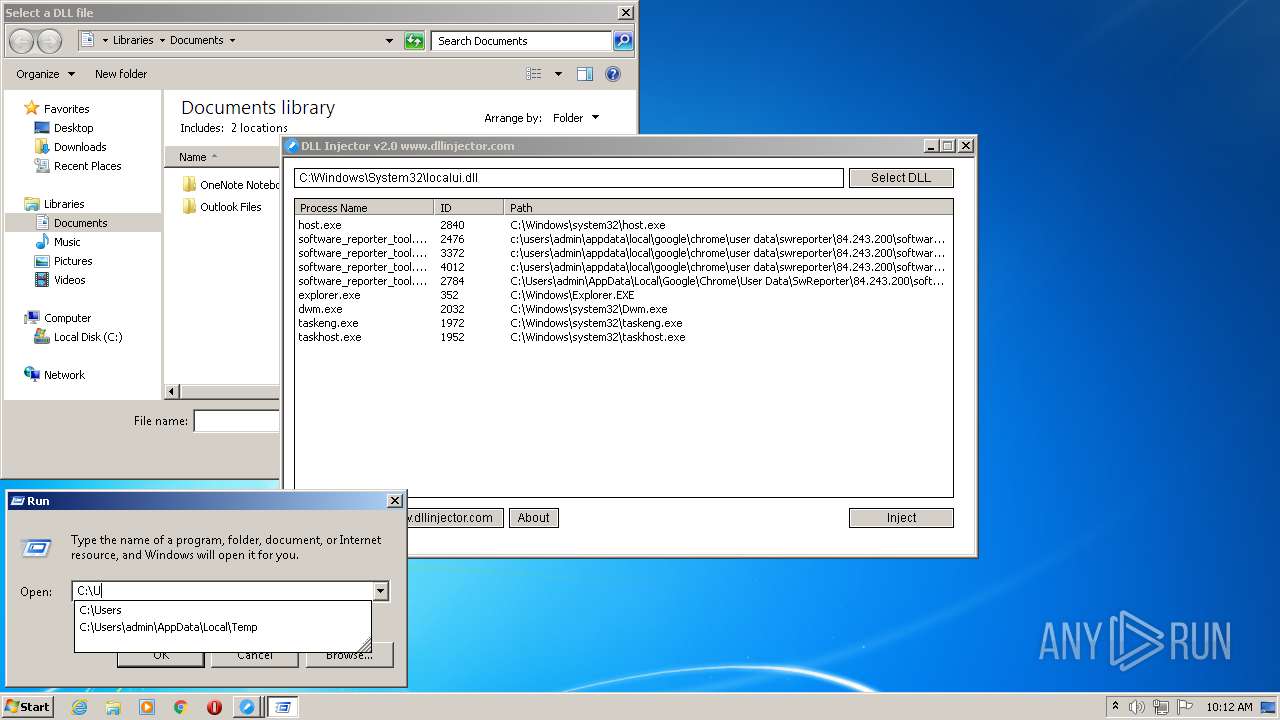
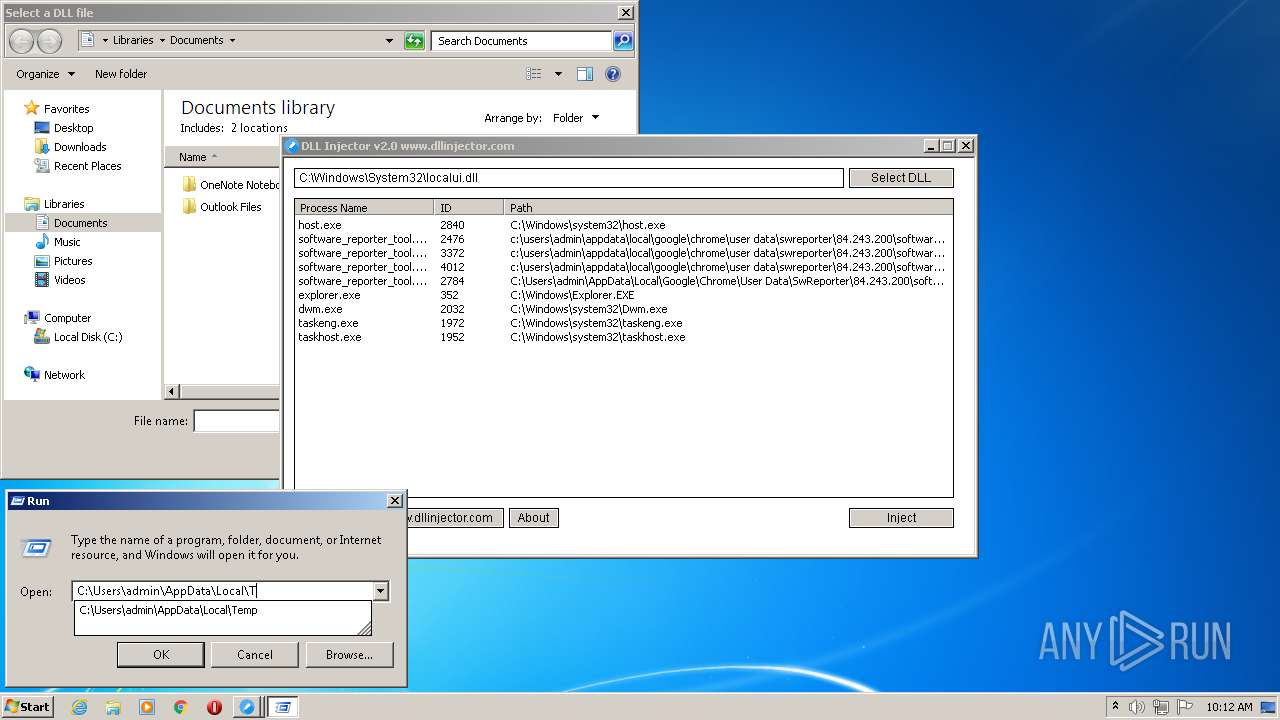
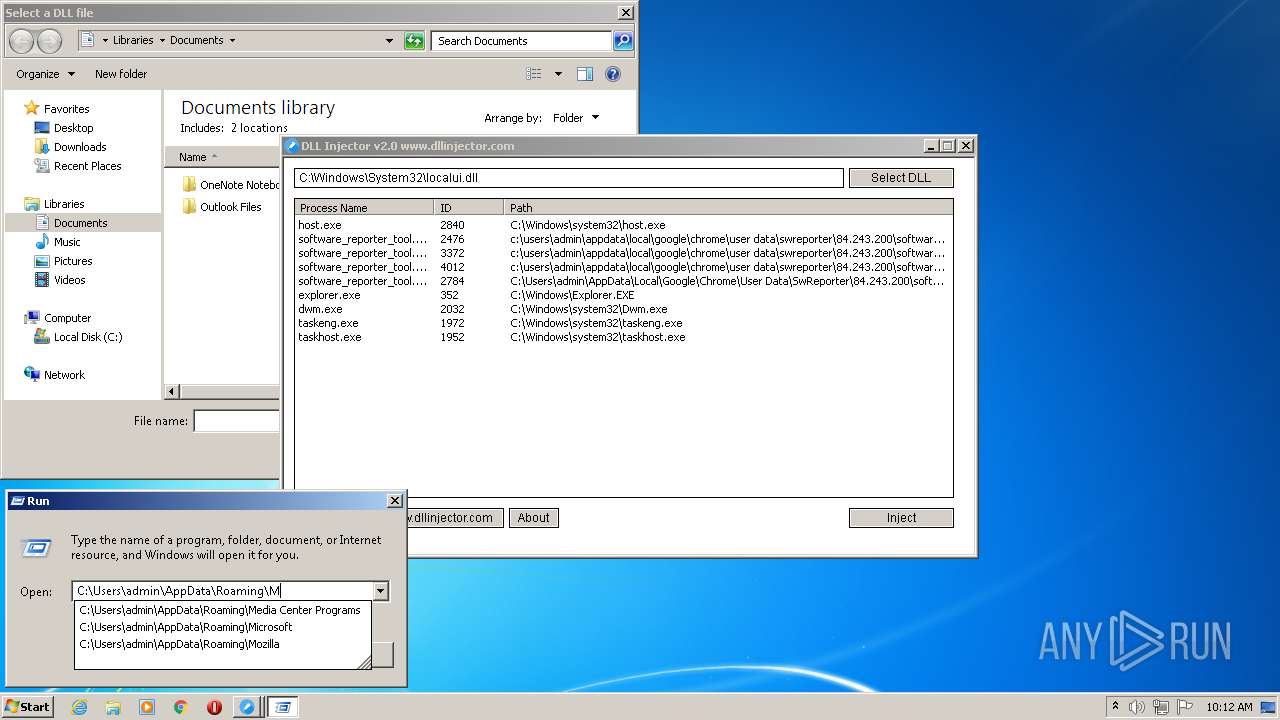
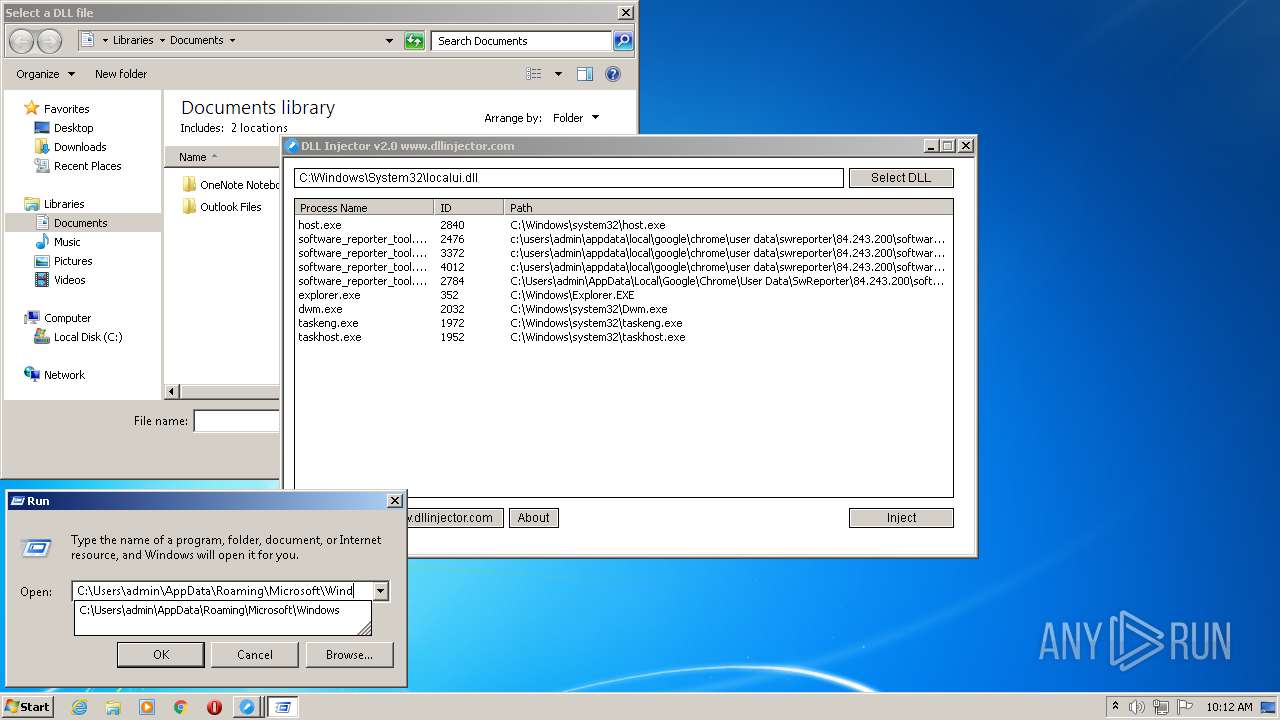
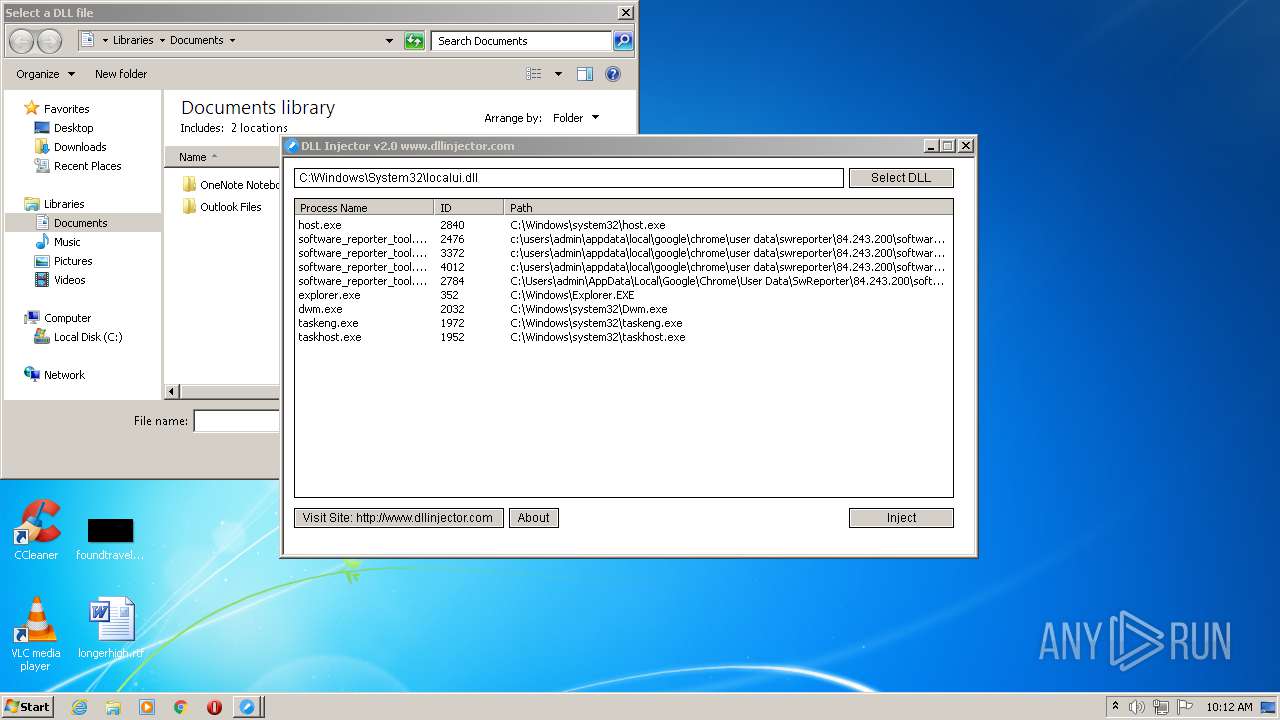
Runs injected code in another process
- dllinjector.exe (PID: 2848)
Application was injected by another process
- explorer.exe (PID: 352)
SUSPICIOUS
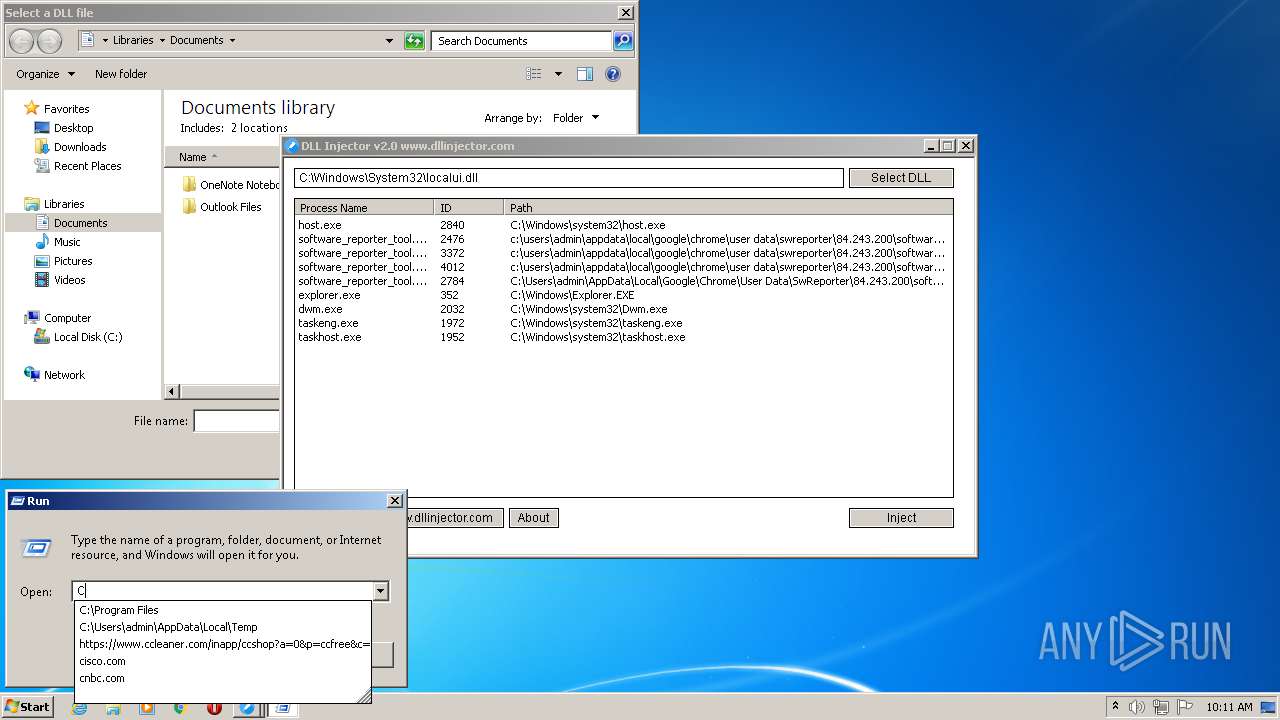
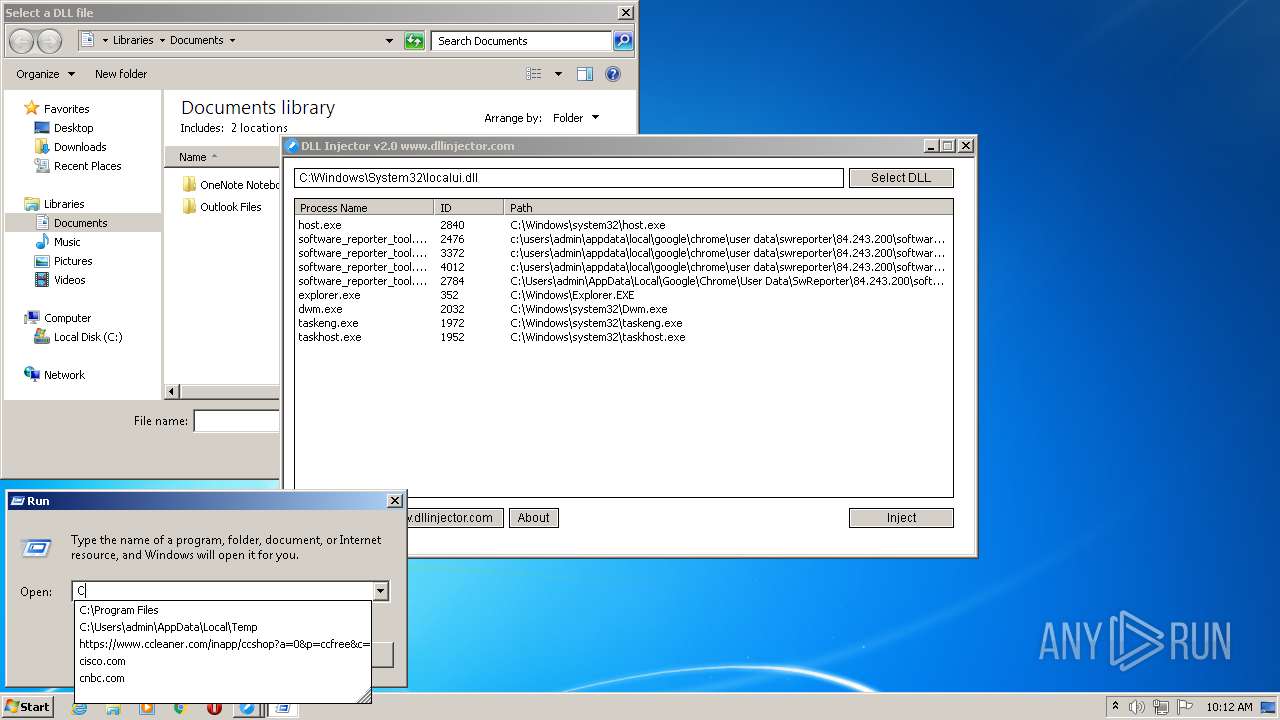
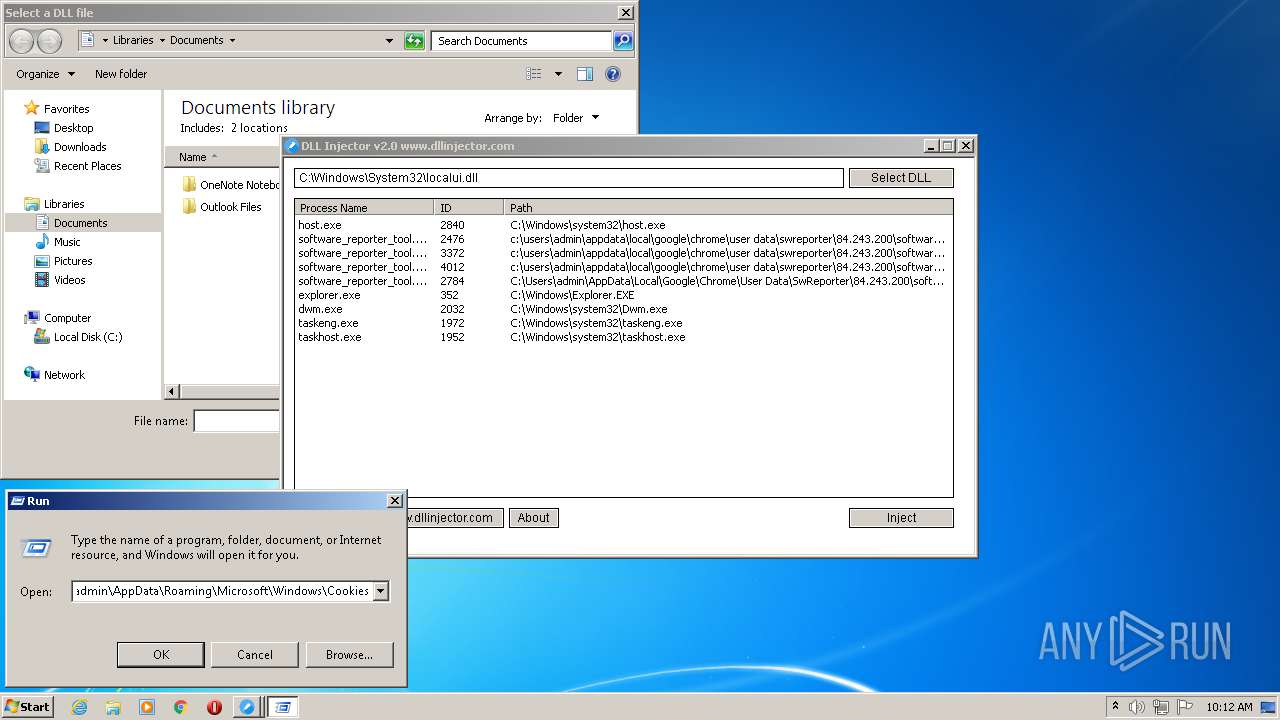
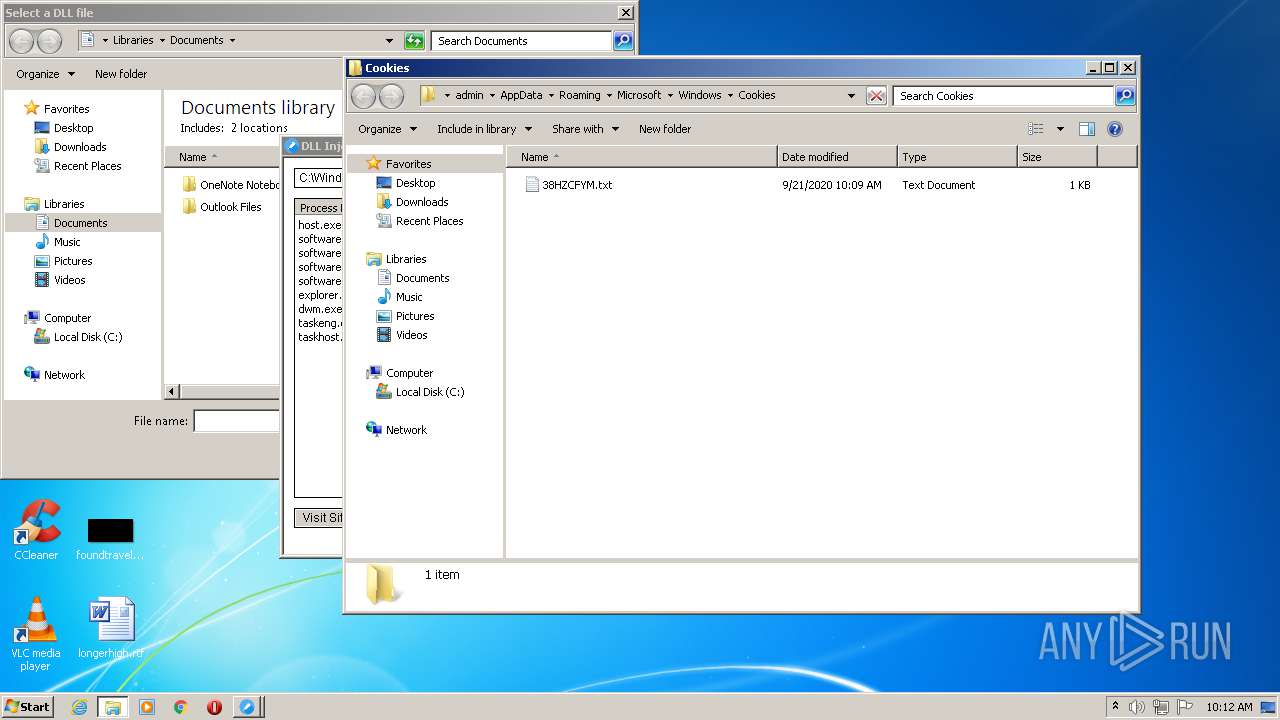
Reads Internet Cache Settings
- dllinjector.exe (PID: 2848)
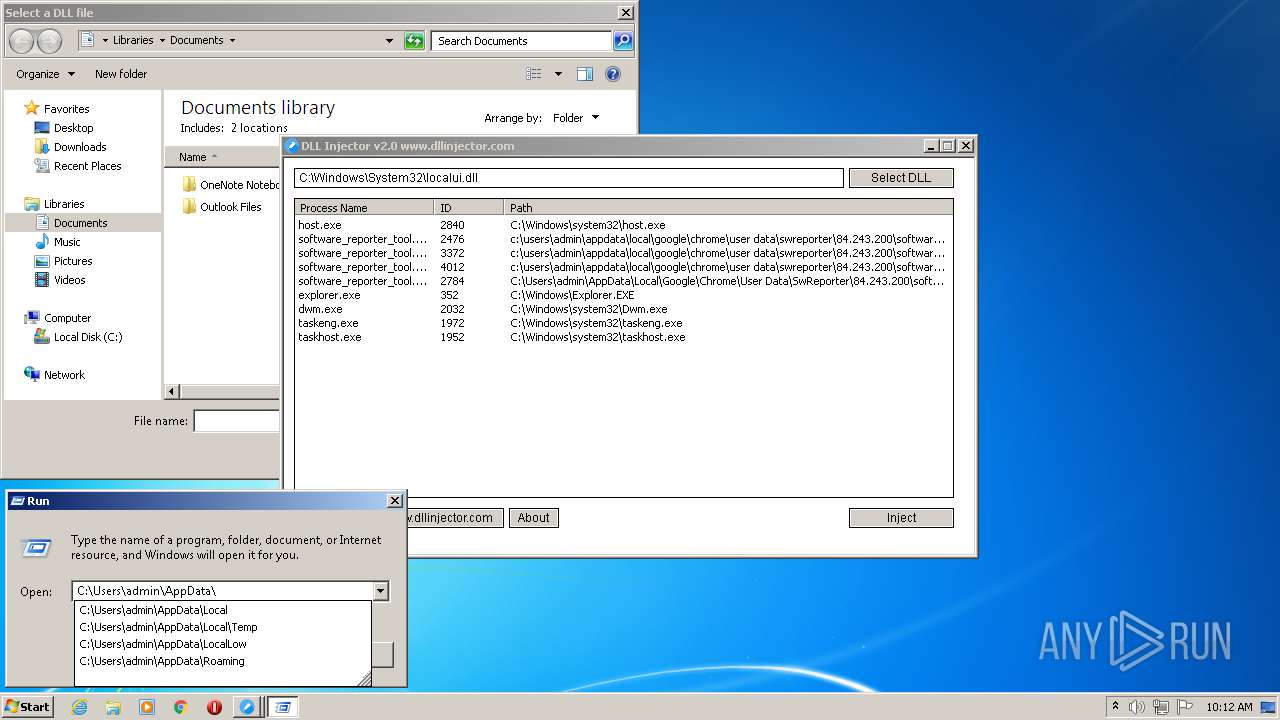
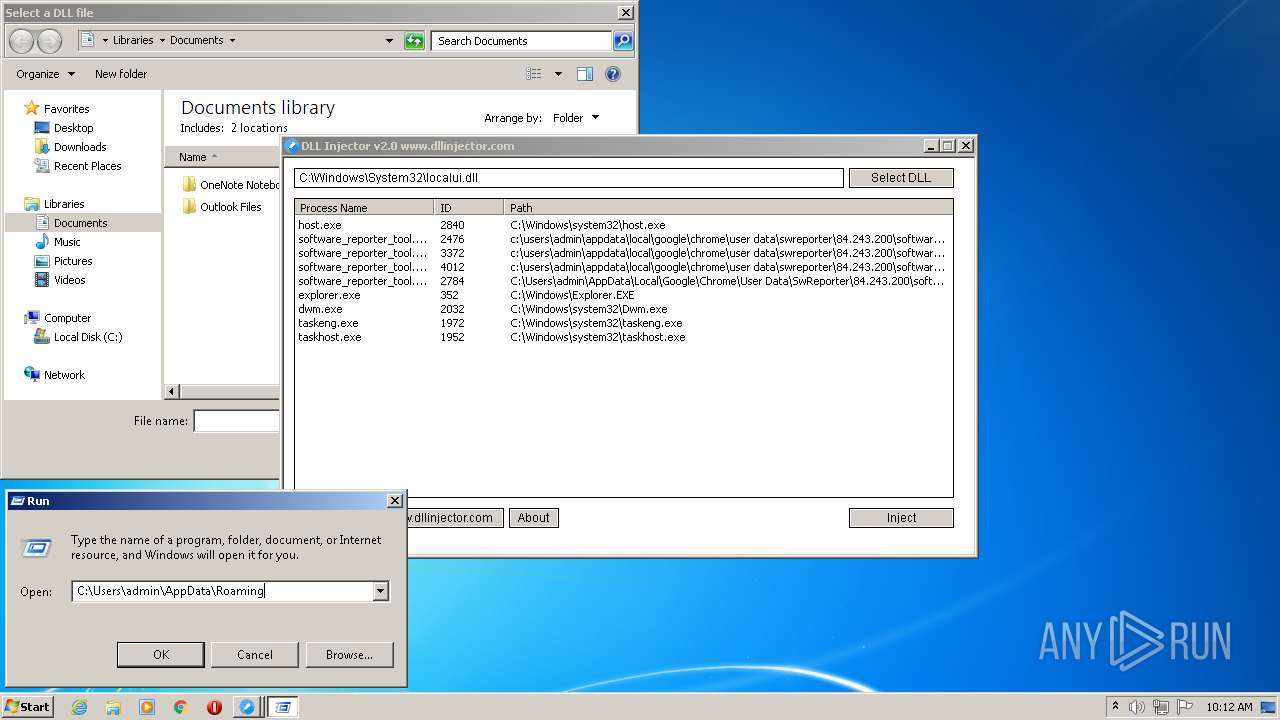
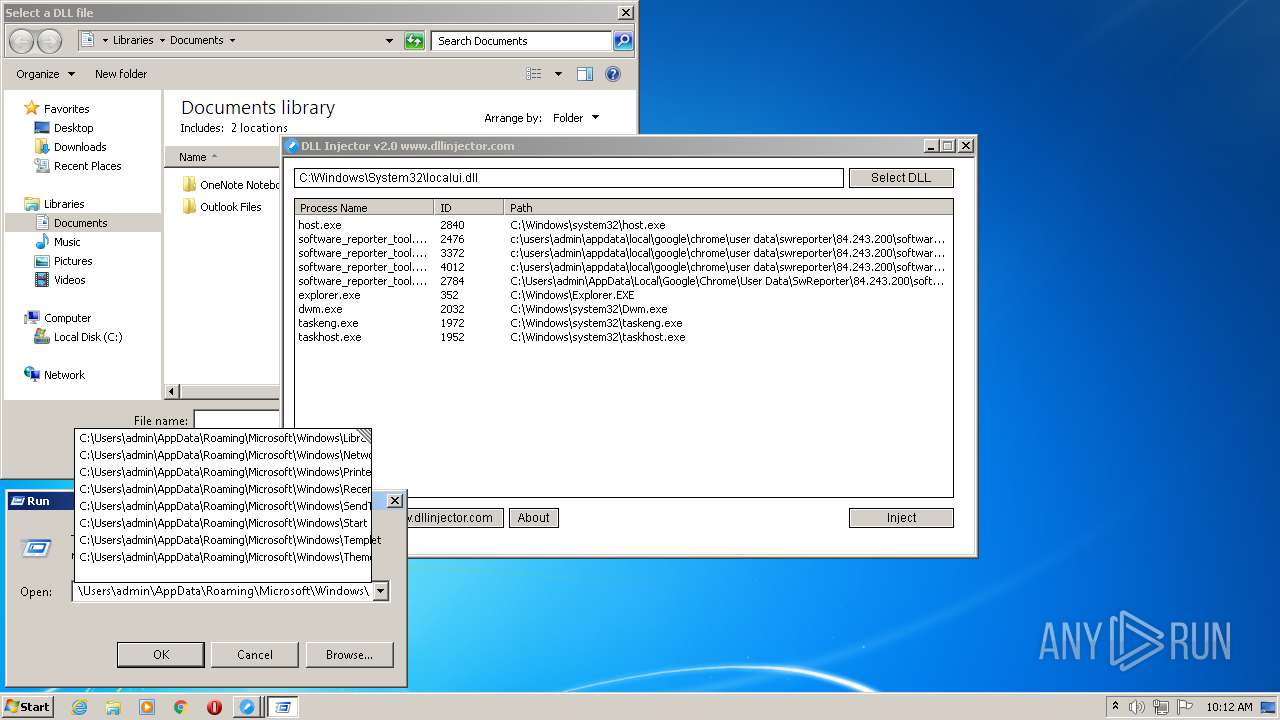
Creates files in the user directory
- explorer.exe (PID: 352)
- dllinjector.exe (PID: 2848)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:12:05 17:41:44+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 441344 |
| InitializedDataSize: | 208896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x34aff |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Dutch |
| CharacterSet: | Unicode |
| CompanyName: | AN Soft |
| FileDescription: | DLL Injector |
| FileVersion: | 2.0.0.0 |
| InternalName: | DLL Injector |
| LegalCopyright: | Copyright (C) 2017 |
| OriginalFileName: | DLLInjector.exe |
| ProductName: | DLL Injector |
| ProductVersion: | 2.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2017 16:41:44 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | AN Soft |
| FileDescription: | DLL Injector |
| FileVersion: | 2.0.0.0 |
| InternalName: | DLL Injector |
| LegalCopyright: | Copyright (C) 2017 |
| OriginalFilename: | DLLInjector.exe |
| ProductName: | DLL Injector |
| ProductVersion: | 2.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 05-Dec-2017 16:41:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006BB44 | 0x0006BC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58395 |
.rdata | 0x0006D000 | 0x00021B12 | 0x00021C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.88613 |
.data | 0x0008F000 | 0x00003B90 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.50858 |
.gfids | 0x00093000 | 0x00000AF4 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.66083 |
.tls | 0x00094000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00095000 | 0x00006C28 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.40942 |
.reloc | 0x0009C000 | 0x00005A28 | 0x00005C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59059 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
101 | 2.01924 | 20 | UNKNOWN | Dutch - Netherlands | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
urlmon.dll |
Total processes
41
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
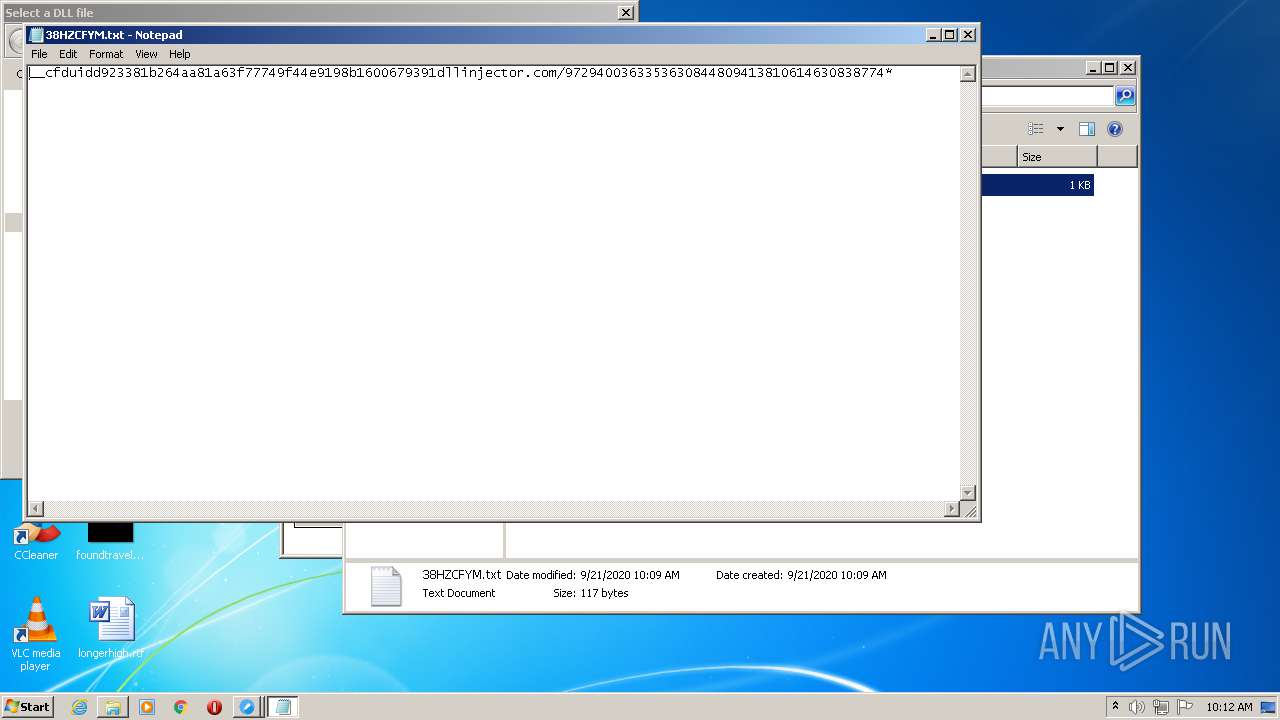
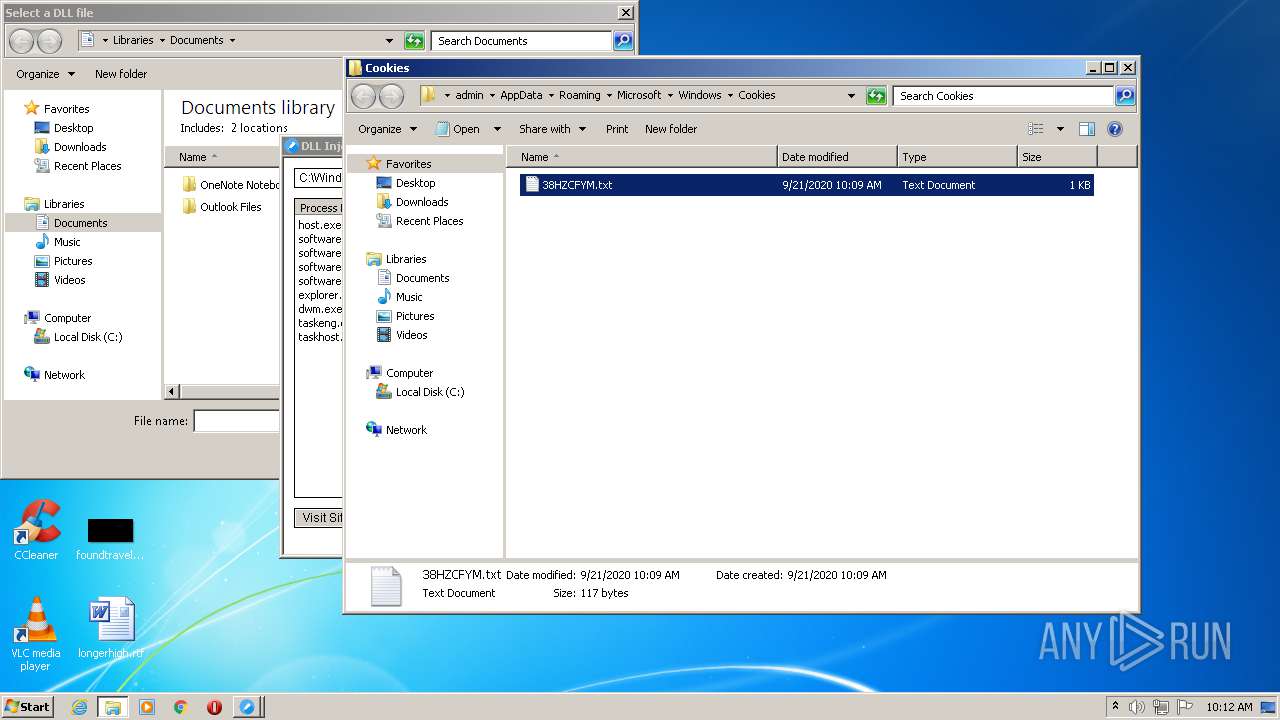
| 1852 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\38HZCFYM.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\AppData\Local\Temp\dllinjector.exe" | C:\Users\admin\AppData\Local\Temp\dllinjector.exe | explorer.exe | ||||||||||||
User: admin Company: AN Soft Integrity Level: MEDIUM Description: DLL Injector Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
Total events
1 673
Read events
1 243
Write events
429
Delete events
1
Modification events
| (PID) Process: | (2848) dllinjector.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2848) dllinjector.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2848) dllinjector.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2848) dllinjector.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2848) dllinjector.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2848) dllinjector.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2848) dllinjector.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2848) dllinjector.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\qyyvawrpgbe.rkr |
Value: 0000000000000000000000001B3A0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
Executable files
0
Suspicious files
6
Text files
3
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | dllinjector.exe | C:\Users\admin\AppData\Local\Temp\Cab77BB.tmp | — | |
MD5:— | SHA256:— | |||
| 2848 | dllinjector.exe | C:\Users\admin\AppData\Local\Temp\Tar77BC.tmp | — | |
MD5:— | SHA256:— | |||
| 2848 | dllinjector.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2848 | dllinjector.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_3ECDE3CFB6938F2BEA92AAAE60EC0B5A | binary | |
MD5:— | SHA256:— | |||
| 2848 | dllinjector.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_3ECDE3CFB6938F2BEA92AAAE60EC0B5A | der | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2848 | dllinjector.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\38HZCFYM.txt | text | |
MD5:— | SHA256:— | |||
| 2848 | dllinjector.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\Cookies.lnk | lnk | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\918e0ecb43d17e23.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2848 | dllinjector.exe | GET | 301 | 104.24.117.171:80 | http://www.dllinjector.com/readweb.php?version=2.0 | US | — | — | malicious |
2848 | dllinjector.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAeh%2FHn1ub9tugazxS8uYVA%3D | US | der | 279 b | whitelisted |
2848 | dllinjector.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2848 | dllinjector.exe | 104.24.117.171:443 | www.dllinjector.com | Cloudflare Inc | US | shared |
2848 | dllinjector.exe | 104.24.117.171:80 | www.dllinjector.com | Cloudflare Inc | US | shared |
2848 | dllinjector.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dllinjector.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
dllinjector.exe | Created folder |