| File name: | DLL Injector Latest Version.exe |
| Full analysis: | https://app.any.run/tasks/2bf403ed-4d72-42d5-aebb-881bd4e96218 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 13:02:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0A5A1030BEBA8CBA4F283A0636231EE1 |
| SHA1: | EFCD77F4FEA4D5CFEC707F9EE936E027B92BB696 |
| SHA256: | 0DB7DDDD89FC145AB250C69C543A0B0CCC5BCE53D017F2FAF63D9A115A011D26 |
| SSDEEP: | 12288:fGDVJ1jU/DhZDkadDoDVMzQZxa4ioGYRWeyc9u/WC/Wd/5A4LGdHnHp9SdpADUk:fgZWuxa4xGdeyc9VC/Wd5LGhnHmdpADR |
MALICIOUS
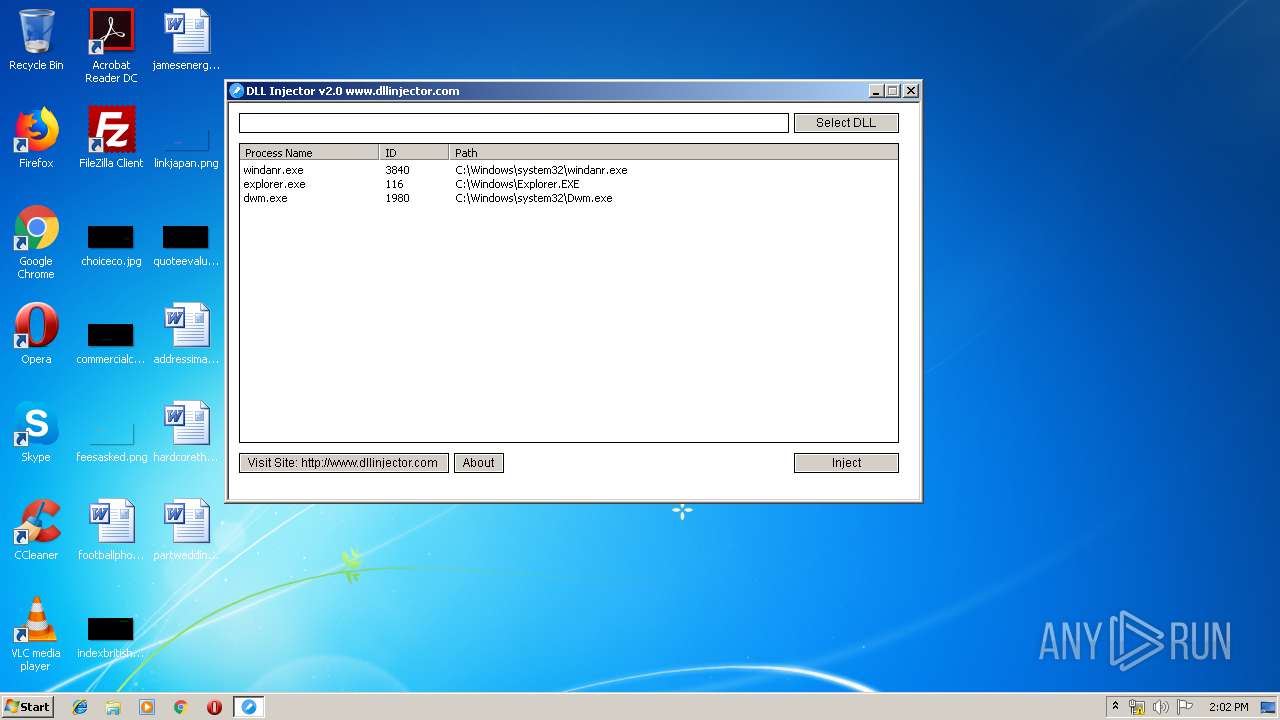
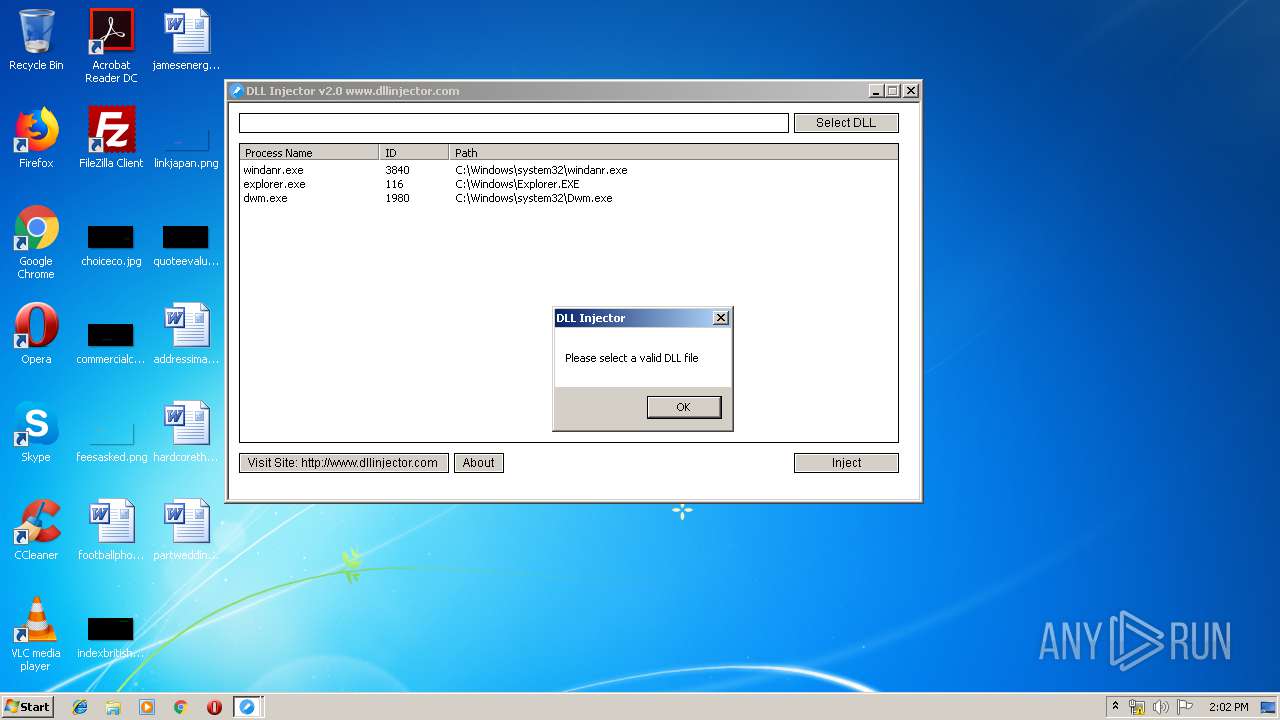
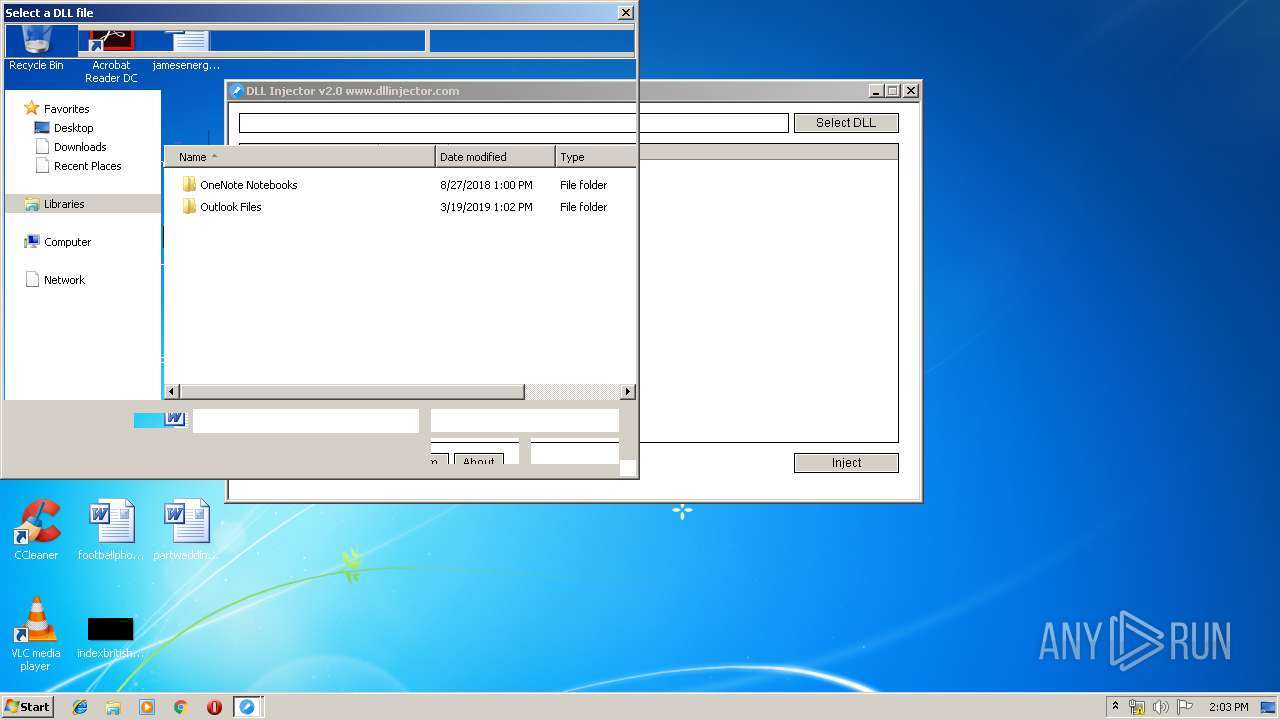
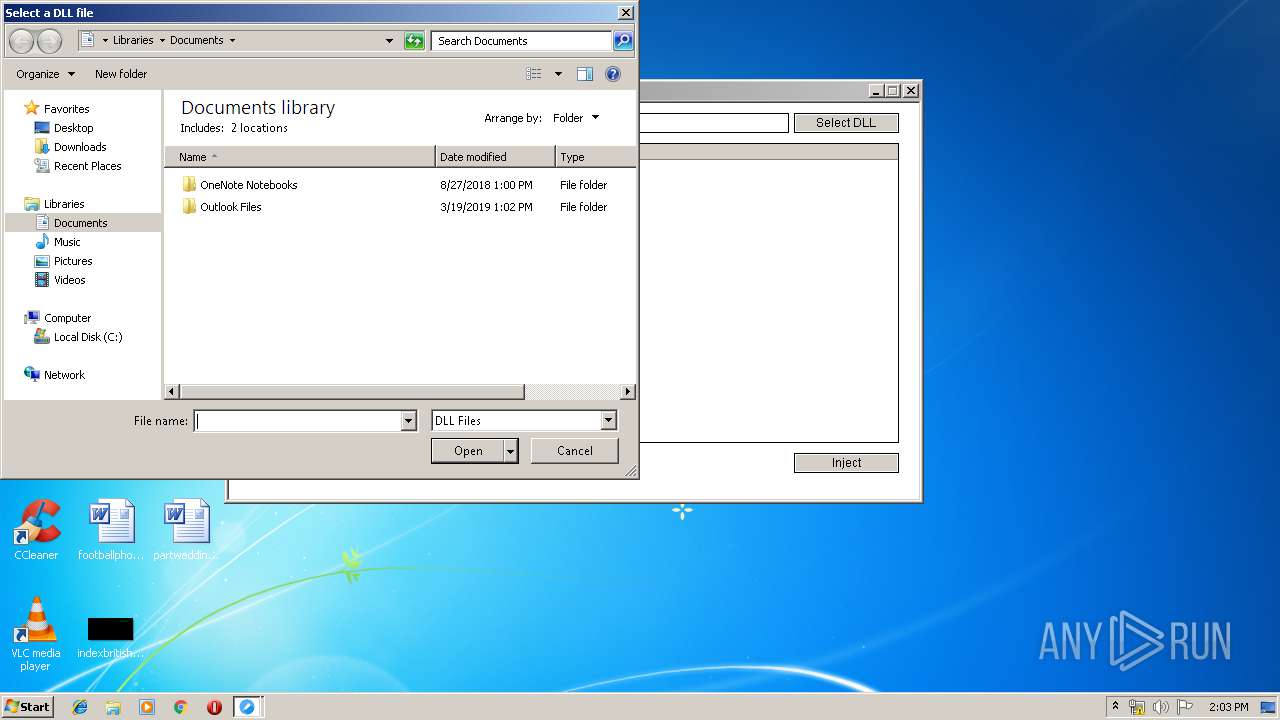
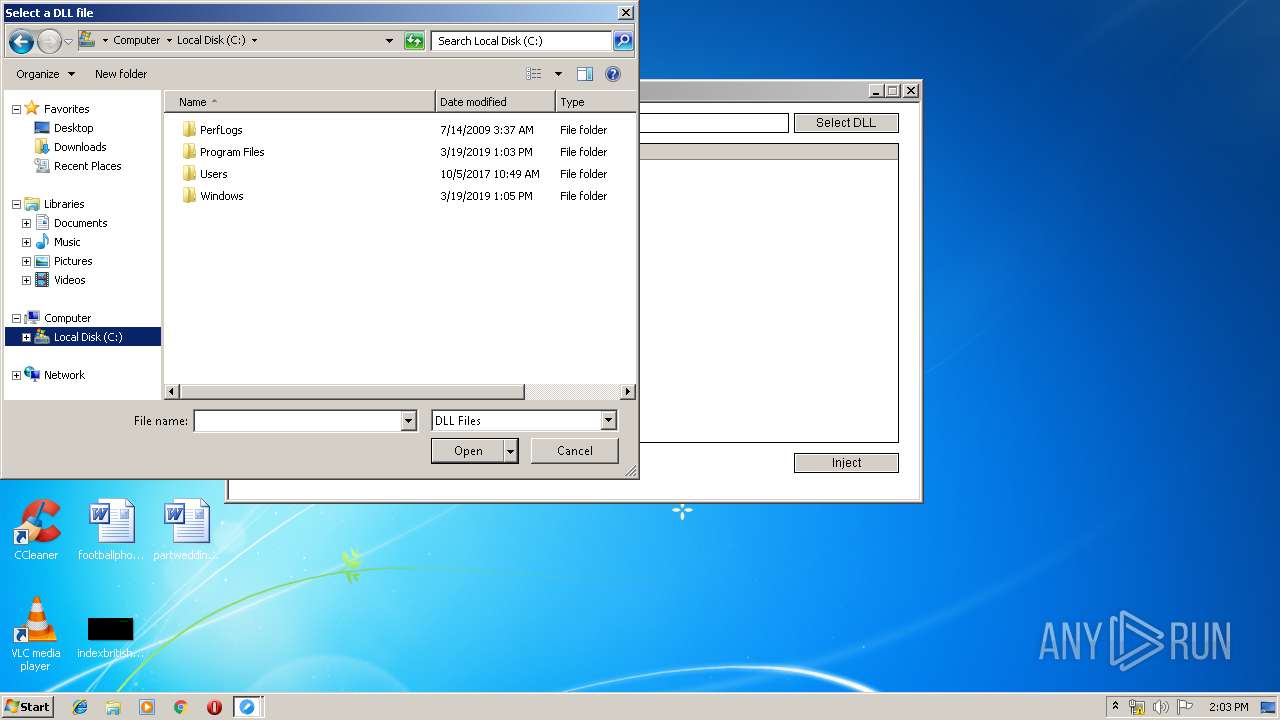
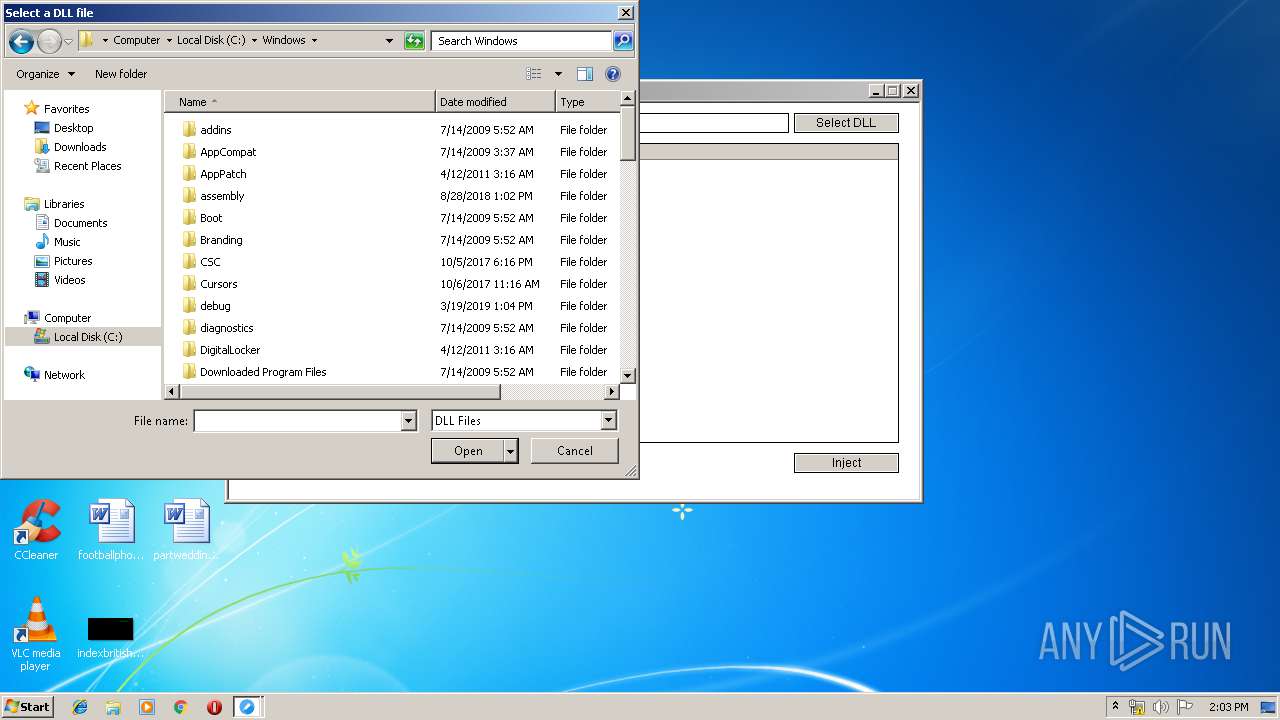
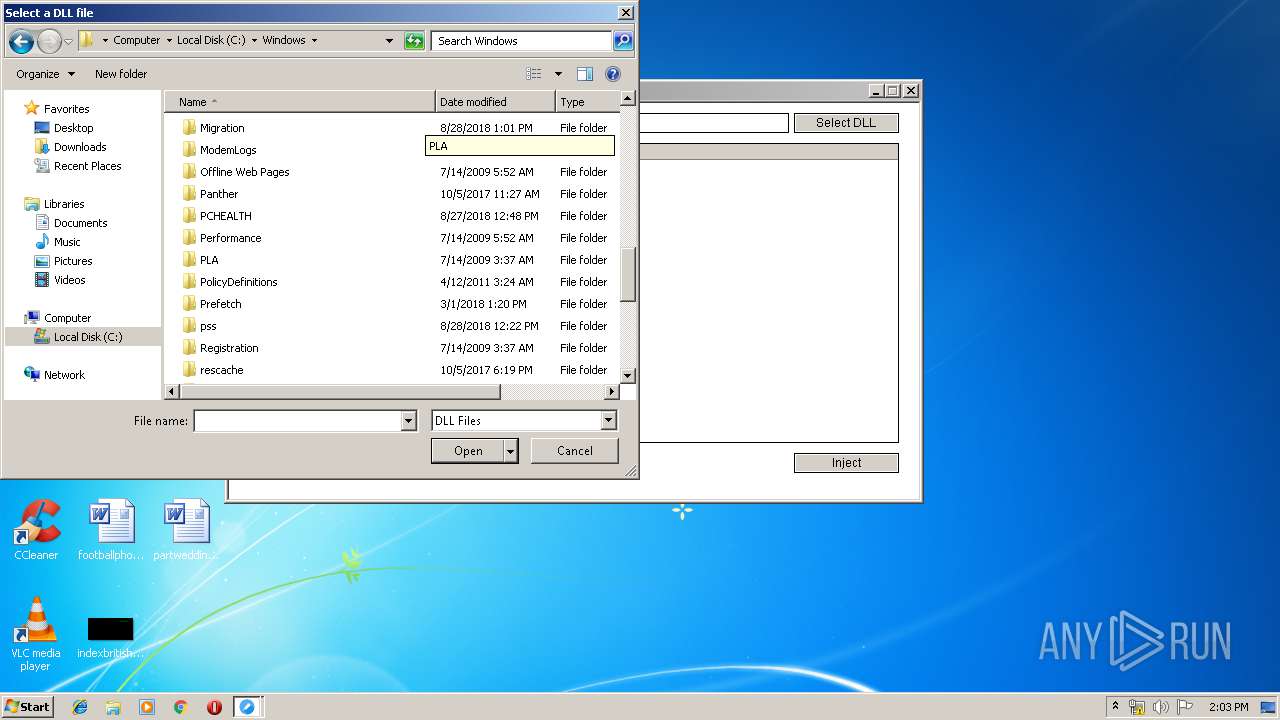
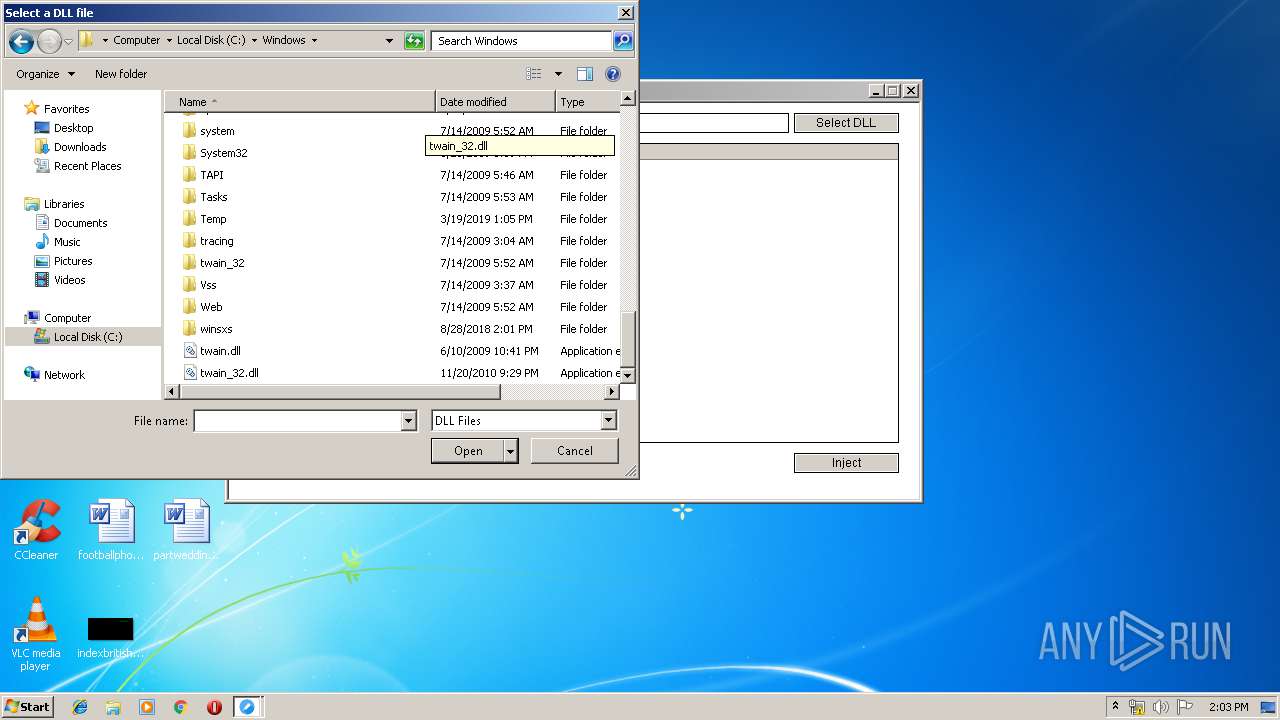
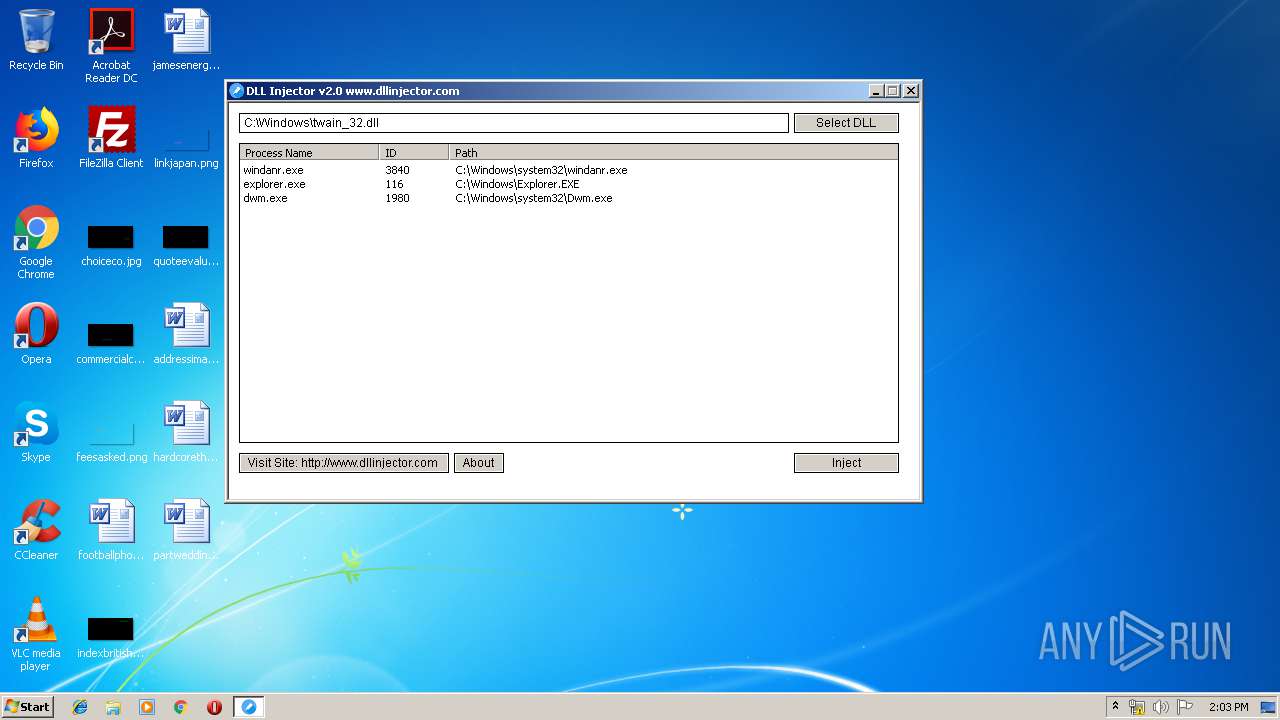
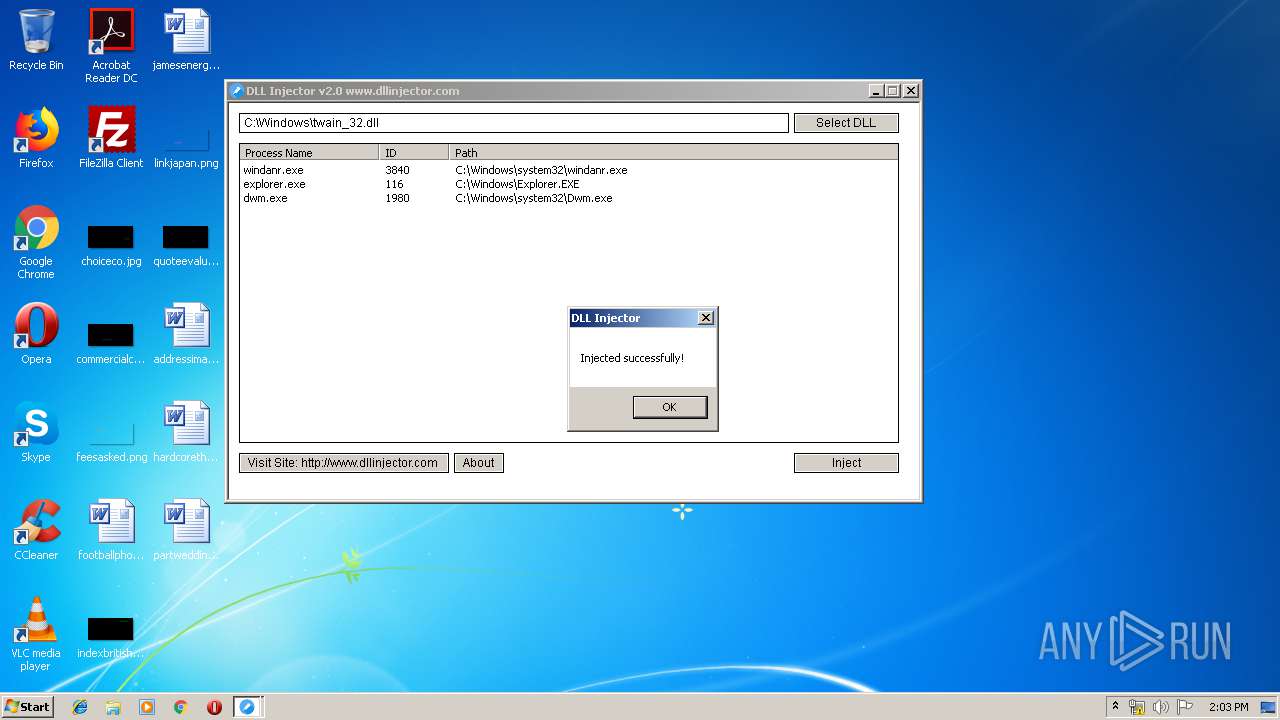
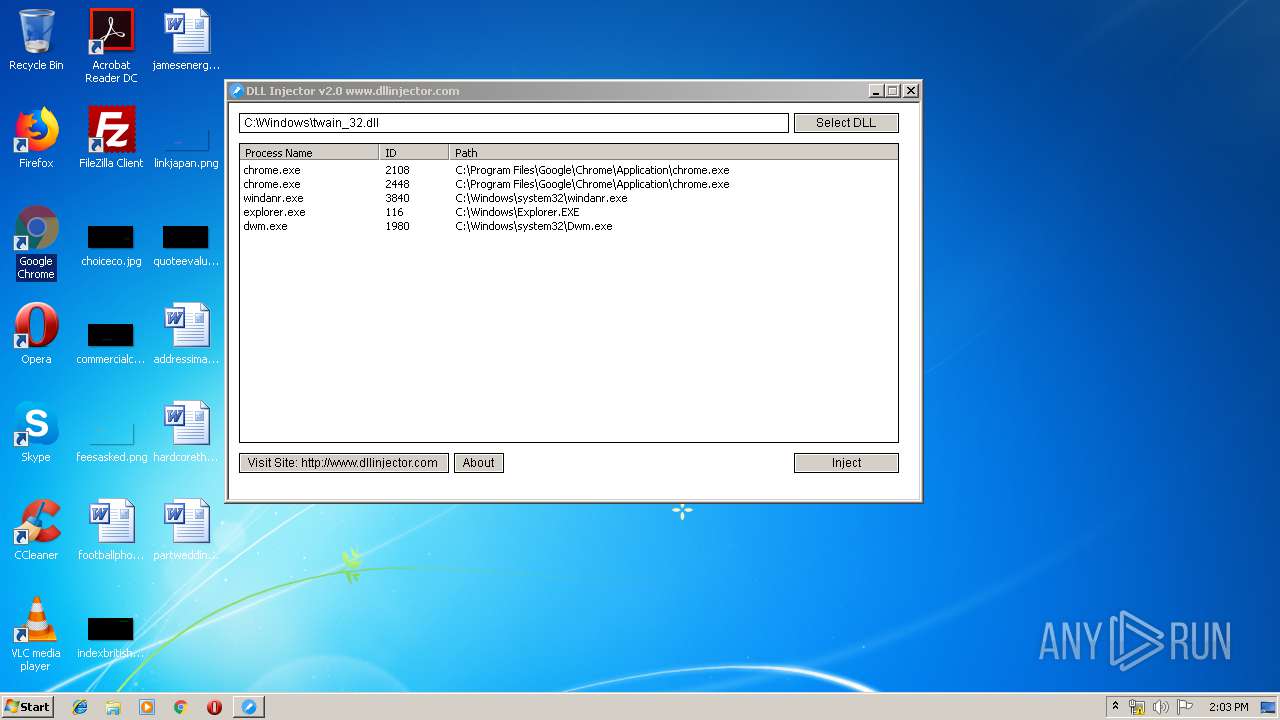
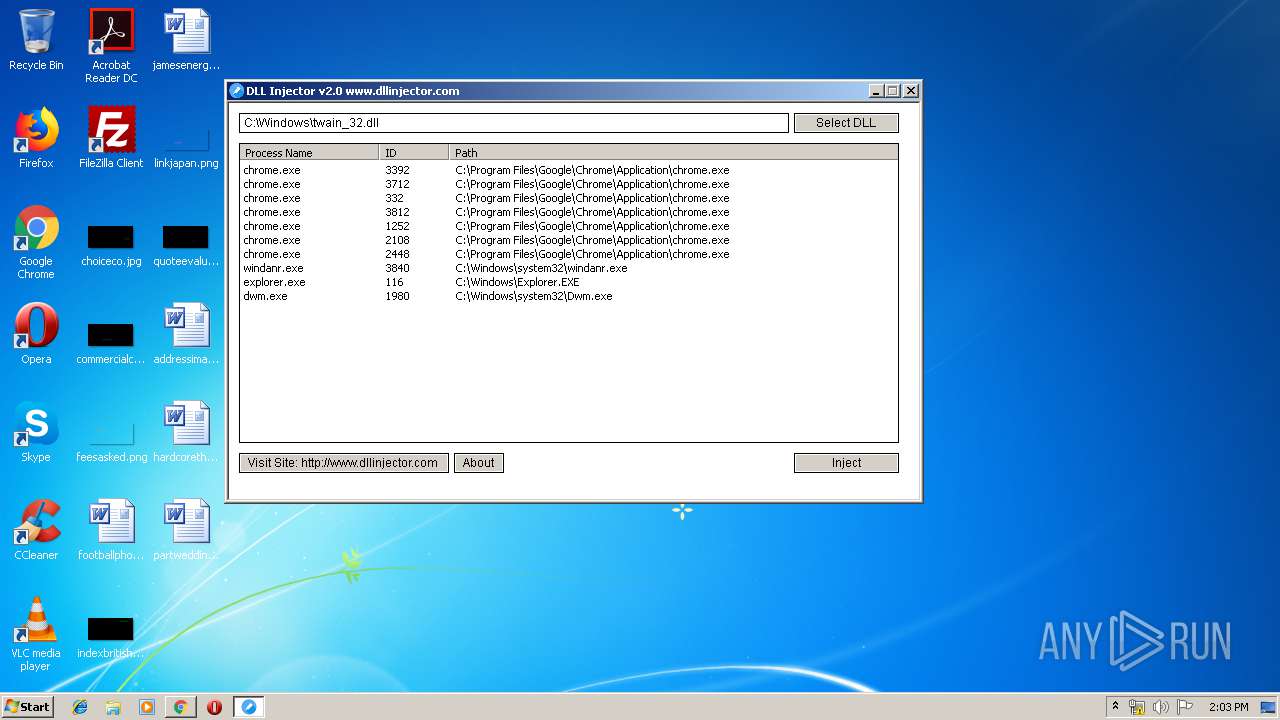
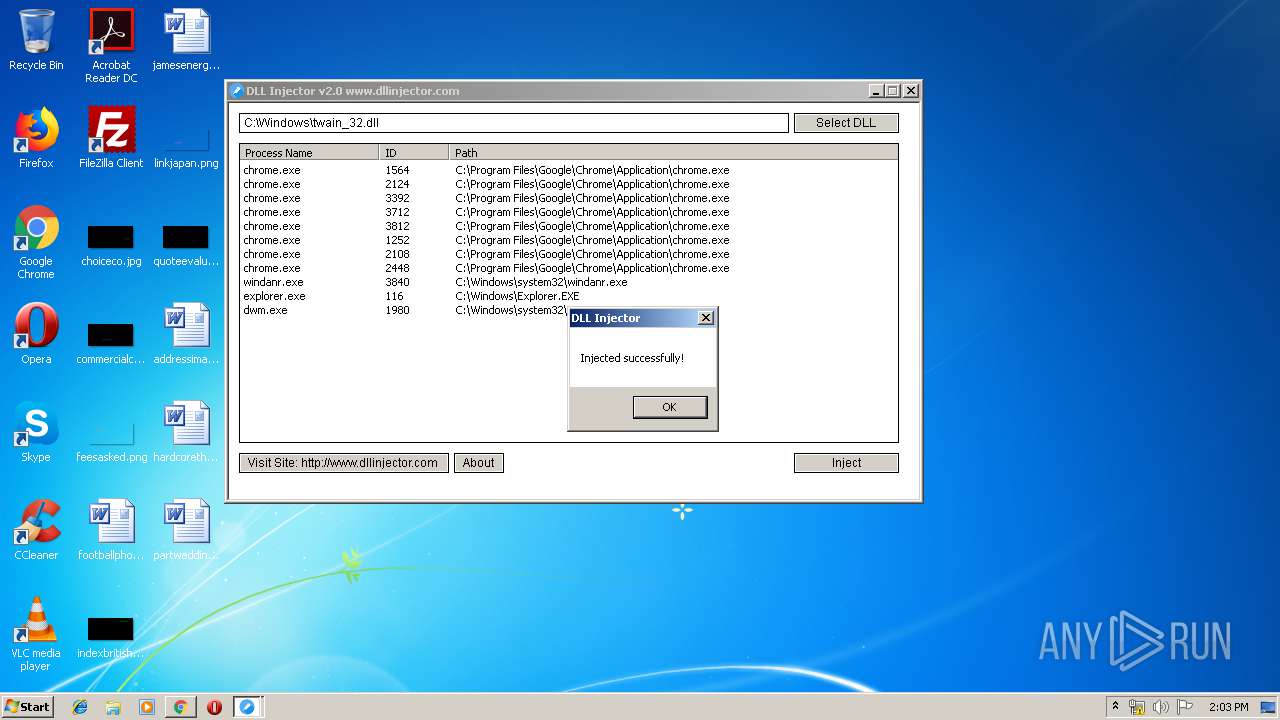
Runs injected code in another process
- DLL Injector Latest Version.exe (PID: 1516)
Application was injected by another process
- windanr.exe (PID: 3840)
SUSPICIOUS
Creates files in the user directory
- DLL Injector Latest Version.exe (PID: 1516)
INFO
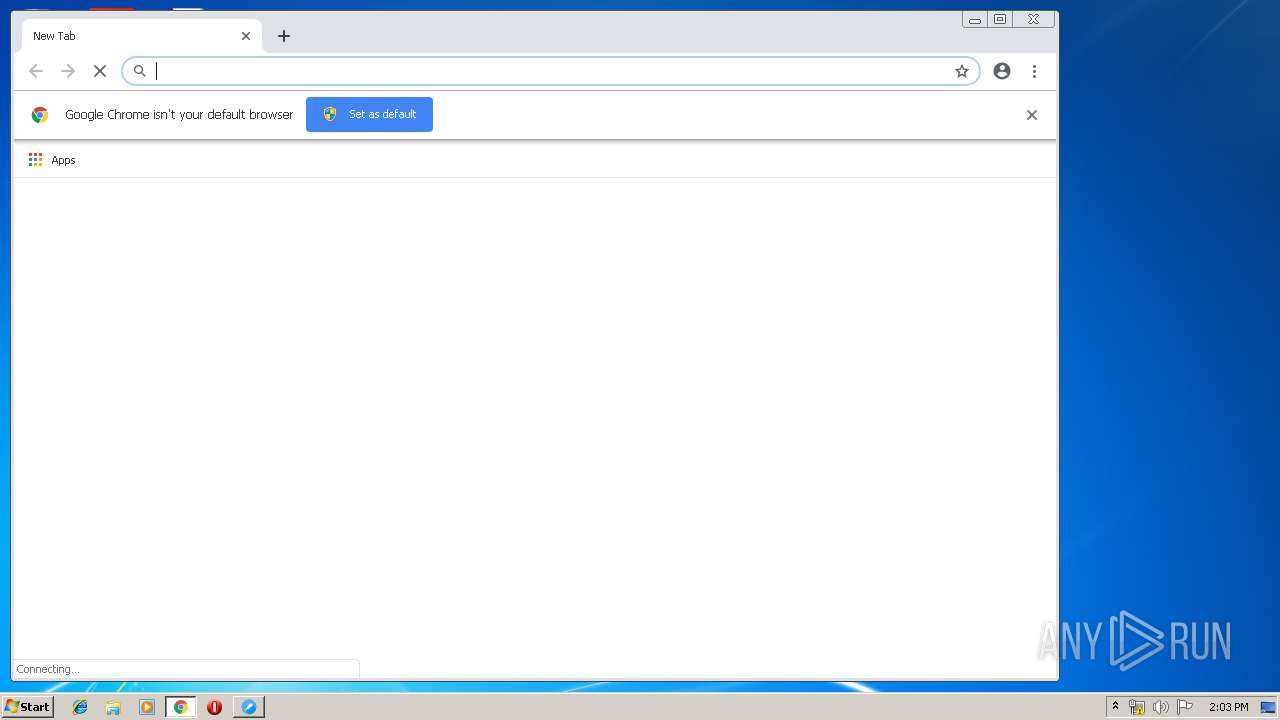
Application launched itself
- chrome.exe (PID: 2448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:12:05 17:41:44+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 441344 |
| InitializedDataSize: | 208896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x34aff |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Dutch |
| CharacterSet: | Unicode |
| CompanyName: | AN Soft |
| FileDescription: | DLL Injector |
| FileVersion: | 2.0.0.0 |
| InternalName: | DLL Injector |
| LegalCopyright: | Copyright (C) 2017 |
| OriginalFileName: | DLLInjector.exe |
| ProductName: | DLL Injector |
| ProductVersion: | 2.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2017 16:41:44 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | AN Soft |
| FileDescription: | DLL Injector |
| FileVersion: | 2.0.0.0 |
| InternalName: | DLL Injector |
| LegalCopyright: | Copyright (C) 2017 |
| OriginalFilename: | DLLInjector.exe |
| ProductName: | DLL Injector |
| ProductVersion: | 2.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 05-Dec-2017 16:41:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006BB44 | 0x0006BC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58395 |
.rdata | 0x0006D000 | 0x00021B12 | 0x00021C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.88613 |
.data | 0x0008F000 | 0x00003B90 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.50858 |
.gfids | 0x00093000 | 0x00000AF4 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.66083 |
.tls | 0x00094000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00095000 | 0x00006C28 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.40942 |
.reloc | 0x0009C000 | 0x00005A28 | 0x00005C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59059 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
101 | 2.01924 | 20 | UNKNOWN | Dutch - Netherlands | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
urlmon.dll |
Total processes
42
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14708445604146329816,9827127192933001447,131072 --enable-features=PasswordImport --service-pipe-token=13722707732322368332 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13722707732322368332 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2460 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1516 | "C:\Users\admin\AppData\Local\Temp\DLL Injector Latest Version.exe" | C:\Users\admin\AppData\Local\Temp\DLL Injector Latest Version.exe | explorer.exe | ||||||||||||
User: admin Company: AN Soft Integrity Level: MEDIUM Description: DLL Injector Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14708445604146329816,9827127192933001447,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2354224306395755820 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2354224306395755820 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f210f18,0x6f210f28,0x6f210f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14708445604146329816,9827127192933001447,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11259699125821166444 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11259699125821166444 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3560 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,14708445604146329816,9827127192933001447,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16307351293146603226 --mojo-platform-channel-handle=4036 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14708445604146329816,9827127192933001447,131072 --enable-features=PasswordImport --service-pipe-token=16993716635775450212 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16993716635775450212 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14708445604146329816,9827127192933001447,131072 --enable-features=PasswordImport --service-pipe-token=486299774380425937 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=486299774380425937 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
860
Read events
702
Write events
154
Delete events
4
Modification events
| (PID) Process: | (1516) DLL Injector Latest Version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DLL Injector Latest Version_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1516) DLL Injector Latest Version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DLL Injector Latest Version_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1516) DLL Injector Latest Version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DLL Injector Latest Version_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1516) DLL Injector Latest Version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DLL Injector Latest Version_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1516) DLL Injector Latest Version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DLL Injector Latest Version_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1516) DLL Injector Latest Version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DLL Injector Latest Version_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1516) DLL Injector Latest Version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DLL Injector Latest Version_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1516) DLL Injector Latest Version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DLL Injector Latest Version_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1516) DLL Injector Latest Version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DLL Injector Latest Version_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1516) DLL Injector Latest Version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DLL Injector Latest Version_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
19
Text files
35
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\eddb414f-f7c2-4c36-ba99-9781b8a00f06.tmp | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
16
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1516 | DLL Injector Latest Version.exe | GET | 301 | 104.24.116.171:80 | http://www.dllinjector.com/readweb.php?version=2.0 | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1516 | DLL Injector Latest Version.exe | 104.24.116.171:80 | www.dllinjector.com | Cloudflare Inc | US | shared |
1516 | DLL Injector Latest Version.exe | 104.24.116.171:443 | www.dllinjector.com | Cloudflare Inc | US | shared |
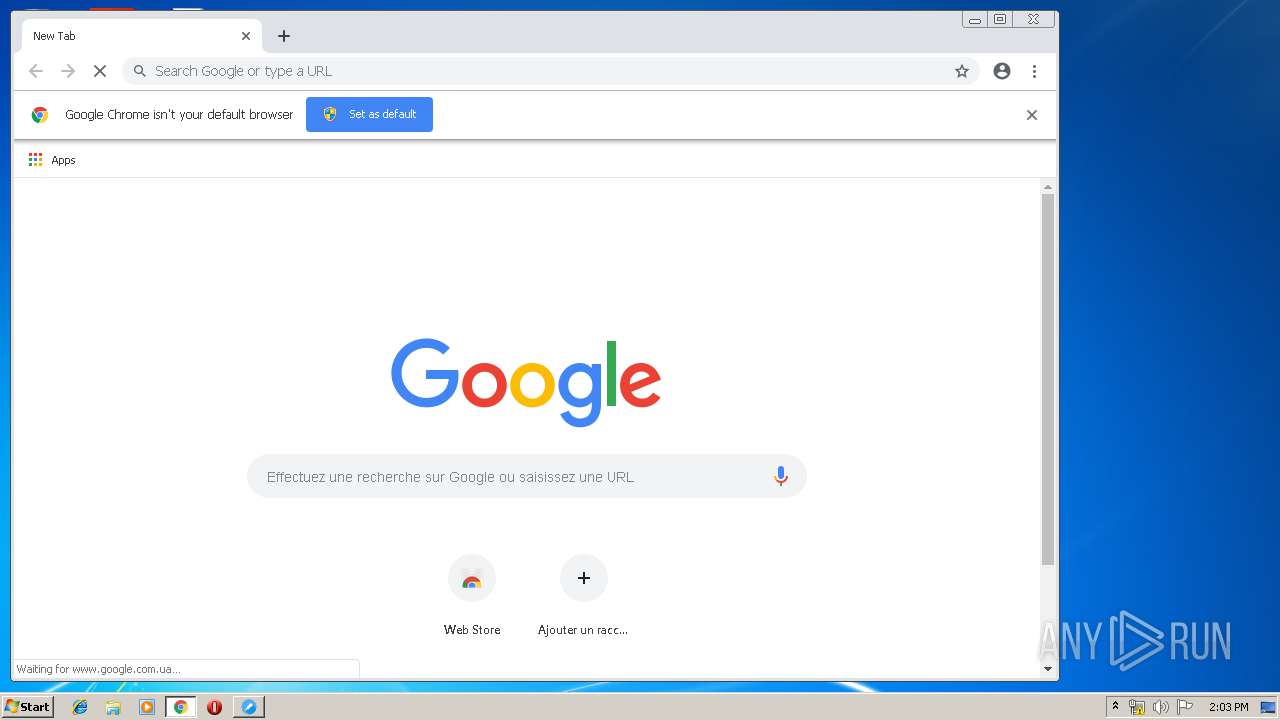
2448 | chrome.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2448 | chrome.exe | 216.58.206.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
2448 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
2448 | chrome.exe | 172.217.21.227:443 | www.google.fr | Google Inc. | US | whitelisted |
2448 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2448 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dllinjector.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
www.google.fr |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
DLL Injector Latest Version.exe | Created folder |