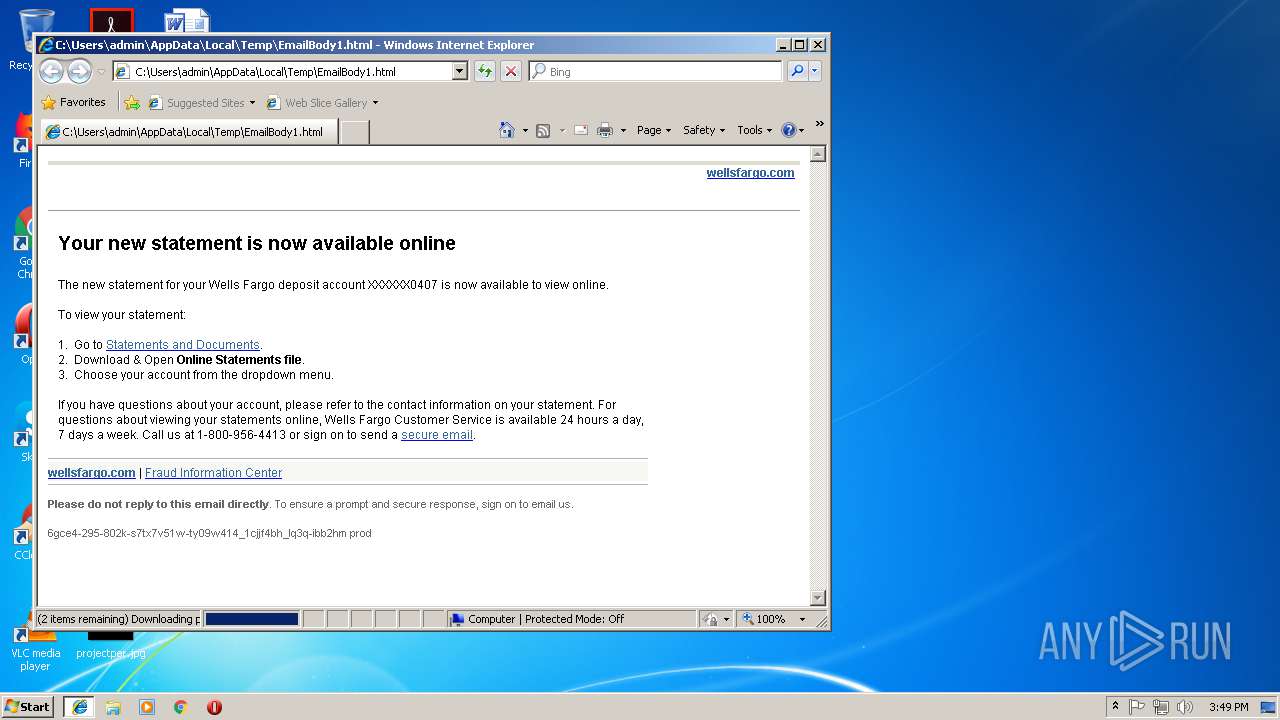
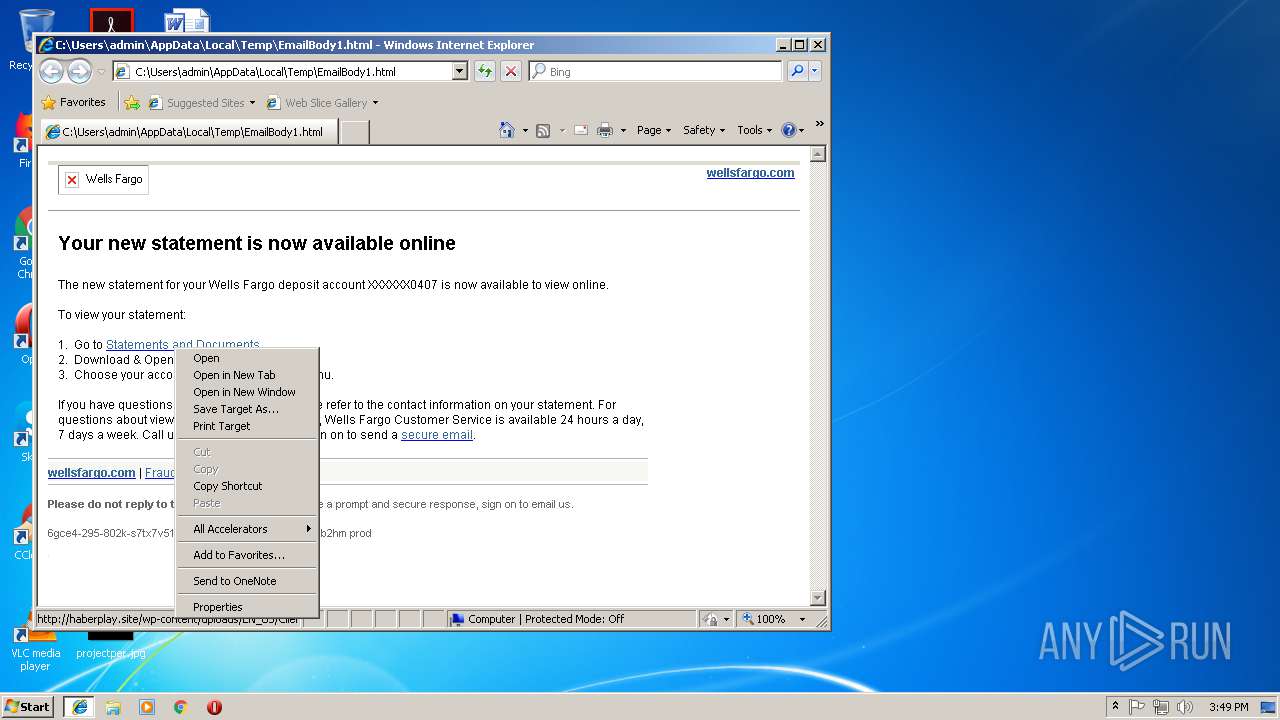
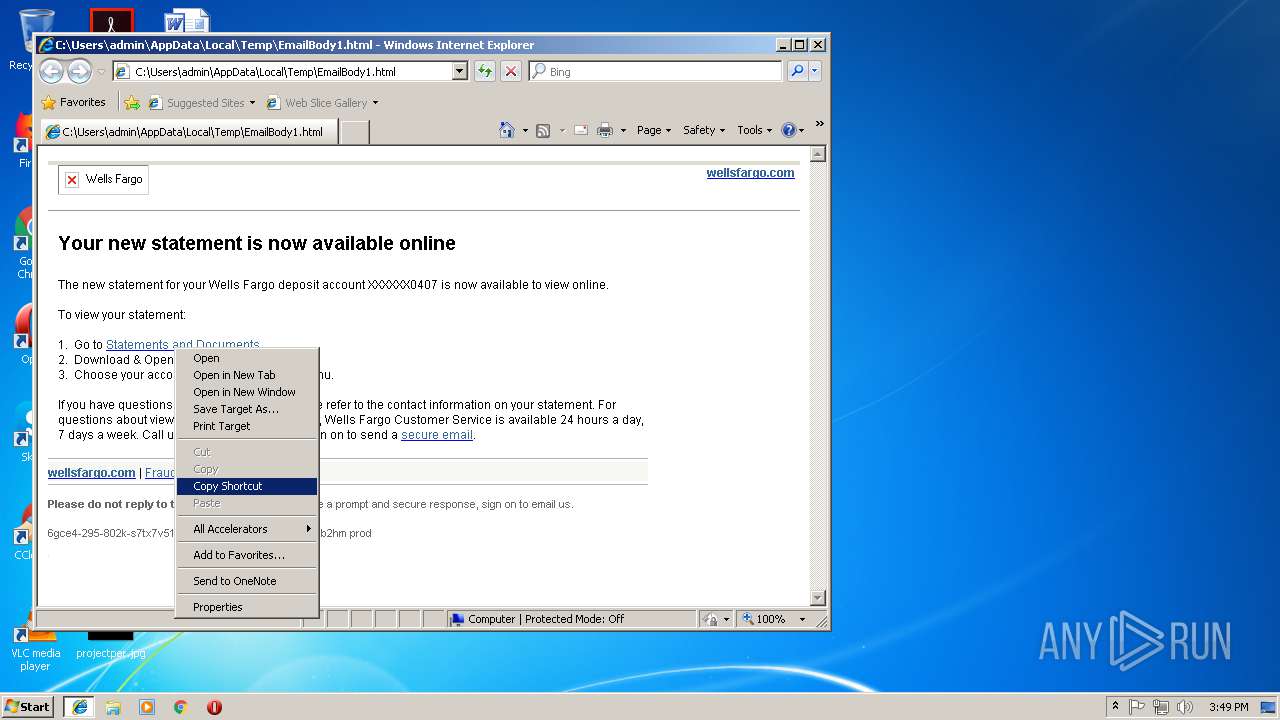
| File name: | EmailBody1.html |
| Full analysis: | https://app.any.run/tasks/1f233e29-c158-4c62-b187-7879148283d7 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2018, 15:48:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text |
| MD5: | F2B514F6672D79762C43BA42C362C4BB |
| SHA1: | 14949FD0570F93D3558683067CB69B86B73BA5E4 |
| SHA256: | 0DAD81A766E060A7E876813B1266052A77CFE6A416E6D1F4D83E9FF8D52D93F0 |
| SSDEEP: | 192:OqofP9g5jhc8anW874lq/EBWbDoVav0xGLNxMF34FIy+nuznlLzRtBfGzGN6dz6N:O6hc8uNiLU5OzNr9i82mM |
MALICIOUS
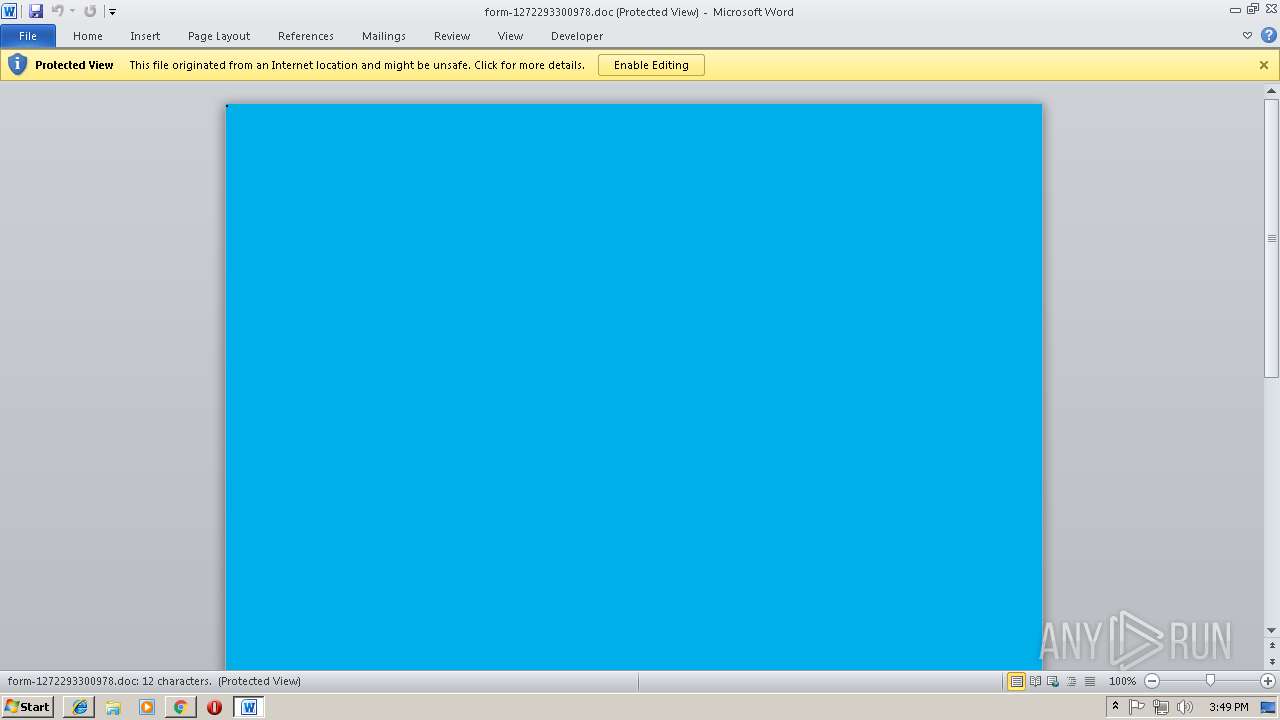
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1148)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 1148)
Application was dropped or rewritten from another process
- 940.exe (PID: 3620)
- 940.exe (PID: 2556)
- lpiograd.exe (PID: 3508)
- lpiograd.exe (PID: 3616)
Emotet process was detected
- lpiograd.exe (PID: 3508)
Downloads executable files from the Internet
- powershell.exe (PID: 3548)
EMOTET was detected
- lpiograd.exe (PID: 3616)
Connects to CnC server
- lpiograd.exe (PID: 3616)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 1148)
- 940.exe (PID: 3620)
- lpiograd.exe (PID: 3508)
Executes PowerShell scripts
- CMD.exe (PID: 3080)
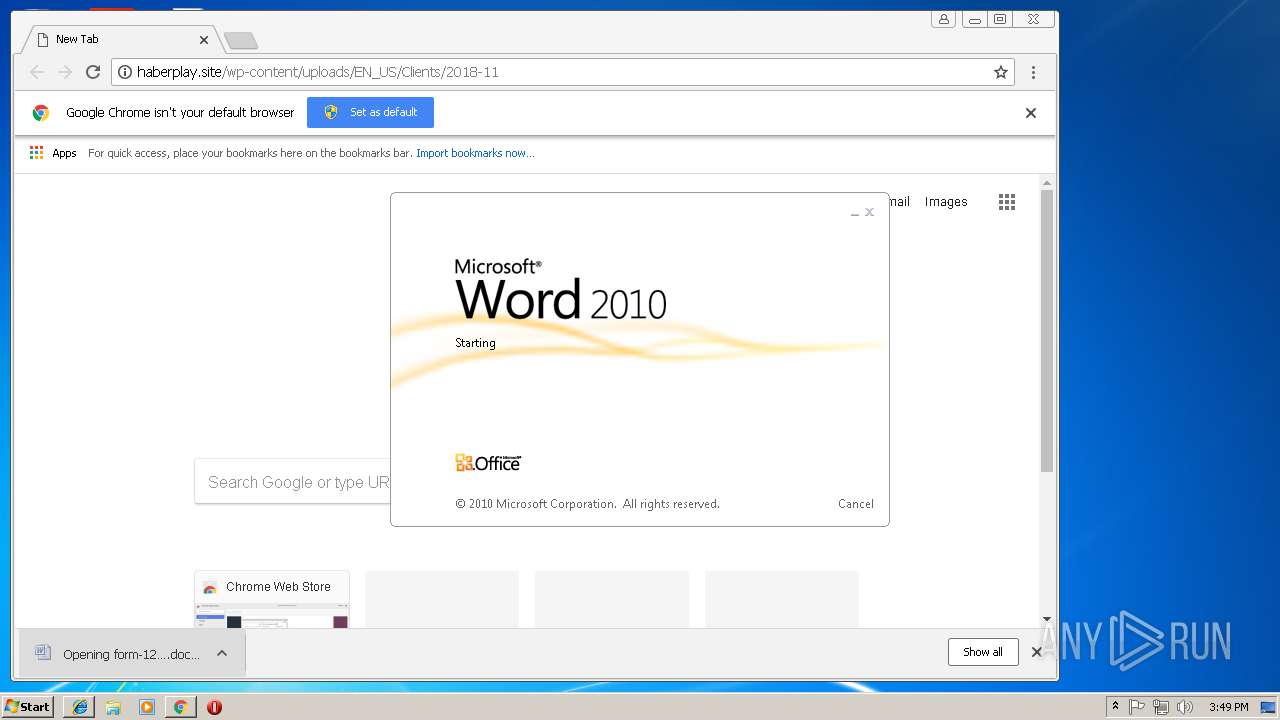
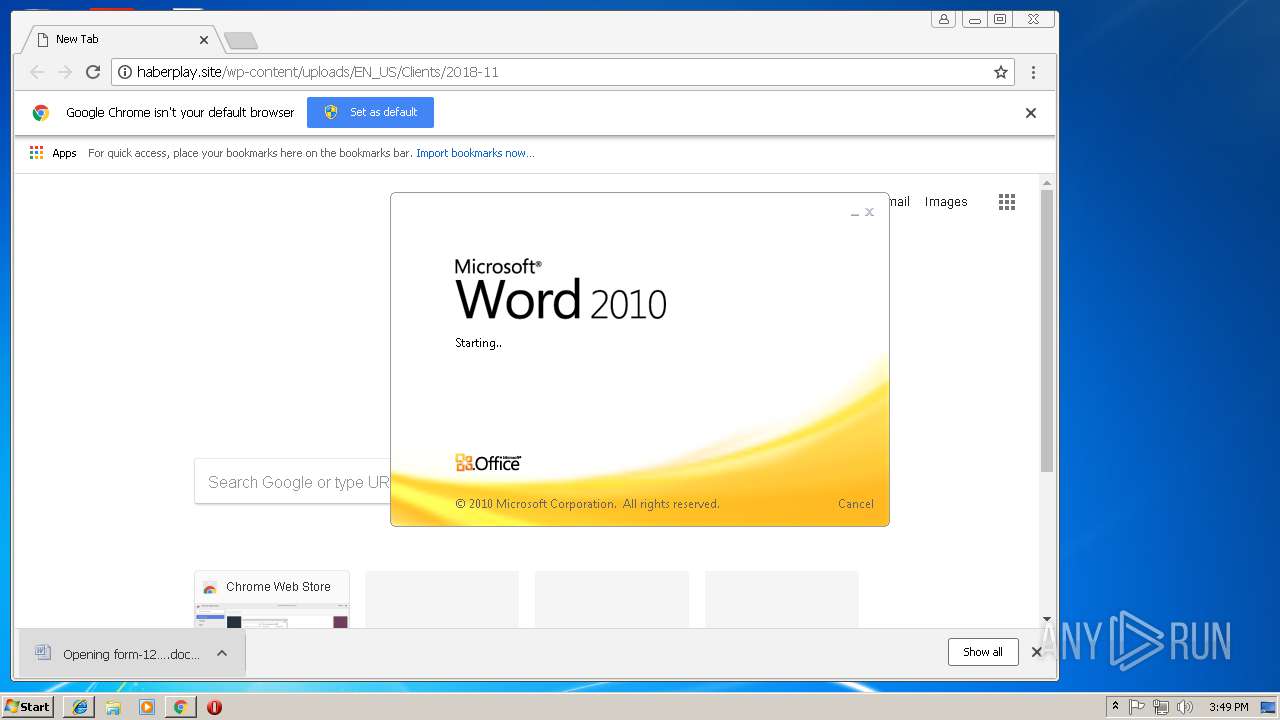
Starts Microsoft Office Application
- chrome.exe (PID: 664)
- WINWORD.EXE (PID: 1148)
Executable content was dropped or overwritten
- powershell.exe (PID: 3548)
- 940.exe (PID: 2556)
Creates files in the user directory
- powershell.exe (PID: 3548)
Starts itself from another location
- 940.exe (PID: 2556)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3332)
- chrome.exe (PID: 664)
Application launched itself
- chrome.exe (PID: 664)
- iexplore.exe (PID: 4048)
Changes internet zones settings
- iexplore.exe (PID: 4048)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1148)
- WINWORD.EXE (PID: 3464)
Reads internet explorer settings
- iexplore.exe (PID: 3332)
Creates files in the user directory
- WINWORD.EXE (PID: 1148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| ContentType: | text/html; charset=windows-1252 |
|---|---|
| ProgID: | Word.Document |
| Generator: | Microsoft Word 14 |
| Originator: | Microsoft Word 14 |
| Author: | Пользователь Windows |
| Template: | NormalEmail |
| TotalEditTime: | 2 minutes |
| CreateDate: | 2018:09:20 16:05:00Z |
| Pages: | 1 |
| Words: | 283 |
| Characters: | 1615 |
| Lines: | 13 |
| Paragraphs: | 3 |
| CharactersWithSpaces: | 1895 |
| RevisionNumber: | 14 |
Total processes
54
Monitored processes
22
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=912,8524548162385521753,10067723645868401888,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=BC11B0F0DA3E94797546E40DEEF35C80 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=BC11B0F0DA3E94797546E40DEEF35C80 --renderer-client-id=6 --mojo-platform-channel-handle=3560 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\form-1272293300978.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=912,8524548162385521753,10067723645868401888,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=371071D119CCDF369E1AC00BFD17A7C2 --mojo-platform-channel-handle=2272 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=912,8524548162385521753,10067723645868401888,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=7AA641E21075067029F1CDF83E38A9C9 --mojo-platform-channel-handle=904 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6e0300b0,0x6e0300c0,0x6e0300cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=912,8524548162385521753,10067723645868401888,131072 --enable-features=PasswordImport --service-pipe-token=5BDD3C4F19D955F8C829A9927CE15A56 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5BDD3C4F19D955F8C829A9927CE15A56 --renderer-client-id=5 --mojo-platform-channel-handle=1836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2556 | "C:\Users\admin\AppData\Local\Temp\940.exe" | C:\Users\admin\AppData\Local\Temp\940.exe | 940.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=912,8524548162385521753,10067723645868401888,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=AC862DE03F515100785320BABD445D97 --mojo-platform-channel-handle=3748 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=912,8524548162385521753,10067723645868401888,131072 --enable-features=PasswordImport --service-pipe-token=0AC422653A409C9D1DDFC8065875D439 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0AC422653A409C9D1DDFC8065875D439 --renderer-client-id=3 --mojo-platform-channel-handle=2068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 474
Read events
2 929
Write events
529
Delete events
16
Modification events
| (PID) Process: | (4048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {D7E3BECF-E36D-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (4048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (4048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (4048) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B00040008000F00310010008800 | |||
Executable files
2
Suspicious files
53
Text files
59
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4048 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4048 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\576710e0-d1d6-4884-bf5e-5e1e80ef7834.tmp | — | |
MD5:— | SHA256:— | |||
| 664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5d1201bc-d4fd-4eef-9c7c-bb66e1ae3956.tmp | — | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018110820181109\index.dat | dat | |
MD5:— | SHA256:— | |||
| 664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF5df6ee.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
16
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3616 | lpiograd.exe | GET | — | 187.163.174.149:8080 | http://187.163.174.149:8080/ | MX | — | — | malicious |
3616 | lpiograd.exe | GET | — | 70.60.50.60:8080 | http://70.60.50.60:8080/ | US | — | — | malicious |
3548 | powershell.exe | GET | 200 | 173.201.98.1:80 | http://madisonda.com/PncwJNSS/ | US | executable | 792 Kb | malicious |
4048 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
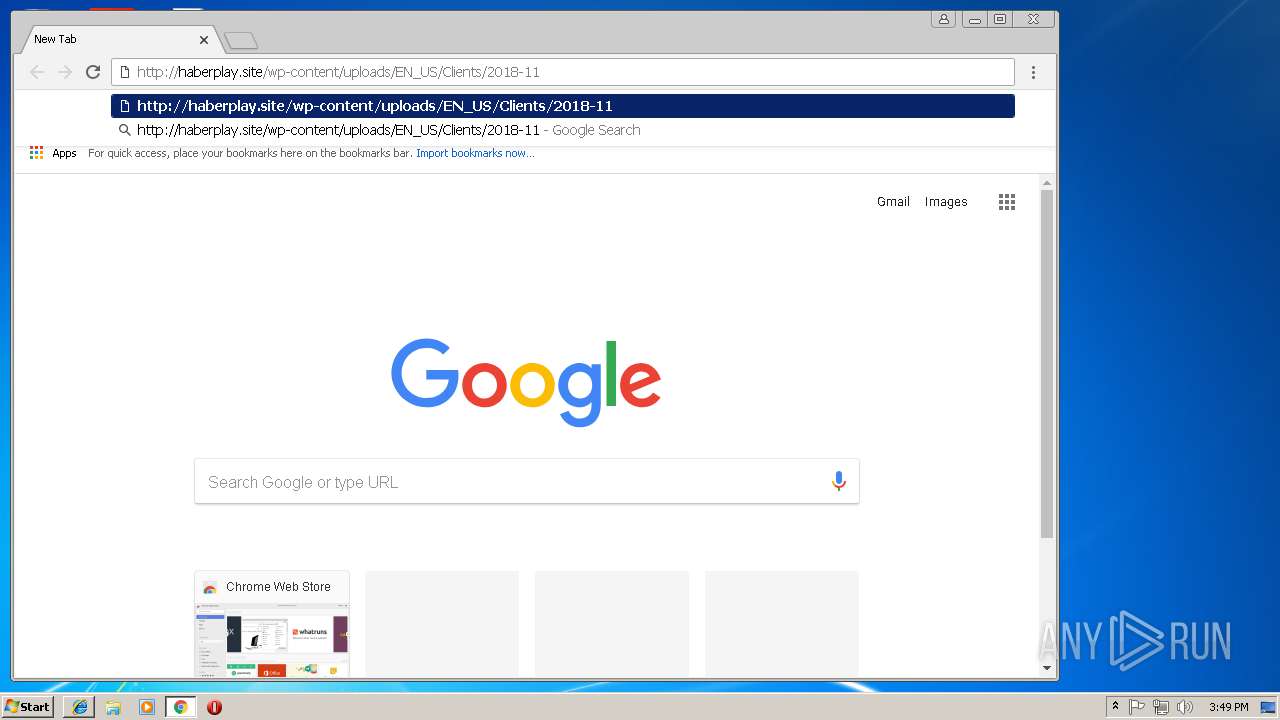
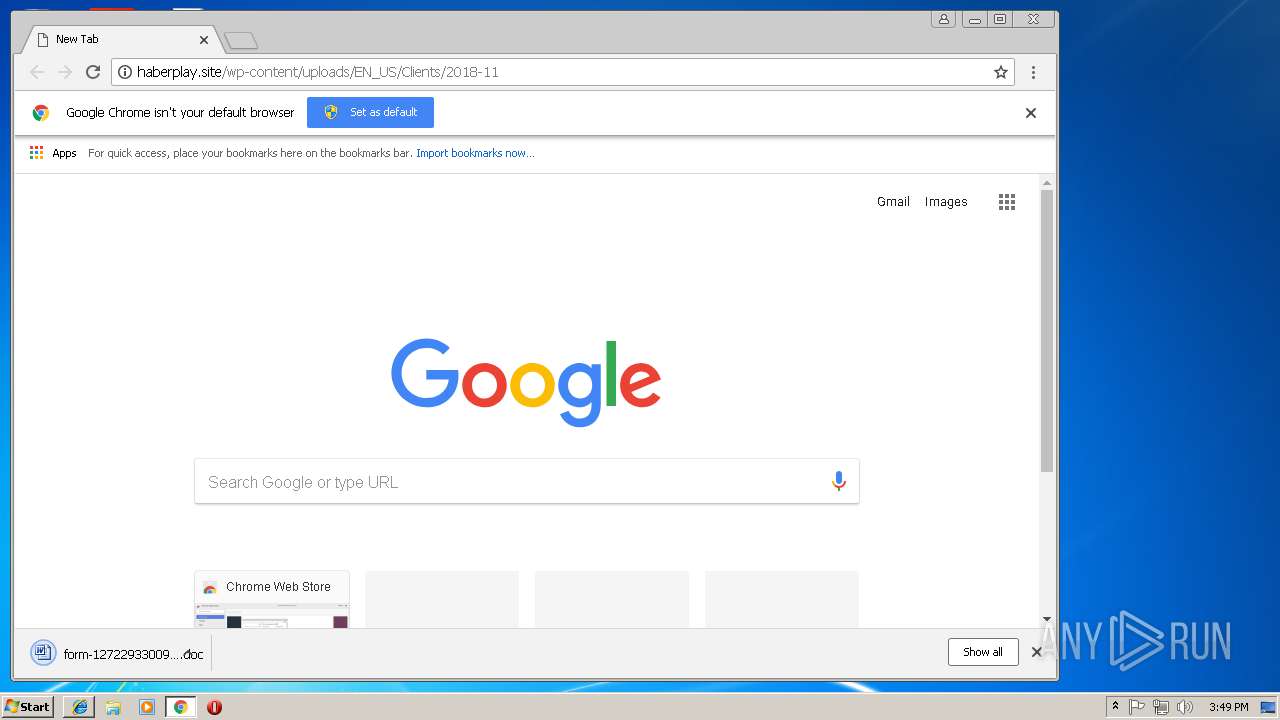
664 | chrome.exe | GET | 301 | 185.22.187.47:80 | http://haberplay.site/wp-content/uploads/EN_US/Clients/2018-11 | TR | html | 617 b | suspicious |
664 | chrome.exe | GET | 200 | 185.22.187.47:80 | http://haberplay.site/wp-content/uploads/EN_US/Clients/2018-11/ | TR | document | 69.6 Kb | suspicious |
3548 | powershell.exe | GET | 301 | 173.201.98.1:80 | http://madisonda.com/PncwJNSS | US | html | 301 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3332 | iexplore.exe | 159.45.2.178:443 | static.wellsfargo.com | Wells Fargo & Company | US | suspicious |
3332 | iexplore.exe | 159.45.2.175:443 | ort.wellsfargo.com | Wells Fargo & Company | US | unknown |
4048 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
664 | chrome.exe | 216.58.215.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
664 | chrome.exe | 172.217.168.36:443 | www.google.com | Google Inc. | US | whitelisted |
664 | chrome.exe | 185.22.187.47:80 | haberplay.site | Cizgi Telekomunikasyon Anonim Sirketi | TR | suspicious |
664 | chrome.exe | 172.217.168.14:443 | apis.google.com | Google Inc. | US | whitelisted |
664 | chrome.exe | 172.217.168.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3548 | powershell.exe | 173.201.98.1:80 | madisonda.com | GoDaddy.com, LLC | US | malicious |
3616 | lpiograd.exe | 70.60.50.60:8080 | — | Time Warner Cable Internet LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
static.wellsfargo.com |
| suspicious |
ort.wellsfargo.com |
| suspicious |
www.bing.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
664 | chrome.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
664 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
664 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3548 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
3548 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3548 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3548 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3616 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2 ETPRO signatures available at the full report