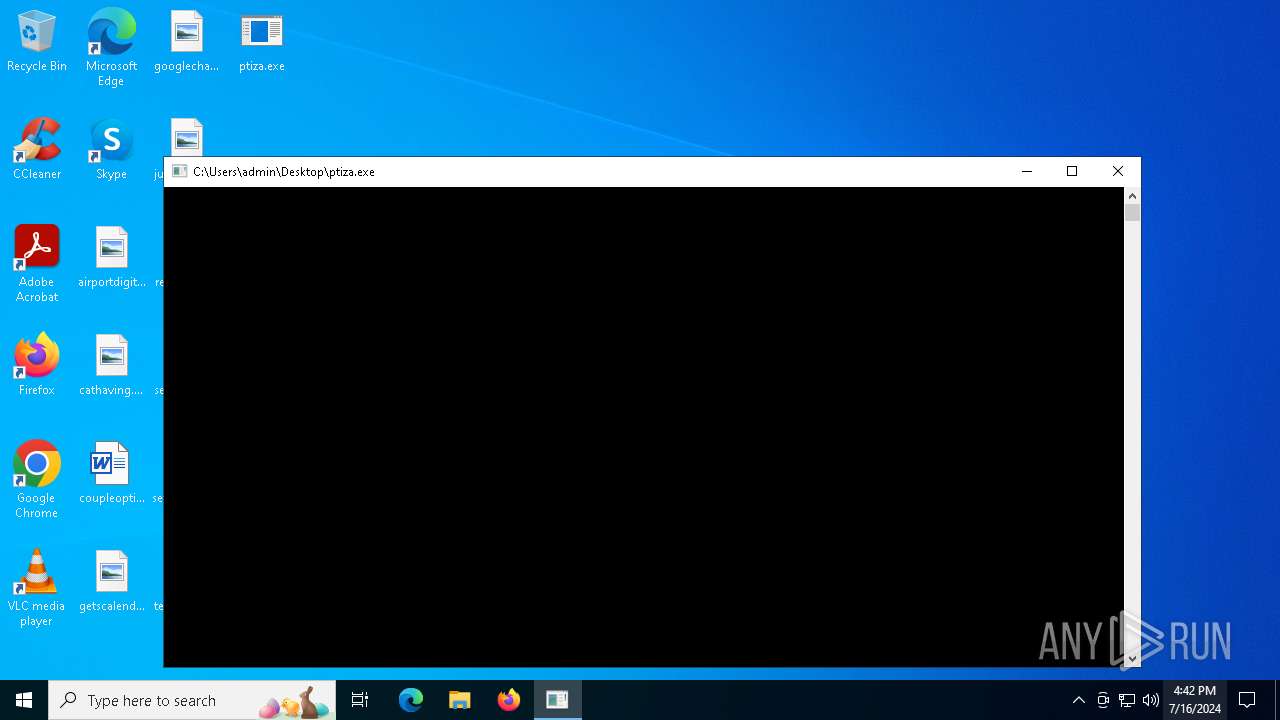
| File name: | ptiza.exe |
| Full analysis: | https://app.any.run/tasks/3ff47e91-e232-44dd-832a-a718cf018722 |
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2024, 16:42:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 3F6764DA4B8ECBCD559375D037DC26A0 |
| SHA1: | 00846950B90A2801B55A8A2F6342F0F303E8361B |
| SHA256: | 0D9BA751A47E198D4A270F29D031CB529CE3B8EA6E59957089D3C96E0E943275 |
| SSDEEP: | 192:dQSI/iIhYZXA4Xi/DxhjEd/JsRceVW85ohJdAN+5pz6ADdDYYYYYYYQ:BI/AmOiLTgdRsRceQ855NiD |
MALICIOUS
Drops the executable file immediately after the start
- ptiza.exe (PID: 3624)
Changes the autorun value in the registry
- ptiza.exe (PID: 3220)
- ptiza.exe (PID: 5408)
Changes appearance of the Explorer extensions
- ptiza.exe (PID: 5408)
- ptiza.exe (PID: 3220)
SUSPICIOUS
Reads security settings of Internet Explorer
- ptiza.exe (PID: 3624)
- ptiza.exe (PID: 6016)
- ptiza.exe (PID: 5408)
- ptiza.exe (PID: 3220)
Application launched itself
- ptiza.exe (PID: 3624)
- ptiza.exe (PID: 6016)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 3736)
Reads the date of Windows installation
- ptiza.exe (PID: 6016)
- ptiza.exe (PID: 3624)
Checks Windows Trust Settings
- ptiza.exe (PID: 5408)
- ptiza.exe (PID: 3220)
INFO
Process checks computer location settings
- ptiza.exe (PID: 3624)
- ptiza.exe (PID: 6016)
Reads the computer name
- ptiza.exe (PID: 3624)
- ptiza.exe (PID: 6016)
- PLUGScheduler.exe (PID: 3736)
- ptiza.exe (PID: 5408)
- ptiza.exe (PID: 3220)
Checks supported languages
- ptiza.exe (PID: 3624)
- ptiza.exe (PID: 3220)
- PLUGScheduler.exe (PID: 3736)
- ptiza.exe (PID: 5408)
- ptiza.exe (PID: 6016)
Reads the software policy settings
- ptiza.exe (PID: 3220)
- ptiza.exe (PID: 5408)
Creates files in the program directory
- PLUGScheduler.exe (PID: 3736)
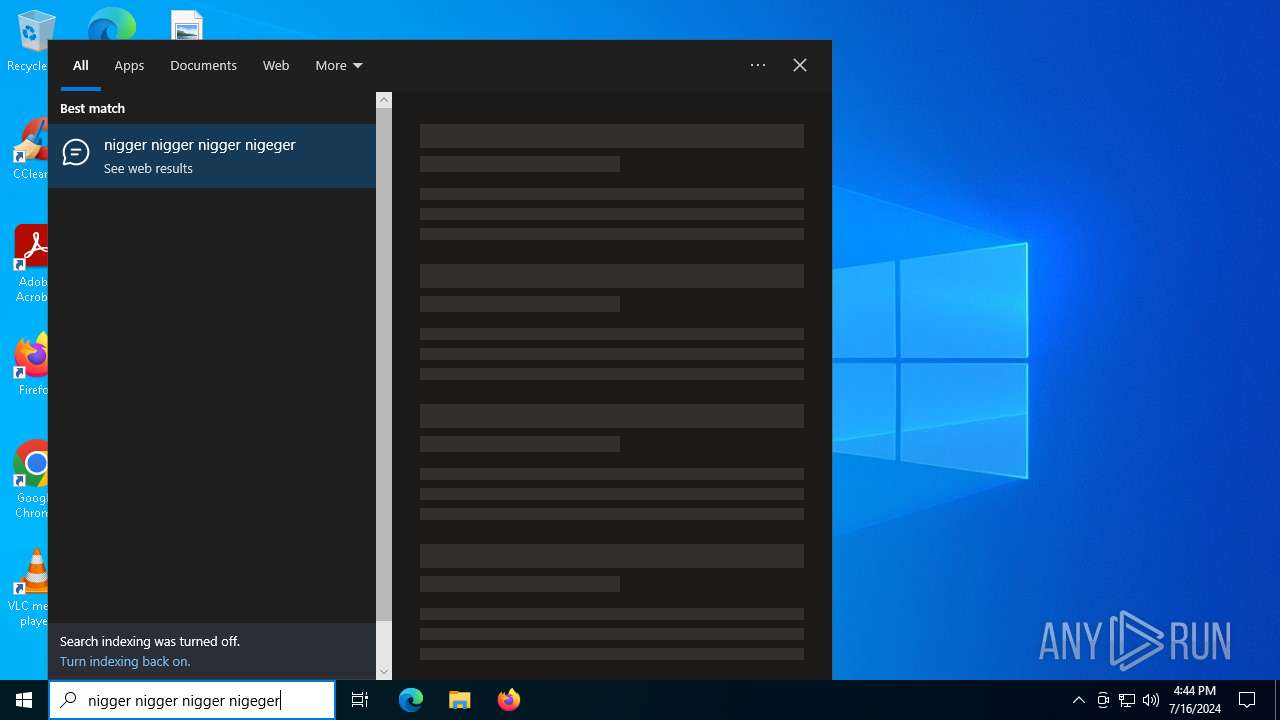
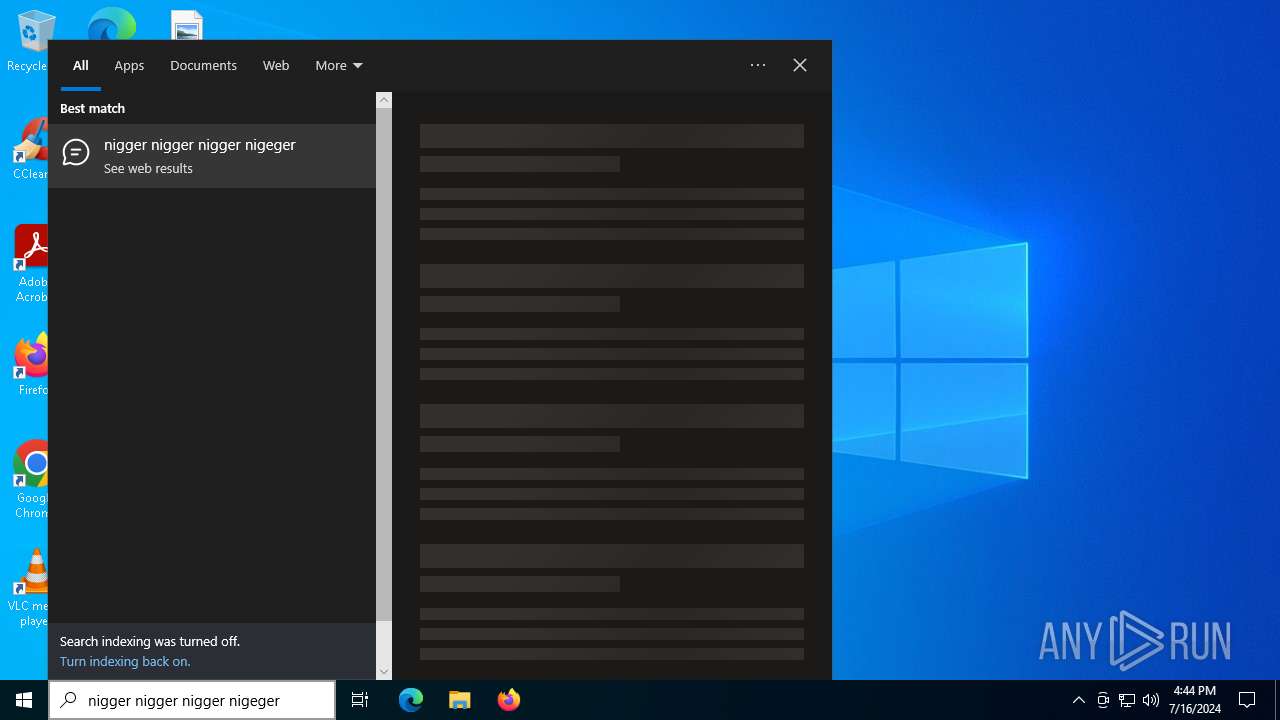
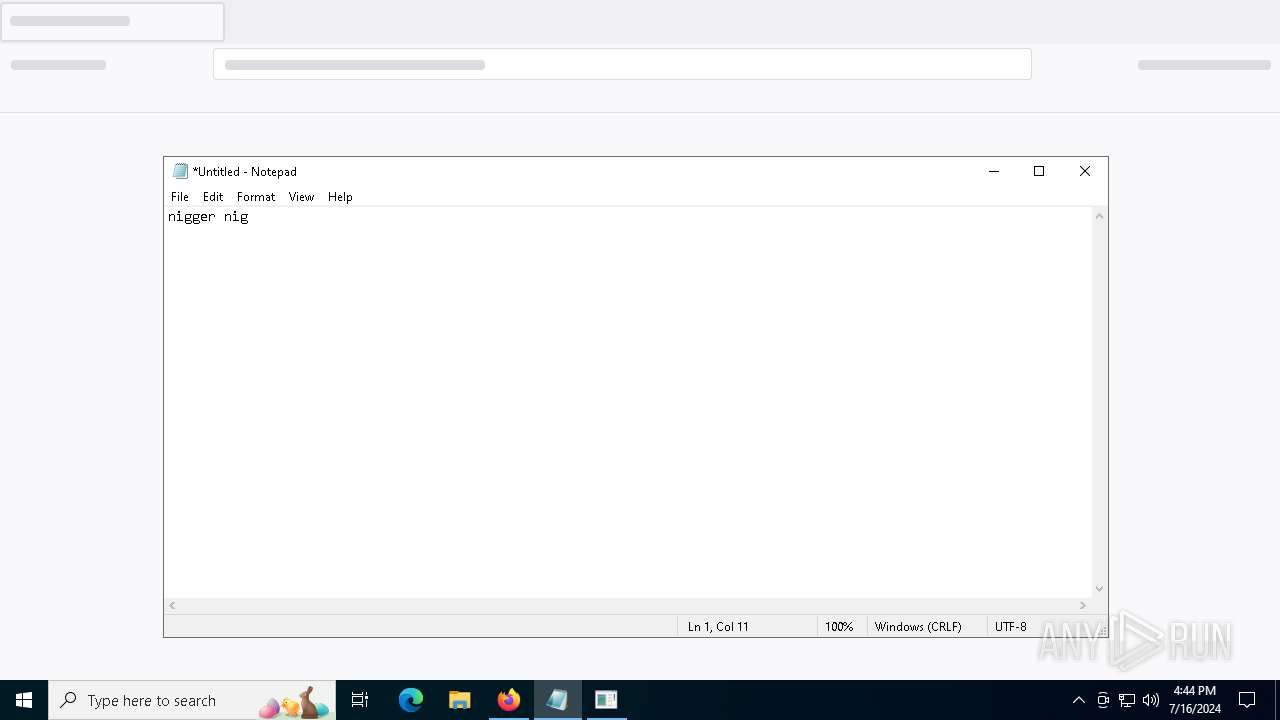
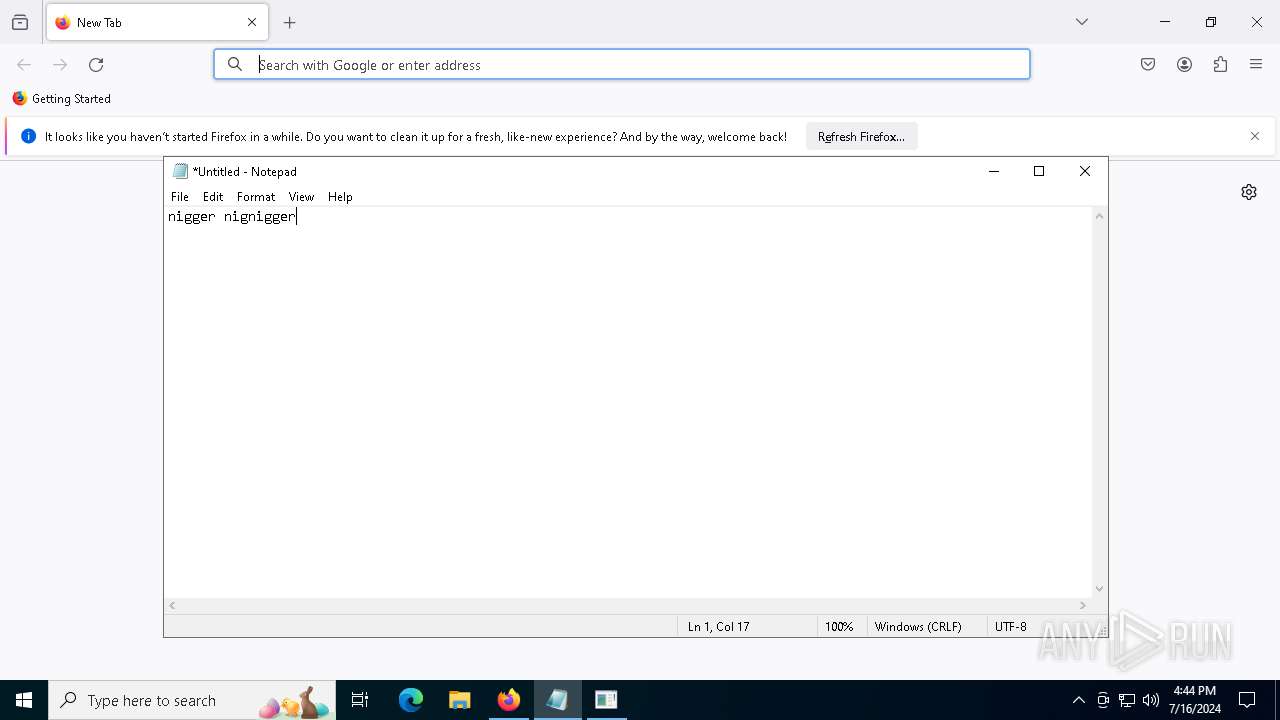
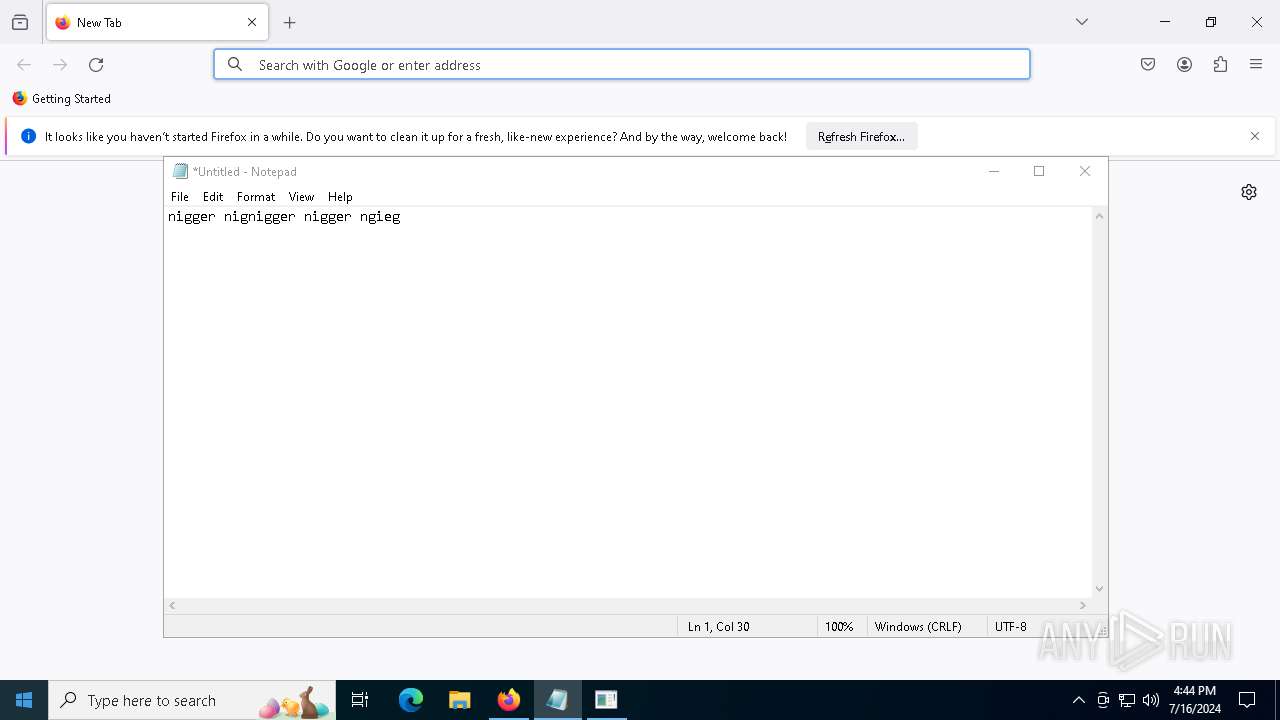
Manual execution by a user
- ptiza.exe (PID: 6016)
- notepad.exe (PID: 6052)
- firefox.exe (PID: 3340)
Reads the machine GUID from the registry
- ptiza.exe (PID: 3220)
- ptiza.exe (PID: 5408)
Checks proxy server information
- ptiza.exe (PID: 5408)
- ptiza.exe (PID: 3220)
Application launched itself
- firefox.exe (PID: 1044)
- firefox.exe (PID: 3340)
Reads Microsoft Office registry keys
- firefox.exe (PID: 1044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:07:16 16:15:40+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.4 |
| CodeSize: | 6656 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1df4 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
255
Monitored processes
20
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1972 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ptiza.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2012 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1828 -parentBuildID 20240213221259 -prefsHandle 1772 -prefMapHandle 1764 -prefsLen 30537 -prefMapSize 244343 -appDir "C:\Program Files\Mozilla Firefox\browser" - {fc352da7-ee2a-479d-9770-aa72bee88c20} 1044 "\\.\pipe\gecko-crash-server-pipe.1044" 210589e1710 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3220 | "C:\Users\admin\Desktop\ptiza.exe" | C:\Users\admin\Desktop\ptiza.exe | ptiza.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
| 3340 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3624 | "C:\Users\admin\Desktop\ptiza.exe" | C:\Users\admin\Desktop\ptiza.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3736 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4532 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ptiza.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ptiza.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5408 | "C:\Users\admin\Desktop\ptiza.exe" | C:\Users\admin\Desktop\ptiza.exe | ptiza.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
Total events
21 999
Read events
21 929
Write events
69
Delete events
1
Modification events
| (PID) Process: | (3624) ptiza.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3624) ptiza.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3624) ptiza.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3624) ptiza.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3220) ptiza.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WindowsUpdate |
Value: C:\Users\admin\Desktop\ptiza.exe | |||
| (PID) Process: | (3220) ptiza.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | Hidden |
Value: 0 | |||
| (PID) Process: | (3220) ptiza.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | ShowSuperHidden |
Value: 0 | |||
| (PID) Process: | (3220) ptiza.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3220) ptiza.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3220) ptiza.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
65
Text files
10
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3736 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.023.etl | etl | |
MD5:44A0E917AD0C126931B1BCD959285A9A | SHA256:DDFBE47E7DFD6D8B7517F2F6FF9808ECF3C0A25F588A9F96D04F4E2B4A578573 | |||
| 3736 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.024.etl | etl | |
MD5:868E79A00A8204448B2FFC4F4D5C08EA | SHA256:148FE324431CB4C826BCF0436147D946AC389A877732612CF40629048B8517DC | |||
| 3736 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.019.etl | etl | |
MD5:A23907B6FDD47DCABFDFD7CF2FCD7671 | SHA256:0C9C33FE9E984A2E5A70EBA51F36B9929A86199E424AF2F8080E1267B87DC970 | |||
| 3736 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.017.etl | etl | |
MD5:A7A21FBC9D00F33F186B34A50E170C13 | SHA256:64CAC91E46D4FC832958232A658431CBF9D8D9F265653ACA2BEB32428D4688EC | |||
| 3736 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.025.etl | etl | |
MD5:2F36C598EBFF5B5CDD898C9691D6BCCB | SHA256:8900C5931ED8E0D1B68082B45CF2F4E8C1025D36825508E0804C916D781B9F50 | |||
| 3736 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.014.etl | etl | |
MD5:8A2BDE0EAFA7E946196A1B114AB636E9 | SHA256:1C338CBDD9316D7FD8F208341466FEDC554A04D489B3A86C736EC3831A2F2BA2 | |||
| 3736 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.015.etl | etl | |
MD5:B53B2070E686FFB1FBC8B06994E7C8D7 | SHA256:A3ABD06F4E40CB700B1908AB6BCD2E27455E13EF076E0BF2345BB2FA369EF802 | |||
| 3736 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.013.etl | etl | |
MD5:C1F87CF12DD702D2185E703BA004D216 | SHA256:9D993487866C9538DC19F281A6346E1796E7478C7C164D61437AF6E698C66125 | |||
| 3736 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.021.etl | etl | |
MD5:C8834D365FAE073DEDE1F1620454CE71 | SHA256:C6DD793EEE1D5551CA507A3C5BFFECA82DD3E29C63C2C6DD218A7D4BFB37046B | |||
| 3736 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.012.etl | etl | |
MD5:09359EE89B0634478ADFF73CDA7BFB12 | SHA256:4D800AC7C55960B107C9D3E40F63130407835E69DF4F5C558C500FC0BD20D8ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
79
TCP/UDP connections
64
DNS requests
64
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2448 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2204 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2448 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | — | 184.86.251.13:443 | https://www.bing.com/AS/API/WindowsCortanaPane/V2/Suggestions?qry=regedit&setlang=en-US&cc=US&nohs=1&qfm=1&cp=7&cvid=917f2af1fe65416cbd620a4b992edbf0&ig=0c07db2ed43b472383863f523ee03420 | unknown | — | — | unknown |
— | — | GET | 200 | 184.86.251.24:443 | https://www.bing.com/rb/18/jnc,nj/6hU_LneafI_NFLeDvM367ebFaKQ.js?bu=DyIrb3t-gQF4cnWyAbUBK6UBK7gB&or=w | unknown | s | 21.3 Kb | unknown |
— | — | POST | — | 93.184.215.14:443 | https://example.com/c2/data | unknown | — | — | unknown |
— | — | GET | 200 | 184.86.251.11:443 | https://www.bing.com/AS/API/WindowsCortanaPane/V2/Suggestions?qry=regedi&setlang=en-US&cc=US&nohs=1&qfm=1&cp=6&cvid=917f2af1fe65416cbd620a4b992edbf0&ig=46856f19730442d7bfc8a588e4a577aa | unknown | binary | 4.01 Kb | unknown |
— | — | GET | 200 | 52.113.194.132:443 | https://ecs.office.com/config/v2/Office/officeclicktorun/16.0.16026.20140/Production/CC?&Clientid=%7b48BA7FDF-353C-4FE5-8D8F-9E31911A3891%7d&Application=officeclicktorun&Platform=win32&Version=16.0.16026.20140&MsoVersion=16.0.16026.20140&ProcessName=officeclicktorun.exe&Audience=Production&Build=ship&Architecture=x64&OsVersion=10.0&OsBuild=19045&Channel=CC&InstallType=C2R&SessionId=%7b43499F55-E9C7-4881-BB48-C4C4E4FE4475%7d&LabMachine=false | unknown | text | 334 Kb | unknown |
— | — | GET | 200 | 184.86.251.8:443 | https://www.bing.com/rb/18/jnc,nj/6hU_LneafI_NFLeDvM367ebFaKQ.js?bu=DyIrb3t-gQF4cnWyAbUBK6UBK7gB&or=w | unknown | s | 21.3 Kb | unknown |
— | — | POST | — | 184.86.251.9:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.23.209.182:443 | — | Akamai International B.V. | GB | unknown |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
2448 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6116 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2204 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2448 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2204 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2448 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2204 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
example.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
Threats
4 ETPRO signatures available at the full report