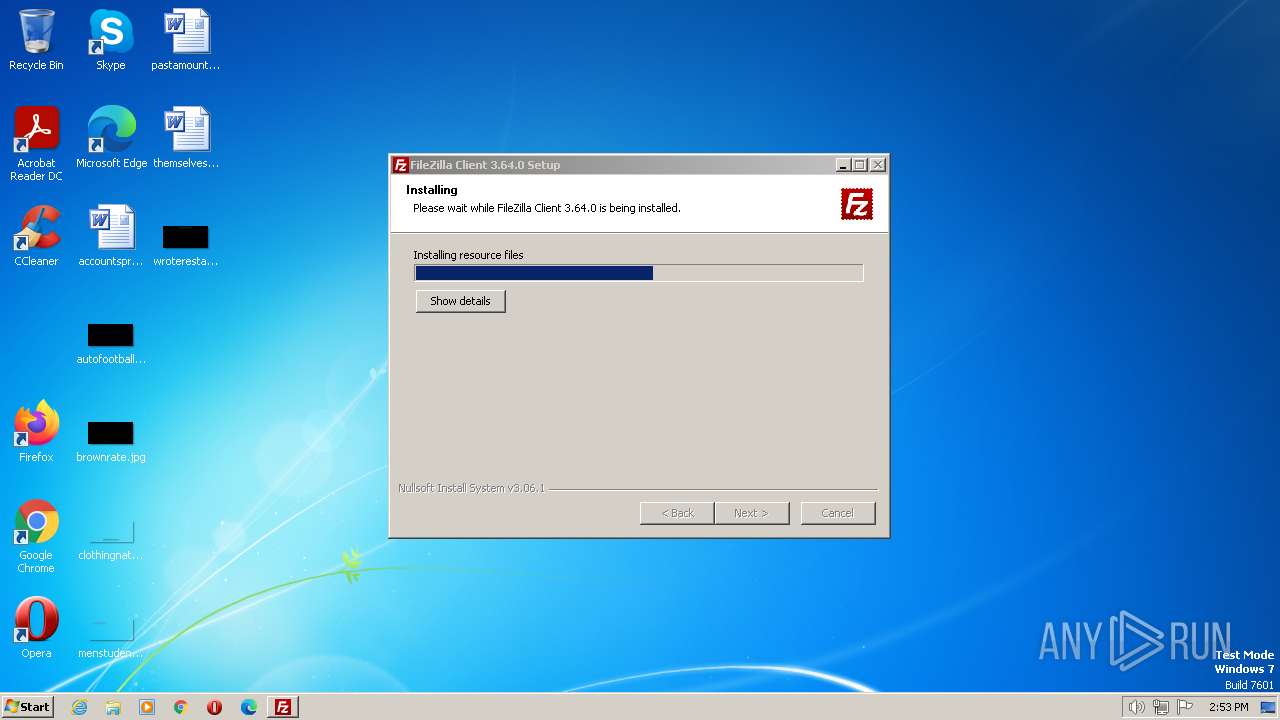
| File name: | FileZilla_3.64.0_win64-setup.exe |
| Full analysis: | https://app.any.run/tasks/98dee956-aa33-426d-8bb1-7b7733163230 |
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2023, 13:52:28 |
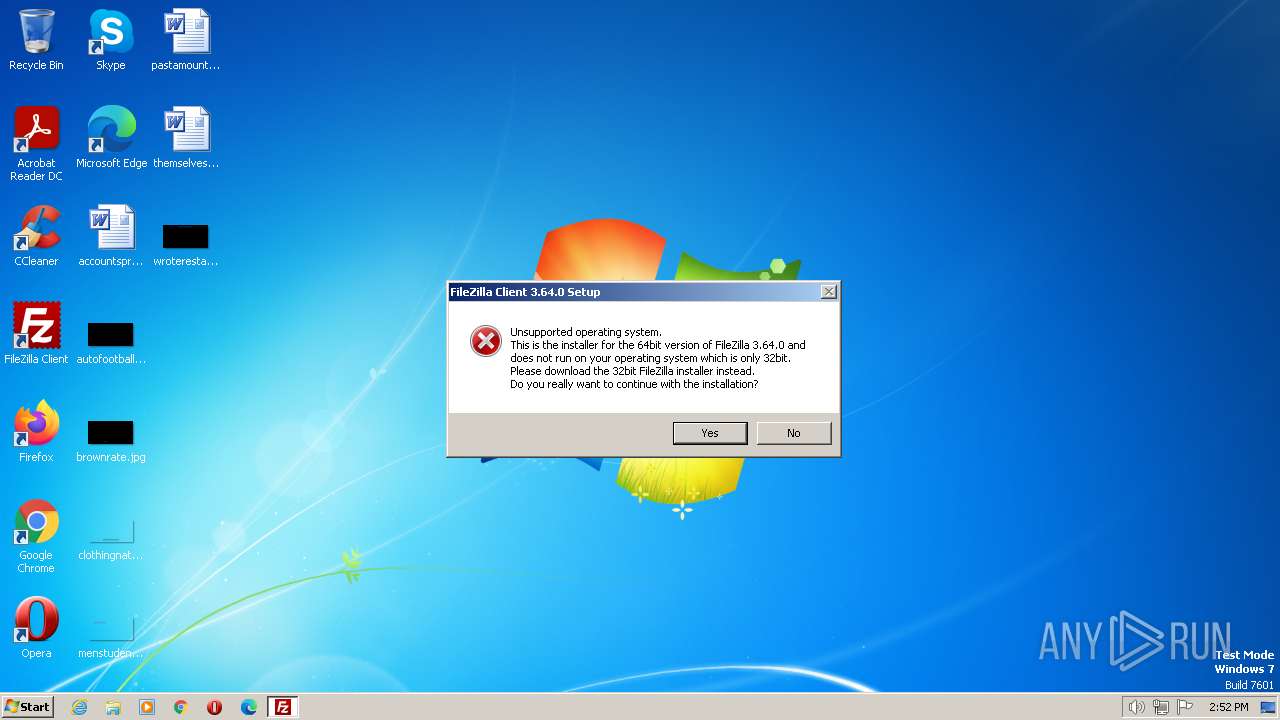
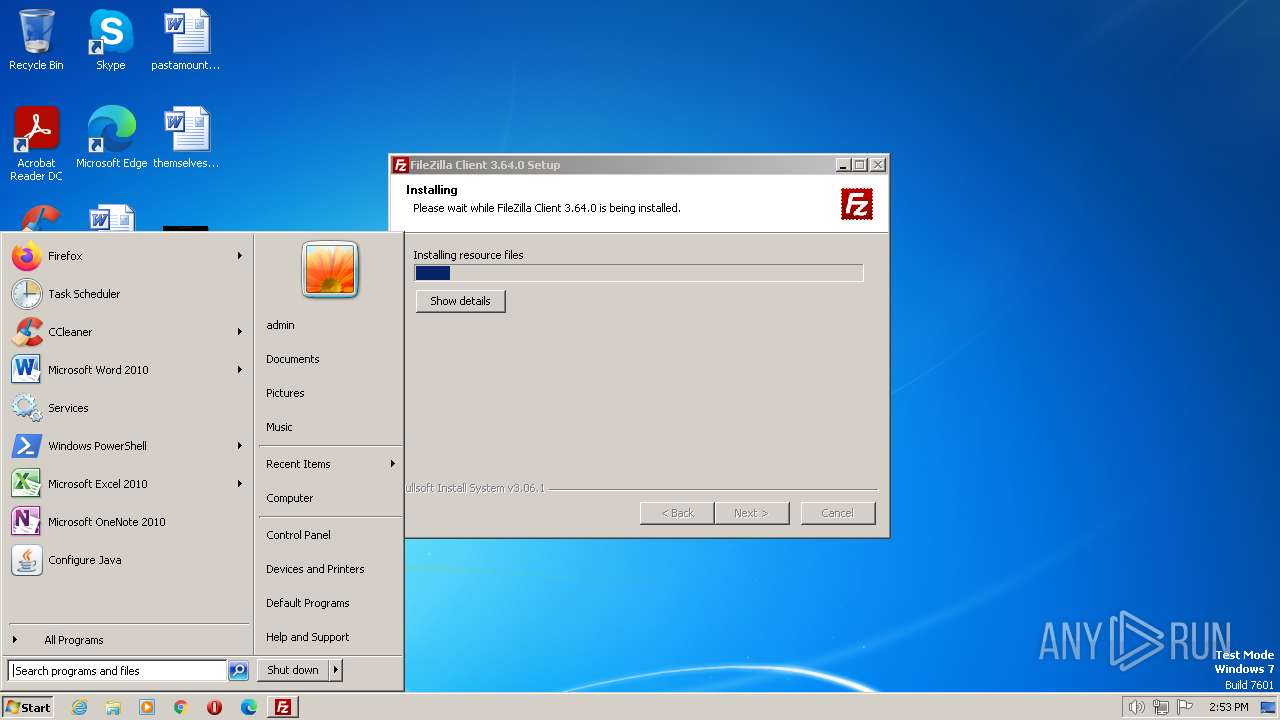
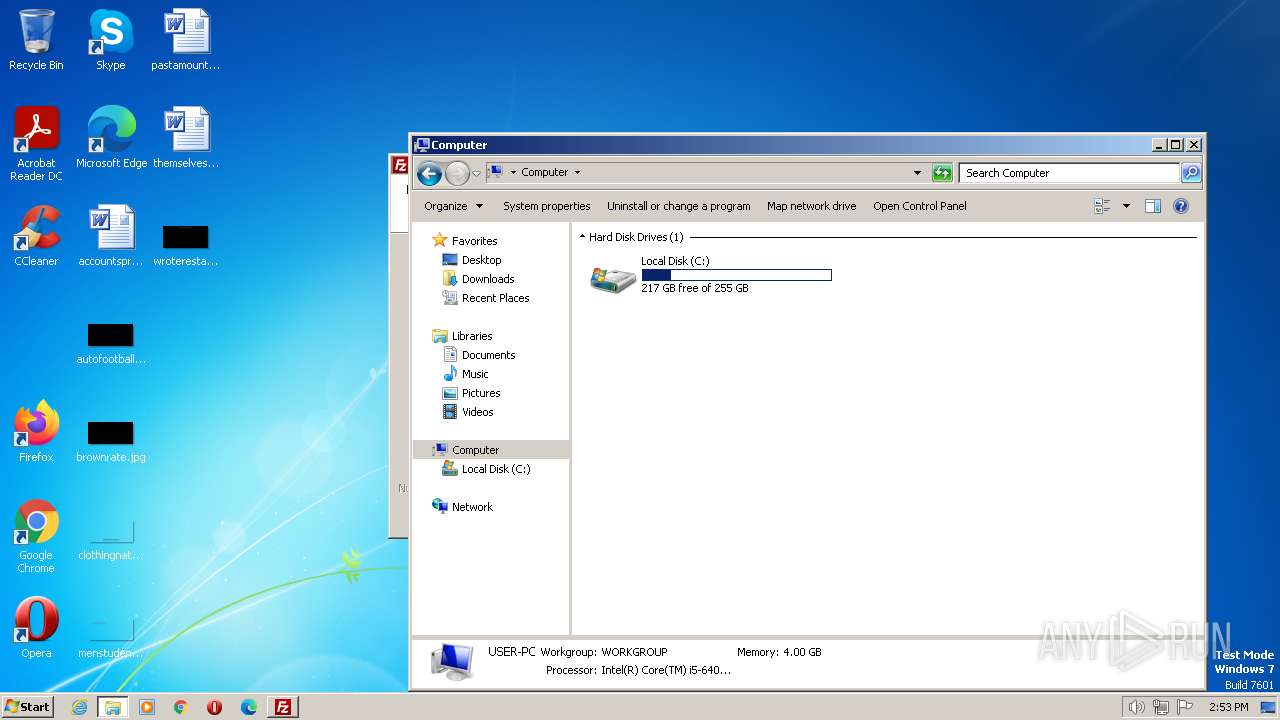
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
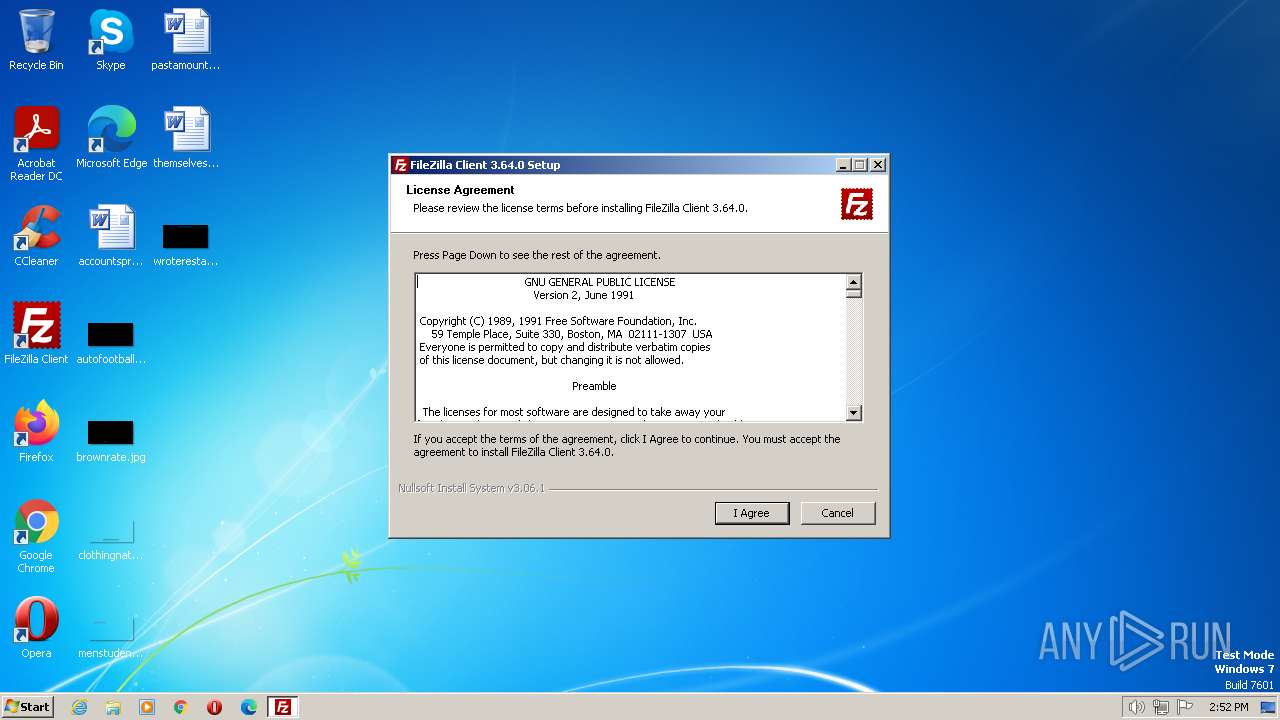
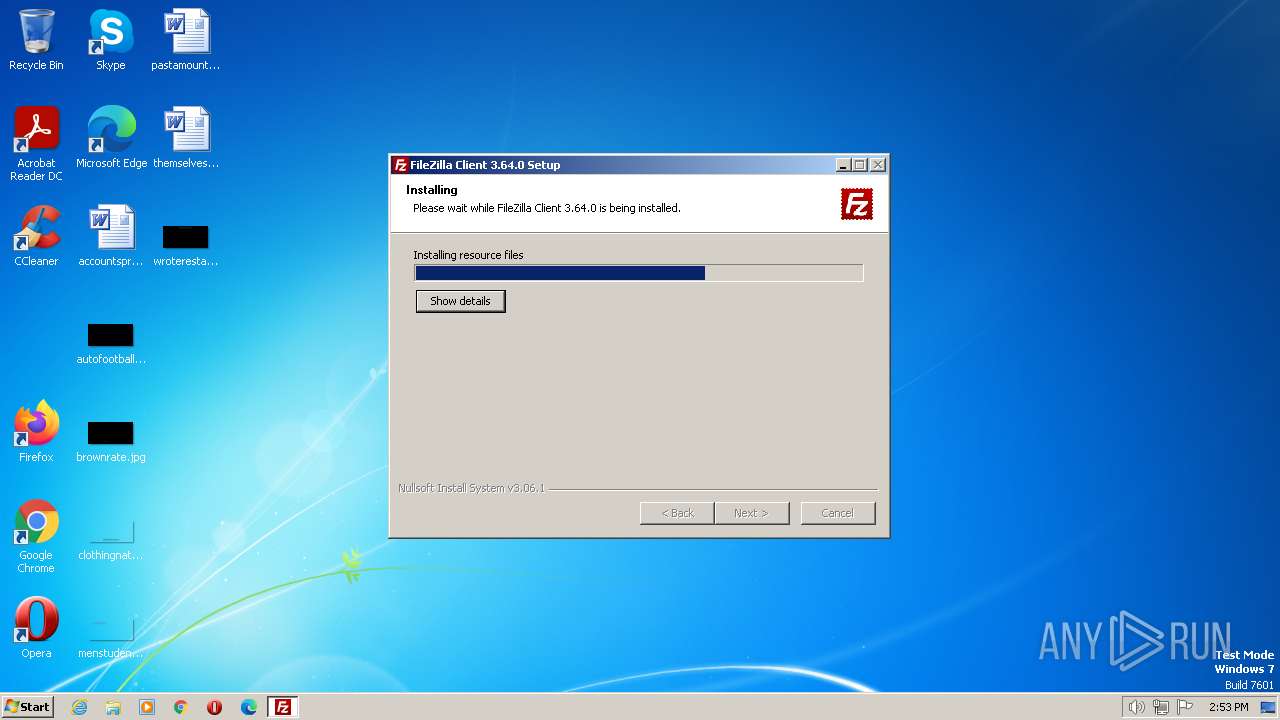
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 6A0ADCF34A2F0AC21089B994DFF02B85 |
| SHA1: | 4C5C3F6D95FADC1ED99AAB2D85F5B7122B041A72 |
| SHA256: | 0D8F5DBE4A1F05DDACDA6493733BED57FC54310C90BC6FDC764FB95A92441B40 |
| SSDEEP: | 196608:8WRJiq6Az8mHlykdYnsdZveP6BX2wEbUeX6gnG4od/q36hnWY4Jmc2TdB68fjC:8WRJD8mUsdIP68wEbjfod/gQnCoc8B12 |
MALICIOUS
Loads dropped or rewritten executable
- FileZilla_3.64.0_win64-setup.exe (PID: 1132)
- FileZilla_3.64.0_win64-setup.exe (PID: 3500)
- uninstall.exe (PID: 3504)
SUSPICIOUS
The process creates files with name similar to system file names
- FileZilla_3.64.0_win64-setup.exe (PID: 1132)
- uninstall.exe (PID: 3504)
- FileZilla_3.64.0_win64-setup.exe (PID: 3500)
Application launched itself
- FileZilla_3.64.0_win64-setup.exe (PID: 1132)
Executable content was dropped or overwritten
- FileZilla_3.64.0_win64-setup.exe (PID: 1132)
- uninstall.exe (PID: 3504)
- FileZilla_3.64.0_win64-setup.exe (PID: 3500)
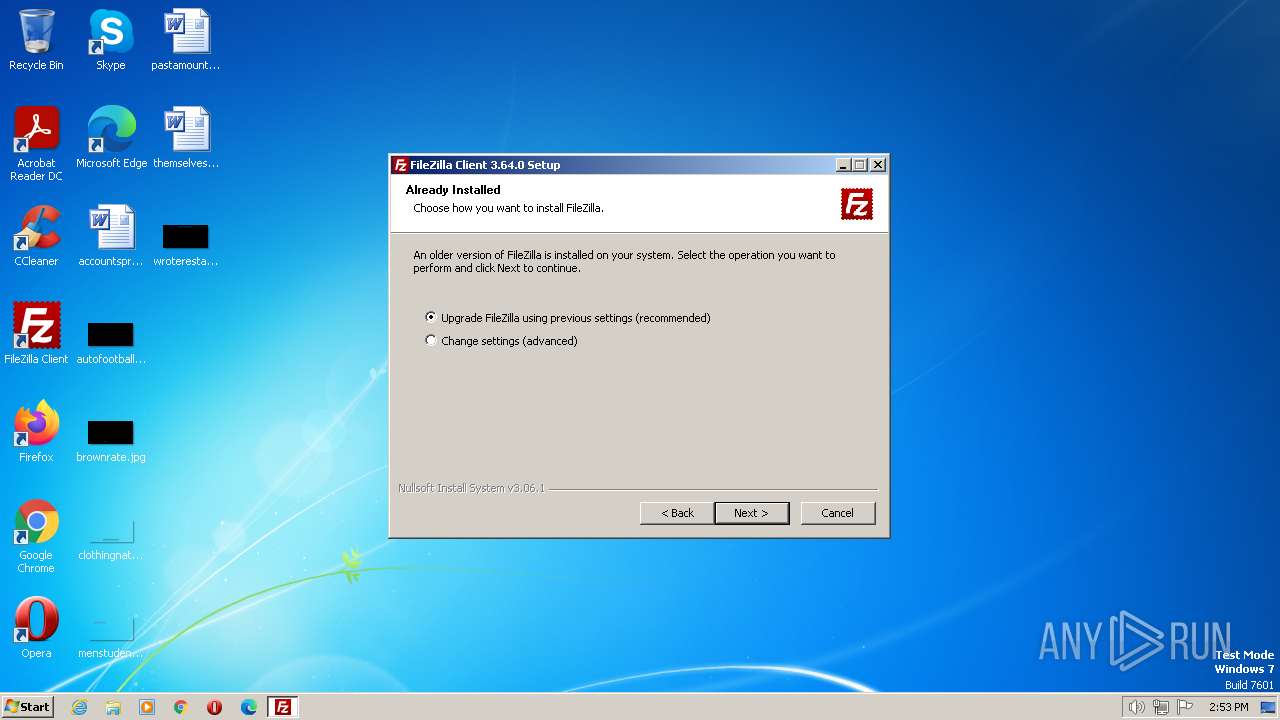
Searches for installed software
- FileZilla_3.64.0_win64-setup.exe (PID: 3500)
Reads the Internet Settings
- FileZilla_3.64.0_win64-setup.exe (PID: 1132)
INFO
Checks supported languages
- FileZilla_3.64.0_win64-setup.exe (PID: 1132)
- FileZilla_3.64.0_win64-setup.exe (PID: 3500)
- uninstall.exe (PID: 3504)
The process checks LSA protection
- FileZilla_3.64.0_win64-setup.exe (PID: 1132)
- FileZilla_3.64.0_win64-setup.exe (PID: 3500)
- uninstall.exe (PID: 3504)
- mmc.exe (PID: 2956)
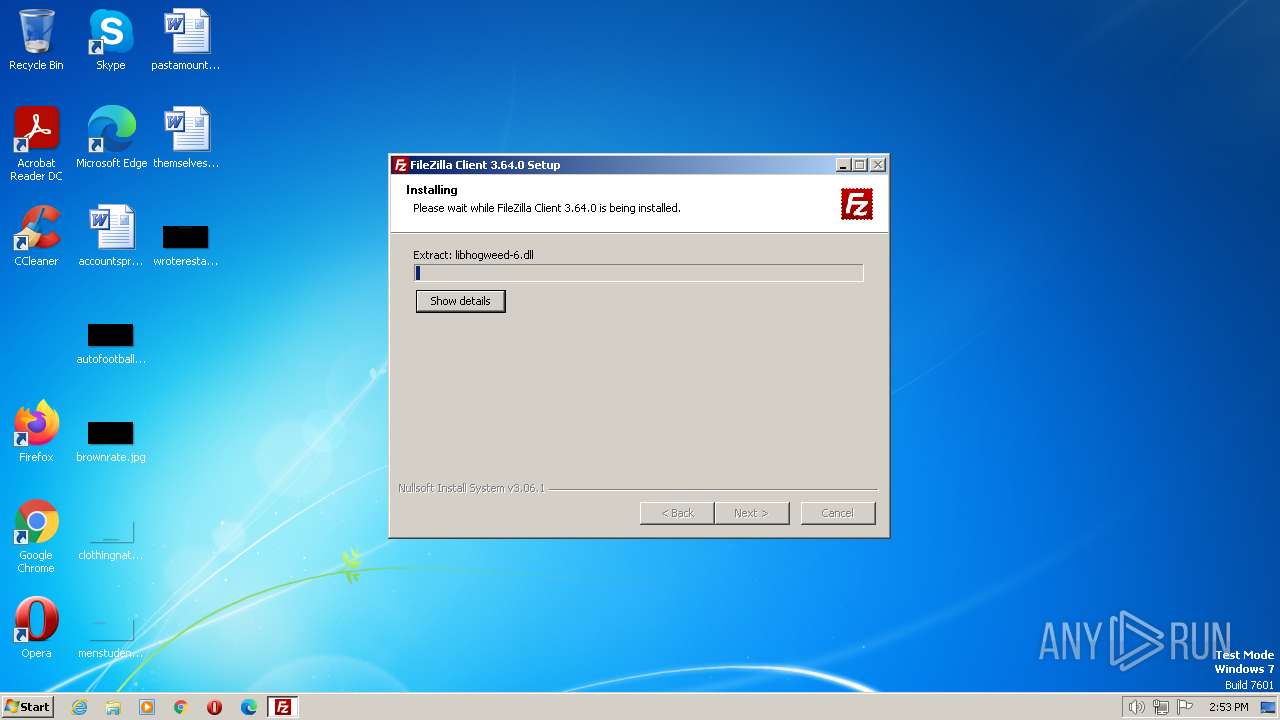
Create files in a temporary directory
- FileZilla_3.64.0_win64-setup.exe (PID: 3500)
- uninstall.exe (PID: 3504)
- FileZilla_3.64.0_win64-setup.exe (PID: 1132)
Reads the computer name
- FileZilla_3.64.0_win64-setup.exe (PID: 3500)
- uninstall.exe (PID: 3504)
- FileZilla_3.64.0_win64-setup.exe (PID: 1132)
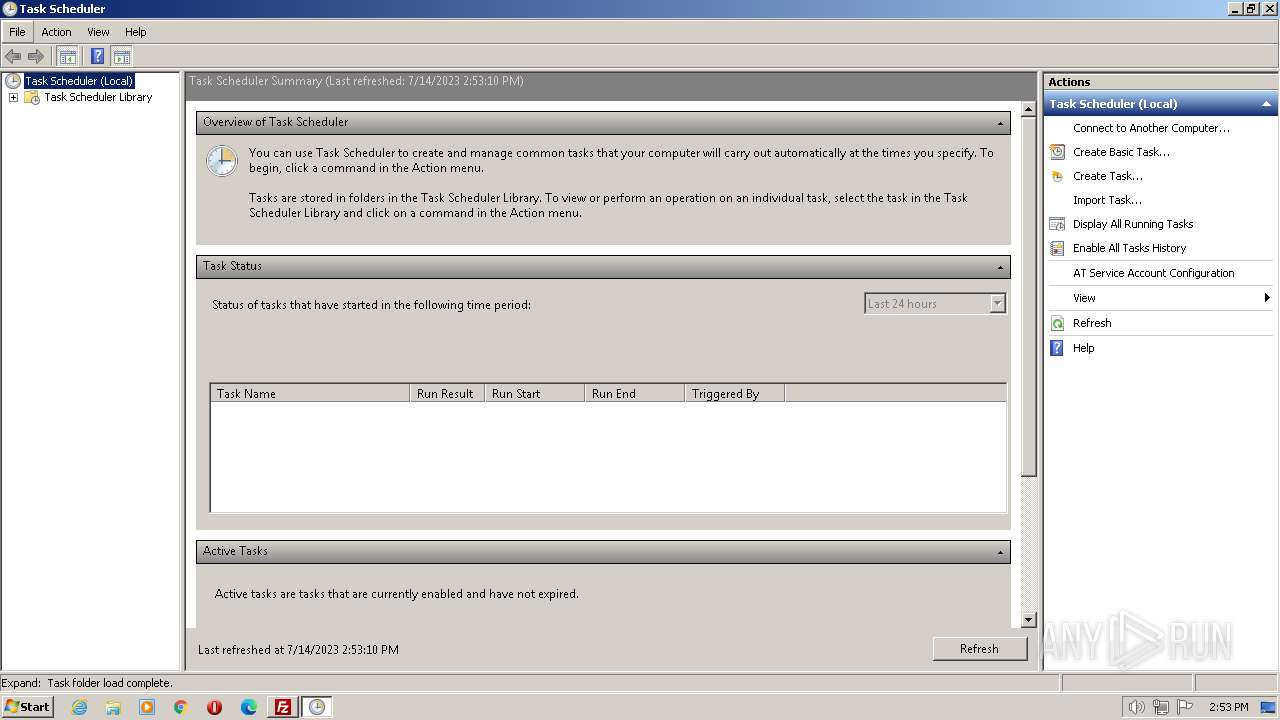
Manual execution by a user
- mmc.exe (PID: 2956)
- mmc.exe (PID: 2300)
Creates files in the program directory
- FileZilla_3.64.0_win64-setup.exe (PID: 3500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 3.64.0 |
|---|---|
| ProductName: | FileZilla |
| OriginalFileName: | FileZilla_3.64.0_win32-setup.exe |
| LegalCopyright: | Tim Kosse |
| FileVersion: | 3.64.0 |
| FileDescription: | FileZilla FTP Client |
| CompanyName: | Tim Kosse |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 3.64.0.0 |
| FileVersionNumber: | 3.64.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x35d8 |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 141824 |
| CodeSize: | 26112 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2020:08:01 02:44:18+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2020 02:44:18 |
| Detected languages: |
|
| CompanyName: | Tim Kosse |
| FileDescription: | FileZilla FTP Client |
| FileVersion: | 3.64.0 |
| LegalCopyright: | Tim Kosse |
| OriginalFilename: | FileZilla_3.64.0_win32-setup.exe |
| ProductName: | FileZilla |
| ProductVersion: | 3.64.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2020 02:44:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006572 | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45392 |
.rdata | 0x00008000 | 0x00001398 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13672 |
.data | 0x0000A000 | 0x00020378 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.09681 |
.ndata | 0x0002B000 | 0x0003A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00065000 | 0x0000A3A0 | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.57293 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29826 | 1061 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.69314 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.16834 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 4.66044 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 2.91531 | 1384 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.63186 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70411 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
48
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | "C:\Users\admin\AppData\Local\Temp\FileZilla_3.64.0_win64-setup.exe" | C:\Users\admin\AppData\Local\Temp\FileZilla_3.64.0_win64-setup.exe | explorer.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: MEDIUM Description: FileZilla FTP Client Exit code: 0 Version: 3.64.0 Modules
| |||||||||||||||
| 2300 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
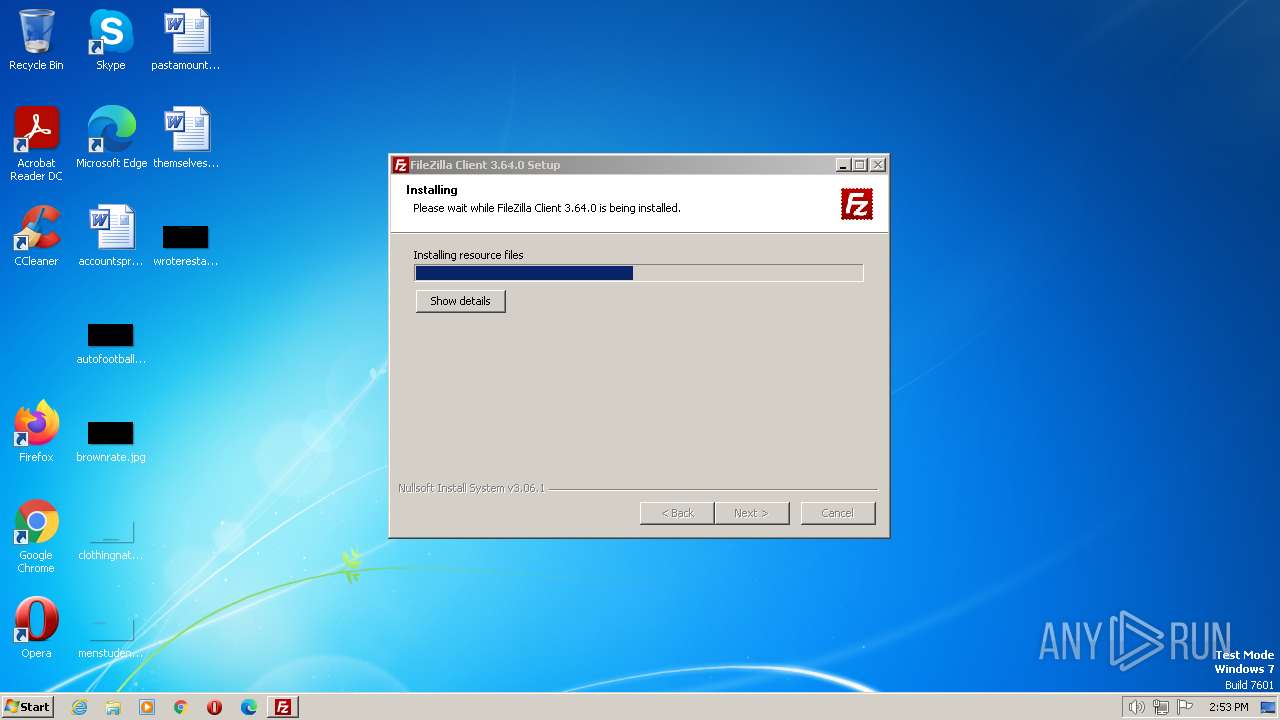
| 3500 | "C:\Users\admin\AppData\Local\Temp\FileZilla_3.64.0_win64-setup.exe" /UAC:90154 /NCRC | C:\Users\admin\AppData\Local\Temp\FileZilla_3.64.0_win64-setup.exe | FileZilla_3.64.0_win64-setup.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: HIGH Description: FileZilla FTP Client Exit code: 0 Version: 3.64.0 Modules
| |||||||||||||||
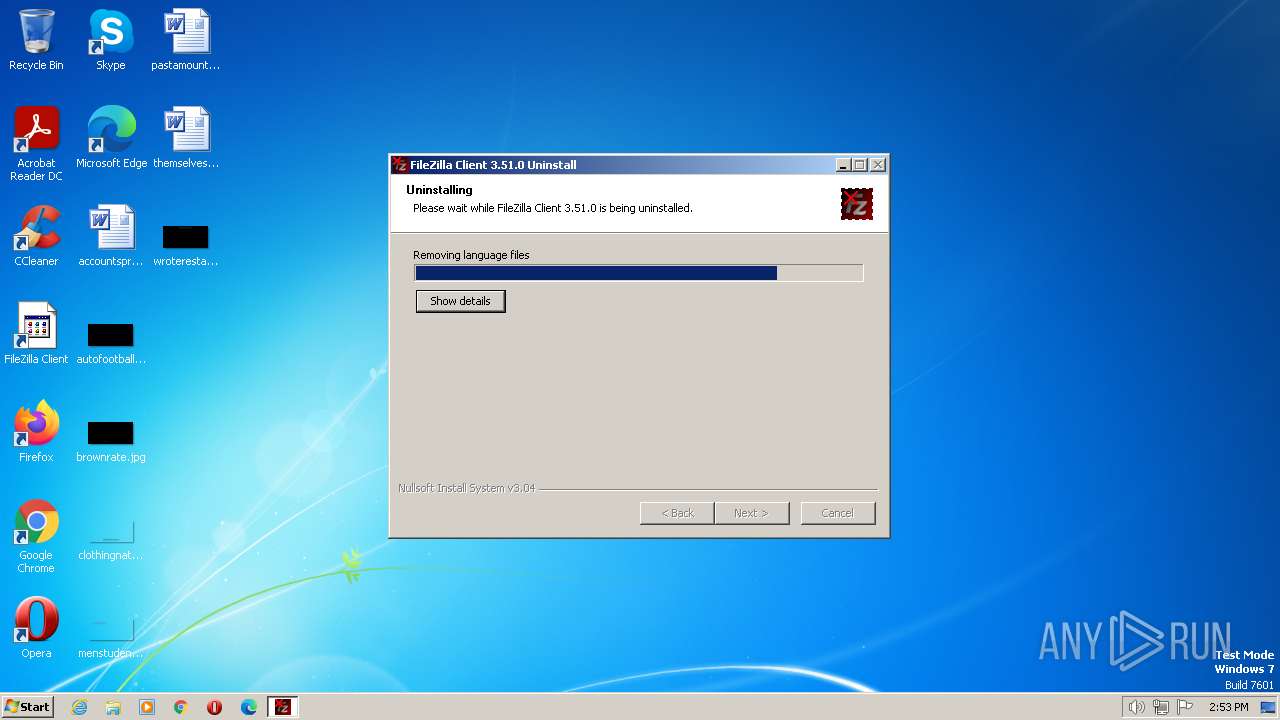
| 3504 | "C:\Program Files\FileZilla FTP Client\uninstall.exe" /frominstall /keepstartmenudir _?=C:\Program Files\FileZilla FTP Client | C:\Program Files\FileZilla FTP Client\uninstall.exe | FileZilla_3.64.0_win64-setup.exe | ||||||||||||
User: admin Company: Tim Kosse Integrity Level: HIGH Description: FileZilla FTP Client Exit code: 0 Version: 3.51.0 Modules
| |||||||||||||||
Total events
2 649
Read events
2 614
Write events
17
Delete events
18
Modification events
| (PID) Process: | (3504) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Directory\shellex\CopyHookHandlers\FileZilla3CopyHook |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3504) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{DB70412E-EEC9-479C-BBA9-BE36BFDDA41B}\InProcServer32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3504) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{DB70412E-EEC9-479C-BBA9-BE36BFDDA41B} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3504) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\FileZilla 3\fzshellext |
| Operation: | delete value | Name: | Enable |
Value: 1 | |||
| (PID) Process: | (3504) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\FileZilla 3\fzshellext |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3504) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\FileZilla 3 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3504) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 104 | |||
| (PID) Process: | (3504) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 105 | |||
| (PID) Process: | (3504) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 106 | |||
| (PID) Process: | (3504) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Windows\TEMP\MicrosoftEdgeUpdate.exe4b51 | |||
Executable files
37
Suspicious files
124
Text files
690
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3500 | FileZilla_3.64.0_win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsb2A27.tmp\UAC.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
| 3500 | FileZilla_3.64.0_win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsb2A27.tmp\System.dll | executable | |
MD5:564BB0373067E1785CBA7E4C24AAB4BF | SHA256:7A9DDEE34562CD3703F1502B5C70E99CD5BBA15DE2B6845A3555033D7F6CB2A5 | |||
| 3504 | uninstall.exe | C:\Users\admin\AppData\Local\Temp\nsc4698.tmp\UserInfo.dll | executable | |
MD5:9EB662F3B5FBDA28BFFE020E0AB40519 | SHA256:9AA388C7DE8E96885ADCB4325AF871B470AC50EDB60D4B0D876AD43F5332FFD1 | |||
| 1132 | FileZilla_3.64.0_win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsx615.tmp\System.dll | executable | |
MD5:564BB0373067E1785CBA7E4C24AAB4BF | SHA256:7A9DDEE34562CD3703F1502B5C70E99CD5BBA15DE2B6845A3555033D7F6CB2A5 | |||
| 1132 | FileZilla_3.64.0_win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsx615.tmp\UserInfo.dll | executable | |
MD5:98FF85B635D9114A9F6A0CD7B9B649D0 | SHA256:933F93A30CE44DF96CBC4AC0B56A8B02EE01DA27E4EA665D1D846357A8FCA8DE | |||
| 3500 | FileZilla_3.64.0_win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsb2A27.tmp\nsDialogs.dll | executable | |
MD5:48F3E7860E1DE2B4E63EC744A5E9582A | SHA256:6BF9CCCD8A600F4D442EFE201E8C07B49605BA35F49A4B3AB22FA2641748E156 | |||
| 3504 | uninstall.exe | C:\Users\admin\AppData\Local\Temp\nsc4698.tmp\UAC.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
| 3504 | uninstall.exe | C:\Users\admin\AppData\Local\Temp\nsc4698.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3500 | FileZilla_3.64.0_win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsb2A27.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3504 | uninstall.exe | C:\Users\admin\AppData\Local\Temp\nsn4688.tmp | binary | |
MD5:6BC4A8D48B7247DDB3A81FB363E967B8 | SHA256:6D601EBBFA6448DB2020162BFD871D78691EB87F5FA671207A41B954068DA2D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3388 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1096 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Threats
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|