| File name: | cloud.bat |
| Full analysis: | https://app.any.run/tasks/b8b2df47-d249-49c7-b543-99614ab6c0d7 |
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2024, 13:17:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (64784), with CRLF line terminators |
| MD5: | 84935458038752E9A471CE410633B305 |
| SHA1: | 6F19C2AAA32341671A4DE0019BF3B2ED183646F1 |
| SHA256: | 0D8F1B4826DBA6E14FAF2C0DFAFABFC6885919B498EF540C8339B9EC693B8B1F |
| SSDEEP: | 12288:QTkLvTKCCAMsY1zKJyV3CfED9Nvlqd0sYwKFPlUvFNGP3kU2/UB:QYqvhQwkO9FlfTcNcXaUB |
MALICIOUS
No malicious indicators.SUSPICIOUS
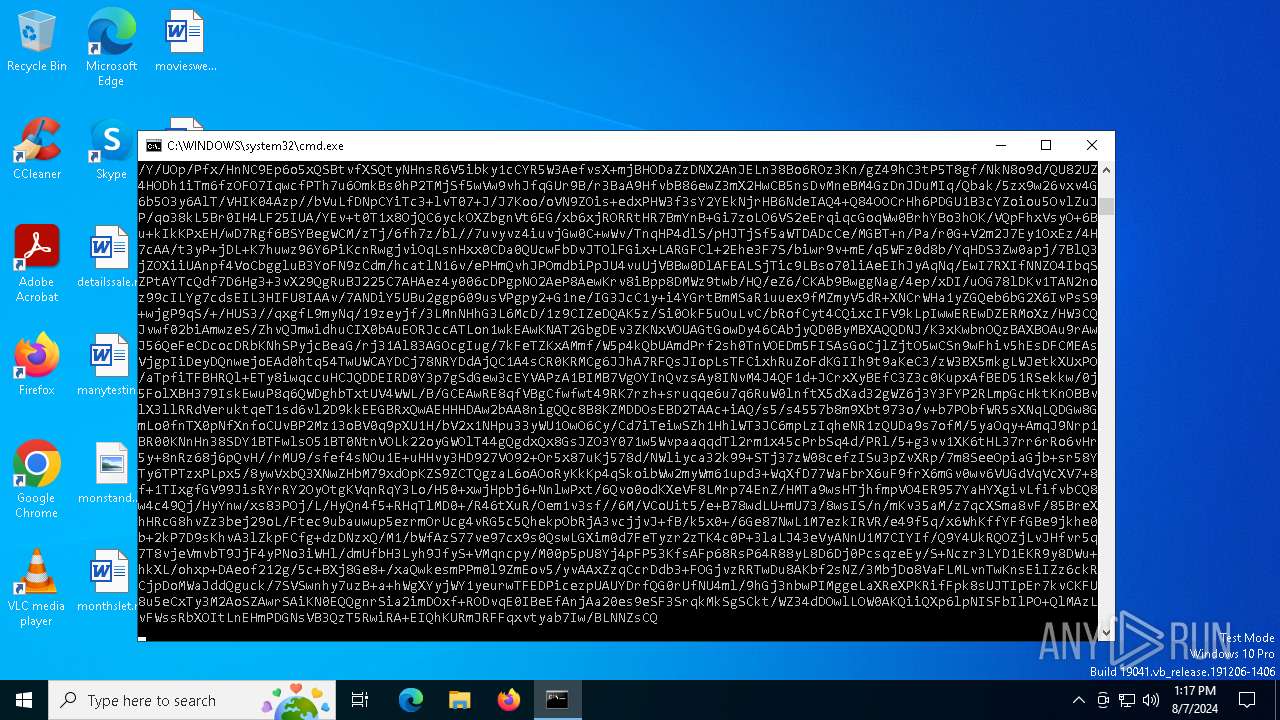
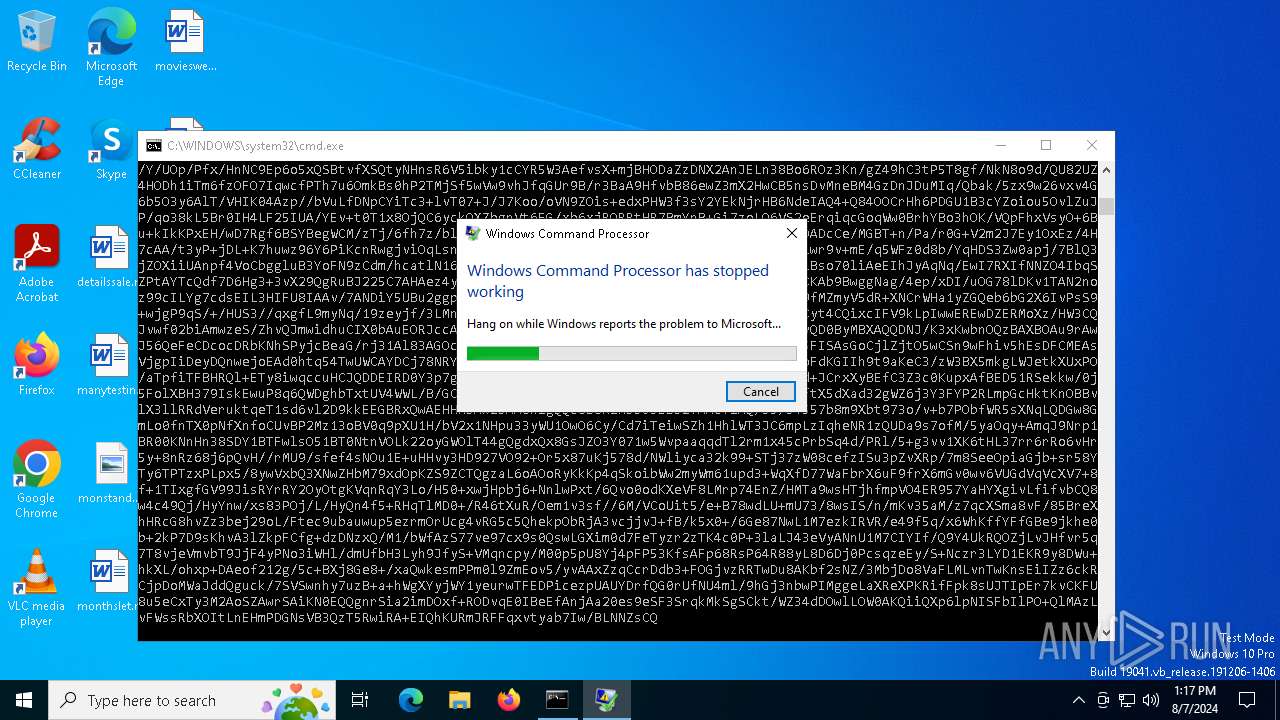
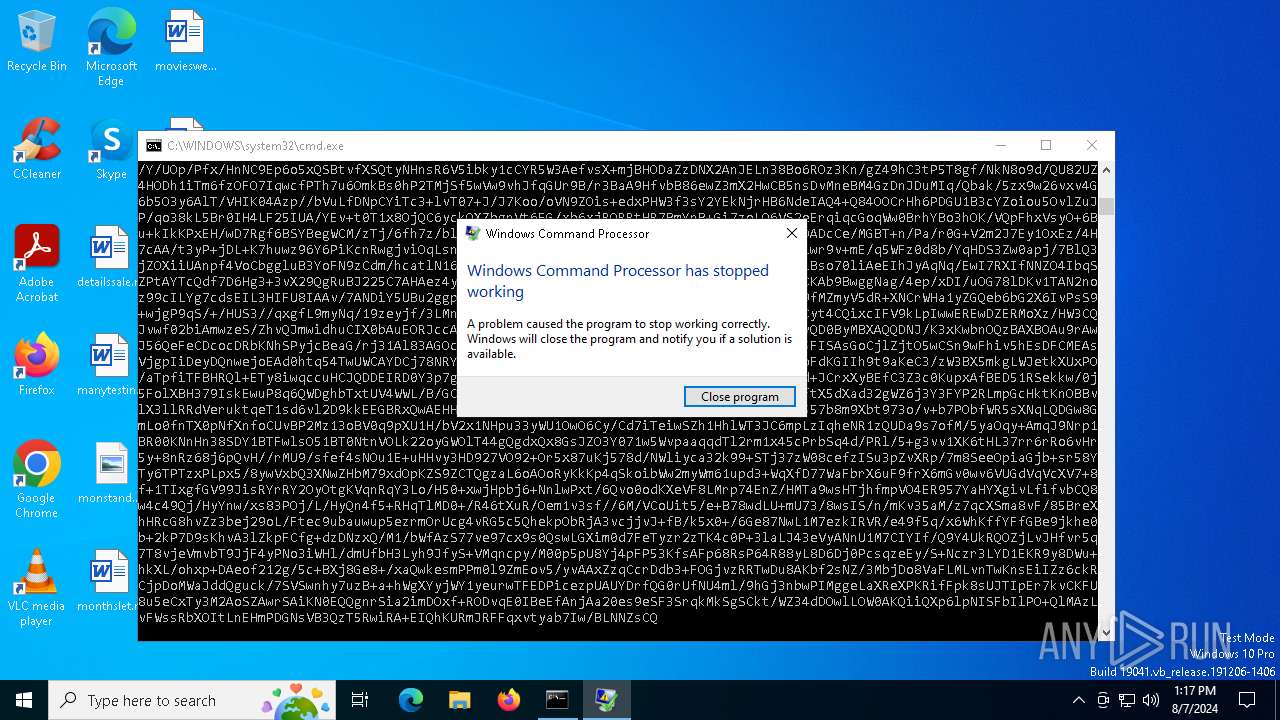
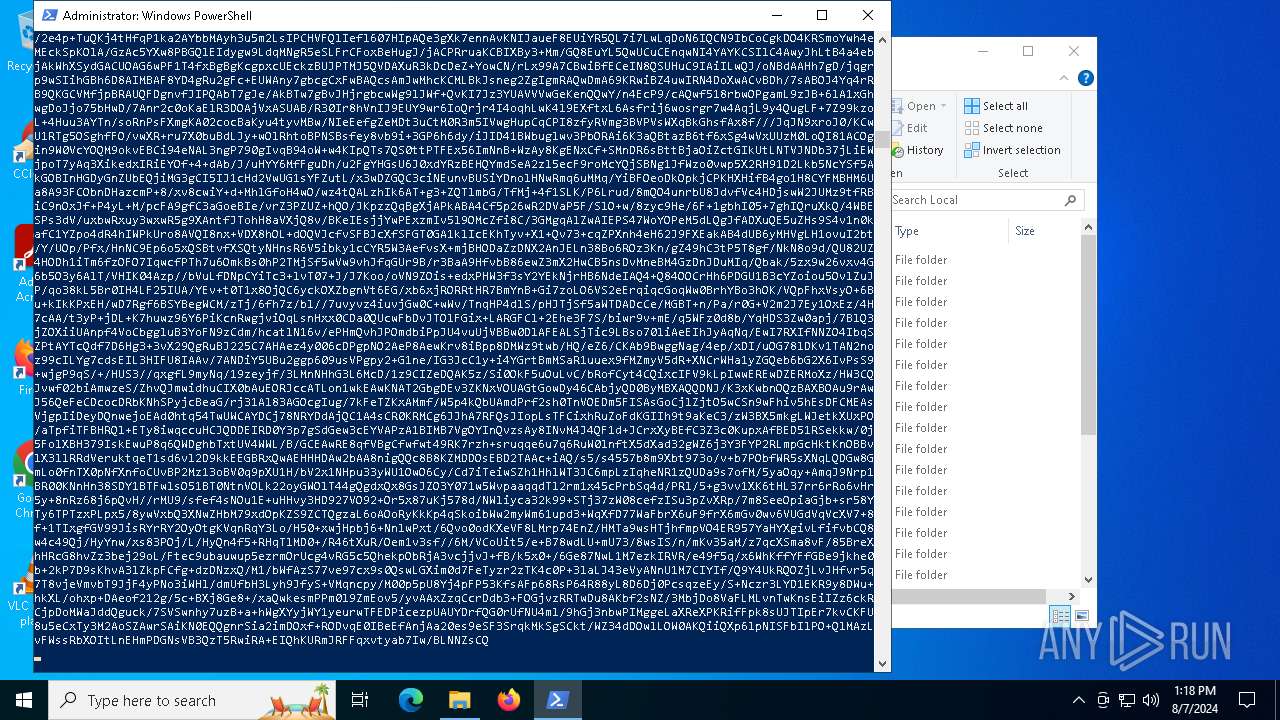
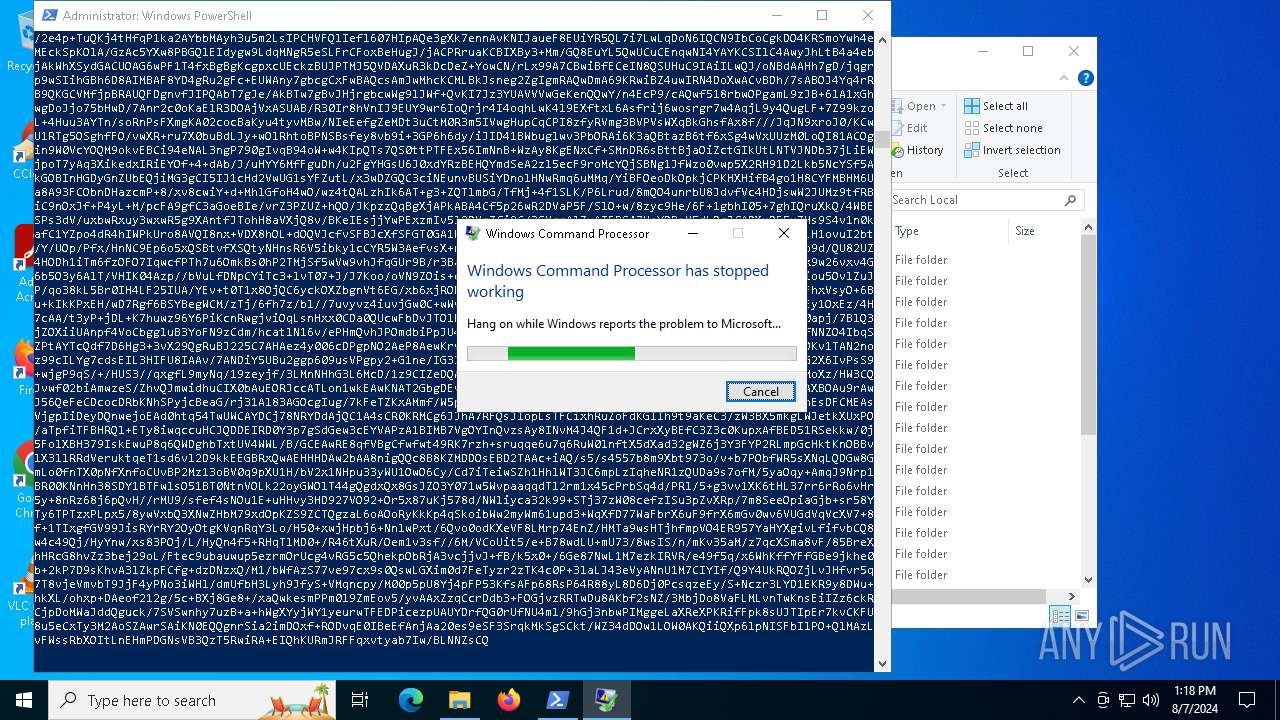
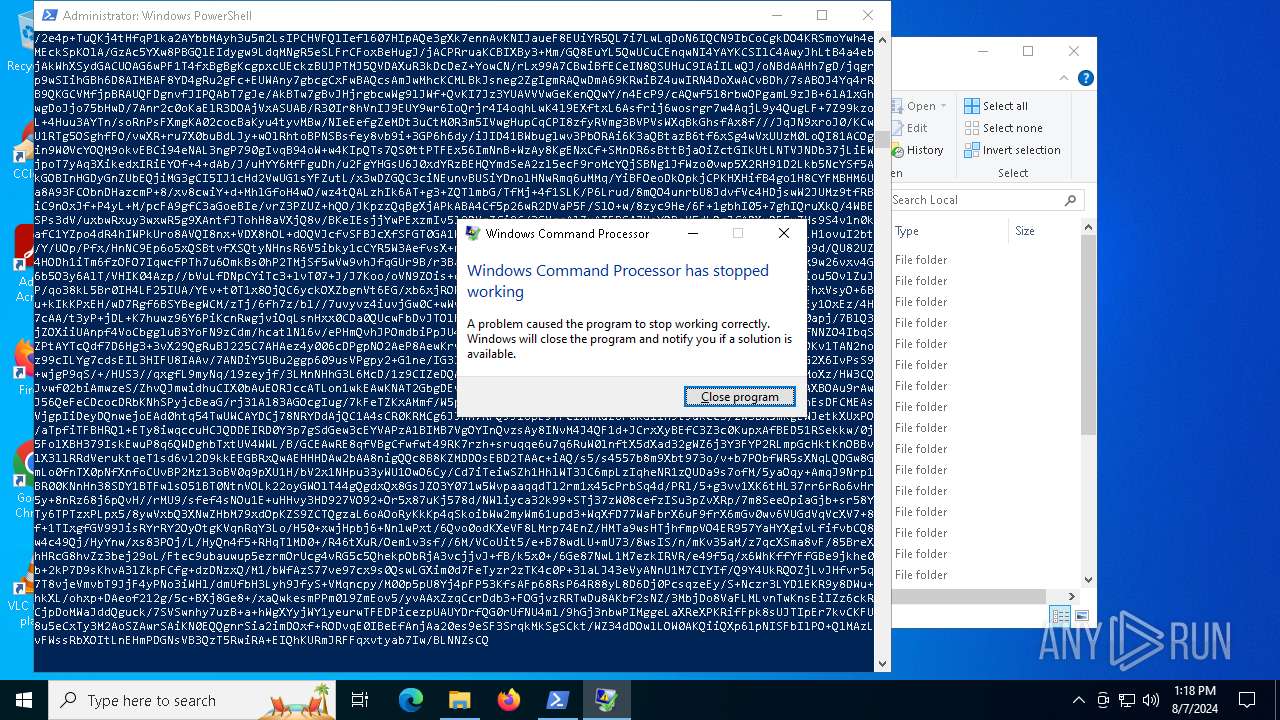
Executes application which crashes
- cmd.exe (PID: 6388)
- cmd.exe (PID: 5400)
The process creates files with name similar to system file names
- WerFault.exe (PID: 6600)
- WerFault.exe (PID: 3036)
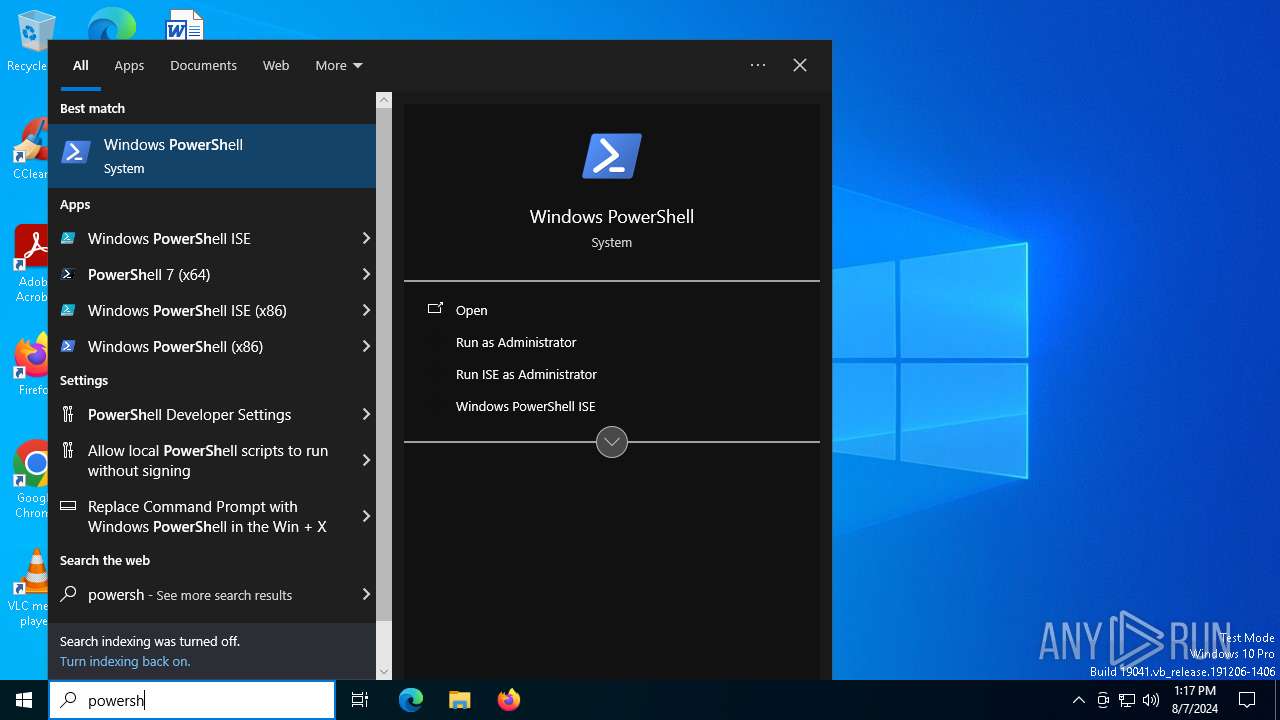
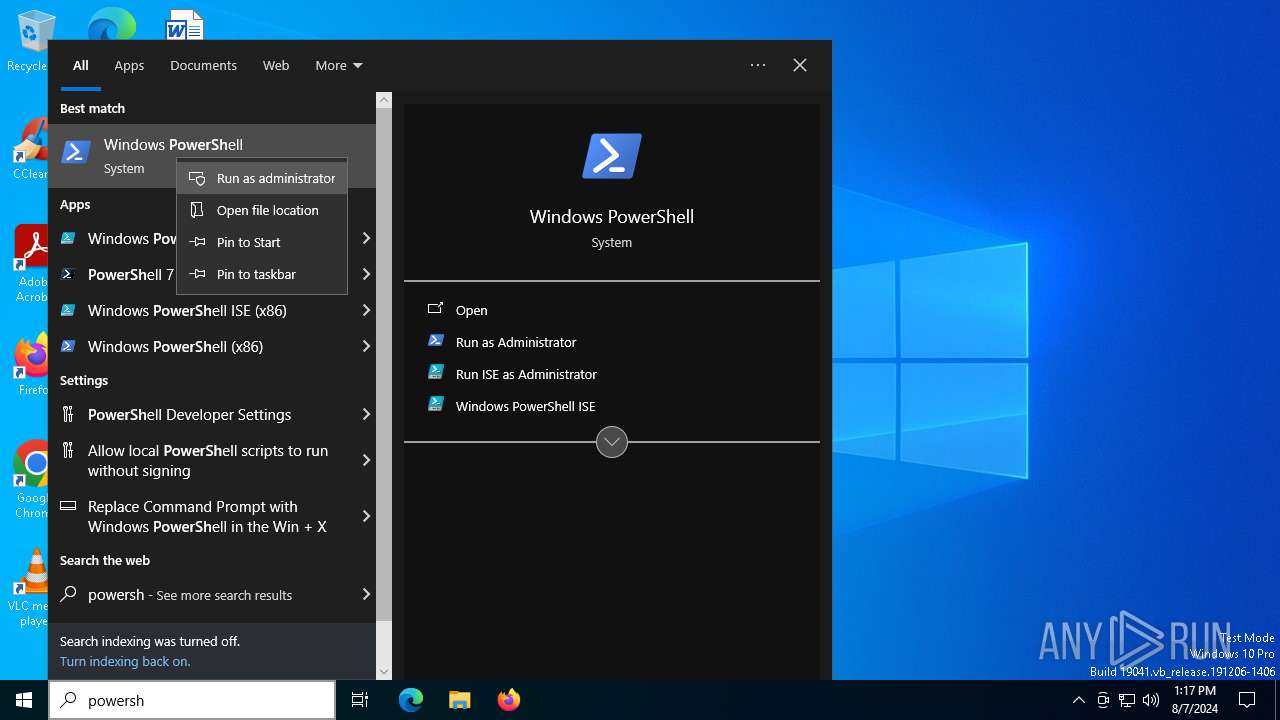
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7124)
Executing commands from a ".bat" file
- powershell.exe (PID: 7124)
INFO
Reads the software policy settings
- WerFault.exe (PID: 6600)
- WerFault.exe (PID: 3036)
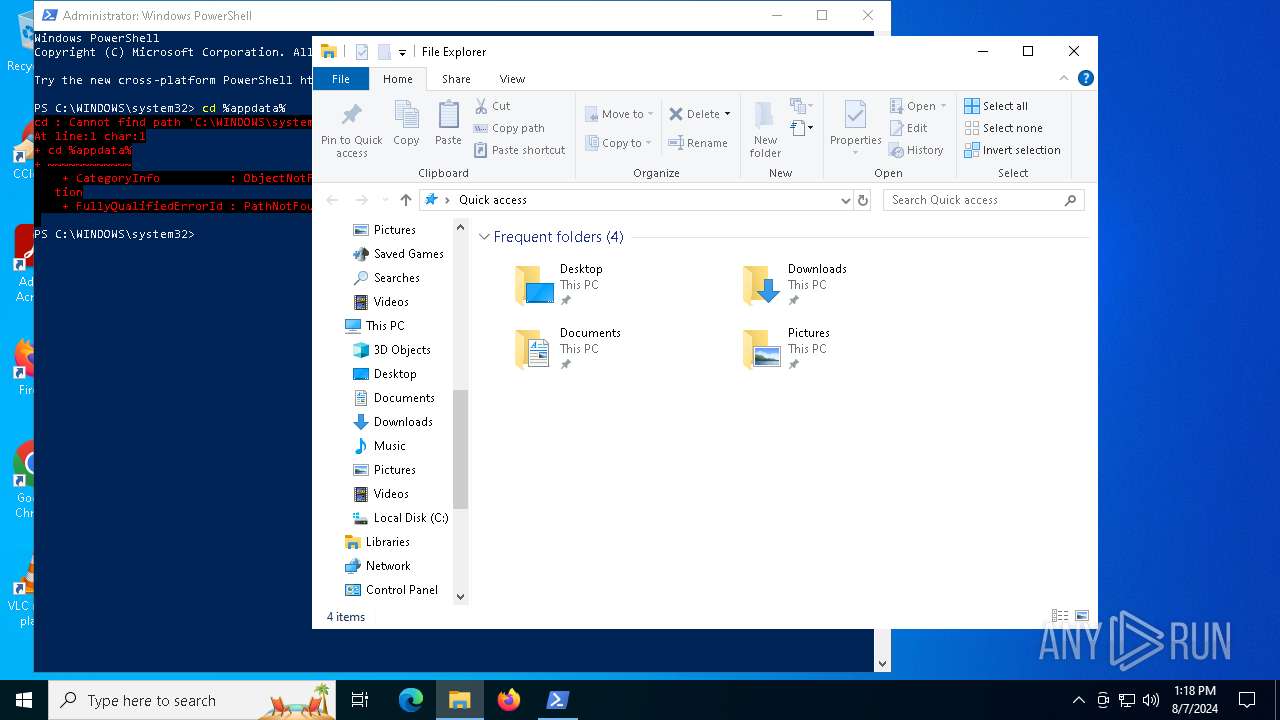
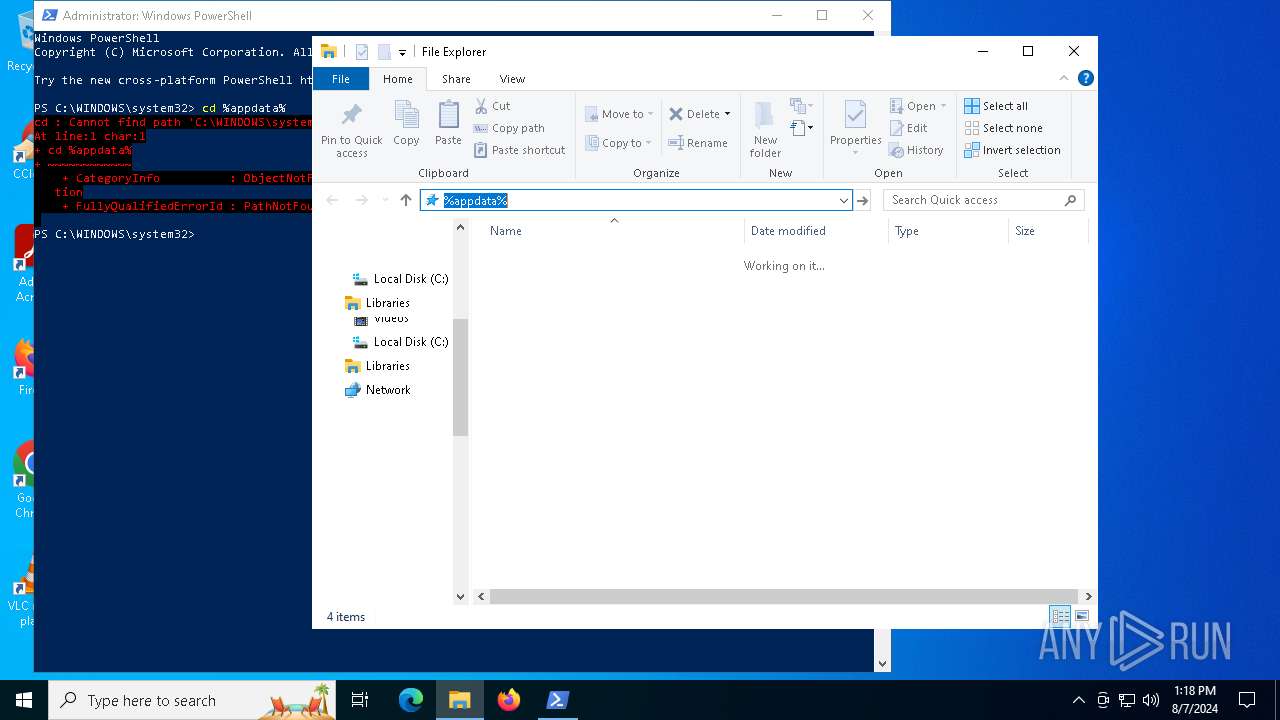
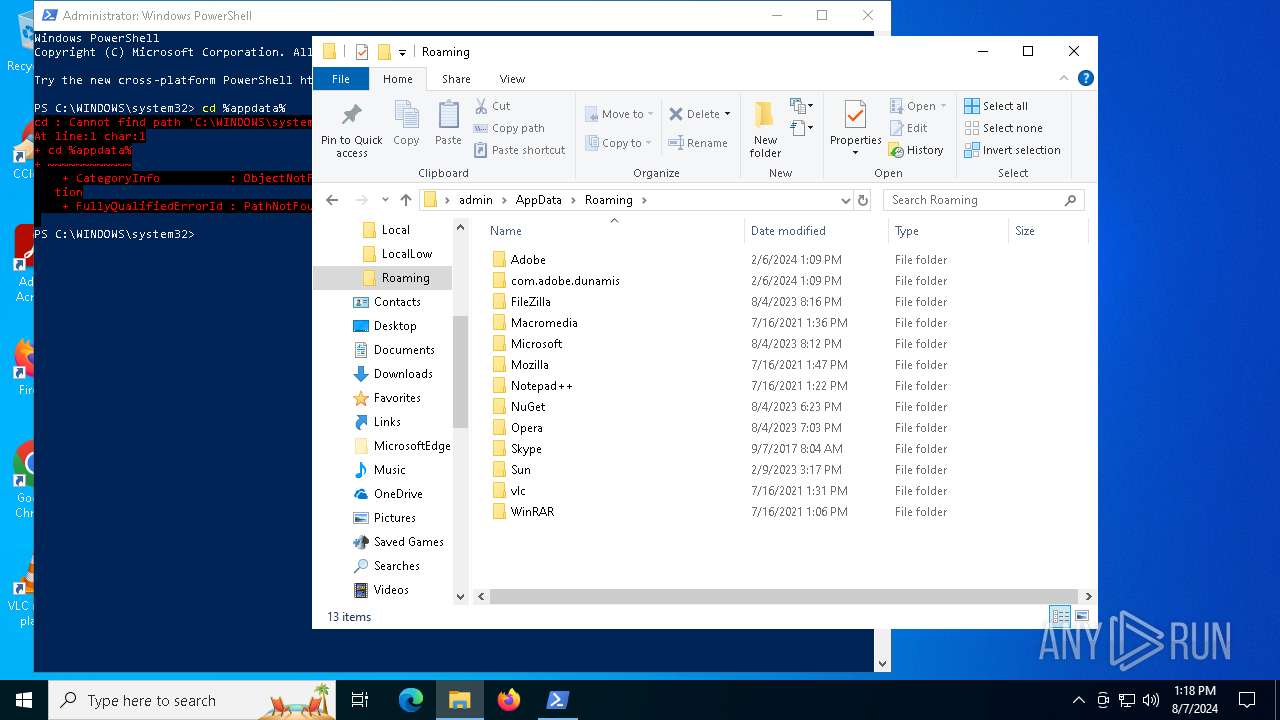
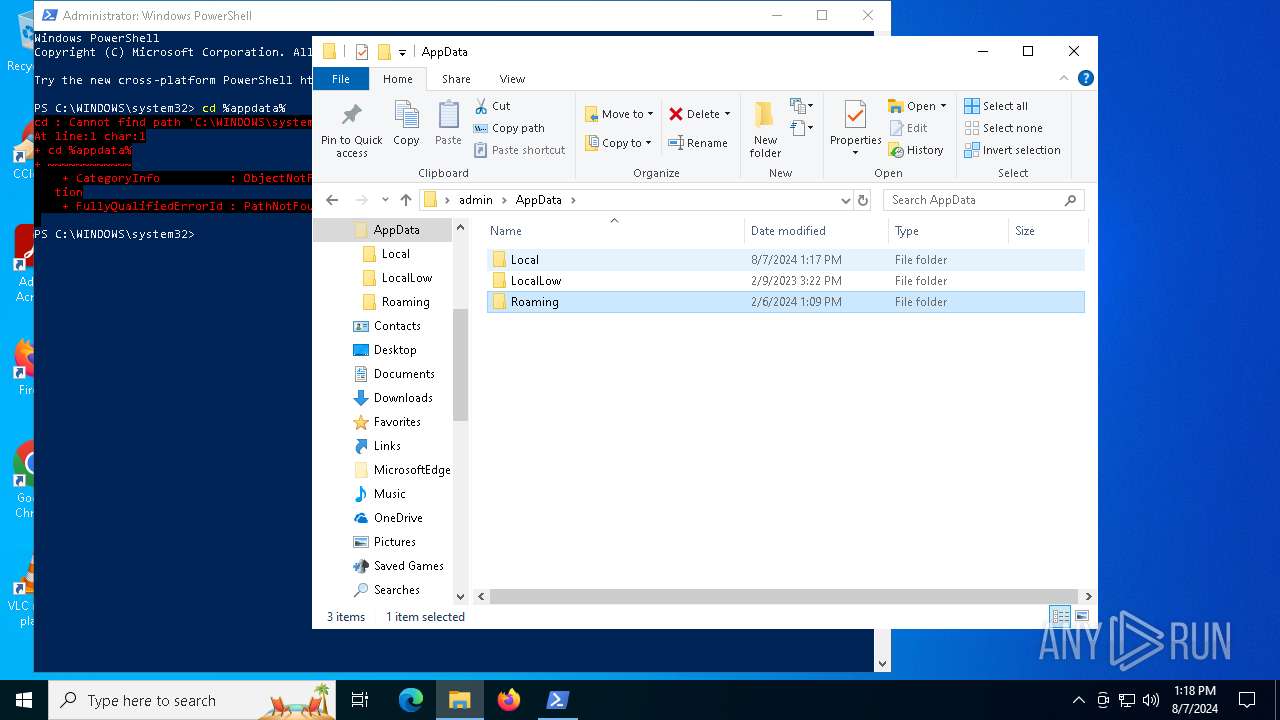
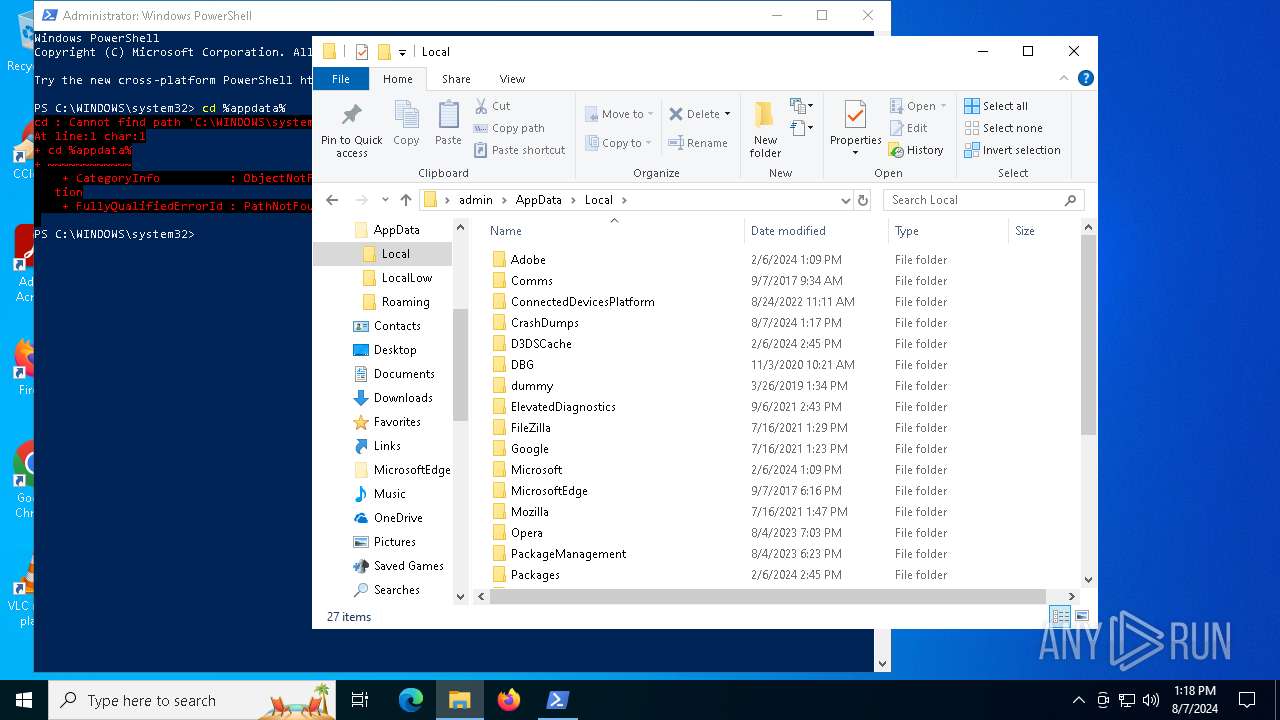
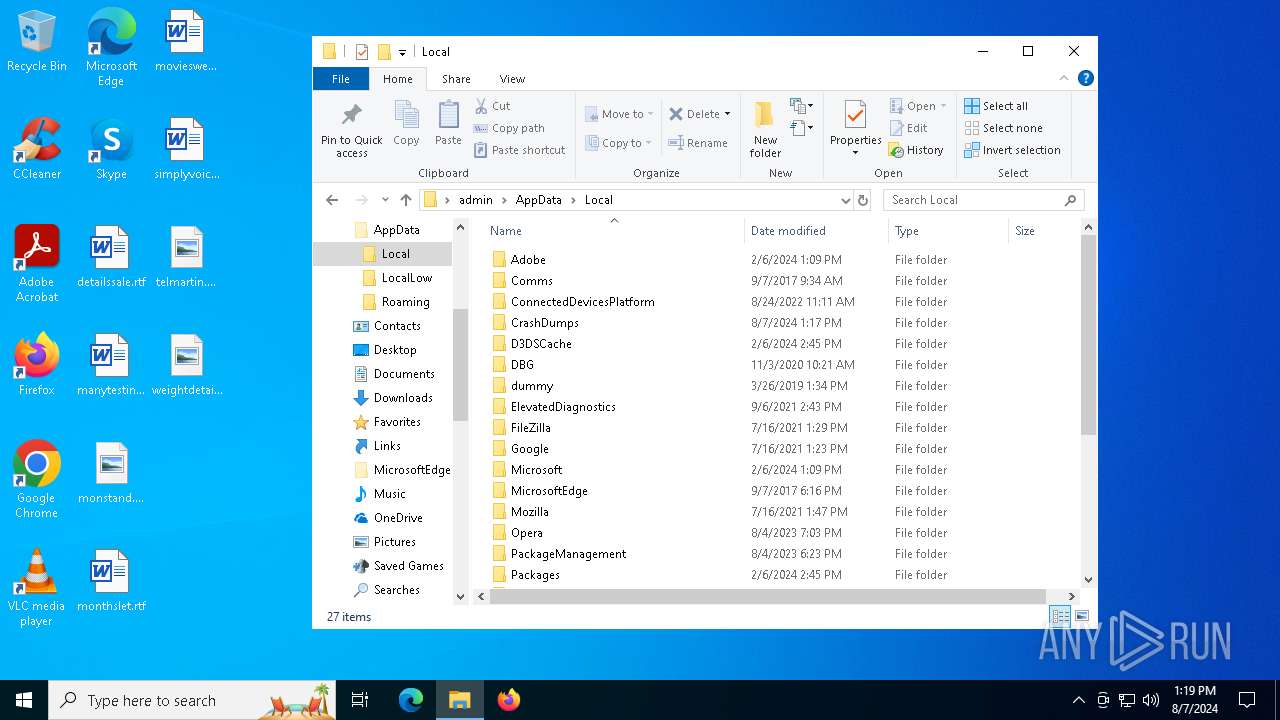
Creates files or folders in the user directory
- WerFault.exe (PID: 6600)
- WerFault.exe (PID: 3036)
Checks proxy server information
- WerFault.exe (PID: 6600)
- WerFault.exe (PID: 3036)
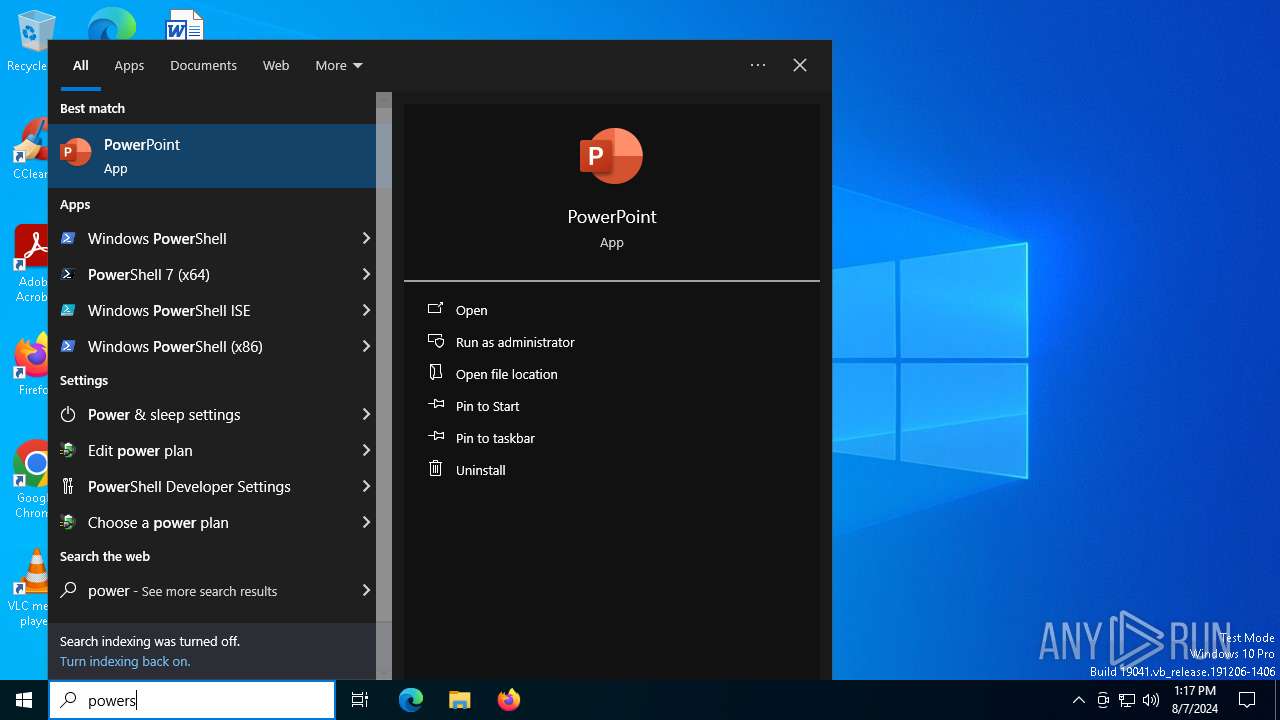
Manual execution by a user
- powershell.exe (PID: 7124)
Checks supported languages
- TextInputHost.exe (PID: 5880)
Reads the computer name
- TextInputHost.exe (PID: 5880)
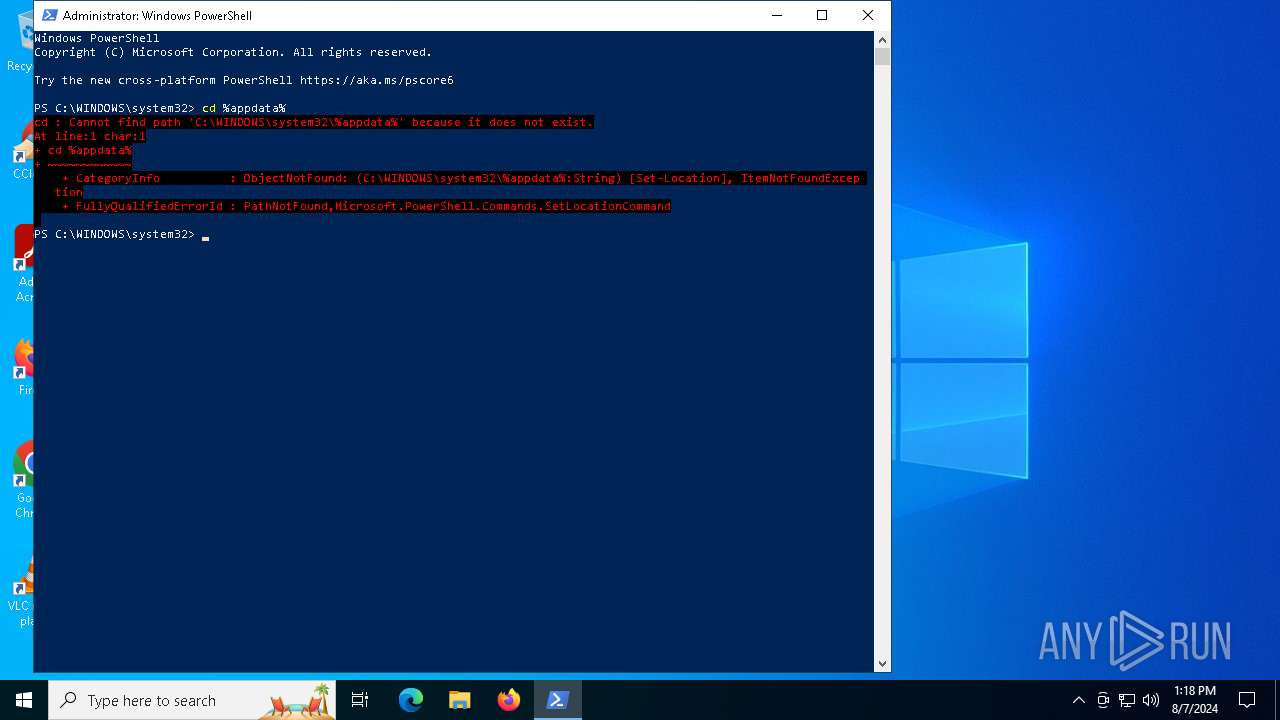
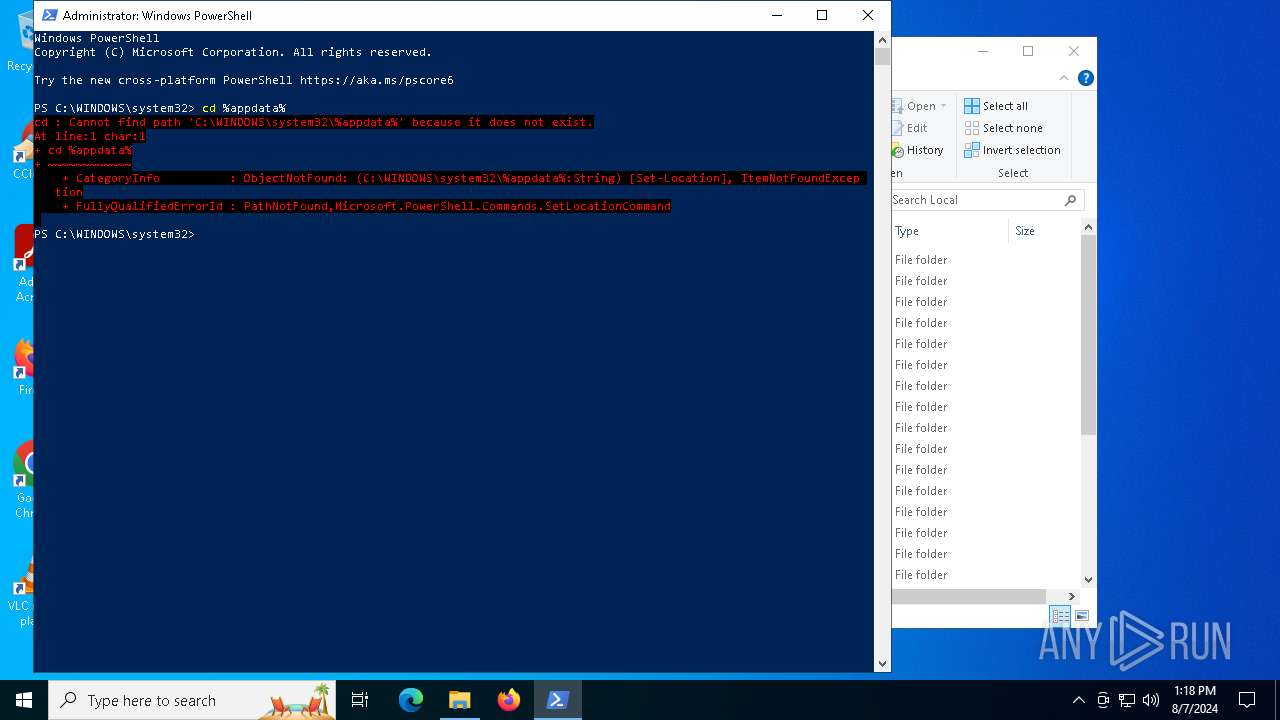
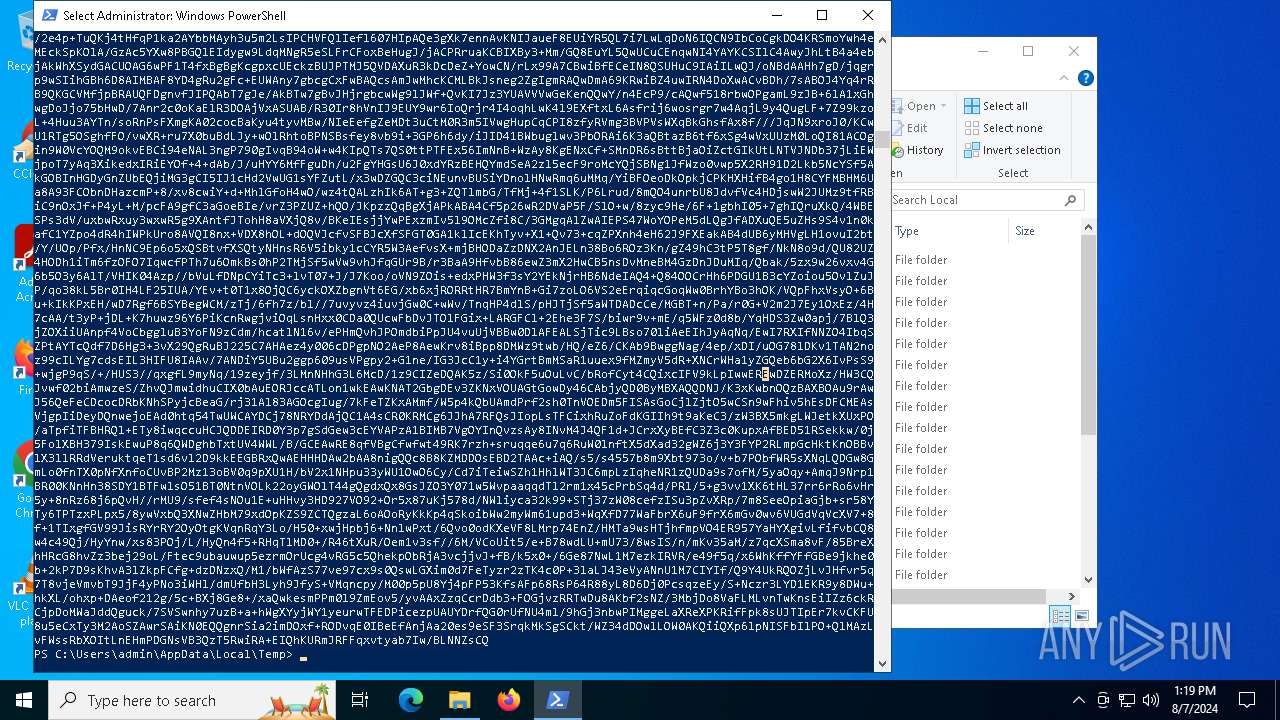
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7124)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
151
Monitored processes
9
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1216 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3036 | C:\WINDOWS\system32\WerFault.exe -u -p 5400 -s 312 | C:\Windows\System32\WerFault.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5180 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5400 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\cloud.bat"" | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221226505 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5880 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 6388 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\cloud.bat" " | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221226505 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6396 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6600 | C:\WINDOWS\system32\WerFault.exe -u -p 6388 -s 324 | C:\Windows\System32\WerFault.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
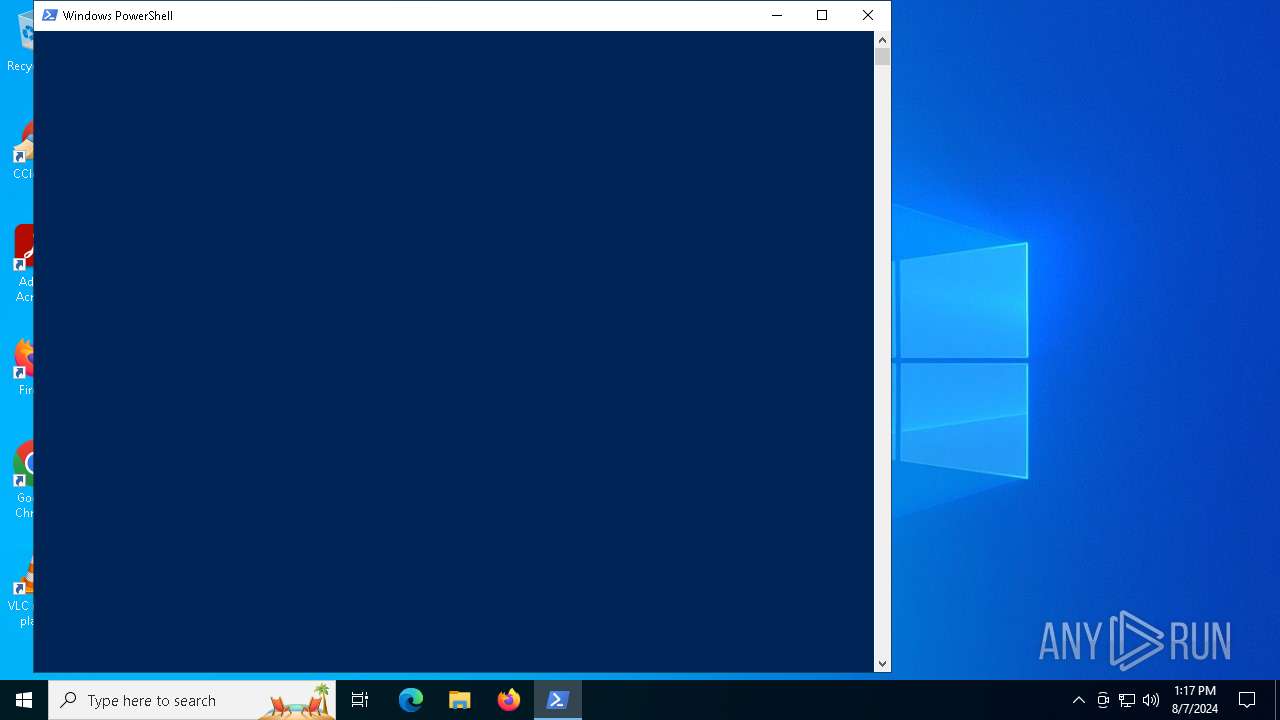
| 7124 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 381
Read events
22 340
Write events
35
Delete events
6
Modification events
| (PID) Process: | (7124) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7124) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7124) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7124) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3036) WerFault.exe | Key: | \REGISTRY\A\{9d605dac-1a83-10f8-48ad-8ba95b1ec921}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (3036) WerFault.exe | Key: | \REGISTRY\A\{9d605dac-1a83-10f8-48ad-8ba95b1ec921}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3036) WerFault.exe | Key: | \REGISTRY\A\{9d605dac-1a83-10f8-48ad-8ba95b1ec921}\Root\InventoryApplicationFile\cmd.exe|5ce9ba8d0d54ad10 |
| Operation: | write | Name: | ProgramId |
Value: 0000f519feec486de87ed73cb92d3cac802400000000 | |||
| (PID) Process: | (3036) WerFault.exe | Key: | \REGISTRY\A\{9d605dac-1a83-10f8-48ad-8ba95b1ec921}\Root\InventoryApplicationFile\cmd.exe|5ce9ba8d0d54ad10 |
| Operation: | write | Name: | FileId |
Value: 0000e9be2f86e3a3bff02d1953aeccf0ed22284596d4 | |||
| (PID) Process: | (3036) WerFault.exe | Key: | \REGISTRY\A\{9d605dac-1a83-10f8-48ad-8ba95b1ec921}\Root\InventoryApplicationFile\cmd.exe|5ce9ba8d0d54ad10 |
| Operation: | write | Name: | LowerCaseLongPath |
Value: c:\windows\system32\cmd.exe | |||
| (PID) Process: | (3036) WerFault.exe | Key: | \REGISTRY\A\{9d605dac-1a83-10f8-48ad-8ba95b1ec921}\Root\InventoryApplicationFile\cmd.exe|5ce9ba8d0d54ad10 |
| Operation: | write | Name: | LongPathHash |
Value: cmd.exe|5ce9ba8d0d54ad10 | |||
Executable files
0
Suspicious files
8
Text files
7
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6600 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_cmd.exe_987f19a6bdad36f4813e8b6b834b54dde12831_cefa1fcf_58f1e53a-6b66-48e5-b637-a92d595ed733\Report.wer | — | |
MD5:— | SHA256:— | |||
| 3036 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_cmd.exe_987f19a6bdad36f4813e8b6b834b54dde12831_cefa1fcf_ac0251b7-7b33-49f5-959e-7a59b56fff1b\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7124 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pi0jzelr.ual.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7124 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RFedb87.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6600 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER687C.tmp.xml | xml | |
MD5:FBADE193D2171CE0C8DEC791DA0BE311 | SHA256:8E0FE8D70891B582C58FF52856EBBEF2728CC702E9DF68CF3D55A5F46FEB7E86 | |||
| 6600 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FB64A9EBEDF48D3895381D5B7D80743D | SHA256:EA21D495930AD76F267A33A0F593DBF0C7EA75E457FCAE49A29DAAD8BD920F42 | |||
| 6600 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:82C30E45BF5F93A5DB1D5E47F913053B | SHA256:2C6BBFF9207065E8800C4AF0CB2748818ABB3CFFC0D6D518FE17F76A232F8967 | |||
| 6600 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\cmd.exe.6388.dmp | dmp | |
MD5:AE6BEA309CD011E986604B6202F175C5 | SHA256:49C953DE73AF637CB7BCCB6C90B5B44F036B0818402175015B6CCDCCB12F2500 | |||
| 7124 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rf1yase2.hfu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3036 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\cmd.exe.5400.dmp | binary | |
MD5:0CE42082A1AAC0BDAC2807F6D2E4CAF3 | SHA256:9E203178D47EC089508046A602D1FBC400D8B0AE9542EFCA801D8CC35EDE7B2D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
51
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3900 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3900 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6912 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
6960 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1792 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4056 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6600 | WerFault.exe | 20.189.173.21:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1792 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 2.23.209.176:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |