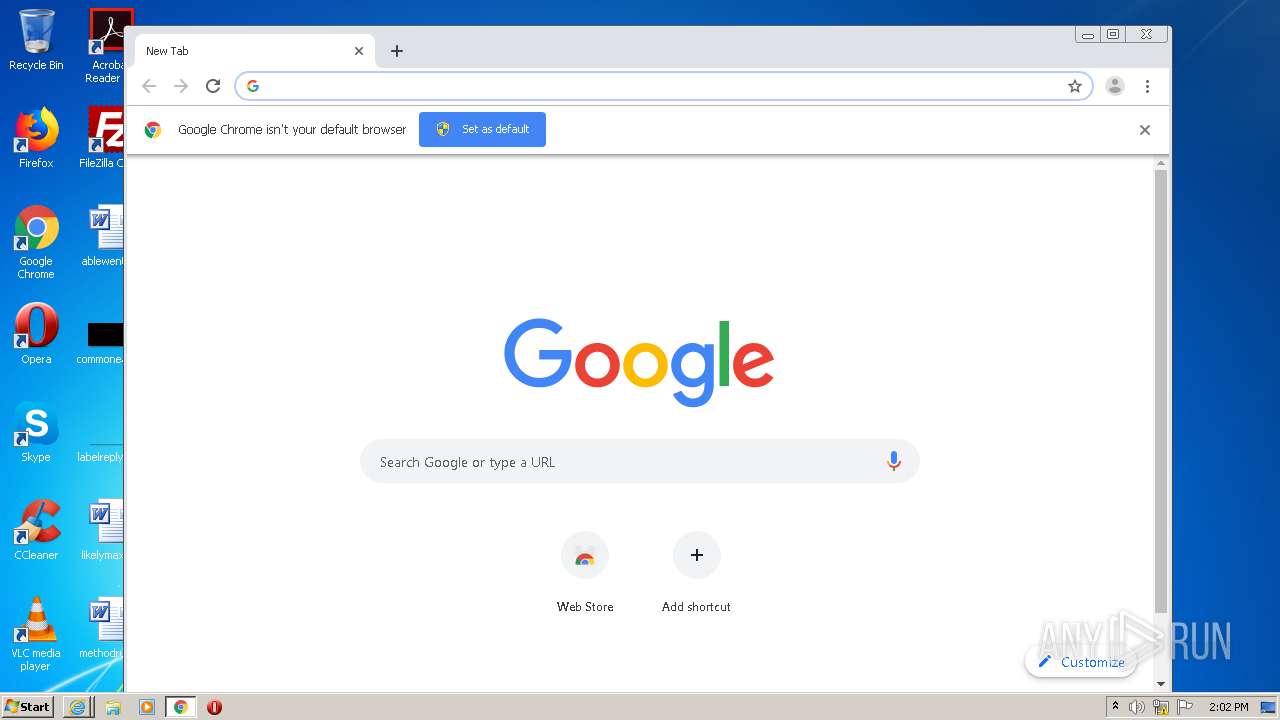
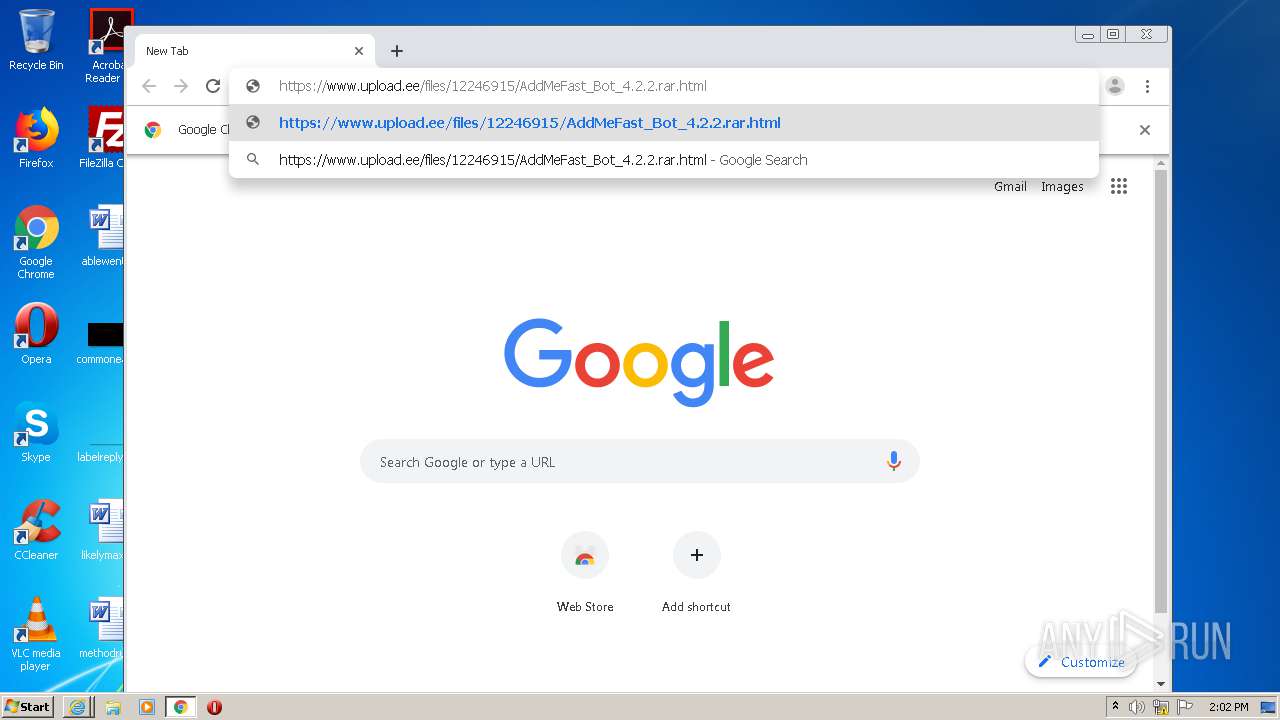
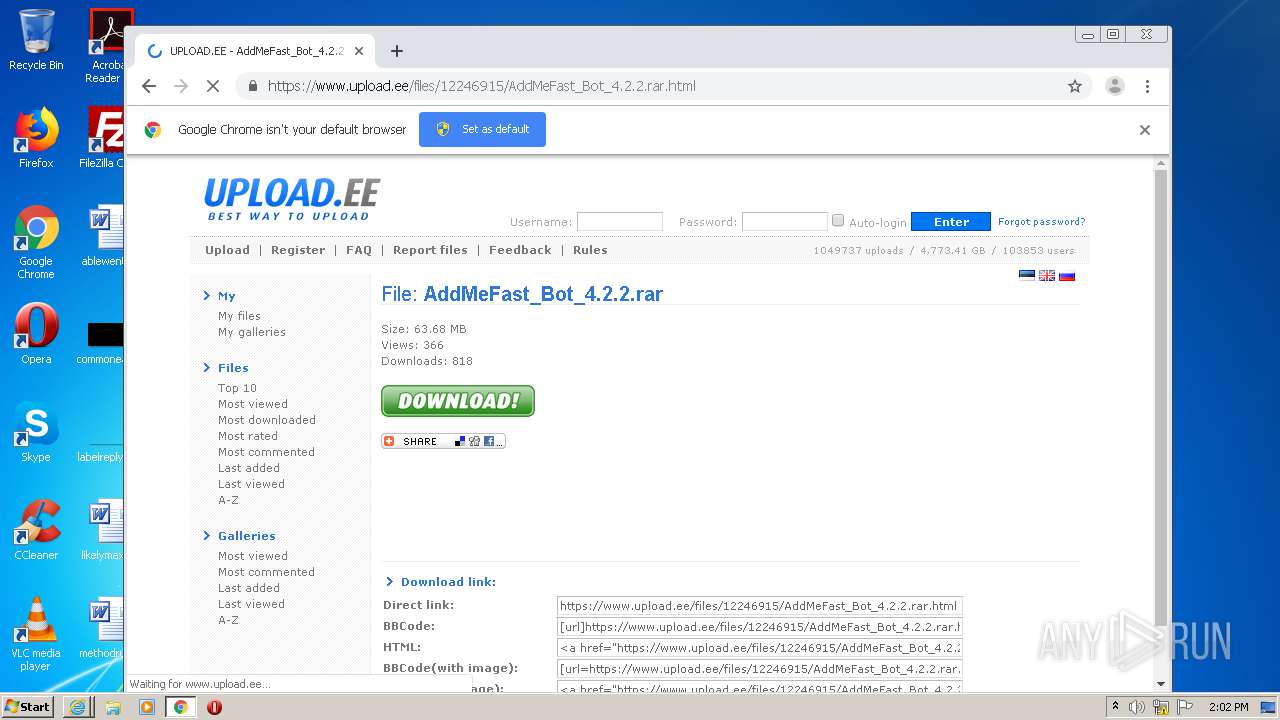
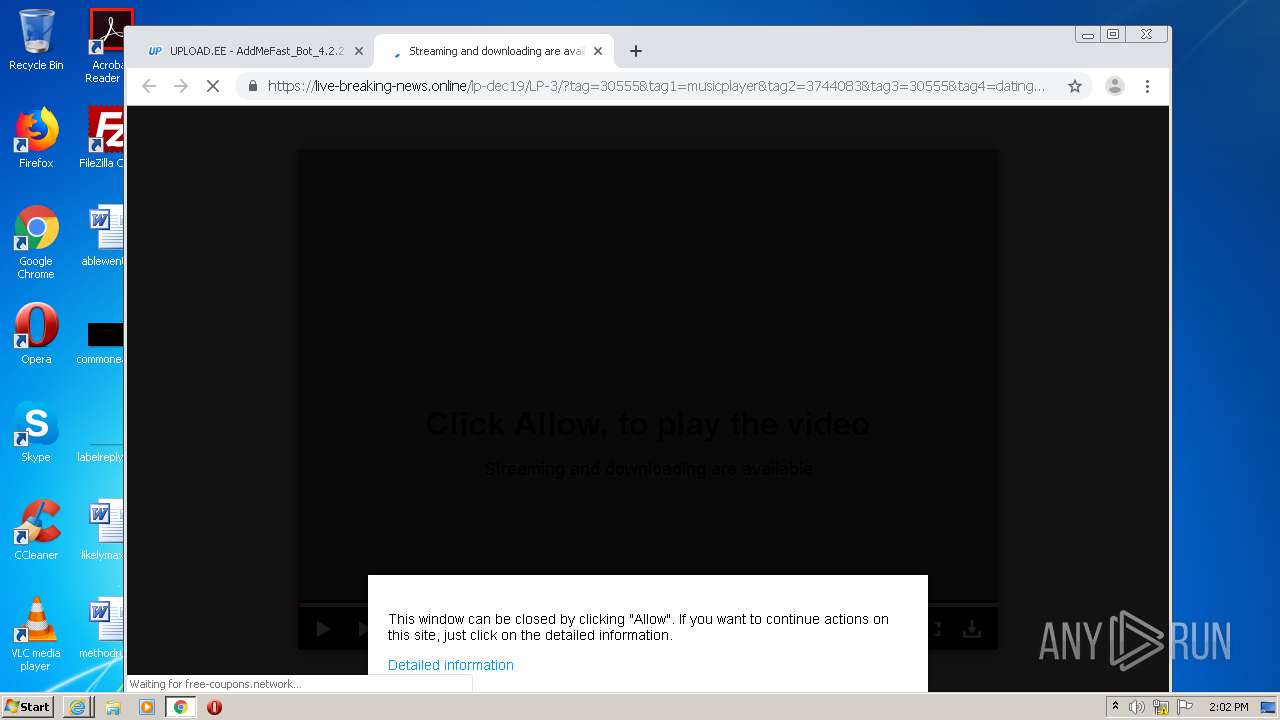
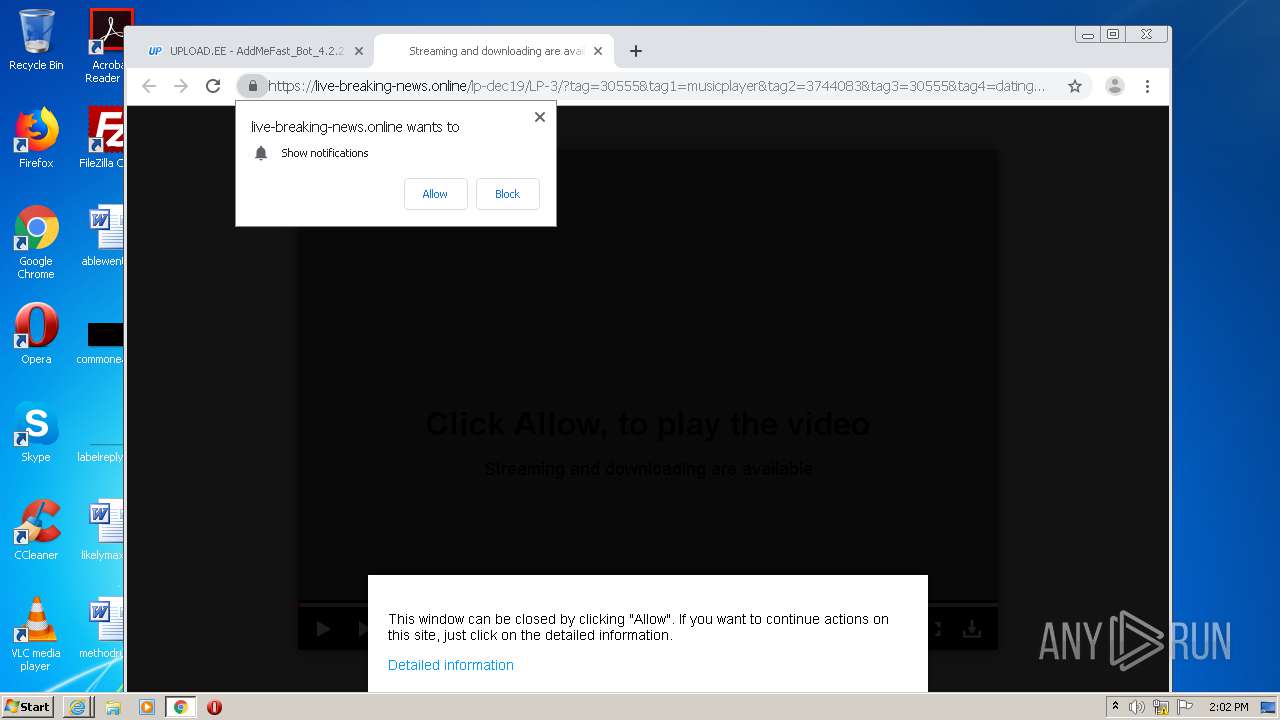
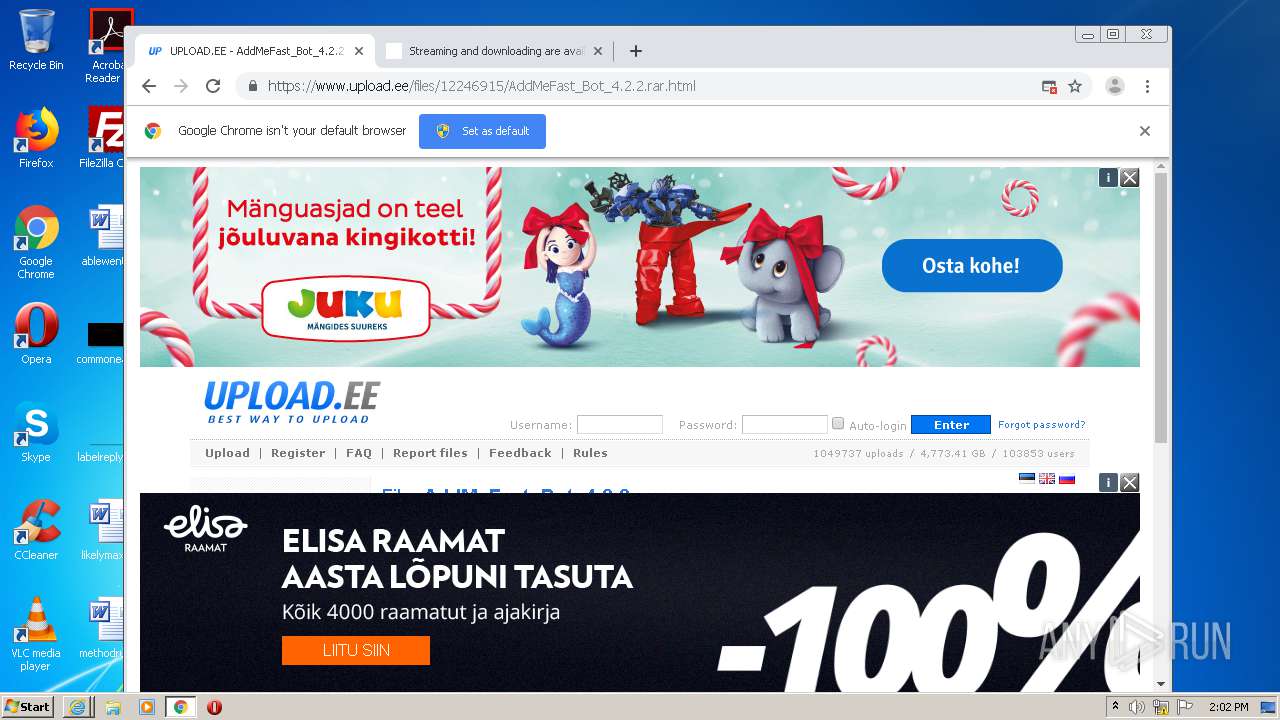
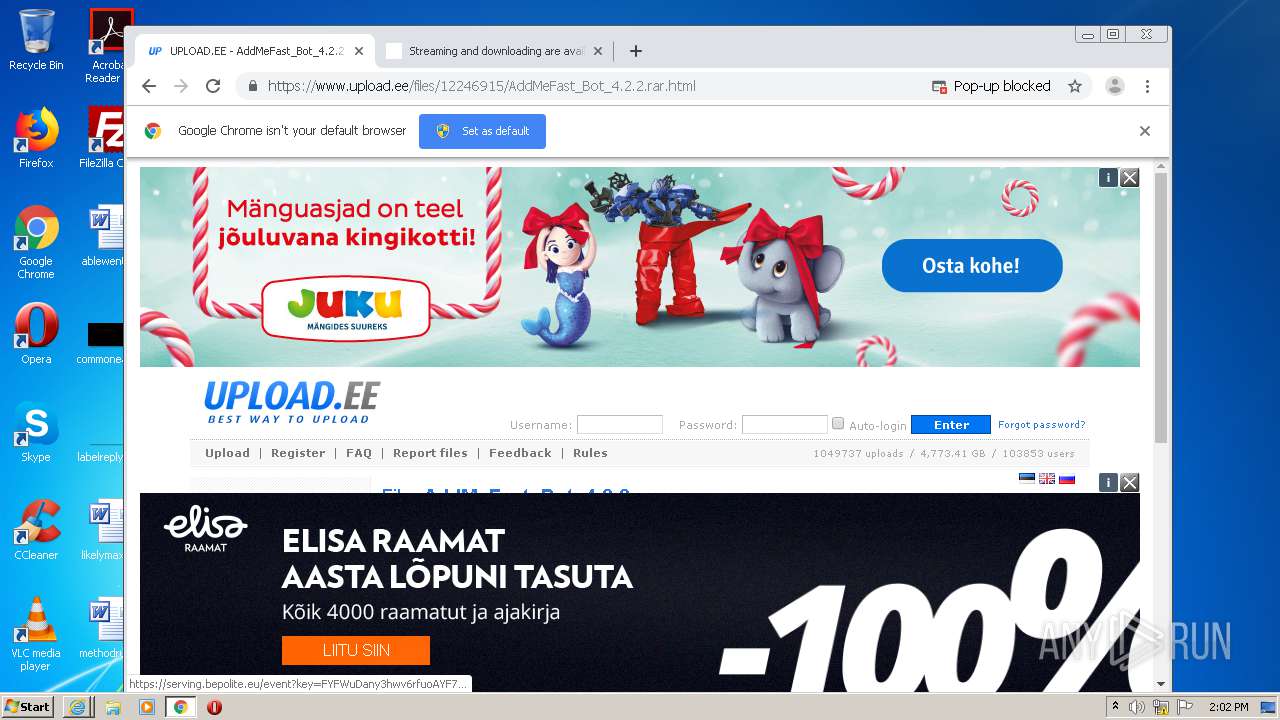
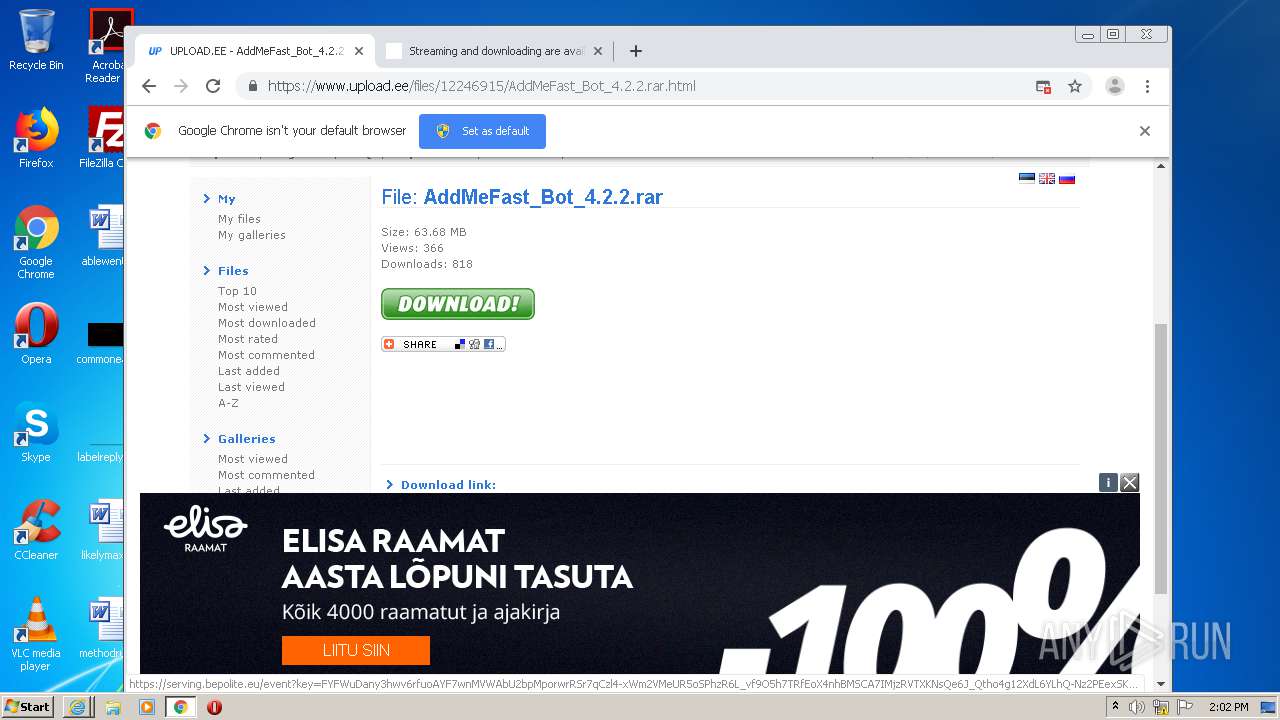
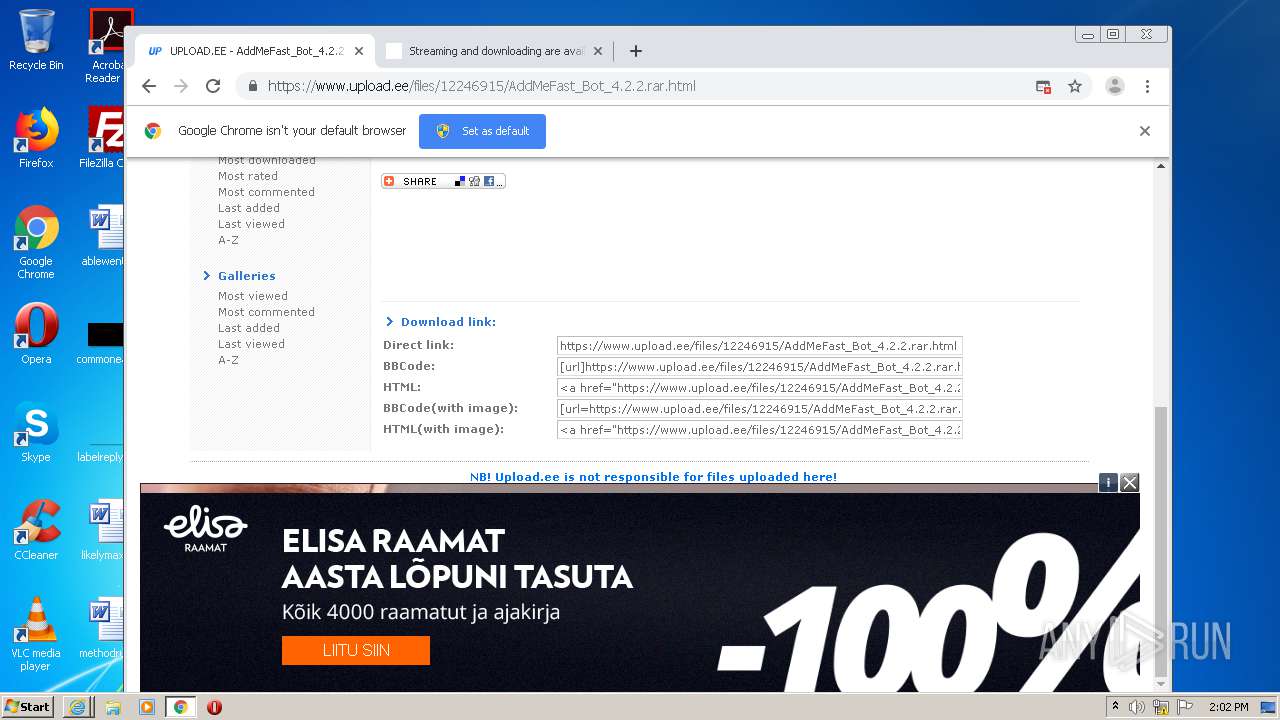
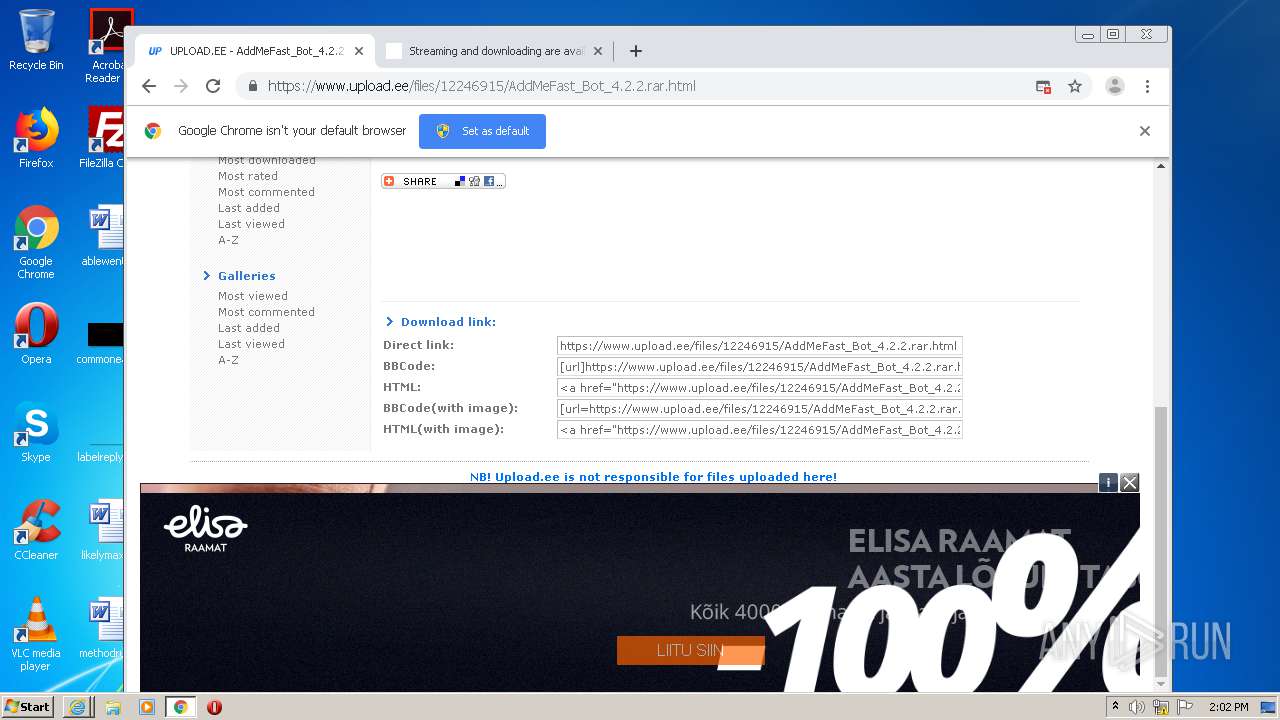
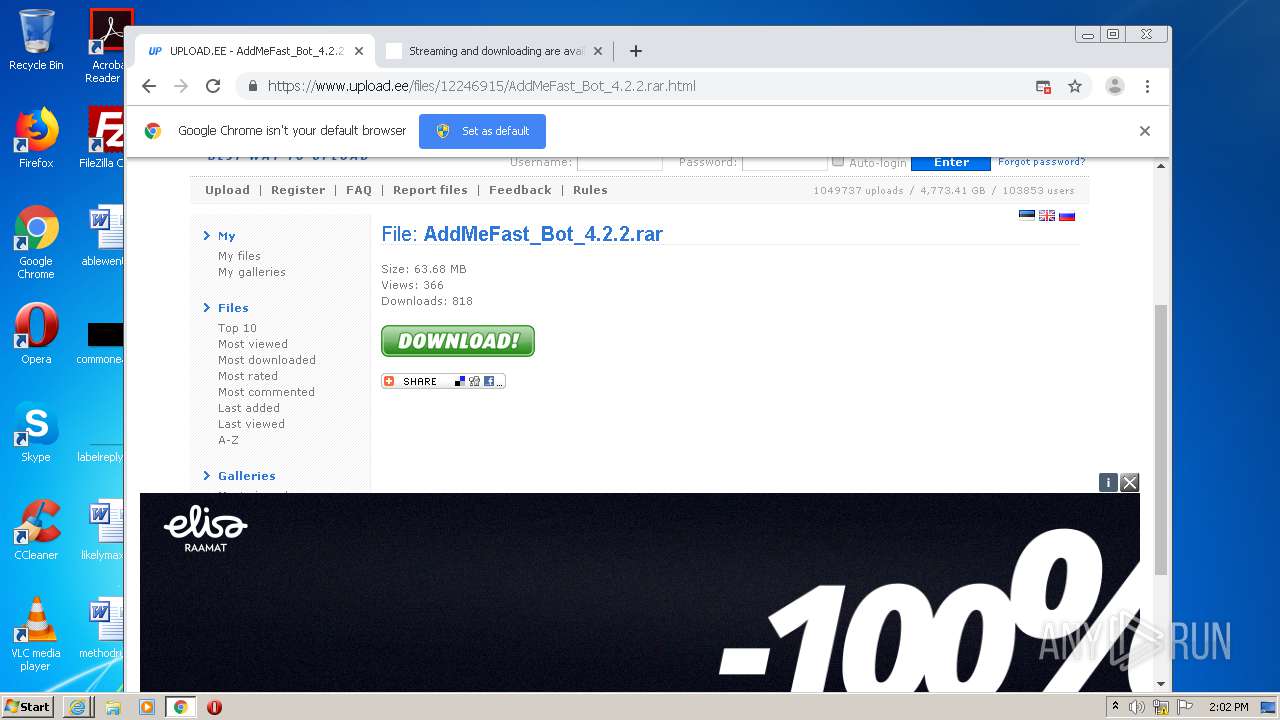
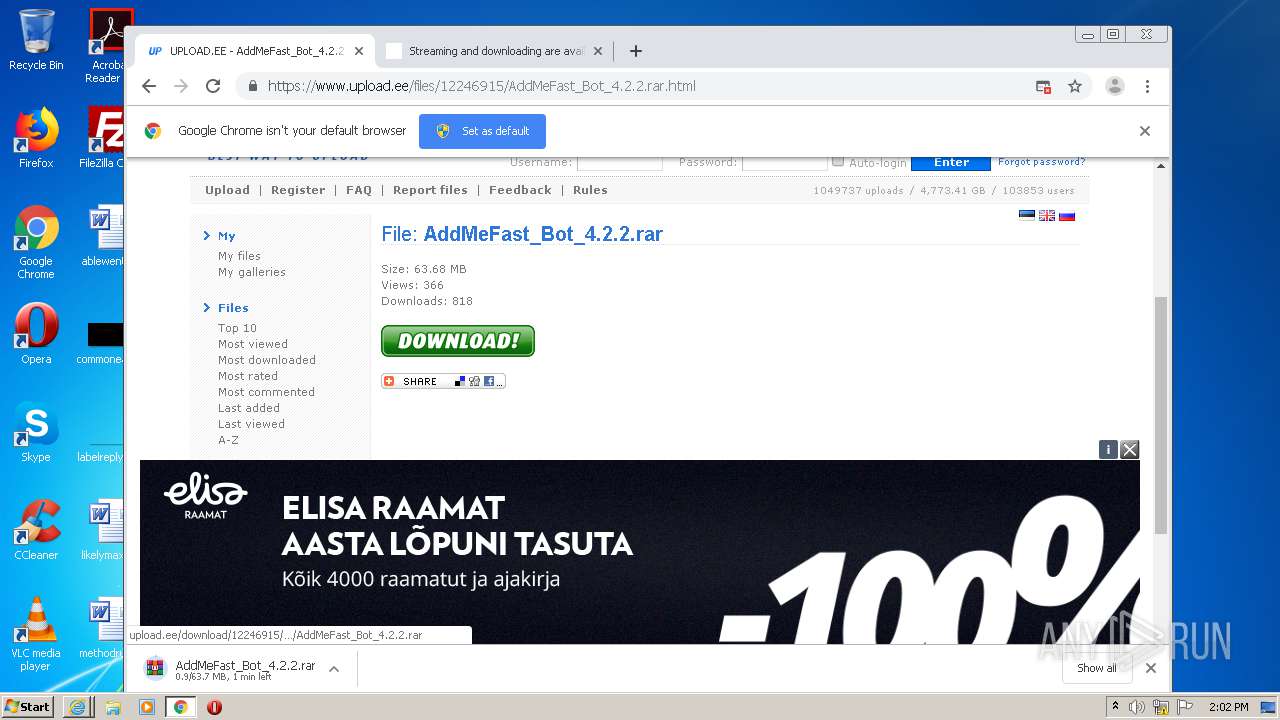
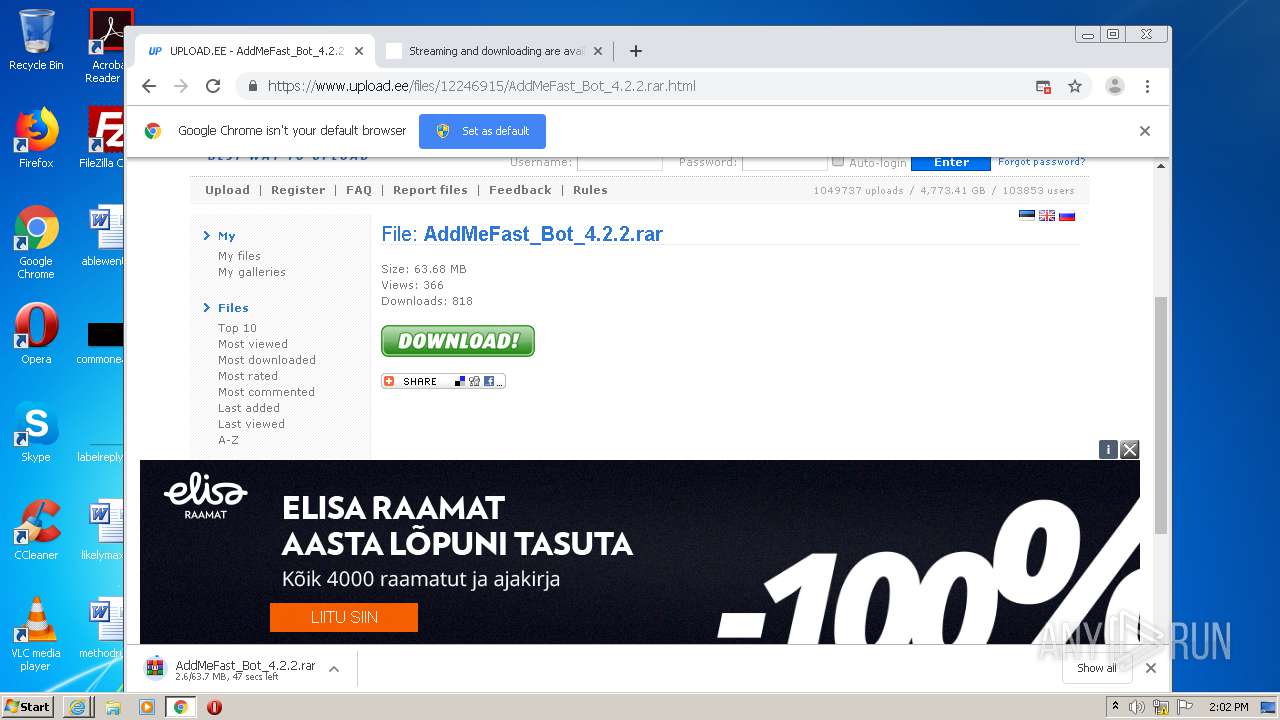
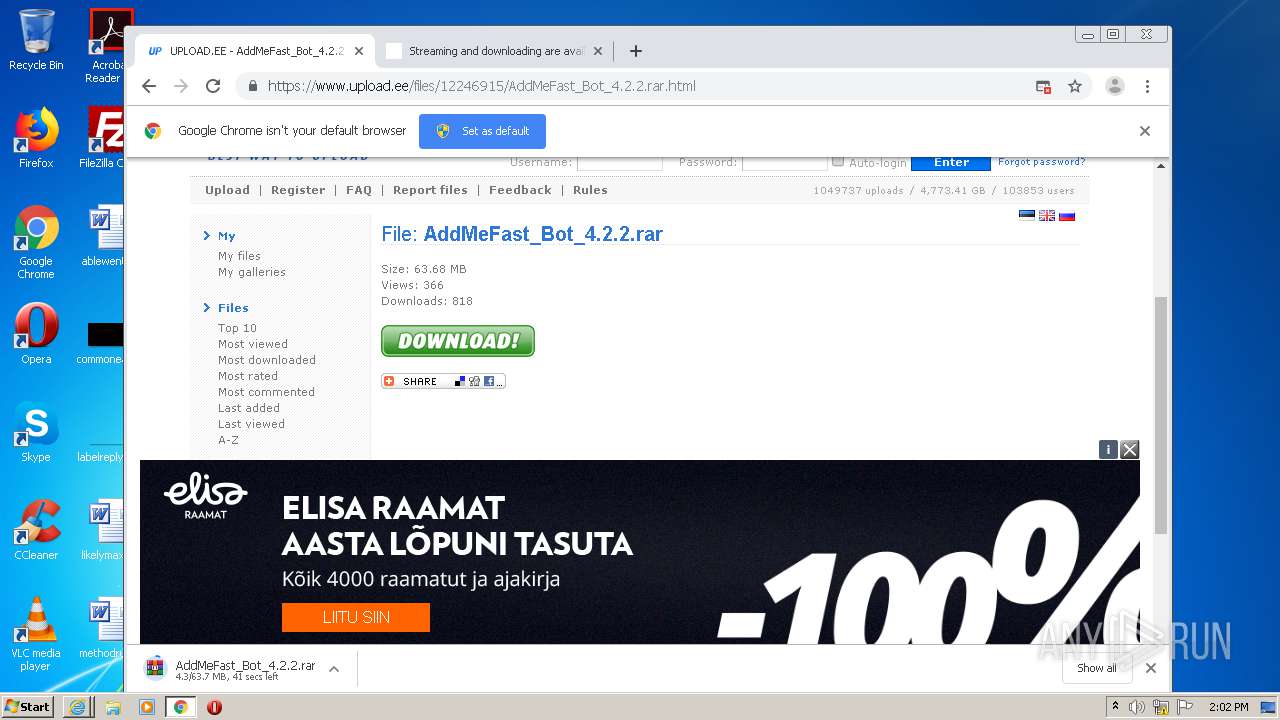
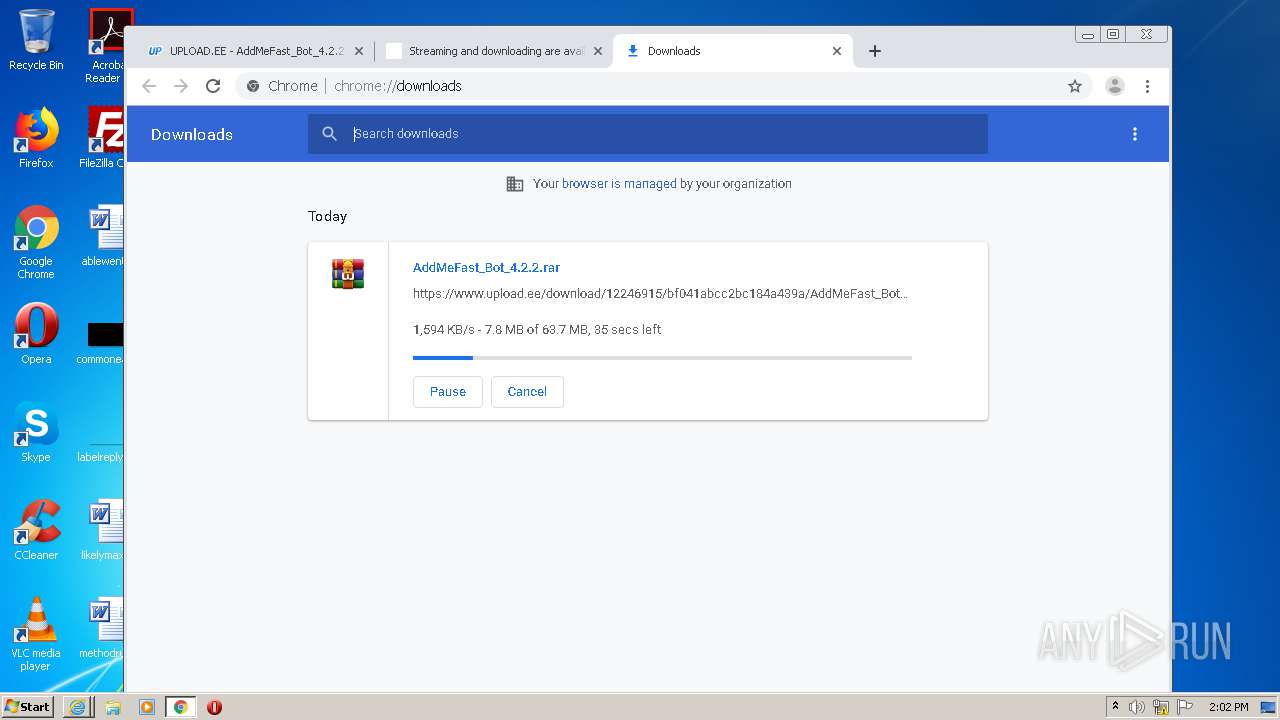
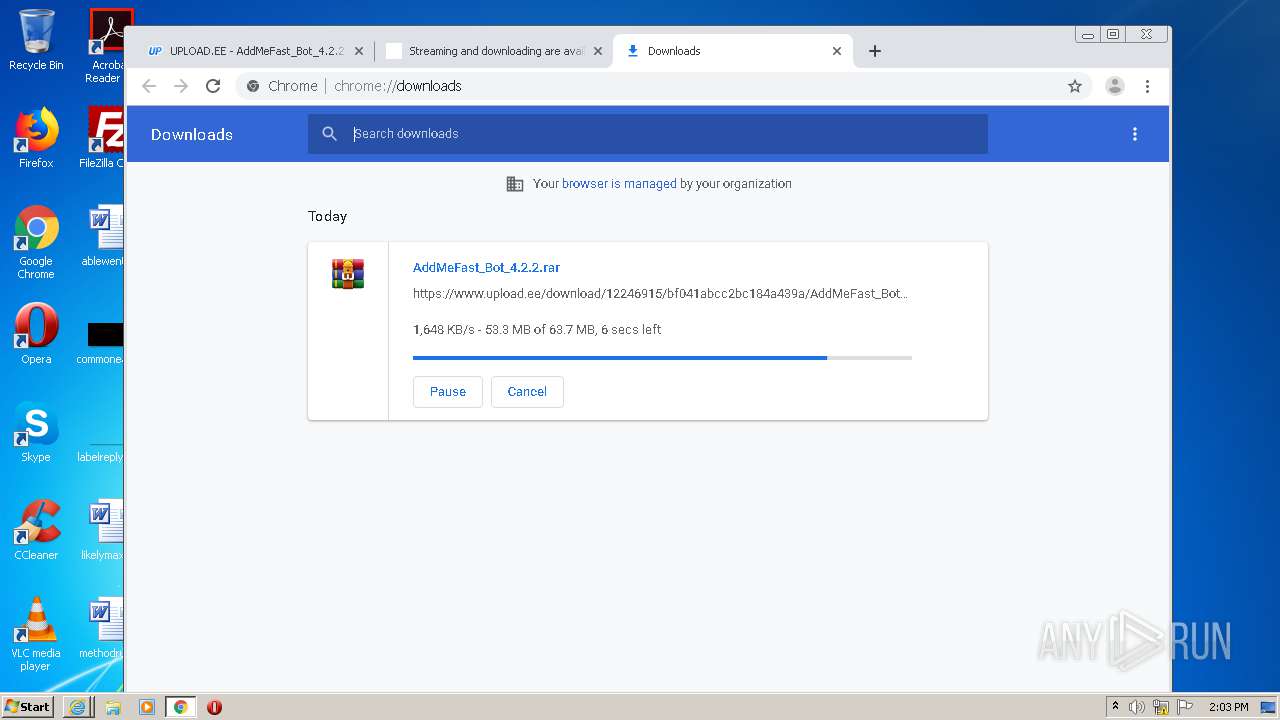
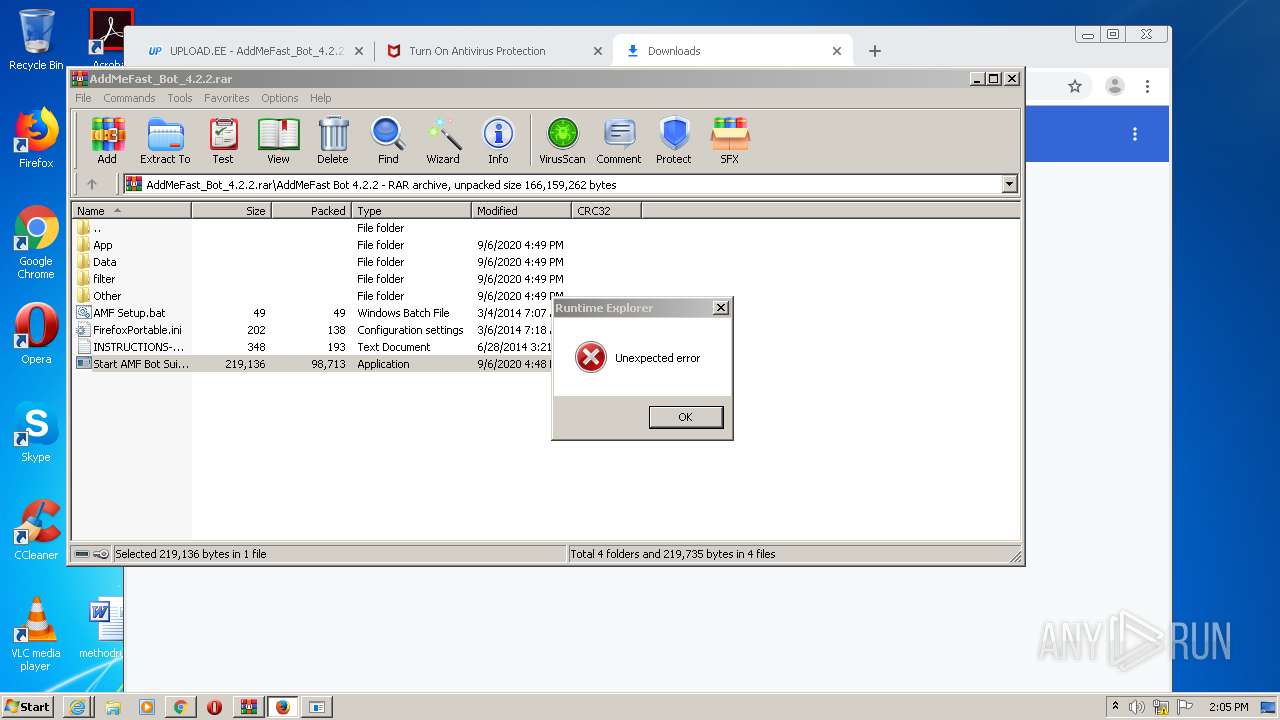
| URL: | https://www.upload.ee/files/12246915/AddMeFast_Bot_4.2.2.rar.html |
| Full analysis: | https://app.any.run/tasks/b3a517b8-ada8-4fa2-b68a-7b75db294876 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 14:01:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1E029145A93C8D8778E03F890F80A909 |
| SHA1: | DC783B003D4F56F1A410F002CCCC992FC30235F4 |
| SHA256: | 0D8878EFF80DE3FF8E0ECFB48DDAB1AB473A5C3505EDDE56FB6D5582D5C88D3E |
| SSDEEP: | 3:N8DSLr7MJmUx9IBd4V3n:2OLr03IfUn |
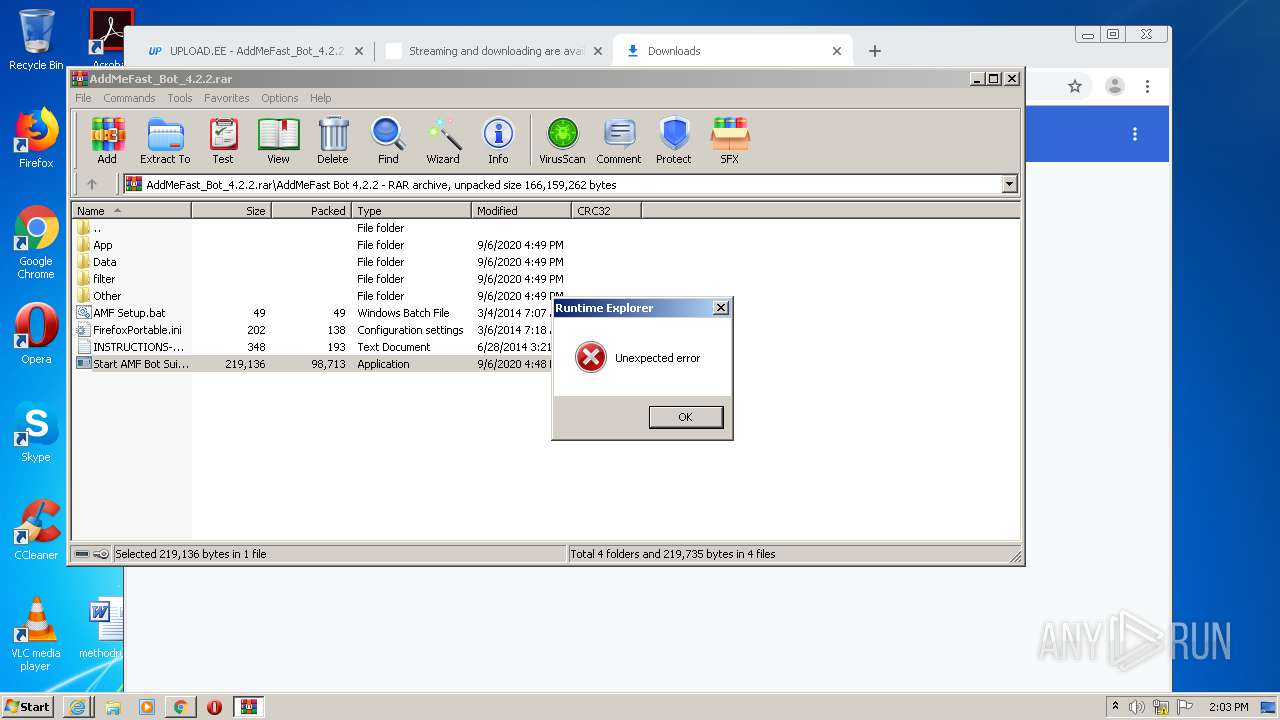
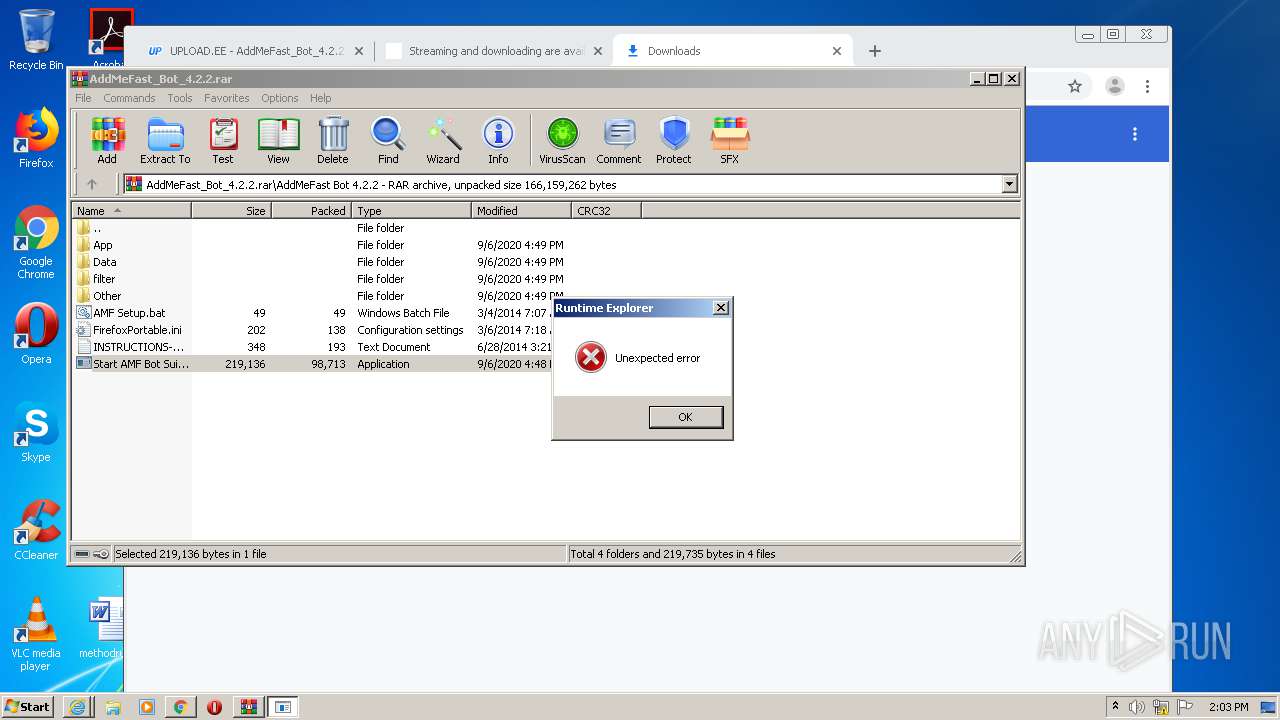
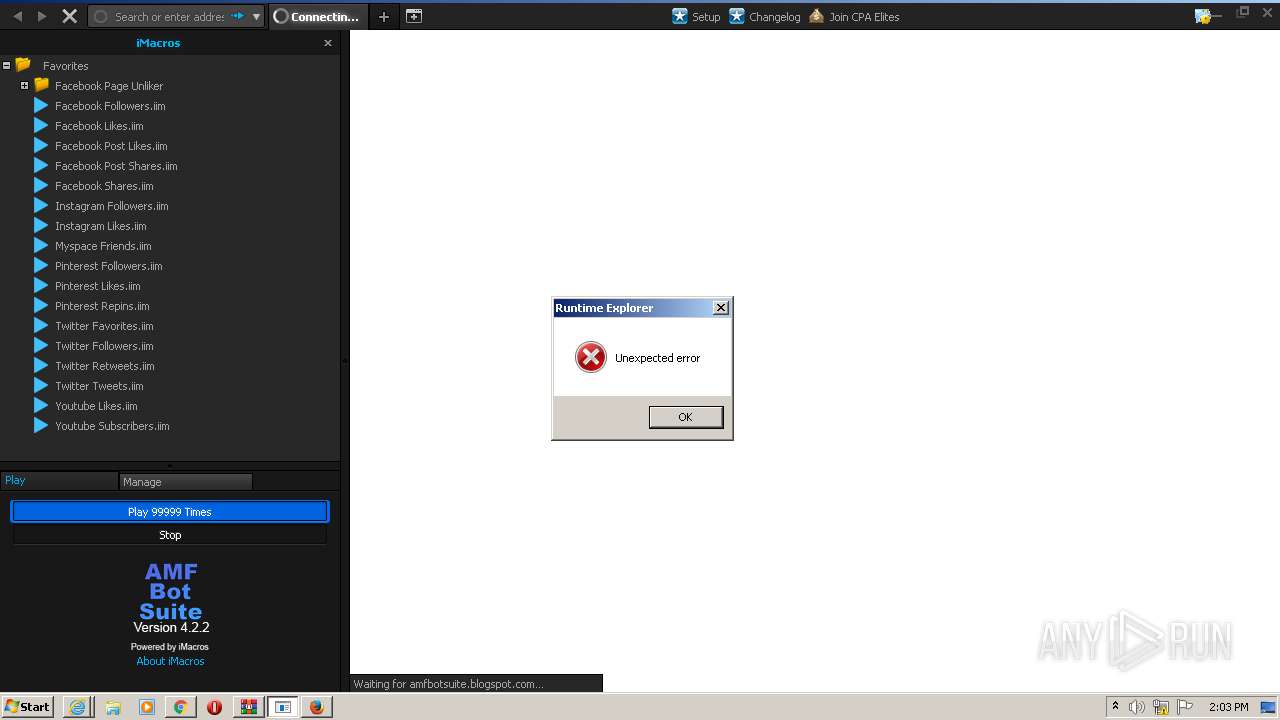
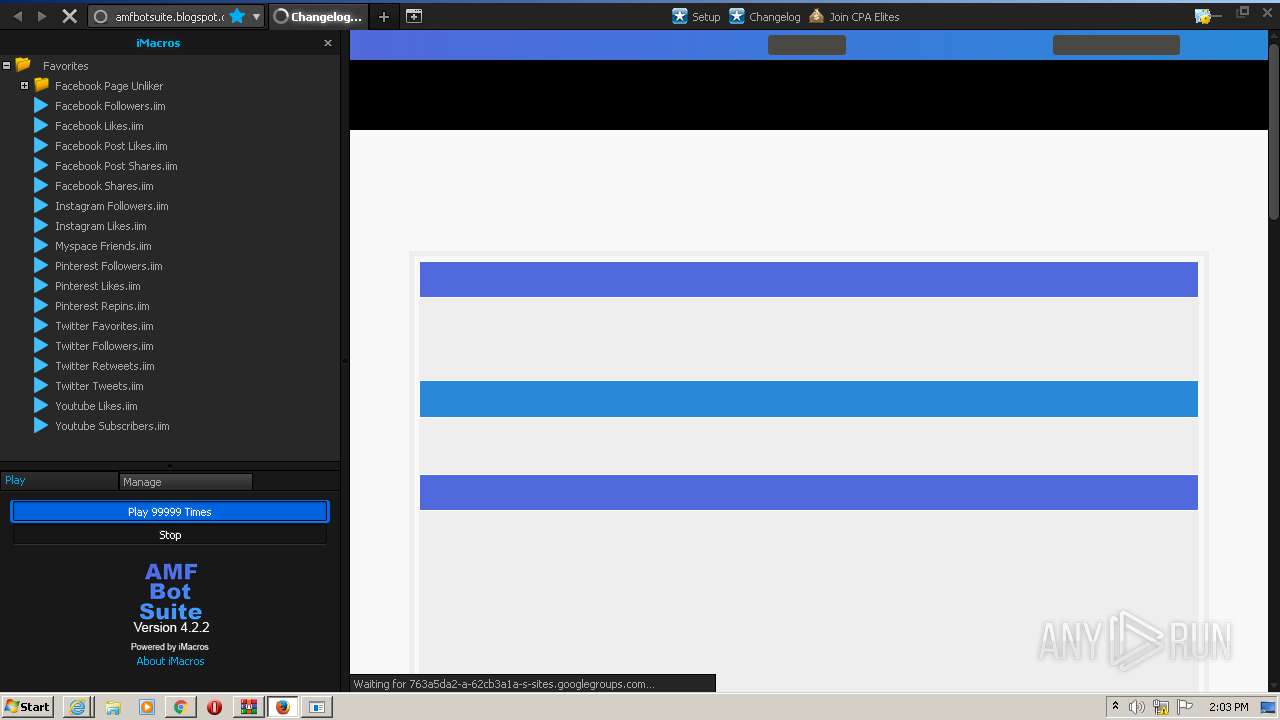
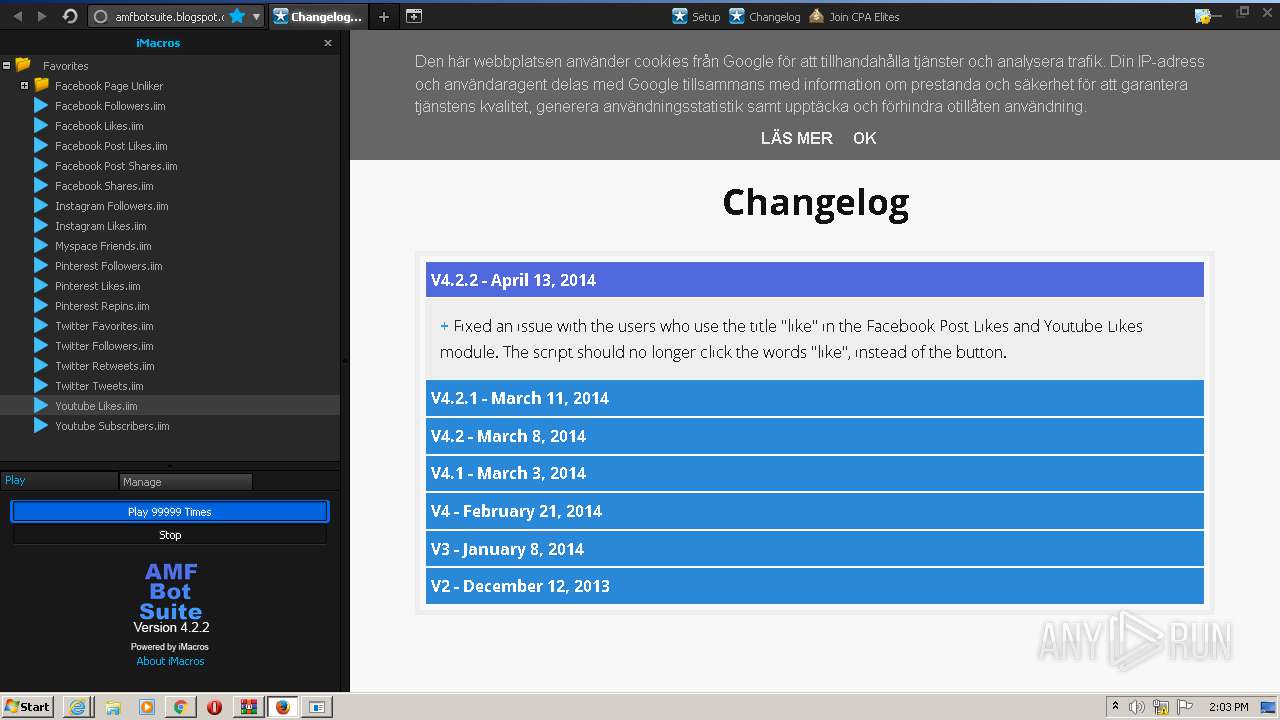
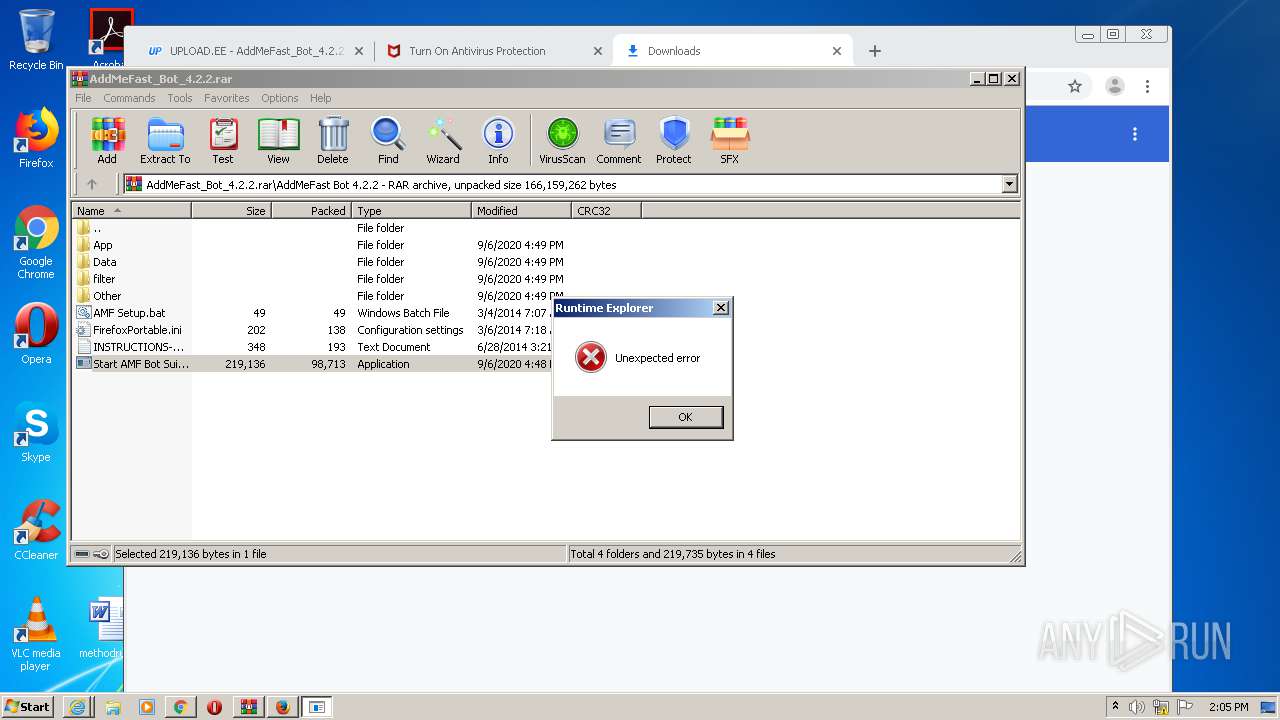
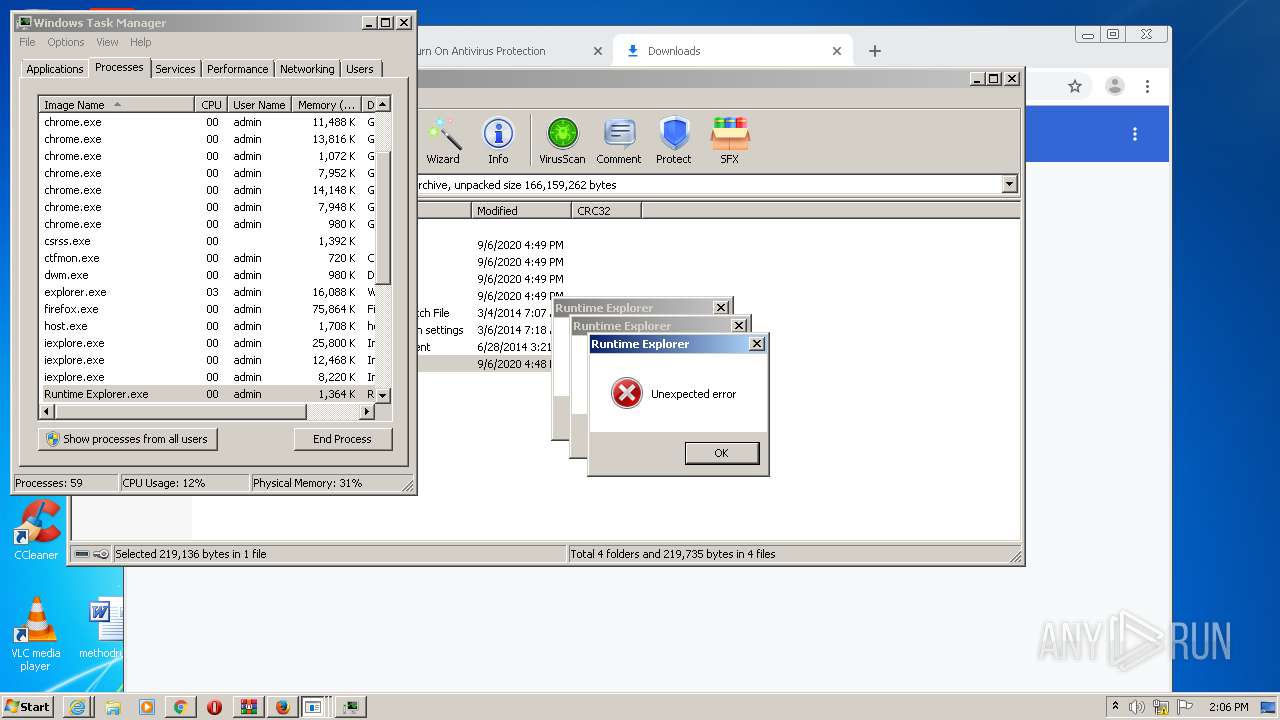
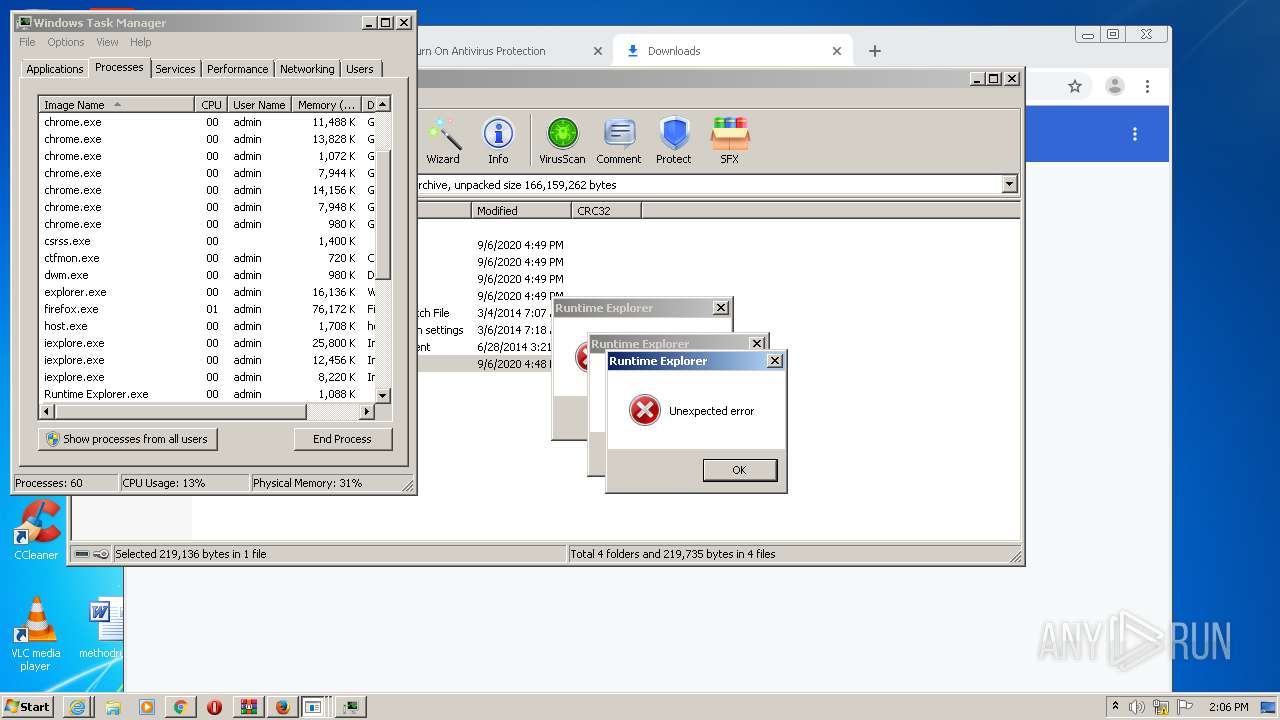
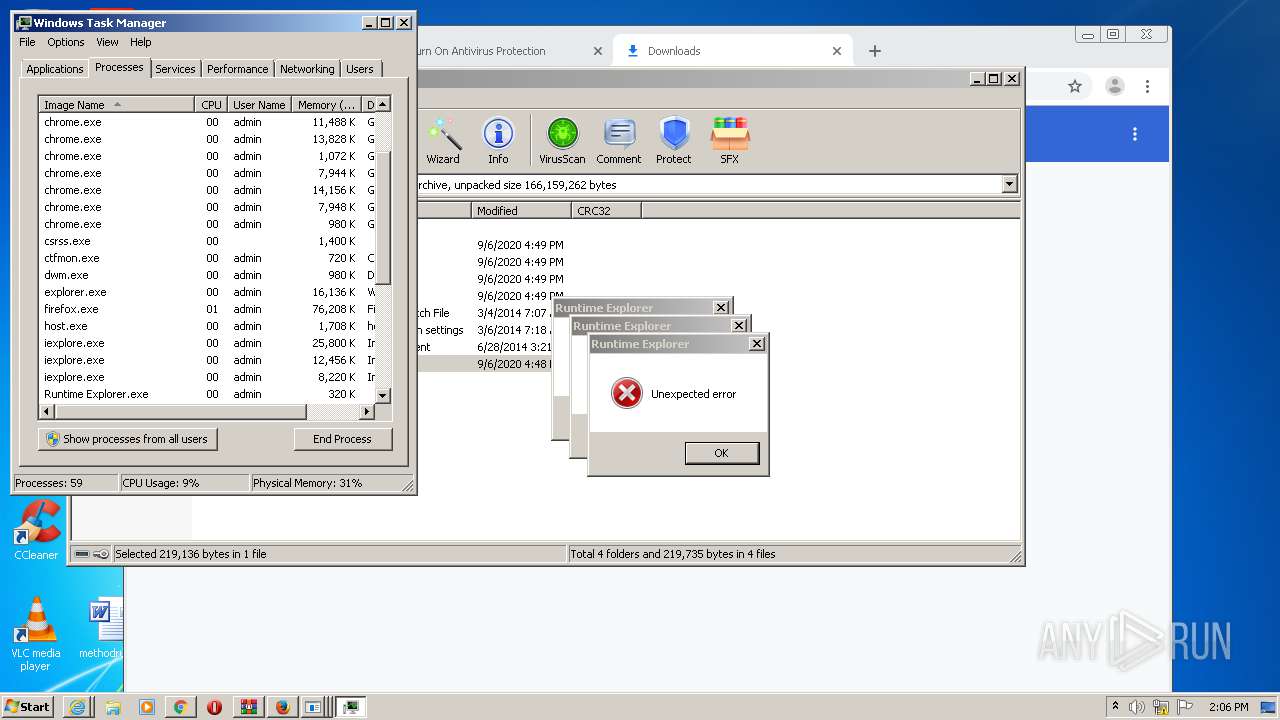
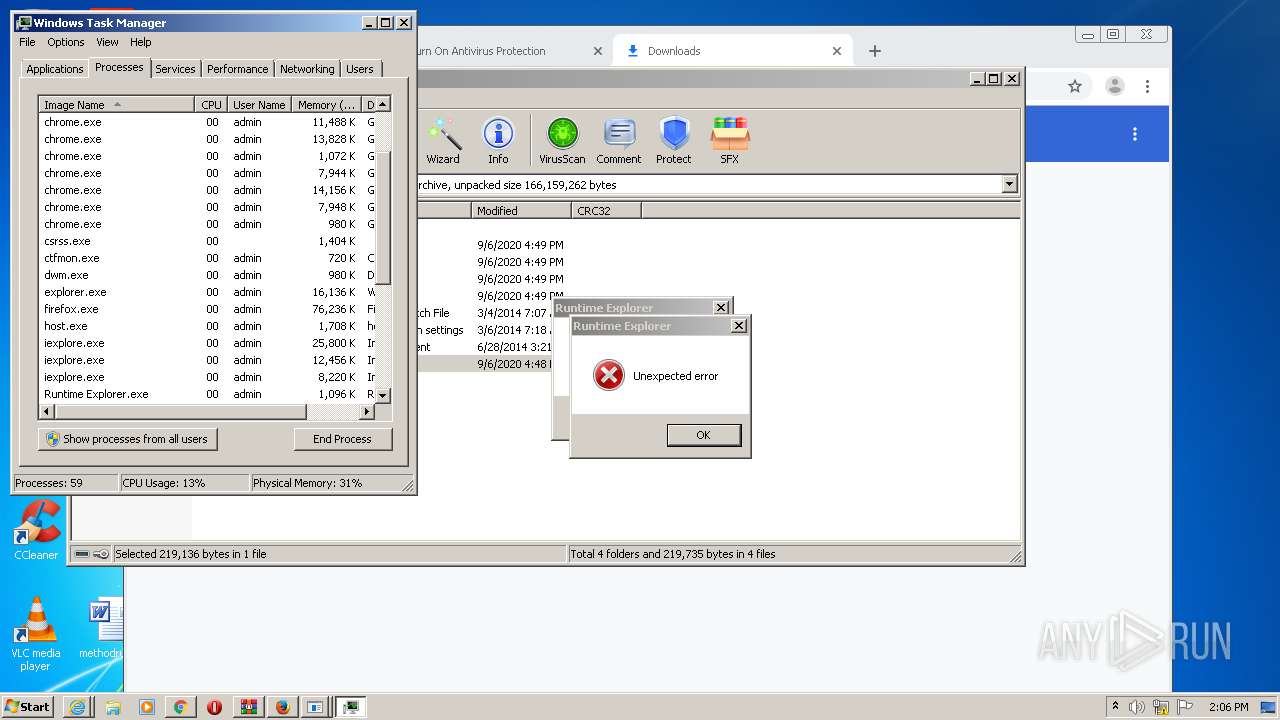
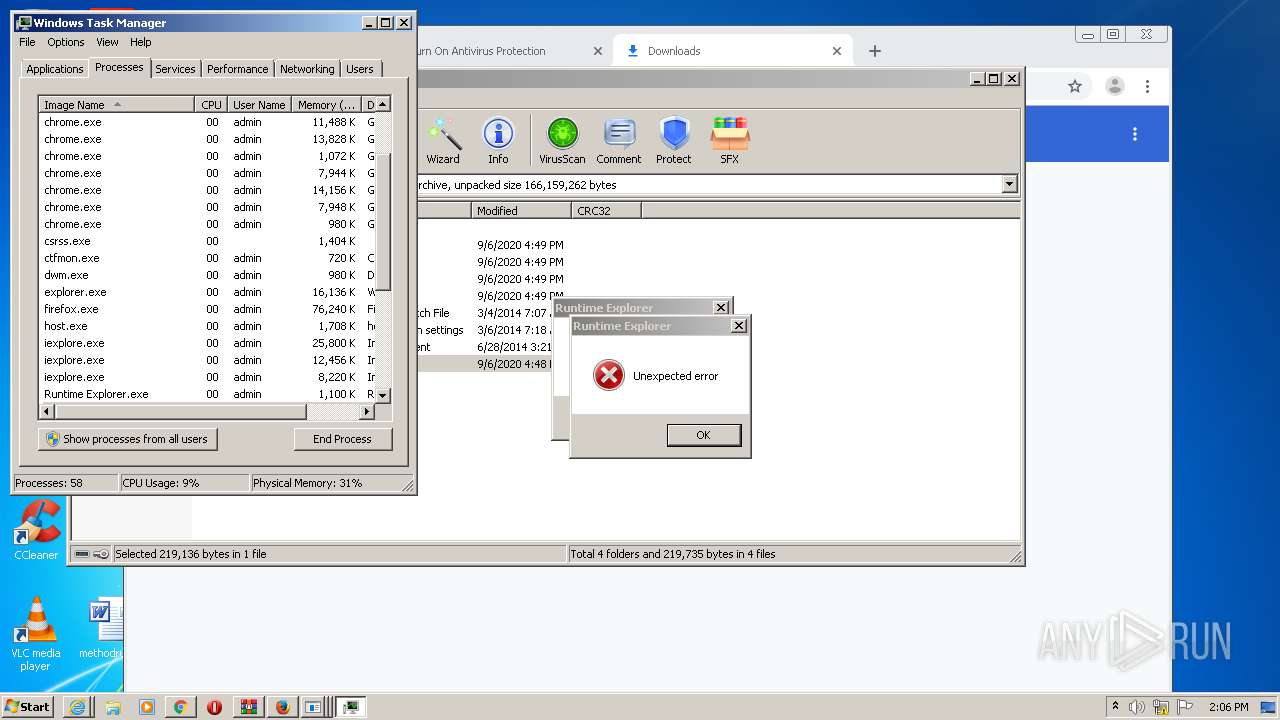
MALICIOUS
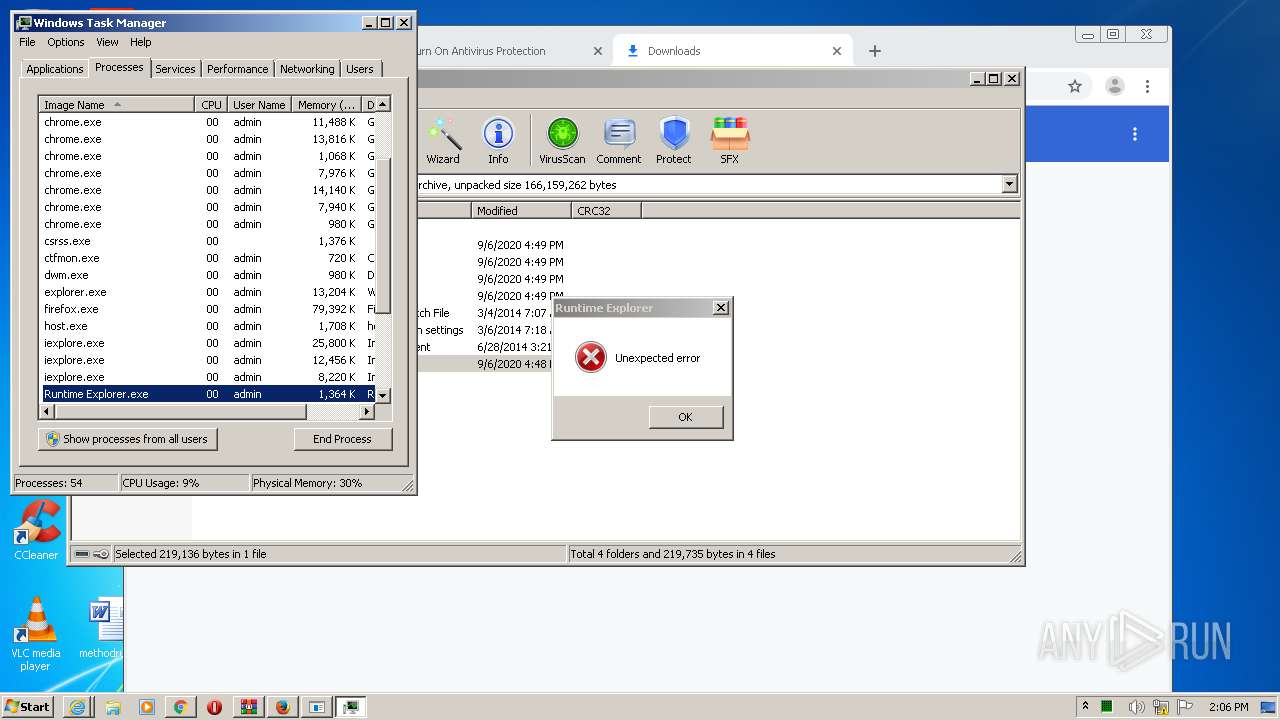
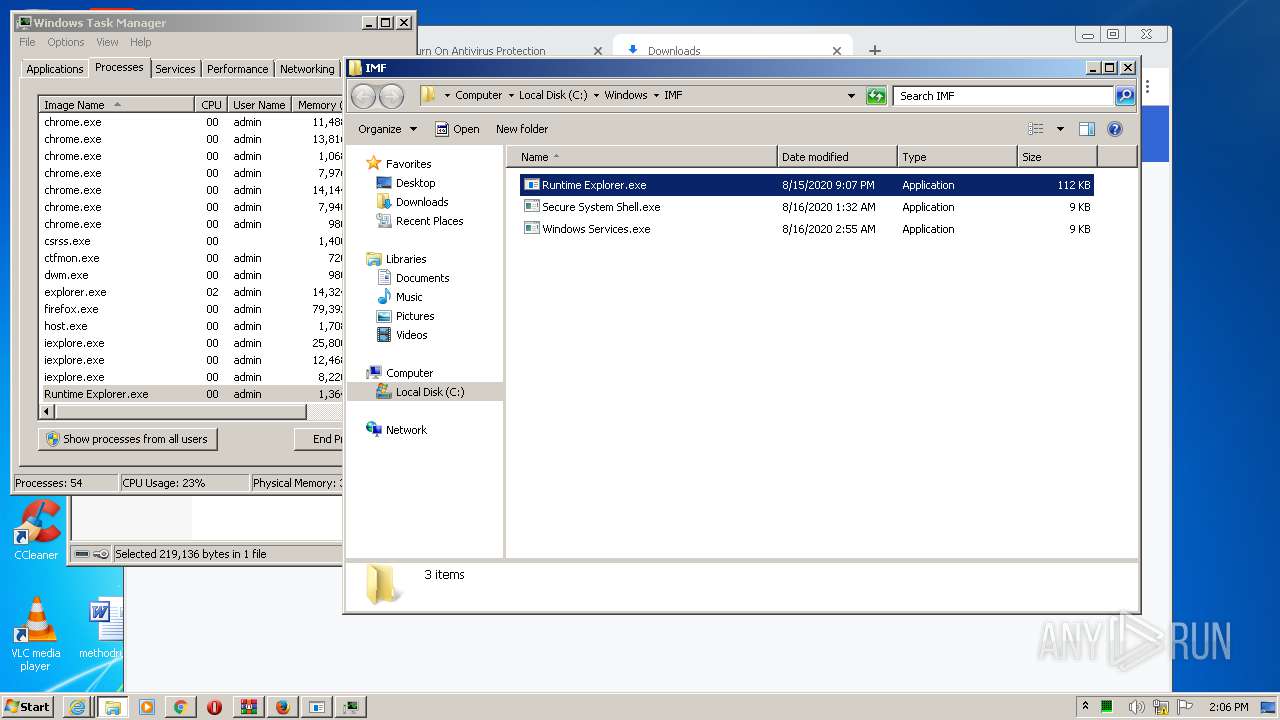
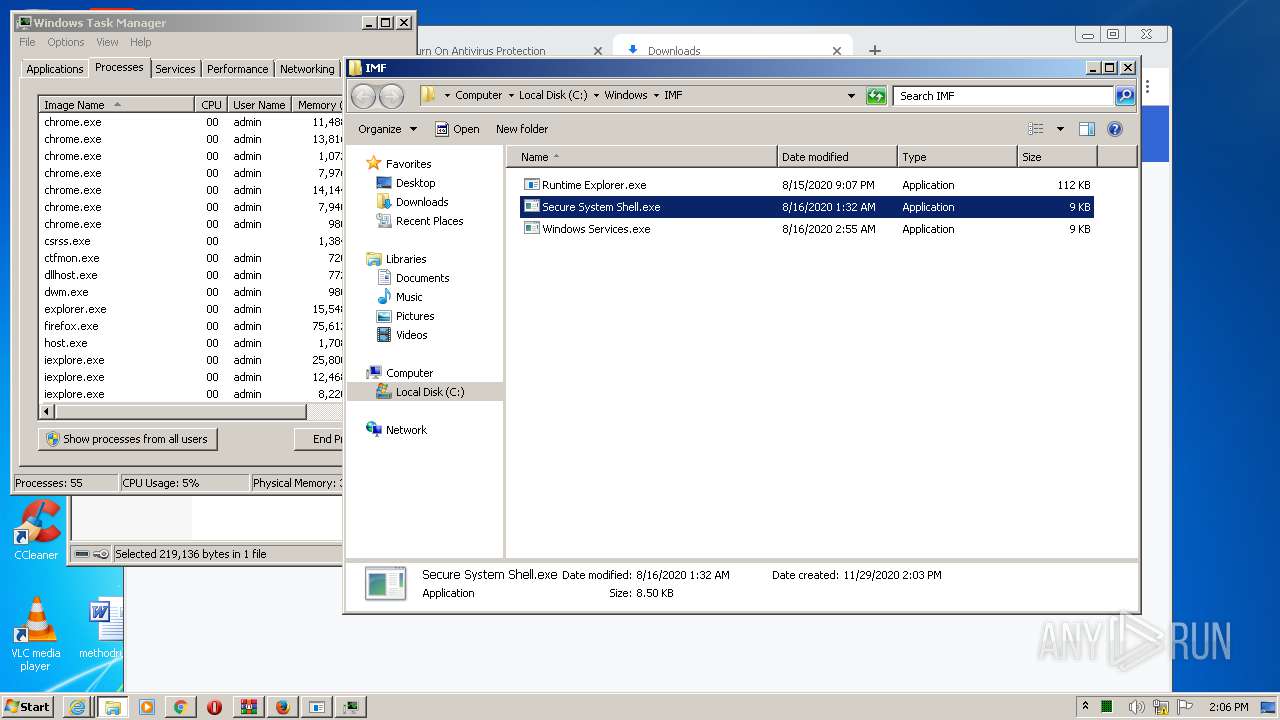
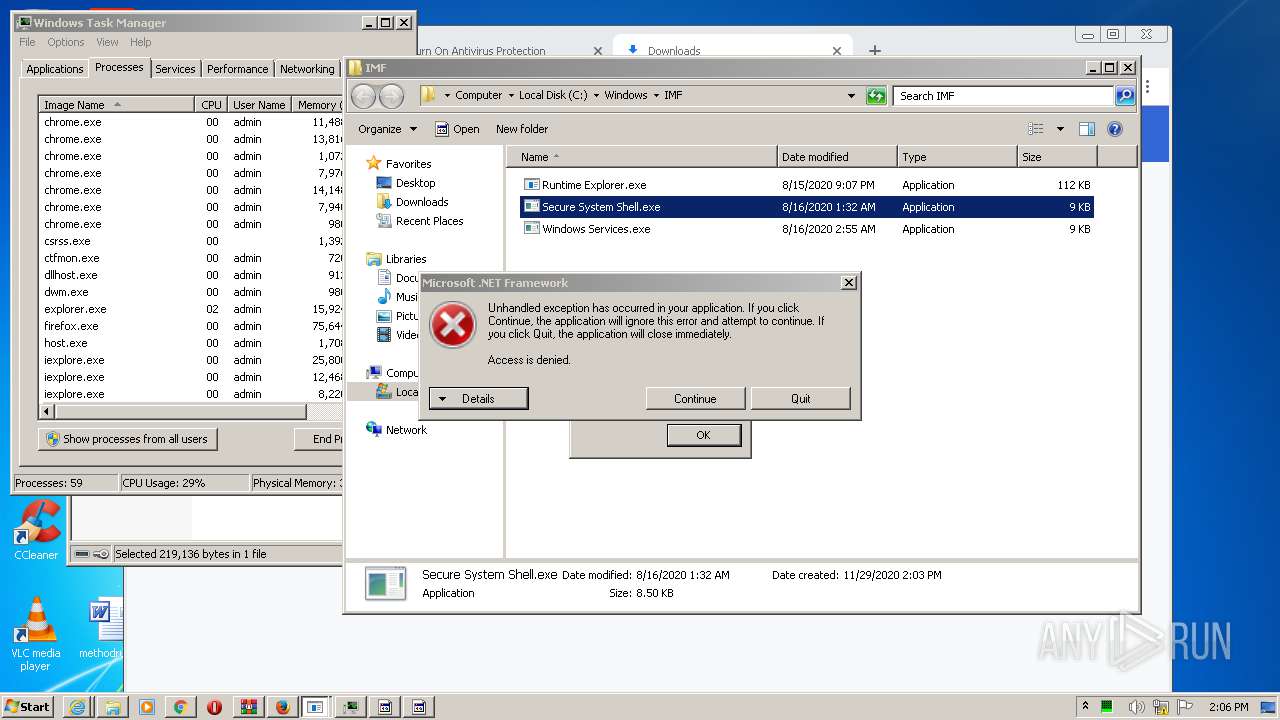
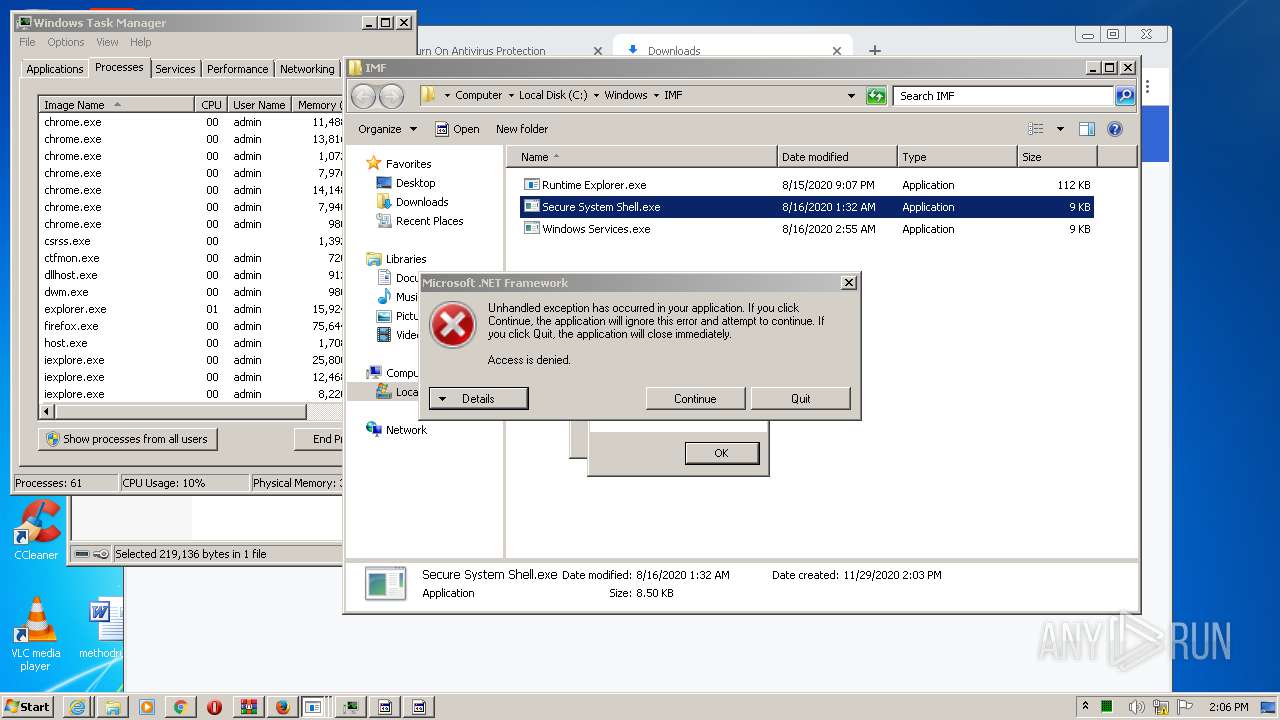
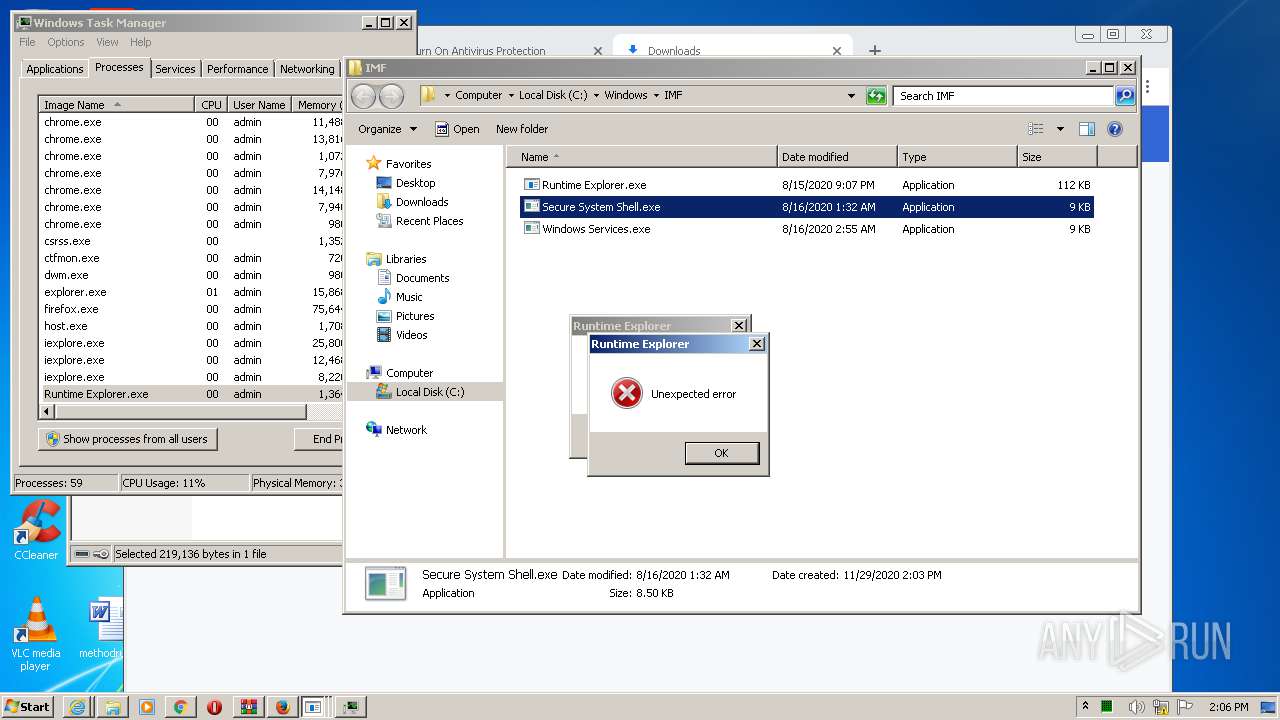
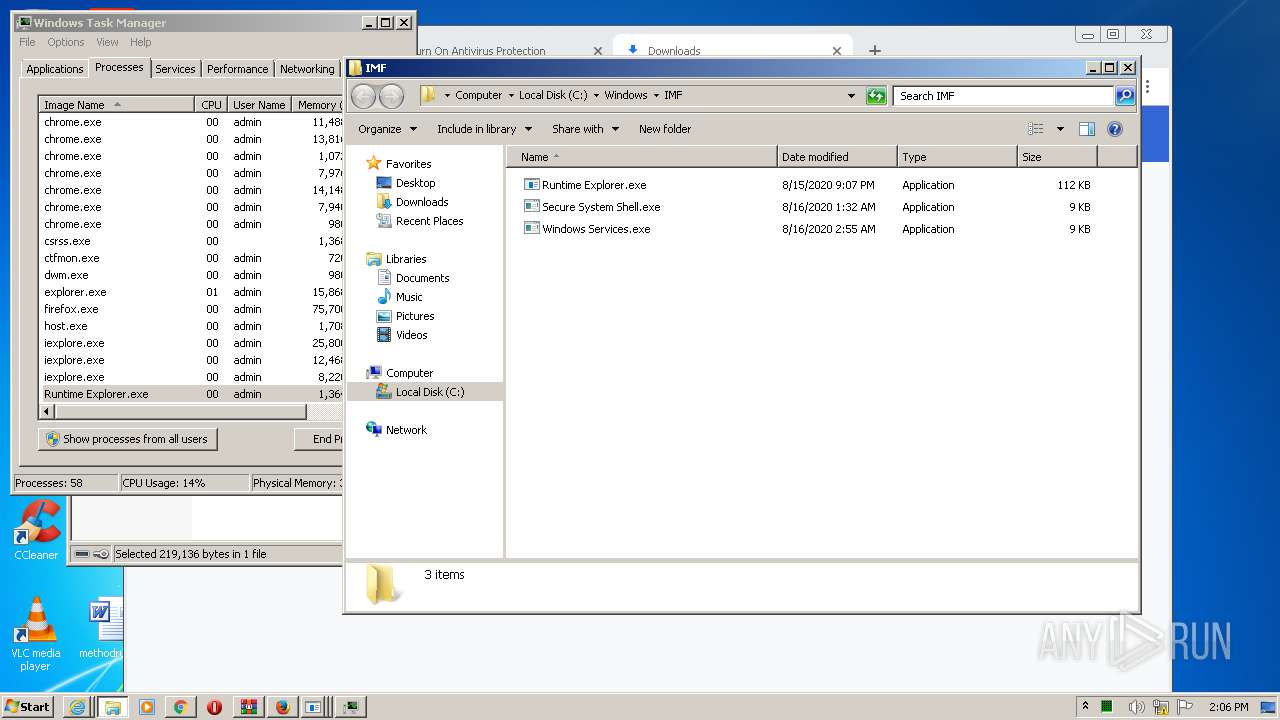
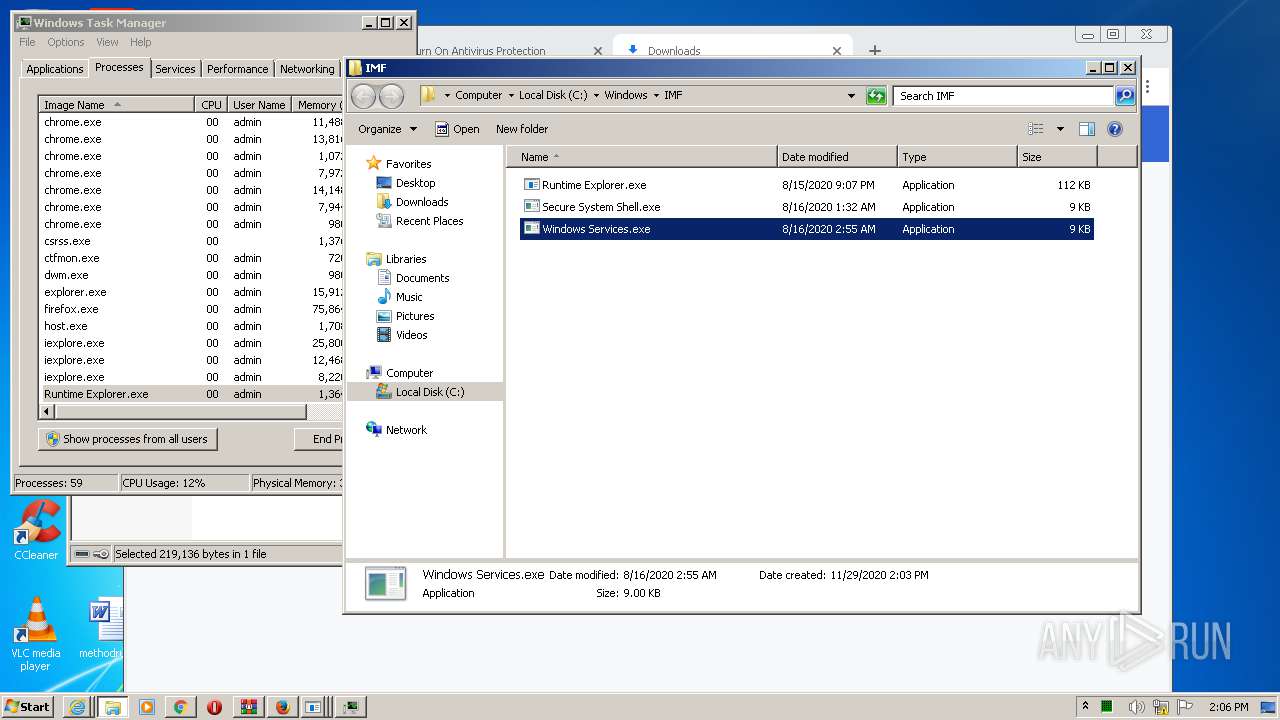
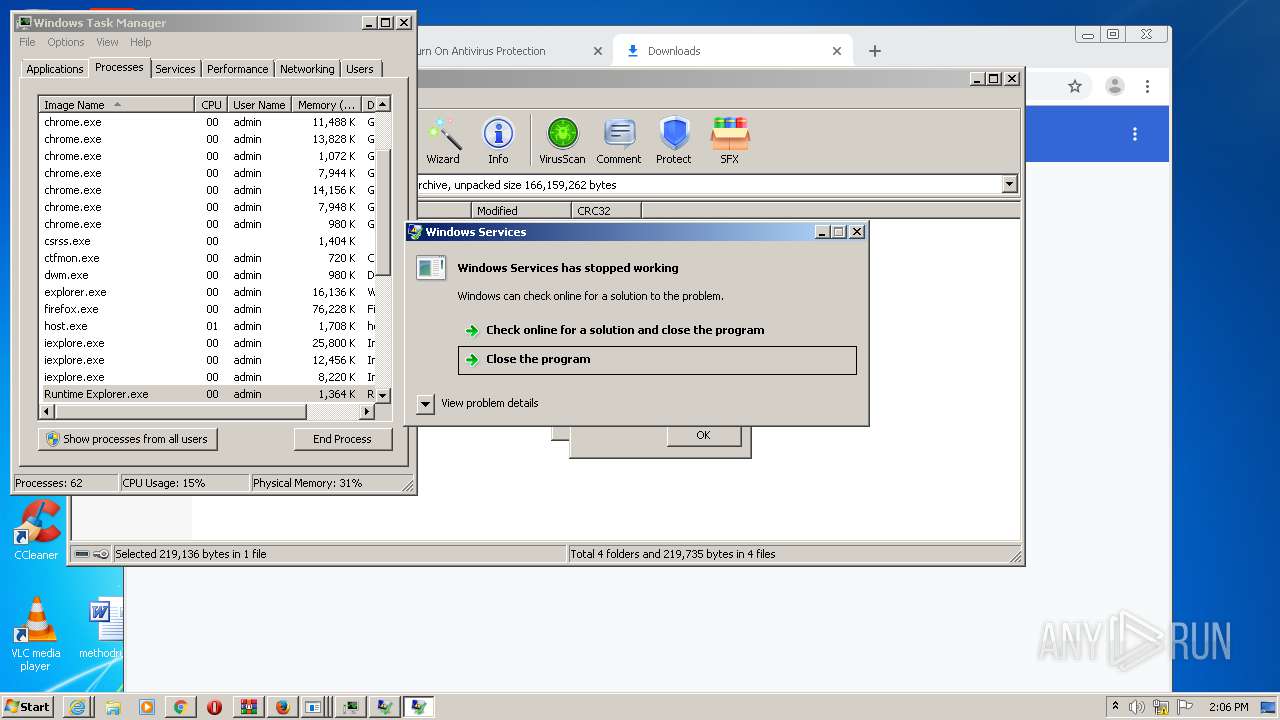
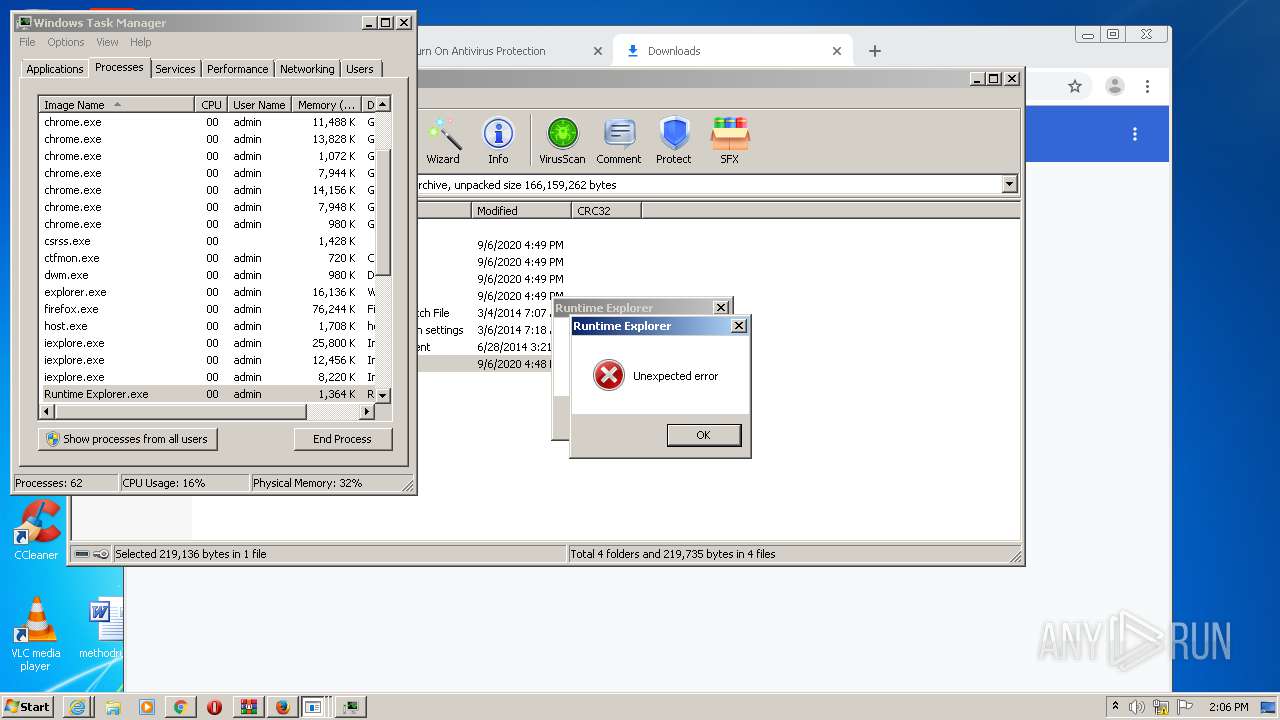
Application was dropped or rewritten from another process
- Runtime Explorer.exe (PID: 3316)
- Secure System Shell.exe (PID: 1068)
- Windows Services.exe (PID: 2844)
- firefox.exe (PID: 3356)
- adm.exe (PID: 1020)
- Runtime Explorer.exe (PID: 2888)
- Launcher.exe (PID: 2832)
- Start AMF Bot Suite V4.2.2.exe (PID: 1228)
- Runtime Explorer.exe (PID: 1992)
- Runtime Explorer.exe (PID: 3164)
- Secure System Shell.exe (PID: 3232)
- Secure System Shell.exe (PID: 2012)
- Windows Services.exe (PID: 3096)
- Runtime Explorer.exe (PID: 2708)
- Windows Services.exe (PID: 1968)
- Runtime Explorer.exe (PID: 3444)
- Runtime Explorer.exe (PID: 3556)
- Runtime Explorer.exe (PID: 3736)
- Runtime Explorer.exe (PID: 1996)
- Runtime Explorer.exe (PID: 2656)
- Windows Services.exe (PID: 3412)
- Runtime Explorer.exe (PID: 2040)
- Runtime Explorer.exe (PID: 3856)
- Runtime Explorer.exe (PID: 3788)
Writes to a start menu file
- Launcher.exe (PID: 2832)
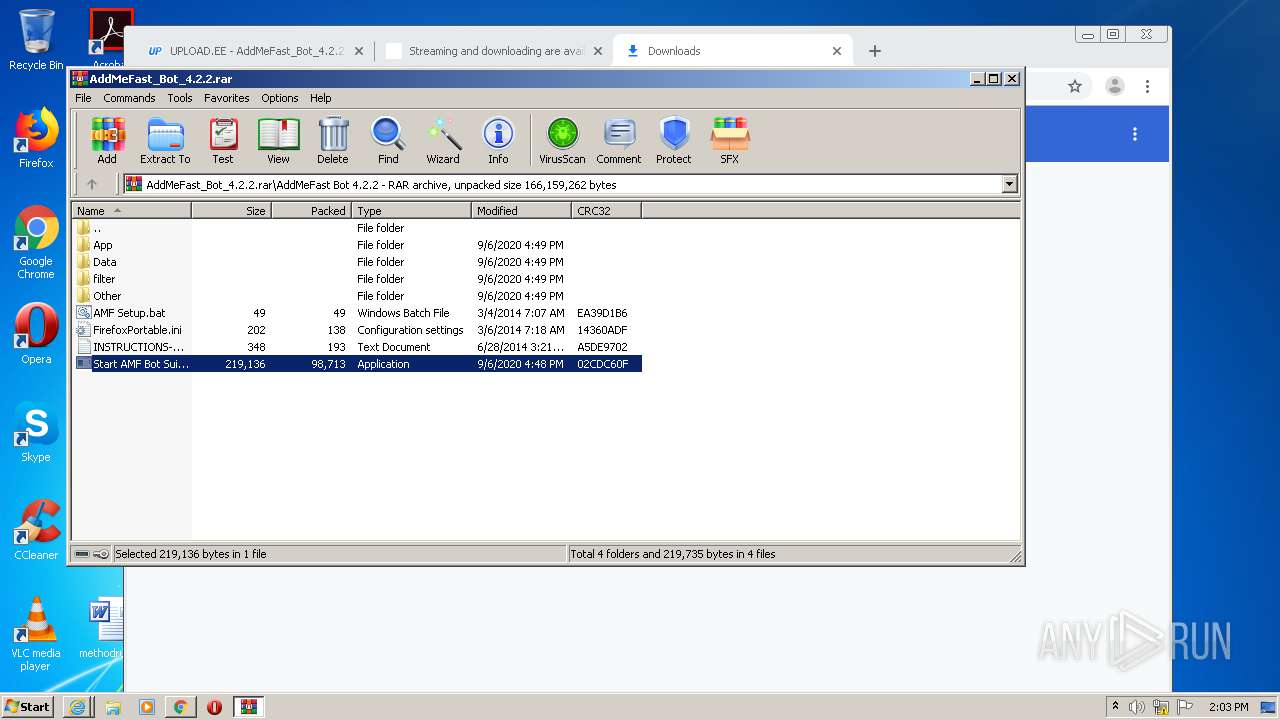
Drops executable file immediately after starts
- Launcher.exe (PID: 2832)
Changes the autorun value in the registry
- Launcher.exe (PID: 2832)
Loads dropped or rewritten executable
- firefox.exe (PID: 3356)
- adm.exe (PID: 1020)
Actions looks like stealing of personal data
- firefox.exe (PID: 3356)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1800)
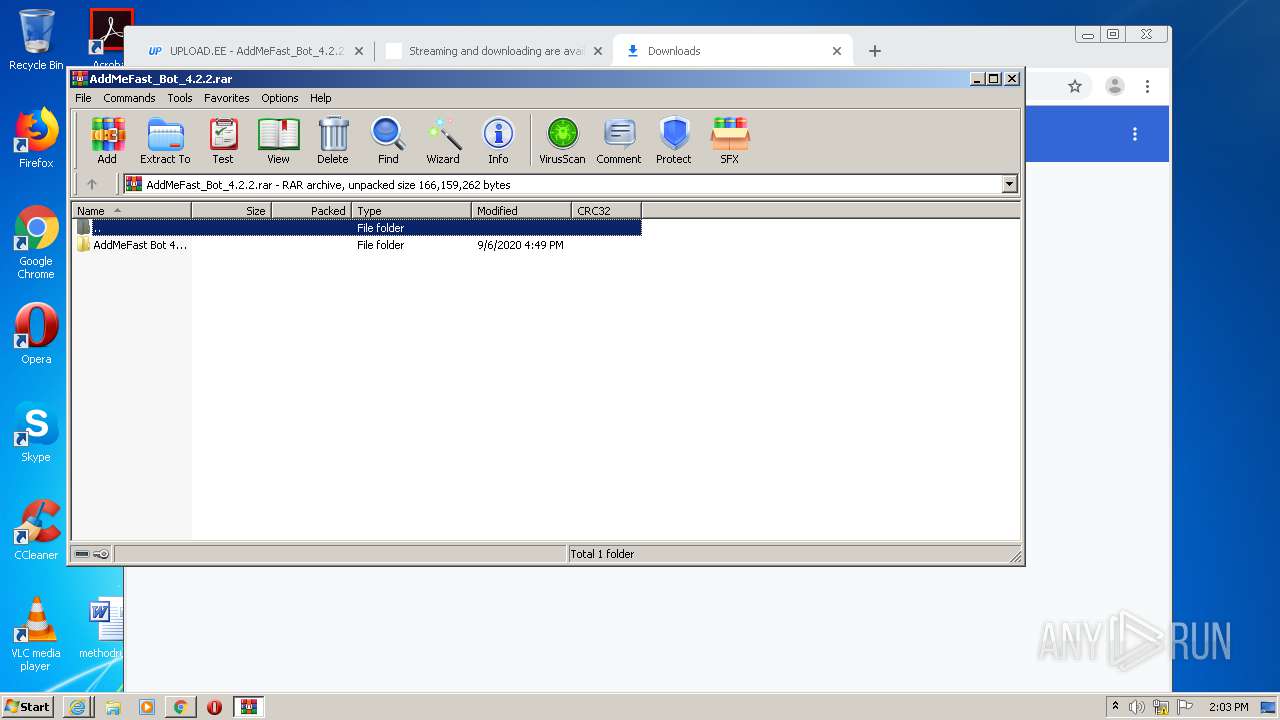
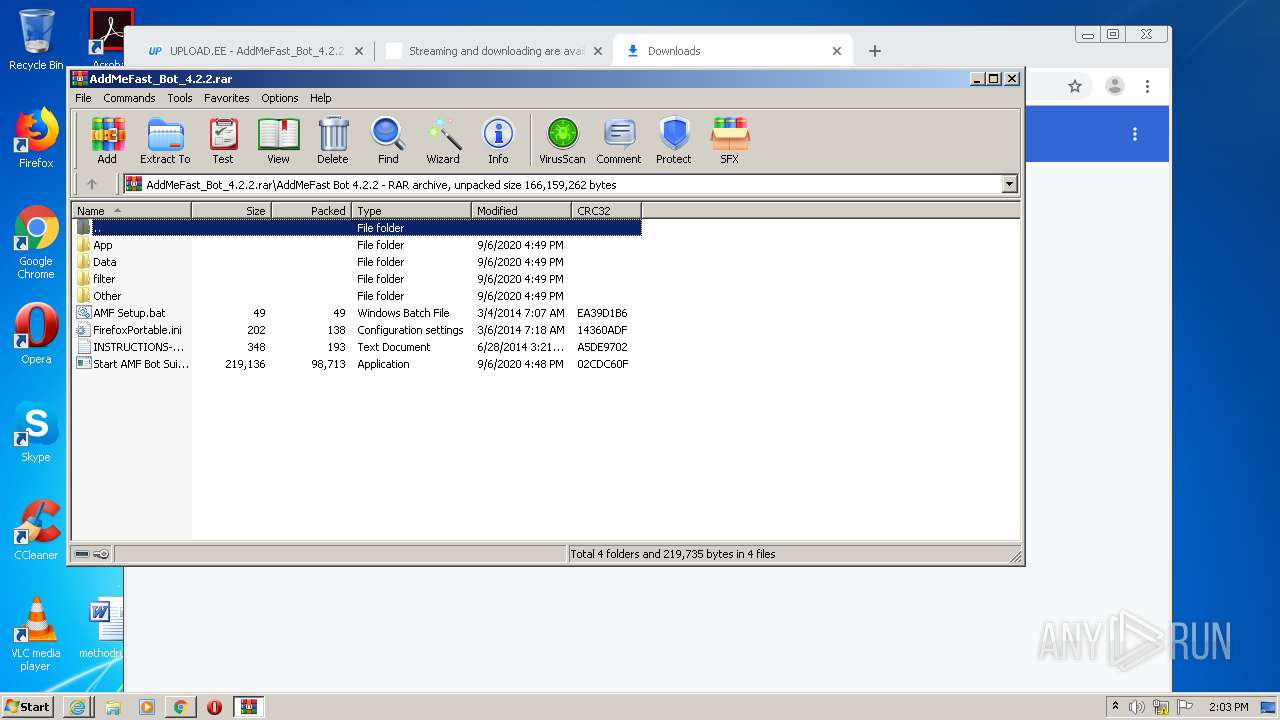
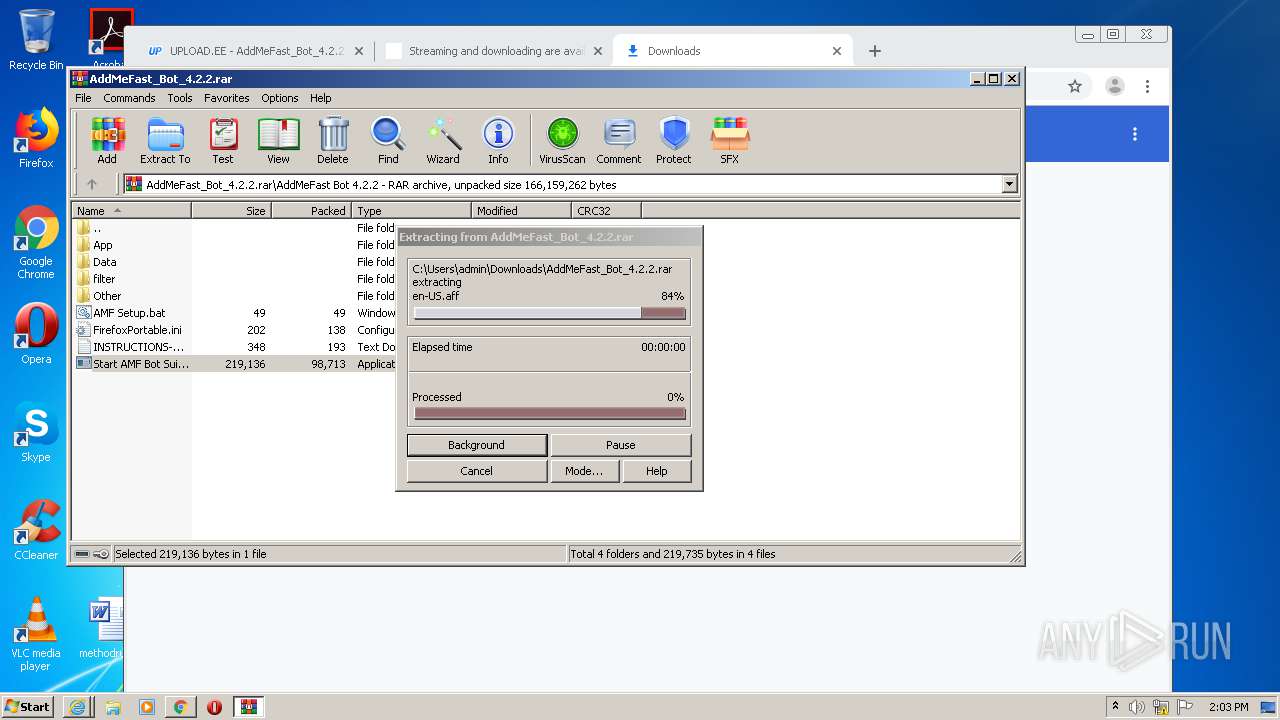
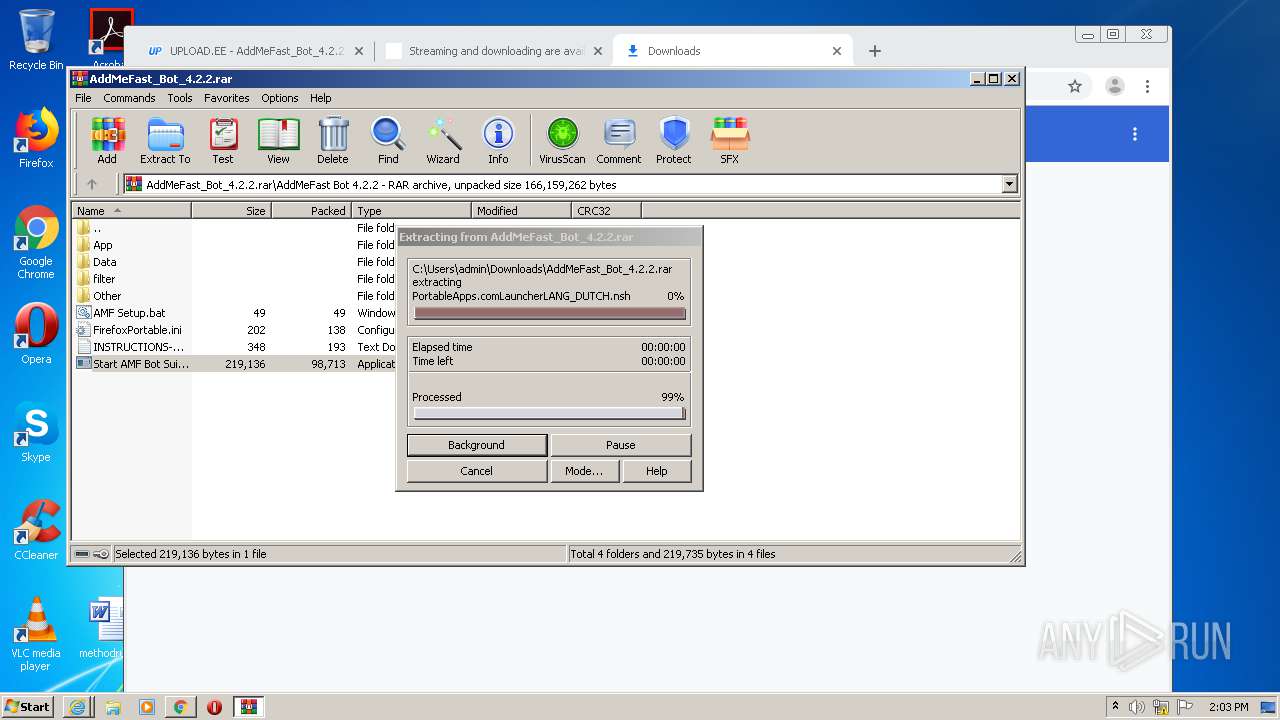
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2380)
- Launcher.exe (PID: 2832)
- adm.exe (PID: 1020)
Drops a file with too old compile date
- WinRAR.exe (PID: 2380)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2380)
- Launcher.exe (PID: 2832)
Creates files in the Windows directory
- Launcher.exe (PID: 2832)
Creates files in the user directory
- Launcher.exe (PID: 2832)
- firefox.exe (PID: 3356)
INFO
Creates files in the user directory
- iexplore.exe (PID: 1268)
- iexplore.exe (PID: 2860)
- iexplore.exe (PID: 2940)
Reads settings of System Certificates
- iexplore.exe (PID: 1268)
- iexplore.exe (PID: 2940)
- iexplore.exe (PID: 2860)
- chrome.exe (PID: 3360)
Application launched itself
- iexplore.exe (PID: 2940)
- chrome.exe (PID: 1800)
Changes internet zones settings
- iexplore.exe (PID: 2940)
Changes settings of System certificates
- iexplore.exe (PID: 2940)
Reads internet explorer settings
- iexplore.exe (PID: 2860)
- iexplore.exe (PID: 1268)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2940)
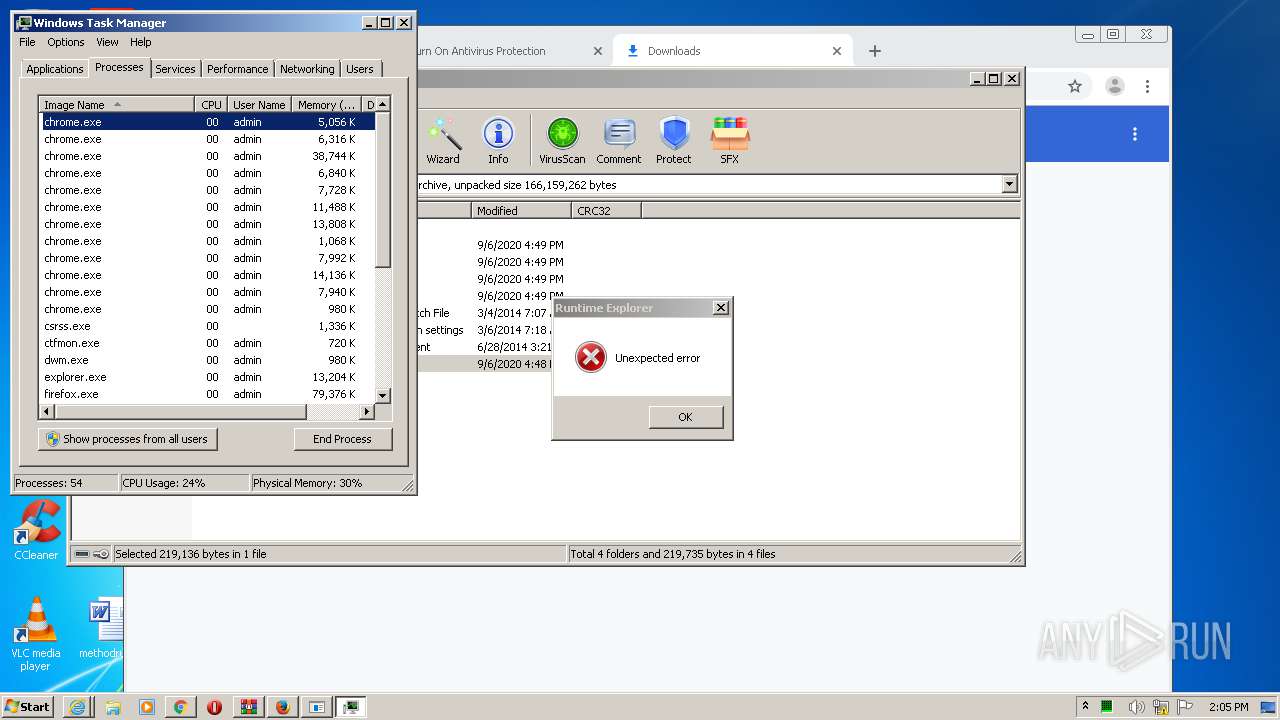
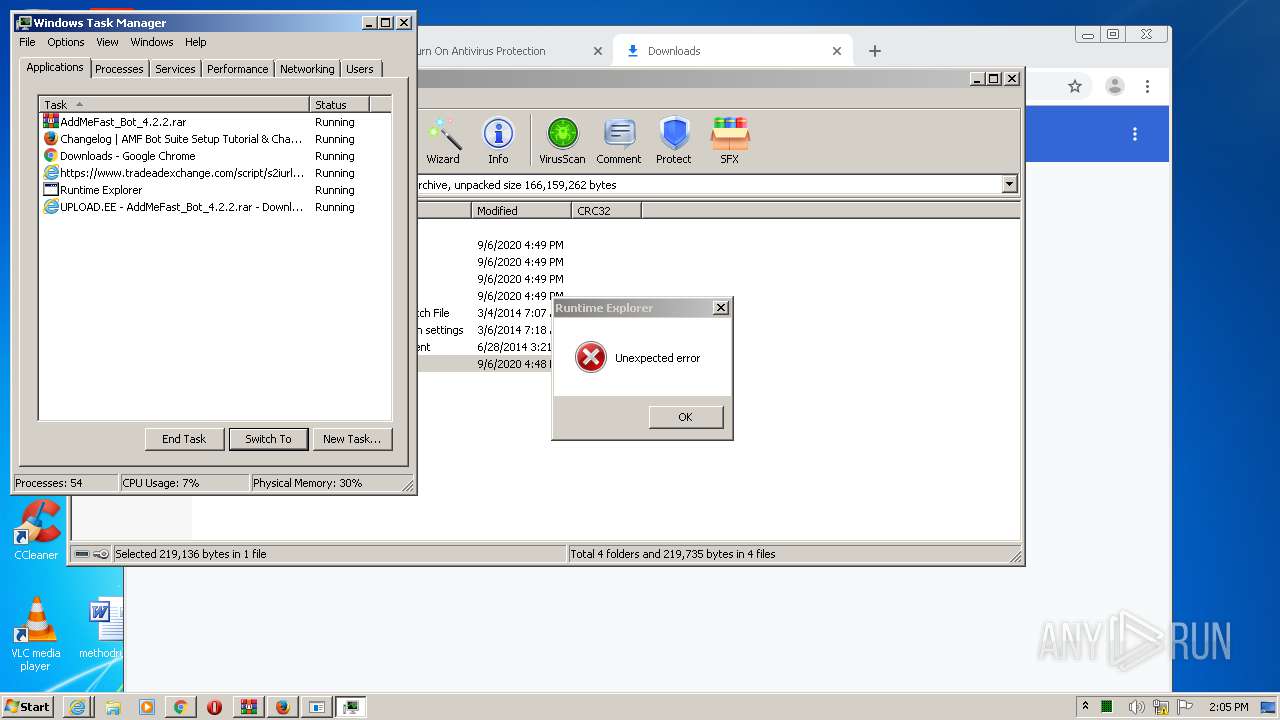
Manual execution by user
- chrome.exe (PID: 1800)
- taskmgr.exe (PID: 2960)
- Secure System Shell.exe (PID: 3232)
- Windows Services.exe (PID: 3412)
Reads the hosts file
- chrome.exe (PID: 1800)
- chrome.exe (PID: 3360)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2380)
- Launcher.exe (PID: 2832)
- firefox.exe (PID: 3356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
119
Monitored processes
71
Malicious processes
10
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,10518835493129285010,16956136156578636139,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10313166757349971883 --mojo-platform-channel-handle=3404 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,10518835493129285010,16956136156578636139,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5558618694474273250 --mojo-platform-channel-handle=5308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,10518835493129285010,16956136156578636139,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18376303265219869947 --mojo-platform-channel-handle=4804 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,10518835493129285010,16956136156578636139,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6797744454988984758 --mojo-platform-channel-handle=5312 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,10518835493129285010,16956136156578636139,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5198589639709304672 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4332 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,10518835493129285010,16956136156578636139,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7415594635895482448 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2380.44967\AddMeFast Bot 4.2.2\filter\adm.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2380.44967\AddMeFast Bot 4.2.2\filter\adm.exe | Start AMF Bot Suite V4.2.2.exe | ||||||||||||
User: admin Company: PortableApps.com Integrity Level: HIGH Description: Mozilla Firefox, Portable Edition Exit code: 0 Version: 1.7.9.0 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,10518835493129285010,16956136156578636139,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2756929452874443149 --mojo-platform-channel-handle=3240 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1068 | "C:\Windows\IMF\Secure System Shell.exe" | C:\Windows\IMF\Secure System Shell.exe | — | Windows Services.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Secure System Shell Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,10518835493129285010,16956136156578636139,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9262695433630164505 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 441
Read events
4 090
Write events
343
Delete events
8
Modification events
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1155441234 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30852696 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
72
Suspicious files
220
Text files
728
Unknown types
93
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1268 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarD51E.tmp | — | |
MD5:— | SHA256:— | |||
| 1268 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_CCF564BE5A3C924B17DDEBDEB5236E12 | binary | |
MD5:— | SHA256:— | |||
| 1268 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\AddMeFast_Bot_4.2.2.rar[1].htm | html | |
MD5:— | SHA256:— | |||
| 1268 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EKPVBXVK.txt | text | |
MD5:— | SHA256:— | |||
| 1268 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_CCF564BE5A3C924B17DDEBDEB5236E12 | der | |
MD5:— | SHA256:— | |||
| 1268 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\AF3BA1CDD96BBC740C9CE3754F348BED_D6FF3D9AAD7A7E8C128787CB37013E62 | binary | |
MD5:— | SHA256:— | |||
| 1268 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\AF3BA1CDD96BBC740C9CE3754F348BED_D6FF3D9AAD7A7E8C128787CB37013E62 | der | |
MD5:— | SHA256:— | |||
| 1268 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabD51D.tmp | compressed | |
MD5:767760B1B3B838B2DE0599D0E76D1C76 | SHA256:C0F37380971FB93ECB0CFA3C2BD6D91CC77F254F0A6CA41EDEFF47FDA0E409CC | |||
| 1268 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_5FDD03068CBBD8A96F3AB9595BA10093 | binary | |
MD5:— | SHA256:— | |||
| 1268 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
183
DNS requests
103
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAilokbNS1yMg9cCtLurU0k%3D | US | der | 471 b | whitelisted |
1268 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1268 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
1268 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1268 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.rapidssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhhZrQET0hvbSHUJmNfBKqR%2FiT7wQUU8oXWfxrwAMhLxqu5KqoHIJW2nUCEAffP8uXPz%2BbuVistZM%2BMKI%3D | US | der | 471 b | shared |
1268 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1268 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFcLuT0XSrlKAgAAAACAVZE%3D | US | der | 471 b | whitelisted |
1268 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFcLuT0XSrlKAgAAAACAVZE%3D | US | der | 471 b | whitelisted |
1268 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
1268 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
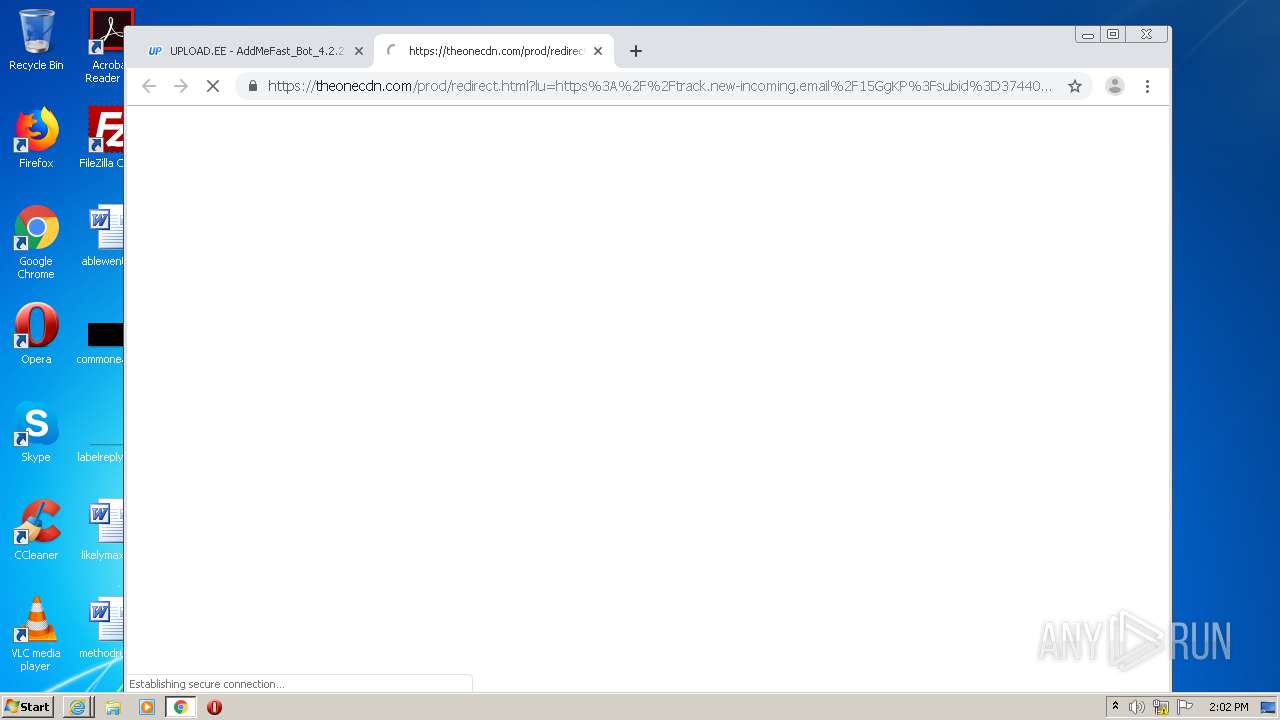
1268 | iexplore.exe | 104.27.143.36:443 | theonecdn.com | Cloudflare Inc | US | unknown |
1268 | iexplore.exe | 172.217.22.34:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1268 | iexplore.exe | 212.47.222.20:443 | serving.bepolite.eu | Linx Telecommunications B.V. | EE | suspicious |
1268 | iexplore.exe | 23.55.163.71:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | US | suspicious |
2940 | iexplore.exe | 37.187.167.53:443 | www.upload.ee | OVH SAS | FR | suspicious |
1268 | iexplore.exe | 23.55.163.68:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | US | suspicious |
2940 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2860 | iexplore.exe | 35.190.74.92:443 | www.tradeadexchange.com | Google Inc. | US | whitelisted |
2860 | iexplore.exe | 23.55.163.68:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | US | suspicious |
2860 | iexplore.exe | 3.90.94.177:443 | dist.acapps.online | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.upload.ee |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.rapidssl.com |
| shared |
www.geniusdexchange.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.tradeadexchange.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3360 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3360 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |