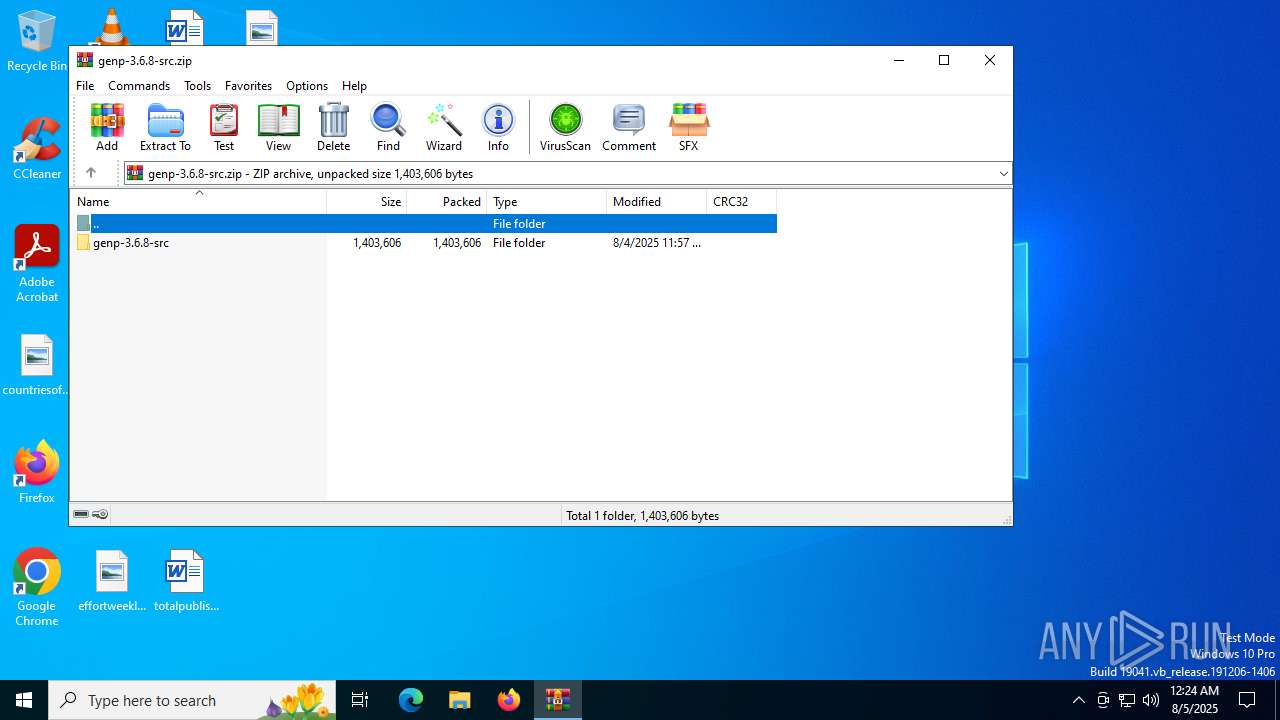
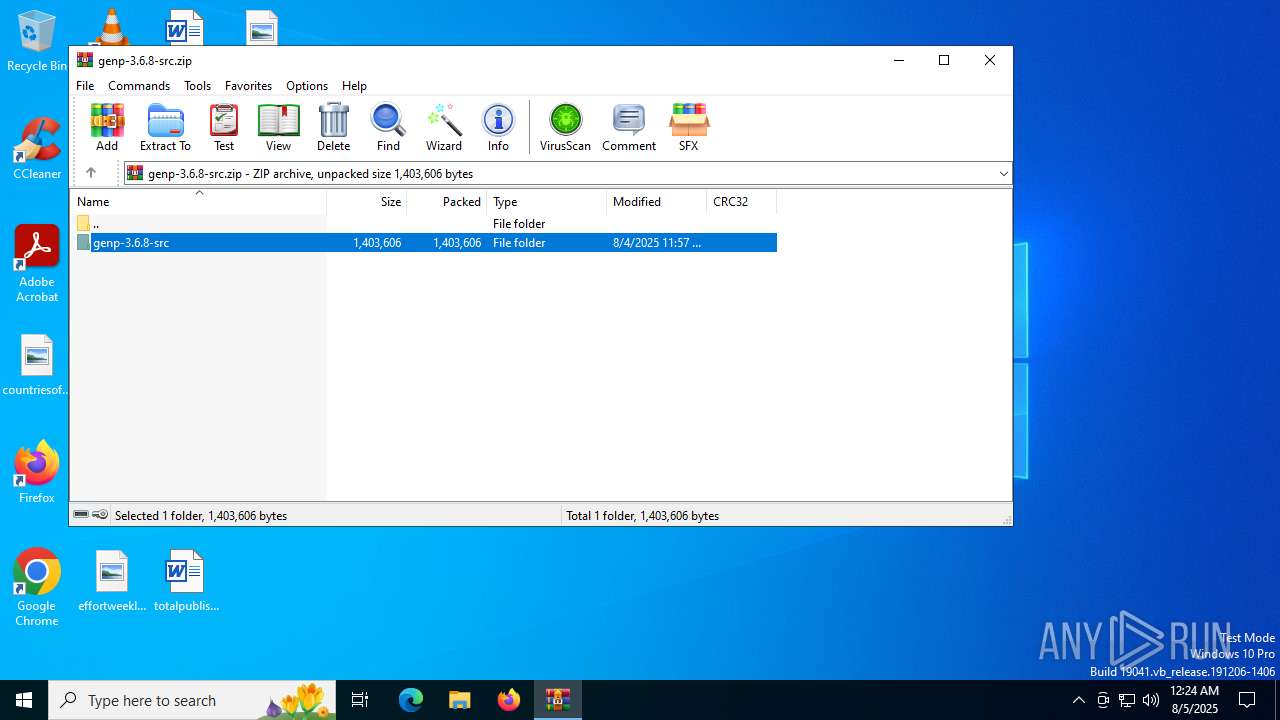
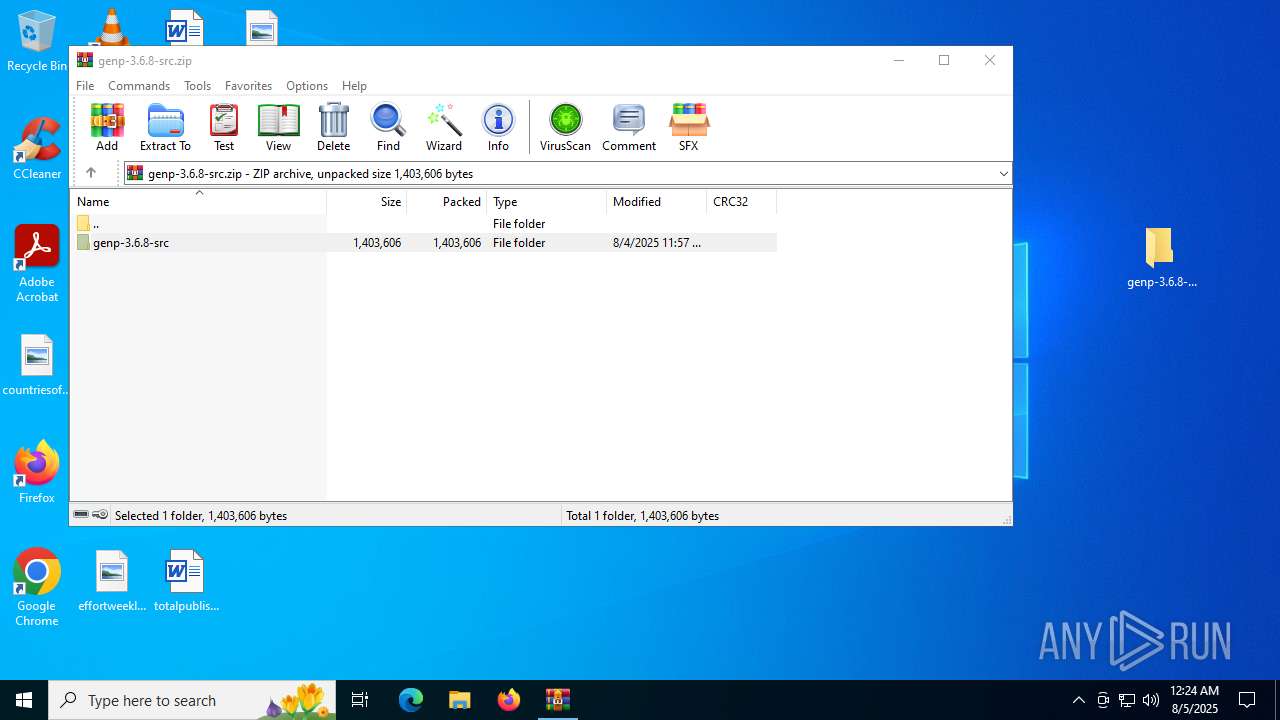
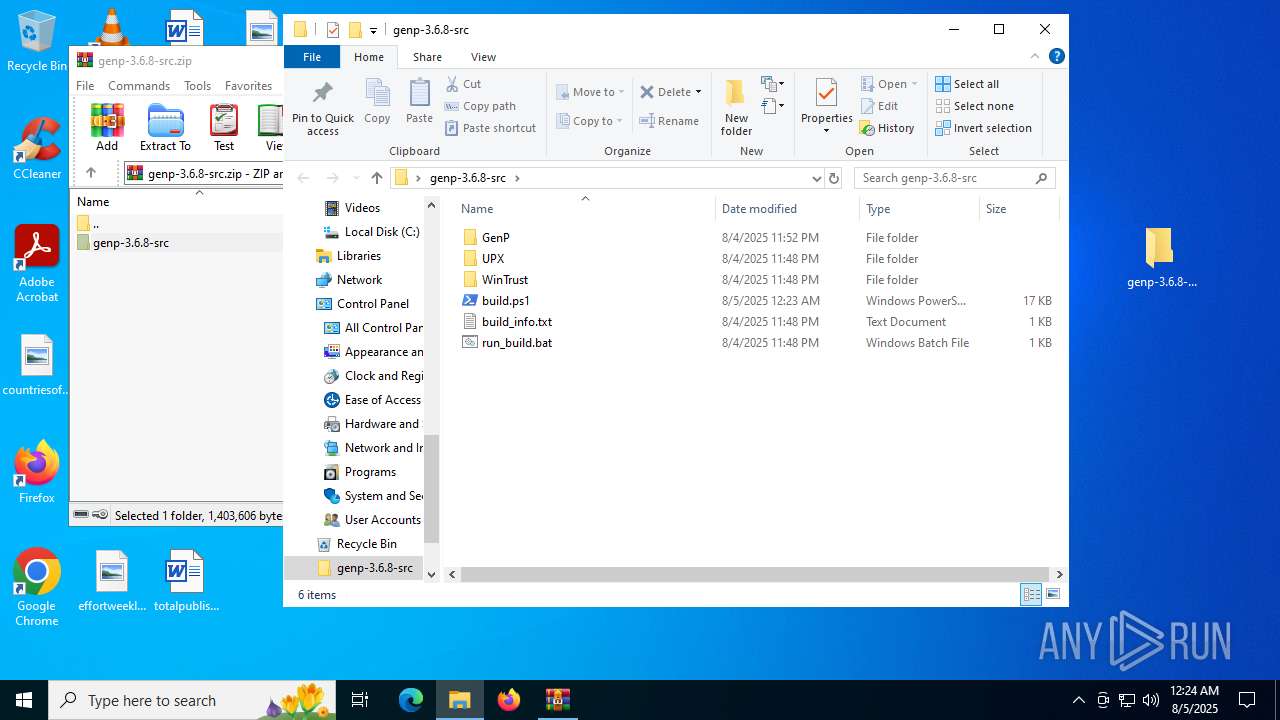
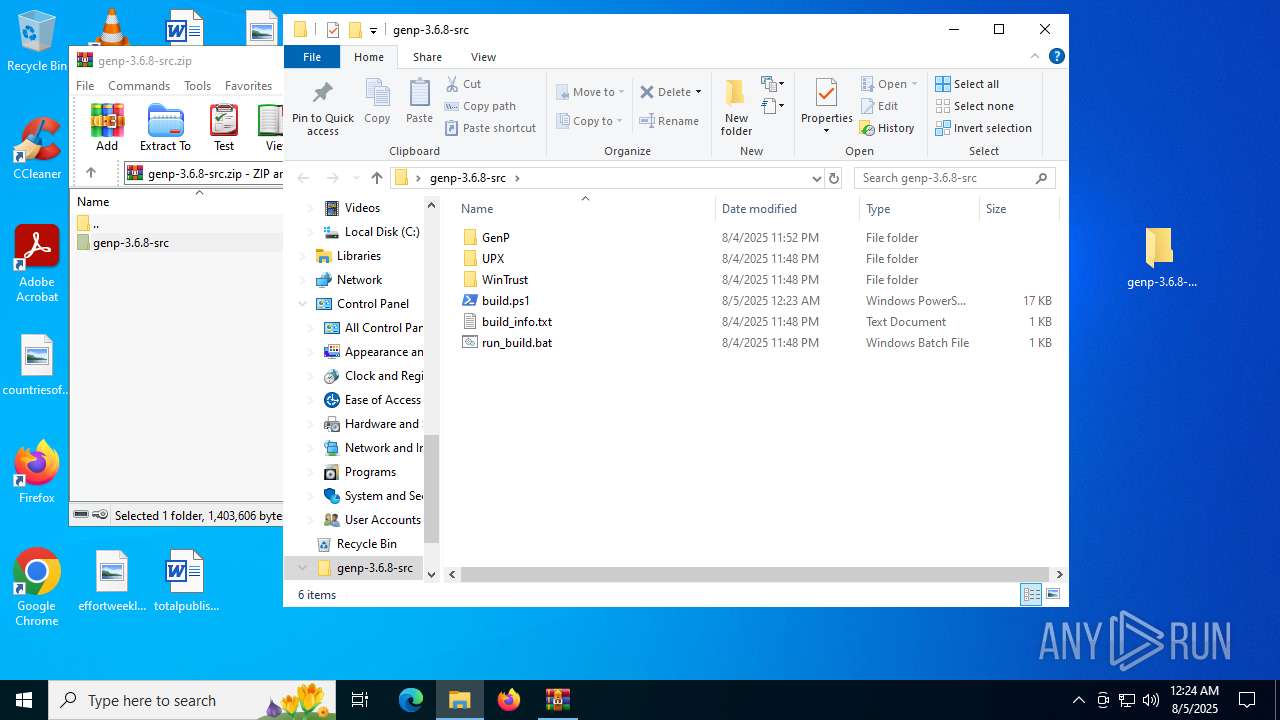
| File name: | genp-3.6.8-src.zip |
| Full analysis: | https://app.any.run/tasks/35ecfc39-8704-4b67-a961-f607a3c77fee |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2025, 00:24:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | E3A46339C44CFC17D386B2AB8BAA8F71 |
| SHA1: | 6FFE8CDAB5E575FB09599F1048378780F51F6D5F |
| SHA256: | 0D7BA3F043EA5CDCE1B74F7386413888F8D2DA59D97427FD2F68B4D702107F04 |
| SSDEEP: | 49152:pd/DzjdDsB5Rrn5mqUEPP84LRUvaflJ5/w1p6C1tGSB3CLlXTlBKcLs:p1D1c5Rrn4qxPLlEIlLRC1tJUs |
MALICIOUS
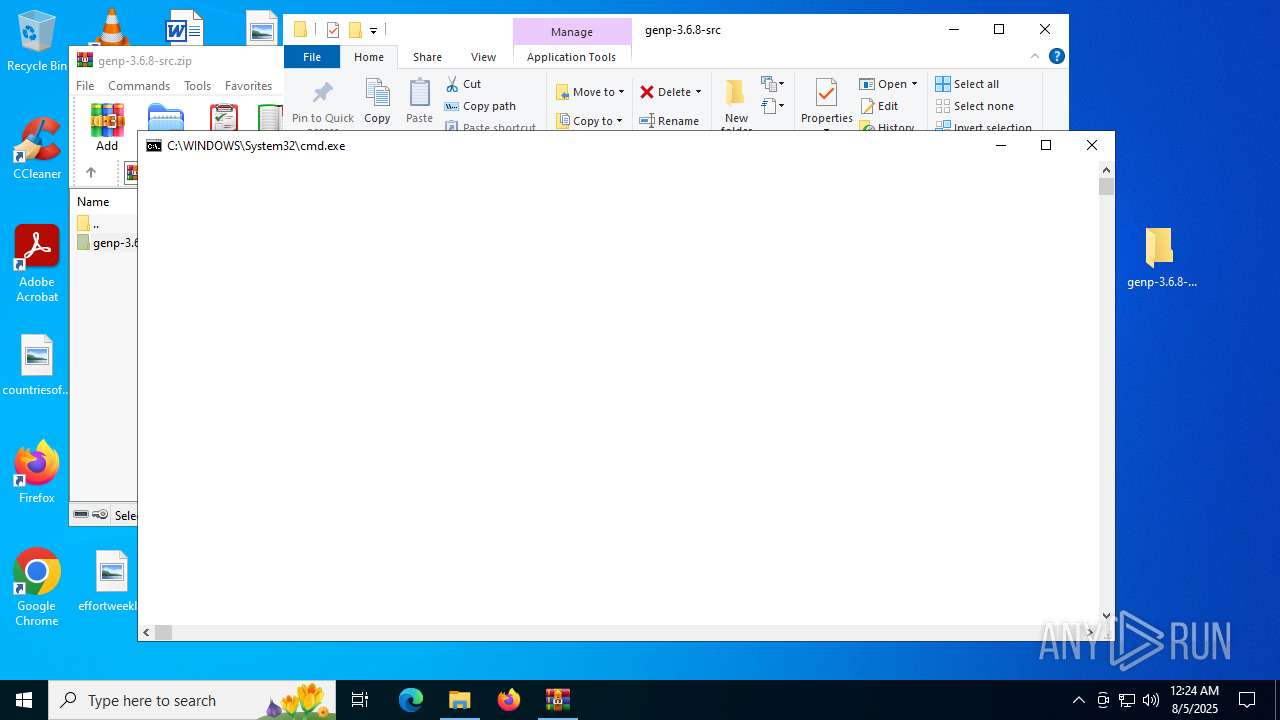
Generic archive extractor
- WinRAR.exe (PID: 3576)
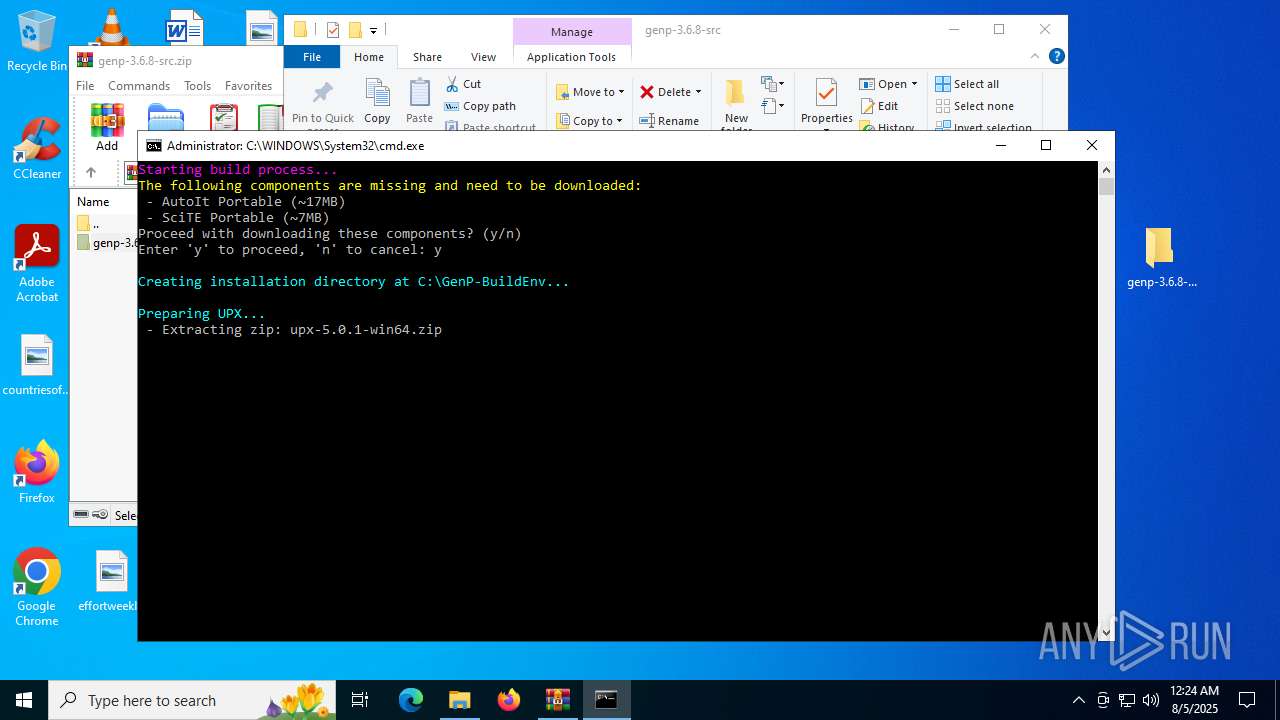
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2400)
Bypass execution policy to execute commands
- powershell.exe (PID: 6304)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 3576)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2400)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 2400)
- net.exe (PID: 1204)
The process executes Powershell scripts
- cmd.exe (PID: 2400)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 6304)
Executable content was dropped or overwritten
- tar.exe (PID: 2040)
The process executes via Task Scheduler
- updater.exe (PID: 6676)
Application launched itself
- updater.exe (PID: 6676)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 3576)
- tar.exe (PID: 2040)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3576)
Manual execution by a user
- cmd.exe (PID: 2400)
Checks supported languages
- tar.exe (PID: 2040)
- updater.exe (PID: 6676)
- updater.exe (PID: 5684)
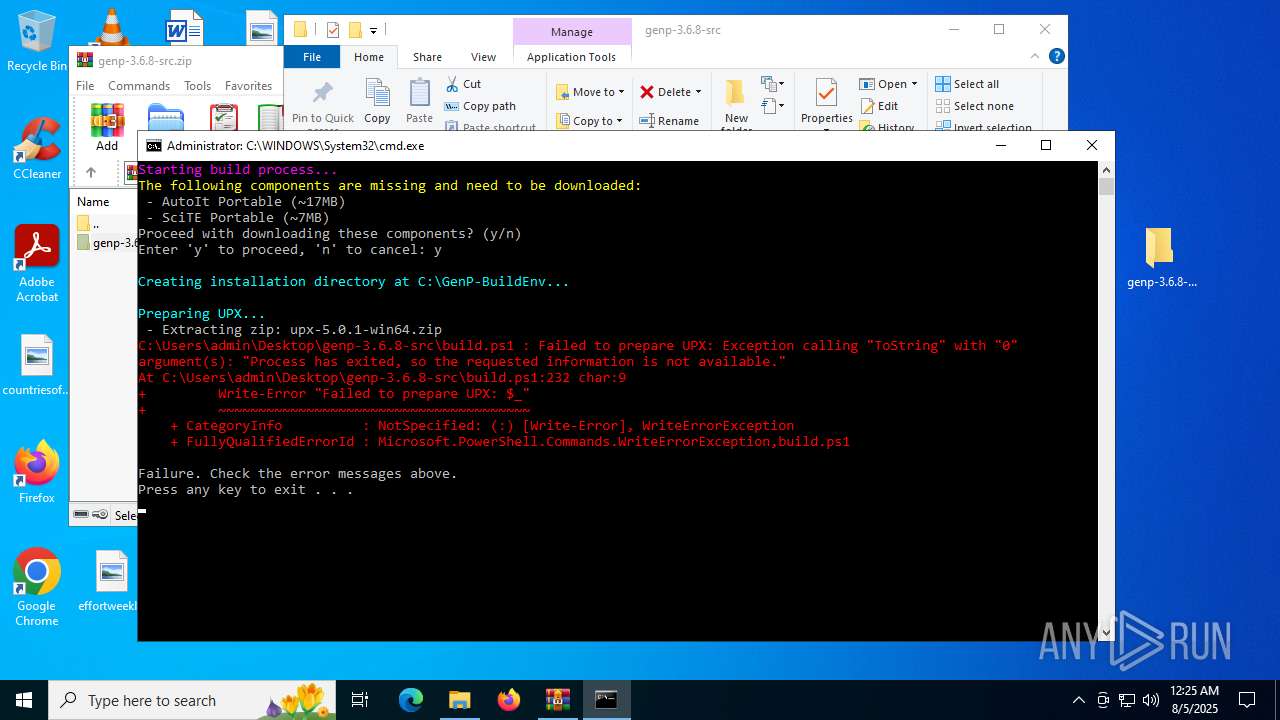
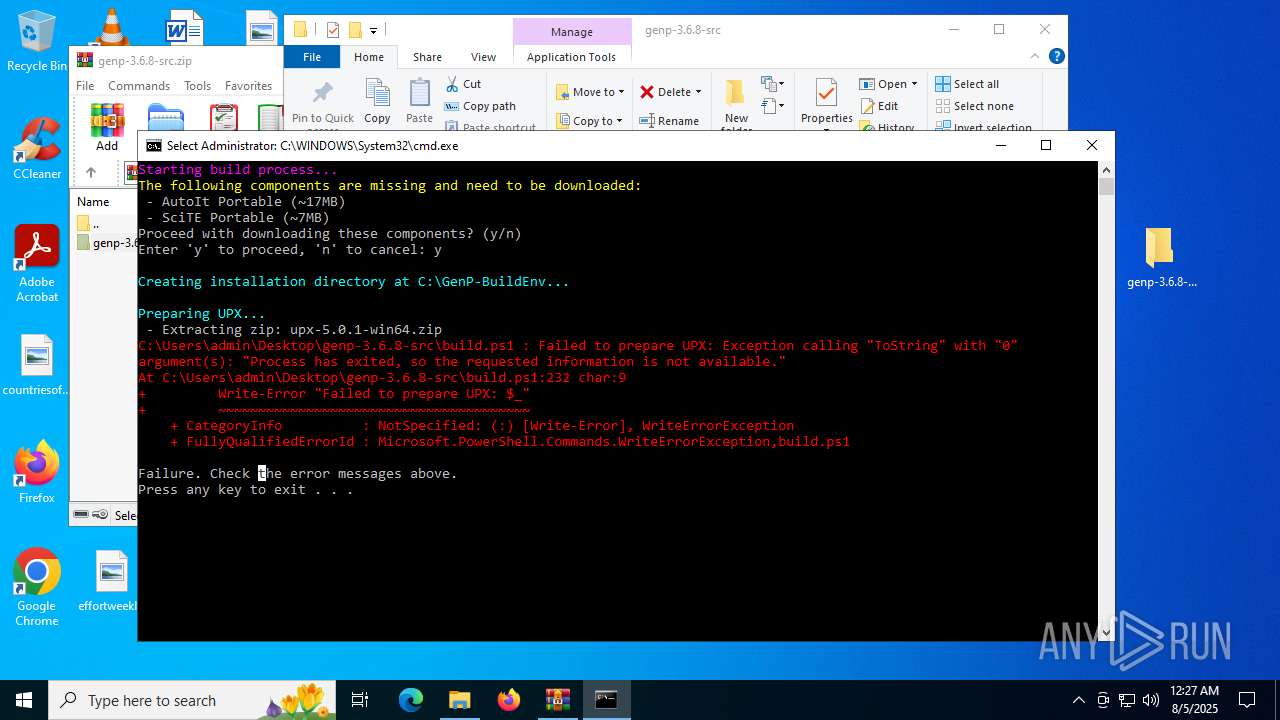
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6304)
Reads the computer name
- updater.exe (PID: 6676)
Process checks whether UAC notifications are on
- updater.exe (PID: 6676)
Checks proxy server information
- slui.exe (PID: 2348)
Reads the software policy settings
- slui.exe (PID: 2348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:08:04 19:57:08 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | genp-3.6.8-src/ |
Total processes
156
Monitored processes
12
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | "C:\WINDOWS\system32\tar.exe" -xf "C:\Users\admin\Desktop\genp-3.6.8-src\UPX\upx-5.0.1-win64.zip" -C "C:\Users\admin\Desktop\genp-3.6.8-src\UPX" | C:\Windows\System32\tar.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: bsdtar archive tool Exit code: 0 Version: 3.5.2 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2348 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
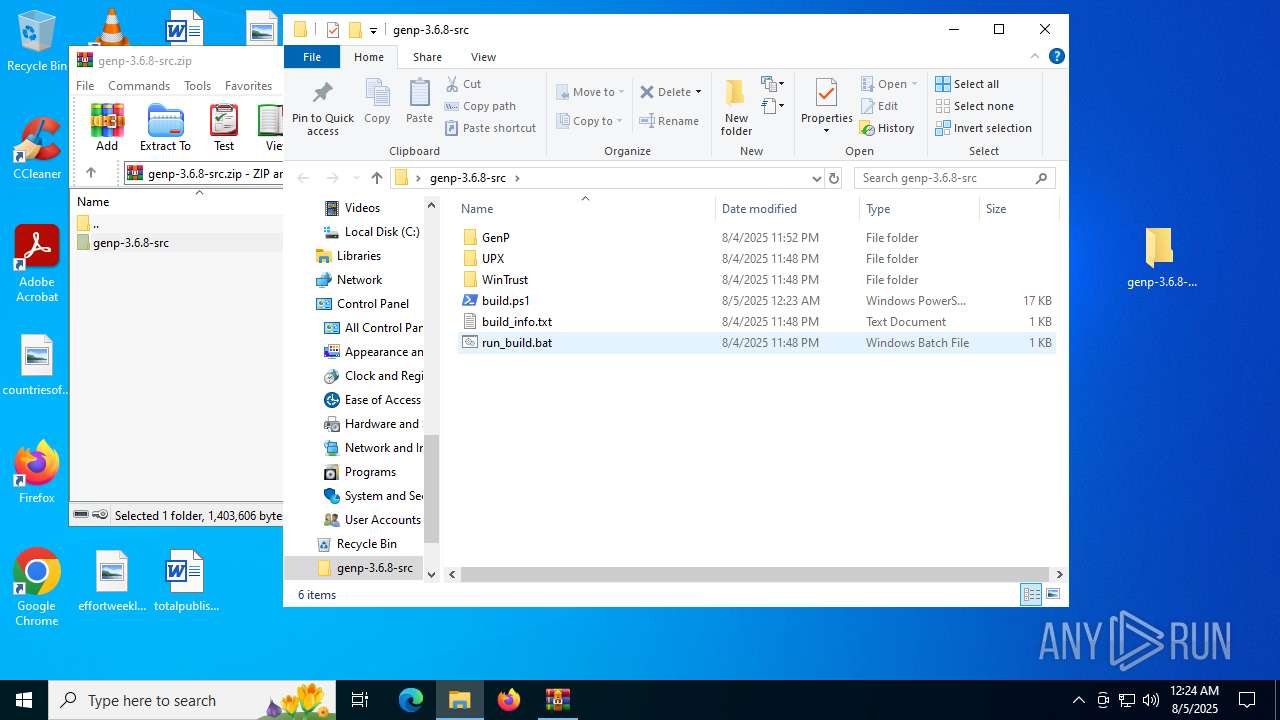
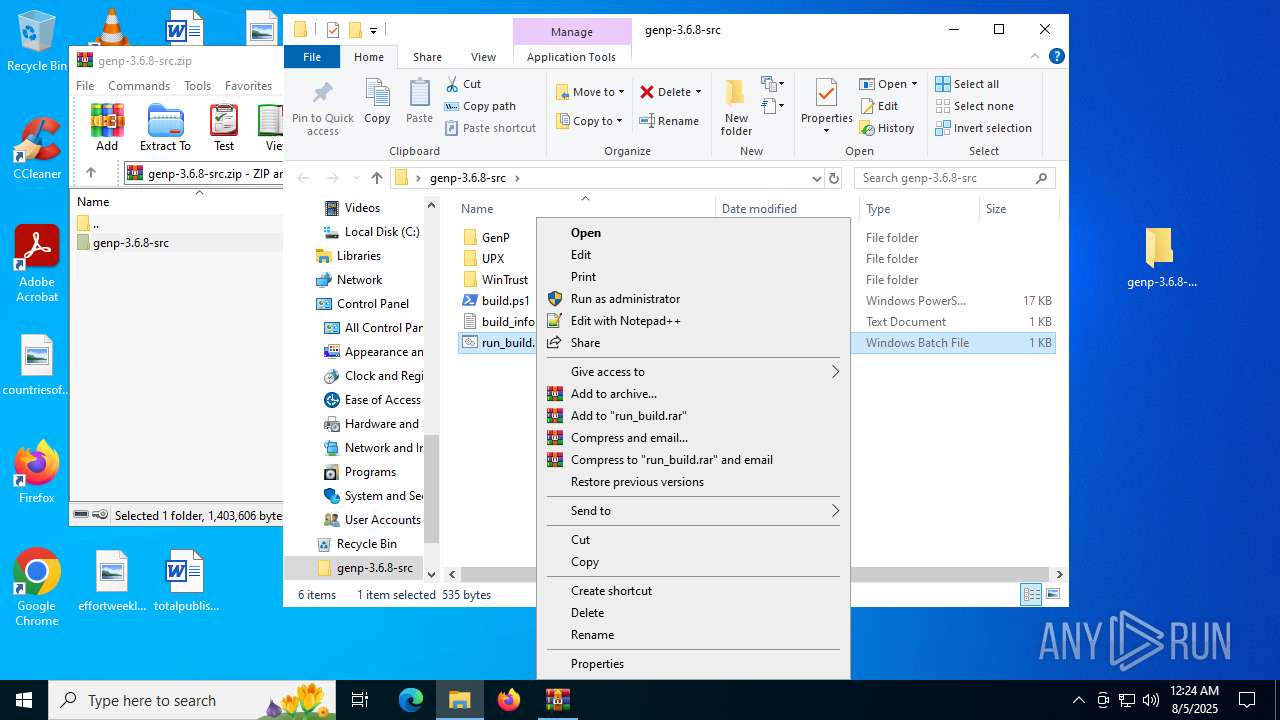
| 2400 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\genp-3.6.8-src\run_build.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2980 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3576 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\genp-3.6.8-src.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3836 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5684 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x298,0x29c,0x2a0,0x274,0x2a4,0x111c460,0x111c46c,0x111c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 6304 | powershell.exe -ExecutionPolicy Bypass -File "C:\Users\admin\Desktop\genp-3.6.8-src\build.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 192
Read events
7 184
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\genp-3.6.8-src.zip | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
3
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.26433\genp-3.6.8-src\WinTrust\wintrust.dll | executable | |
MD5:1B3BF770D4F59CA883391321A21923AE | SHA256:ECB263D1F71B514CBD3ABAE65BAC84942355E0C2B31C3C11BA35709716CAAEE4 | |||
| 2040 | tar.exe | C:\Users\admin\Desktop\genp-3.6.8-src\UPX\upx-5.0.1-win64\upx-doc.txt | text | |
MD5:2B20CF0D043C8B5C0FC0F27AECEF750D | SHA256:CDFBF5D3955DA09942C1993D8E9049EA47709765CAE5DDF134E8BF0856A28435 | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.26433\genp-3.6.8-src\UPX\upx-5.0.1-win64.zip | compressed | |
MD5:C7E44B194229B217D7E859C14714BA2F | SHA256:C288989437CE70646A62799A4DCF25B4EC7AD8FBB4F93A29E25C14856659C1A4 | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.26433\genp-3.6.8-src\GenP\Skull.ico | image | |
MD5:C37B537E533890560FE52664A7F1C1A0 | SHA256:1532311559D17CF7ECC0BE72FB47EC7D0EA086C414E2280566E0803133FD1D50 | |||
| 2040 | tar.exe | C:\Users\admin\Desktop\genp-3.6.8-src\UPX\upx-5.0.1-win64\NEWS | text | |
MD5:7A0E1C2D94CB31AC4F834B184F7E71B2 | SHA256:61816A7E22748A7D595D2080A0BD9DD03FF2A11A75F919981F27597FC8F63D84 | |||
| 6304 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gdcp5x0a.gl5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.26433\genp-3.6.8-src\run_build.bat | text | |
MD5:2A1B445614F030C40FB92204611C1034 | SHA256:E89150350B8B4D6957C180B8C044F367CDEA8D0D0B71C8F59DCA8F9EC99A2BE5 | |||
| 2040 | tar.exe | C:\Users\admin\Desktop\genp-3.6.8-src\UPX\upx-5.0.1-win64\THANKS.txt | text | |
MD5:AB6A6106F9A2AF3C3A54AD878FE1355C | SHA256:33BCF25CEDD3865B26B92B7E20E3A0F2F51BDEBEDC360122D0627995CFB4C2A6 | |||
| 2040 | tar.exe | C:\Users\admin\Desktop\genp-3.6.8-src\UPX\upx-5.0.1-win64\upx.1 | text | |
MD5:CC9D2D9860B8397A7DE936120E26F04E | SHA256:406C403C530A928E3F090D4872809CA57C9D72D9E33B15FF0EBCF572BB182451 | |||
| 2040 | tar.exe | C:\Users\admin\Desktop\genp-3.6.8-src\UPX\upx-5.0.1-win64\upx.exe | executable | |
MD5:A14ACD4E0FD7F388B6C42CDE82FEC28B | SHA256:8DEF9DABA0817636962E60878E117EE1DCBA6C3F64FB4BC13449D447385F1B5B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
29
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 193.108.153.158:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4032 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1740 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1740 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
5884 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4172 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 193.108.153.158:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4032 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |