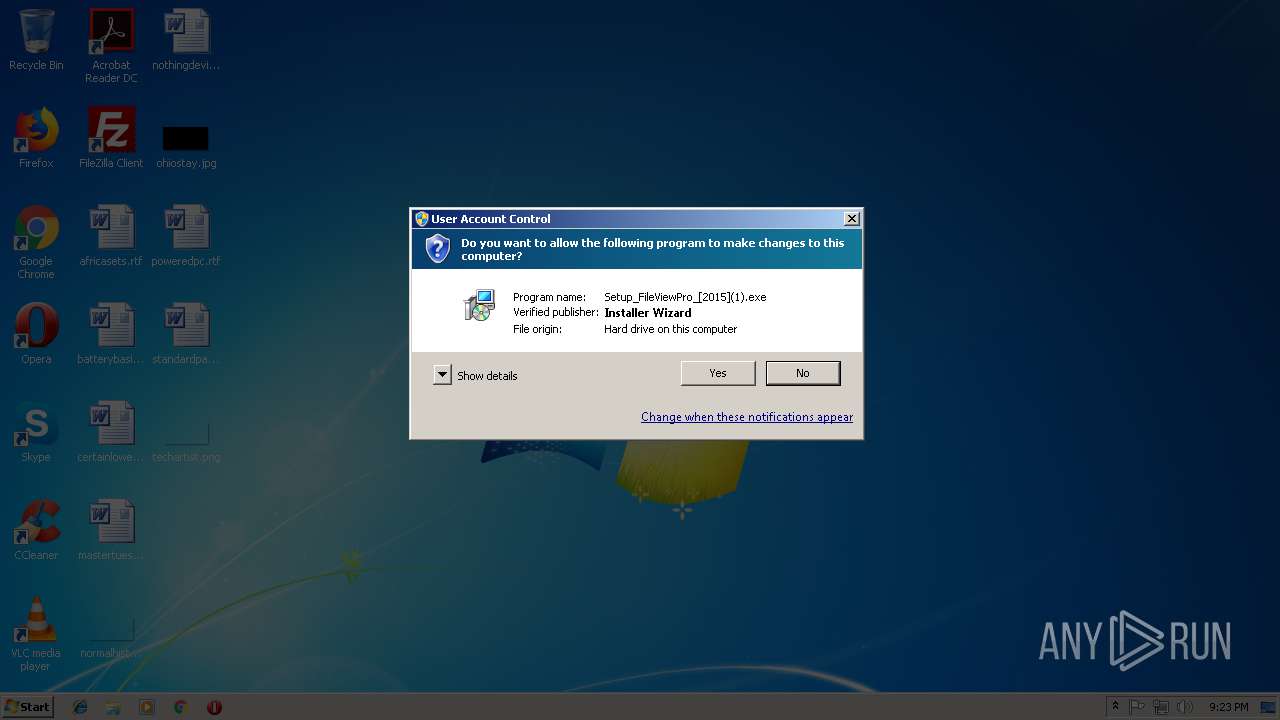
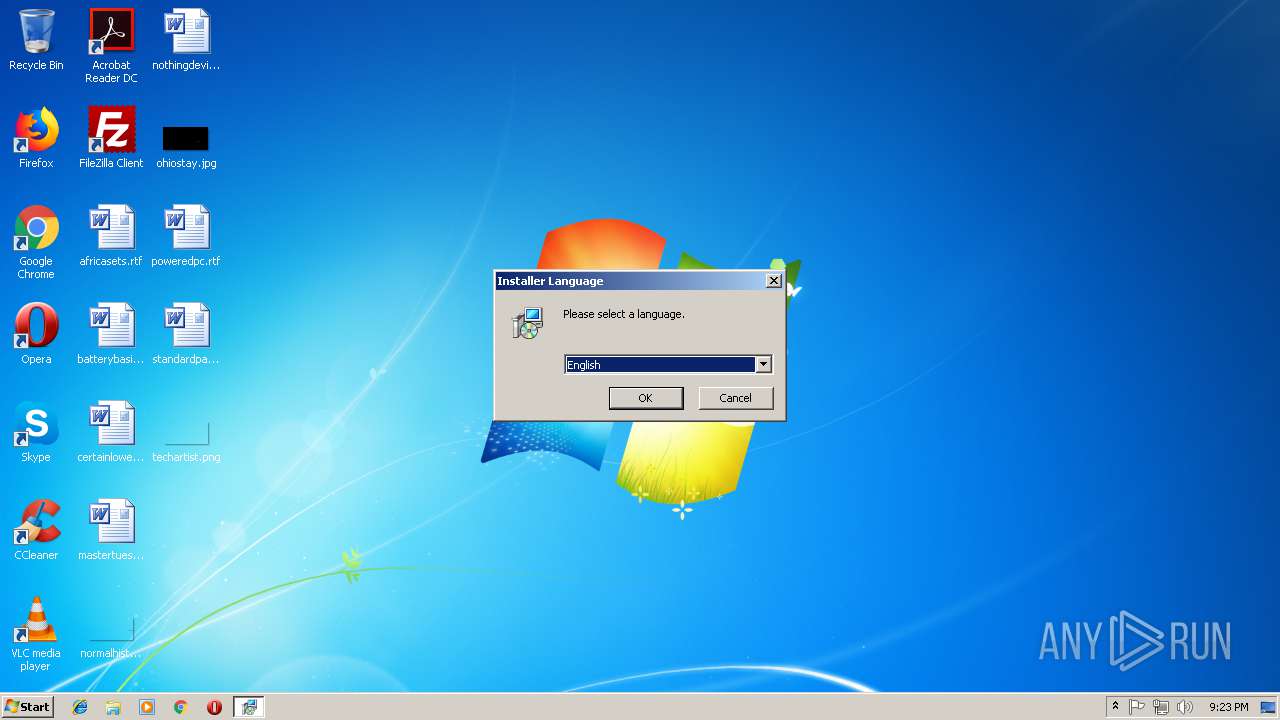
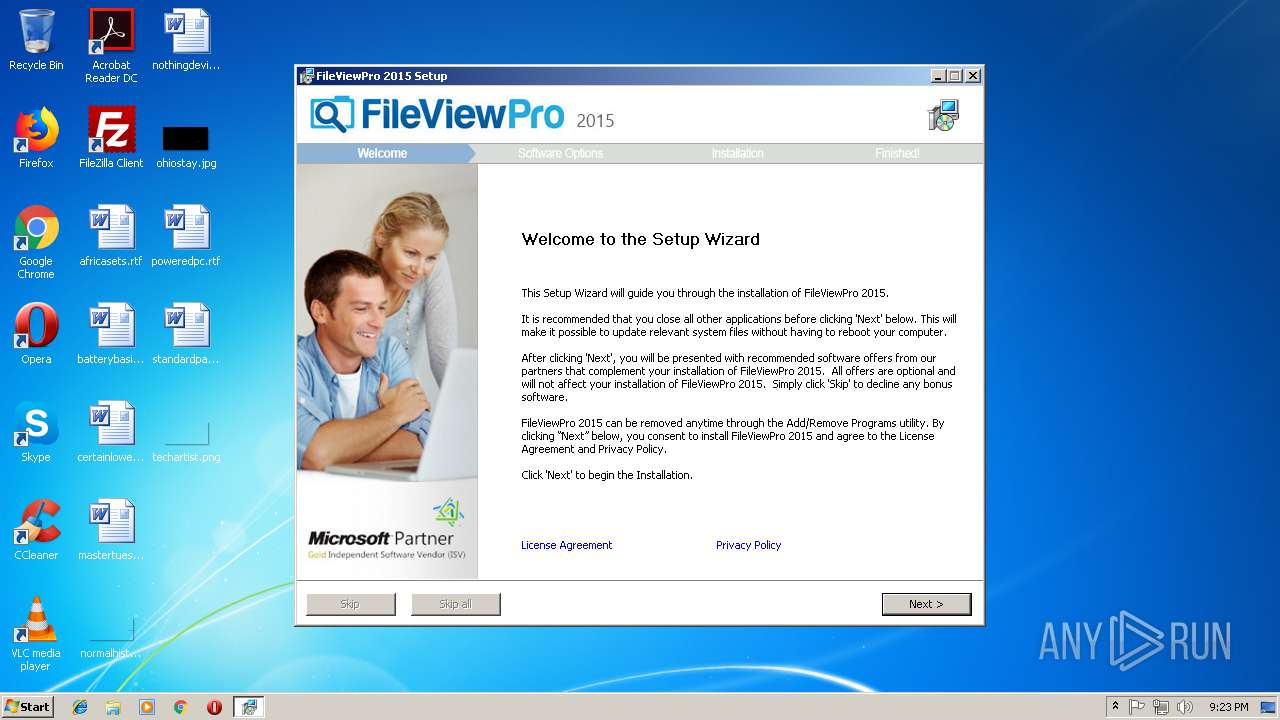
| File name: | Setup_FileViewPro_[2015](1).exe |
| Full analysis: | https://app.any.run/tasks/452398d9-e4c2-46fc-ba1e-2ddc8c5bfe0c |
| Verdict: | Malicious activity |
| Analysis date: | October 03, 2018, 20:22:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 578274049BA6266E263646D2EAE1B657 |
| SHA1: | 1CA92C4EA18B2DE382FC69916810CB1A57DD294A |
| SHA256: | 0D7423A347F37B7164DCC0972947F105525F0061805BFEA78108502FA3611F80 |
| SSDEEP: | 49152:o1/k0J5NxR792pqvEAZCv0wjTOvUT0cLzYuoP7MaQX8Mx12KwV+kQH:K/RBcpqvNZaqvAe1P7MZMMx4hVKH |
MALICIOUS
Loads dropped or rewritten executable
- Setup_FileViewPro_[2015](1).exe (PID: 2076)
- 7z.exe (PID: 2908)
- 7z.exe (PID: 2808)
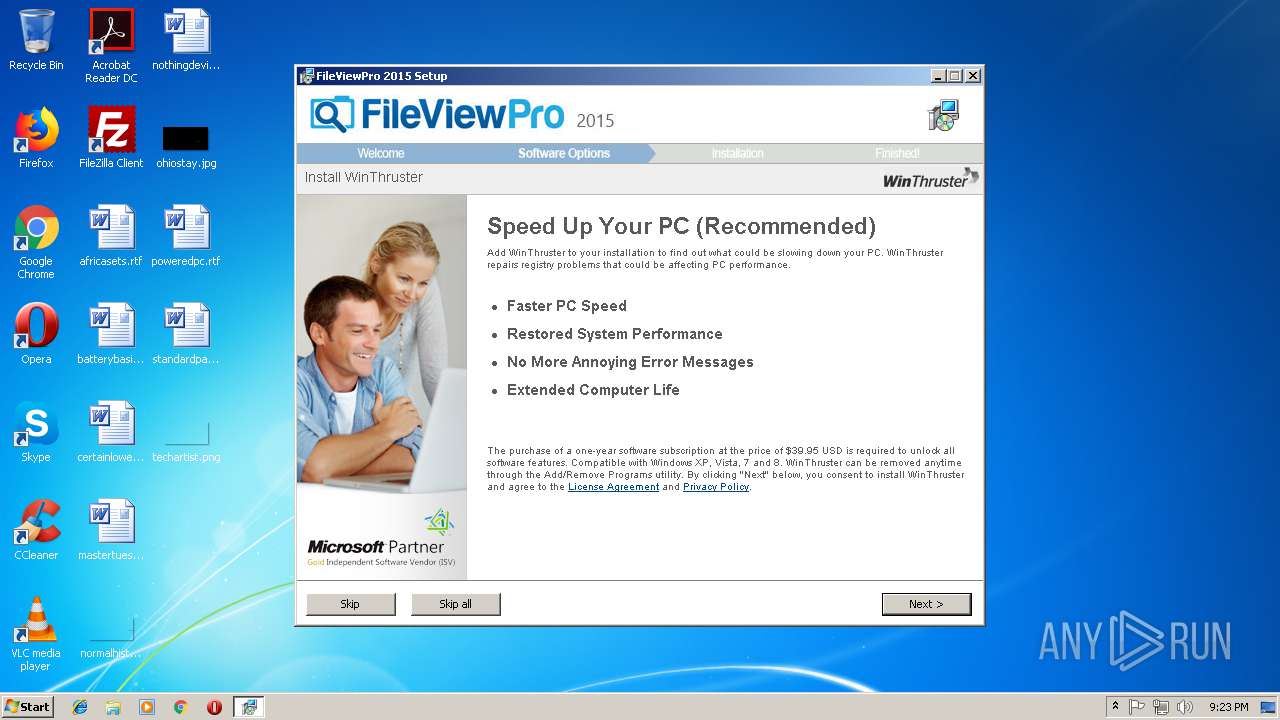
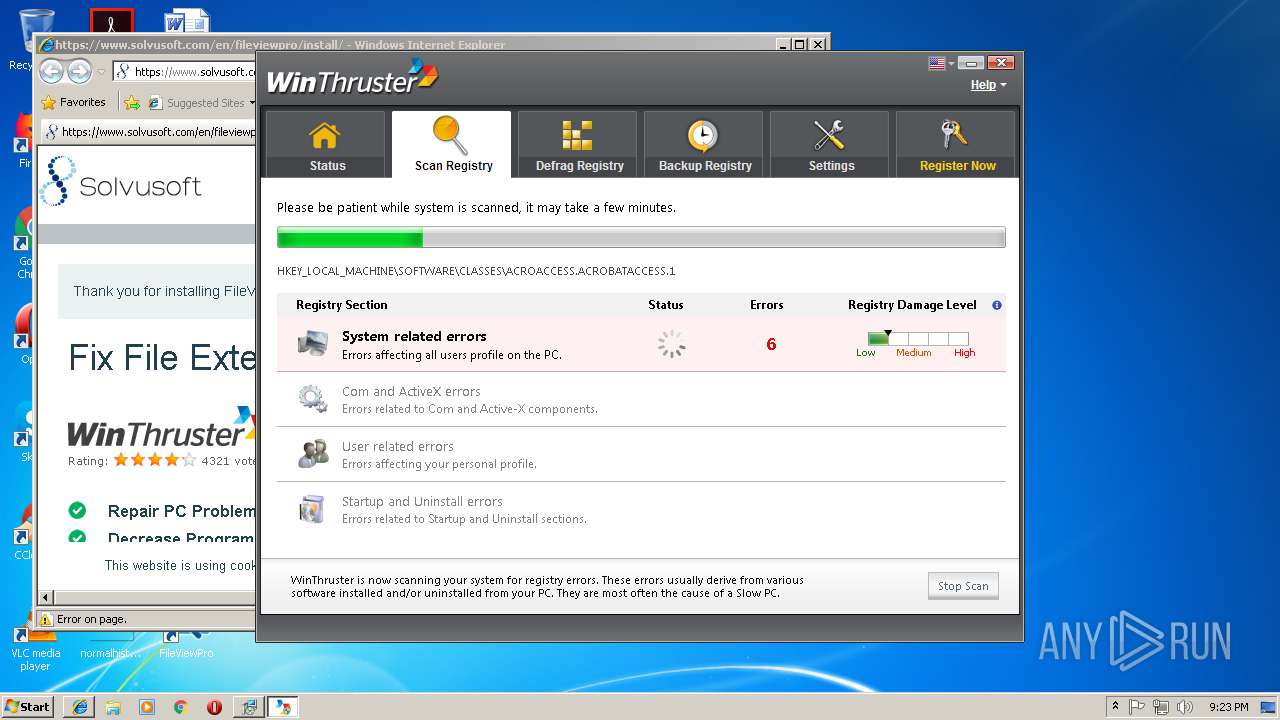
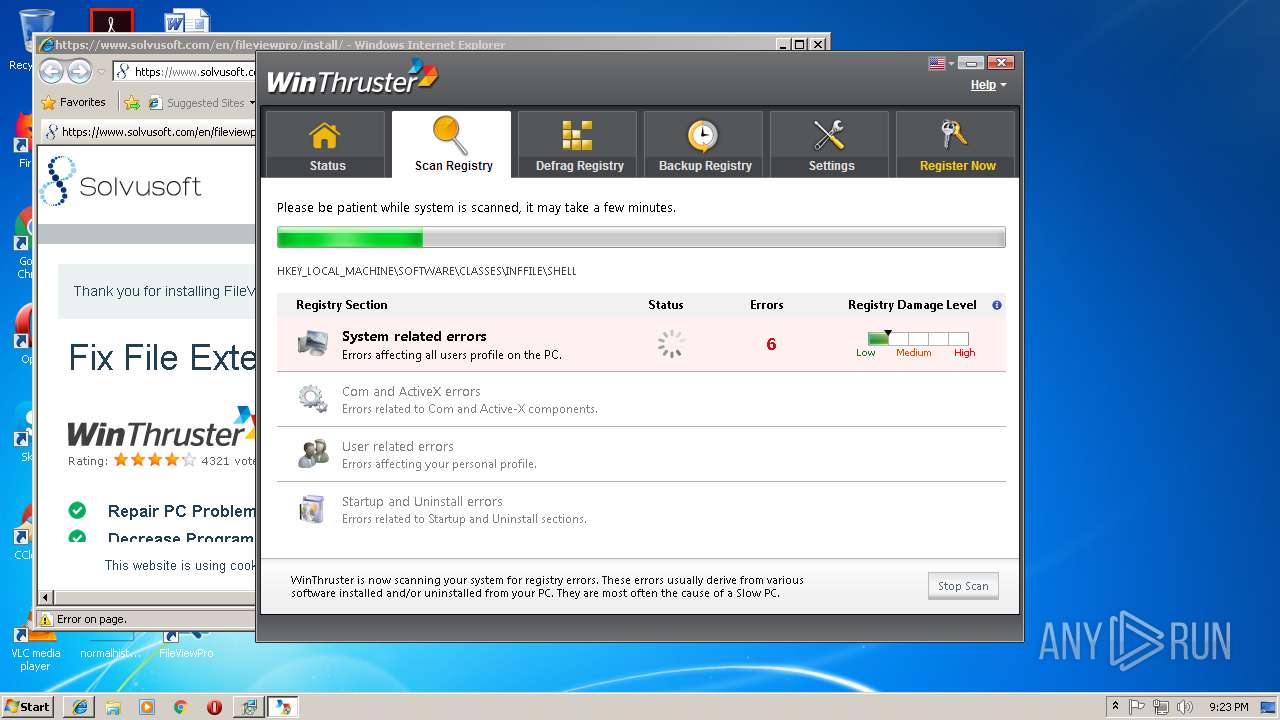
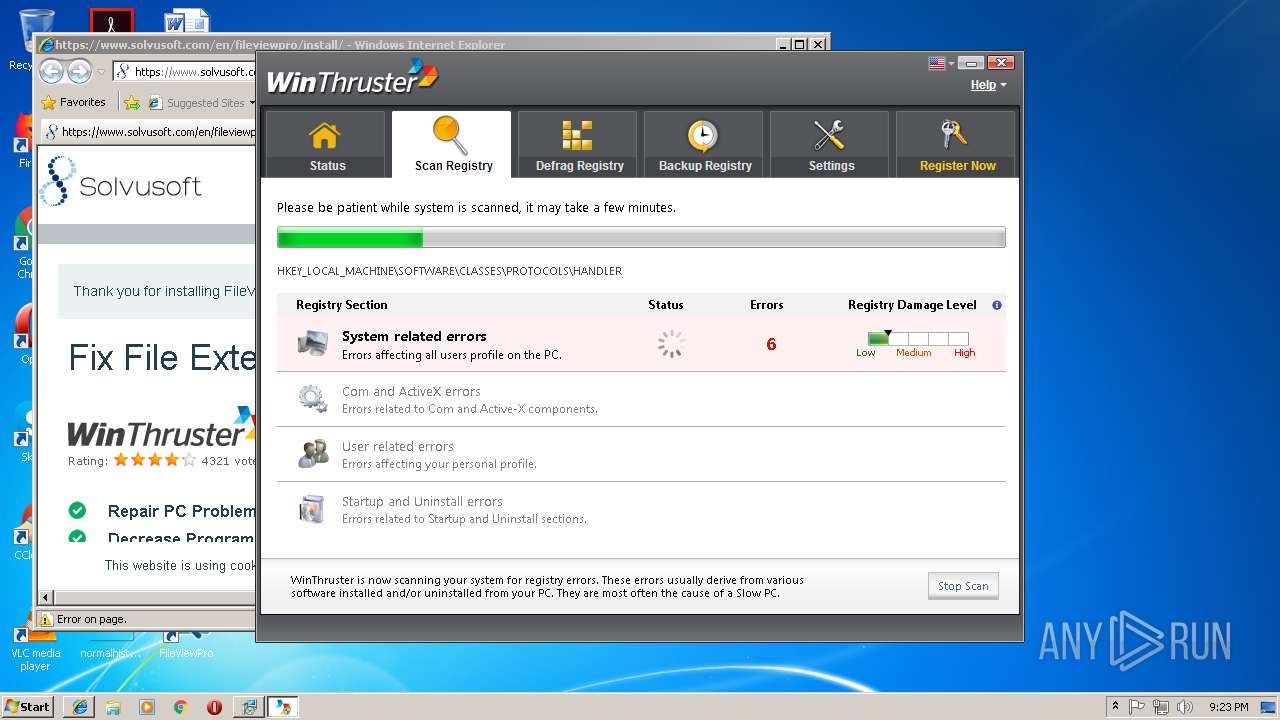
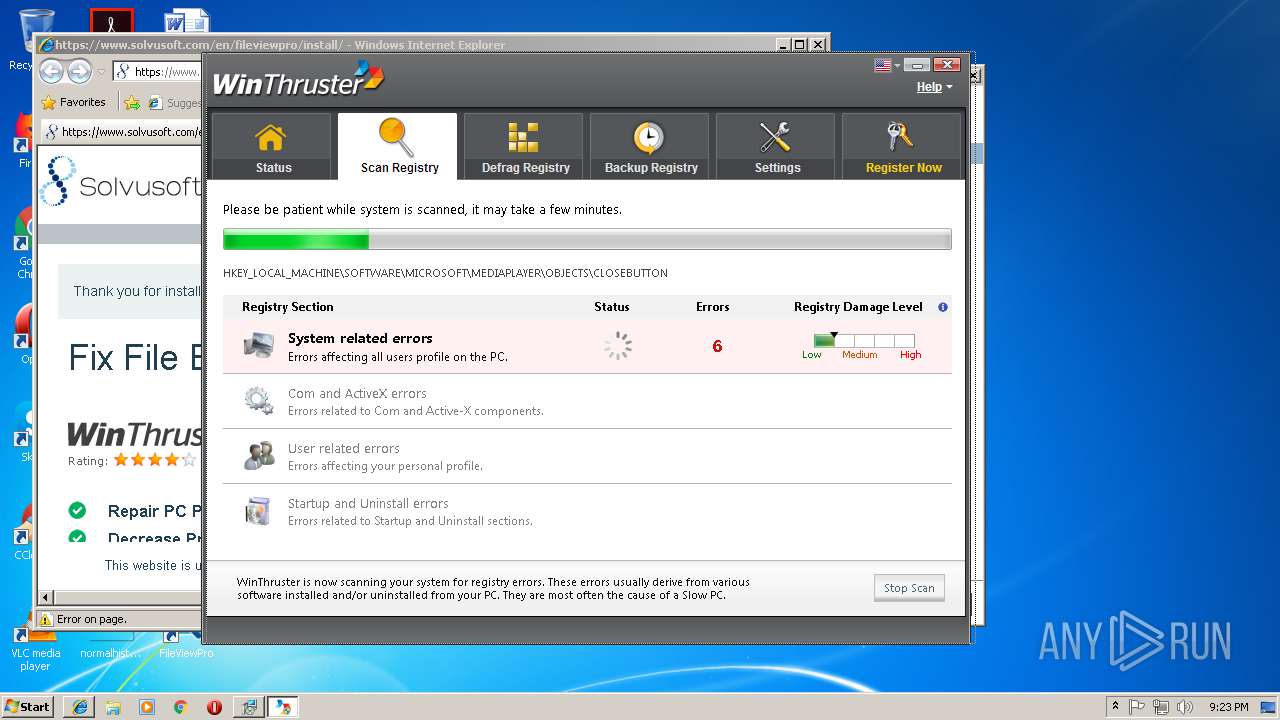
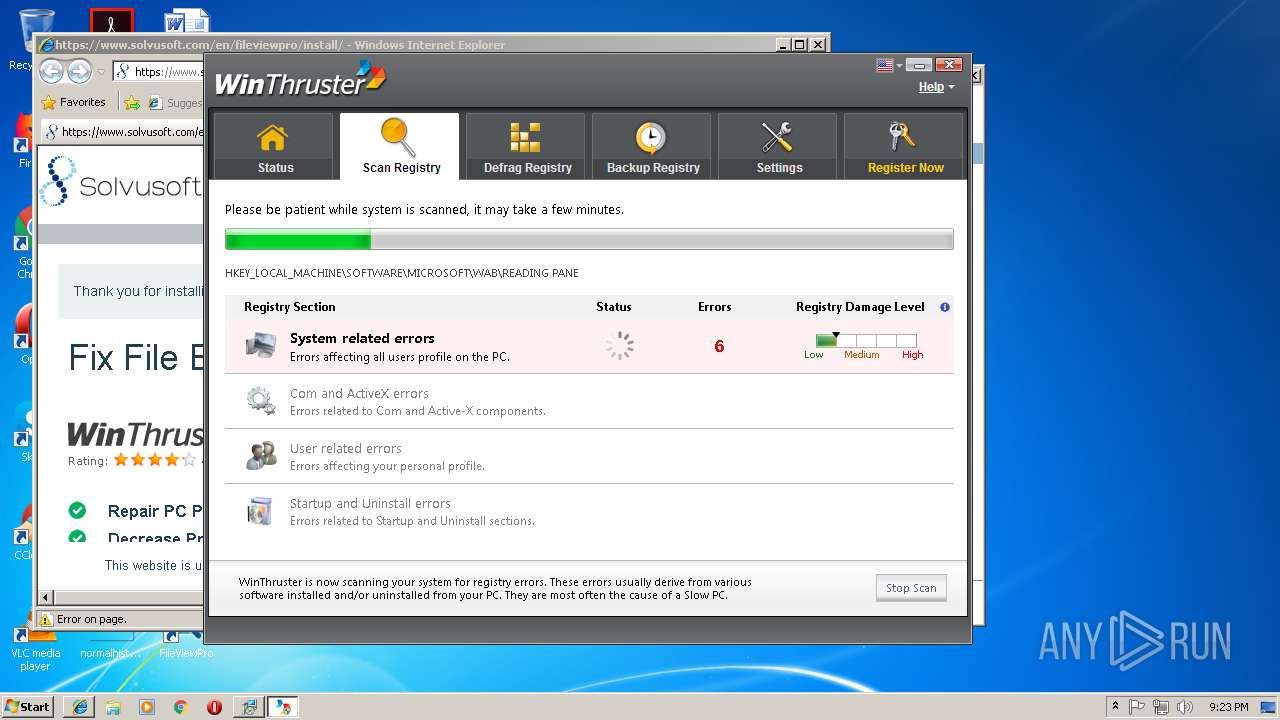
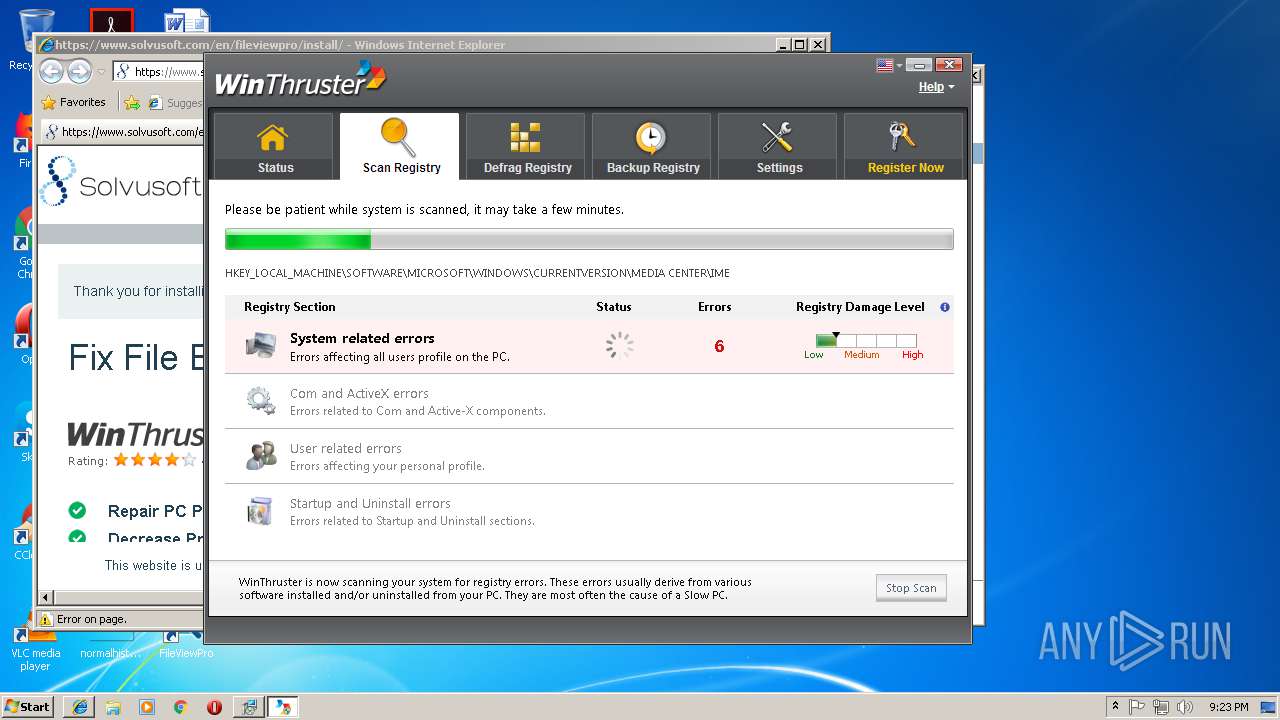
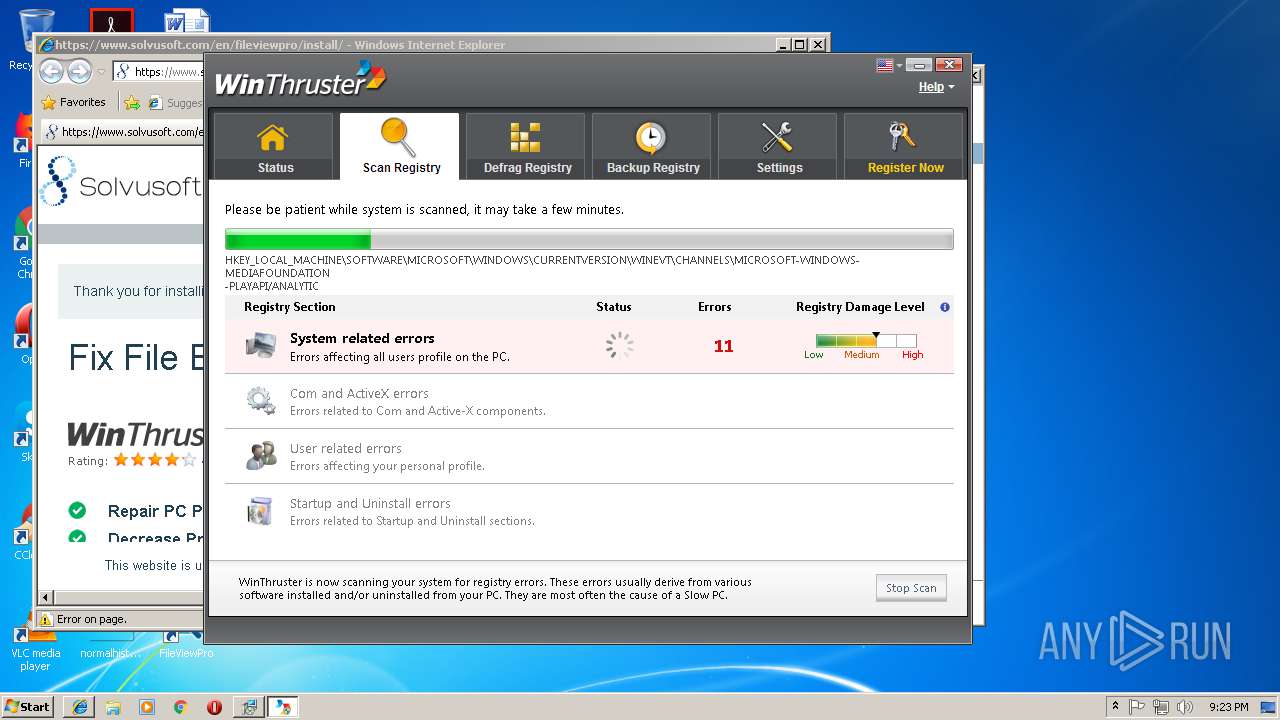
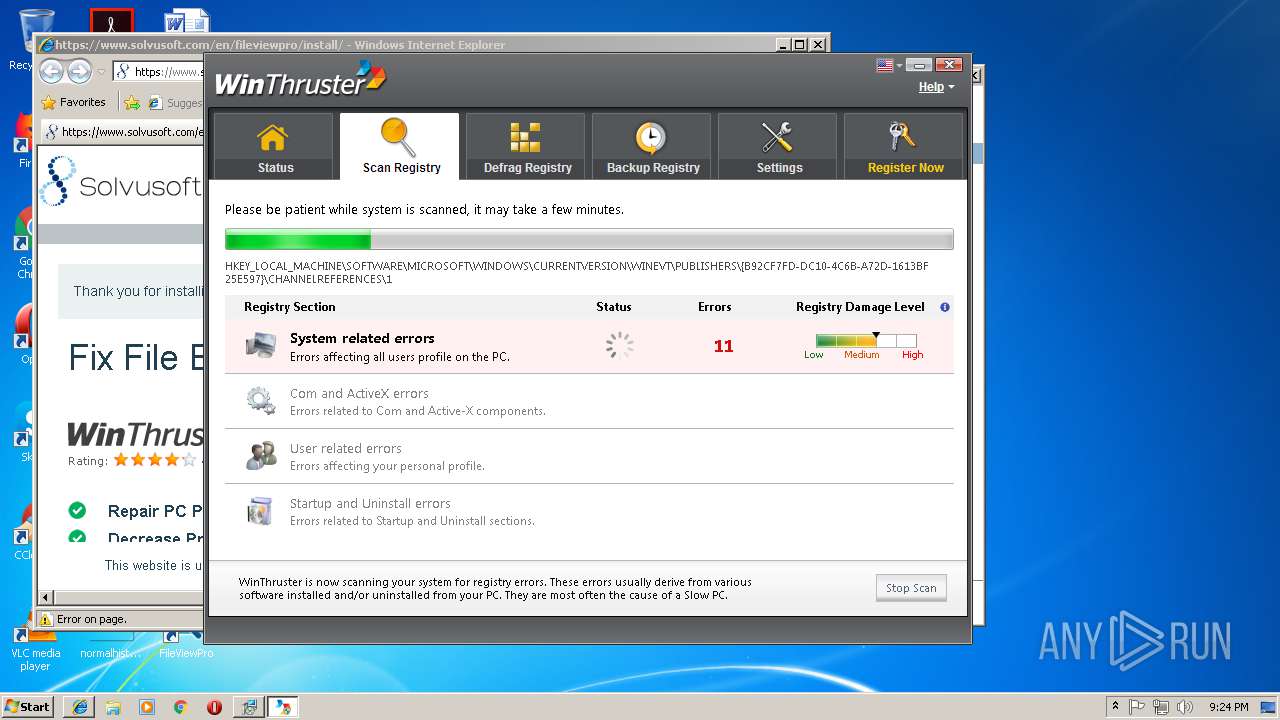
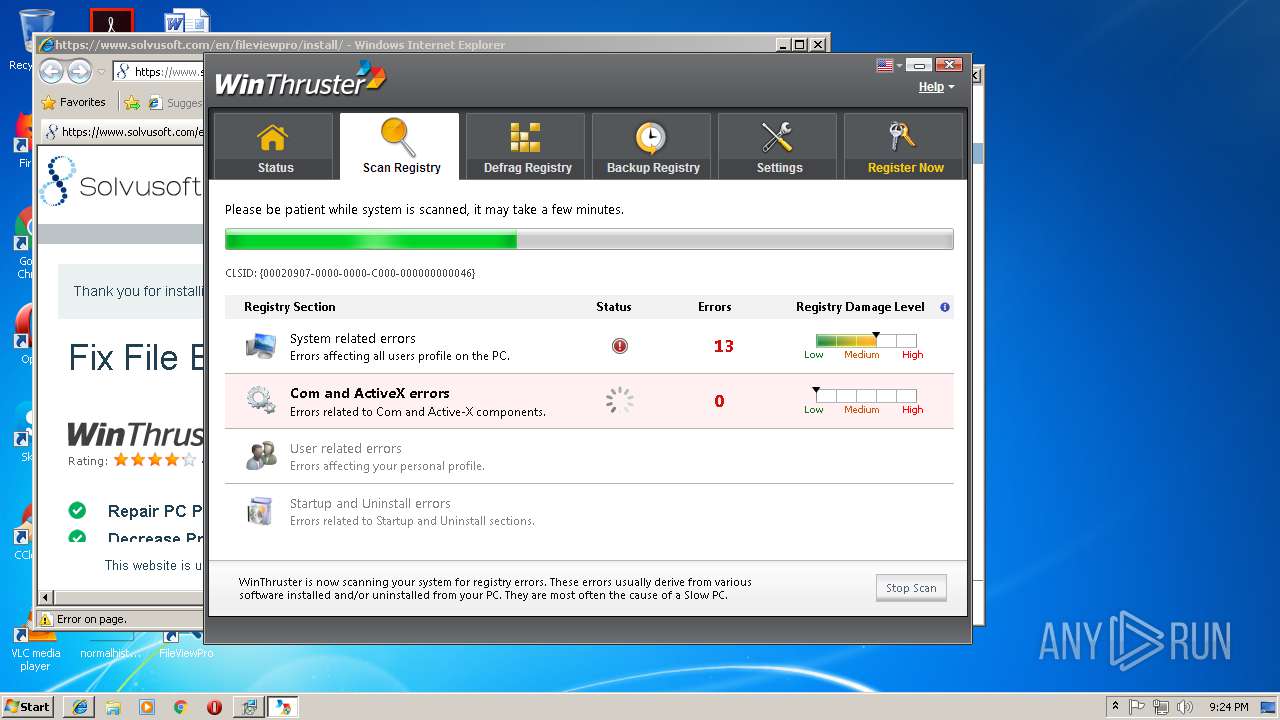
- WinThruster.exe (PID: 2668)
Application was dropped or rewritten from another process
- 7z.exe (PID: 2908)
- 7z.exe (PID: 2808)
- WinThruster_2013.exe (PID: 3128)
- ns7D69.tmp (PID: 3864)
- ns7E54.tmp (PID: 2160)
- ns81D0.tmp (PID: 4076)
- ns82AC.tmp (PID: 1508)
- FileViewPro_Build_112514.exe (PID: 2960)
- WinThruster.exe (PID: 2668)
Loads the Task Scheduler COM API
- WinThruster.exe (PID: 2668)
Loads the Task Scheduler DLL interface
- WinThruster.exe (PID: 2668)
SUSPICIOUS
Executable content was dropped or overwritten
- 7z.exe (PID: 2908)
- Setup_FileViewPro_[2015](1).exe (PID: 2076)
- FileViewPro_Build_112514.exe (PID: 2960)
- WinThruster_2013.exe (PID: 3128)
- 7z.exe (PID: 2808)
- FileViewPro_Build_112514.tmp (PID: 3276)
- WinThruster_2013.tmp (PID: 1320)
Starts application with an unusual extension
- Setup_FileViewPro_[2015](1).exe (PID: 2076)
Reads internet explorer settings
- Setup_FileViewPro_[2015](1).exe (PID: 2076)
- WinThruster.exe (PID: 2668)
Starts CMD.EXE for commands execution
- ns7D69.tmp (PID: 3864)
- ns7E54.tmp (PID: 2160)
- ns81D0.tmp (PID: 4076)
- ns82AC.tmp (PID: 1508)
Reads Internet Cache Settings
- Setup_FileViewPro_[2015](1).exe (PID: 2076)
Reads Windows owner settings
- FileViewPro_Build_112514.tmp (PID: 3276)
- WinThruster_2013.tmp (PID: 1320)
Reads the Windows organization settings
- FileViewPro_Build_112514.tmp (PID: 3276)
- WinThruster_2013.tmp (PID: 1320)
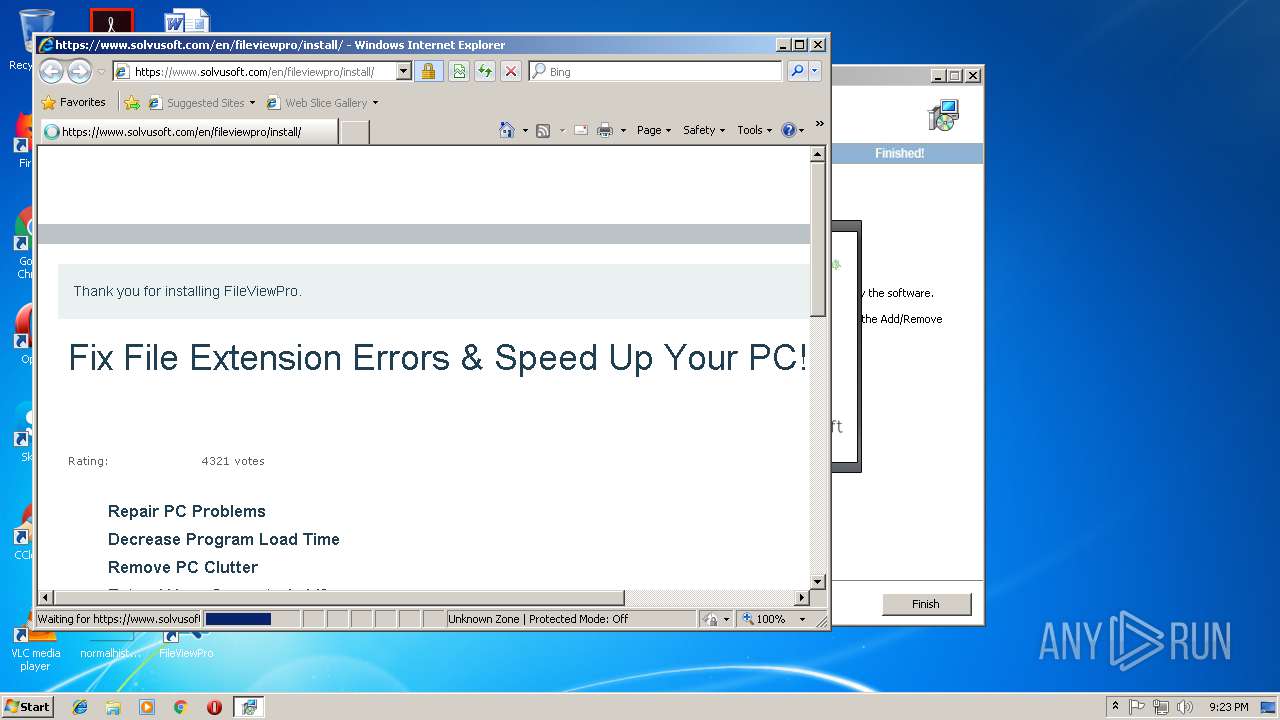
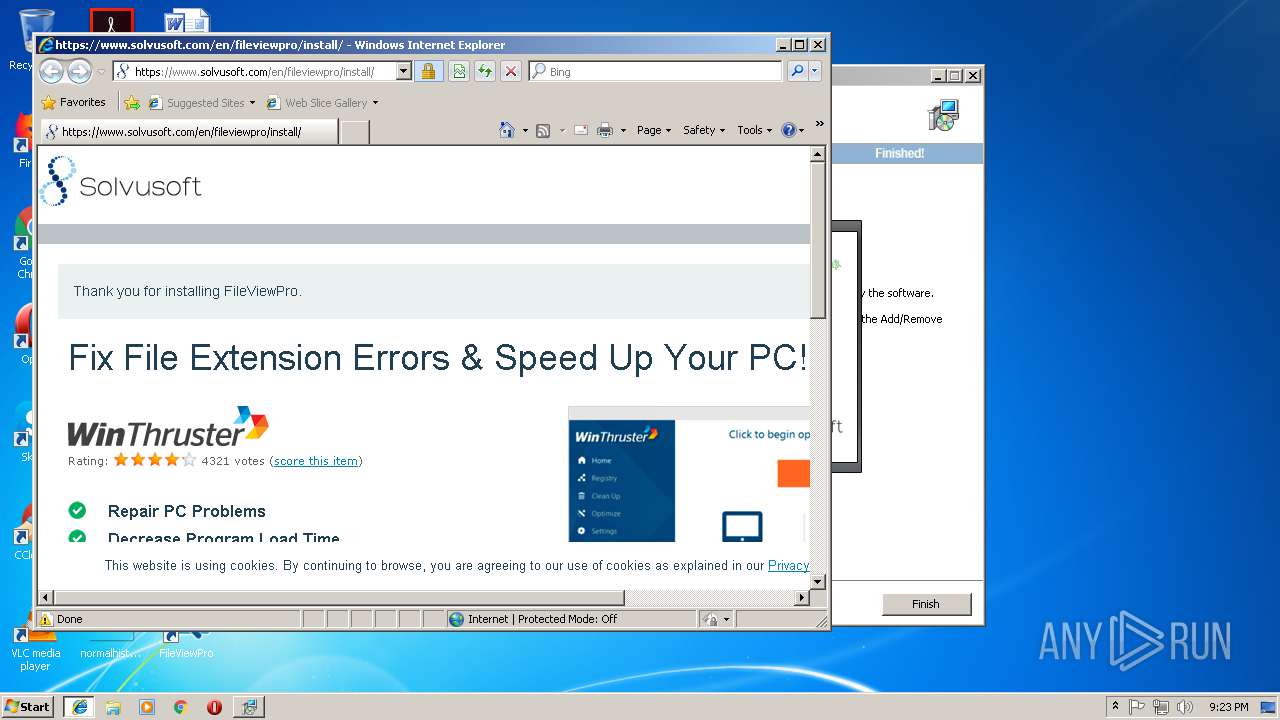
Starts Internet Explorer
- WinThruster_2013.tmp (PID: 1320)
Creates files in the Windows directory
- WinThruster_2013.tmp (PID: 1320)
- WinThruster.exe (PID: 2668)
Creates COM task schedule object
- WinThruster.exe (PID: 2668)
Creates files in the user directory
- WinThruster.exe (PID: 2668)
Check for Java to be installed
- WinThruster.exe (PID: 2668)
Reads default file associations for system extensions
- WinThruster.exe (PID: 2668)
Searches for installed software
- WinThruster.exe (PID: 2668)
INFO
Creates files in the program directory
- WinThruster_2013.tmp (PID: 1320)
- FileViewPro_Build_112514.tmp (PID: 3276)
Loads dropped or rewritten executable
- FileViewPro_Build_112514.tmp (PID: 3276)
- WinThruster_2013.tmp (PID: 1320)
Creates a software uninstall entry
- WinThruster_2013.tmp (PID: 1320)
- FileViewPro_Build_112514.tmp (PID: 3276)
Changes settings of System certificates
- iexplore.exe (PID: 3284)
Application launched itself
- iexplore.exe (PID: 3804)
Changes internet zones settings
- iexplore.exe (PID: 3804)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3284)
Reads internet explorer settings
- iexplore.exe (PID: 3284)
Reads Internet Cache Settings
- iexplore.exe (PID: 3284)
Creates files in the user directory
- iexplore.exe (PID: 3284)
Application was dropped or rewritten from another process
- FileViewPro_Build_112514.tmp (PID: 3276)
- WinThruster_2013.tmp (PID: 1320)
Reads Microsoft Office registry keys
- WinThruster.exe (PID: 2668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:11:09 12:22:34+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 31232 |
| InitializedDataSize: | 1961472 |
| UninitializedDataSize: | 90112 |
| EntryPoint: | 0x3a9e |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Nov-2014 11:22:34 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 09-Nov-2014 11:22:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000078C0 | 0x00007A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46825 |
.rdata | 0x00009000 | 0x00002B7A | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.5024 |
.data | 0x0000C000 | 0x001DA258 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.79989 |
.ndata | 0x001E7000 | 0x00DA6000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00F8D000 | 0x00007070 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.83749 |
.reloc | 0x00F95000 | 0x00000A18 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.14366 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21712 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.69042 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 3.34446 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.60495 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.71364 | 642 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.89384 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
58
Monitored processes
19
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | cmd /c C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\Setup_FileViewPro_[2015]\unpack-1.bat | C:\Windows\system32\cmd.exe | — | ns82AC.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1320 | "C:\Users\admin\AppData\Local\Temp\is-RC2D8.tmp\WinThruster_2013.tmp" /SL5="$380216,3416180,143360,C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\Setup_FileViewPro_[2015]\dir-1\WinThruster_2013.exe" /verysilent | C:\Users\admin\AppData\Local\Temp\is-RC2D8.tmp\WinThruster_2013.tmp | WinThruster_2013.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1508 | "C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\ns82AC.tmp" C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\Setup_FileViewPro_[2015]\unpack-1.bat | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\ns82AC.tmp | — | Setup_FileViewPro_[2015](1).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1776 | cmd /c C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\Setup_FileViewPro_[2015]\join-5.bat | C:\Windows\system32\cmd.exe | — | ns7D69.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\AppData\Local\Temp\Setup_FileViewPro_[2015](1).exe" | C:\Users\admin\AppData\Local\Temp\Setup_FileViewPro_[2015](1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2160 | "C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\ns7E54.tmp" C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\Setup_FileViewPro_[2015]\unpack-5.bat | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\ns7E54.tmp | — | Setup_FileViewPro_[2015](1).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2316 | "C:\Users\admin\AppData\Local\Temp\Setup_FileViewPro_[2015](1).exe" | C:\Users\admin\AppData\Local\Temp\Setup_FileViewPro_[2015](1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2524 | cmd /c C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\Setup_FileViewPro_[2015]\join-1.bat | C:\Windows\system32\cmd.exe | — | ns81D0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2668 | "C:\Program Files\WinThruster\WinThruster.exe" | C:\Program Files\WinThruster\WinThruster.exe | WinThruster_2013.tmp | ||||||||||||
User: admin Company: Solvusoft Corporation Integrity Level: HIGH Description: WinThruster Exit code: 0 Version: 1.79.69.2469 Modules
| |||||||||||||||
| 2808 | 7z.exe x -odir-1 complete-file-1.zip | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\Setup_FileViewPro_[2015]\7z.exe | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Console Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
Total events
3 803
Read events
3 579
Write events
216
Delete events
8
Modification events
| (PID) Process: | (2076) Setup_FileViewPro_[2015](1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2076) Setup_FileViewPro_[2015](1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2076) Setup_FileViewPro_[2015](1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_FileViewPro_[2015](1)_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2076) Setup_FileViewPro_[2015](1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_FileViewPro_[2015](1)_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2076) Setup_FileViewPro_[2015](1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_FileViewPro_[2015](1)_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2076) Setup_FileViewPro_[2015](1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_FileViewPro_[2015](1)_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2076) Setup_FileViewPro_[2015](1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_FileViewPro_[2015](1)_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2076) Setup_FileViewPro_[2015](1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_FileViewPro_[2015](1)_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2076) Setup_FileViewPro_[2015](1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_FileViewPro_[2015](1)_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2076) Setup_FileViewPro_[2015](1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_FileViewPro_[2015](1)_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
98
Suspicious files
14
Text files
120
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2076 | Setup_FileViewPro_[2015](1).exe | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\NSISdl.dll | executable | |
MD5:— | SHA256:— | |||
| 2076 | Setup_FileViewPro_[2015](1).exe | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\fileviewpro-2015-bonus-edition.jpg | image | |
MD5:— | SHA256:— | |||
| 2076 | Setup_FileViewPro_[2015](1).exe | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\nsArray.pdb | pdb | |
MD5:6AEE0E72609A8610498D13269A9DFC54 | SHA256:62CAFD3146E0425ABAE0140D7A5624993BB7E7ADA0C7B67D7E07F7F650D338F2 | |||
| 2076 | Setup_FileViewPro_[2015](1).exe | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\inetc.pdb | pdb | |
MD5:BB0D5487E423BAA4D6CBAED5F7E330C6 | SHA256:4C1D94B28952F65462DA058E51D3B7EF813F13A5A4C74EB9BED3C557EBAC67B9 | |||
| 2076 | Setup_FileViewPro_[2015](1).exe | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\progress_welcome.jpg | image | |
MD5:C31FF5F4C648C9239D91B47171104872 | SHA256:2D0F7CC6BA0B7259A5D5E2EADE1FACE762CF46DB335E7CC5D1982F3312B36B55 | |||
| 2076 | Setup_FileViewPro_[2015](1).exe | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\LangDLL.dll | executable | |
MD5:D202091693CE9FEE894C5A38484683AA | SHA256:EA9BC93DEF62805CC2D9E0116B5A0BB0AA7CCBBD0D516E43E5A89F5806698874 | |||
| 2076 | Setup_FileViewPro_[2015](1).exe | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\Banner.dll | executable | |
MD5:978CE7033321CC4793AD7FBAB6E4EE2F | SHA256:893F154F62264786DEAD3DF552C671D48AAF757B89805F5AA864BE650C469D6D | |||
| 2076 | Setup_FileViewPro_[2015](1).exe | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\button.bmp | image | |
MD5:19AE63749B1247EFD5318E632DFBBE4D | SHA256:6F5E51BEABF1AE13E0F1D368D1FC0CFBDE7CD860204E02578C325CB6ECC1C25A | |||
| 2076 | Setup_FileViewPro_[2015](1).exe | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\nsWeb.dll | executable | |
MD5:36382F1D8E93727900EFE9ED4388693E | SHA256:413FFCB2EBF34A2EF2873E2B03D21CF2021DBFAB7B259DE3EA2AC310F38EBD4E | |||
| 2076 | Setup_FileViewPro_[2015](1).exe | C:\Users\admin\AppData\Local\Temp\nsq58DF.tmp\nsArray.dll | executable | |
MD5:E9DF0C769FAB7F03CA4C24F1D5117381 | SHA256:62116DF27594BE55AAF70F6B63D5C393CA98E2133D1B3CC602592488F5ACE217 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
24
DNS requests
12
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2076 | Setup_FileViewPro_[2015](1).exe | GET | 200 | 2.19.43.105:80 | http://www.solvusoft.com/file-downloads/builds/static_delivery/file_parts/fileviewpro/build_112514/FileViewPro_Build_112514.zip.003 | unknown | binary | 5.00 Mb | whitelisted |
2076 | Setup_FileViewPro_[2015](1).exe | GET | 200 | 2.19.43.105:80 | http://www.solvusoft.com/file-downloads/builds/static_delivery/file_parts/fileviewpro/build_112514/FileViewPro_Build_112514.zip.001 | unknown | compressed | 5.00 Mb | whitelisted |
2076 | Setup_FileViewPro_[2015](1).exe | GET | 200 | 2.19.43.105:80 | http://www.solvusoft.com/file-downloads/builds/static_delivery/file_parts/fileviewpro/build_112514/FileViewPro_Build_112514.zip.002 | unknown | binary | 5.00 Mb | whitelisted |
2076 | Setup_FileViewPro_[2015](1).exe | GET | 200 | 2.19.43.105:80 | http://www.solvusoft.com/file-downloads/builds/static_delivery/file_parts/fileviewpro/build_112514/FileViewPro_Build_112514.zip.004 | unknown | binary | 4.34 Mb | whitelisted |
2076 | Setup_FileViewPro_[2015](1).exe | GET | 200 | 2.19.43.105:80 | http://www.solvusoft.com/file-downloads/builds/deliverysystem/file_parts/winthruster/systweak/build_101414/WinThruster_Build_STWK_101414.zip.001 | unknown | compressed | 2.00 Mb | whitelisted |
3284 | iexplore.exe | GET | 301 | 2.19.43.105:80 | http://www.solvusoft.com/en/winthruster/install/?ver=wtsystwk179&utm_source=winthruster&utm_campaign=default&utm_medium=newbuild | unknown | html | 177 b | whitelisted |
2076 | Setup_FileViewPro_[2015](1).exe | GET | 200 | 2.19.43.105:80 | http://www.solvusoft.com/file-downloads/builds/deliverysystem/file_parts/winthruster/systweak/build_101414/WinThruster_Build_STWK_101414.zip.002 | unknown | binary | 1.63 Mb | whitelisted |
2076 | Setup_FileViewPro_[2015](1).exe | GET | 200 | 2.19.43.105:80 | http://www.solvusoft.com/file-downloads/builds/deliverysystem/file_parts/winthruster/systweak/build_101414/WinThruster_Build_STWK_101414.zip.001 | unknown | compressed | 2.00 Mb | whitelisted |
3284 | iexplore.exe | GET | 301 | 2.19.43.105:80 | http://www.solvusoft.com/en/fileviewpro/install/ | unknown | html | 177 b | whitelisted |
3804 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2076 | Setup_FileViewPro_[2015](1).exe | 2.19.43.105:80 | www.solvusoft.com | Akamai International B.V. | — | whitelisted |
3804 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3284 | iexplore.exe | 2.19.43.105:80 | www.solvusoft.com | Akamai International B.V. | — | whitelisted |
3284 | iexplore.exe | 2.19.43.105:443 | www.solvusoft.com | Akamai International B.V. | — | whitelisted |
3284 | iexplore.exe | 23.45.106.123:443 | seal.websecurity.norton.com | Akamai International B.V. | NL | whitelisted |
3284 | iexplore.exe | 216.58.210.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3284 | iexplore.exe | 151.101.2.110:443 | js-agent.newrelic.com | Fastly | US | suspicious |
3284 | iexplore.exe | 172.217.21.238:443 | www.googlecommerce.com | Google Inc. | US | whitelisted |
3284 | iexplore.exe | 216.58.206.14:443 | www.youtube.com | Google Inc. | US | whitelisted |
3284 | iexplore.exe | 216.58.210.14:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.solvusoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
seal.websecurity.norton.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
js-agent.newrelic.com |
| whitelisted |
www.googlecommerce.com |
| whitelisted |
www.youtube.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
bam.nr-data.net |
| whitelisted |
s.ytimg.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2076 | Setup_FileViewPro_[2015](1).exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
2076 | Setup_FileViewPro_[2015](1).exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
2076 | Setup_FileViewPro_[2015](1).exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
2076 | Setup_FileViewPro_[2015](1).exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
2076 | Setup_FileViewPro_[2015](1).exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
2076 | Setup_FileViewPro_[2015](1).exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
2076 | Setup_FileViewPro_[2015](1).exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
2076 | Setup_FileViewPro_[2015](1).exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
2076 | Setup_FileViewPro_[2015](1).exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
2076 | Setup_FileViewPro_[2015](1).exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
Process | Message |
|---|---|
WinThruster.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
WinThruster.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |