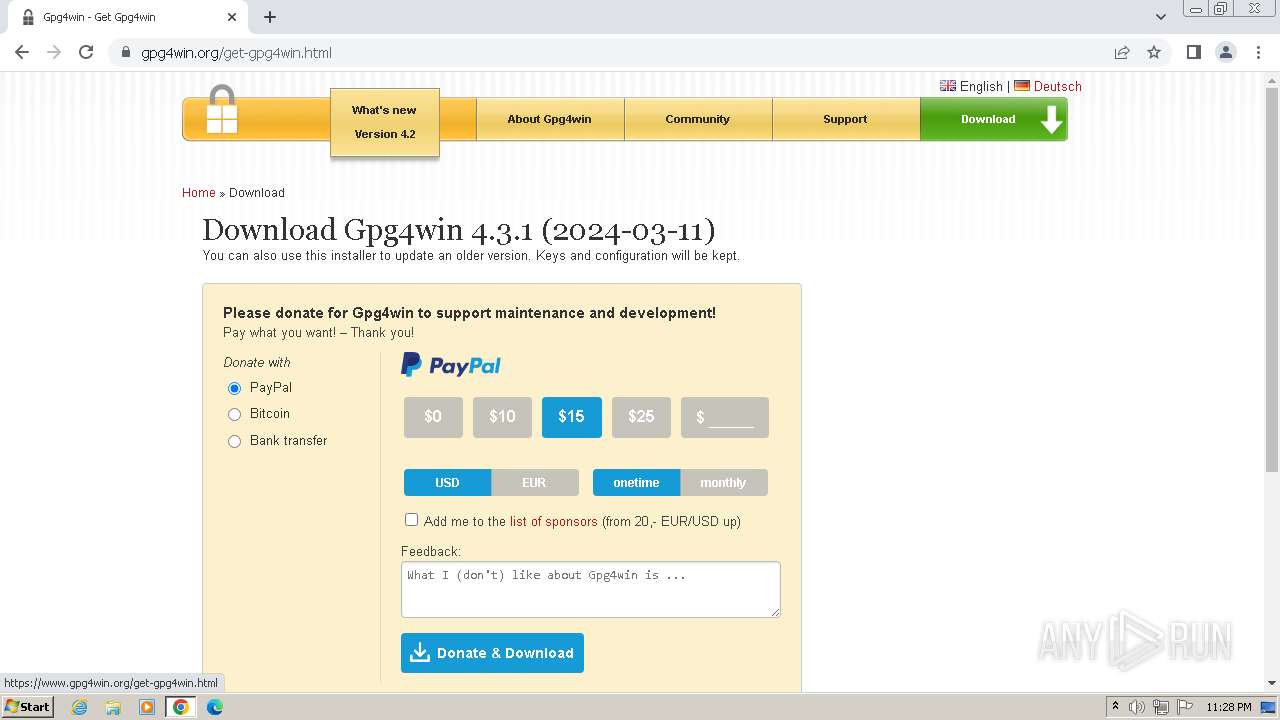
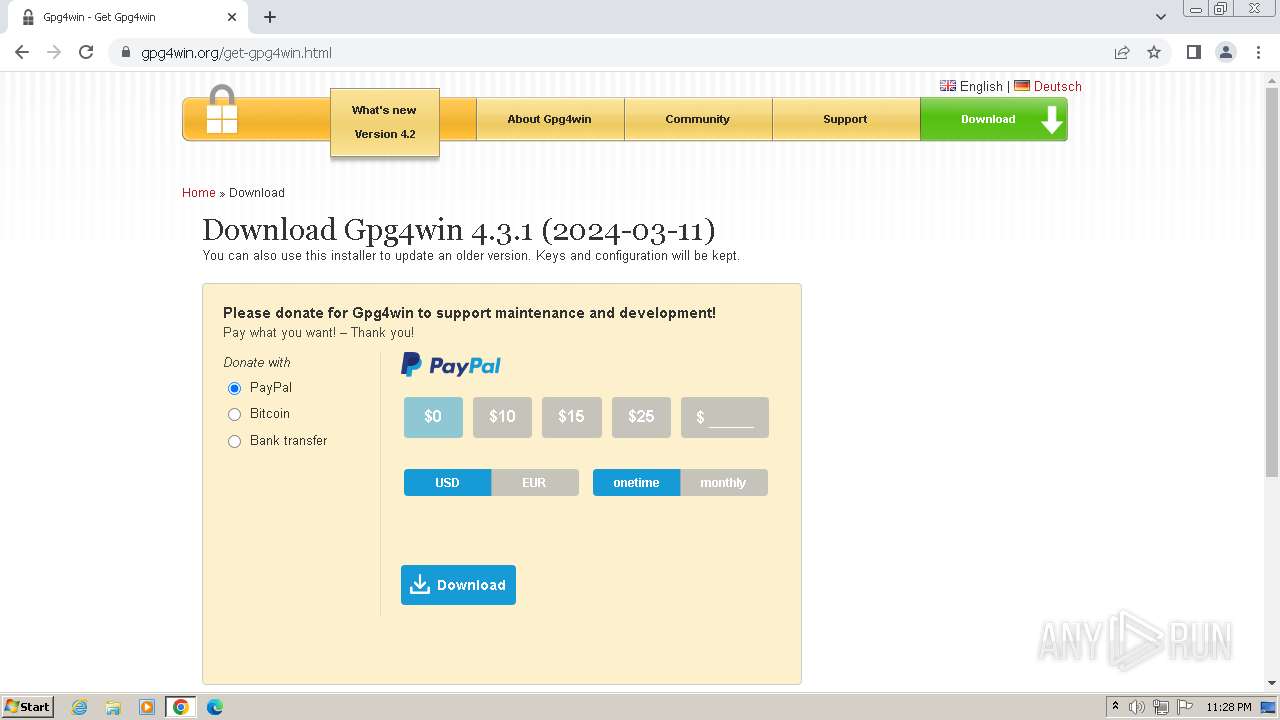
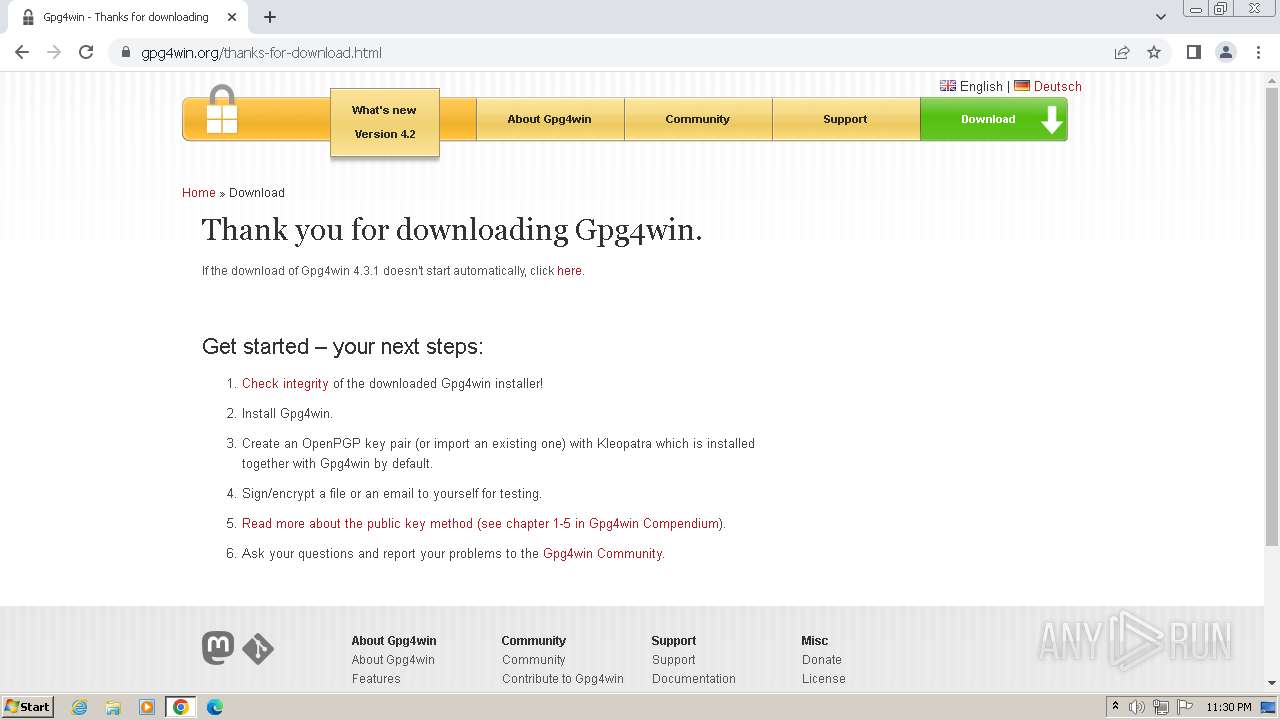
| URL: | http://www.gpg4win.org/ |
| Full analysis: | https://app.any.run/tasks/70346554-4f22-4eb2-b8cb-1fbe54e92824 |
| Verdict: | Malicious activity |
| Analysis date: | June 02, 2024, 22:27:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2D2D04684909DD5B3C100AFC0B82A650 |
| SHA1: | A30D539780EC43D1B8C84A9156AD0C2AB5AD785D |
| SHA256: | 0D6DC708A7AF8D9BC505BF12CF35A4E0244805130ABBD5EC92DCDDA05A337B16 |
| SSDEEP: | 3:N1KJS4b/K5n:Cc4Kn |
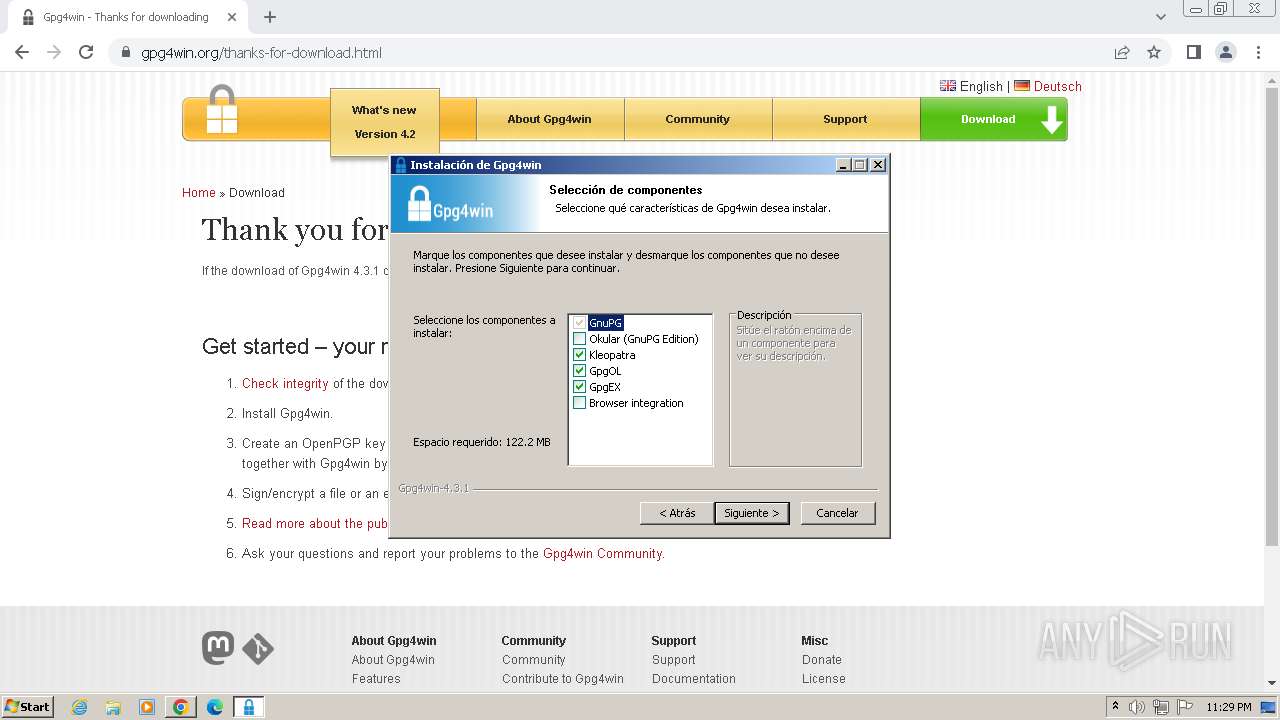
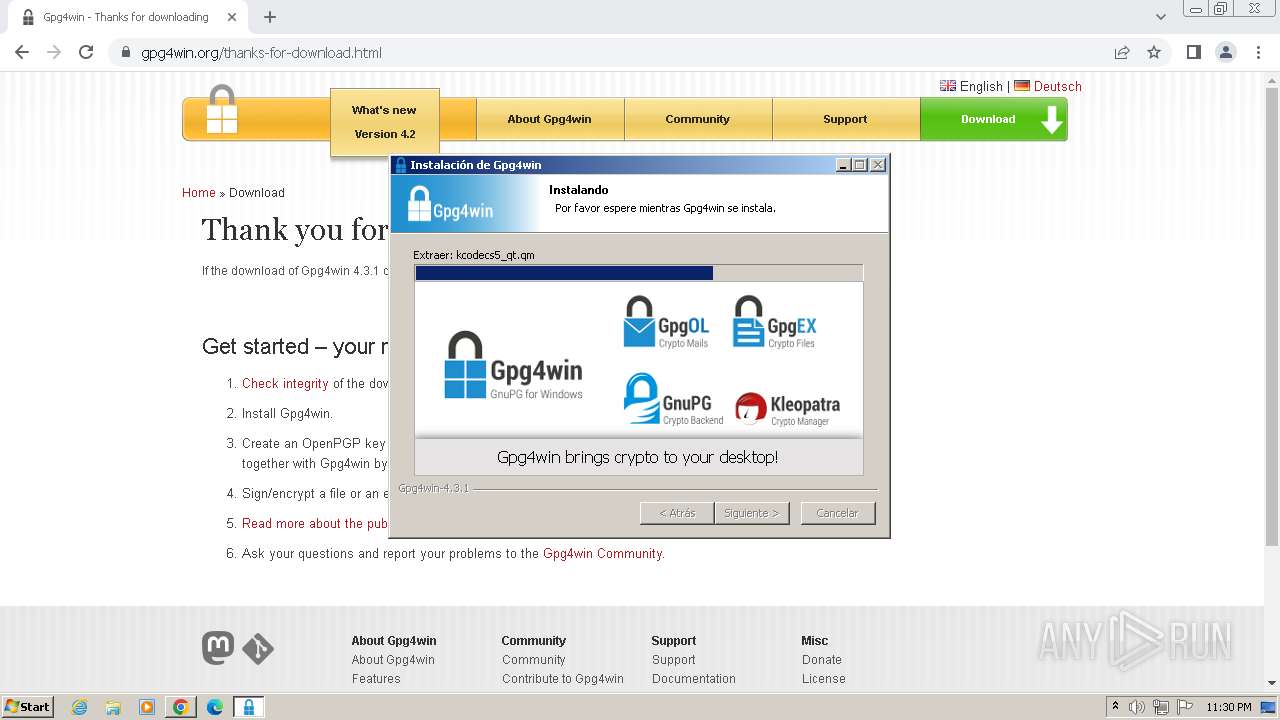
MALICIOUS
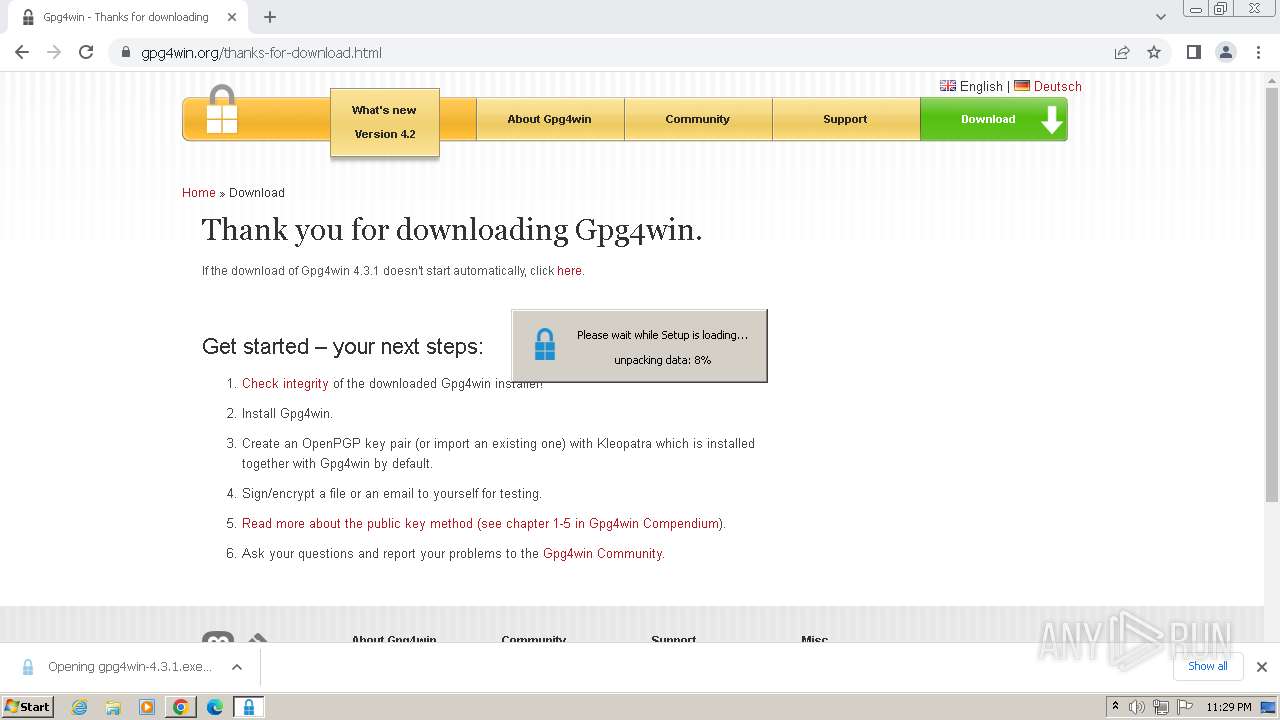
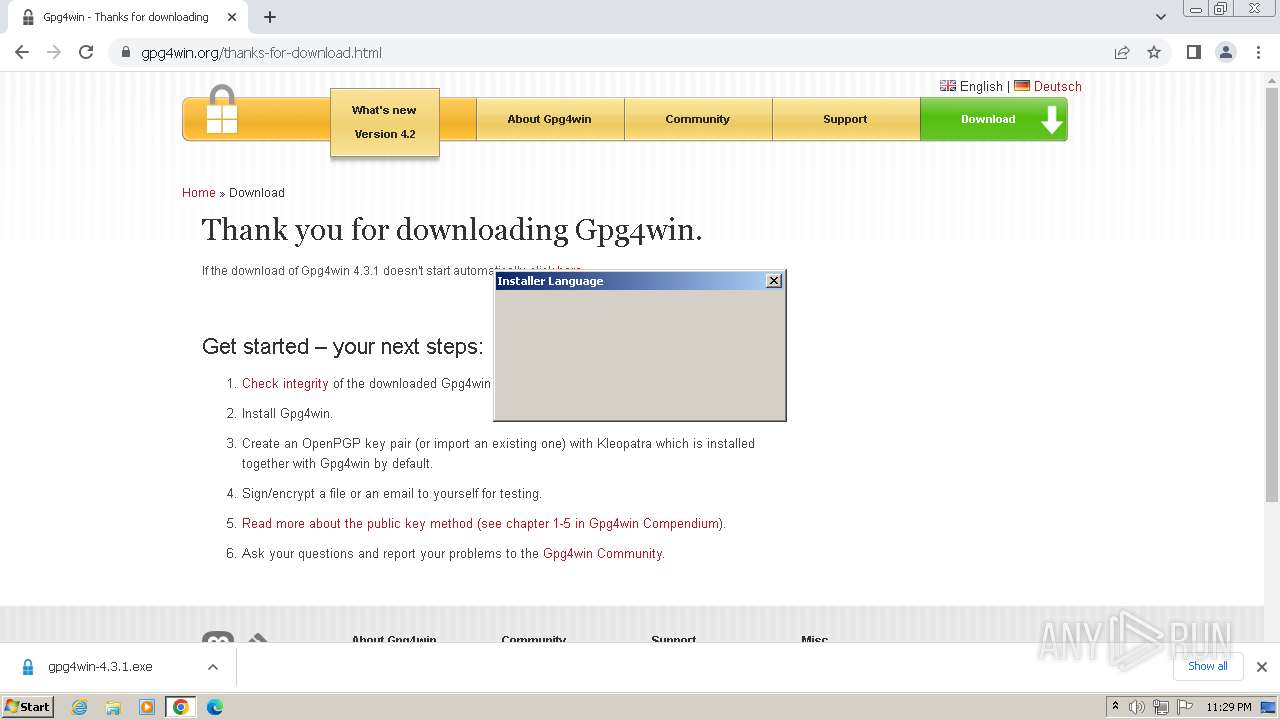
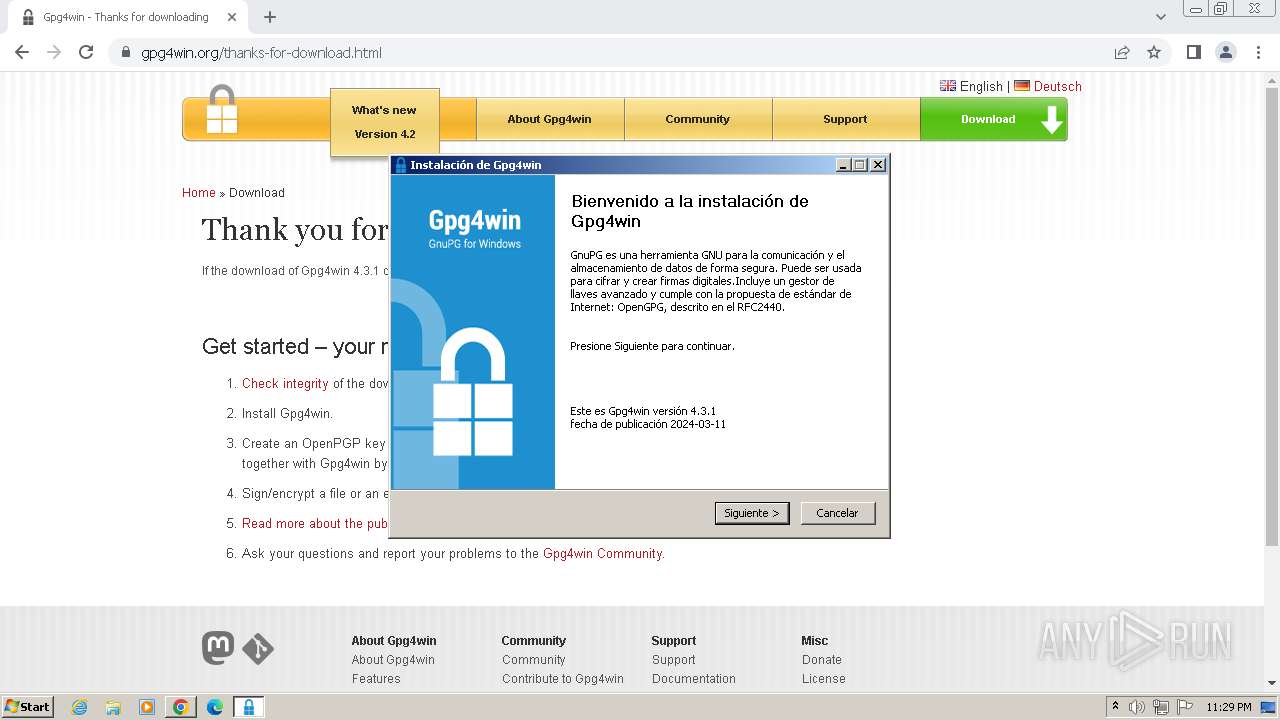
Drops the executable file immediately after the start
- gpg4win-4.3.1.exe (PID: 2904)
- gnupg-w32-2.4.5_20240307-bin.exe (PID: 3100)
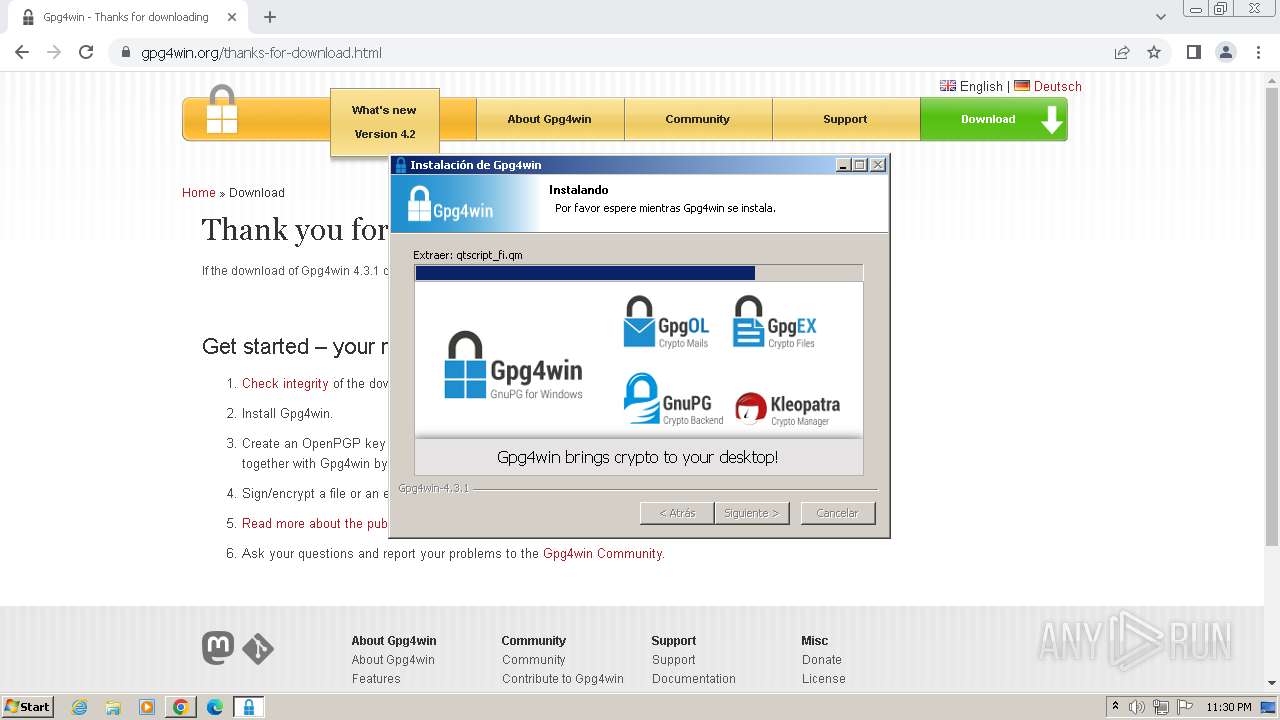
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- gpg4win-4.3.1.exe (PID: 2904)
- gnupg-w32-2.4.5_20240307-bin.exe (PID: 3100)
The process creates files with name similar to system file names
- gpg4win-4.3.1.exe (PID: 2904)
- gnupg-w32-2.4.5_20240307-bin.exe (PID: 3100)
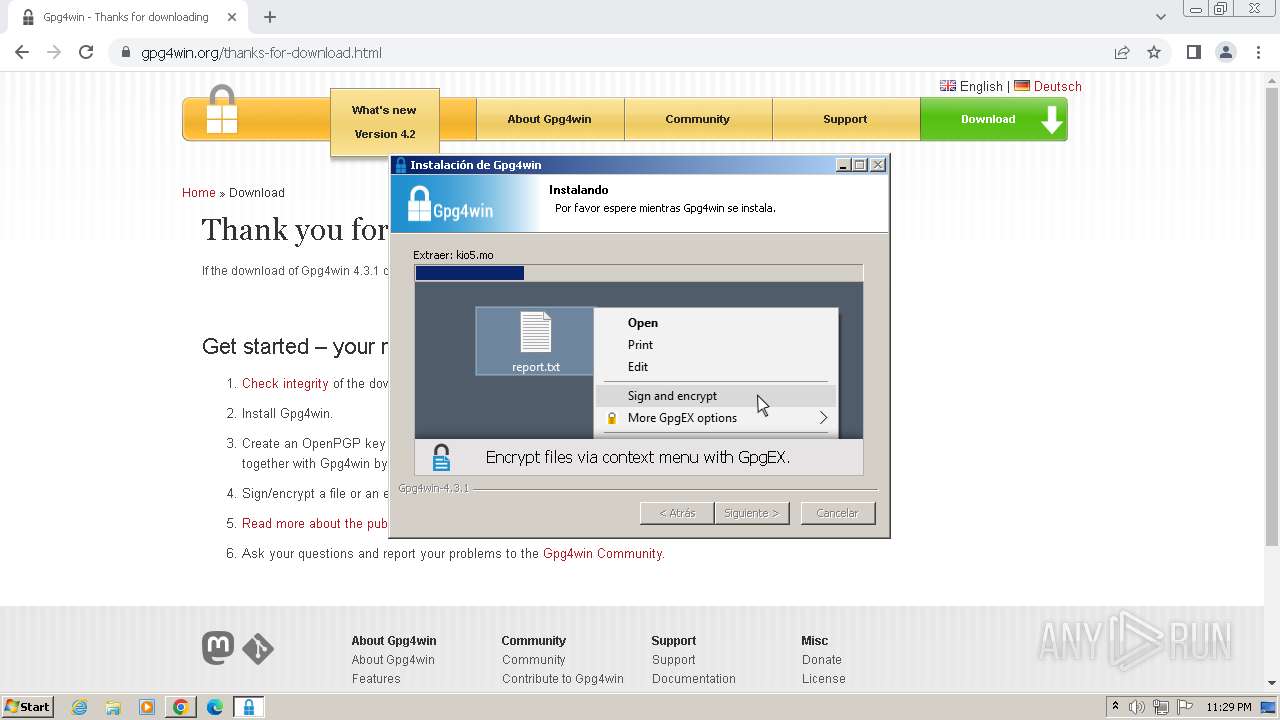
Executable content was dropped or overwritten
- gpg4win-4.3.1.exe (PID: 2904)
- gnupg-w32-2.4.5_20240307-bin.exe (PID: 3100)
Reads the Internet Settings
- gpg4win-4.3.1.exe (PID: 2904)
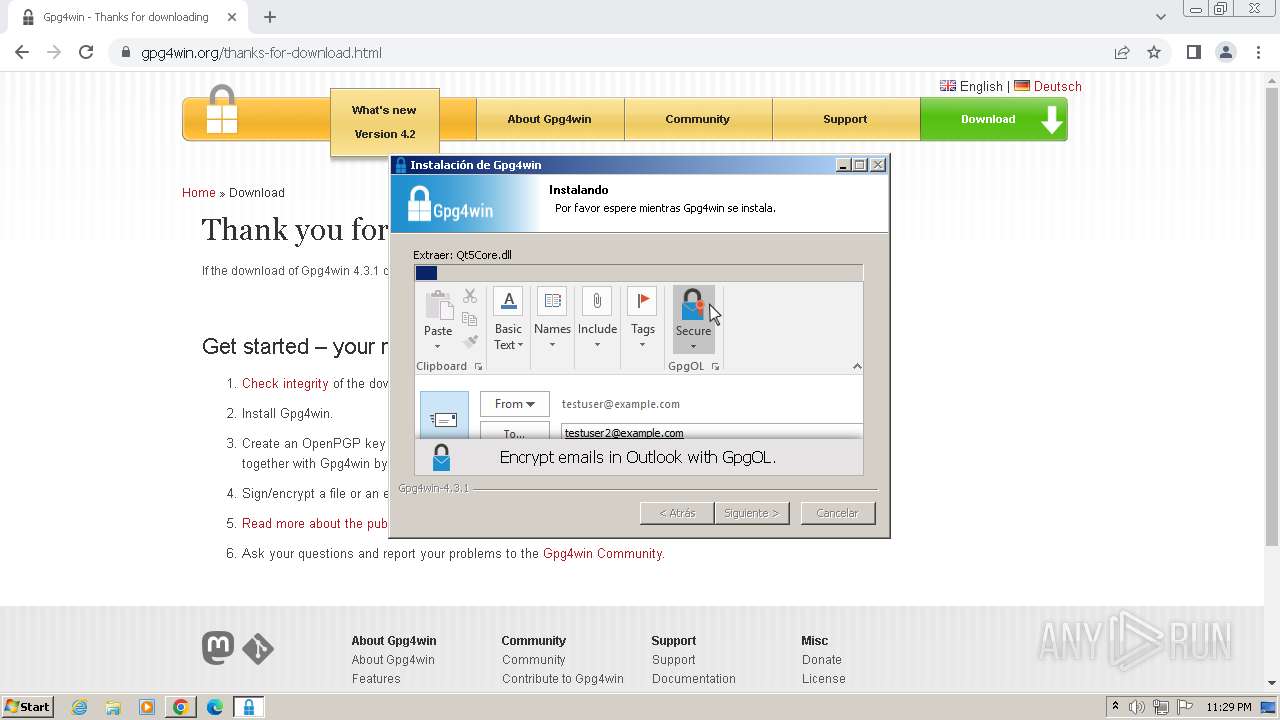
Reads Microsoft Outlook installation path
- gpg4win-4.3.1.exe (PID: 2904)
Creates a software uninstall entry
- gpg4win-4.3.1.exe (PID: 2904)
- gnupg-w32-2.4.5_20240307-bin.exe (PID: 3100)
Creates/Modifies COM task schedule object
- gpg4win-4.3.1.exe (PID: 2904)
INFO
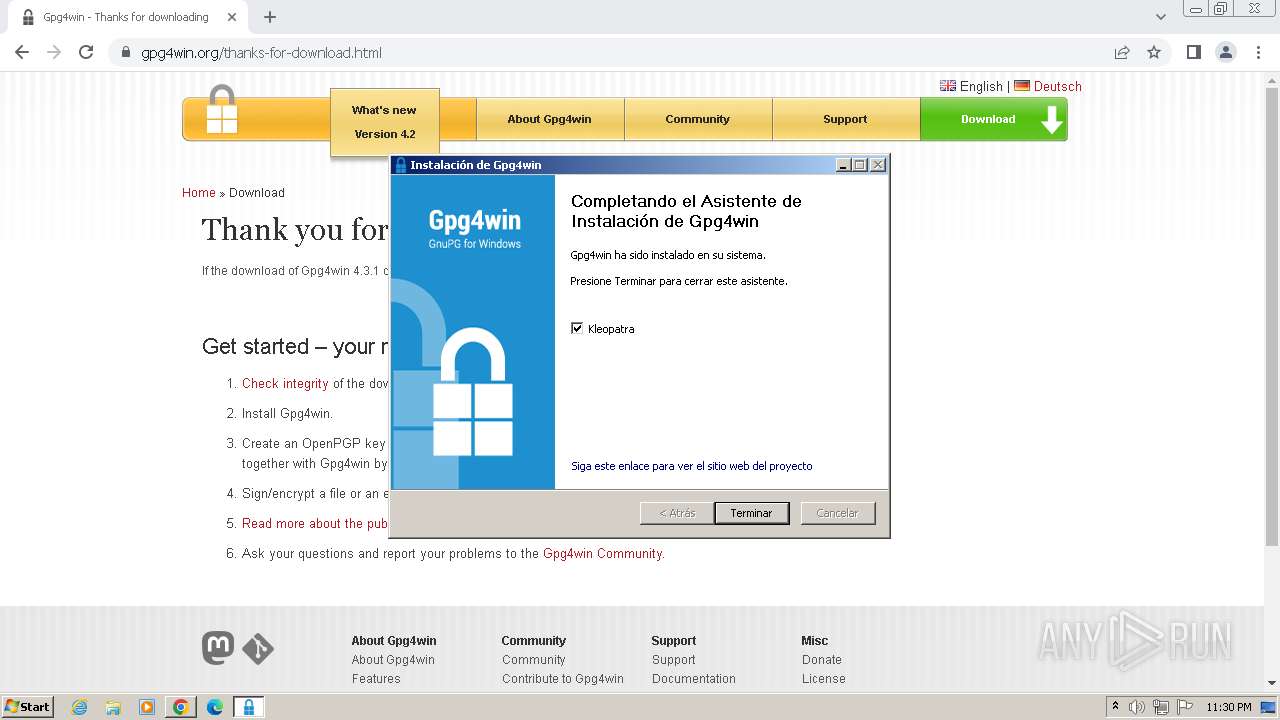
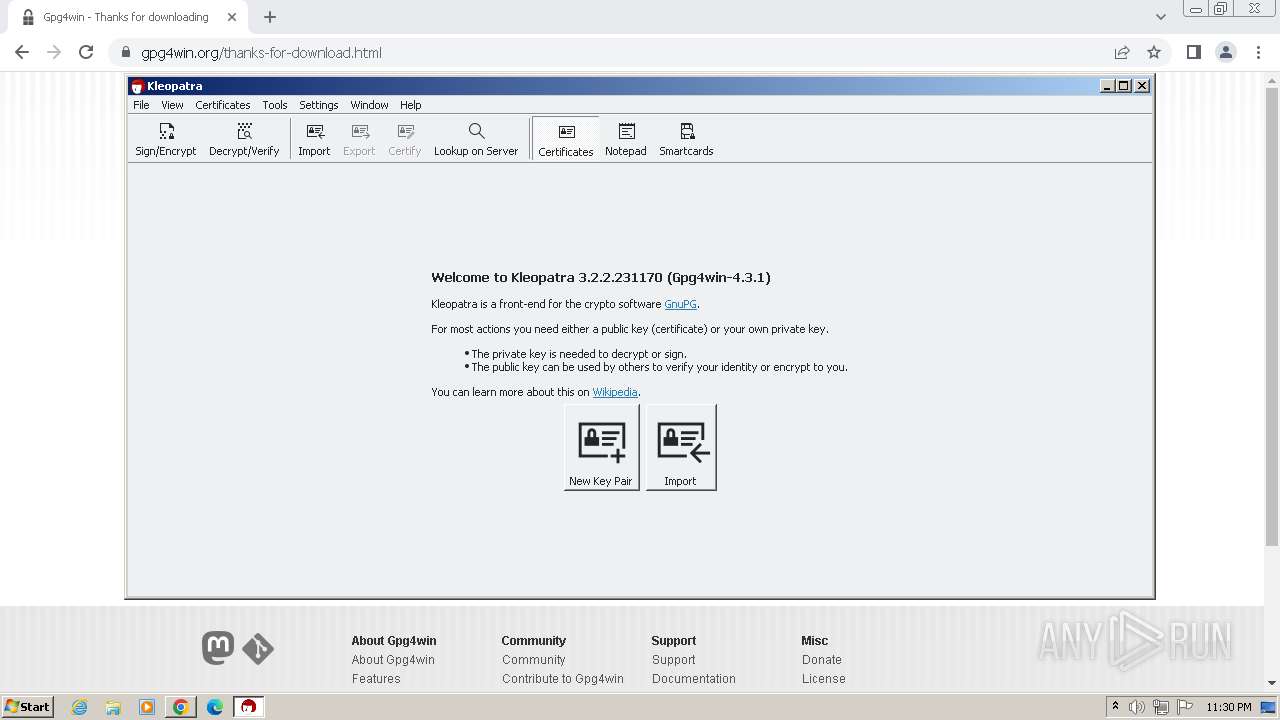
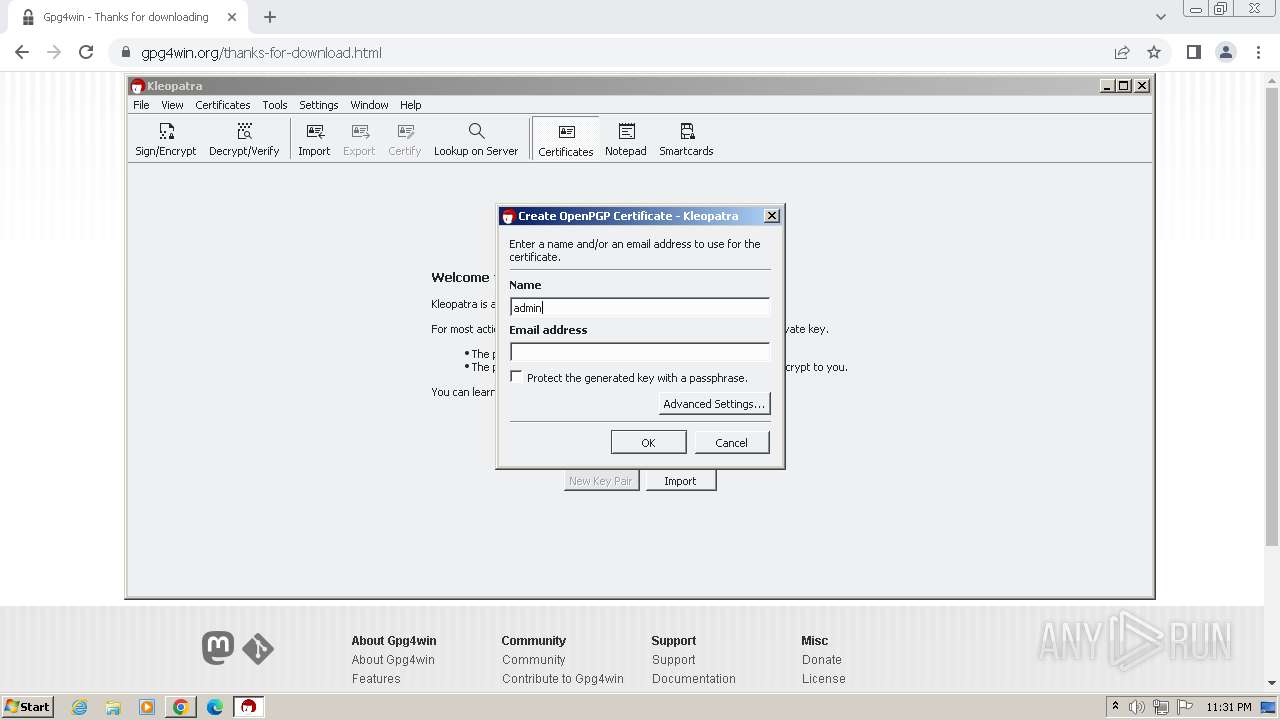
Manual execution by a user
- wmpnscfg.exe (PID: 568)
- kleopatra.exe (PID: 3516)
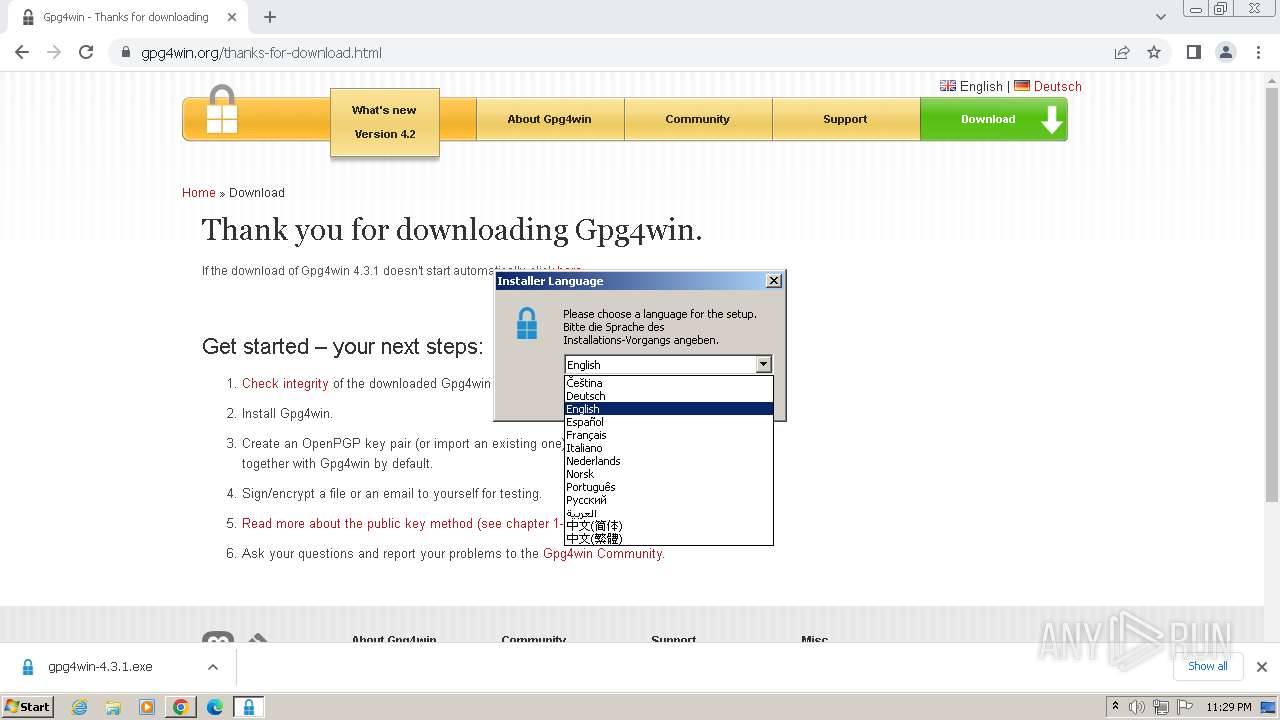
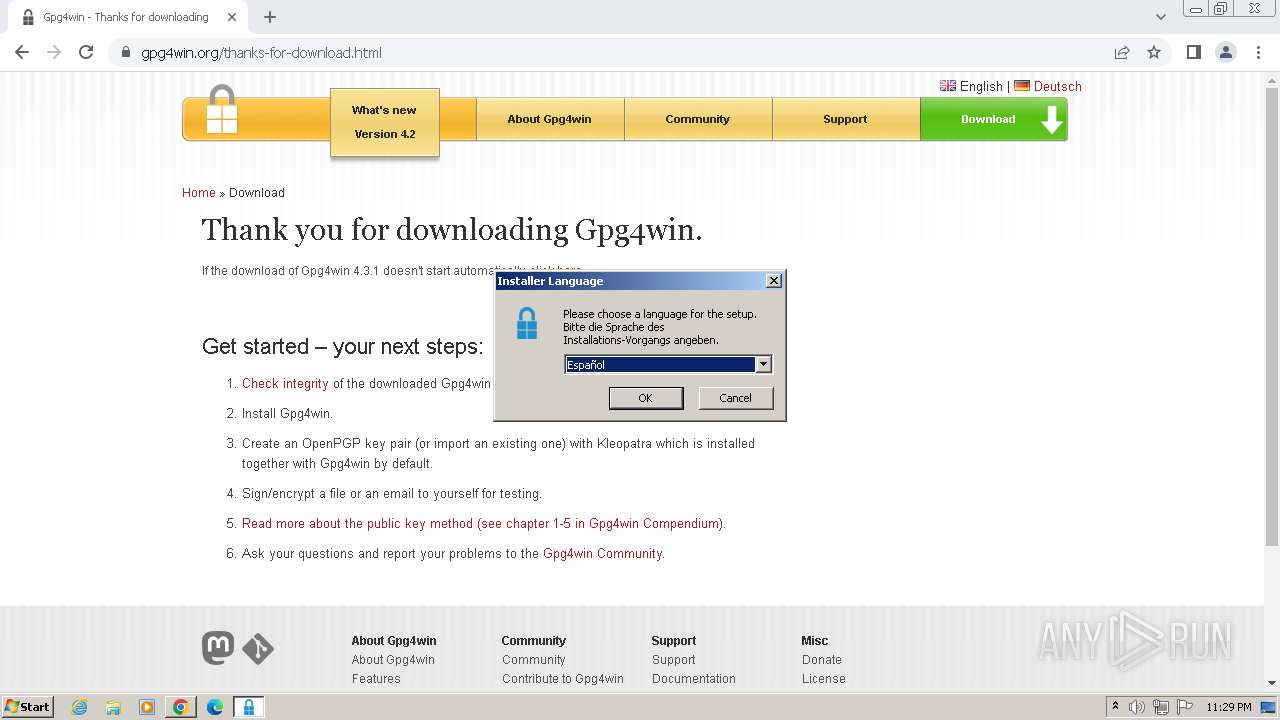
Checks supported languages
- wmpnscfg.exe (PID: 568)
- gpg4win-4.3.1.exe (PID: 2904)
- kleopatra.exe (PID: 3516)
- gnupg-w32-2.4.5_20240307-bin.exe (PID: 3100)
- gpgme-w32spawn.exe (PID: 3916)
- gpgconf.exe (PID: 3924)
- gpgme-w32spawn.exe (PID: 3932)
- gpg.exe (PID: 1628)
- gpgconf.exe (PID: 4088)
- gpgme-w32spawn.exe (PID: 768)
- gpgme-w32spawn.exe (PID: 1944)
- gpgconf.exe (PID: 568)
- gpgme-w32spawn.exe (PID: 2104)
- gpgconf.exe (PID: 1940)
- gpgconf.exe (PID: 2080)
- gpg-agent.exe (PID: 2072)
- gpgsm.exe (PID: 1120)
- gpg.exe (PID: 3212)
- gpgconf.exe (PID: 1788)
- gpg-agent.exe (PID: 2472)
- gpgme-w32spawn.exe (PID: 2476)
- gpgconf.exe (PID: 1012)
- gpg.exe (PID: 3148)
- gpgme-w32spawn.exe (PID: 3556)
- gpgconf.exe (PID: 3560)
- gpgsm.exe (PID: 2464)
- gpgsm.exe (PID: 2460)
- gpg-connect-agent.exe (PID: 2180)
- gpgme-w32spawn.exe (PID: 1592)
- dirmngr.exe (PID: 4060)
- keyboxd.exe (PID: 3792)
- keyboxd.exe (PID: 3312)
- gpgme-w32spawn.exe (PID: 2360)
- gpgconf.exe (PID: 2632)
- gpg-agent.exe (PID: 328)
- gpgme-w32spawn.exe (PID: 1288)
- scdaemon.exe (PID: 1240)
- gpgconf.exe (PID: 2768)
- scdaemon.exe (PID: 2392)
- gpgconf.exe (PID: 916)
- dirmngr.exe (PID: 2740)
- dirmngr.exe (PID: 2876)
- gpgme-w32spawn.exe (PID: 3468)
- gpgme-w32spawn.exe (PID: 1960)
- gpgconf.exe (PID: 3896)
- gpg-agent.exe (PID: 3504)
- gpgme-w32spawn.exe (PID: 2668)
- gpgme-w32spawn.exe (PID: 2444)
- gpgme-w32spawn.exe (PID: 2924)
- gpgsm.exe (PID: 2944)
- keyboxd.exe (PID: 2960)
- gpgme-w32spawn.exe (PID: 2832)
- gpgme-w32spawn.exe (PID: 2988)
- gpgconf.exe (PID: 2664)
- gpgme-w32spawn.exe (PID: 2540)
- gpgconf.exe (PID: 2816)
- gpg.exe (PID: 2848)
- gpgme-w32spawn.exe (PID: 1868)
- gpgme-w32spawn.exe (PID: 3296)
- gpgsm.exe (PID: 2836)
- scdaemon.exe (PID: 2528)
- gpg.exe (PID: 2796)
- gpgme-w32spawn.exe (PID: 2940)
- gpg.exe (PID: 3444)
- gpgme-w32spawn.exe (PID: 3684)
- gpg.exe (PID: 3756)
- gpg.exe (PID: 2404)
- gpgme-w32spawn.exe (PID: 1772)
- gpgme-w32spawn.exe (PID: 3672)
- gpg.exe (PID: 3620)
- gpgsm.exe (PID: 3524)
- gpg.exe (PID: 304)
Reads the computer name
- wmpnscfg.exe (PID: 568)
- gpg4win-4.3.1.exe (PID: 2904)
- gnupg-w32-2.4.5_20240307-bin.exe (PID: 3100)
- kleopatra.exe (PID: 3516)
- scdaemon.exe (PID: 2528)
- gpg-agent.exe (PID: 2472)
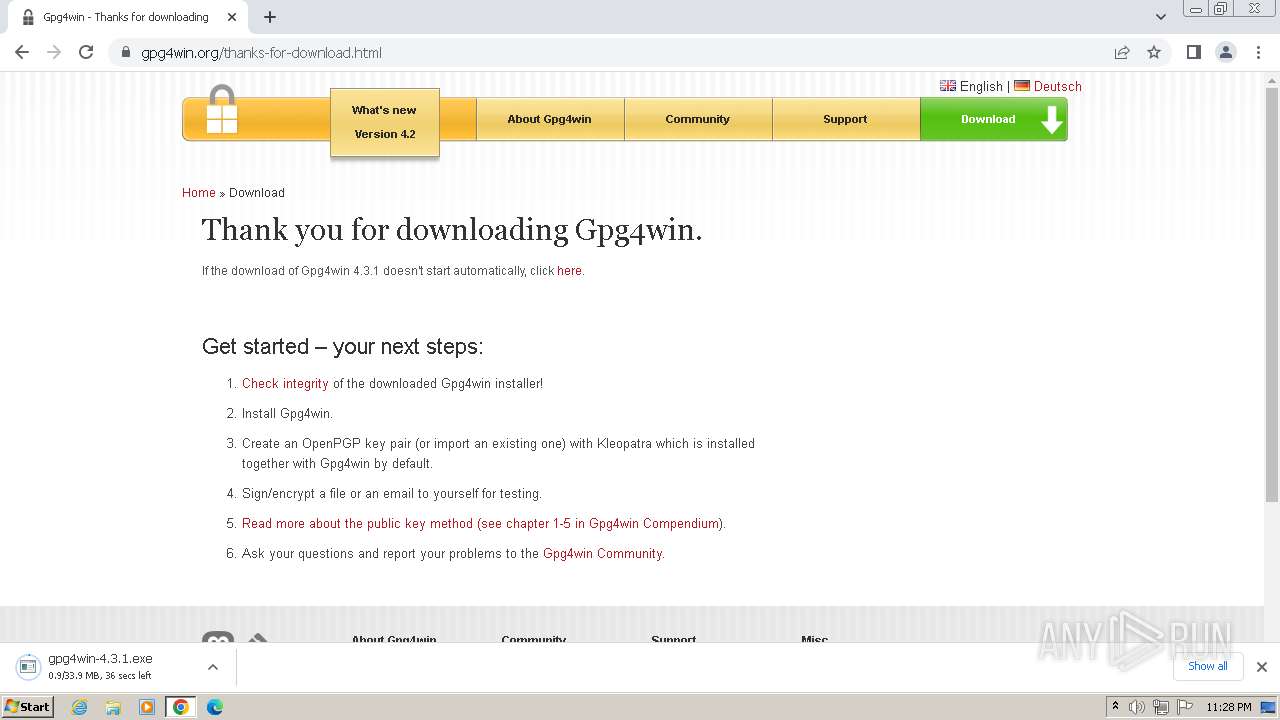
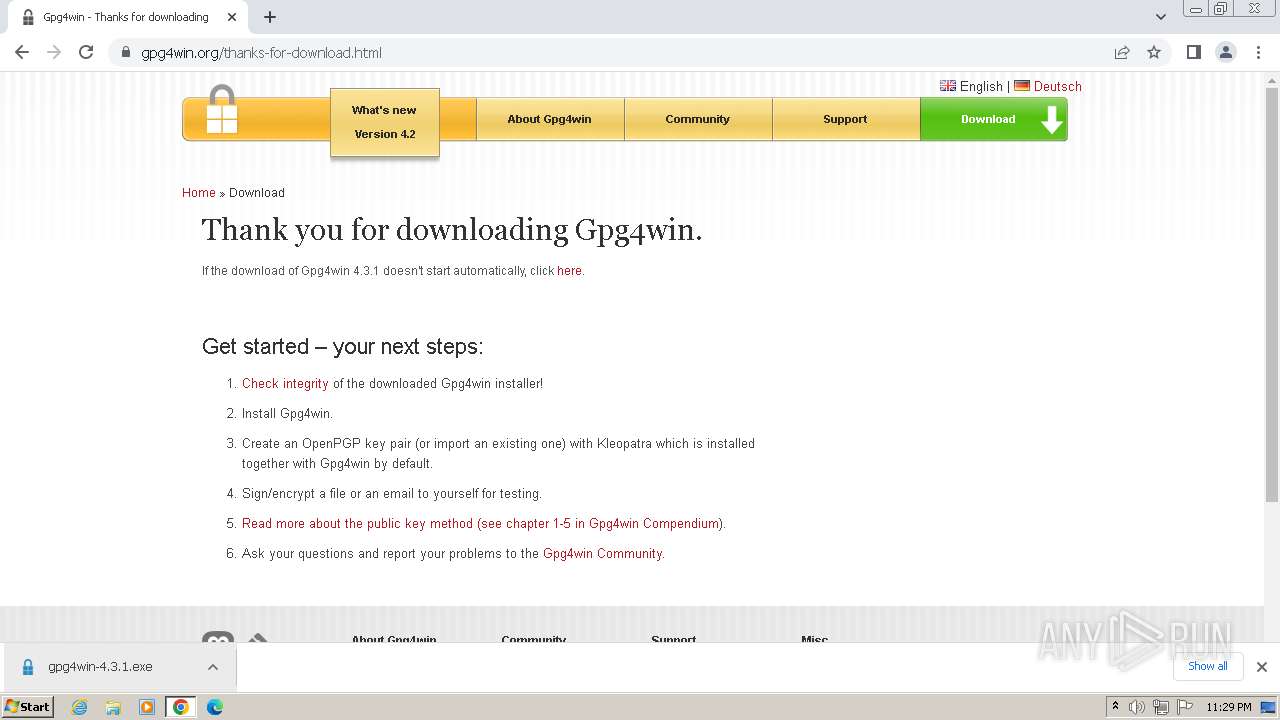
The process uses the downloaded file
- chrome.exe (PID: 3968)
- chrome.exe (PID: 2676)
Executable content was dropped or overwritten
- chrome.exe (PID: 3968)
- chrome.exe (PID: 3076)
- chrome.exe (PID: 3256)
Drops the executable file immediately after the start
- chrome.exe (PID: 3968)
- chrome.exe (PID: 3076)
- chrome.exe (PID: 3256)
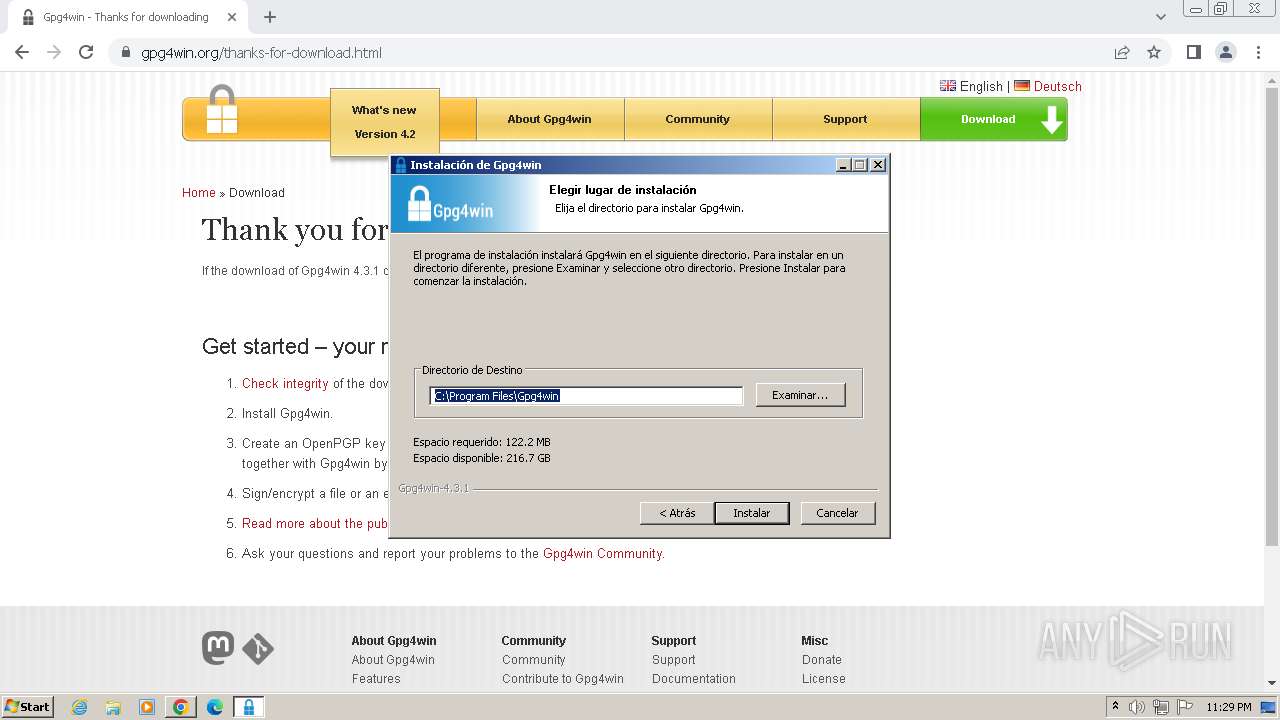
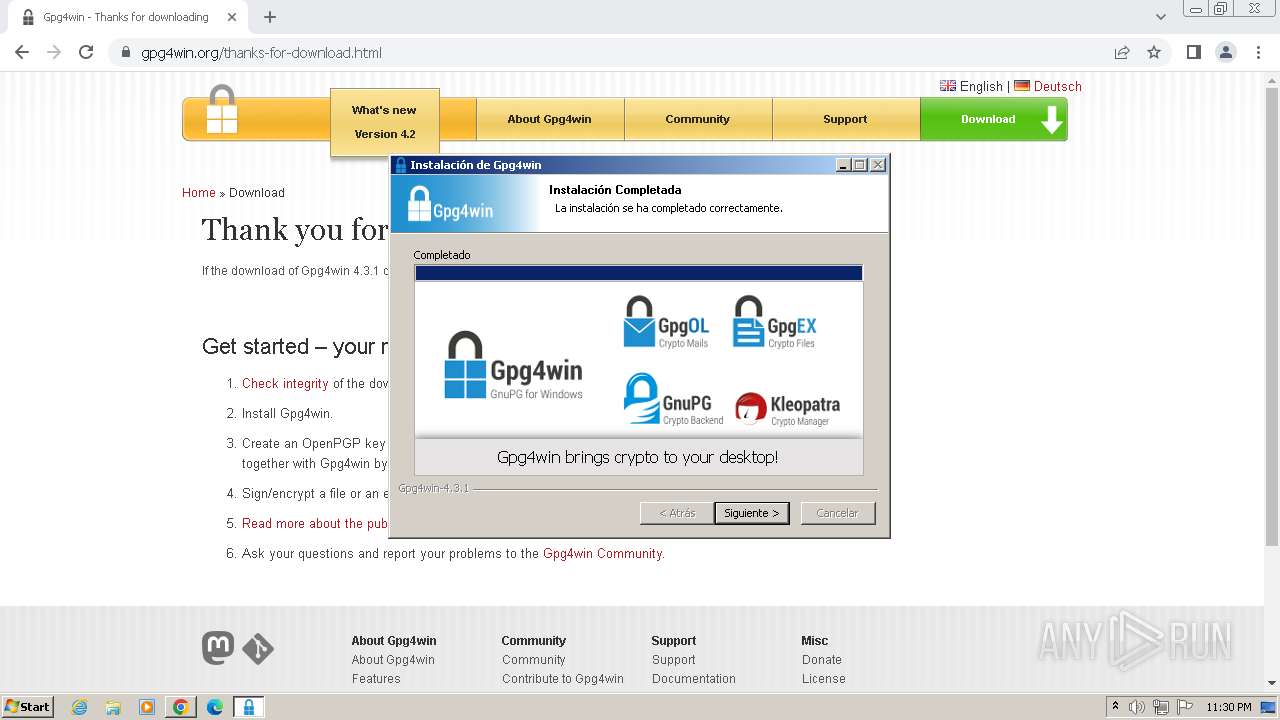
Create files in a temporary directory
- gpg4win-4.3.1.exe (PID: 2904)
- kleopatra.exe (PID: 3516)
- gnupg-w32-2.4.5_20240307-bin.exe (PID: 3100)
Reads the machine GUID from the registry
- gpg4win-4.3.1.exe (PID: 2904)
- kleopatra.exe (PID: 3516)
- gpg-agent.exe (PID: 2472)
- keyboxd.exe (PID: 2960)
- scdaemon.exe (PID: 2528)
Application launched itself
- chrome.exe (PID: 3968)
Creates files in the program directory
- gpg4win-4.3.1.exe (PID: 2904)
- gnupg-w32-2.4.5_20240307-bin.exe (PID: 3100)
Dropped object may contain TOR URL's
- gnupg-w32-2.4.5_20240307-bin.exe (PID: 3100)
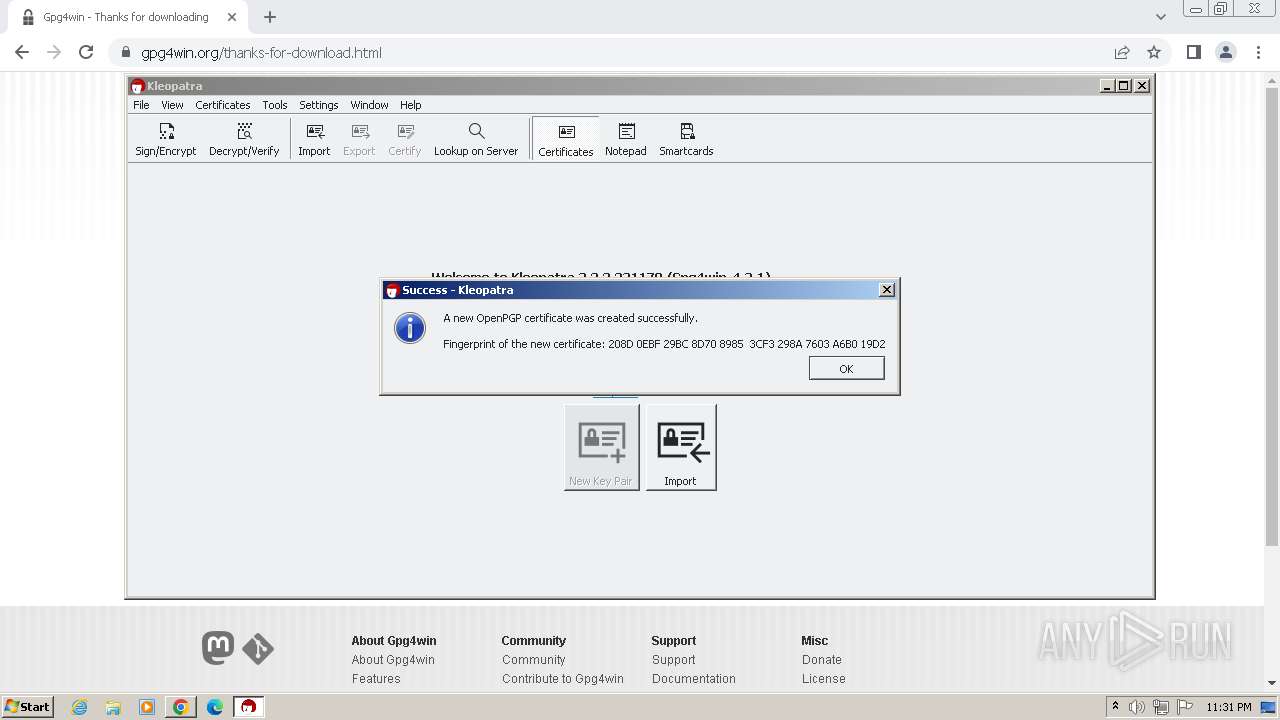
Creates files or folders in the user directory
- kleopatra.exe (PID: 3516)
- gpgconf.exe (PID: 3924)
- gpg-connect-agent.exe (PID: 2180)
- gpg-agent.exe (PID: 2472)
- gpg.exe (PID: 2848)
- keyboxd.exe (PID: 2960)
- scdaemon.exe (PID: 2528)
- gpg.exe (PID: 3756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
163
Monitored processes
99
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
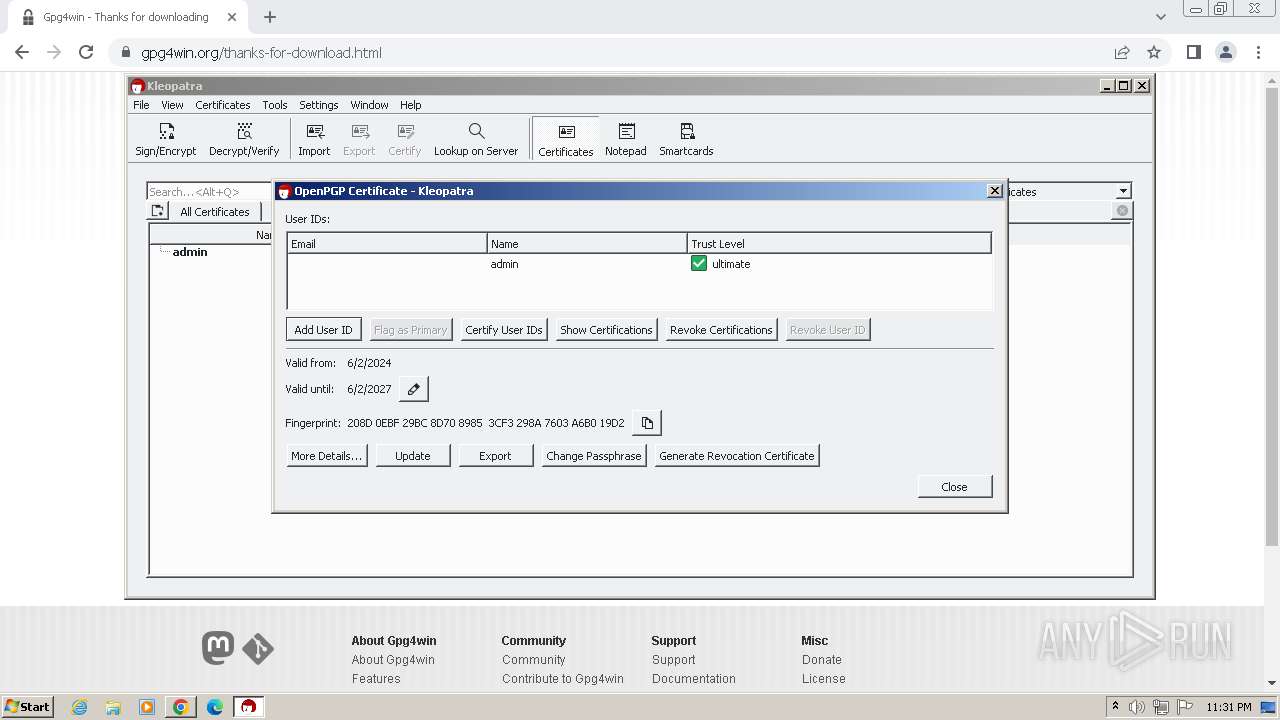
| 304 | "C:\\\\Program Files\\\\GnuPG\\\\bin\\\\gpg.exe" "--batch" "--status-fd" "4" "--logger-fd" "12" "--no-tty" "--charset=utf8" "--enable-progress-filter" "--exit-on-status-write-error" "--ttyname=/dev/tty" "--with-colons" "--with-tofu-info" "--with-secret" "--with-keygrip" "--with-sig-check" "--list-options" "show-sig-subpackets=\"20,26\"" "--check-sigs" "--" "208D0EBF29BC8D7089853CF3298A7603A6B019D2" | C:\Program Files\GnuPG\bin\gpg.exe | — | gpgme-w32spawn.exe | |||||||||||
User: admin Company: g10 Code GmbH Integrity Level: MEDIUM Description: GnuPG’s OpenPGP tool Exit code: 0 Version: 2.4.5 (cbff323b3) built on <anon> at <none> Modules
| |||||||||||||||
| 328 | "C:\Program Files\GnuPG\bin\gpg-agent.exe" --dump-option-table | C:\Program Files\GnuPG\bin\gpg-agent.exe | — | gpgconf.exe | |||||||||||
User: admin Company: g10 Code GmbH Integrity Level: MEDIUM Description: GnuPG’s private key daemon Exit code: 0 Version: 2.4.5 (cbff323b3) built on <anon> at <none> Modules
| |||||||||||||||
| 568 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 568 | "C:\\\\Program Files\\\\GnuPG\\\\bin\\\\gpgconf.exe" "--version" | C:\Program Files\GnuPG\bin\gpgconf.exe | — | gpgme-w32spawn.exe | |||||||||||
User: admin Company: g10 Code GmbH Integrity Level: MEDIUM Description: GnuPG’s config tool Exit code: 0 Version: 2.4.5 (cbff323b3) built on <anon> at <none> Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1516 --field-trial-handle=1176,i,6645191564554342864,3283260136610375866,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 768 | "C:\\Program Files\\Gpg4win\\bin\\gpgme-w32spawn.exe" "C:\\Users\\admin\\AppData\\Local\\Temp\\gpgme-WNSqJi" "C:\\Program Files\\GnuPG\\bin\\gpg.exe" "--version" | C:\Program Files\Gpg4win\bin\gpgme-w32spawn.exe | — | kleopatra.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1276 --field-trial-handle=1176,i,6645191564554342864,3283260136610375866,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 916 | "C:\\\\Program Files\\\\GnuPG\\\\bin\\\\gpgconf.exe" "--list-options" "dirmngr" | C:\Program Files\GnuPG\bin\gpgconf.exe | — | gpgme-w32spawn.exe | |||||||||||
User: admin Company: g10 Code GmbH Integrity Level: MEDIUM Description: GnuPG’s config tool Exit code: 0 Version: 2.4.5 (cbff323b3) built on <anon> at <none> Modules
| |||||||||||||||
| 1012 | "C:\\\\Program Files\\\\GnuPG\\\\bin\\\\gpgconf.exe" "--list-options" "gpg" | C:\Program Files\GnuPG\bin\gpgconf.exe | — | gpgme-w32spawn.exe | |||||||||||
User: admin Company: g10 Code GmbH Integrity Level: MEDIUM Description: GnuPG’s config tool Exit code: 0 Version: 2.4.5 (cbff323b3) built on <anon> at <none> Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3764 --field-trial-handle=1176,i,6645191564554342864,3283260136610375866,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
27 537
Read events
27 277
Write events
252
Delete events
8
Modification events
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
132
Suspicious files
1 077
Text files
195
Unknown types
262
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF104681.TMP | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF104690.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:FF6BABA737D50E515029C3F3A1305BBC | SHA256:670EED15EAA8E3F1A4F8612B229654EB0C64107AEAF0B1017E4BD45E3F7EED83 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF104681.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1049cc.TMP | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:98CC34E7F20FD8F55568DB9B3D3B507E | SHA256:8D3D74EC41FF0CCE1F26B23F66E5981B7F59C40AB0DBB468B3A3E5E63C80F3C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
33
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
820 | chrome.exe | GET | 301 | 46.4.134.23:80 | http://www.gpg4win.org/ | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
820 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
3968 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
820 | chrome.exe | 46.4.134.23:80 | www.gpg4win.org | Hetzner Online GmbH | DE | unknown |
820 | chrome.exe | 46.4.134.23:443 | www.gpg4win.org | Hetzner Online GmbH | DE | unknown |
3968 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
820 | chrome.exe | 216.58.206.36:443 | www.google.com | GOOGLE | US | whitelisted |
820 | chrome.exe | 142.250.184.234:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gpg4win.org |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
files.gpg4win.org |
| unknown |
update.googleapis.com |
| unknown |
edgedl.me.gvt1.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
gpg4win-4.3.1.exe | Created: |
gpg4win-4.3.1.exe | CLSID\{42d30988-1a3a-11da-c687-000d6080e735} |
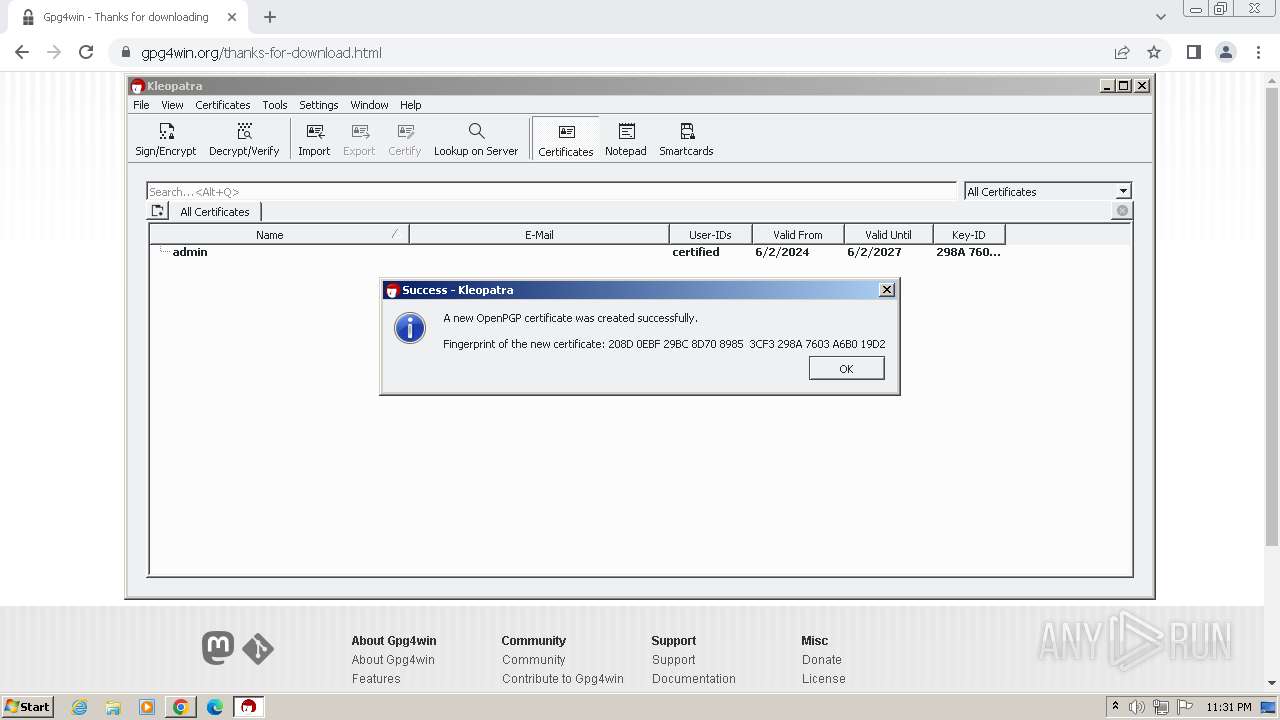
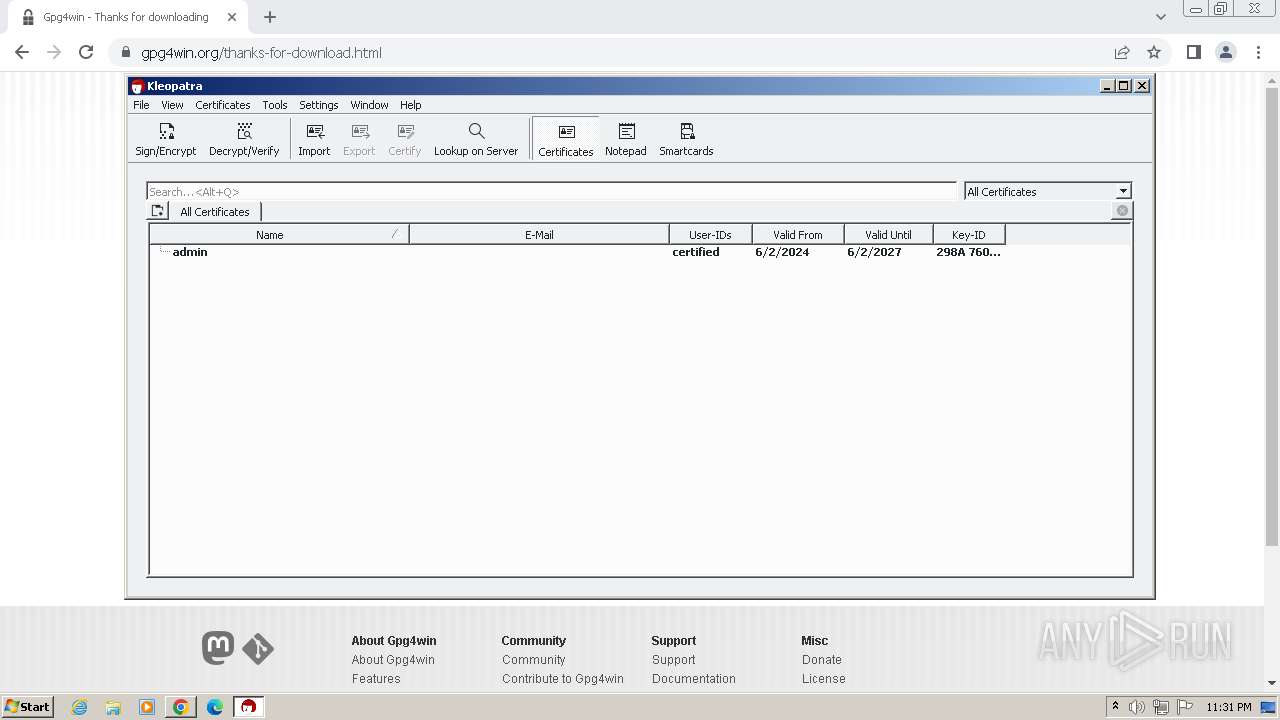
kleopatra.exe | org.kde.pim.kleopatra: Created responder: "kleopatraResponder" with handle: 0x2017c
|
kleopatra.exe | org.kde.pim.kleopatra: Startup timing: 88 ms: Application created
|
kleopatra.exe | org.kde.pim.kleopatra: Responder handle: 0x0
|
kleopatra.exe | org.kde.pim.kleopatra: Application created
|
kleopatra.exe | org.kde.pim.kleopatra: Startup timing: 91 ms: Service created
|
kleopatra.exe | org.kde.pim.kleopatra: Startup timing: 99 ms: GPGME Initialized
|
kleopatra.exe | org.kde.pim.kleopatra: Got ElevationToken 0
|
kleopatra.exe | org.kde.pim.kleopatra: Startup timing: 101 ms: Checking backend versions
|