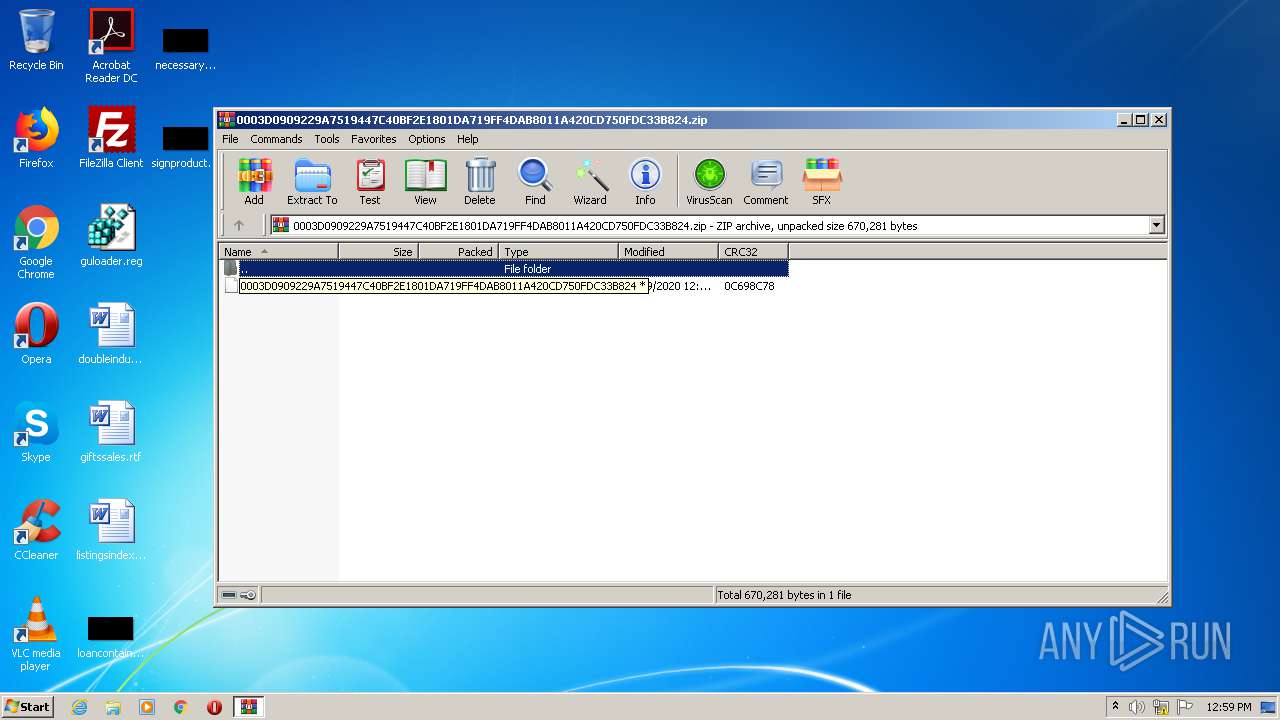
| File name: | 0003D0909229A7519447C40BF2E1801DA719FF4DAB8011A420CD750FDC33B824.zip |
| Full analysis: | https://app.any.run/tasks/c1612ca3-d36a-419e-9d1b-c5b4f6210fa4 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 12:59:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | EACEC1272A6A05C52FC7F039CCDFA285 |
| SHA1: | D0414B4C00EC309ADFFA8AD14C9FBD9571B601BC |
| SHA256: | 0D5866734A8CBAF8925F887121811FCD8F7DDFBE5BED92231FE7C9A4A7878CB7 |
| SSDEEP: | 12288:tPBVAEc1Sxpty/uE9/qIuqUs1Lo5dBhH0LjC4IgEVuA7NF0ZdByWPtpHe:tJVAEcyt3EBfuNs1MNhUod7NFGdBq |
MALICIOUS
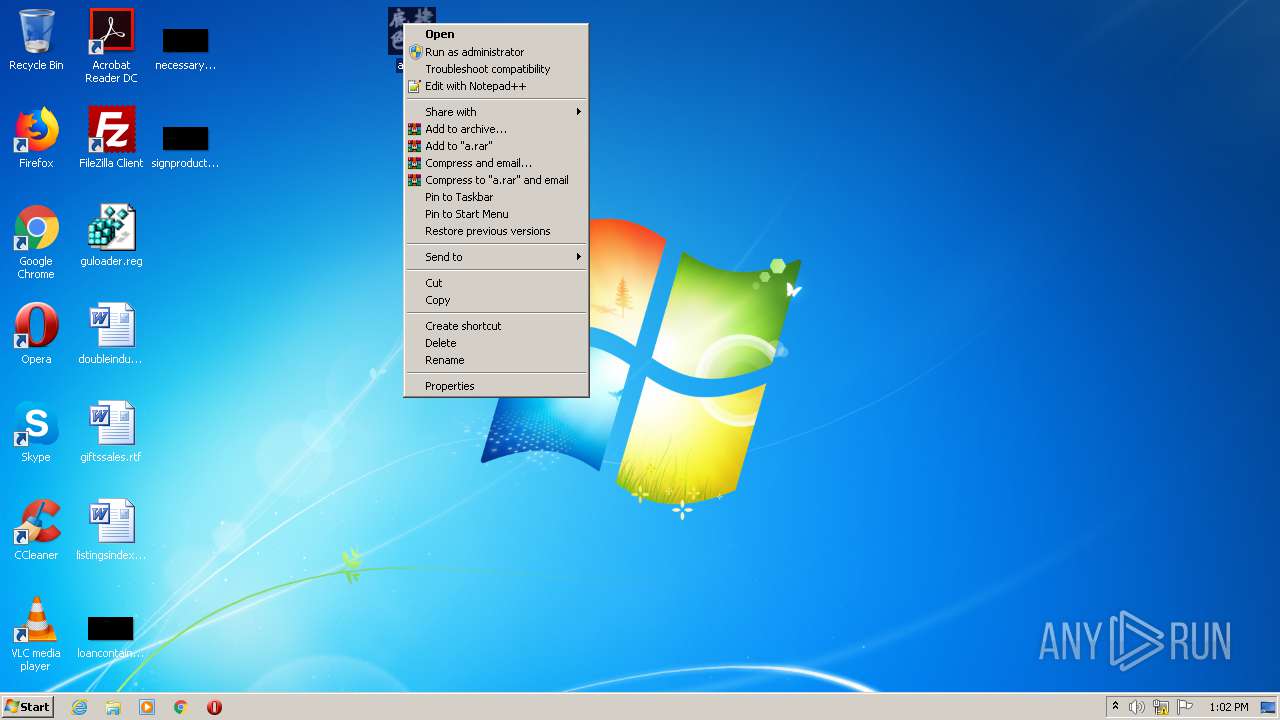
Application was dropped or rewritten from another process
- a.exe (PID: 1144)
- a.exe (PID: 2976)
- a.exe (PID: 848)
Drops executable file immediately after starts
- a.exe (PID: 1144)
Loads dropped or rewritten executable
- a.exe (PID: 1144)
- a.exe (PID: 848)
SUSPICIOUS
Executable content was dropped or overwritten
- a.exe (PID: 1144)
Creates files in the Windows directory
- a.exe (PID: 1144)
Creates COM task schedule object
- a.exe (PID: 1144)
- a.exe (PID: 848)
Executed via COM
- DllHost.exe (PID: 1372)
Drops a file with too old compile date
- a.exe (PID: 1144)
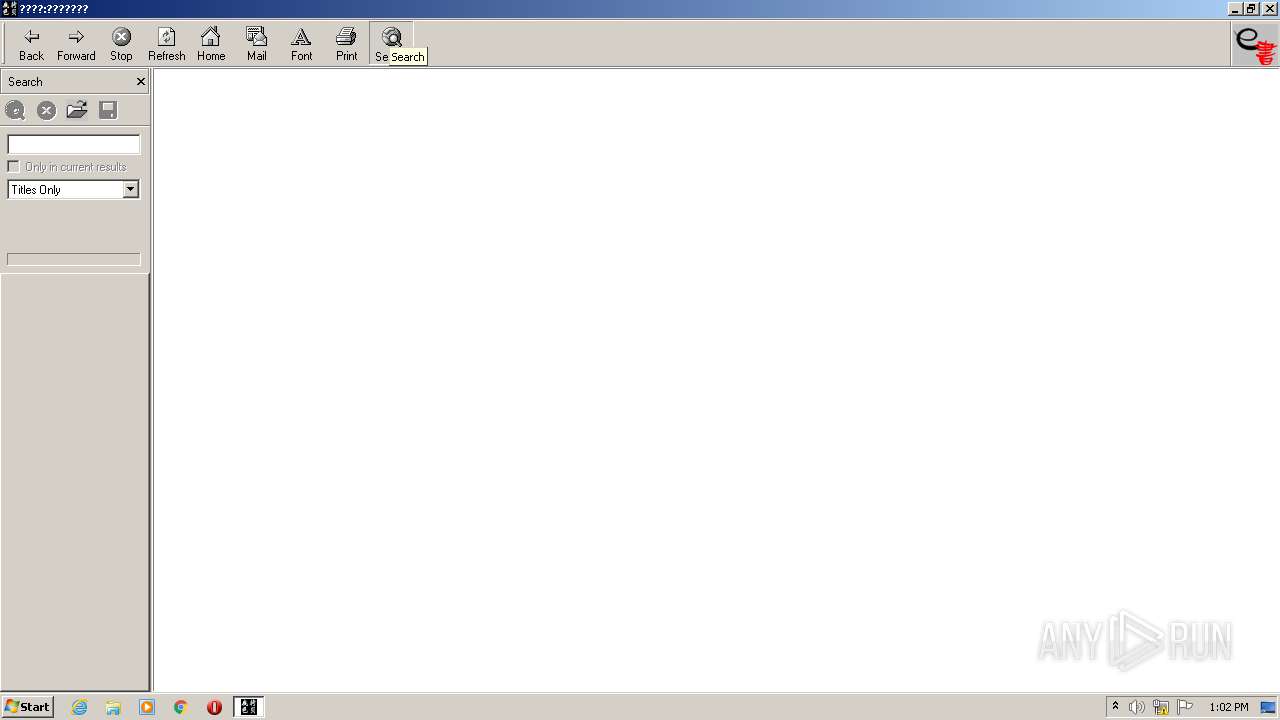
Reads internet explorer settings
- a.exe (PID: 1144)
- a.exe (PID: 848)
INFO
Reads the hosts file
- RdrCEF.exe (PID: 1064)
Application launched itself
- RdrCEF.exe (PID: 1064)
- AcroRd32.exe (PID: 2676)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 2676)
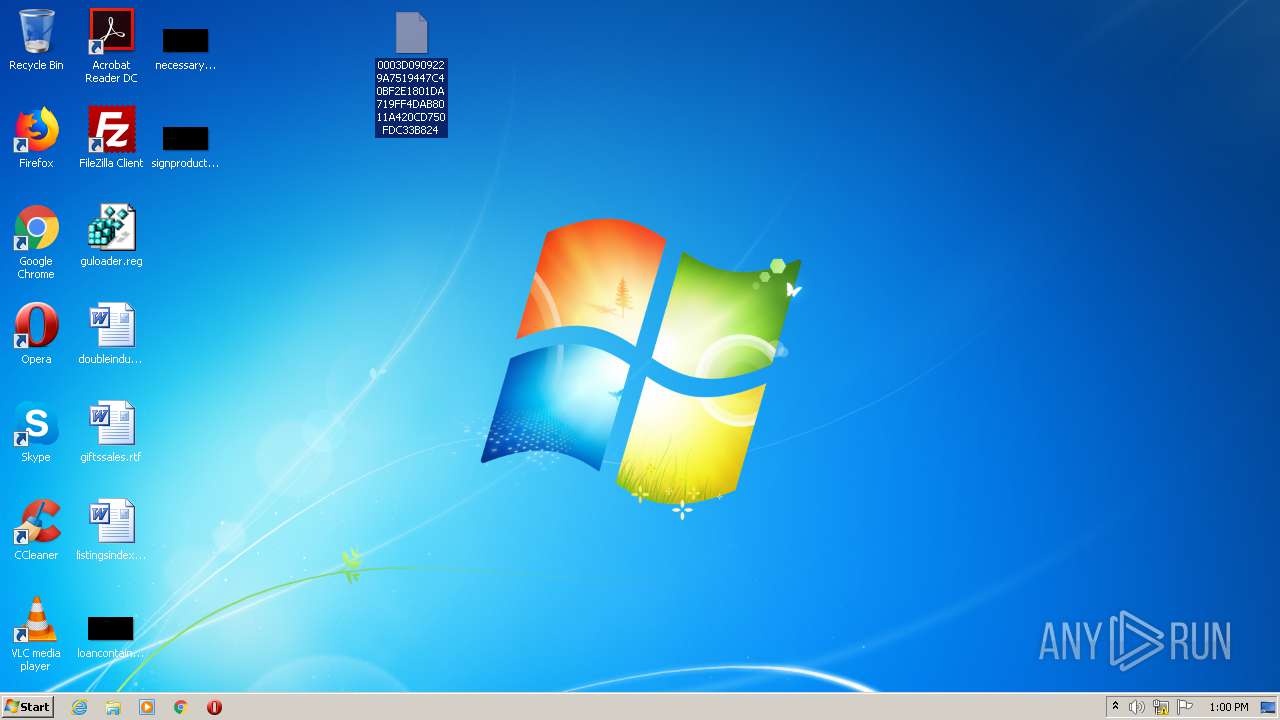
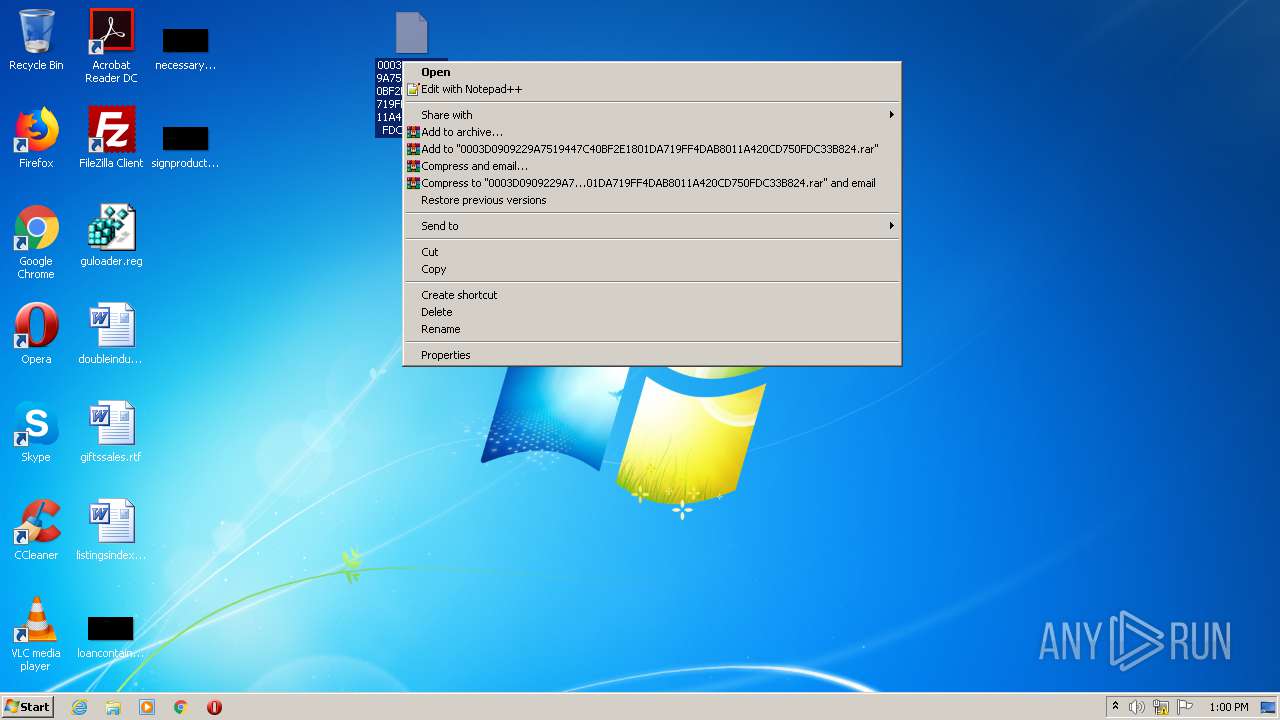
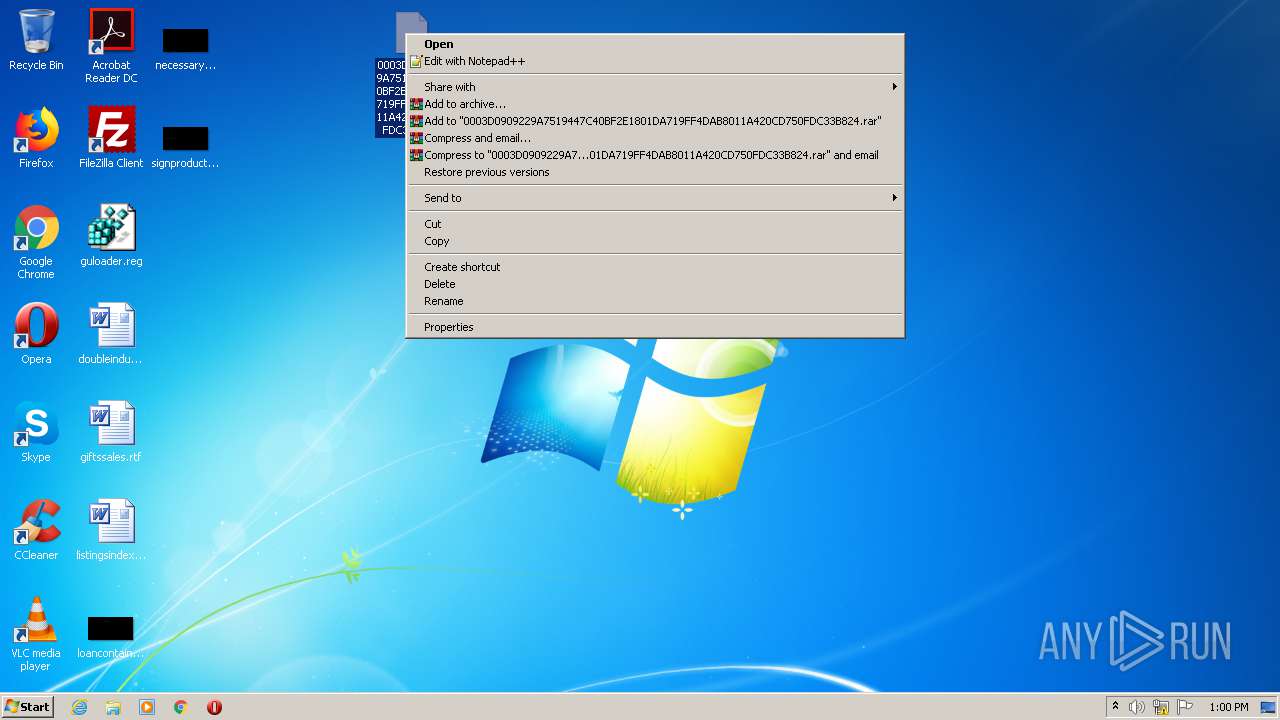
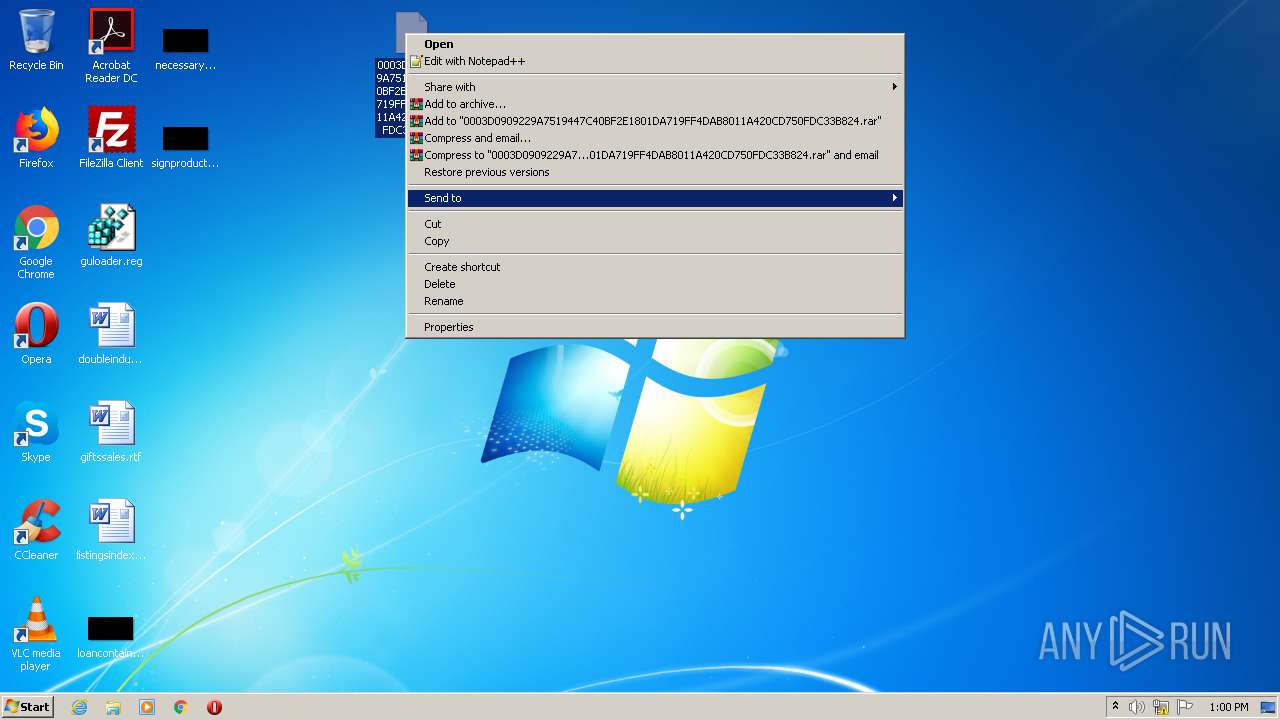
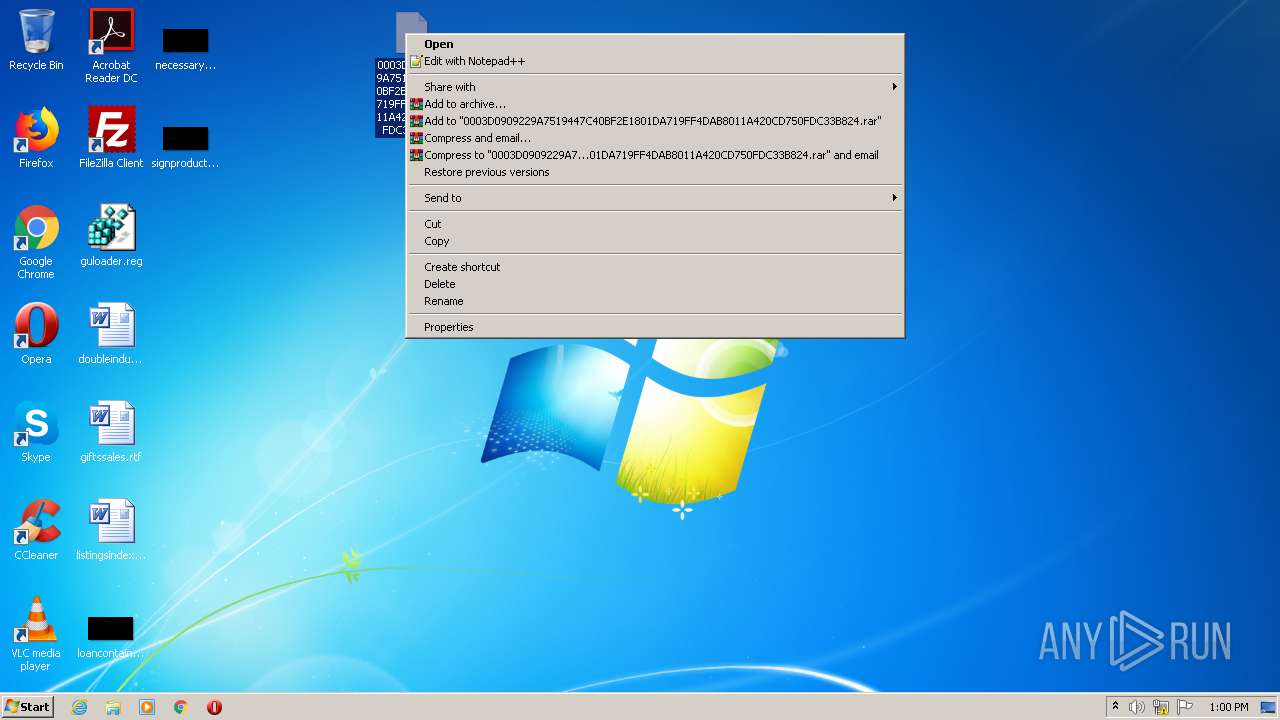
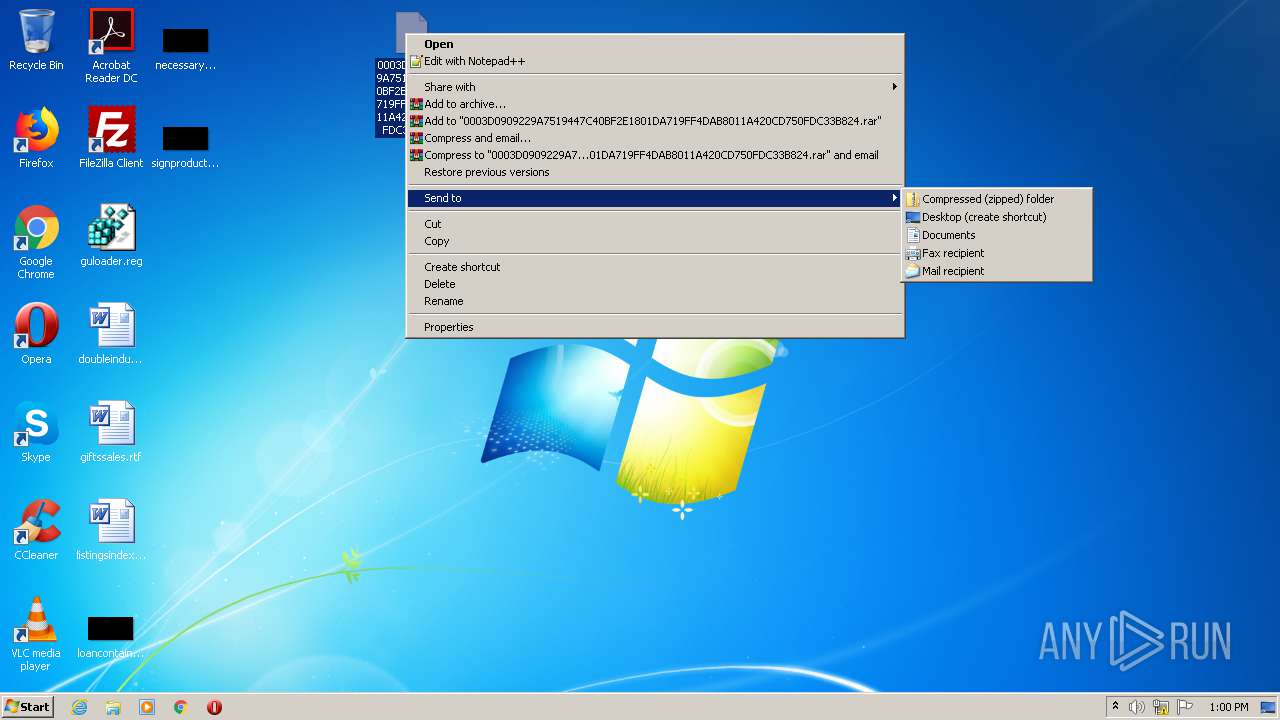
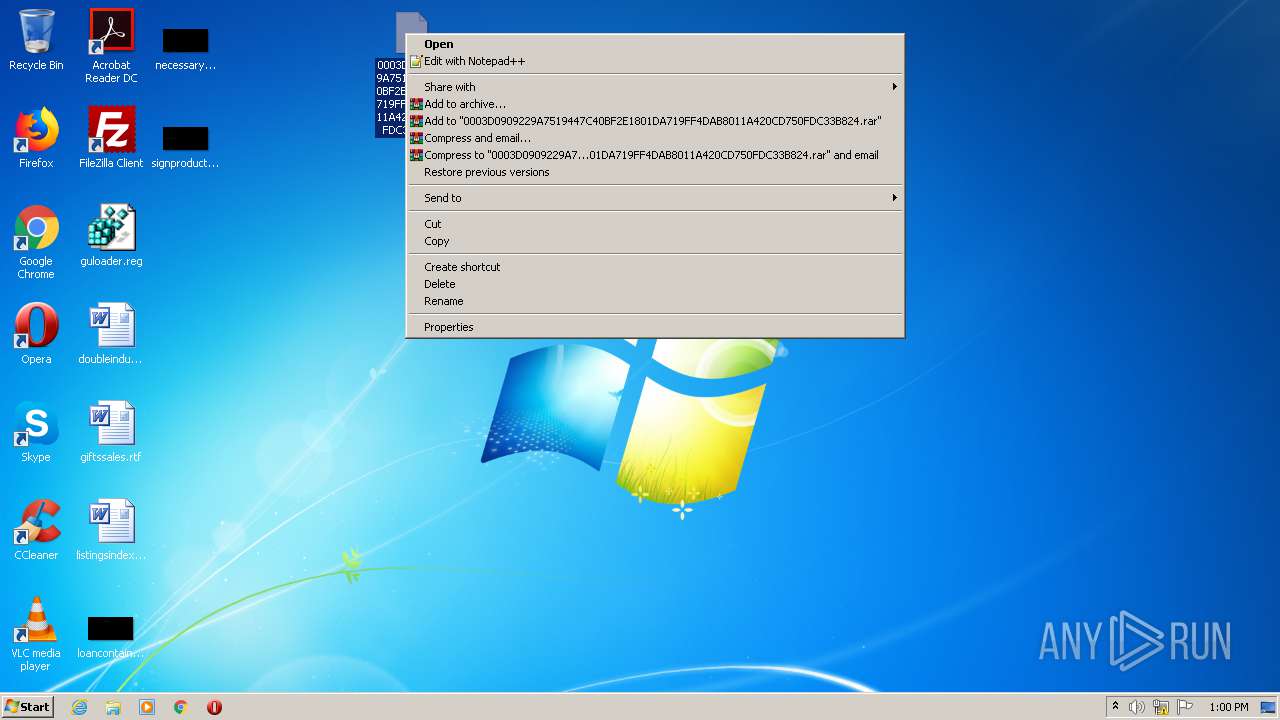
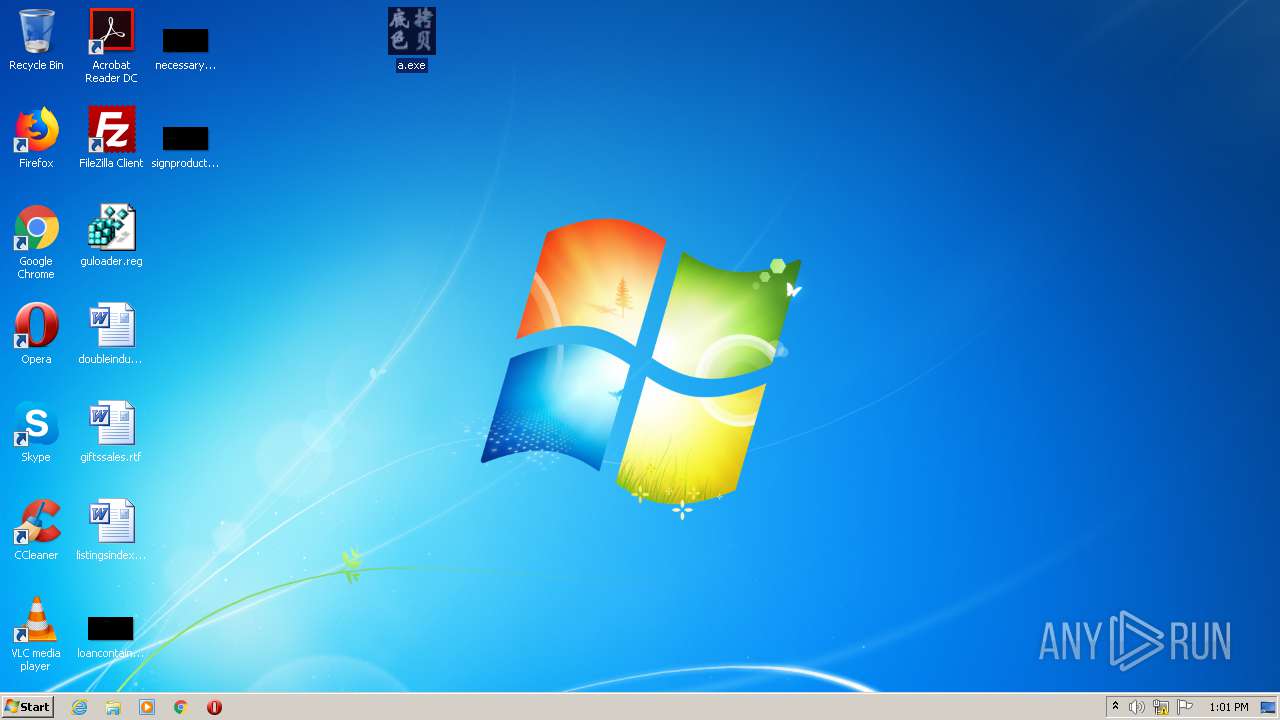
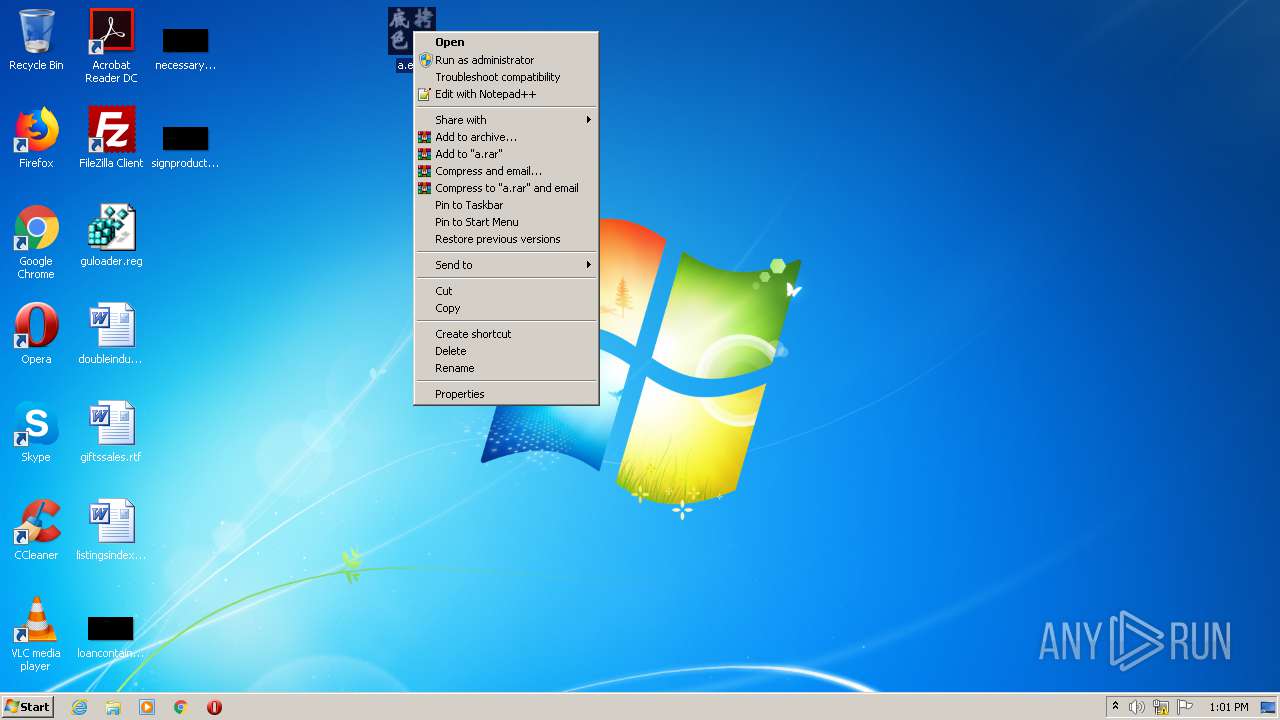
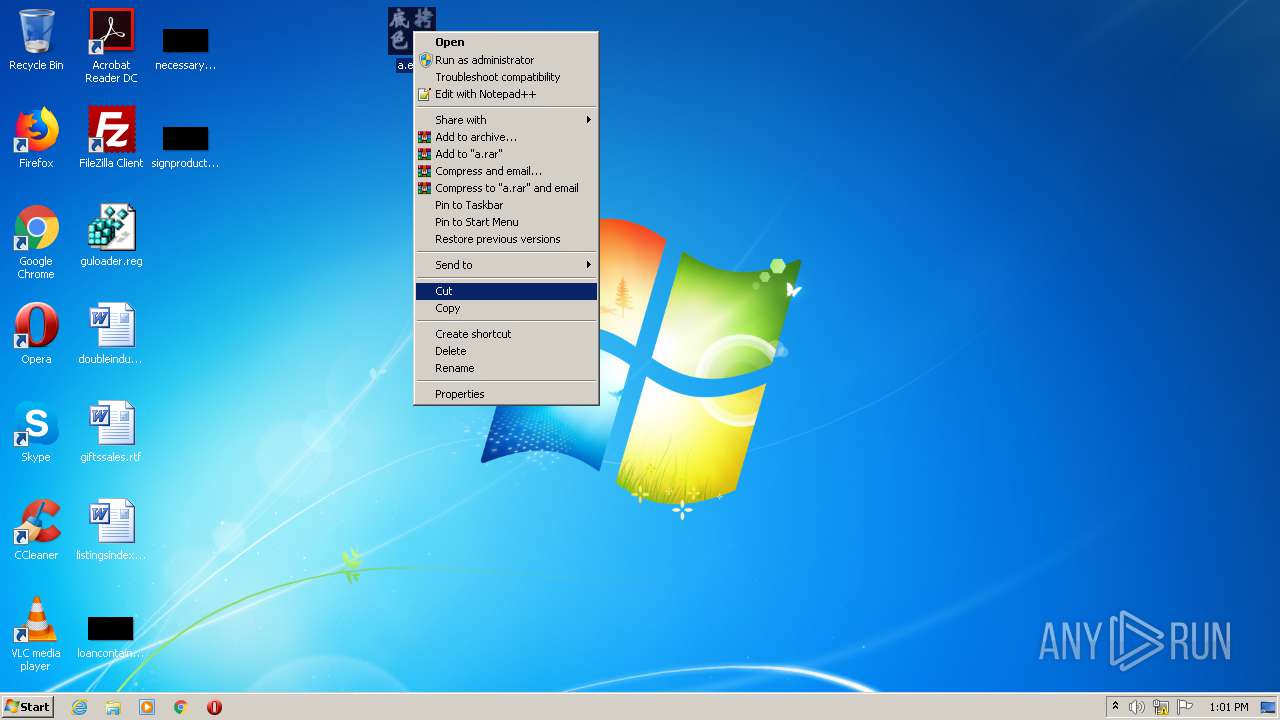
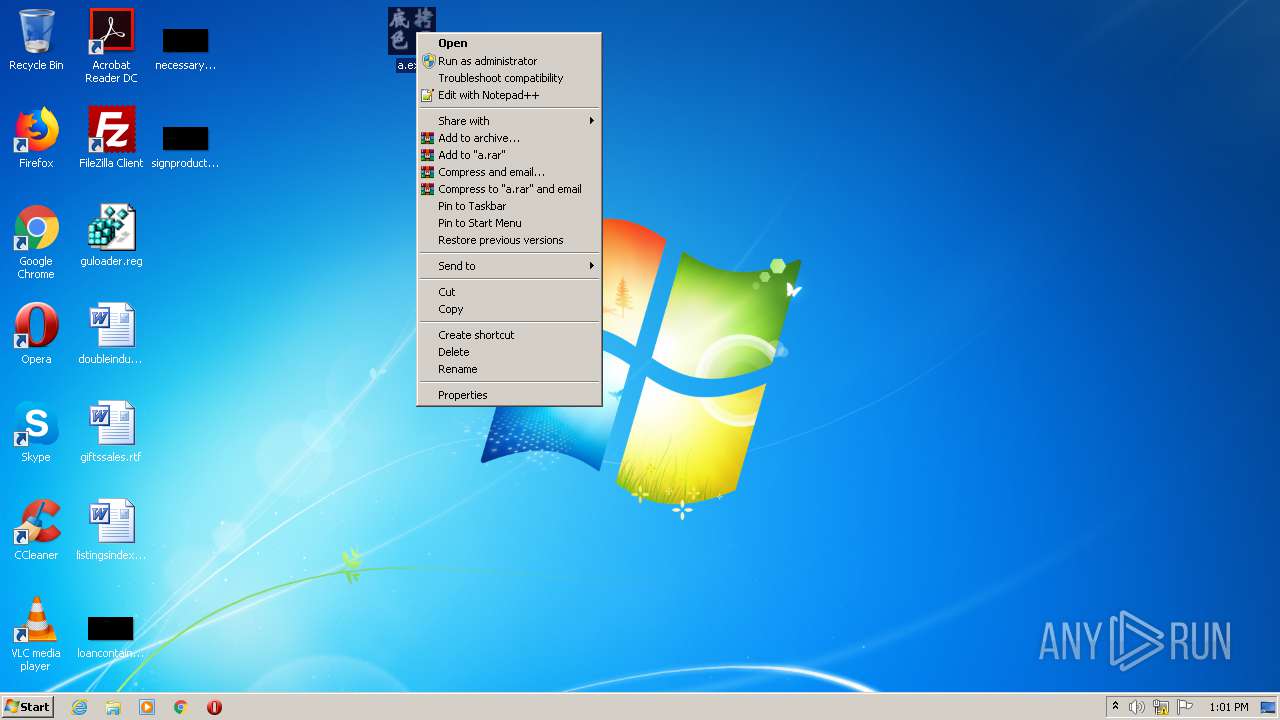
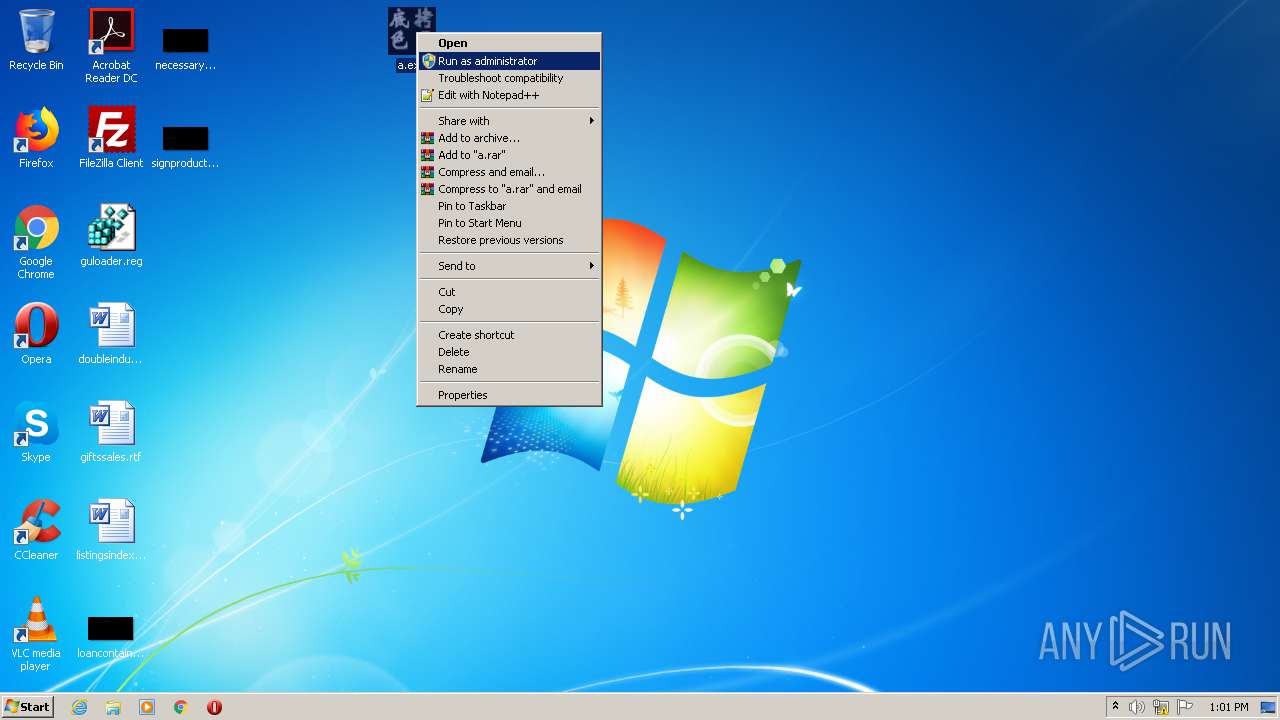
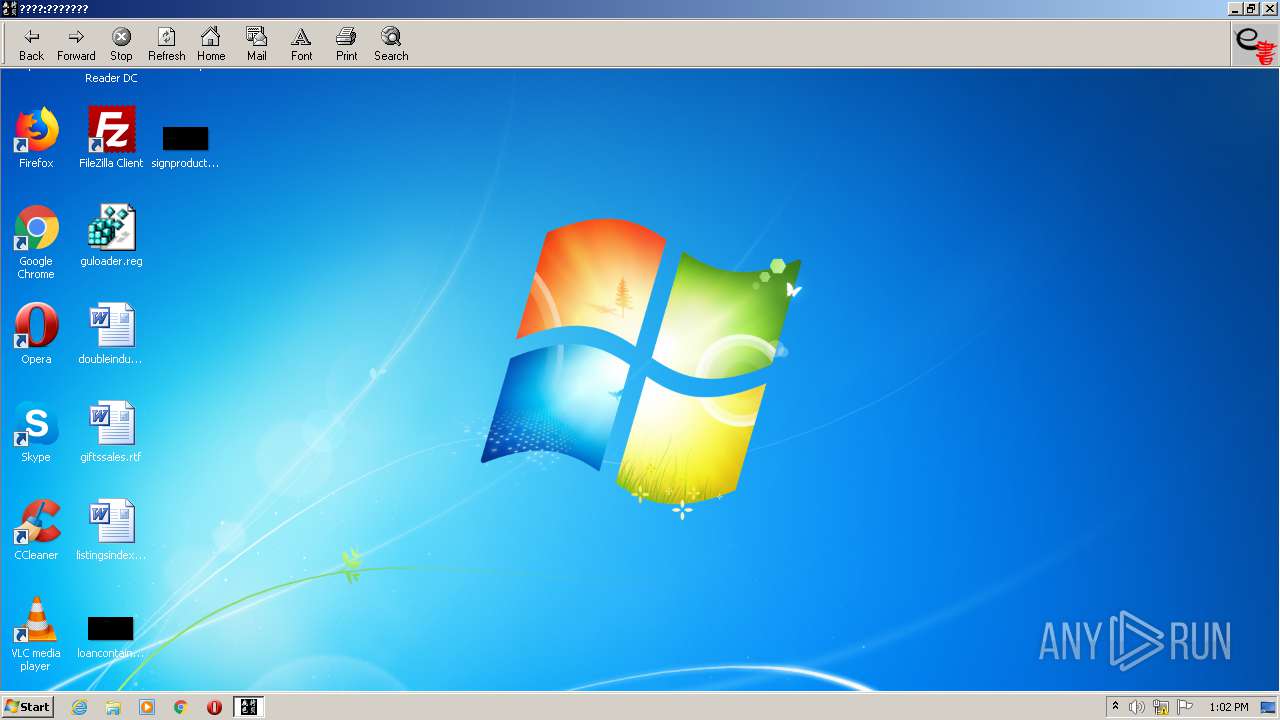
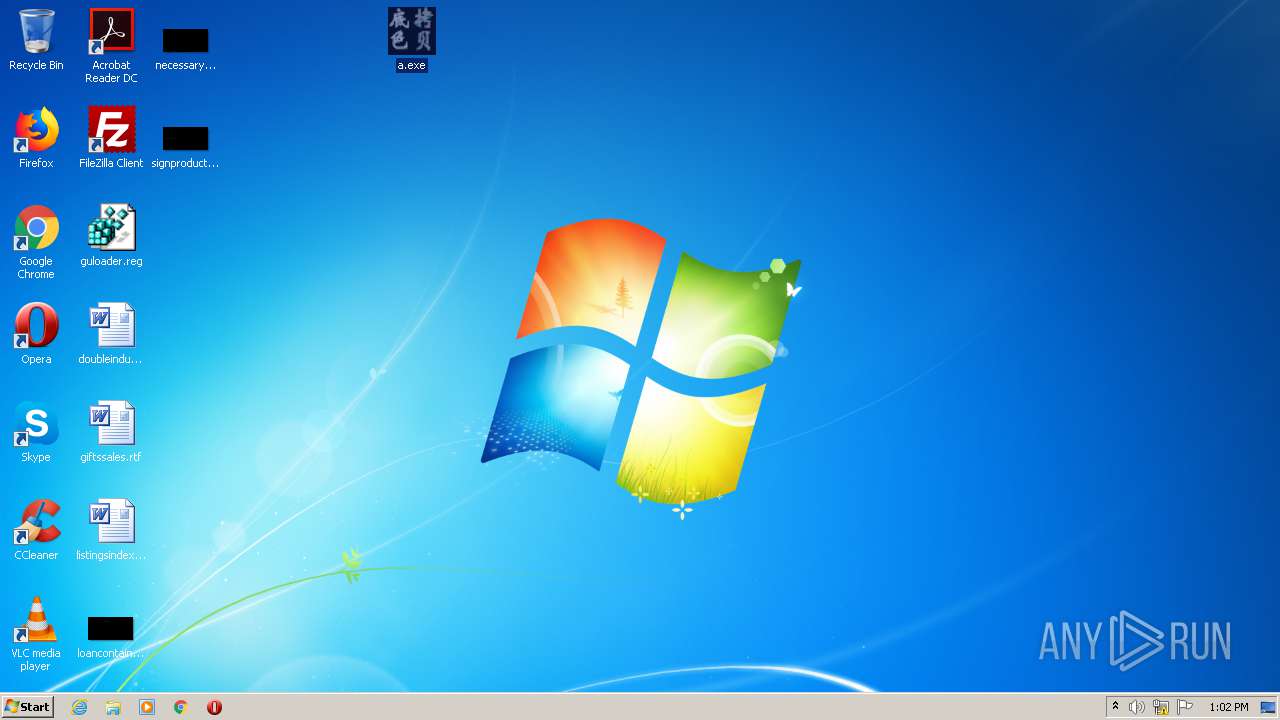
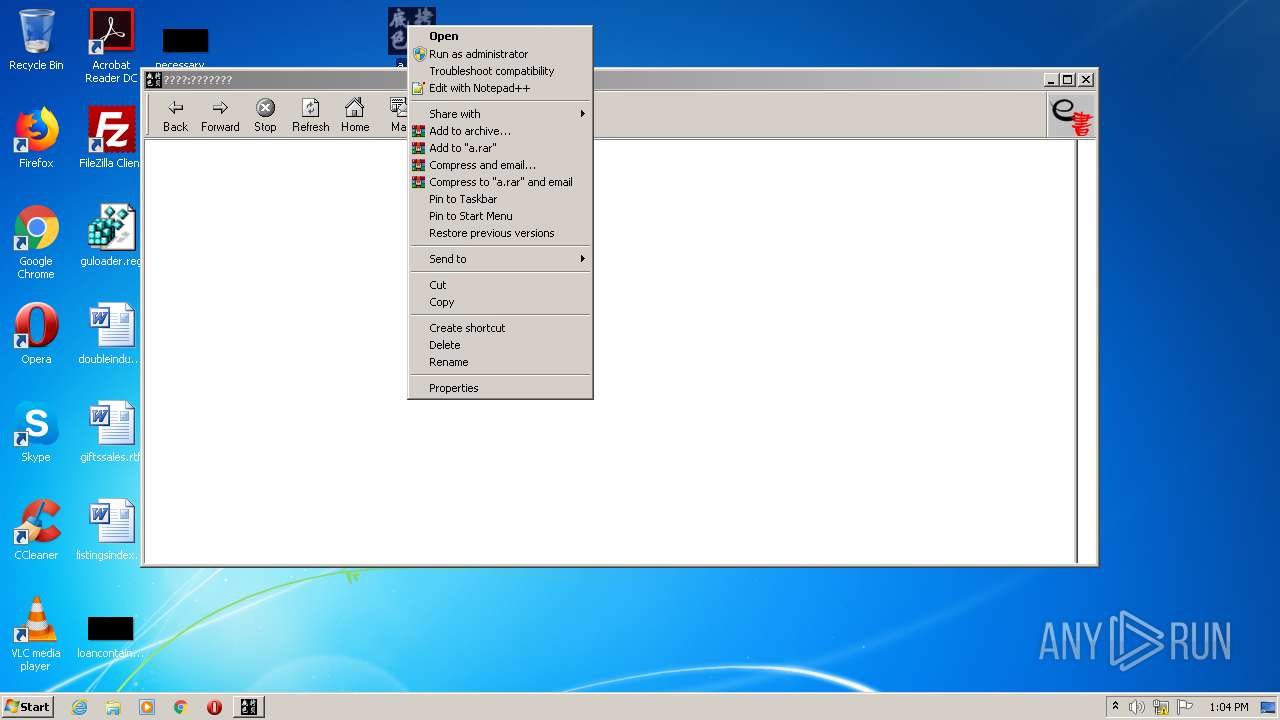
Manual execution by user
- rundll32.exe (PID: 1092)
- a.exe (PID: 2976)
- a.exe (PID: 1144)
- a.exe (PID: 848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
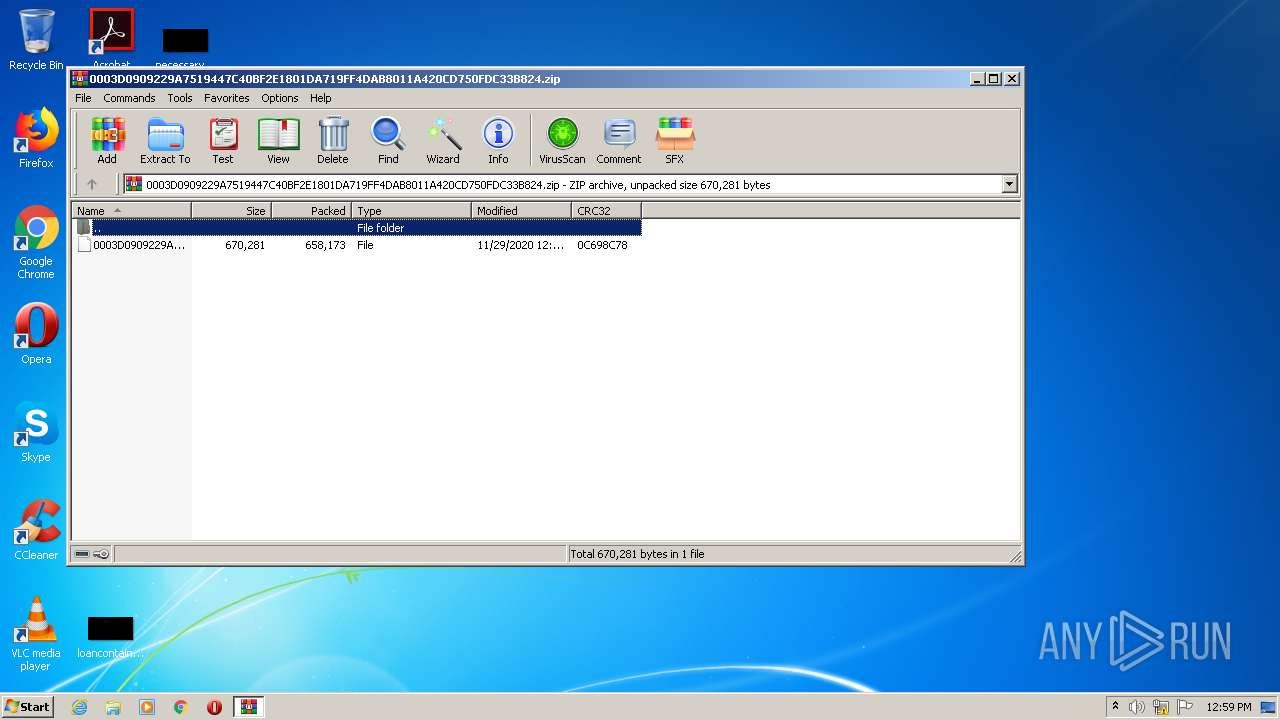
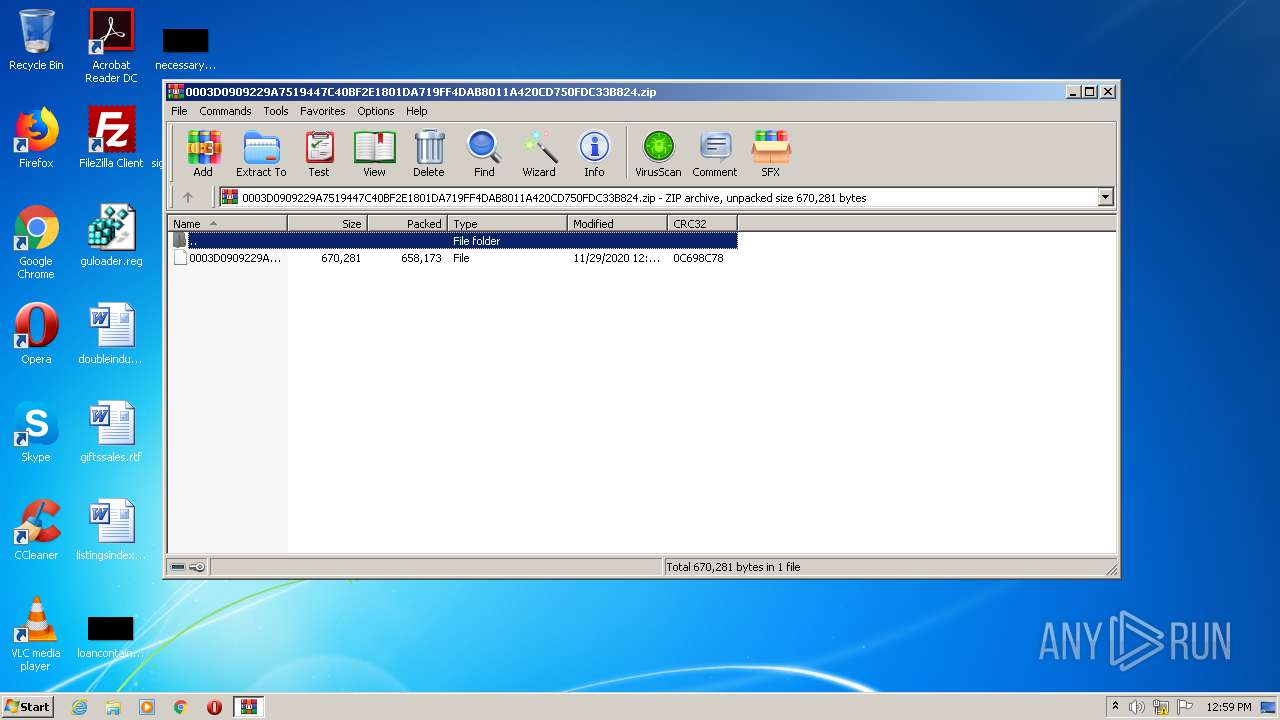
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:11:29 12:04:26 |
| ZipCRC: | 0x0c698c78 |
| ZipCompressedSize: | 658173 |
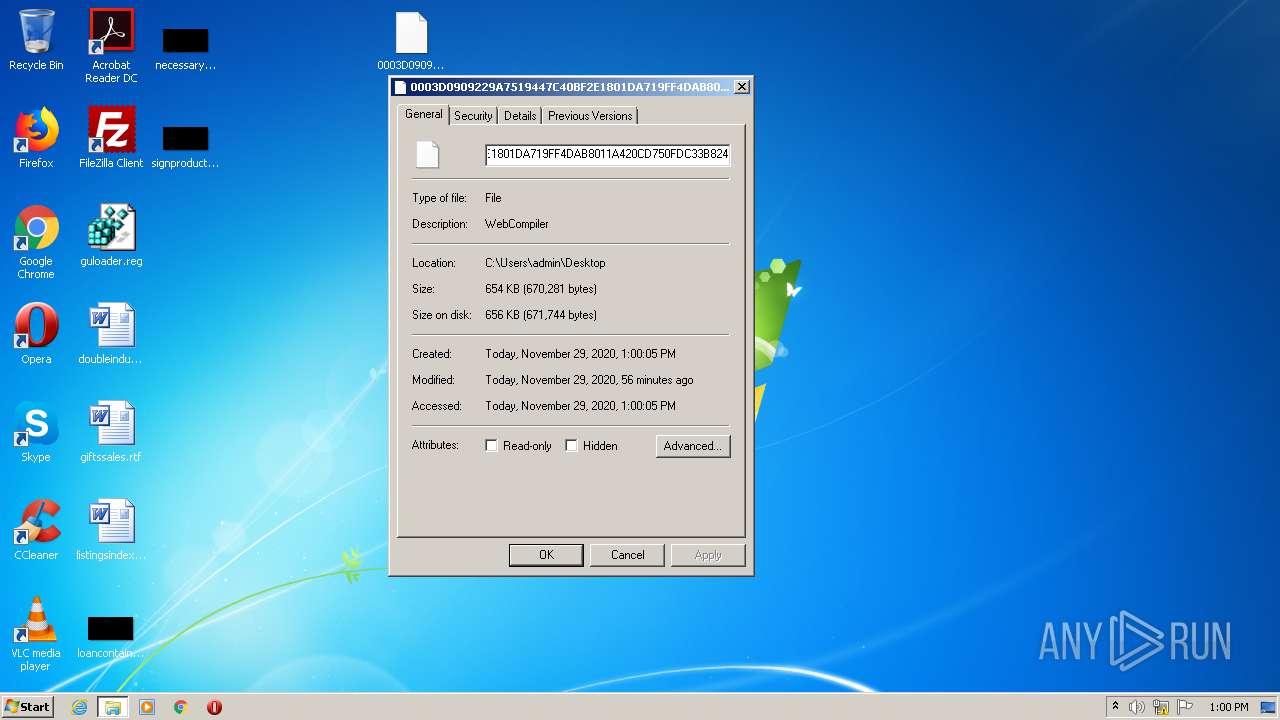
| ZipUncompressedSize: | 670281 |
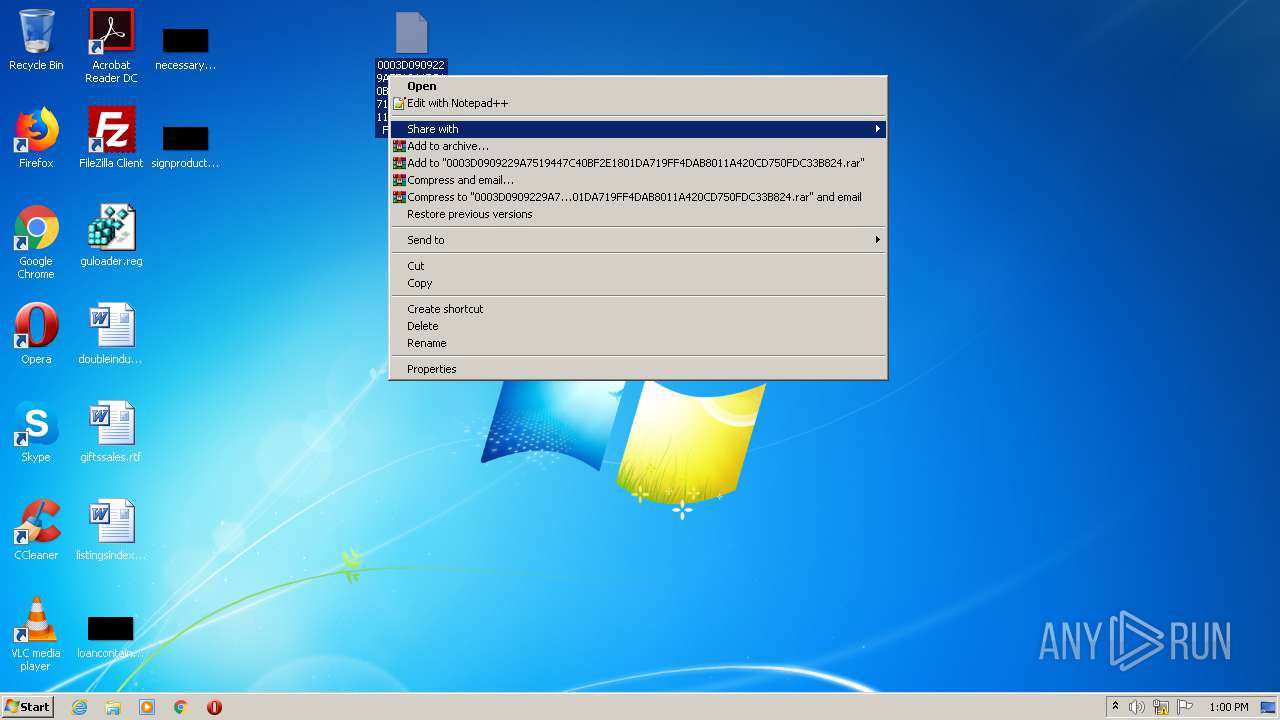
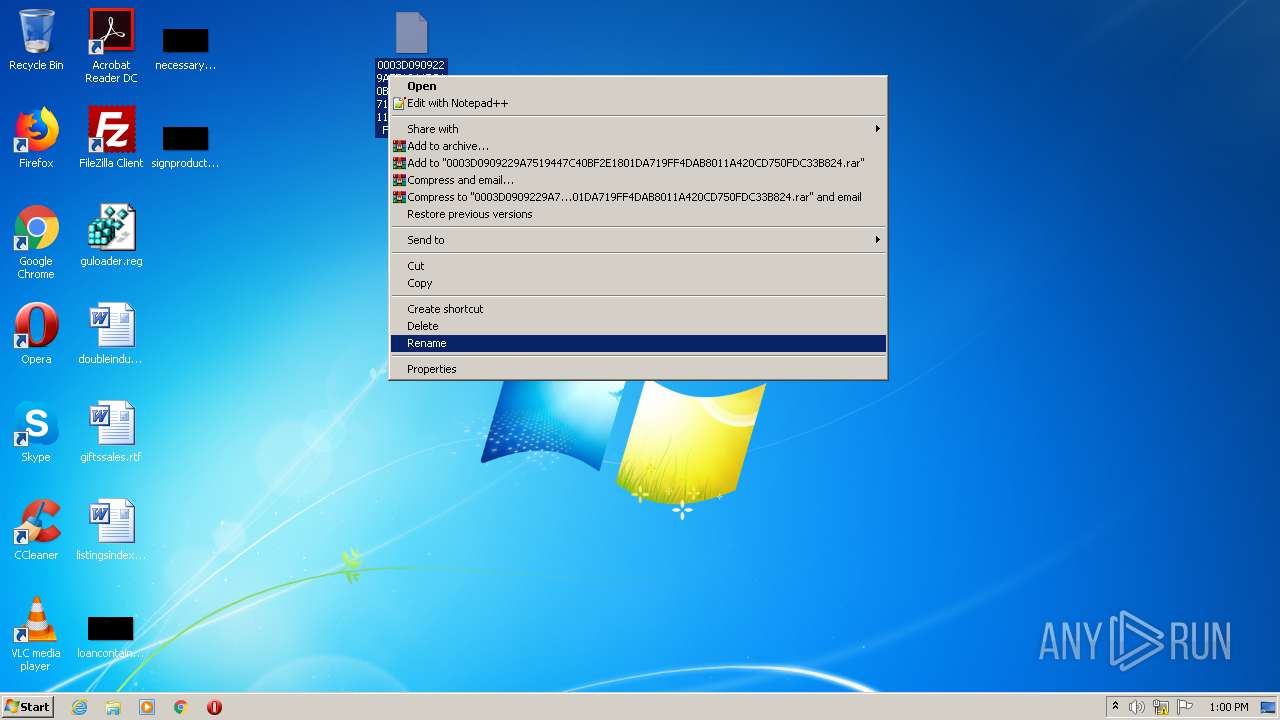
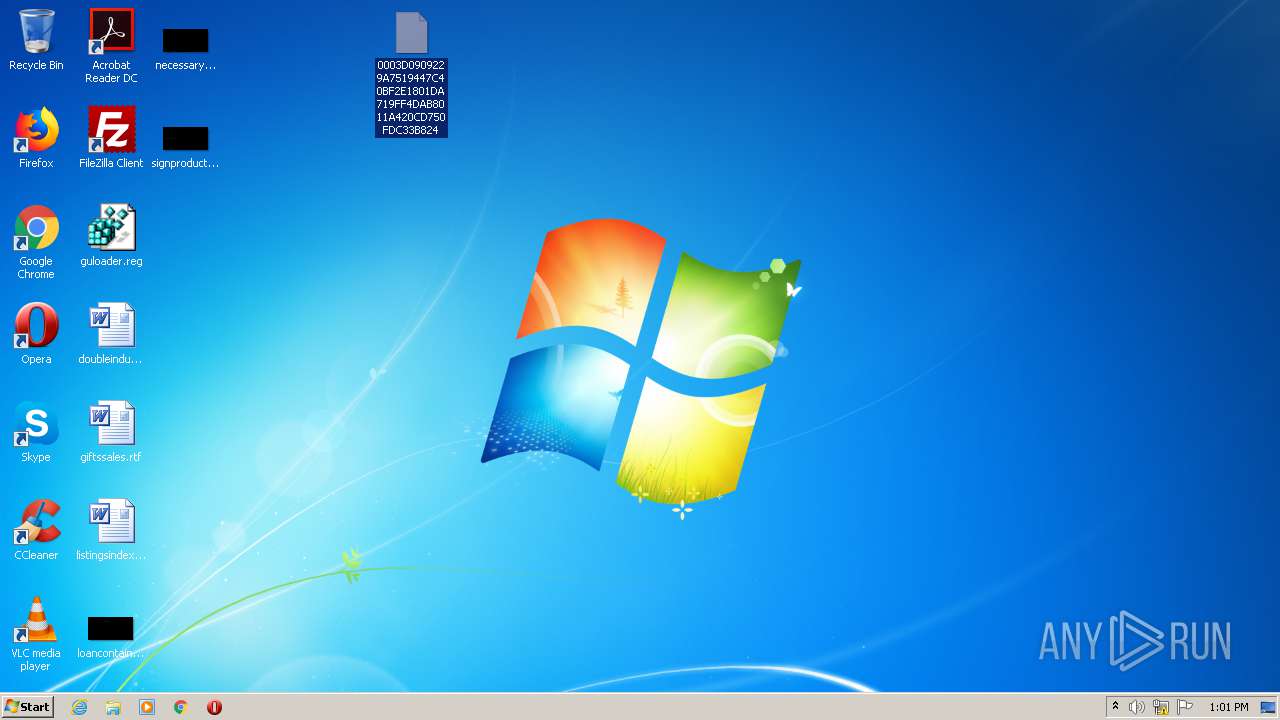
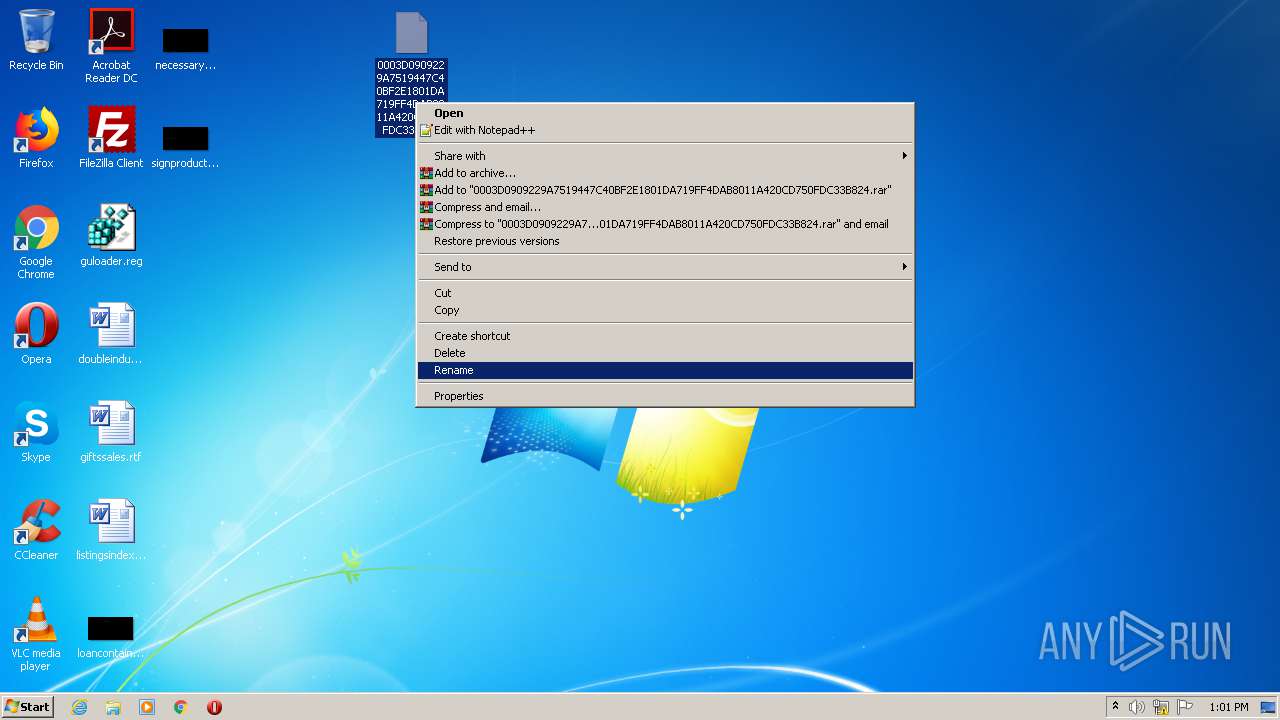
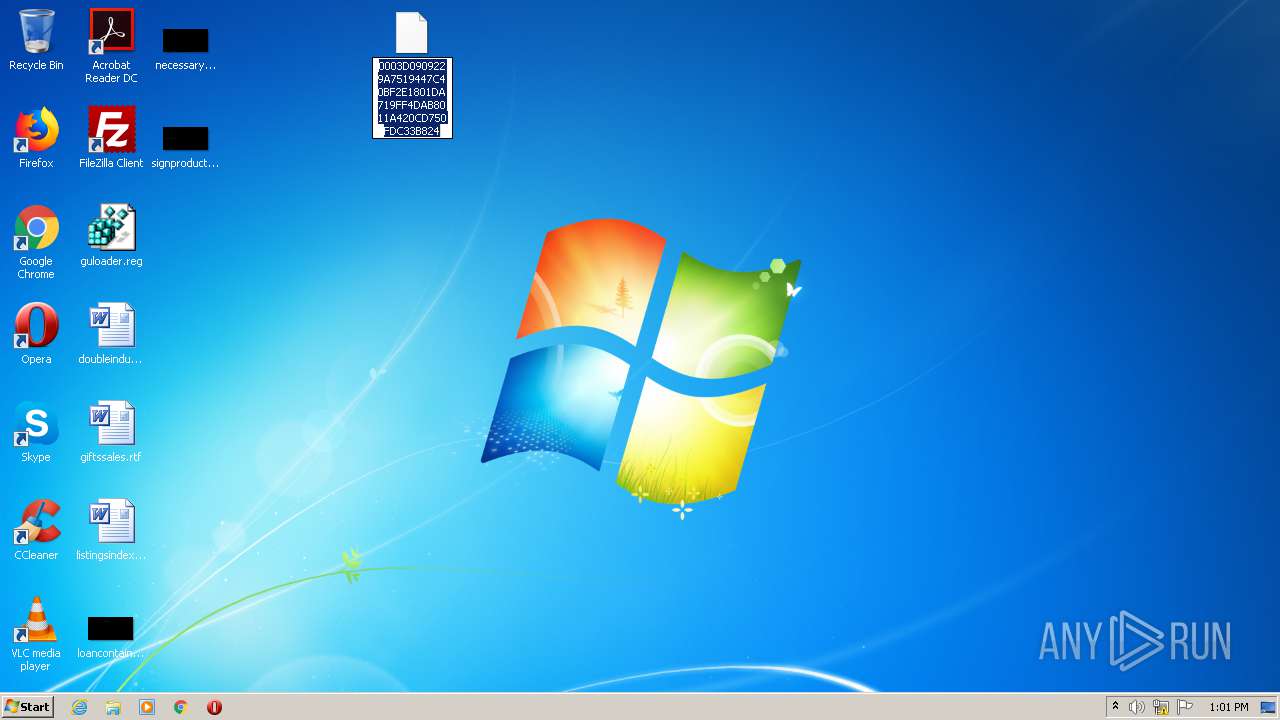
| ZipFileName: | 0003D0909229A7519447C40BF2E1801DA719FF4DAB8011A420CD750FDC33B824 |
Total processes
54
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
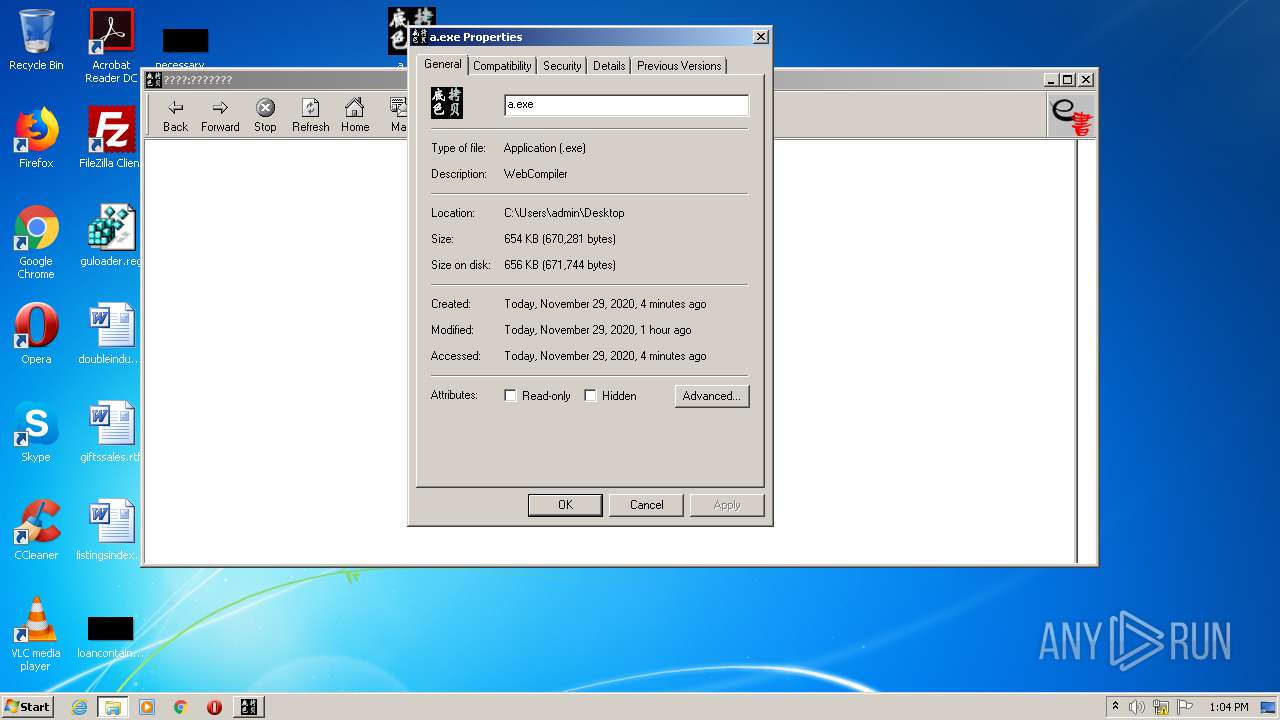
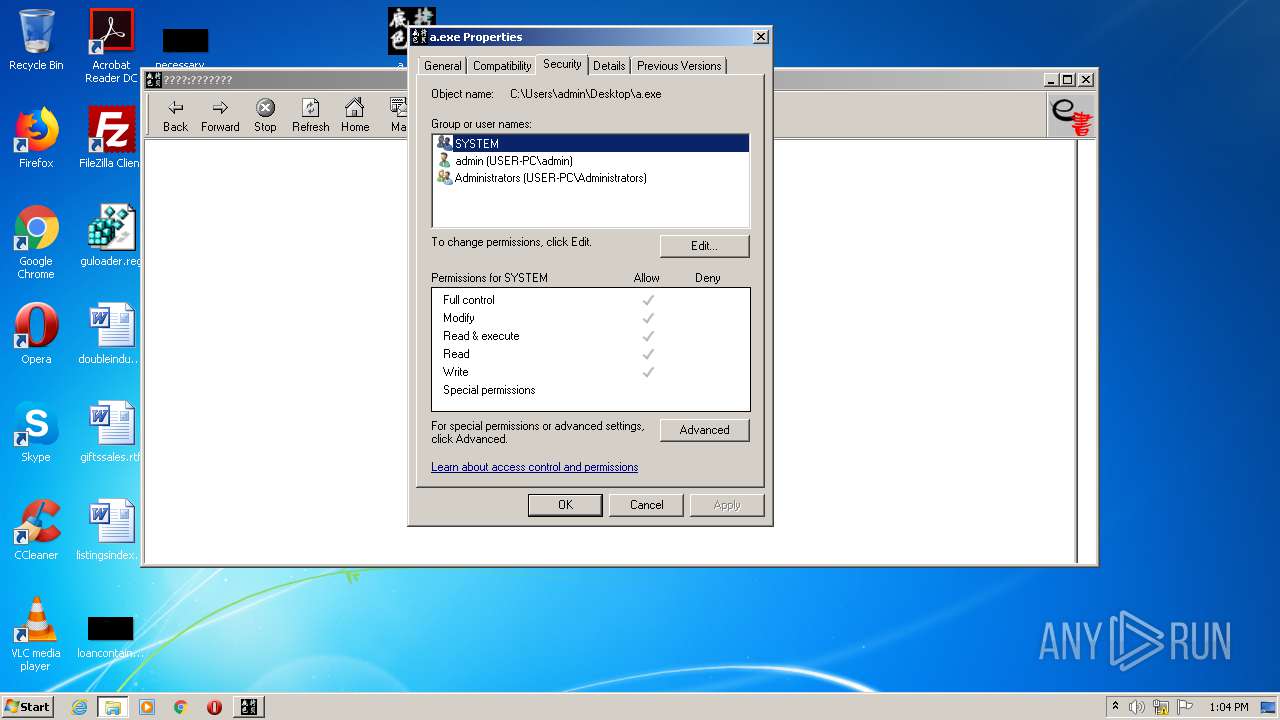
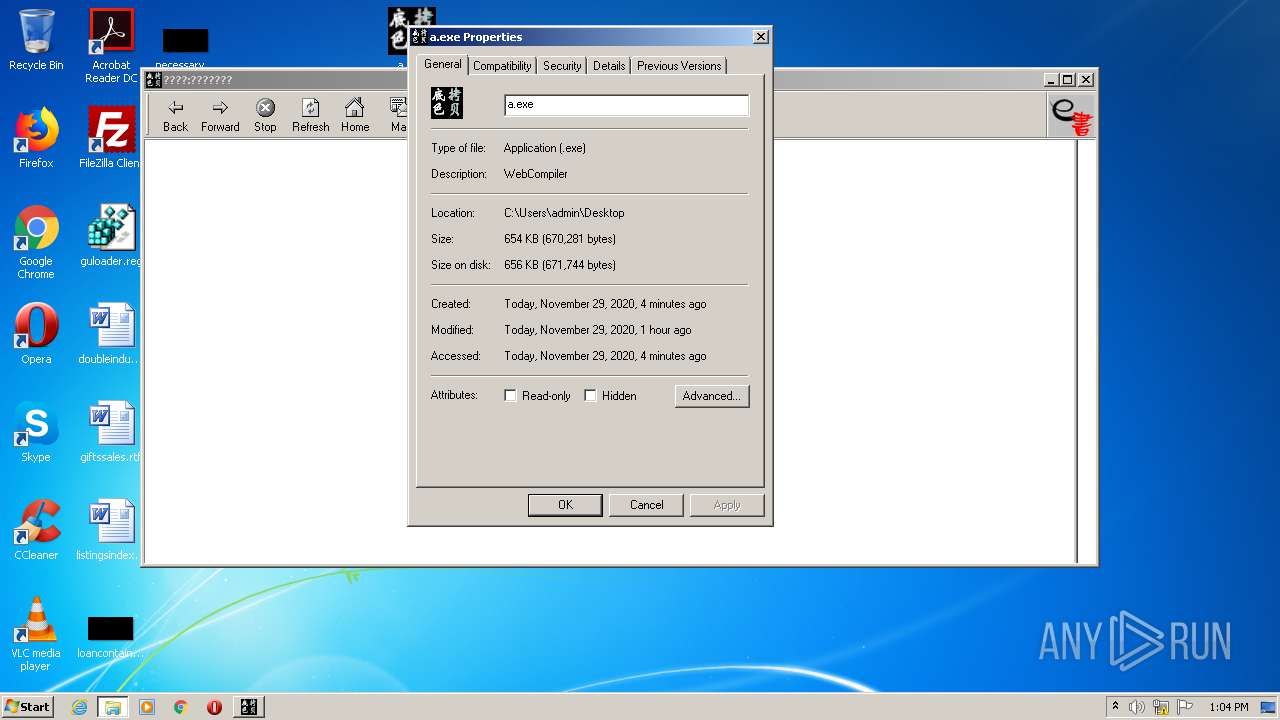
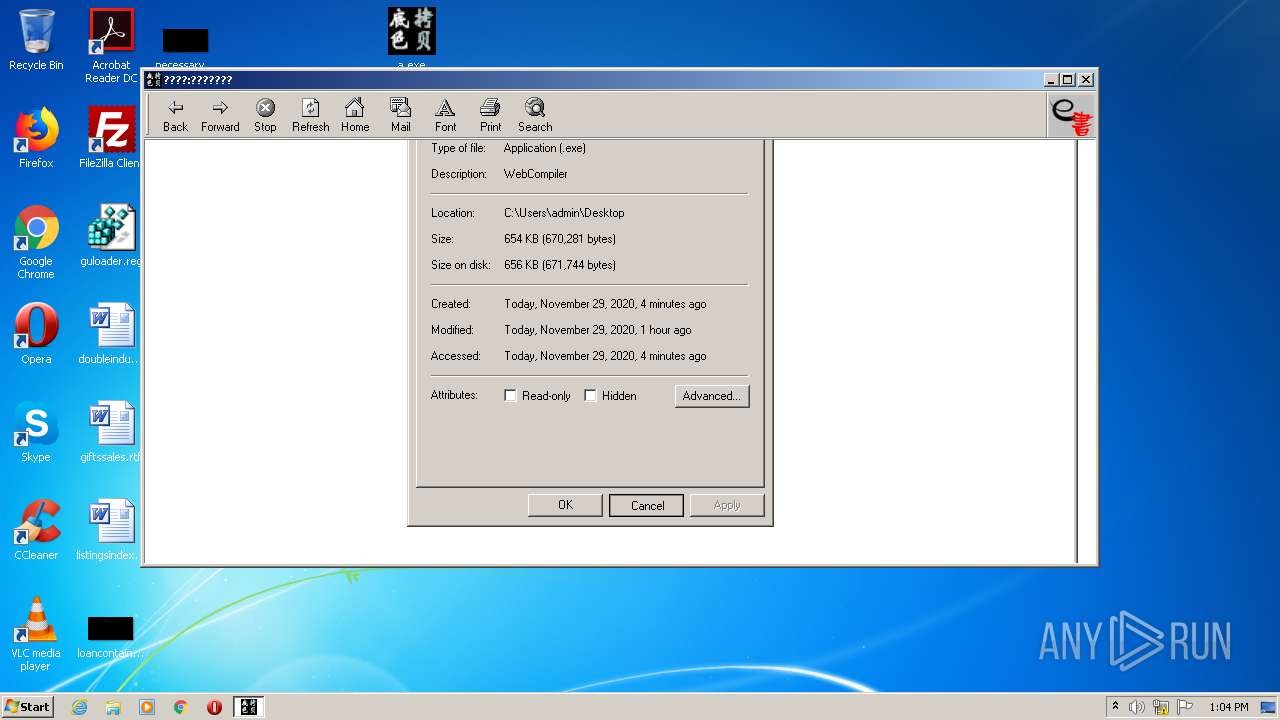
| 848 | "C:\Users\admin\Desktop\a.exe" | C:\Users\admin\Desktop\a.exe | explorer.exe | ||||||||||||
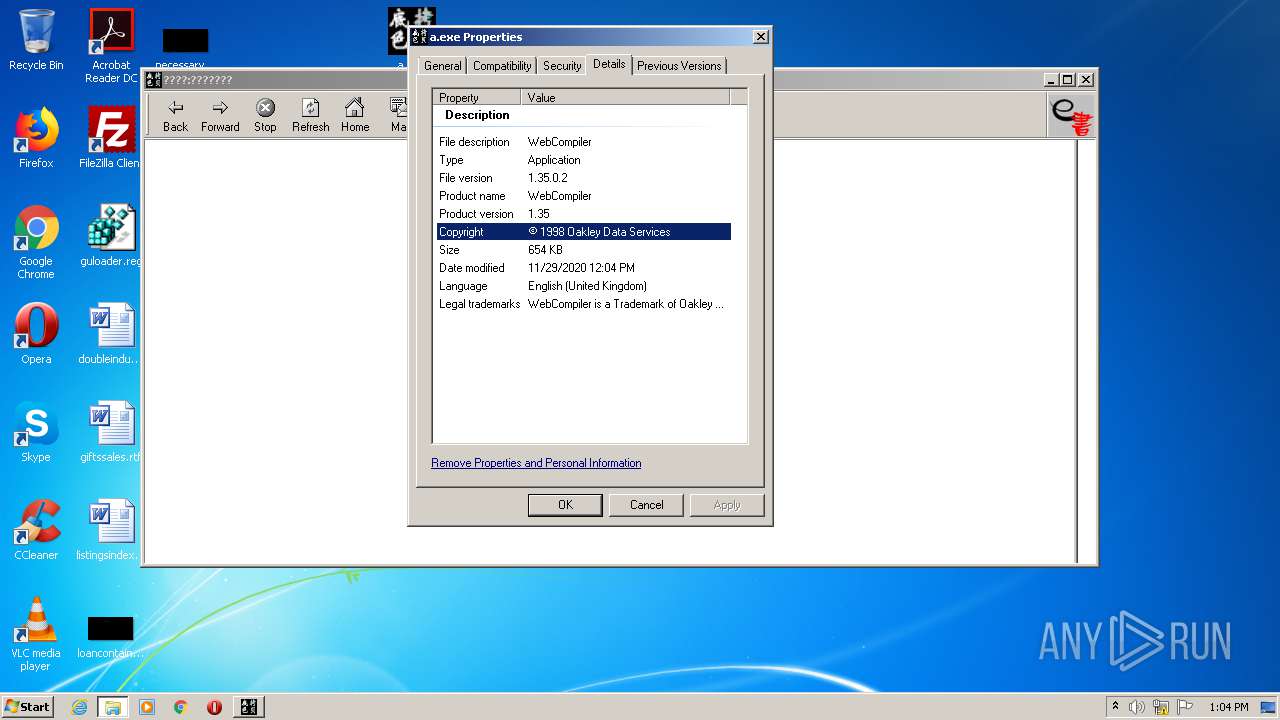
User: admin Company: Oakley Data Services Integrity Level: HIGH Description: WebCompiler Exit code: 3221225547 Version: 1.35.0.2 Modules
| |||||||||||||||
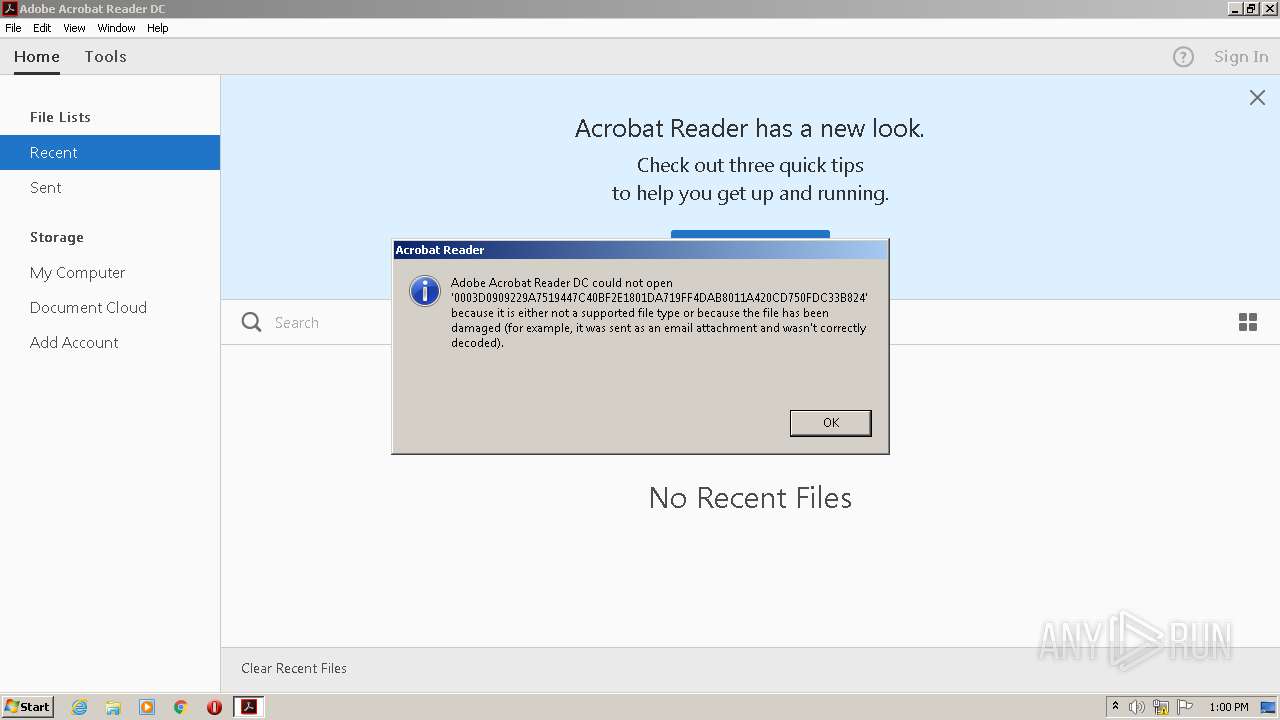
| 936 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\Desktop\0003D0909229A7519447C40BF2E1801DA719FF4DAB8011A420CD750FDC33B824" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 3221225547 Version: 15.23.20053.211670 Modules
| |||||||||||||||
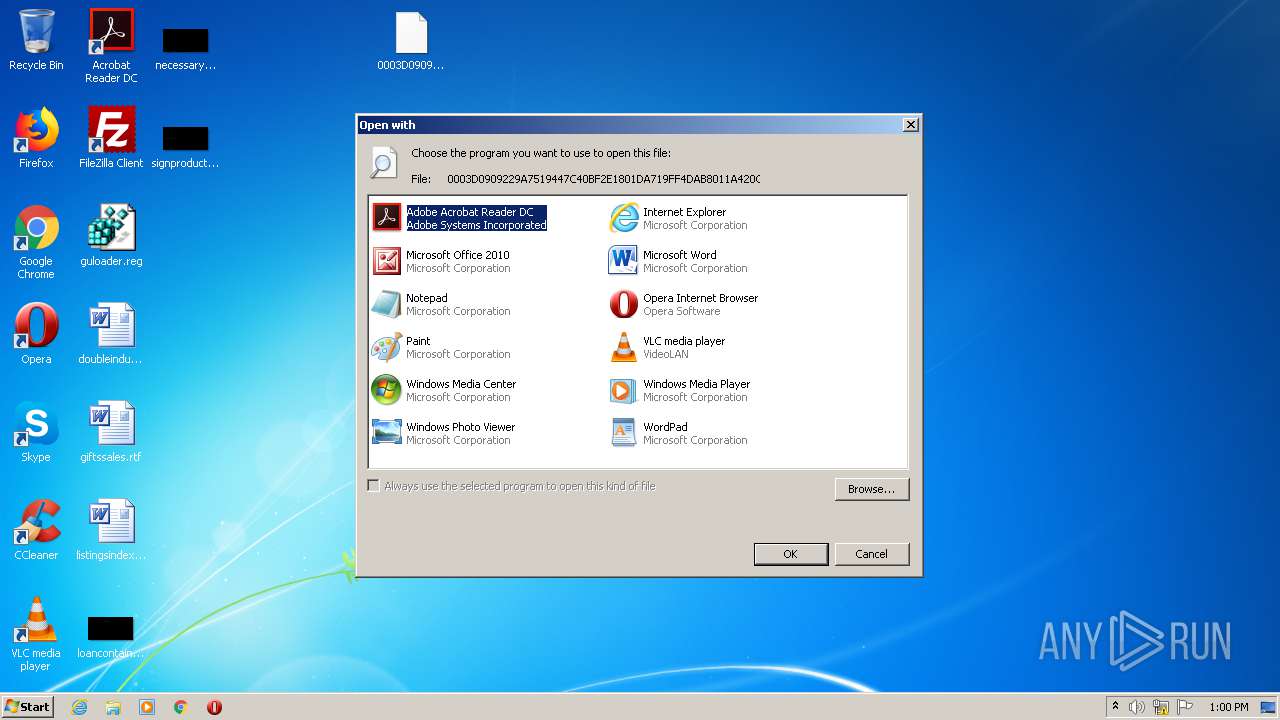
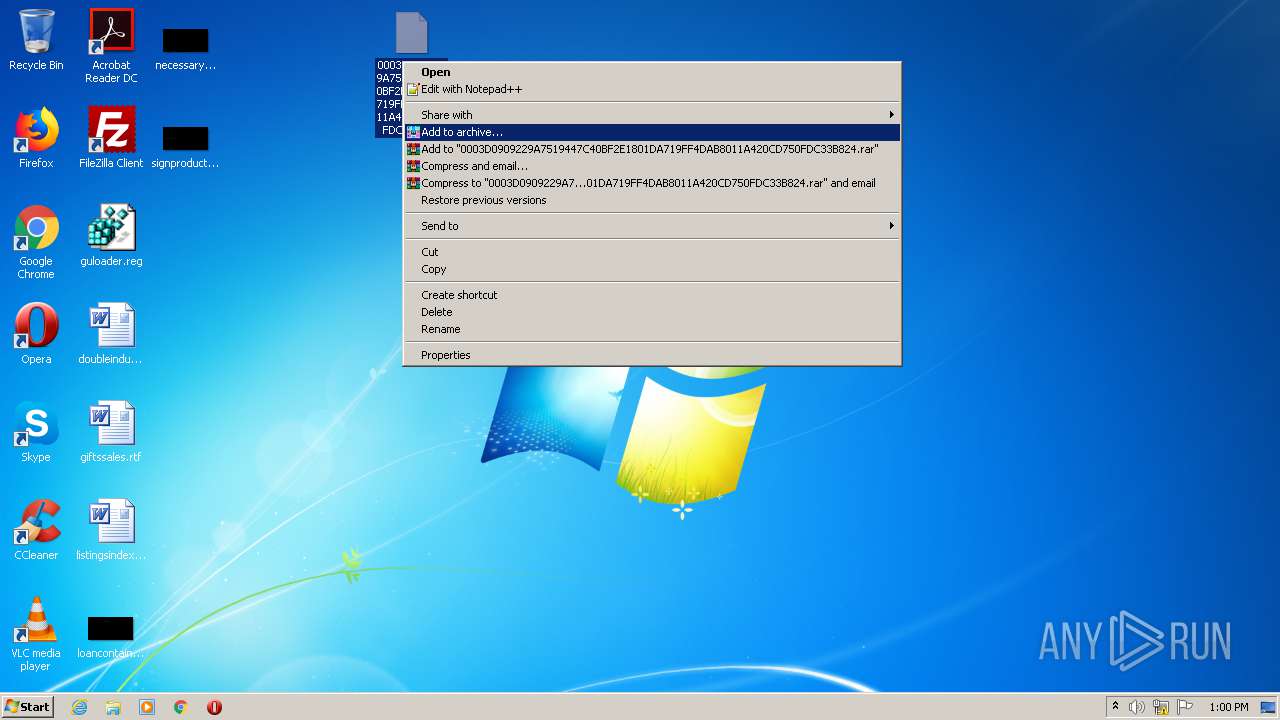
| 1092 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\0003D0909229A7519447C40BF2E1801DA719FF4DAB8011A420CD750FDC33B824 | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1144 | "C:\Users\admin\Desktop\a.exe" | C:\Users\admin\Desktop\a.exe | explorer.exe | ||||||||||||
User: admin Company: Oakley Data Services Integrity Level: HIGH Description: WebCompiler Exit code: 3221225547 Version: 1.35.0.2 Modules
| |||||||||||||||
| 1372 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="1064.0.400157520\801350775" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\0003D0909229A7519447C40BF2E1801DA719FF4DAB8011A420CD750FDC33B824.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2676 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\Desktop\0003D0909229A7519447C40BF2E1801DA719FF4DAB8011A420CD750FDC33B824" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\Desktop\a.exe" | C:\Users\admin\Desktop\a.exe | — | explorer.exe | |||||||||||
User: admin Company: Oakley Data Services Integrity Level: MEDIUM Description: WebCompiler Exit code: 217 Version: 1.35.0.2 Modules
| |||||||||||||||
Total events
1 073
Read events
876
Write events
197
Delete events
0
Modification events
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\0003D0909229A7519447C40BF2E1801DA719FF4DAB8011A420CD750FDC33B824.zip | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
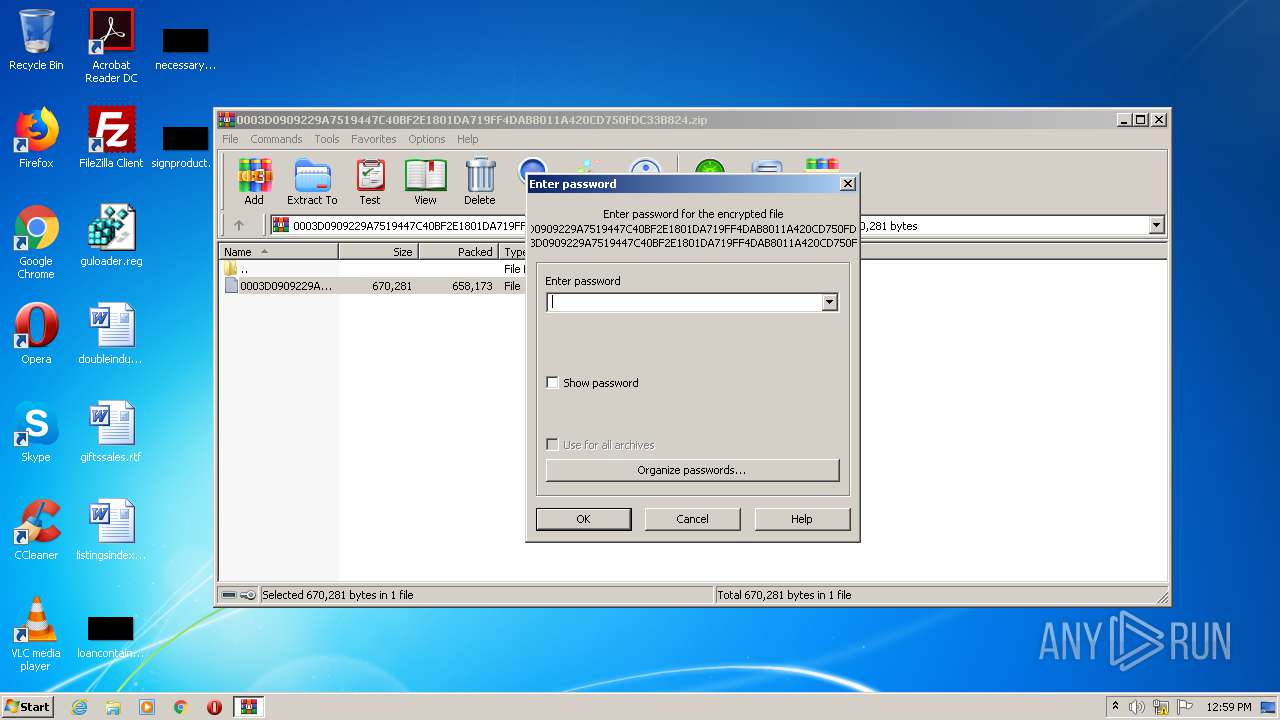
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFD50000006B0000009504000060020000 | |||
Executable files
1
Suspicious files
3
Text files
4
Unknown types
5
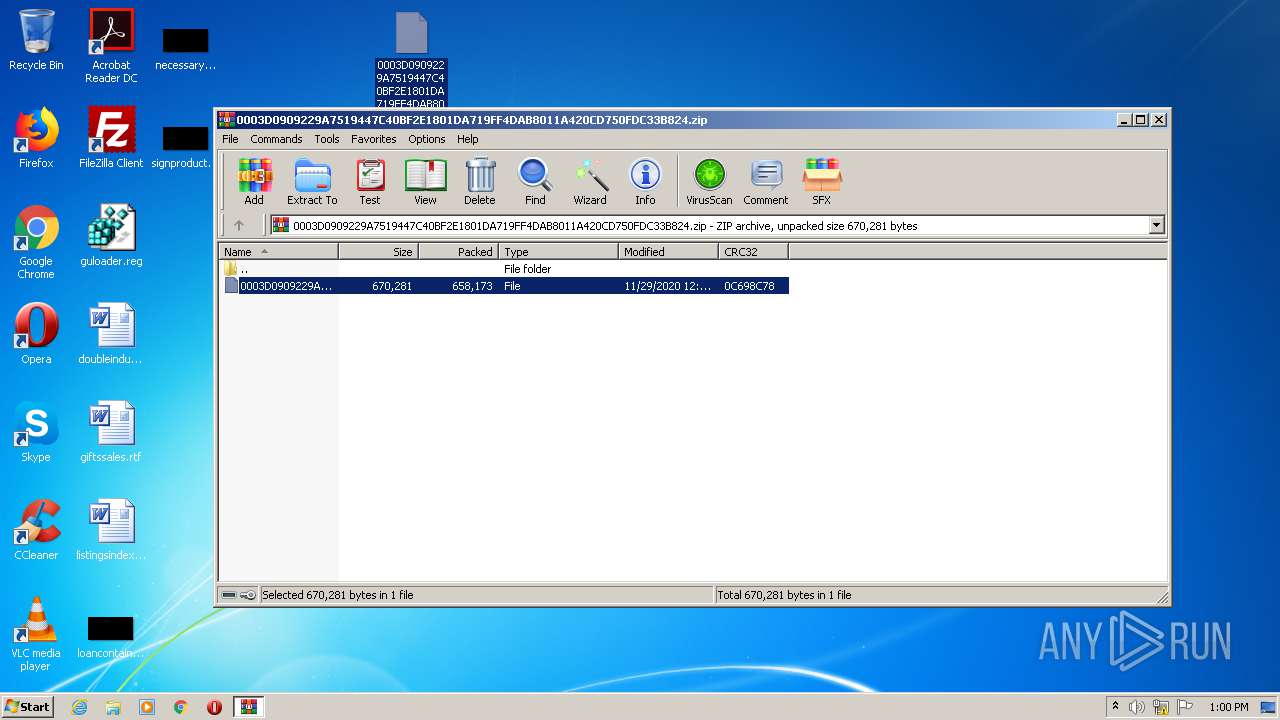
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2488.12694\0003D0909229A7519447C40BF2E1801DA719FF4DAB8011A420CD750FDC33B824 | — | |
MD5:— | SHA256:— | |||
| 936 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 936 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\AdobeFnt16.lst.936 | — | |
MD5:— | SHA256:— | |||
| 936 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeFnt16.lst.936 | — | |
MD5:— | SHA256:— | |||
| 936 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages | sqlite | |
MD5:— | SHA256:— | |||
| 2676 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeSysFnt15.lst | ps | |
MD5:— | SHA256:— | |||
| 2676 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\AcroFnt15.lst | ps | |
MD5:— | SHA256:— | |||
| 936 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\IconCacheRdr65536.dat | binary | |
MD5:— | SHA256:— | |||
| 2676 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeCMapFnt15.lst | ps | |
MD5:— | SHA256:— | |||
| 1064 | RdrCEF.exe | C:\Users\admin\AppData\Local\Adobe\AcroCef\DC\Acrobat\Cache\data_1 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report