| download: | WildTangentHelper-1.0.0.437.exe |
| Full analysis: | https://app.any.run/tasks/ce4536db-08b0-4c83-bf53-e40cfd1294ba |
| Verdict: | Malicious activity |
| Analysis date: | March 18, 2021, 00:39:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | BDED9C3ACBC05C8DC6CF6E1AB46595DF |
| SHA1: | 105A2A05121D1106A47605507F4E9C0025D96B2C |
| SHA256: | 0D56B010BB9C12B7BA02A3941E84548F3F97BC026657386FFA2C4A9939A82162 |
| SSDEEP: | 98304:o/vNVki0d9bk6DnPmvyXoc8rb0D/Nr8WB:oHNSb9zPmvy4y/Nr88 |
MALICIOUS
Loads dropped or rewritten executable
- WildTangentHelper-1.0.0.437.exe (PID: 2496)
Application was dropped or rewritten from another process
- nsFAEB.tmp (PID: 956)
- nsFC72.tmp (PID: 2820)
- nsFEA6.tmp (PID: 4056)
- ns260.tmp (PID: 1872)
- WildTangentHelperService.exe (PID: 2888)
- ns484.tmp (PID: 4080)
- WildTangentHelperService.exe (PID: 2080)
- ns101E.tmp (PID: 1344)
Starts NET.EXE for service management
- nsFC72.tmp (PID: 2820)
- ns484.tmp (PID: 4080)
Changes settings of System certificates
- WildTangentHelperService.exe (PID: 2080)
SUSPICIOUS
Drops a file with too old compile date
- WildTangentHelper-1.0.0.437.exe (PID: 2496)
Starts application with an unusual extension
- WildTangentHelper-1.0.0.437.exe (PID: 2496)
Creates a directory in Program Files
- WildTangentHelper-1.0.0.437.exe (PID: 2496)
Uses TASKKILL.EXE to kill process
- nsFEA6.tmp (PID: 4056)
Executable content was dropped or overwritten
- WildTangentHelper-1.0.0.437.exe (PID: 2496)
Drops a file with a compile date too recent
- WildTangentHelper-1.0.0.437.exe (PID: 2496)
Drops a file that was compiled in debug mode
- WildTangentHelper-1.0.0.437.exe (PID: 2496)
Creates files in the program directory
- WildTangentHelper-1.0.0.437.exe (PID: 2496)
- WildTangentHelperService.exe (PID: 2888)
Creates a software uninstall entry
- WildTangentHelper-1.0.0.437.exe (PID: 2496)
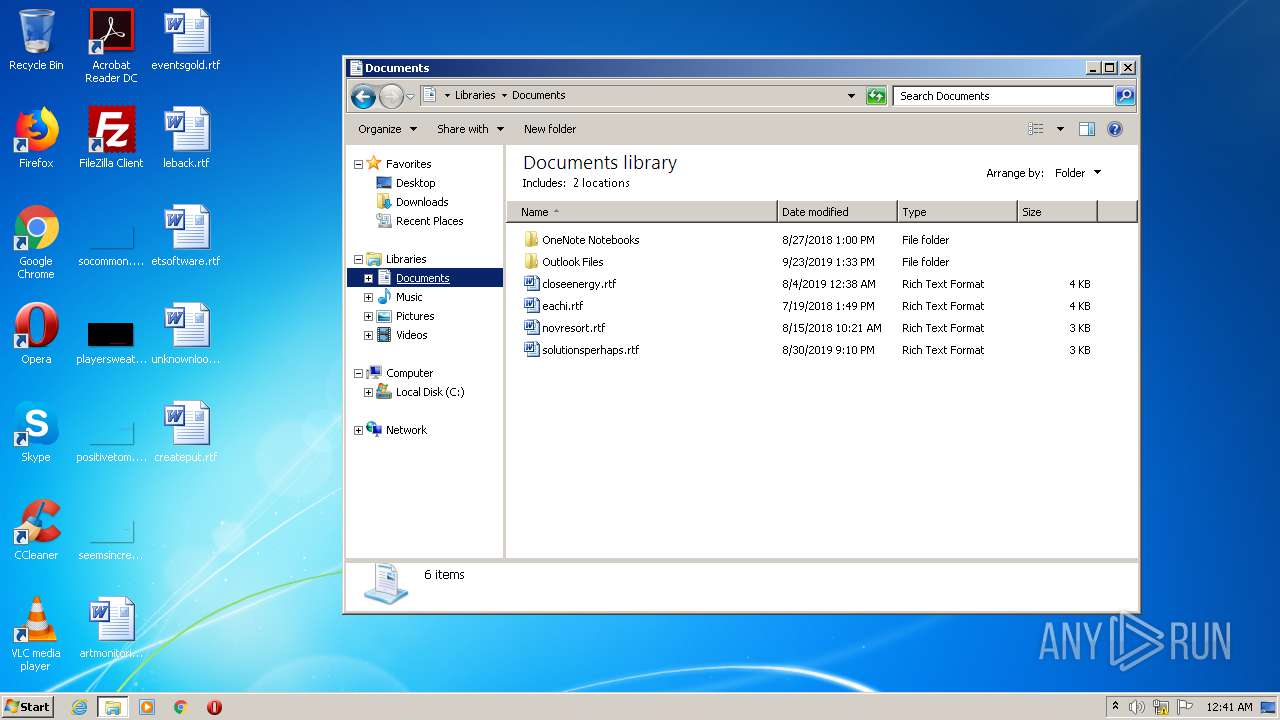
Creates files in the user directory
- WildTangentHelperService.exe (PID: 2888)
Adds / modifies Windows certificates
- WildTangentHelperService.exe (PID: 2080)
Executed as Windows Service
- WildTangentHelperService.exe (PID: 2080)
Removes files from Windows directory
- WildTangentHelperService.exe (PID: 2080)
Creates or modifies windows services
- WildTangentHelperService.exe (PID: 2080)
Creates files in the Windows directory
- WildTangentHelperService.exe (PID: 2080)
Starts SC.EXE for service management
- ns101E.tmp (PID: 1344)
INFO
Reads settings of System Certificates
- WildTangentHelperService.exe (PID: 2080)
Manual execution by user
- explorer.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:08 18:42:56+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 139776 |
| InitializedDataSize: | 40960 |
| UninitializedDataSize: | 4096 |
| EntryPoint: | 0x10012 |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.437 |
| ProductVersionNumber: | 1.0.0.437 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyName: | gamigo, Inc. |
| FileDescription: | WildTangentHelper |
| FileVersion: | 1.0.0.437 |
| LegalCopyright: | gamigo, Inc. All rights reserved. |
| ProductName: | WildTangent Helper |
| ProductVersion: | 1.0.0.437 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Dec-2009 17:42:56 |
| Detected languages: |
|
| CompanyName: | gamigo, Inc. |
| FileDescription: | WildTangentHelper |
| FileVersion: | 1.0.0.437 |
| LegalCopyright: | gamigo, Inc. All rights reserved. |
| ProductName: | WildTangent Helper |
| ProductVersion: | 1.0.0.437 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 08-Dec-2009 17:42:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002219B | 0x00022200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.68406 |
.rdata | 0x00024000 | 0x000073C8 | 0x00007400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.21433 |
.data | 0x0002C000 | 0x0003905C | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.83409 |
.ndata | 0x00066000 | 0x00024000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0008A000 | 0x000007B0 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.68654 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.65542 | 86 | Latin 1 / Western European | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
111 | 2.48825 | 96 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
64
Monitored processes
17
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Users\admin\AppData\Local\Temp\nsfFADA.tmp\nsFAEB.tmp" "C:\Program Files\WildTangent Games\Integration\WildTangentHelperService.exe" /LockService | C:\Users\admin\AppData\Local\Temp\nsfFADA.tmp\nsFAEB.tmp | — | WildTangentHelper-1.0.0.437.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225501 Modules
| |||||||||||||||
| 1344 | "C:\Users\admin\AppData\Local\Temp\nsfFADA.tmp\ns101E.tmp" sc start wildtangenthelper | C:\Users\admin\AppData\Local\Temp\nsfFADA.tmp\ns101E.tmp | — | WildTangentHelper-1.0.0.437.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1056 Modules
| |||||||||||||||
| 1472 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1872 | "C:\Users\admin\AppData\Local\Temp\nsfFADA.tmp\ns260.tmp" "C:\Program Files\WildTangent Games\Integration\WildTangentHelperService.exe" /Service | C:\Users\admin\AppData\Local\Temp\nsfFADA.tmp\ns260.tmp | — | WildTangentHelper-1.0.0.437.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2064 | net stop wildtangenthelper | C:\Windows\system32\net.exe | — | nsFC72.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2080 | "C:\Program Files\WildTangent Games\Integration\WildTangentHelperService.exe" | C:\Program Files\WildTangent Games\Integration\WildTangentHelperService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2496 | "C:\Users\admin\AppData\Local\Temp\WildTangentHelper-1.0.0.437.exe" | C:\Users\admin\AppData\Local\Temp\WildTangentHelper-1.0.0.437.exe | explorer.exe | ||||||||||||
User: admin Company: gamigo, Inc. Integrity Level: HIGH Description: WildTangentHelper Exit code: 0 Version: 1.0.0.437 Modules
| |||||||||||||||
| 2512 | C:\Windows\system32\net1 stop wildtangenthelper | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2680 | "C:\Users\admin\AppData\Local\Temp\WildTangentHelper-1.0.0.437.exe" | C:\Users\admin\AppData\Local\Temp\WildTangentHelper-1.0.0.437.exe | — | explorer.exe | |||||||||||
User: admin Company: gamigo, Inc. Integrity Level: MEDIUM Description: WildTangentHelper Exit code: 3221226540 Version: 1.0.0.437 Modules
| |||||||||||||||
| 2800 | sc start wildtangenthelper | C:\Windows\system32\sc.exe | — | ns101E.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1056 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
477
Read events
413
Write events
64
Delete events
0
Modification events
| (PID) Process: | (2496) WildTangentHelper-1.0.0.437.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A39303AB-4898-4F12-BAA0-0B8630F86DB4} |
| Operation: | write | Name: | EstimatedSize |
Value: 5884 | |||
| (PID) Process: | (2496) WildTangentHelper-1.0.0.437.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A39303AB-4898-4F12-BAA0-0B8630F86DB4} |
| Operation: | write | Name: | Size |
Value: | |||
| (PID) Process: | (2496) WildTangentHelper-1.0.0.437.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A39303AB-4898-4F12-BAA0-0B8630F86DB4} |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.0.437 | |||
| (PID) Process: | (2496) WildTangentHelper-1.0.0.437.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A39303AB-4898-4F12-BAA0-0B8630F86DB4} |
| Operation: | write | Name: | DisplayName |
Value: WildTangent Helper | |||
| (PID) Process: | (2496) WildTangentHelper-1.0.0.437.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A39303AB-4898-4F12-BAA0-0B8630F86DB4} |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\WildTangent Games\Integration\wildgames.ico | |||
| (PID) Process: | (2496) WildTangentHelper-1.0.0.437.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A39303AB-4898-4F12-BAA0-0B8630F86DB4} |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\WildTangent Games\Integration\uninstaller.exe" | |||
| (PID) Process: | (2496) WildTangentHelper-1.0.0.437.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A39303AB-4898-4F12-BAA0-0B8630F86DB4} |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\WildTangent Games\Integration | |||
| (PID) Process: | (2496) WildTangentHelper-1.0.0.437.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A39303AB-4898-4F12-BAA0-0B8630F86DB4} |
| Operation: | write | Name: | Publisher |
Value: WildTangent | |||
| (PID) Process: | (2496) WildTangentHelper-1.0.0.437.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A39303AB-4898-4F12-BAA0-0B8630F86DB4} |
| Operation: | write | Name: | URLInfoAbout |
Value: https://www.wildtangent.com | |||
| (PID) Process: | (2496) WildTangentHelper-1.0.0.437.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A39303AB-4898-4F12-BAA0-0B8630F86DB4} |
| Operation: | write | Name: | HelpLink |
Value: https://support.wildgames.com | |||
Executable files
25
Suspicious files
20
Text files
16
Unknown types
6
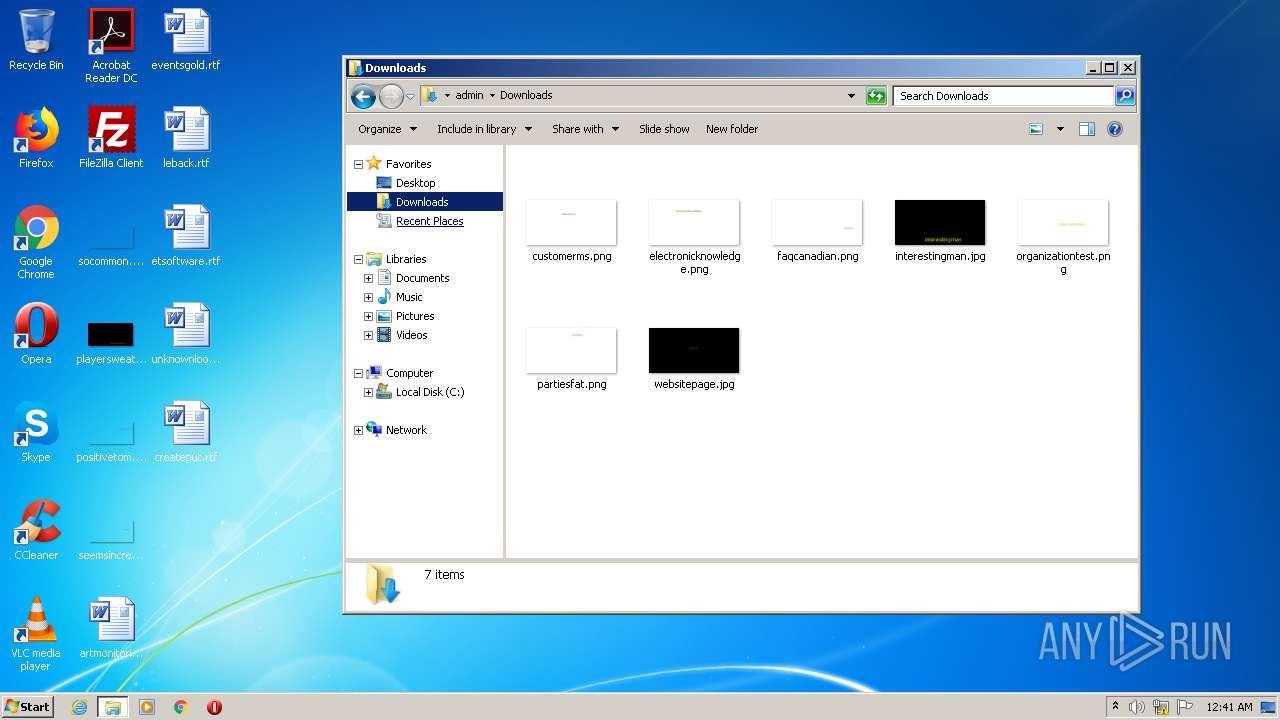
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2496 | WildTangentHelper-1.0.0.437.exe | C:\Users\admin\AppData\Local\Temp\nsfFADA.tmp\nsFAEB.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | WildTangentHelper-1.0.0.437.exe | C:\Users\admin\AppData\Local\Temp\nsfFADA.tmp\nsFC72.tmp | executable | |
MD5:— | SHA256:— | |||
| 2496 | WildTangentHelper-1.0.0.437.exe | C:\Users\admin\AppData\Local\Temp\nsfFADA.tmp\System.dll | executable | |
MD5:86305E201F18D5D8B79737B429AF06E4 | SHA256:67556CCEC8C2A26821FFF9E0C352108B79CD56733A3D3881683C31AE02525D94 | |||
| 2496 | WildTangentHelper-1.0.0.437.exe | C:\Program Files\WildTangent Games\Integration\wildgames.new | image | |
MD5:2E33A2CB68C081968CF1F64A75C8480A | SHA256:B1D8087941E7F08ACFFF34A1935E691CD3335CA30915C5DDD9E273C2F71F9B07 | |||
| 2496 | WildTangentHelper-1.0.0.437.exe | C:\Users\admin\AppData\Local\Temp\nsfFADA.tmp\nsFEA6.tmp | executable | |
MD5:— | SHA256:— | |||
| 2496 | WildTangentHelper-1.0.0.437.exe | C:\Program Files\WildTangent Games\Integration\WildTangentHelperService.new | executable | |
MD5:C58D0CF705BA20AE656AF5FB94EF89AA | SHA256:62C41D440EEB433CAB5EC105B939D3C6BBB3CD81A343057FAC053734F96DCE01 | |||
| 2496 | WildTangentHelper-1.0.0.437.exe | C:\Program Files\WildTangent Games\Integration\ShellHlp.new | executable | |
MD5:354CC7454CB56736F77F43AC1D2C6906 | SHA256:074A218D606416869D69FDE570F08B010E0316D0C5F3B285D21C1F51CE33BA75 | |||
| 2496 | WildTangentHelper-1.0.0.437.exe | C:\Program Files\WildTangent Games\Integration\GameLauncherx64.new | executable | |
MD5:DF27ECFBE5E034E5A323CDC12264FC66 | SHA256:AE52D75E3E8CF9F444B4F08B5B447167AC8B05F4393F65D6A851B0187EDB917D | |||
| 2496 | WildTangentHelper-1.0.0.437.exe | C:\Program Files\WildTangent Games\Integration\GameLauncherDll.new | executable | |
MD5:595F9BC3C91CF2EA4B6B8EB468F04B29 | SHA256:71BE13D9D0B0C215CE4771C4D40E1195D41A36E4BBB598467355E2B9E249C05B | |||
| 2496 | WildTangentHelper-1.0.0.437.exe | C:\Program Files\WildTangent Games\Integration\uninstaller.new | executable | |
MD5:08304FE47722E2E0979109D30D7274DF | SHA256:8930A1CE709BA7B100BE6E649B64DDAC67E1800FFF9D37641200FD2796EECA64 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
9
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2080 | WildTangentHelperService.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.2 Kb | whitelisted |
2080 | WildTangentHelperService.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEAn5ZVd3dPxzbEWiPA%2FCQC8%3D | US | der | 471 b | whitelisted |
2080 | WildTangentHelperService.exe | GET | 200 | 13.32.23.89:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2080 | WildTangentHelperService.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.2 Kb | whitelisted |
2080 | WildTangentHelperService.exe | GET | 200 | 13.32.23.16:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2080 | WildTangentHelperService.exe | GET | 200 | 13.32.23.69:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2080 | WildTangentHelperService.exe | 151.139.241.4:443 | onlinecheck.wildtangent.com | netDNA | US | unknown |
2080 | WildTangentHelperService.exe | 13.32.23.89:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
— | — | 13.32.23.16:80 | o.ss2.us | Amazon.com, Inc. | US | unknown |
2080 | WildTangentHelperService.exe | 13.32.23.69:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
2080 | WildTangentHelperService.exe | 65.9.58.32:443 | clientservices.wildtangent.com | AT&T Services, Inc. | US | suspicious |
2080 | WildTangentHelperService.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
2080 | WildTangentHelperService.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onlinecheck.wildtangent.com |
| suspicious |
www.download.windowsupdate.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
clientservices.wildtangent.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
Threats
Process | Message |
|---|---|
WildTangentHelper-1.0.0.437.exe | WTHelperInstallUninstall :: ---------------------------Start Install--------------------------- |
WildTangentHelper-1.0.0.437.exe | WTHelperInstallUninstall :: Delete obsolete files |
WildTangentHelper-1.0.0.437.exe | WTHelperInstallUninstall :: Delete any .bak files |
WildTangentHelper-1.0.0.437.exe | WTHelperInstallUninstall :: Delete any .new files |
WildTangentHelper-1.0.0.437.exe | WTHelperInstallUninstall :: Place all .new files |
WildTangentHelper-1.0.0.437.exe | WTHelperInstallUninstall :: Stopping WTHelper |
WildTangentHelper-1.0.0.437.exe | WTHelperInstallUninstall :: StopWTHelperWait : Begin |
WildTangentHelper-1.0.0.437.exe | WTHelperInstallUninstall :: StopWTHelperWait : End |
WildTangentHelper-1.0.0.437.exe | WTHelperInstallUninstall :: RetryRenameFiles() : Returning true - complete w/o errors |
WildTangentHelper-1.0.0.437.exe | WTHelperInstallUninstall :: File operations completed successfully |