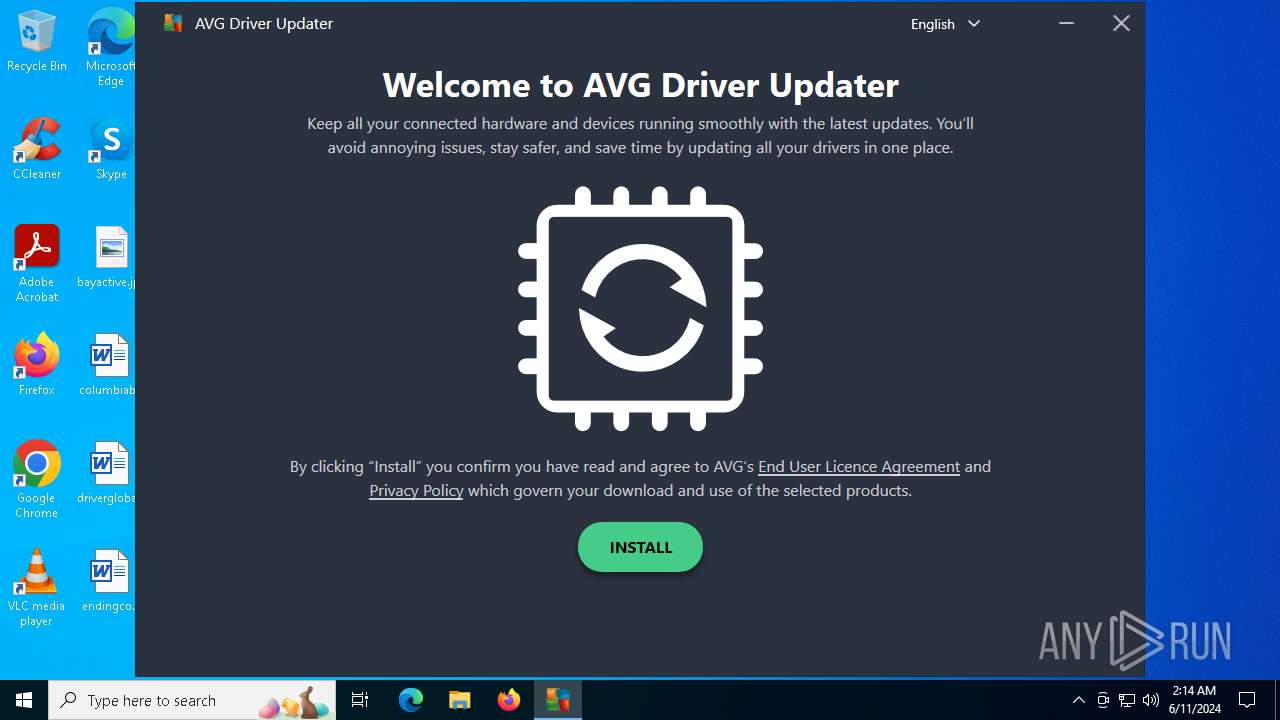
| File name: | avg_driver_updater_online_setup.exe |
| Full analysis: | https://app.any.run/tasks/1661fe91-6ce6-4d04-b78a-d63bf94b016b |
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2024, 02:12:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DAD379E3CB00D226A20BB6A5186A063D |
| SHA1: | D7DA6B05DD4B6DAFF2DAD5FAC9CA04675B7E5B15 |
| SHA256: | 0D4DE118B121000855EDD4F25C76D6D0ABECDF7175213FE0C46AED467B169CA4 |
| SSDEEP: | 49152:xVmo2pOxcEHYHZB5LlXW34Vvz+lATrY82GMpgX2DISkzNyM:xVmleHYHZB5LlXW34R4ATrY8xCIS |
MALICIOUS
Drops the executable file immediately after the start
- avg_driver_updater_online_setup.exe (PID: 4500)
- icarus.exe (PID: 4428)
- icarus.exe (PID: 5396)
Creates a writable file in the system directory
- icarus.exe (PID: 5396)
SUSPICIOUS
Executable content was dropped or overwritten
- avg_driver_updater_online_setup.exe (PID: 4500)
- icarus.exe (PID: 4428)
- icarus.exe (PID: 5396)
Starts itself from another location
- icarus.exe (PID: 4428)
The process creates files with name similar to system file names
- icarus.exe (PID: 5396)
Process drops legitimate windows executable
- icarus.exe (PID: 5396)
The process drops C-runtime libraries
- icarus.exe (PID: 5396)
The process verifies whether the antivirus software is installed
- icarus.exe (PID: 5396)
INFO
Reads the machine GUID from the registry
- avg_driver_updater_online_setup.exe (PID: 4500)
- icarus.exe (PID: 4428)
- icarus.exe (PID: 5396)
- icarus_ui.exe (PID: 1204)
Checks supported languages
- avg_driver_updater_online_setup.exe (PID: 4500)
- icarus.exe (PID: 4428)
- icarus.exe (PID: 5396)
- icarus_ui.exe (PID: 1204)
Reads the computer name
- icarus_ui.exe (PID: 1204)
- avg_driver_updater_online_setup.exe (PID: 4500)
- icarus.exe (PID: 4428)
- icarus.exe (PID: 5396)
Checks proxy server information
- avg_driver_updater_online_setup.exe (PID: 4500)
Reads the software policy settings
- avg_driver_updater_online_setup.exe (PID: 4500)
Create files in a temporary directory
- avg_driver_updater_online_setup.exe (PID: 4500)
- icarus.exe (PID: 5396)
- icarus.exe (PID: 4428)
Creates files in the program directory
- avg_driver_updater_online_setup.exe (PID: 4500)
- icarus.exe (PID: 4428)
- icarus.exe (PID: 5396)
- icarus_ui.exe (PID: 1204)
Reads CPU info
- icarus.exe (PID: 5396)
- icarus.exe (PID: 4428)
- icarus_ui.exe (PID: 1204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:04:12 10:34:12+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.38 |
| CodeSize: | 1038848 |
| InitializedDataSize: | 513536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x54180 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 24.4.7245.0 |
| ProductVersionNumber: | 24.1.5025.12498 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | AVG Technologies |
| FileDescription: | AVG Self-Extract Package |
| FileVersion: | 24.4.7245.0 |
| InternalName: | icarus_sfx |
| LegalCopyright: | Copyright © 2024 AVG Technologies |
| MainProductId: | avg-du |
| OriginalFileName: | icarus_sfx.exe |
| ProductId: | avg-icarus |
| ProductName: | AVG Installer |
| ProductVersion: | 24.1.5025.12498 |
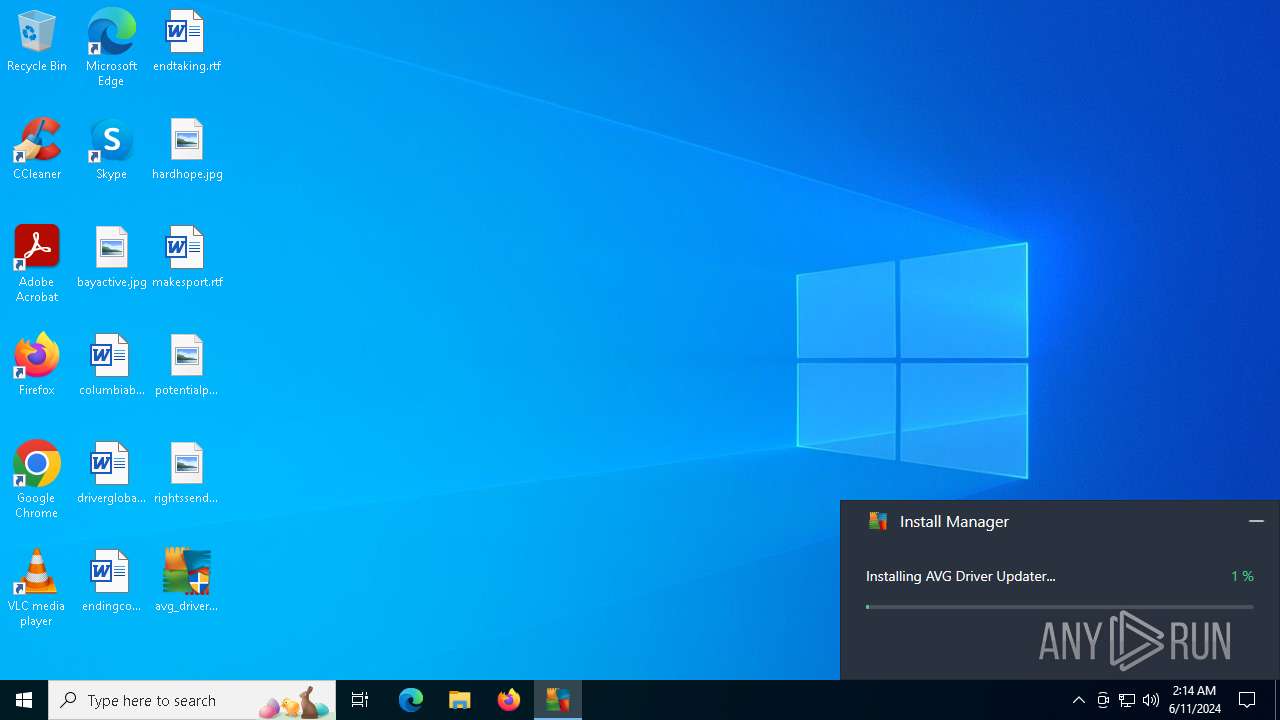
Total processes
121
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 788 | "C:\Users\admin\Desktop\avg_driver_updater_online_setup.exe" | C:\Users\admin\Desktop\avg_driver_updater_online_setup.exe | — | explorer.exe | |||||||||||
User: admin Company: AVG Technologies Integrity Level: MEDIUM Description: AVG Self-Extract Package Exit code: 3221226540 Version: 24.4.7245.0 Modules
| |||||||||||||||
| 1204 | C:\WINDOWS\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\common\icarus_ui.exe /sssid:4500 /er_master:master_ep_9ac36830-dff5-4cfd-9b5d-6c46997a0619 /er_ui:ui_ep_d5f051ec-b071-4228-80cf-a410870bf05f | C:\Windows\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\common\icarus_ui.exe | — | icarus.exe | |||||||||||
User: admin Company: AVG Technologies Integrity Level: HIGH Description: AVG UI Version: 24.4.7245.0 Modules
| |||||||||||||||
| 4428 | C:\WINDOWS\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\common\icarus.exe /icarus-info-path:C:\WINDOWS\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\icarus-info.xml /install /sssid:4500 | C:\Windows\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\common\icarus.exe | avg_driver_updater_online_setup.exe | ||||||||||||
User: admin Company: AVG Technologies Integrity Level: HIGH Description: AVG Installer Version: 24.4.7245.0 Modules
| |||||||||||||||
| 4500 | "C:\Users\admin\Desktop\avg_driver_updater_online_setup.exe" | C:\Users\admin\Desktop\avg_driver_updater_online_setup.exe | explorer.exe | ||||||||||||
User: admin Company: AVG Technologies Integrity Level: HIGH Description: AVG Self-Extract Package Version: 24.4.7245.0 Modules
| |||||||||||||||
| 5396 | C:\WINDOWS\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\avg-du\icarus.exe /sssid:4500 /er_master:master_ep_9ac36830-dff5-4cfd-9b5d-6c46997a0619 /er_ui:ui_ep_d5f051ec-b071-4228-80cf-a410870bf05f /er_slave:avg-du_slave_ep_87dece3a-069d-4548-ae01-71137aeaa2db /slave:avg-du | C:\Windows\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\avg-du\icarus.exe | icarus.exe | ||||||||||||
User: admin Company: AVG Technologies Integrity Level: HIGH Description: AVG Installer Version: 24.4.7245.0 Modules
| |||||||||||||||
Total events
5 282
Read events
5 257
Write events
24
Delete events
1
Modification events
| (PID) Process: | (4500) avg_driver_updater_online_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\1D0EC6DE-4A80-4CC3-A335-E6E41C951198 |
| Operation: | write | Name: | 5FD38555-4B16-40AE-9A09-E2C969CB74AF |
Value: F6D4F52220BB5A3D7246A004278BB23F | |||
| (PID) Process: | (4500) avg_driver_updater_online_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\C06AEB9D-8774-46E7-8160-8321BCD14D9F |
| Operation: | write | Name: | 7CCD586D-2ABC-42FF-A23B-3731F4F183D9 |
Value: F6D4F52220BB5A3D7246A004278BB23F | |||
| (PID) Process: | (4500) avg_driver_updater_online_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\1D0EC6DE-4A80-4CC3-A335-E6E41C951198 |
| Operation: | write | Name: | 8C5CFDF4-AB05-4EB0-8EF6-7B4620DC2CF3 |
Value: AQAAANCMnd8BFdERjHoAwE/Cl+sBAAAApq+o0yPoKEeNuCKYuJ0fdAQAAAACAAAAAAAQZgAAAAEAACAAAADTMQyQlgrEszteUUzAi88k1nKEDeCYSyg5ac6H7VT1VQAAAAAOgAAAAAIAACAAAAB41w1ofSXfQlO4D3dTg/qCMOSsQMPZb/CEJOug8YIw0VAAAAAC+b8iz+JeMJp4zFquvAUyn9IigqWPLRyRft+UaRo2uW3ER7QJKn0gKWnLOlTPkkYVesHaf2DvNR3Fu4cgYO4pJQTJBPEVjZWmaaLUu/q2H0AAAADDxu0gQPHxSrwboaQoVszOgc9KZNVmr2Tv4JeiKQff6IE3nJG9kFE1xe7wSCWAJY32nYkuhGT6oUnJaDkjIFg+ | |||
| (PID) Process: | (4500) avg_driver_updater_online_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\C06AEB9D-8774-46E7-8160-8321BCD14D9F |
| Operation: | write | Name: | 5E1D6A55-0134-486E-A166-38C2E4919BB1 |
Value: AQAAANCMnd8BFdERjHoAwE/Cl+sBAAAApq+o0yPoKEeNuCKYuJ0fdAQAAAACAAAAAAAQZgAAAAEAACAAAADTMQyQlgrEszteUUzAi88k1nKEDeCYSyg5ac6H7VT1VQAAAAAOgAAAAAIAACAAAAB41w1ofSXfQlO4D3dTg/qCMOSsQMPZb/CEJOug8YIw0VAAAAAC+b8iz+JeMJp4zFquvAUyn9IigqWPLRyRft+UaRo2uW3ER7QJKn0gKWnLOlTPkkYVesHaf2DvNR3Fu4cgYO4pJQTJBPEVjZWmaaLUu/q2H0AAAADDxu0gQPHxSrwboaQoVszOgc9KZNVmr2Tv4JeiKQff6IE3nJG9kFE1xe7wSCWAJY32nYkuhGT6oUnJaDkjIFg+ | |||
| (PID) Process: | (4500) avg_driver_updater_online_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\1D0EC6DE-4A80-4CC3-A335-E6E41C951198 |
| Operation: | write | Name: | 144807F0-DE37-4C62-9C05-EB4CC64A7A2F |
Value: 7a8e8f11-d192-491f-9a6d-630686551697 | |||
| (PID) Process: | (4500) avg_driver_updater_online_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\C06AEB9D-8774-46E7-8160-8321BCD14D9F |
| Operation: | write | Name: | 56C7A9DA-4B11-406A-8B1A-EFF157C294D6 |
Value: 7a8e8f11-d192-491f-9a6d-630686551697 | |||
| (PID) Process: | (4428) icarus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\1D0EC6DE-4A80-4CC3-A335-E6E41C951198 |
| Operation: | write | Name: | 144807F0-DE37-4C62-9C05-EB4CC64A7A2F |
Value: 7a8e8f11-d192-491f-9a6d-630686551697 | |||
| (PID) Process: | (4428) icarus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\C06AEB9D-8774-46E7-8160-8321BCD14D9F |
| Operation: | write | Name: | 56C7A9DA-4B11-406A-8B1A-EFF157C294D6 |
Value: 7a8e8f11-d192-491f-9a6d-630686551697 | |||
| (PID) Process: | (4428) icarus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\1D0EC6DE-4A80-4CC3-A335-E6E41C951198 |
| Operation: | write | Name: | 5FD38555-4B16-40AE-9A09-E2C969CB74AF |
Value: F6D4F52220BB5A3D7246A004278BB23F | |||
| (PID) Process: | (4428) icarus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\C06AEB9D-8774-46E7-8160-8321BCD14D9F |
| Operation: | write | Name: | 7CCD586D-2ABC-42FF-A23B-3731F4F183D9 |
Value: F6D4F52220BB5A3D7246A004278BB23F | |||
Executable files
64
Suspicious files
70
Text files
17
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4500 | avg_driver_updater_online_setup.exe | C:\ProgramData\AVG\Icarus\Logs\sfx.log | text | |
MD5:ECAA88F7FA0BF610A5A26CF545DCD3AA | SHA256:F1945CD6C19E56B3C1C78943EF5EC18116907A4CA1EFC40A57D48AB1DB7ADFC5 | |||
| 4500 | avg_driver_updater_online_setup.exe | C:\WINDOWS\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\common\product-info.xml | xml | |
MD5:F3DBA4960B27996F6C252C86F4ED3AAA | SHA256:E6CB33B6976BCADFB145D3A1AB02BA6CF8FBF3CCA1CF0F4072F9347404094591 | |||
| 4500 | avg_driver_updater_online_setup.exe | C:\Users\admin\AppData\Local\Temp\F07D8C6A-04B6-4025-869C-70A788D7B5C0 | binary | |
MD5:87654923BABD72DF43F88B2635199EC1 | SHA256:4CDC640E375572A8B3C5C06EC693426E427114A047B05243B0CB09B40787FDF7 | |||
| 4500 | avg_driver_updater_online_setup.exe | C:\WINDOWS\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\common\icarus.exe | executable | |
MD5:97856AB19BE2842F985C899CCDE7E312 | SHA256:2569A72D3A55EA7AD690D708907245C221664C5C88CADBC19E1967135FA40514 | |||
| 4500 | avg_driver_updater_online_setup.exe | C:\WINDOWS\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\common\icarus_ui.exe | executable | |
MD5:7EBAE16A6EA514E55F7160C3539261CC | SHA256:F27F92F003505DBCA839513D233198211860DE0EF487973A5CE0761D8E8EBFB9 | |||
| 4428 | icarus.exe | C:\ProgramData\AVG\Icarus\Logs\report.log | — | |
MD5:— | SHA256:— | |||
| 4500 | avg_driver_updater_online_setup.exe | C:\WINDOWS\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\common\dump_process.exe | executable | |
MD5:C22D80D43019235520344972EFEC9FF2 | SHA256:5841A3DF4784E008B8F2C567F15BB28CDB4CB4CA35C750F1108DFB1CCB6011F0 | |||
| 4500 | avg_driver_updater_online_setup.exe | C:\WINDOWS\Temp\asw-0439a3fb-8849-45aa-88b2-96228c6e3108\common\3e1187d9-38e9-45f8-9cac-e0d66135627e | binary | |
MD5:B1DA394894B0EBFA0AE7401846E7045B | SHA256:8E3029BB9D4E329D3B4D2FBED8B5B3C4056EB979A5855BB793157DFA3DDA89F5 | |||
| 4500 | avg_driver_updater_online_setup.exe | C:\Users\admin\AppData\Local\Temp\D566D7D7-DCD6-471C-8109-BE0AD33199E3 | binary | |
MD5:51CACEA0FBAE8346C20FB94EFEEF8809 | SHA256:5749457FC3E5EE160FE41B6BC0743A890B38FD3F09965828BD19FE269E5BD434 | |||
| 4500 | avg_driver_updater_online_setup.exe | C:\Users\admin\AppData\Local\Temp\6358C710-B89F-46B9-93F2-F6CAC44F5286 | binary | |
MD5:DC7957F0E32968C1E88F95283B3AA970 | SHA256:200B196B3E24086068437C3E4F49CD6FEC4CFB26CB6E0E52A53735B6FABC76B4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
140
TCP/UDP connections
34
DNS requests
21
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5140 | MoUsoCoreWorker.exe | GET | 200 | 95.101.54.128:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
— | — | GET | 200 | 2.22.41.10:443 | https://honzik.avcdn.net/universe/73ee/5495/78de/73ee549578ded906711189edcef0eedbc9db7ccbd30cf7776bd1f7dd9e034339.lzma | unknown | — | 25.4 Kb | unknown |
— | — | POST | 200 | 34.117.223.223:443 | https://analytics.avcdn.net/v4/receive/json/25 | unknown | — | 19 b | unknown |
— | — | GET | 200 | 2.22.41.10:443 | https://honzik.avcdn.net/defs/avg-du/release.xml.lzma | unknown | compressed | 1.91 Kb | unknown |
— | — | GET | 200 | 2.22.41.10:443 | https://honzik.avcdn.net/defs/avg-du/release.xml.lzma | unknown | compressed | 1.91 Kb | unknown |
— | — | POST | 200 | 34.117.223.223:443 | https://analytics.avcdn.net/v4/receive/json/25 | unknown | — | — | unknown |
— | — | POST | — | 34.117.223.223:443 | https://analytics.avcdn.net/v4/receive/json/25 | unknown | — | — | unknown |
— | — | GET | 200 | 2.22.41.10:443 | https://honzik.avcdn.net/universe/0e18/6570/2916/0e1865702916ae47aafc54c6199e3a73acb735ae888f9a8dd7bc4656268ef9ea.lzma | unknown | compressed | 1.40 Mb | unknown |
— | — | POST | 200 | 34.117.223.223:443 | https://analytics.avcdn.net/v4/receive/json/25 | unknown | binary | 19 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5548 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5036 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5140 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5140 | MoUsoCoreWorker.exe | 95.101.54.128:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4500 | avg_driver_updater_online_setup.exe | 34.117.223.223:443 | analytics.avcdn.net | GOOGLE-CLOUD-PLATFORM | US | unknown |
4500 | avg_driver_updater_online_setup.exe | 23.212.89.10:443 | honzik.avcdn.net | AKAMAI-AS | MX | unknown |
5548 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
analytics.avcdn.net |
| unknown |
crl.microsoft.com |
| whitelisted |
honzik.avcdn.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
shepherd.avcdn.net |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET HUNTING Suspicious POST With Reference to WINDOWS Folder Possible Malware Infection |
— | — | A Network Trojan was detected | ET HUNTING Suspicious POST With Reference to WINDOWS Folder Possible Malware Infection |
— | — | A Network Trojan was detected | ET HUNTING Suspicious POST With Reference to WINDOWS Folder Possible Malware Infection |
— | — | A Network Trojan was detected | ET HUNTING Suspicious POST With Reference to WINDOWS Folder Possible Malware Infection |
— | — | A Network Trojan was detected | ET HUNTING Suspicious POST With Reference to WINDOWS Folder Possible Malware Infection |
— | — | A Network Trojan was detected | ET HUNTING Suspicious POST With Reference to WINDOWS Folder Possible Malware Infection |
— | — | A Network Trojan was detected | ET HUNTING Suspicious POST With Reference to WINDOWS Folder Possible Malware Infection |
— | — | A Network Trojan was detected | ET HUNTING Suspicious POST With Reference to WINDOWS Folder Possible Malware Infection |
— | — | A Network Trojan was detected | ET HUNTING Suspicious POST With Reference to WINDOWS Folder Possible Malware Infection |
— | — | A Network Trojan was detected | ET HUNTING Suspicious POST With Reference to WINDOWS Folder Possible Malware Infection |
Process | Message |
|---|---|
avg_driver_updater_online_setup.exe | [2024-06-11 02:13:02.080] [error ] [isfx ] [ 4500: 3688] [A976E7: 115] GET fail err:12002, msg:'Unable to receive response', retries:'1', downloaded:'0'
|
avg_driver_updater_online_setup.exe | [2024-06-11 02:13:34.095] [error ] [isfx ] [ 4500: 3688] [A976E7: 115] GET fail err:12002, msg:'Unable to receive response', retries:'1', downloaded:'0'
|