| download: | f7a61bdebdc89925b10ab3681e6d9e46.jpg |
| Full analysis: | https://app.any.run/tasks/6890c2ba-835d-451f-bf65-bb9792ccad92 |
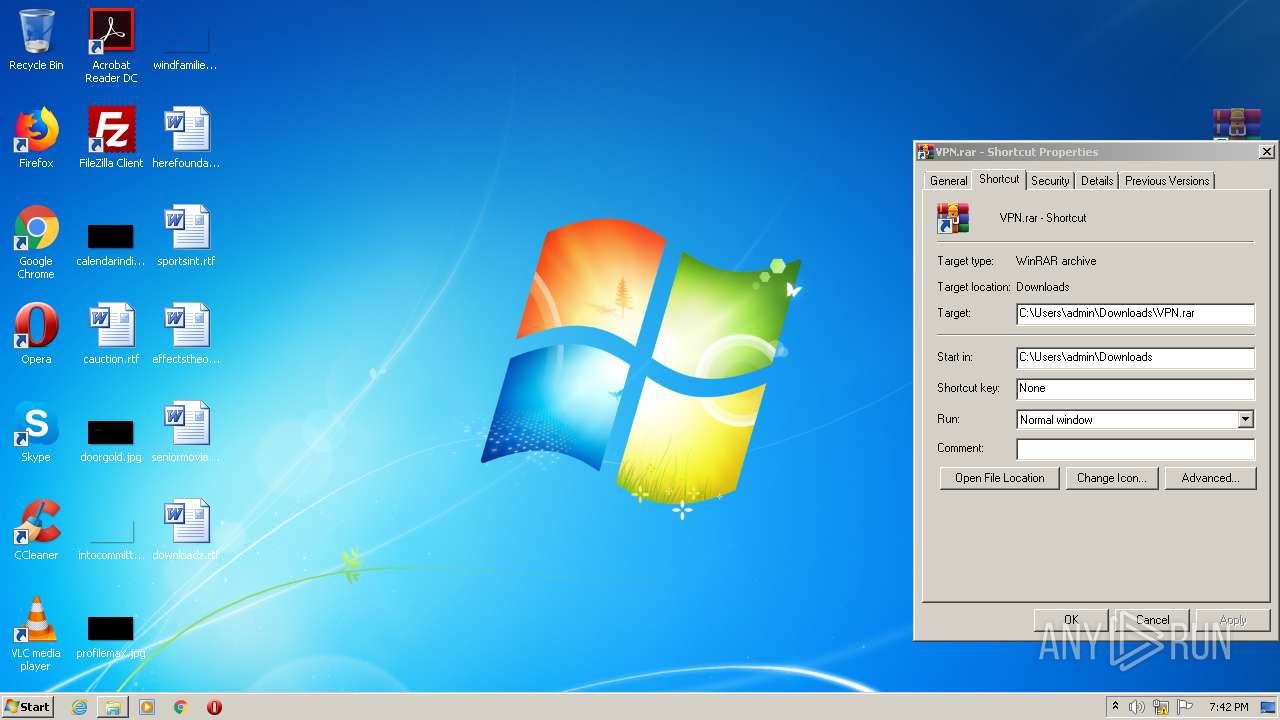
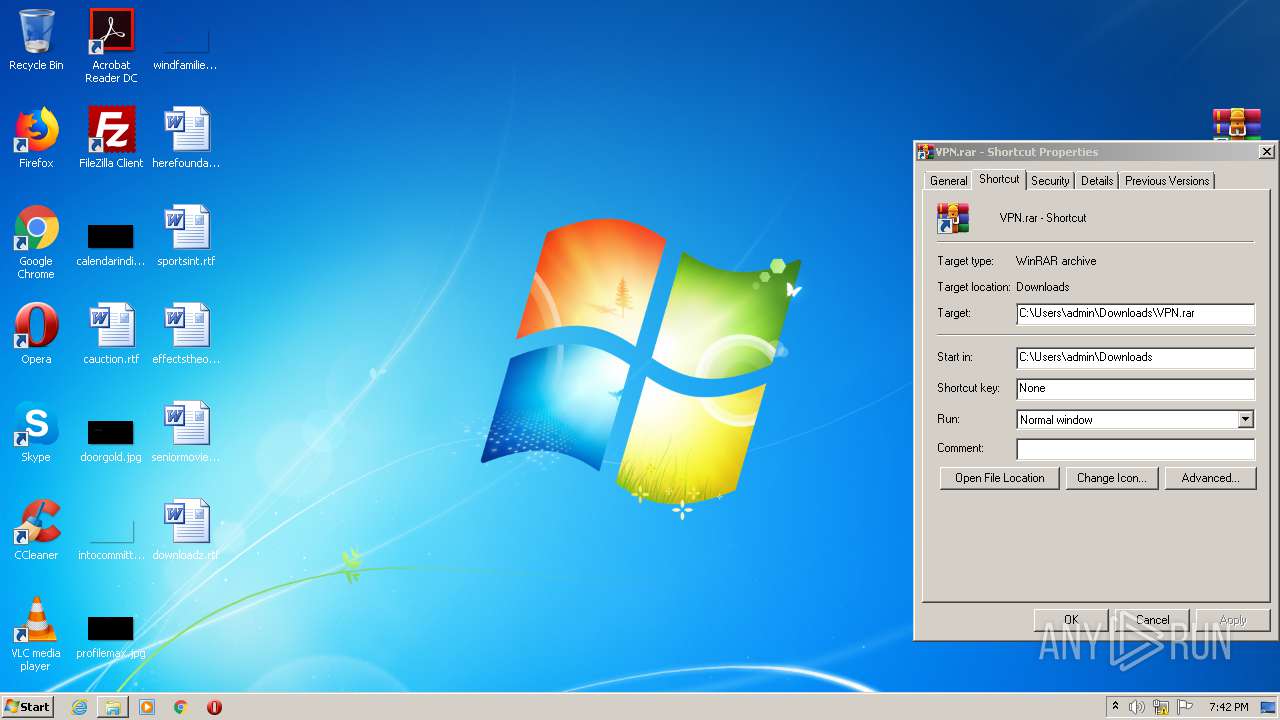
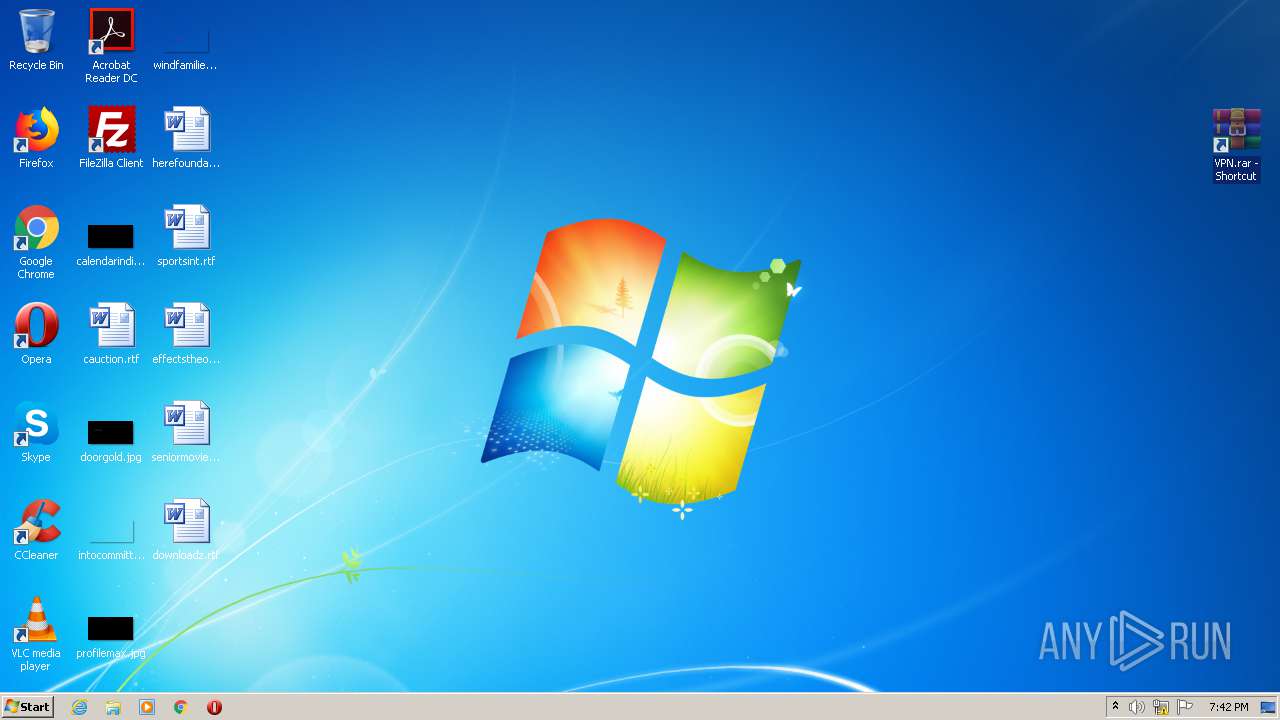
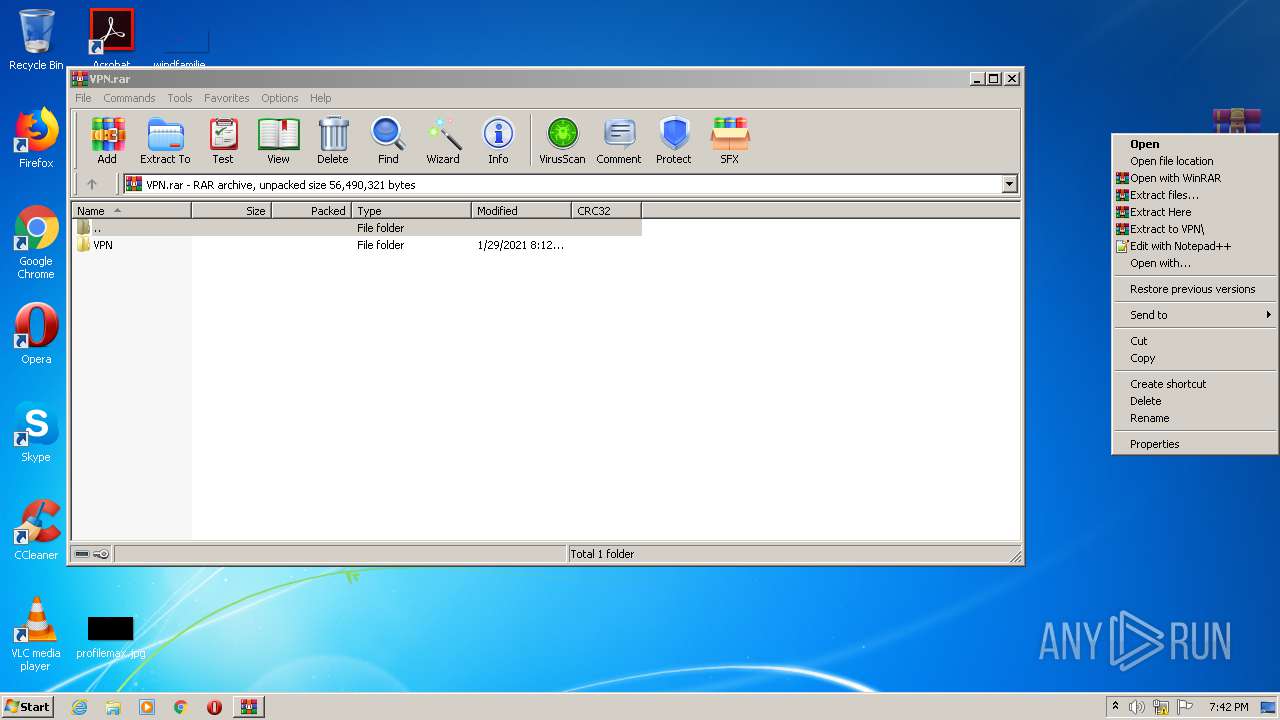
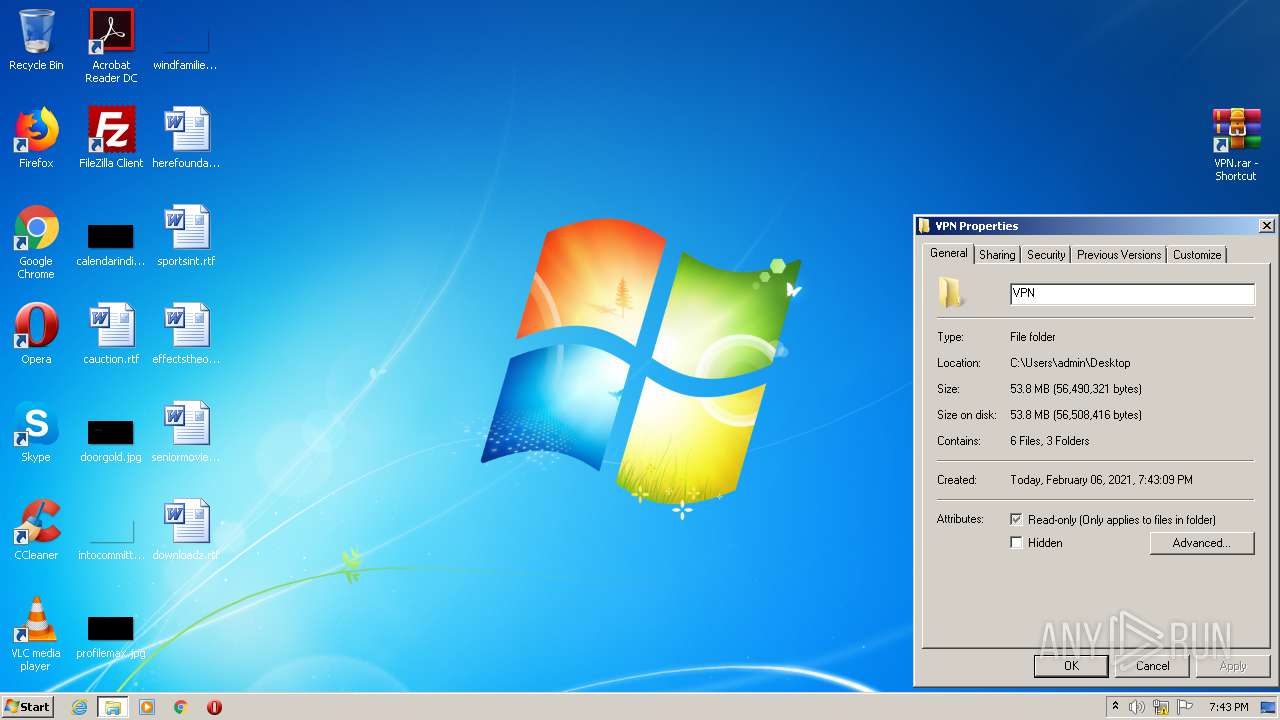
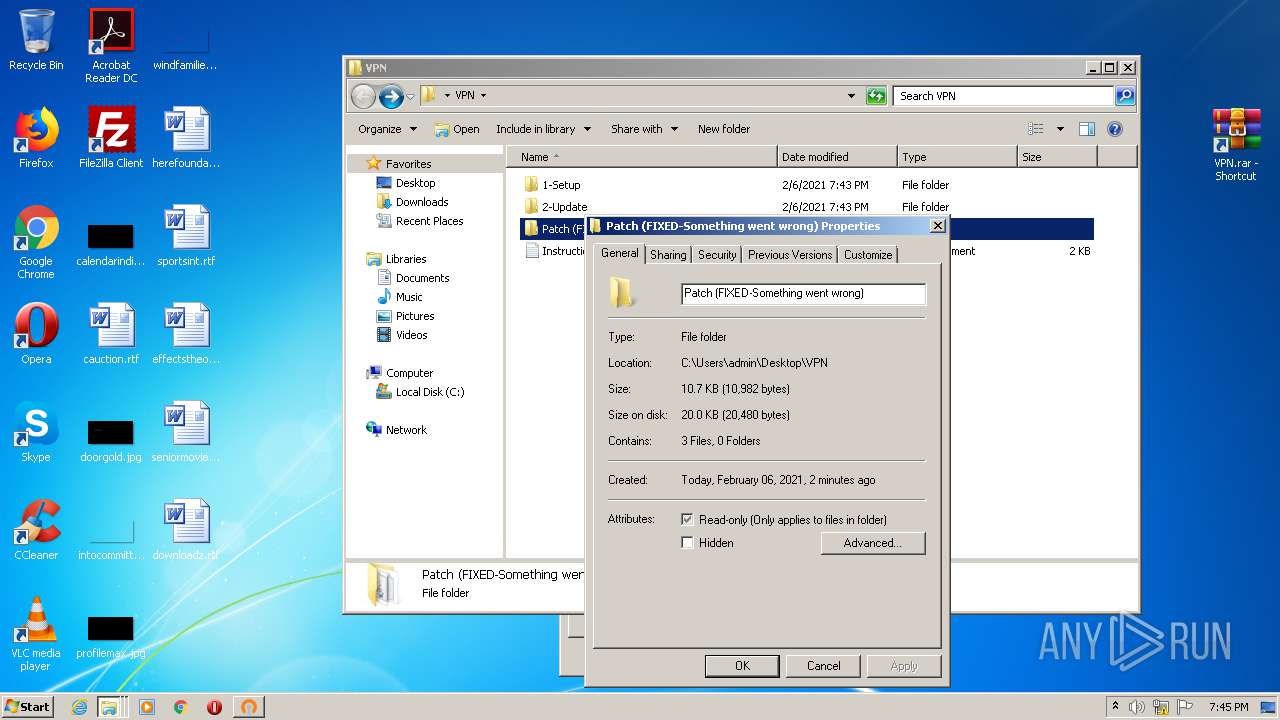
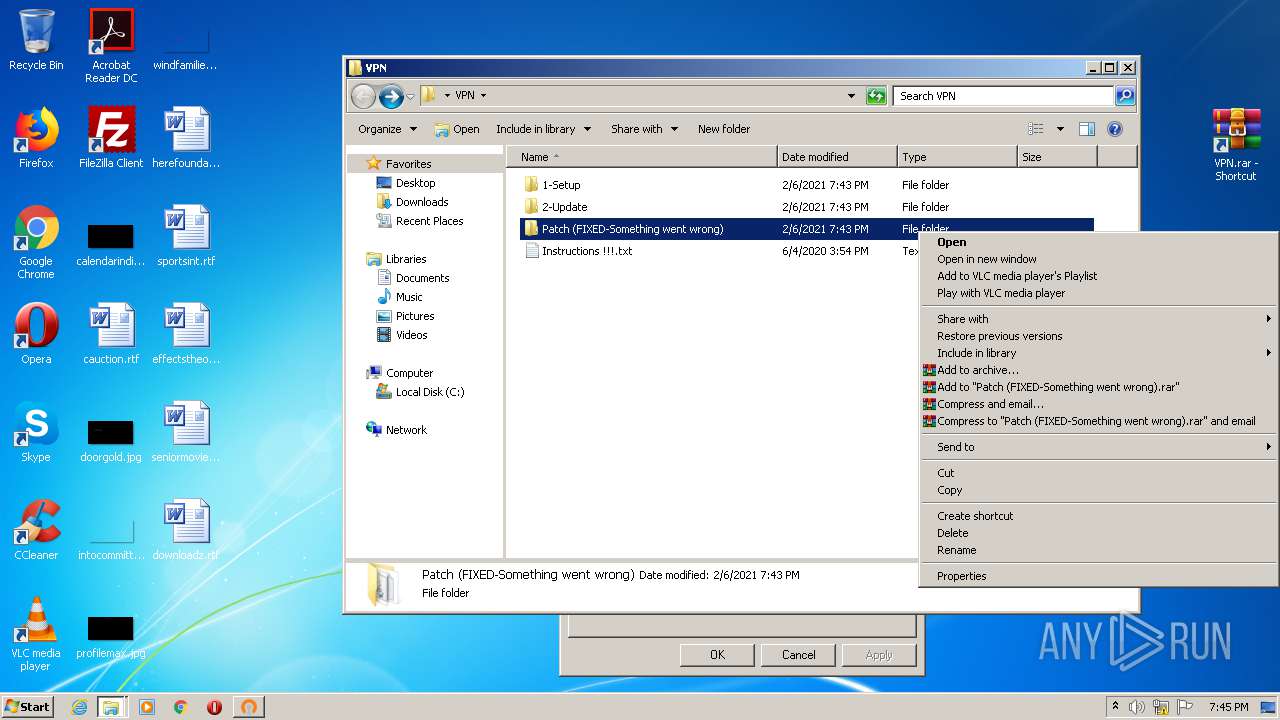
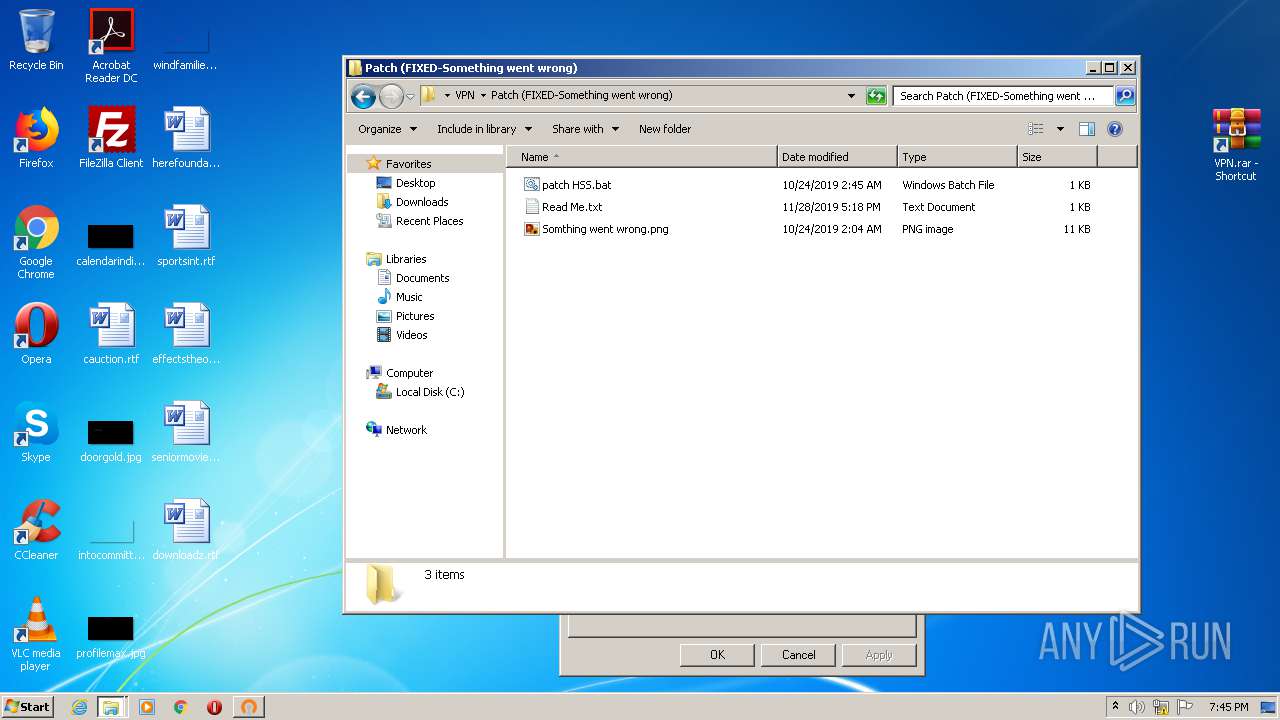
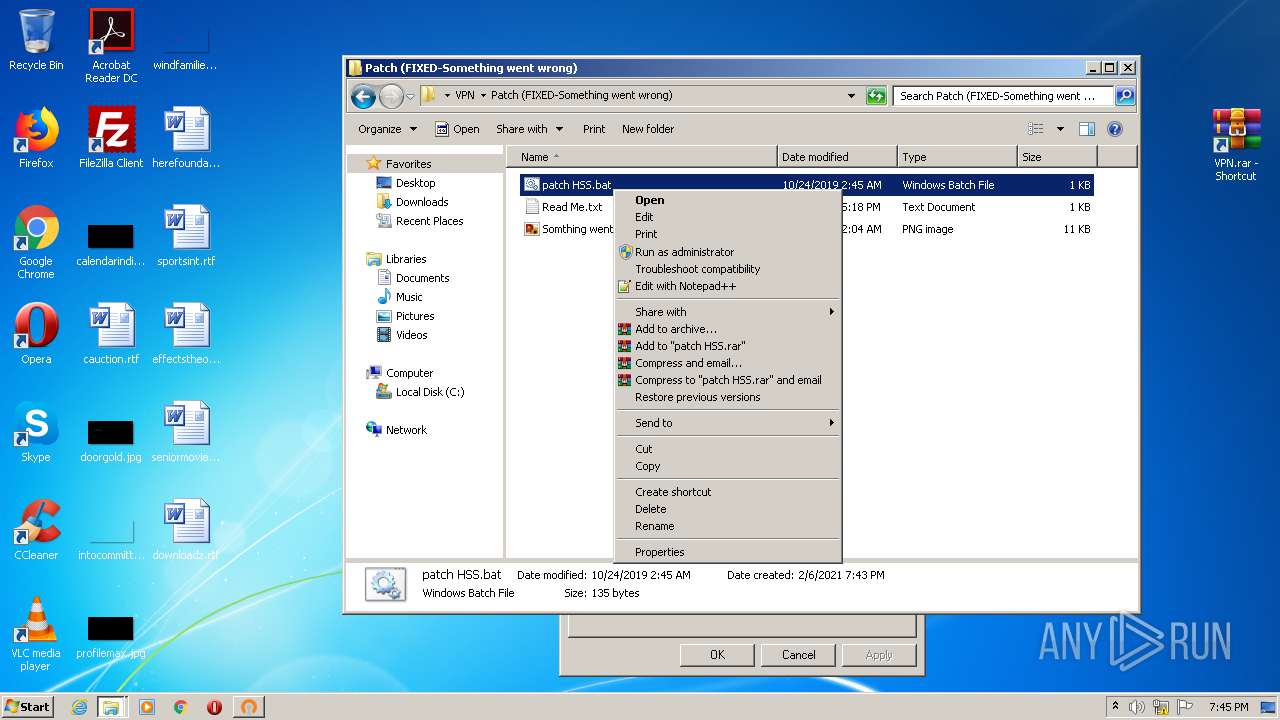
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2021, 19:41:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | image/jpeg |
| File info: | JPEG image data, Exif standard: [TIFF image data, big-endian, direntries=0], progressive, precision 8, 564x564, frames 3 |
| MD5: | 210215974BB38BD710188B241776D6C7 |
| SHA1: | 74E80BE894114DD9D97CAF93EAD63CCEE8E7C88C |
| SHA256: | 0D4AAA0EEE4EEEFF7D7039C41F45D97302D7F154A8B8C76DD10C7D0AD1400217 |
| SSDEEP: | 768:ClgPJTYwwhVJAFCNEvGnw8WoxTmOYIdVUplIRAxpe6QTZS/QGTnJ:C8Jk1VJAeEvGnvfMOYIdVULxDQk/jTJ |
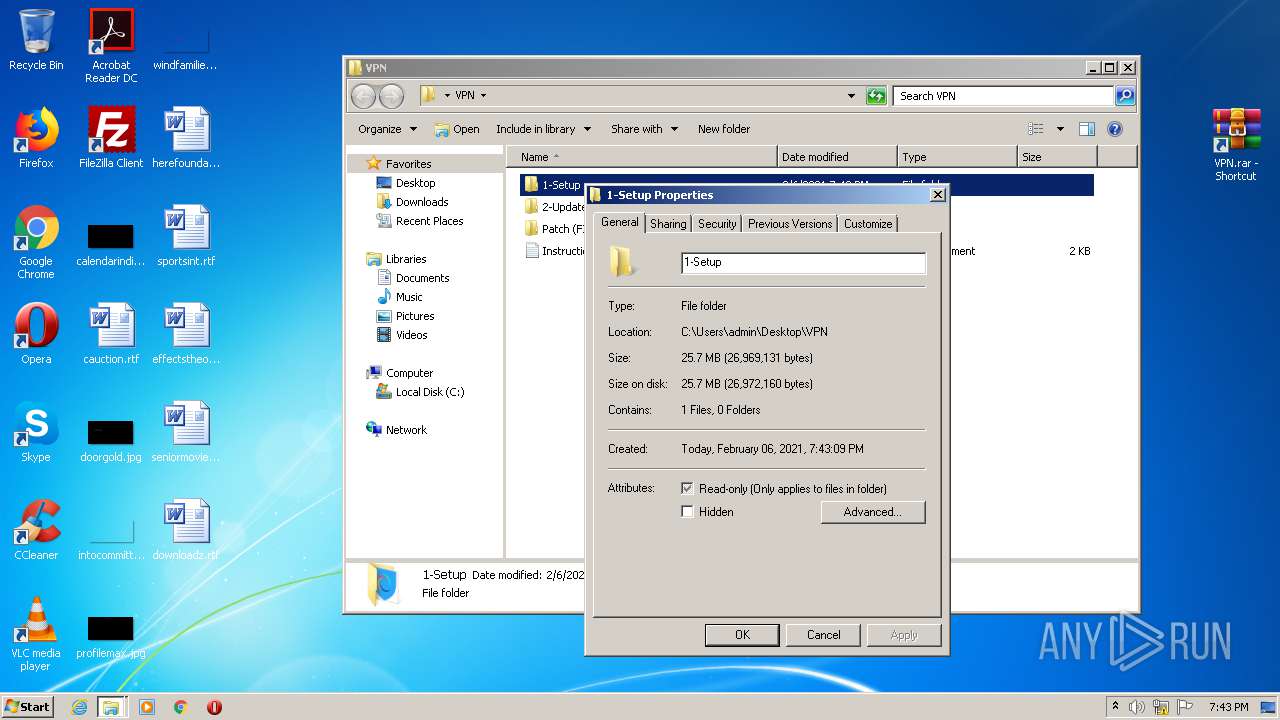
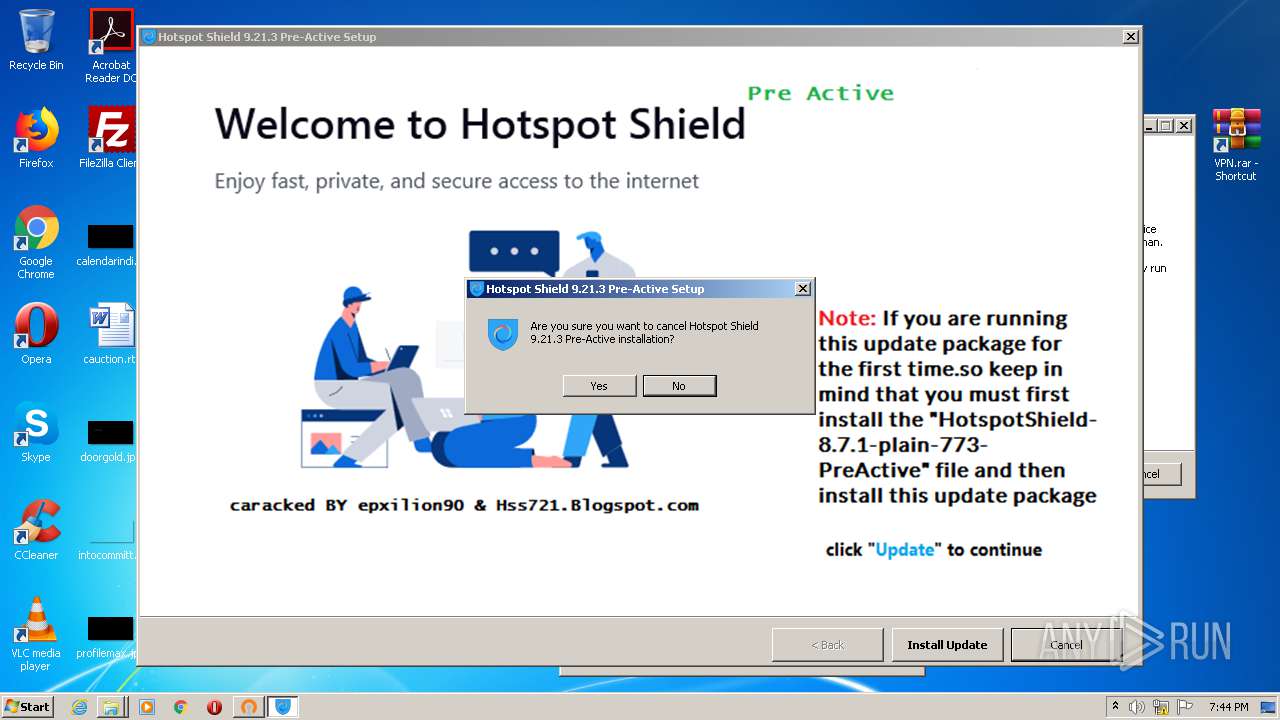
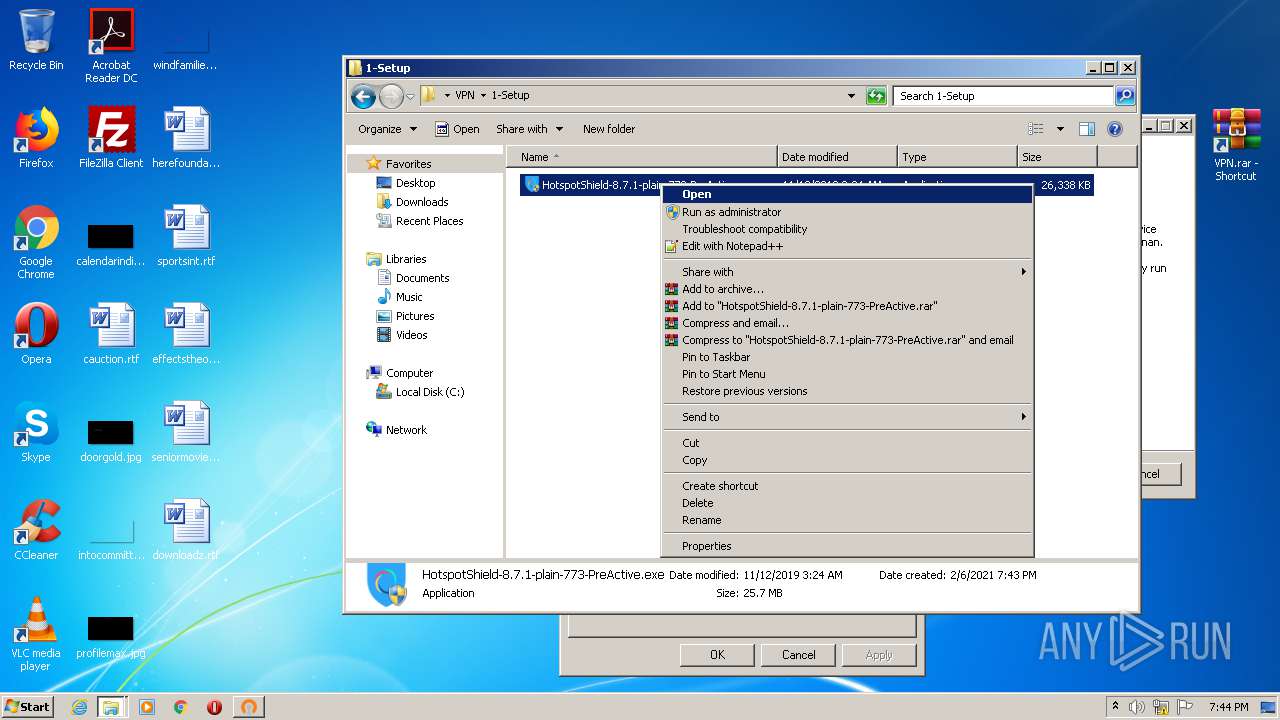
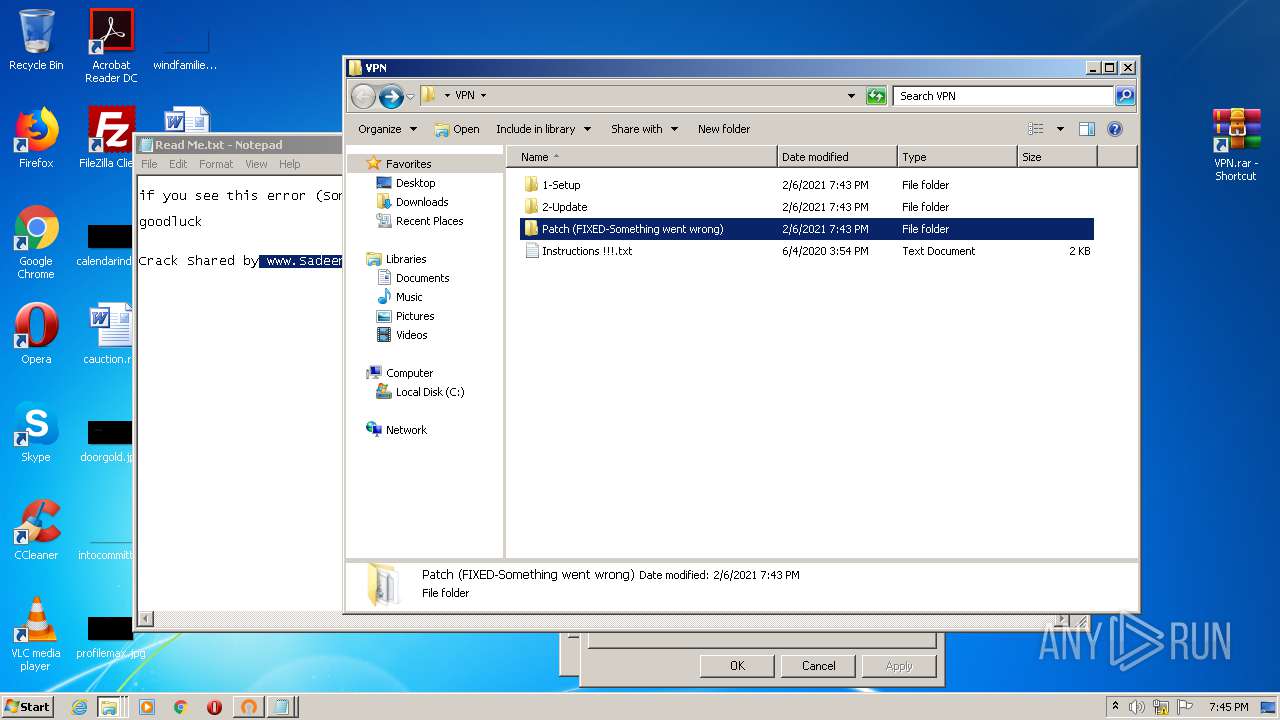
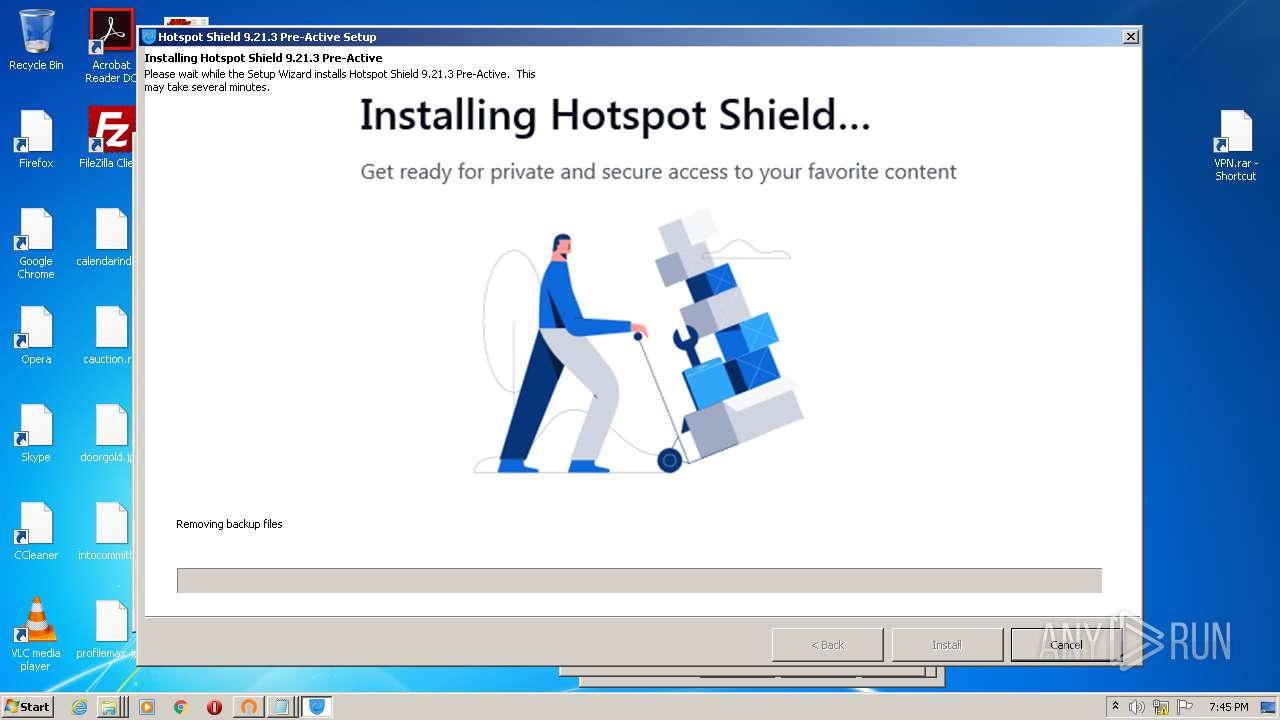
MALICIOUS
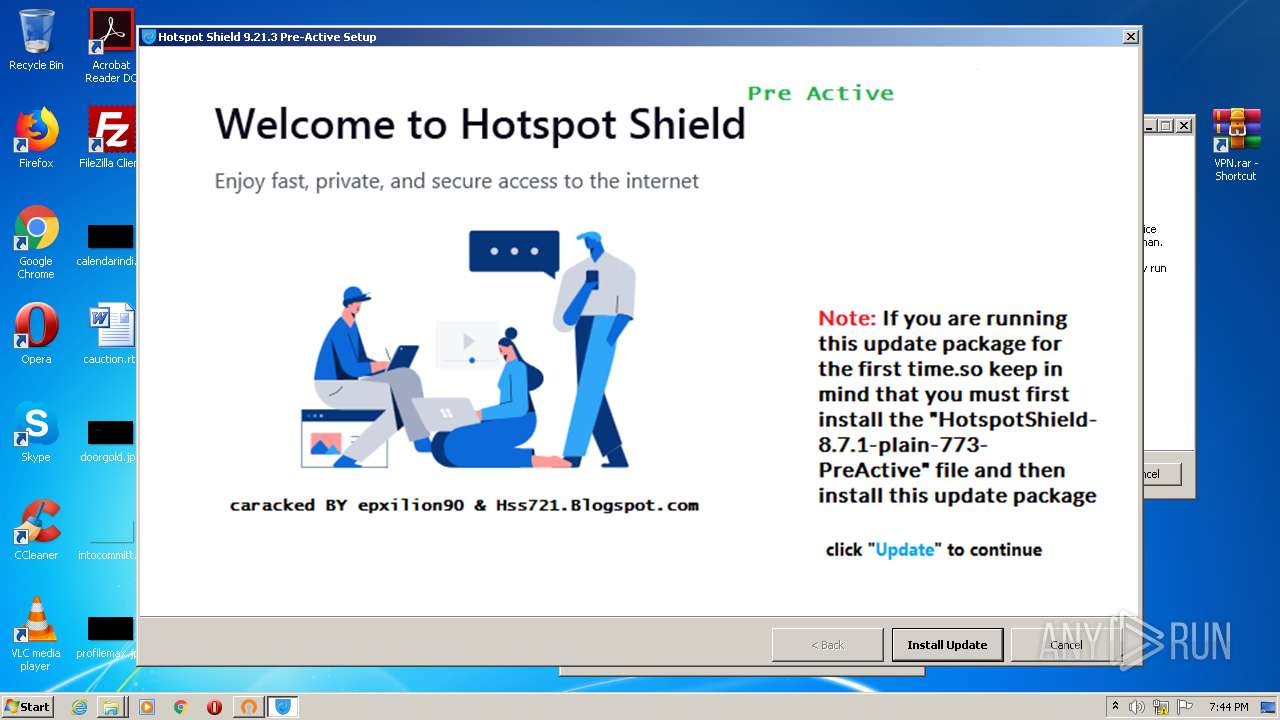
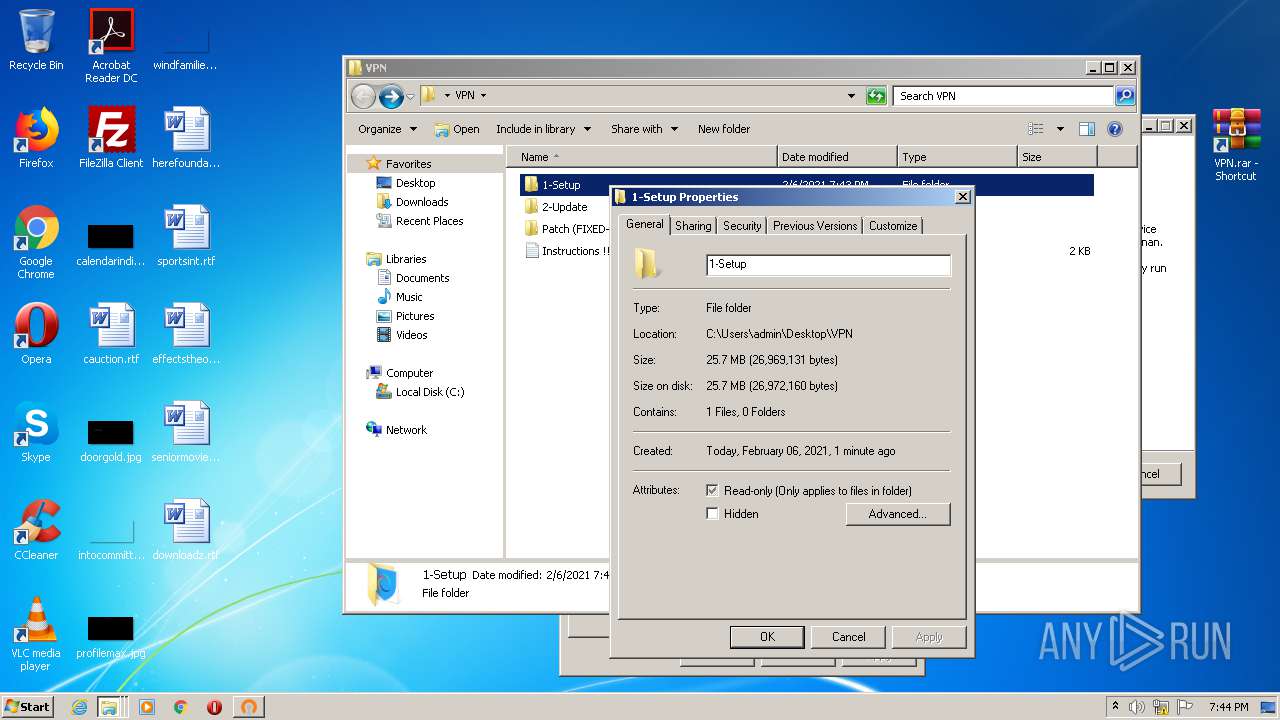
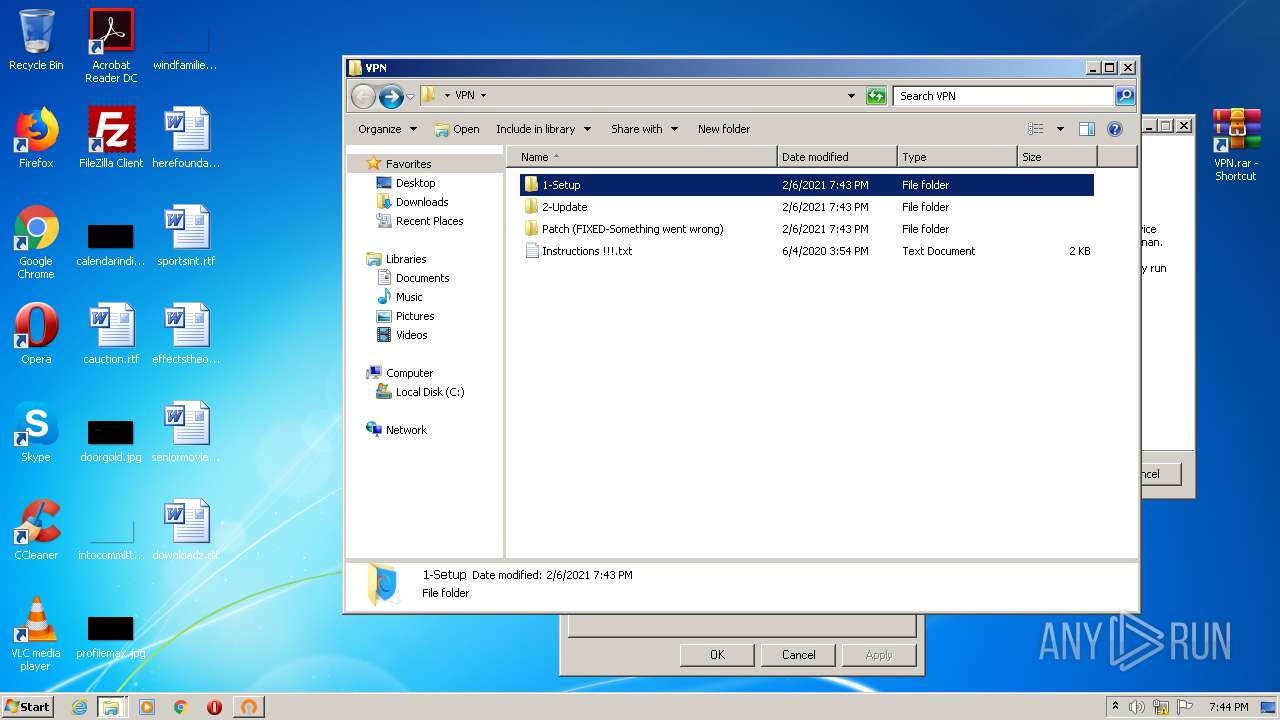
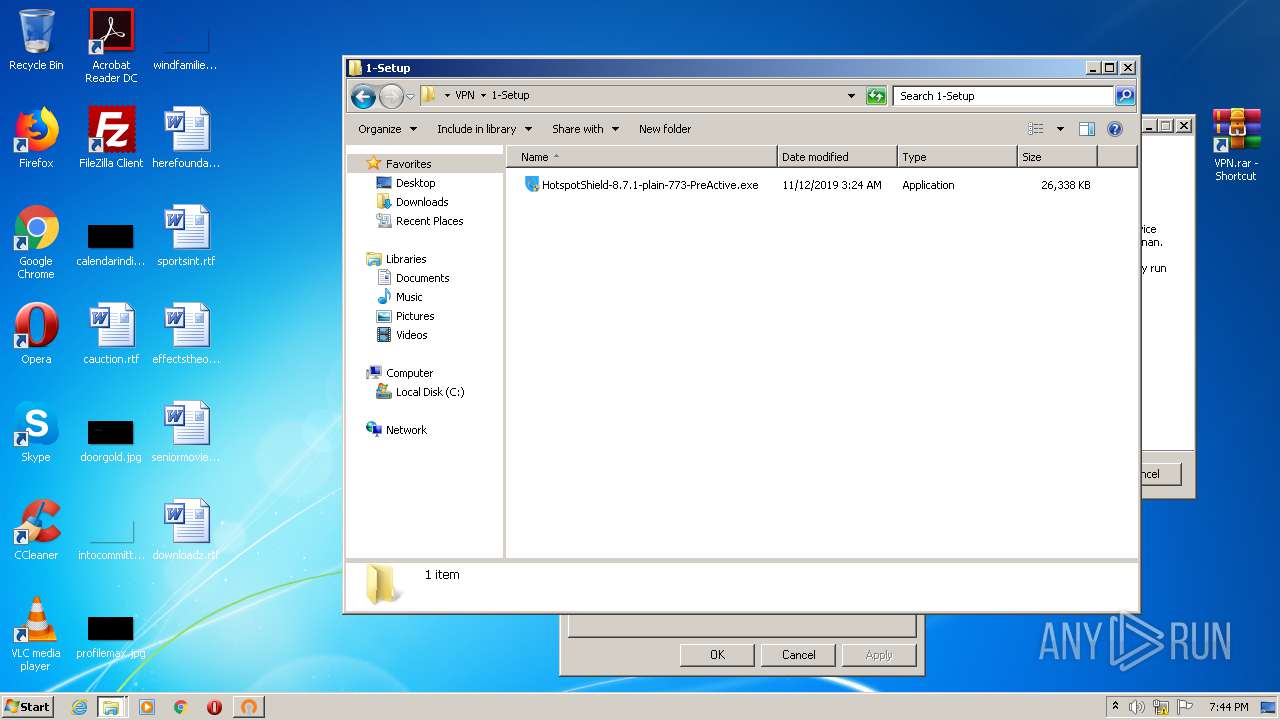
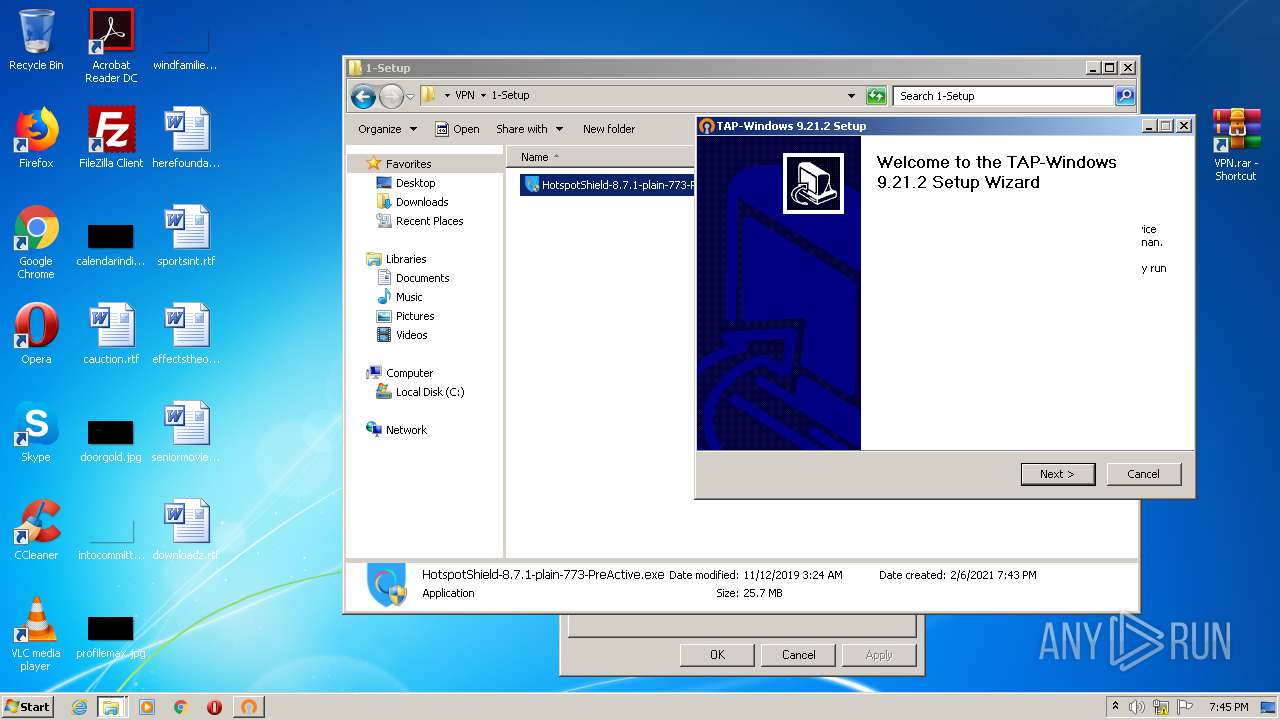
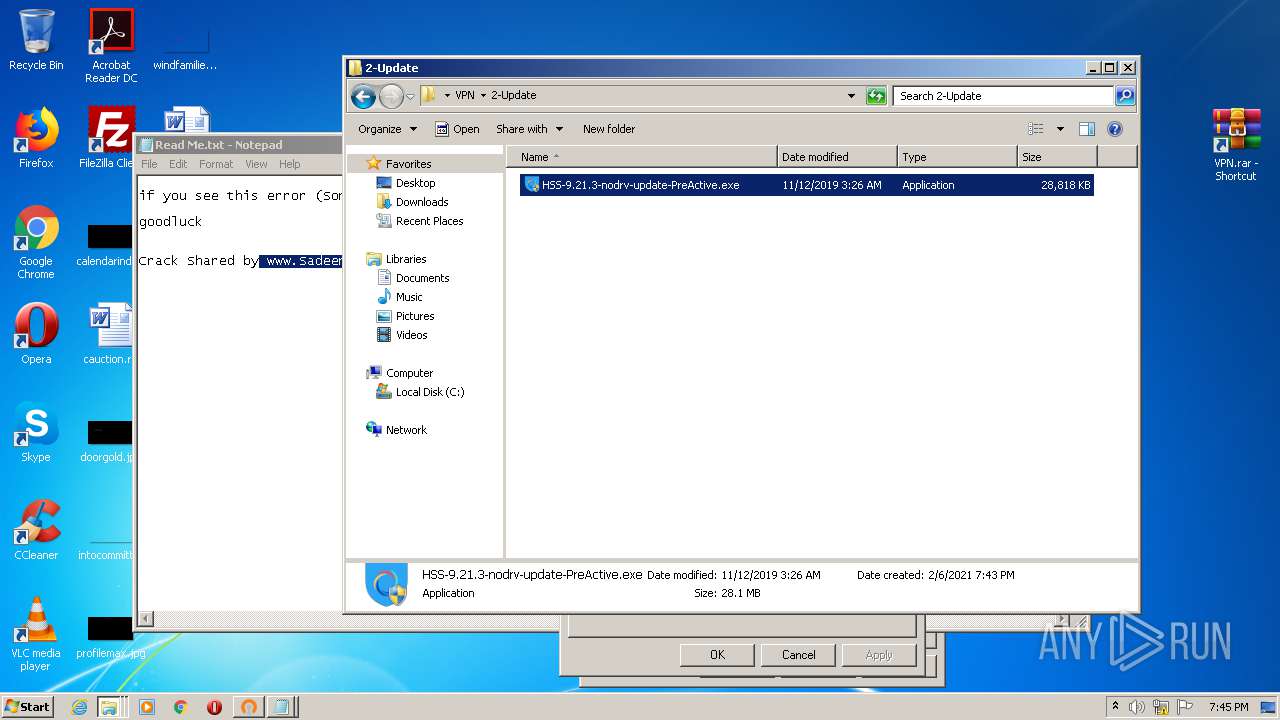
Application was dropped or rewritten from another process
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 972)
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 2088)
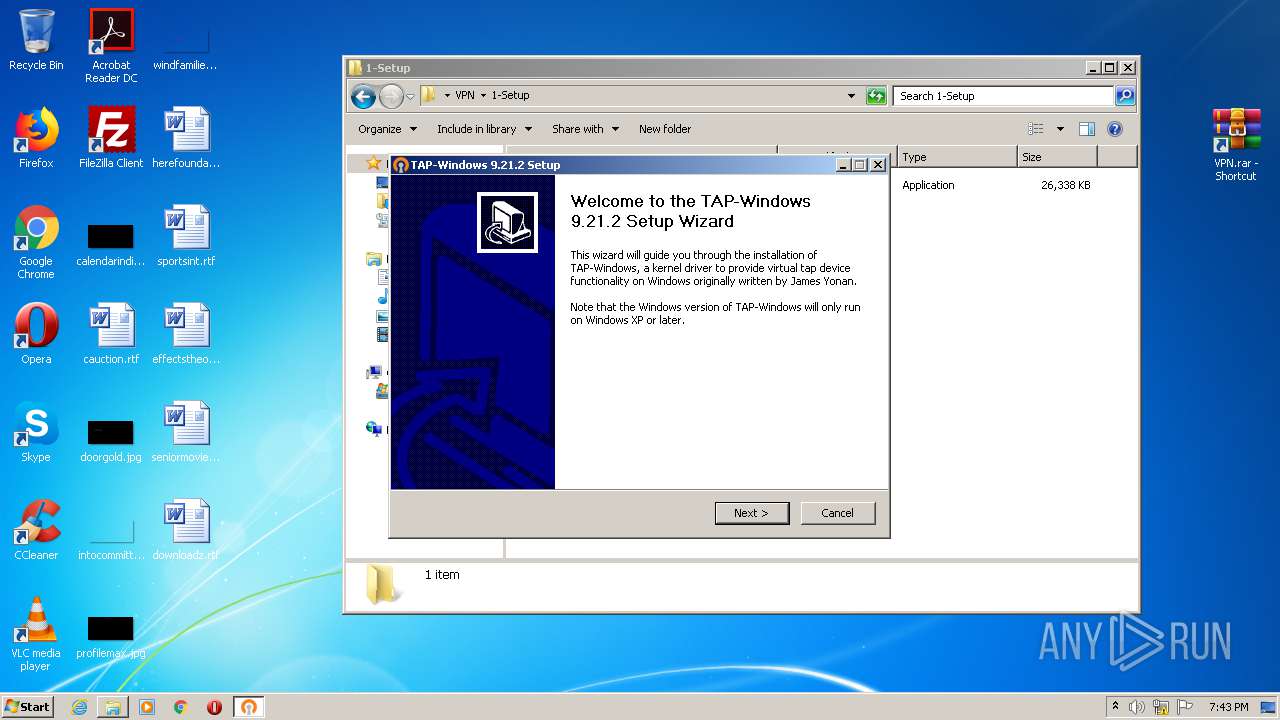
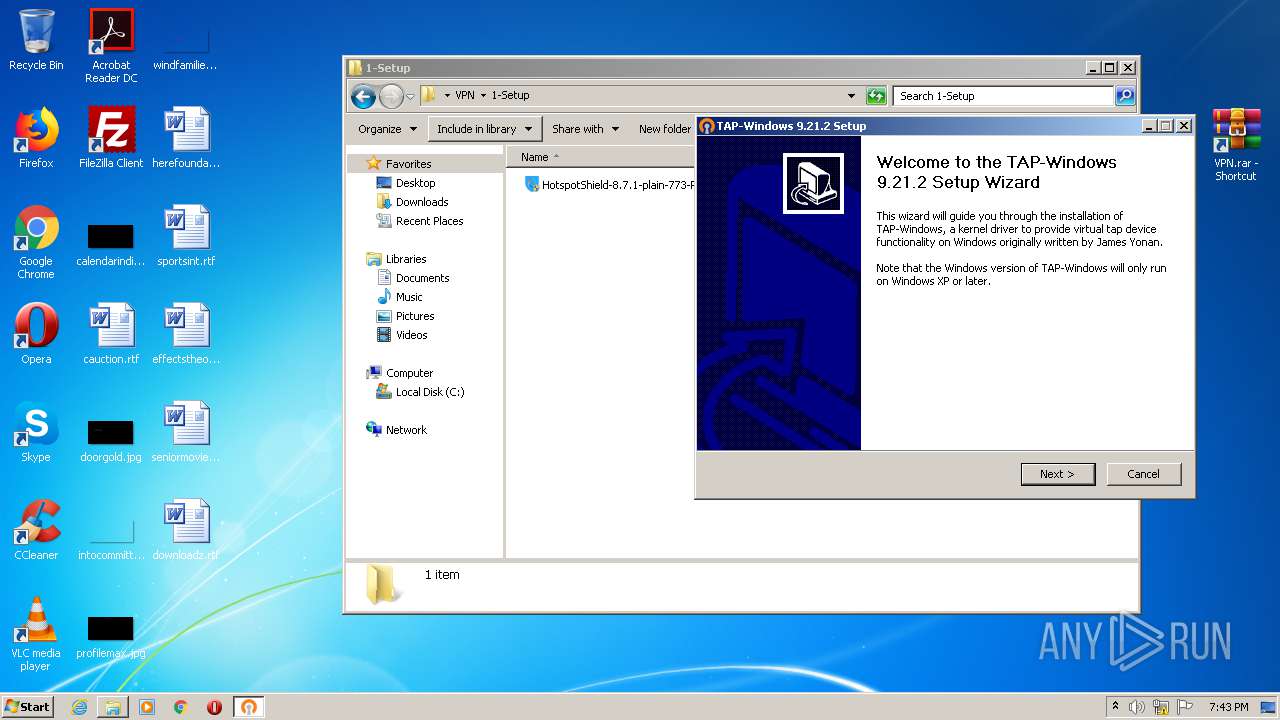
- tap-windows-9.21.2.exe (PID: 2708)
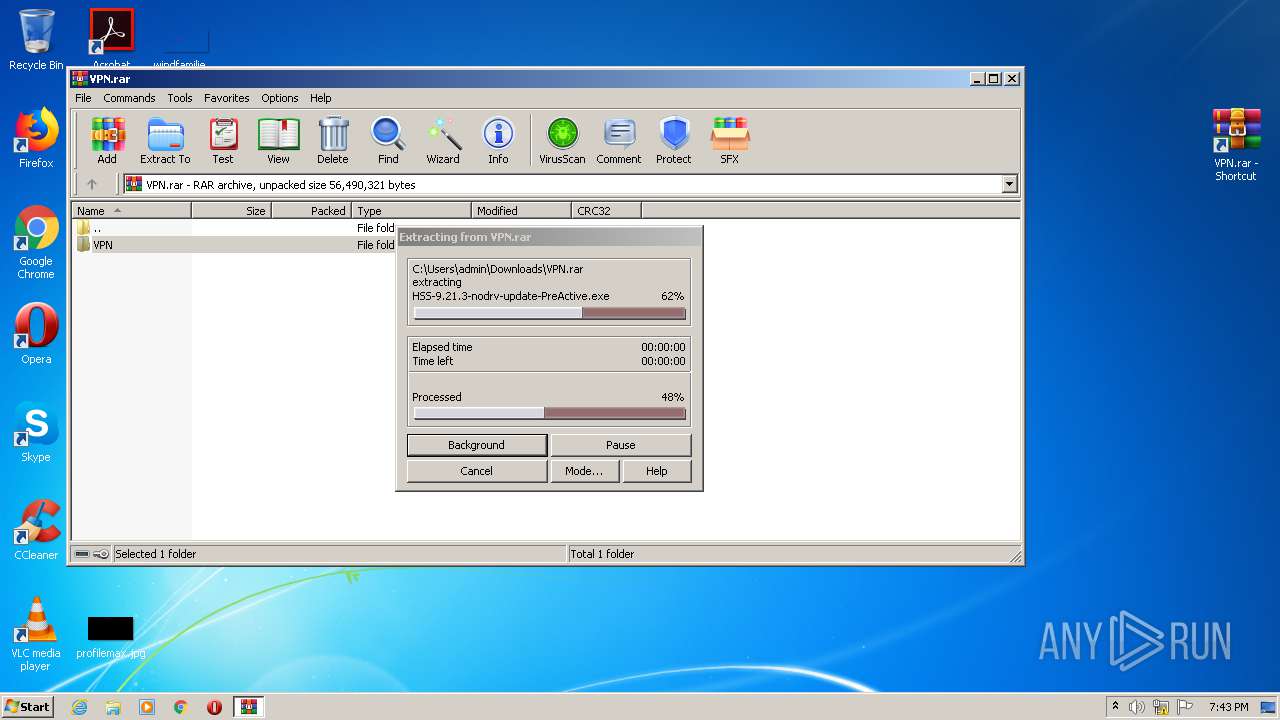
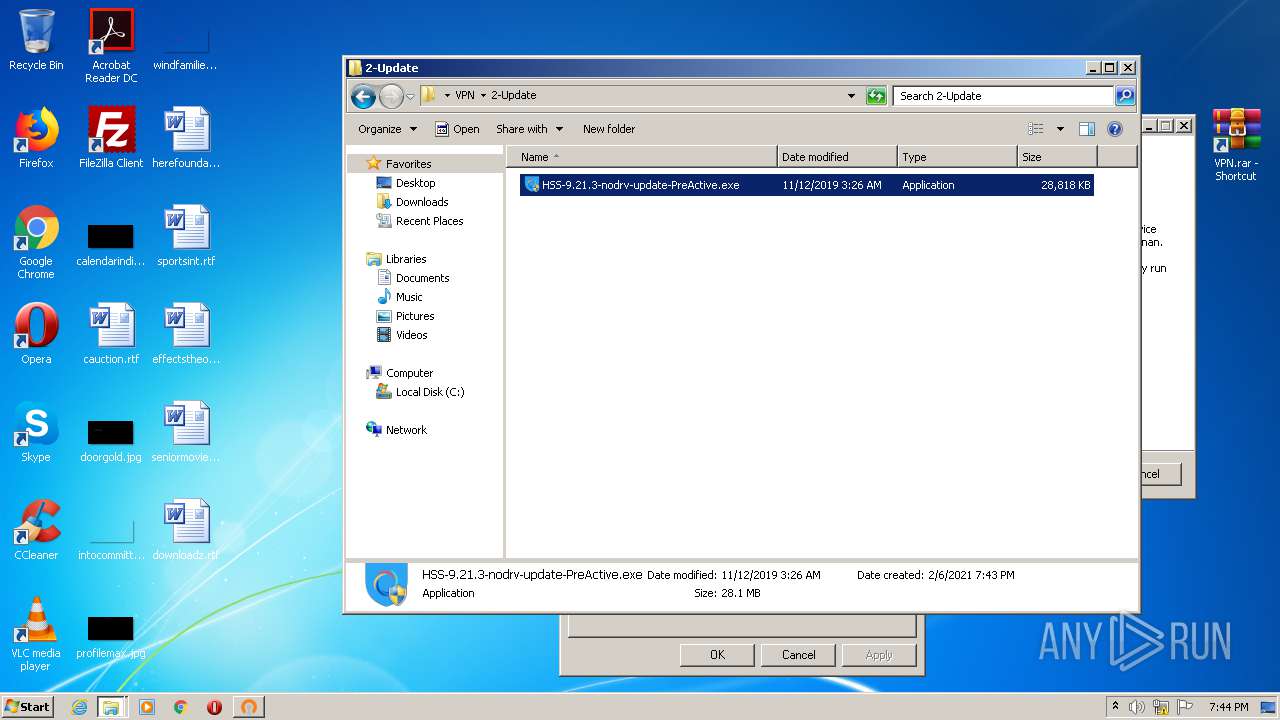
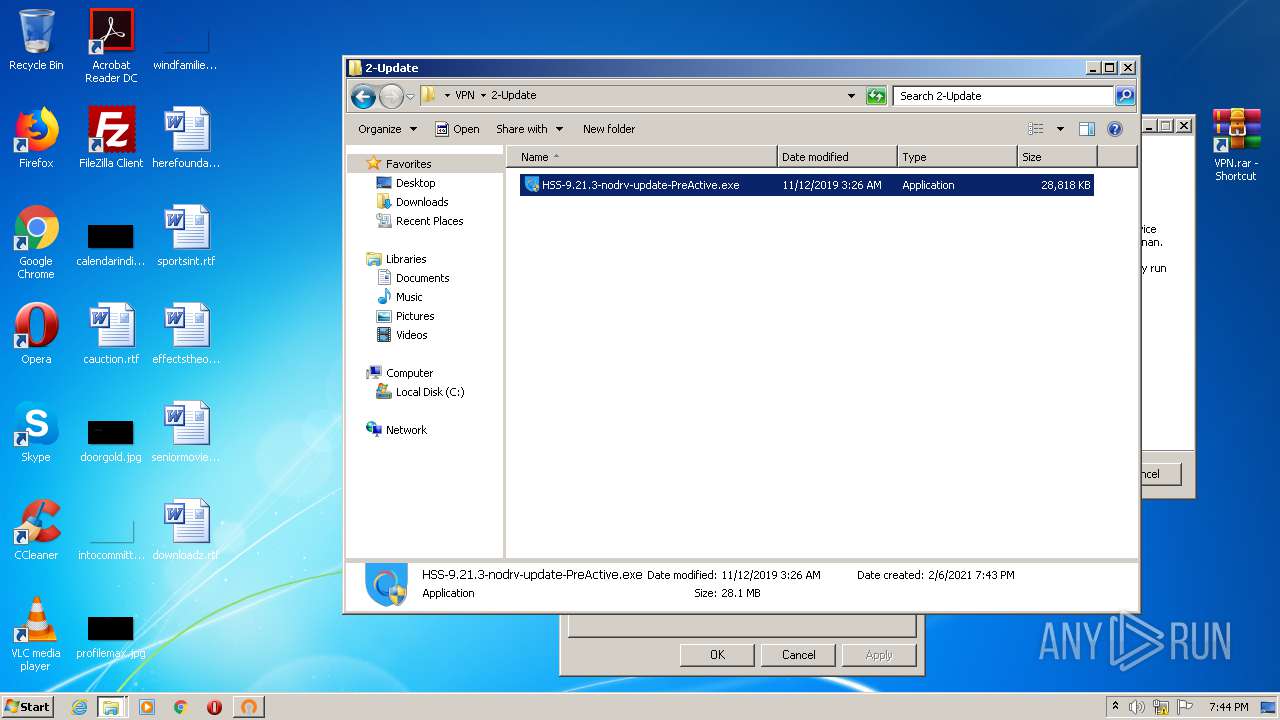
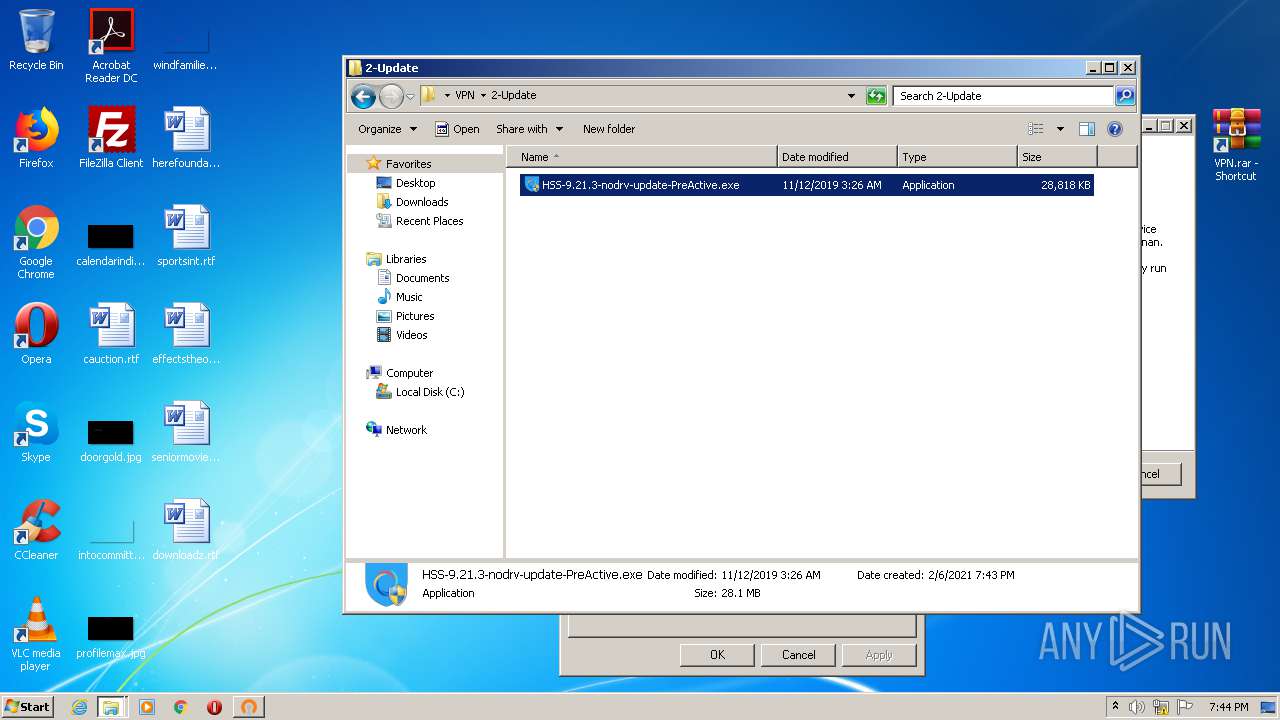
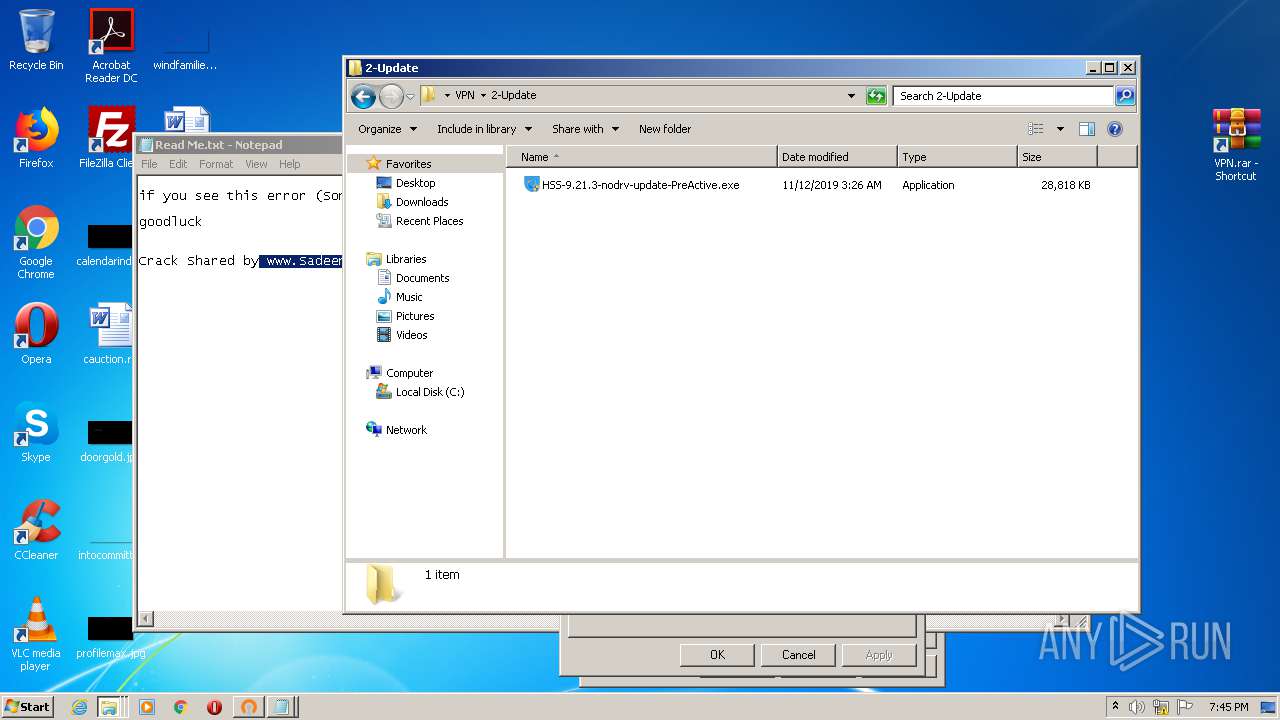
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 2016)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 3416)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 2804)
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 952)
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 4024)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 3328)
- cmw_srv.exe (PID: 2516)
- hsscp.exe (PID: 1348)
- hsscp.exe (PID: 2696)
- hsscp.exe (PID: 2424)
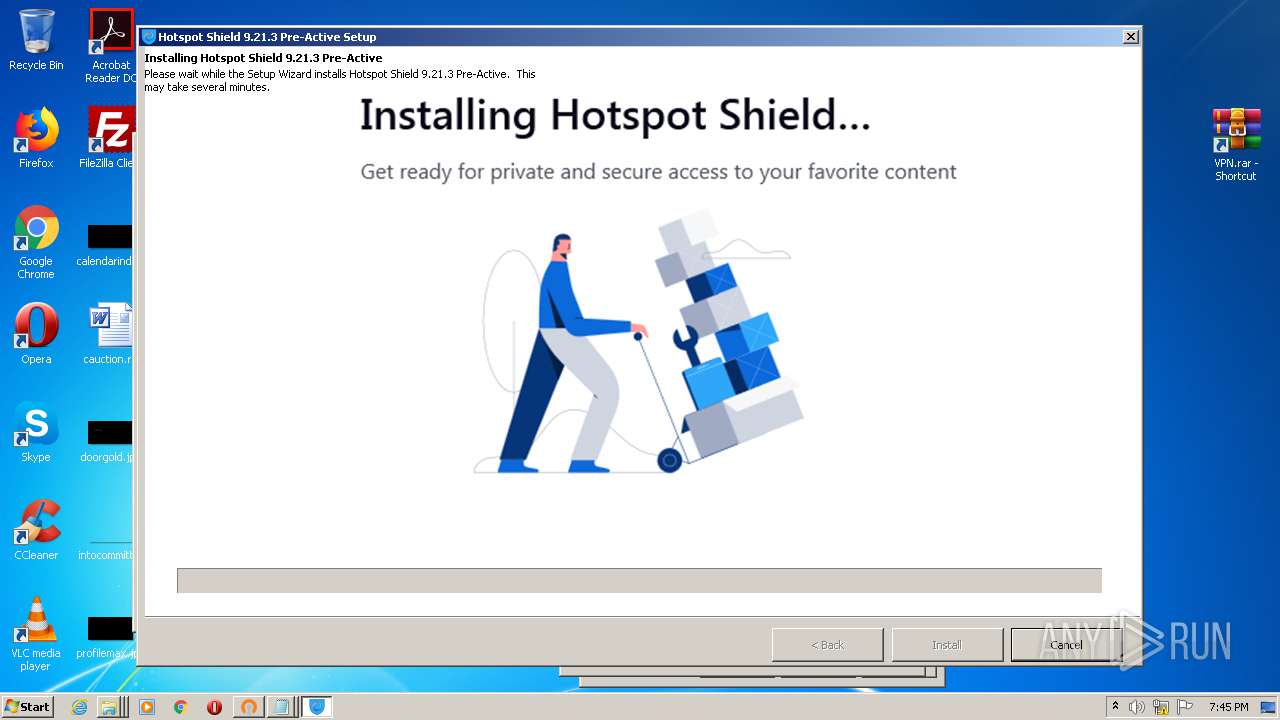
Drops executable file immediately after starts
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 2572)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 3128)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 1080)
Loads the Task Scheduler DLL interface
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 2572)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 3128)
Loads dropped or rewritten executable
- tap-windows-9.21.2.exe (PID: 2708)
- cmw_srv.exe (PID: 2516)
- hsscp.exe (PID: 2696)
- hsscp.exe (PID: 2424)
- hsscp.exe (PID: 1348)
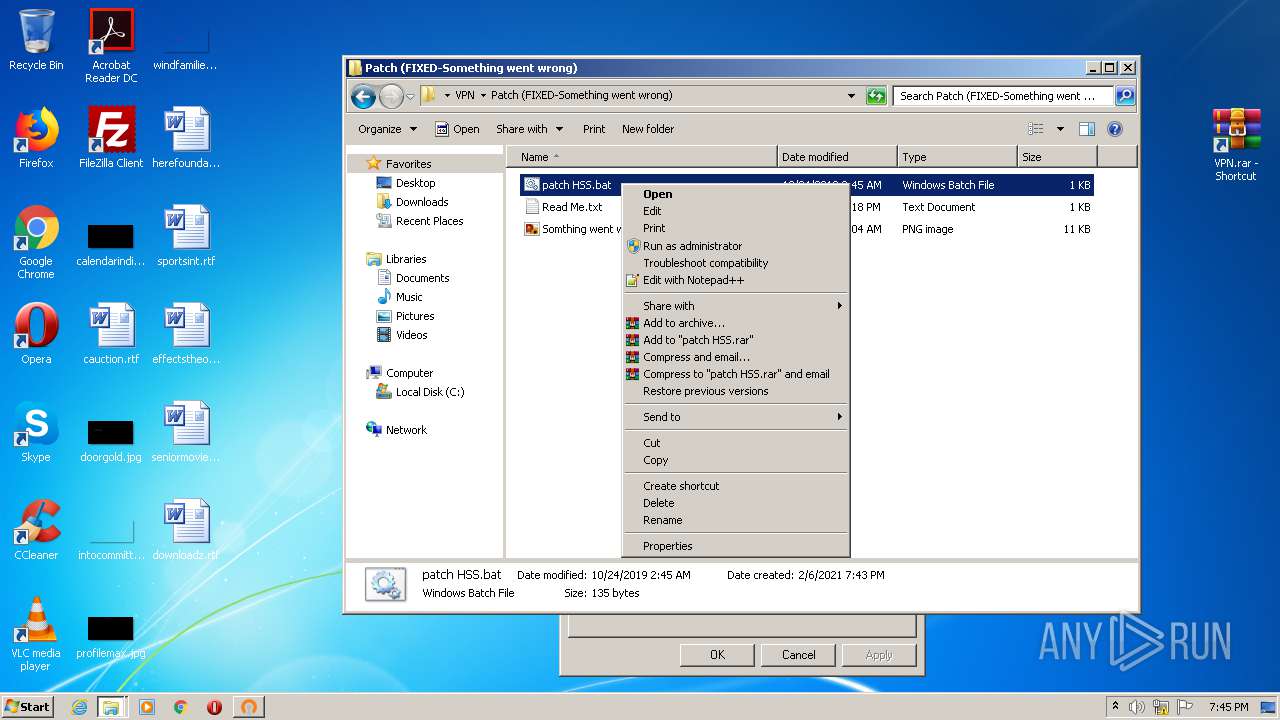
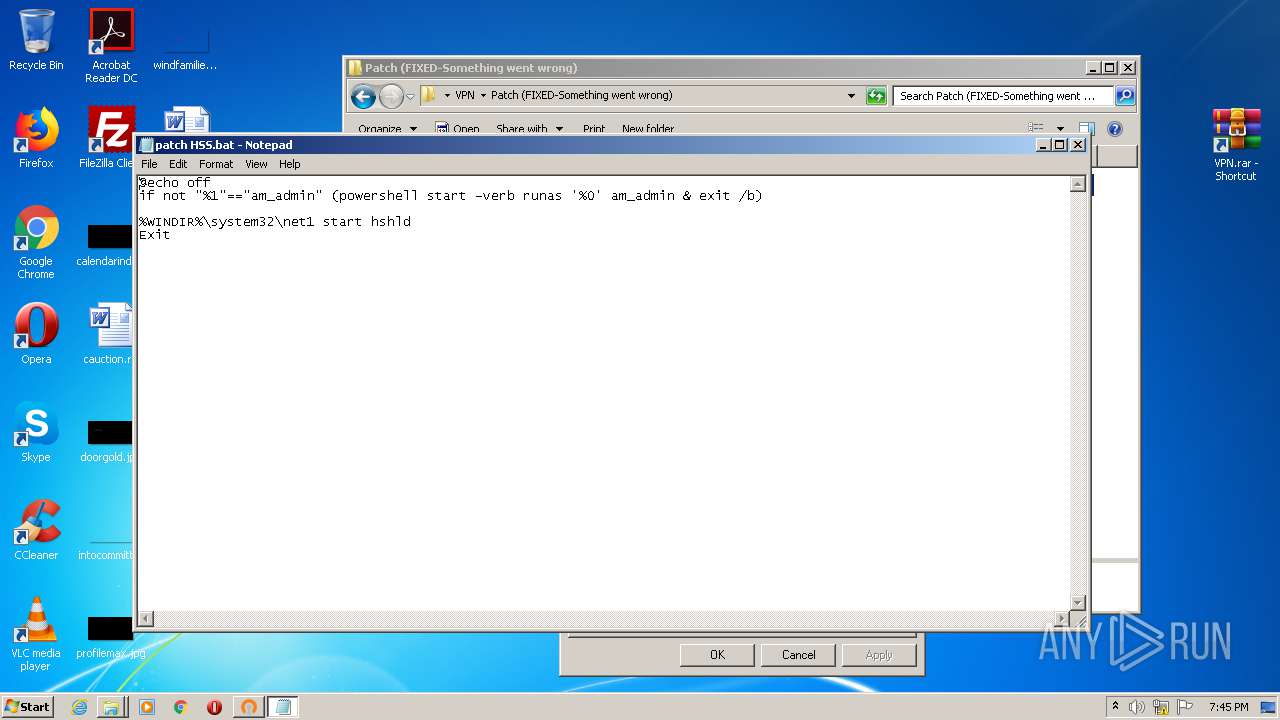
Executes PowerShell scripts
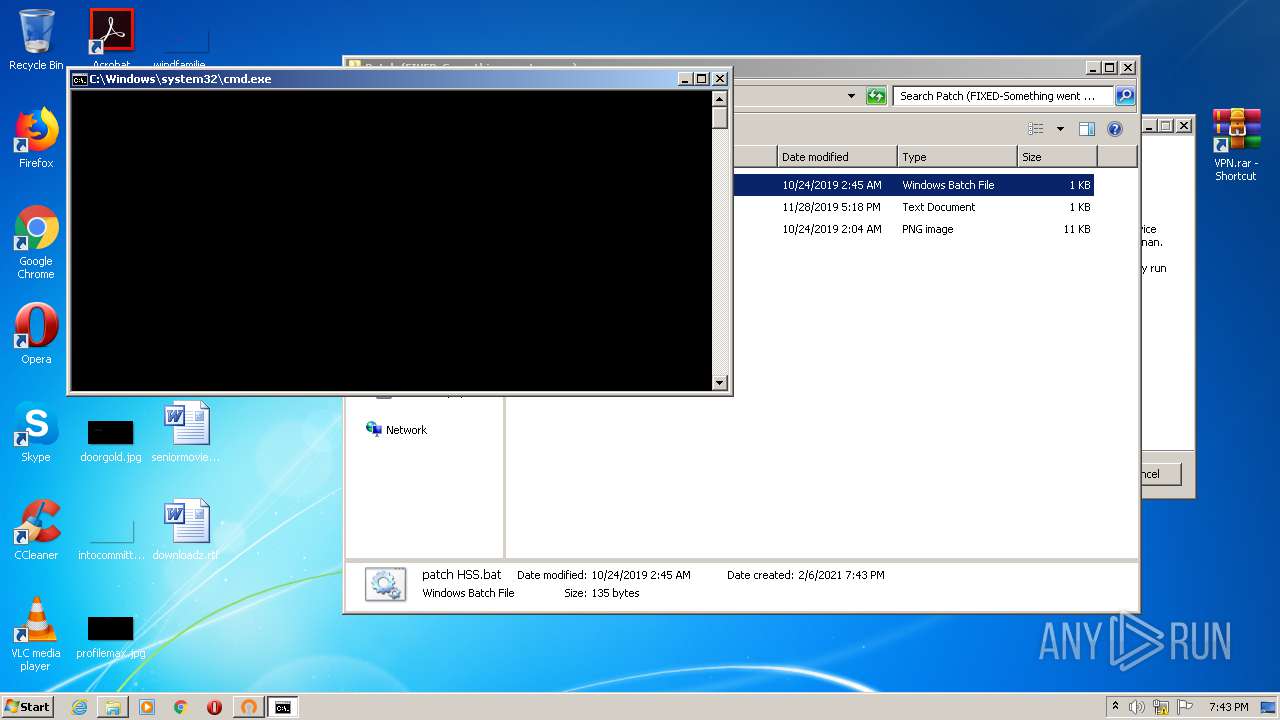
- cmd.exe (PID: 1584)
Writes to the hosts file
- msiexec.exe (PID: 1644)
Changes settings of System certificates
- cmw_srv.exe (PID: 2516)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2800)
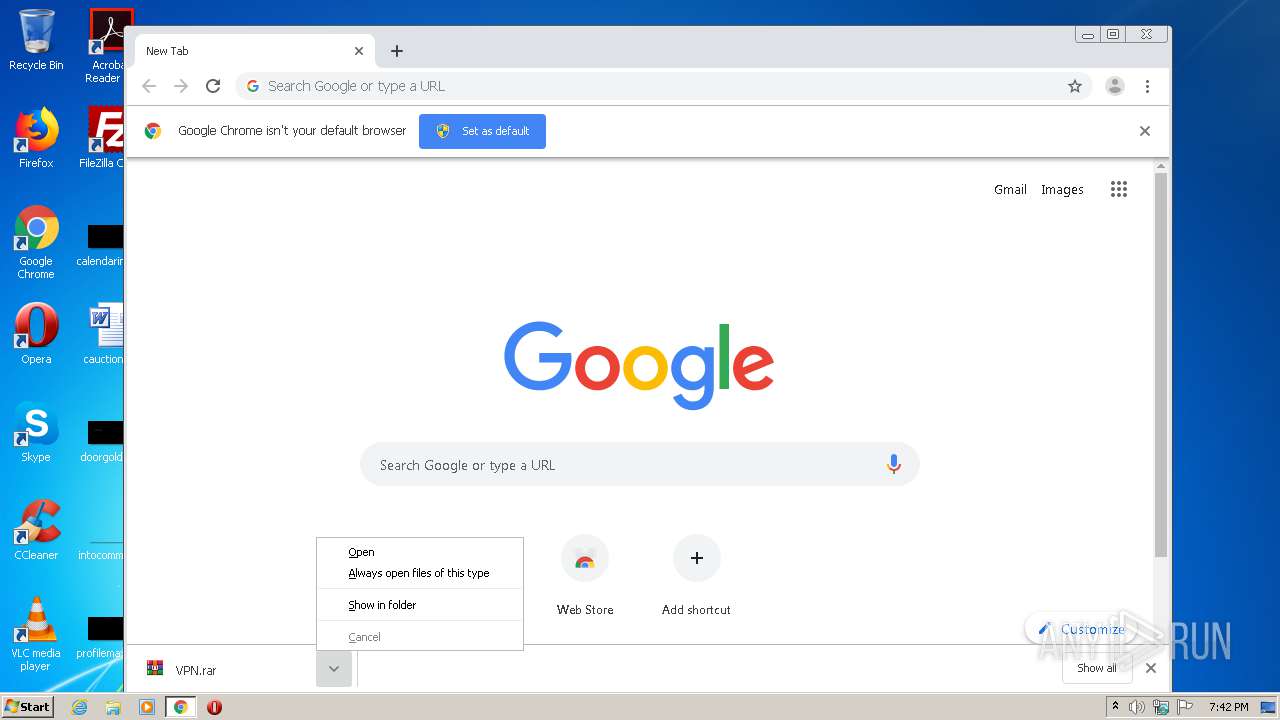
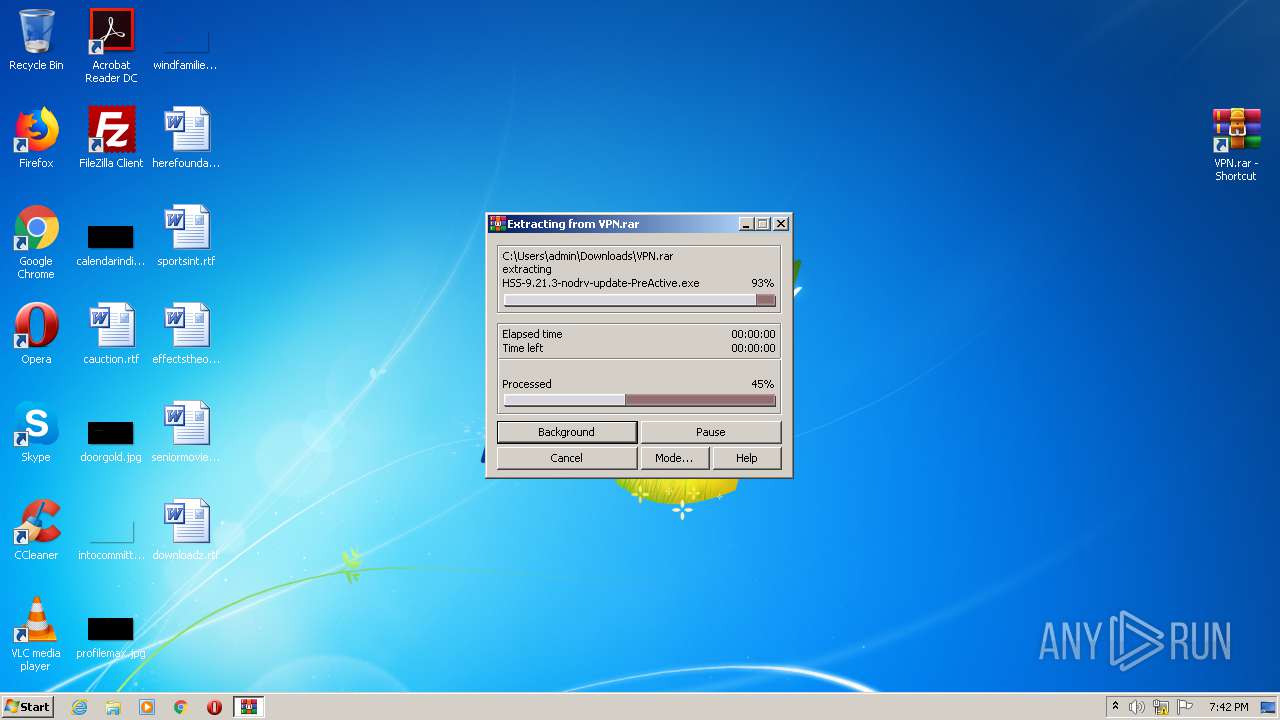
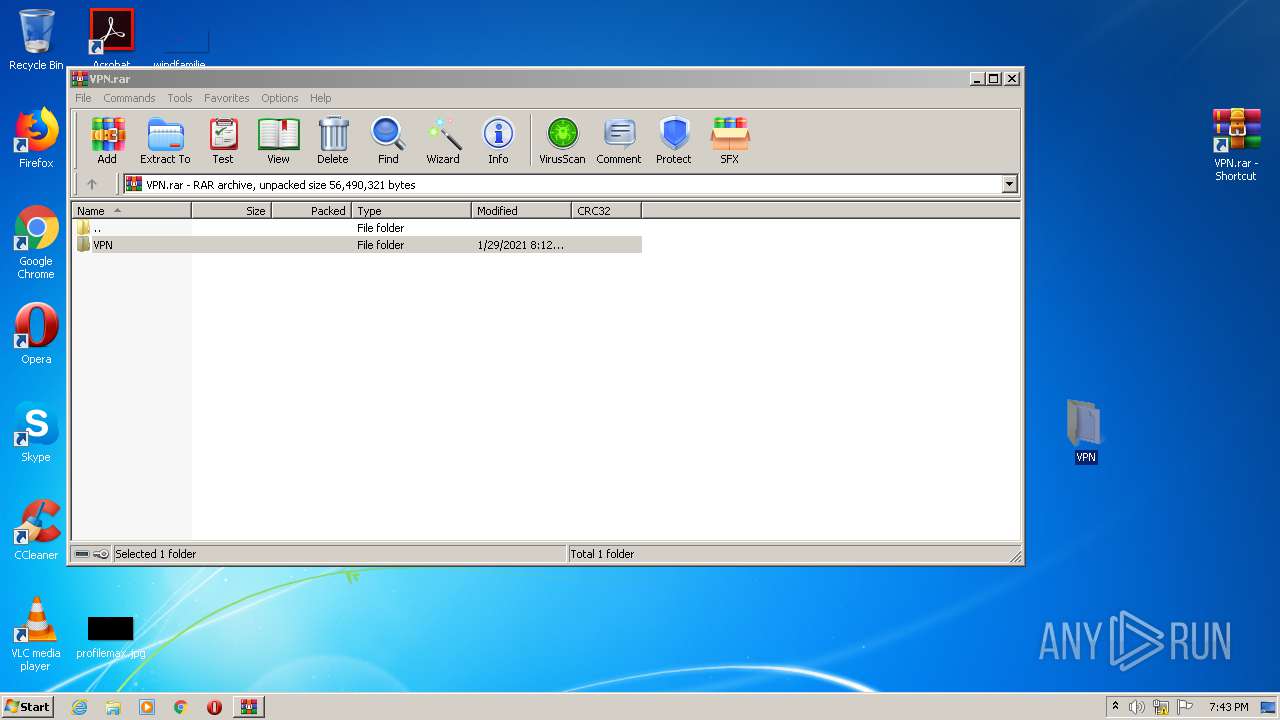
Executable content was dropped or overwritten
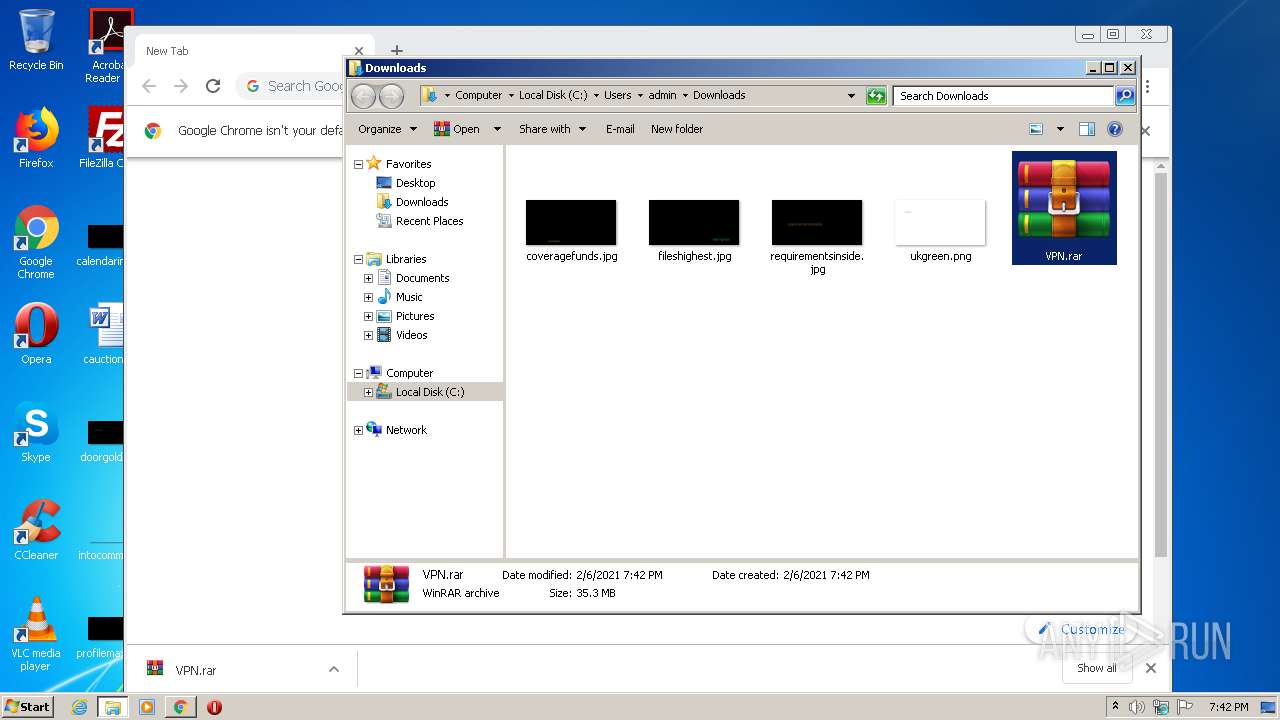
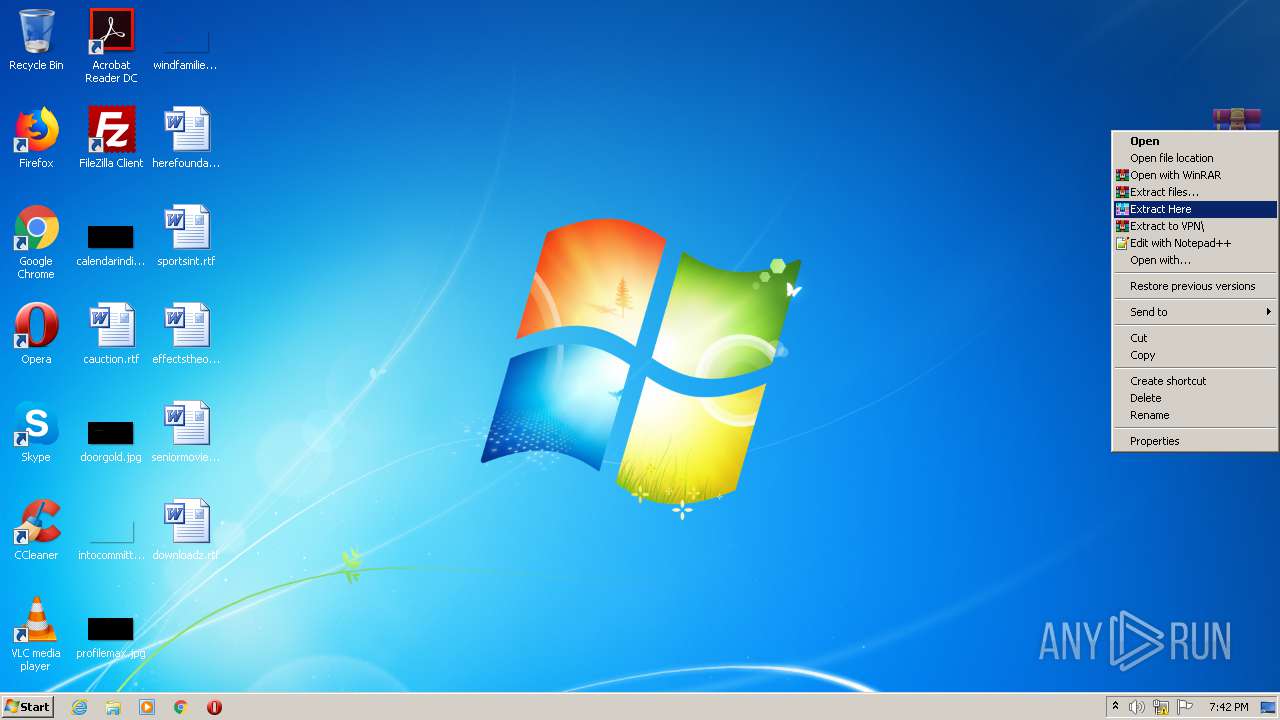
- WinRAR.exe (PID: 3228)
- WinRAR.exe (PID: 2580)
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 2572)
- tap-windows-9.21.2.exe (PID: 2708)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 3128)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 1080)
- msiexec.exe (PID: 1644)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 2480)
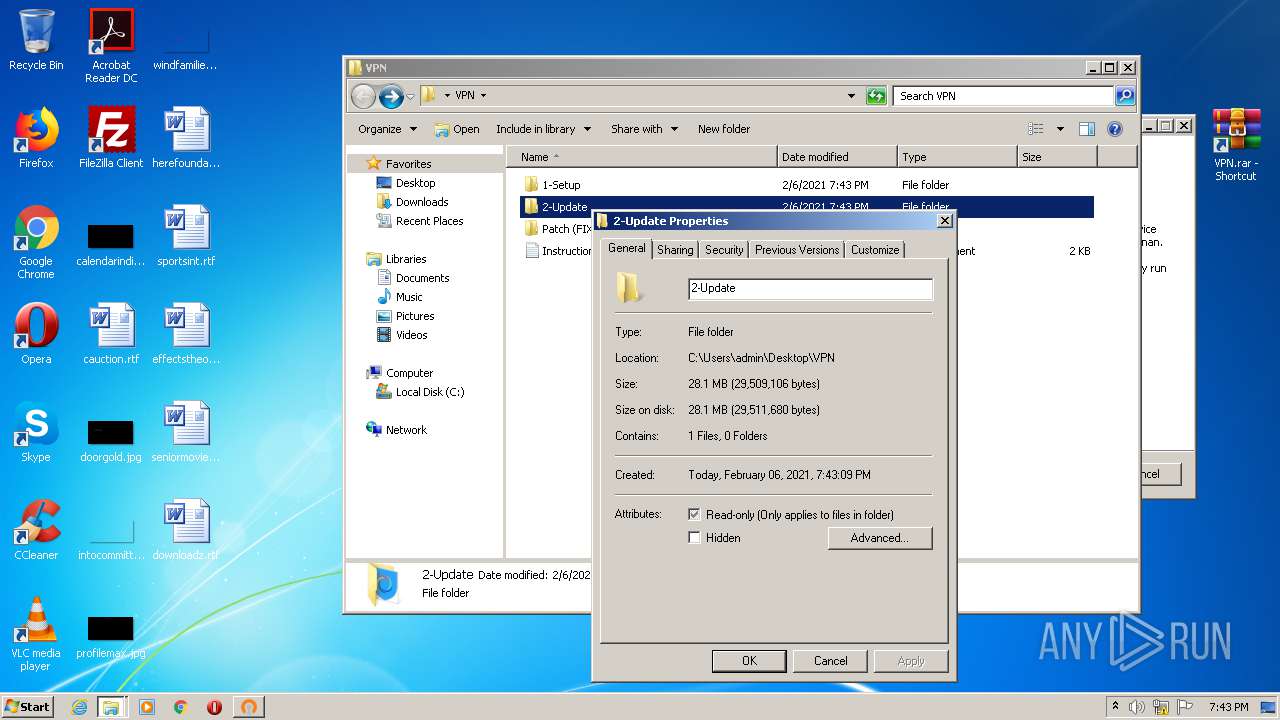
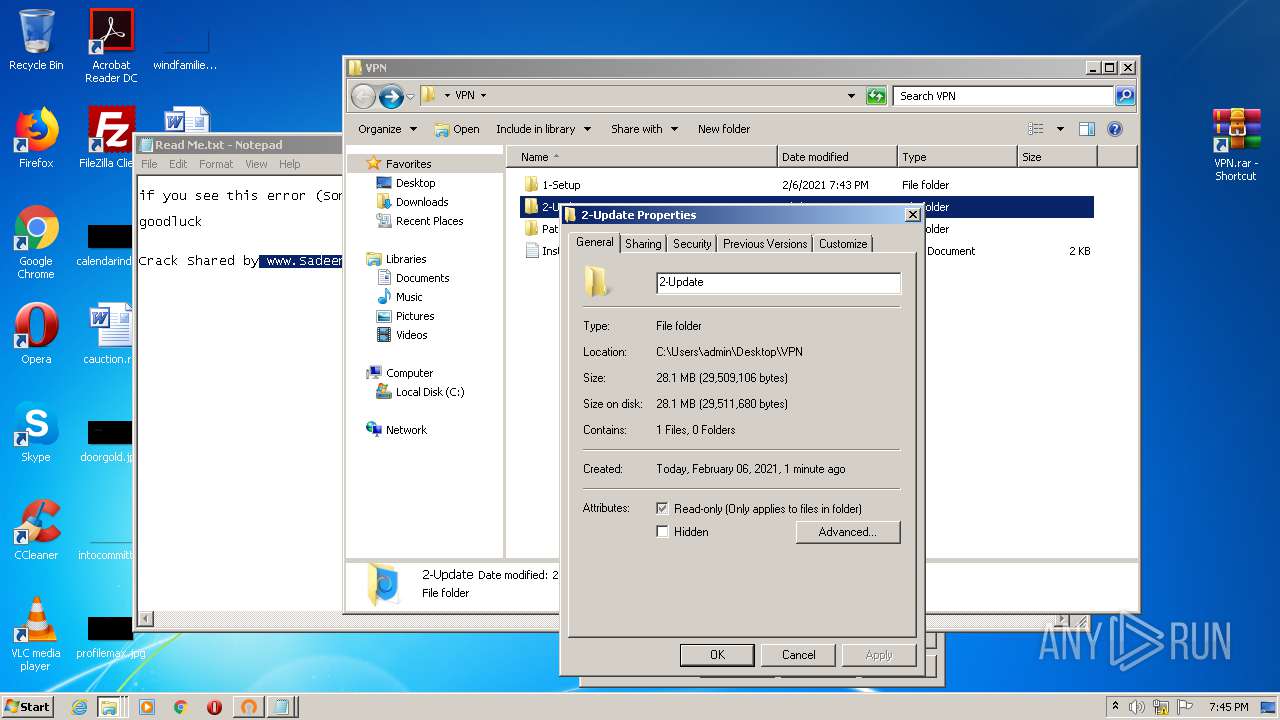
Creates files in the user directory
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 2572)
- powershell.exe (PID: 3176)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 3128)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 1080)
Drops a file that was compiled in debug mode
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 2572)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 3128)
- msiexec.exe (PID: 1644)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 2480)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 1080)
Creates files in the Windows directory
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 2572)
- msiexec.exe (PID: 1644)
- cmw_srv.exe (PID: 2516)
Drops a file with too old compile date
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 2572)
- tap-windows-9.21.2.exe (PID: 2708)
- msiexec.exe (PID: 1644)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 3176)
Application launched itself
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 1080)
Creates a directory in Program Files
- msiexec.exe (PID: 1644)
Creates files in the driver directory
- msiexec.exe (PID: 1644)
Executed as Windows Service
- cmw_srv.exe (PID: 2516)
Creates files in the program directory
- cmw_srv.exe (PID: 2516)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 2480)
Reads Environment values
- cmw_srv.exe (PID: 2516)
Removes files from Windows directory
- cmw_srv.exe (PID: 2516)
Adds / modifies Windows certificates
- cmw_srv.exe (PID: 2516)
Changes IE settings (feature browser emulation)
- hsscp.exe (PID: 2424)
- hsscp.exe (PID: 1348)
INFO
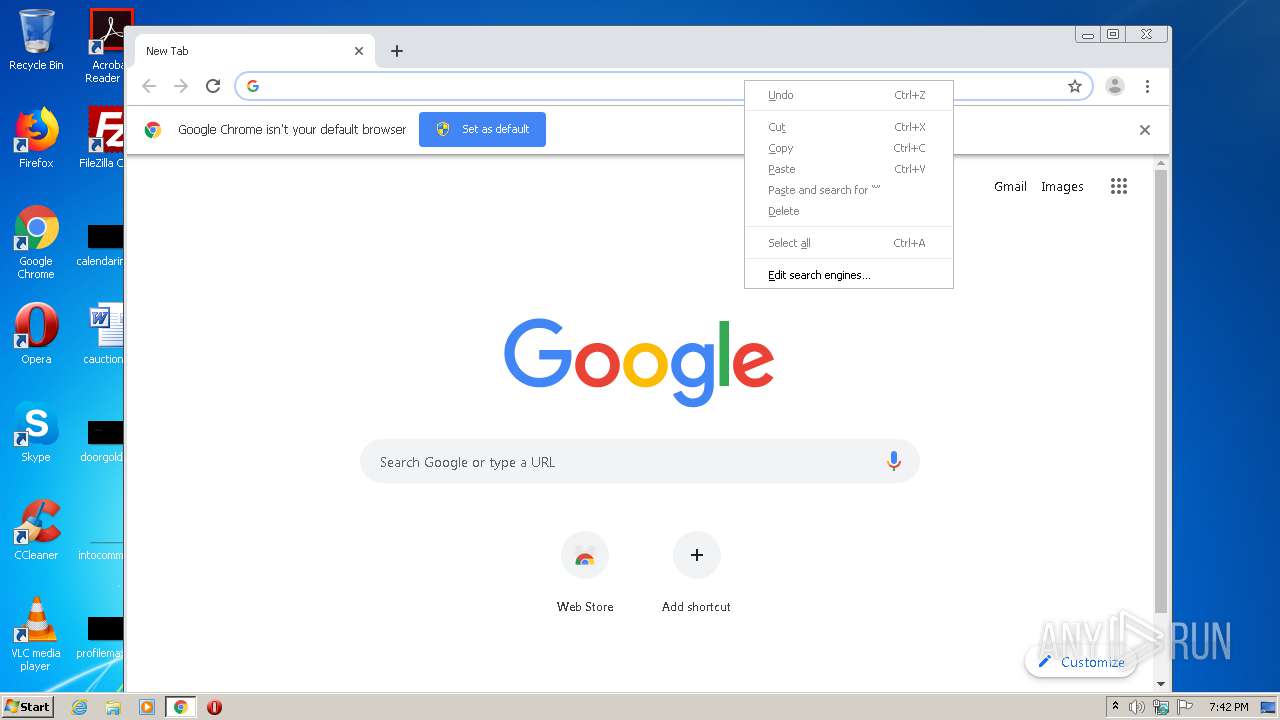
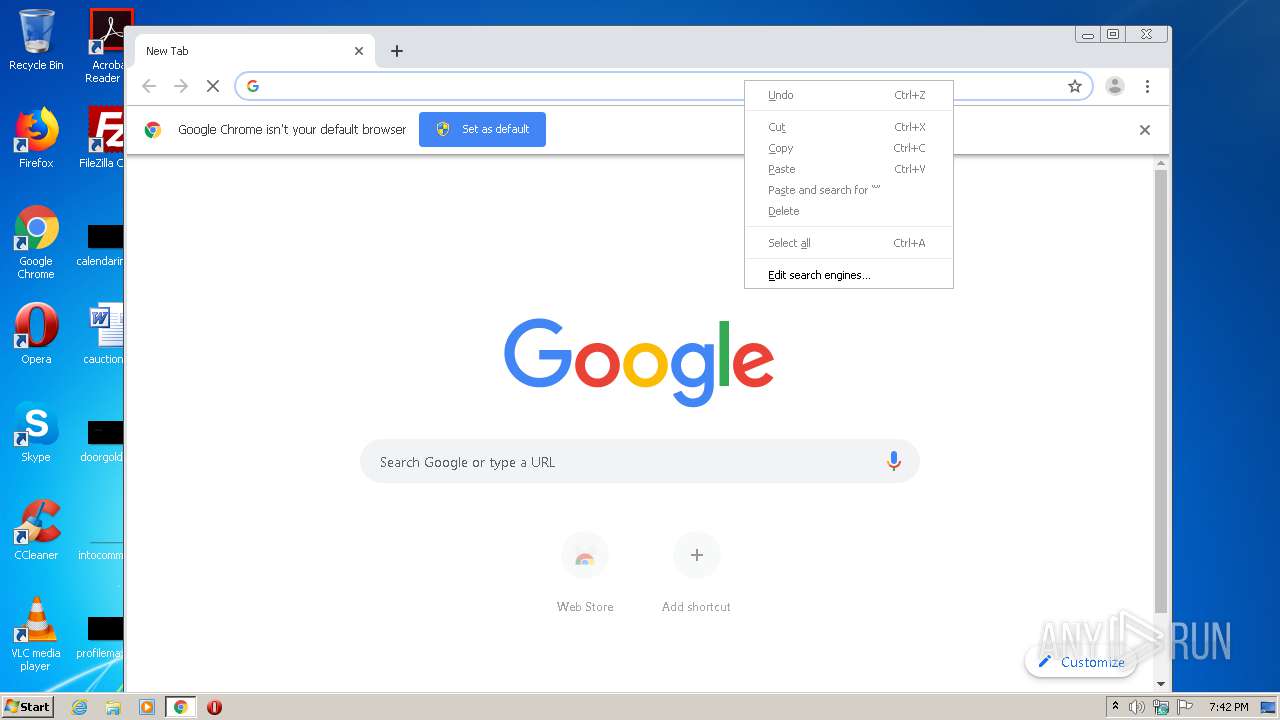
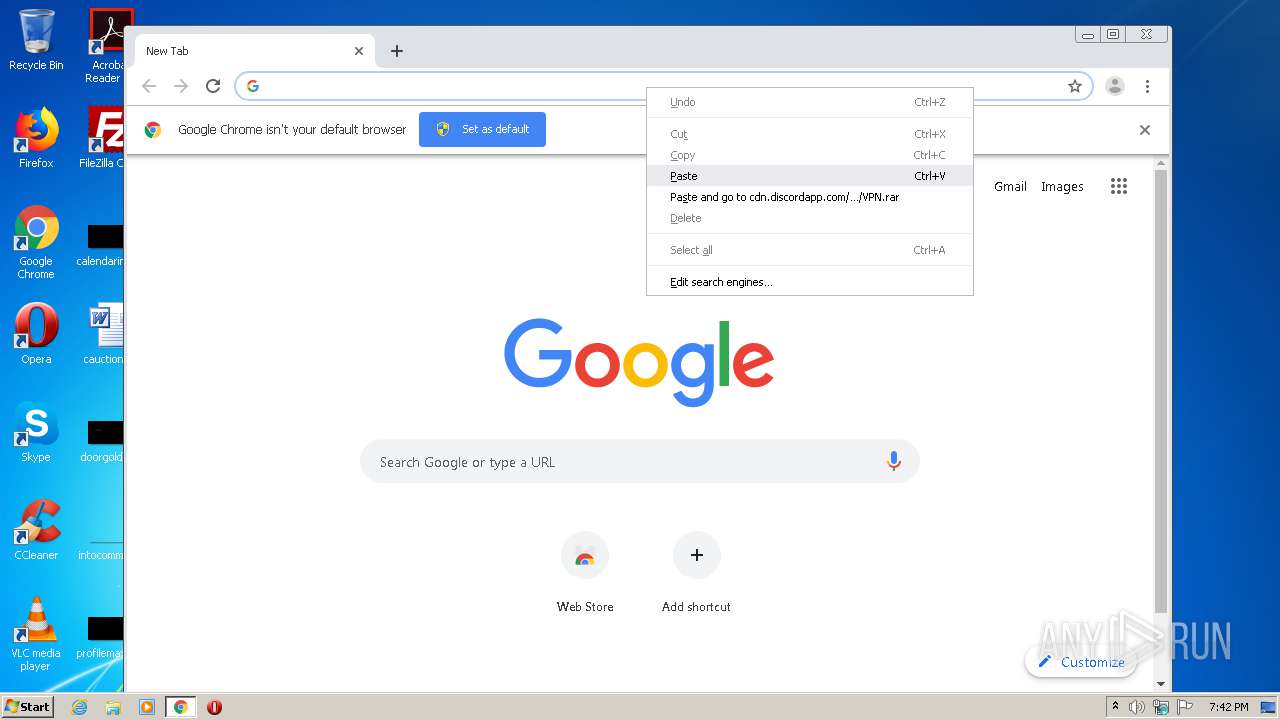
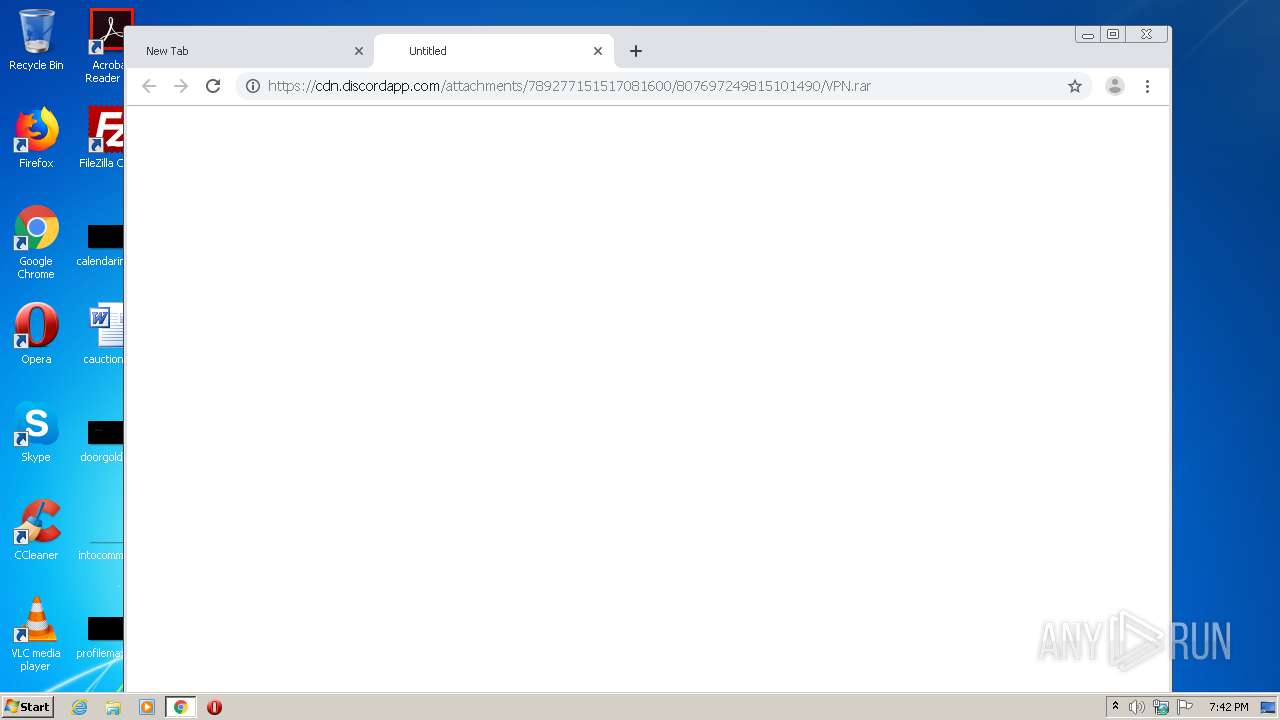
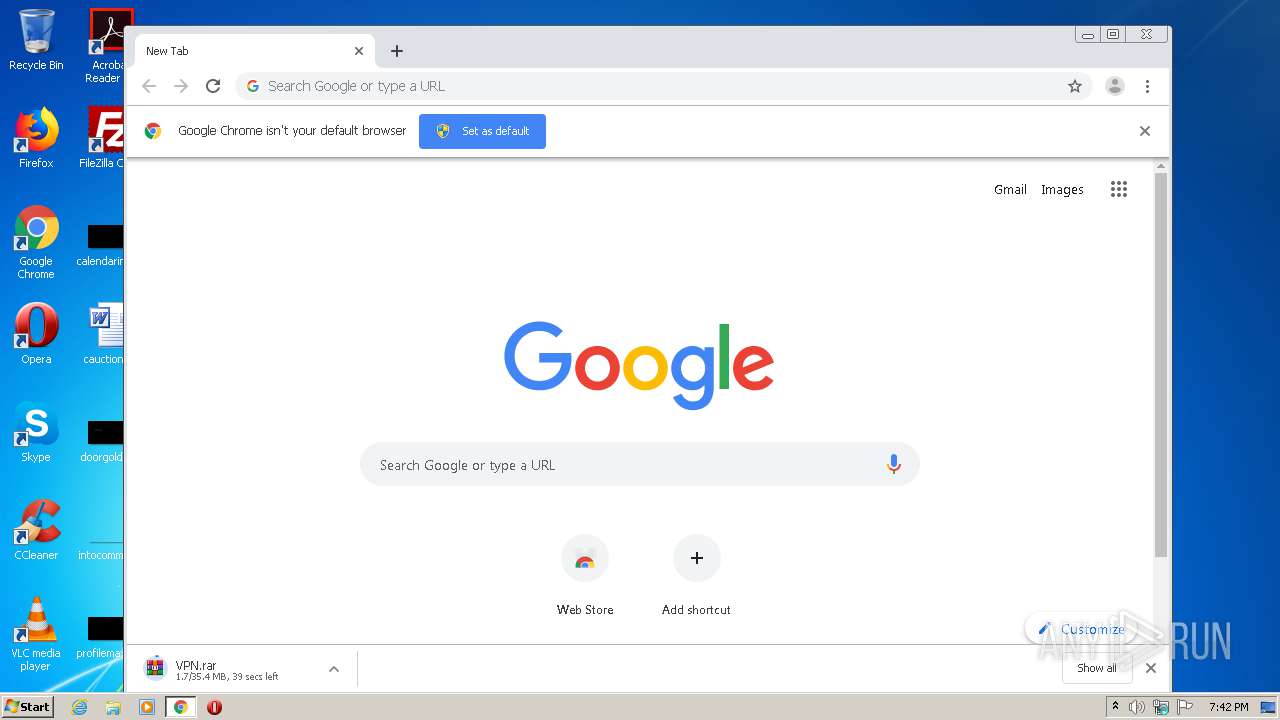
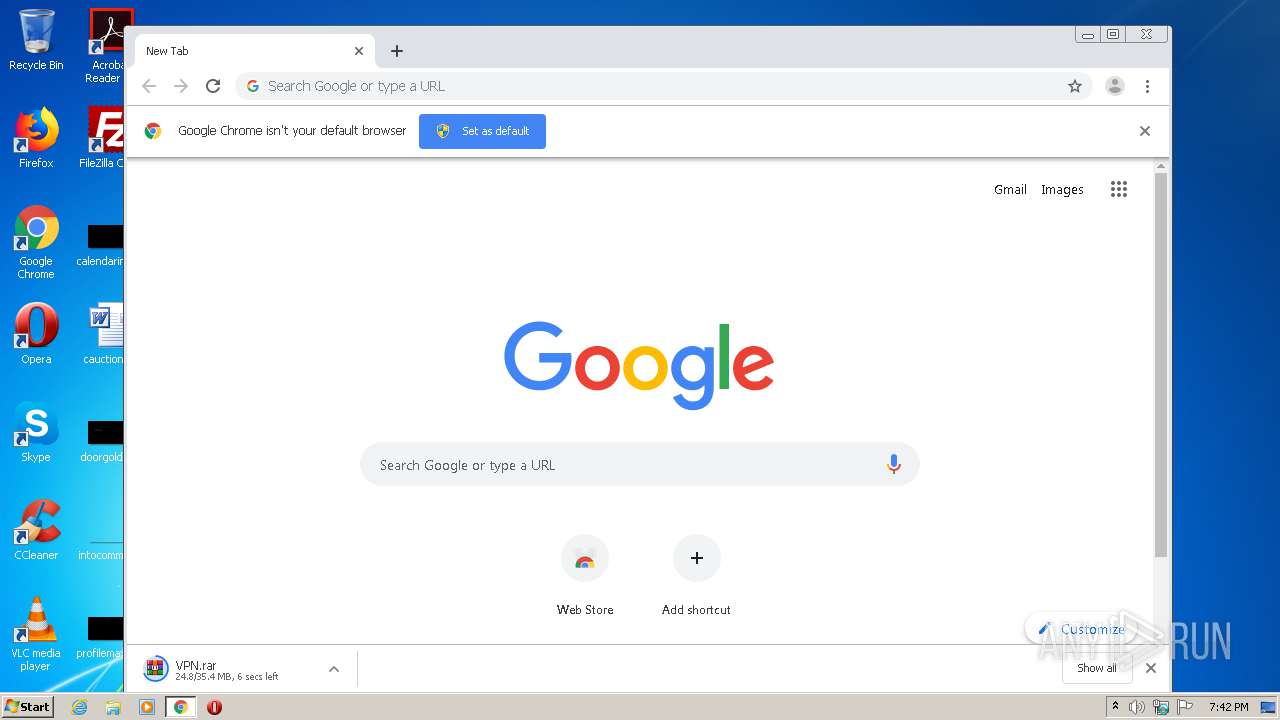
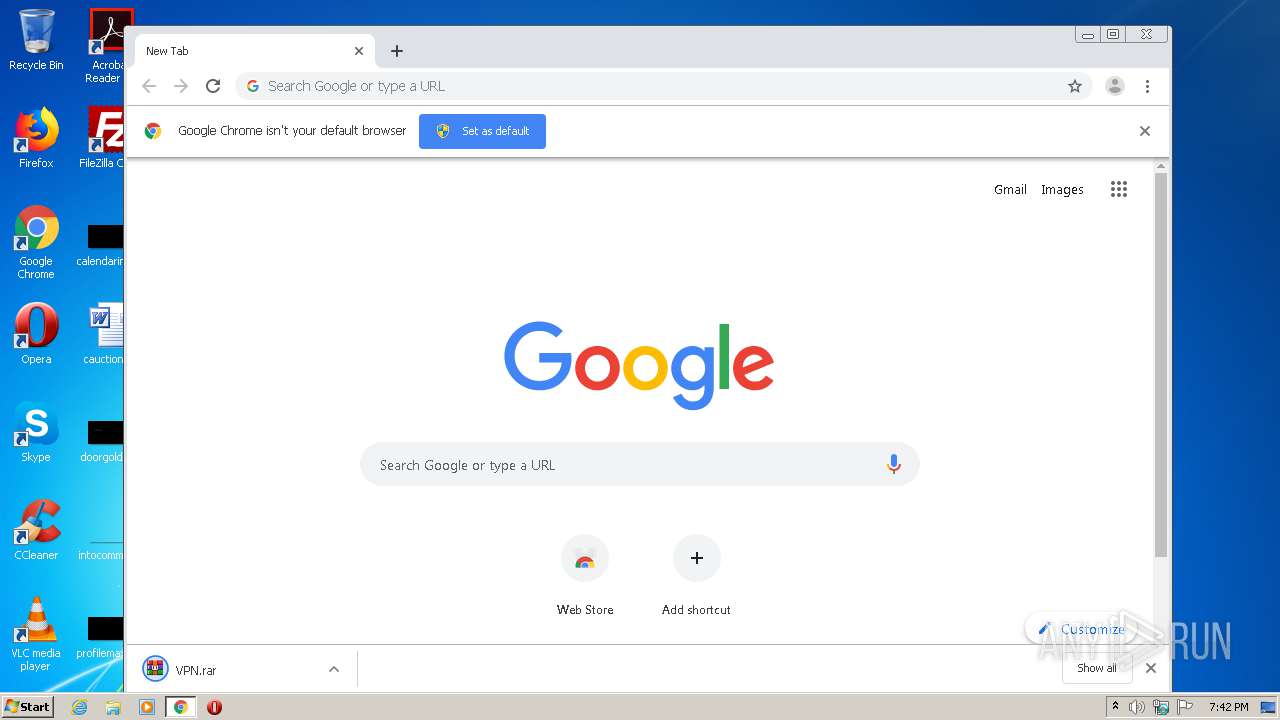
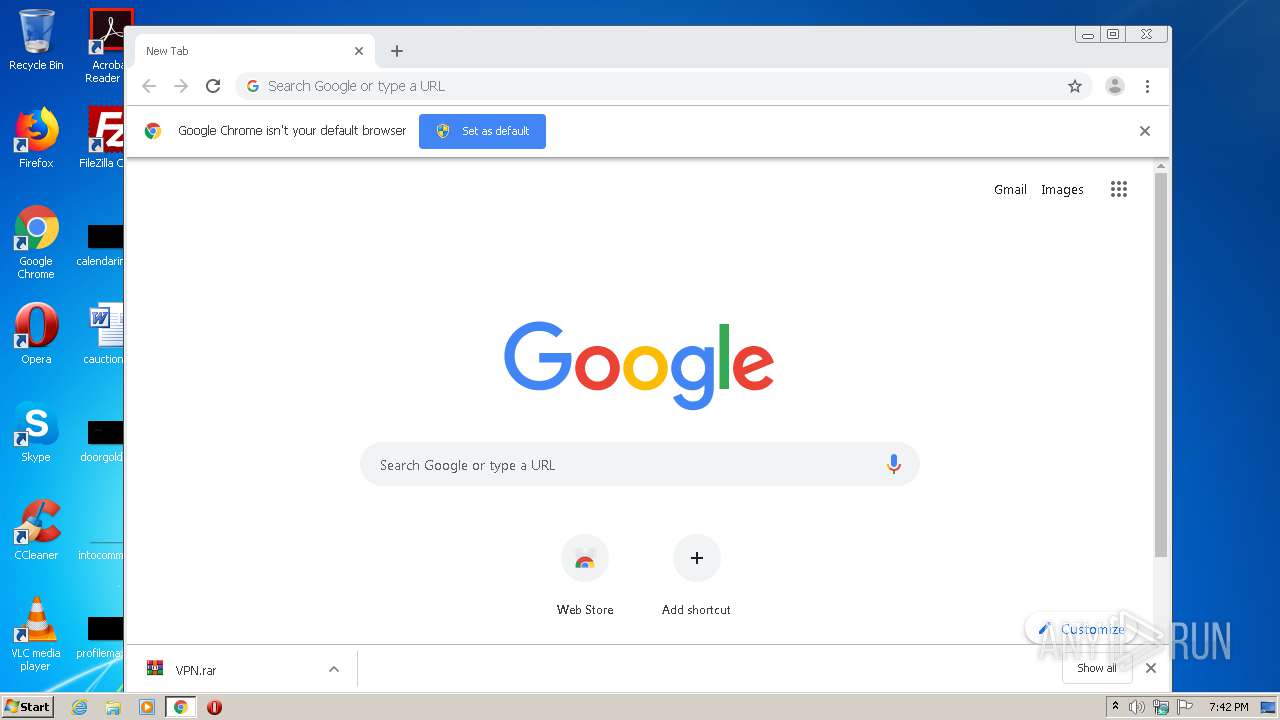
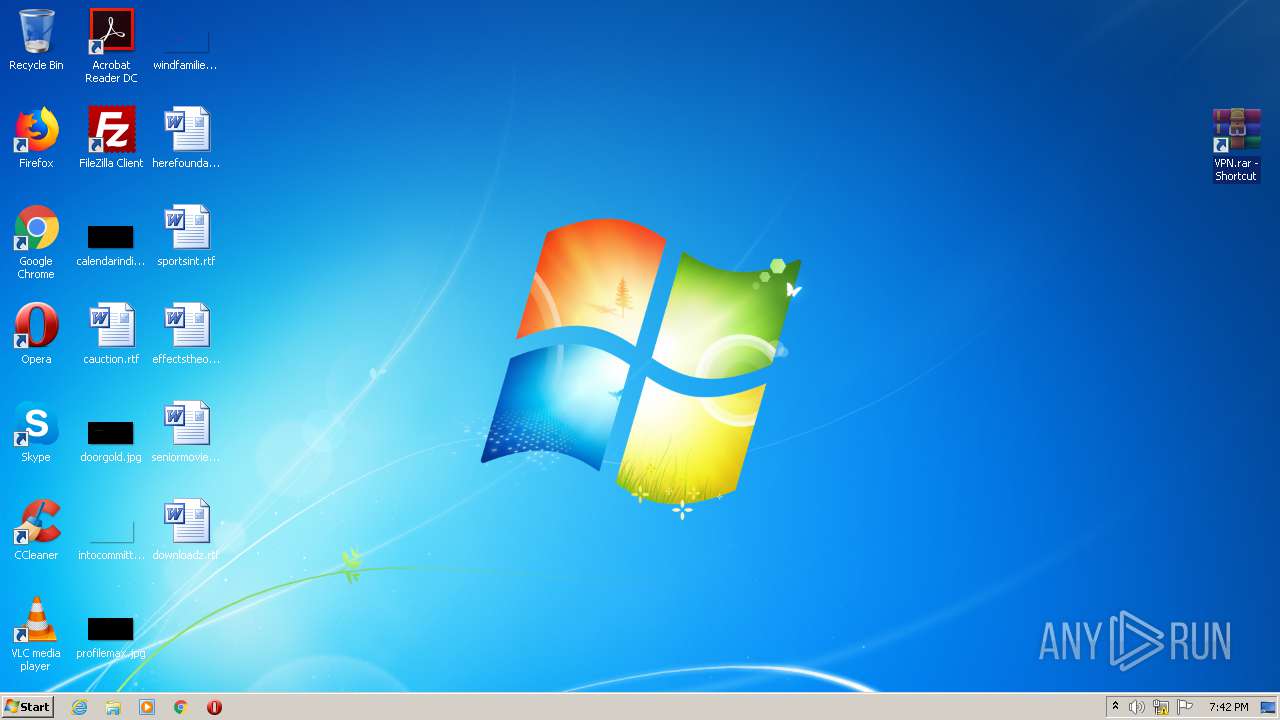
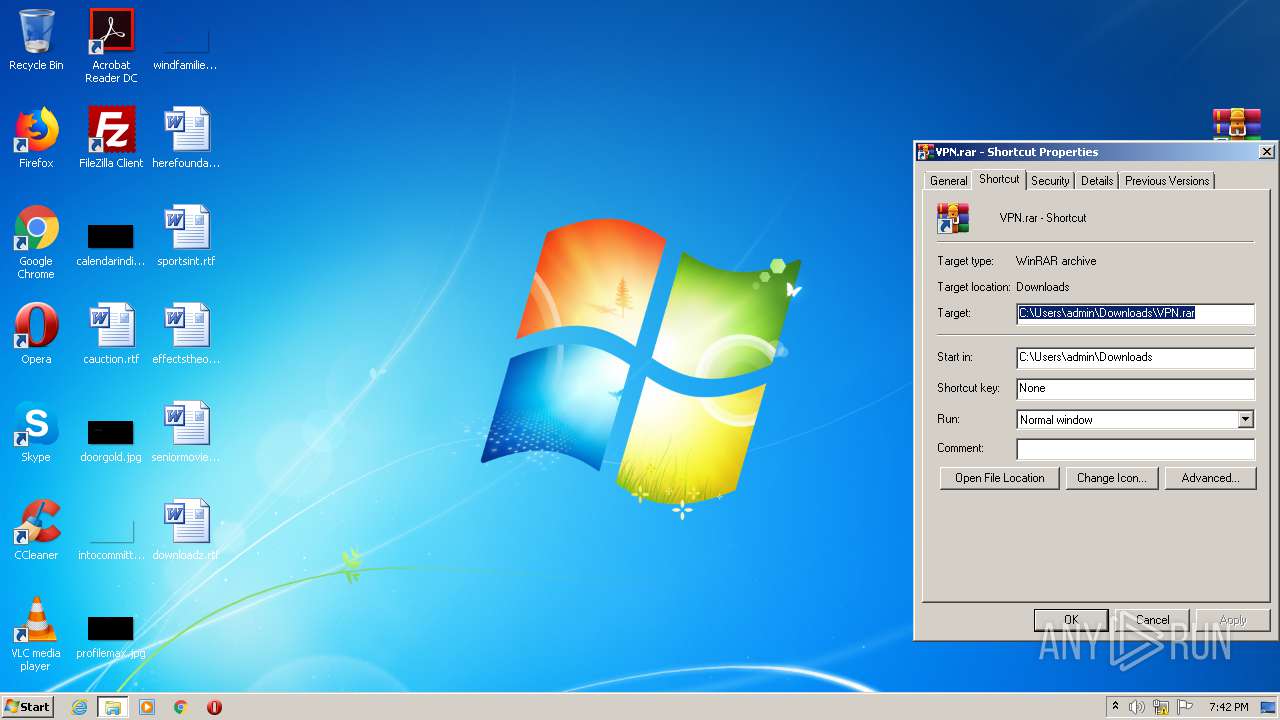
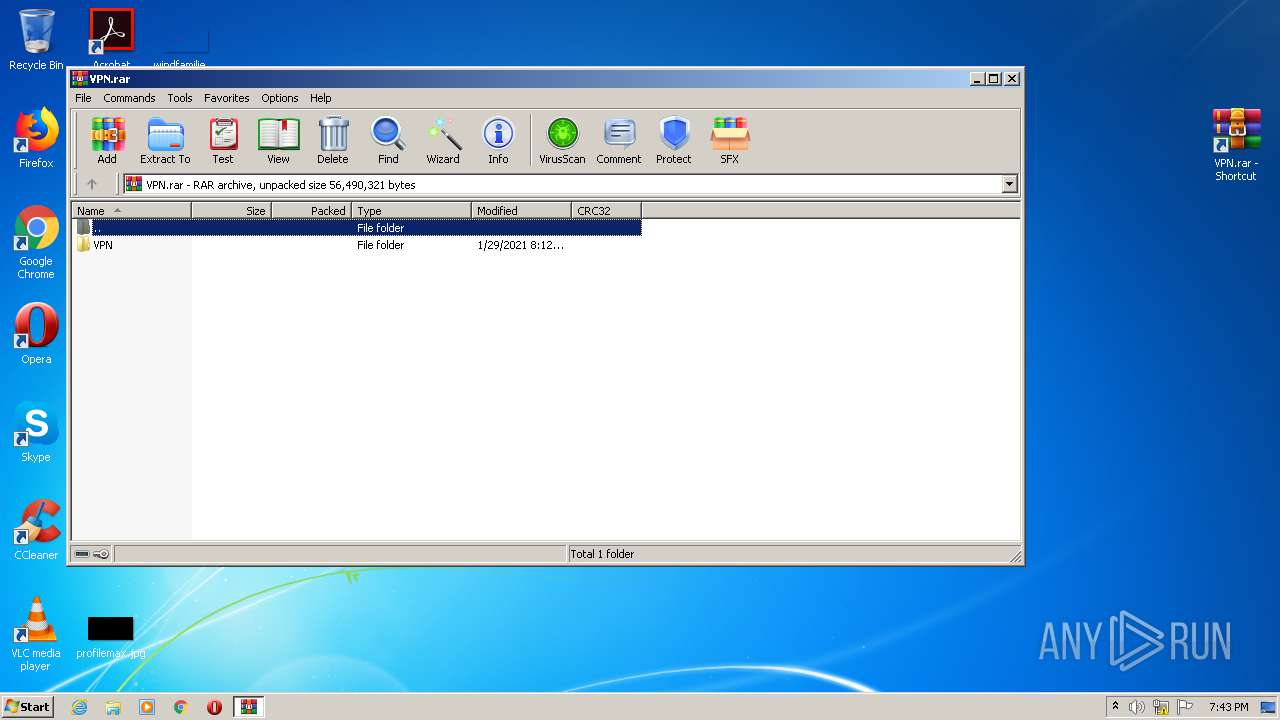
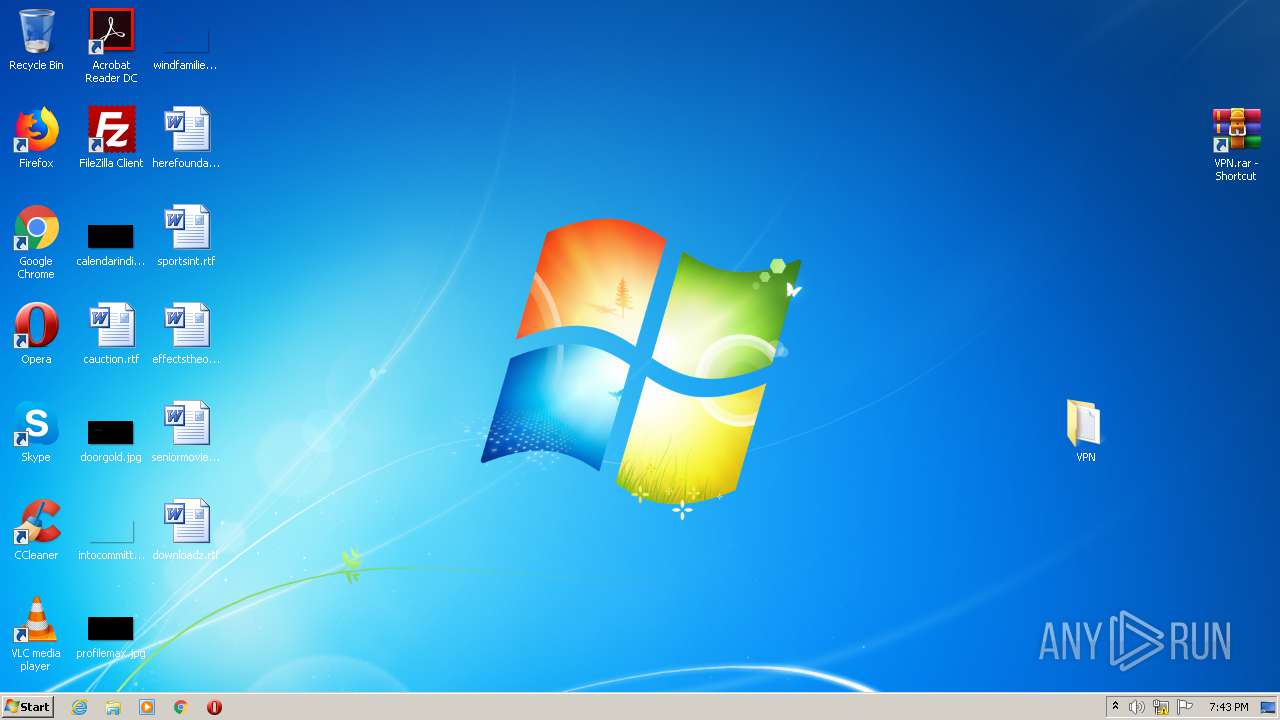
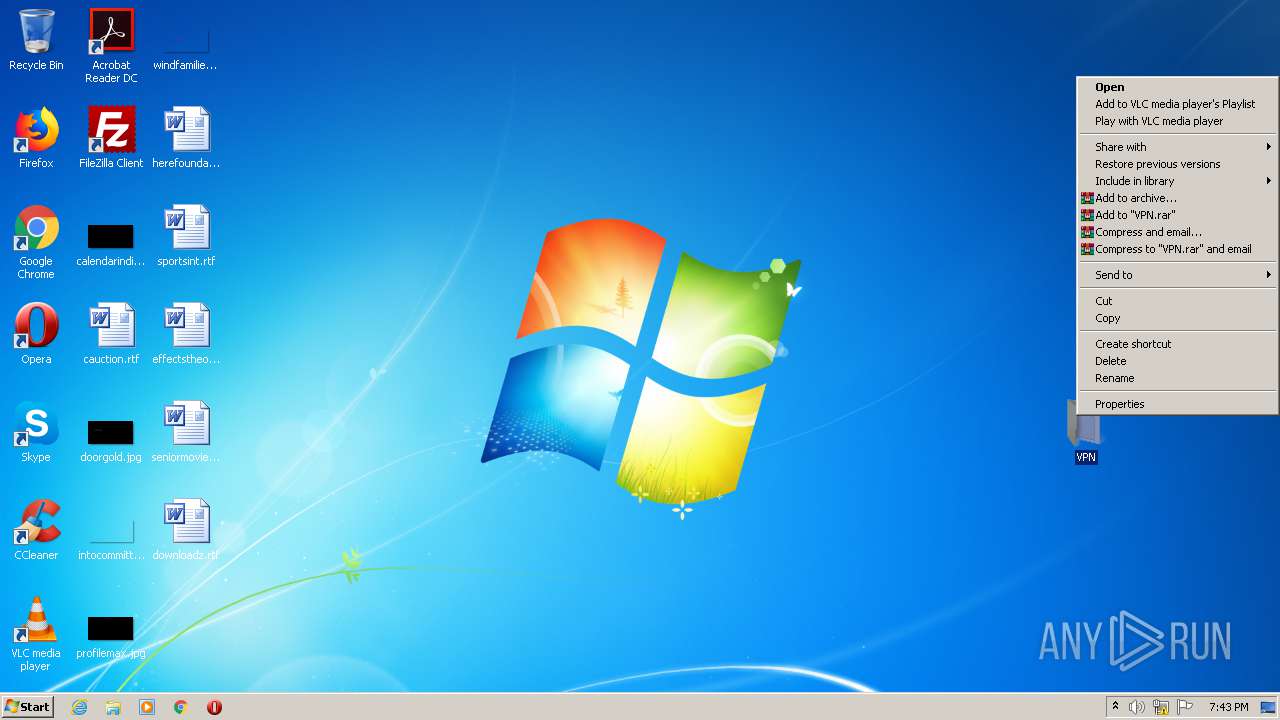
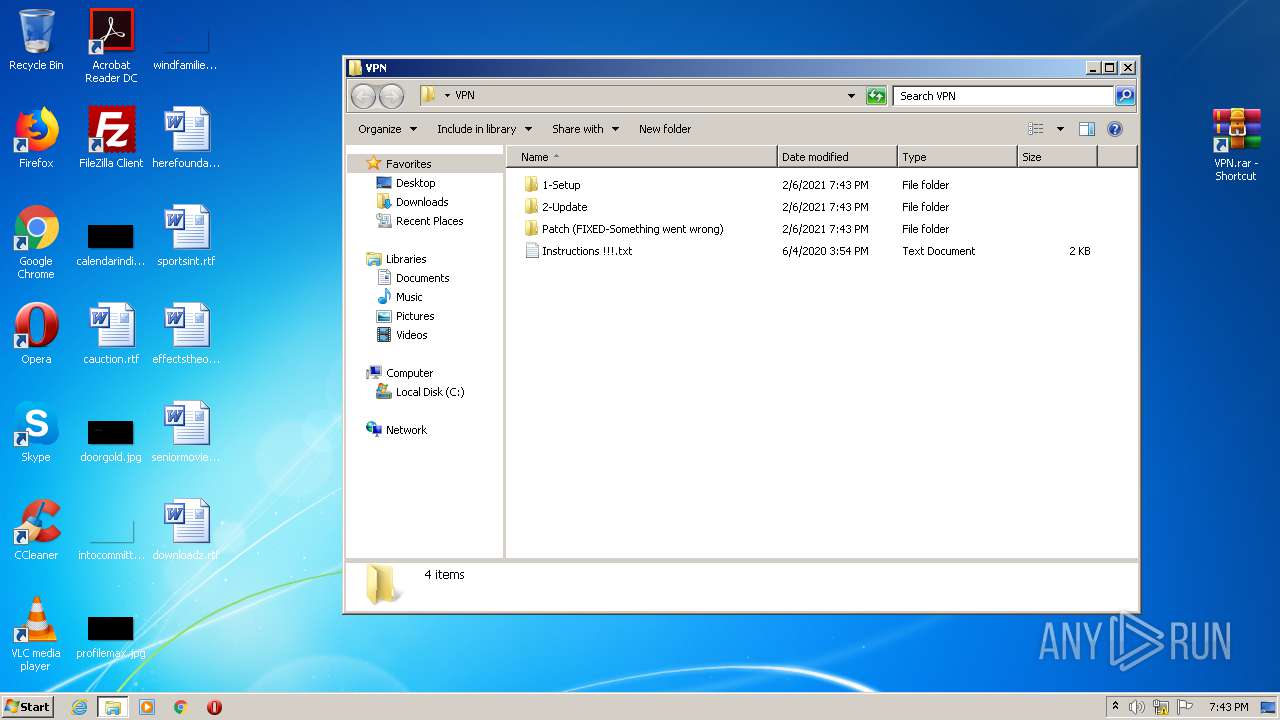
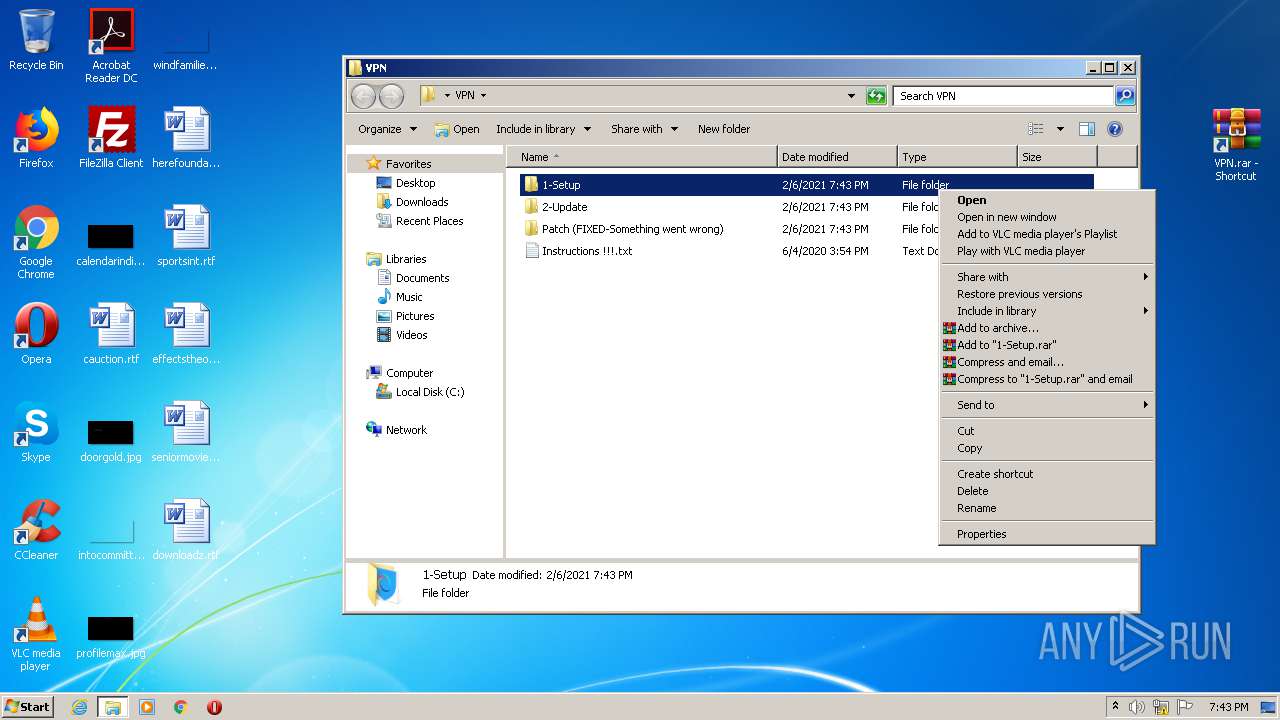
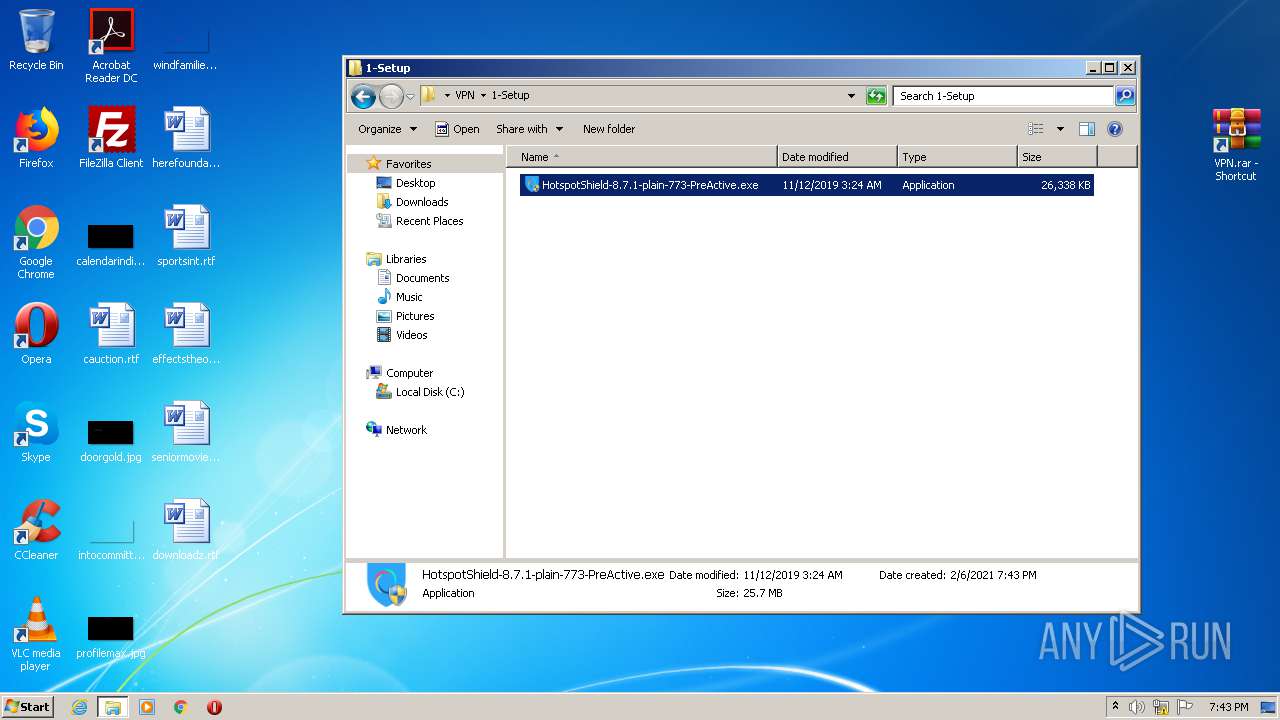
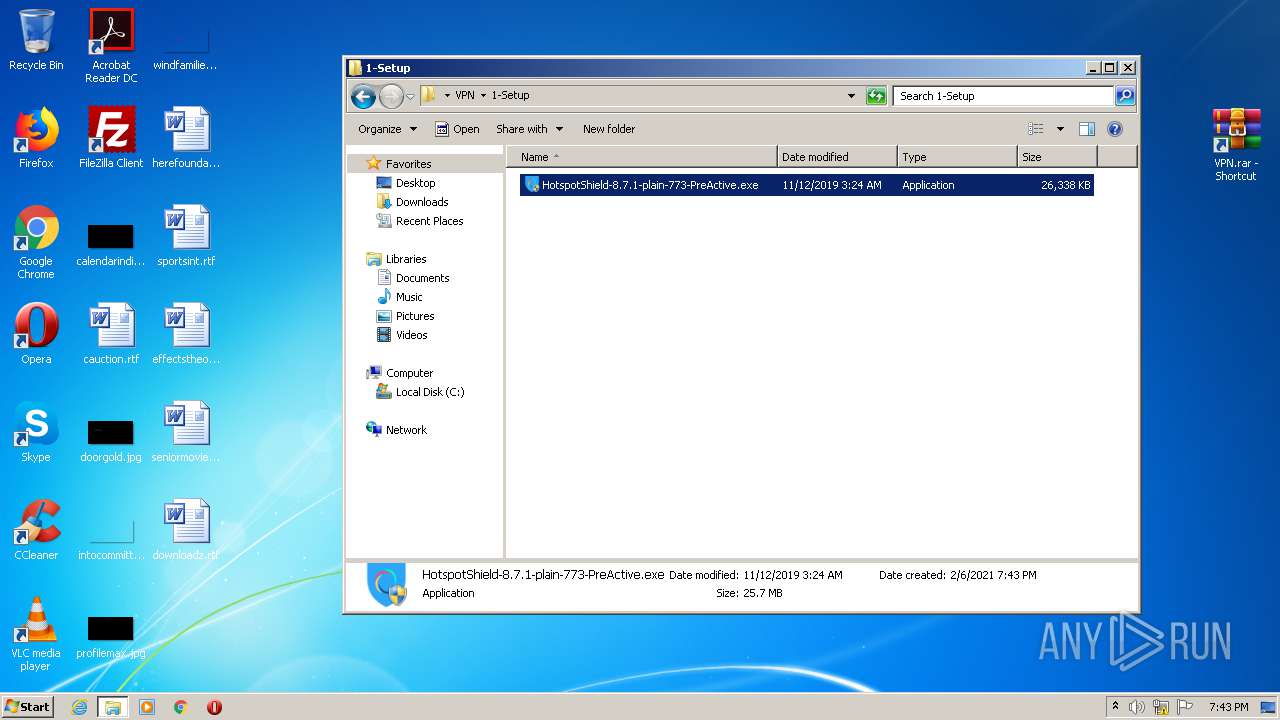
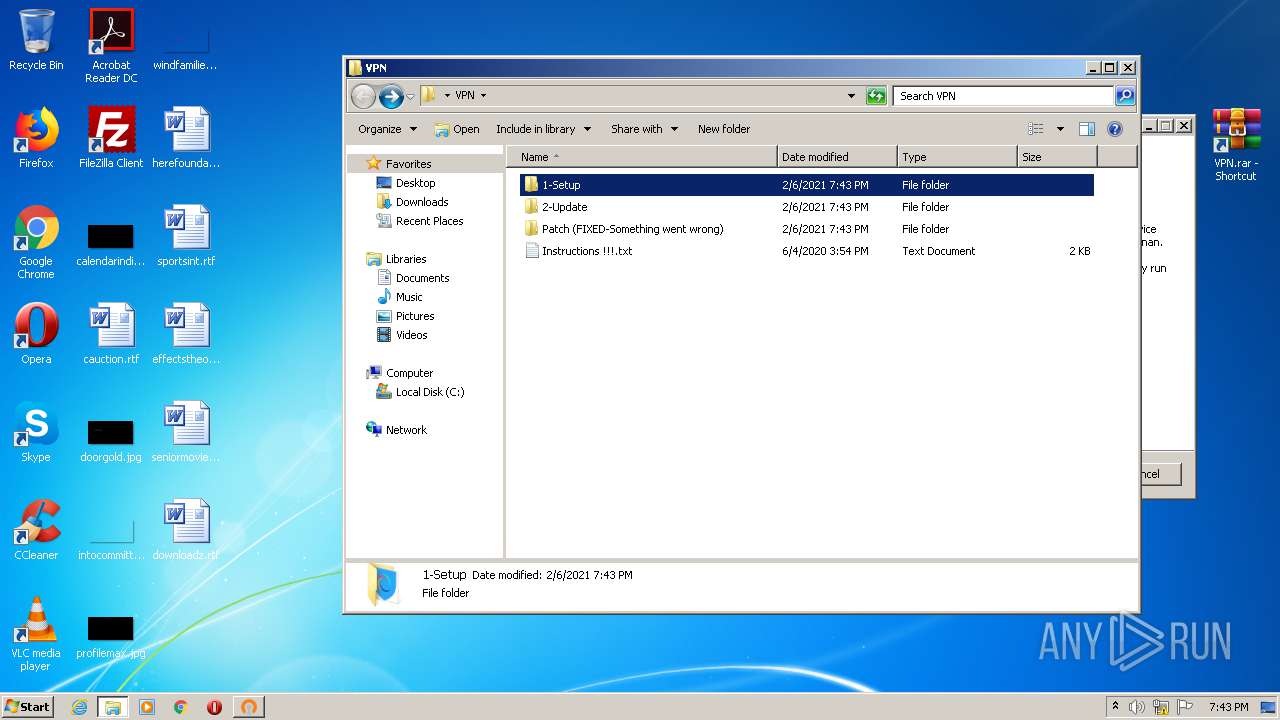
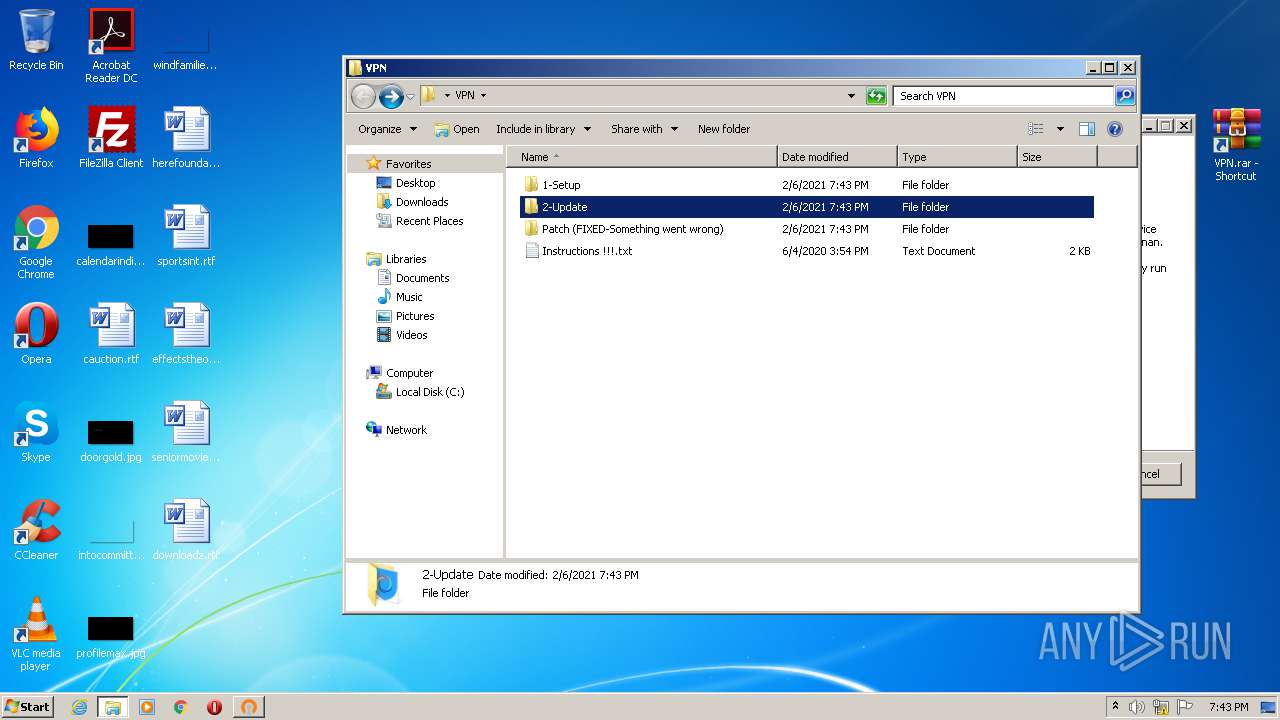
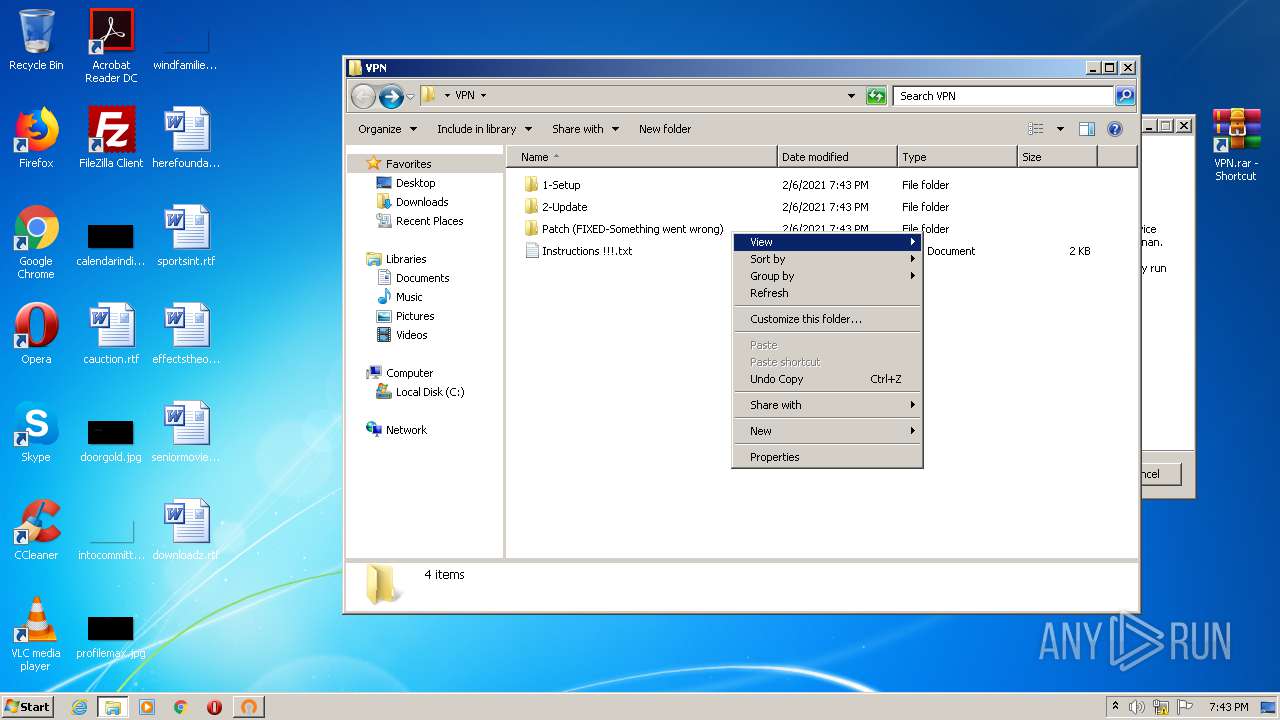
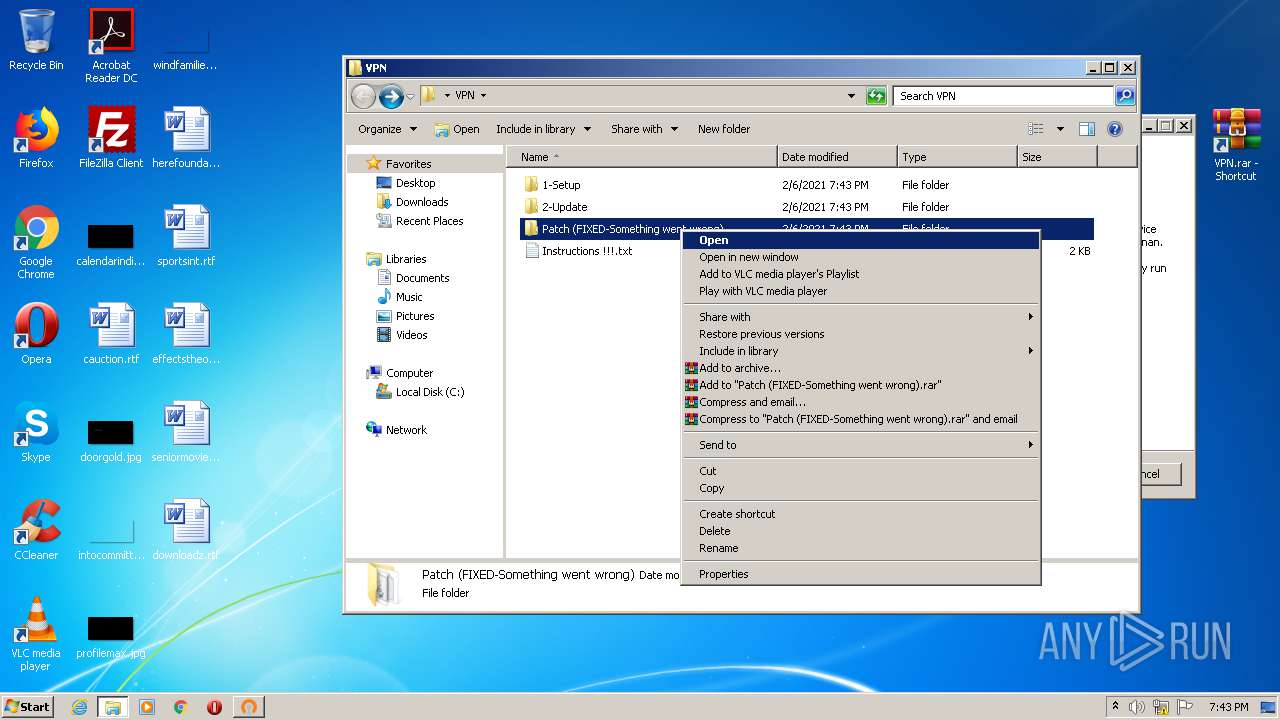
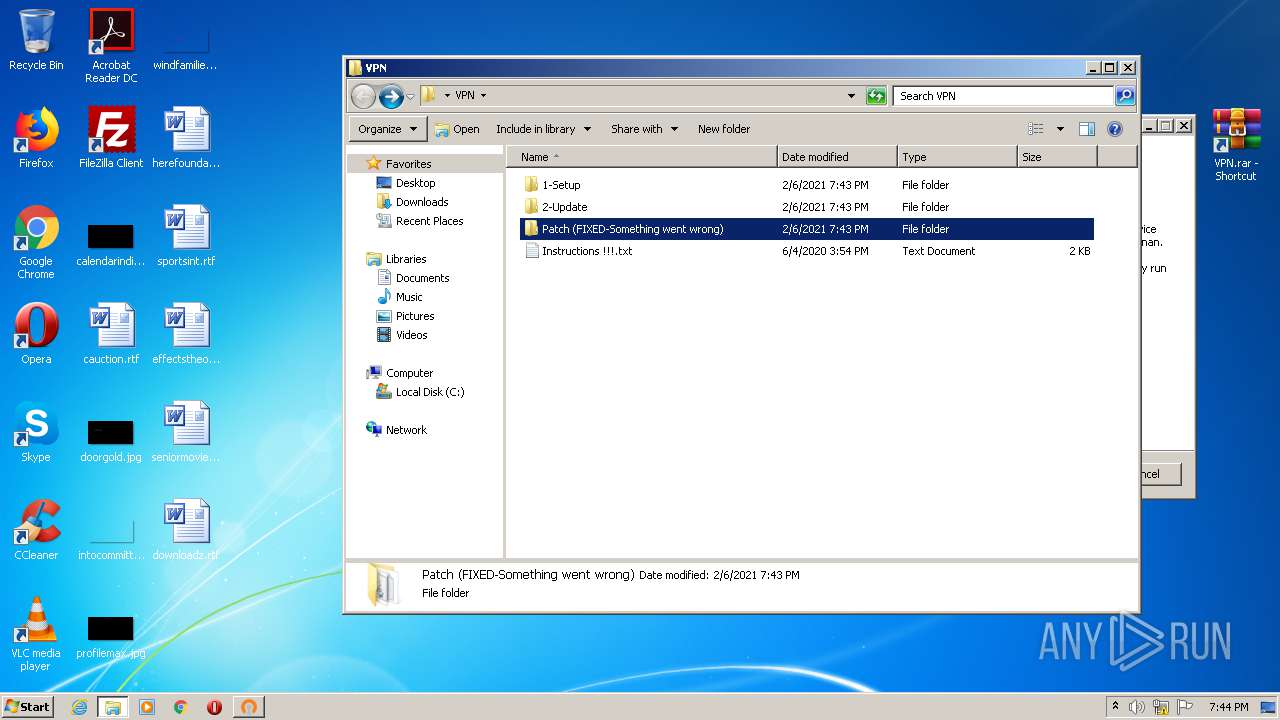
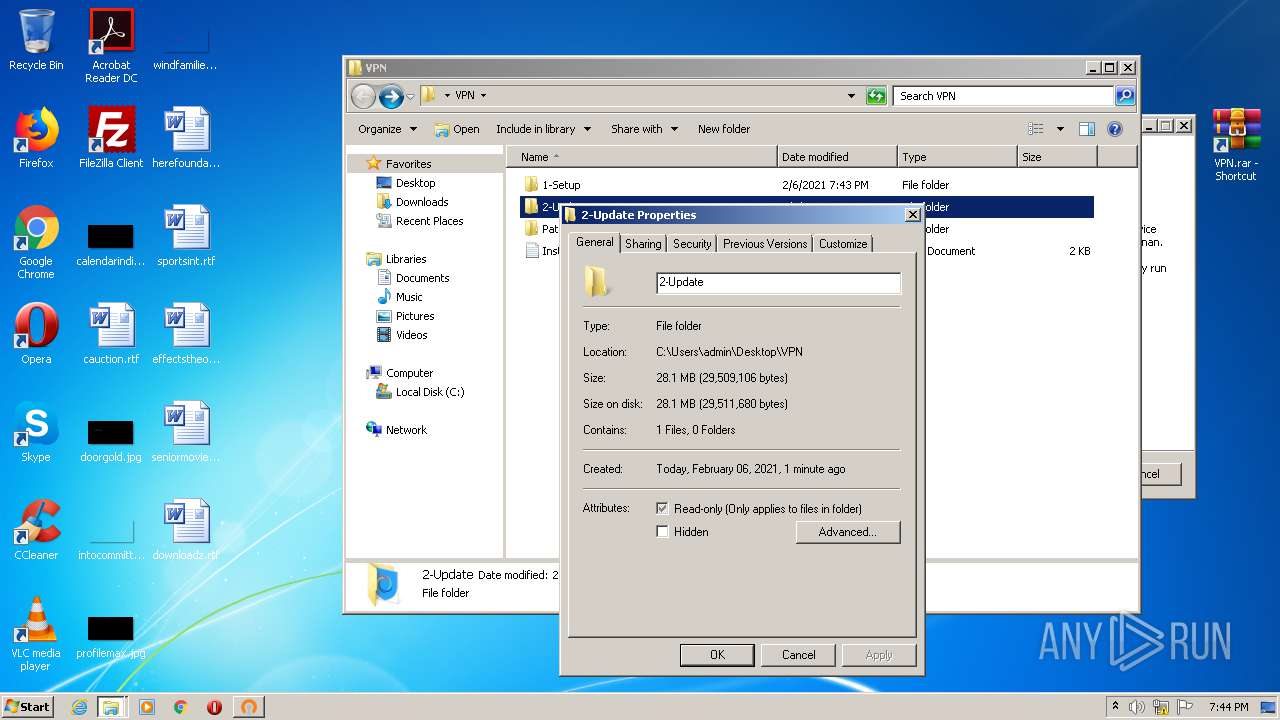
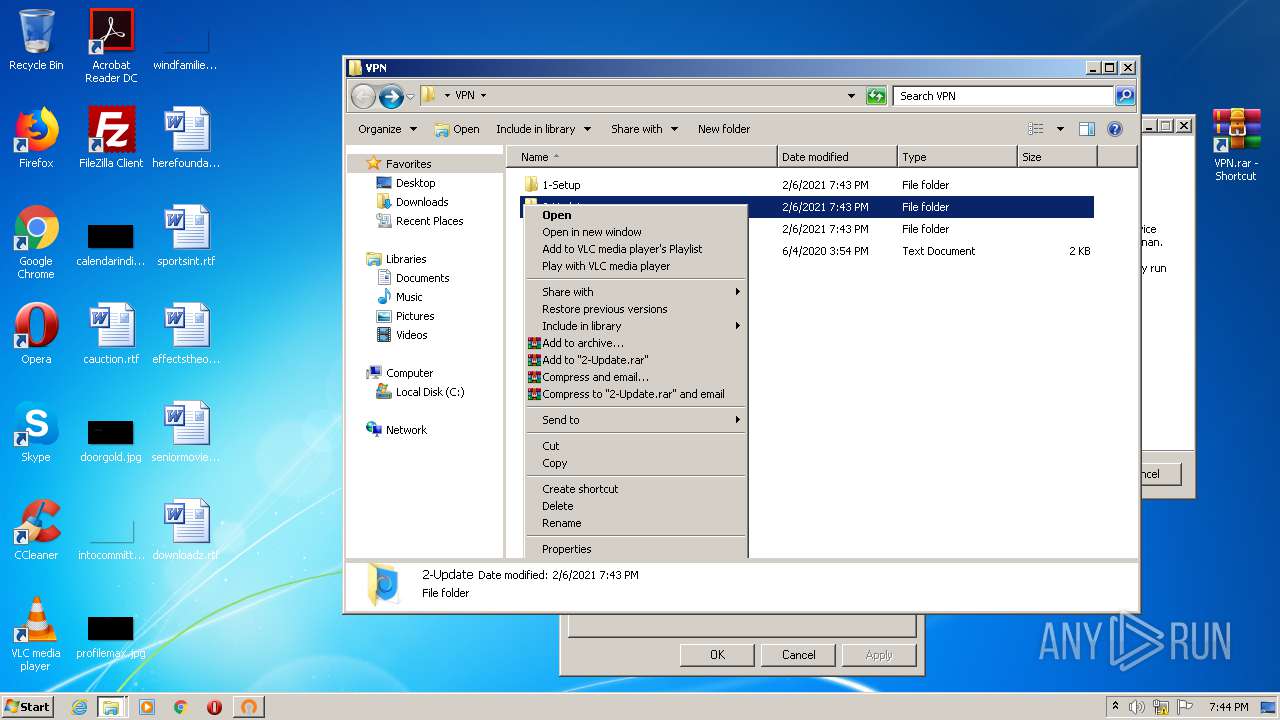
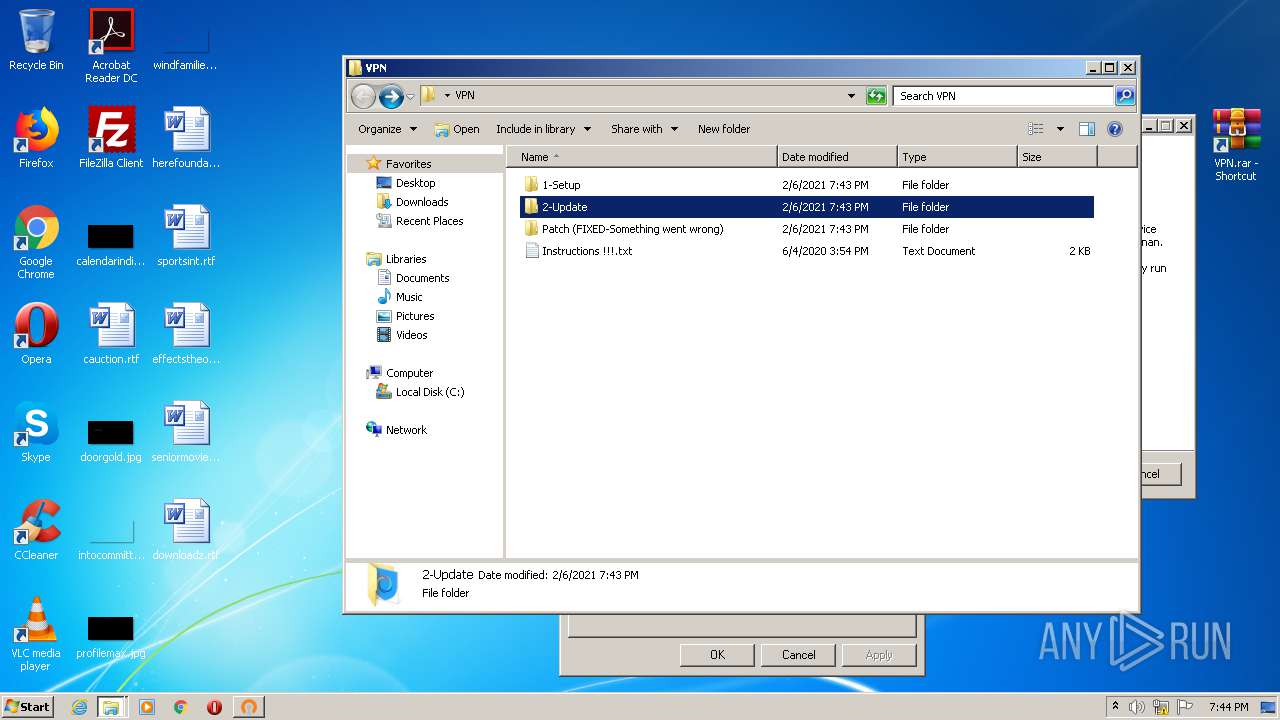
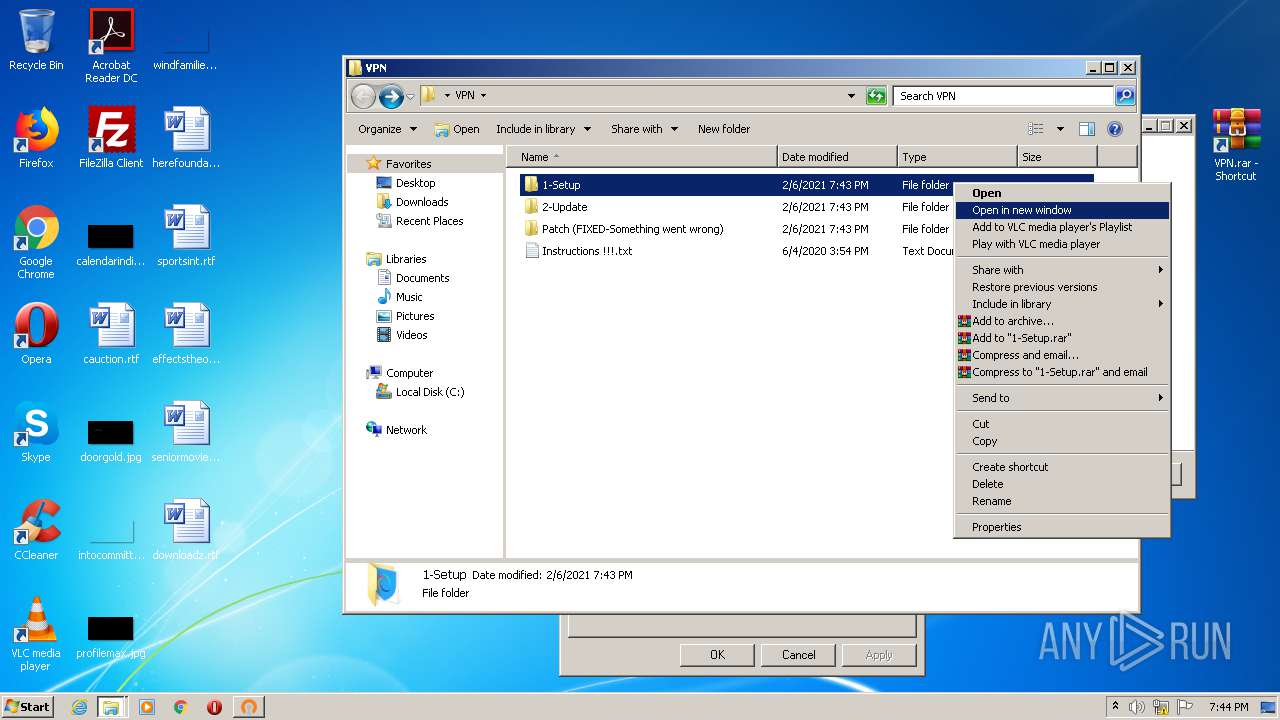
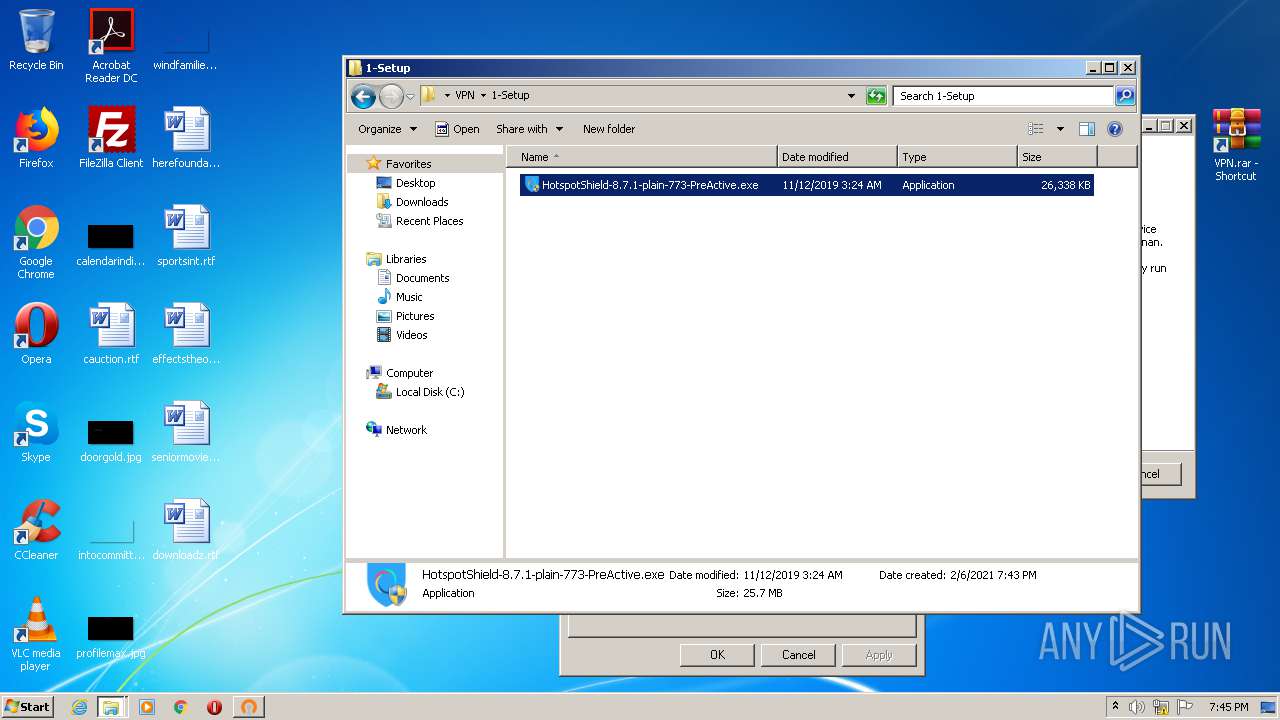
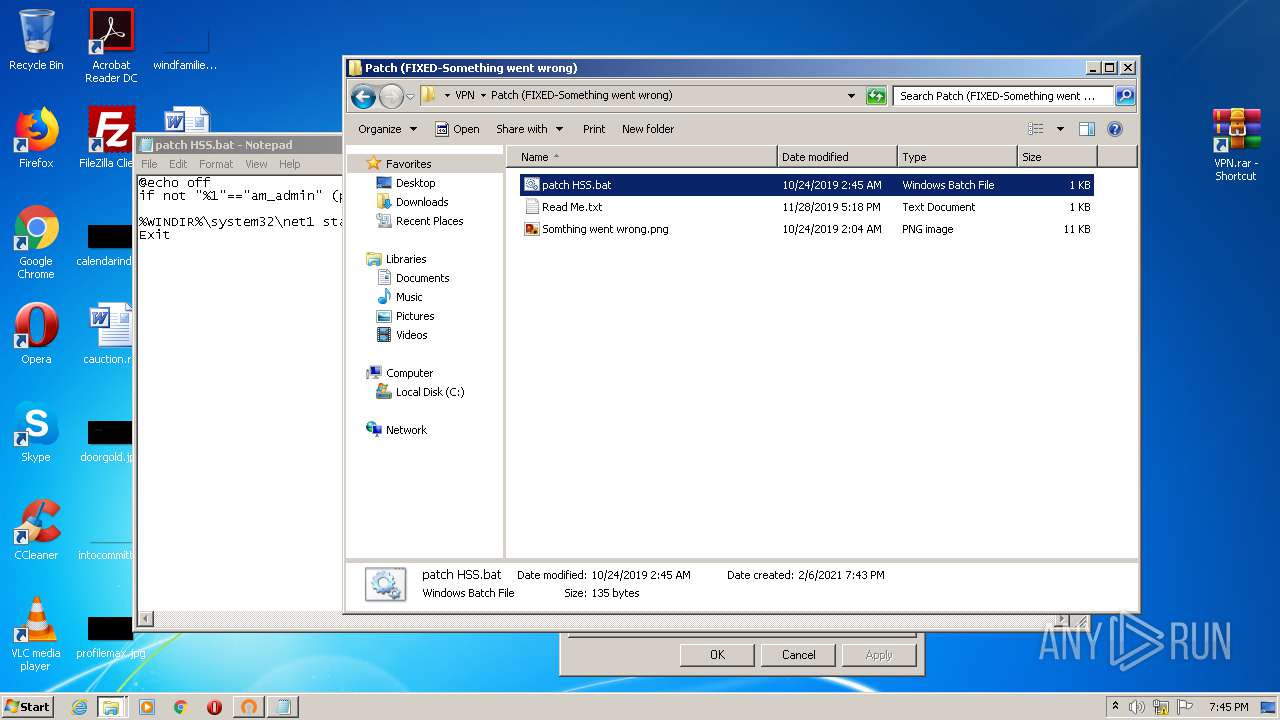
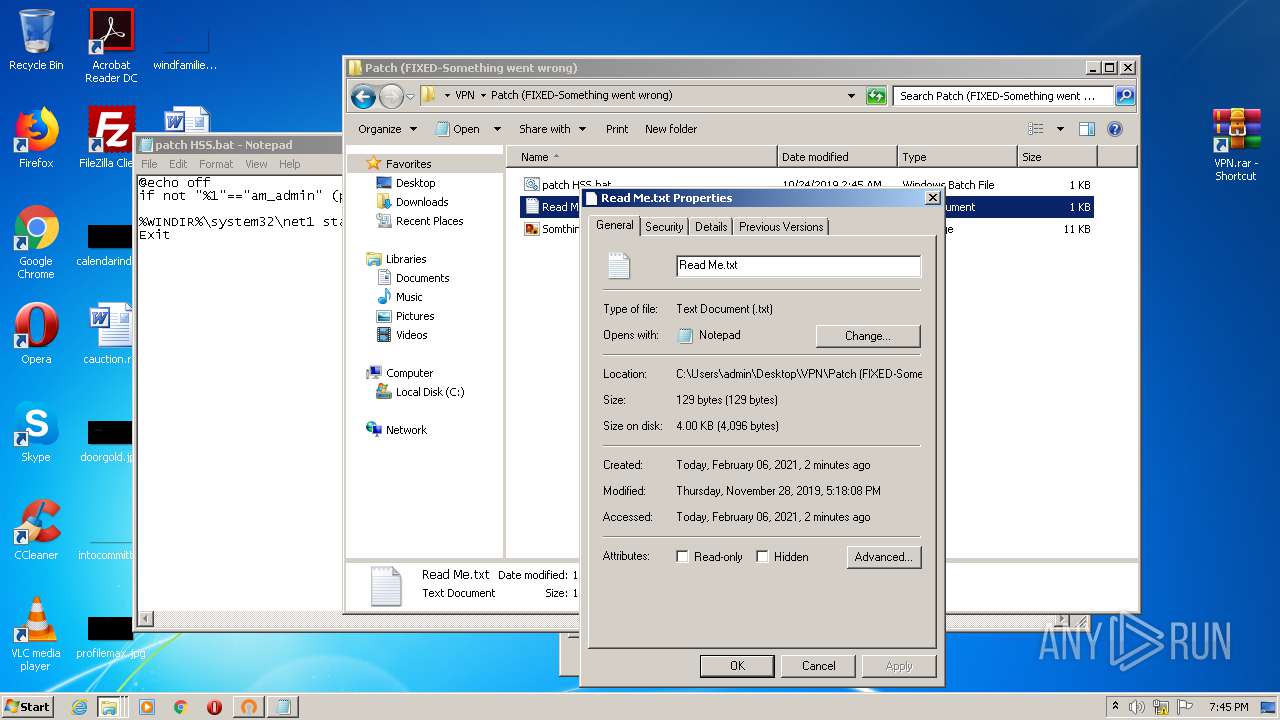
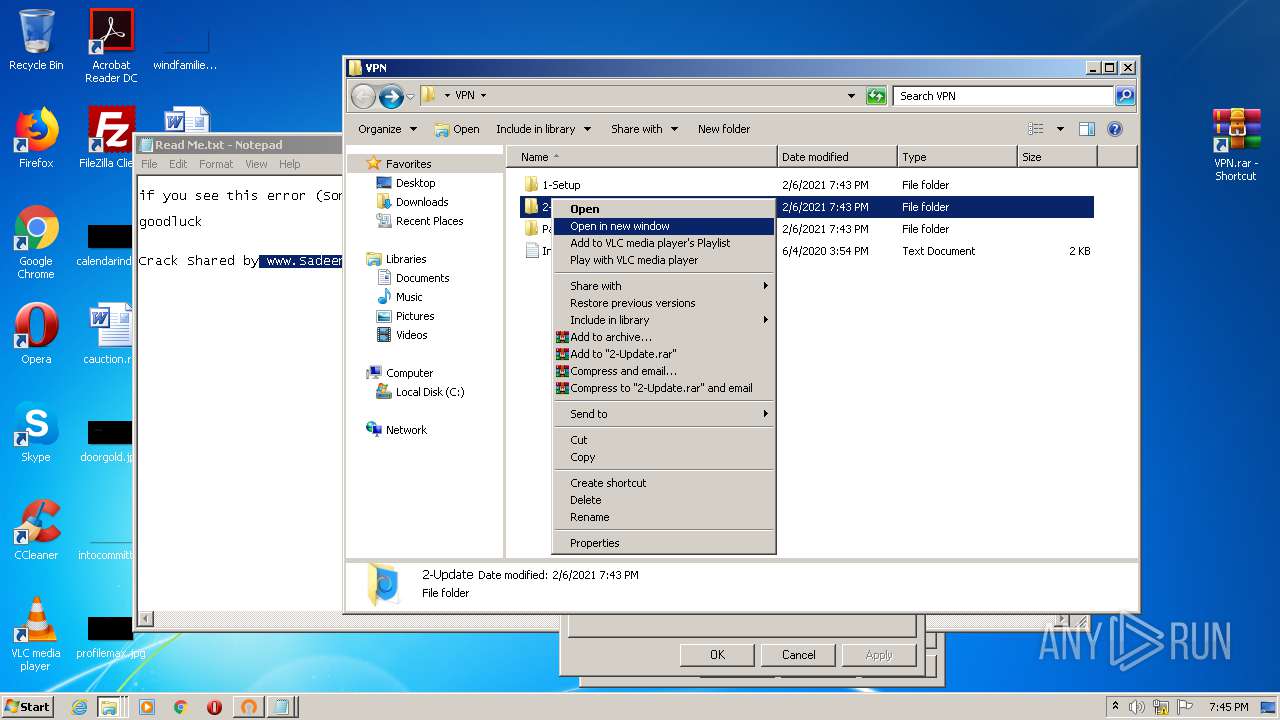
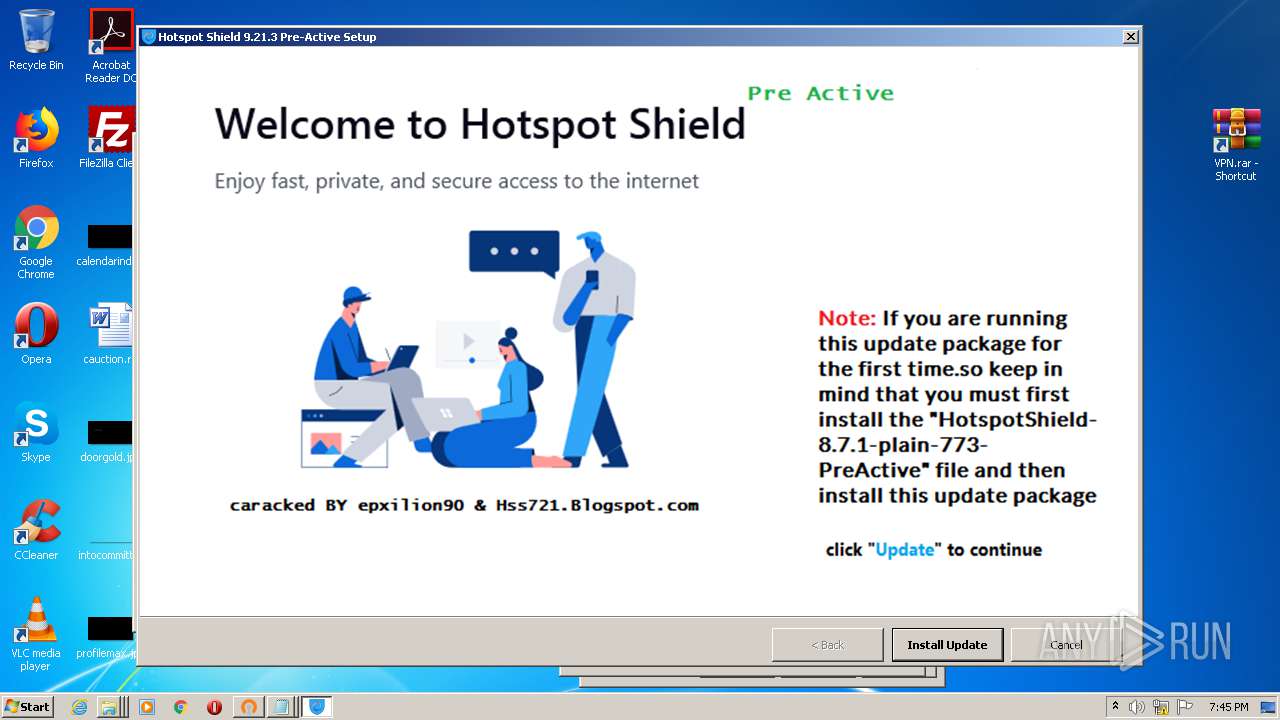
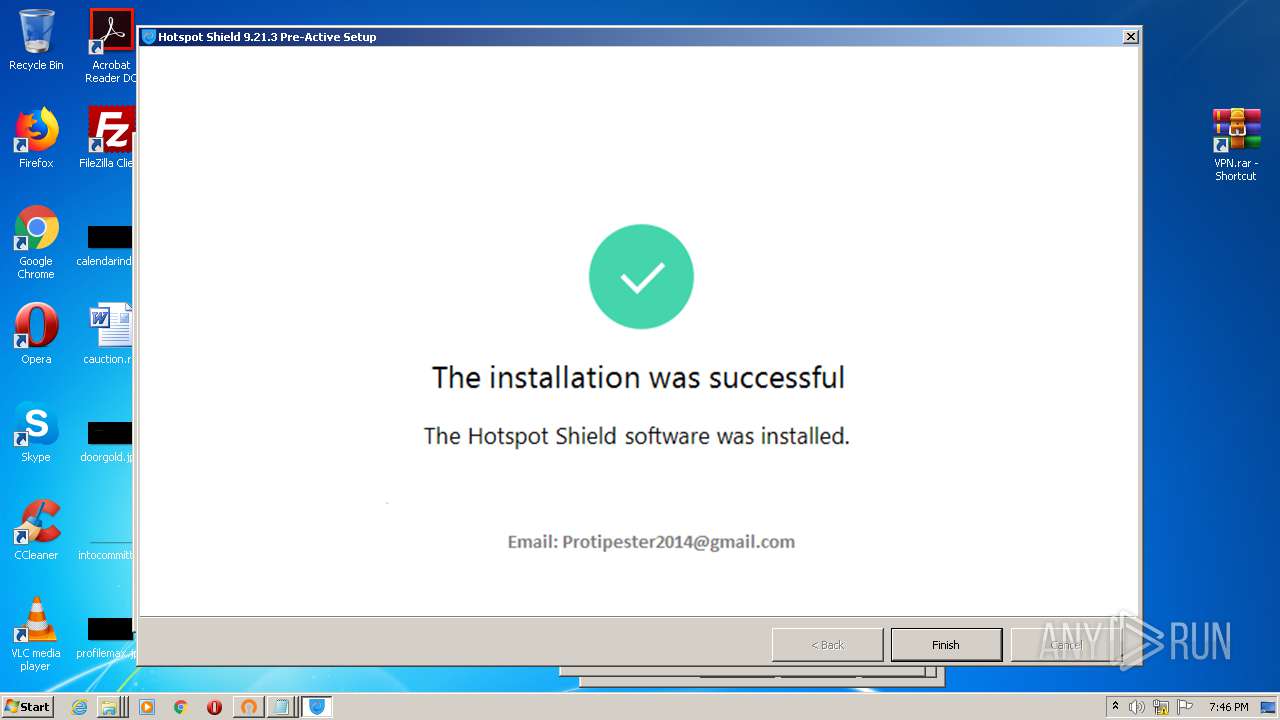
Manual execution by user
- chrome.exe (PID: 2800)
- WinRAR.exe (PID: 3228)
- WinRAR.exe (PID: 2580)
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 2088)
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 972)
- cmd.exe (PID: 1584)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 3416)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 2016)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 3328)
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 4024)
- HotspotShield-8.7.1-plain-773-PreActive.exe (PID: 952)
- NOTEPAD.EXE (PID: 1220)
- NOTEPAD.EXE (PID: 2388)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 2804)
Application launched itself
- chrome.exe (PID: 2800)
- msiexec.exe (PID: 1644)
Reads the hosts file
- chrome.exe (PID: 2800)
- chrome.exe (PID: 2484)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 3128)
- HSS-9.21.3-nodrv-update-PreActive.exe (PID: 1080)
- msiexec.exe (PID: 1644)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2820)
- MsiExec.exe (PID: 3044)
- MsiExec.exe (PID: 860)
- MsiExec.exe (PID: 2384)
- MsiExec.exe (PID: 2852)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 1644)
Creates a software uninstall entry
- msiexec.exe (PID: 1644)
Reads settings of System Certificates
- cmw_srv.exe (PID: 2516)
Creates files in the program directory
- msiexec.exe (PID: 1644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jpg | | | JFIF-EXIF JPEG Bitmap (55.5) |
|---|---|---|
| .jpg | | | JPEG bitmap (33.3) |
| .mp3 | | | MP3 audio (11.1) |
EXIF
Composite
| ImageSize: | 564x564 |
|---|---|
| Megapixels: | 0.318 |
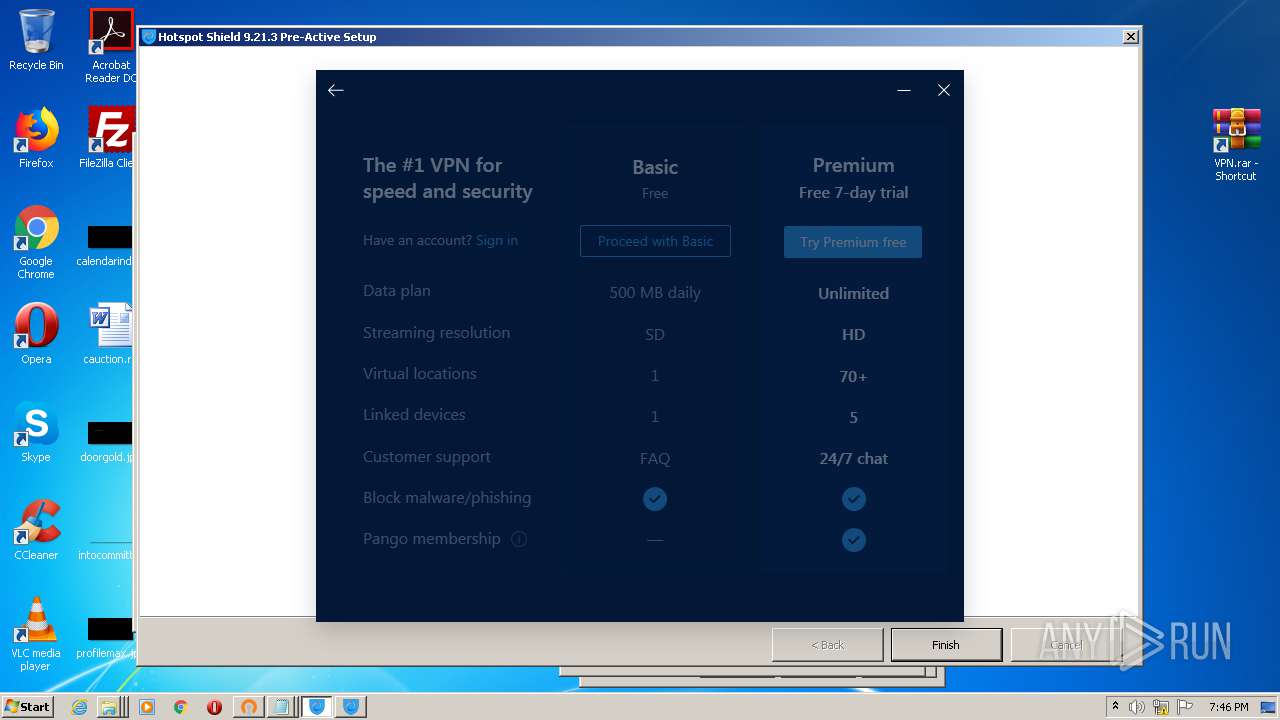
Total processes
130
Monitored processes
67
Malicious processes
14
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,9135827580714482843,17675801233449319125,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9684438492824964041 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,9135827580714482843,17675801233449319125,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3040980628225010250 --mojo-platform-channel-handle=3604 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,9135827580714482843,17675801233449319125,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11645592498879167387 --mojo-platform-channel-handle=3692 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 860 | C:\Windows\system32\MsiExec.exe -Embedding 43D9C1E9710E271146CE89A3DC0B8EBA | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
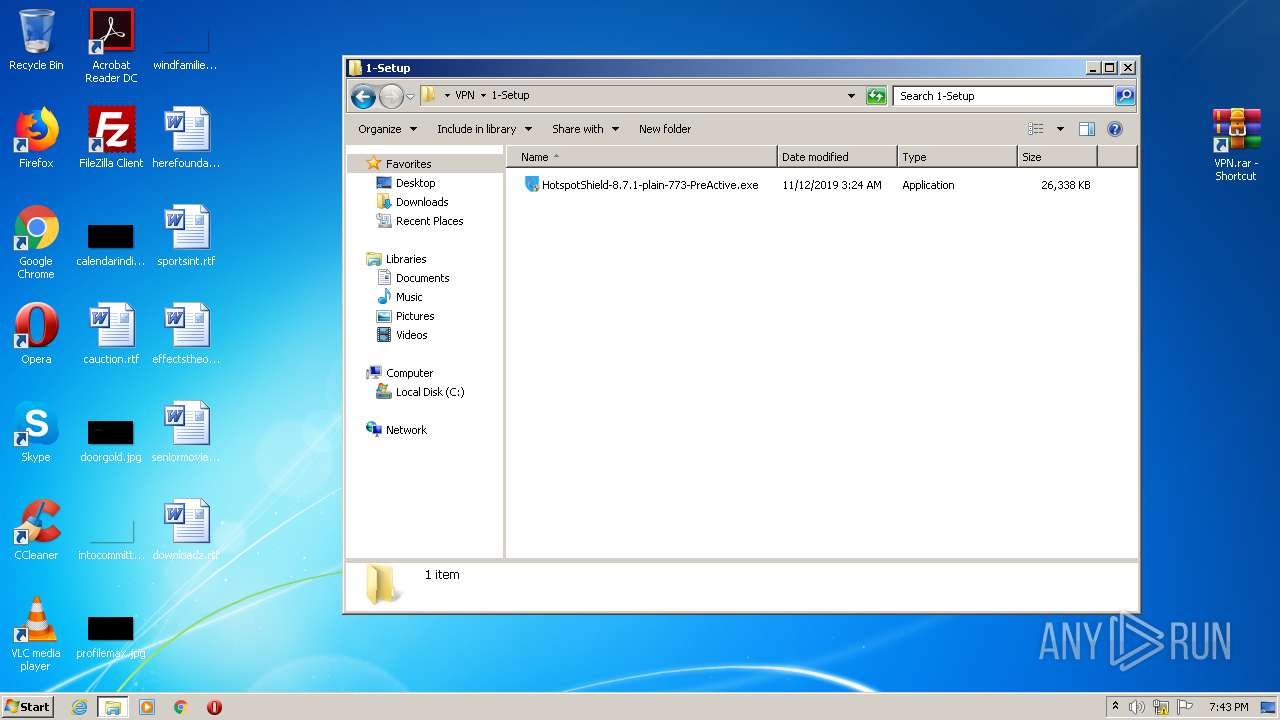
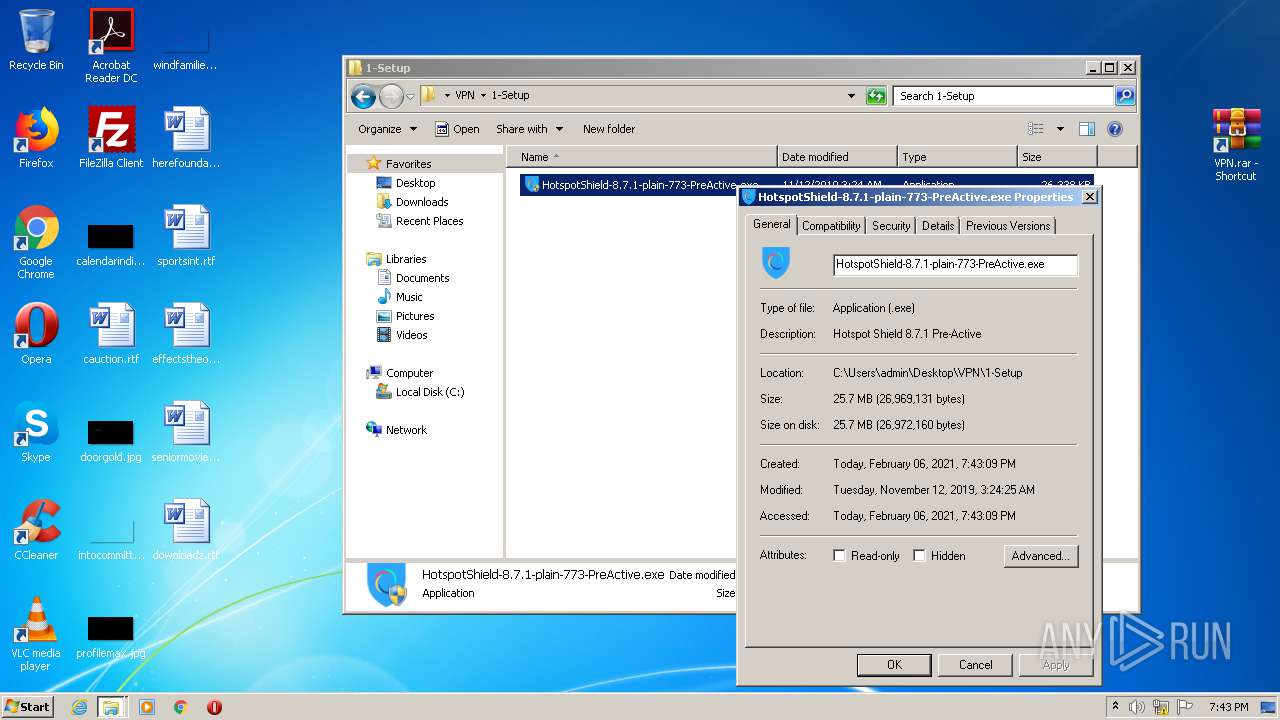
| 952 | "C:\Users\admin\Desktop\VPN\1-Setup\HotspotShield-8.7.1-plain-773-PreActive.exe" | C:\Users\admin\Desktop\VPN\1-Setup\HotspotShield-8.7.1-plain-773-PreActive.exe | explorer.exe | ||||||||||||
User: admin Company: hss721.blogspot.com Integrity Level: HIGH Description: Hotspot Shield 8.7.1 Pre-Active Exit code: 0 Version: 8.7.1.11380 Modules
| |||||||||||||||
| 972 | "C:\Users\admin\Desktop\VPN\1-Setup\HotspotShield-8.7.1-plain-773-PreActive.exe" | C:\Users\admin\Desktop\VPN\1-Setup\HotspotShield-8.7.1-plain-773-PreActive.exe | — | explorer.exe | |||||||||||
User: admin Company: hss721.blogspot.com Integrity Level: MEDIUM Description: Hotspot Shield 8.7.1 Pre-Active Exit code: 3221226540 Version: 8.7.1.11380 Modules
| |||||||||||||||
| 1080 | "C:\Users\admin\AppData\Local\Turbo.net\Sandbox\Hotspot Shield 9.21.3 Pre-Active\9.21.3.11422\local\stubexe\0x79A60C24E2CB02F7\HSS-9.21.3-nodrv-update-PreActive.exe" /864A627C-C6B2-464A-AA13-25D62F282BD8 | C:\Users\admin\Desktop\HSS-9.21.3-nodrv-update-PreActive.exe | HSS-9.21.3-nodrv-update-PreActive.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
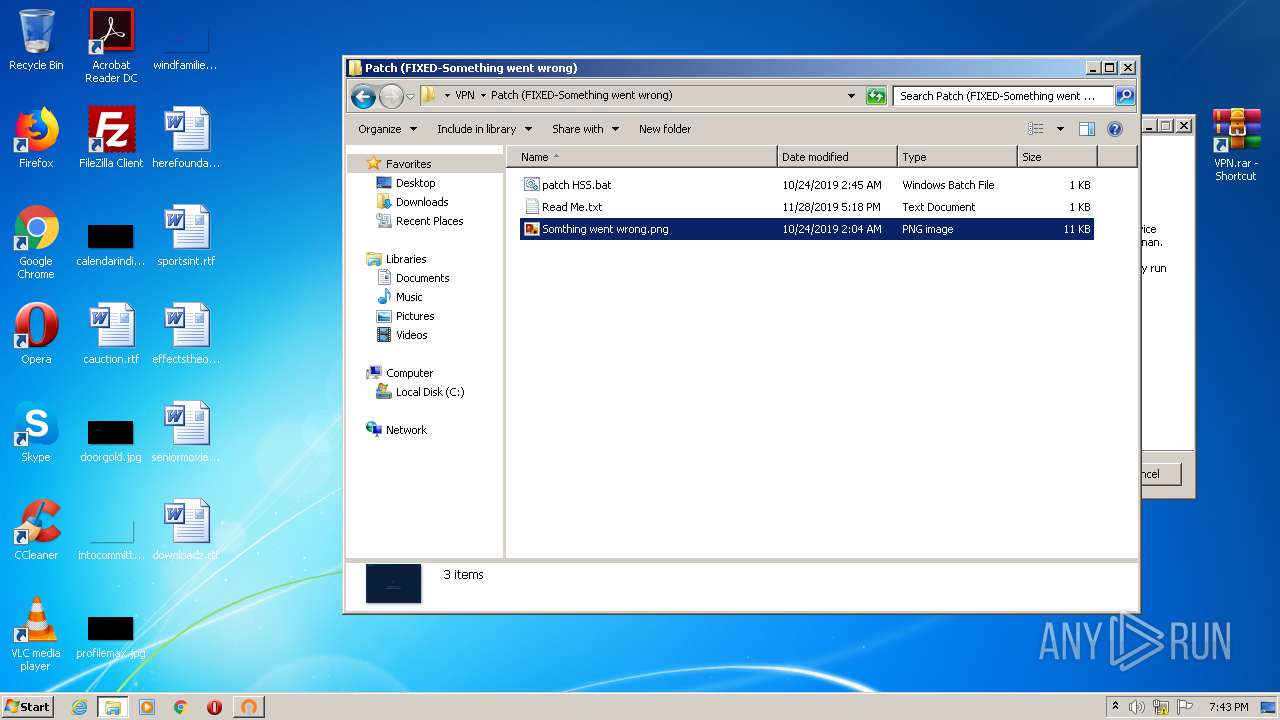
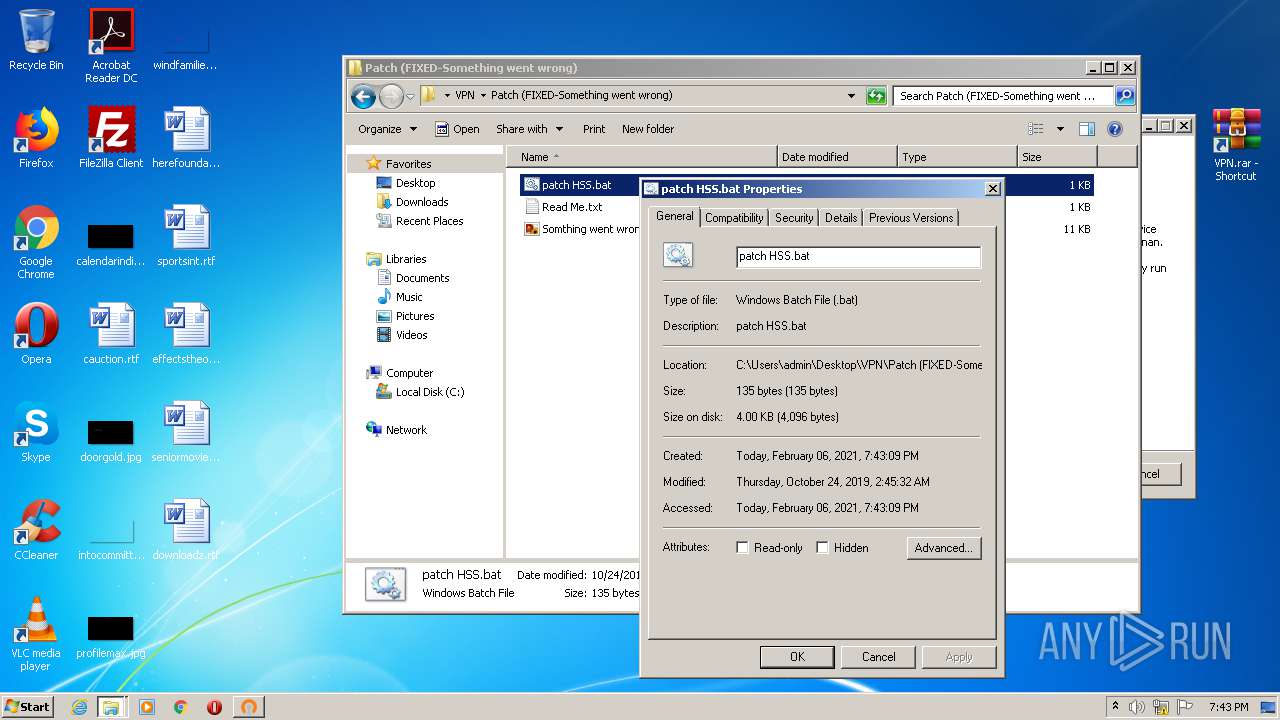
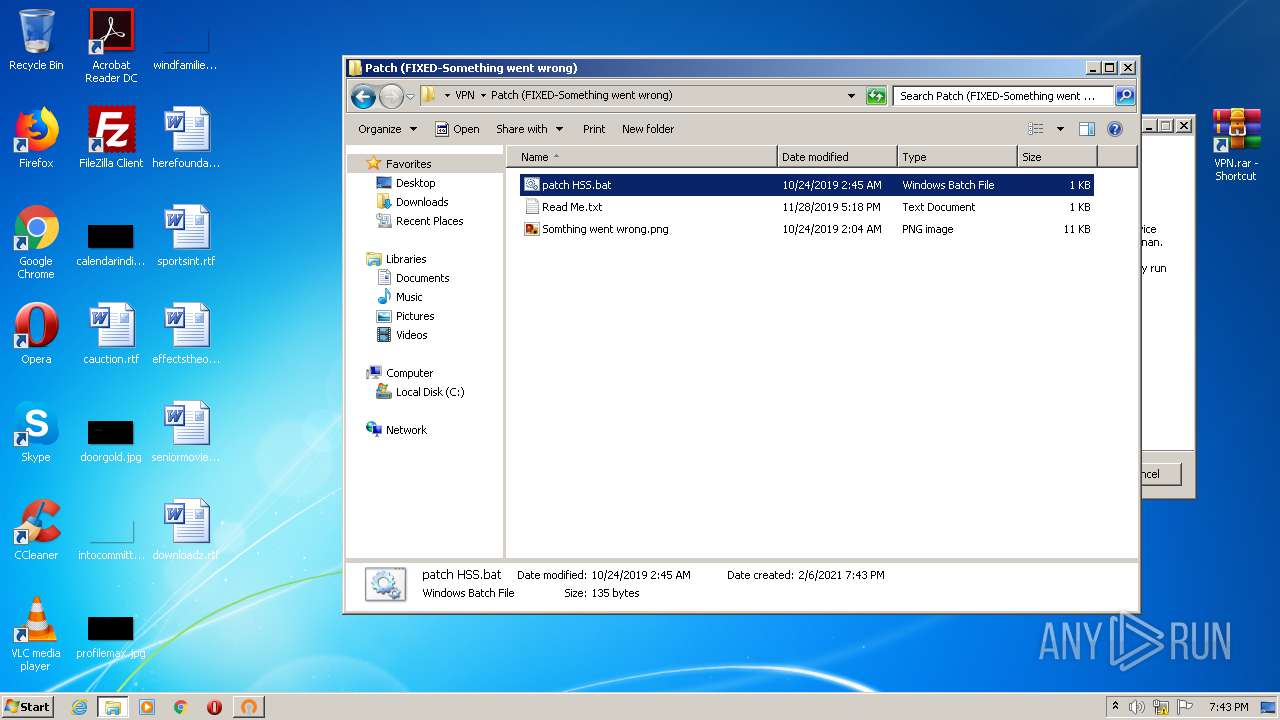
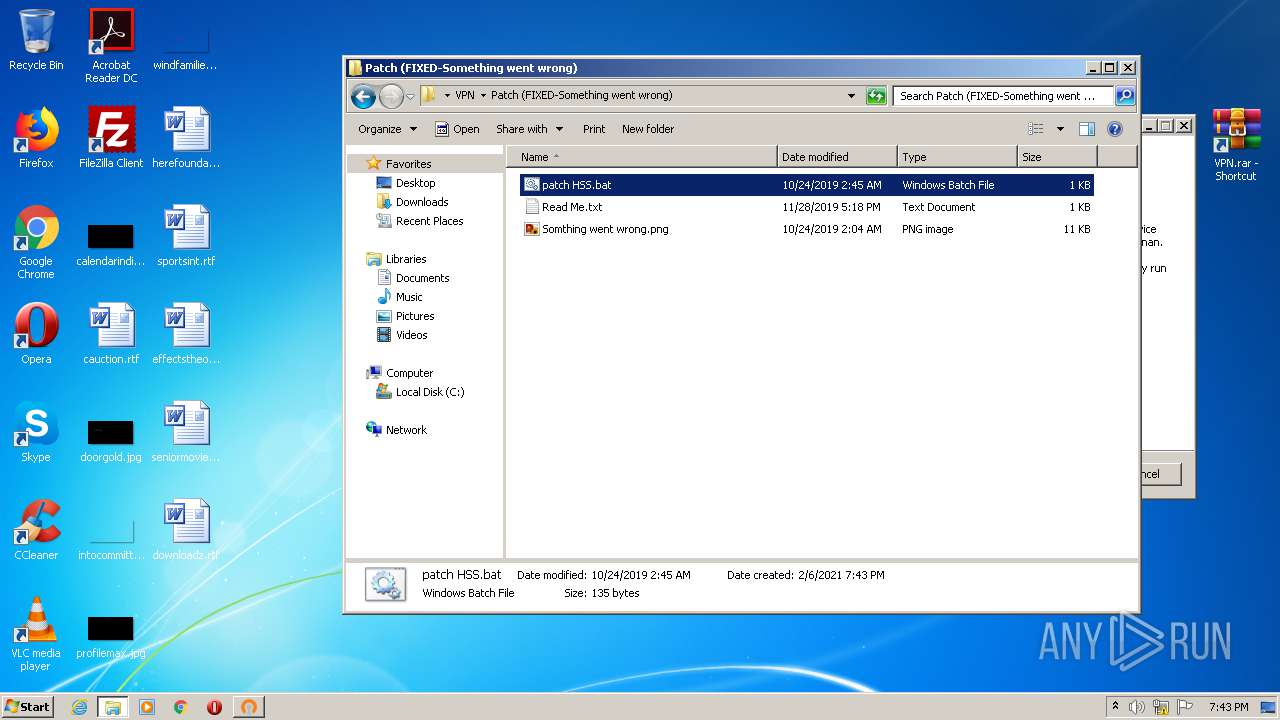
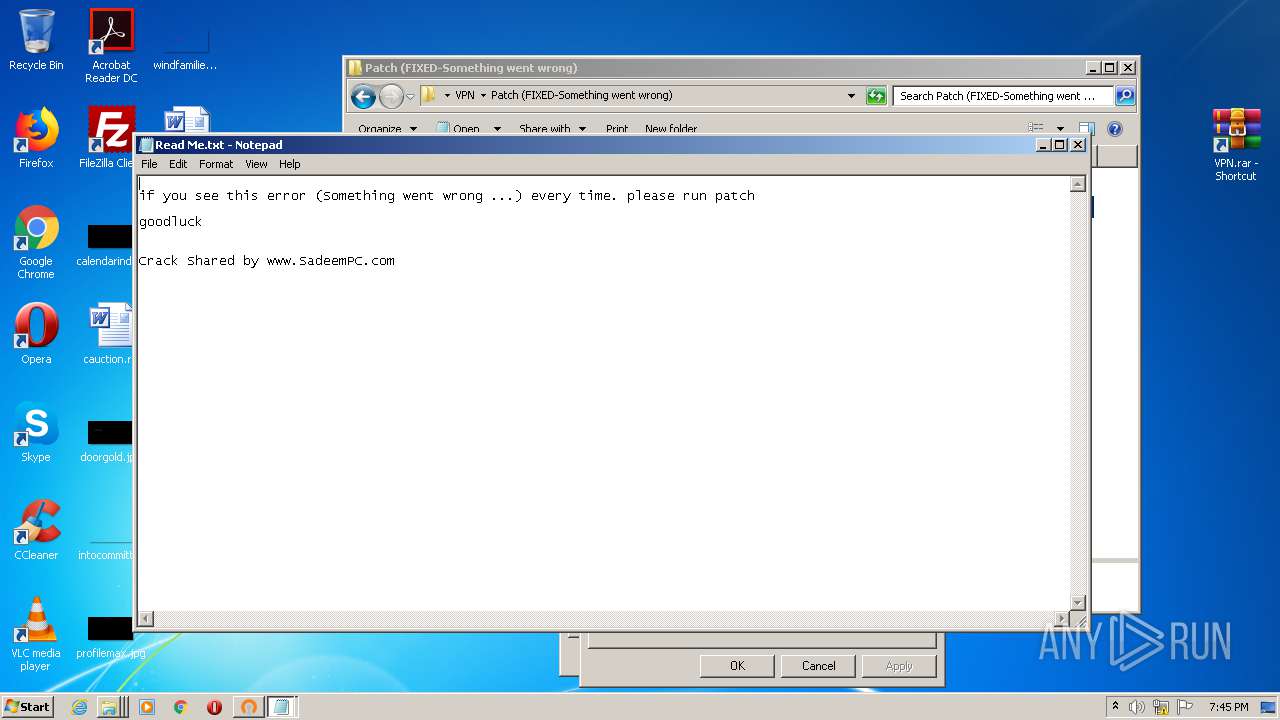
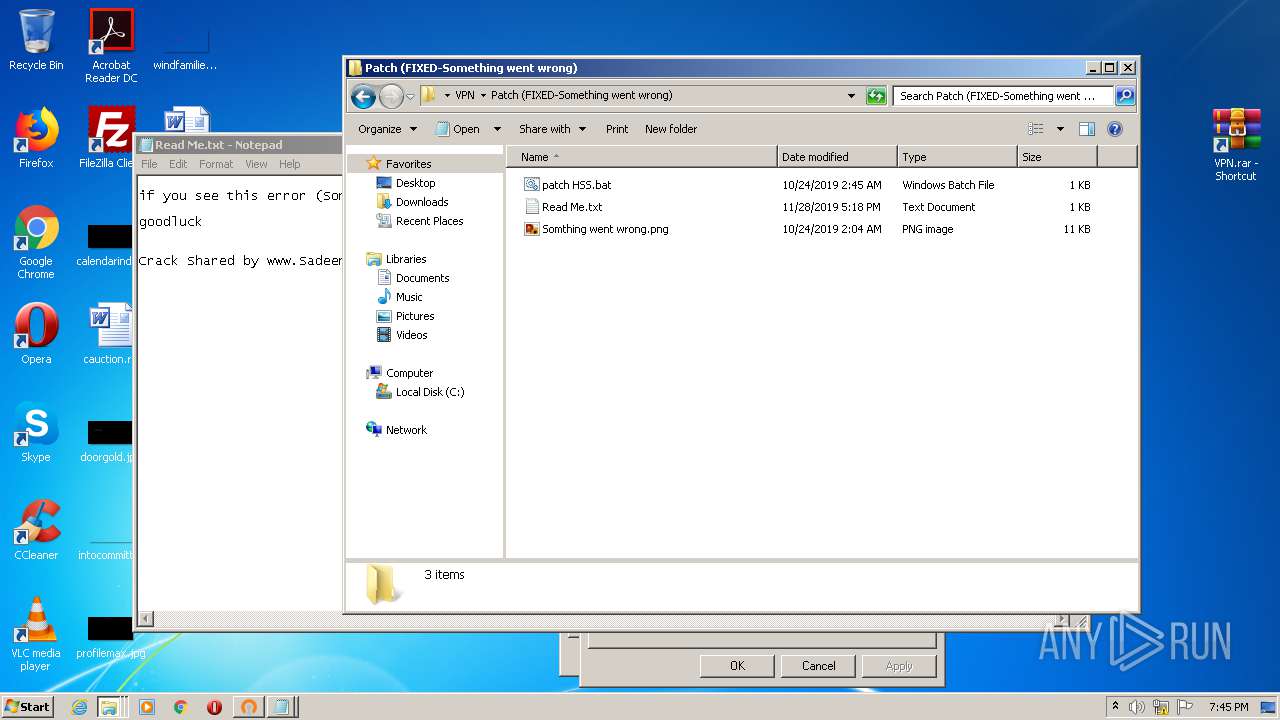
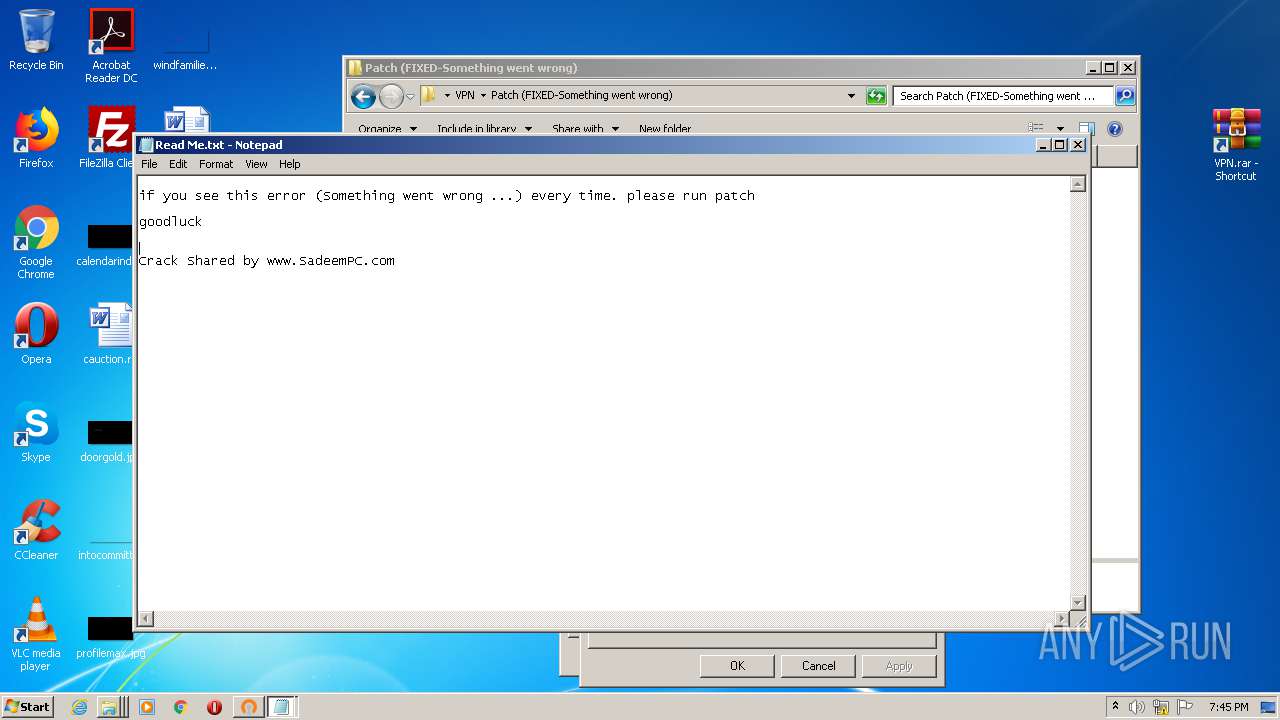
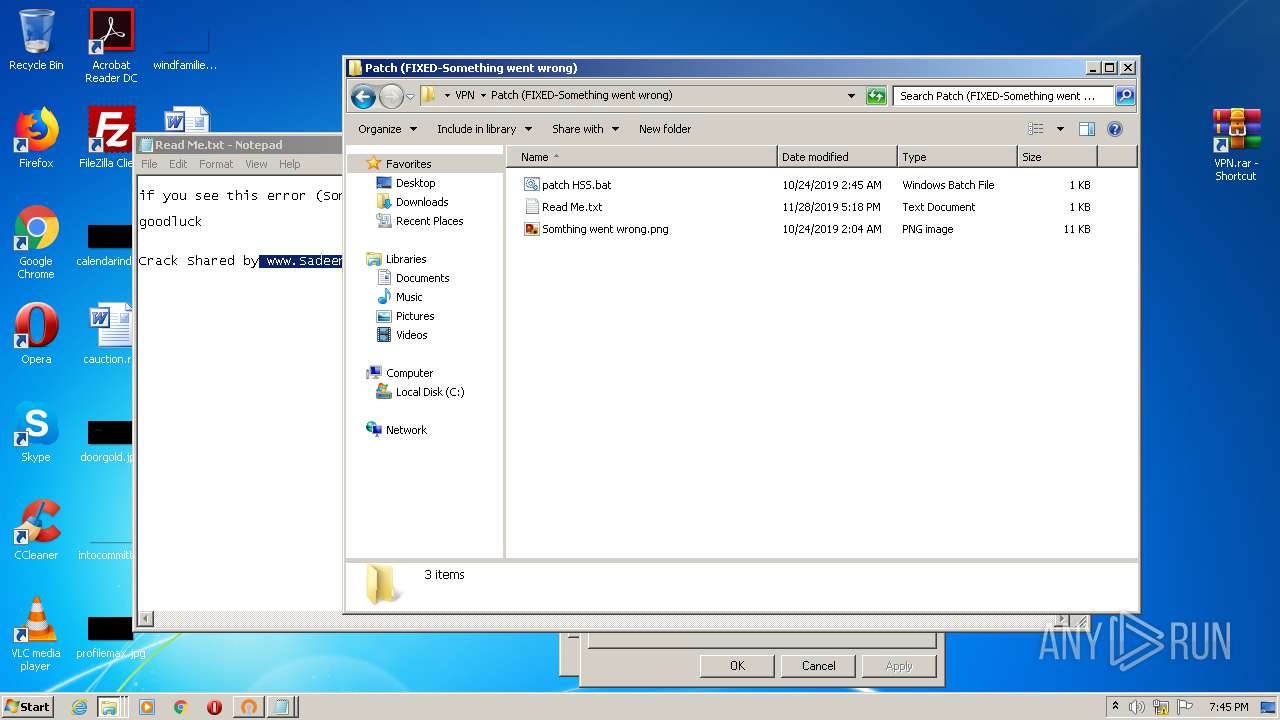
| 1220 | "C:\Windows\System32\NOTEPAD.EXE" C:\Users\admin\Desktop\VPN\Patch (FIXED-Something went wrong)\patch HSS.bat | C:\Windows\System32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Hotspot Shield\bin\hsscp.exe" | C:\Program Files\Hotspot Shield\bin\hsscp.exe | — | msiexec.exe | |||||||||||
User: admin Company: AnchorFree Inc. Integrity Level: HIGH Description: Hotspot Shield Exit code: 0 Version: 9.21.3.11422 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,9135827580714482843,17675801233449319125,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10093703943331395775 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 999
Read events
4 438
Write events
543
Delete events
18
Modification events
| (PID) Process: | (1552) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: rundll32.exe | |||
| (PID) Process: | (1552) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2800-13257114118246250 |
Value: 259 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
115
Suspicious files
48
Text files
387
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-601EF106-AF0.pma | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b069bbf0-bb99-491c-b282-466ce8253197.tmp | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF147780.TMP | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF147993.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
33
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2516 | cmw_srv.exe | GET | 204 | 142.250.185.142:80 | http://google.com/generate_204 | US | — | — | malicious |
2516 | cmw_srv.exe | GET | 200 | 23.37.43.27:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | NL | der | 1.71 Kb | whitelisted |
2516 | cmw_srv.exe | GET | 200 | 23.51.123.27:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEGfxU7IK0zmcft3OLGyv12Y%3D | NL | der | 1.57 Kb | shared |
2484 | chrome.exe | GET | 200 | 142.250.34.2:80 | http://edgedl.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2484 | chrome.exe | 209.85.233.94:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2484 | chrome.exe | 142.250.186.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2484 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2484 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2484 | chrome.exe | 142.250.186.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2484 | chrome.exe | 142.250.105.101:443 | apis.google.com | Google Inc. | US | whitelisted |
2484 | chrome.exe | 172.217.18.110:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2484 | chrome.exe | 64.233.185.104:443 | www.google.com | Google Inc. | US | whitelisted |
2484 | chrome.exe | 162.159.135.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
— | — | 162.159.135.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.nl |
| whitelisted |
Threats
Process | Message |
|---|---|
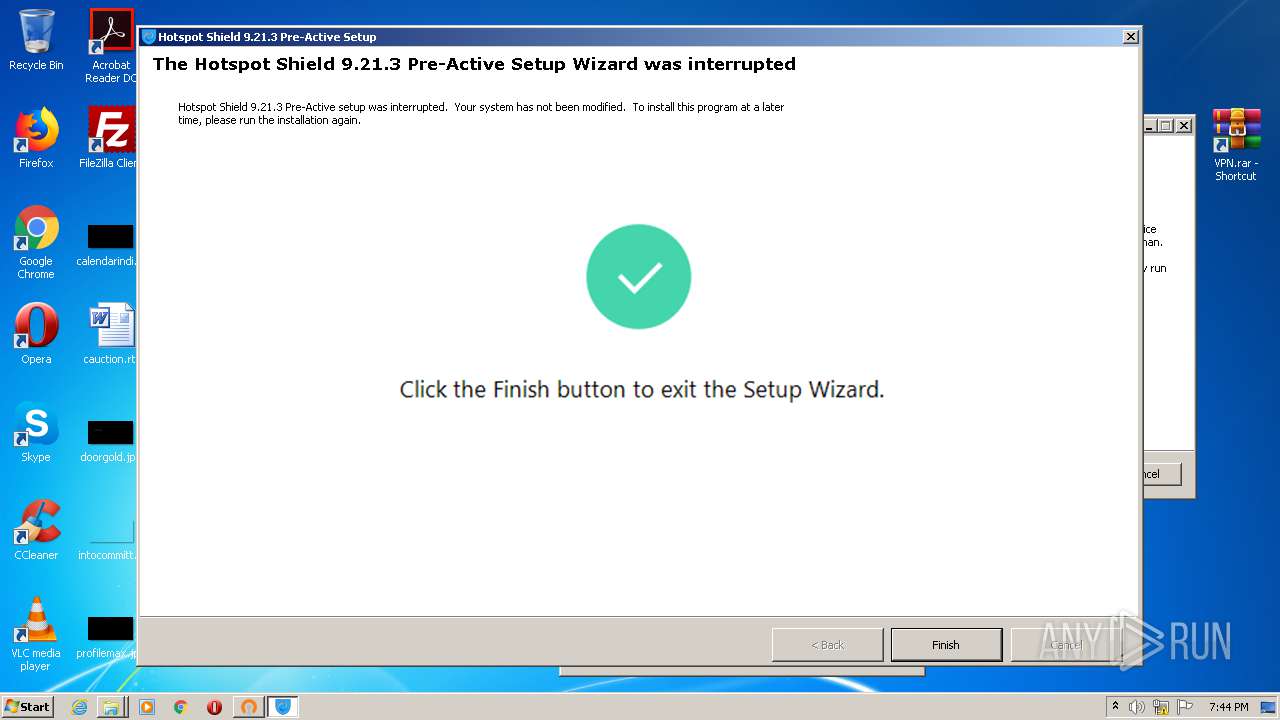
HotspotShield-8.7.1-plain-773-PreActive.exe | Another instance of setup is already running. |