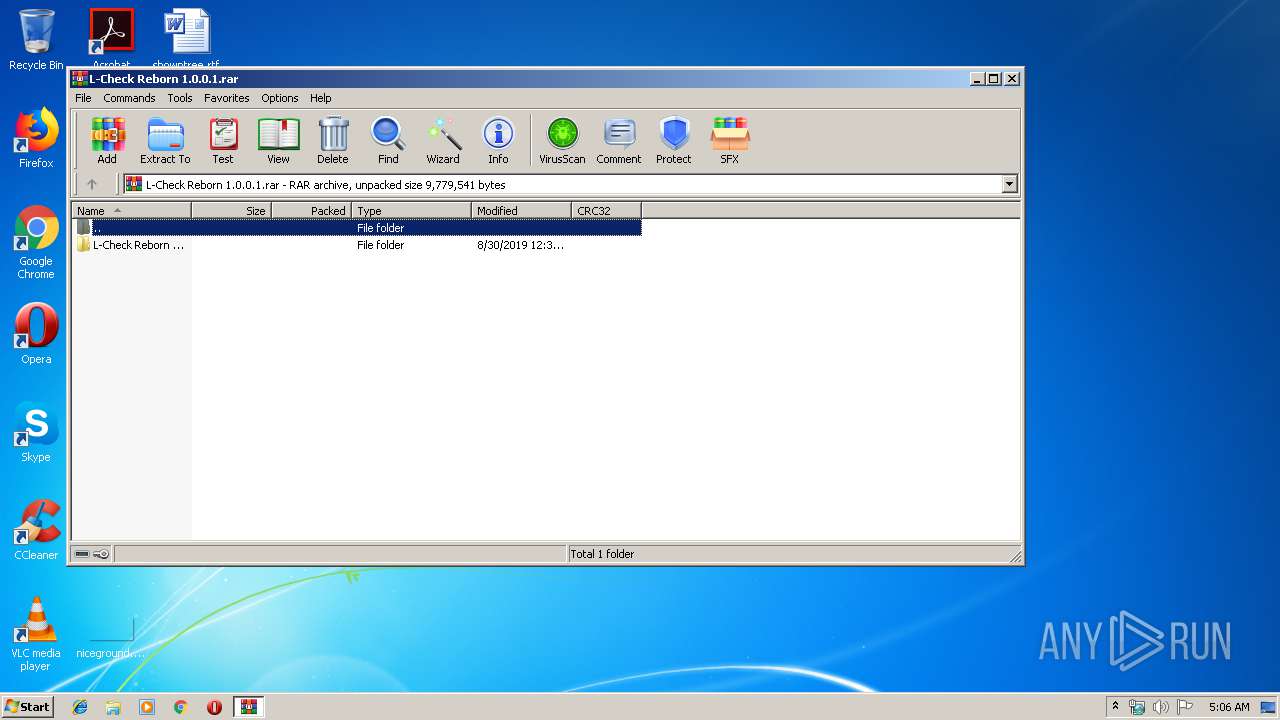
| File name: | L-Check Reborn 1.0.0.1.rar |
| Full analysis: | https://app.any.run/tasks/1a799173-ff64-452d-870d-e208b9ef3d10 |
| Verdict: | No threats detected |
| Analysis date: | September 06, 2019, 04:06:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 24E33A71507E22802A2D2B6FDEC0FDA2 |
| SHA1: | F88B3C3F24451515280C67DACB087BF2710AFCD2 |
| SHA256: | 0D458EE418A8F7D323B0D84DFE5841F494CC92828CB1C711BD4D09C4A2D3CB79 |
| SSDEEP: | 98304:Lgl4QI+Jm0Qe0HlWhKqhLl/nktuE/OW5I8QaA1LBZrLQ4hq4N51hI9C:LLSghlWhKqL5nk3/Bq/aorLL9L1hV |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
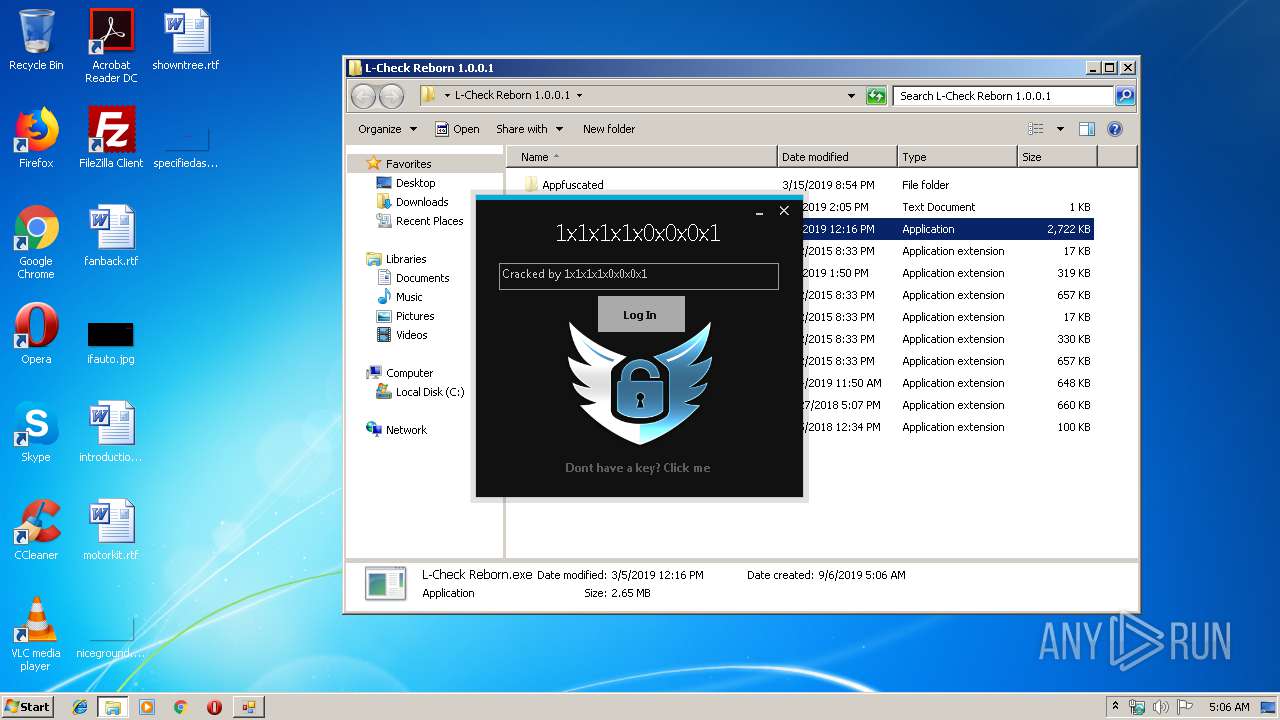
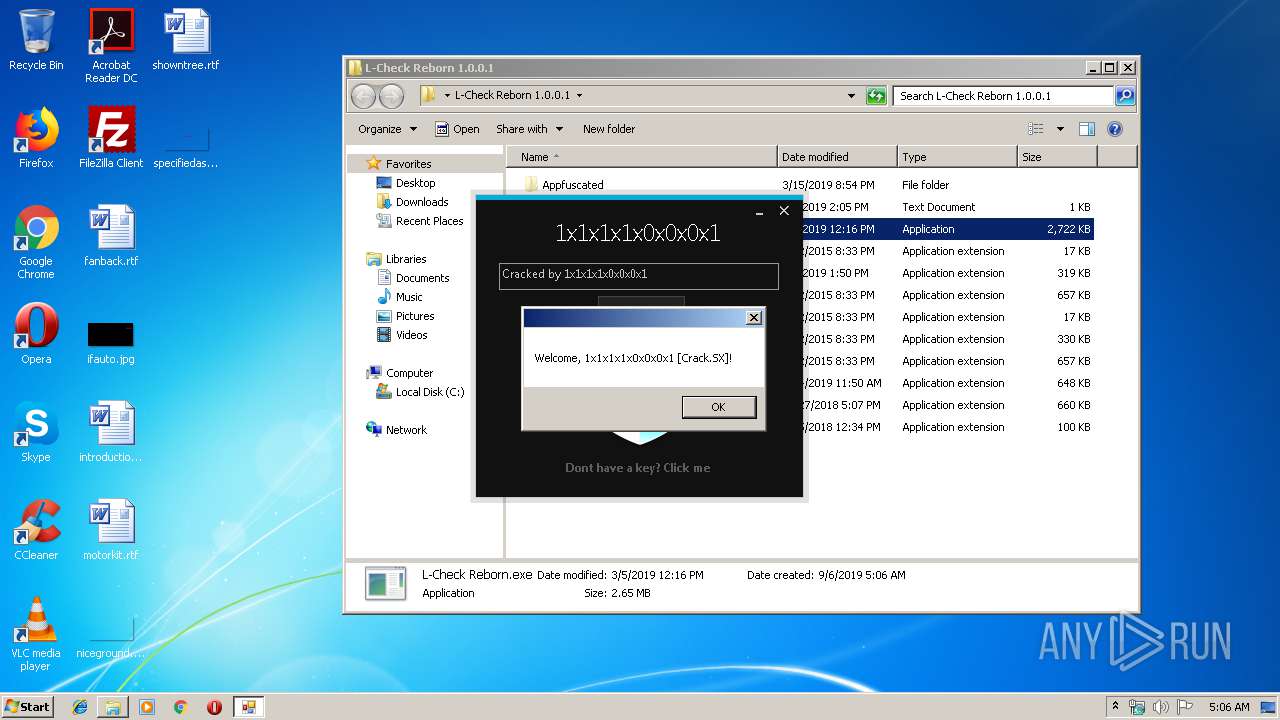
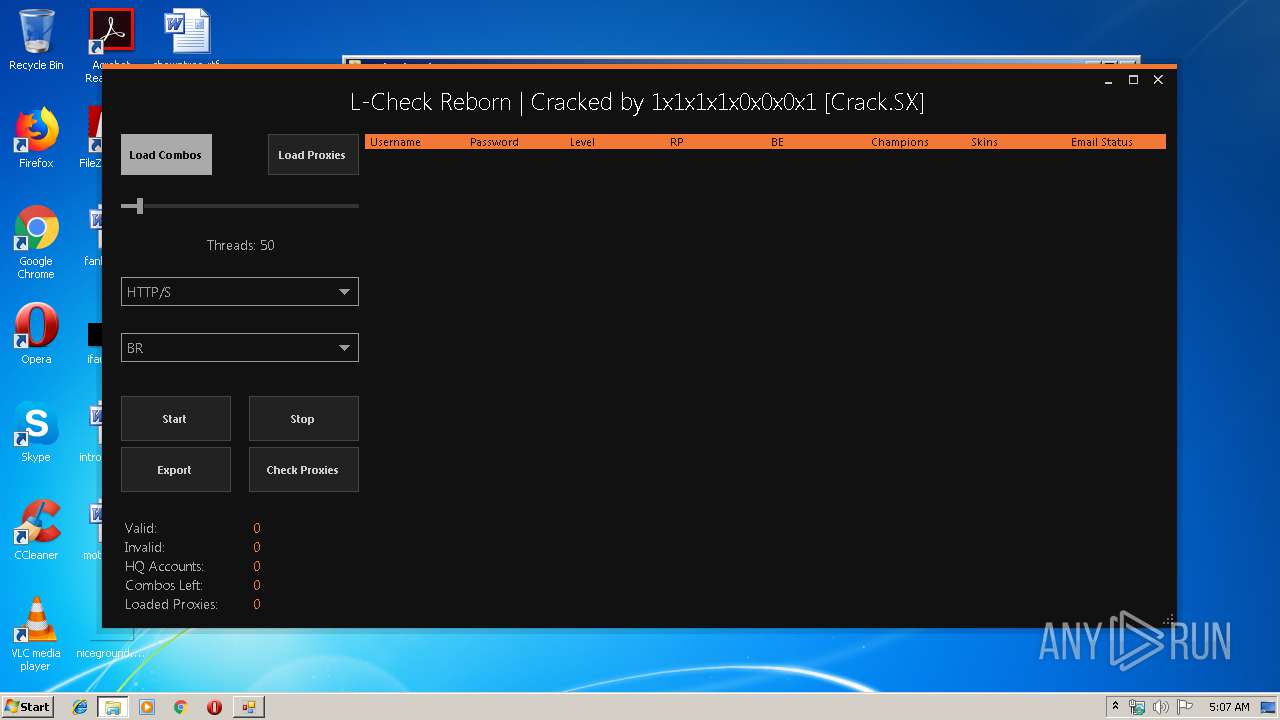
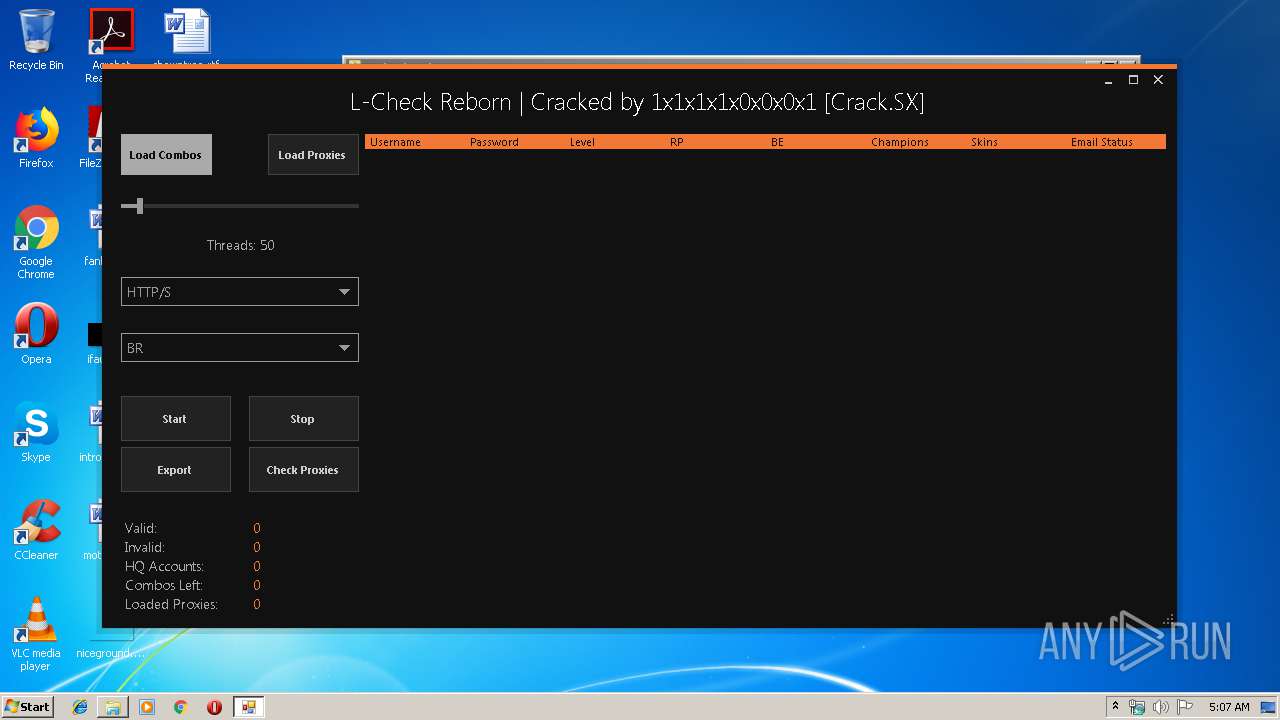
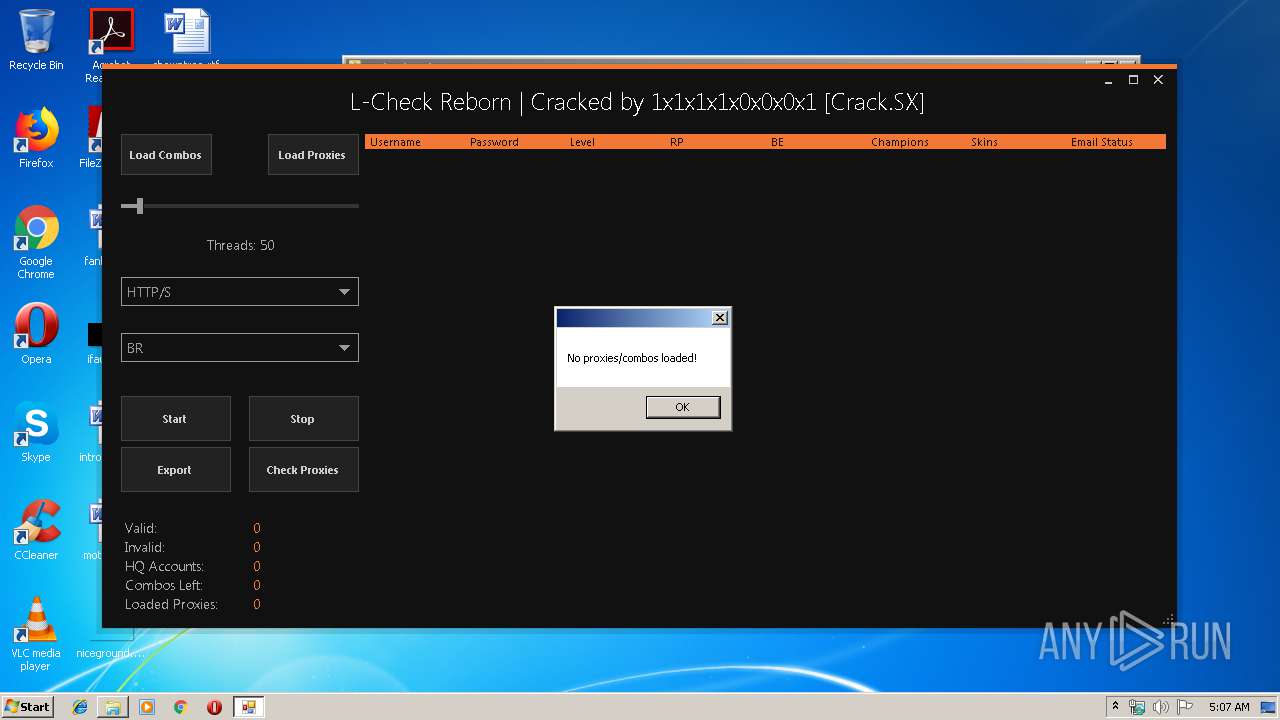
Manual execution by user
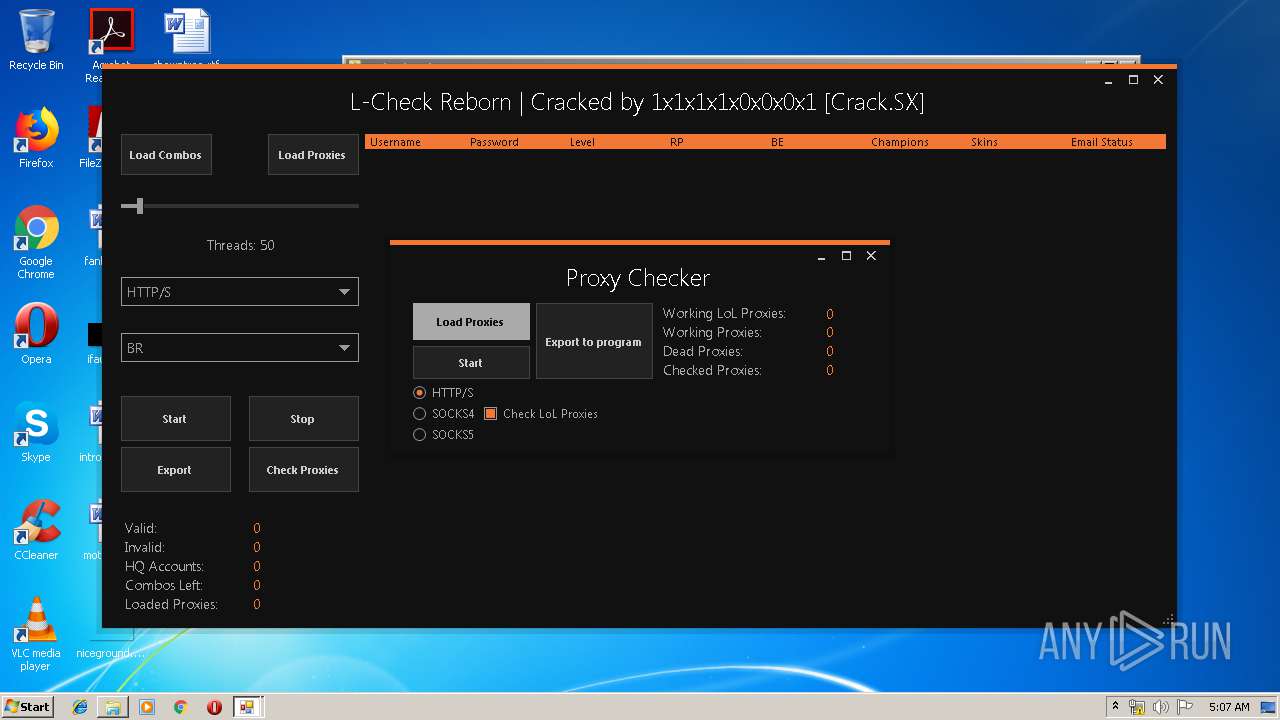
- L-Check Reborn.exe (PID: 3596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
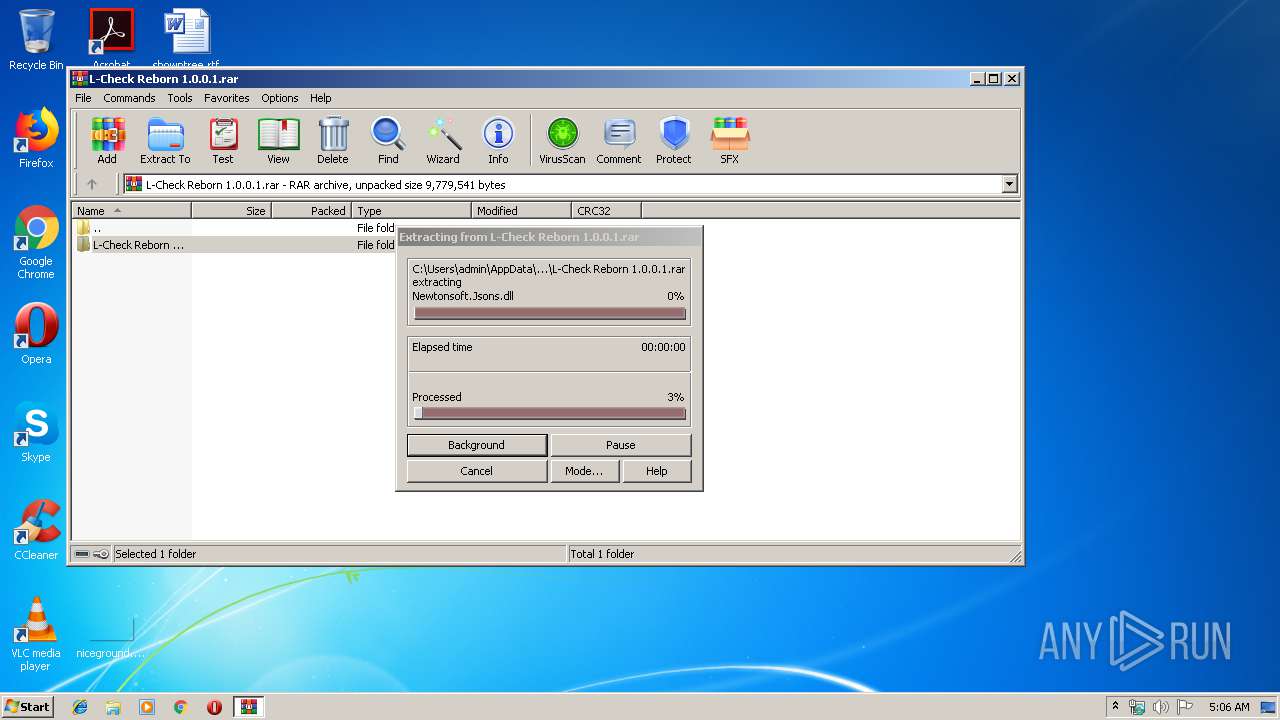
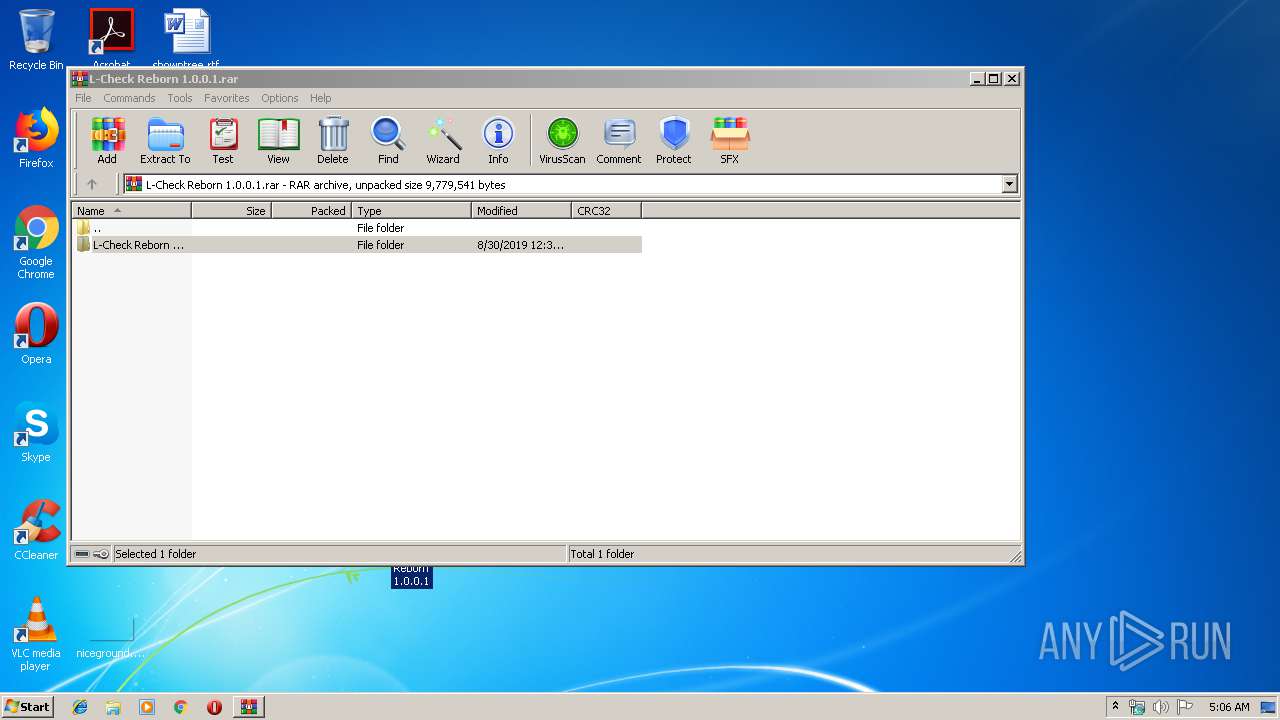
| 3576 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\L-Check Reborn 1.0.0.1.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3596 | "C:\Users\admin\Desktop\L-Check Reborn 1.0.0.1\L-Check Reborn.exe" | C:\Users\admin\Desktop\L-Check Reborn 1.0.0.1\L-Check Reborn.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: L-Check Reborn Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 055
Read events
980
Write events
74
Delete events
1
Modification events
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\L-Check Reborn 1.0.0.1.rar | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3576) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
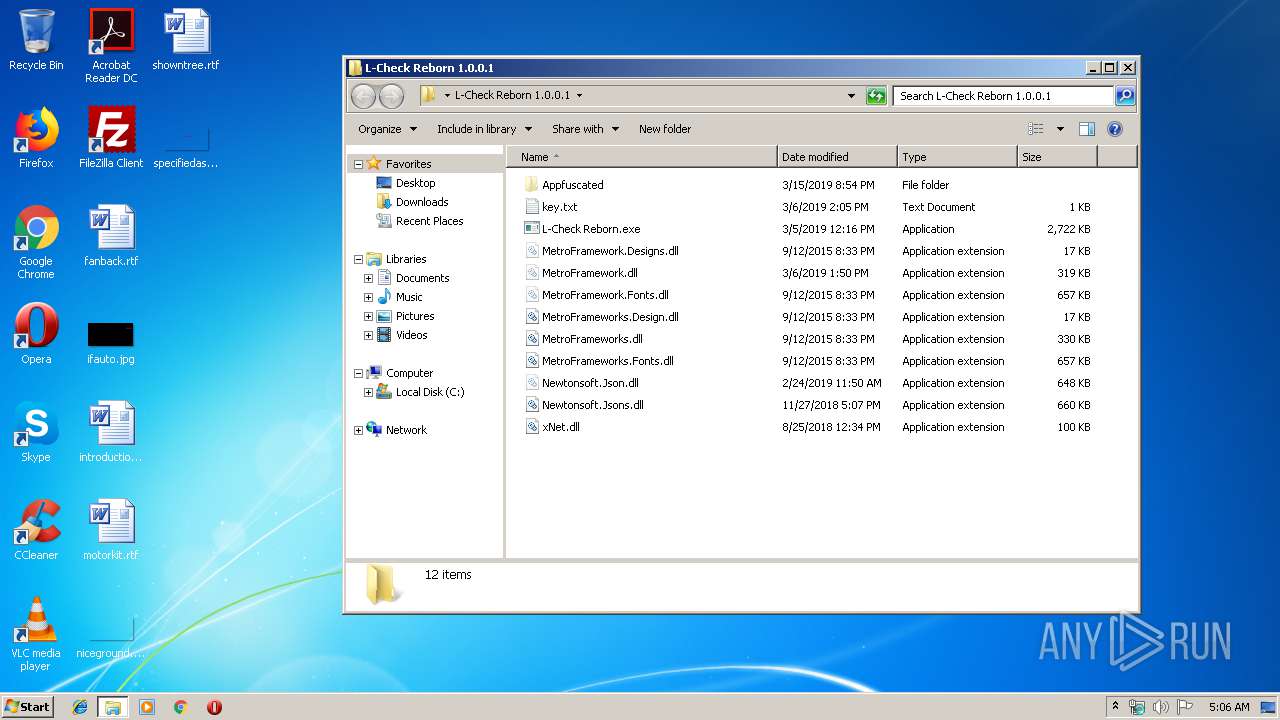
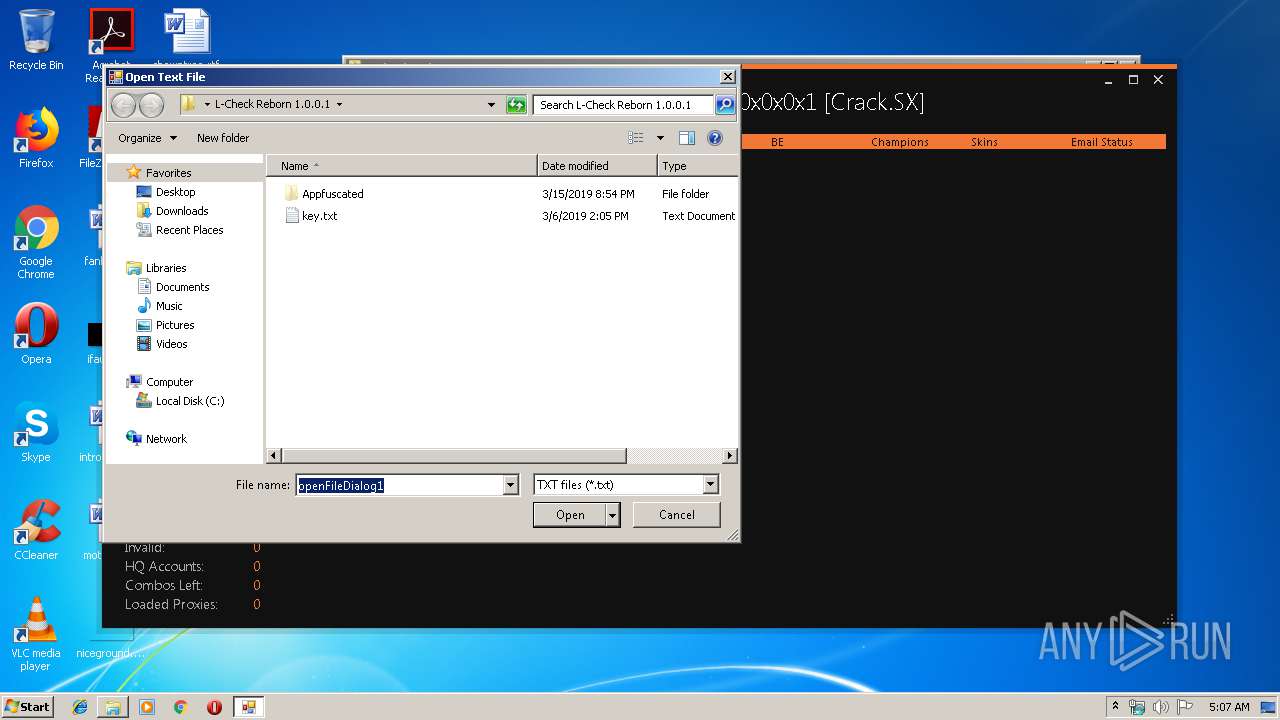
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.30759\L-Check Reborn 1.0.0.1\Appfuscated\MetroFramework.dll | — | |
MD5:— | SHA256:— | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.30759\L-Check Reborn 1.0.0.1\Appfuscated\Newtonsoft.Json.dll | — | |
MD5:— | SHA256:— | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.30759\L-Check Reborn 1.0.0.1\Appfuscated\project.map.xml | — | |
MD5:— | SHA256:— | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.30759\L-Check Reborn 1.0.0.1\key.txt | — | |
MD5:— | SHA256:— | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.30759\L-Check Reborn 1.0.0.1\L-Check Reborn.exe | — | |
MD5:— | SHA256:— | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.30759\L-Check Reborn 1.0.0.1\MetroFramework.Designs.dll | — | |
MD5:— | SHA256:— | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.30759\L-Check Reborn 1.0.0.1\MetroFramework.dll | — | |
MD5:— | SHA256:— | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.30759\L-Check Reborn 1.0.0.1\MetroFramework.Fonts.dll | — | |
MD5:— | SHA256:— | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.30759\L-Check Reborn 1.0.0.1\MetroFrameworks.Design.dll | — | |
MD5:— | SHA256:— | |||
| 3576 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3576.30759\L-Check Reborn 1.0.0.1\MetroFrameworks.dll | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.24.1.112:443 | cracked.to | Cloudflare Inc | US | shared |
3596 | L-Check Reborn.exe | 104.24.1.112:443 | cracked.to | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cracked.to |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
Process | Message |
|---|---|
L-Check Reborn.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|