| download: | /krnl.msi |
| Full analysis: | https://app.any.run/tasks/57aebfbe-d6ea-484b-958b-72ae5b8914df |
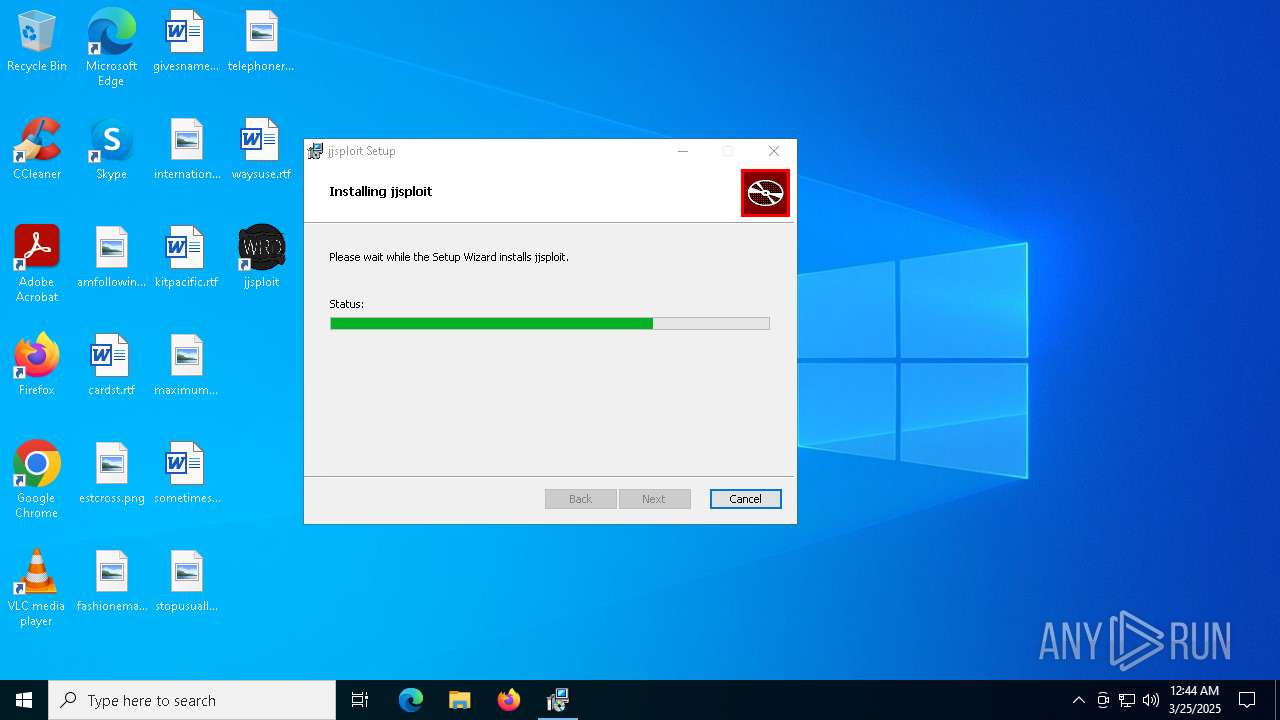
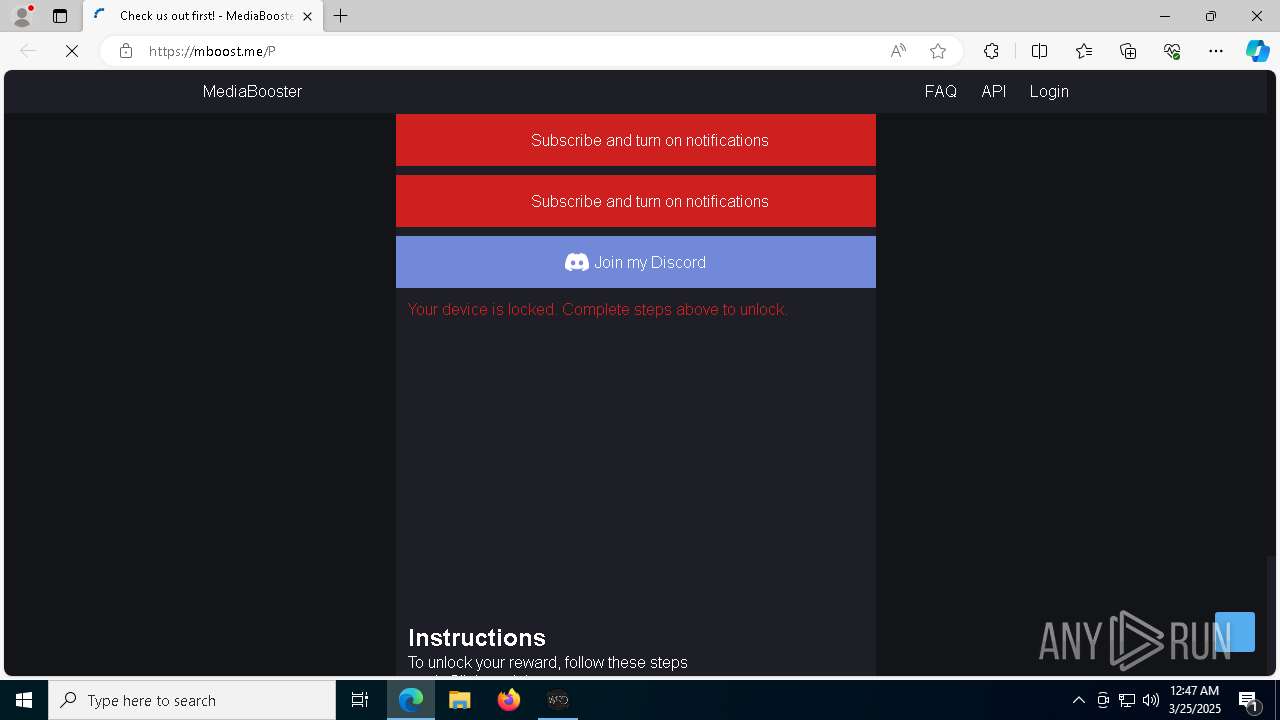
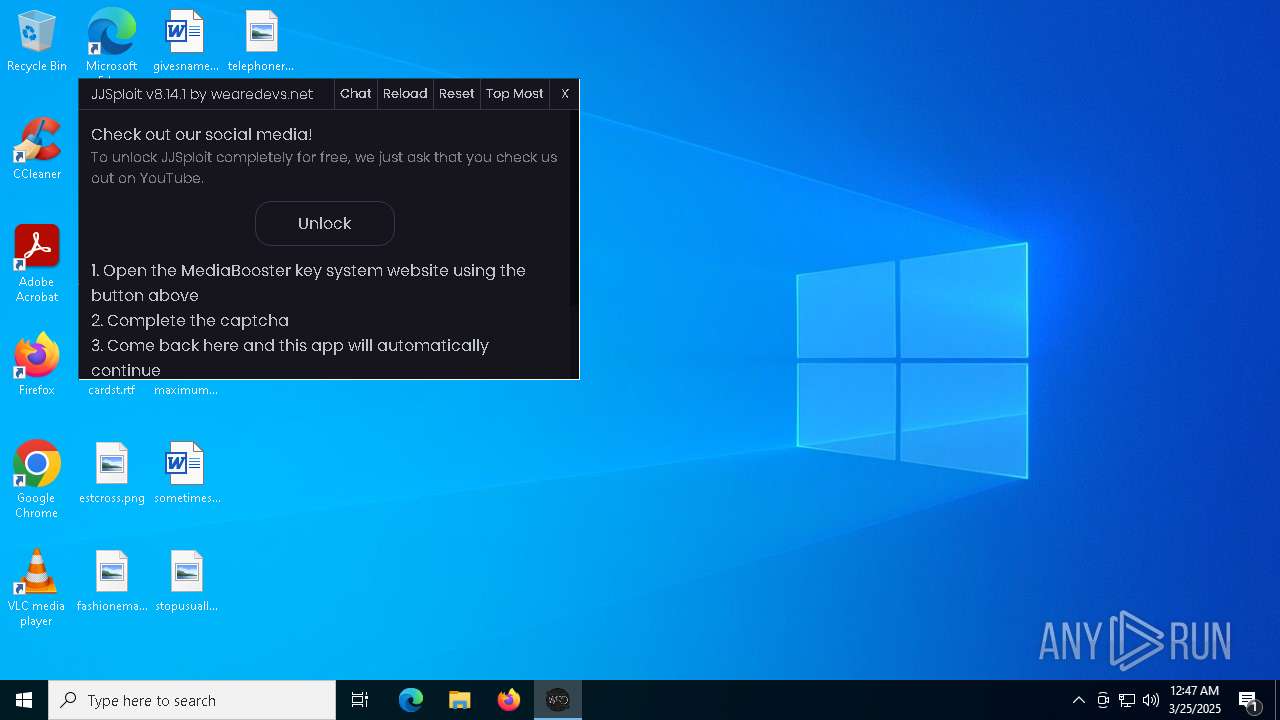
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 00:43:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
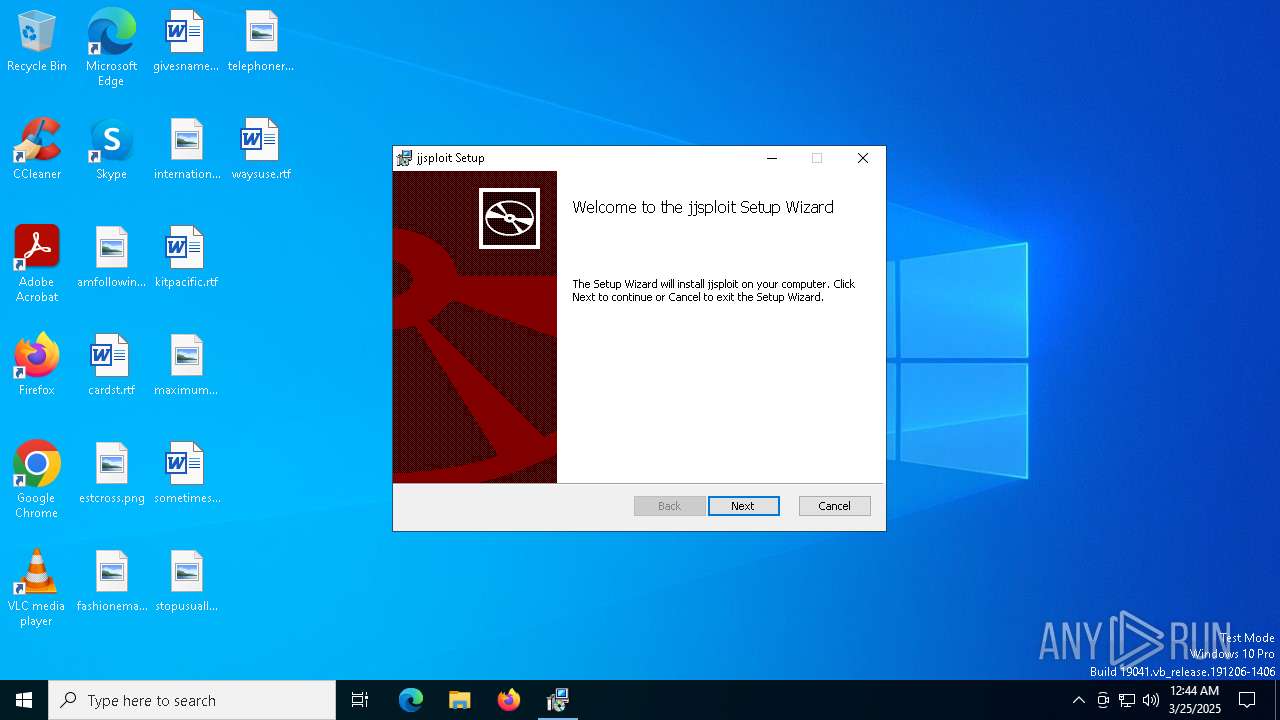
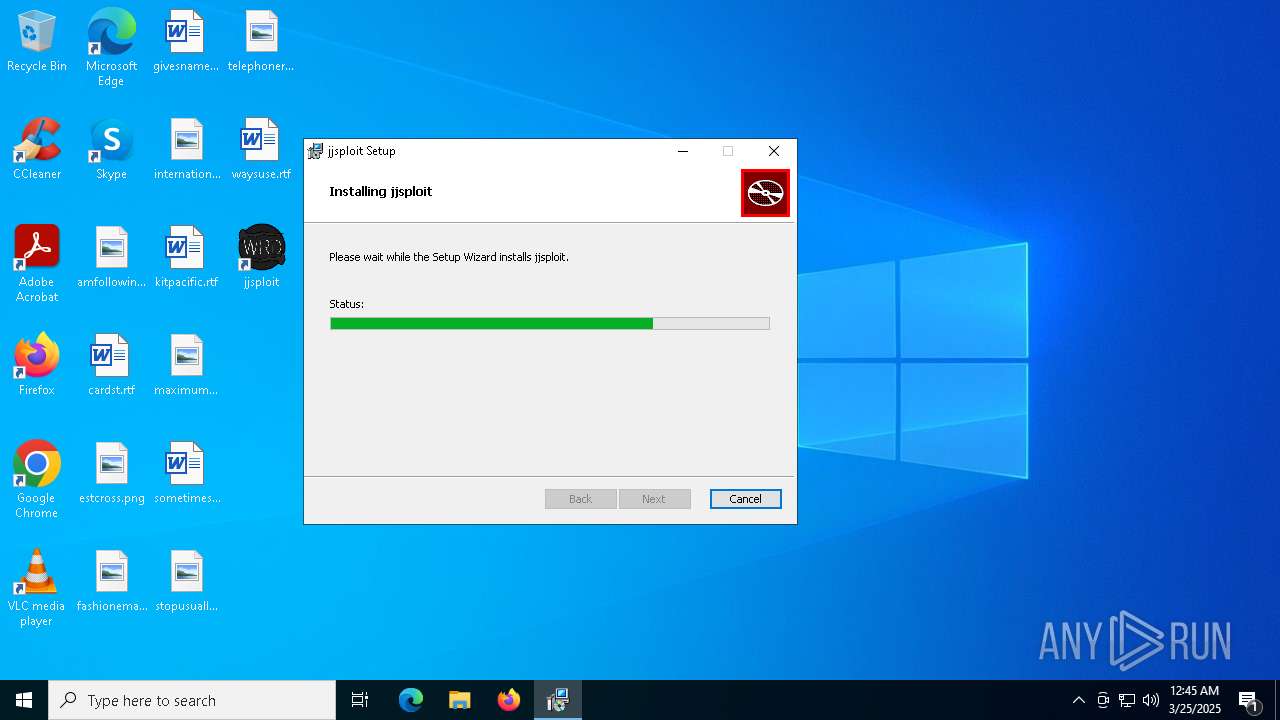
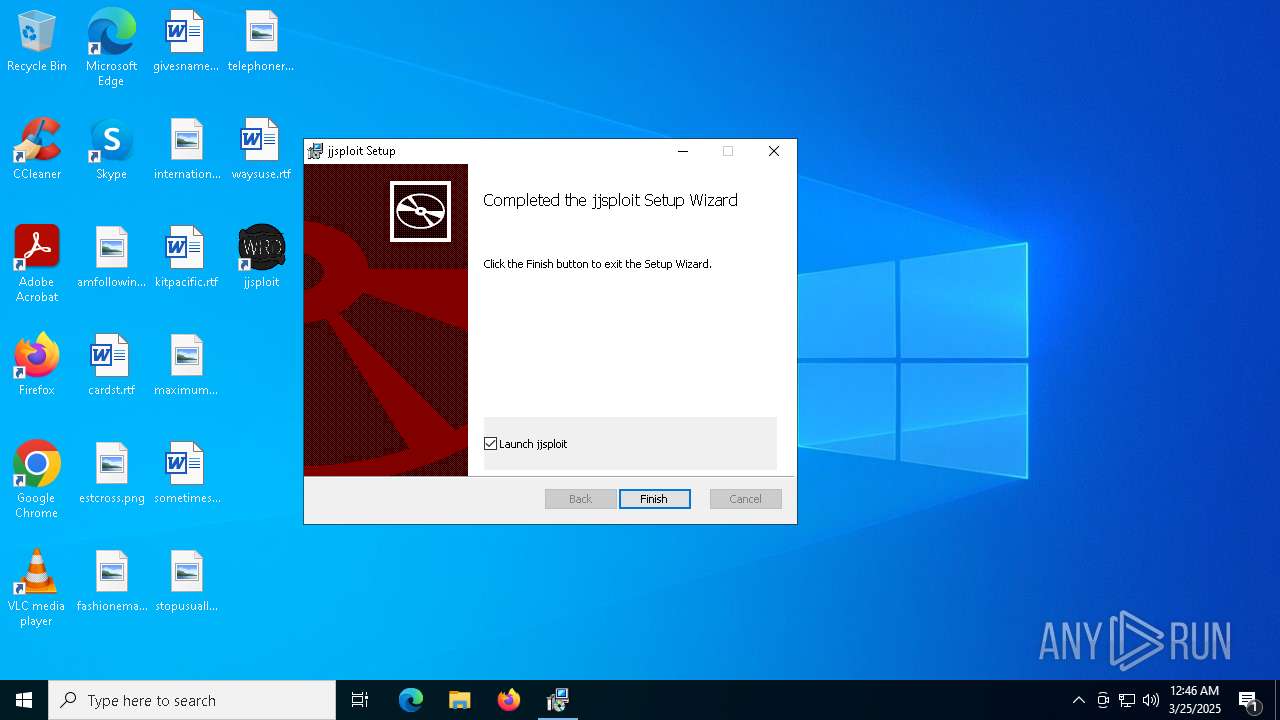
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: jjsploit, Author: wearedevs, Keywords: Installer, Comments: This installer database contains the logic and data required to install jjsploit., Template: x64;0, Revision Number: {520ECEE8-0814-41B5-A3A2-A3DC4D26C168}, Create Time/Date: Tue Mar 18 19:57:40 2025, Last Saved Time/Date: Tue Mar 18 19:57:40 2025, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2 |
| MD5: | 90FE4EA1323D1B17C90EFDC69FA13CF5 |
| SHA1: | B92333FD238D9BCF80CFD170251C0ED05AE5EDC6 |
| SHA256: | 0D411F1B891CA8240EE7FB73ADCF4C0DFF02869B043BE19B57A4F5B0257BAC32 |
| SSDEEP: | 98304:PvwaAJ4neZ16VC+t0RBdxMqUyWTgv3qSbiWkJbSlFuVJrml+NaFXWpdP3j+IwFII:qRjctLTUDH |
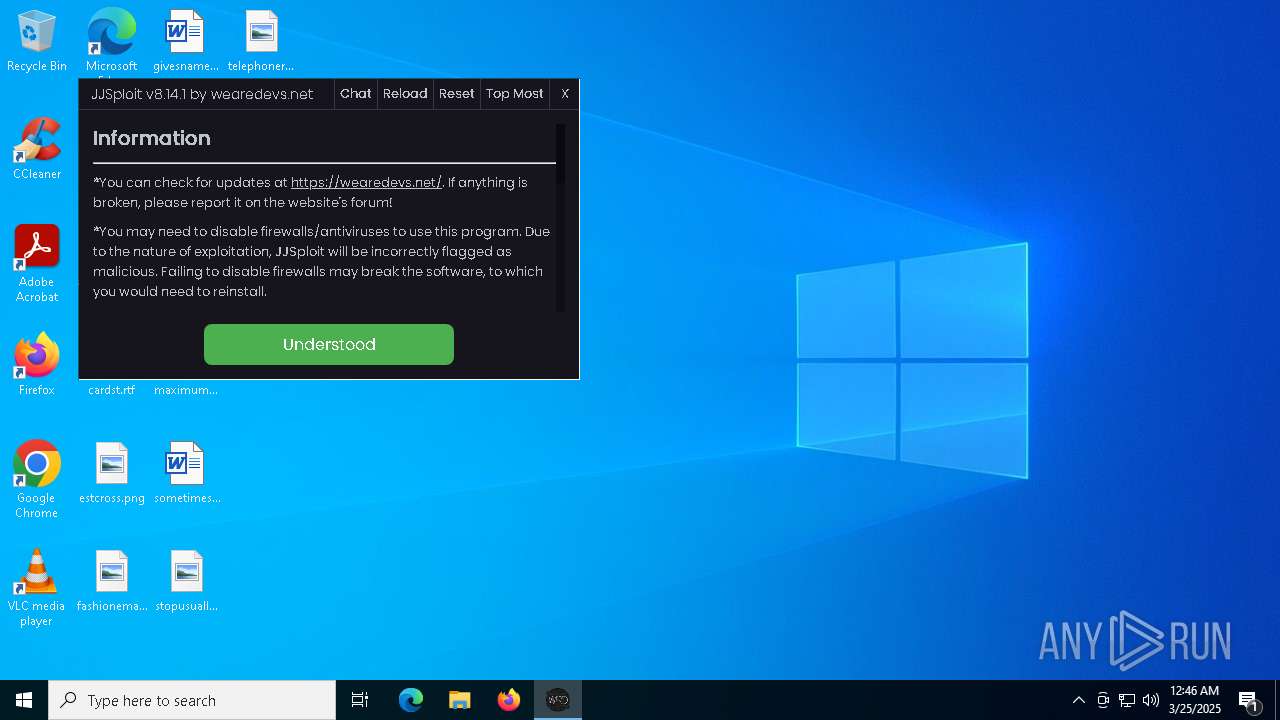
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 5164)
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 5588)
The DLL Hijacking
- msedgewebview2.exe (PID: 872)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5640)
Starts process via Powershell
- powershell.exe (PID: 5164)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 5640)
Downloads file from URI via Powershell
- powershell.exe (PID: 5164)
Manipulates environment variables
- powershell.exe (PID: 5164)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 5640)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 5164)
Executable content was dropped or overwritten
- powershell.exe (PID: 5164)
- MicrosoftEdgeUpdate.exe (PID: 5588)
- MicrosoftEdgeWebview2Setup.exe (PID: 4212)
- MicrosoftEdge_X64_134.0.3124.85.exe (PID: 7944)
- setup.exe (PID: 7964)
Executes as Windows Service
- VSSVC.exe (PID: 6708)
Process drops legitimate windows executable
- powershell.exe (PID: 5164)
- MicrosoftEdgeUpdate.exe (PID: 5588)
- MicrosoftEdgeWebview2Setup.exe (PID: 4212)
- MicrosoftEdge_X64_134.0.3124.85.exe (PID: 7944)
- setup.exe (PID: 7964)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 5588)
- MicrosoftEdgeWebview2Setup.exe (PID: 4212)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 5588)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7084)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 924)
- MicrosoftEdgeUpdate.exe (PID: 4152)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4336)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 5588)
- ShellExperienceHost.exe (PID: 7236)
- MicrosoftEdgeUpdate.exe (PID: 4304)
- msedgewebview2.exe (PID: 232)
- jjsploit.exe (PID: 5304)
Application launched itself
- setup.exe (PID: 7964)
- MicrosoftEdgeUpdate.exe (PID: 4304)
- msedgewebview2.exe (PID: 232)
Creates a software uninstall entry
- setup.exe (PID: 7964)
Searches for installed software
- setup.exe (PID: 7964)
INFO
Checks supported languages
- msiexec.exe (PID: 5640)
- msiexec.exe (PID: 4424)
- MicrosoftEdgeUpdate.exe (PID: 5588)
- MicrosoftEdgeWebview2Setup.exe (PID: 4212)
- MicrosoftEdgeUpdate.exe (PID: 4152)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7084)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 924)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4336)
- MicrosoftEdgeUpdate.exe (PID: 6208)
- MicrosoftEdgeUpdate.exe (PID: 5020)
- MicrosoftEdgeUpdate.exe (PID: 4304)
- ShellExperienceHost.exe (PID: 7236)
- MicrosoftEdge_X64_134.0.3124.85.exe (PID: 7944)
- setup.exe (PID: 7964)
- setup.exe (PID: 7984)
- msedgewebview2.exe (PID: 232)
- jjsploit.exe (PID: 5304)
- msedgewebview2.exe (PID: 5260)
- msedgewebview2.exe (PID: 7876)
- msedgewebview2.exe (PID: 7264)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 1180)
- BackgroundTransferHost.exe (PID: 3332)
- BackgroundTransferHost.exe (PID: 5384)
- BackgroundTransferHost.exe (PID: 4724)
- BackgroundTransferHost.exe (PID: 4068)
Reads the computer name
- msiexec.exe (PID: 5640)
- msiexec.exe (PID: 4424)
- MicrosoftEdgeUpdate.exe (PID: 5588)
- MicrosoftEdgeUpdate.exe (PID: 4152)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7084)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 924)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4336)
- MicrosoftEdgeUpdate.exe (PID: 6208)
- MicrosoftEdgeUpdate.exe (PID: 5020)
- MicrosoftEdgeUpdate.exe (PID: 4304)
- ShellExperienceHost.exe (PID: 7236)
- setup.exe (PID: 7964)
- MicrosoftEdge_X64_134.0.3124.85.exe (PID: 7944)
- msedgewebview2.exe (PID: 232)
- jjsploit.exe (PID: 5304)
- msedgewebview2.exe (PID: 5260)
An automatically generated document
- msiexec.exe (PID: 2136)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 3332)
- MicrosoftEdgeUpdate.exe (PID: 4304)
- MicrosoftEdge_X64_134.0.3124.85.exe (PID: 7944)
- setup.exe (PID: 7984)
- setup.exe (PID: 7964)
- msedgewebview2.exe (PID: 232)
- msedgewebview2.exe (PID: 3300)
- msedgewebview2.exe (PID: 5260)
- jjsploit.exe (PID: 5304)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2136)
- msiexec.exe (PID: 5640)
Creates a software uninstall entry
- msiexec.exe (PID: 5640)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 3332)
- MicrosoftEdgeUpdate.exe (PID: 6208)
- slui.exe (PID: 1764)
- MicrosoftEdgeUpdate.exe (PID: 4304)
- slui.exe (PID: 7660)
- MicrosoftEdgeUpdate.exe (PID: 6256)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 3332)
- powershell.exe (PID: 5164)
- MicrosoftEdgeUpdate.exe (PID: 6208)
- MicrosoftEdgeUpdate.exe (PID: 4304)
- slui.exe (PID: 7660)
- MicrosoftEdgeUpdate.exe (PID: 6256)
- msedgewebview2.exe (PID: 232)
Disables trace logs
- powershell.exe (PID: 5164)
The sample compiled with english language support
- powershell.exe (PID: 5164)
- MicrosoftEdgeWebview2Setup.exe (PID: 4212)
- MicrosoftEdgeUpdate.exe (PID: 5588)
- MicrosoftEdge_X64_134.0.3124.85.exe (PID: 7944)
- setup.exe (PID: 7964)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 4212)
Manages system restore points
- SrTasks.exe (PID: 2096)
Create files in a temporary directory
- MicrosoftEdgeWebview2Setup.exe (PID: 4212)
- MicrosoftEdgeUpdate.exe (PID: 5588)
- msedgewebview2.exe (PID: 232)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 5588)
- msedgewebview2.exe (PID: 232)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 6208)
Reads the machine GUID from the registry
- MicrosoftEdgeUpdate.exe (PID: 4304)
- msedgewebview2.exe (PID: 232)
Application launched itself
- msedge.exe (PID: 4000)
- msedge.exe (PID: 6592)
Reads CPU info
- msedgewebview2.exe (PID: 232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
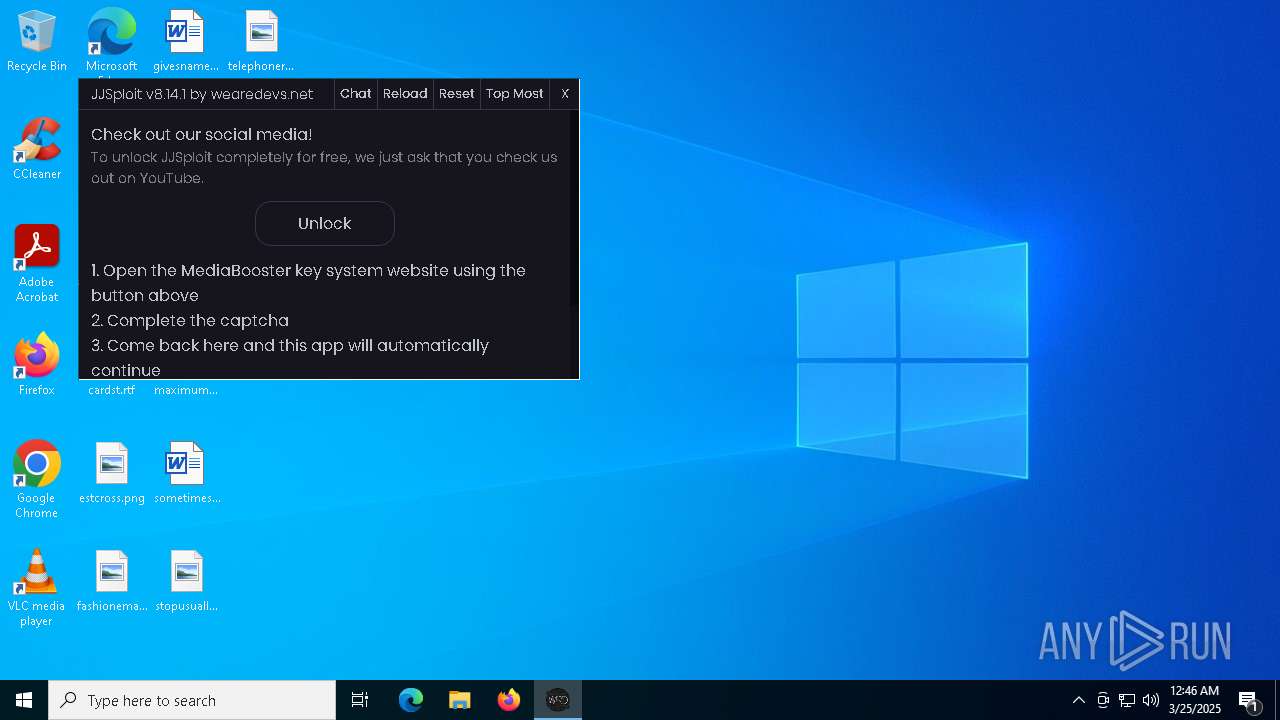
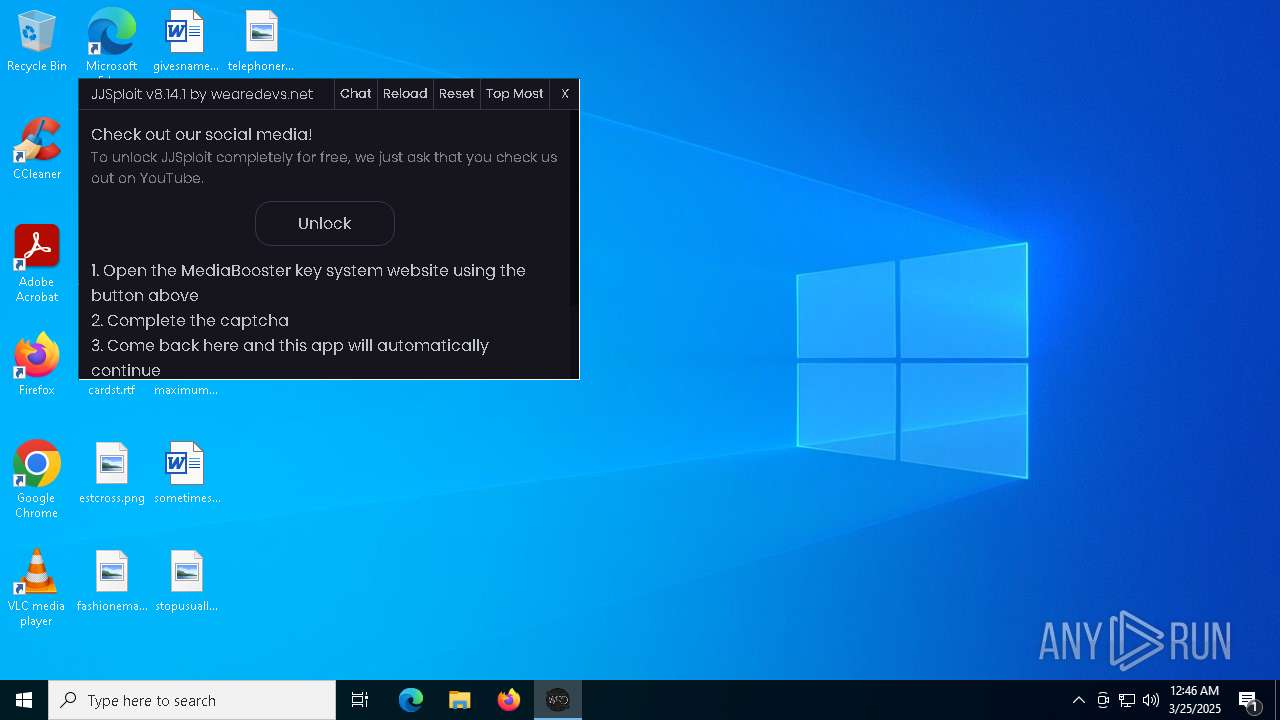
| Subject: | jjsploit |
| Author: | wearedevs |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install jjsploit. |
| Template: | x64;0 |
| RevisionNumber: | {520ECEE8-0814-41B5-A3A2-A3DC4D26C168} |
| CreateDate: | 2025:03:18 19:57:40 |
| ModifyDate: | 2025:03:18 19:57:40 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
Total processes
220
Monitored processes
71
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\134.0.3124.85\msedgewebview2.exe" --embedded-browser-webview=1 --webview-exe-name=jjsploit.exe --webview-exe-version=8.14.1 --user-data-dir="C:\Users\admin\AppData\Local\net.wearedevs\EBWebView" --noerrdialogs --embedded-browser-webview-dpi-awareness=2 --autoplay-policy=no-user-gesture-required --disable-features=msWebOOUI,msPdfOOUI,msSmartScreenProtection --lang=en-US --mojo-named-platform-channel-pipe=5304.7776.4500454934581444562 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\134.0.3124.85\msedgewebview2.exe | — | jjsploit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 134.0.3124.85 Modules
| |||||||||||||||
| 872 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\134.0.3124.85\msedgewebview2.exe" --type=gpu-process --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\net.wearedevs\EBWebView" --webview-exe-name=jjsploit.exe --webview-exe-version=8.14.1 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --no-pre-read-main-dll --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=1820,i,7961389850471104207,17959756937978138417,262144 --enable-features=ForceSWDCompWhenDCompFallbackRequired,msAggressiveCacheTrimming,msCustomDataPartition,msWebView2NoTabForScreenShare,msWindowsTaskManager --disable-features=BackForwardCache,BackgroundTabLoadingFromPerformanceManager,CloseOmniboxPopupOnInactiveAreaClick,CollectAVProductsInfo,CollectCodeIntegrityInfo,EnableHangWatcher,FilterAdsOnAbusiveSites,GetWifiProtocol,LoginDetection,MediaFoundationCameraUsageMonitoring,PreconnectToSearch,SafetyHub,SegmentationPlatform,SpareRendererForSitePerProcess,Ukm,WebPayments,msAITrackerClassification,msAbydosForWindowlessWV2,msAffirmVirtualCard,msAllowChromeWebstore,msAllowMSAPrtSSOForNonMSAProfile,msApplicationGuard,msAskBeforeClosingMultipleTabs,msAutoToggleAADPrtSSOForNonAADProfile,msAutofillEdgeCoupons,msAutofillEdgeCouponsAutoApply,msAutofillEdgeServiceRequest,msAutomaticTabFreeze,msBrowserSettingsSupported,msCoarseGeolocationService,msDataProtection,msDesktopMode,msDesktopRewards,msDisableVariationsSeedFetchThrottling,msEEProactiveHistory,msEdgeAdPlatformUI,msEdgeAddWebCapturetoCollections,msEdgeAutofillAdvancedSuggestionsBasic,msEdgeAutofillOneClickAutocomplete,msEdgeAutofillSaveGSPR100InDb,msEdgeAutofillShowDeployedPassword,msEdgeAutofillSs,msEdgeBrowserEssentialsShowUpdateSection,msEdgeCloudConfigService,msEdgeCloudConfigServiceV2,msEdgeCohorts,msEdgeCollectionsPrismExperiment1,msEdgeCollectionsPrismOverallMigration,msEdgeComposeNext,msEdgeEnableNurturingFramework,msEdgeEnclavePrefsBasic,msEdgeEnclavePrefsNotification,msEdgeFaviconService,msEdgeHJTelemetry,msEdgeHubAppSkype,msEdgeImageEditorUI,msEdgeLinkDoctor,msEdgeMouseGestureDefaultEnabled,msEdgeMouseGestureSupported,msEdgeNewDeviceFre,msEdgeOnRampFRE,msEdgeOnRampImport,msEdgePDFCMHighlightUX,msEdgePasswordIris,msEdgePasswordIrisSaveBubble,msEdgeProngPersonalization,msEdgeReadingView,msEdgeRose,msEdgeSendTabToSelf,msEdgeSettingsImport,msEdgeSettingsImportV2,msEdgeShoppingPersistentStorage,msEdgeShoppingPersonalizedCashbackBingHeader,msEdgeShoppingUI,msEdgeSmartFind,msEdgeSuperDragDefaultEnabled,msEdgeSuperDragDropSupported,msEdgeTipping,msEdgeTranslate,msEdgeUseCaptivePortalService,msEnableCustomJobMemoryLimitsOnXbox,msEnableMIPForPDF,msEnablePdfUpsell,msEnableThirdPartyScanning,msEnableWebSignInCta,msEnableWebToBrowserSignIn,msEndpointDlp,msEntityExtraction,msExtensionTelemetryFramework,msExternalTaskManager,msFileSystemAccessDirectoryIterationBlocklistCheck,msForceBrowserSignIn,msForeignSessionsPage,msGeolocationAccessService,msGeolocationOSLocationPermissionFallback,msGeolocationSQMService,msGeolocationService,msGrowthInfraLaunchSourceLogging,msGuidedSwitchAllowed,msHubPinPersist,msImplicitSignin,msIrm,msIrmv2,msKlarnaVirtualCard,msLoadStatistics,msLogIsEdgePinnedToTaskbarOnLaunch,msMIPCrossTenantPdfViewSupport,msMdatpWebSiteDlp,msNotificationPermissionForPWA,msOnHoverSearchInSidebar,msOpenOfficeDocumentsInWebViewer,msPasswordBreachDetection,msPdfAnnotationsVisibility,msPdfDataRecovery,msPdfDigitalSignatureRead,msPdfFreeText,msPdfFreeTextForCJK,msPdfHighlightMode,msPdfInking,msPdfKeyphraseSupport,msPdfOOUI,msPdfPopupMarkerRenderer,msPdfShare,msPdfSharedLibrary,msPdfTextNote,msPdfTextNoteMoreMenu,msPdfThumbnailCache,msPdfUnderside,msPdfViewRestore,msPersonalizationUMA,msPriceComparison,msPromptDefaultHandlerForPDF,msReactiveSearch,msReadAloud,msReadAloudPdf,msRedirectToShoreline,msRevokeExtensions,msSaasDlp,msShoppingTrigger,msShorelineSearch,msShorelineSearchFindOnPageWebUI,msShowOfflineGameEntrance,msShowReadAloudIconInAddressBar,msShowUXForAADPrtSSOForNonAADProfile,msSmartScreenProtection,msSuspendMessageForNewSessionWhenHavingPendingNavigation,msSyncEdgeCollections,msTabResourceStats,msTokenizationAutofillInlineEnabled,msTouchMode,msTriggeringSignalGenerator,msUserUnderstanding,msVideoSuperResolutionUI,msWalletBuyNow,msWalletCheckout,msWalletDiagnosticDataLogger,msWalletHubEntry,msWalletHubIntlP3,msWalletPartialCard,msWalletPasswordCategorization,msWalletPasswordCategorizationPlatformExpansion,msWalletTokenizationCardMetadata,msWalletTokenizedAutofill,msWebAssist,msWebAssistHistorySearchService,msWebOOUI,msWindowsUserActivities,msZipPayVirtualCard --variations-seed-version --mojo-platform-channel-handle=1816 /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\134.0.3124.85\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Version: 134.0.3124.85 Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4124 --field-trial-handle=2468,i,15203847351246676719,1427791432541078913,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.45\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.45\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.45 Modules
| |||||||||||||||
| 1180 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=6076 --field-trial-handle=2468,i,15203847351246676719,1427791432541078913,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1764 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\krnl.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2400 --field-trial-handle=2404,i,6012606653723379666,10626864609850816894,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
29 190
Read events
26 225
Write events
2 880
Delete events
85
Modification events
| (PID) Process: | (1180) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1180) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1180) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3332) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3332) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3332) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5384) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5384) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5384) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4724) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
225
Suspicious files
229
Text files
87
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\0e38e4b0-c595-46e0-b874-ac4771419df2.down_data | — | |
MD5:— | SHA256:— | |||
| 5640 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5640 | msiexec.exe | C:\Windows\Installer\117e16.msi | — | |
MD5:— | SHA256:— | |||
| 3332 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
| 3332 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:FAABA7DC2EE173B093A427F1BC55A2D7 | SHA256:4DD64BD9866CD2A98768C0EEC05A5C90DB4D329F6CB974E65D5A2A73F65DBE29 | |||
| 3332 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\f829c78f-18b3-4b81-945c-523afca8ec98.up_meta_secure | binary | |
MD5:1F8A0BC86FB85D89EF35F0D9F41B79F2 | SHA256:3E1FF09A4A31D0F6285CA48D103F98DEEA0DB1F370C82E7BE7EDA846139A3F54 | |||
| 5640 | msiexec.exe | C:\Windows\Temp\~DF38A45651B825DA53.TMP | binary | |
MD5:607DC076099107B1FF6C8979F2C37C1C | SHA256:3C70E93AE762172B8700B592A291C19C0FC2195EBFAAC2E166BA93A6545FABAF | |||
| 5640 | msiexec.exe | C:\Program Files\jjsploit\resources\luascripts\animations\walkthrough.lua | text | |
MD5:348E2FCFE114EF12E8DB7AE75F24DE15 | SHA256:10409B6D213DB5683EC415FA1A8CDE85B38FD057C9AA7B88C3FE4FBB19CD54B0 | |||
| 5640 | msiexec.exe | C:\Program Files\jjsploit\resources\luascripts\jailbreak\walkspeed.lua | binary | |
MD5:76D6BC545A92D108FF8A18614A5DB4AD | SHA256:A7931EE89662C563637E1752228923D182F42F3A70286D4FD0A1FFF993C9766D | |||
| 5640 | msiexec.exe | C:\Program Files\jjsploit\jjsploit.exe | executable | |
MD5:383EF1F70F833F175C588CAB85110FDA | SHA256:2C349879607FF4788B904CAC39A1593D676B04EB4FE783F02BC1418D8C05E1F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
89
DNS requests
92
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7488 | svchost.exe | GET | — | 2.22.242.227:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/54330a82-b66a-4d12-9e98-b1ce9efcbd87?P1=1743468305&P2=404&P3=2&P4=Nzks9F%2fCtp%2bAsCxYHeCzFQ8eZzG2nD5t9ioZ%2fehnPl4TnnVRyp1fW8F6SSZ%2bZ5mo0vIiwF978irFD95ZWsa9bg%3d%3d | unknown | — | — | whitelisted |
4380 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6112 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3332 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6112 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7488 | svchost.exe | HEAD | 200 | 2.22.242.227:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/54330a82-b66a-4d12-9e98-b1ce9efcbd87?P1=1743468305&P2=404&P3=2&P4=Nzks9F%2fCtp%2bAsCxYHeCzFQ8eZzG2nD5t9ioZ%2fehnPl4TnnVRyp1fW8F6SSZ%2bZ5mo0vIiwF978irFD95ZWsa9bg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4380 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4380 | backgroundTaskHost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7488 | svchost.exe | Misc activity | ET INFO Packed Executable Download |
5260 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5260 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5260 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5260 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5260 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5260 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5260 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5260 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5260 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |