| File name: | 314-Fliqlo Setup.exe |
| Full analysis: | https://app.any.run/tasks/1dafb367-1c6c-4bd5-89c6-720c6598505b |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2019, 18:03:06 |
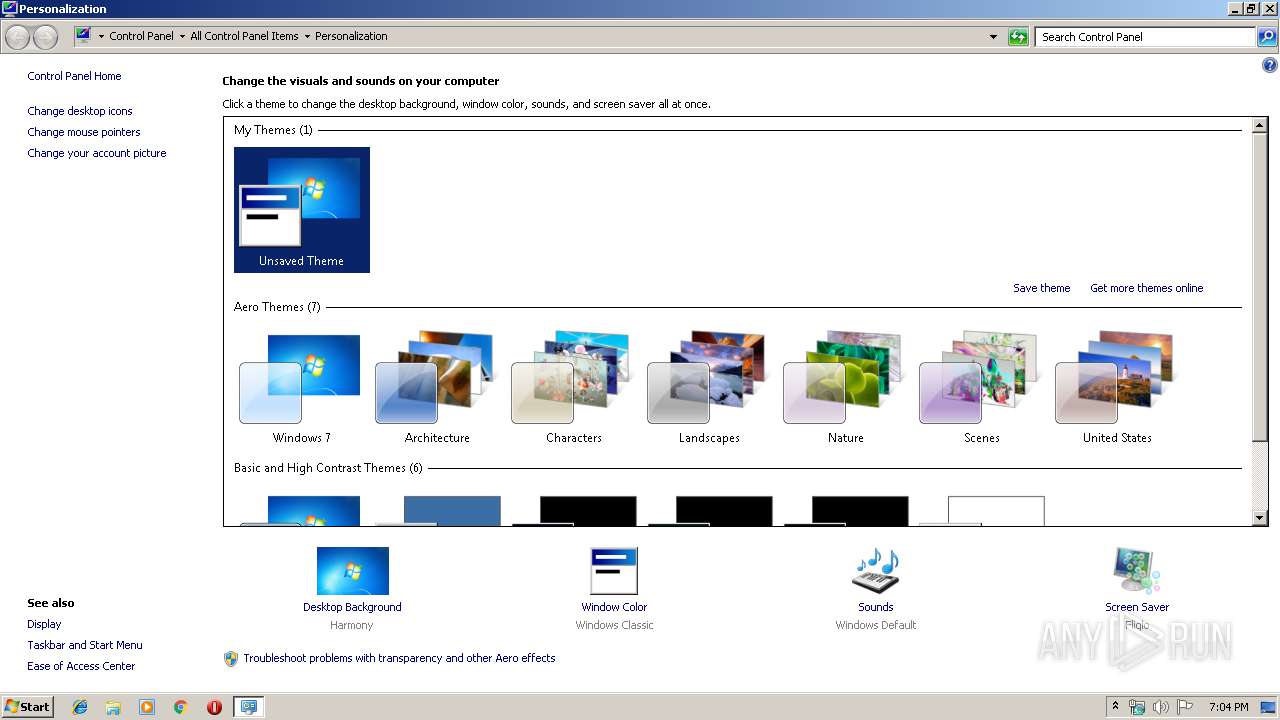
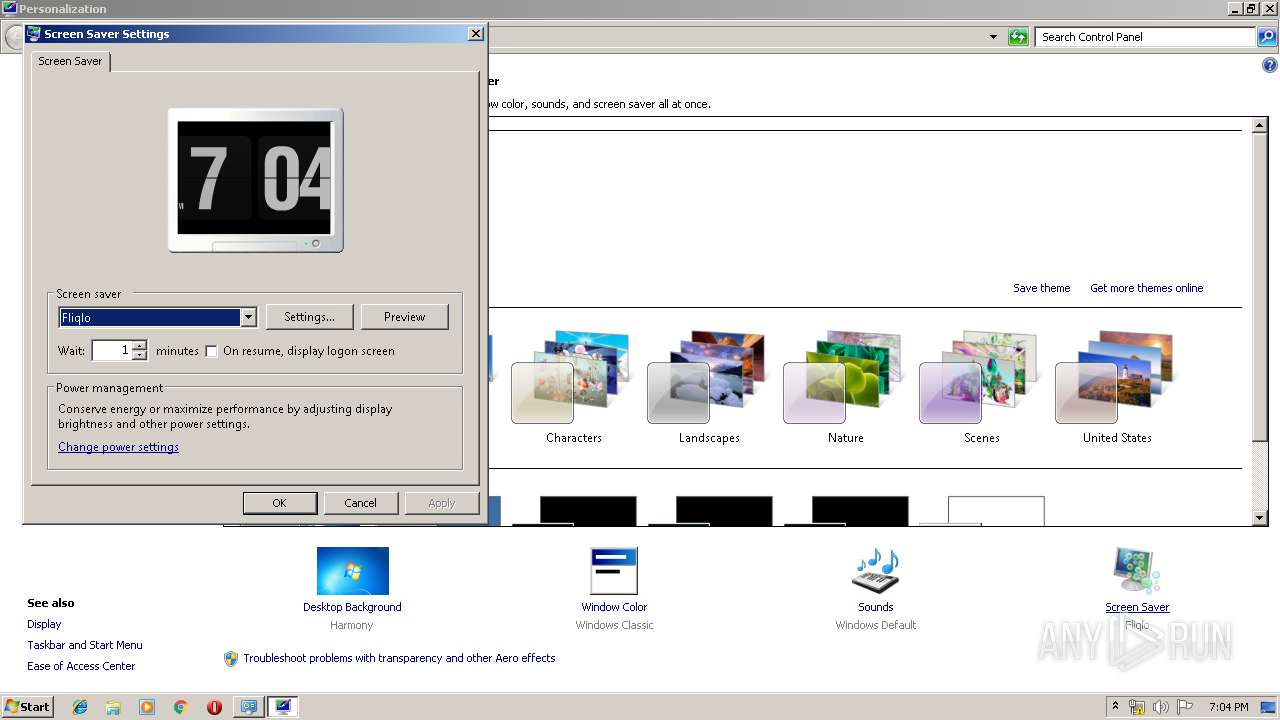
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8630D93FA5297EB76E0F9099ABC220DA |
| SHA1: | 4C05D4745137C7B8E2CA304F3E2D5A80CA4DC581 |
| SHA256: | 0D38C697E869451A96ADE9D5C7BE28464C93562E906055D6B7960E7F12A87180 |
| SSDEEP: | 98304:7nTikwhtVoWjJI4Yaaq3EgXG1UbPtP+GUjFrOevzjoV:UTI4Qq3EeOaPC0qjoV |
MALICIOUS
Application was dropped or rewritten from another process
- 314-Fliqlo Setup.exe (PID: 2556)
- Fliqlo.scr (PID: 2588)
- Fliqlo.scr (PID: 4064)
- Fliqlo.scr (PID: 2832)
- Fliqlo.scr (PID: 2700)
- Fliqlo.scr (PID: 3168)
- 314-Fliqlo Setup.exe (PID: 2872)
- Fliqlo.scr (PID: 3672)
- Fliqlo.scr (PID: 3800)
Loads dropped or rewritten executable
- Fliqlo.scr (PID: 2588)
- 314-Fliqlo Setup.exe (PID: 2872)
- explorer.exe (PID: 252)
- Fliqlo.scr (PID: 3800)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- 314-Fliqlo Setup.exe (PID: 3160)
- explorer.exe (PID: 252)
Creates a software uninstall entry
- 314-Fliqlo Setup.exe (PID: 2872)
Creates files in the program directory
- Fliqlo.scr (PID: 2832)
- Fliqlo.scr (PID: 3168)
- 314-Fliqlo Setup.exe (PID: 2872)
Creates files in the user directory
- Fliqlo.scr (PID: 3168)
- explorer.exe (PID: 252)
- Fliqlo.scr (PID: 2832)
Executable content was dropped or overwritten
- 314-Fliqlo Setup.exe (PID: 2872)
- 314-Fliqlo Setup.exe (PID: 3160)
Creates files in the Windows directory
- 314-Fliqlo Setup.exe (PID: 2872)
Starts application with an unusual extension
- rundll32.exe (PID: 2596)
- rundll32.exe (PID: 2468)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (49.2) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (16.2) |
| .scr | | | Windows screen saver (14.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 426496 |
| InitializedDataSize: | 100352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6905c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.3.0 |
| ProductVersionNumber: | 4.0.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 4.0.3.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 4.0.3.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000681D0 | 0x00068200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5533 |
DATA | 0x0006A000 | 0x000014E4 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.22226 |
BSS | 0x0006C000 | 0x00000EED | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0006D000 | 0x00002732 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.99973 |
.tls | 0x00070000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00071000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.158427 |
.reloc | 0x00072000 | 0x00007440 | 0x00007600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.65463 |
.rsrc | 0x0007A000 | 0x0000D158 | 0x0000D200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.12404 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85046 | 483 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.72846 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.69864 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.15749 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.41955 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.68711 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 2.91604 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4080 | 3.37878 | 2320 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4081 | 3.25128 | 1312 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4082 | 3.25323 | 1400 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
SHFolder.dll |
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
47
Monitored processes
13
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
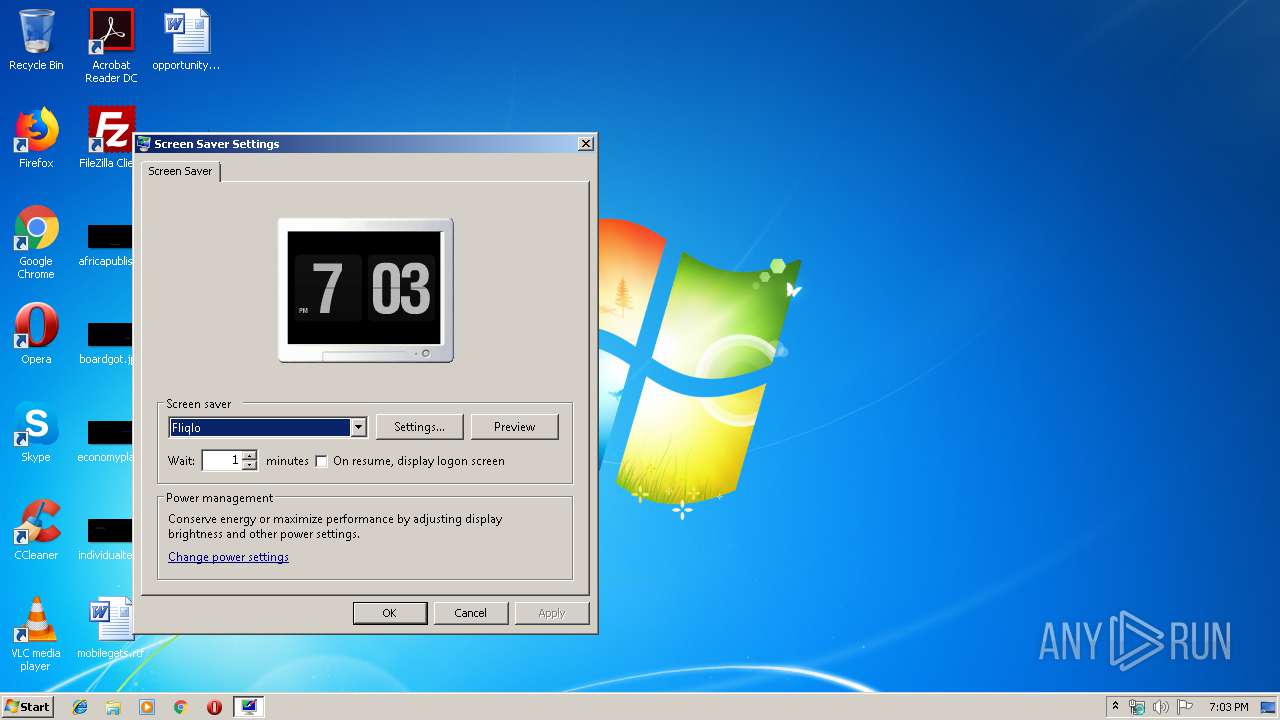
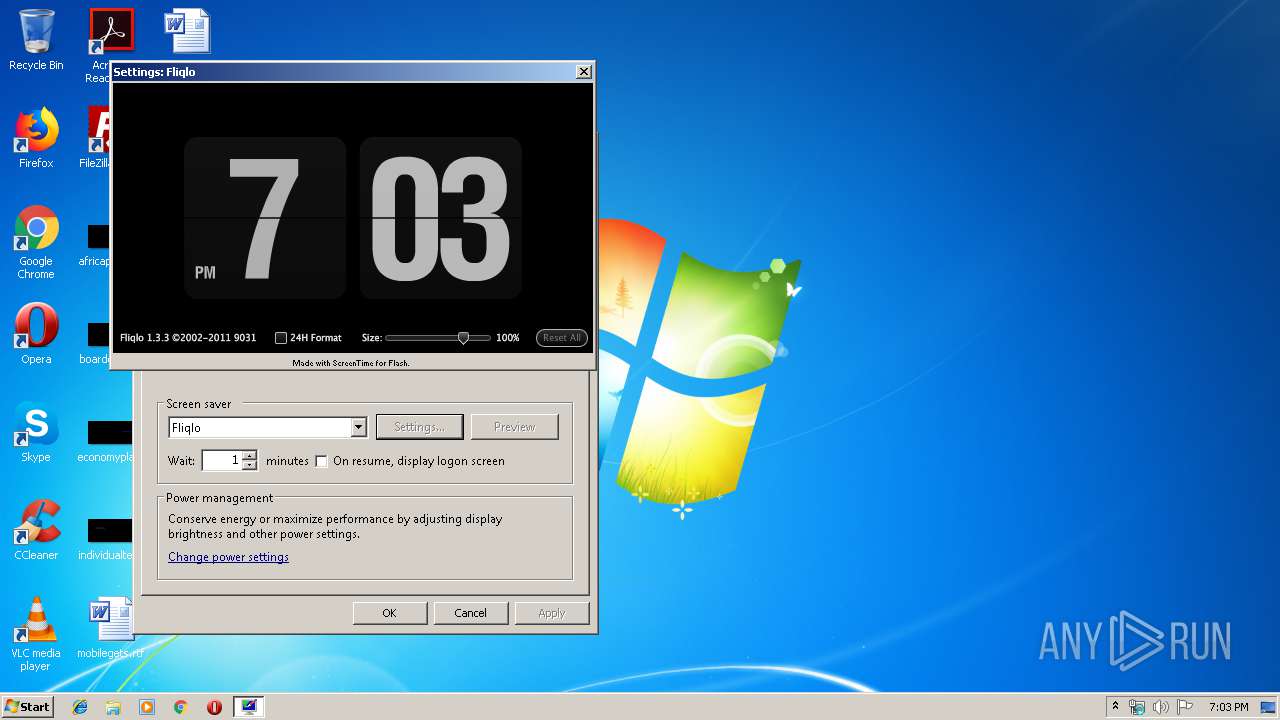
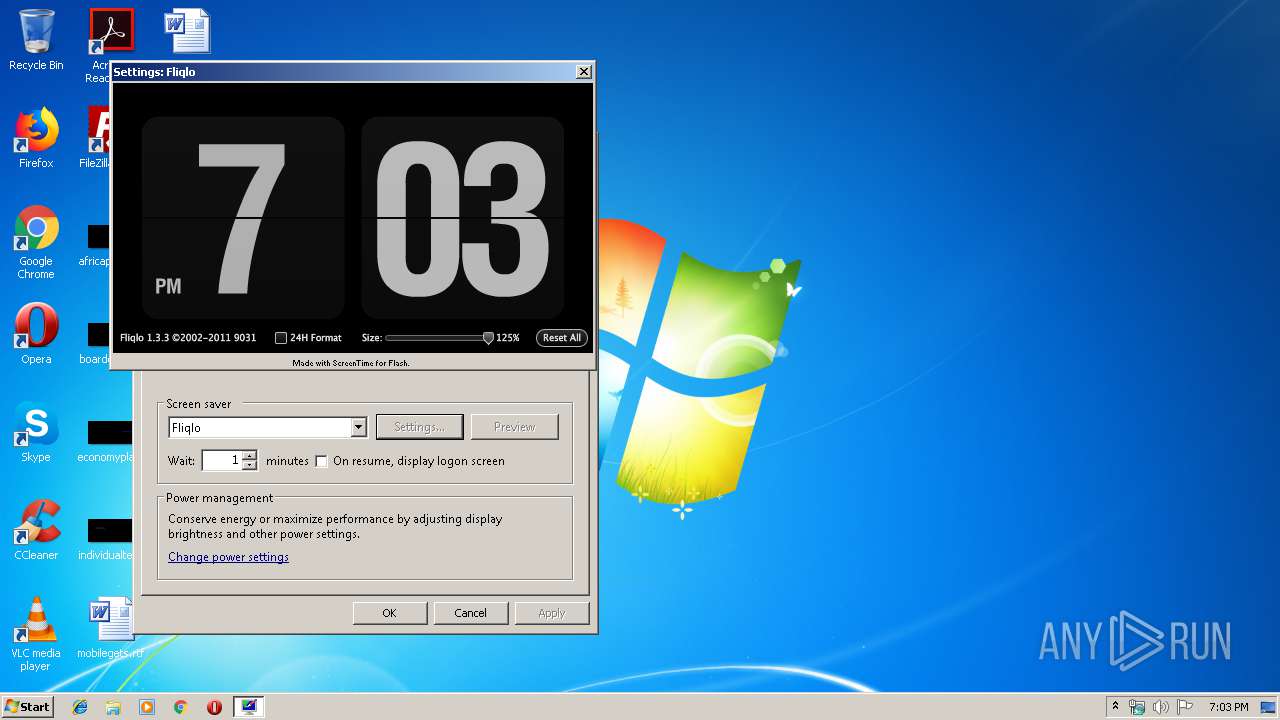
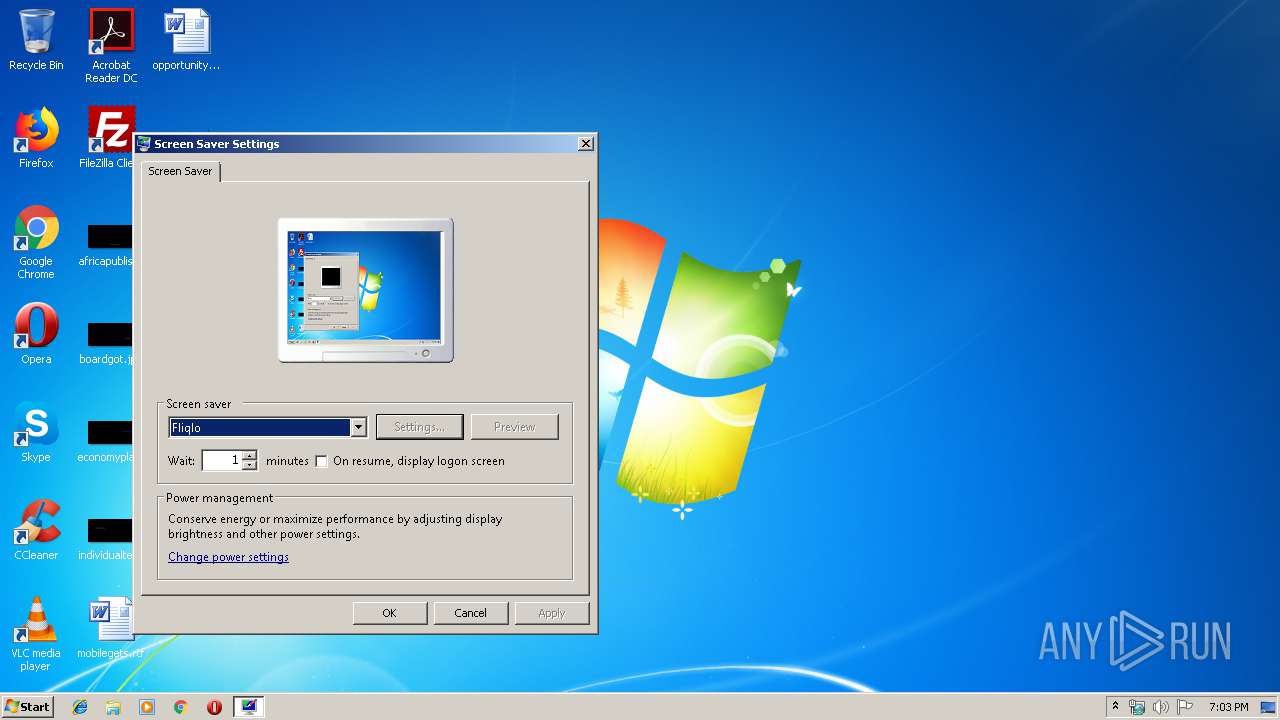
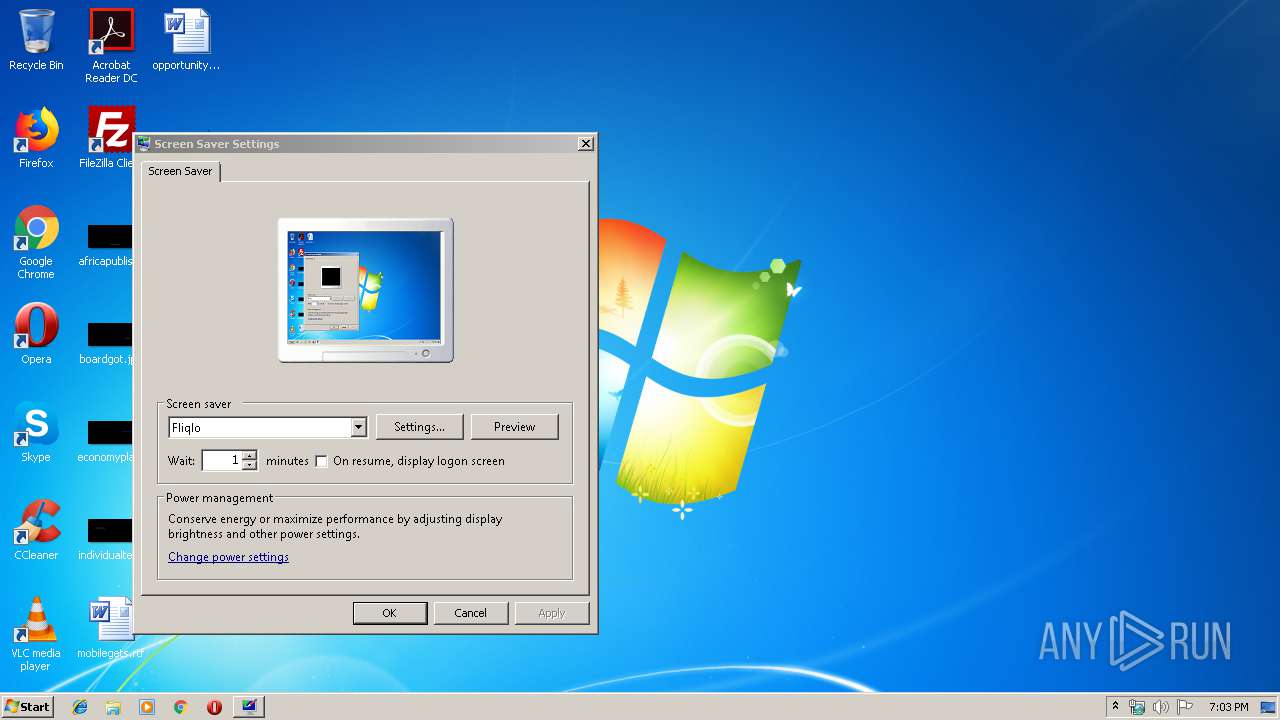
| 2468 | rundll32.exe shell32.dll,Control_RunDLL desk.cpl,,1 | C:\Windows\system32\rundll32.exe | — | 314-Fliqlo Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Users\admin\AppData\Local\Screentime\STF1\314-Fliqlo Setup.exe" /l=196912 | C:\Users\admin\AppData\Local\Screentime\STF1\314-Fliqlo Setup.exe | — | 314-Fliqlo Setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Screen Saver Installer Exit code: 3221226540 Version: 4.0.3.0 Modules
| |||||||||||||||
| 2588 | C:\Windows\system32\Fliqlo.scr /s | C:\Windows\system32\Fliqlo.scr | — | rundll32.exe | |||||||||||
User: admin Company: ScreenTime Media Integrity Level: MEDIUM Description: ScreenTime Screensaver Engine Exit code: 0 Version: 4.0.2 Modules
| |||||||||||||||
| 2596 | "C:\Windows\System32\rundll32.exe" shell32.dll,Control_RunDLL desk.cpl,ScreenSaver,@ScreenSaver | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2700 | C:\Windows\system32\Fliqlo.scr /p 131448 | C:\Windows\system32\Fliqlo.scr | — | rundll32.exe | |||||||||||
User: admin Company: ScreenTime Media Integrity Level: MEDIUM Description: ScreenTime Screensaver Engine Exit code: 0 Version: 4.0.2 Modules
| |||||||||||||||
| 2832 | C:\Windows\system32\Fliqlo.scr /p 131448 | C:\Windows\system32\Fliqlo.scr | rundll32.exe | ||||||||||||
User: admin Company: ScreenTime Media Integrity Level: MEDIUM Description: ScreenTime Screensaver Engine Exit code: 0 Version: 4.0.2 Modules
| |||||||||||||||
| 2872 | "C:\Users\admin\AppData\Local\Screentime\STF1\314-Fliqlo Setup.exe" /l=196912 | C:\Users\admin\AppData\Local\Screentime\STF1\314-Fliqlo Setup.exe | 314-Fliqlo Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Screen Saver Installer Exit code: 0 Version: 4.0.3.0 Modules
| |||||||||||||||
| 3160 | "C:\Users\admin\AppData\Local\Temp\314-Fliqlo Setup.exe" | C:\Users\admin\AppData\Local\Temp\314-Fliqlo Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 4.0.3.0 Modules
| |||||||||||||||
| 3168 | C:\Windows\system32\Fliqlo.scr /c:131390 | C:\Windows\system32\Fliqlo.scr | — | rundll32.exe | |||||||||||
User: admin Company: ScreenTime Media Integrity Level: MEDIUM Description: ScreenTime Screensaver Engine Exit code: 2 Version: 4.0.2 Modules
| |||||||||||||||
Total events
1 694
Read events
1 392
Write events
302
Delete events
0
Modification events
| (PID) Process: | (3160) 314-Fliqlo Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3160) 314-Fliqlo Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2468) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2468) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @themeui.dll,-854 |
Value: Windows Classic | |||
| (PID) Process: | (2468) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @themeui.dll,-2019 |
Value: Normal | |||
| (PID) Process: | (2468) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @themeui.dll,-850 |
Value: High Contrast #1 | |||
| (PID) Process: | (2468) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @themeui.dll,-851 |
Value: High Contrast #2 | |||
| (PID) Process: | (2468) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @themeui.dll,-852 |
Value: High Contrast Black | |||
| (PID) Process: | (2468) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @themeui.dll,-853 |
Value: High Contrast White | |||
| (PID) Process: | (2468) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @mmres.dll,-800 |
Value: Windows Default | |||
Executable files
14
Suspicious files
2
Text files
3
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | 314-Fliqlo Setup.exe | C:\Users\admin\AppData\Local\Screentime\STF2\Fliqlo.ssd | — | |
MD5:— | SHA256:— | |||
| 3160 | 314-Fliqlo Setup.exe | C:\Users\admin\AppData\Local\Screentime\STF1\314-Fliqlo Setup.DE | executable | |
MD5:— | SHA256:— | |||
| 3160 | 314-Fliqlo Setup.exe | C:\Users\admin\AppData\Local\Screentime\STF1\314-Fliqlo Setup.ES | executable | |
MD5:— | SHA256:— | |||
| 3160 | 314-Fliqlo Setup.exe | C:\Users\admin\AppData\Local\Screentime\STF1\314-Fliqlo Setup.FR | executable | |
MD5:— | SHA256:— | |||
| 2832 | Fliqlo.scr | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 2832 | Fliqlo.scr | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sol | — | |
MD5:— | SHA256:— | |||
| 3168 | Fliqlo.scr | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\#local\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 3160 | 314-Fliqlo Setup.exe | C:\Users\admin\AppData\Local\Screentime\STF1\314-Fliqlo Setup.JPN | executable | |
MD5:— | SHA256:— | |||
| 3168 | Fliqlo.scr | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 3160 | 314-Fliqlo Setup.exe | C:\Users\admin\AppData\Local\Screentime\STF1\314-Fliqlo Setup.CAT | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2832 | Fliqlo.scr | GET | 301 | 199.204.248.117:80 | http://services.screentime.com/saver?purpose=askUsersFirewallAppForOnlineContentPermission&platform=Windows&version=3.7&command=ping | US | html | 353 b | suspicious |
2832 | Fliqlo.scr | GET | 200 | 199.204.248.117:80 | http://services.screentime.com/saver/?purpose=askUsersFirewallAppForOnlineContentPermission&platform=Windows&version=3.7&command=ping | US | html | 742 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2832 | Fliqlo.scr | 199.204.248.117:80 | services.screentime.com | CONTINENTAL BROADBAND PENNSYLVANIA, INC. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
services.screentime.com |
| suspicious |