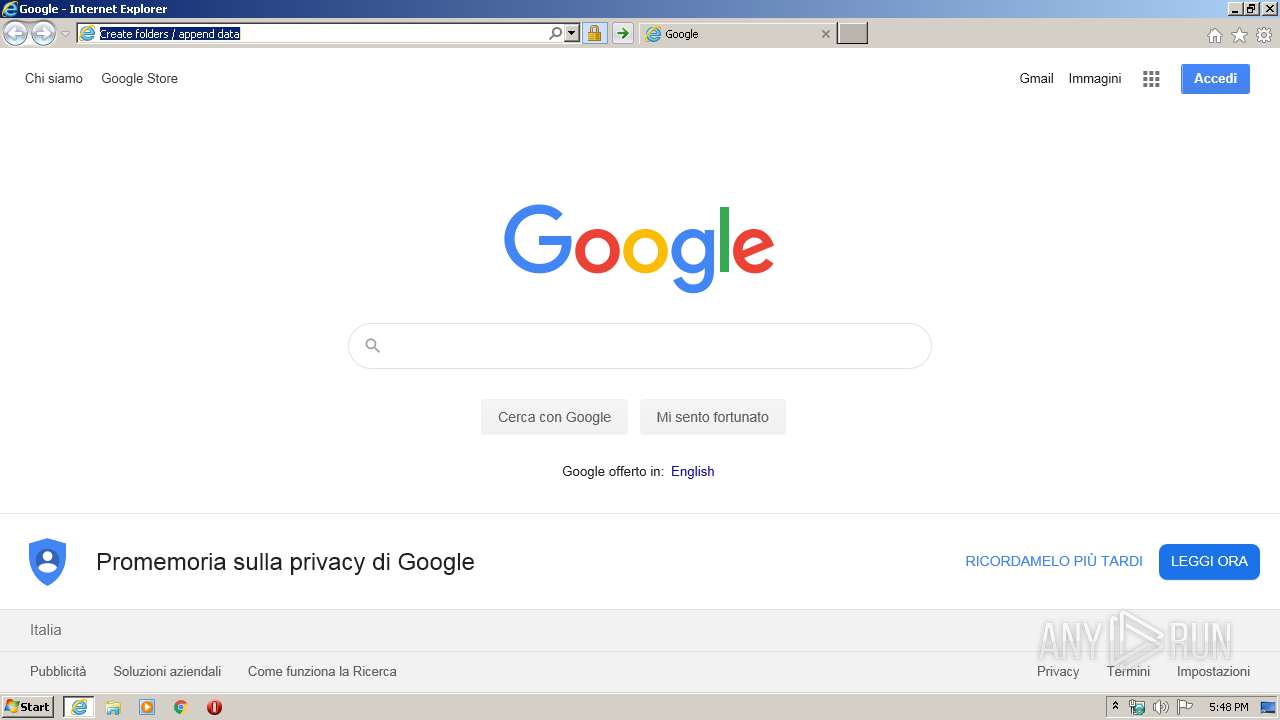
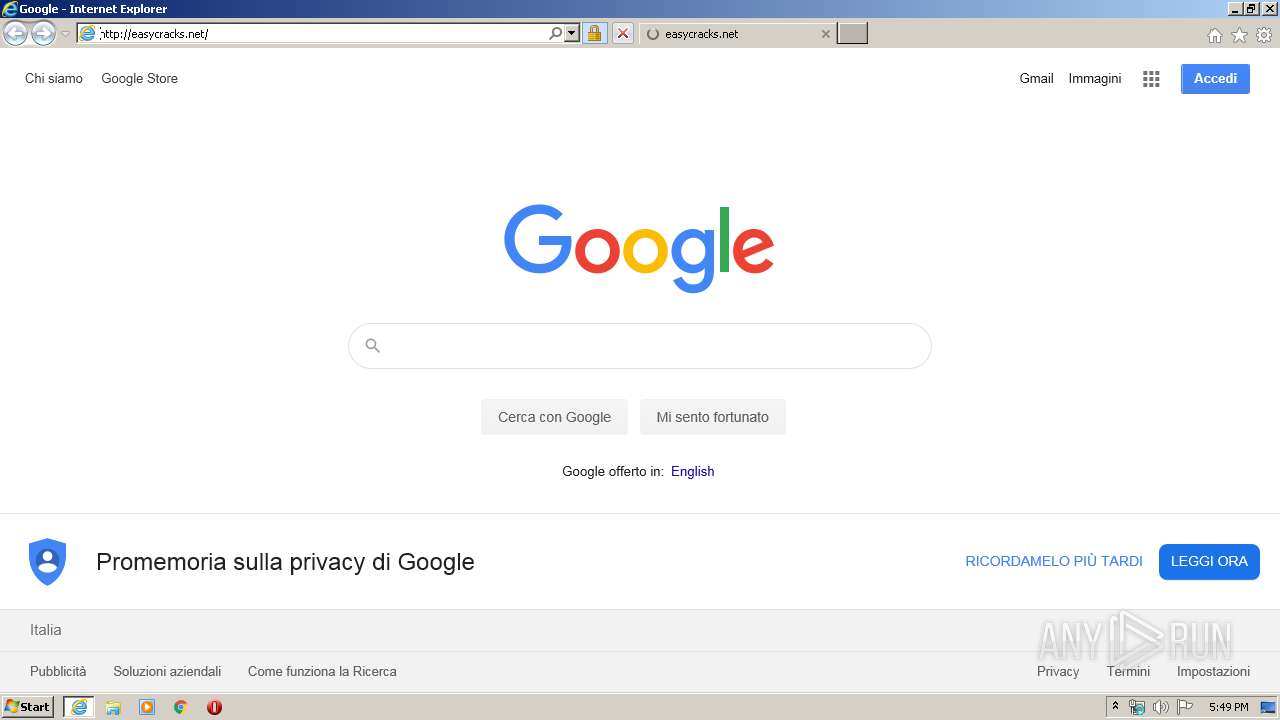
| URL: | http://Easycracks.net |
| Full analysis: | https://app.any.run/tasks/f85fba9c-aa0b-46e0-b37c-4ccbb61e8cd3 |
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2020, 17:48:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 15685CD124B3270798E71EF04781060E |
| SHA1: | DE01A69D0130719CB8E0BEF7797E7622D3A5E320 |
| SHA256: | 0D11AF79E489093B964EF756D960C6FAFF4F7A900C4BF82AE01AD2F0C1A00613 |
| SSDEEP: | 3:N1KwGXto:C7O |
MALICIOUS
Connects to CnC server
- iexplore.exe (PID: 4004)
SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2556)
- iexplore.exe (PID: 4004)
Changes internet zones settings
- iexplore.exe (PID: 2556)
Application launched itself
- iexplore.exe (PID: 2556)
Reads internet explorer settings
- iexplore.exe (PID: 4004)
Creates files in the user directory
- iexplore.exe (PID: 4004)
Reads settings of System Certificates
- iexplore.exe (PID: 2556)
- iexplore.exe (PID: 4004)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2556)
Changes settings of System certificates
- iexplore.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
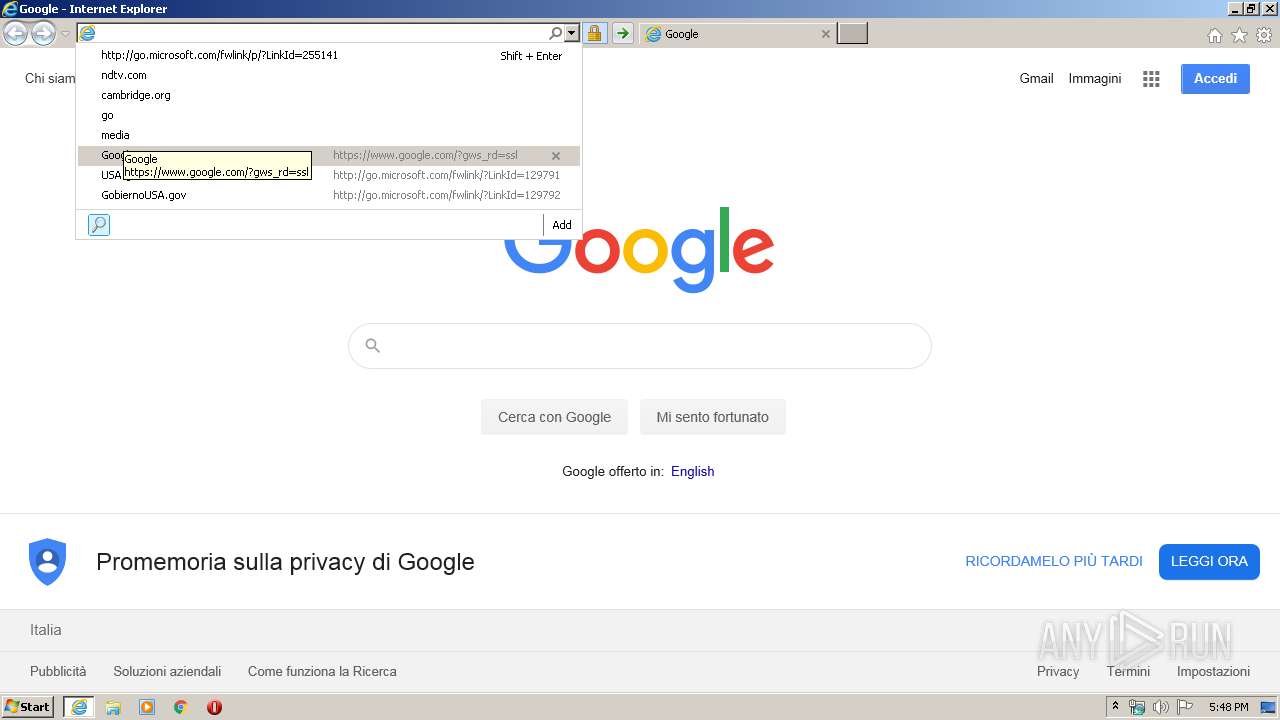
| 2556 | "C:\Program Files\Internet Explorer\iexplore.exe" http://Easycracks.net | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4004 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2556 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 104
Read events
805
Write events
3 582
Delete events
1 717
Modification events
| (PID) Process: | (4004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 4265698816 | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30797004 | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
19
Text files
85
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4004 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PGXAICWX.txt | — | |
MD5:— | SHA256:— | |||
| 4004 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9032.tmp | — | |
MD5:— | SHA256:— | |||
| 4004 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9033.tmp | — | |
MD5:— | SHA256:— | |||
| 4004 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\24X8C0F2.txt | — | |
MD5:— | SHA256:— | |||
| 4004 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
| 4004 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\U2815OK4.txt | — | |
MD5:— | SHA256:— | |||
| 4004 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3PCSQWH5.txt | text | |
MD5:— | SHA256:— | |||
| 4004 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BE8B021F9E811DFC8C8A28572A17C05A_EE6FD365CEA70AC1381BEED92EFF2B2D | binary | |
MD5:— | SHA256:— | |||
| 4004 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
75
DNS requests
31
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
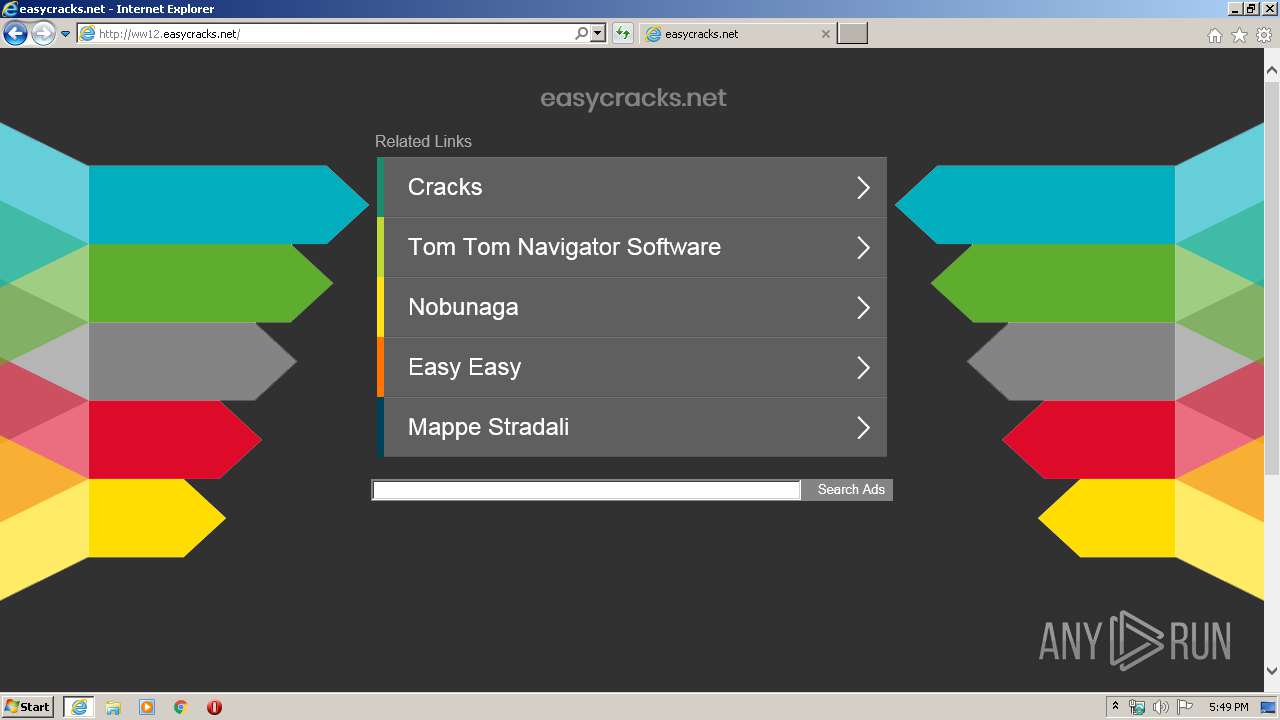
4004 | iexplore.exe | GET | 302 | 173.192.101.24:80 | http://p237996.infopicked.com/adServe/domainClick?ai=U8ZURO00fl2SYrelsQnMH5lA7GUW-HKEciyxKRlES6DhH2lrXnMnkpTLni6O_bWTGW2M-edZHsAhJSl_EVXEcdBObiWMD4tAIL21jCtCf6AJhUg7v22G0jhnPQfylNscV29IB8WqRbe5EXcHUXnUq_FFzqKDcsZ503wlfnQlreYBsYRD6CCI5RNecs-9vJK1f_1vyTLYjVsoLuBAIS3oVWWp__riXRnqGnLL9g3RhC2ktJmalqtYdZjIilsK9IV1ujk8cdugKbzmppkcUS_GjgGXVJuRWpEGwFHe8-IbtOTaPI3CDFx_TyP7mk1bIMnLmn-959f6DtYrmaG7NYcOGFt1qWUu66kFqUzaeYhSjwo4wze4caGpDvAdDxfNZOFVxWfBO_Pgkf9Lj9hxf0SJk0tVfUbfcXAUJnPWw0bavLxuFSFLz0EJSRe7zzBJbLAQvEGFQ0jWJkN4bvlPQArirXHpAiEoSXb7bgejlzf67IHJhBqnpFAYj9ilJX2Njxml&ui=tmxvfbadWlldvuMNwCCY97BxJKm2U5HnLWXp3on882KiNKxwAofaTA0TwyMmfdNzY3SCSClU0r38c68QLgbs6s_KQEwvpjAlH28GIJbFsql7EbH7hsdlxtxt42o_0iXiv4iYFImmJT4&si=1&oref=540607889c6f1392f5016709ff951176&rb=d_wwTvPFgK4&rr=0&isco=t | US | — | — | suspicious |
4004 | iexplore.exe | GET | 302 | 67.227.226.240:80 | http://easycracks.net/ | US | — | — | malicious |
4004 | iexplore.exe | GET | 200 | 2.21.242.197:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
4004 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDvdxhhS3x8DggAAAAALnGY | US | der | 472 b | whitelisted |
4004 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCZXC%2BXyoEf%2BQgAAAAALnGl | US | der | 472 b | whitelisted |
2556 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
4004 | iexplore.exe | GET | 200 | 2.21.242.197:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
4004 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCZXC%2BXyoEf%2BQgAAAAALnGl | US | der | 472 b | whitelisted |
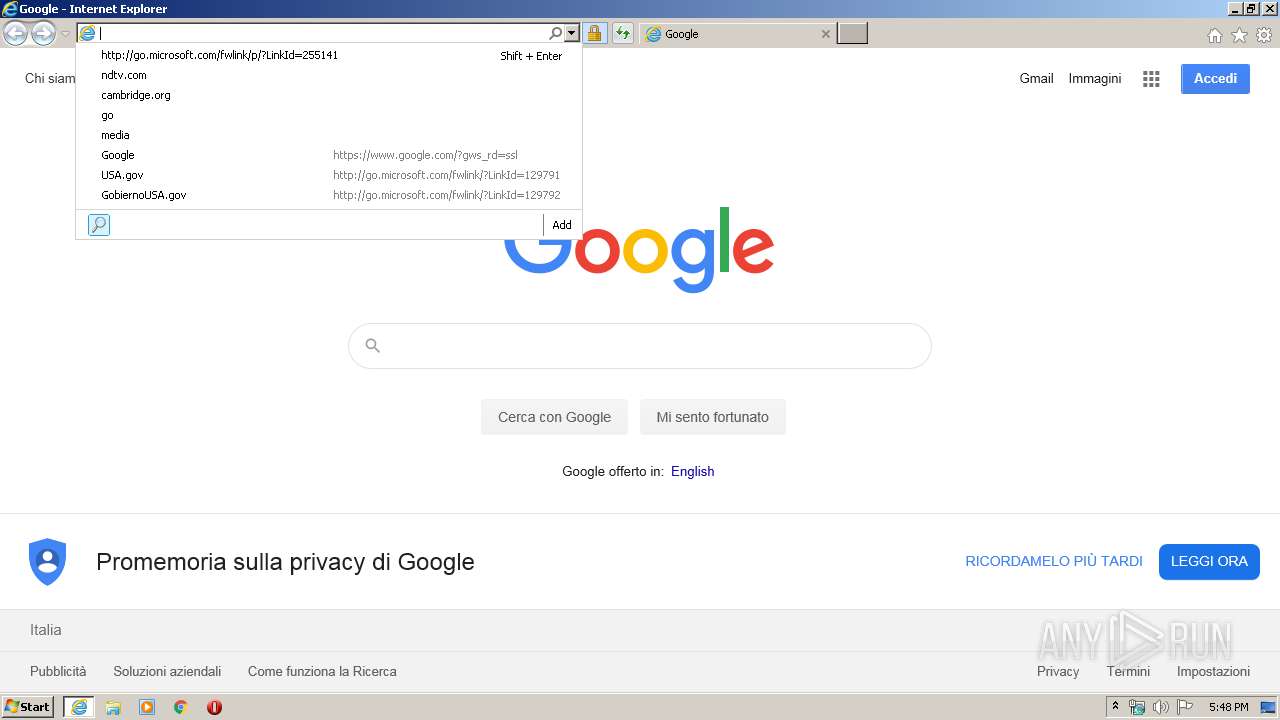
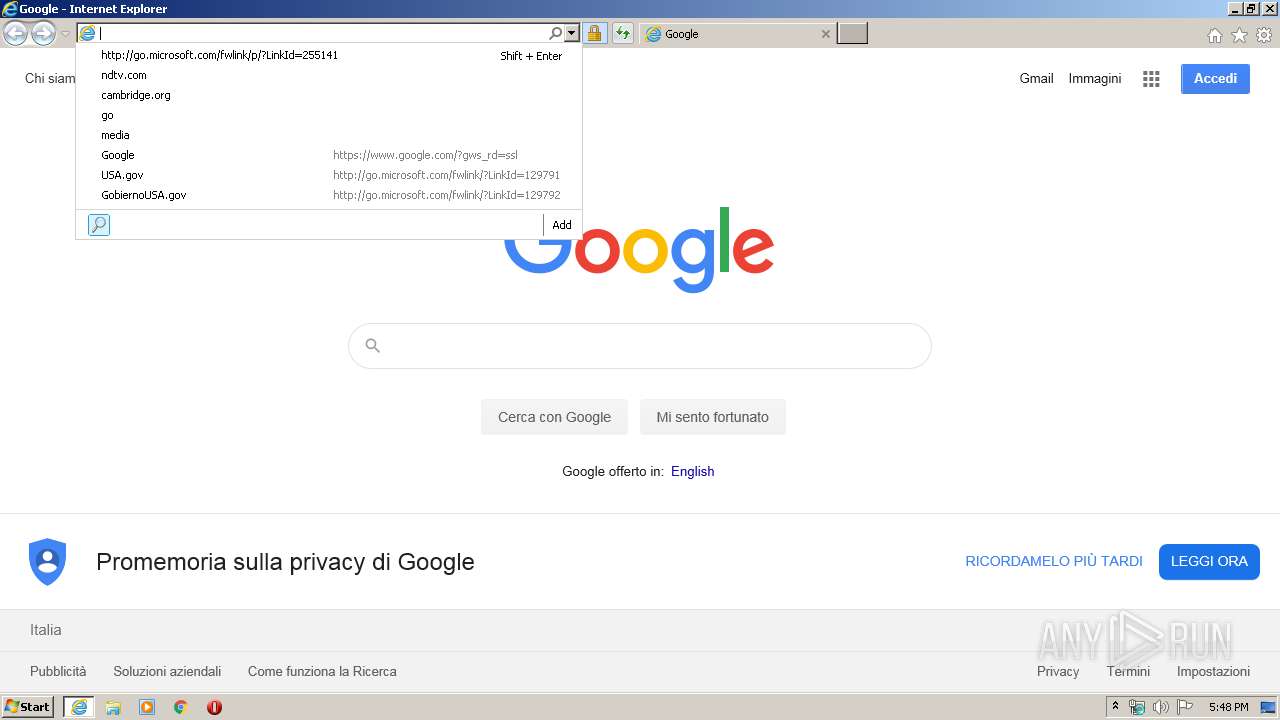
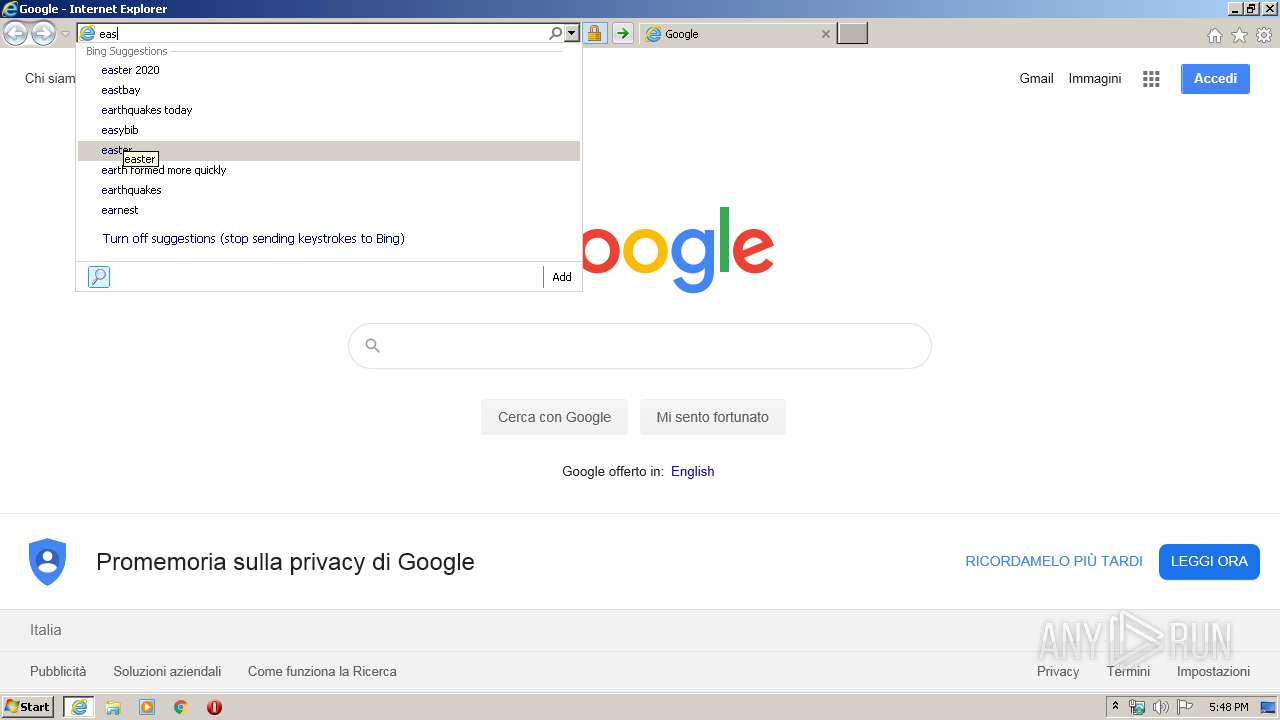
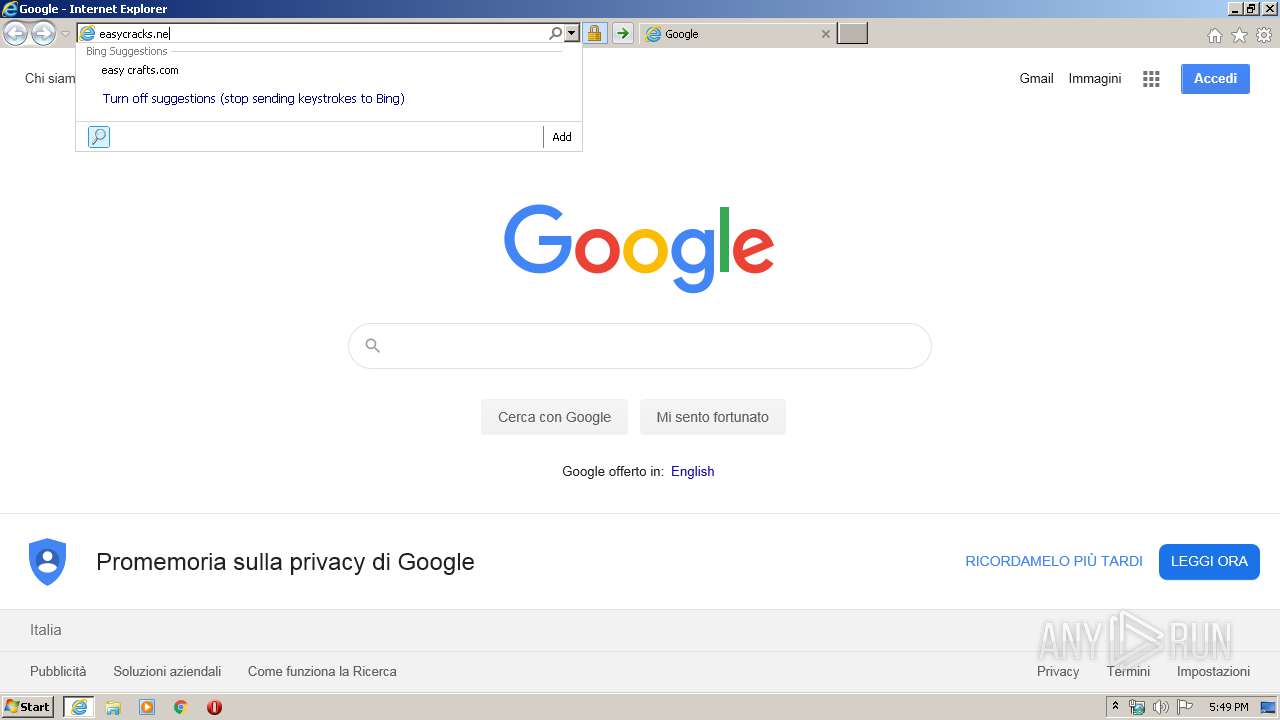
4004 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=easycracks.n&maxwidth=506&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 188 b | whitelisted |
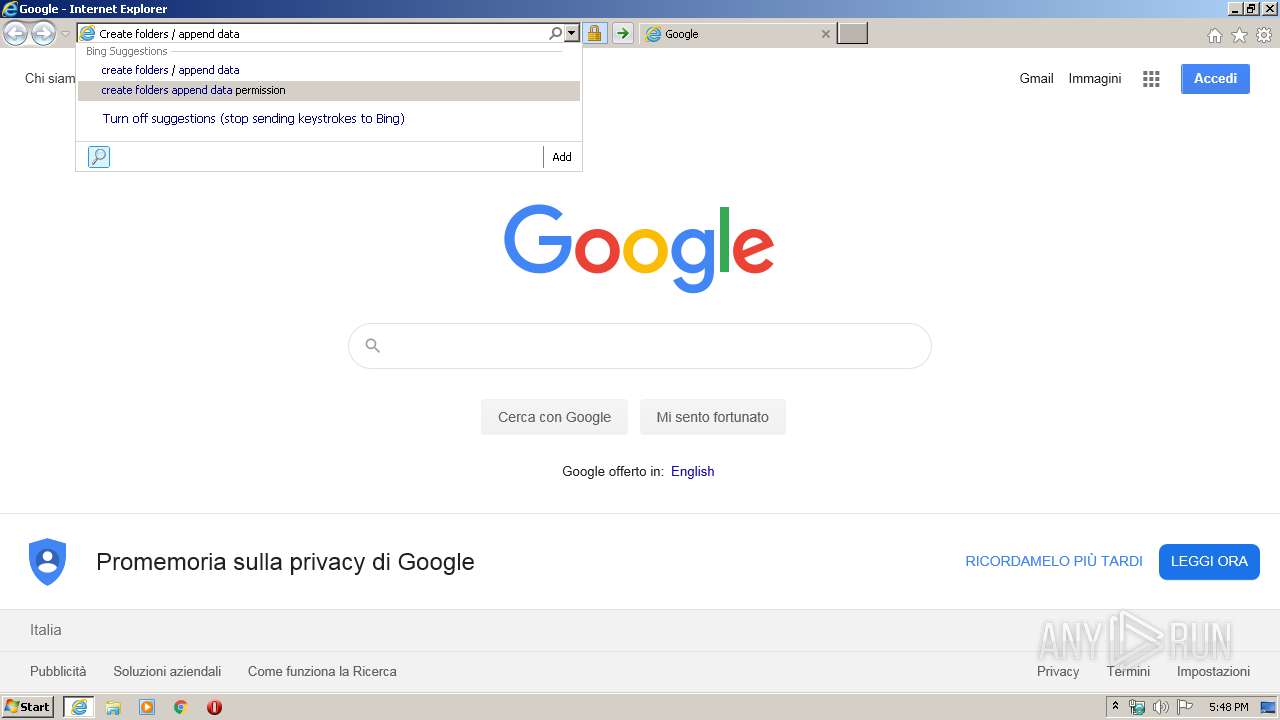
4004 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=Create+folders+%2F+append+data&maxwidth=506&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 211 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2556 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4004 | iexplore.exe | 67.227.226.240:80 | easycracks.net | Liquid Web, L.L.C | US | malicious |
4004 | iexplore.exe | 2.21.242.197:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
4004 | iexplore.exe | 173.192.101.24:80 | infopicked.com | SoftLayer Technologies Inc. | US | suspicious |
4004 | iexplore.exe | 116.202.114.158:443 | eutrx.com | 334,Udyog Vihar | IN | unknown |
— | — | 172.217.16.206:80 | google.com | Google Inc. | US | whitelisted |
4004 | iexplore.exe | 172.217.23.132:80 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.132:80 | www.google.com | Google Inc. | US | whitelisted |
4004 | iexplore.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
4004 | iexplore.exe | 172.217.16.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
easycracks.net |
| malicious |
infopicked.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
p237996.infopicked.com |
| suspicious |
eutrx.com |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
google.com |
| malicious |
www.google.com |
| malicious |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4004 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Parkingcrew Monetize Tracker Checkin |
4004 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Parkingcrew Monetize Tracker Checkin |