analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
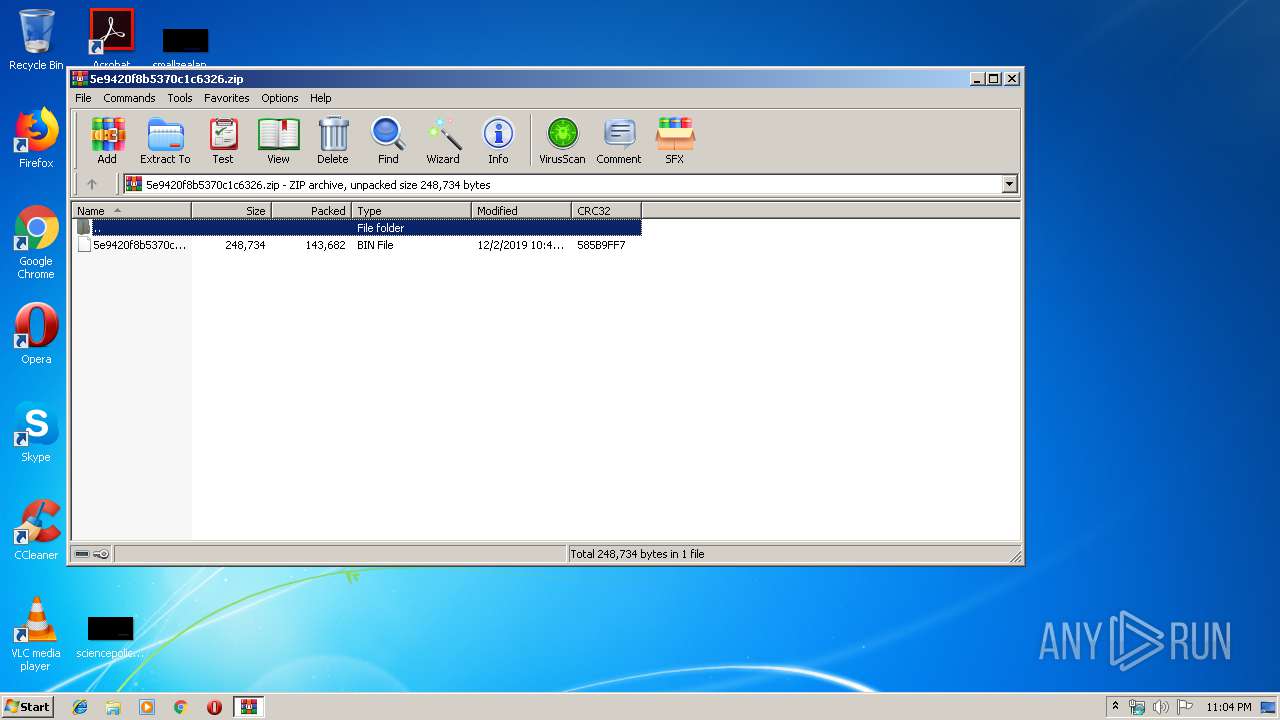
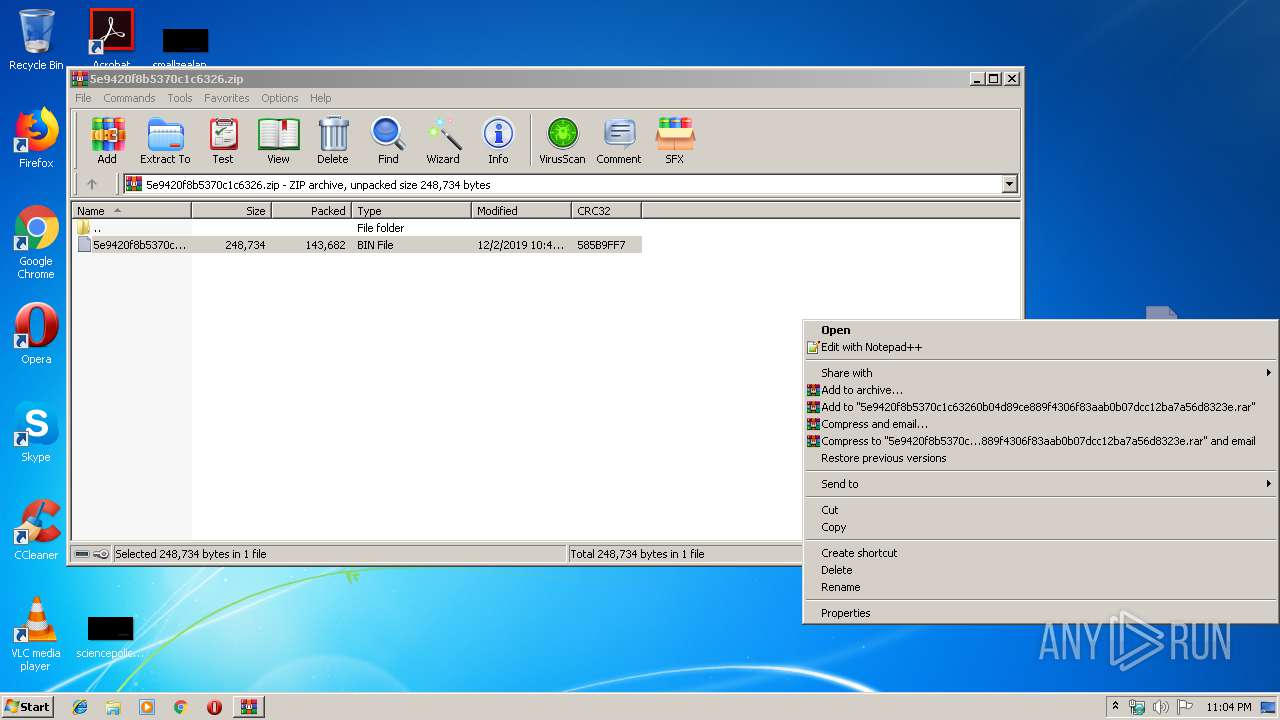
| File name: | 5e9420f8b5370c1c6326.zip |
| Full analysis: | https://app.any.run/tasks/66dcd7d1-ffcc-4740-9b54-7399889864bd |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 23:04:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 3CC6799CCB1D6ACDC9A7E4ED585FD6C4 |
| SHA1: | 34746A6DD8D60B3A9201759FB6EC09588BCF9DDC |
| SHA256: | 0CF79AE21692707FC7EC1647BE2927E8A3F448FDC60851F9A7F0F88C1B09989D |
| SSDEEP: | 3072:uKjosI1Vr30XNXlEDHVn+Y7sZP8V+y+B5YAhpjYe33zTkxvZM9wBrEt:uK0sqVr30XZlEbUoUDTpMe3vEZM9Mwt |
MALICIOUS
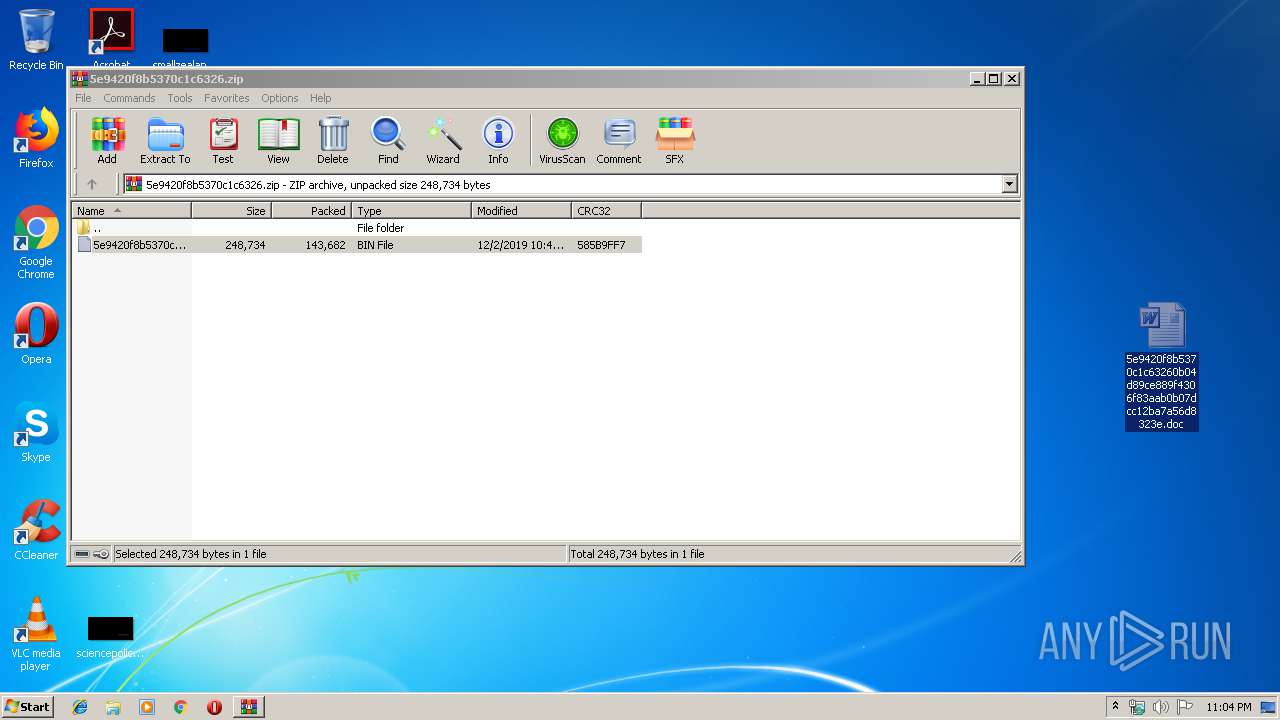
Drops known malicious document
- WINWORD.EXE (PID: 2888)
SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2888)
- WINWORD.EXE (PID: 2092)
Manual execution by user
- WINWORD.EXE (PID: 2092)
- WINWORD.EXE (PID: 2888)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2888)
- WINWORD.EXE (PID: 2092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
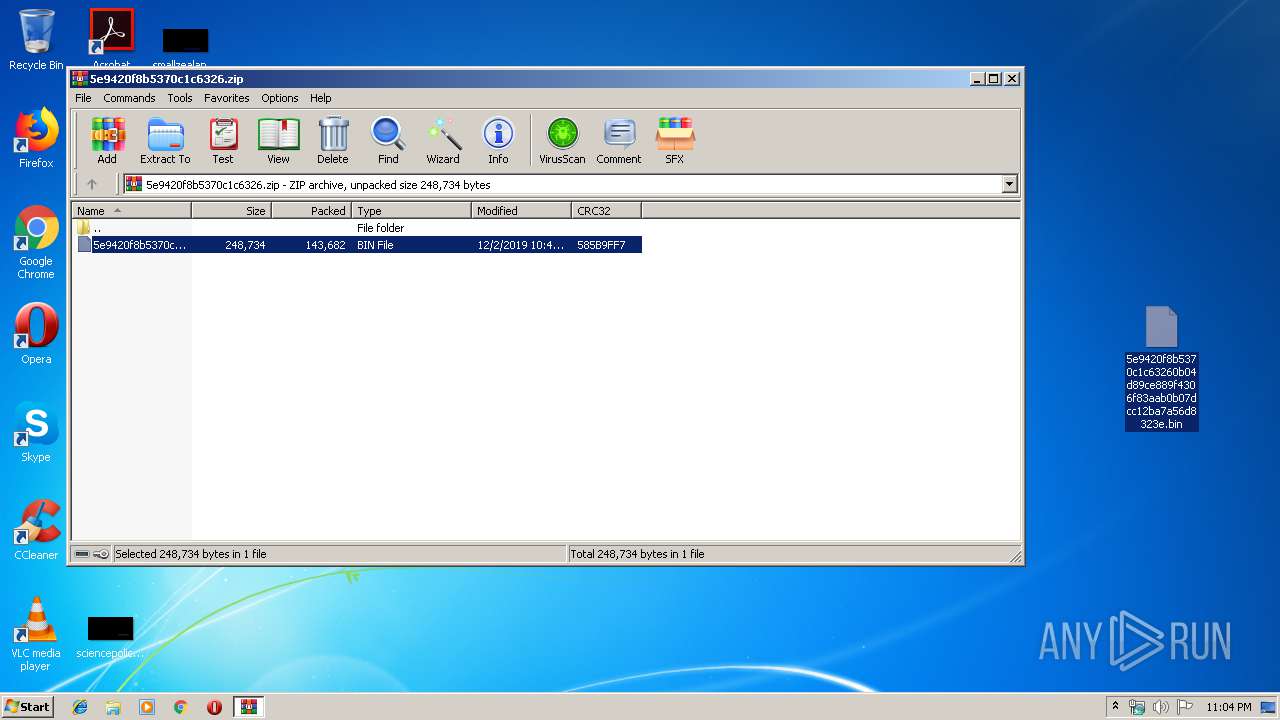
| ZipFileName: | 5e9420f8b5370c1c63260b04d89ce889f4306f83aab0b07dcc12ba7a56d8323e.bin |
|---|---|
| ZipUncompressedSize: | 248734 |
| ZipCompressedSize: | 143682 |
| ZipCRC: | 0x585b9ff7 |
| ZipModifyDate: | 2019:12:02 22:47:13 |
| ZipCompression: | Deflated |
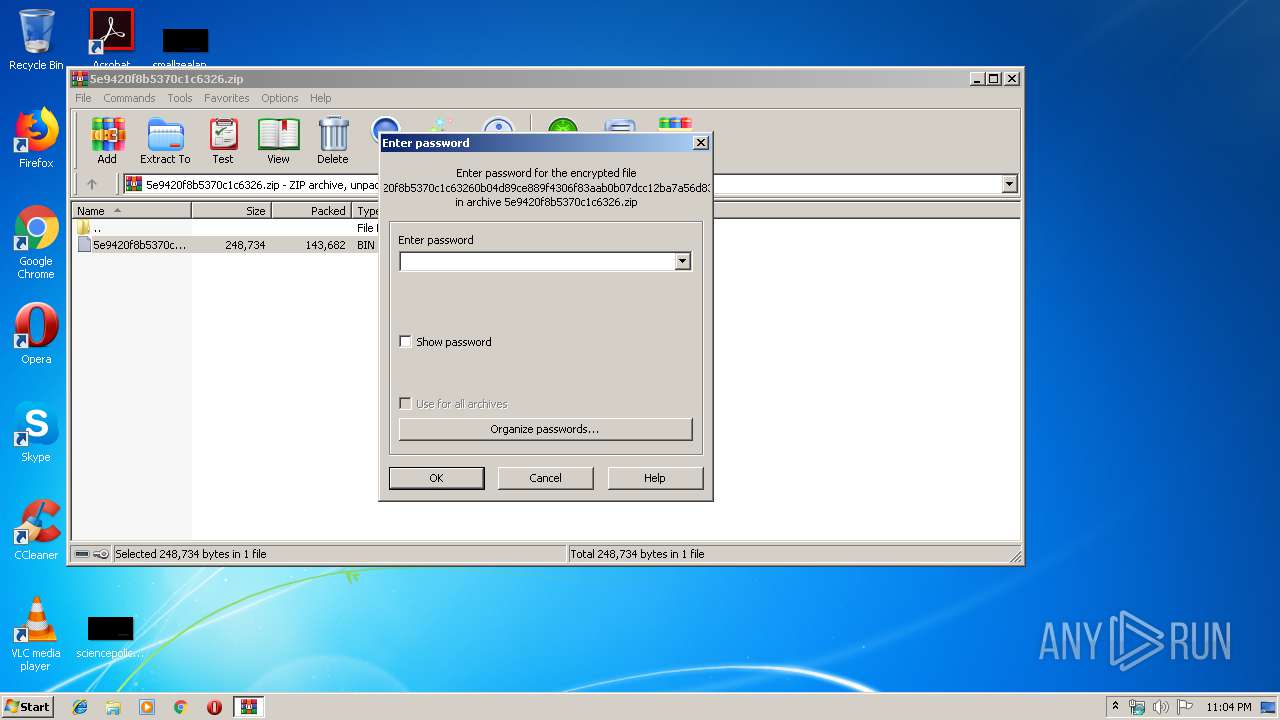
| ZipBitFlag: | 0x0001 |
| ZipRequiredVersion: | 788 |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2200 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\5e9420f8b5370c1c6326.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.60.0 | ||||
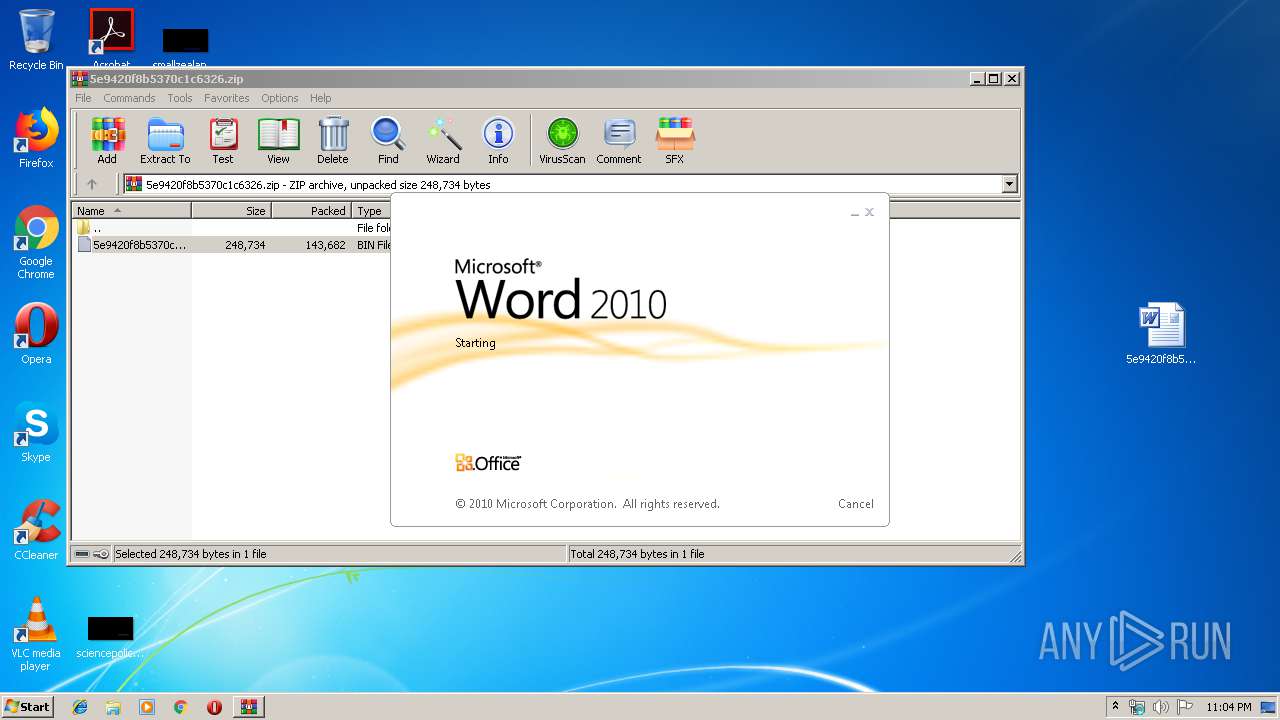
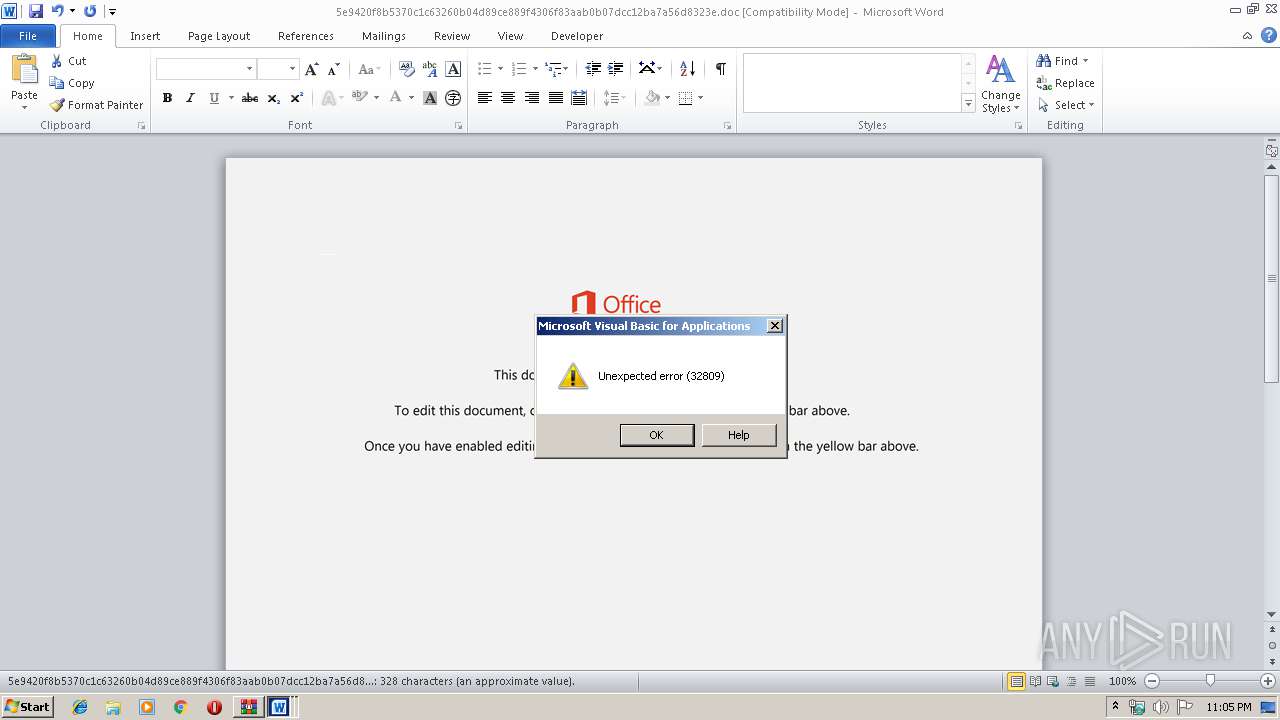
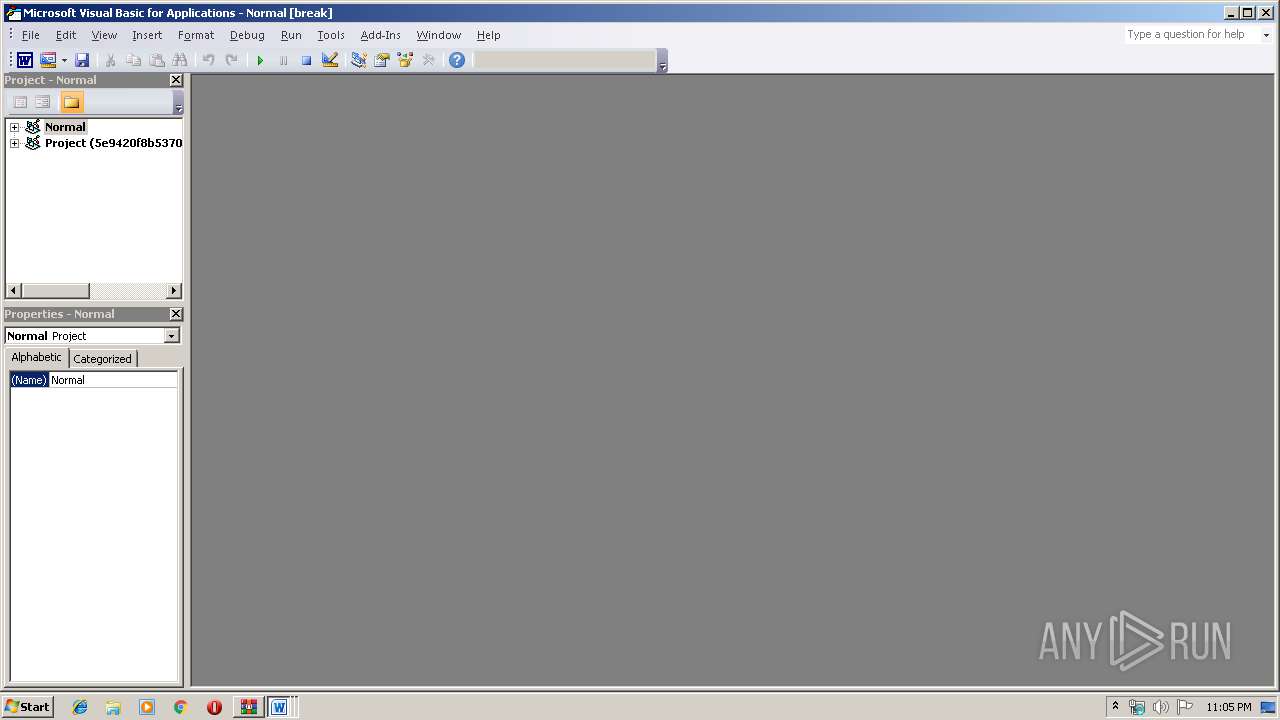
| 2888 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\5e9420f8b5370c1c63260b04d89ce889f4306f83aab0b07dcc12ba7a56d8323e.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 | ||||
| 2092 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\5e9420f8b5370c1c63260b04d89ce889f4306f83aab0b07dcc12ba7a56d8323e.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 | ||||
Total events
3 901
Read events
3 230
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
6
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
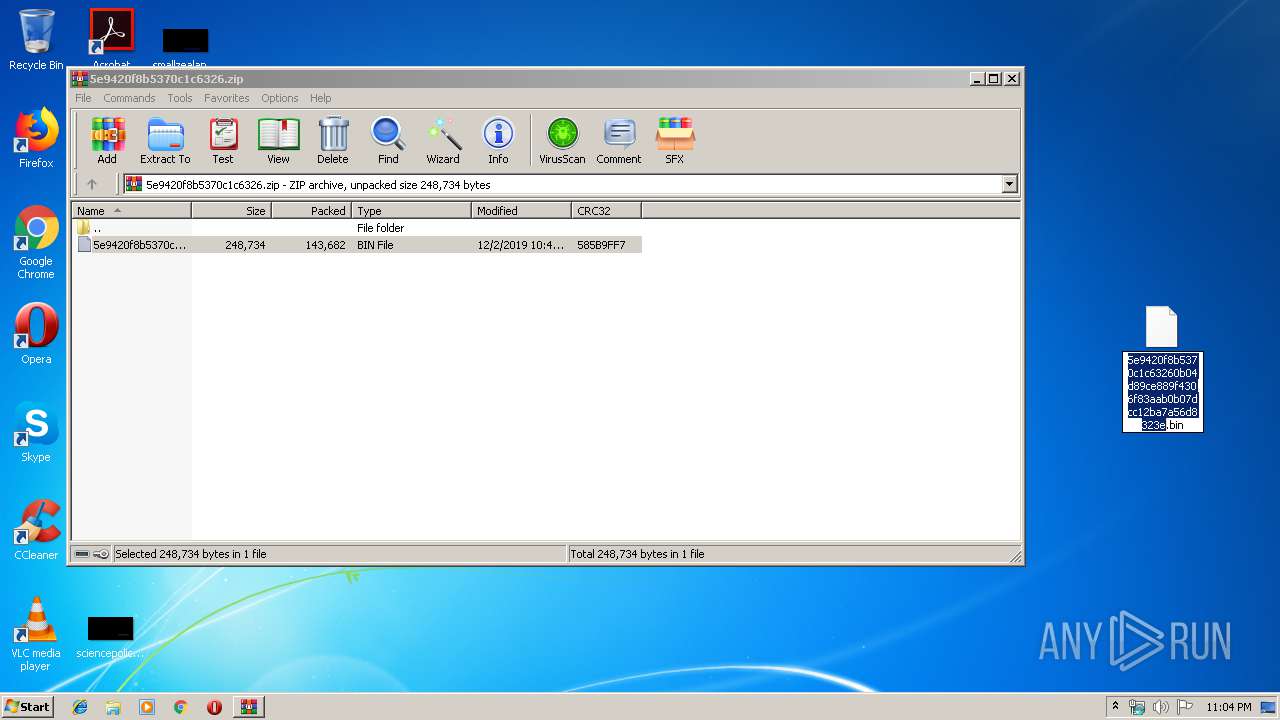
| 2200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2200.38287\5e9420f8b5370c1c63260b04d89ce889f4306f83aab0b07dcc12ba7a56d8323e.bin | — | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR25FC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR25FD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C62558BE.wmf | — | |
MD5:— | SHA256:— | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9BCF35A7.wmf | — | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FA4316B2.wmf | — | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A7D5130B.wmf | — | |
MD5:— | SHA256:— | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B635437C.wmf | — | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\477B5990.wmf | — | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8602EC51.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report