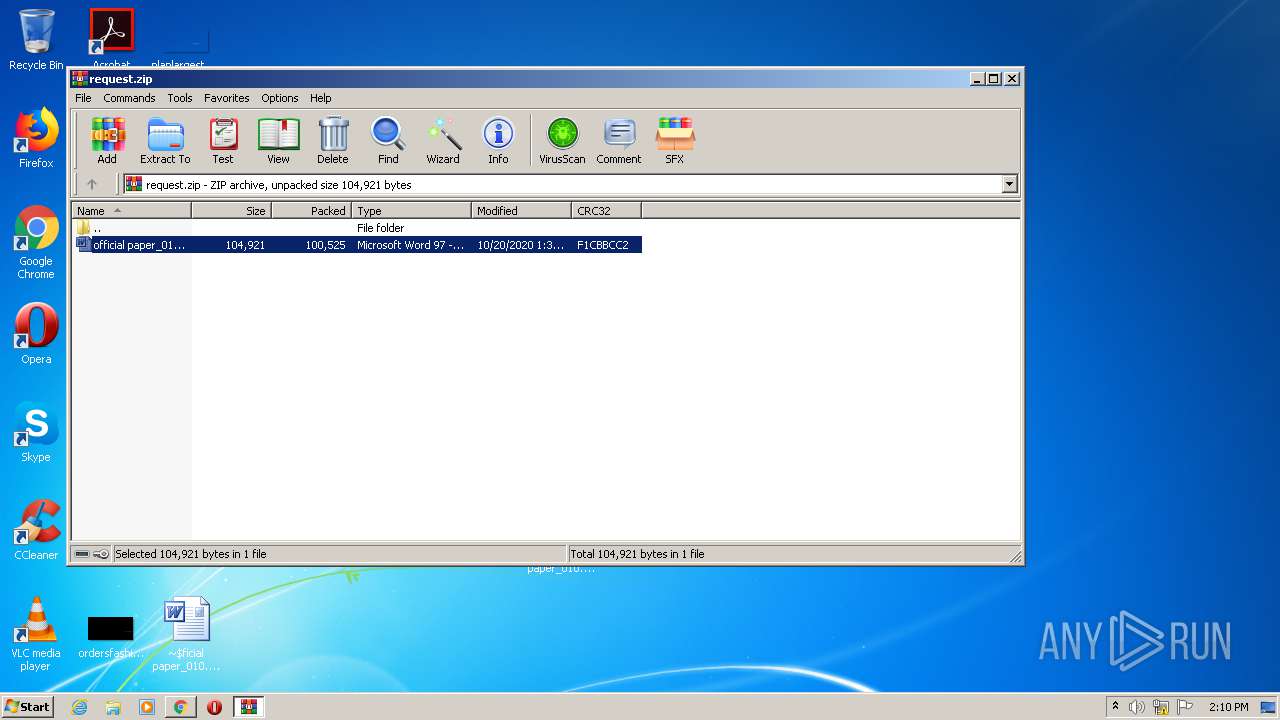
| File name: | request.zip |
| Full analysis: | https://app.any.run/tasks/2842c2ee-a7dc-474b-a825-a9cb169e56b6 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 13:05:44 |
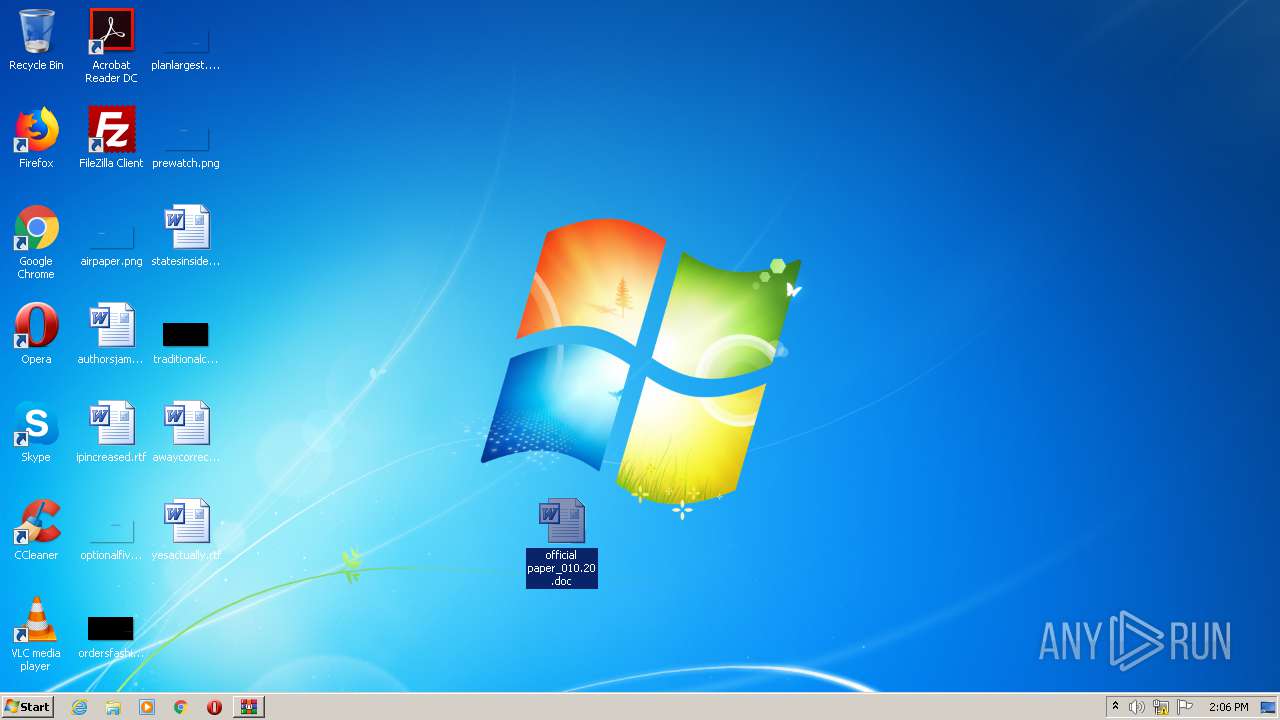
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 6EC8F45A23D94DF9B50033796D315805 |
| SHA1: | 27889CA5114A57AEA24EAEB7050F1DDFB368ED46 |
| SHA256: | 0CDD85E468616C38C04872CF0CD0532ACAA1C3748D16E65F0459DF301273A048 |
| SSDEEP: | 3072:aYQkXvITN8Xad2gKzERBo8/xdpAr25+oWPTBSbufq4+:apUgYadOC68/pAr25jMTsaV+ |
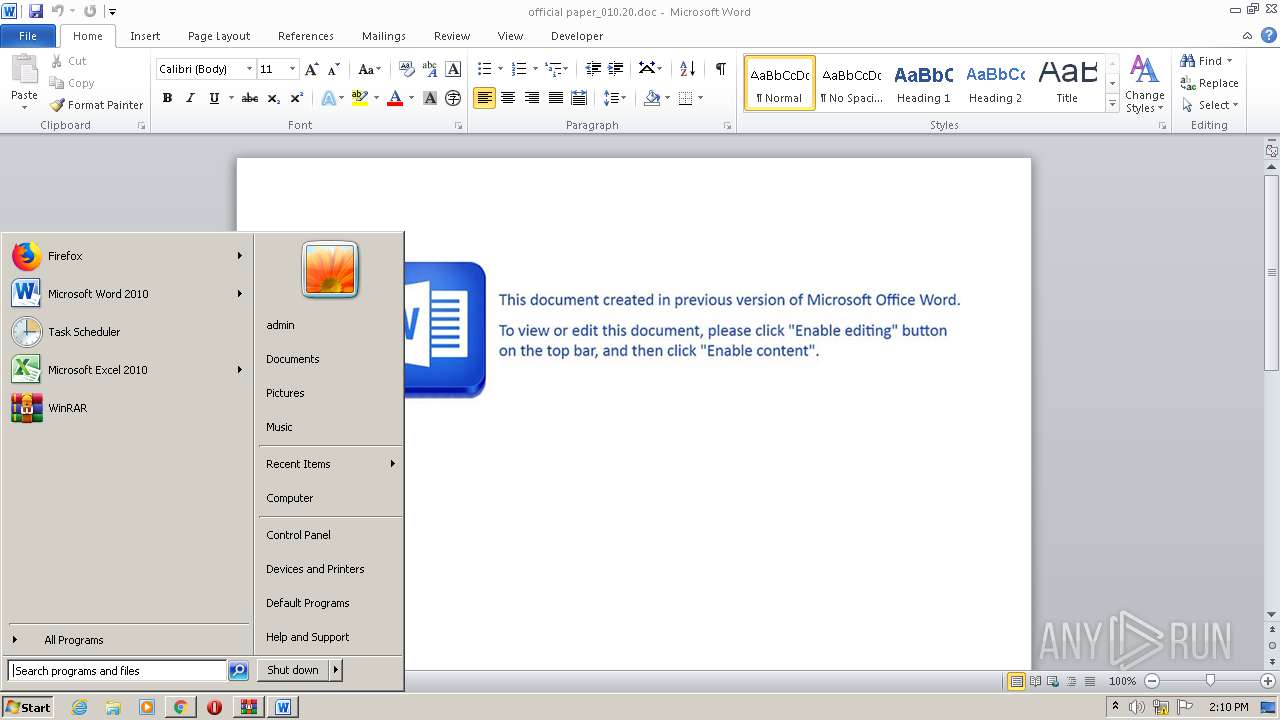
MALICIOUS
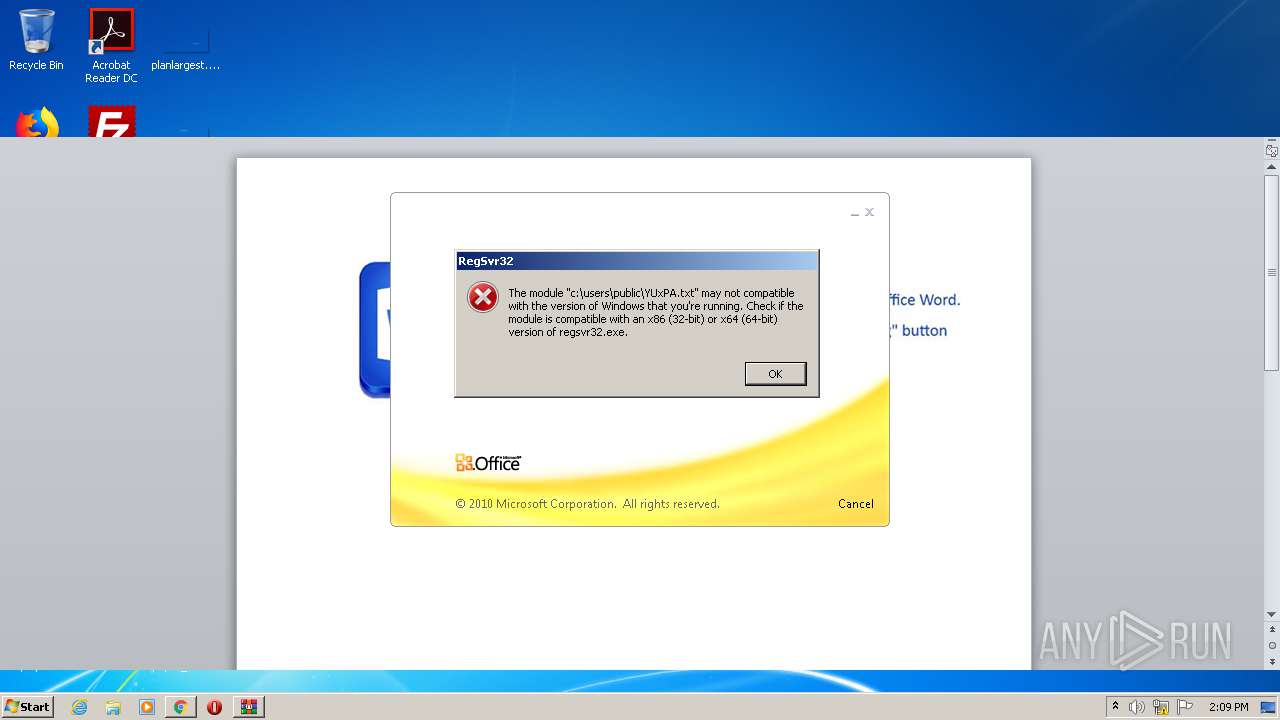
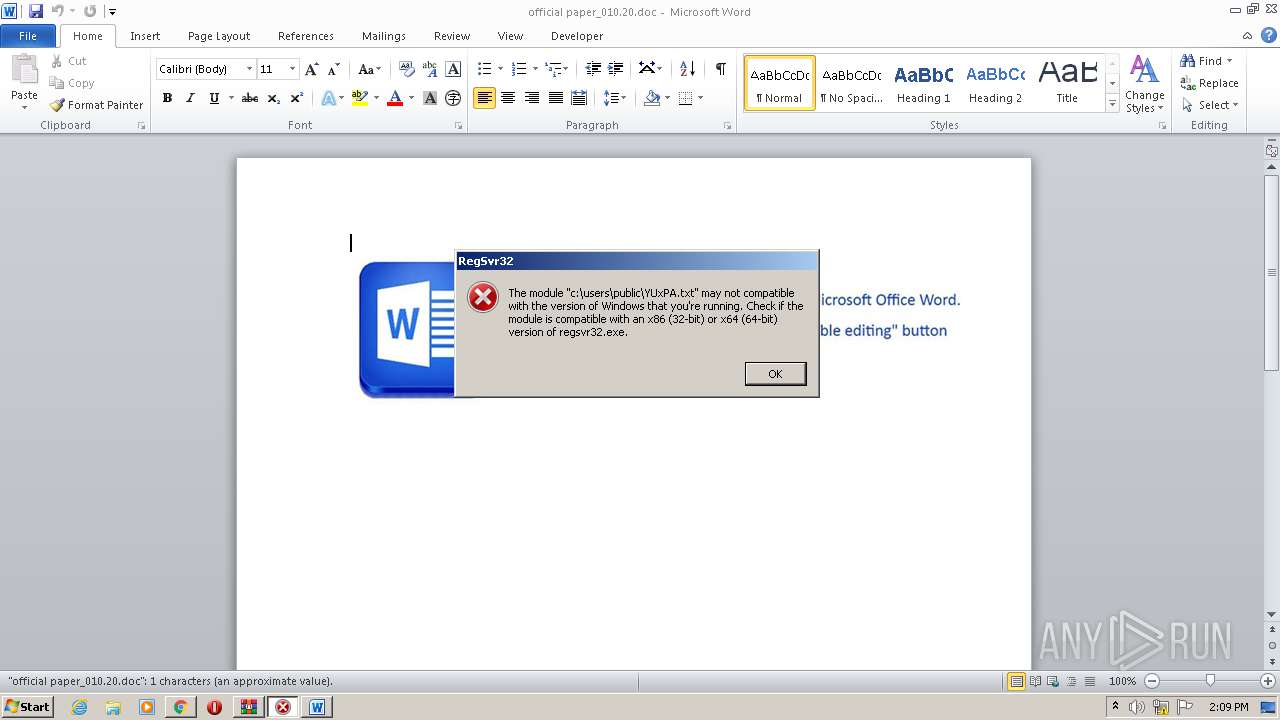
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2960)
Registers / Runs the DLL via REGSVR32.EXE
- WINWORD.EXE (PID: 2960)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3076)
Reads the hosts file
- chrome.exe (PID: 2228)
- chrome.exe (PID: 3076)
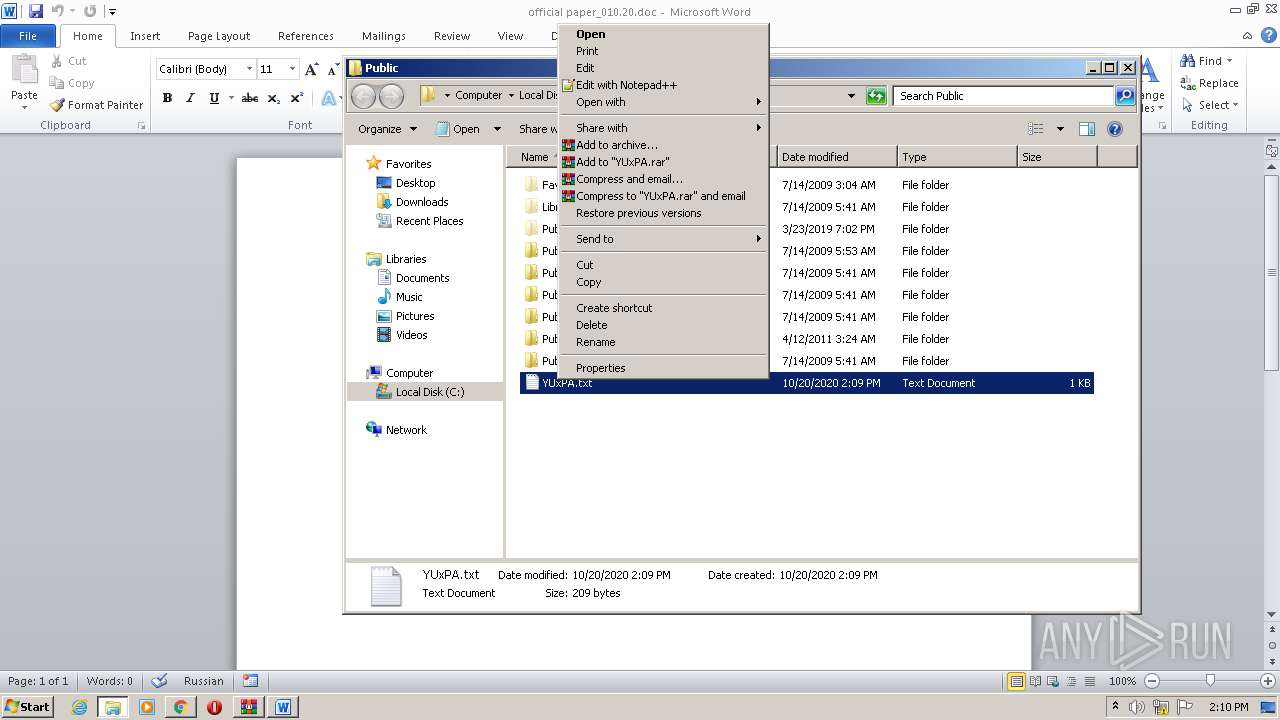
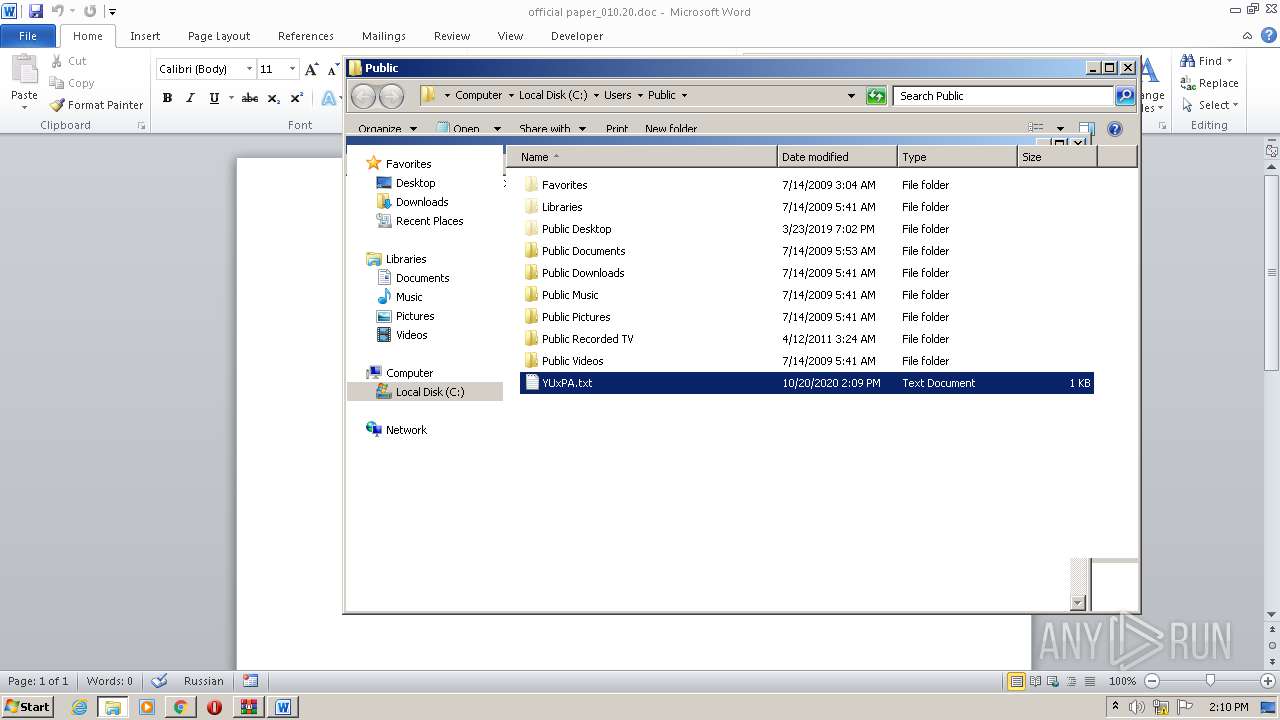
Manual execution by user
- verclsid.exe (PID: 3096)
- NOTEPAD.EXE (PID: 3860)
- chrome.exe (PID: 3076)
- WINWORD.EXE (PID: 2960)
Reads settings of System Certificates
- chrome.exe (PID: 2228)
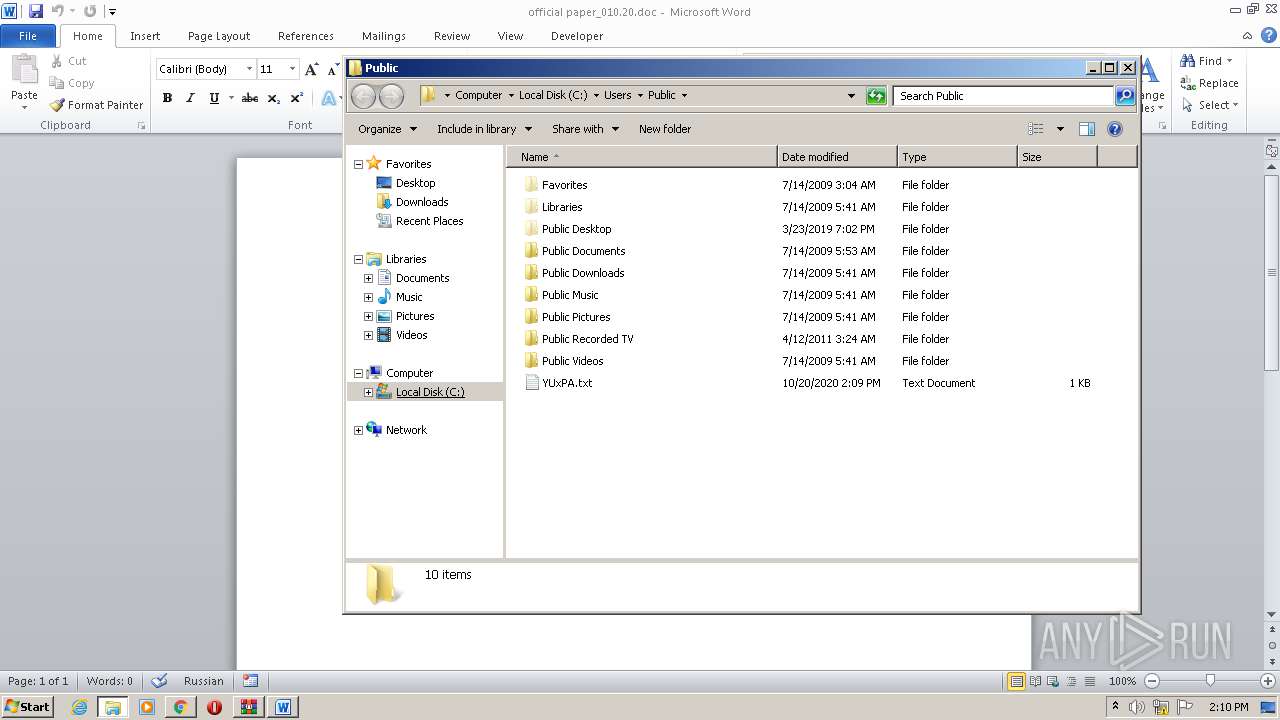
Creates files in the user directory
- WINWORD.EXE (PID: 2960)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
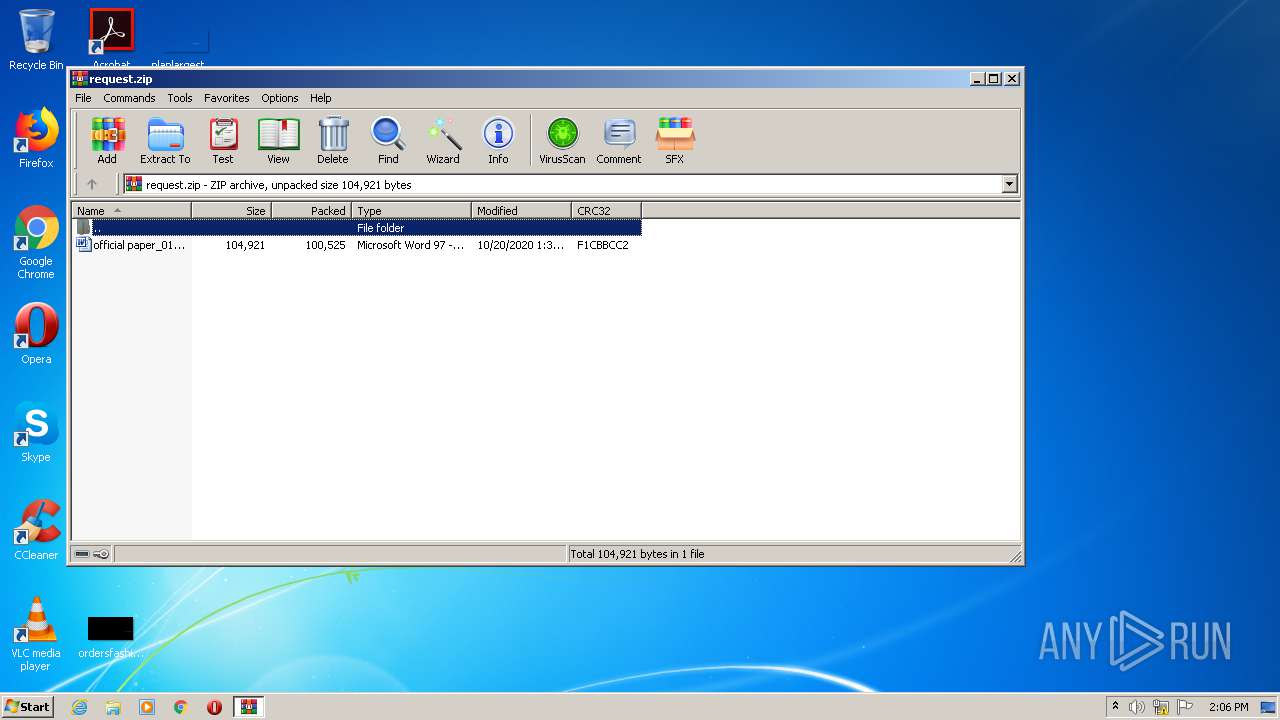
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:10:20 01:34:26 |
| ZipCRC: | 0xf1cbbcc2 |
| ZipCompressedSize: | 100525 |
| ZipUncompressedSize: | 104921 |
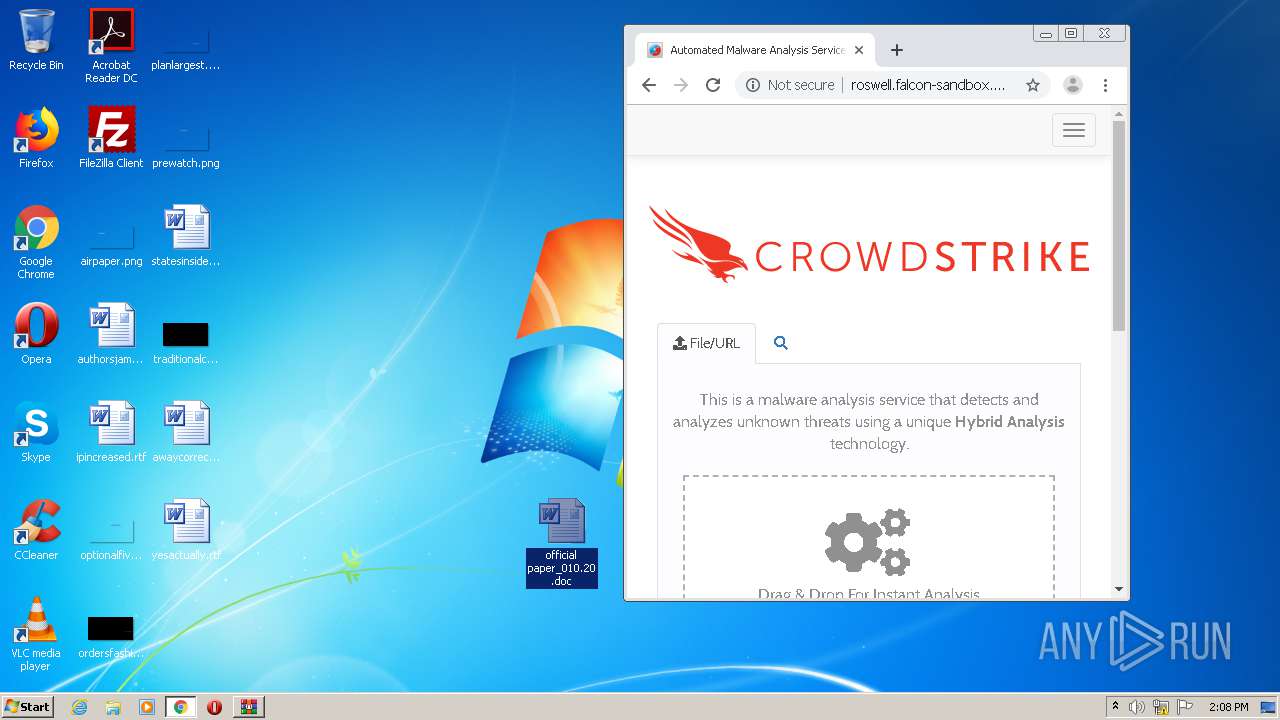
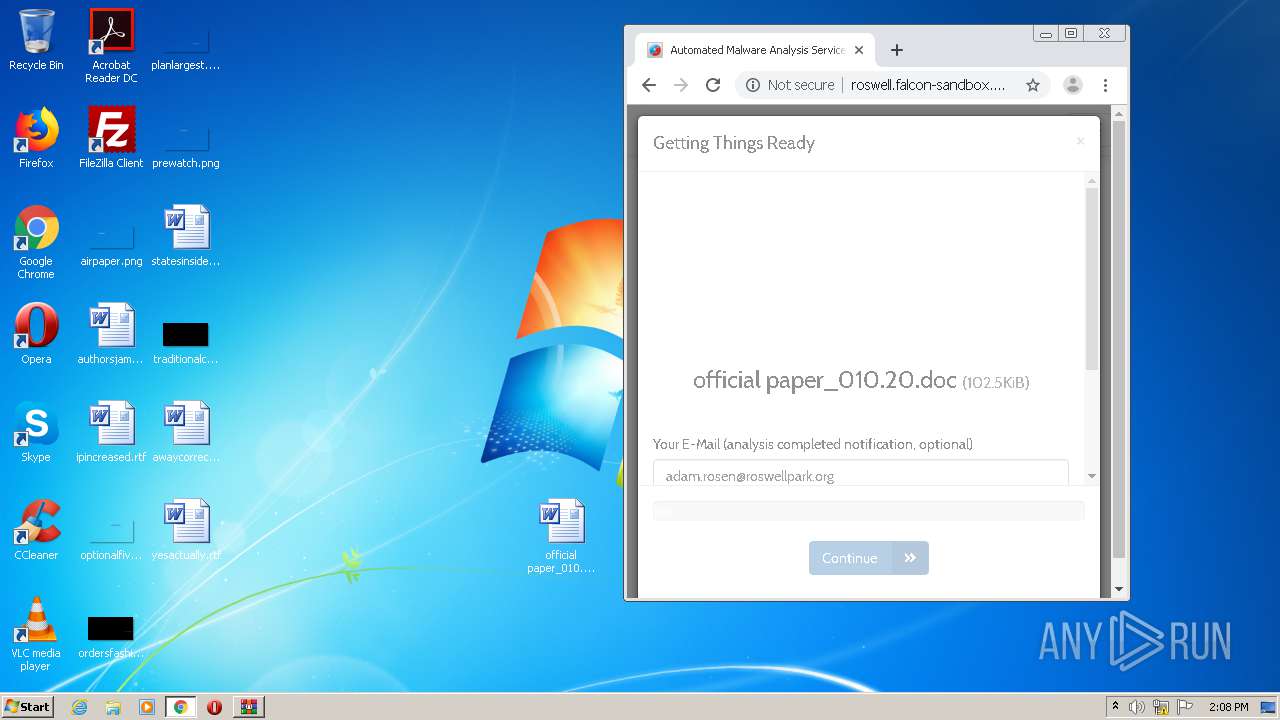
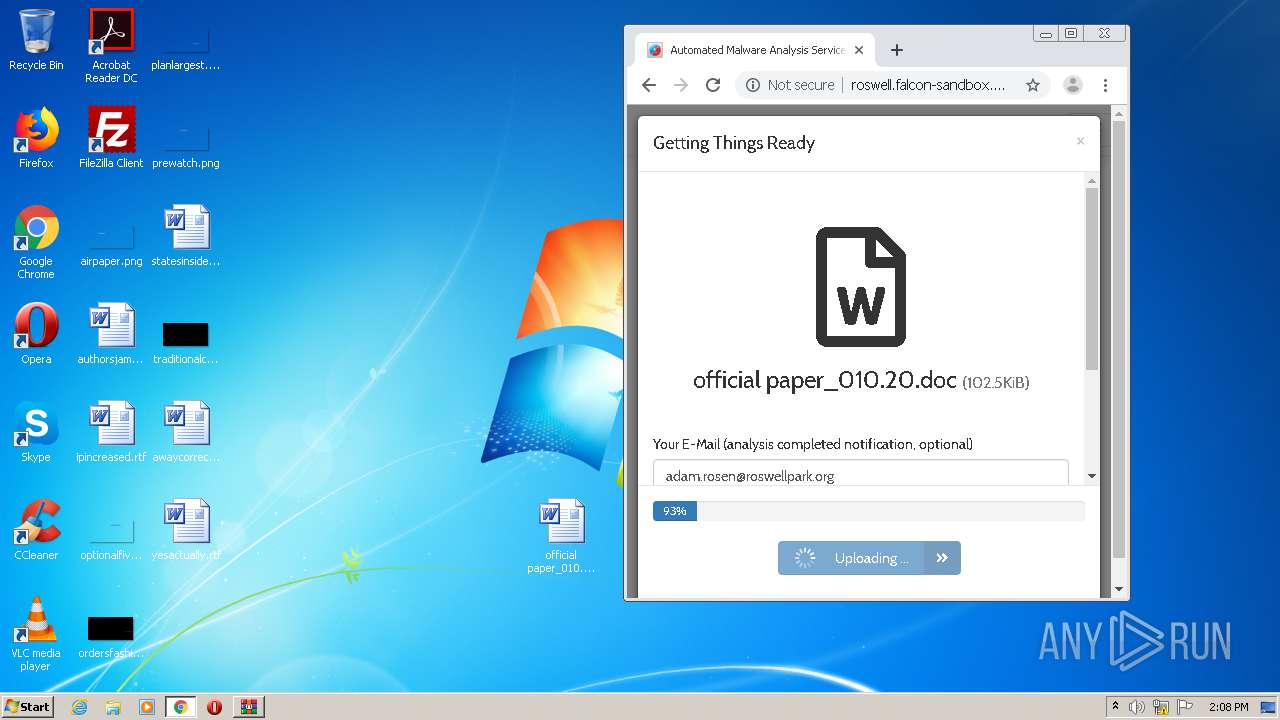
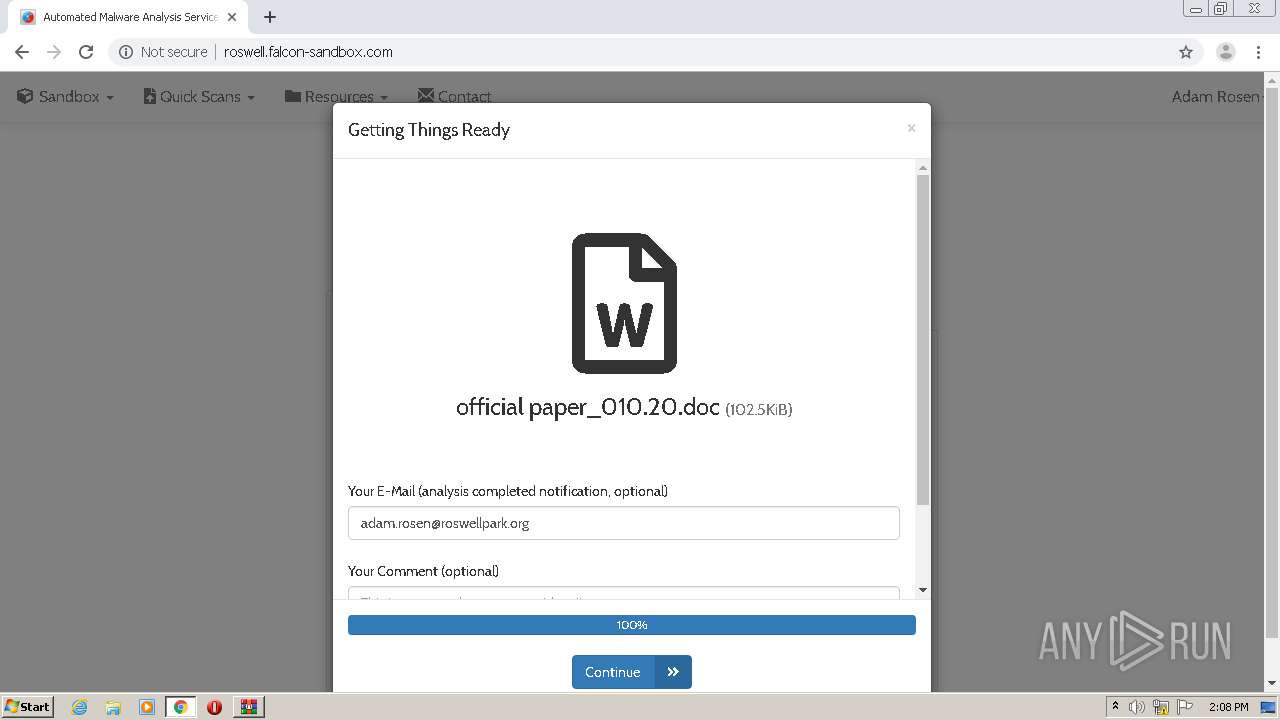
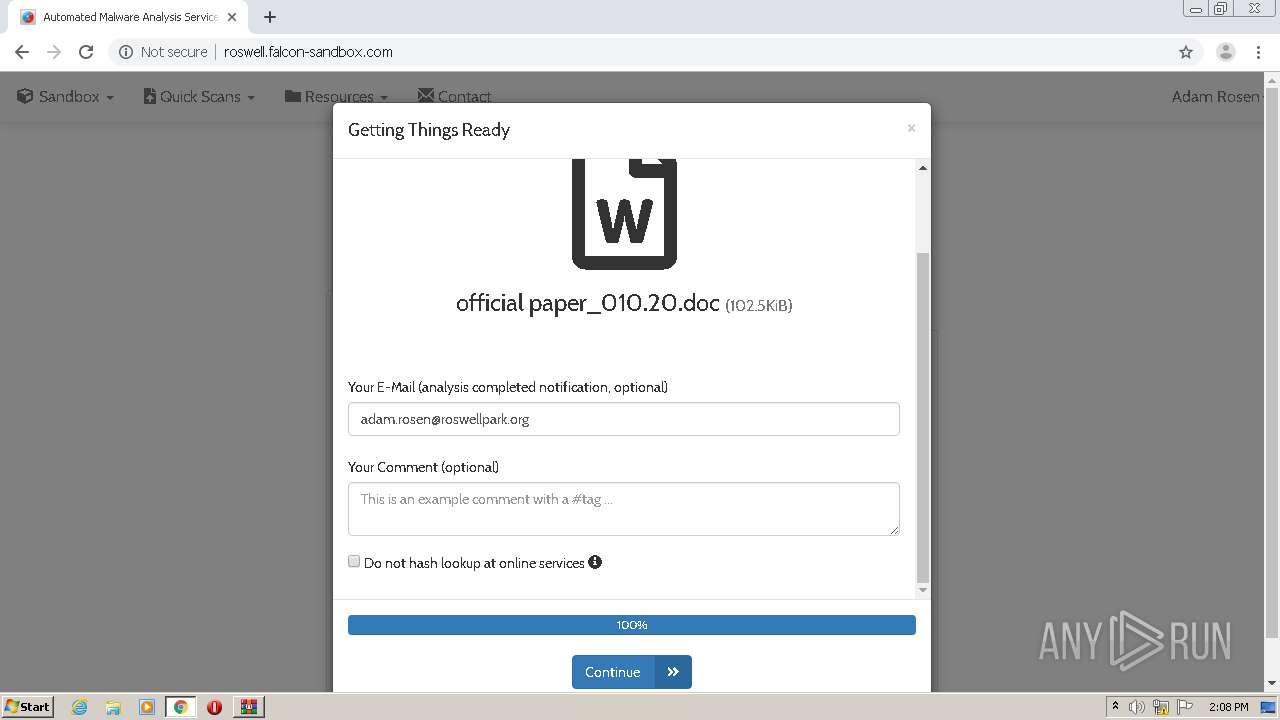
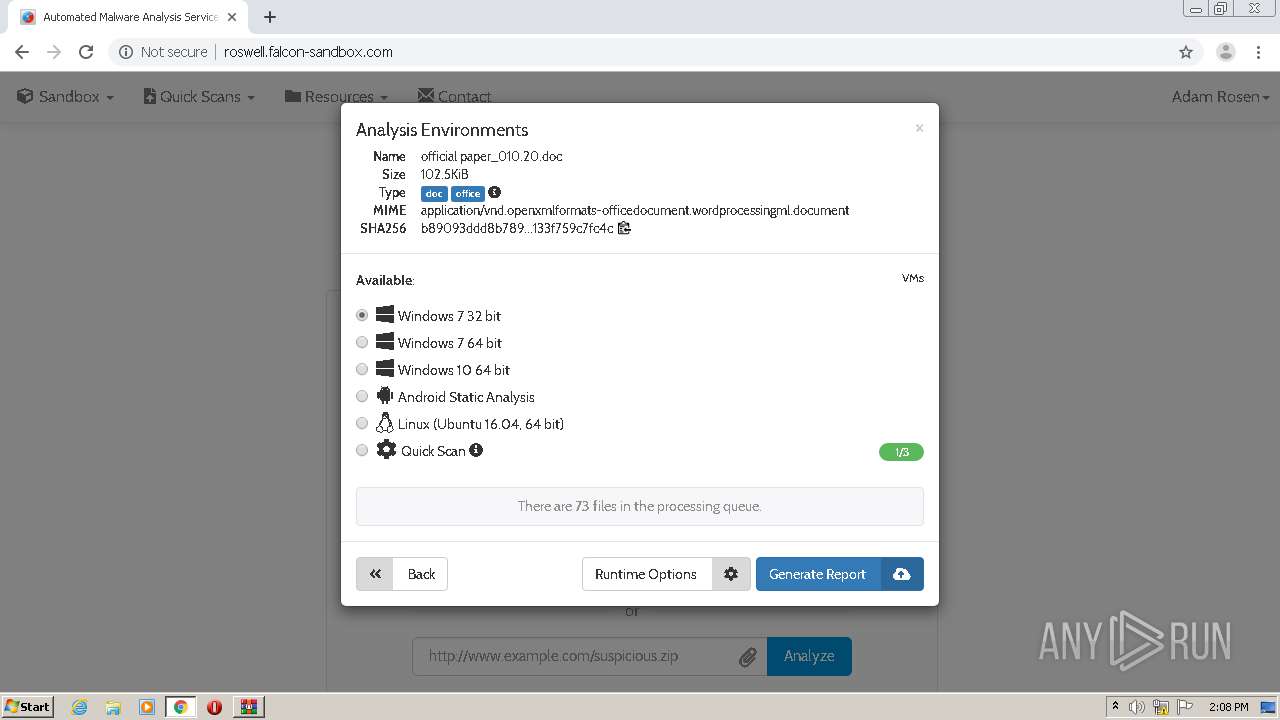
| ZipFileName: | official paper_010.20.doc |
Total processes
69
Monitored processes
25
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,639739047992616890,17896949895693129942,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12449537295807273976 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,639739047992616890,17896949895693129942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=101636672030439275 --mojo-platform-channel-handle=2496 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,639739047992616890,17896949895693129942,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8024927668191978239 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6bc7a9d0,0x6bc7a9e0,0x6bc7a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,639739047992616890,17896949895693129942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5008314484911049634 --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2848 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,639739047992616890,17896949895693129942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1855037610689781642 --mojo-platform-channel-handle=3352 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,639739047992616890,17896949895693129942,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3697831840999226006 --mojo-platform-channel-handle=3456 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,639739047992616890,17896949895693129942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5762744219970680244 --mojo-platform-channel-handle=3460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
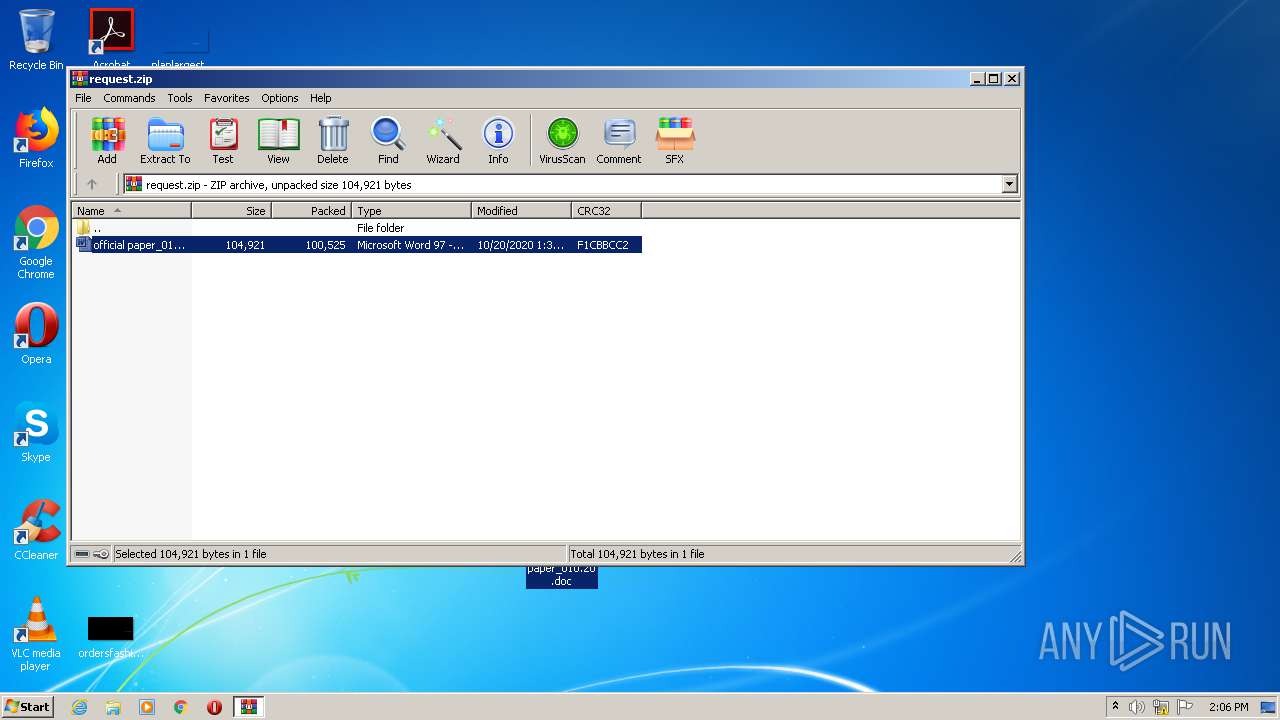
| 2496 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\request.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
3 343
Read events
2 157
Write events
1 035
Delete events
151
Modification events
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\request.zip | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
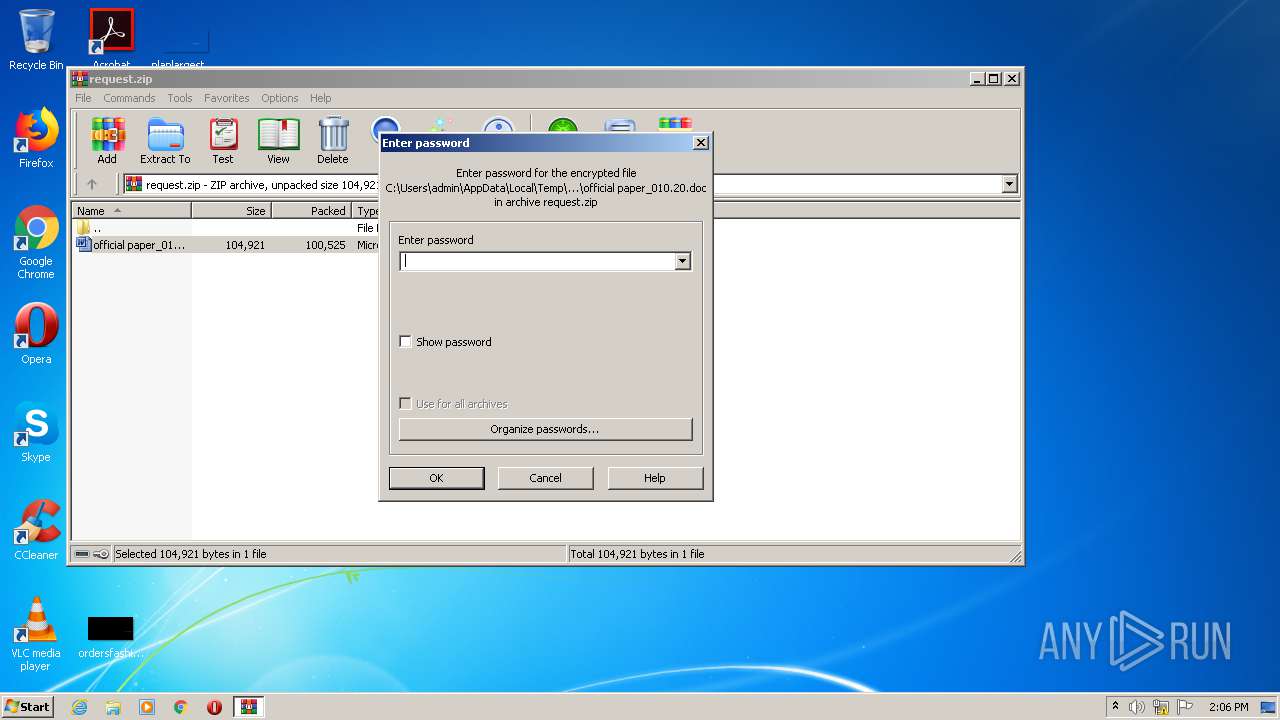
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
0
Suspicious files
40
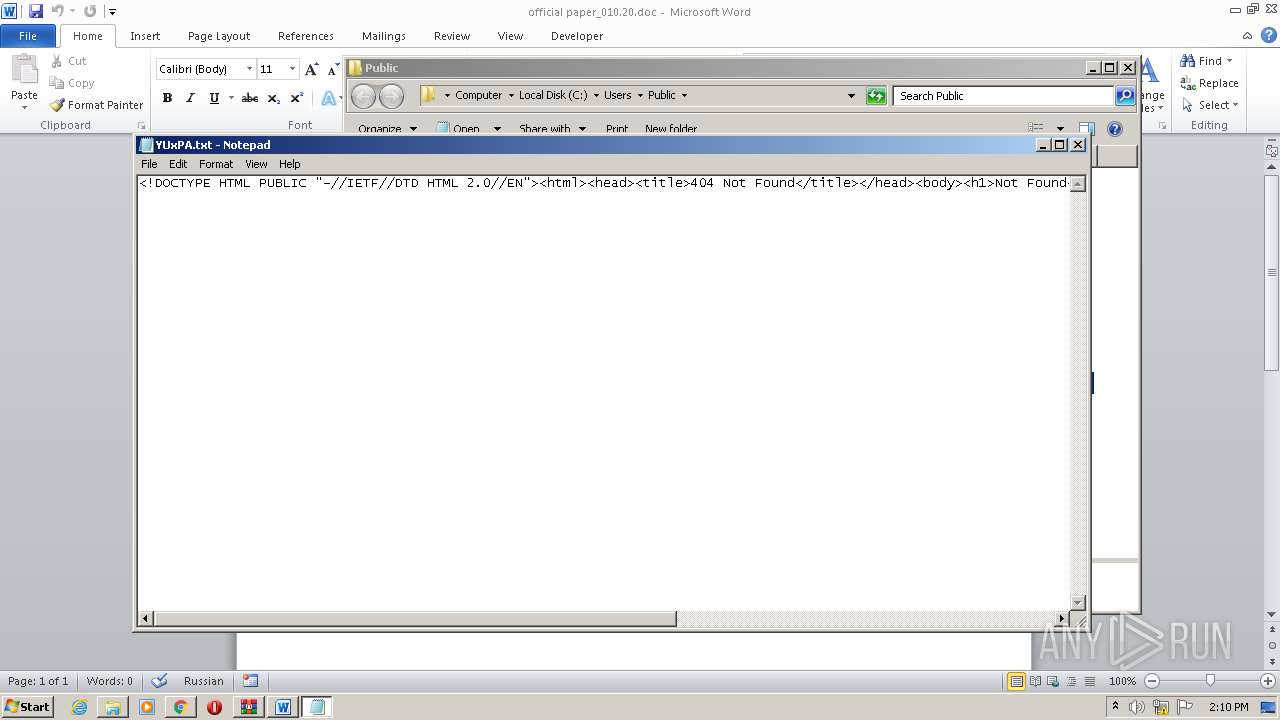
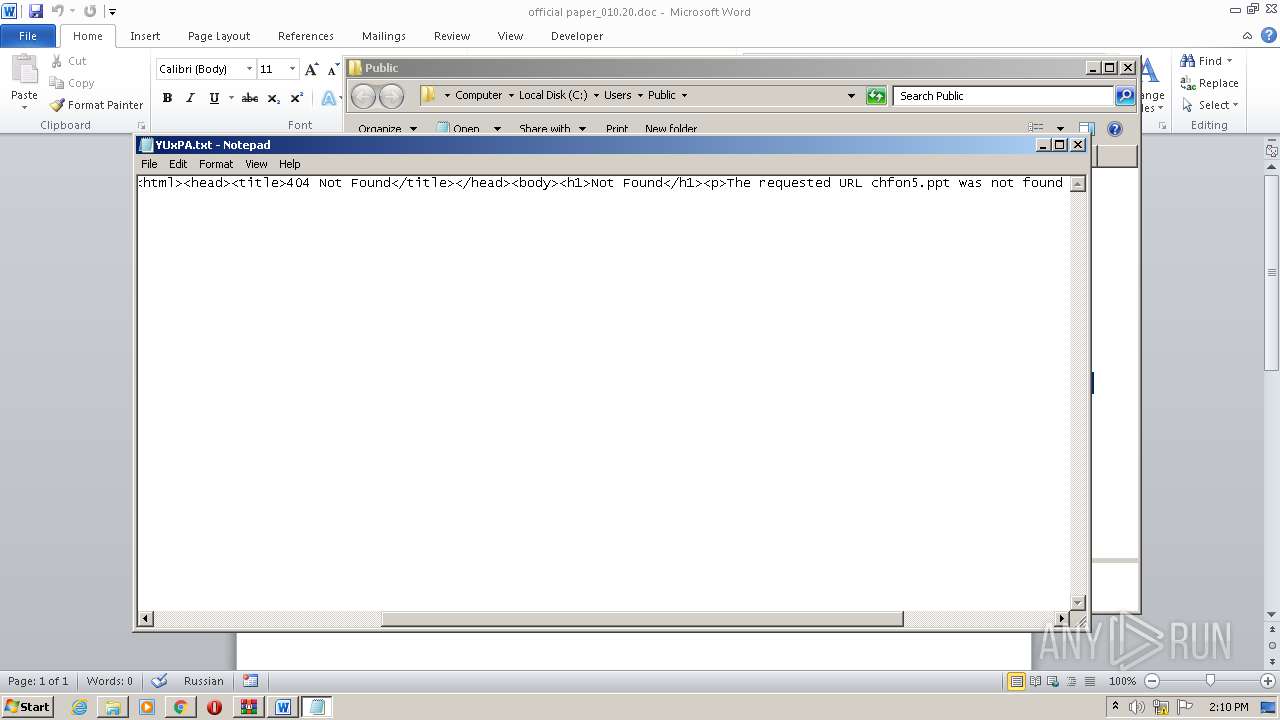
Text files
100
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8EE0DC-C04.pma | — | |
MD5:— | SHA256:— | |||
| 3076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a3e43591-e010-4090-b56c-00d0f5c0ea22.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
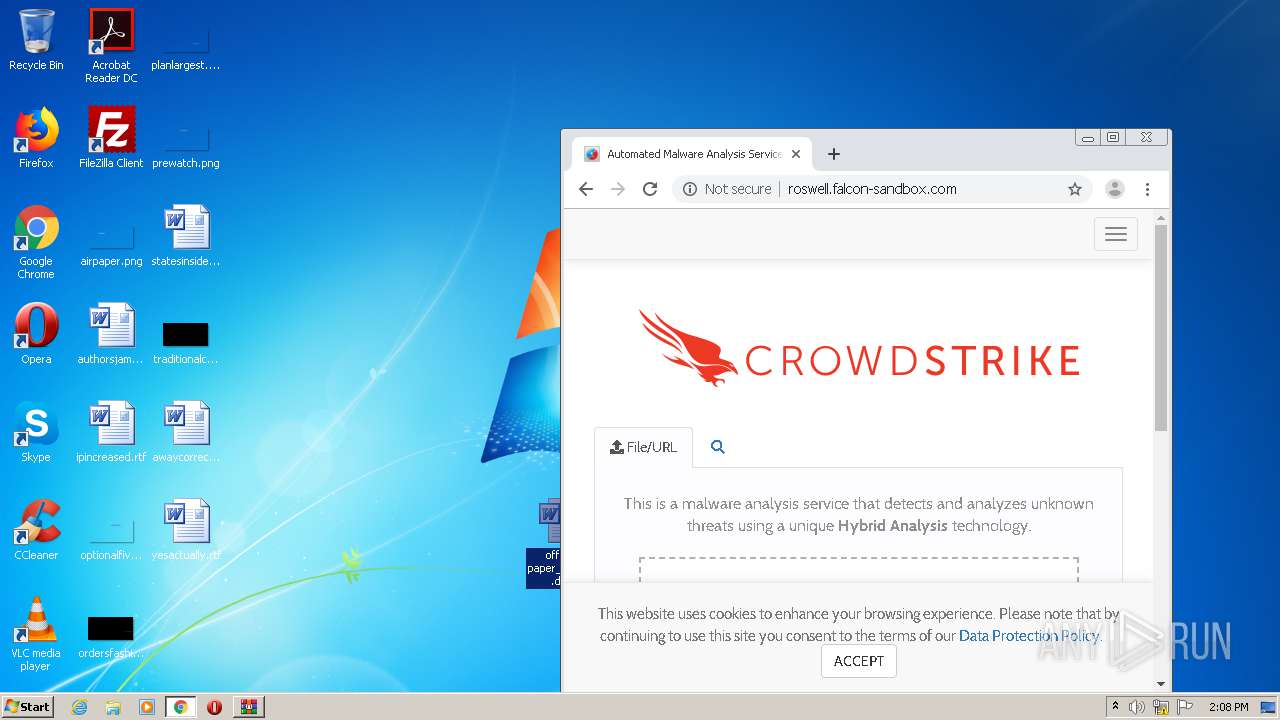
| 2496 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2496.1075\official paper_010.20.doc | document | |
MD5:— | SHA256:— | |||
| 3076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2dc856.TMP | text | |
MD5:— | SHA256:— | |||
| 3076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF2dc8f2.TMP | text | |
MD5:— | SHA256:— | |||
| 3076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
25
DNS requests
20
Threats
1
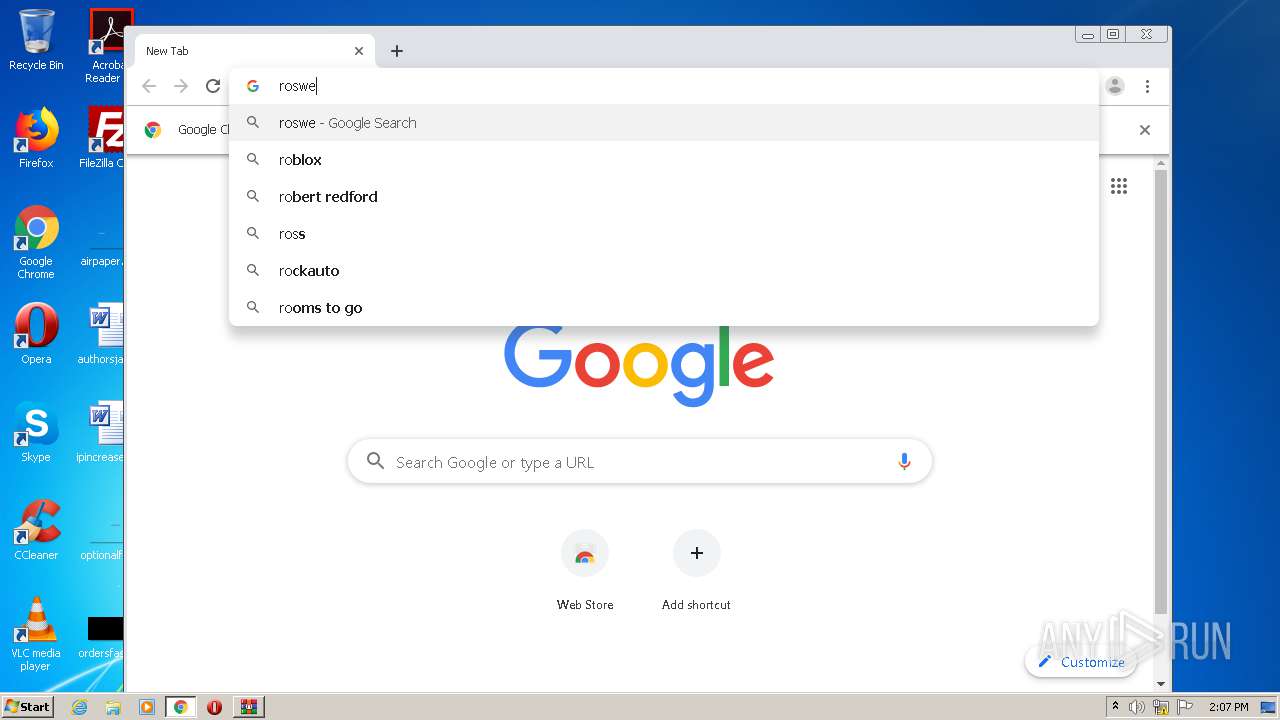
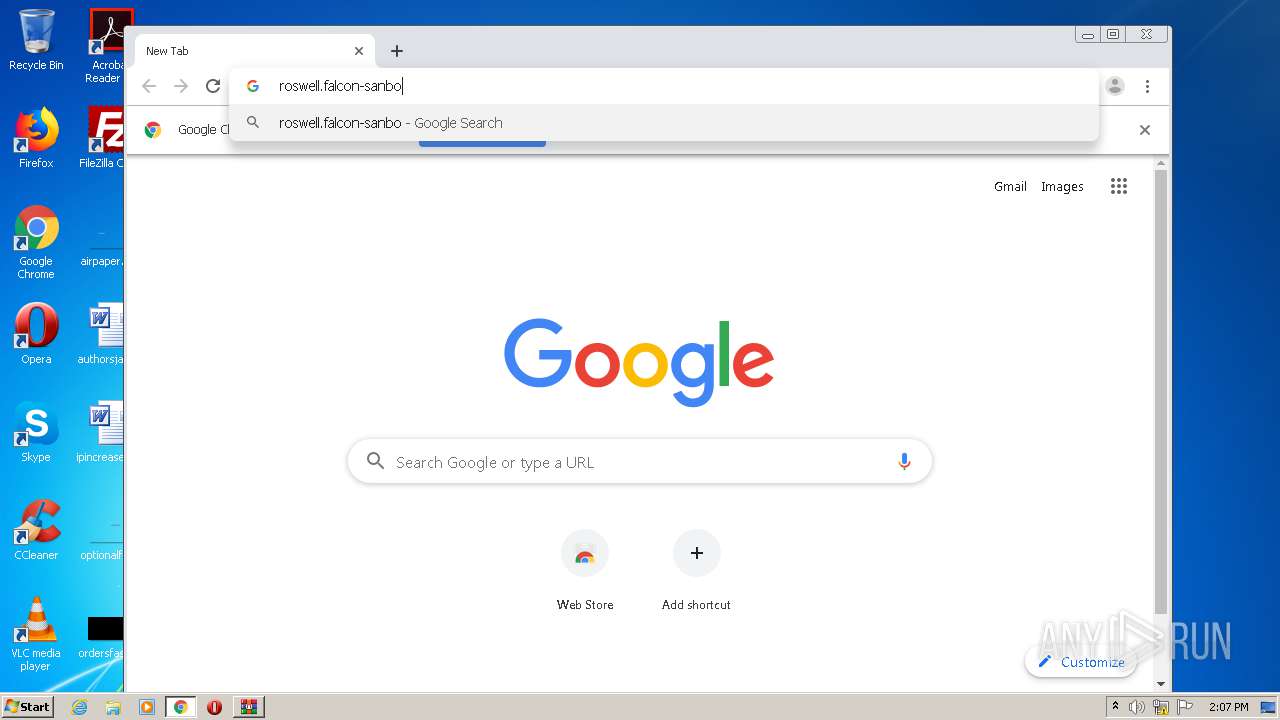
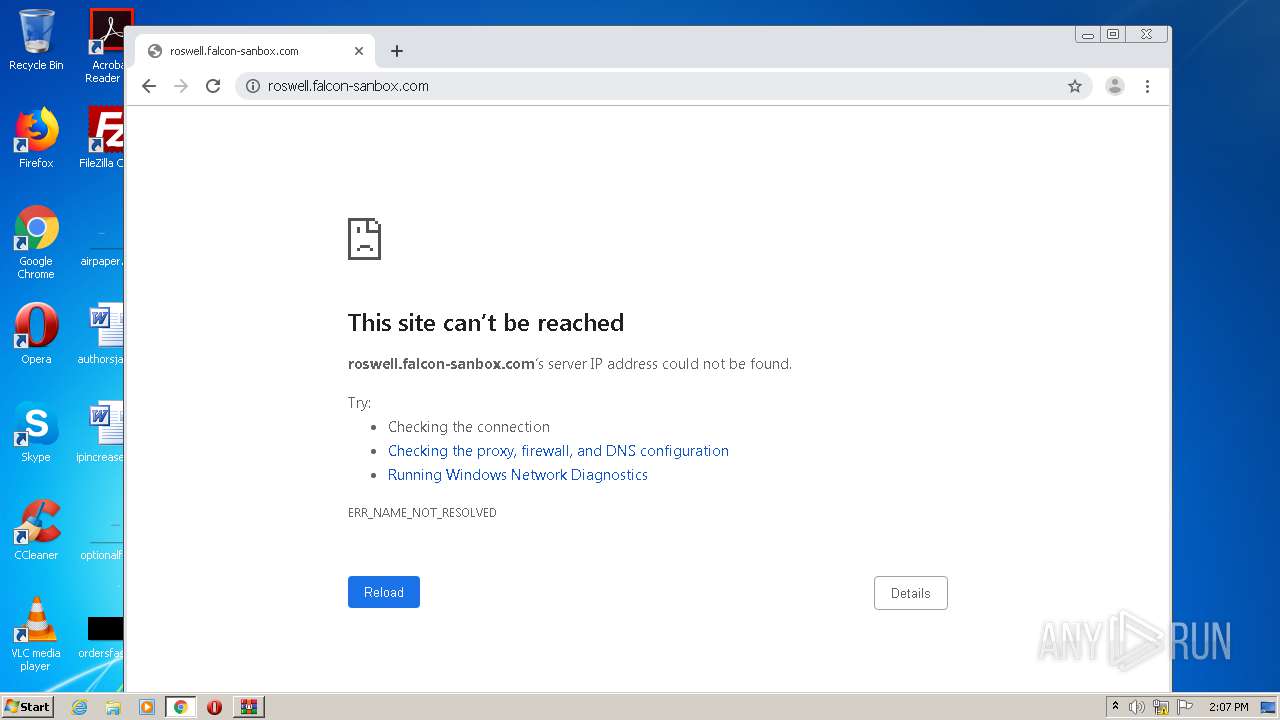
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
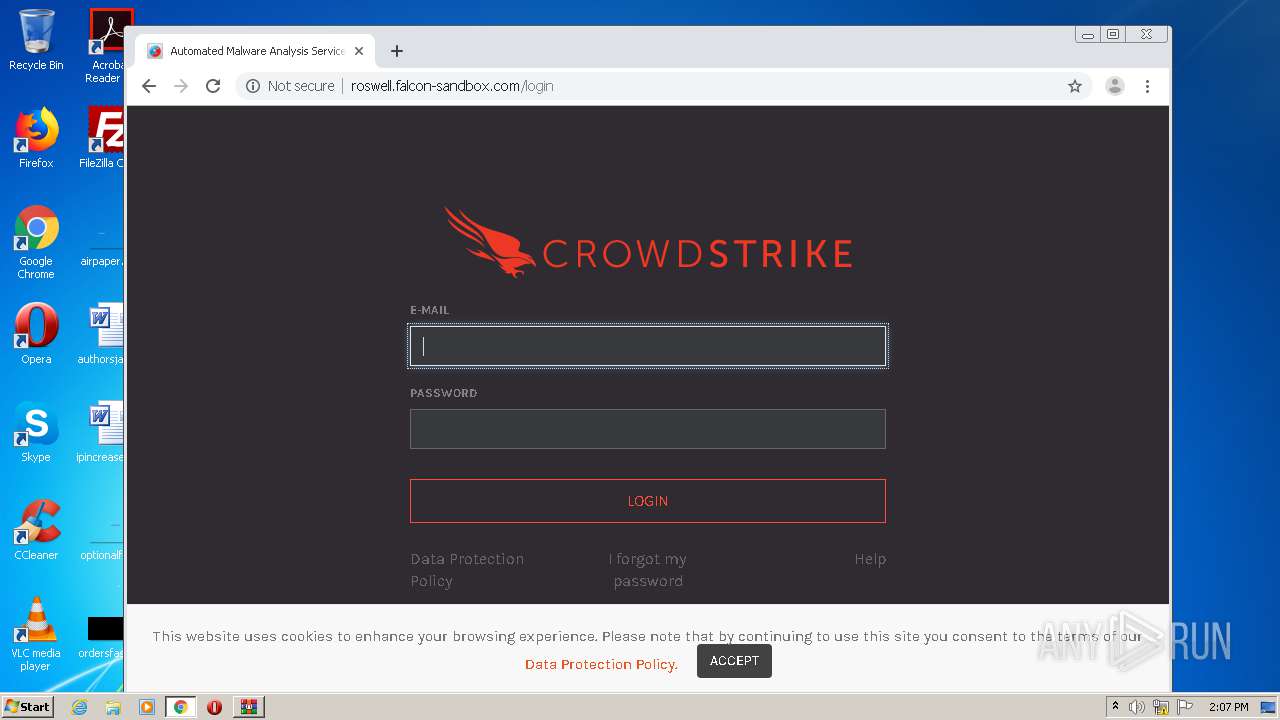
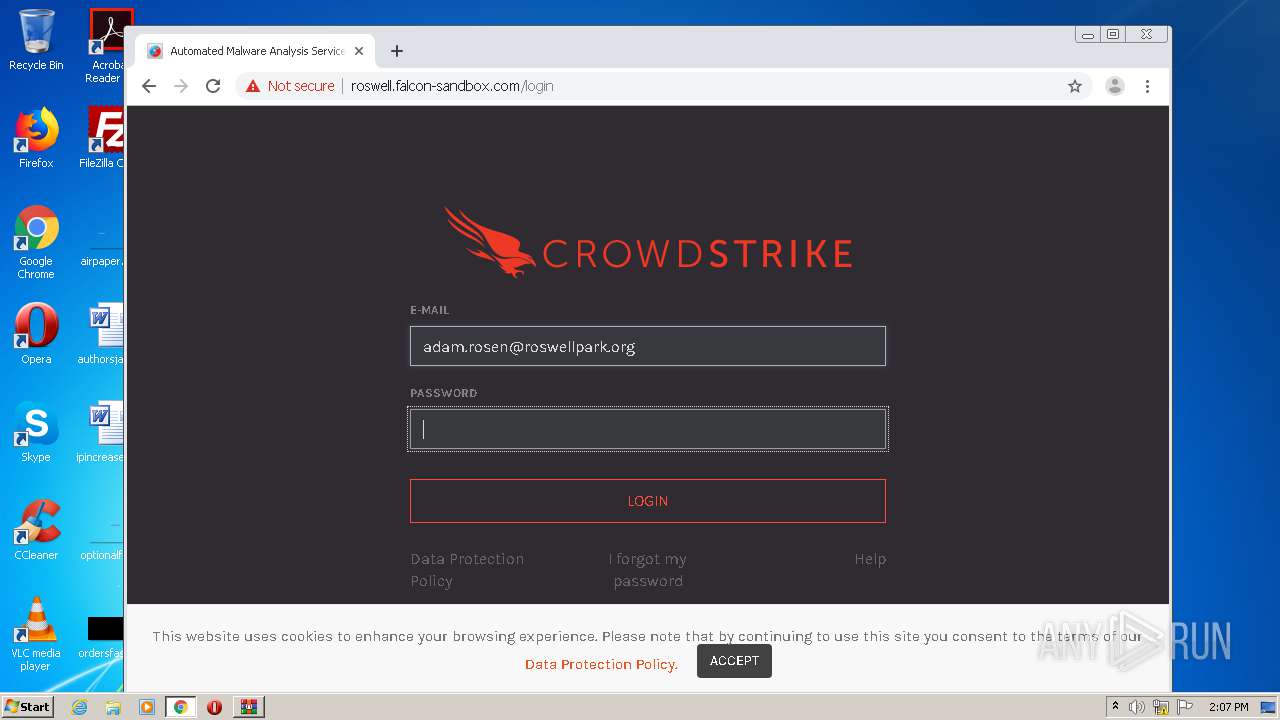
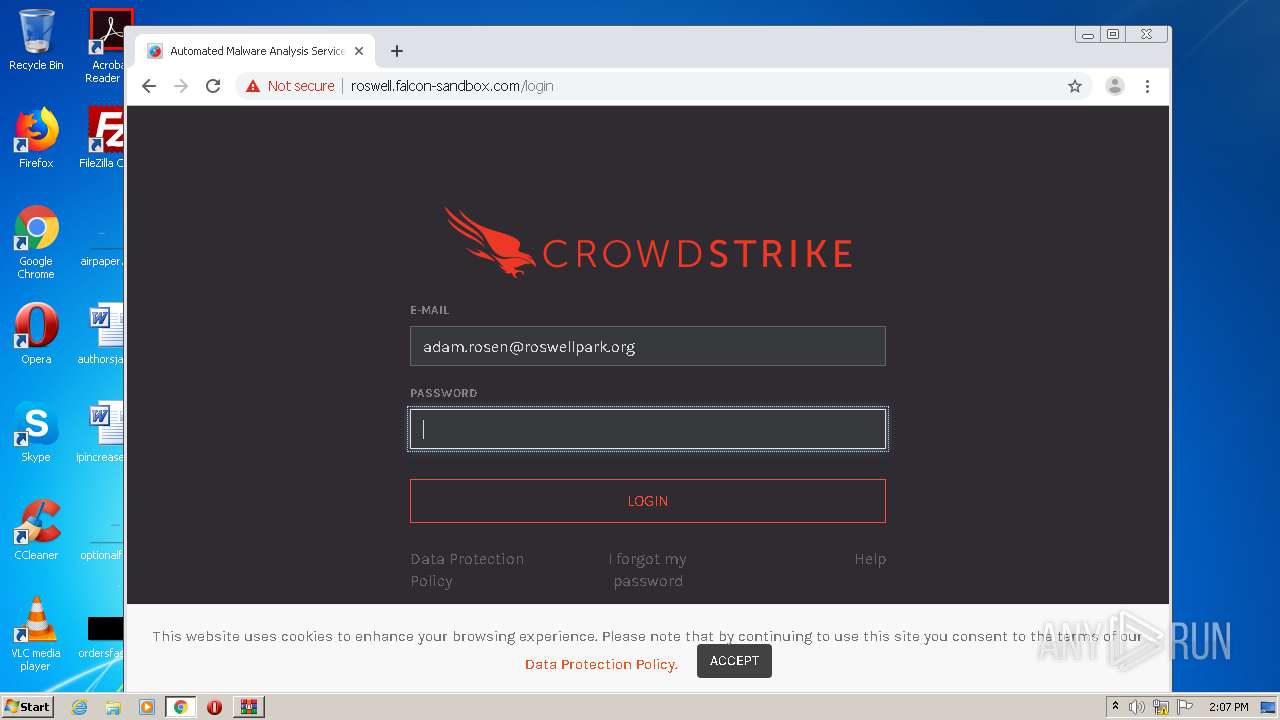
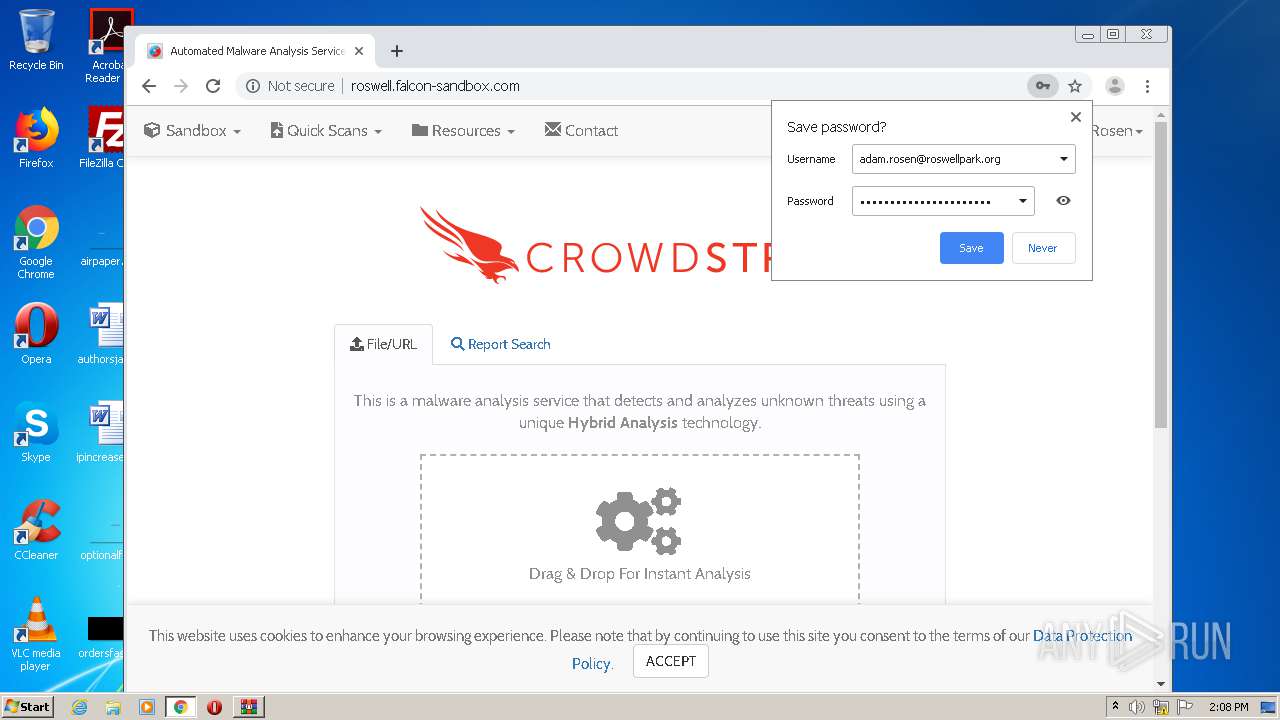
2228 | chrome.exe | GET | 302 | 52.8.248.79:80 | http://roswell.falcon-sandbox.com/ | US | — | — | unknown |
2228 | chrome.exe | GET | 200 | 52.8.248.79:80 | http://roswell.falcon-sandbox.com/login | US | html | 8.83 Kb | unknown |
2228 | chrome.exe | GET | 200 | 52.8.248.79:80 | http://roswell.falcon-sandbox.com/assets/7e51997b4f7837e71683eabb36c91143b3d8cd242fdc44dcb31005eb700cb112.min.css | US | text | 76.2 Kb | unknown |
2228 | chrome.exe | GET | 200 | 52.8.248.79:80 | http://roswell.falcon-sandbox.com/lib/google-fonts/fonts/karla-400-normal.woff | US | woff | 8.55 Kb | unknown |
2228 | chrome.exe | GET | 200 | 52.8.248.79:80 | http://roswell.falcon-sandbox.com/lib/google-fonts/fonts/karla-700-normal.woff | US | woff | 8.98 Kb | unknown |
2228 | chrome.exe | GET | 200 | 52.8.248.79:80 | http://roswell.falcon-sandbox.com/ | US | html | 7.36 Kb | unknown |
2228 | chrome.exe | GET | 200 | 52.8.248.79:80 | http://roswell.falcon-sandbox.com/assets/51e1d7f6ddcf7be77f8cbd9b1b6164437793750d6fc75912f55a396b179d95e4.min.css | US | text | 65.1 Kb | unknown |
2228 | chrome.exe | GET | 200 | 52.8.248.79:80 | http://roswell.falcon-sandbox.com/assets/49bb49b253b9d3e85a8c967f31bd0aea84635e899c13a605d3977271c6991460.min.js | US | text | 152 Kb | unknown |
2228 | chrome.exe | GET | 200 | 52.8.248.79:80 | http://roswell.falcon-sandbox.com/lib/google-fonts/fonts/cabin-400-normal.woff | US | woff | 22.6 Kb | unknown |
2228 | chrome.exe | GET | 200 | 52.8.248.79:80 | http://roswell.falcon-sandbox.com/img/cs.svg | US | image | 1.64 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2228 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 216.58.212.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 172.217.23.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2228 | chrome.exe | 52.8.248.79:80 | roswell.falcon-sandbox.com | Amazon.com, Inc. | US | unknown |
2228 | chrome.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2960 | WINWORD.EXE | 194.40.243.61:80 | bsls9ny.com | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2228 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |