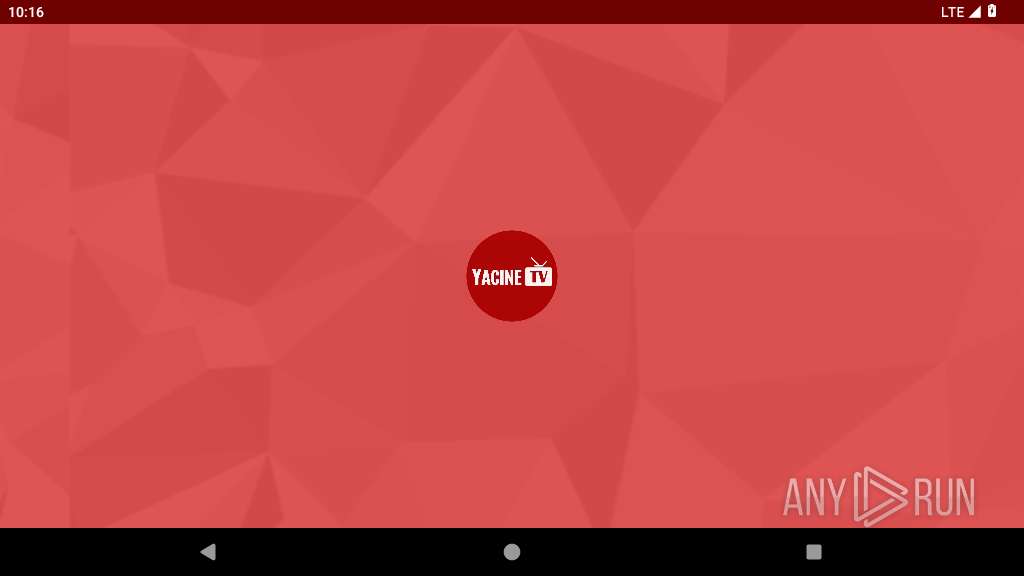
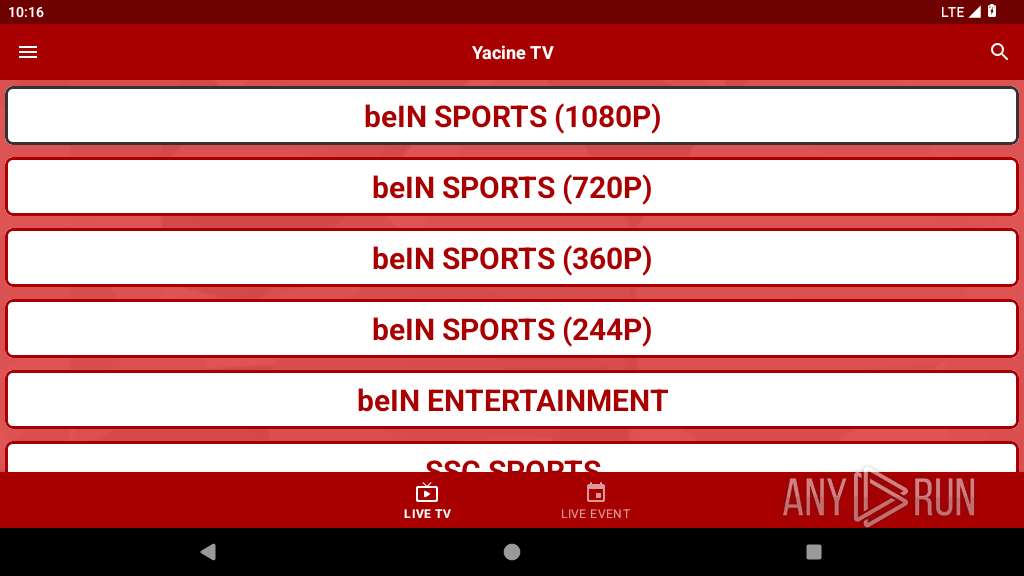
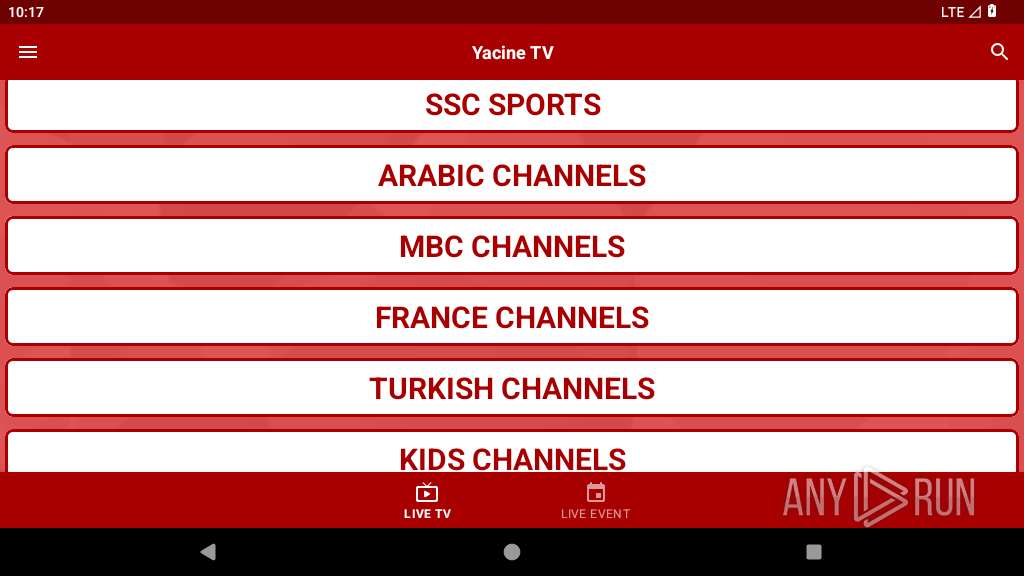
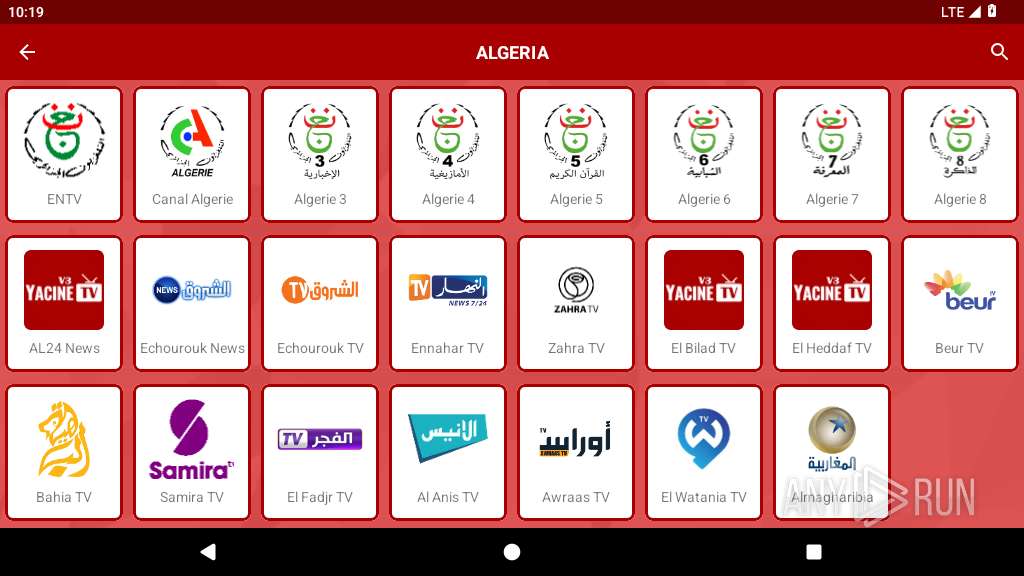
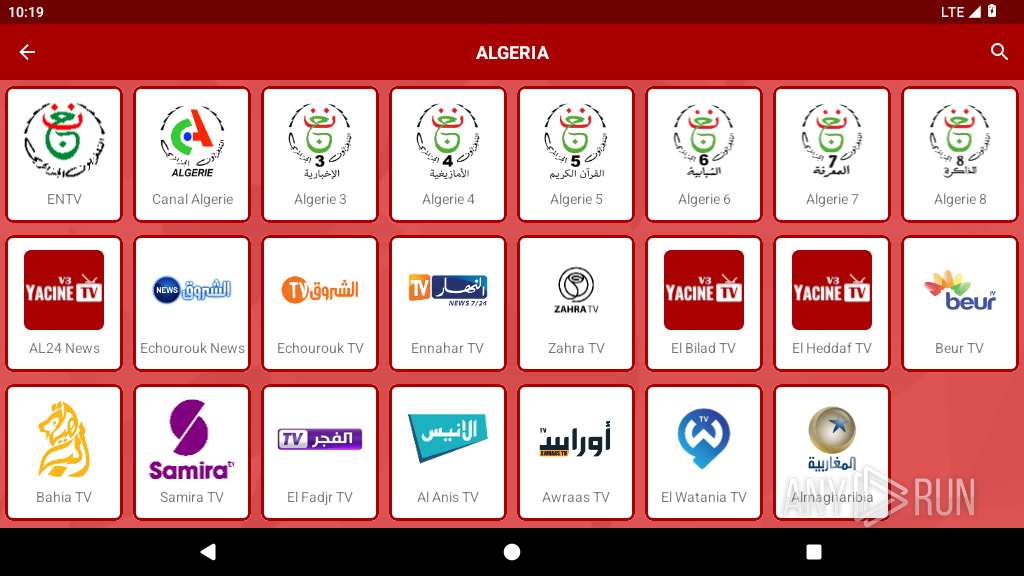
| File name: | ycnV3.2.apk |
| Full analysis: | https://app.any.run/tasks/567a9a33-fbcb-4143-97a8-d0d6309995c0 |
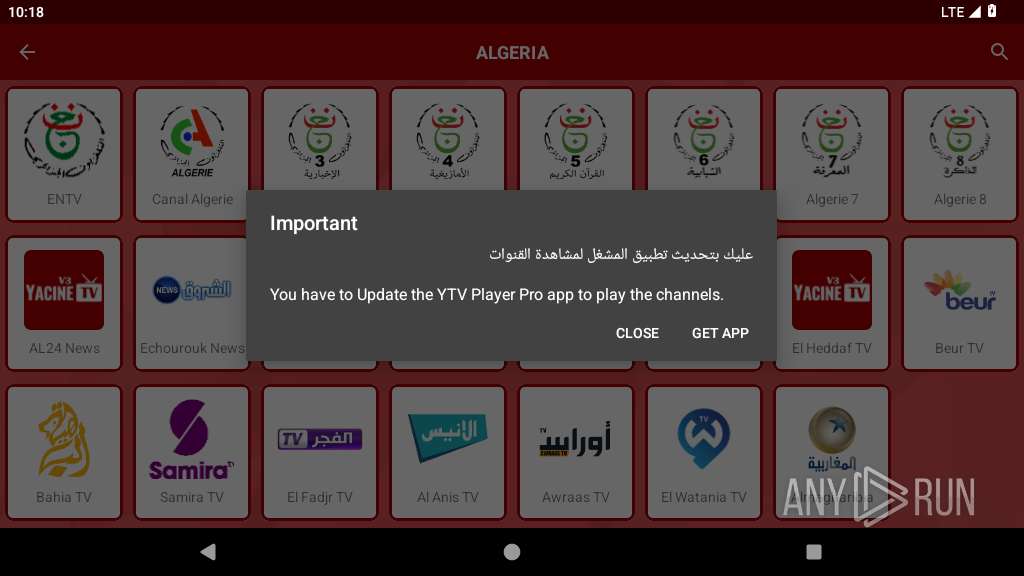
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2025, 10:16:10 |
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with gradle app-metadata.properties |
| MD5: | 2CAAC2E815BB3828F6B320D3CAA5BCEE |
| SHA1: | 640F759111156BD2443D7941510AA478D4CA8D66 |
| SHA256: | 0CBC222443477B45EDBFD4D15033868D910D3758CAE38C22204771677EC2DE1B |
| SSDEEP: | 98304:StU18Xu0Trlf0MBsLqEgvsYYtvyJ0GvxiIPhrYwIOWQBuB5qA35HN09bie+GXLju:dLZDH8e6gqH6P |
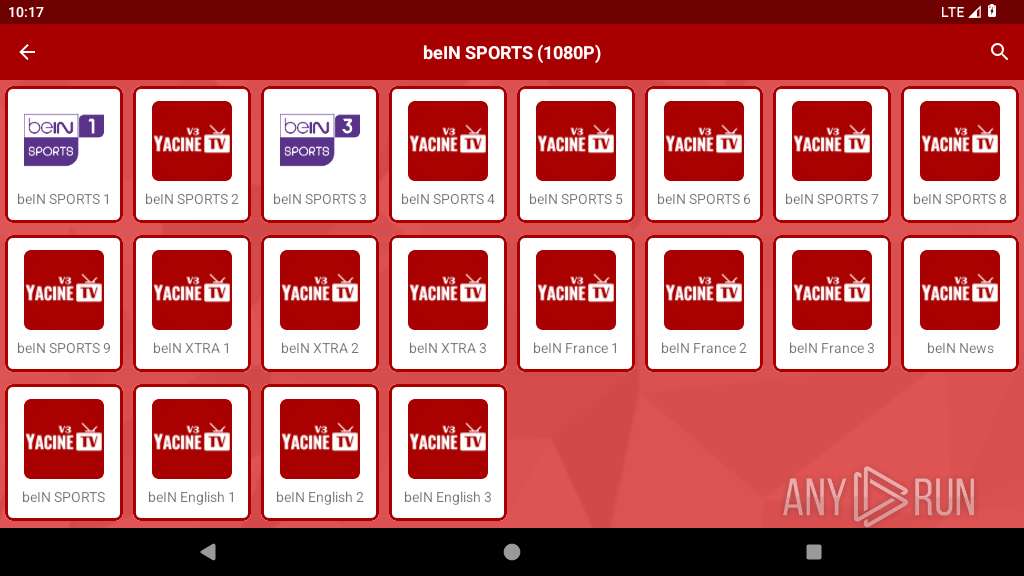
MALICIOUS
Hides app icon from display
- app_process64 (PID: 2252)
Detects root access on device
- app_process64 (PID: 2252)
SUSPICIOUS
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2252)
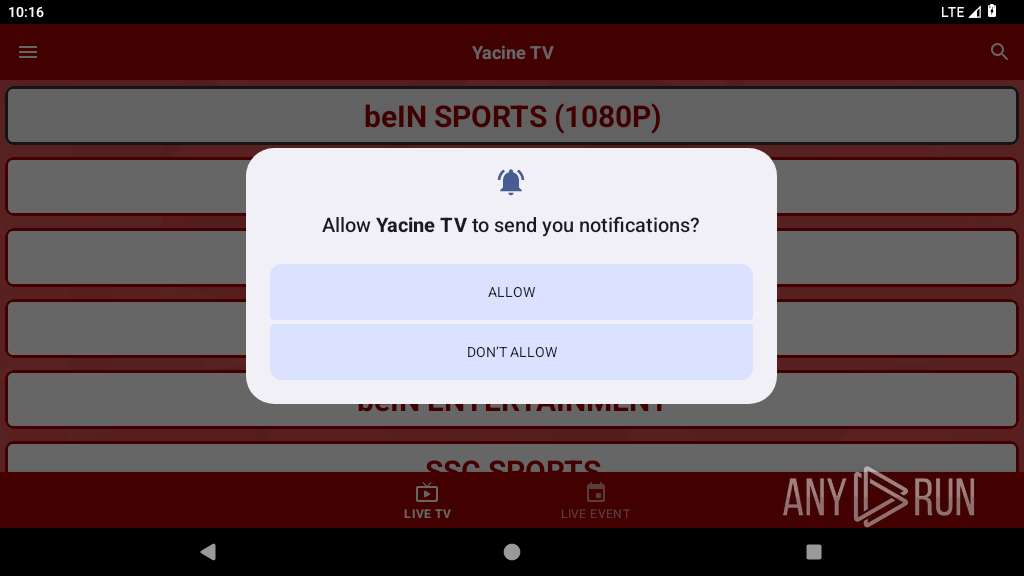
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2252)
Creates a WakeLock to manage power state
- app_process64 (PID: 2252)
Accesses system-level resources
- app_process64 (PID: 2252)
Acquires a wake lock to keep the device awake
- app_process64 (PID: 2252)
Returns the name of the current network operator
- app_process64 (PID: 2252)
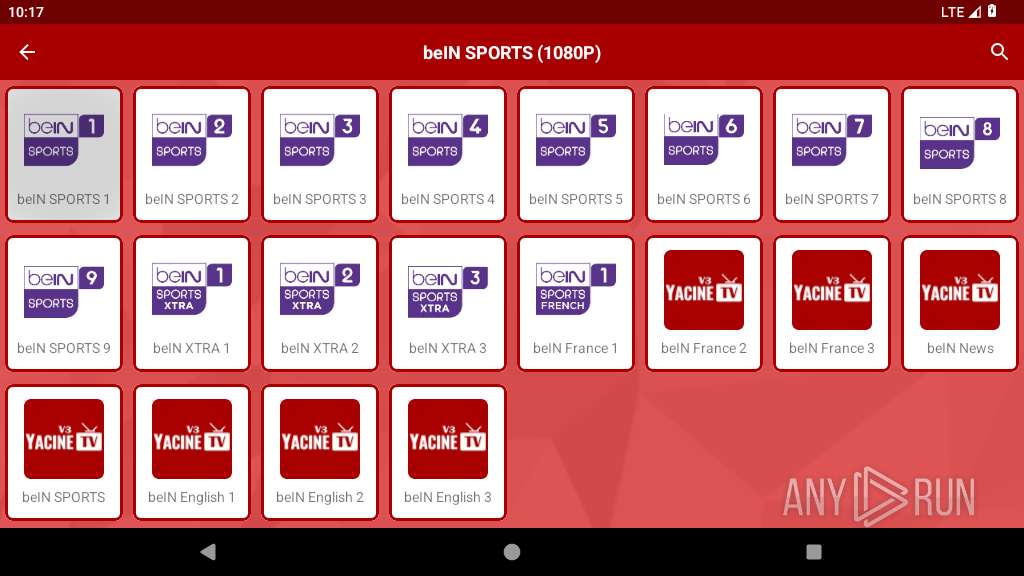
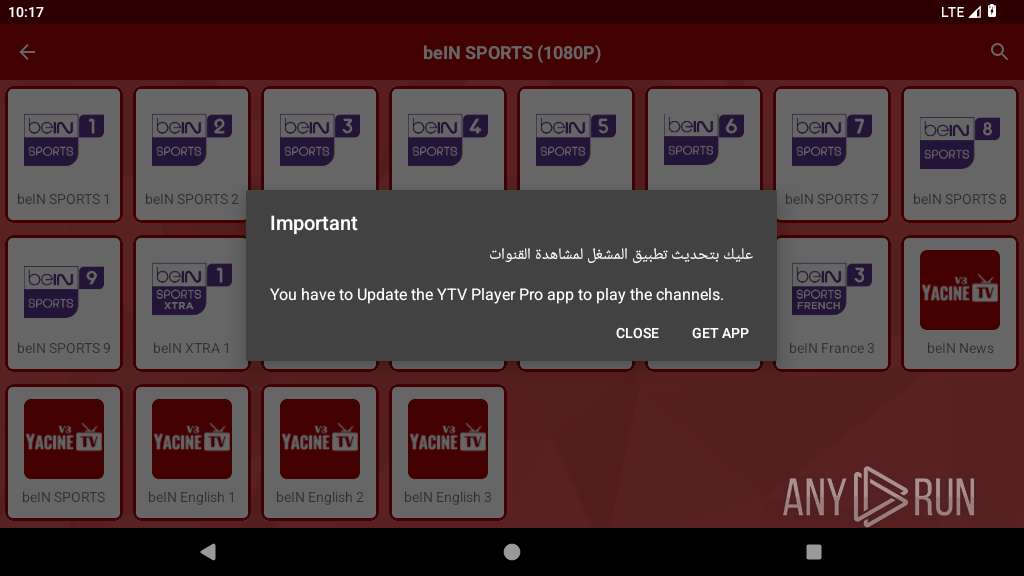
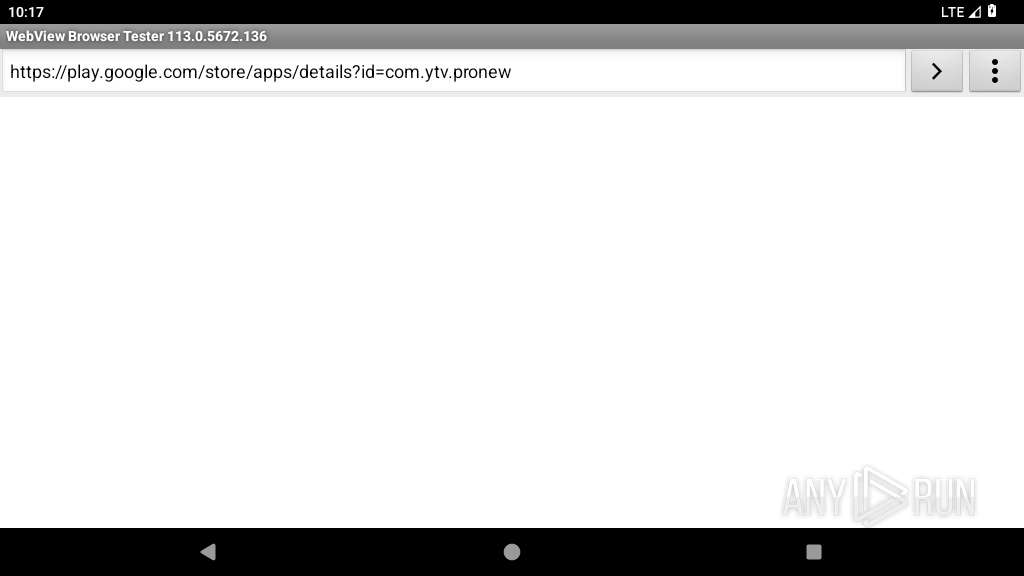
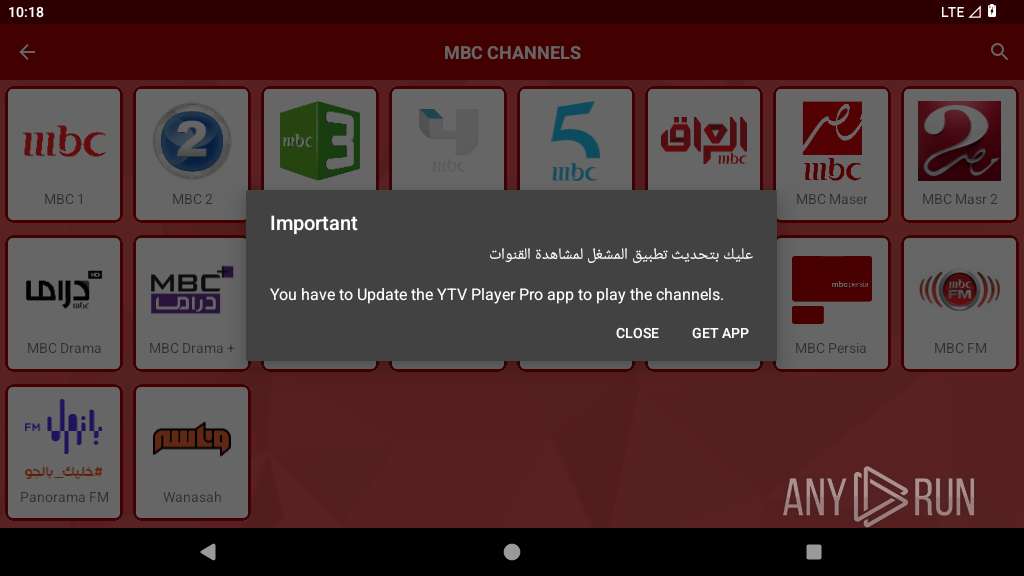
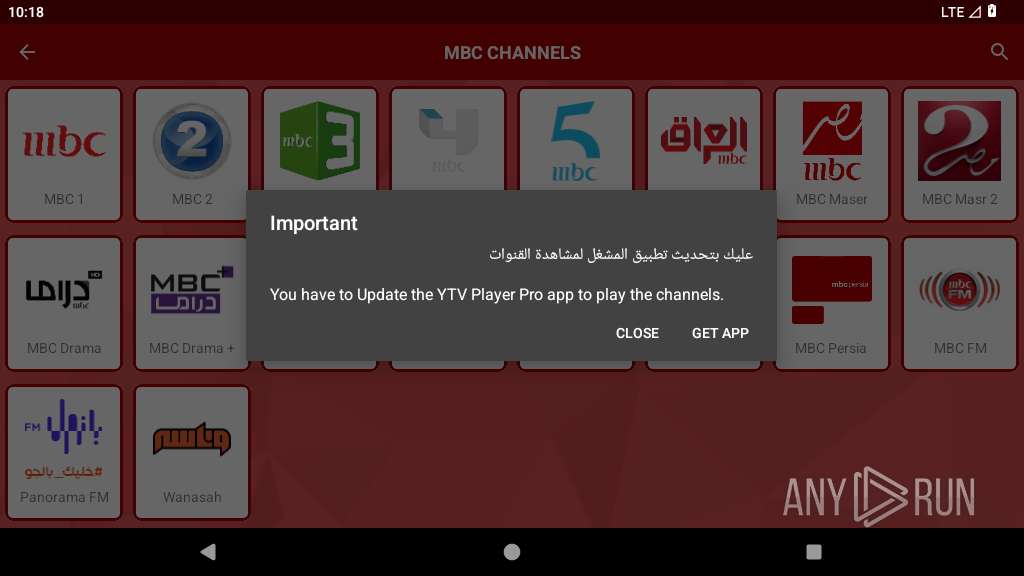
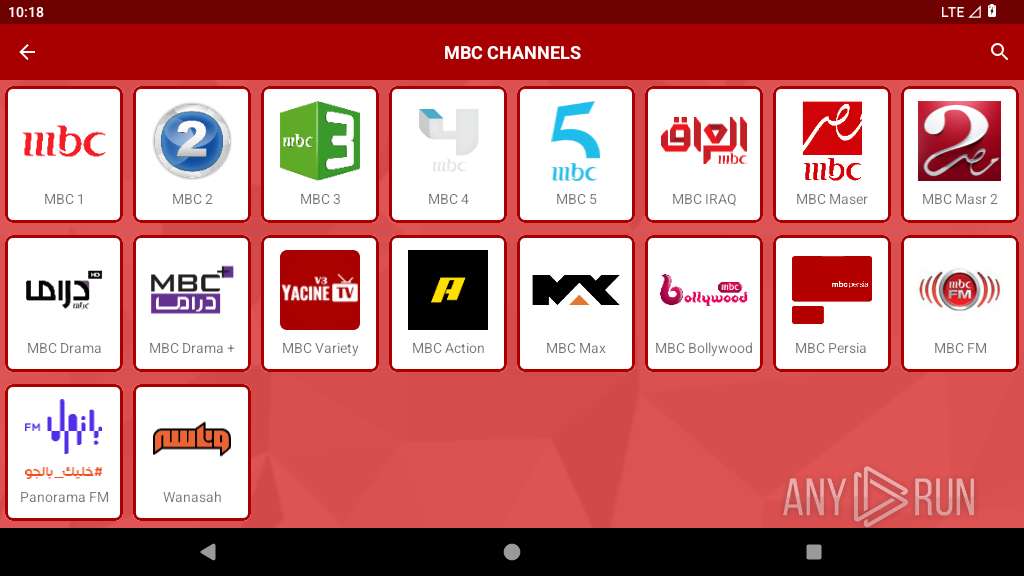
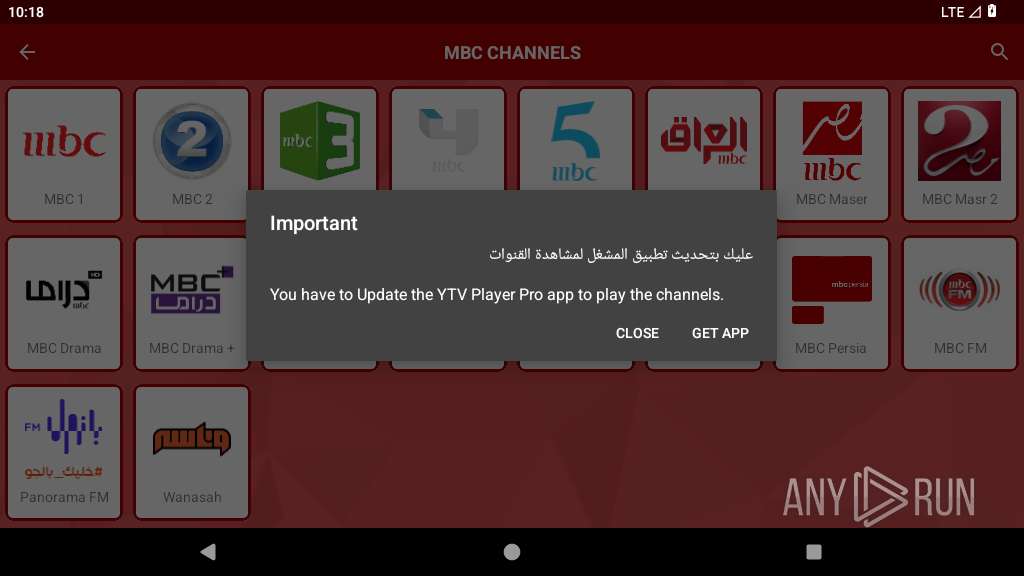
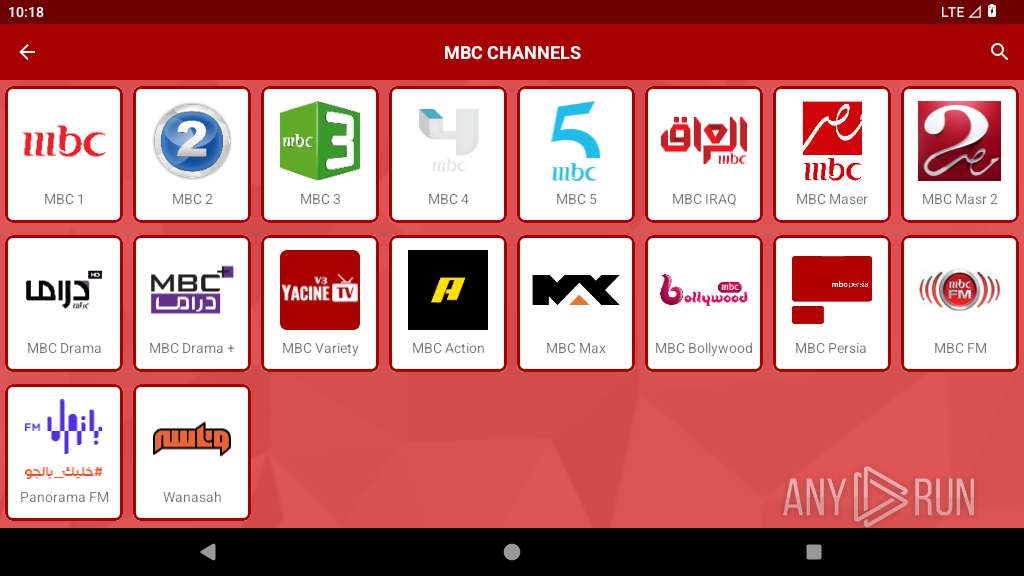
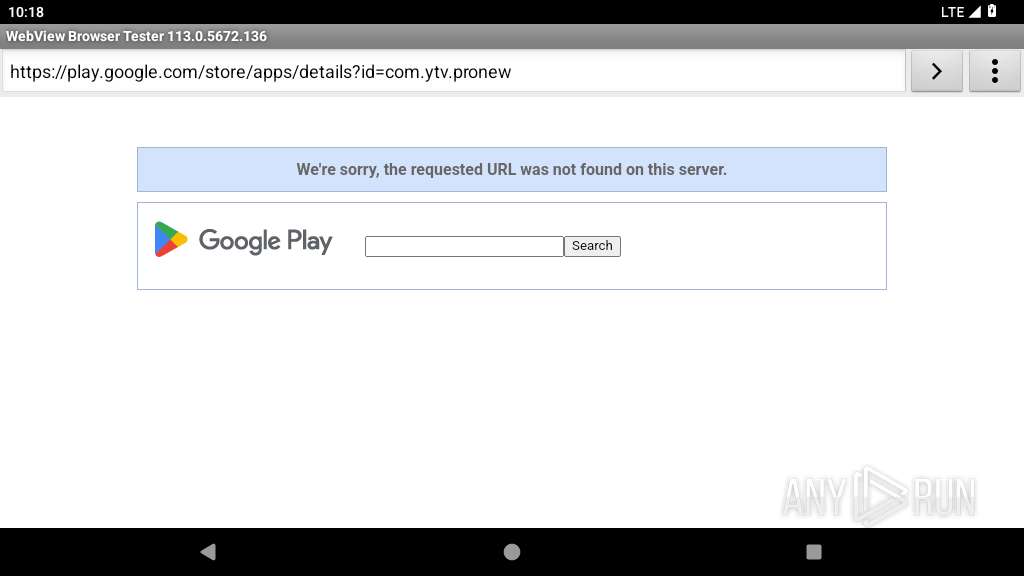
Launches a new activity
- app_process64 (PID: 2252)
Establishing a connection
- app_process64 (PID: 2252)
INFO
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2252)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2252)
Handles throwable exceptions in the app
- app_process64 (PID: 2252)
Dynamically loads a class in Java
- app_process64 (PID: 2252)
Gets file name without full path
- app_process64 (PID: 2252)
Returns elapsed time since boot
- app_process64 (PID: 2252)
Stores data using SQLite database
- app_process64 (PID: 2252)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2252)
Dynamically registers broadcast event listeners
- app_process64 (PID: 2252)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2252)
Loads a native library into the application
- app_process64 (PID: 2252)
Retrieves the value of a global system setting
- app_process64 (PID: 2252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (62.8) |
|---|---|---|
| .jar | | | Java Archive (17.3) |
| .vym | | | VYM Mind Map (14.9) |
| .zip | | | ZIP compressed archive (4.7) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1981:01:01 01:01:02 |
| ZipCRC: | 0xaa2cdc4d |
| ZipCompressedSize: | 52 |
| ZipUncompressedSize: | 56 |
| ZipFileName: | META-INF/com/android/build/gradle/app-metadata.properties |
Total processes
130
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 343 | /system/bin/netd | /system/bin/netd | init | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
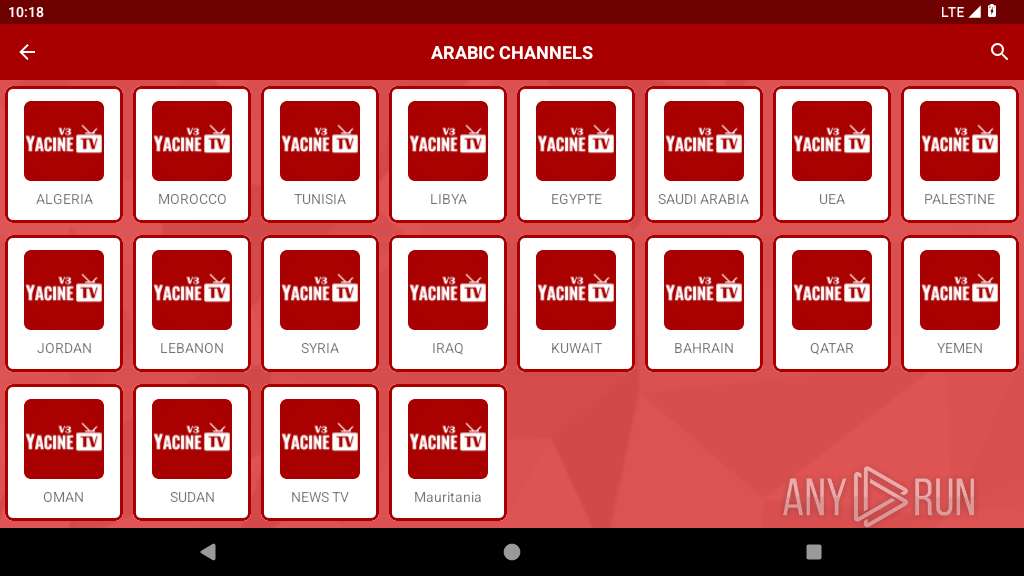
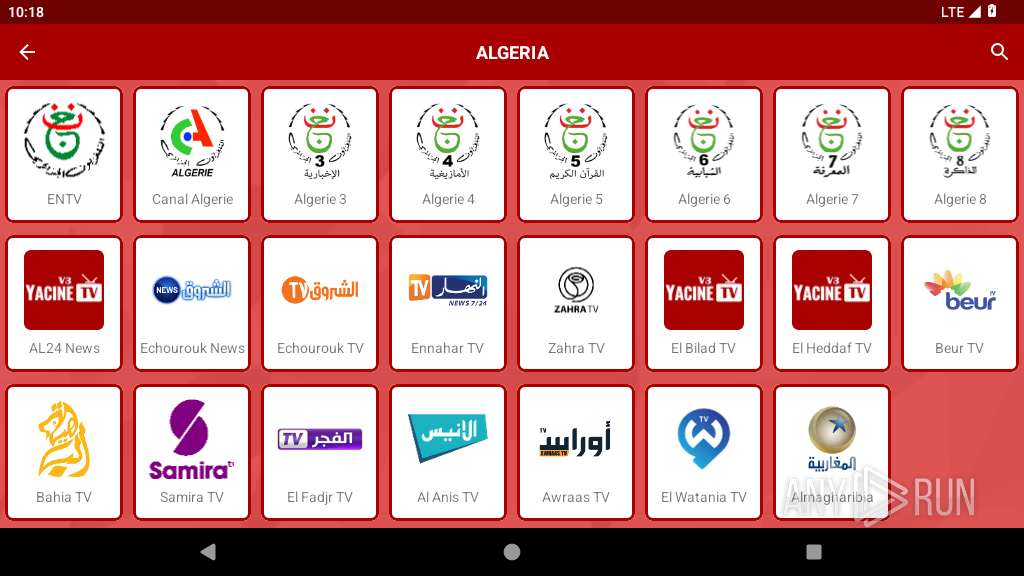
| 2252 | ver3.ycntivi.off | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 9 | ||||
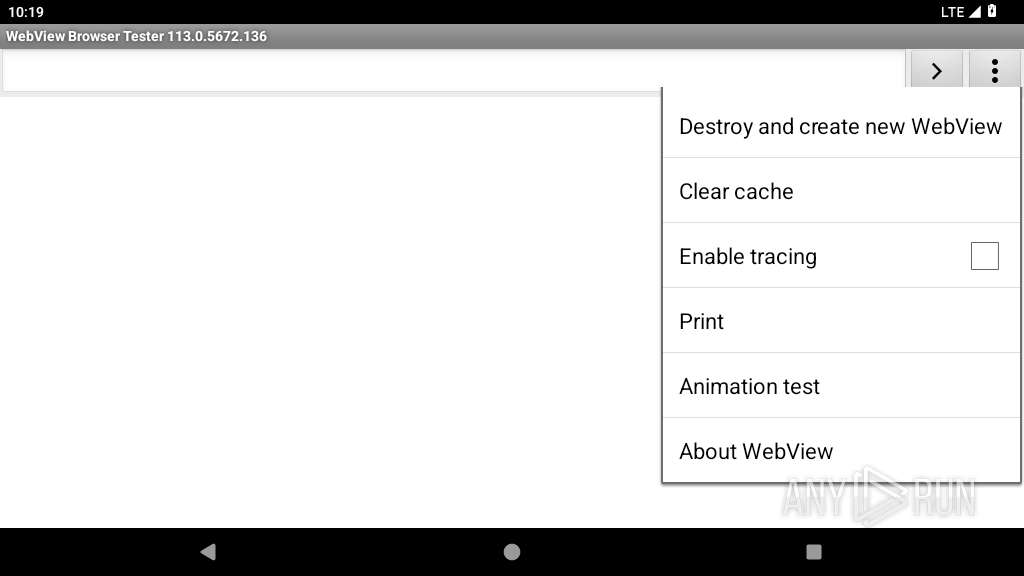
| 2425 | org.chromium.webview_shell | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2451 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2452 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2499 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
20
Text files
216
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2252 | app_process64 | /data/data/ver3.ycntivi.off/no_backup/androidx.work.workdb-journal | binary | |
MD5:— | SHA256:— | |||
| 2252 | app_process64 | /data/data/ver3.ycntivi.off/no_backup/androidx.work.workdb-wal | binary | |
MD5:— | SHA256:— | |||
| 2252 | app_process64 | /data/data/ver3.ycntivi.off/shared_prefs/FirebaseHeartBeatW0RFRkFVTFRd+MTo2OTIzMzA1ODQxOTY6YW5kcm9pZDo2OGVhOWYwYzkyMGFhMTc5MDRjYWQx.xml | xml | |
MD5:— | SHA256:— | |||
| 2252 | app_process64 | /data/data/ver3.ycntivi.off/shared_prefs/com.google.android.gms.analytics.prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2252 | app_process64 | /data/data/ver3.ycntivi.off/shared_prefs/com.google.firebase.messaging.xml | xml | |
MD5:— | SHA256:— | |||
| 2252 | app_process64 | /data/data/ver3.ycntivi.off/shared_prefs/com.google.android.gms.measurement.prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2252 | app_process64 | /data/data/ver3.ycntivi.off/files/PersistedInstallation2745903093421574289tmp | binary | |
MD5:— | SHA256:— | |||
| 2252 | app_process64 | /data/data/ver3.ycntivi.off/files/PersistedInstallation.W0RFRkFVTFRd+MTo2OTIzMzA1ODQxOTY6YW5kcm9pZDo2OGVhOWYwYzkyMGFhMTc5MDRjYWQx.json | binary | |
MD5:— | SHA256:— | |||
| 2252 | app_process64 | /data/data/ver3.ycntivi.off/databases/google_app_measurement_local.db | binary | |
MD5:— | SHA256:— | |||
| 2252 | app_process64 | /data/data/ver3.ycntivi.off/files/PersistedInstallation2908578597058247810tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
60
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.251.39.99:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
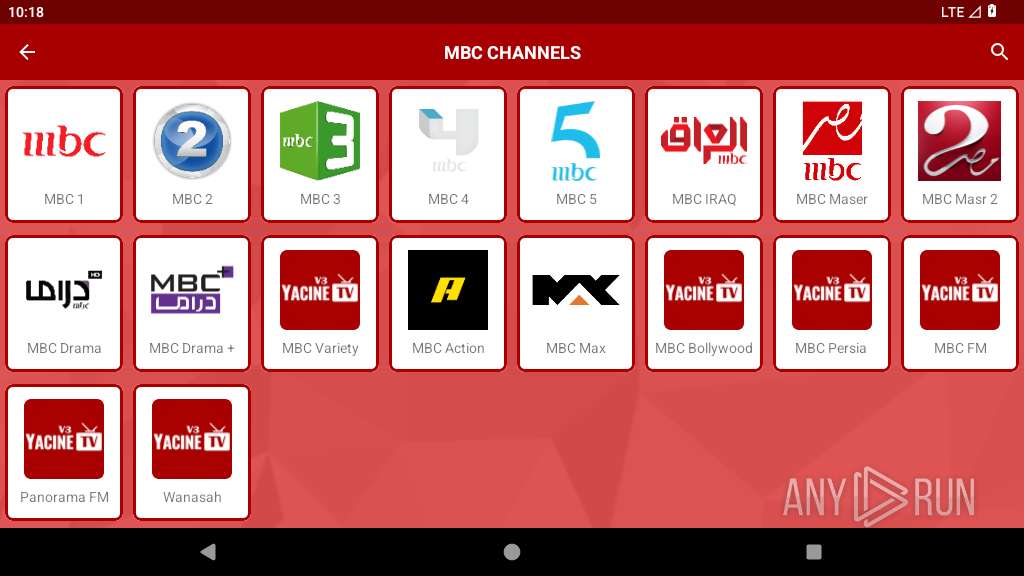
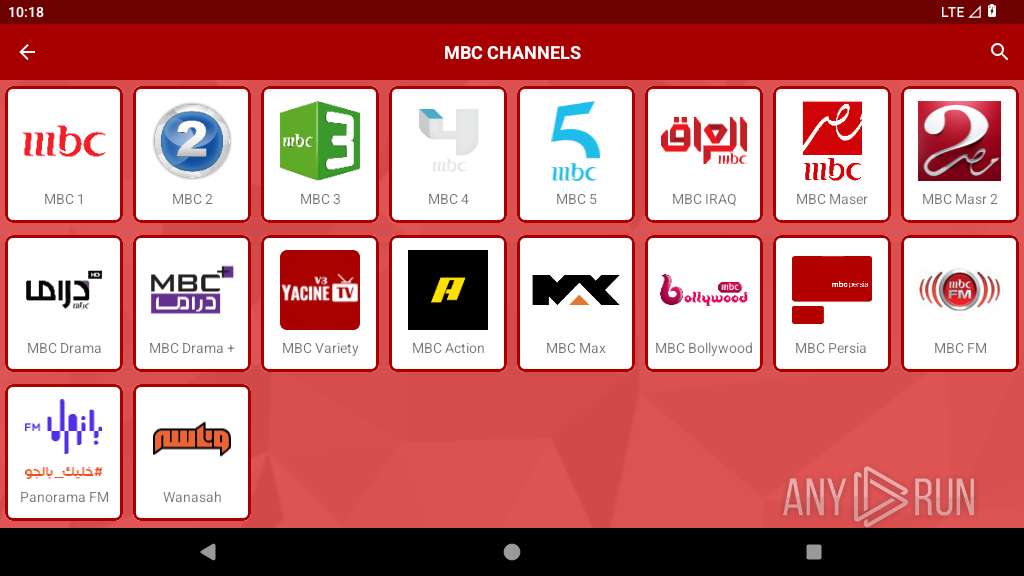
2252 | app_process64 | GET | — | 91.108.98.190:80 | http://www.tunisvista.com/medias/mbc-drama-plus-tv-live-online-streaming.png | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
447 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 216.239.35.8:123 | time.android.com | — | — | whitelisted |
343 | netd | 8.8.8.8:443 | — | — | — | malicious |
— | — | 8.8.8.8:853 | — | GOOGLE | US | malicious |
— | — | 172.217.23.196:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.39.99:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.250.27.81:443 | — | GOOGLE | US | unknown |
575 | app_process64 | 216.239.35.0:123 | time.android.com | — | — | whitelisted |
575 | app_process64 | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
575 | app_process64 | 216.239.35.12:123 | time.android.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
time.android.com |
| whitelisted |
V91yz6-dnsotls-ds.metric.gstatic.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |