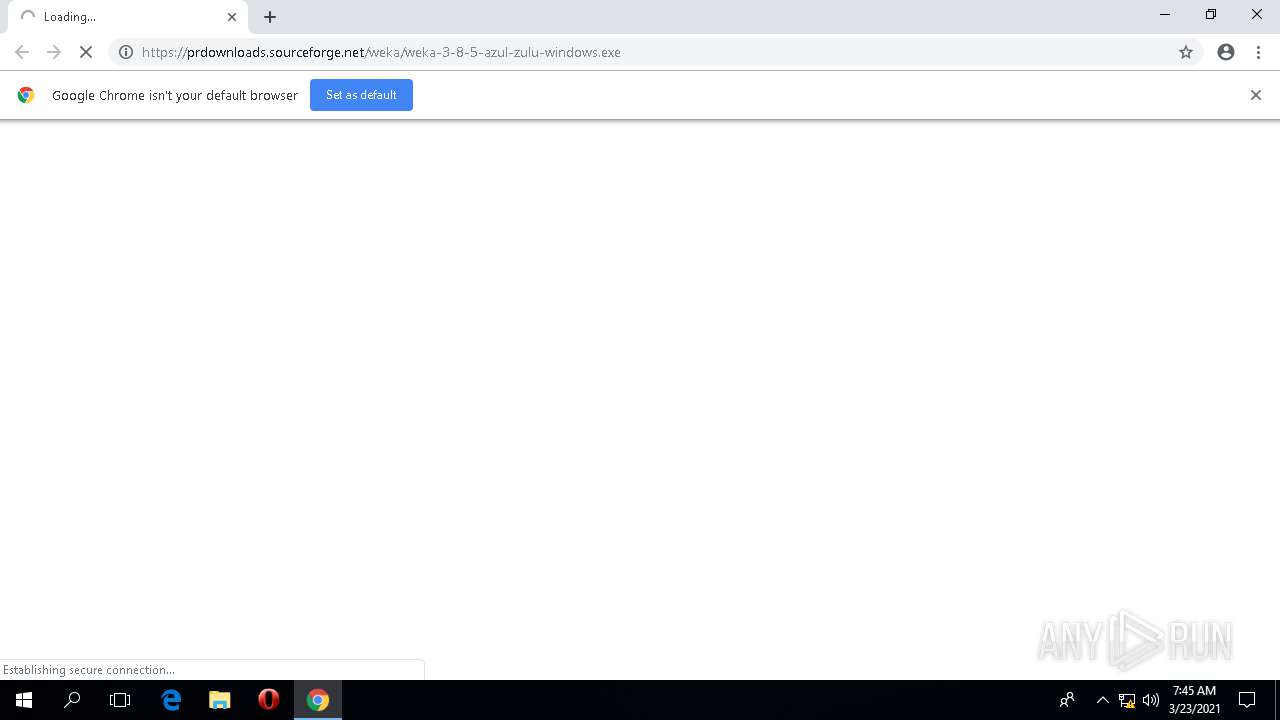
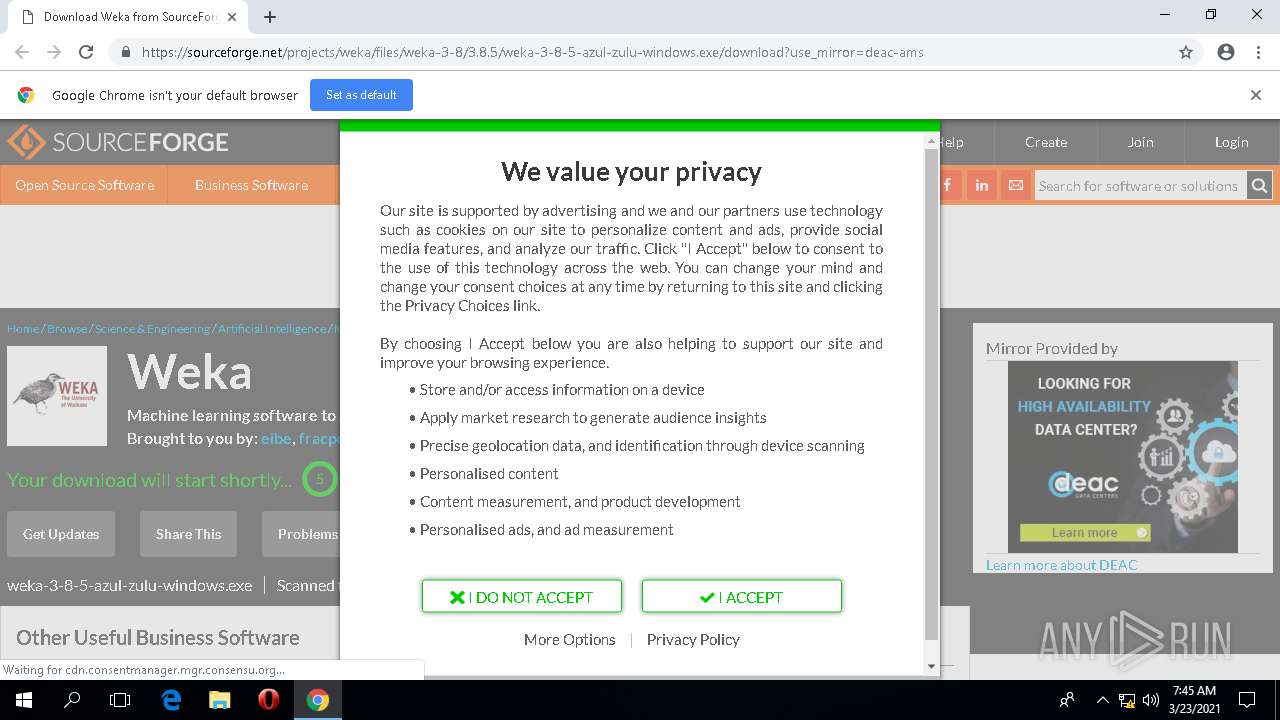
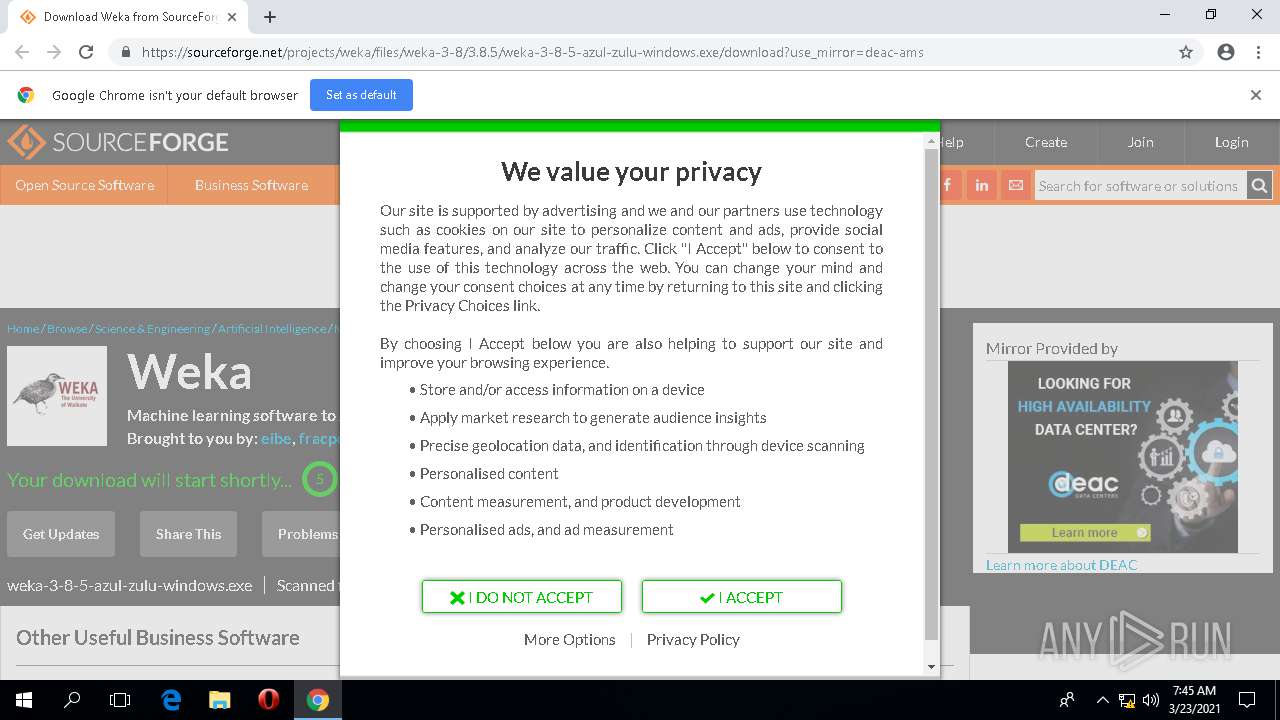
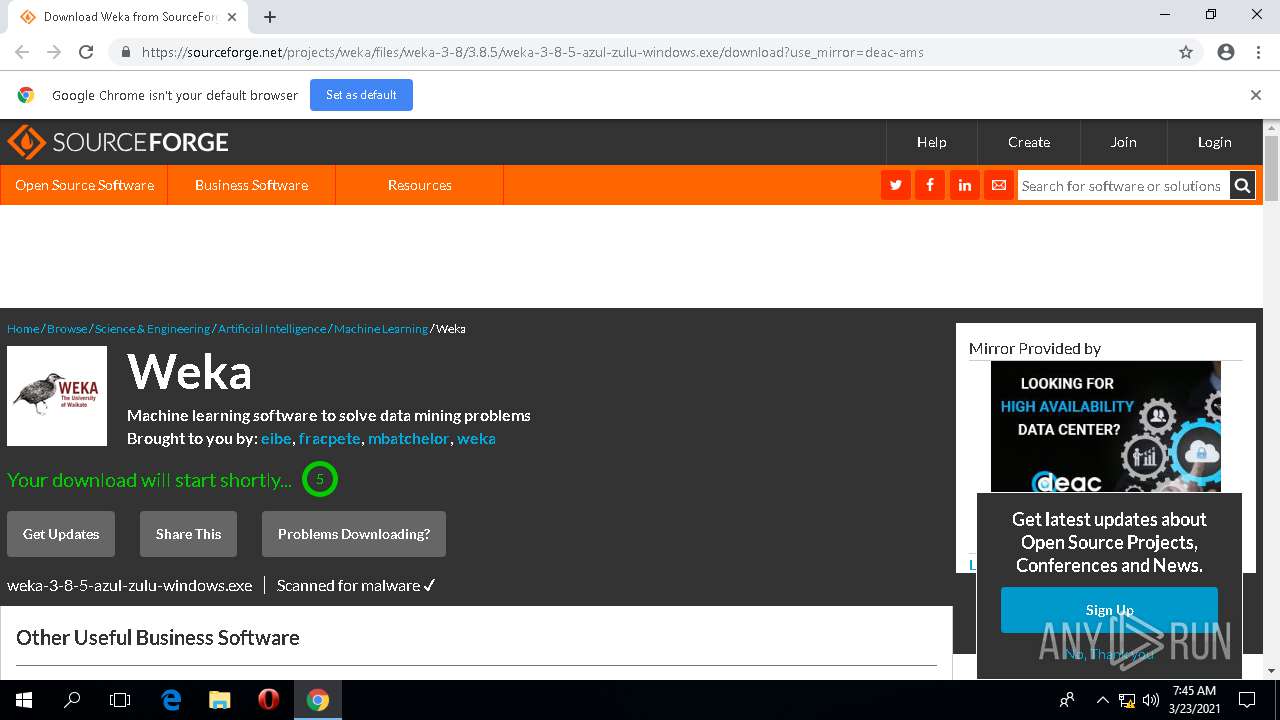
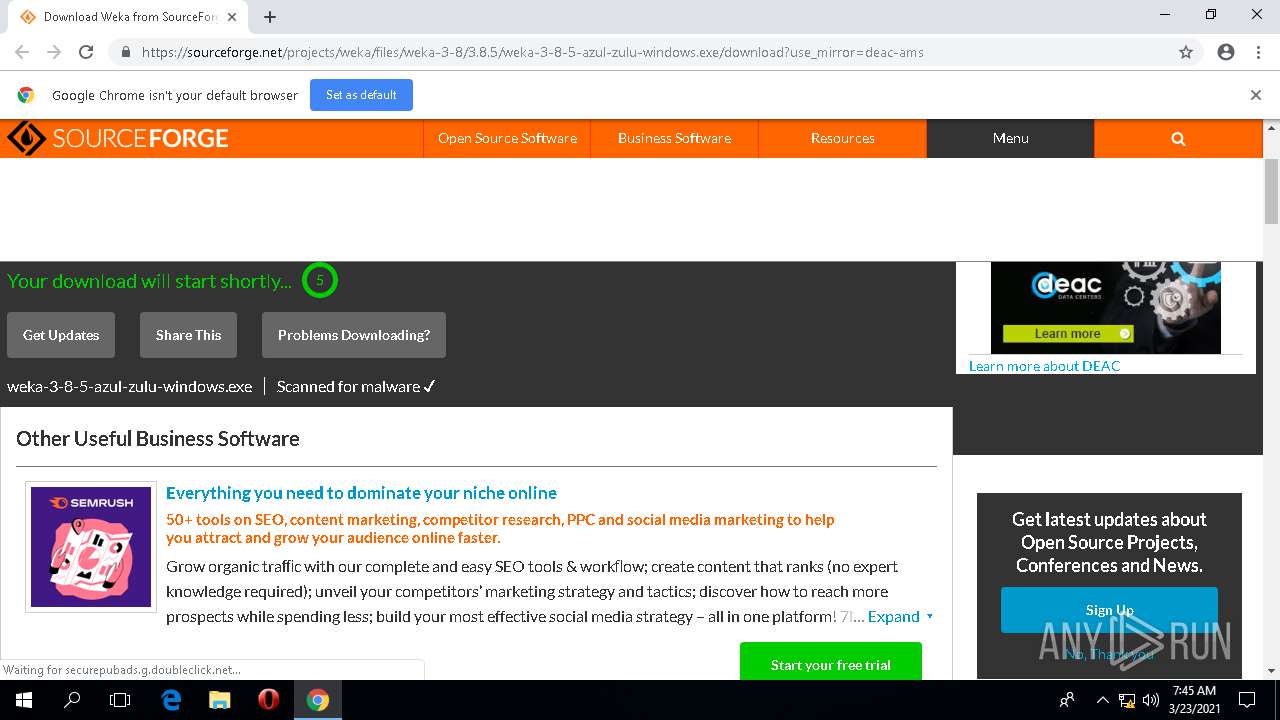
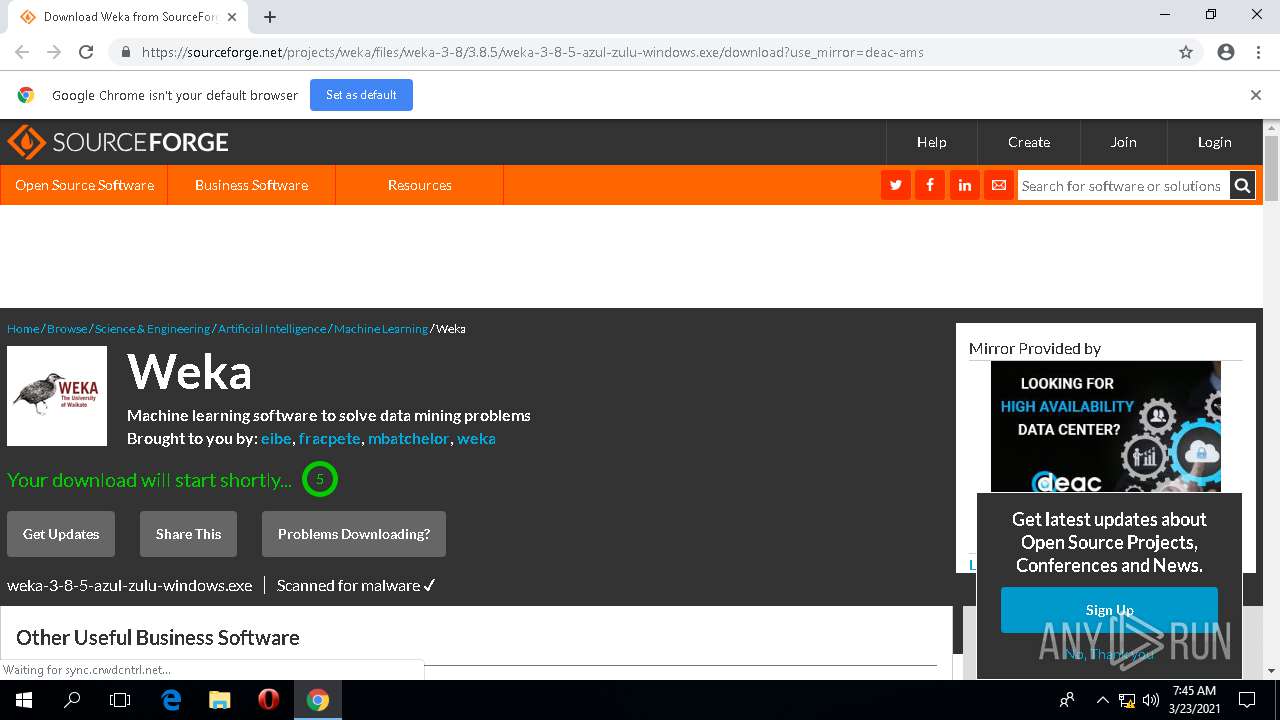
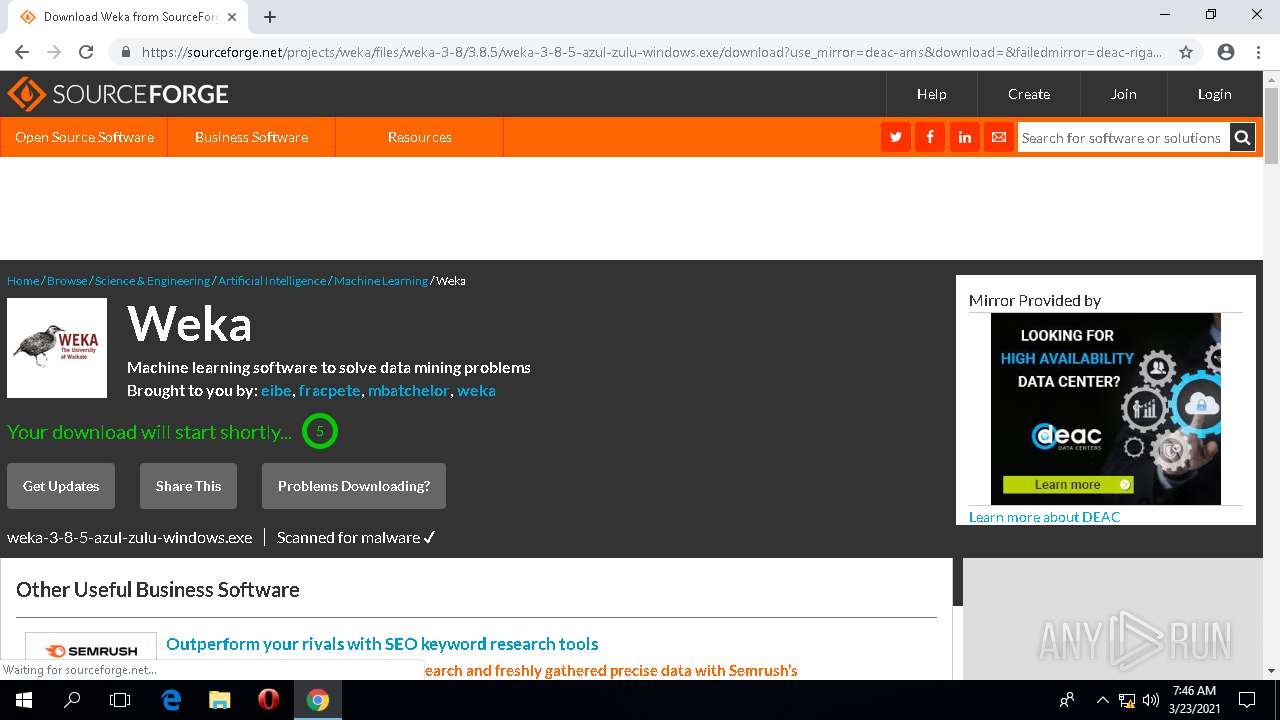
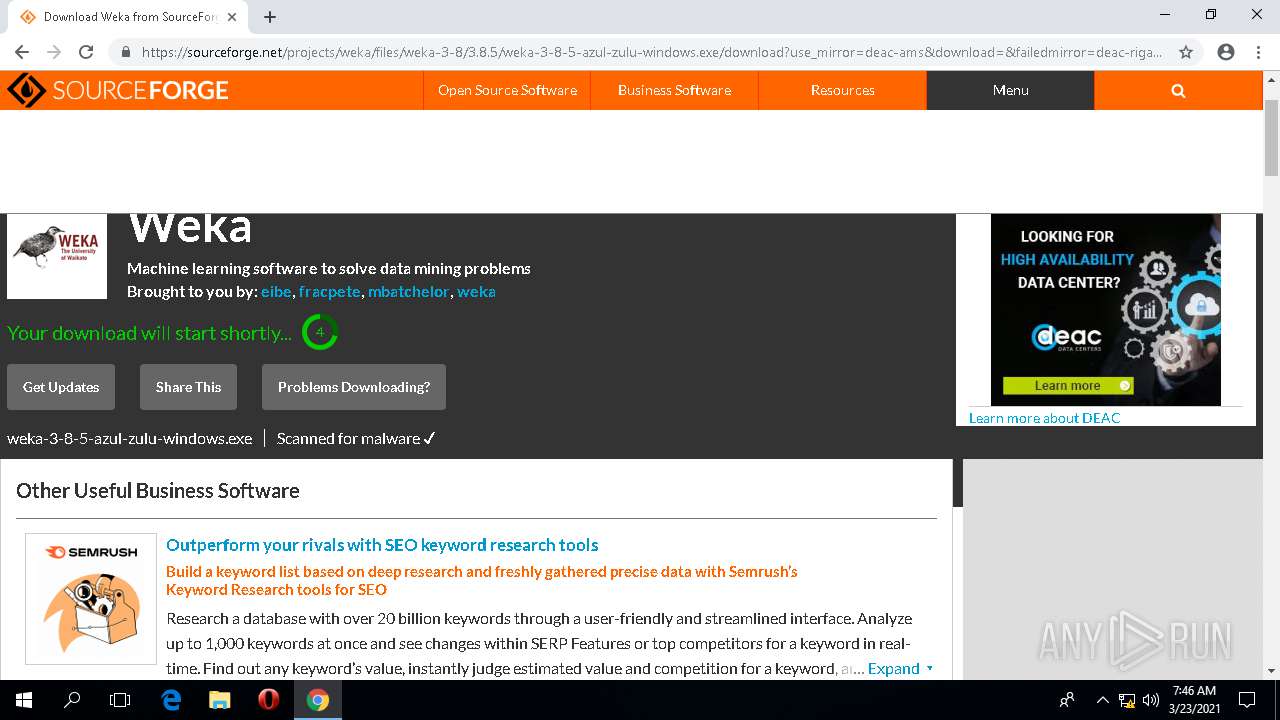
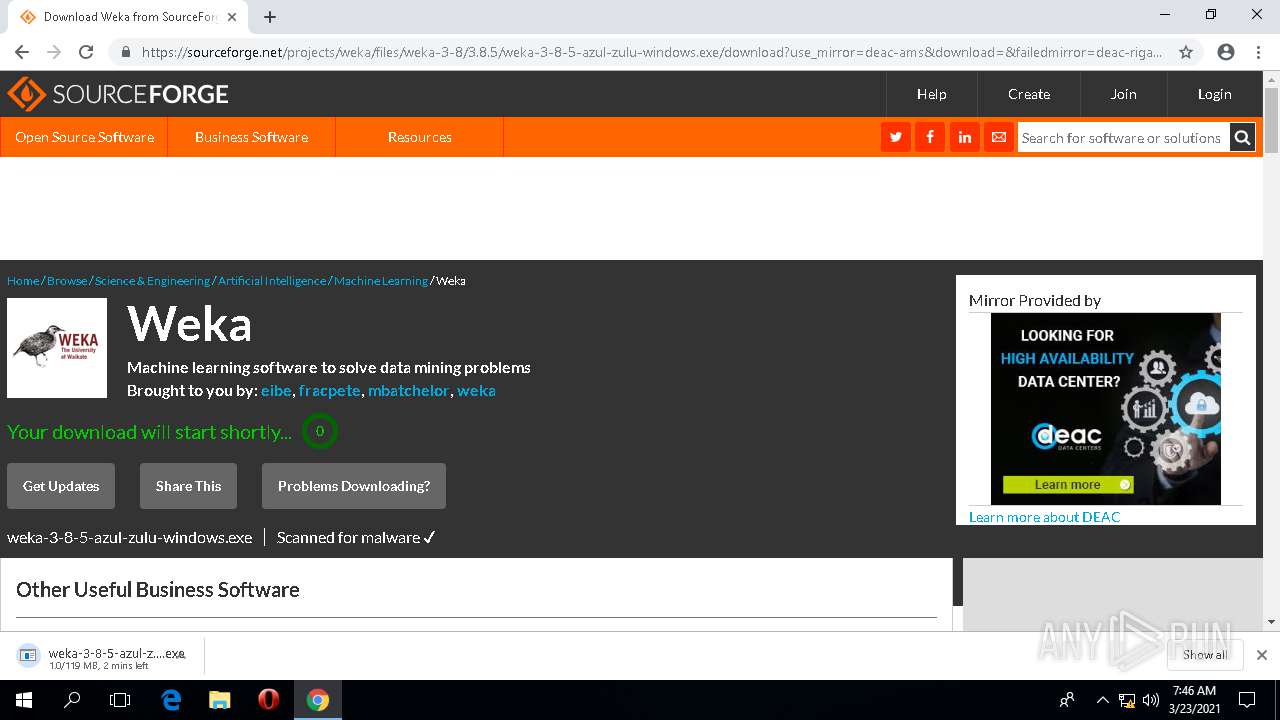
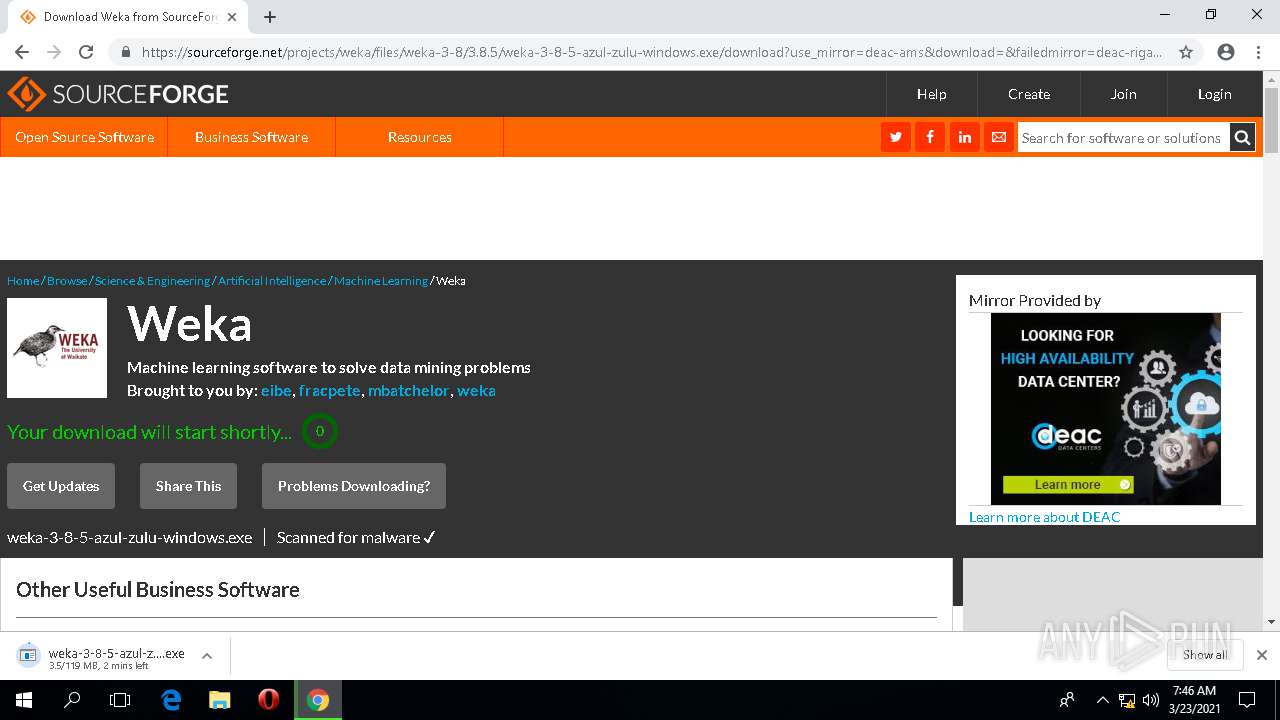
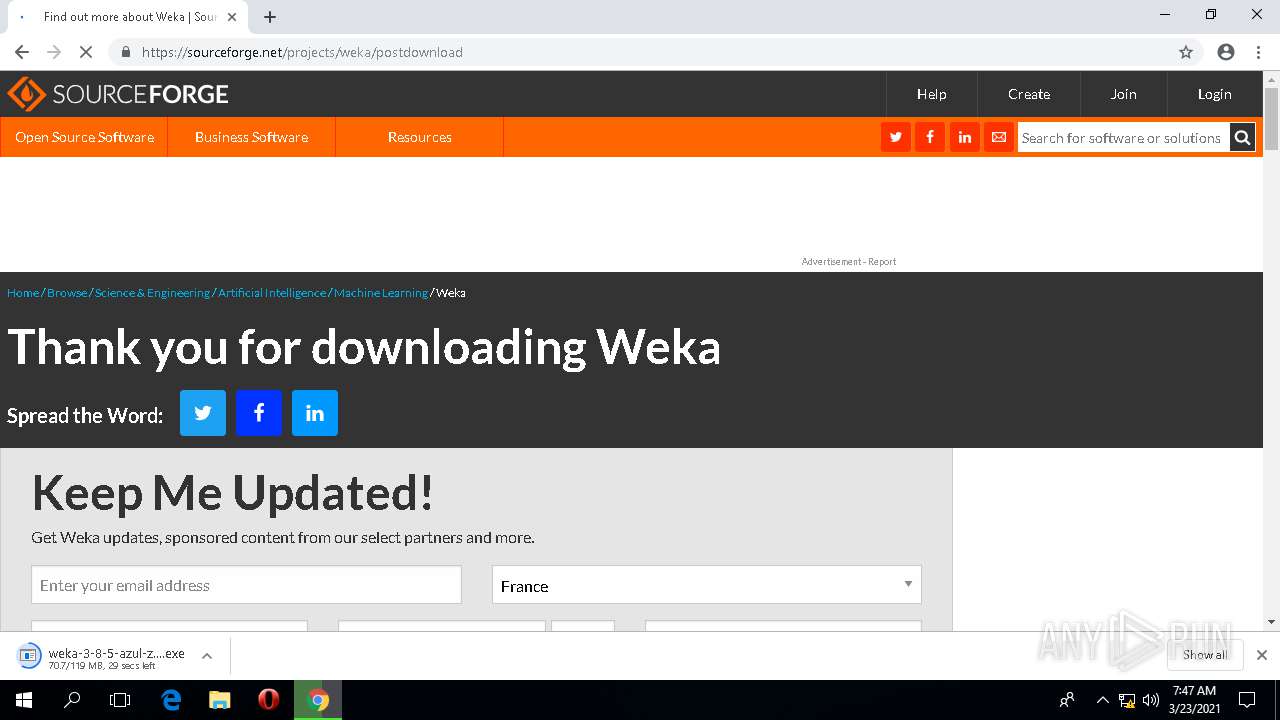
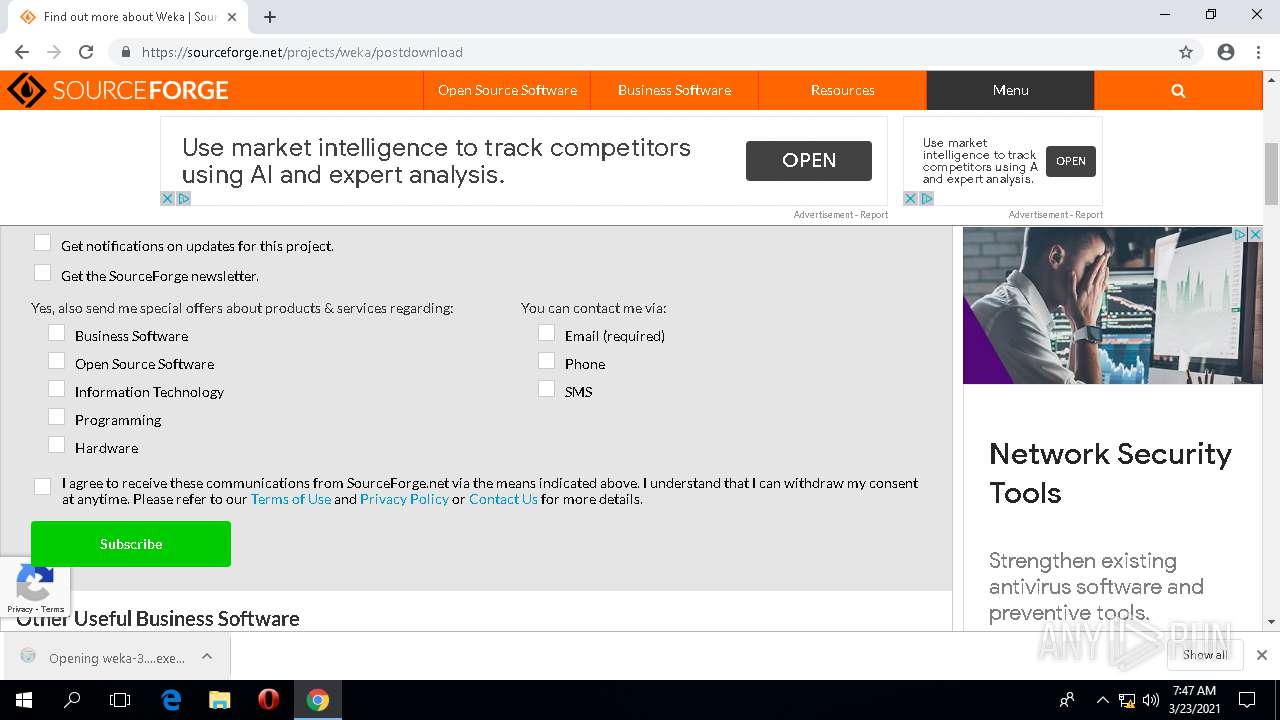
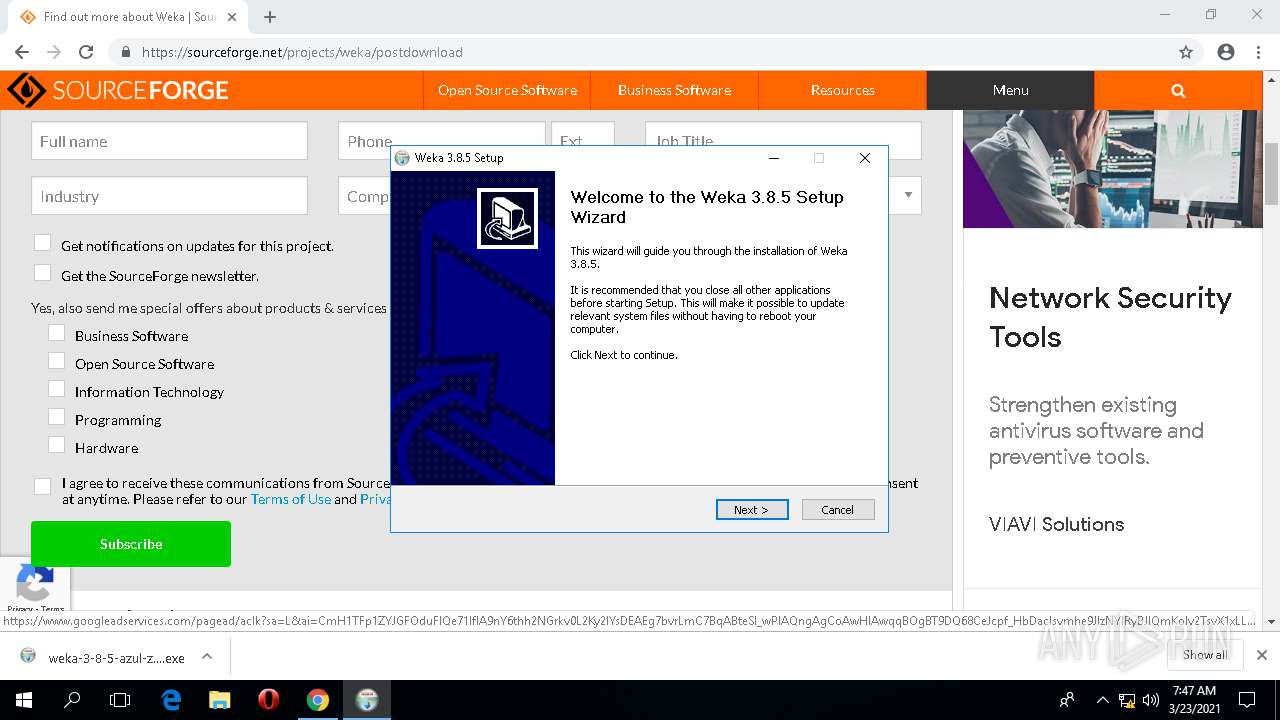
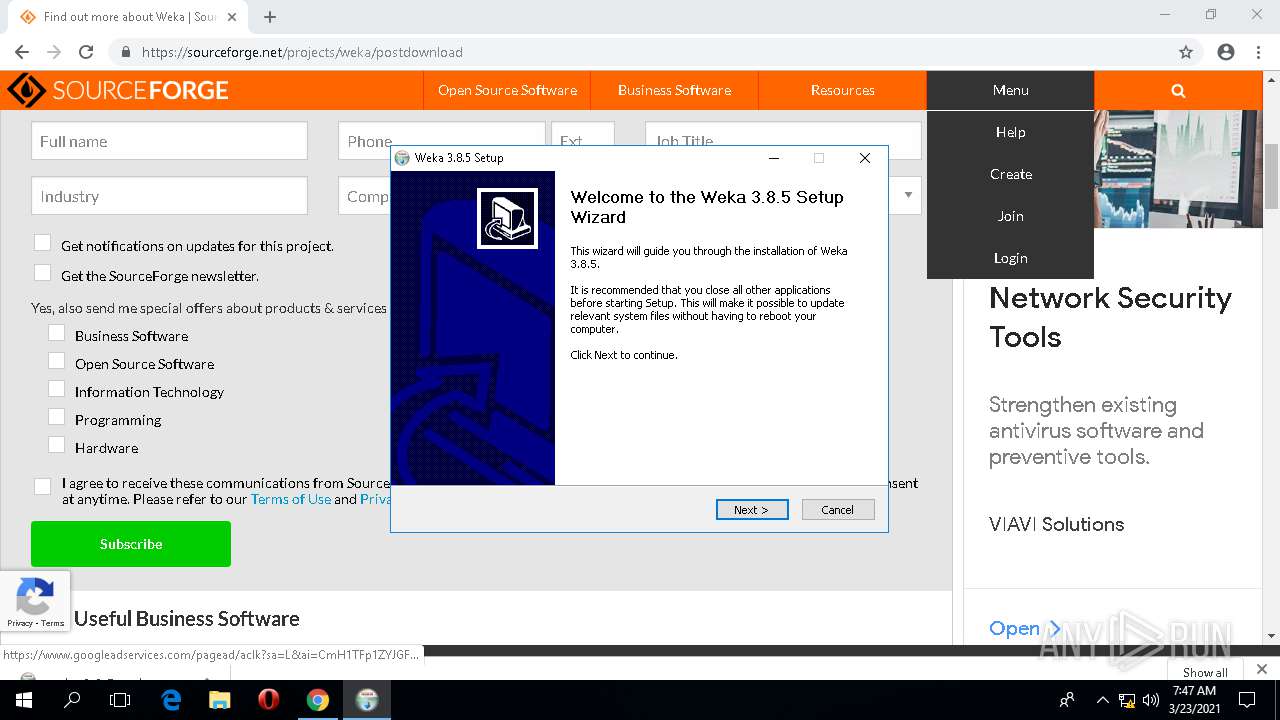
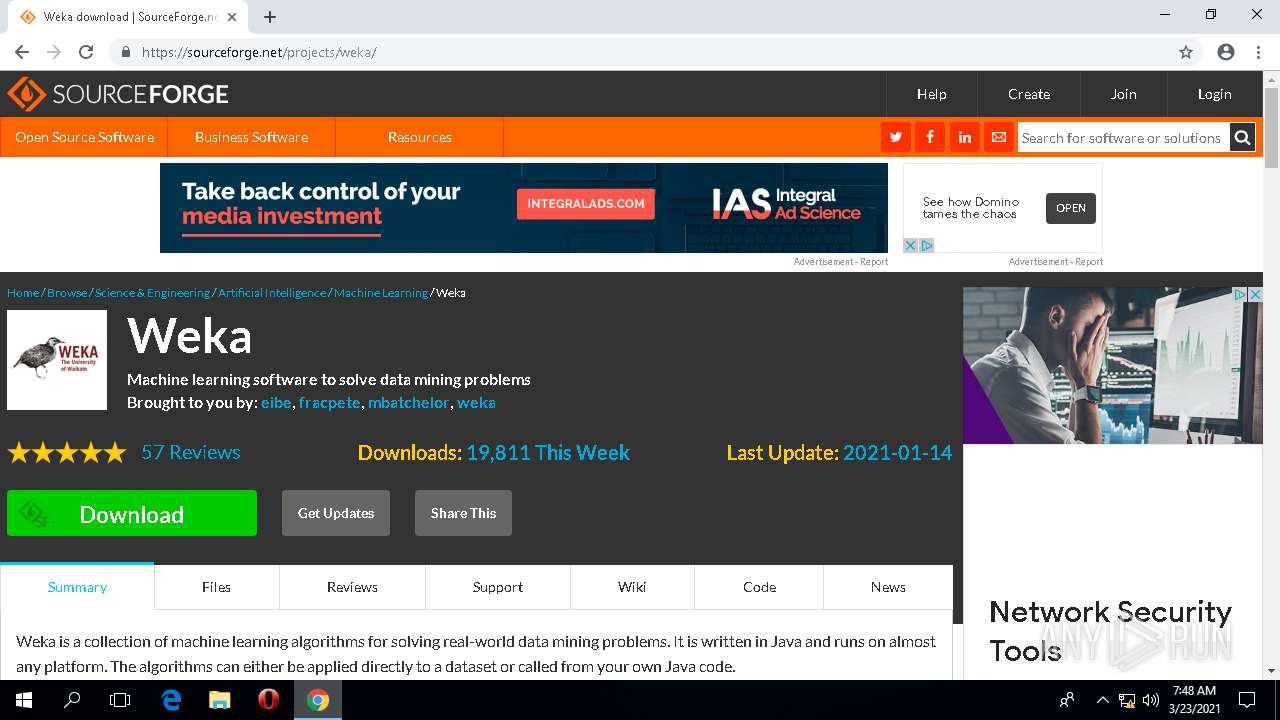
| URL: | https://prdownloads.sourceforge.net/weka/weka-3-8-5-azul-zulu-windows.exe |
| Full analysis: | https://app.any.run/tasks/863fe7e7-43f3-446a-91cf-9136890afd65 |
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2021, 07:45:18 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MD5: | CA9A95DB12A66A92AC9BCF77B13BCDE6 |
| SHA1: | 44205CDD73B663E4E246F00E652CDB458DF3926B |
| SHA256: | 0CB62A8ECC9C9F28B750202C53B611B7DD3B04D4580E438DEA8B7CE8F05BE78B |
| SSDEEP: | 3:N8TBKE4LVSuLAseSQIPVfHBSrA:2NzknvSrA |
MALICIOUS
Application was dropped or rewritten from another process
- weka-3-8-5-azul-zulu-windows.exe (PID: 3760)
- weka-3-8-5-azul-zulu-windows.exe (PID: 3532)
- java.exe (PID: 992)
- java.exe (PID: 1844)
Loads dropped or rewritten executable
- weka-3-8-5-azul-zulu-windows.exe (PID: 3760)
- java.exe (PID: 992)
- java.exe (PID: 1844)
SUSPICIOUS
Drops a file with too old compile date
- chrome.exe (PID: 4164)
- weka-3-8-5-azul-zulu-windows.exe (PID: 3760)
Executable content was dropped or overwritten
- chrome.exe (PID: 4164)
- weka-3-8-5-azul-zulu-windows.exe (PID: 3760)
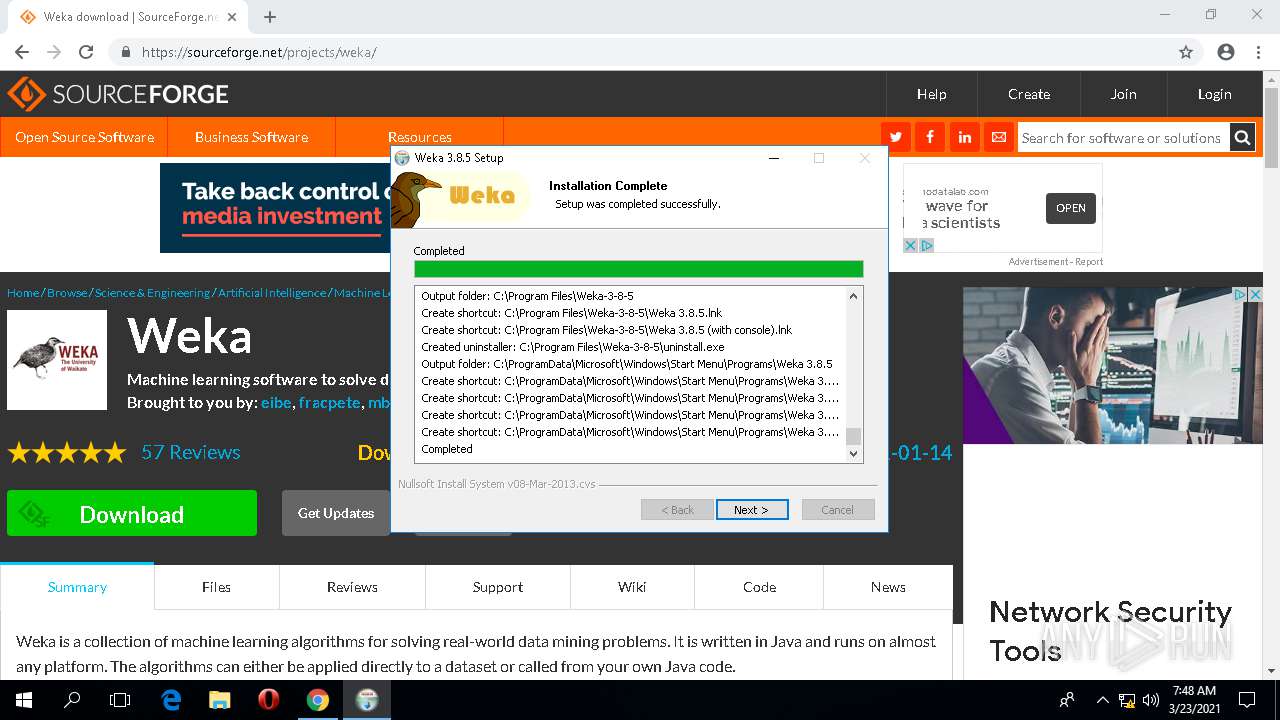
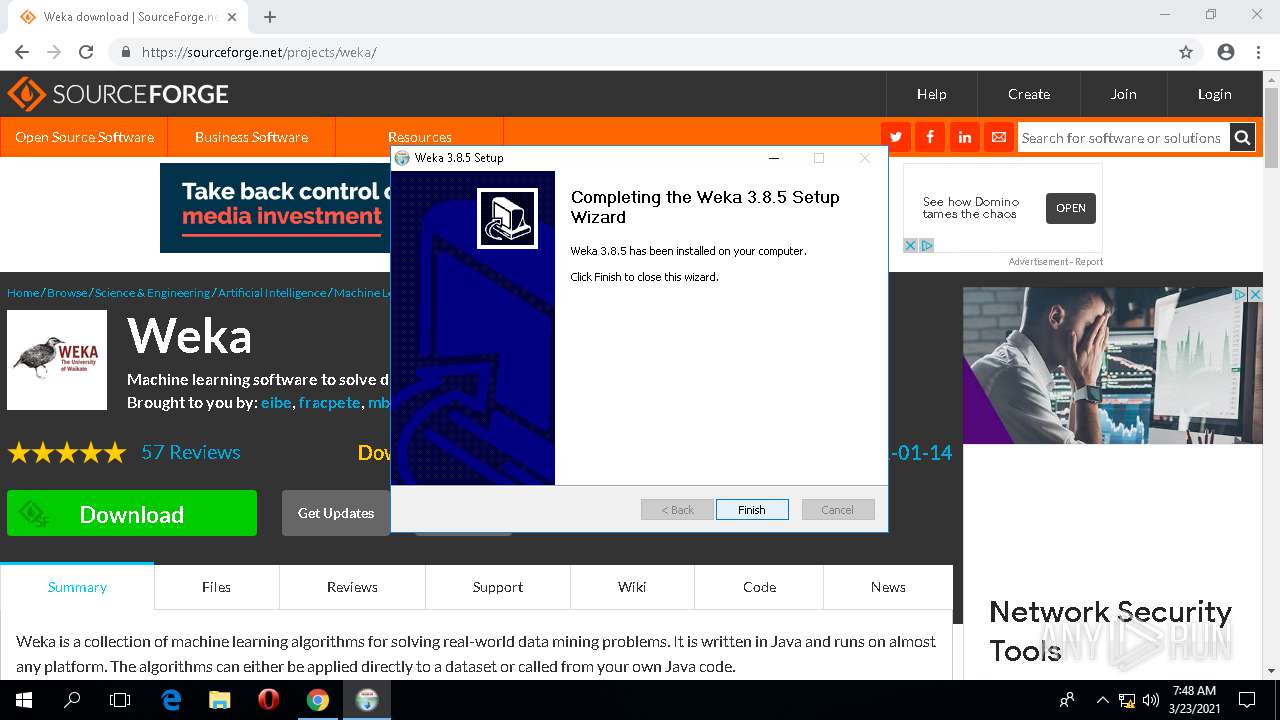
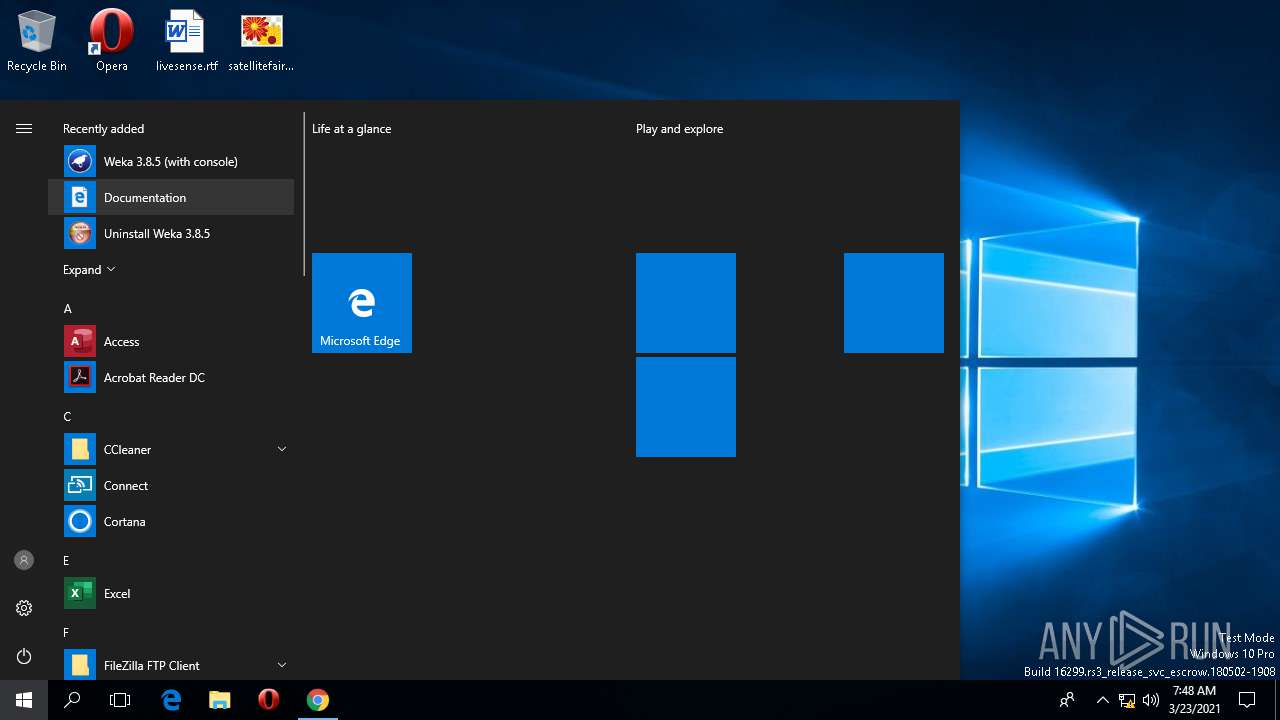
Creates a software uninstall entry
- weka-3-8-5-azul-zulu-windows.exe (PID: 3760)
Executed via COM
- DllHost.exe (PID: 4796)
- RuntimeBroker.exe (PID: 4564)
- DllHost.exe (PID: 4472)
Drops a file with a compile date too recent
- weka-3-8-5-azul-zulu-windows.exe (PID: 3760)
Drops a file that was compiled in debug mode
- weka-3-8-5-azul-zulu-windows.exe (PID: 3760)
Changes default file association
- weka-3-8-5-azul-zulu-windows.exe (PID: 3760)
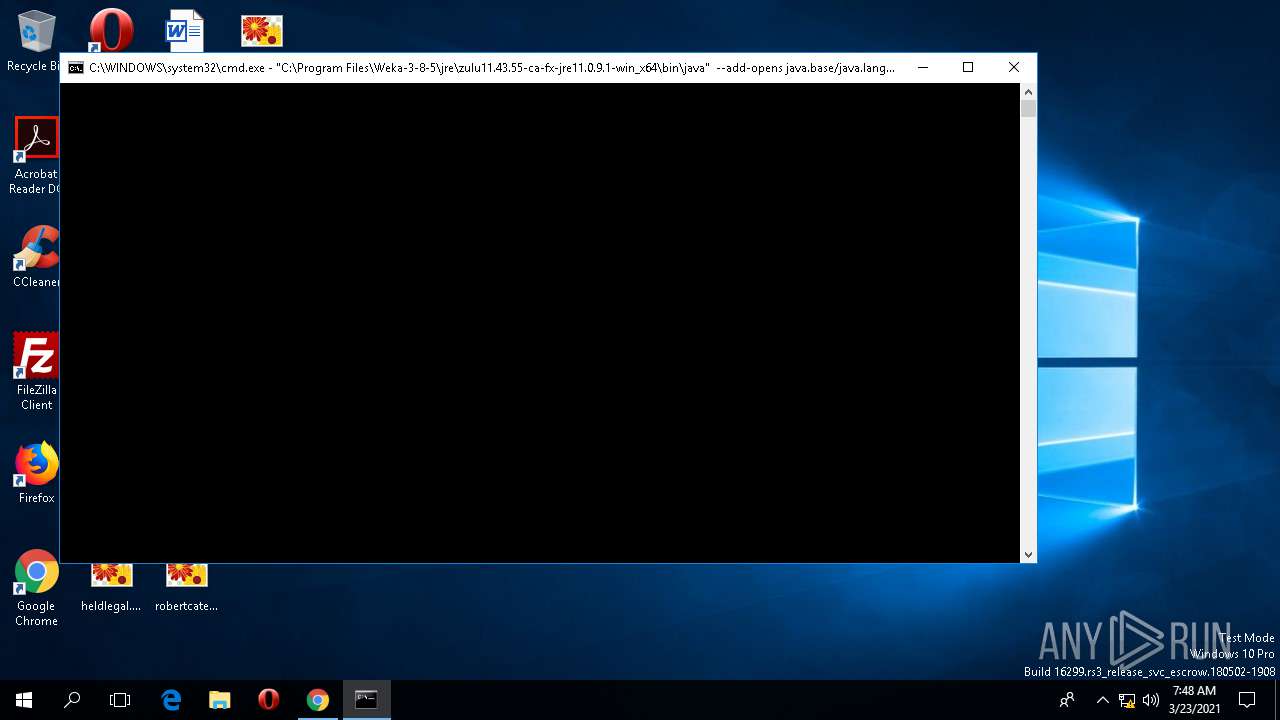
Starts CMD.EXE for commands execution
- java.exe (PID: 992)
- cmd.exe (PID: 5392)
Application launched itself
- cmd.exe (PID: 5392)
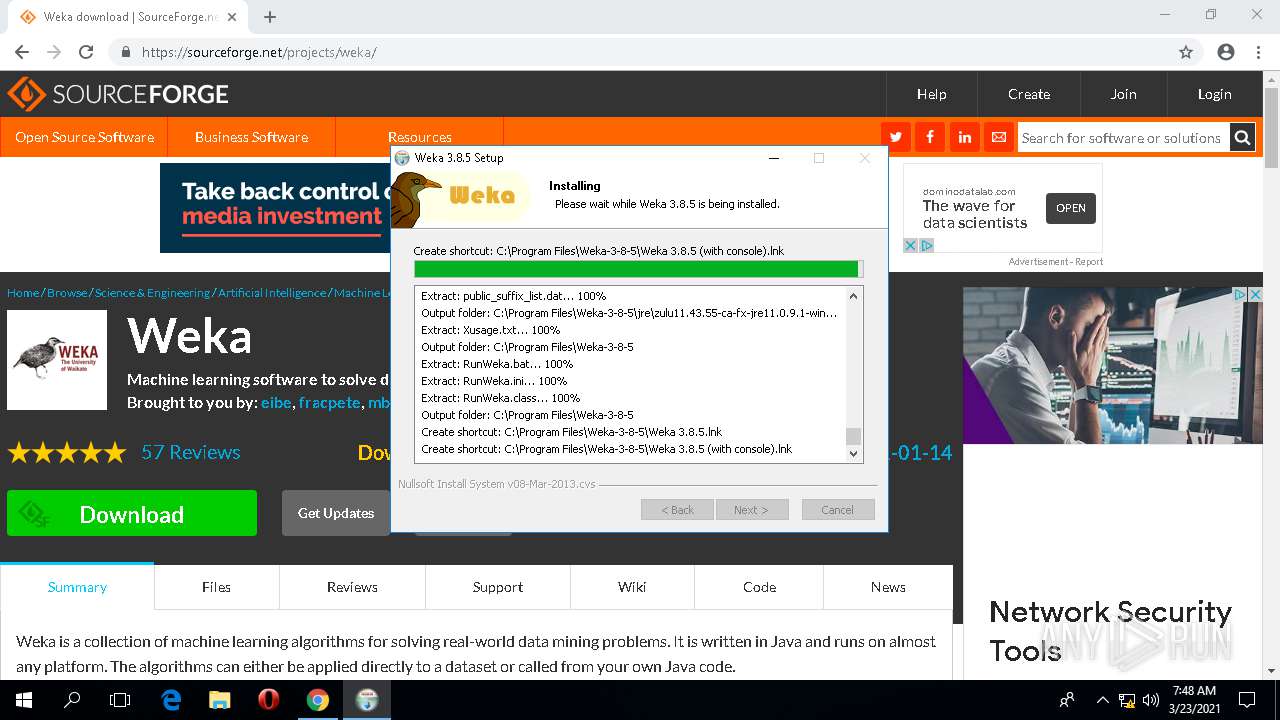
Creates a directory in Program Files
- weka-3-8-5-azul-zulu-windows.exe (PID: 3760)
Creates files in the program directory
- weka-3-8-5-azul-zulu-windows.exe (PID: 3760)
INFO
Application launched itself
- chrome.exe (PID: 4164)
Reads settings of System Certificates
- chrome.exe (PID: 4164)
Reads the software policy settings
- chrome.exe (PID: 4164)
Searches for installed software
- chrome.exe (PID: 4164)
Reads the hosts file
- chrome.exe (PID: 4164)
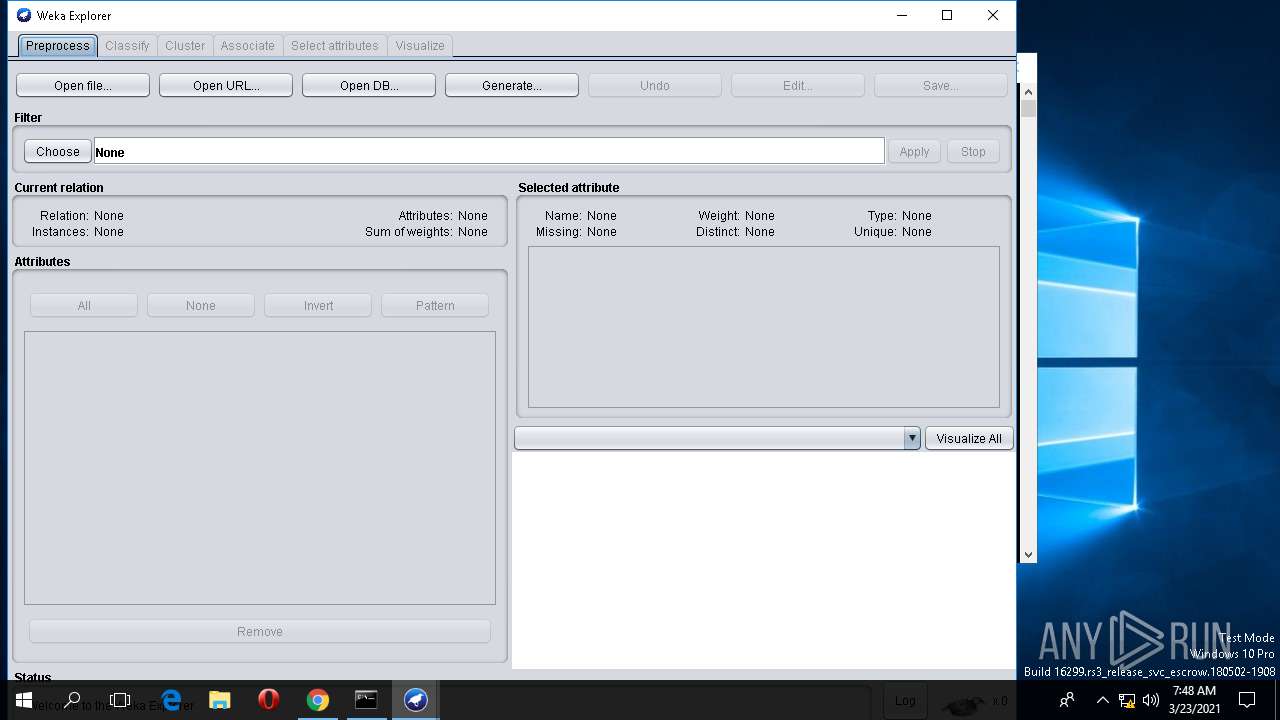
Manual execution by user
- java.exe (PID: 992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
122
Monitored processes
34
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1544,11945738543569447729,4144102885696980164,131072 --lang=en-US --no-sandbox --service-request-channel-token=4611820331829552369 --mojo-platform-channel-handle=6116 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 688 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1544,11945738543569447729,4144102885696980164,131072 --disable-gpu-compositing --service-pipe-token=16600470930117298744 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16600470930117298744 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4668 /prefetch:1 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 716 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1544,11945738543569447729,4144102885696980164,131072 --gpu-preferences=KAAAAAAAAACAAwABAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9615050314457006412 --mojo-platform-channel-handle=1560 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 804 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4780 --on-initialized-event-handle=640 --parent-handle=644 /prefetch:6 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
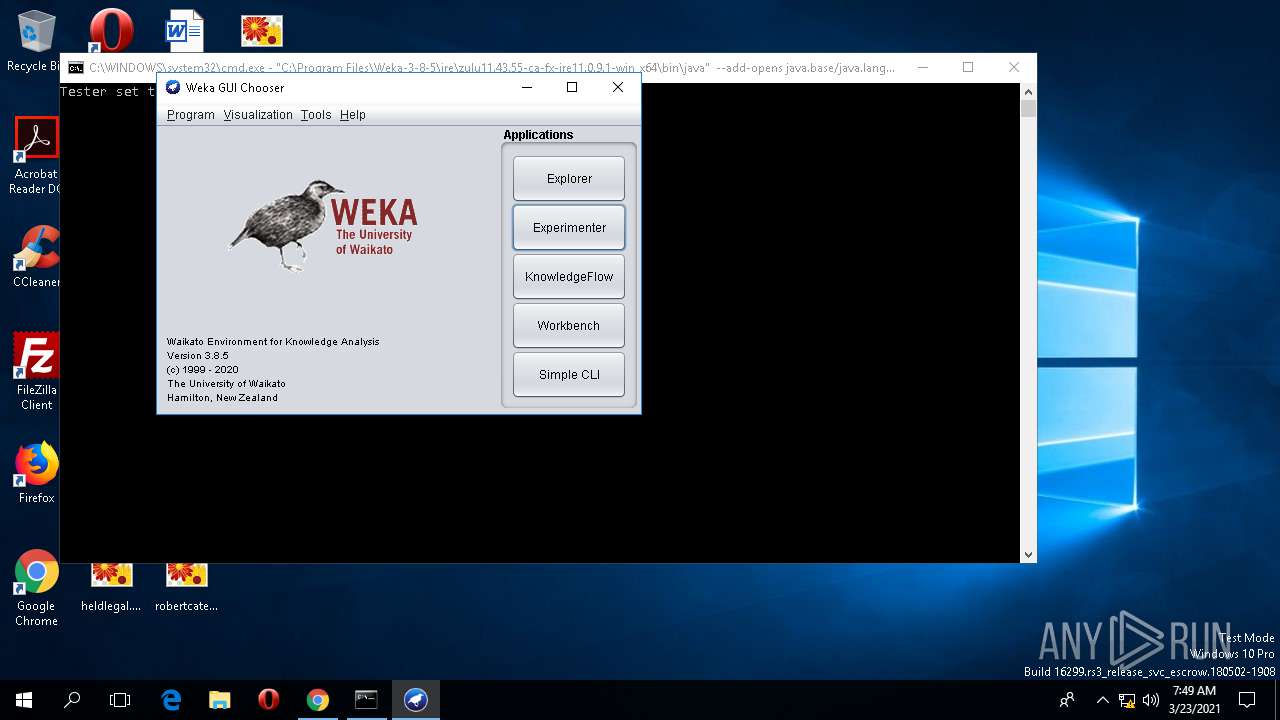
| 992 | "C:\Program Files\Weka-3-8-5\jre\zulu11.43.55-ca-fx-jre11.0.9.1-win_x64\bin\java.exe" -classpath "C:\Program Files\Weka-3-8-5" RunWeka -i "C:\Program Files\Weka-3-8-5\RunWeka.ini" -w "C:\Program Files\Weka-3-8-5\weka.jar" -c console -jre-path "C:\Program Files\Weka-3-8-5\jre\zulu11.43.55-ca-fx-jre11.0.9.1-win_x64" | C:\Program Files\Weka-3-8-5\jre\zulu11.43.55-ca-fx-jre11.0.9.1-win_x64\bin\java.exe | — | explorer.exe | |||||||||||
User: admin Company: Azul Systems Inc. Integrity Level: MEDIUM Description: Zulu Platform x64 Architecture Exit code: 0 Version: 11.43+55 Modules
| |||||||||||||||
| 1216 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1544,11945738543569447729,4144102885696980164,131072 --disable-gpu-compositing --service-pipe-token=2123964939476011587 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2123964939476011587 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5260 /prefetch:1 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1544,11945738543569447729,4144102885696980164,131072 --disable-gpu-compositing --service-pipe-token=12841878232605701779 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12841878232605701779 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3240 /prefetch:1 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
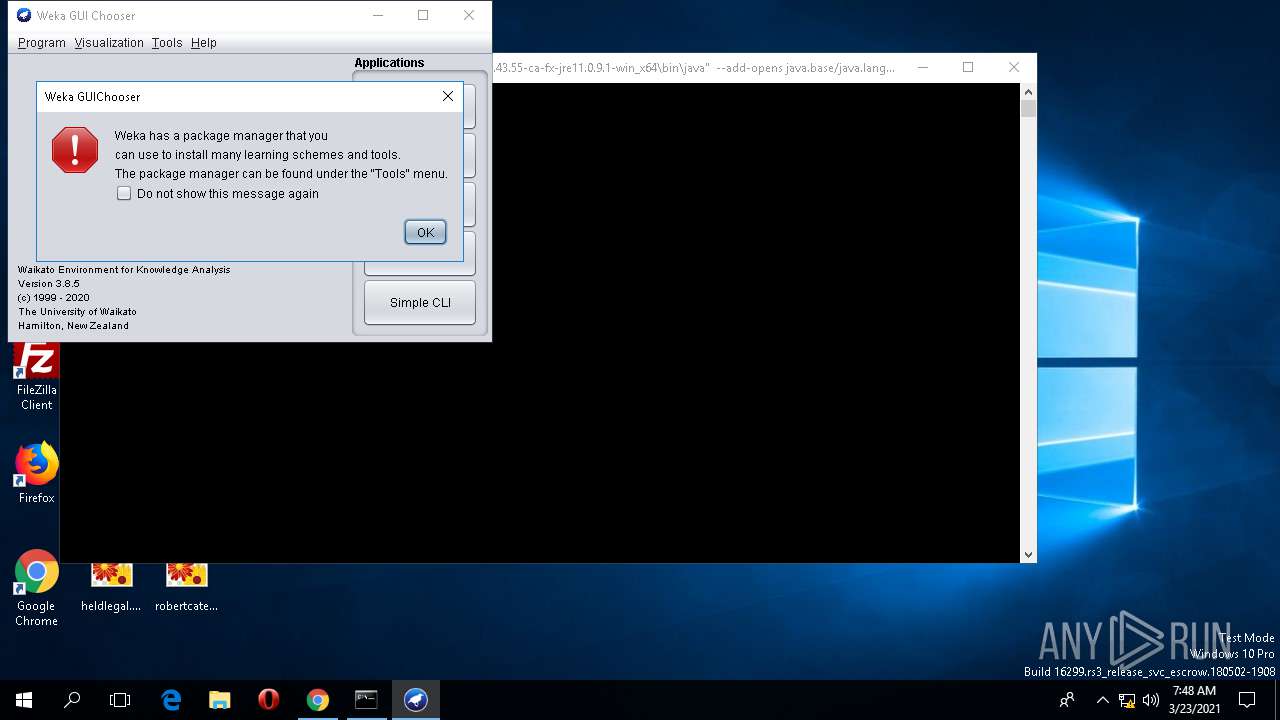
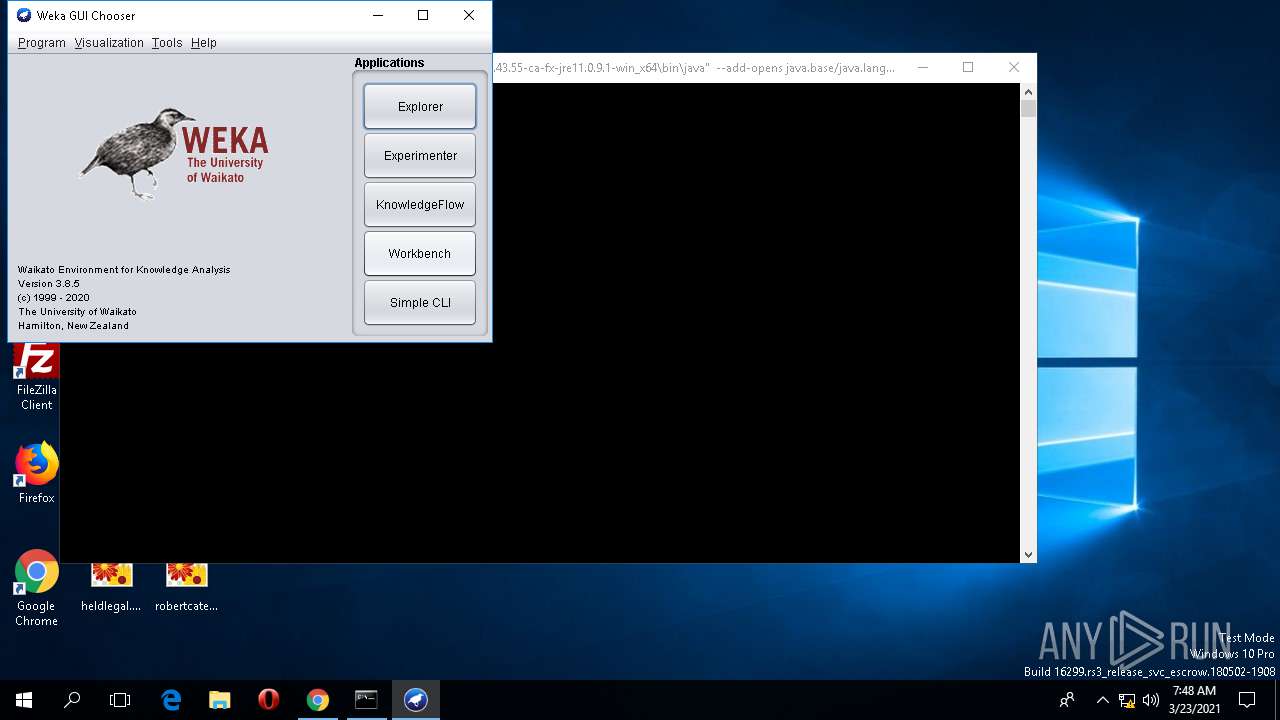
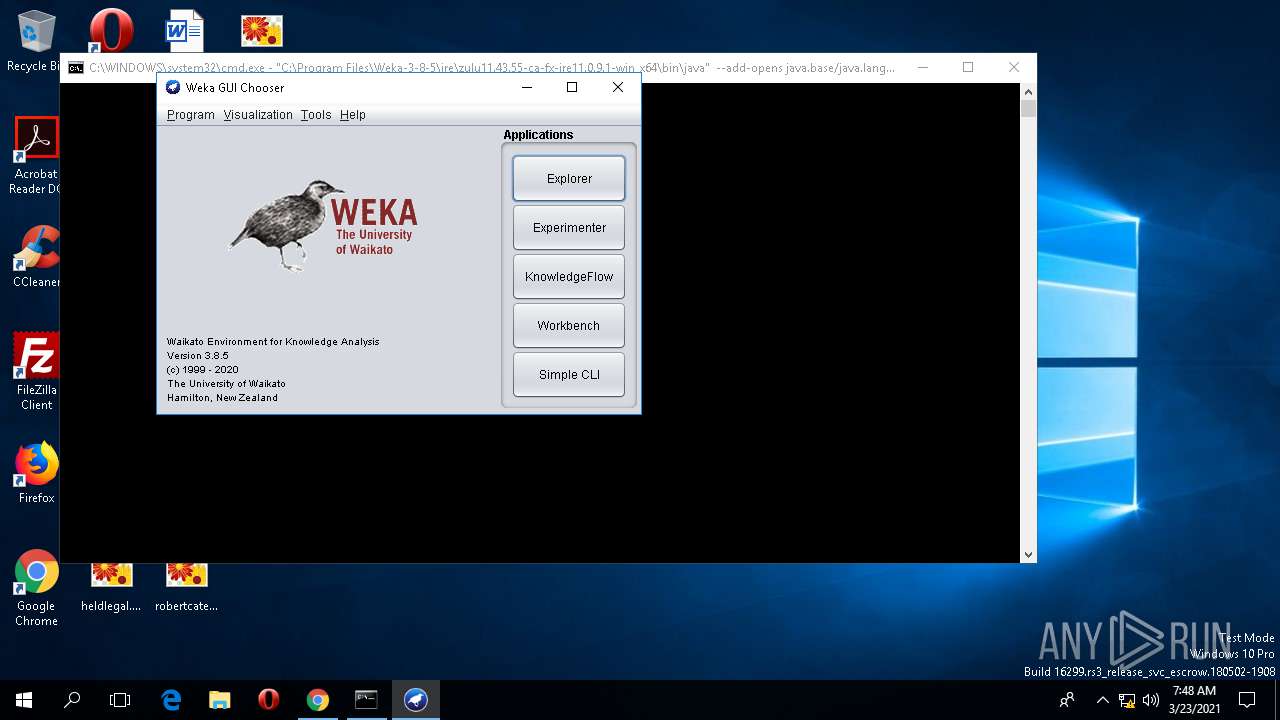
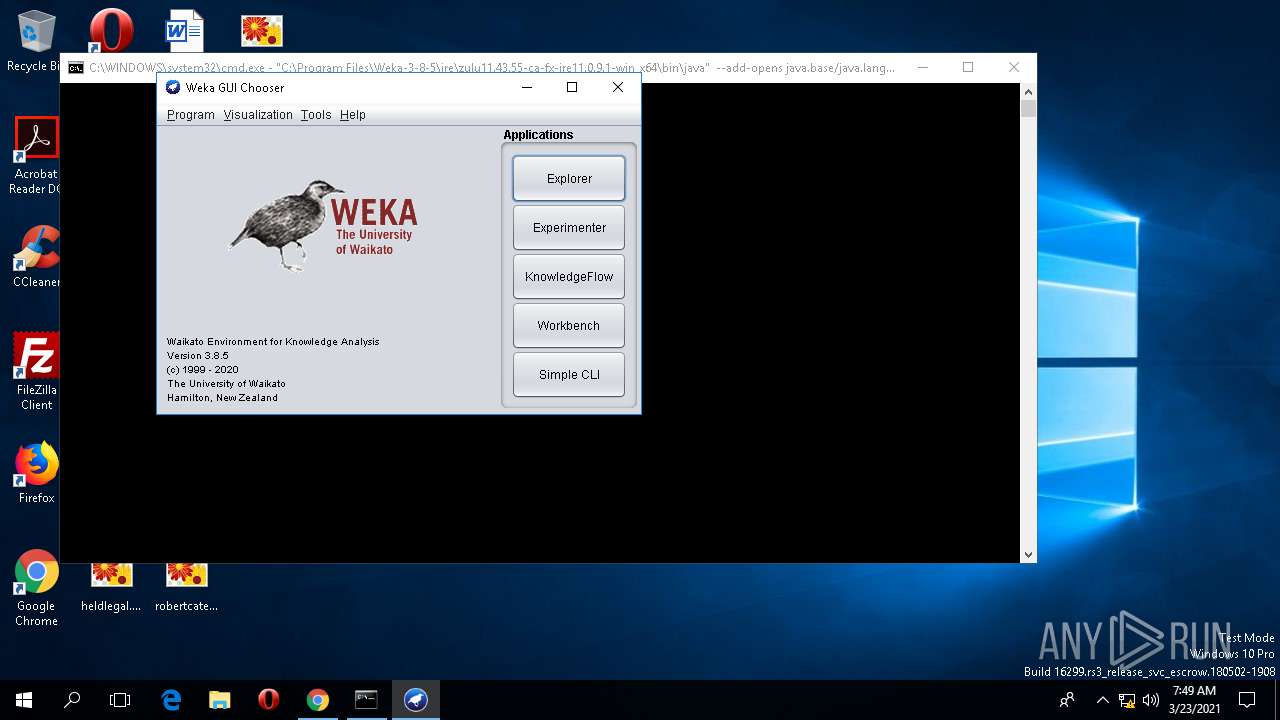
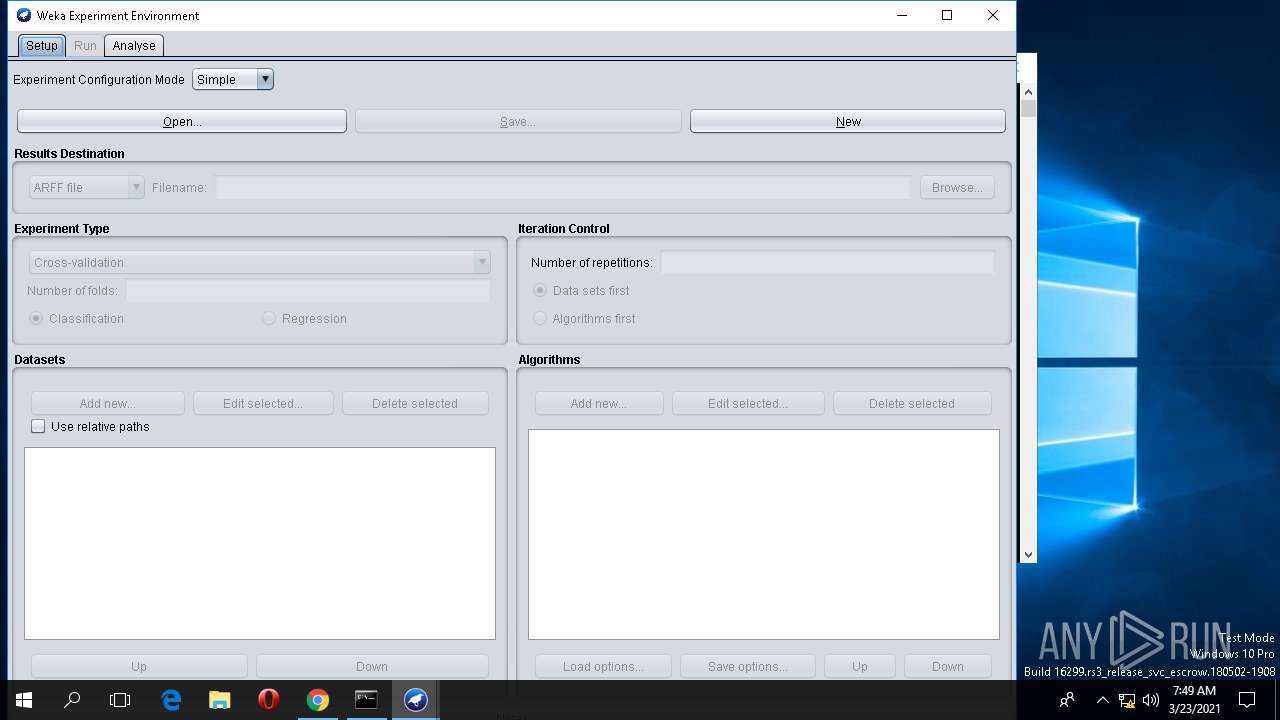
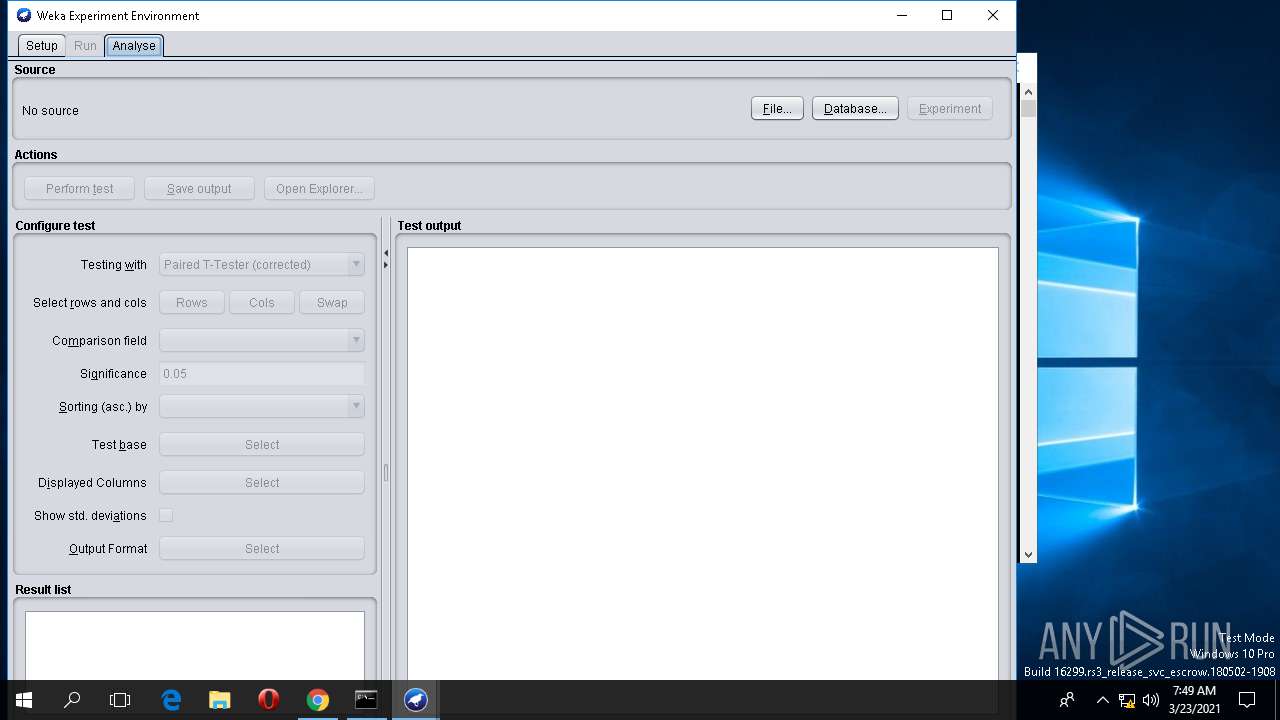
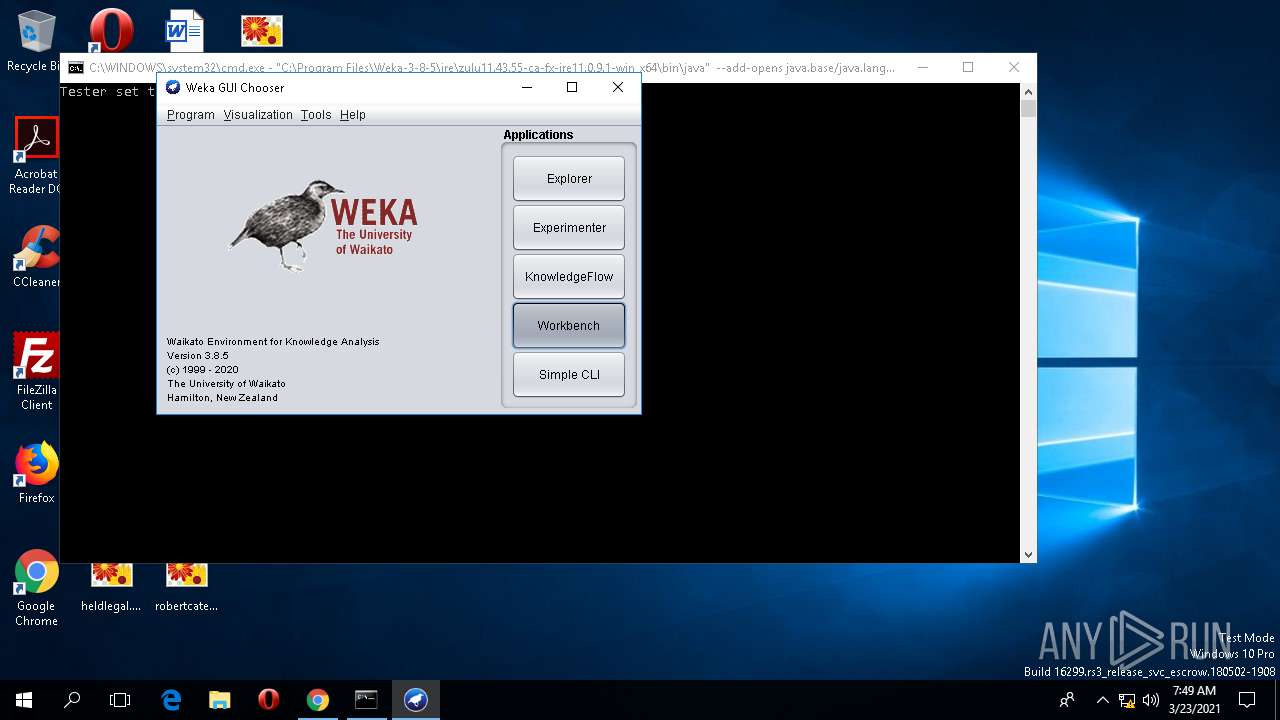
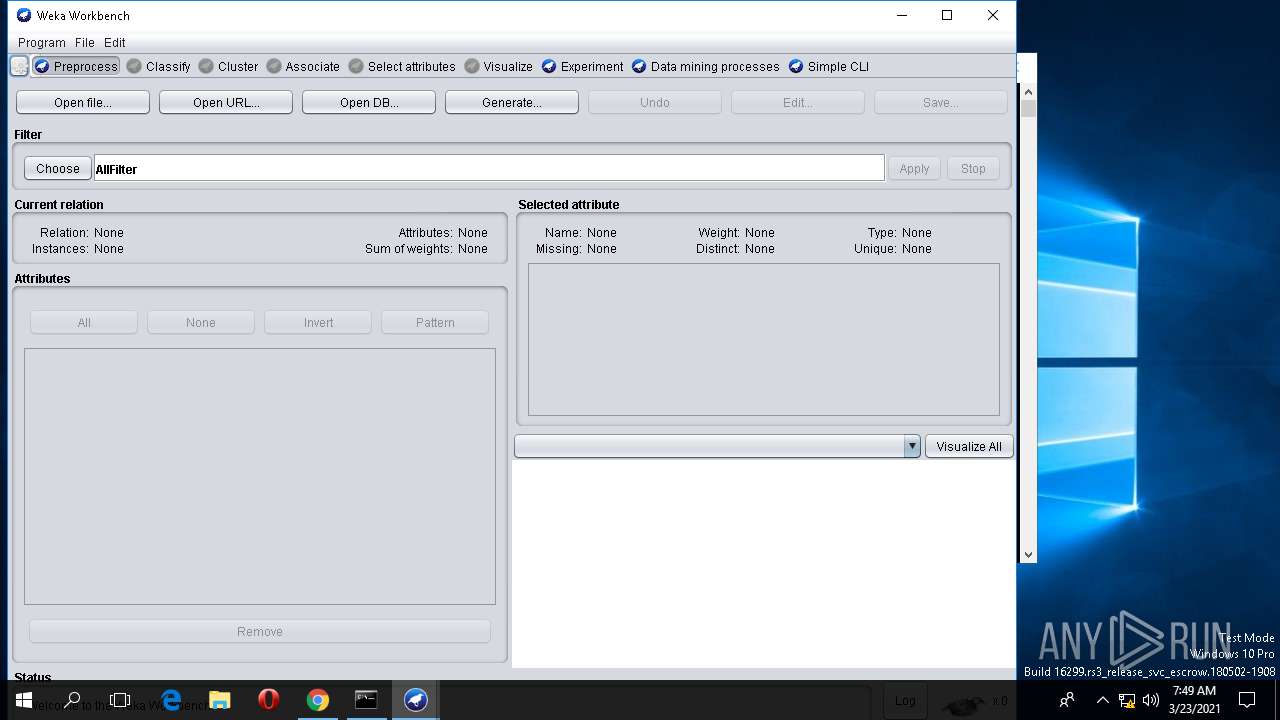
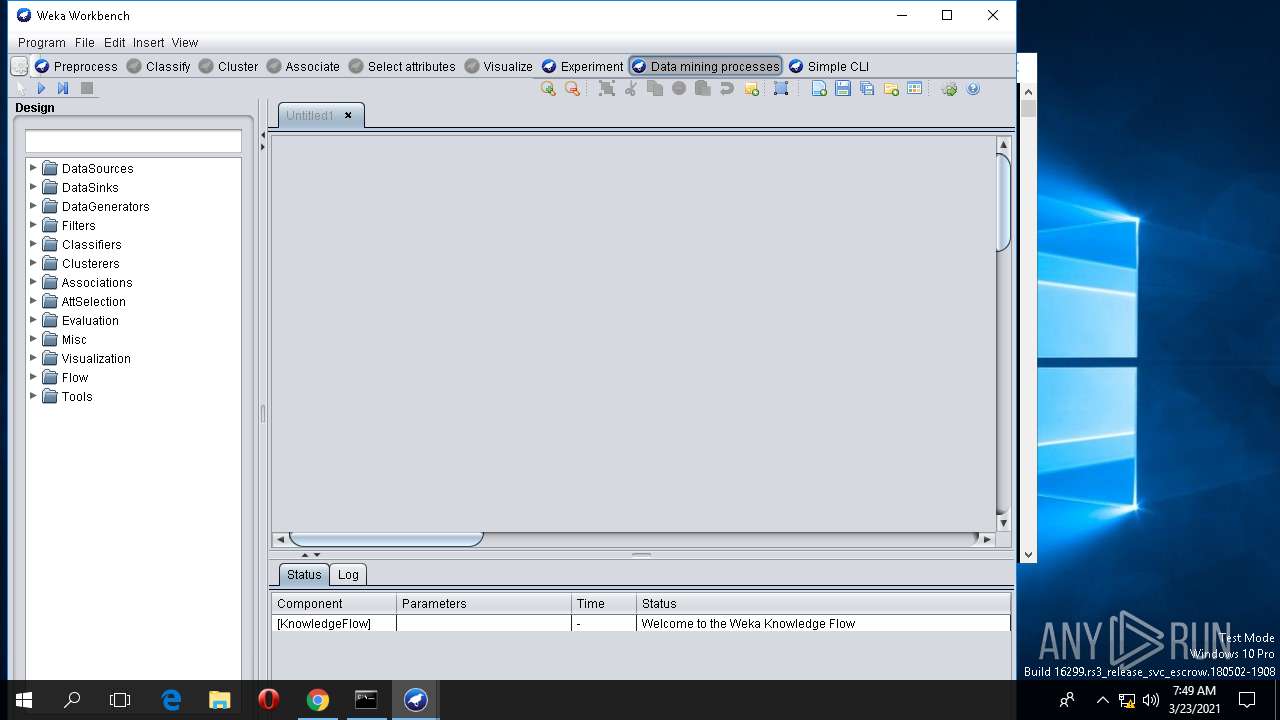
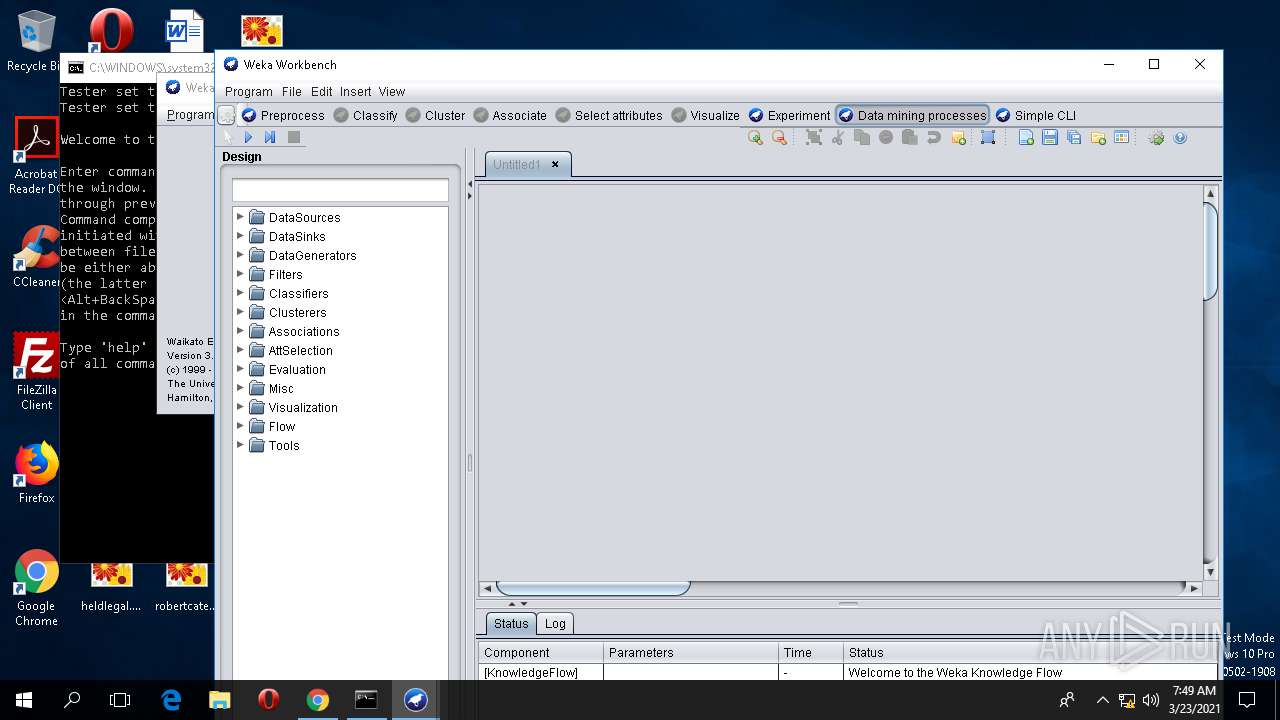
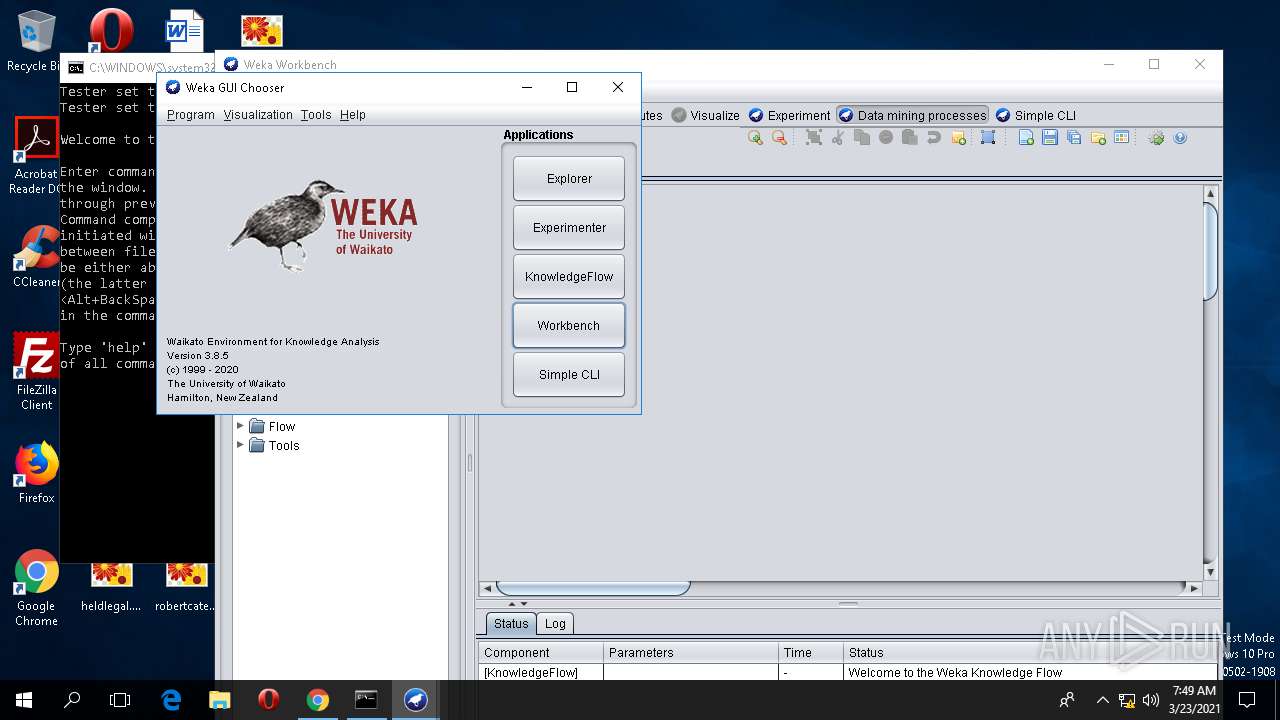
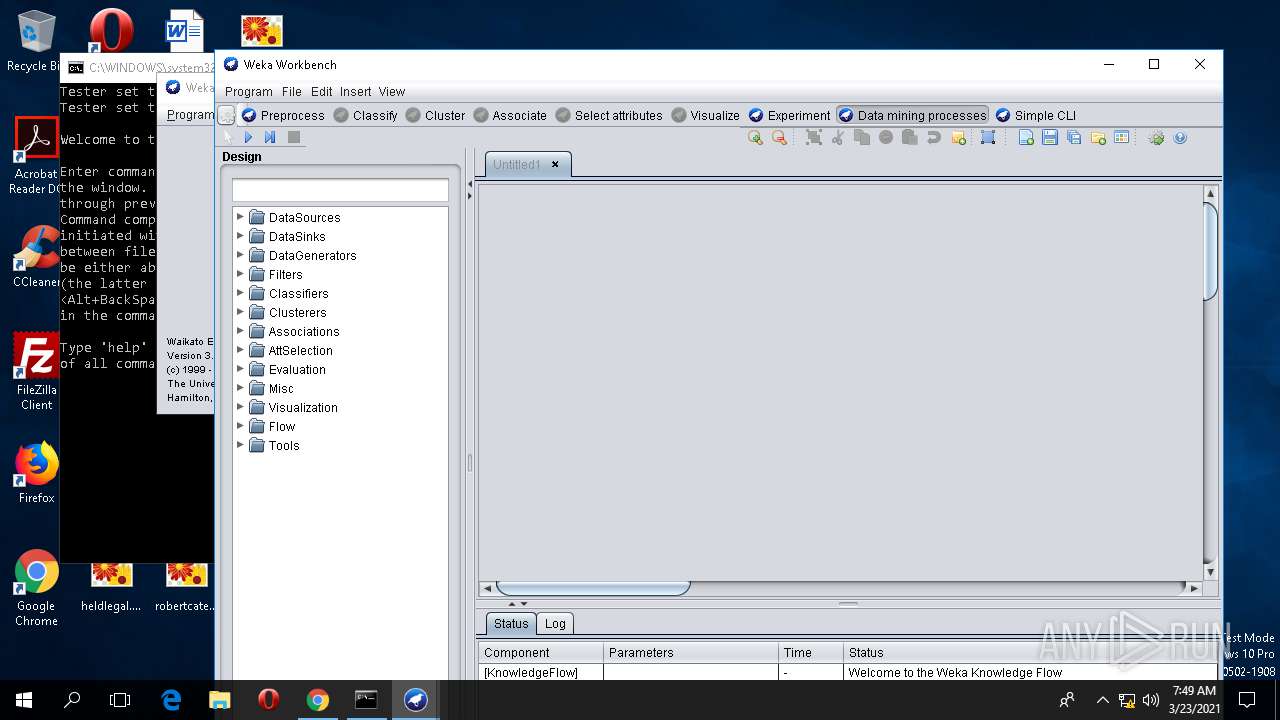
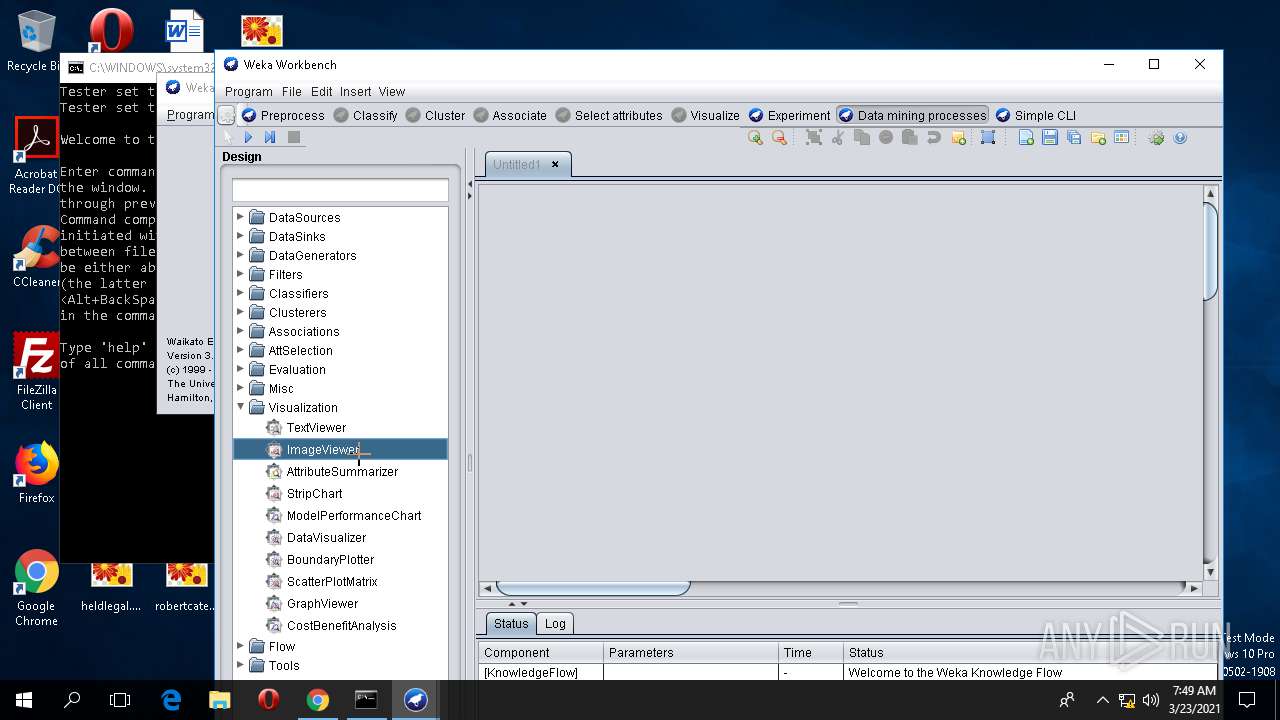
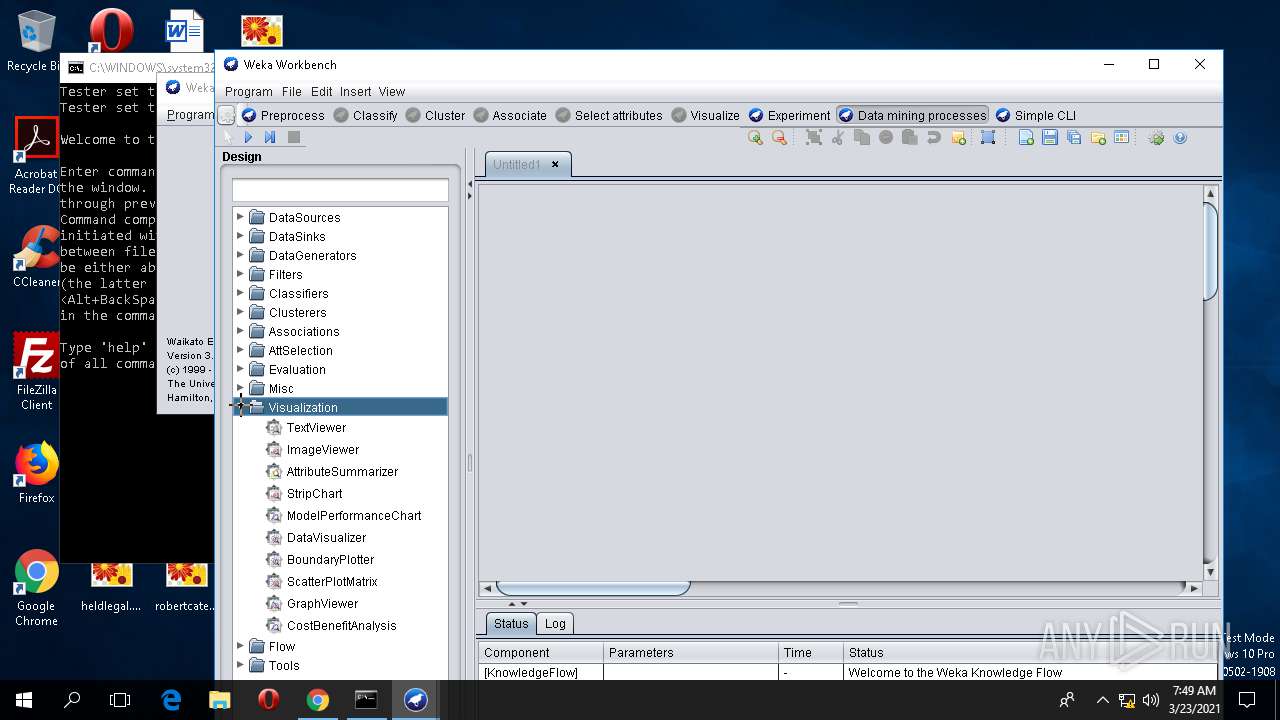
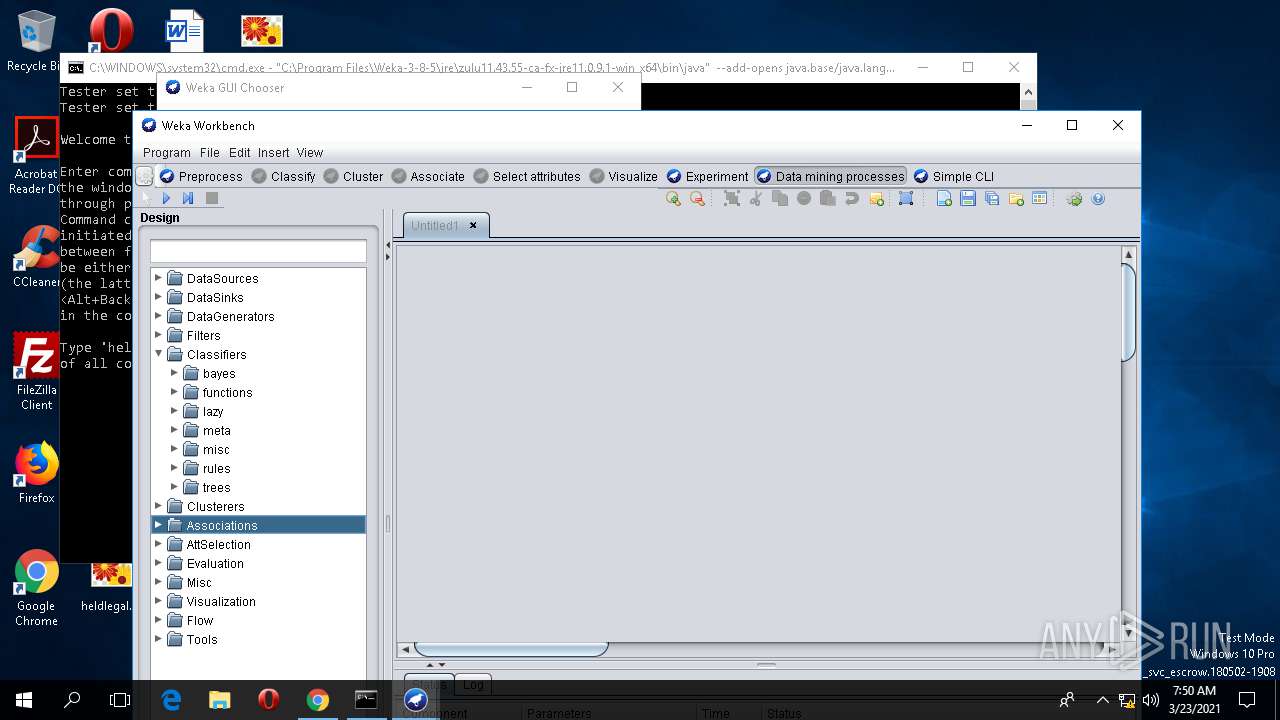
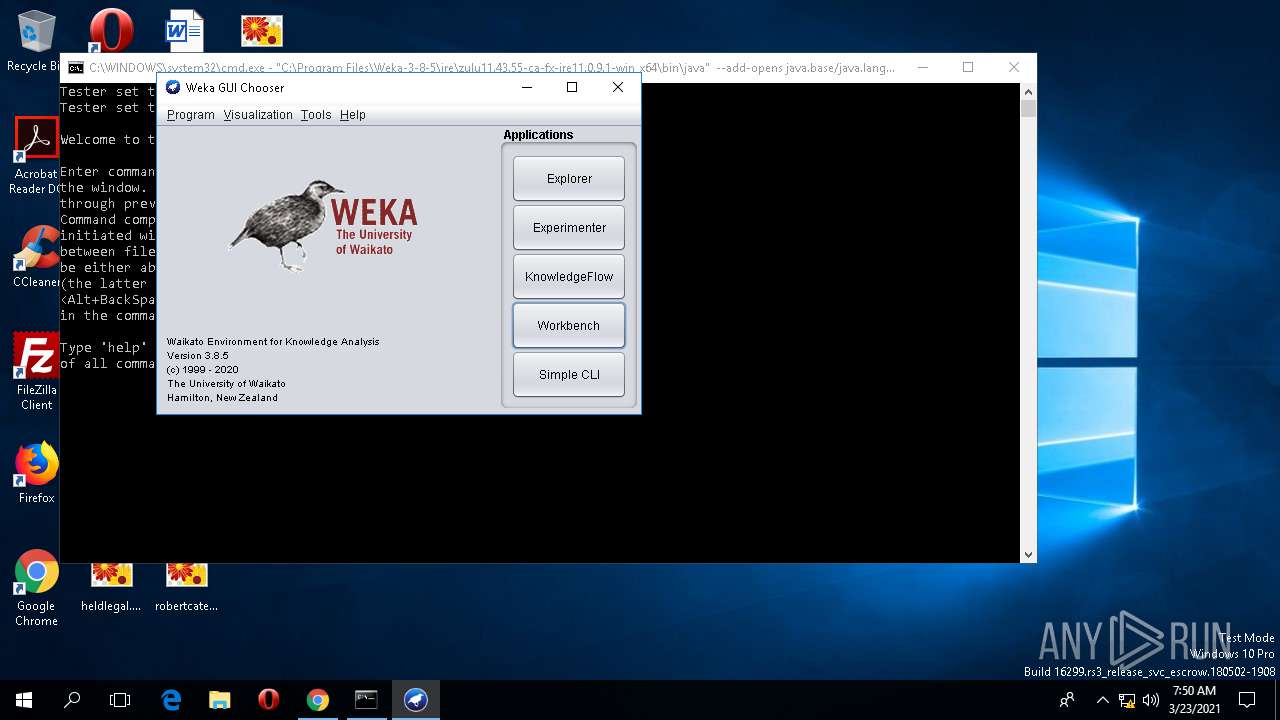
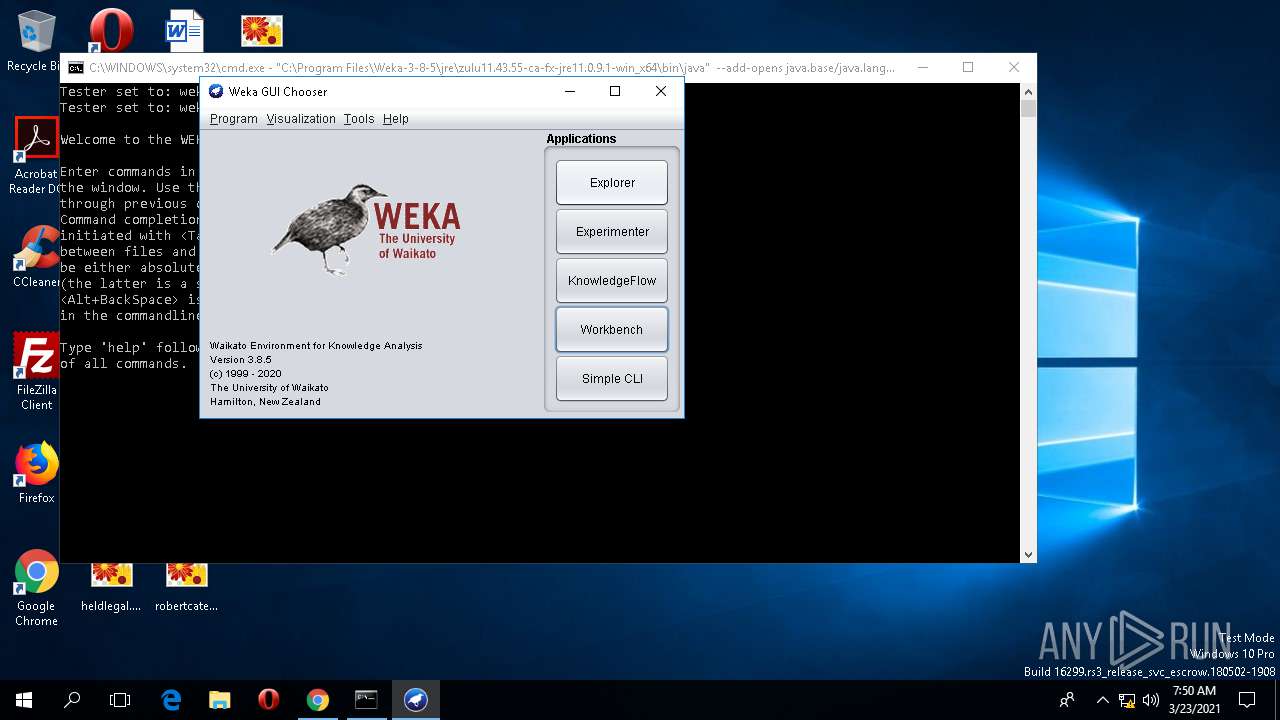
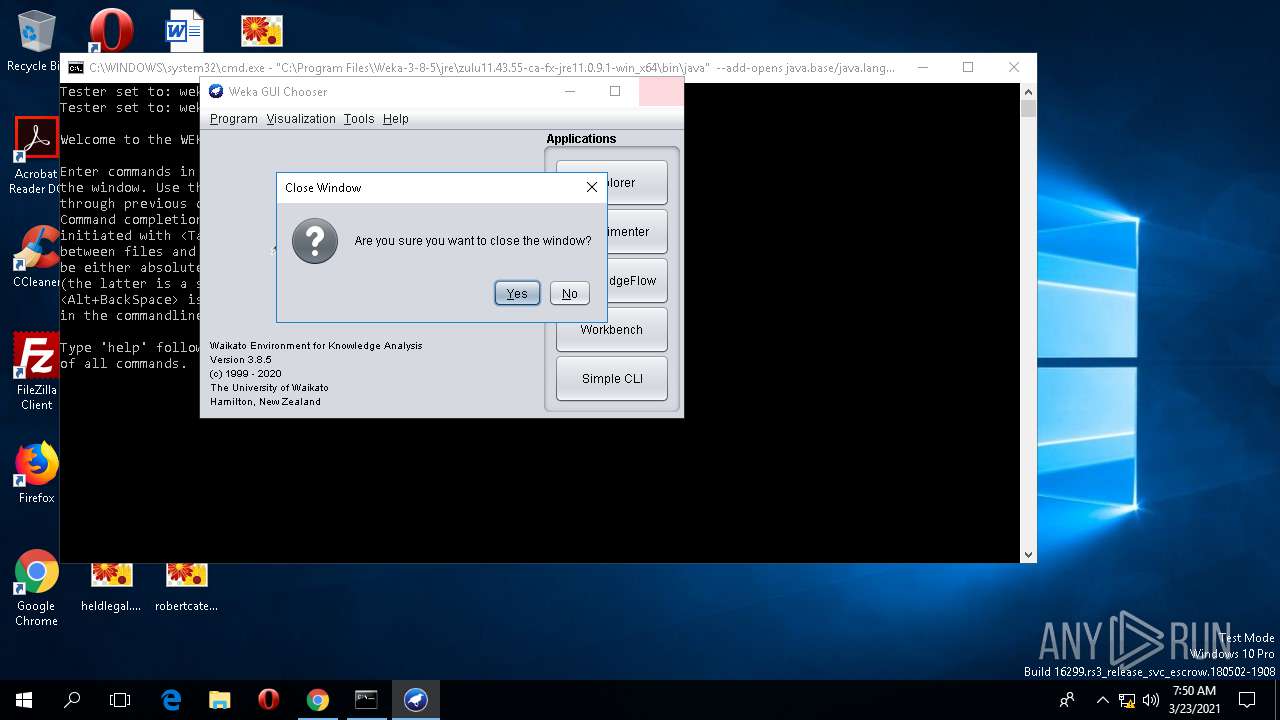
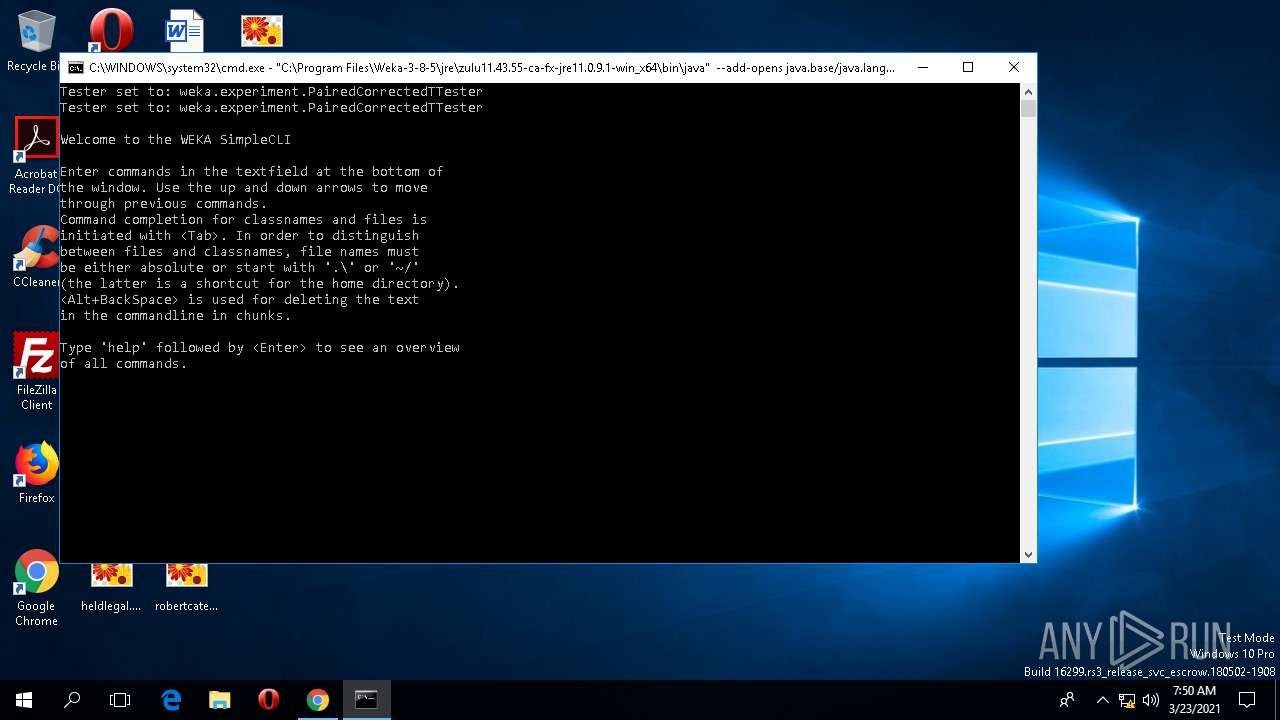
| 1844 | "C:\Program Files\Weka-3-8-5\jre\zulu11.43.55-ca-fx-jre11.0.9.1-win_x64\bin\java" --add-opens java.base/java.lang=ALL-UNNAMED -Xss20m -Dfile.encoding=Cp1252 -Djava.net.useSystemProxies=true -classpath "C:/Program Files/Weka-3-8-5/weka.jar;" weka.gui.GUIChooser | C:\Program Files\Weka-3-8-5\jre\zulu11.43.55-ca-fx-jre11.0.9.1-win_x64\bin\java.exe | — | cmd.exe | |||||||||||
User: admin Company: Azul Systems Inc. Integrity Level: MEDIUM Description: Zulu Platform x64 Architecture Exit code: 0 Version: 11.43+55 Modules
| |||||||||||||||
| 2840 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1544,11945738543569447729,4144102885696980164,131072 --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwABAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1198395234853146112 --mojo-platform-channel-handle=5096 /prefetch:2 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 3488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | java.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 007
Read events
4 774
Write events
230
Delete events
3
Modification events
| (PID) Process: | (4164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 4164-13260959134699793 |
Value: 259 | |||
| (PID) Process: | (4164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (4164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 4000-13240569530726669 |
Value: 0 | |||
| (PID) Process: | (4164) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
117
Suspicious files
200
Text files
2 478
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a9e092b2-be82-4c91-82f9-910d66f9a21d.tmp | — | |
MD5:— | SHA256:— | |||
| 4164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000012.dbtmp | — | |
MD5:— | SHA256:— | |||
| 4164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 4164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 4164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\984166fd-a70a-48a8-9750-da7f822ec2bc.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
125
DNS requests
72
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4164 | chrome.exe | 216.105.38.13:443 | prdownloads.sourceforge.net | American Internet Services, LLC. | US | malicious |
4164 | chrome.exe | 104.18.14.218:443 | a.fsdn.com | Cloudflare Inc | US | unknown |
4164 | chrome.exe | 142.250.185.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4164 | chrome.exe | 142.250.185.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
4164 | chrome.exe | 142.250.186.100:443 | www.google.com | Google Inc. | US | whitelisted |
4164 | chrome.exe | 87.230.98.74:443 | consentmanager.mgr.consensu.org | Host Europe GmbH | DE | unknown |
4164 | chrome.exe | 195.181.175.54:443 | cdn.consentmanager.mgr.consensu.org | Datacamp Limited | DE | suspicious |
4164 | chrome.exe | 142.250.186.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
4164 | chrome.exe | 104.18.31.83:443 | c.sf-syn.com | Cloudflare Inc | US | shared |
4164 | chrome.exe | 192.0.77.2:443 | i2.wp.com | Automattic, Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
prdownloads.sourceforge.net |
| suspicious |
sourceforge.net |
| whitelisted |
a.fsdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.consentmanager.mgr.consensu.org |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
consentmanager.mgr.consensu.org |
| whitelisted |
www.google.com |
| malicious |
c.sf-syn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |