| download: | 1.ps1 |
| Full analysis: | https://app.any.run/tasks/5690c11d-08b1-41d4-9adb-d1e7a07a124b |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 08:35:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 251693A1F083025B4BD813C41007F398 |
| SHA1: | 4F18A0BEA47F5269CD4BE59A80FDB5C32F585EE7 |
| SHA256: | 0CA956121157DC8E444488BF554D35F555558BA49C2D2DAC4914F3F9D8CB22E7 |
| SSDEEP: | 48:UxcOSuxVUoXWVihpg4mzX1CuiKs3Q7d/ae2niX5O4nKn2As7G4+kCN78:U4uGHiKsg7d/ae2niX5O4Kn2P7d7 |
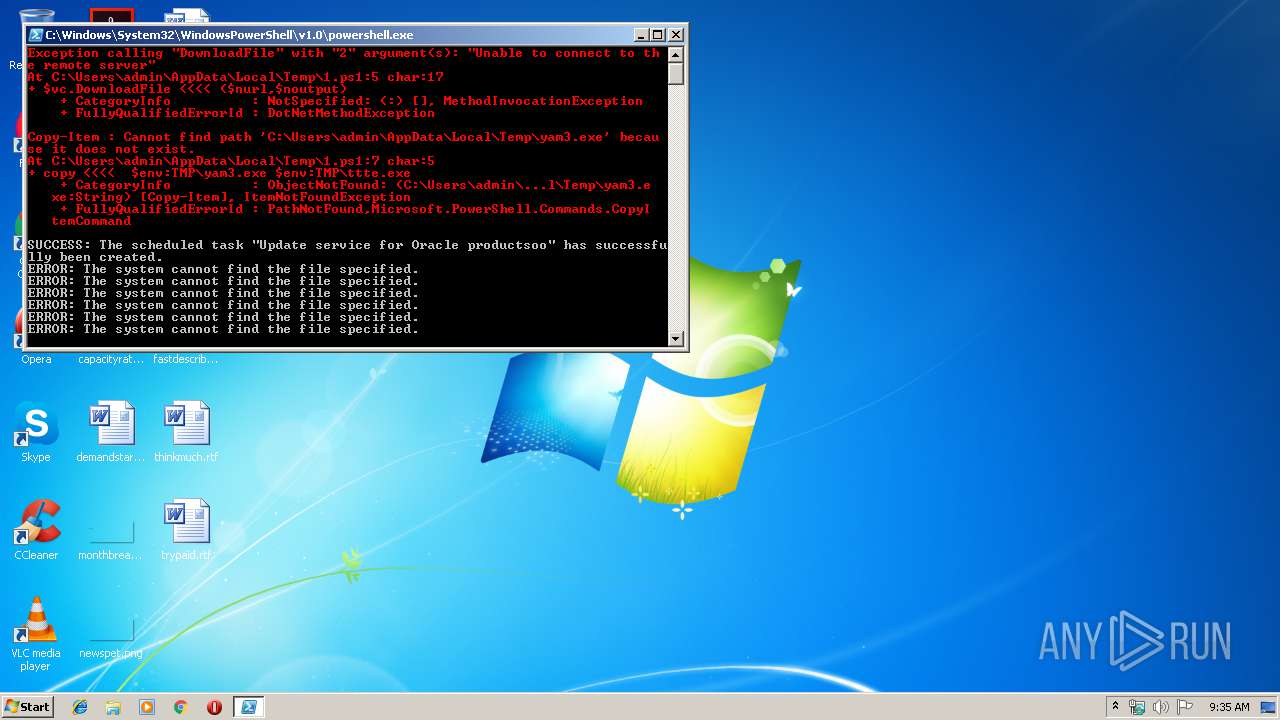
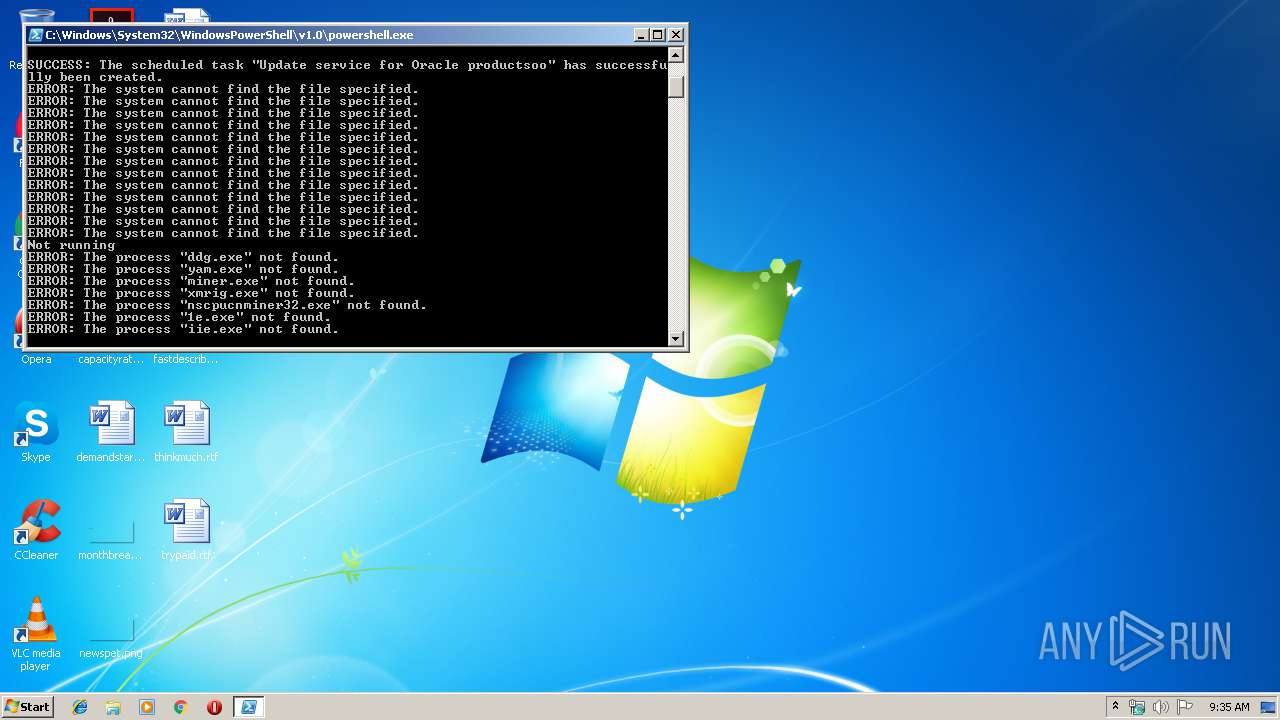
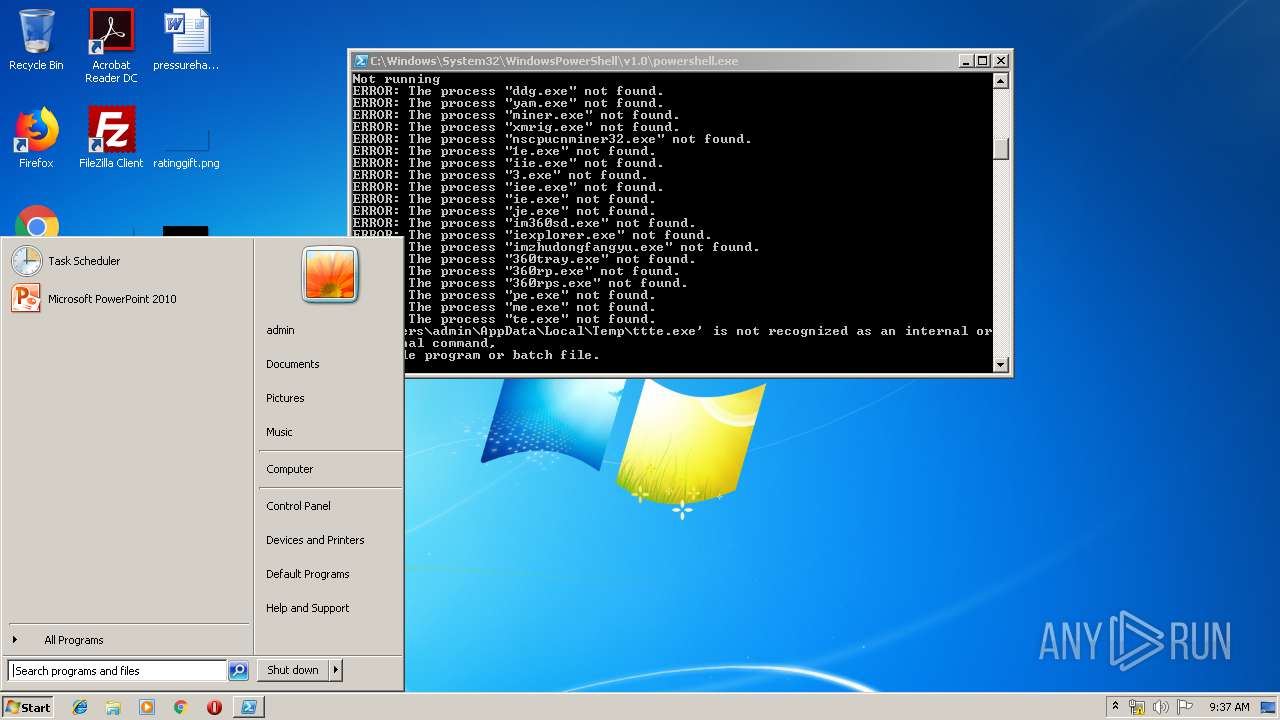
MALICIOUS
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2860)
- schtasks.exe (PID: 720)
- schtasks.exe (PID: 4048)
- schtasks.exe (PID: 2704)
- schtasks.exe (PID: 3284)
- schtasks.exe (PID: 3872)
- schtasks.exe (PID: 2524)
- schtasks.exe (PID: 3708)
- schtasks.exe (PID: 3132)
- schtasks.exe (PID: 2392)
- schtasks.exe (PID: 2980)
- schtasks.exe (PID: 756)
- schtasks.exe (PID: 3588)
- schtasks.exe (PID: 3456)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 2952)
SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2952)
Creates files in the user directory
- powershell.exe (PID: 2952)
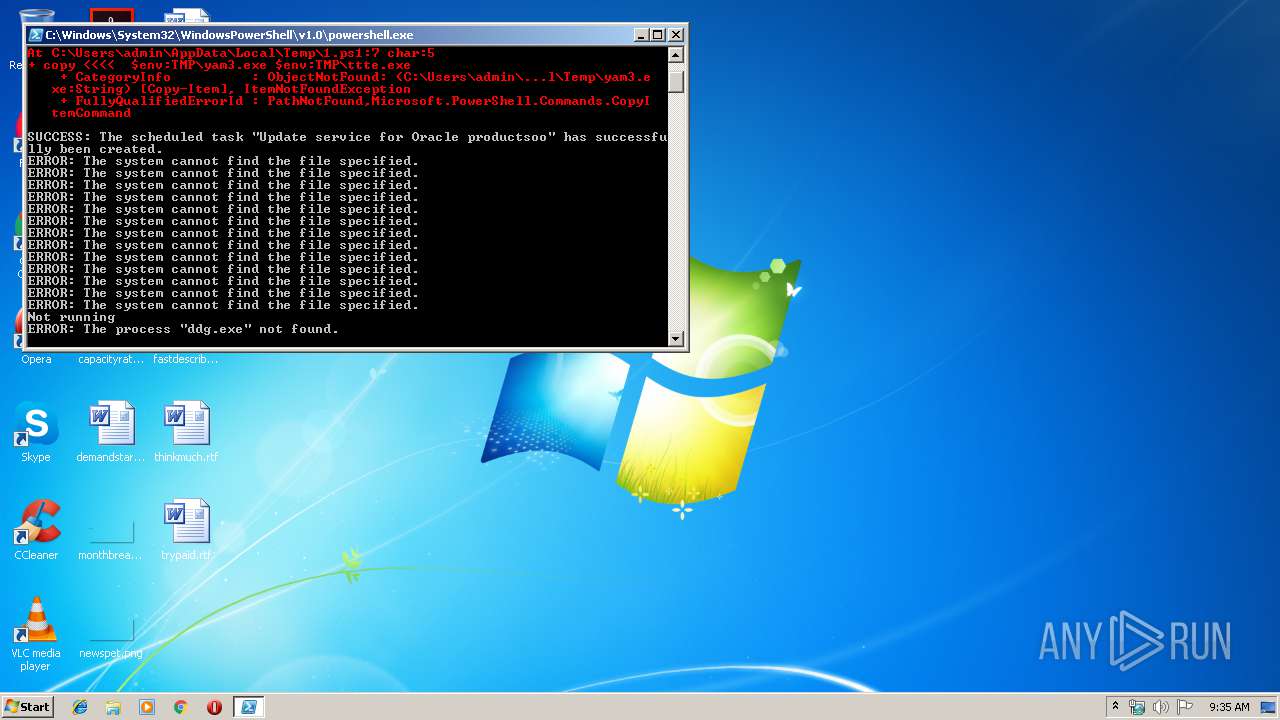
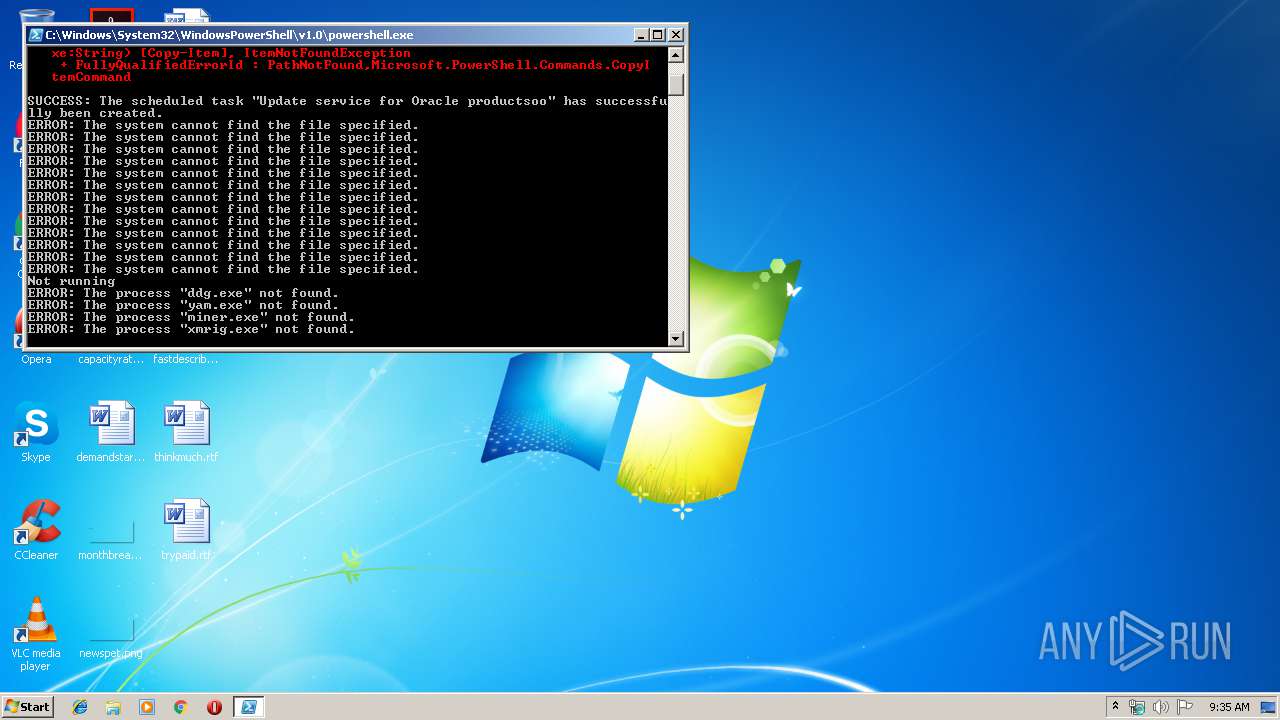
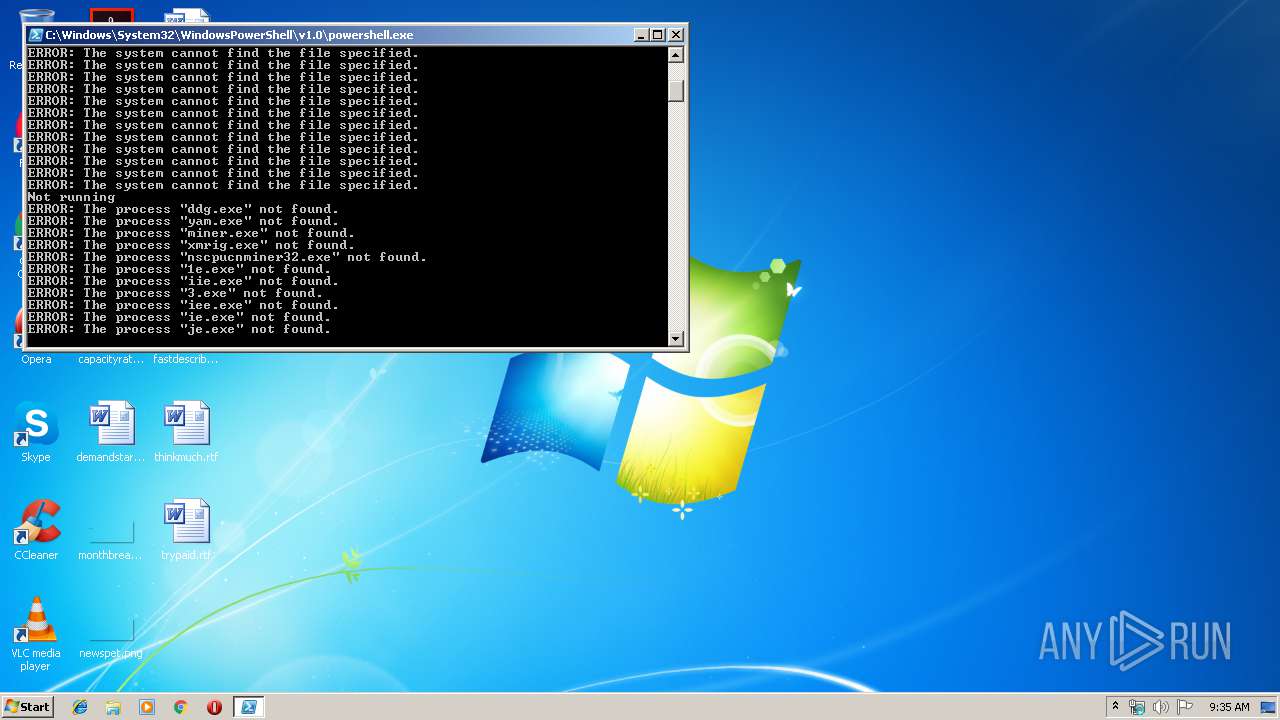
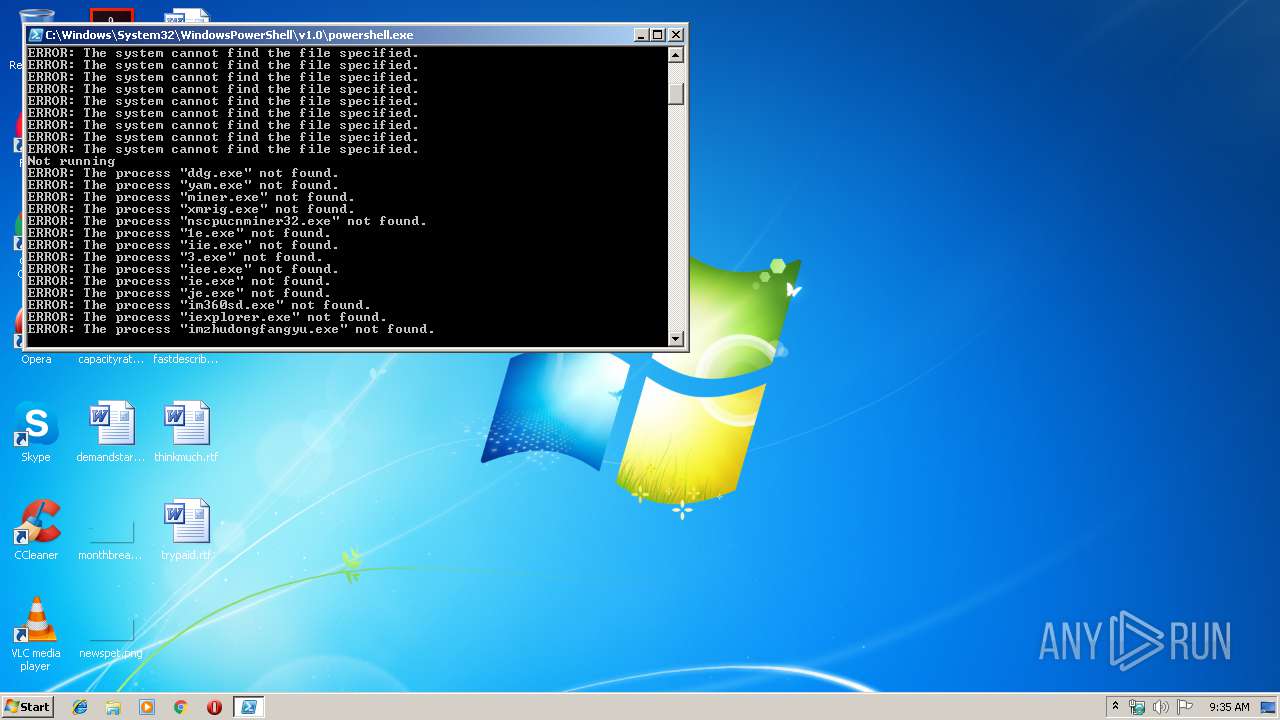
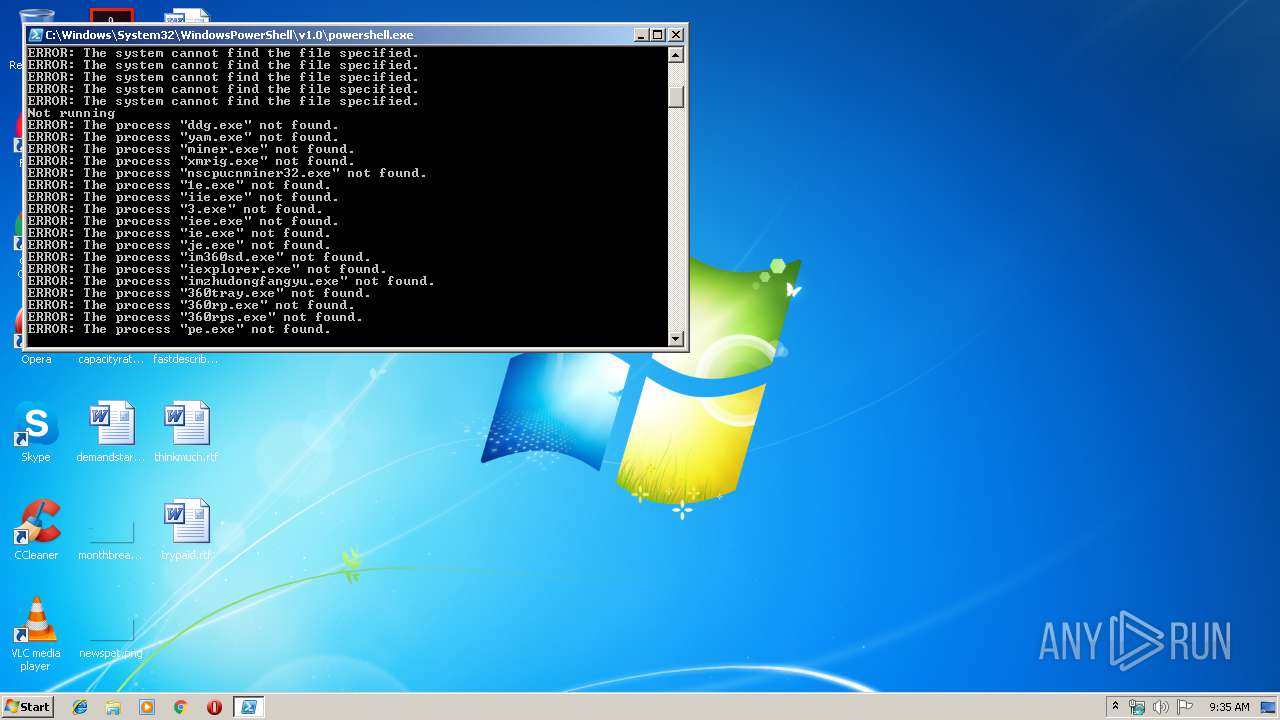
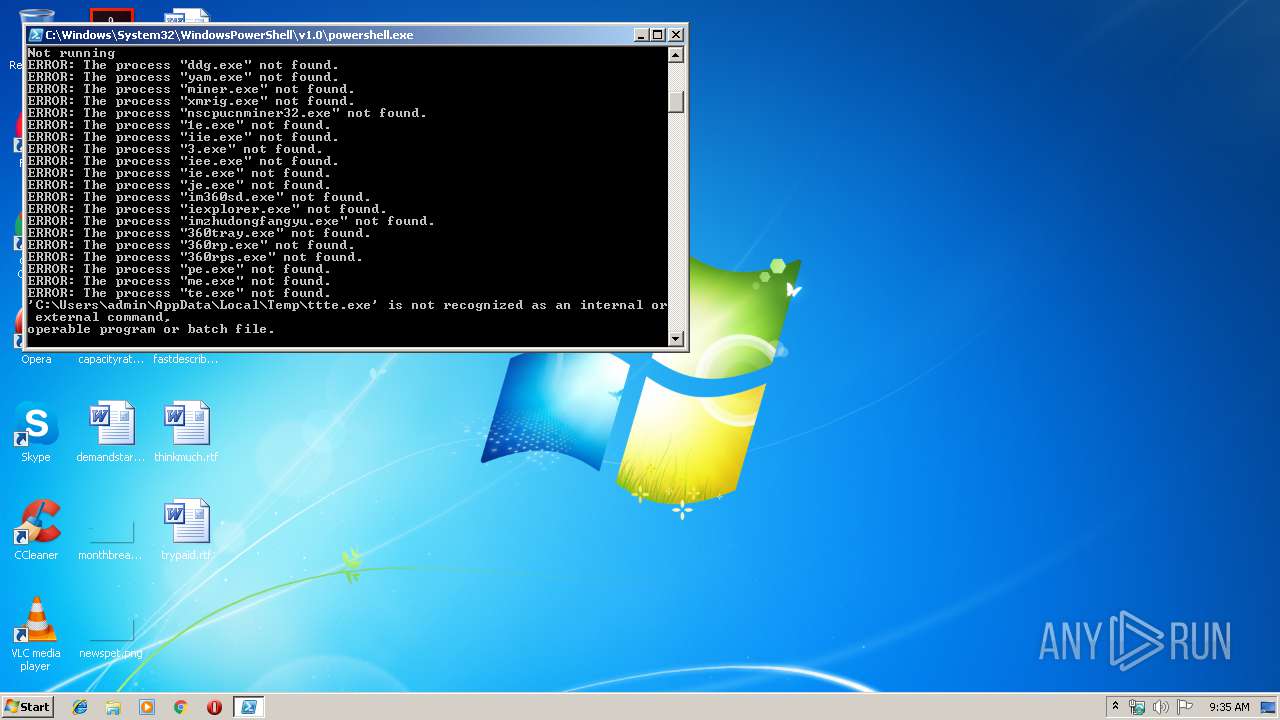
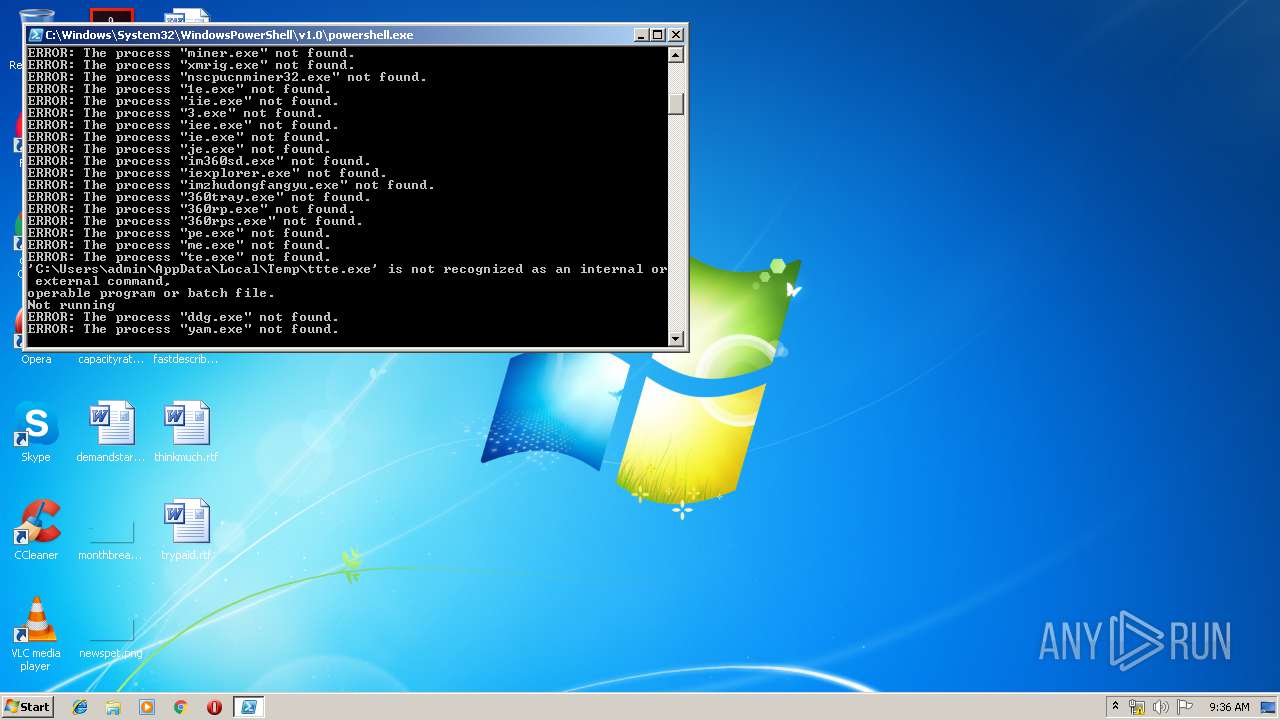
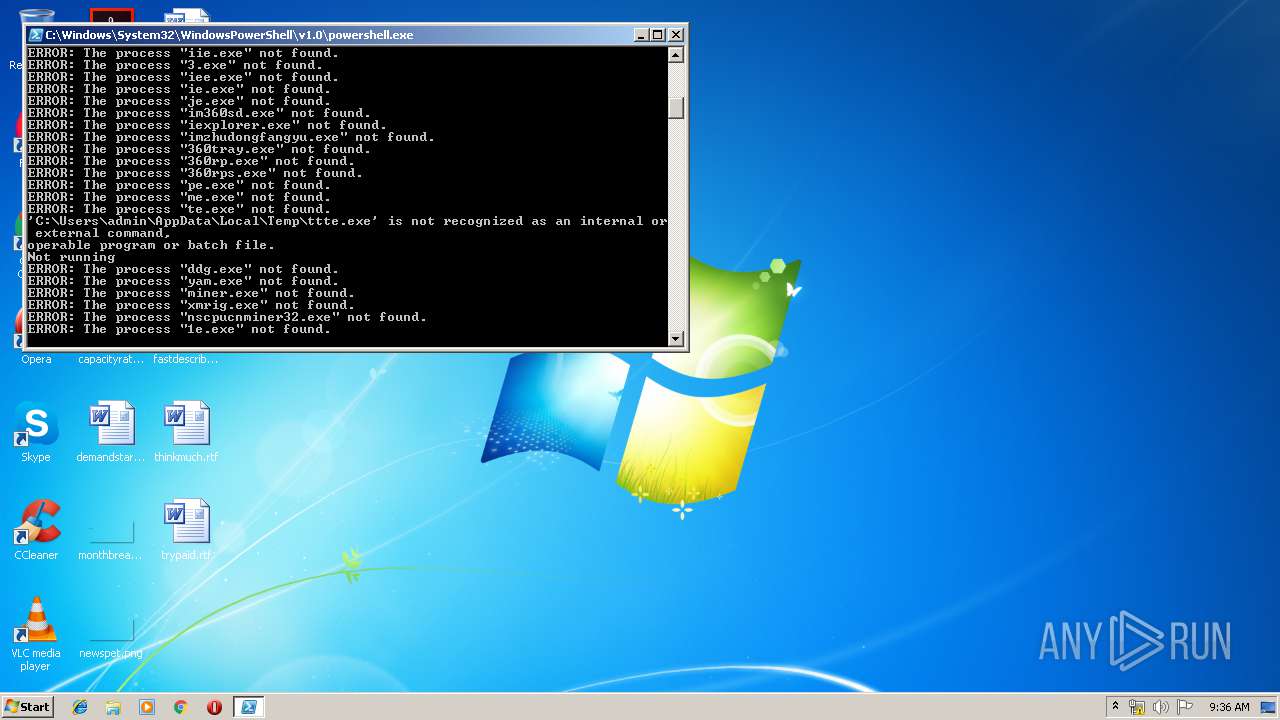
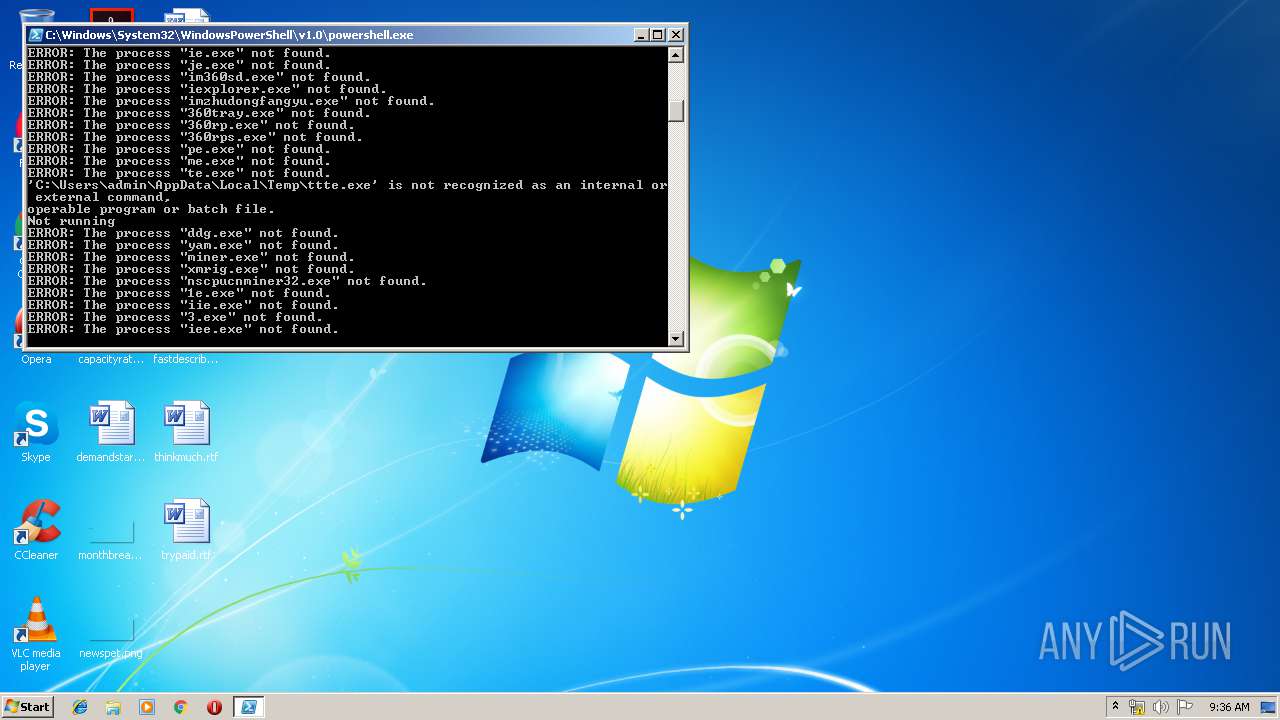
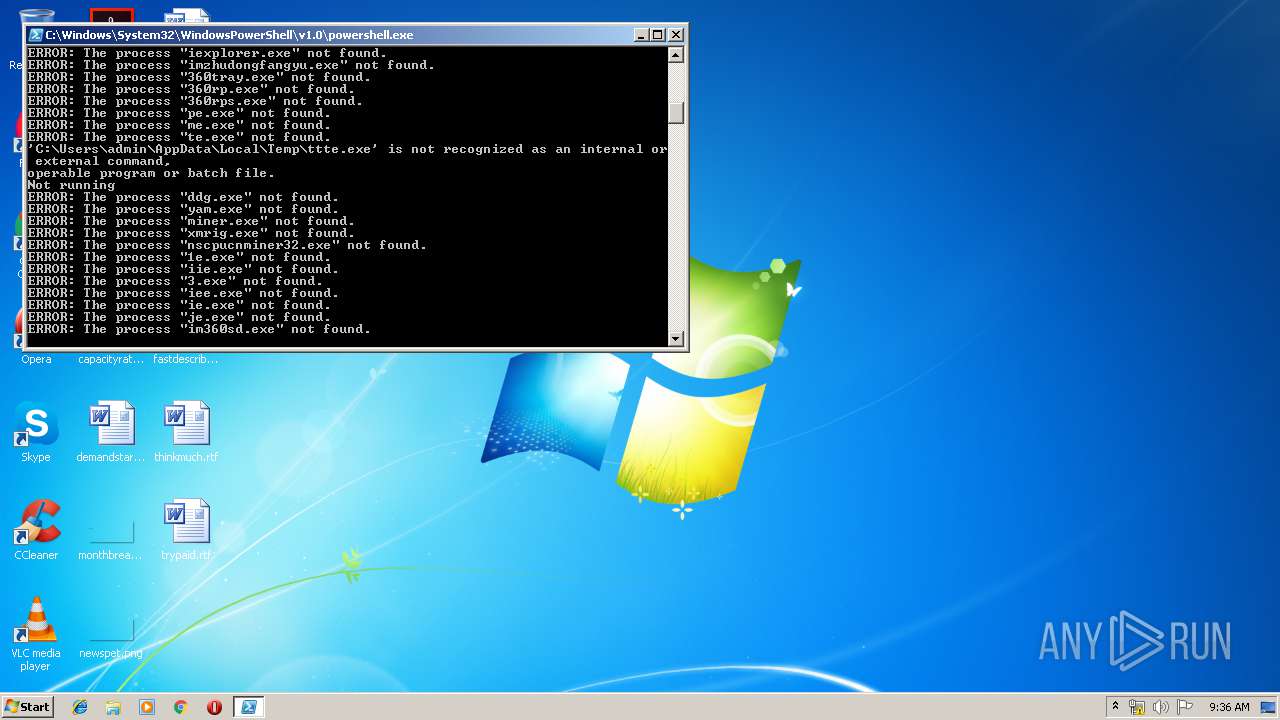
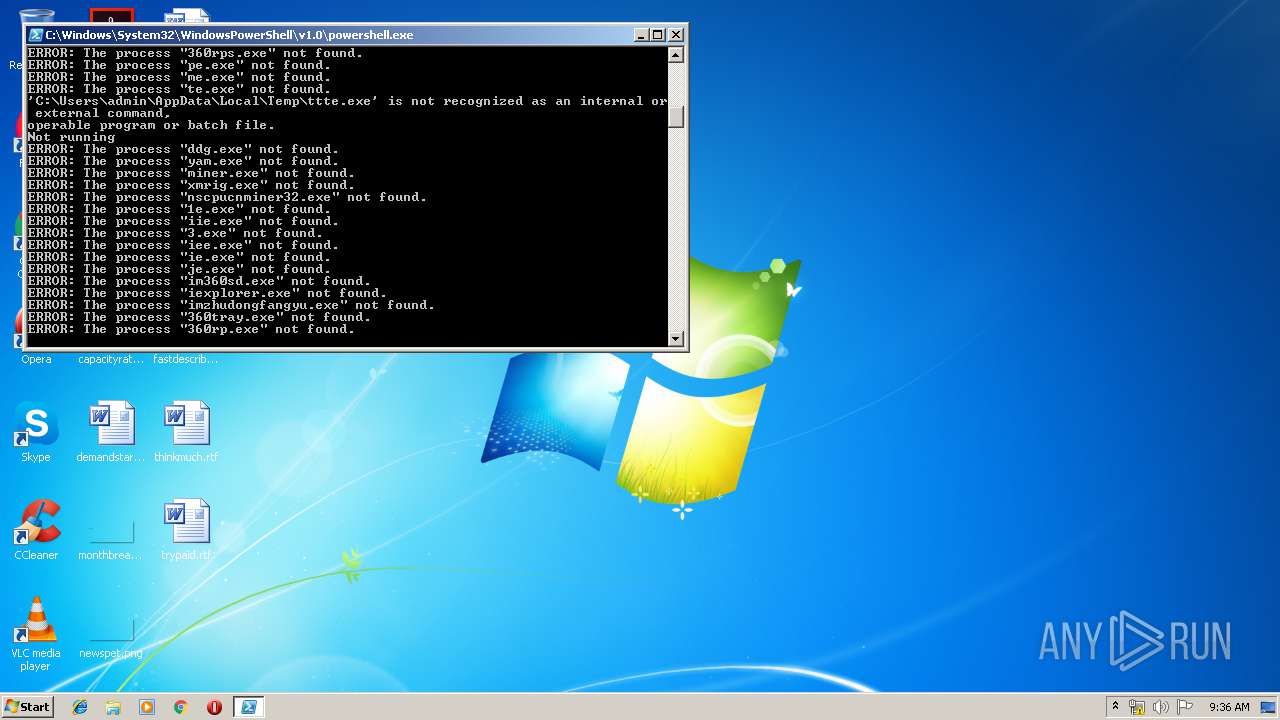
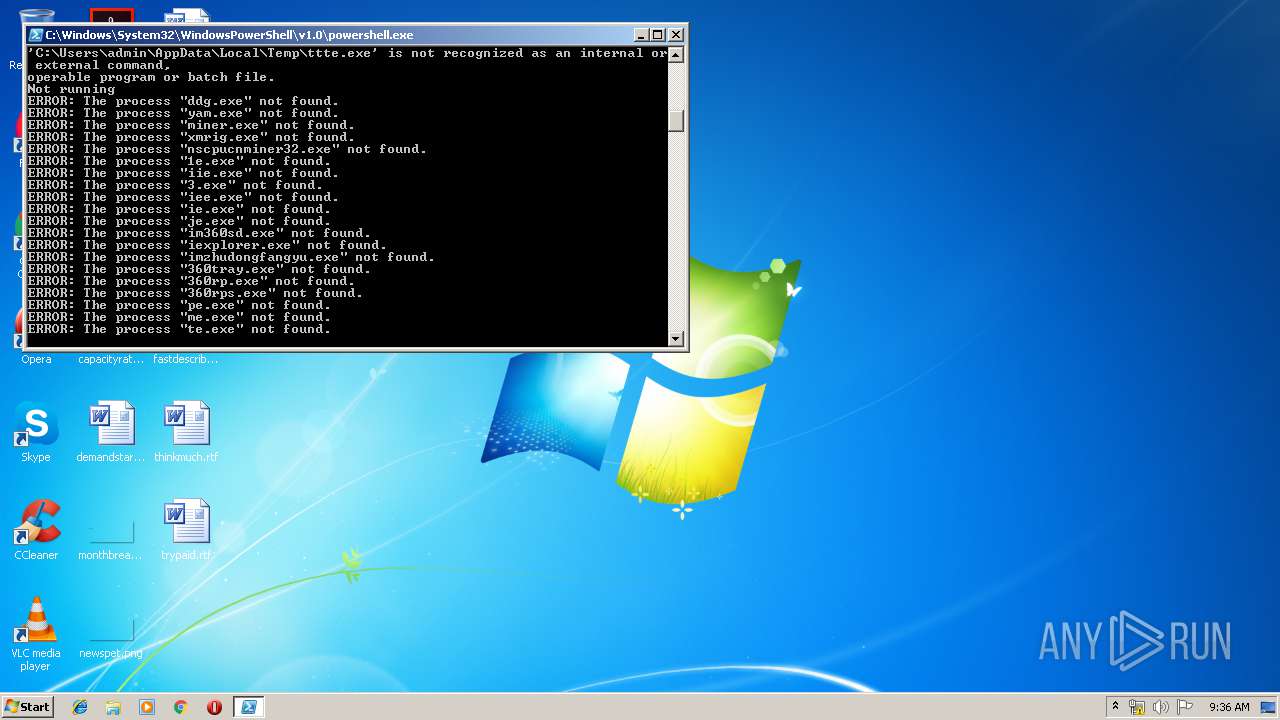
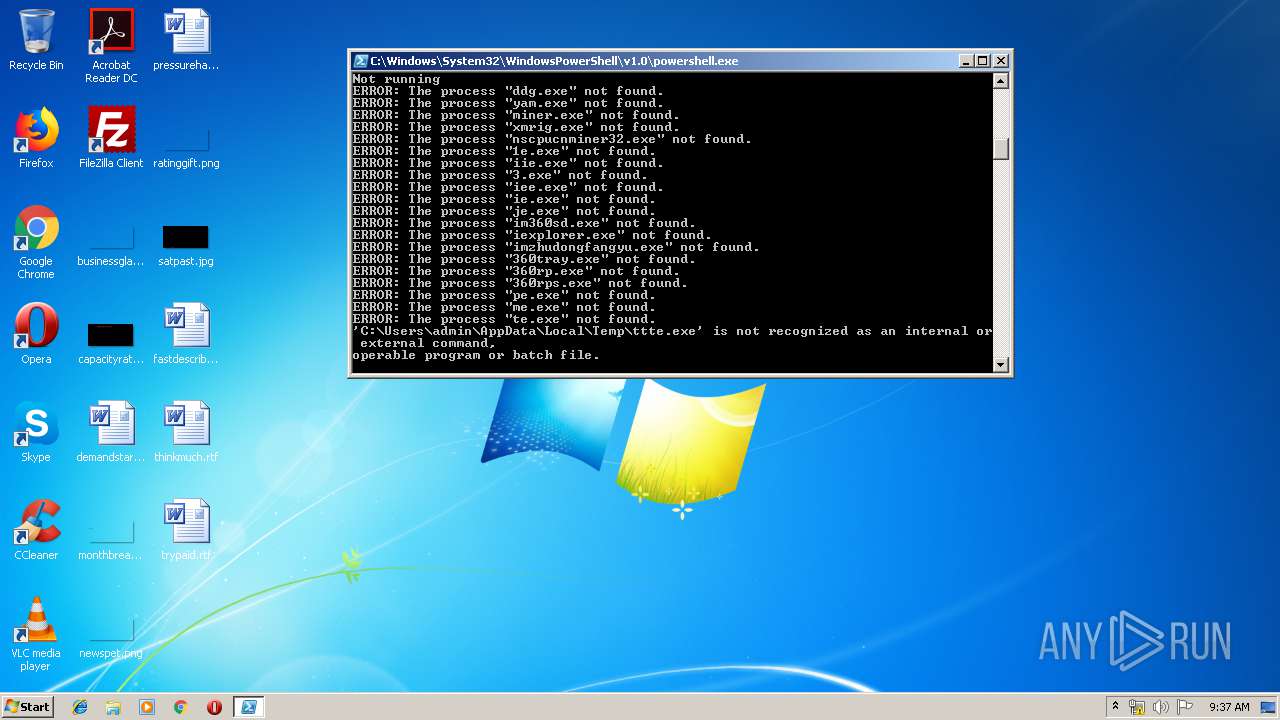
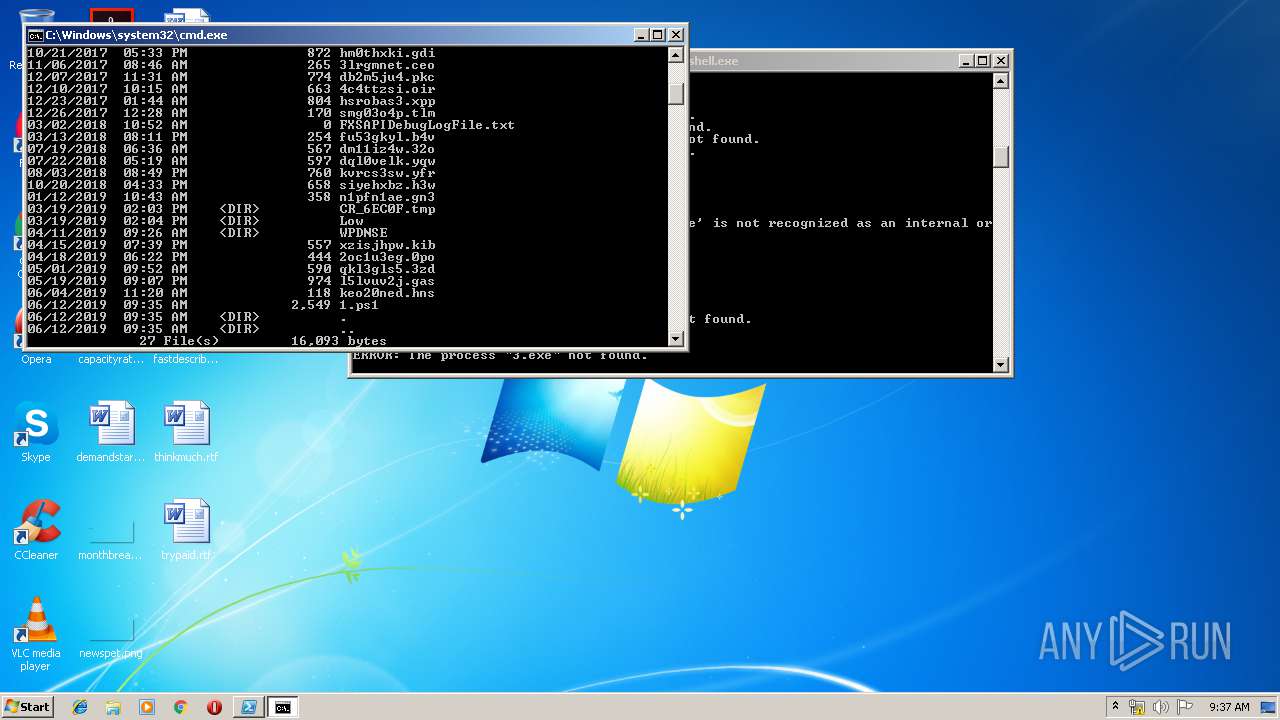
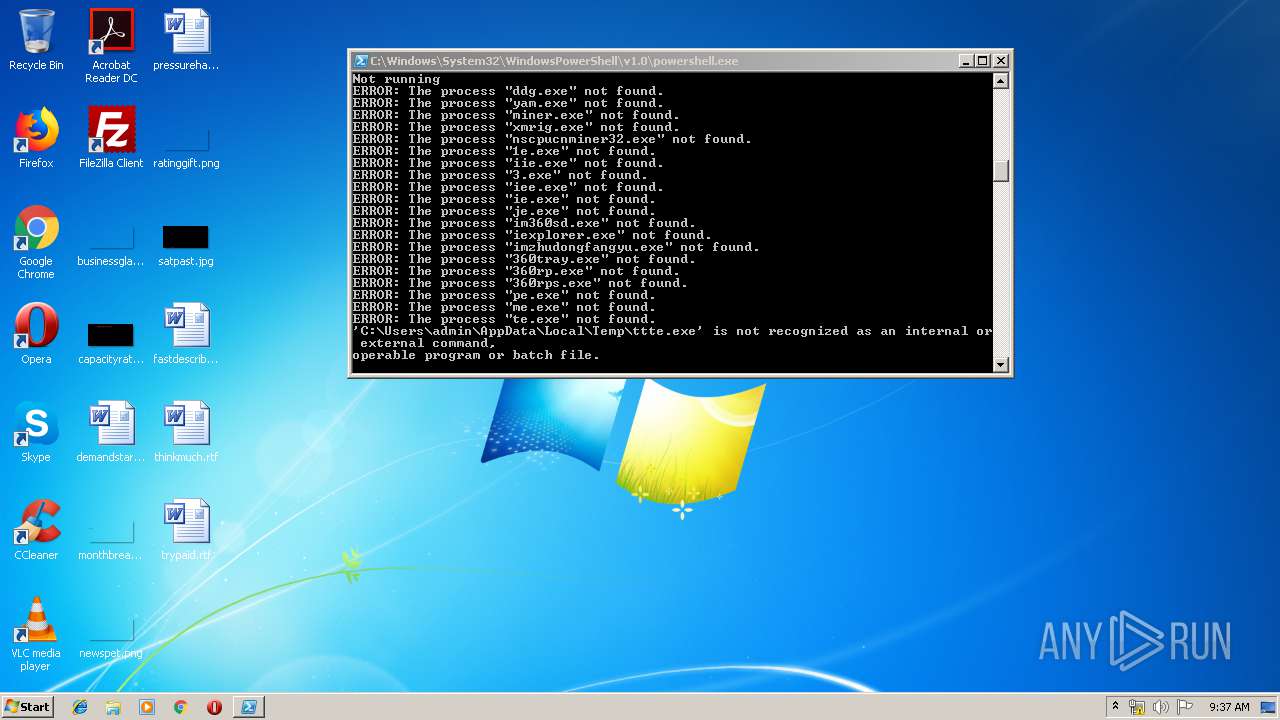
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2220)
- cmd.exe (PID: 4016)
- cmd.exe (PID: 2484)
- cmd.exe (PID: 3256)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 2528)
- cmd.exe (PID: 2872)
- cmd.exe (PID: 2168)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 2856)
- cmd.exe (PID: 3788)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 3400)
- cmd.exe (PID: 3012)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 3448)
- cmd.exe (PID: 2668)
- cmd.exe (PID: 720)
- cmd.exe (PID: 2548)
- cmd.exe (PID: 4080)
- cmd.exe (PID: 3592)
- cmd.exe (PID: 2808)
- cmd.exe (PID: 2224)
- cmd.exe (PID: 3136)
- cmd.exe (PID: 3332)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 3588)
- cmd.exe (PID: 1868)
- cmd.exe (PID: 2816)
- cmd.exe (PID: 3824)
- cmd.exe (PID: 2628)
- cmd.exe (PID: 308)
- cmd.exe (PID: 3316)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 3196)
- cmd.exe (PID: 3312)
- cmd.exe (PID: 868)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 2528)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 2448)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 3148)
- cmd.exe (PID: 1952)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 2584)
- cmd.exe (PID: 1732)
- cmd.exe (PID: 3836)
- cmd.exe (PID: 2344)
- cmd.exe (PID: 3392)
- cmd.exe (PID: 1864)
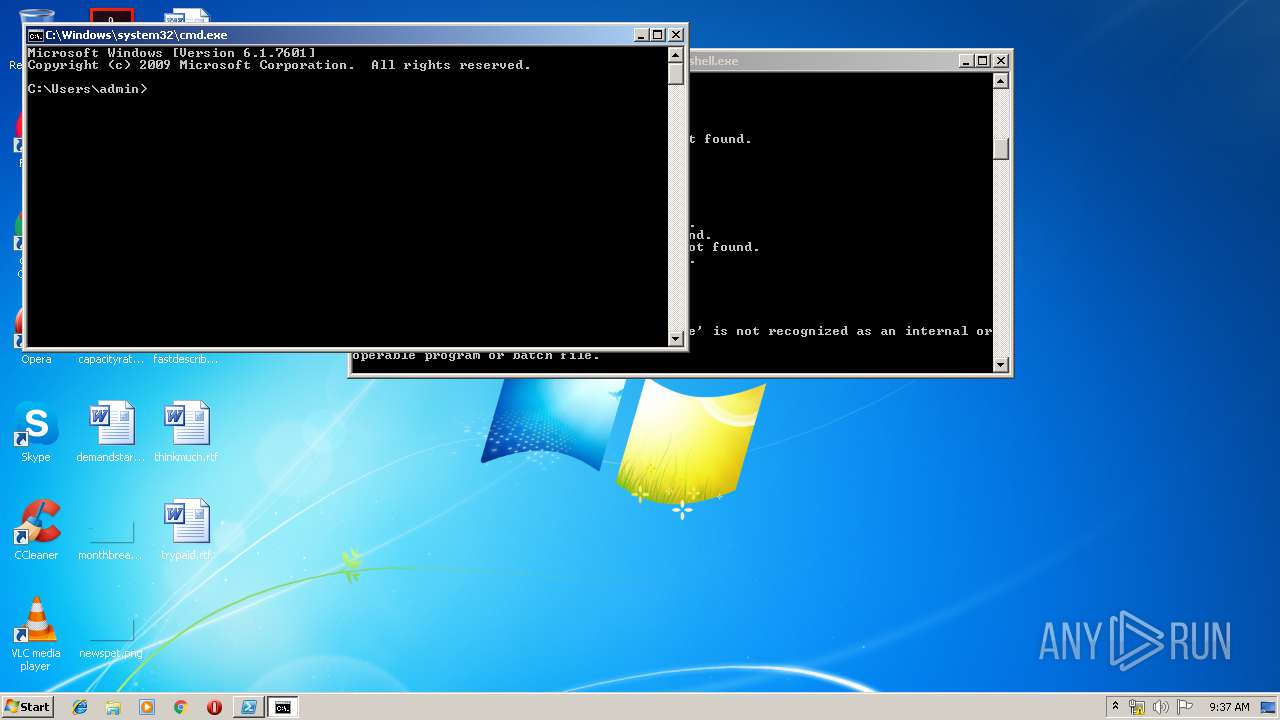
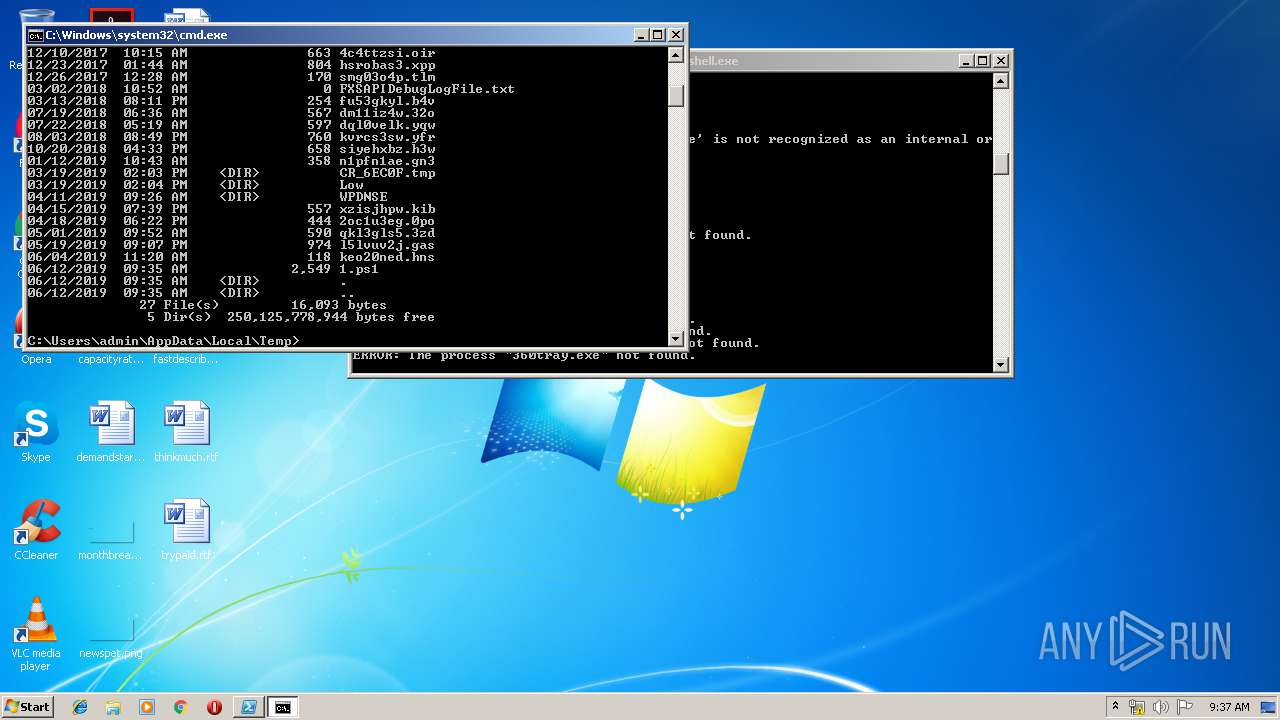
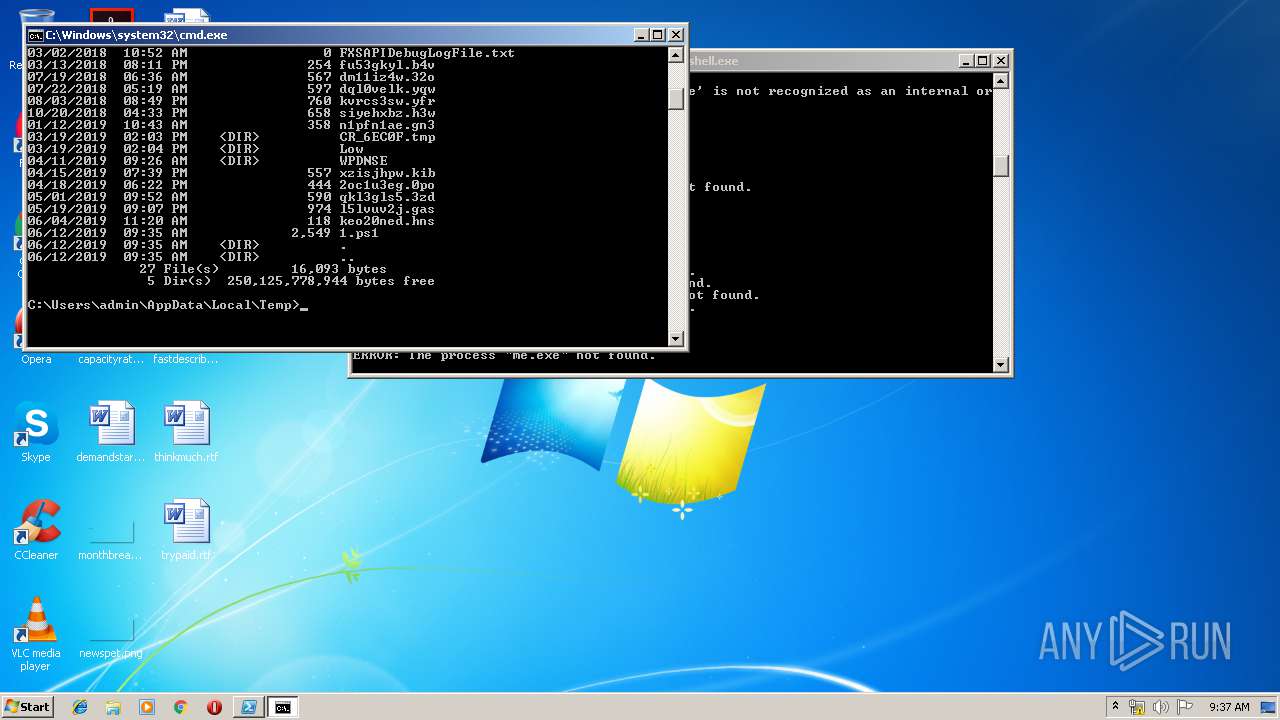
Starts CMD.EXE for commands execution
- powershell.exe (PID: 2952)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 3744)
- cmd.exe (PID: 3640)
- cmd.exe (PID: 864)
INFO
Manual execution by user
- cmd.exe (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
174
Monitored processes
139
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | taskkill /IM miner.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 308 | "C:\Windows\system32\cmd.exe" /C taskkill /IM te.exe /f | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 720 | "C:\Windows\system32\schtasks.exe" /Create /SC MINUTE /TN "Update service for Oracle productsoo" /TR "PowerShell.exe -ExecutionPolicy bypass -windowstyle hidden -noexit -File C:\Users\admin\SchTask1.ps1" /MO 6 /F | C:\Windows\system32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 720 | "C:\Windows\system32\cmd.exe" /C taskkill /IM yam.exe /f | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 756 | "C:\Windows\system32\schtasks.exe" /Delete /TN "Update service for Oracle productsm" /F | C:\Windows\system32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | taskkill /IM imzhudongfangyu.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | "C:\Windows\system32\cmd.exe" /C taskkill /IM iexplorer.exe /f | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 868 | "C:\Windows\system32\cmd.exe" /C taskkill /IM ddg.exe /f | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1344 | taskkill /IM iexplorer.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1732 | "C:\Windows\system32\cmd.exe" /C taskkill /IM me.exe /f | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
732
Read events
661
Write events
71
Delete events
0
Modification events
| (PID) Process: | (2952) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2952) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2952) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2952) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2952) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2952) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2952) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2952) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2952) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2952) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
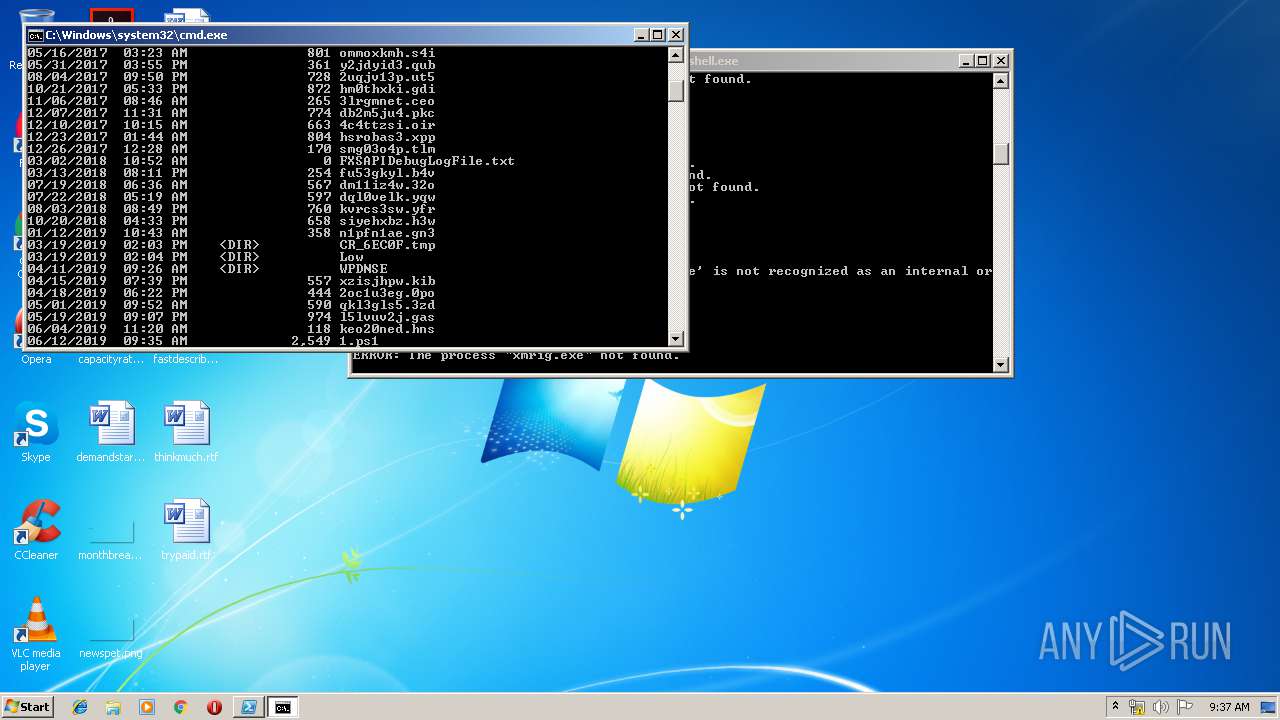
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
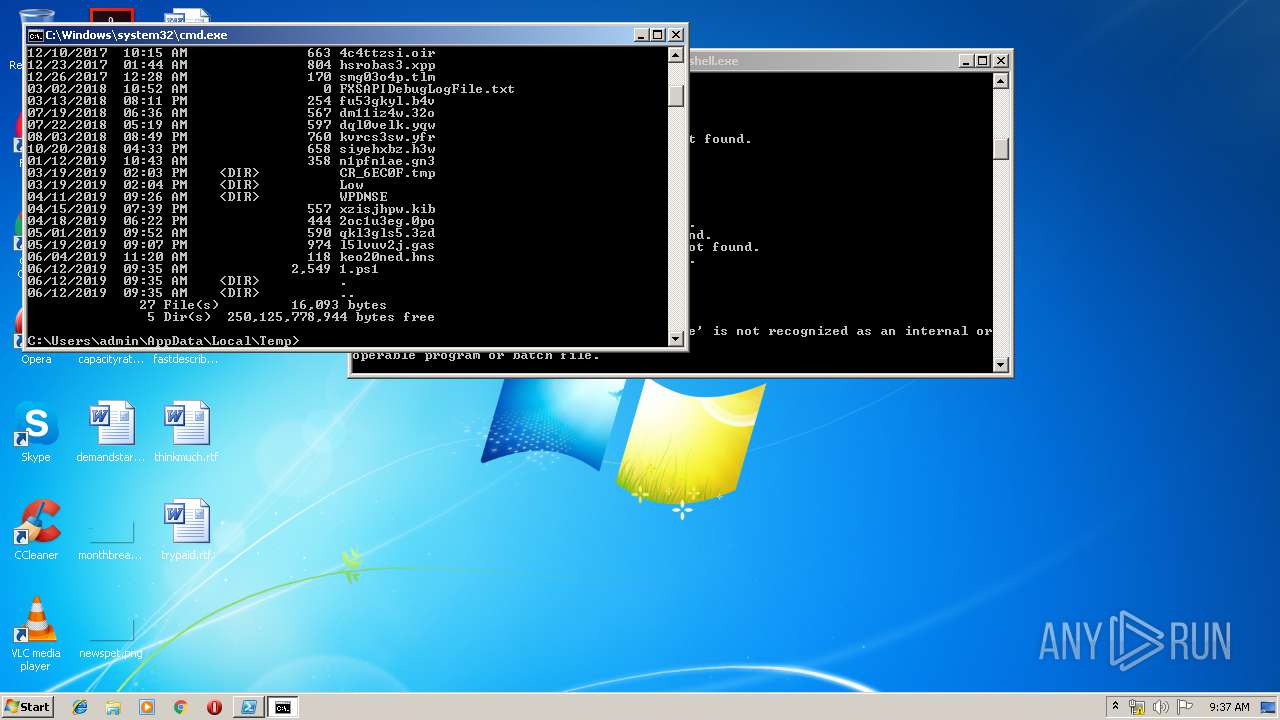
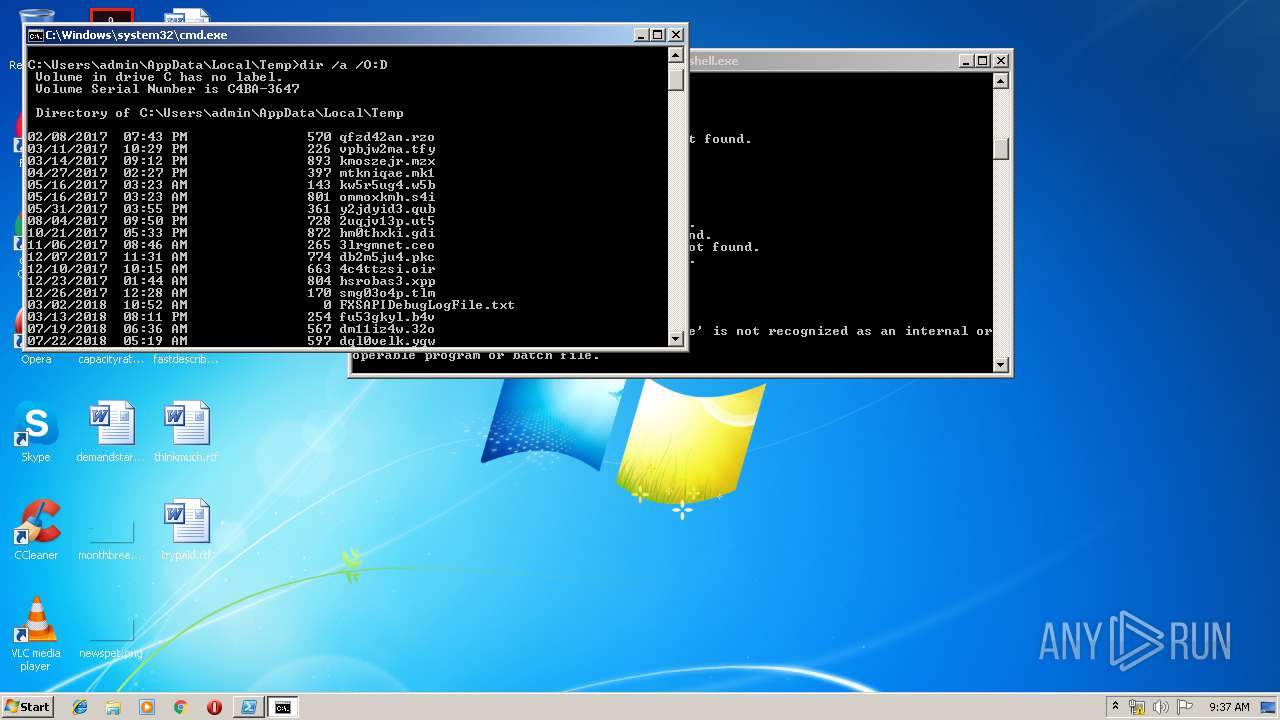
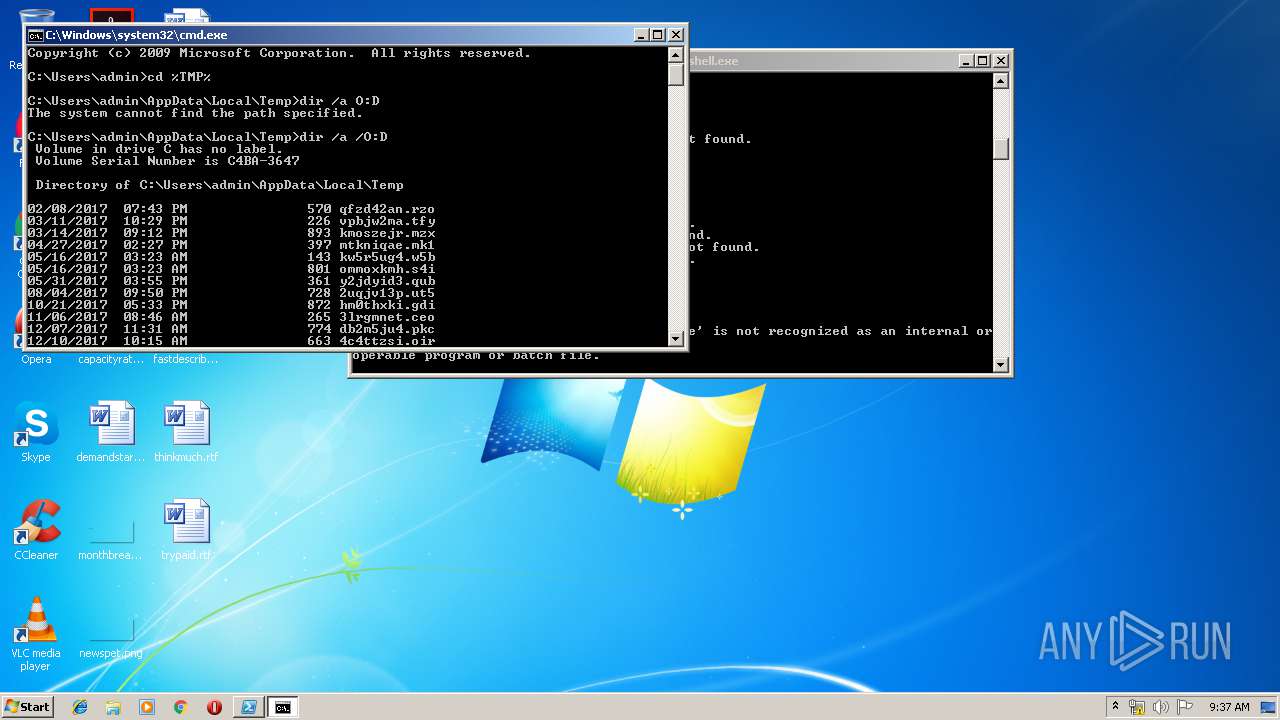
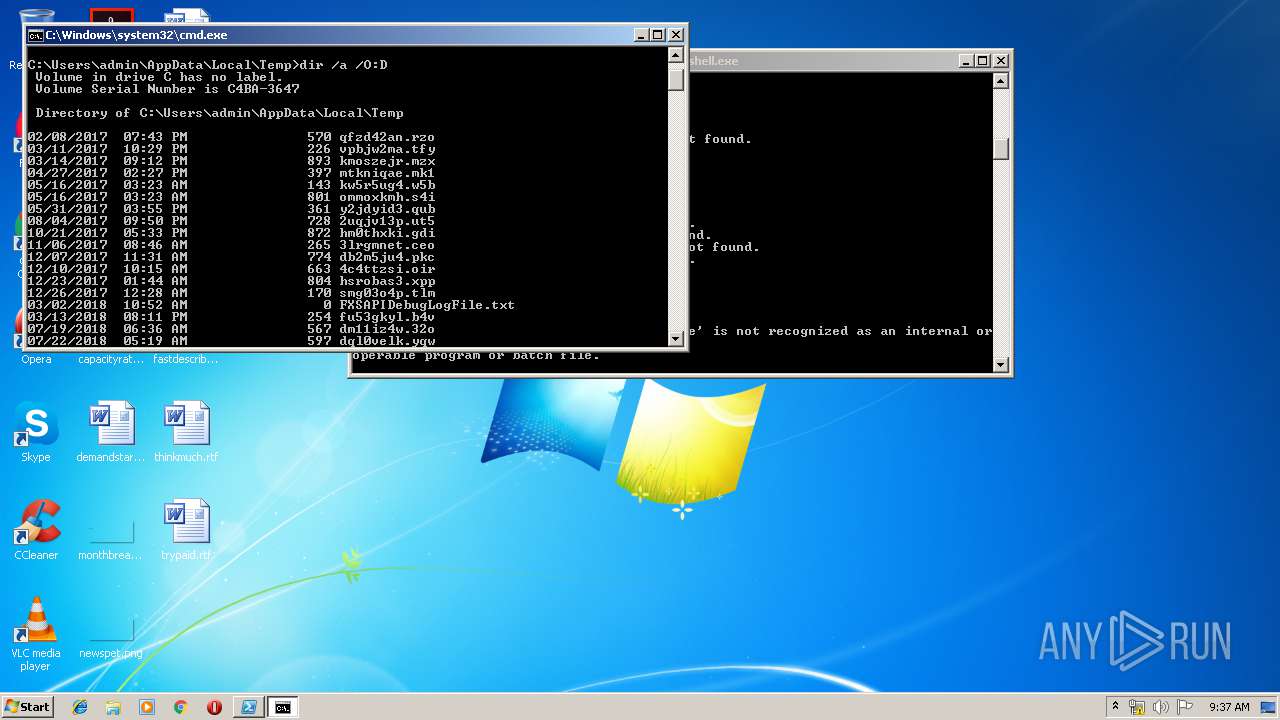
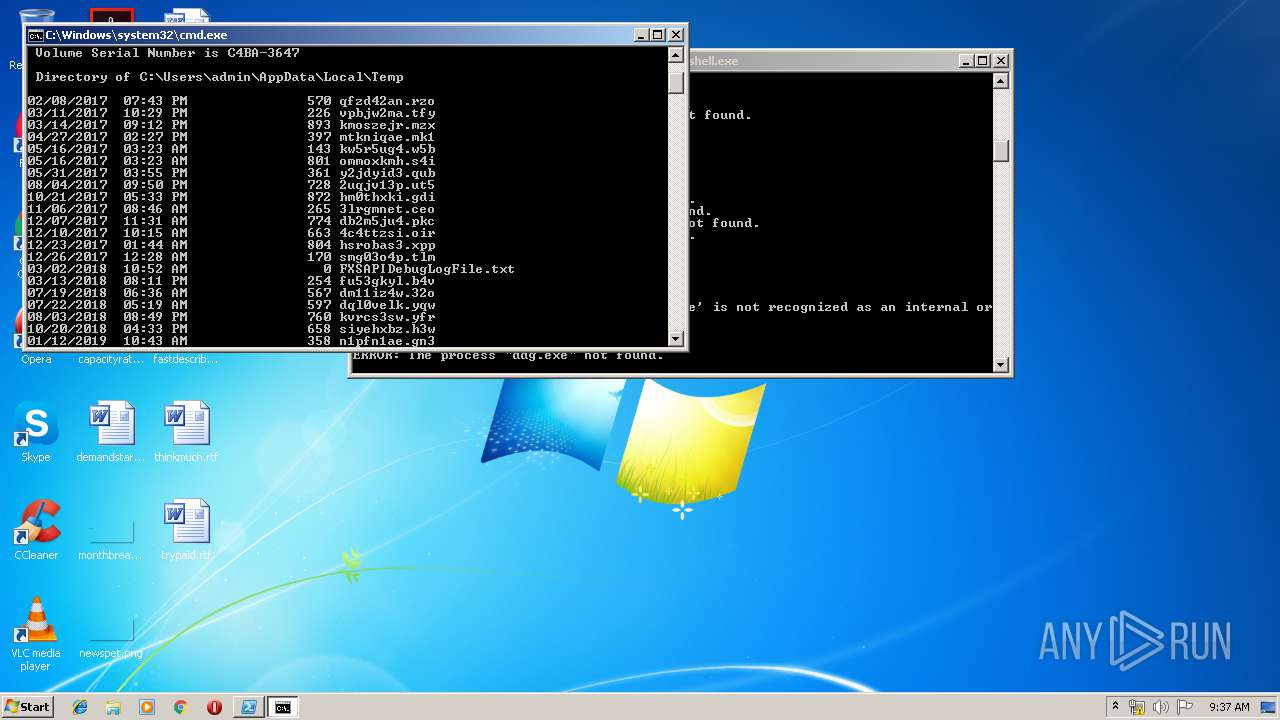
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7SV6S74KK9ZV4BWPQDCB.temp | — | |
MD5:— | SHA256:— | |||
| 2952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF14e974.TMP | binary | |
MD5:— | SHA256:— | |||
| 2952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2952 | powershell.exe | C:\Users\admin\SchTask.ps1 | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | powershell.exe | 192.99.142.235:8220 | — | OVH SAS | CA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |