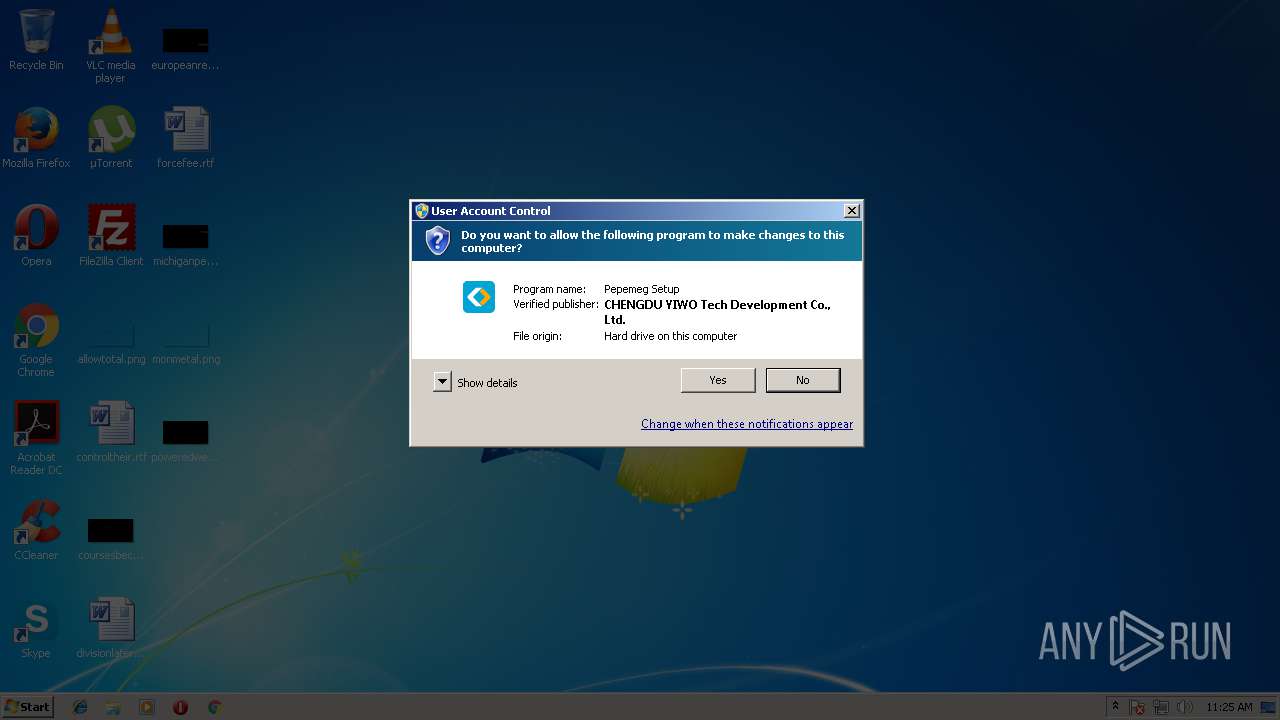
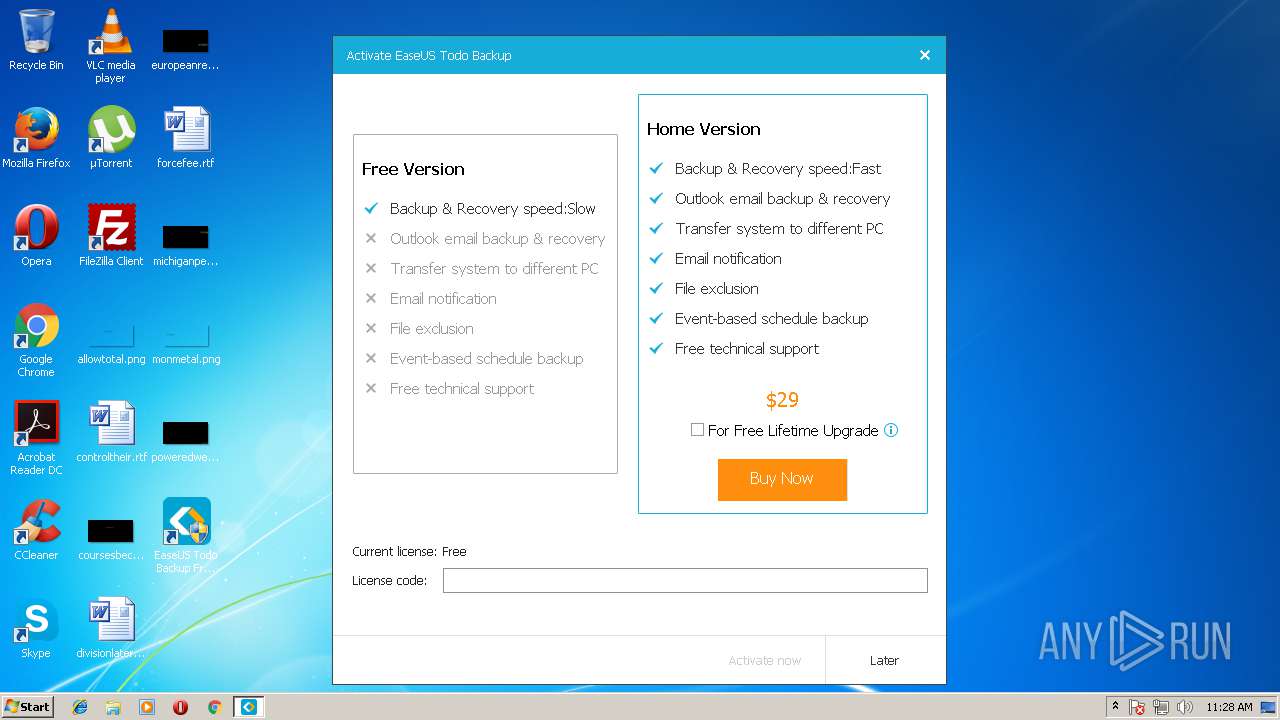
| File name: | innosetup.exe |
| Full analysis: | https://app.any.run/tasks/c2a75613-b38b-4565-a414-5596e0e7aa33 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2018, 10:25:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 757A01CFEDCBC2CD0D8DAF8E93D2CD76 |
| SHA1: | 1EB6172DB588D2CC1E7D866B57A3FD0EE14599BF |
| SHA256: | 0C9B56C5A80B3566E828843AD702235C76CFB67AAF85943DB2E32406860040E4 |
| SSDEEP: | 49152:tOdxq1dbmj8vU8l/h7fLnSwo4xV7GJ64TwKg30jK2pQacr6:UDSqo88l/h7LSLWCBMKOJ |
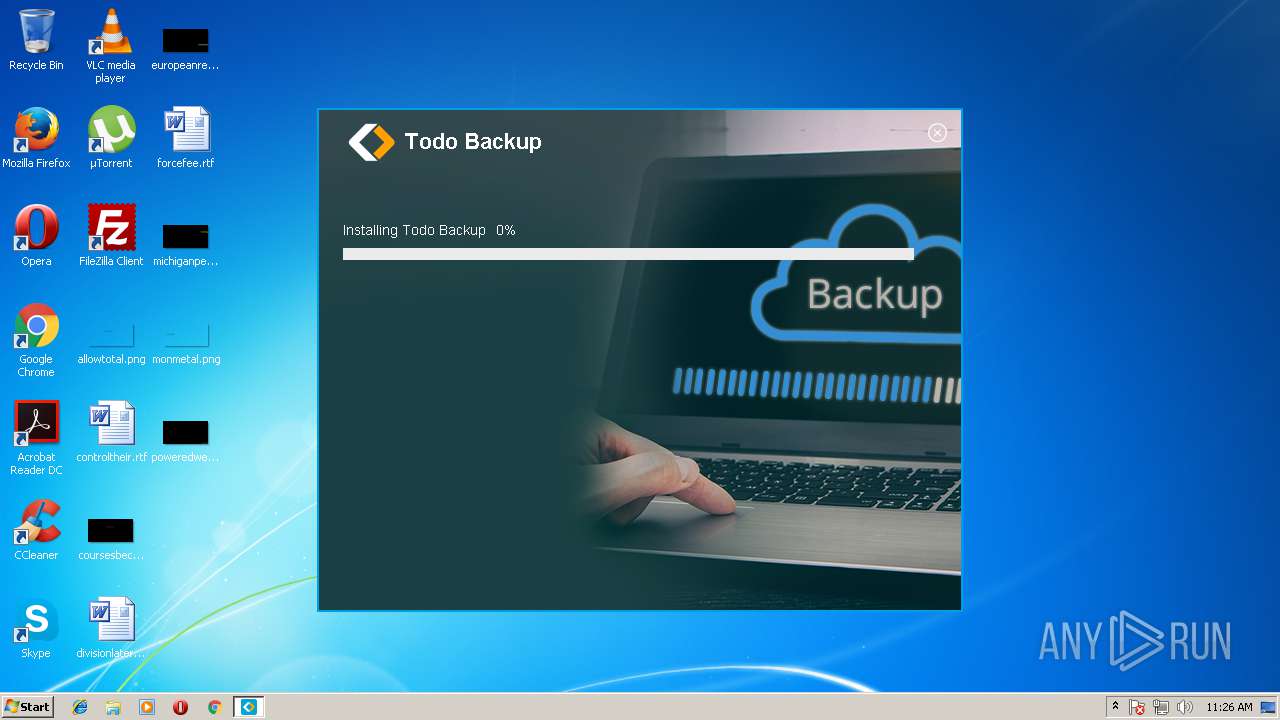
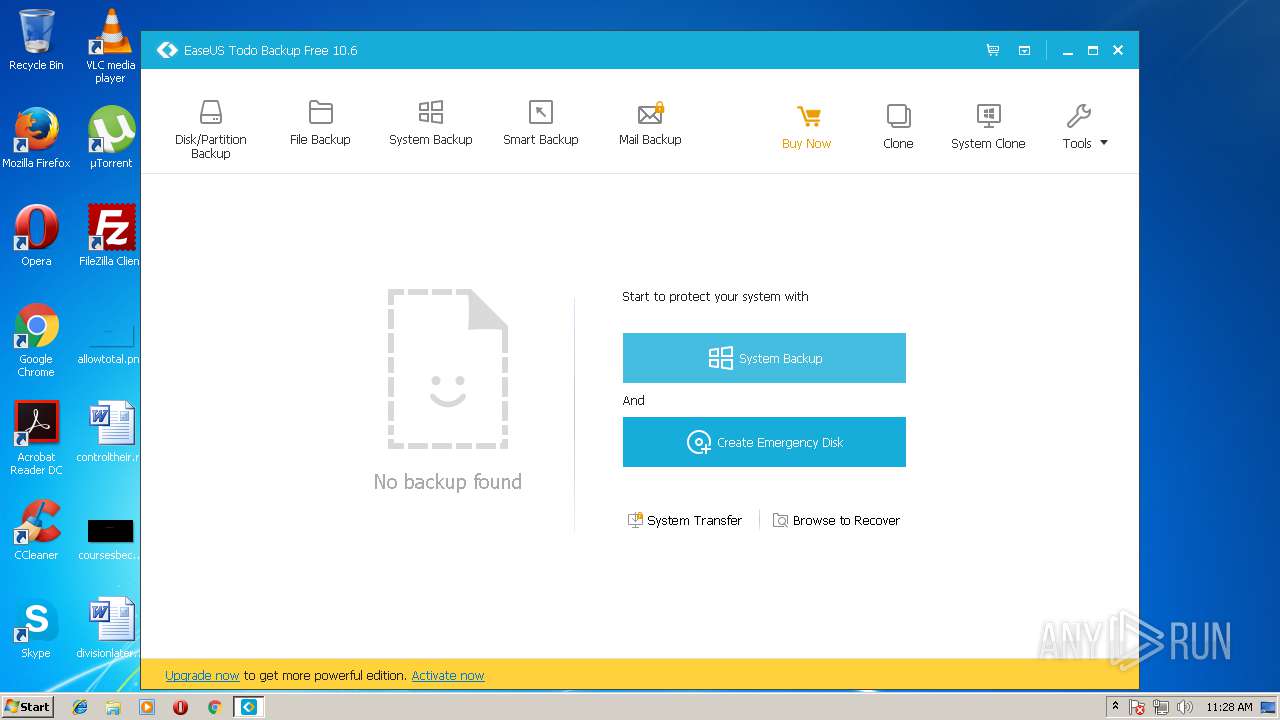
MALICIOUS
Application was dropped or rewritten from another process
- Agent.exe (PID: 4012)
- Agent.exe (PID: 2600)
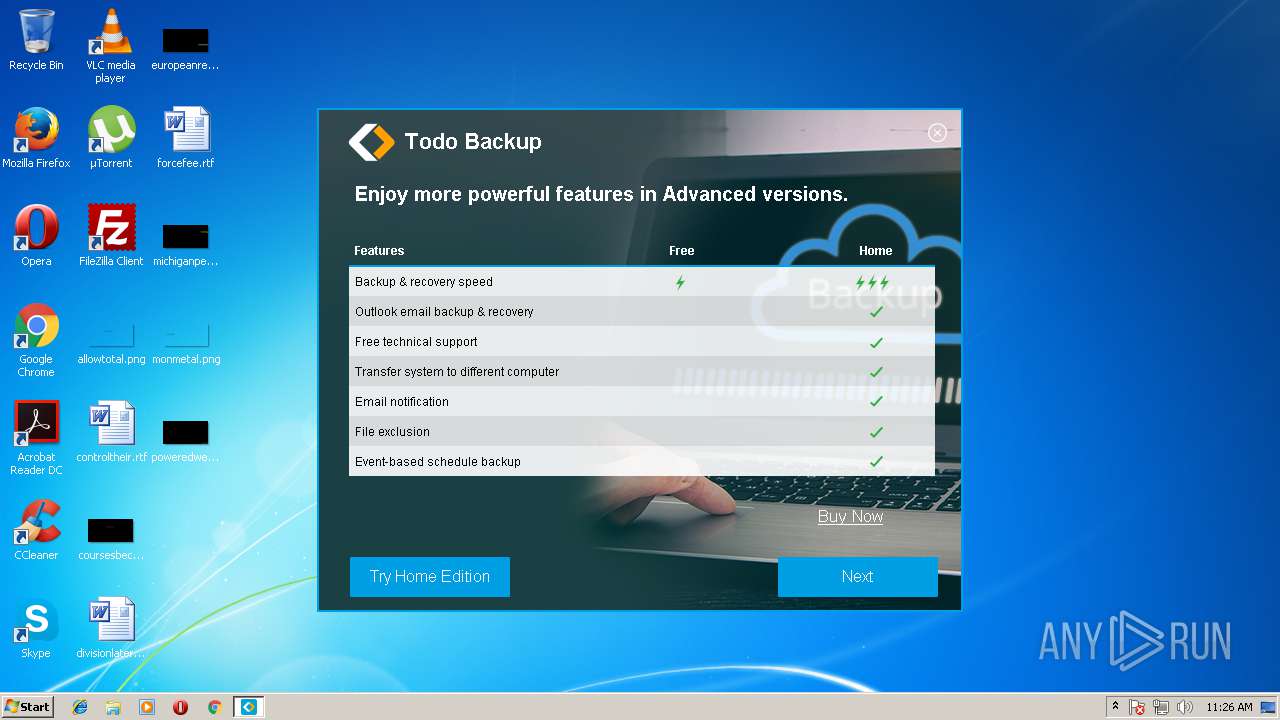
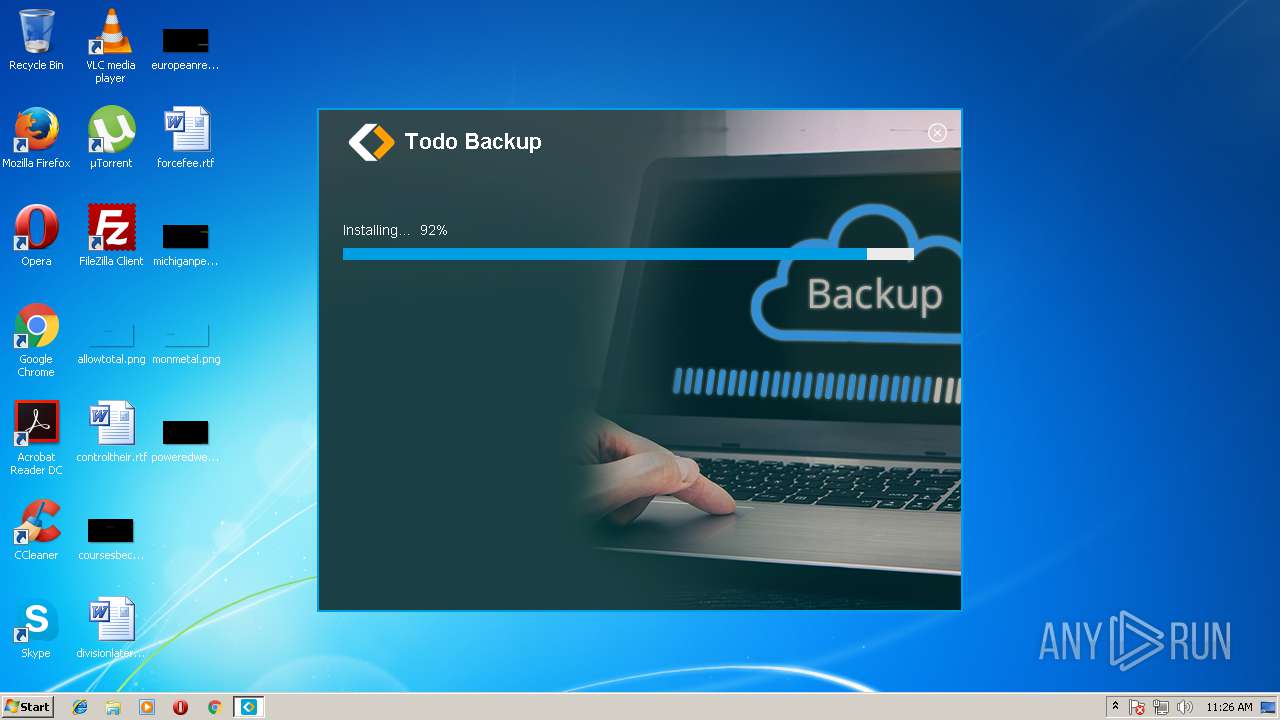
Loads dropped or rewritten executable
- Agent.exe (PID: 2600)
- TodoBackupService.exe (PID: 2956)
- TBConsoleUI.exe (PID: 3404)
- TbService.exe (PID: 2408)
SUSPICIOUS
Application launched itself
- innosetup.exe (PID: 2016)
- cmd.exe (PID: 1272)
Reads CPU info
- innosetup.exe (PID: 1440)
Reads the machine GUID from the registry
- innosetup.exe (PID: 1440)
Reads productID from registry
- innosetup.exe (PID: 1440)
Creates files in the program directory
- innosetup.exe (PID: 1440)
- drvsetup.exe (PID: 3968)
- uexperice.exe (PID: 2472)
- Agent.exe (PID: 4012)
- Agent.exe (PID: 2600)
- uexperice.exe (PID: 3364)
- uexperice.exe (PID: 1840)
- TBConsoleUI.exe (PID: 3404)
- EuDownload.exe (PID: 1216)
Reads internet explorer settings
- innosetup.exe (PID: 1440)
Reads the date of Windows installation
- innosetup.exe (PID: 1440)
Executable content was dropped or overwritten
- innosetup.exe (PID: 1440)
- SETUP.exe (PID: 2208)
- SETUP.tmp (PID: 2652)
Starts CMD.EXE for commands execution
- innosetup.exe (PID: 1440)
- cmd.exe (PID: 1272)
Reads Windows owner settings
- SETUP.tmp (PID: 2652)
Reads the Windows organization settings
- SETUP.tmp (PID: 2652)
Creates files in the Windows directory
- SETUP.tmp (PID: 2652)
- drvsetup.exe (PID: 3968)
- Agent.exe (PID: 2600)
- WinChkdsk.exe (PID: 3348)
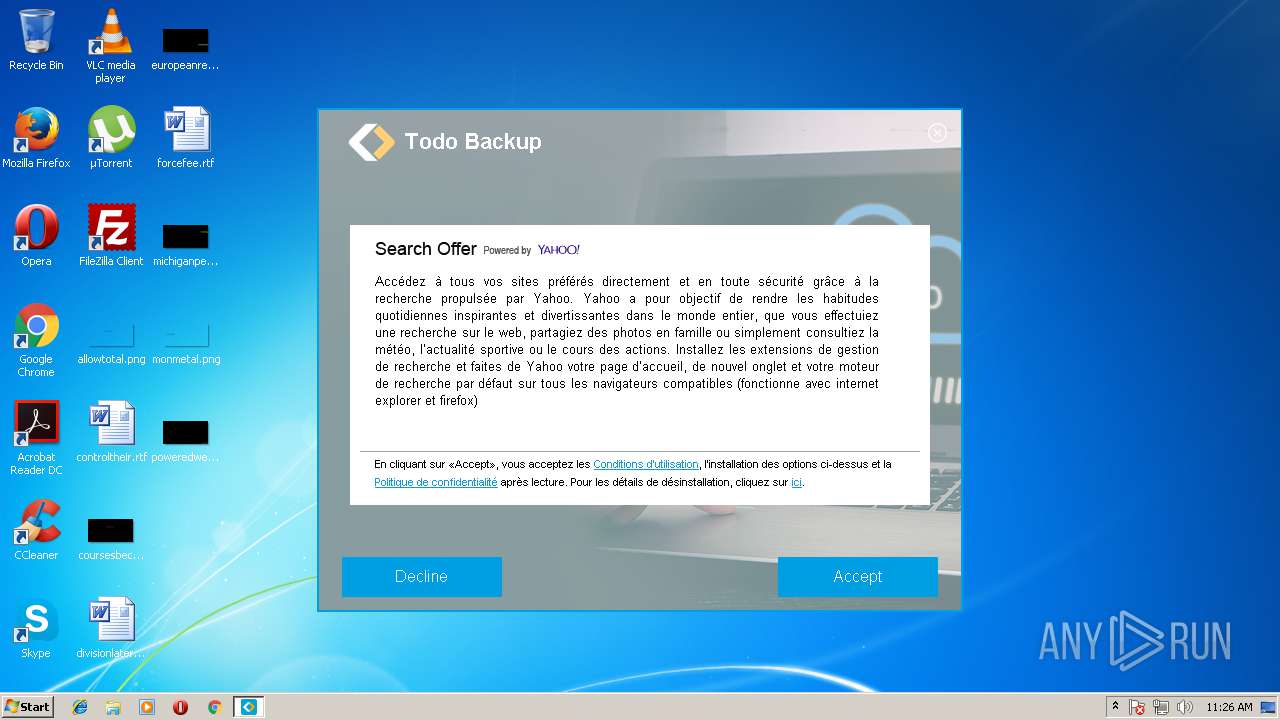
Changes IE settings (feature browser emulation)
- SETUP.tmp (PID: 2652)
Removes files from Windows directory
- drvsetup.exe (PID: 3968)
Creates COM task schedule object
- AppSetup.exe (PID: 2464)
Modifies the open verb of a shell class
- AppSetup.exe (PID: 2464)
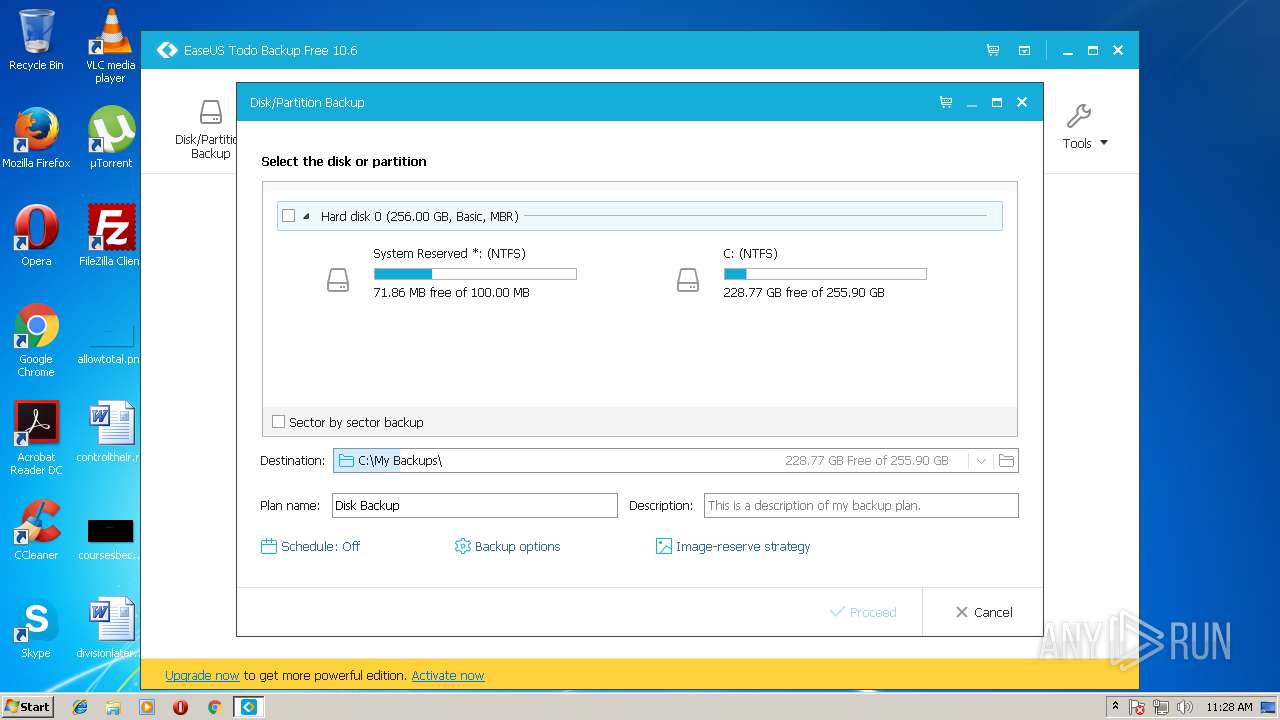
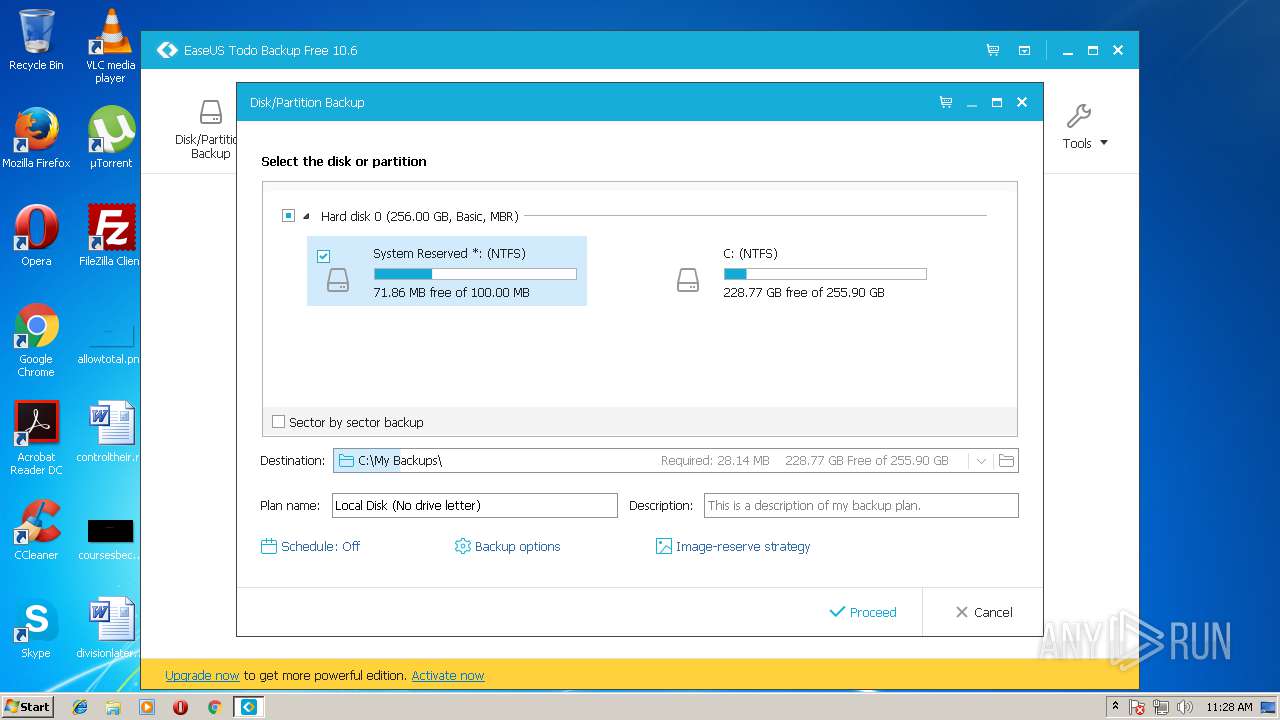
Low-level read access rights to disk partition
- uexperice.exe (PID: 3584)
- uexperice.exe (PID: 3364)
- Agent.exe (PID: 2600)
- vds.exe (PID: 2396)
- TbService.exe (PID: 2408)
Creates files in the driver directory
- drvsetup.exe (PID: 3968)
Creates or modifies windows services
- Agent.exe (PID: 4012)
- WinChkdsk.exe (PID: 3348)
INFO
Dropped object may contain URL's
- innosetup.exe (PID: 1440)
- SETUP.tmp (PID: 2652)
Loads dropped or rewritten executable
- SETUP.tmp (PID: 2652)
Application was dropped or rewritten from another process
- SETUP.tmp (PID: 2652)
Creates a software uninstall entry
- SETUP.tmp (PID: 2652)
Creates or modifies windows services
- vssvc.exe (PID: 2816)
Creates files in the program directory
- SETUP.tmp (PID: 2652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
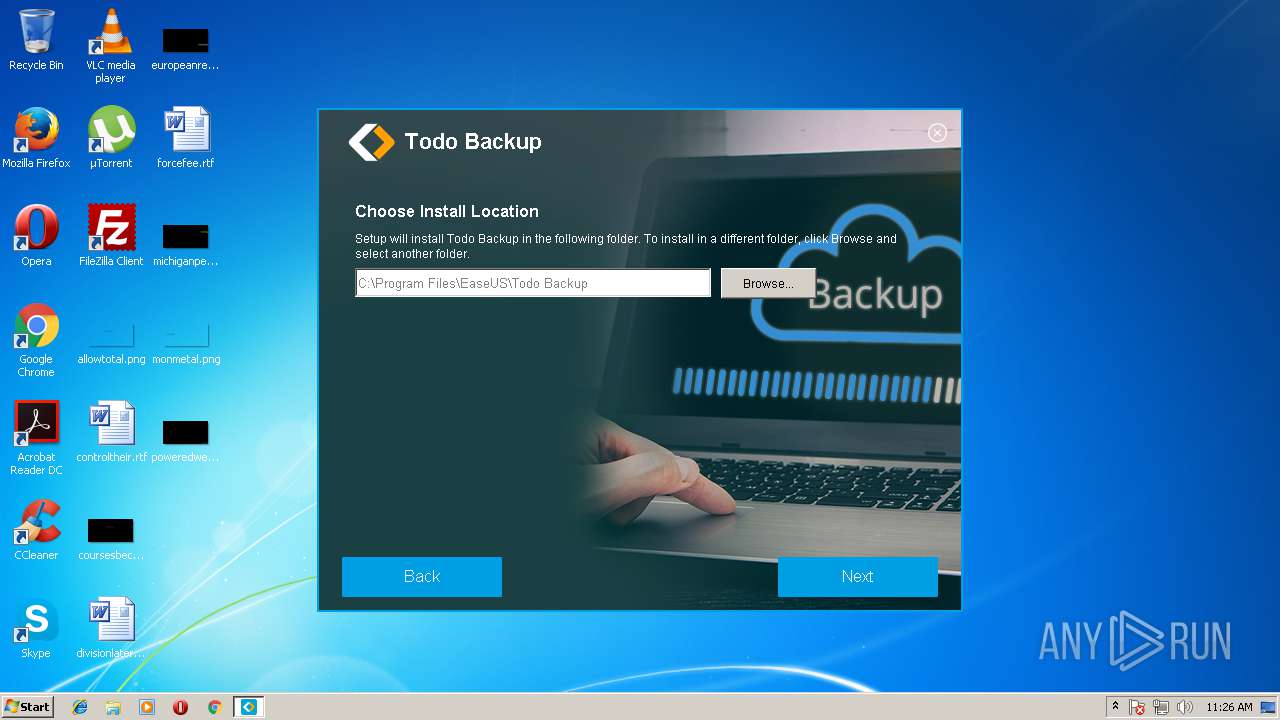
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 382976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c40 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Pepemeg Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Pepemeg |
| ProductVersion: | 5.2.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Pepemeg Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | Pepemeg |
| ProductVersion: | 5.2.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009364 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55898 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.7391 |
BSS | 0x0000C000 | 0x00000E88 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x0005C7E4 | 0x0005C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.54931 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.40389 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.11666 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.11212 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.94423 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.77944 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 2.21627 | 270376 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
97
Monitored processes
38
Malicious processes
9
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1216 | "C:\Program Files\EaseUS\Todo Backup\bin\uexperice.exe" -t 37379 "64" | C:\Program Files\EaseUS\Todo Backup\bin\uexperice.exe | — | SETUP.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\EaseUS\Todo Backup\bin\EuDownload.exe" https://update.easeus.com/update/tb/innerbuy/tb_home_innerbuy_flag_cfg.ini "C:\Program Files\EaseUS\Todo Backup\InnerBuy\res\InnerBuyConfig.ini" 0 "" 2 2952 | C:\Program Files\EaseUS\Todo Backup\bin\EuDownload.exe | TBConsoleUI.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1272 | /d /c TIMEOUT 1 & cmd /d /c copy /B /Y "C:\Users\admin\AppData\Local\Temp\D59311751876881.dat"+"C:\Users\admin\AppData\Local\Temp\D59311751876882.dat" "C:\Users\admin\AppData\Local\Temp\in04D4D345\0DA31EC7_stp\SETUP.exe" & cmd /d /c del "C:\Users\admin\AppData\Local\Temp\D59311751876881.dat" & cmd /d /c del "C:\Users\admin\AppData\Local\Temp\D59311751876882.dat" | C:\Windows\system32\cmd.exe | — | innosetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1364 | "C:\Program Files\EaseUS\Todo Backup\bin\Loader.exe" | C:\Program Files\EaseUS\Todo Backup\bin\Loader.exe | — | innosetup.exe | |||||||||||
User: admin Company: CHENGDU YIWO Tech Development Co., Ltd Integrity Level: HIGH Description: EaseUS Todo Backup Application Exit code: 0 Version: 10.6.0.0 Modules
| |||||||||||||||
| 1440 | "C:\Users\admin\AppData\Local\Temp\innosetup.exe" /RSF /ppn:YyhwYgxaFRAiP211FM5W /mnl | C:\Users\admin\AppData\Local\Temp\innosetup.exe | innosetup.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Pepemeg Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1524 | "C:\Program Files\EaseUS\Todo Backup\bin\uexperice.exe" -t 4104 "1033" | C:\Program Files\EaseUS\Todo Backup\bin\uexperice.exe | — | SETUP.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\EaseUS\Todo Backup\bin\uexperice.exe" -i 1 | C:\Program Files\EaseUS\Todo Backup\bin\uexperice.exe | SETUP.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2016 | "C:\Users\admin\AppData\Local\Temp\innosetup.exe" | C:\Users\admin\AppData\Local\Temp\innosetup.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Pepemeg Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2092 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 585
Read events
1 408
Write events
171
Delete events
6
Modification events
| (PID) Process: | (2016) innosetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2016) innosetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1440) innosetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1440) innosetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1440) innosetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1440) innosetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\innosetup_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1440) innosetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\innosetup_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1440) innosetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\innosetup_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1440) innosetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\innosetup_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1440) innosetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\innosetup_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
52
Suspicious files
5
Text files
78
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1440 | innosetup.exe | C:\Users\admin\AppData\Local\Temp\000BEB45.log | — | |
MD5:— | SHA256:— | |||
| 1440 | innosetup.exe | C:\Users\admin\AppData\Local\Temp\inH78112540302\css\ie6_main.css | text | |
MD5:— | SHA256:— | |||
| 1440 | innosetup.exe | C:\Users\admin\AppData\Local\Temp\inH78112540302\css\main.scss | text | |
MD5:— | SHA256:— | |||
| 1440 | innosetup.exe | C:\Users\admin\AppData\Local\Temp\inH78112540302\css\main.css | text | |
MD5:— | SHA256:— | |||
| 1440 | innosetup.exe | C:\Users\admin\AppData\Local\Temp\inH78112540302\css\ie6_main.scss | text | |
MD5:— | SHA256:— | |||
| 1440 | innosetup.exe | C:\Users\admin\AppData\Local\Temp\inH78112540302\form.bmp.Mask | binary | |
MD5:D2FC989F9C2043CD32332EC0FAD69C70 | SHA256:27DD029405CBFB0C3BF8BAC517BE5DB9AA83E981B1DC2BD5C5D6C549FA514101 | |||
| 1440 | innosetup.exe | C:\Users\admin\AppData\Local\Temp\inH78112540302\css\_helpers.scss | text | |
MD5:5F158DBBD9FC4594A2F6C13854501916 | SHA256:BF12B79F67F1CB9988797F7D81F6F504C8DFE0F0435482E64819A140DBC8DA14 | |||
| 1440 | innosetup.exe | C:\Users\admin\AppData\Local\Temp\inH78112540302\css\helpers\_border.scss | text | |
MD5:681FB7EB197E8E7EBD89F828D1181FD6 | SHA256:51E8AFA69ED6D92EB82F71939B0B8FD34EF23FAECEE457698238E5A4F28DF984 | |||
| 1440 | innosetup.exe | C:\Users\admin\AppData\Local\Temp\inH78112540302\css\_functions.scss | text | |
MD5:8F7259DE64F6DDF352BF461F44D34A81 | SHA256:80EDC9D67172BC830D68D33F4547735FB072CADF3EF25AAB37A10B50DB87A069 | |||
| 1440 | innosetup.exe | C:\Users\admin\AppData\Local\Temp\inH78112540302\css\_variables.scss | text | |
MD5:07922410C30F0117CBC3C140F14AEA88 | SHA256:AF1999B49C03F5DCBB19466466FAC2D8172C684C0FF18931B85A8D0A06332C73 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
17
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1440 | innosetup.exe | GET | — | 192.96.201.161:80 | http://remote.luritt-dohifa.com/app/Easeus_Pub_PI_TB/TodoBackup_Free_010218.cis | US | — | — | malicious |
1440 | innosetup.exe | GET | 206 | 185.59.222.146:80 | http://vpn.luritt-dohifa.com/app/Easeus_Pub_PI_TB/TodoBackup_Free_010218.cis | NL | binary | 16.4 Mb | malicious |
1440 | innosetup.exe | GET | 206 | 185.59.222.146:80 | http://vpn.luritt-dohifa.com/app/Easeus_Pub_PI_TB/TodoBackup_Free_010218.cis | NL | binary | 6.93 Mb | malicious |
1440 | innosetup.exe | GET | 206 | 185.59.222.146:80 | http://vpn.luritt-dohifa.com/app/Easeus_Pub_PI_TB/TodoBackup_Free_010218.cis | NL | binary | 15.4 Mb | malicious |
1440 | innosetup.exe | GET | 206 | 185.59.222.146:80 | http://vpn.luritt-dohifa.com/app/Easeus_Pub_PI_TB/TodoBackup_Free_010218.cis | NL | drz | 4.39 Mb | malicious |
1440 | innosetup.exe | POST | 200 | 52.213.10.43:80 | http://dev.luritt-dohifa.com/ | IE | — | — | suspicious |
1440 | innosetup.exe | POST | 200 | 52.213.10.43:80 | http://dev.luritt-dohifa.com/ | IE | — | — | suspicious |
1440 | innosetup.exe | POST | 200 | 52.48.96.210:80 | http://web.luritt-dohifa.com/Easeus_Pub_PI_TB/ | IE | binary | 544 Kb | malicious |
1440 | innosetup.exe | POST | 200 | 52.213.10.43:80 | http://dev.luritt-dohifa.com/ | IE | — | — | suspicious |
1440 | innosetup.exe | POST | 200 | 52.213.10.43:80 | http://dev.luritt-dohifa.com/ | IE | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1440 | innosetup.exe | 52.48.96.210:80 | web.luritt-dohifa.com | Amazon.com, Inc. | IE | whitelisted |
1440 | innosetup.exe | 52.213.10.43:80 | dev.luritt-dohifa.com | Amazon.com, Inc. | IE | unknown |
1440 | innosetup.exe | 192.96.201.161:80 | img.luritt-dohifa.com | Leaseweb USA, Inc. | US | malicious |
1440 | innosetup.exe | 185.59.222.146:80 | vpn.luritt-dohifa.com | Datacamp Limited | NL | malicious |
1840 | uexperice.exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
2100 | EuDownload.exe | 157.185.150.117:443 | update.easeus.com | — | US | suspicious |
1216 | EuDownload.exe | 157.185.150.117:443 | update.easeus.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
web.luritt-dohifa.com |
| malicious |
dev.luritt-dohifa.com |
| suspicious |
img.luritt-dohifa.com |
| malicious |
vpn.luritt-dohifa.com |
| malicious |
remote.luritt-dohifa.com |
| malicious |
track.easeus.com |
| suspicious |
update.easeus.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Agent.exe | Init Log |
Agent.exe | Ldq : Agent start install! |
Agent.exe |
Ldq : Agent call CreateService!
|
Agent.exe |
Ldq : Agent call CreateService is success!
|
Agent.exe | Init Log |
Agent.exe |
Ldq : Agent entry ServiceMain!
|
Agent.exe |
Ldq : Agent set service description!
|
SETUP.tmp | AddEaseUSFirewallException,001 lpctszFilePath=C:\Program Files\EaseUS\Todo Backup\bin\TbService.exe |
Agent.exe | socket closed
|
Agent.exe |
Zy : Instance CheckTool!
|