| File name: | Radic.exe |
| Full analysis: | https://app.any.run/tasks/c01274d4-999f-42c4-b790-ad31ad1b6761 |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 21:02:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | BB2F48B69ABD46648A761792B2897D97 |
| SHA1: | 85D1258E9A79AE070F7988424BBD70C2A3297F46 |
| SHA256: | 0C8F8CD027232CD9FC15C4045CCD9B94FEE33DF10F9B9778168F8148B23AFE52 |
| SSDEEP: | 24576:nQtPrAxYQ3BjTHhNqQk97dkaZf/4sr4akMgRxHbeE8hdFelnFHDqlKah6T9dx:nQPrtIZzh6dkaZf/58fRxS38ooh |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- Radic.exe (PID: 476)
Reads the computer name
- Radic.exe (PID: 476)
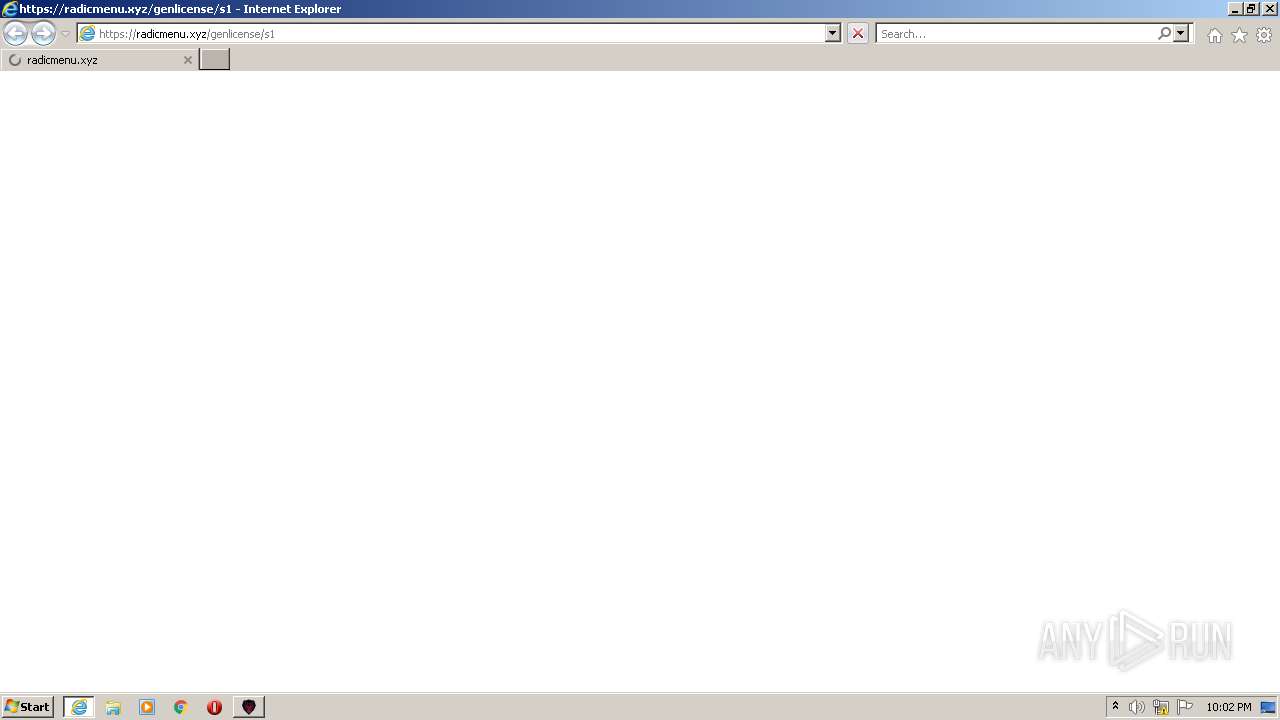
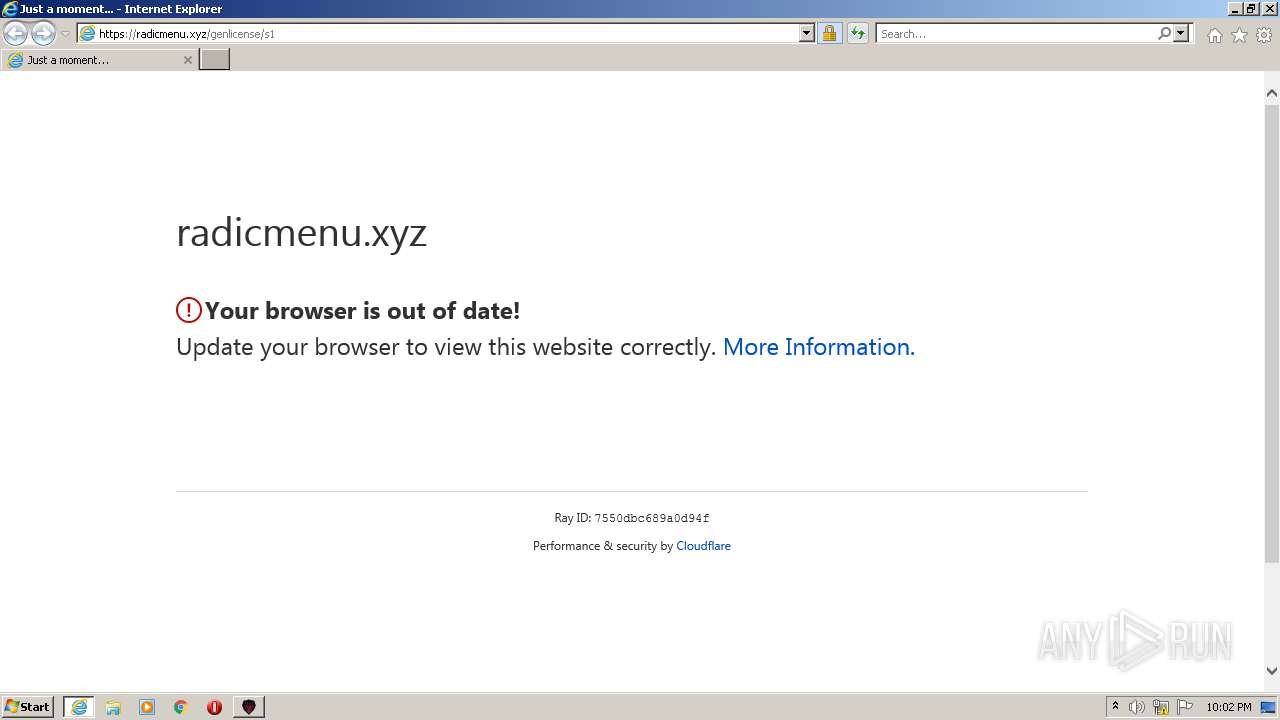
Starts Internet Explorer
- Radic.exe (PID: 476)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2692)
INFO
Checks supported languages
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 2692)
Reads the computer name
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 2692)
Application launched itself
- iexplore.exe (PID: 2076)
Changes internet zones settings
- iexplore.exe (PID: 2076)
Reads settings of System Certificates
- iexplore.exe (PID: 2692)
- iexplore.exe (PID: 2076)
Checks Windows Trust Settings
- iexplore.exe (PID: 2692)
- iexplore.exe (PID: 2076)
Changes settings of System certificates
- iexplore.exe (PID: 2692)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2692)
Reads the date of Windows installation
- iexplore.exe (PID: 2076)
Creates files in the user directory
- iexplore.exe (PID: 2692)
Reads internet explorer settings
- iexplore.exe (PID: 2692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2022-Jul-30 18:57:07 |
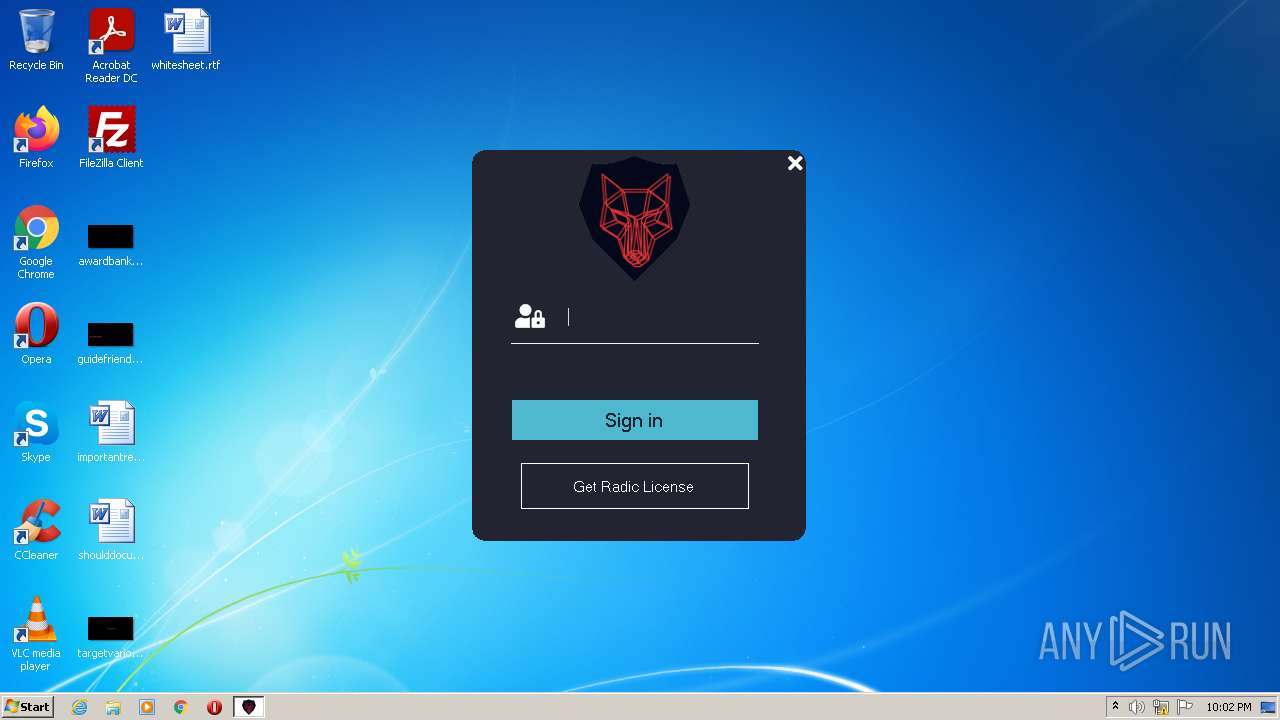
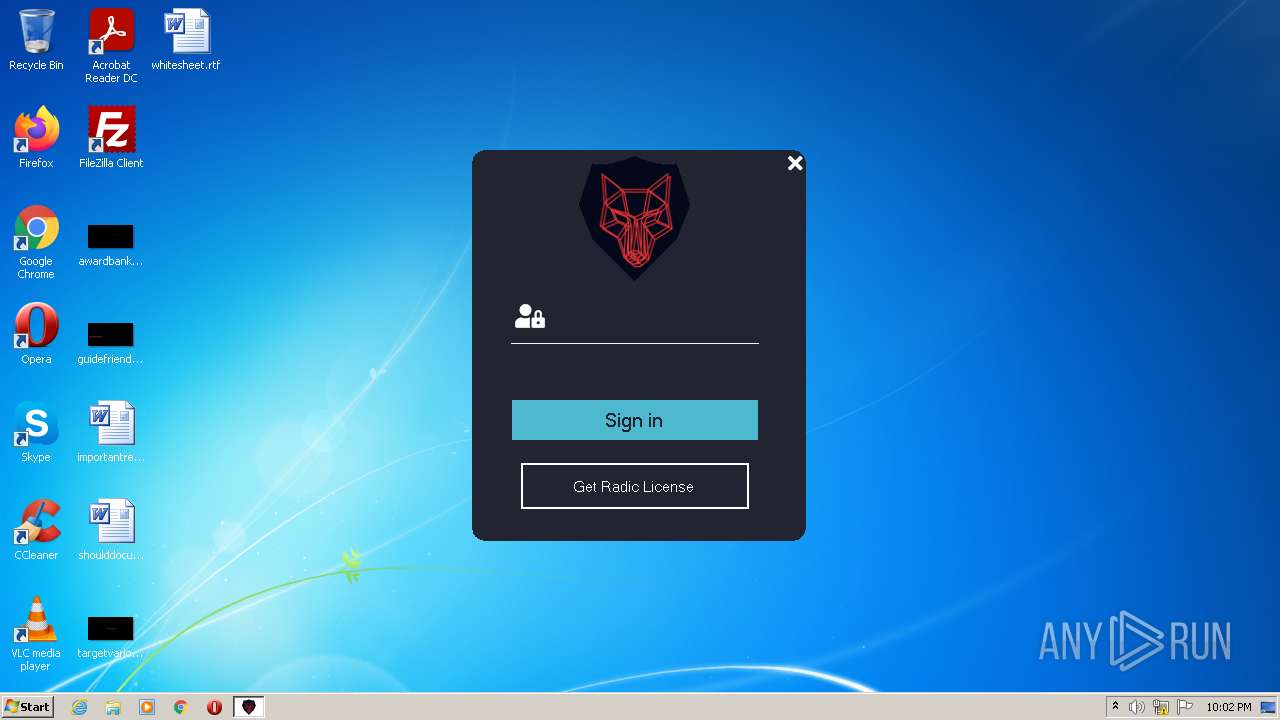
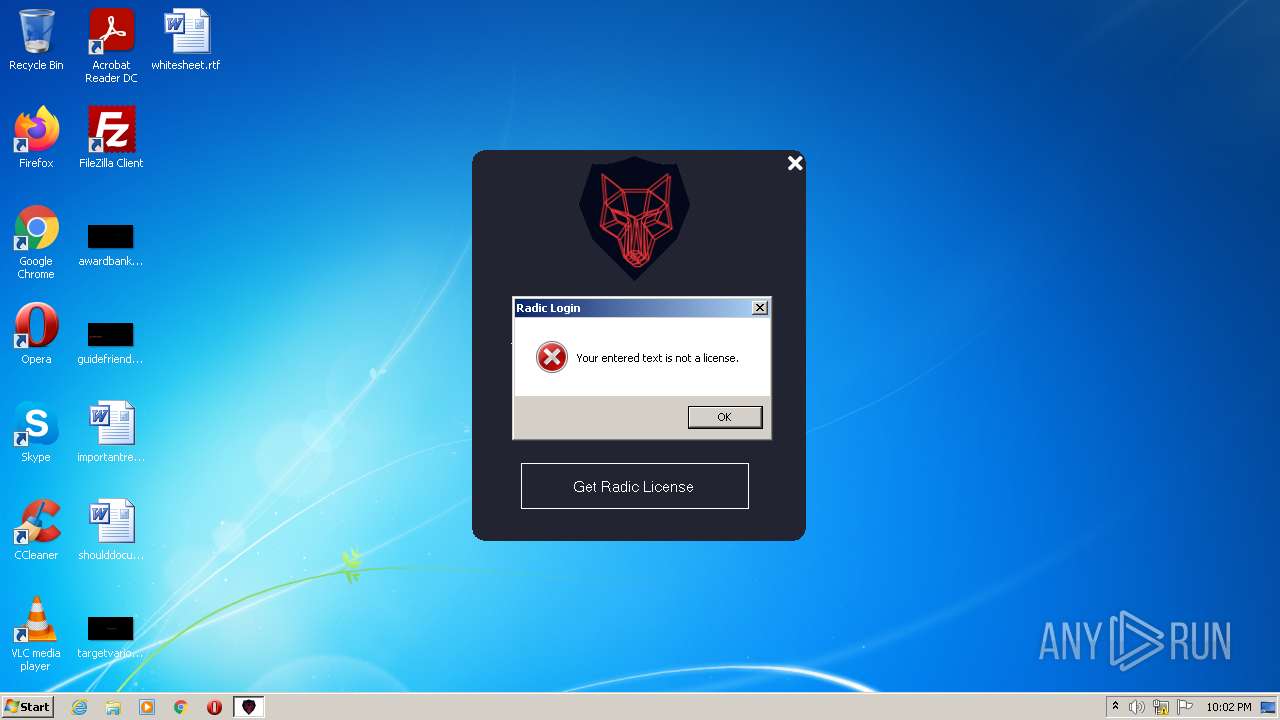
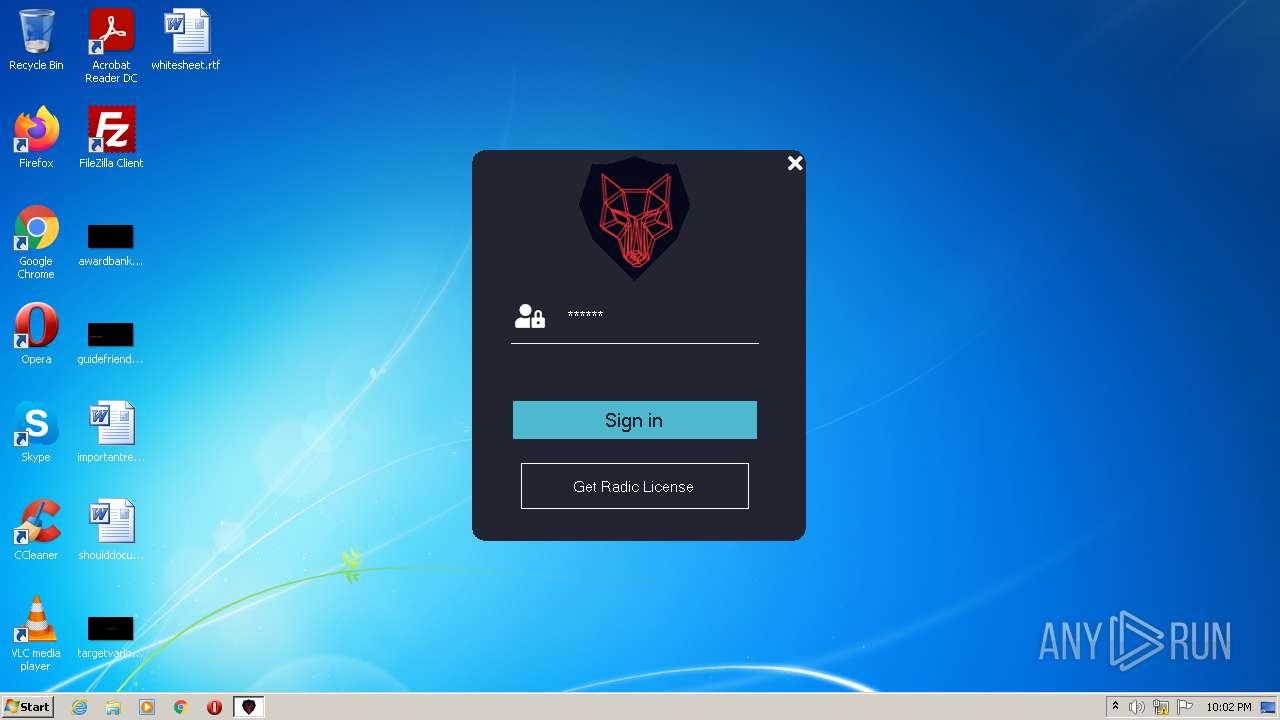
| Comments: | The launcher for the Radic GTA 5 Mod Menu! |
| CompanyName: | - |
| FileDescription: | Radic Launcher |
| FileVersion: | 1.0.0.0 |
| InternalName: | Radic Launcher.exe |
| LegalCopyright: | Copyright © 2022 |
| LegalTrademarks: | Radic Development |
| OriginalFilename: | Radic Launcher.exe |
| ProductName: | Radic Launcher |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 5 |
| TimeDateStamp: | 2022-Jul-30 18:57:07 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
\x14>&Z\x1a\x0f\x054 | 8192 | 1476824 | 1477120 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99987 |
.text | 1490944 | 49856 | 50176 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.25836 |
.rsrc | 1548288 | 143163 | 143360 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.49154 |
Section_4 | 1695744 | 16 | 512 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.142636 |
.reloc | 1703936 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.97693 | 38289 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 3.60671 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.85449 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.02369 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.26712 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.5984 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.79908 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 (#2) | 3.33212 | 960 | UNKNOWN | UNKNOWN | RT_VERSION |
1 (#3) | 5.09263 | 3683 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
40
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | "C:\Users\admin\AppData\Local\Temp\Radic.exe" | C:\Users\admin\AppData\Local\Temp\Radic.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: Radic Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
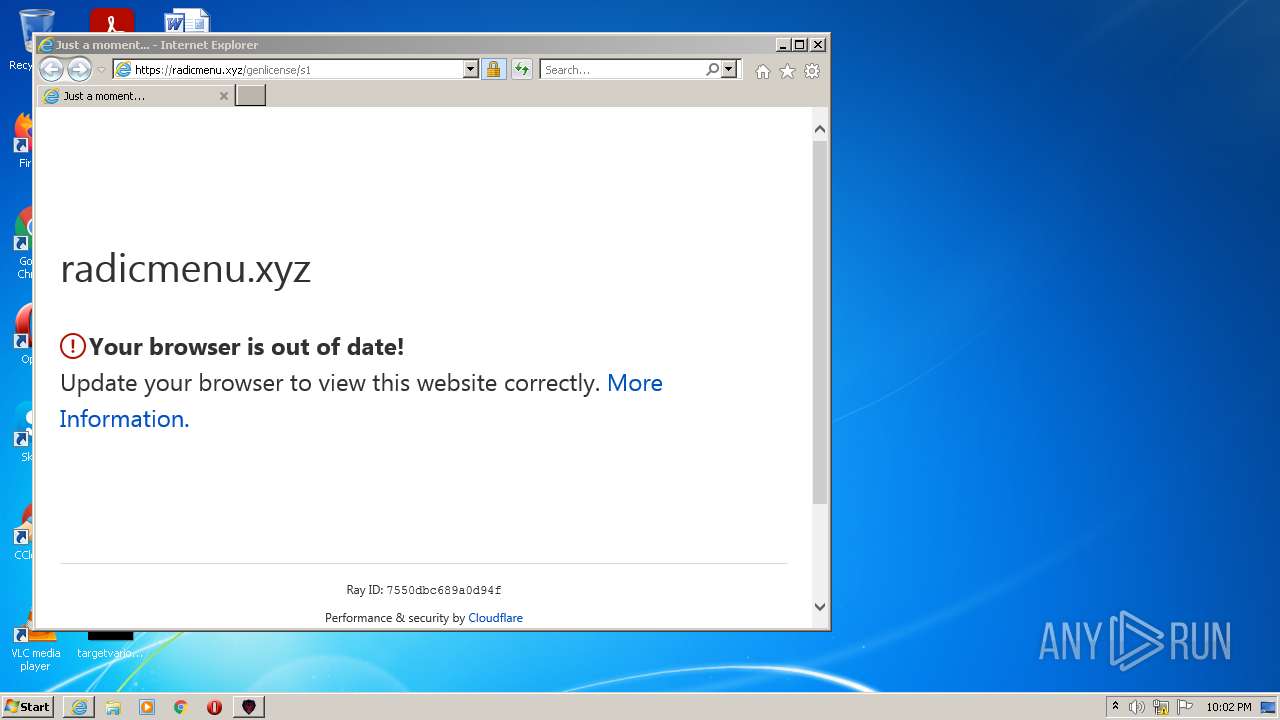
| 2076 | "C:\Program Files\Internet Explorer\iexplore.exe" https://radicmenu.xyz/genlicense/s1 | C:\Program Files\Internet Explorer\iexplore.exe | Radic.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2076 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3024 | "C:\Users\admin\AppData\Local\Temp\Radic.exe" | C:\Users\admin\AppData\Local\Temp\Radic.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Radic Launcher Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
19 586
Read events
19 457
Write events
128
Delete events
1
Modification events
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988340 | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988340 | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2076) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
16
Text files
11
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75814BCBAD95318DB3AF65FBC2678EB9 | der | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar77F5.tmp | cat | |
MD5:— | SHA256:— | |||
| 2076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75814BCBAD95318DB3AF65FBC2678EB9 | binary | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\challenges[1].css | text | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
19
DNS requests
12
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2692 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?66718e852d72a2c1 | US | compressed | 60.9 Kb | whitelisted |
2692 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?68eb1c49322ba3b9 | US | compressed | 4.70 Kb | whitelisted |
2692 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c4030856f5854bae | US | compressed | 60.9 Kb | whitelisted |
2692 | iexplore.exe | GET | 200 | 184.24.77.67:80 | http://e1.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBTvkAFw3ViPKmUeIVEf3NC7b1ErqwQUWvPtK%2Fw2wjd5uVIw6lRvz1XLLqwCEgQ9fEKDFEefMknhB07YBJLlyg%3D%3D | US | der | 346 b | whitelisted |
2692 | iexplore.exe | GET | 200 | 96.16.145.230:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
2692 | iexplore.exe | GET | 200 | 96.16.145.230:80 | http://x2.c.lencr.org/ | US | der | 300 b | whitelisted |
2692 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e21de2ed86390e33 | US | compressed | 60.9 Kb | whitelisted |
2076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2692 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bef54d0e759156ea | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2692 | iexplore.exe | 188.114.97.3:443 | radicmenu.xyz | CLOUDFLARENET | NL | malicious |
2692 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2692 | iexplore.exe | 96.16.145.230:80 | x1.c.lencr.org | AKAMAI-AS | DE | suspicious |
2692 | iexplore.exe | 184.24.77.67:80 | e1.o.lencr.org | Akamai International B.V. | DE | unknown |
2076 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2076 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
2076 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
radicmenu.xyz |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
e1.o.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2692 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2692 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |