| File name: | xuyao |
| Full analysis: | https://app.any.run/tasks/55166628-b8de-4027-a5c7-9c13b54e5c45 |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2024, 14:41:59 |
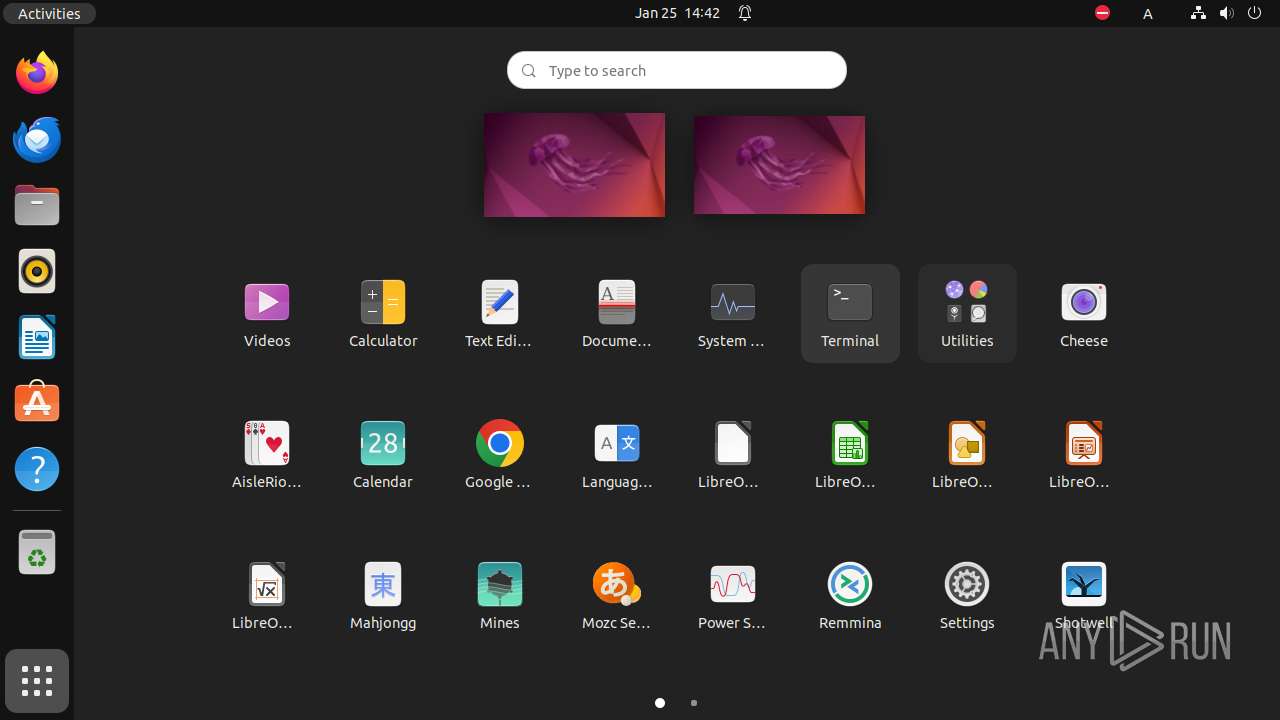
| OS: | Ubuntu 22.04.2 |
| MIME: | application/x-pie-executable |
| File info: | ELF 64-bit LSB pie executable, x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, BuildID[sha1]=5b9db3314147d71c79ff222376e4f664faeeb0ba, for GNU/Linux 3.2.0, not stripped |
| MD5: | 0B9C20BDF31D24CD67B57B44CDFE284B |
| SHA1: | 2A002007FA2BDF138819A7FFD082AB0392F64034 |
| SHA256: | 0C7E94CDEEF56D9111AEB413C6B260C5D5561E9016273D264FBF3D6FB52A2698 |
| SSDEEP: | 192:R5XwweMnuuuuuuudw4LPADt6oNbpj9f/DCKVYJ0lvhBHeQww/vi:jYQuuuuuuuddLPADt6ohXDX1hd |
MALICIOUS
No malicious indicators.SUSPICIOUS
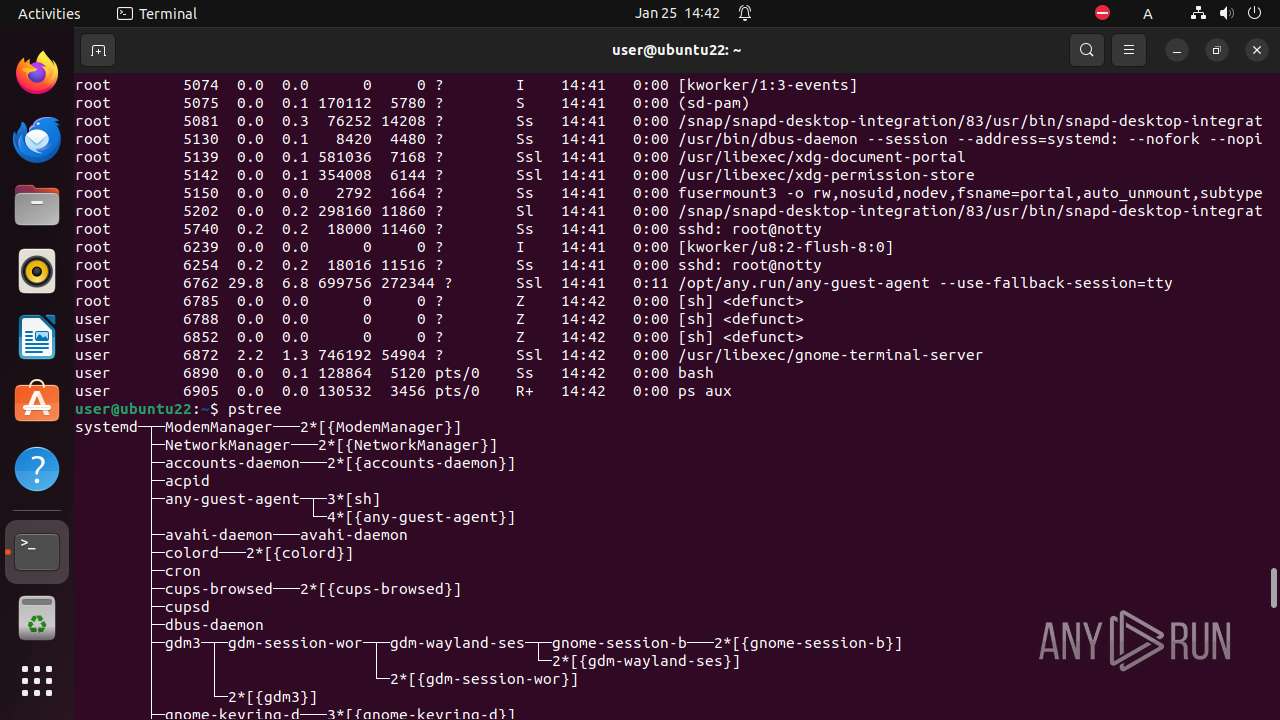
Modifies file or directory owner
- sudo (PID: 6853)
Checks system locale (may determine the language used by the system)
- xuyao.o (PID: 6857)
Changes file or directory permissions
- sh (PID: 6852)
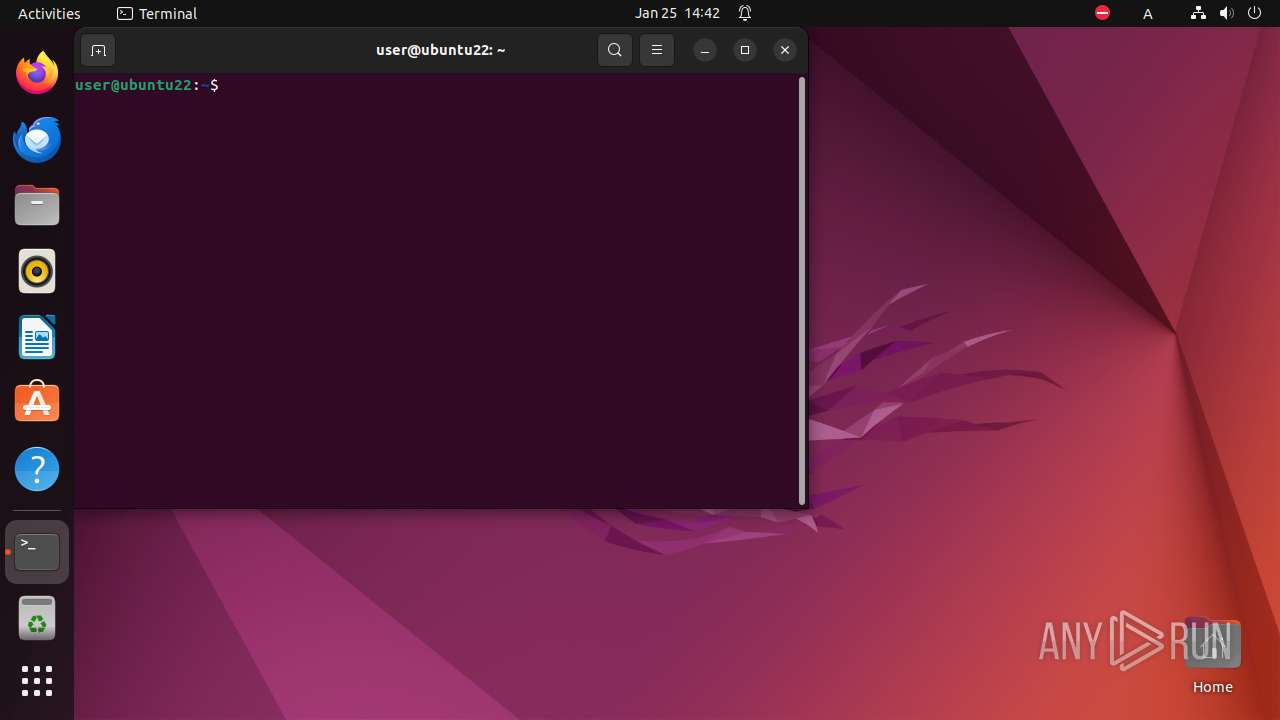
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 6872)
- bash (PID: 6859)
Reads passwd file
- id (PID: 6901)
- chown (PID: 6854)
- xuyao.o (PID: 6857)
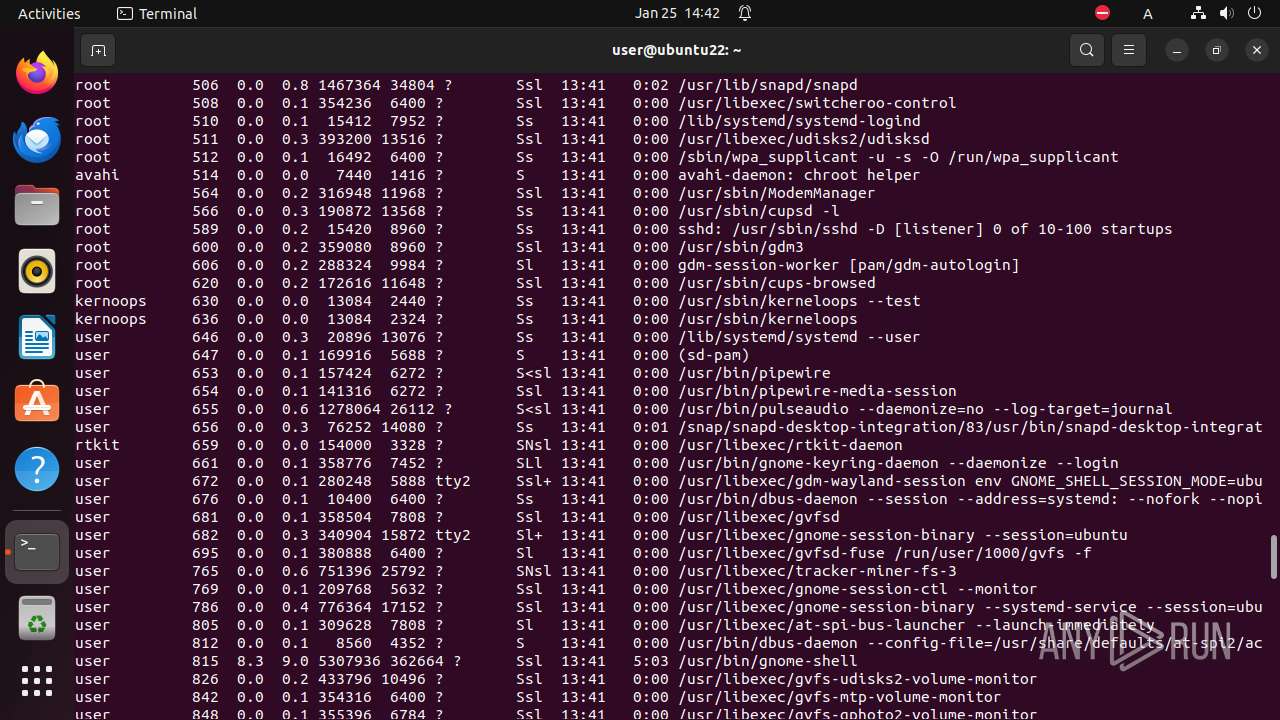
- ps (PID: 6905)
- bash (PID: 6890)
- whoami (PID: 6902)
- ps (PID: 6904)
Checks timezone
- ps (PID: 6905)
- gnome-terminal (PID: 6864)
- ps (PID: 6904)
Checks how long the system has been running
- bash (PID: 6890)
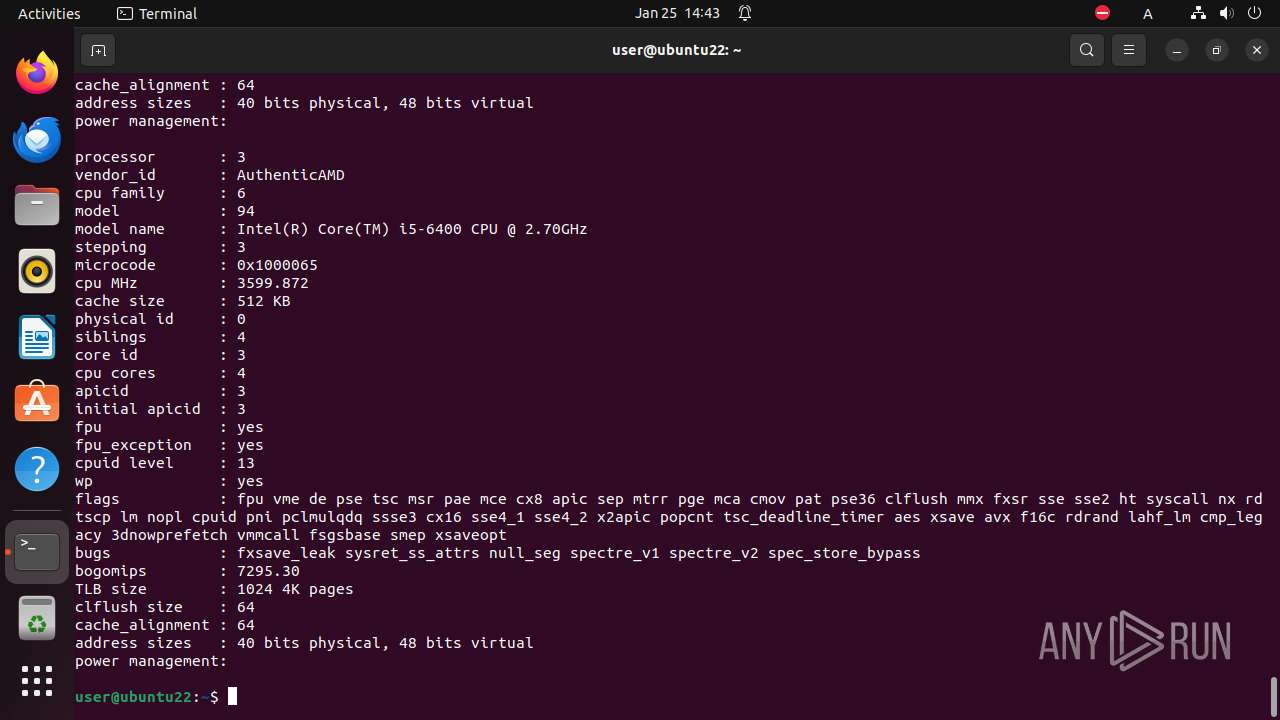
Gets information about CPU, Memory or Filesystem
- bash (PID: 6890)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (49.8) |
|---|
EXIF
EXE
| CPUArchitecture: | 64 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Shared object file |
| CPUType: | AMD x86-64 |
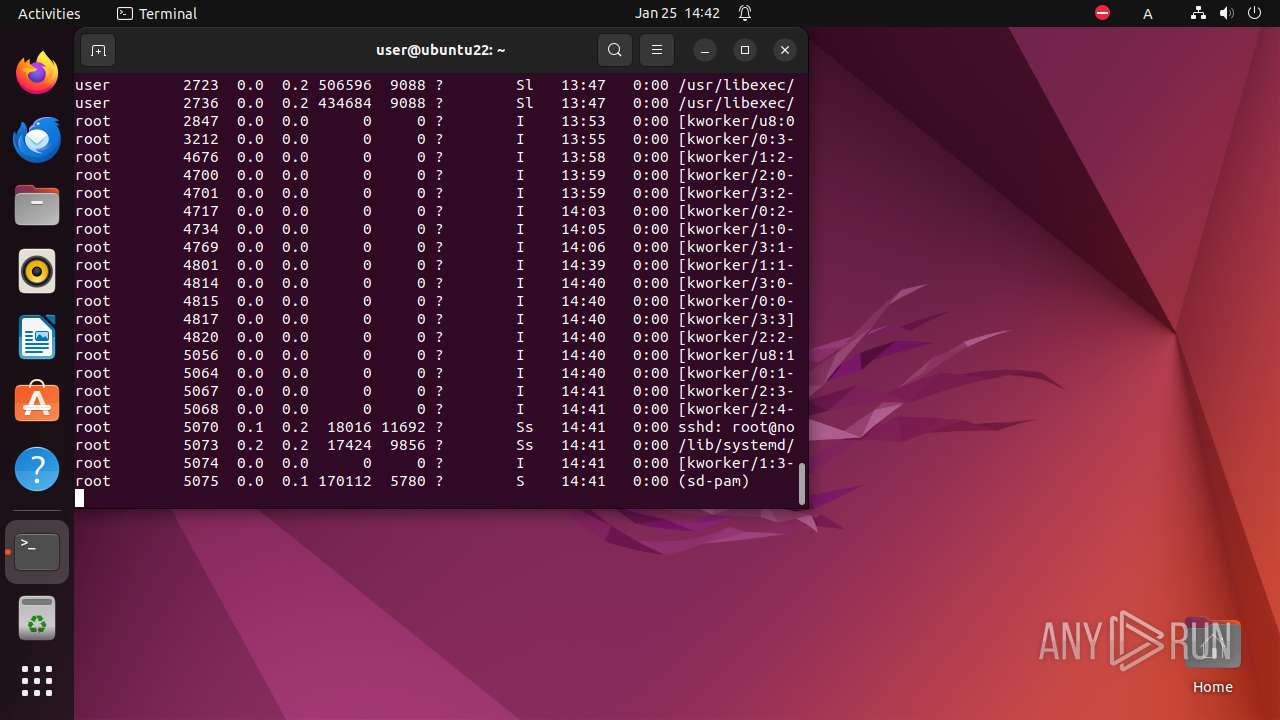
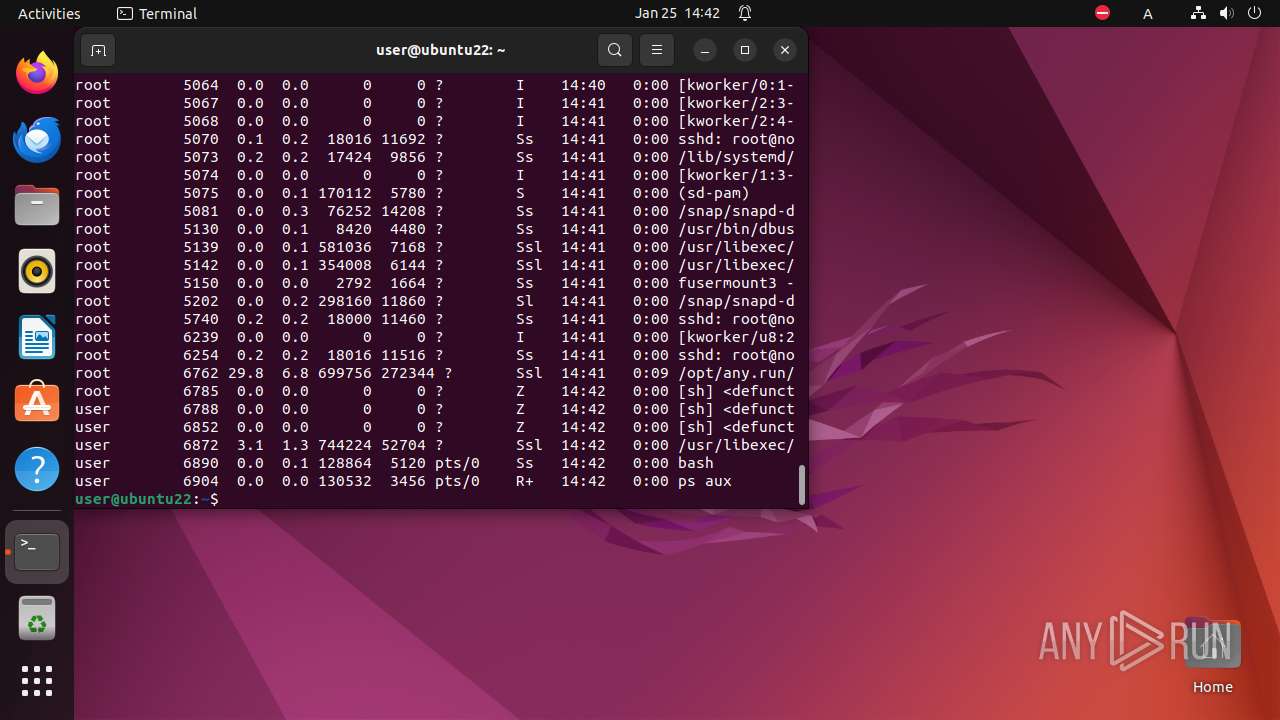
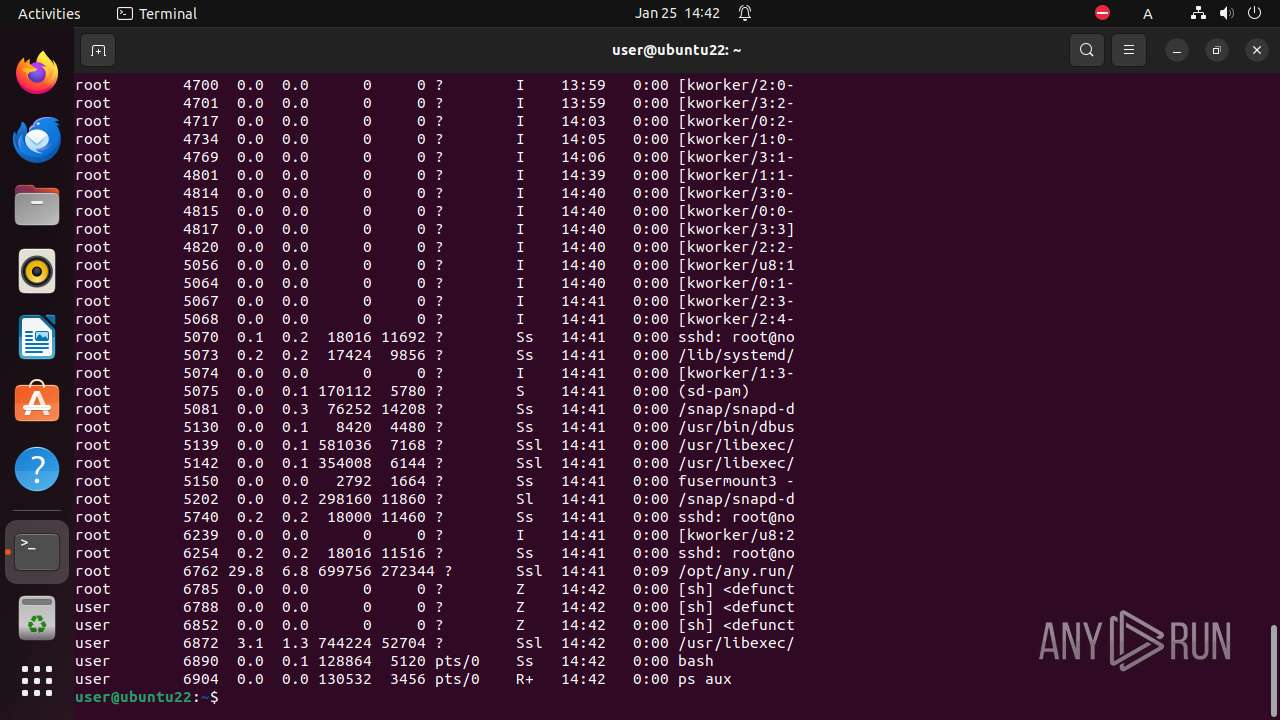
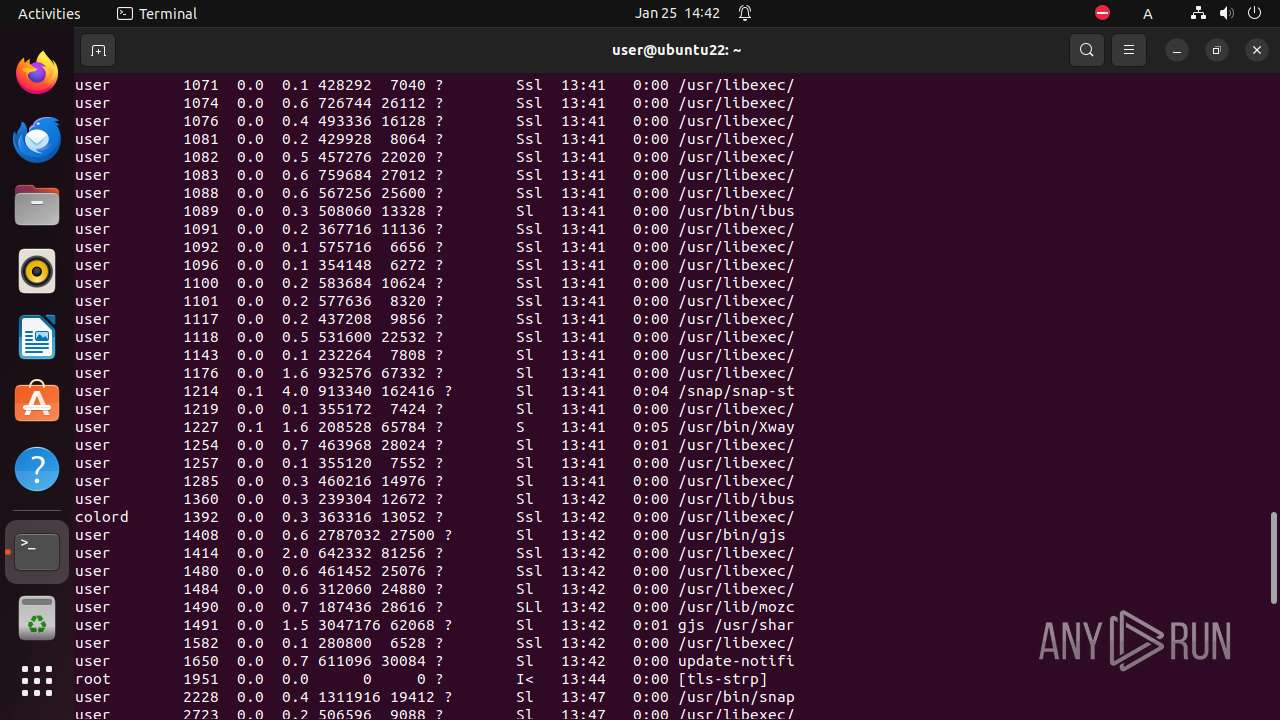
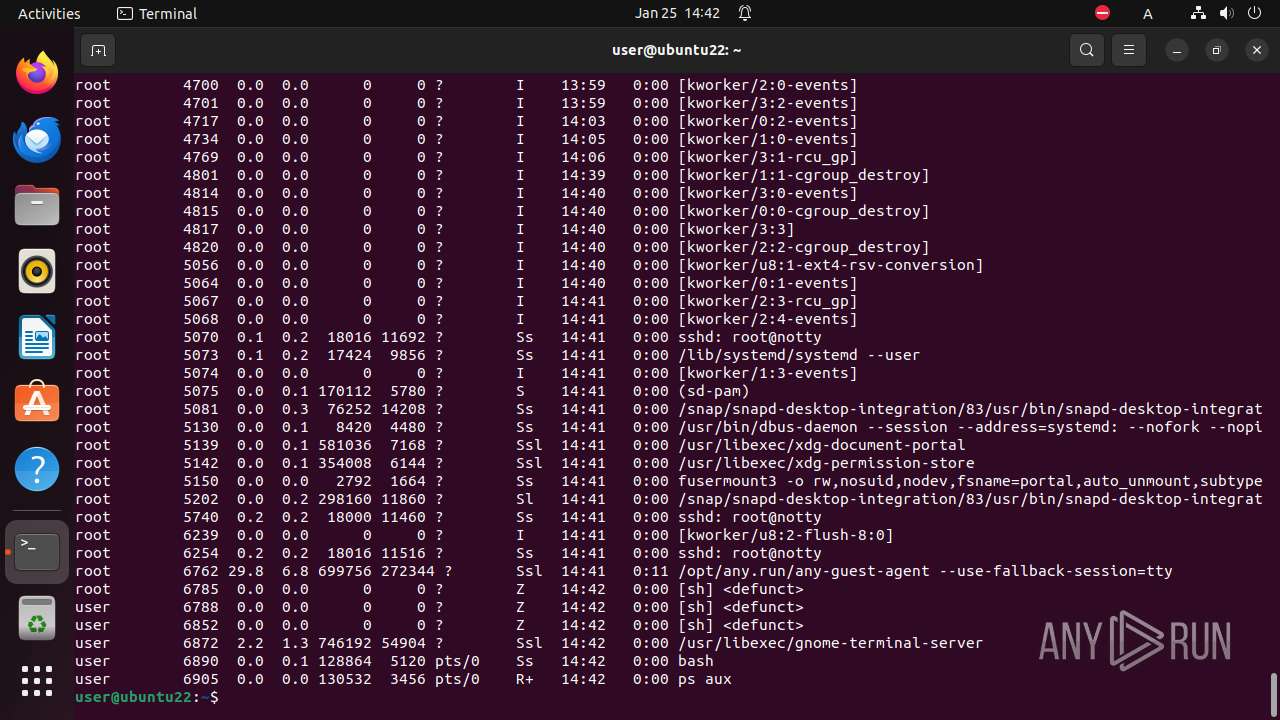
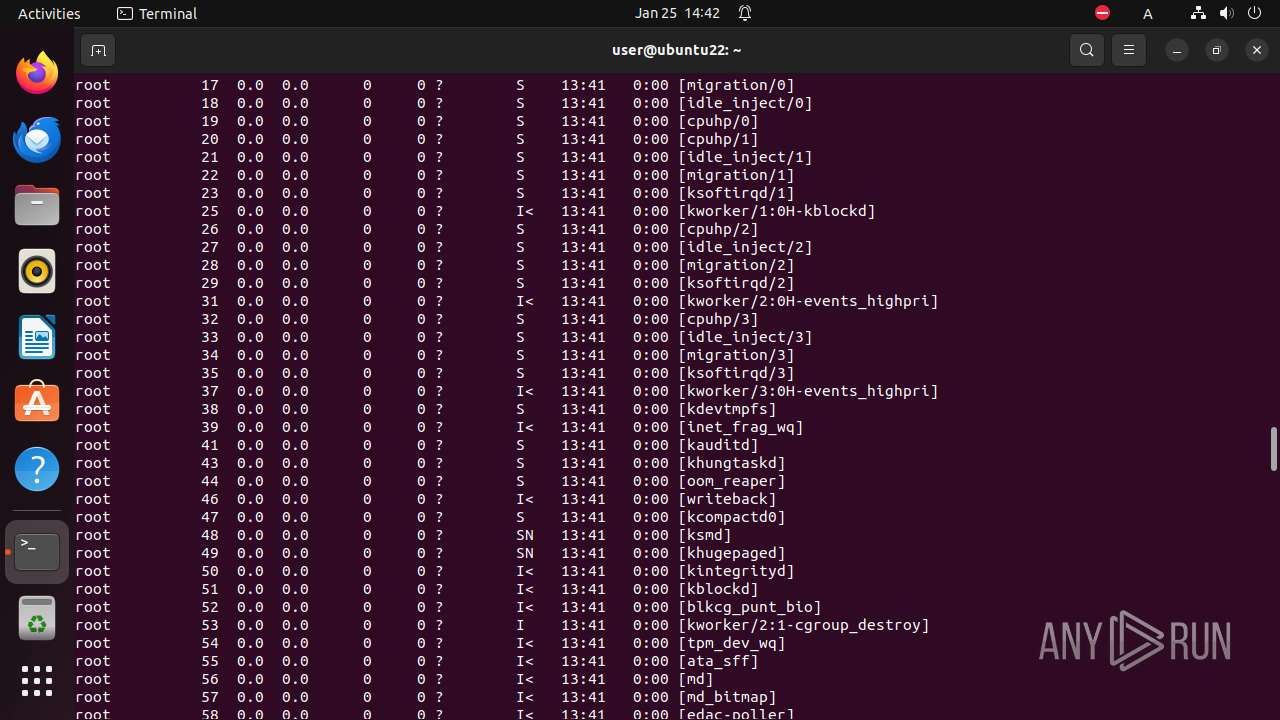
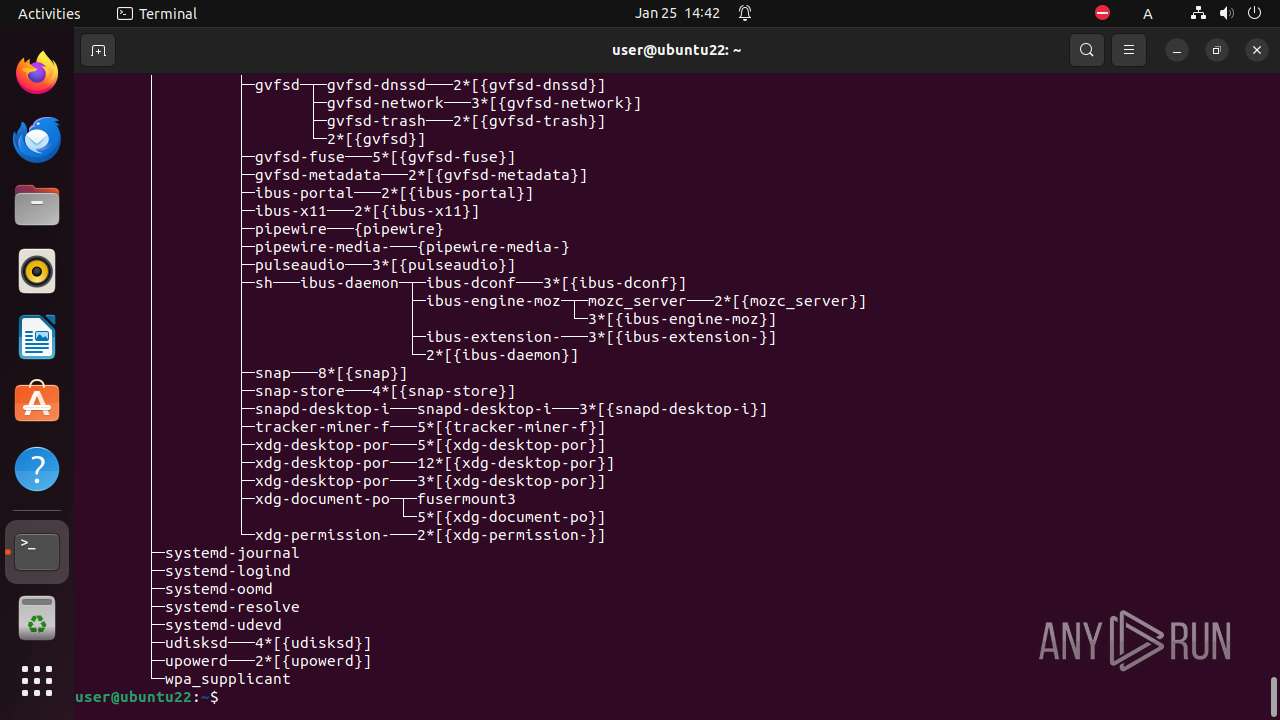
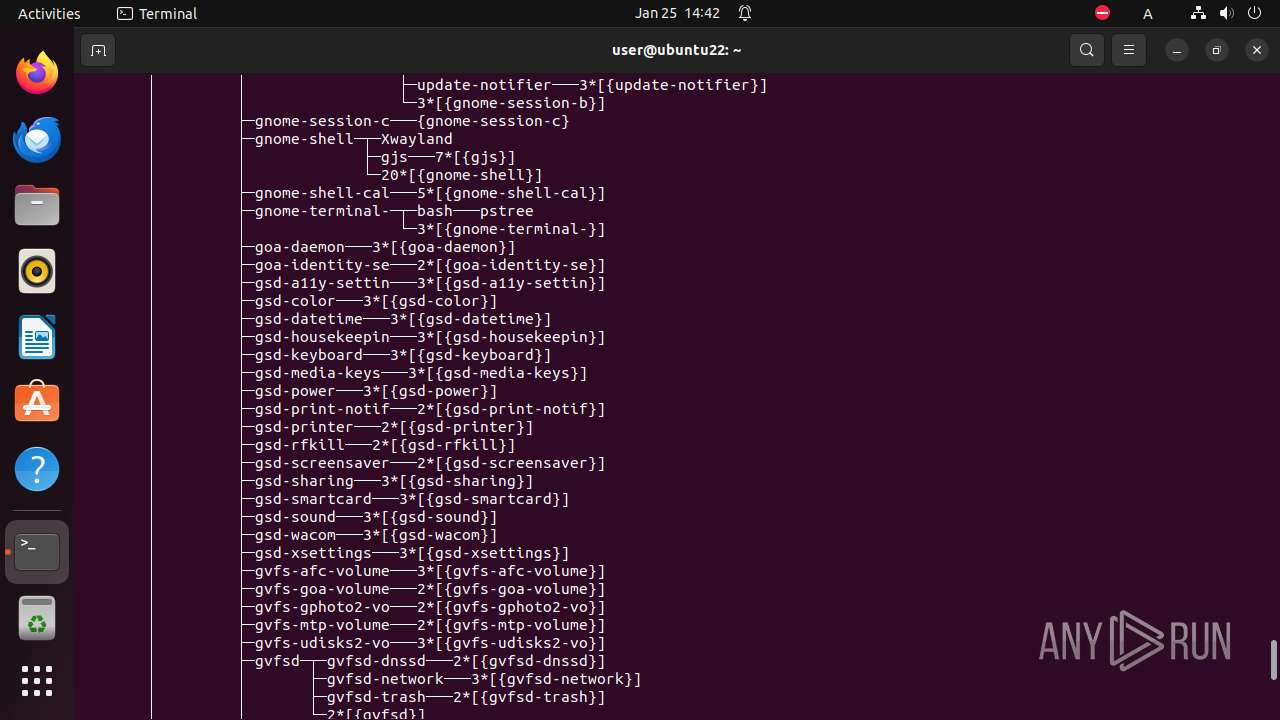
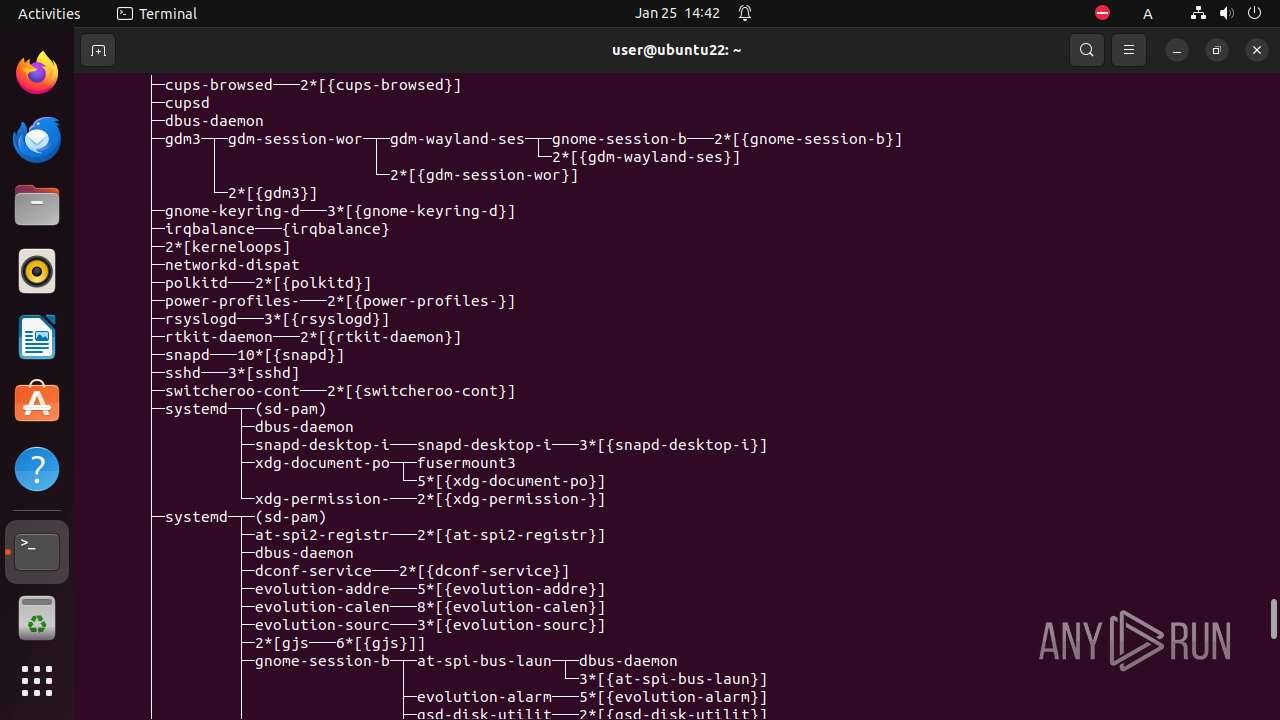
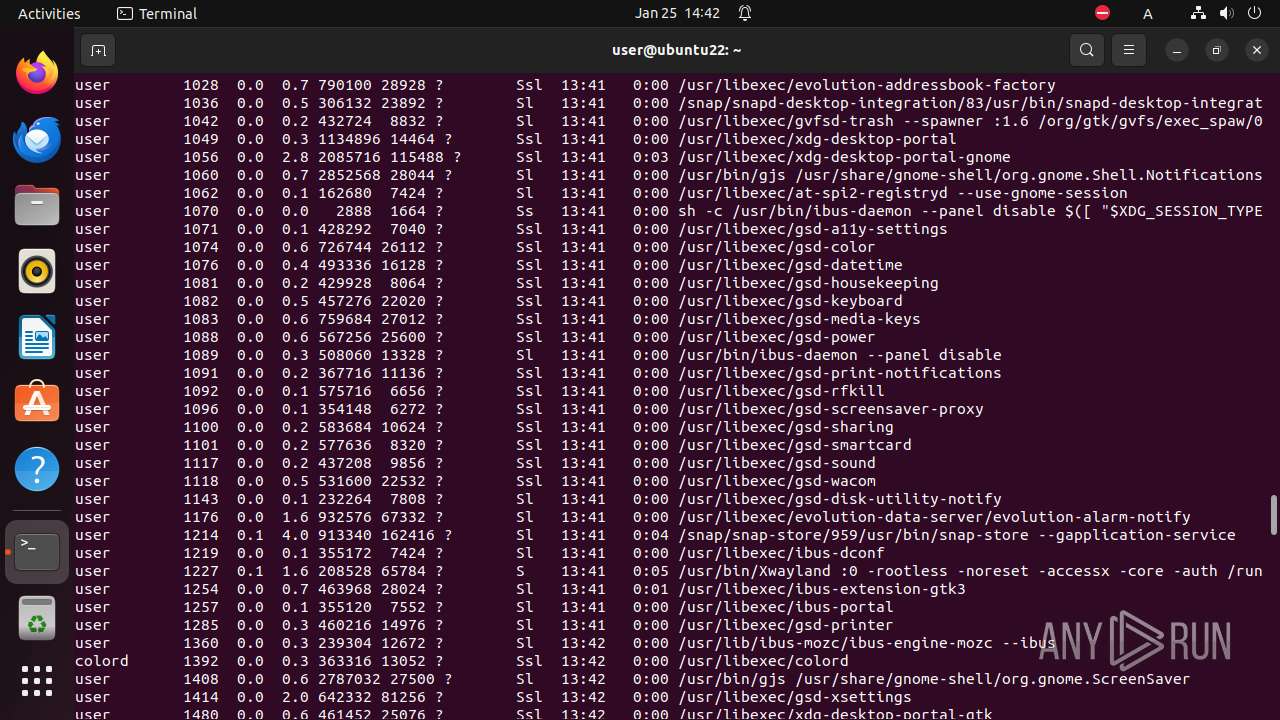
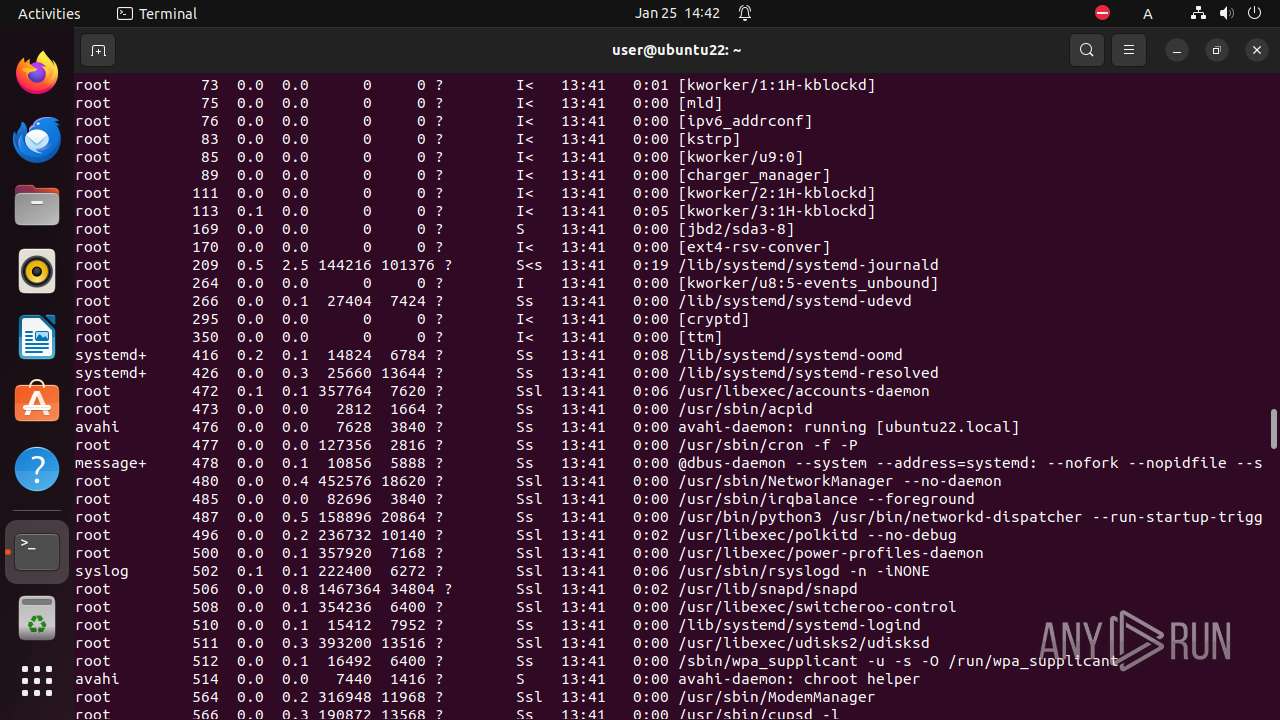
Total processes
249
Monitored processes
33
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
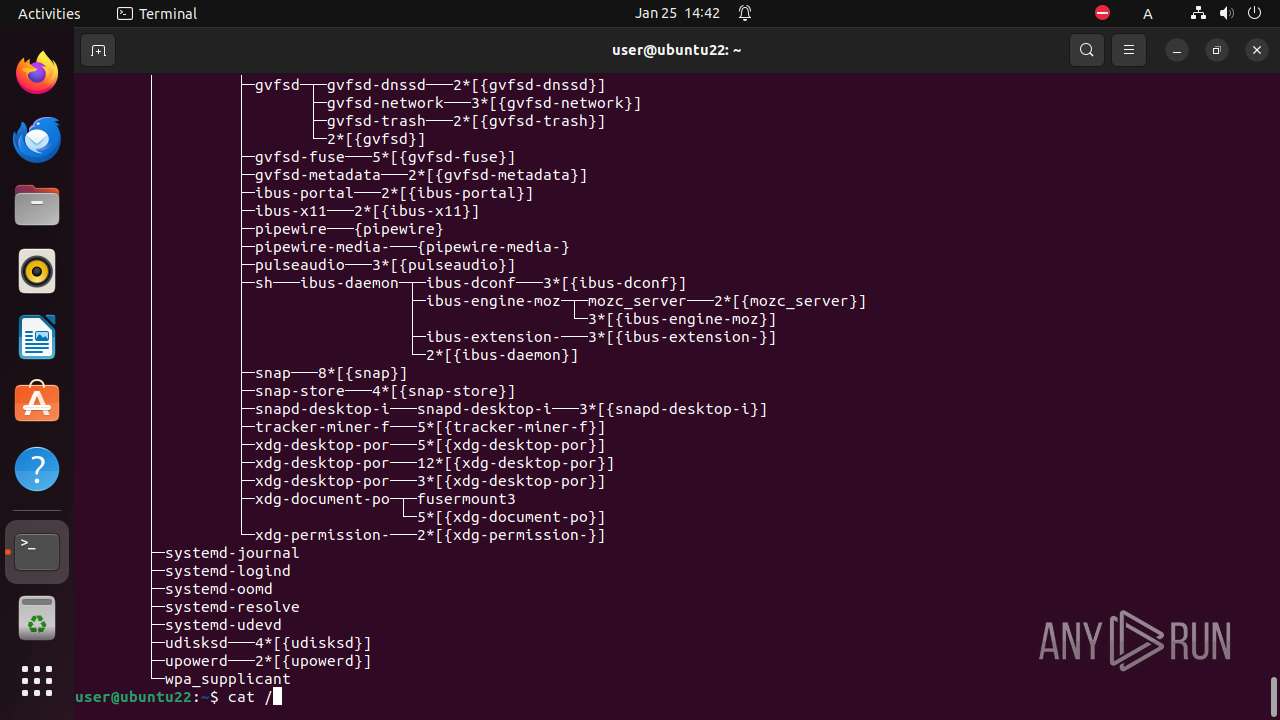
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
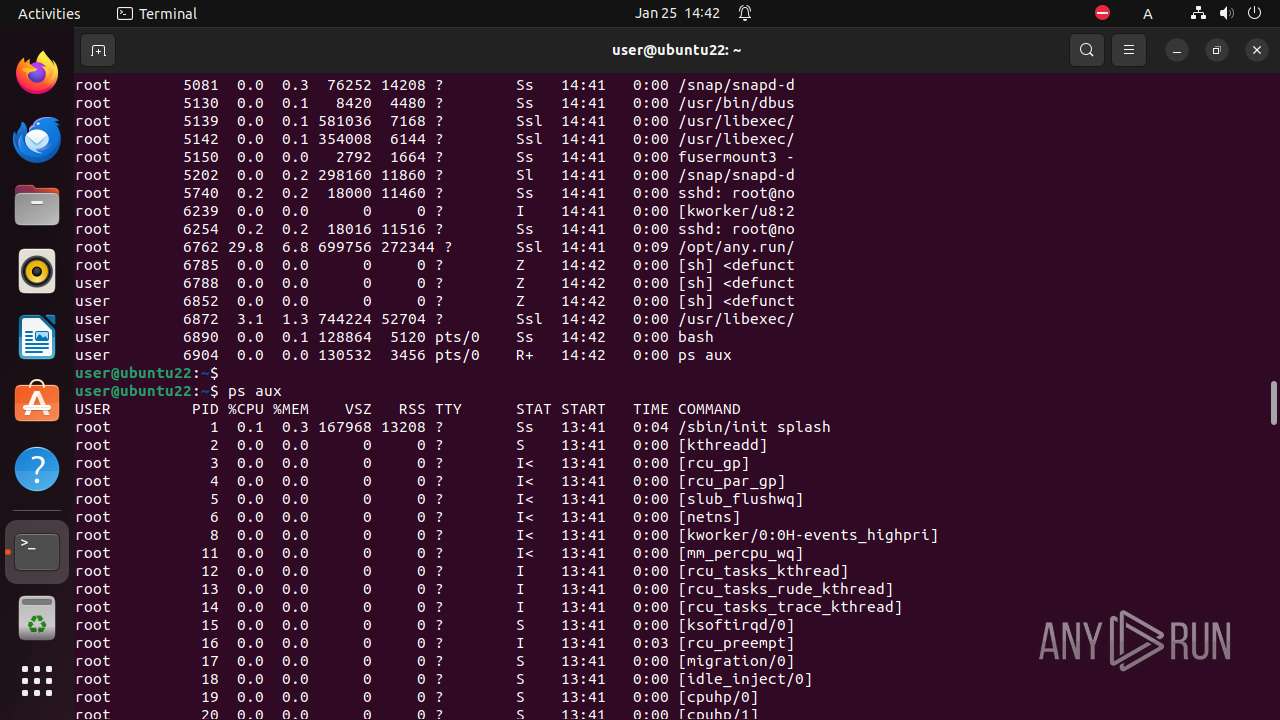
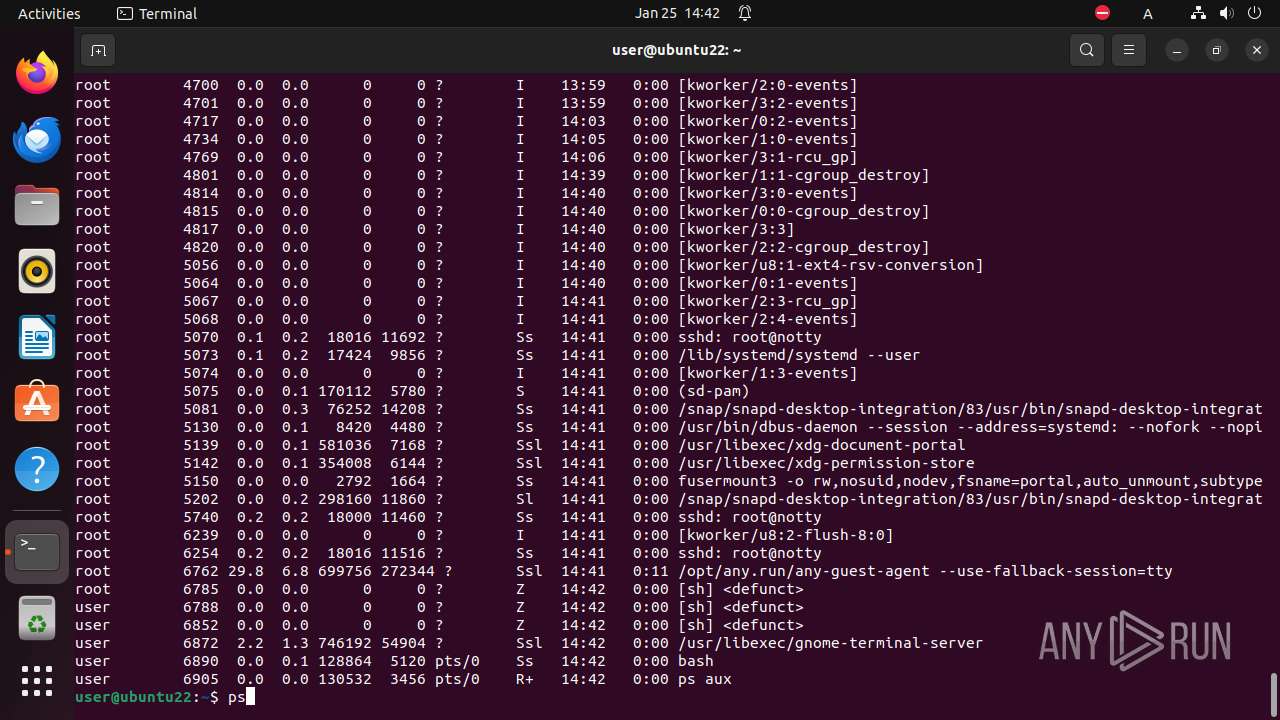
| 6852 | /bin/sh -c "sudo chown user \"/tmp/xuyao\.o\" && chmod +x \"/tmp/xuyao\.o\" && DISPLAY=:0 sudo -i \"/tmp/xuyao\.o\" " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 6762 | ||||
| 6853 | sudo chown user /tmp/xuyao.o | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6854 | chown user /tmp/xuyao.o | /usr/bin/chown | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6855 | chmod +x /tmp/xuyao.o | /usr/bin/chmod | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6856 | sudo -i /tmp/xuyao.o | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 6762 | ||||
| 6857 | /tmp/xuyao.o | /tmp/xuyao.o | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 6762 | ||||
| 6858 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | xuyao.o |
User: root Integrity Level: UNKNOWN Exit code: 1214 | ||||
| 6859 | -bash --login -c \/tmp\/xuyao\.o | /usr/bin/bash | — | xuyao.o |
User: root Integrity Level: UNKNOWN Exit code: 1214 | ||||
| 6860 | sh -c "cat /usr/etc/debuginfod/*\.urls 2>/dev/null" | /usr/bin/sh | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 1214 | ||||
| 6861 | tr \n " " | /usr/bin/tr | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 1214 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
54.100.168.192.in-addr.arpa |
| unknown |
connectivity-check.ubuntu.com |
| unknown |