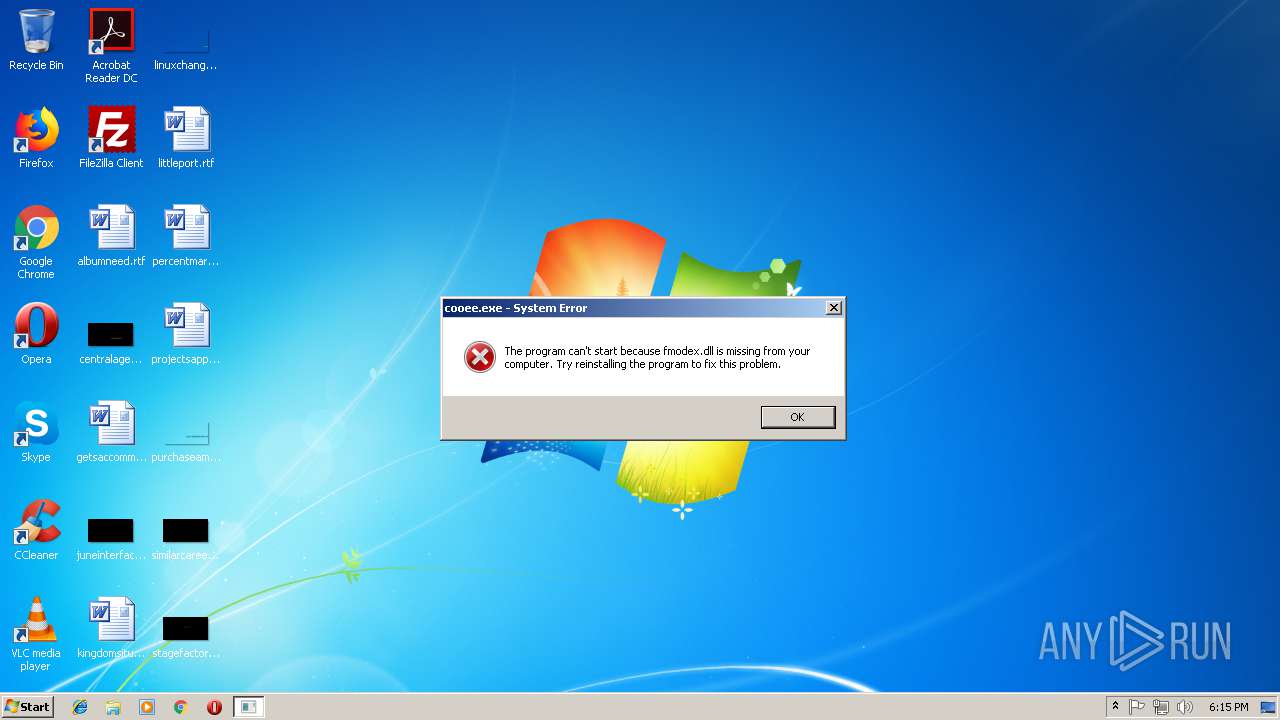
| File name: | cooee.exe |
| Full analysis: | https://app.any.run/tasks/c988c557-a665-40aa-89f5-f53e52968091 |
| Verdict: | No threats detected |
| Analysis date: | October 20, 2018, 17:15:23 |
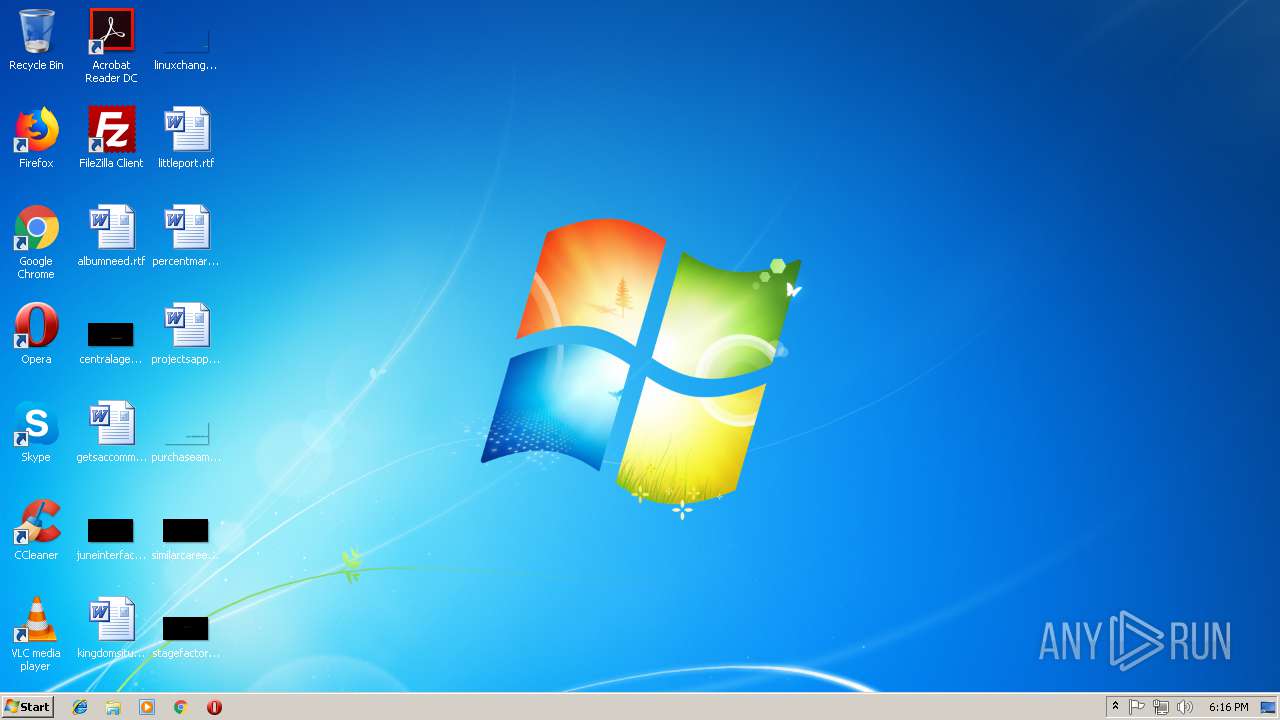
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1755FC12B1F72167C069AAF3E299CEAB |
| SHA1: | 9B66438BD2EED17E9A5DB4BC92152798E8814743 |
| SHA256: | 0C7A48EF79B559BF029B77CAB757E37E89B4E25931D7FCD4080A182A60B4D3E4 |
| SSDEEP: | 196608:wYaG2TuR1DXRfVUykWJHD2NGS0f5BSroM86:wYaG/Hi7rR86 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
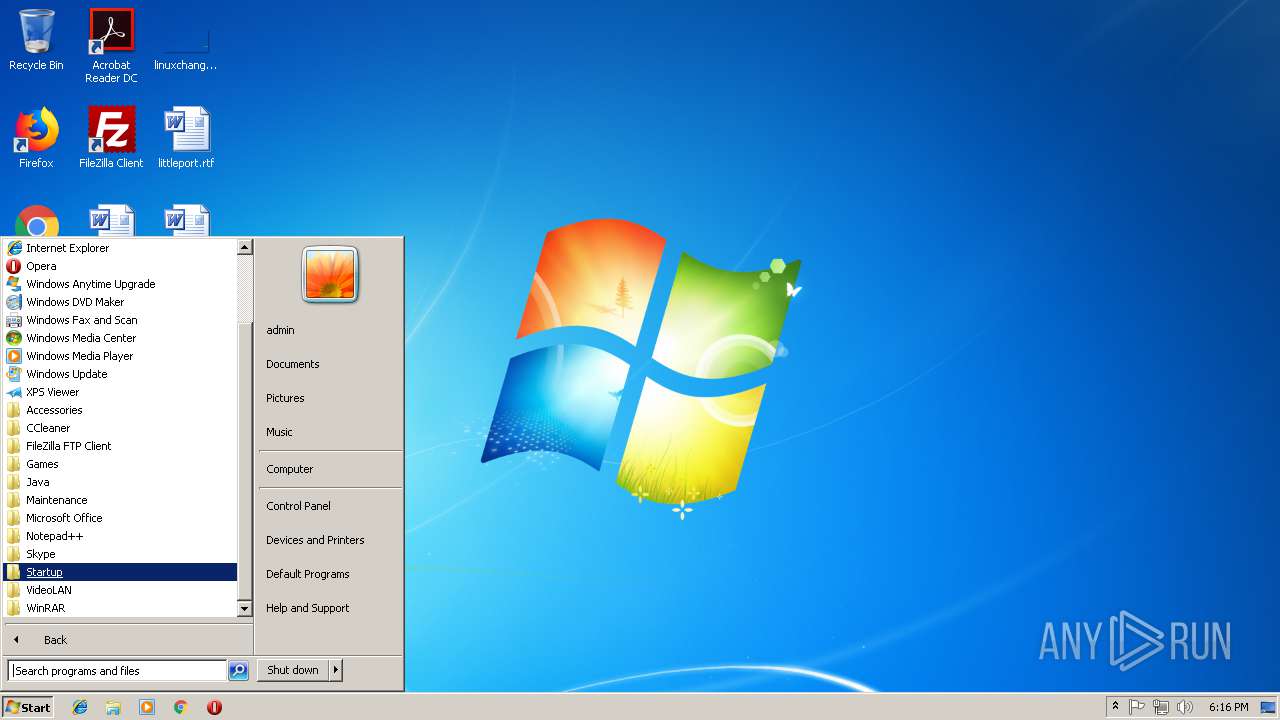
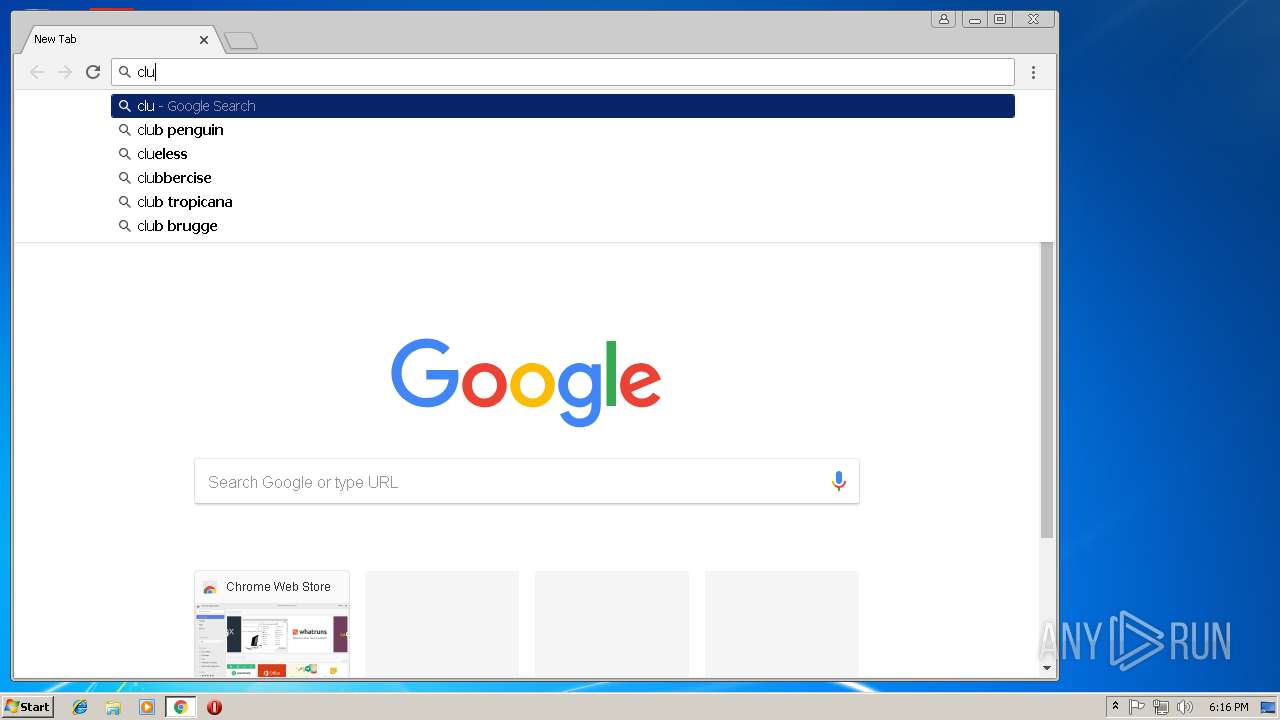
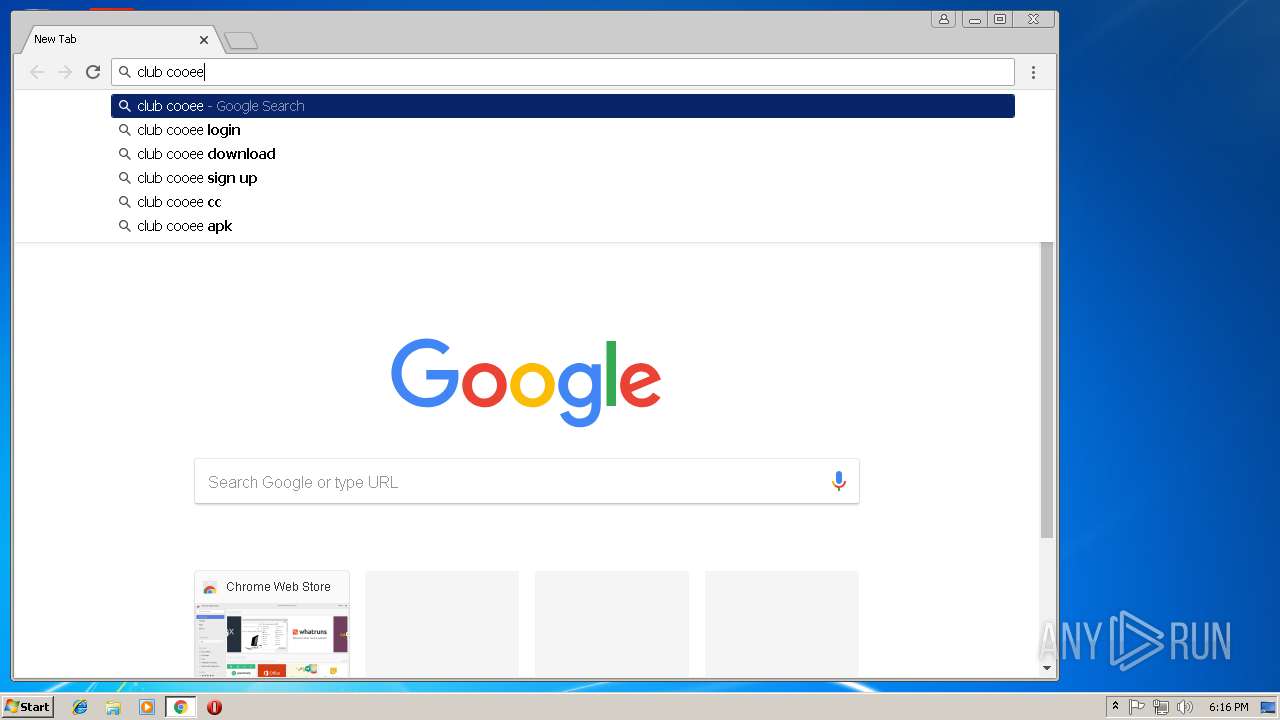
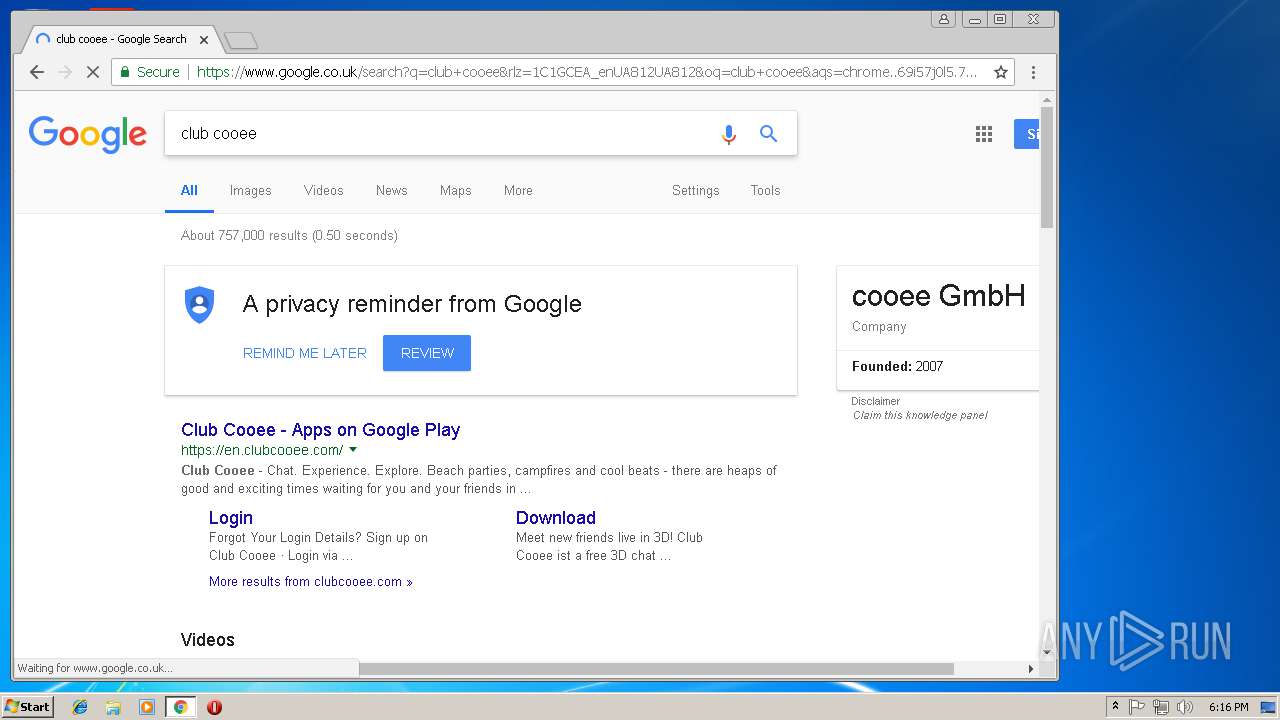
Application launched itself
- chrome.exe (PID: 3112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:11 08:40:28+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 6188032 |
| InitializedDataSize: | 7487488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x355606 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.8.76.0 |
| ProductVersionNumber: | 1.8.76.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | cooee GmbH |
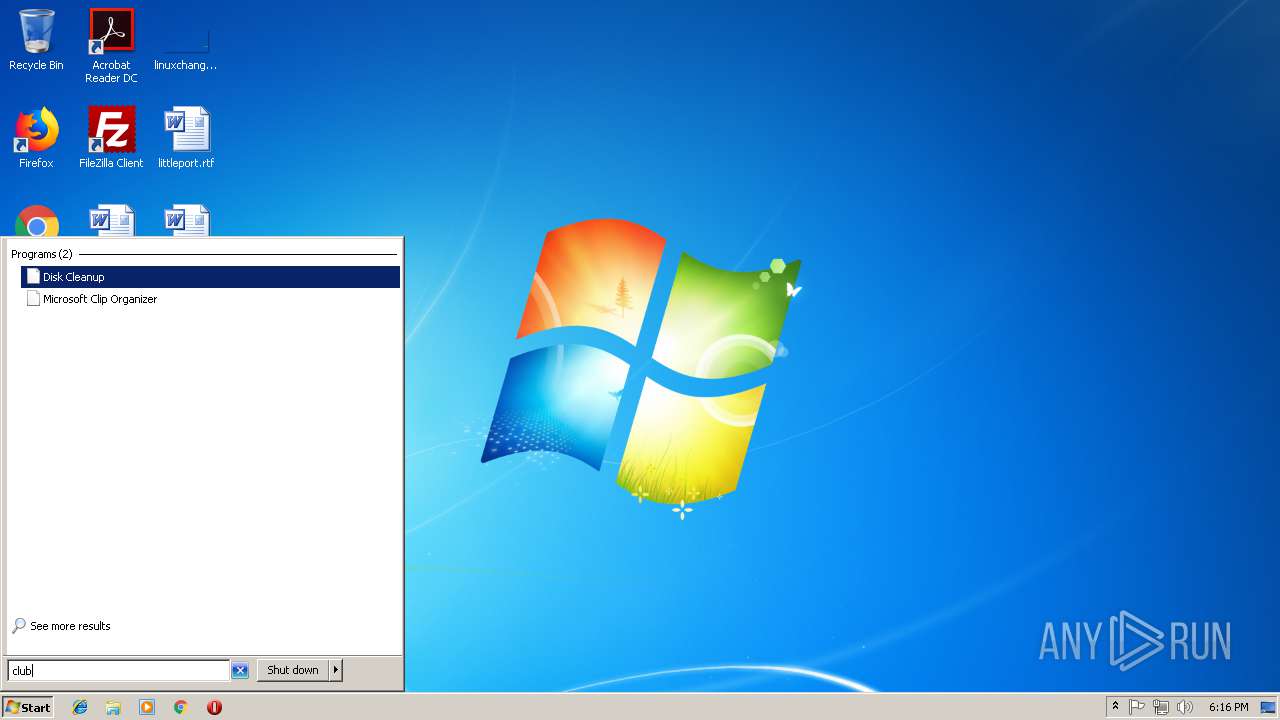
| FileDescription: | Club Cooee Client Application |
| FileVersion: | 1.8.76.0 |
| InternalName: | cooee |
| LegalCopyright: | (c) cooee GmbH |
| OriginalFileName: | cooee.exe |
| ProductName: | Club Cooee |
| ProductVersion: | 1.8.76.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Oct-2018 06:40:28 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | cooee GmbH |
| FileDescription: | Club Cooee Client Application |
| FileVersion: | 1.8.76.0 |
| InternalName: | cooee |
| LegalCopyright: | (c) cooee GmbH |
| OriginalFilename: | cooee.exe |
| ProductName: | Club Cooee |
| ProductVersion: | 1.8.76.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000138 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Oct-2018 06:40:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x005E6B92 | 0x005E6C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57944 |
.rdata | 0x005E8000 | 0x000BD9B2 | 0x000BDA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.37596 |
.data | 0x006A6000 | 0x00622020 | 0x005E3400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.90814 |
.rsrc | 0x00CC9000 | 0x000063EC | 0x00006400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.13858 |
.reloc | 0x00CD0000 | 0x0007CC24 | 0x0007CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.30114 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27698 | 1011 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.38331 | 4264 | Latin 1 / Western European | German - Germany | RT_ICON |
3 | 6.19276 | 1128 | Latin 1 / Western European | German - Germany | RT_ICON |
4 | 5.33347 | 1128 | Latin 1 / Western European | German - Germany | RT_ICON |
5 | 5.38388 | 1128 | Latin 1 / Western European | German - Germany | RT_ICON |
6 | 5.19144 | 1128 | Latin 1 / Western European | German - Germany | RT_ICON |
7 | 4.58758 | 1128 | Latin 1 / Western European | German - Germany | RT_ICON |
8 | 4.77389 | 1128 | Latin 1 / Western European | German - Germany | RT_ICON |
9 | 5.80626 | 1128 | Latin 1 / Western European | German - Germany | RT_ICON |
10 | 1.72161 | 748 | Latin 1 / Western European | German - Germany | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
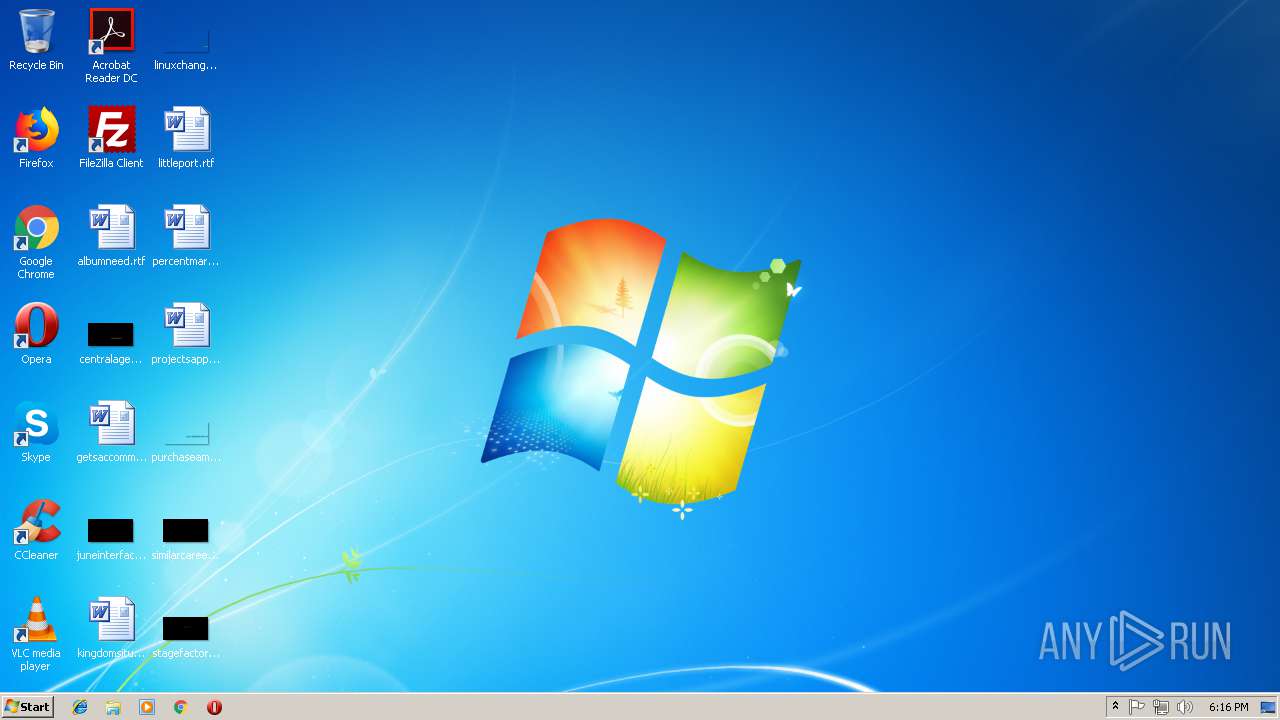
Total processes
44
Monitored processes
13
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=916,12388578483578348880,8626921971078520351,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=F7C084821F9017E358DBDEB79F679759 --mojo-platform-channel-handle=904 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,12388578483578348880,8626921971078520351,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=678CC4AA49FDD39DBF6BD6088007A683 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=678CC4AA49FDD39DBF6BD6088007A683 --renderer-client-id=8 --mojo-platform-channel-handle=3792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,12388578483578348880,8626921971078520351,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=53A21026E9DF5DE53573F11F62FBE2FD --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=53A21026E9DF5DE53573F11F62FBE2FD --renderer-client-id=6 --mojo-platform-channel-handle=3576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=916,12388578483578348880,8626921971078520351,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D292472ABFCFD06350923BB2474091F4 --mojo-platform-channel-handle=1668 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,12388578483578348880,8626921971078520351,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=AFCC44EADCC3BEC5F77B4A2C7E8BD977 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=AFCC44EADCC3BEC5F77B4A2C7E8BD977 --renderer-client-id=9 --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3264 | "C:\Users\admin\AppData\Local\Temp\cooee.exe" | C:\Users\admin\AppData\Local\Temp\cooee.exe | — | explorer.exe | |||||||||||
User: admin Company: cooee GmbH Integrity Level: MEDIUM Description: Club Cooee Client Application Exit code: 3221225781 Version: 1.8.76.0 Modules
| |||||||||||||||
| 3380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,12388578483578348880,8626921971078520351,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=913FA7C669C3504CD6971C3CD3D00385 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=913FA7C669C3504CD6971C3CD3D00385 --renderer-client-id=10 --mojo-platform-channel-handle=3576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,12388578483578348880,8626921971078520351,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=831658BF4C7F213707239D573861AAB0 --mojo-platform-channel-handle=3772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,12388578483578348880,8626921971078520351,131072 --enable-features=PasswordImport --service-pipe-token=D51CA545C871D65D7BAAE86085E954B6 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D51CA545C871D65D7BAAE86085E954B6 --renderer-client-id=5 --mojo-platform-channel-handle=1884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
128
Read events
87
Write events
38
Delete events
3
Modification events
| (PID) Process: | (3112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3112-13184529392140250 |
Value: 259 | |||
| (PID) Process: | (3112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3112) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3112-13184529392140250 |
Value: 259 | |||
| (PID) Process: | (3112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
47
Text files
50
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\219dad1d-52e1-441e-96ec-f33845fc4c33.tmp | — | |
MD5:— | SHA256:— | |||
| 3112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a0e3da75-39b4-4f65-8d5a-f93f5086ea81.tmp | — | |
MD5:— | SHA256:— | |||
| 3112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 3112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3112 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF5cc4a8.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
31
DNS requests
20
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3112 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 172.217.16.163:443 | www.google.de | Google Inc. | US | whitelisted |
3112 | chrome.exe | 172.217.16.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 172.217.22.78:443 | apis.google.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 216.58.205.226:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
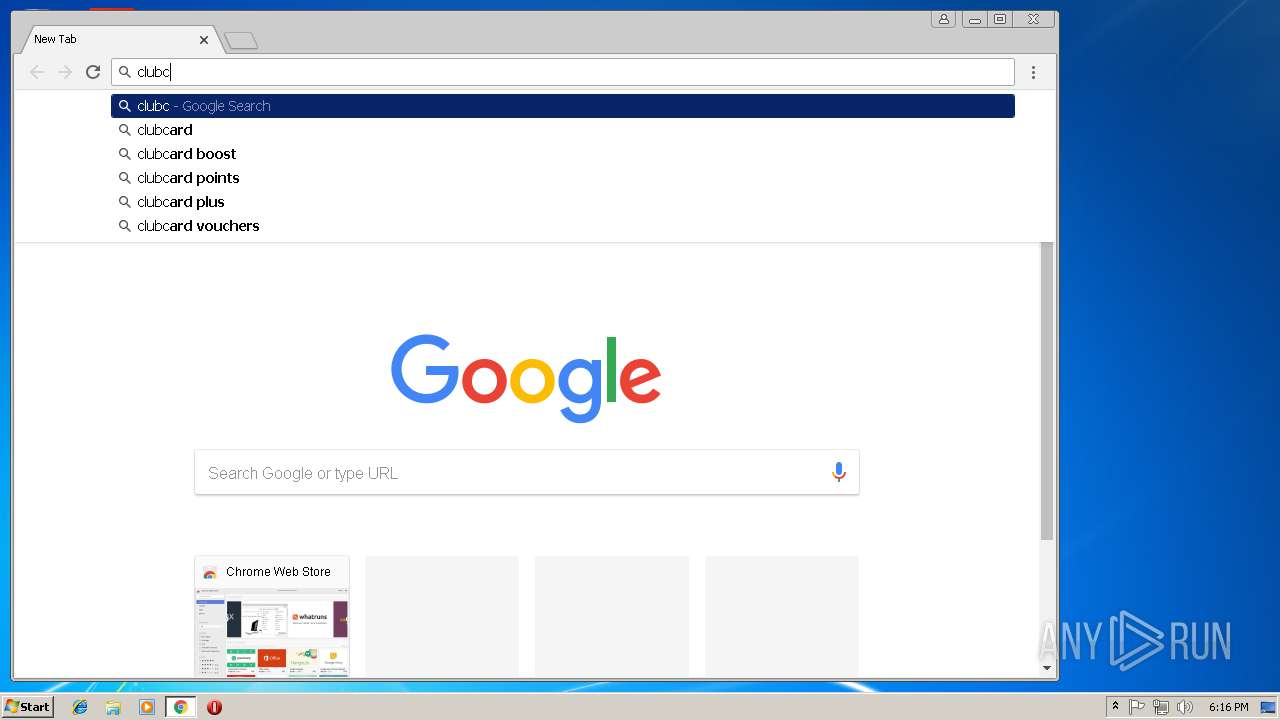
3112 | chrome.exe | 138.201.83.142:443 | en.clubcooee.com | Hetzner Online GmbH | DE | unknown |
3112 | chrome.exe | 216.58.207.34:443 | adservice.google.co.uk | Google Inc. | US | whitelisted |
3112 | chrome.exe | 62.113.194.2:443 | cdn.clubcooee.com | 23media GmbH | DE | malicious |
3112 | chrome.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |
fonts.googleapis.com |
| whitelisted |