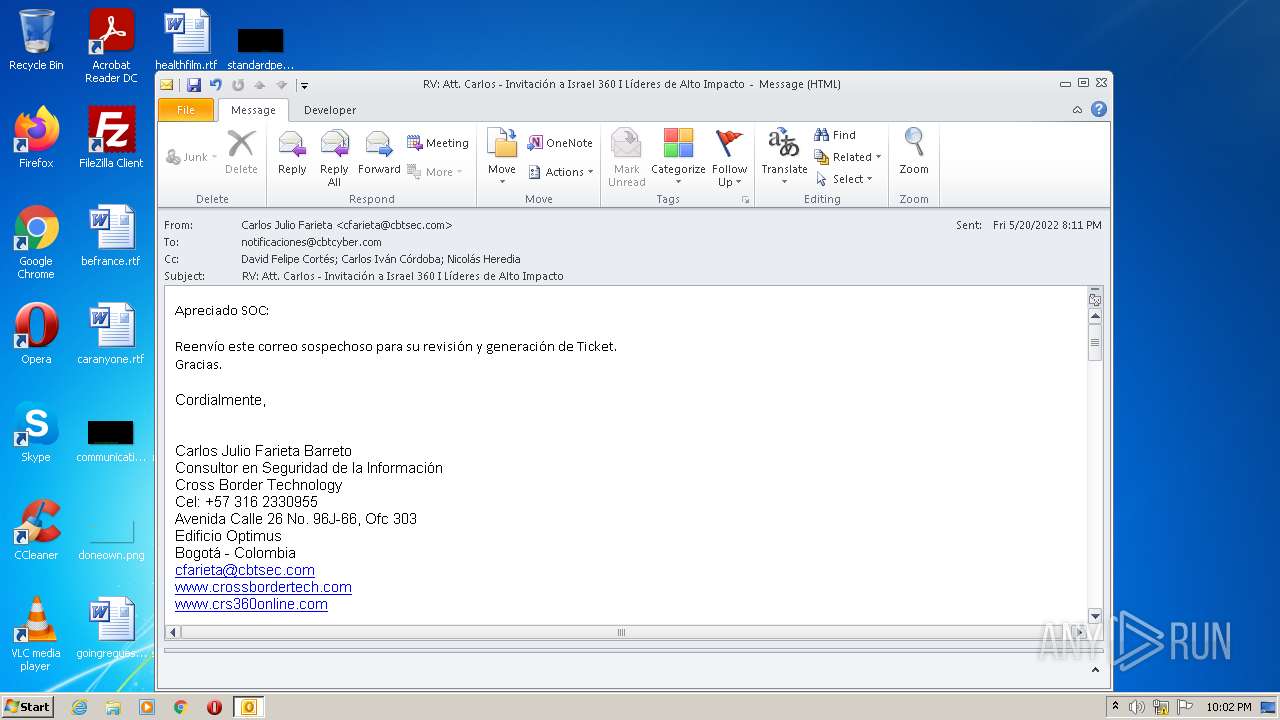
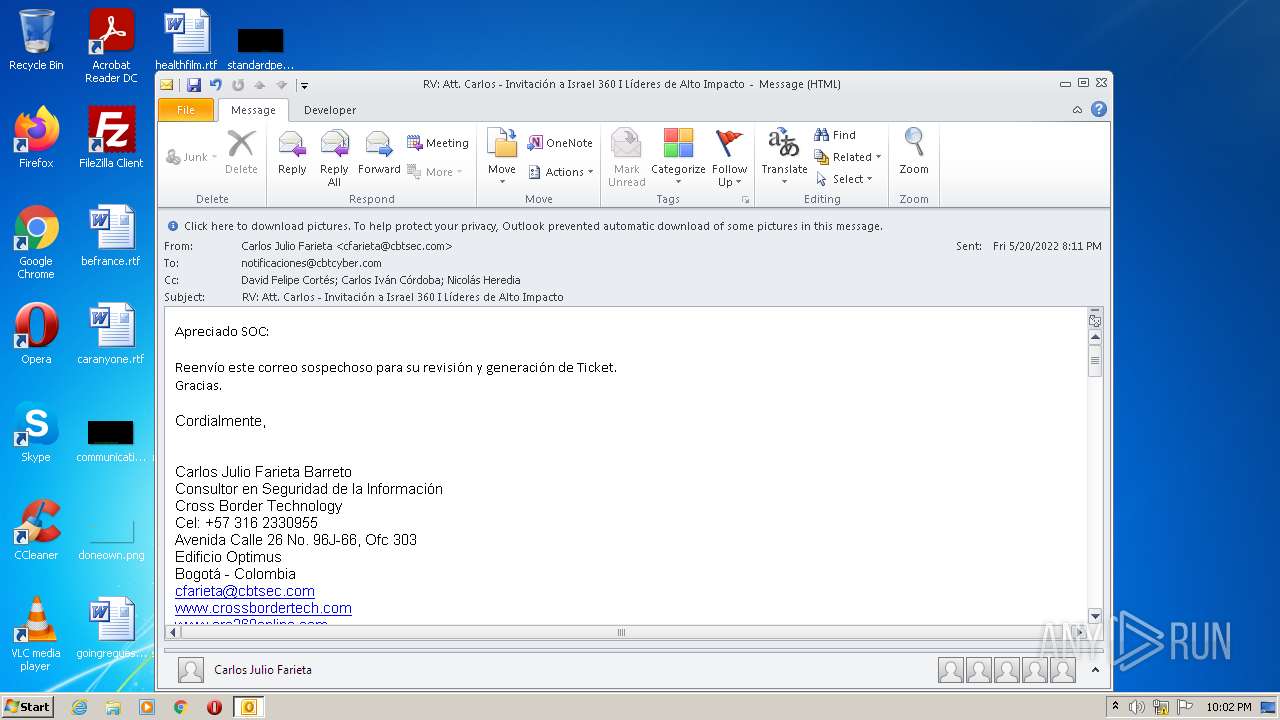
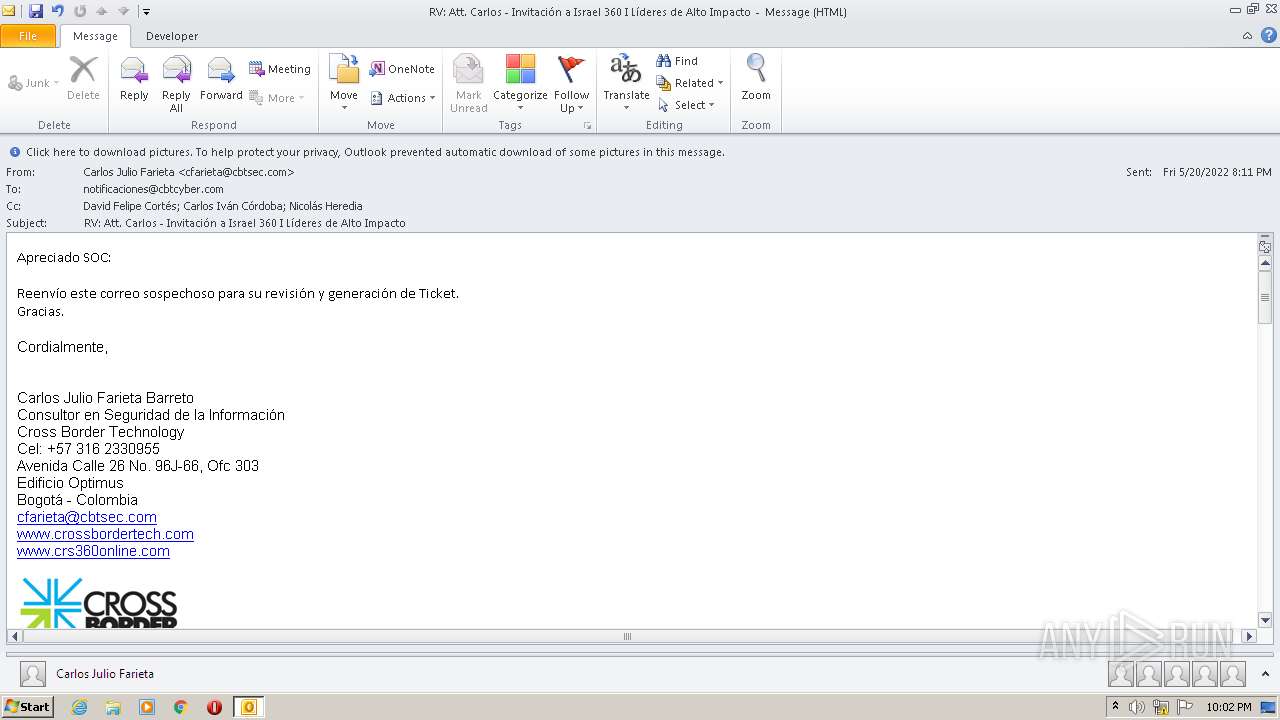
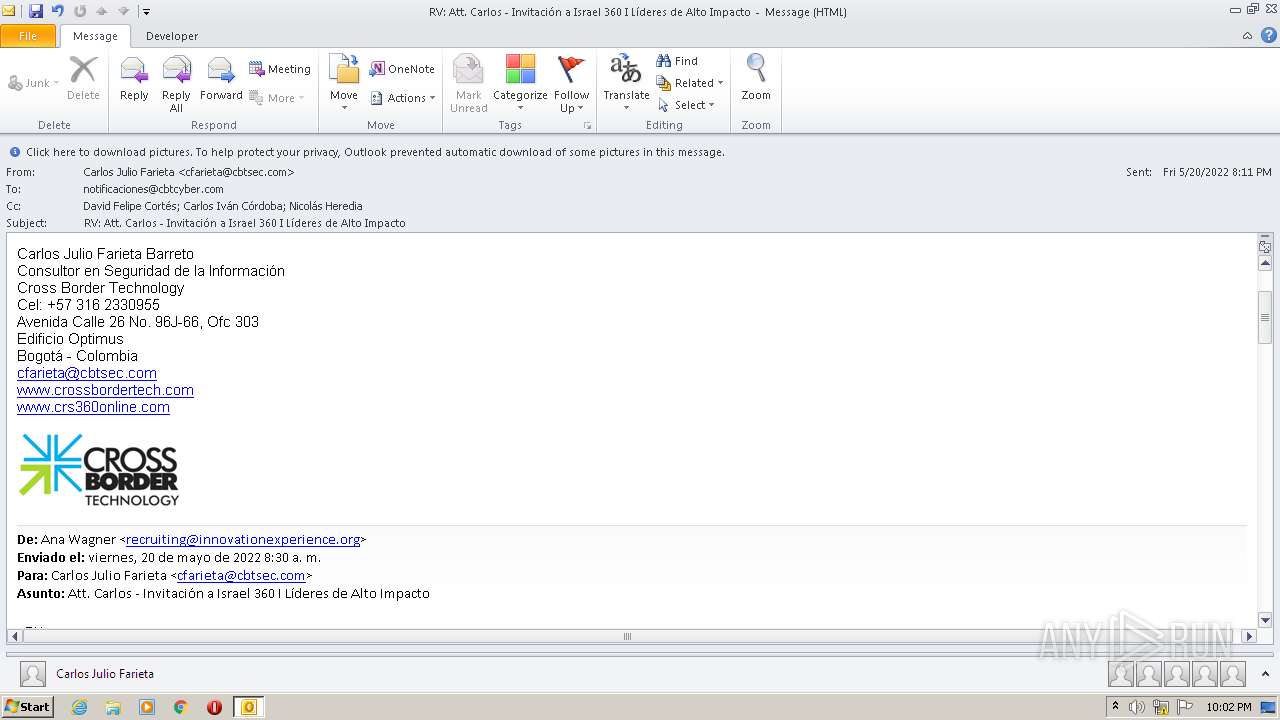
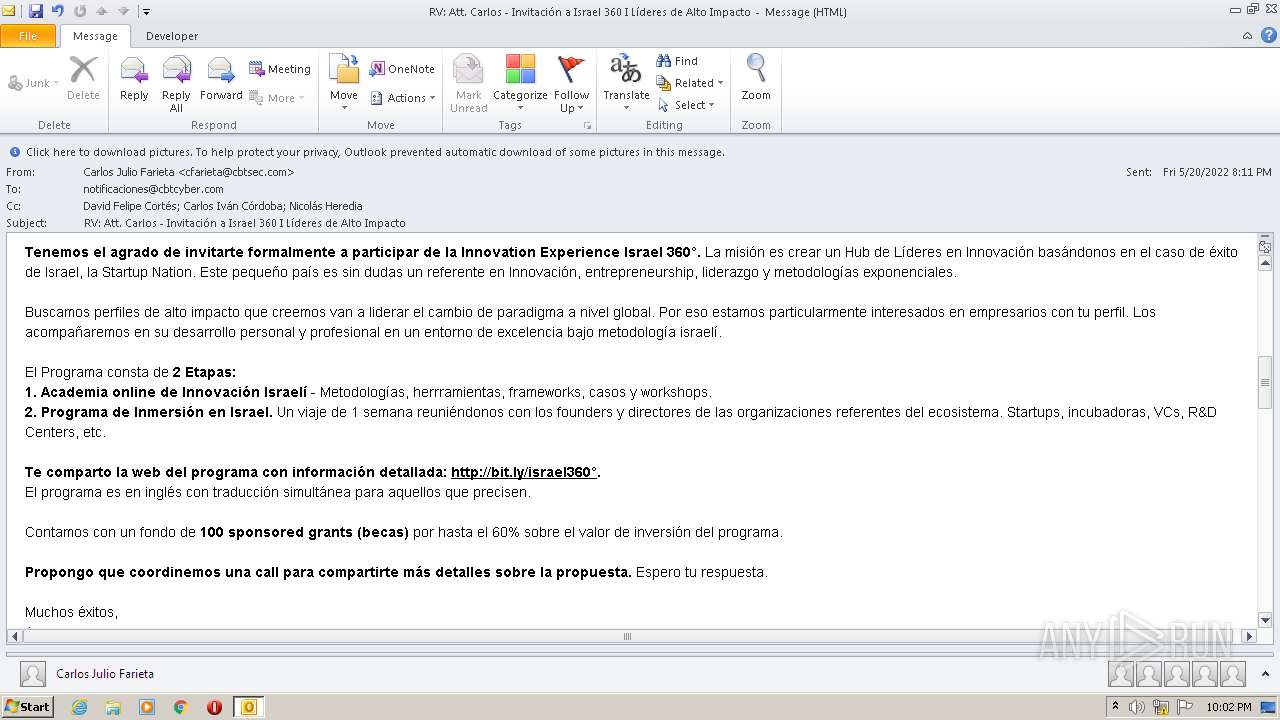
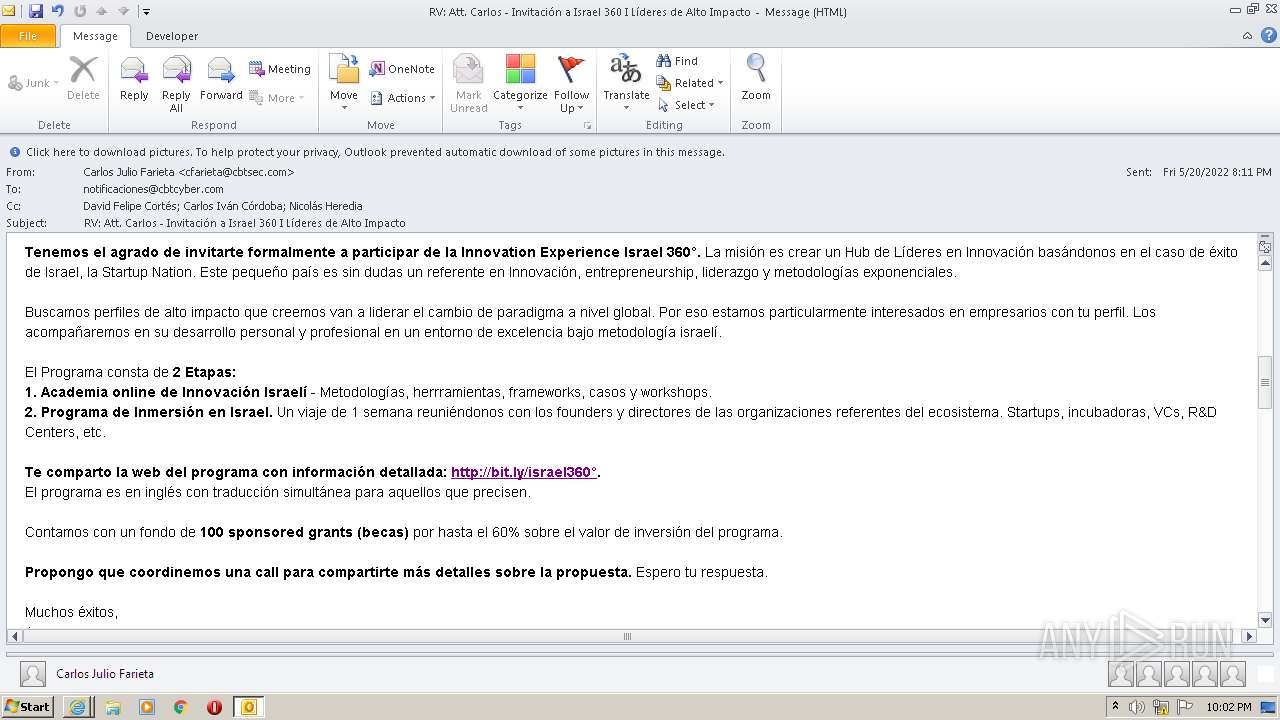
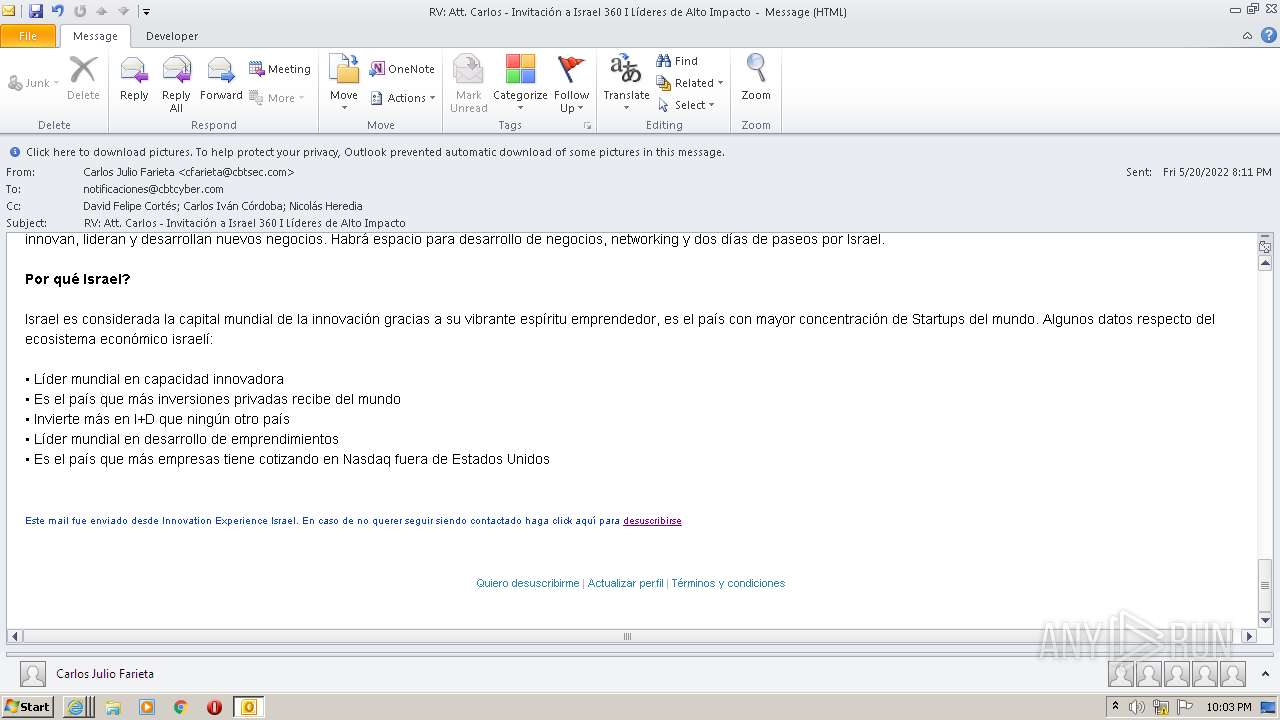
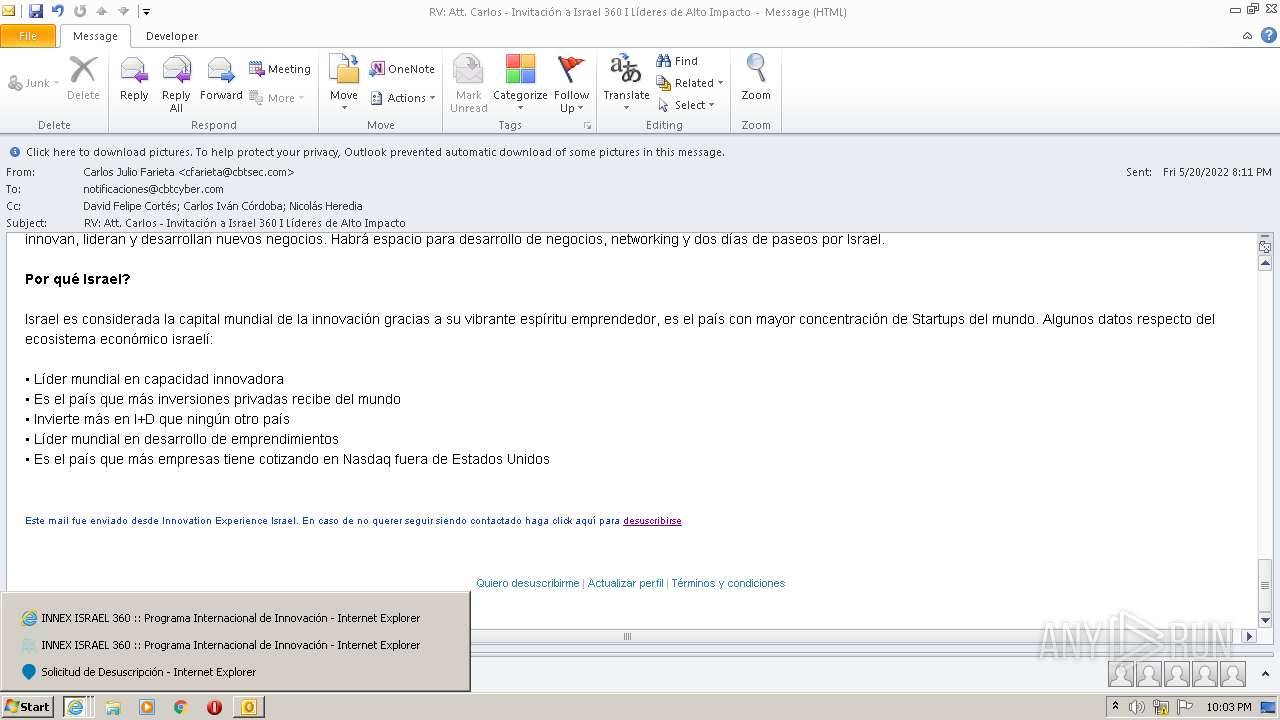
| File name: | RV Att. Carlos - Invitación a Israel 360 I Líderes de Alto Impacto.msg |
| Full analysis: | https://app.any.run/tasks/0b3fbab6-a274-48ef-bb54-442dfd2bc045 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 21:02:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 195506844A1A154D0AB7F87AA266C6E6 |
| SHA1: | 5F91CAC28E690F4FE92AE651721B4CAAAF9E443F |
| SHA256: | 0C787FA1D2BD05F817C841651388F668CBC8D4ABC135F4A797D81B2B64FF6E3A |
| SSDEEP: | 1536:ZwF42Htt9zzlfUx/NJRf6Zof6ND3qJZLAEfpbPtU31Dp4:ZwFT9zhfUjJRFyZoAE4 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 628)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 628)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 268)
- iexplore.exe (PID: 1692)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2968)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2968)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2968)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2968)
INFO
Creates files in the user directory
- OUTLOOK.EXE (PID: 628)
- iexplore.exe (PID: 268)
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 3900)
Checks supported languages
- OUTLOOK.EXE (PID: 628)
- iexplore.exe (PID: 2700)
- iexplore.exe (PID: 3900)
- iexplore.exe (PID: 268)
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 1692)
Reads the computer name
- OUTLOOK.EXE (PID: 628)
- iexplore.exe (PID: 3900)
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 2700)
- iexplore.exe (PID: 268)
- iexplore.exe (PID: 1692)
Searches for installed software
- OUTLOOK.EXE (PID: 628)
Changes internet zones settings
- iexplore.exe (PID: 3900)
- iexplore.exe (PID: 2700)
Application launched itself
- iexplore.exe (PID: 3900)
- iexplore.exe (PID: 2700)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 628)
Reads settings of System Certificates
- iexplore.exe (PID: 268)
- iexplore.exe (PID: 3900)
- iexplore.exe (PID: 2700)
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 1692)
Reads internet explorer settings
- iexplore.exe (PID: 268)
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 1692)
Checks Windows Trust Settings
- iexplore.exe (PID: 3900)
- iexplore.exe (PID: 2700)
- iexplore.exe (PID: 268)
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 1692)
Reads CPU info
- iexplore.exe (PID: 268)
- iexplore.exe (PID: 2592)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3900)
Changes settings of System certificates
- iexplore.exe (PID: 3900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
47
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2700 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 628 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\RV Att. Carlos - Invitación a Israel 360 I Líderes de Alto Impacto.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2700 CREDAT:2954522 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3900 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
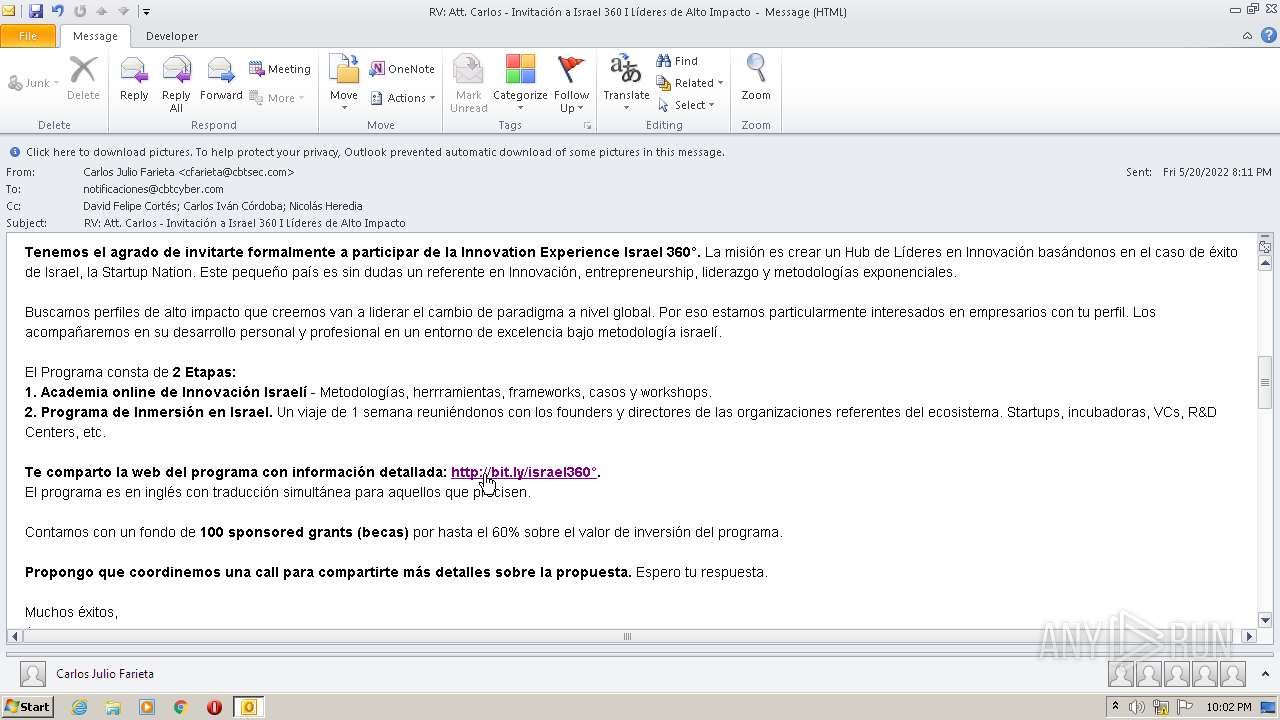
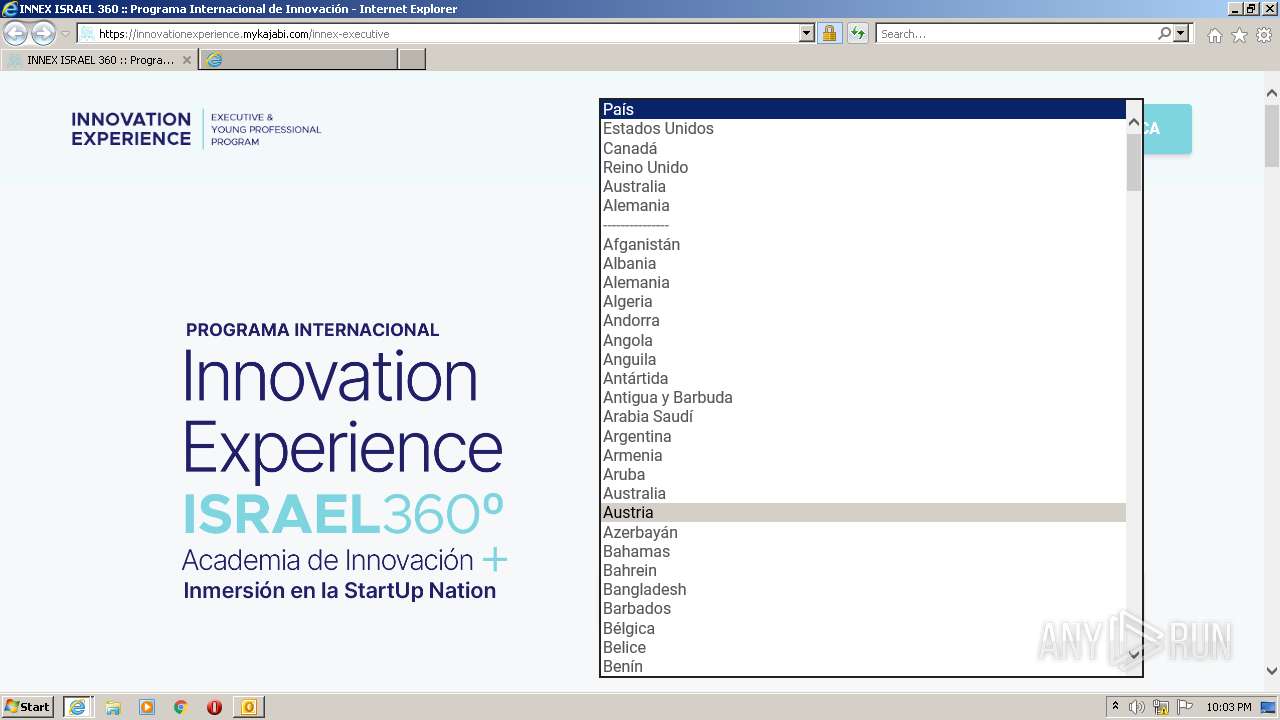
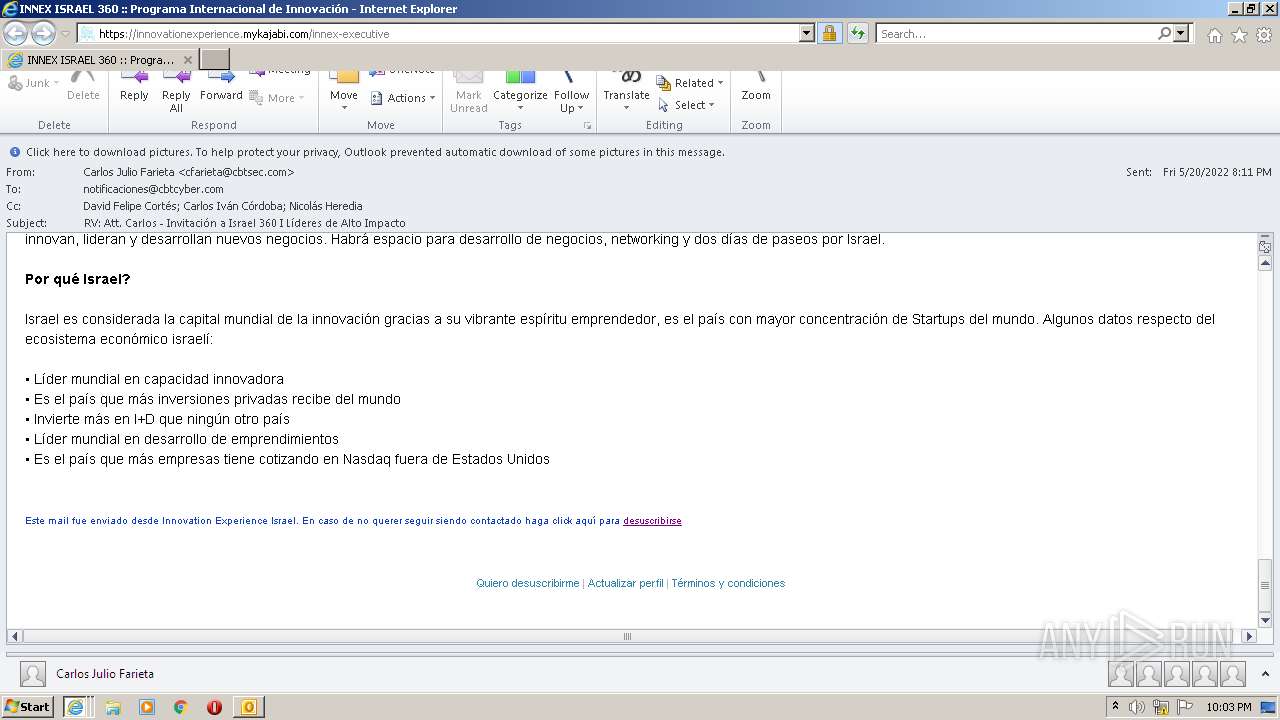
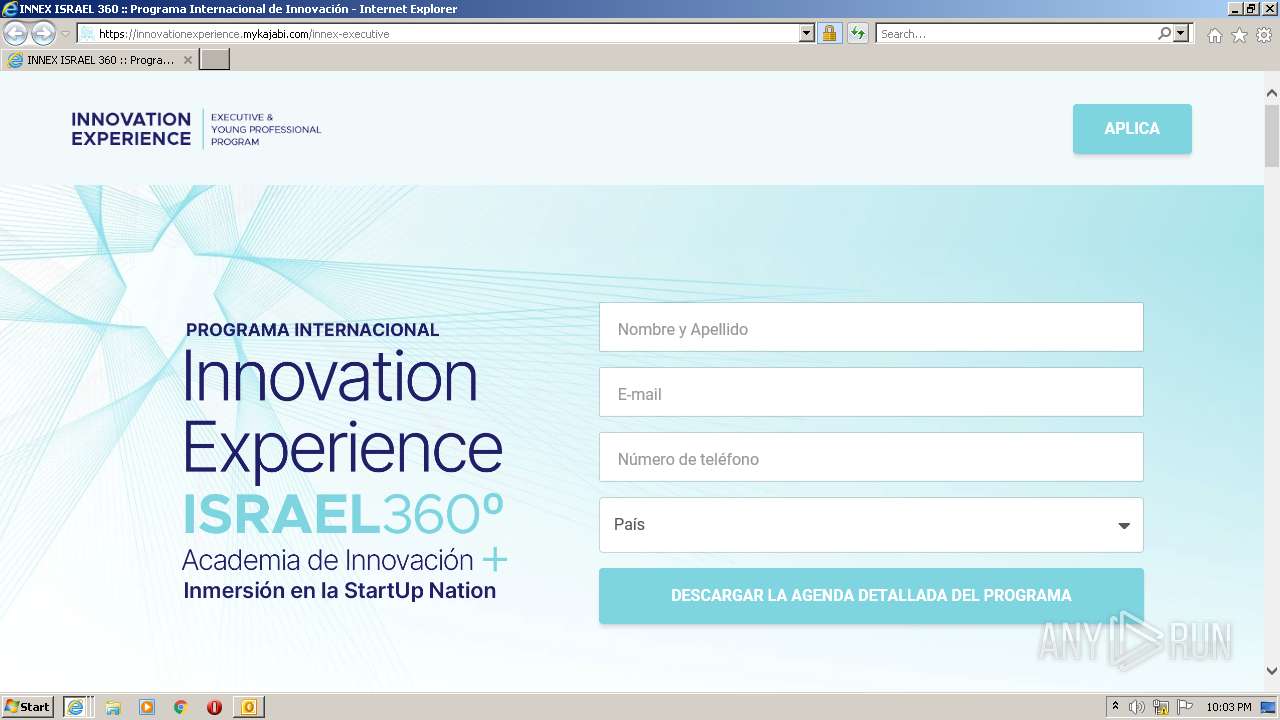
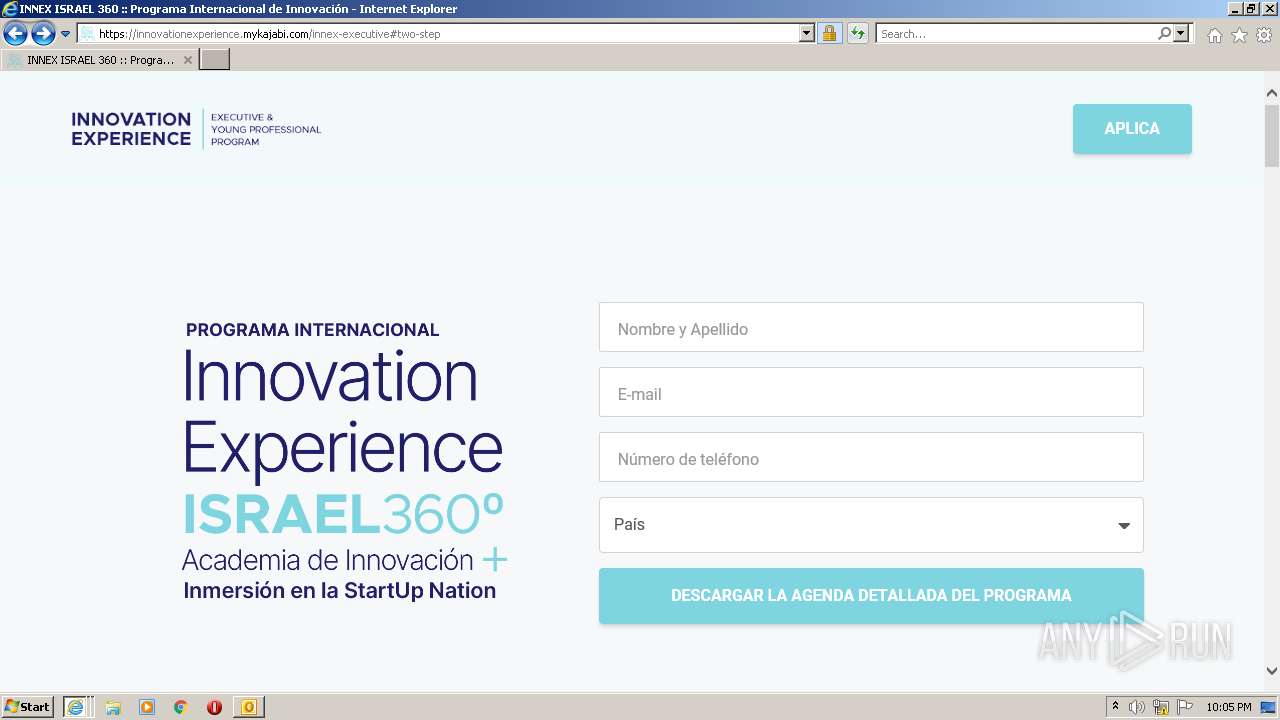
| 2700 | "C:\Program Files\Internet Explorer\iexplore.exe" https://nts.embluemail.com/p/cl?data=Dg9uLee9ElZeY6I8DJTcio8h2giNp7fQIm7tGQsqhiiiIz1FIUHNXnQK7nwbK1foym8fTqt0WtZCMCGYko4bd627EEQLfdPLzGPFMxuLctI%3D!-!8a2cp,,*-*,j2go5b!-!http%3A%2F%2Fbit.ly%2Fisrael360%C2%B0%3Futm_source=emBlue%26utm_medium=email%26utm_campaign=Flow+ANA+360+-+Espa%C3%B1ol%26utm_content=Temp+ANA+360+-+Espa%C3%B1ol+N%C2%BA+1--Att.+Carlos+-+Invitaci%C3%B3n+a+Israel+360+I+L%C3%ADderes+de+Alto+Impacto%26utm_term=none--3--none--0-10--TRIGGER | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2968 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3900 | "C:\Program Files\Internet Explorer\iexplore.exe" https://nts.embluemail.com/p/cl?data=Dg9uLee9ElZeY6I8DJTcio8h2giNp7fQIm7tGQsqhiiiIz1FIUHNXnQK7nwbK1foym8fTqt0WtZCMCGYko4bd627EEQLfdPLzGPFMxuLctI%3D!-!8a2cp,,*-*,j2go5b!-!http%3A%2F%2Fbit.ly%2Fisrael360%C2%B0%3Futm_source=emBlue%26utm_medium=email%26utm_campaign=Flow+ANA+360+-+Espa%C3%B1ol%26utm_content=Temp+ANA+360+-+Espa%C3%B1ol+N%C2%BA+1--Att.+Carlos+-+Invitaci%C3%B3n+a+Israel+360+I+L%C3%ADderes+de+Alto+Impacto%26utm_term=none--3--none--0-10--TRIGGER | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
58 832
Read events
57 465
Write events
1 344
Delete events
23
Modification events
| (PID) Process: | (628) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (628) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (628) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (628) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (628) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (628) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (628) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (628) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (628) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (628) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
50
Text files
149
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 628 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9116.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 628 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 628 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 628 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 268 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:— | SHA256:— | |||
| 268 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 268 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | der | |
MD5:— | SHA256:— | |||
| 628 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F9162ECE.dat | image | |
MD5:— | SHA256:— | |||
| 268 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | binary | |
MD5:— | SHA256:— | |||
| 268 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
239
DNS requests
56
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
628 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
268 | iexplore.exe | GET | 200 | 13.225.84.13:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
268 | iexplore.exe | GET | 200 | 13.225.84.13:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
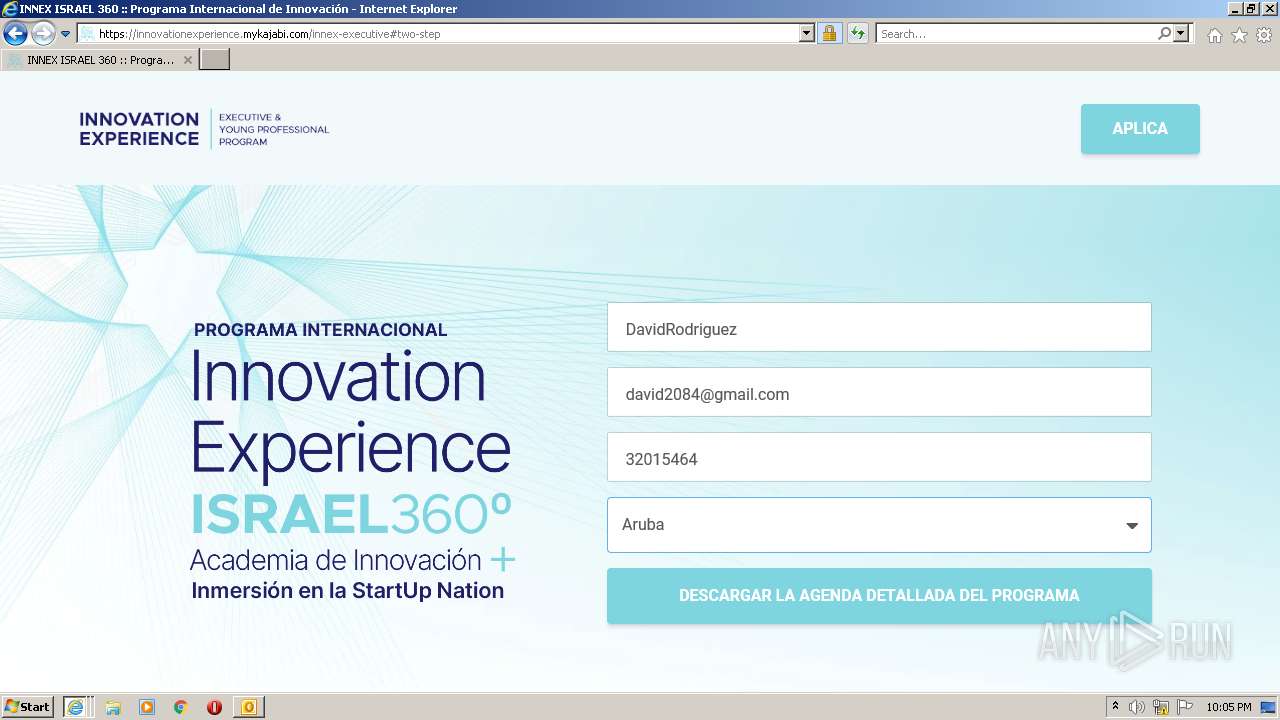
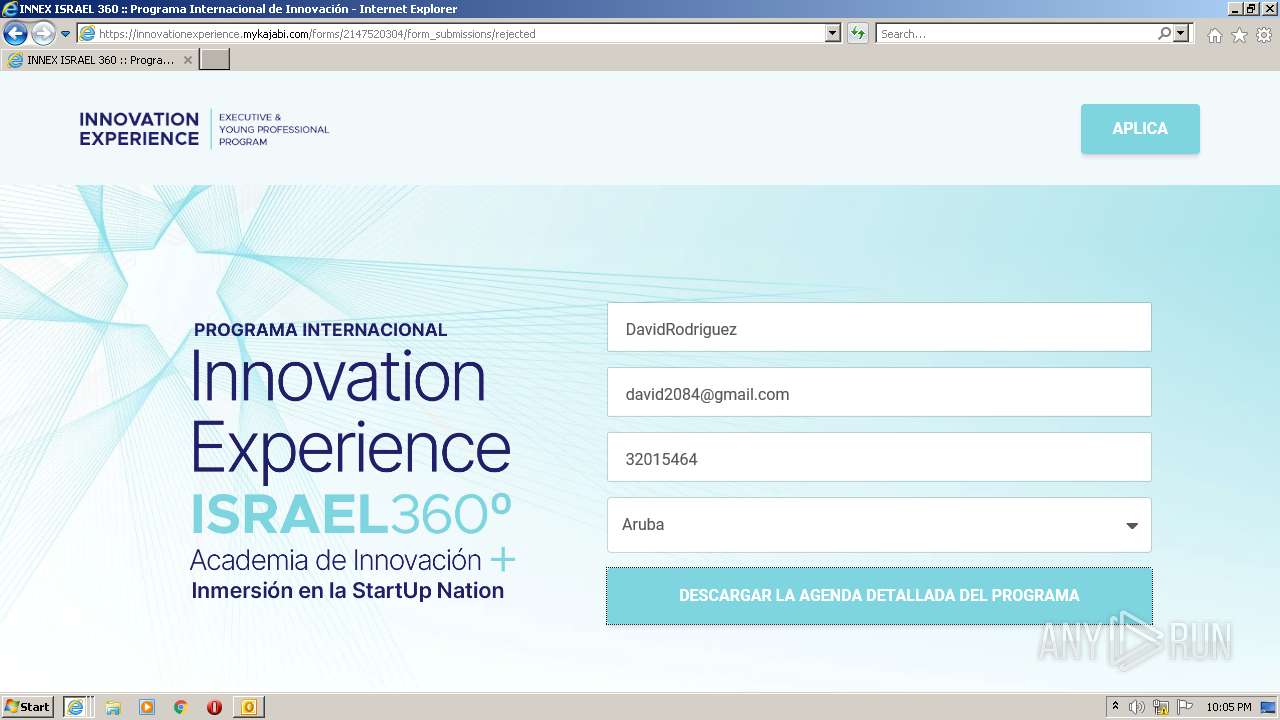
268 | iexplore.exe | GET | 301 | 67.199.248.10:80 | http://bit.ly/israel360%C2%B0?utm_source=emBlue&utm_medium=email&utm_campaign=Flow%20ANA%20360%20-%20Espa%C3%B1ol&utm_content=Temp%20ANA%20360%20-%20Espa%C3%B1ol%20N%C2%BA%201--Att.%20Carlos%20-%20Invitaci%C3%B3n%20a%20Israel%20360%20I%20L%C3%ADderes%20de%20Alto%20Impacto&utm_term=none--3--none--0-10--TRIGGER | US | html | 144 b | shared |
268 | iexplore.exe | GET | 200 | 13.225.84.97:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2592 | iexplore.exe | GET | 200 | 13.225.84.13:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3900 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2592 | iexplore.exe | GET | 301 | 67.199.248.10:80 | http://bit.ly/israel360%C2%B0?utm_source=emBlue&utm_medium=email&utm_campaign=Flow%20ANA%20360%20-%20Espa%C3%B1ol&utm_content=Temp%20ANA%20360%20-%20Espa%C3%B1ol%20N%C2%BA%201--Att.%20Carlos%20-%20Invitaci%C3%B3n%20a%20Israel%20360%20I%20L%C3%ADderes%20de%20Alto%20Impacto&utm_term=none--3--none--0-10--TRIGGER | US | html | 144 b | shared |
2592 | iexplore.exe | GET | 200 | 13.225.84.88:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAHCQIkCXpSK3L31QZgvrds%3D | US | der | 471 b | whitelisted |
268 | iexplore.exe | GET | 200 | 13.225.84.88:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAHCQIkCXpSK3L31QZgvrds%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
628 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
268 | iexplore.exe | 54.233.180.243:443 | nts.embluemail.com | Amazon.com, Inc. | BR | unknown |
268 | iexplore.exe | 95.140.236.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | GB | whitelisted |
268 | iexplore.exe | 13.225.84.97:80 | o.ss2.us | — | US | unknown |
— | — | 54.233.180.243:443 | nts.embluemail.com | Amazon.com, Inc. | BR | unknown |
2592 | iexplore.exe | 54.233.180.243:443 | nts.embluemail.com | Amazon.com, Inc. | BR | unknown |
2592 | iexplore.exe | 13.225.84.13:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
2592 | iexplore.exe | 13.225.84.88:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
268 | iexplore.exe | 13.225.84.88:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
3900 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
nts.embluemail.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
bit.ly |
| shared |