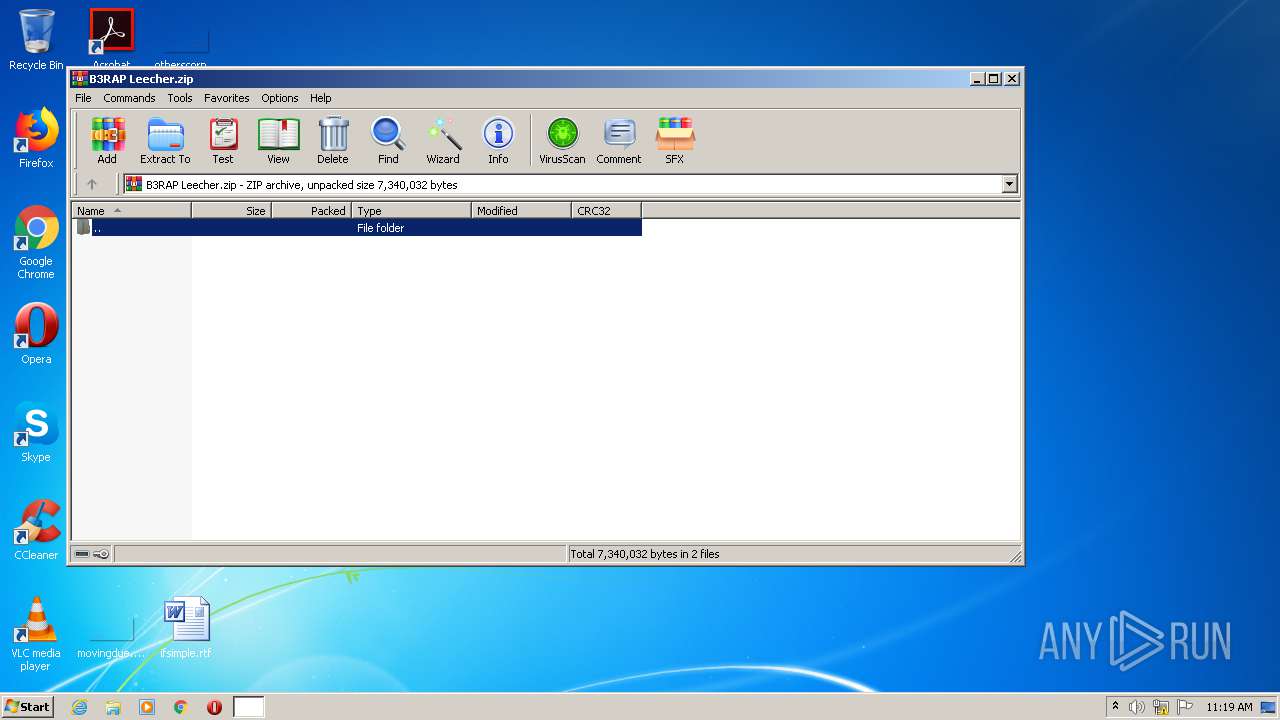
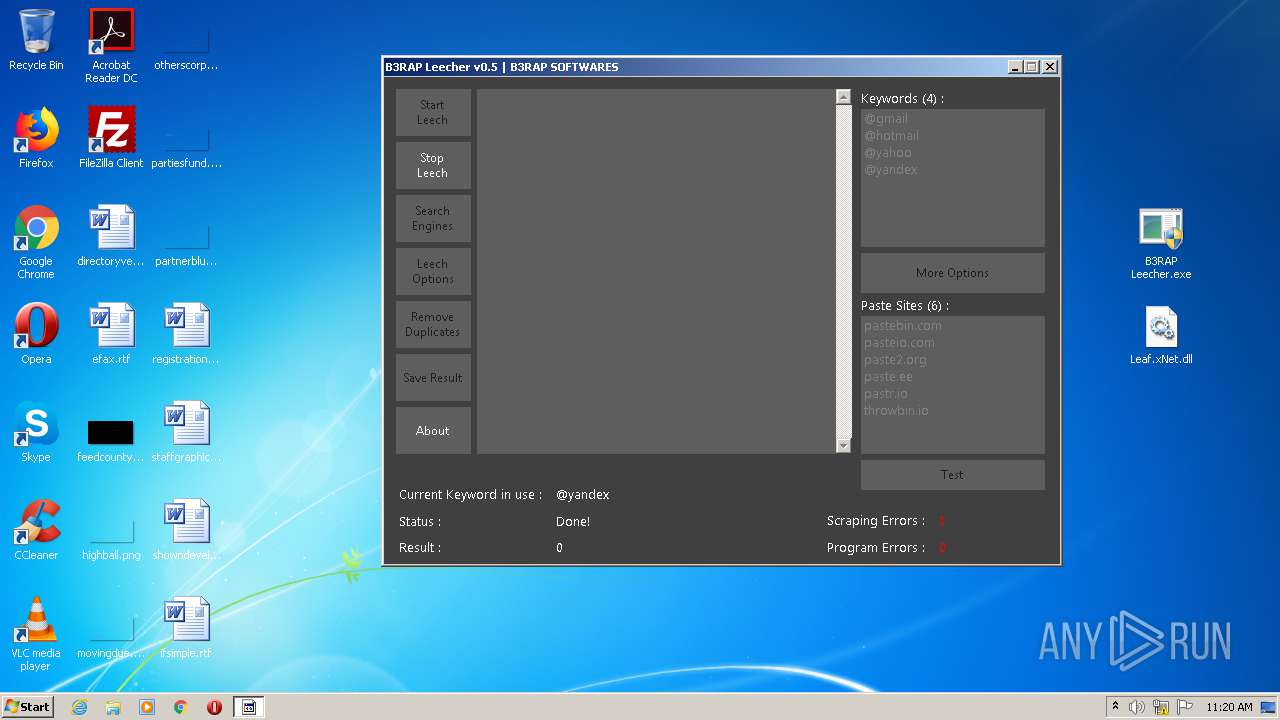
| File name: | B3RAP Leecher.zip |
| Full analysis: | https://app.any.run/tasks/a29c36e8-aae5-483e-8d43-69392e764bab |
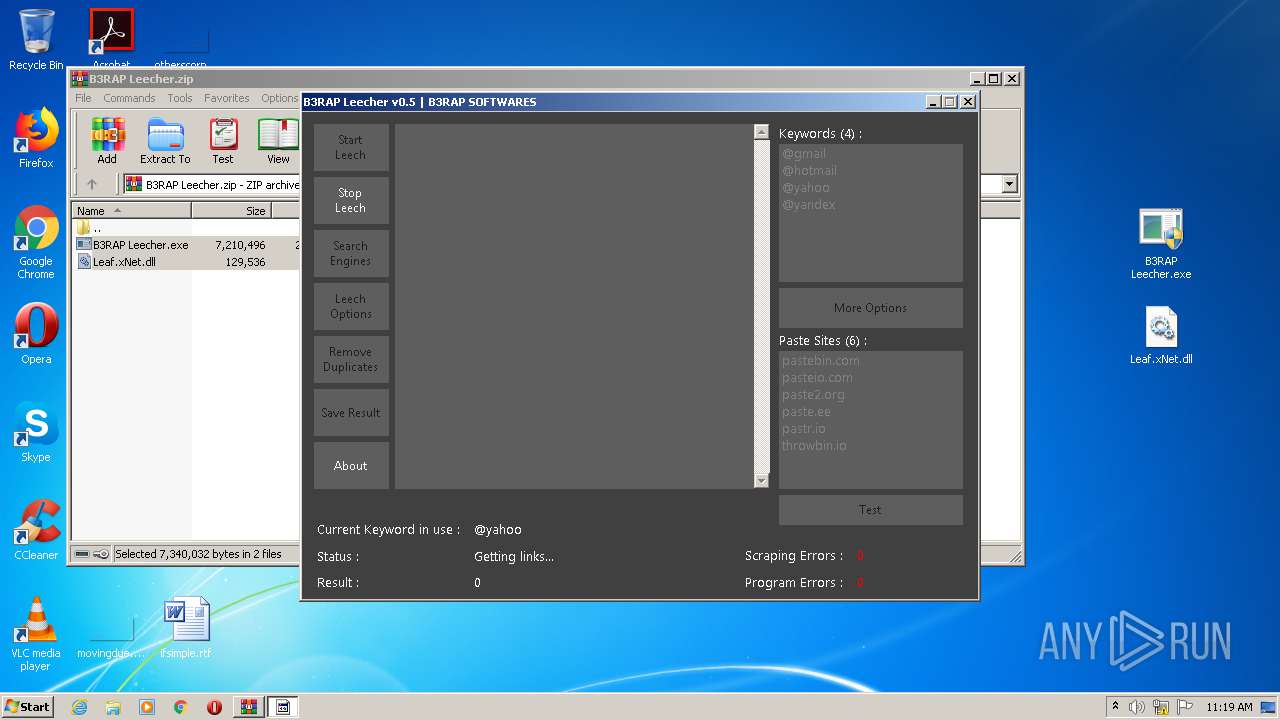
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 11:18:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8DDC6C8712D123C6F9EF0BE104E69C9A |
| SHA1: | ABC5DC8933C31F503E599EB6F97679C3F96EA1C5 |
| SHA256: | 0C77F38A484F635CB6E96DD9FC37C4A8C47BB5DEAE0D3B62FA8E576FE70D5F05 |
| SSDEEP: | 49152:6msMXfeEeWI46wbWVZ3ERF1oSekoUjX4bjFpROLctqDeICmLJ5uR2rDI3LXnCLlI:6msMPjaITRFu7PHbyc1IXzm2YbXnsa9h |
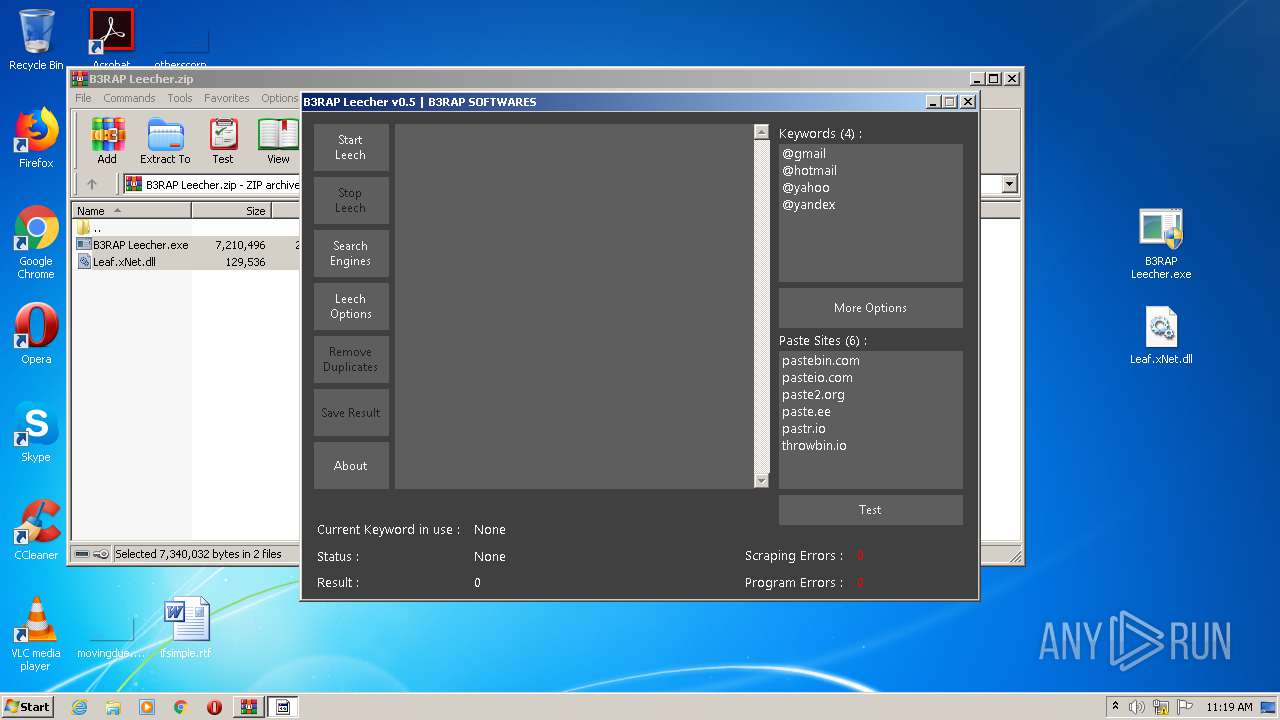
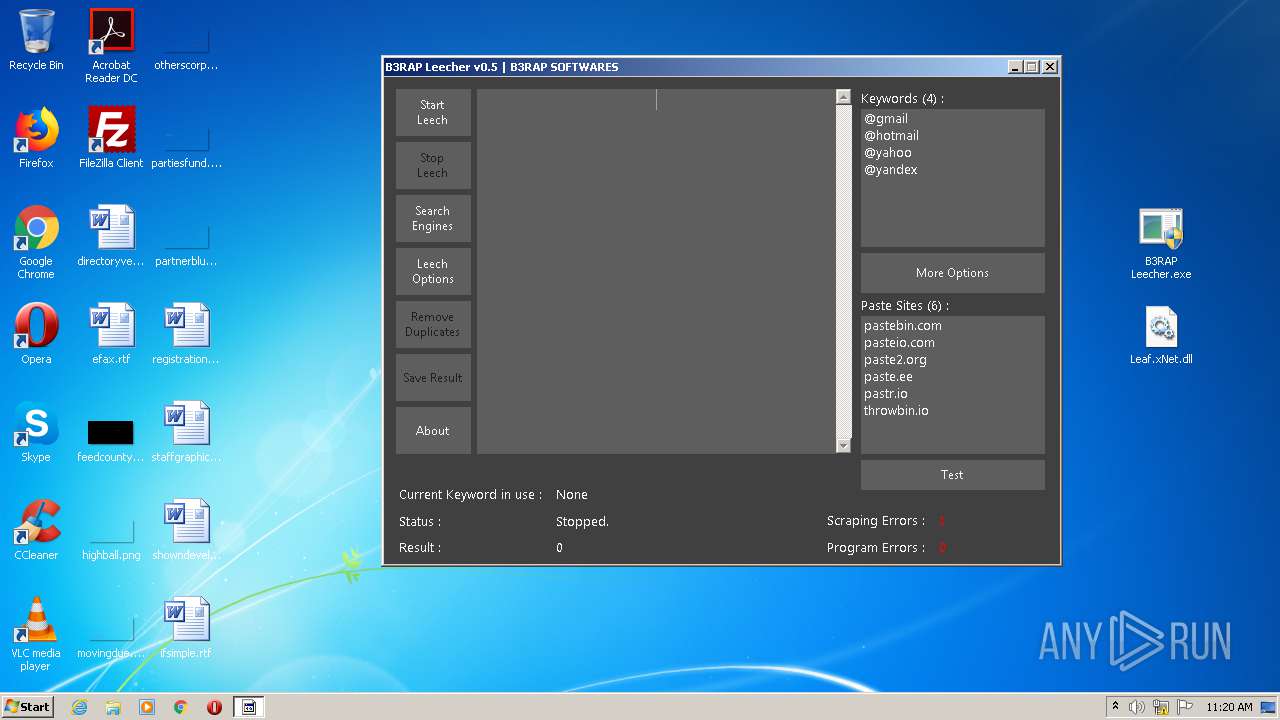
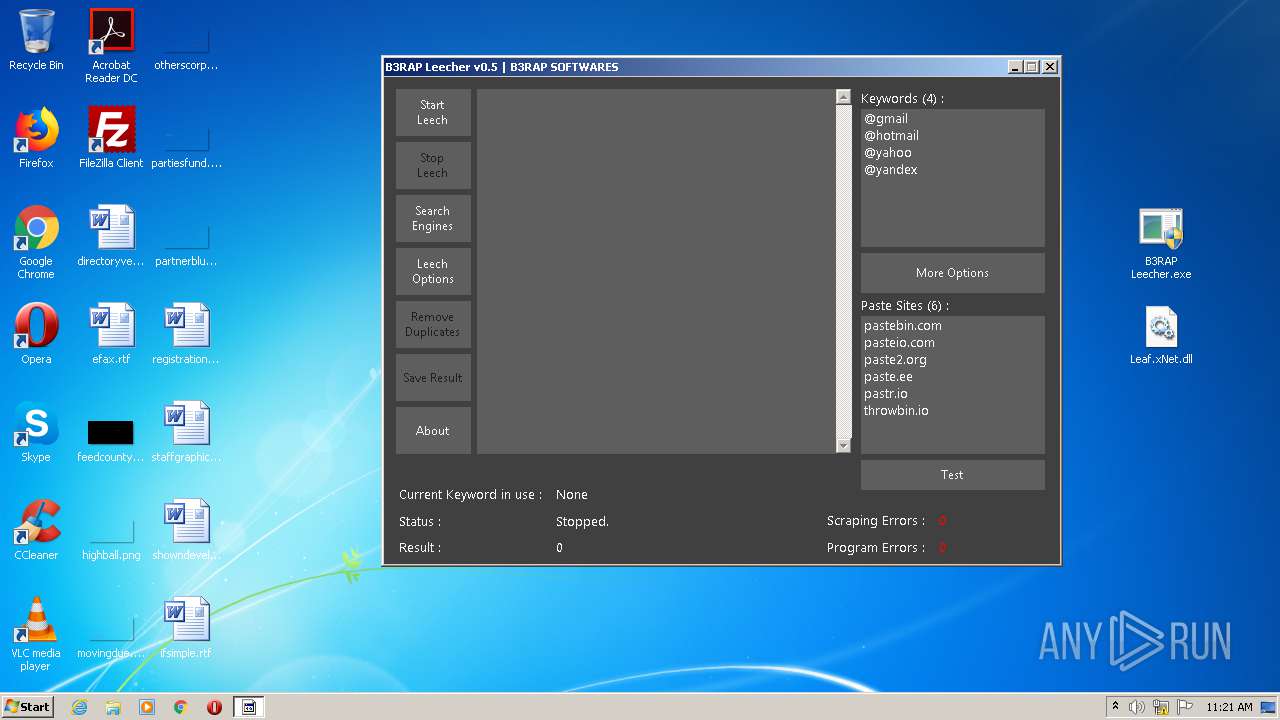
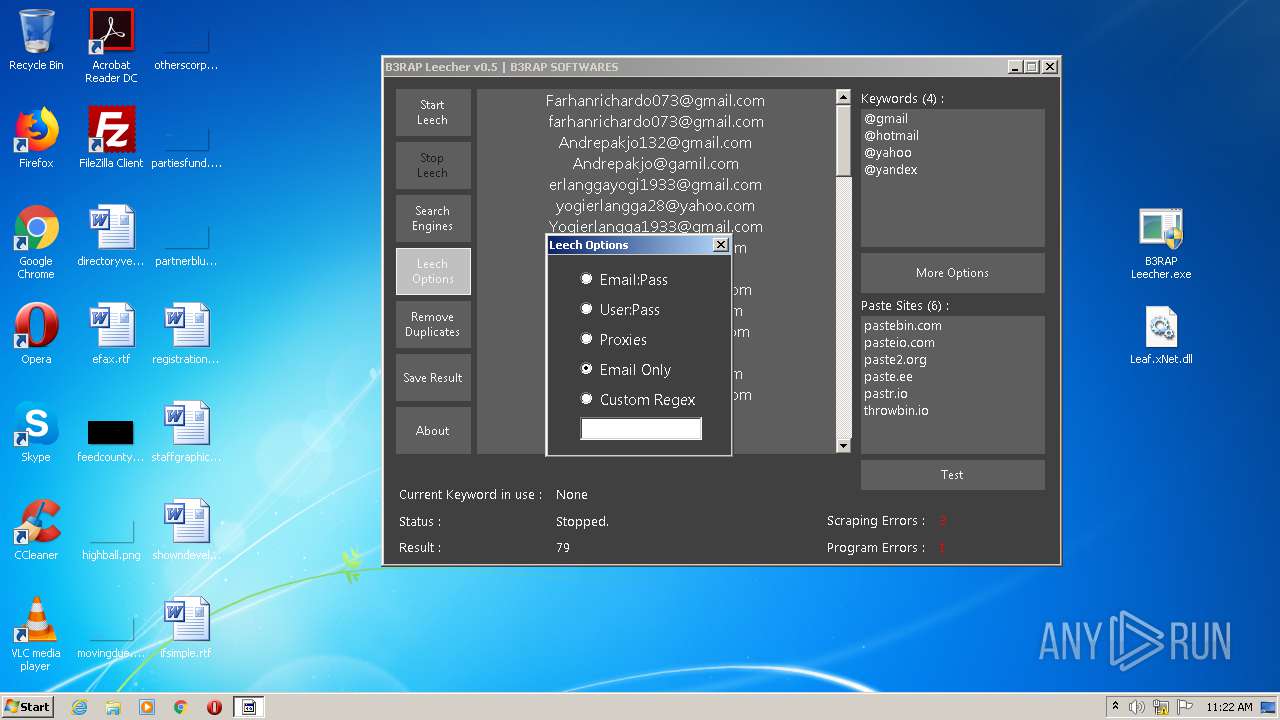
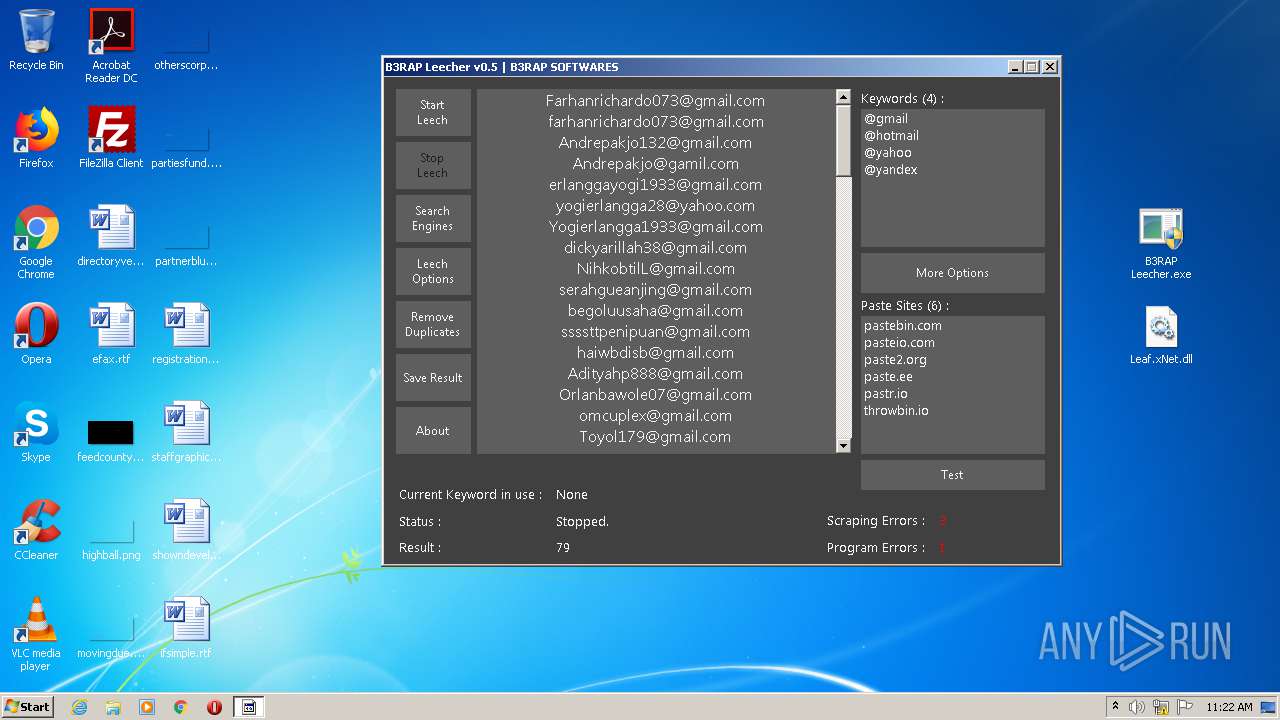
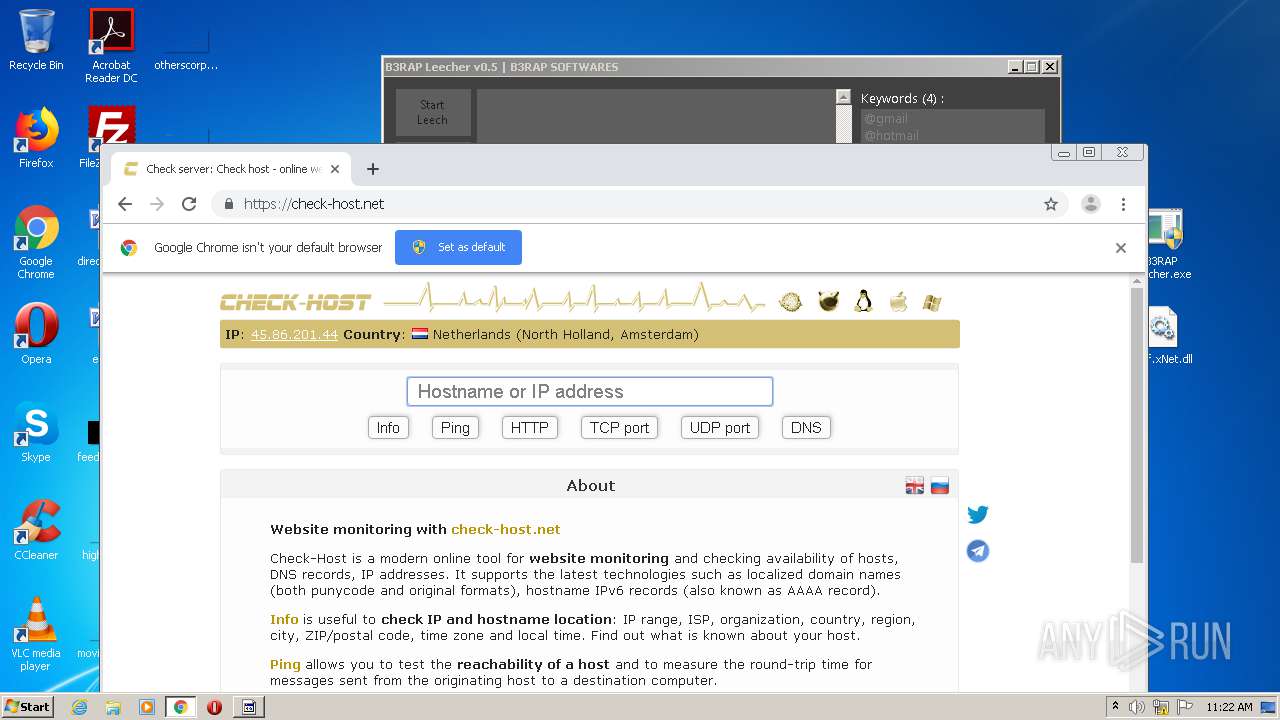
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3164)
- B3RAP Leecher.exe (PID: 2580)
Application was dropped or rewritten from another process
- B3RAP Leecher.exe (PID: 2580)
- B3RAP Leecher.exe (PID: 1564)
Drops executable file immediately after starts
- B3RAP Leecher.exe (PID: 2580)
Changes settings of System certificates
- B3RAP Leecher.exe (PID: 2580)
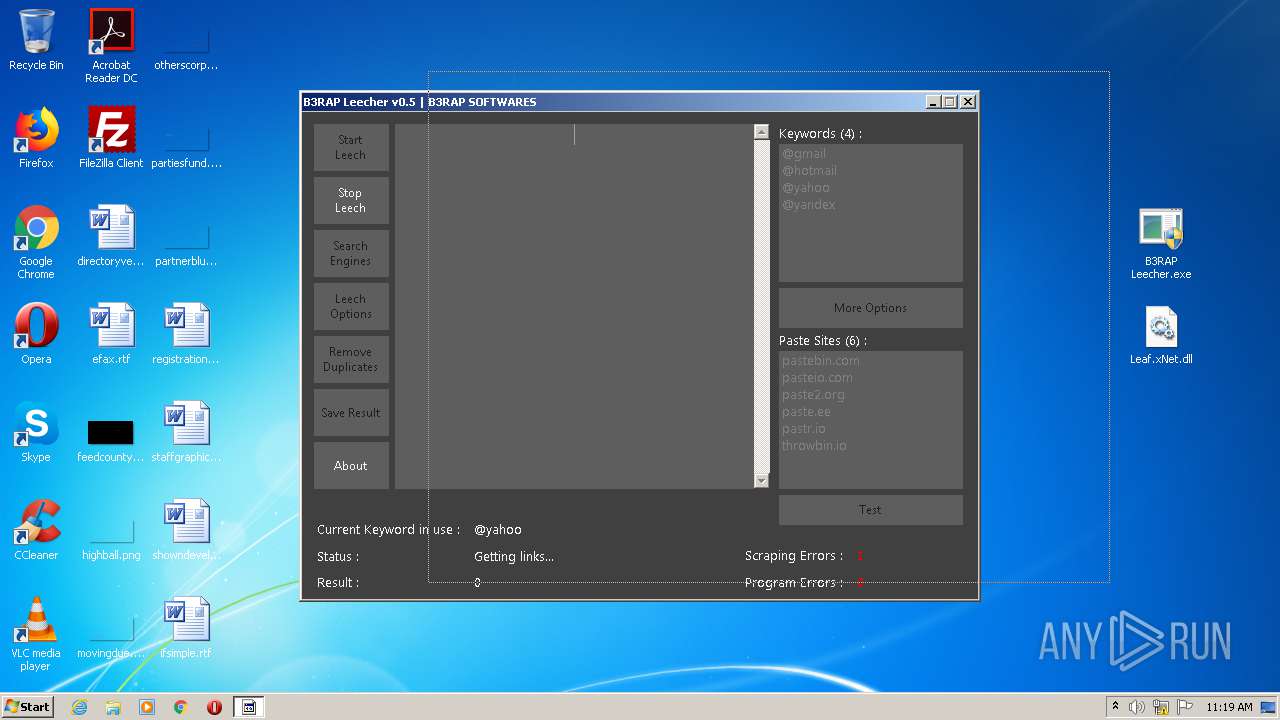
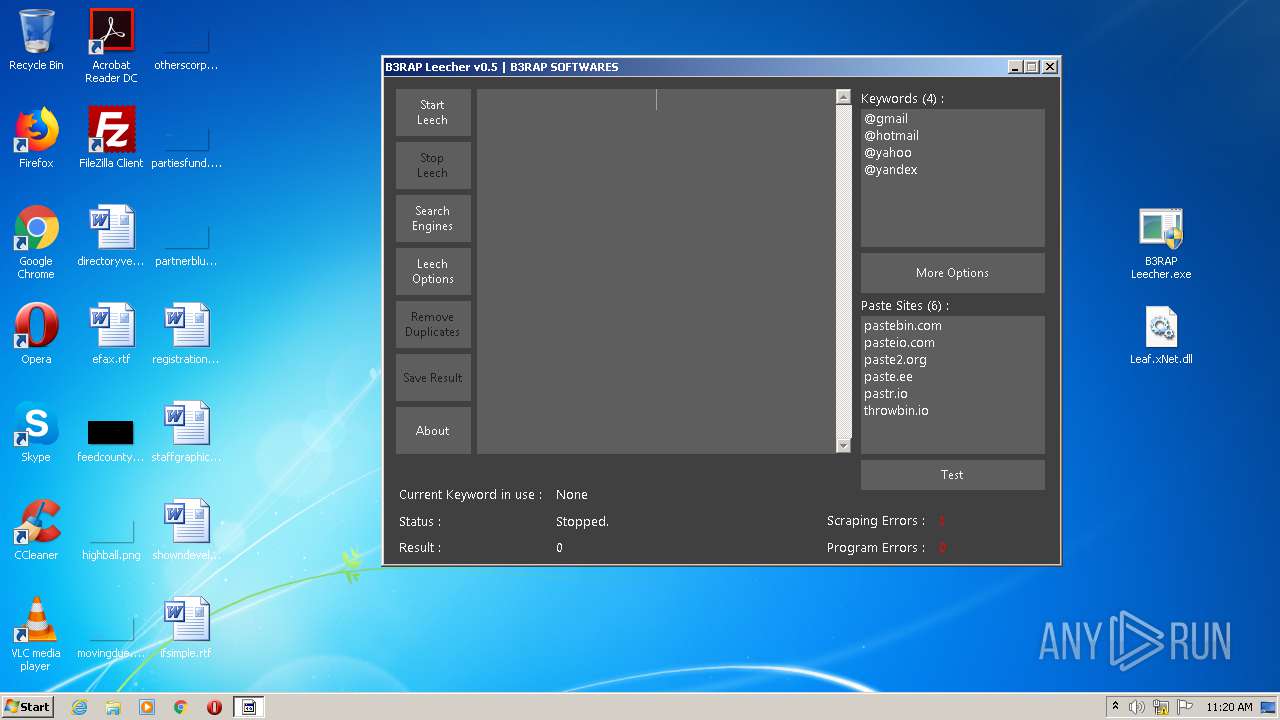
SUSPICIOUS
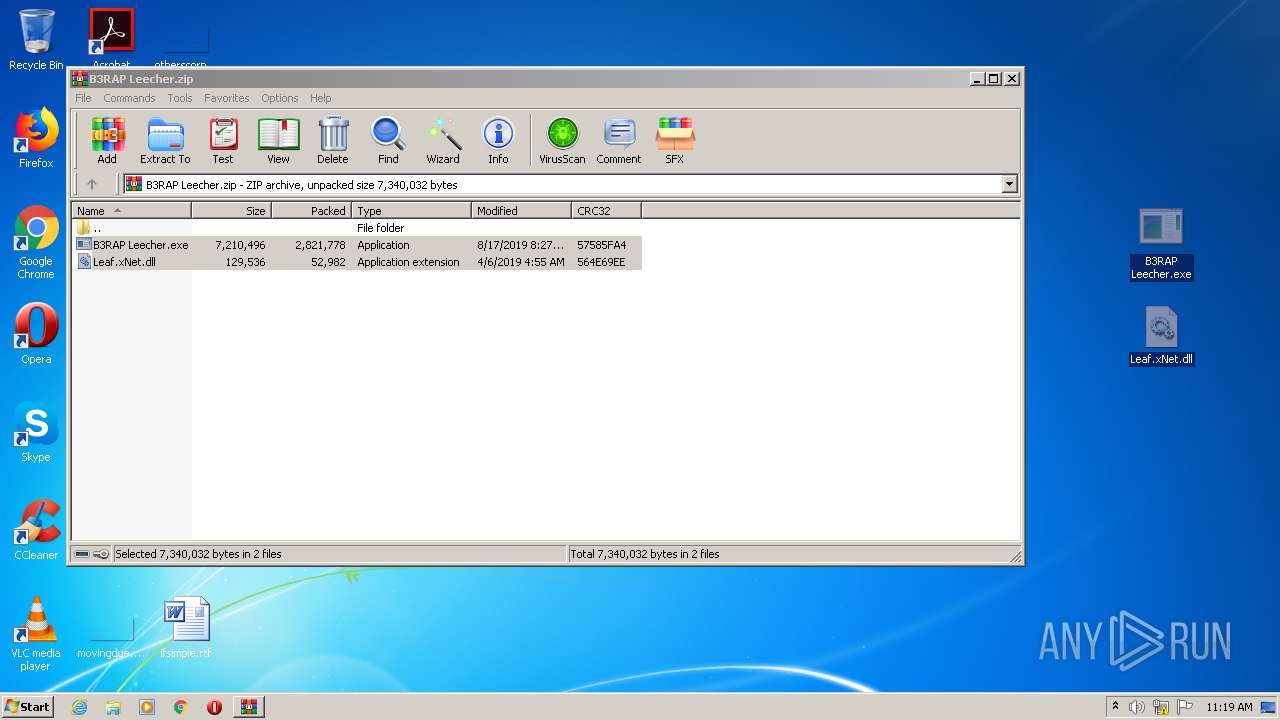
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2668)
- B3RAP Leecher.exe (PID: 2580)
Drops a file with too old compile date
- WinRAR.exe (PID: 2668)
- B3RAP Leecher.exe (PID: 2580)
Creates files in the user directory
- B3RAP Leecher.exe (PID: 2580)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2668)
- B3RAP Leecher.exe (PID: 2580)
Adds / modifies Windows certificates
- B3RAP Leecher.exe (PID: 2580)
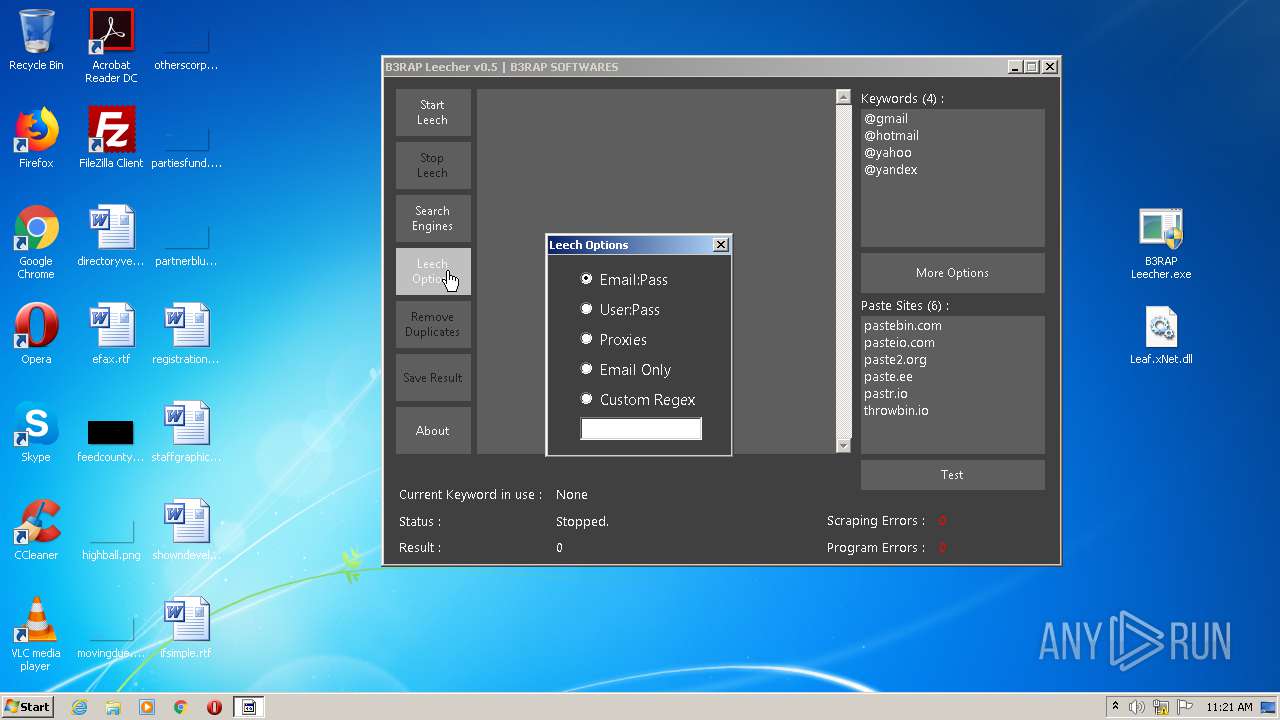
INFO
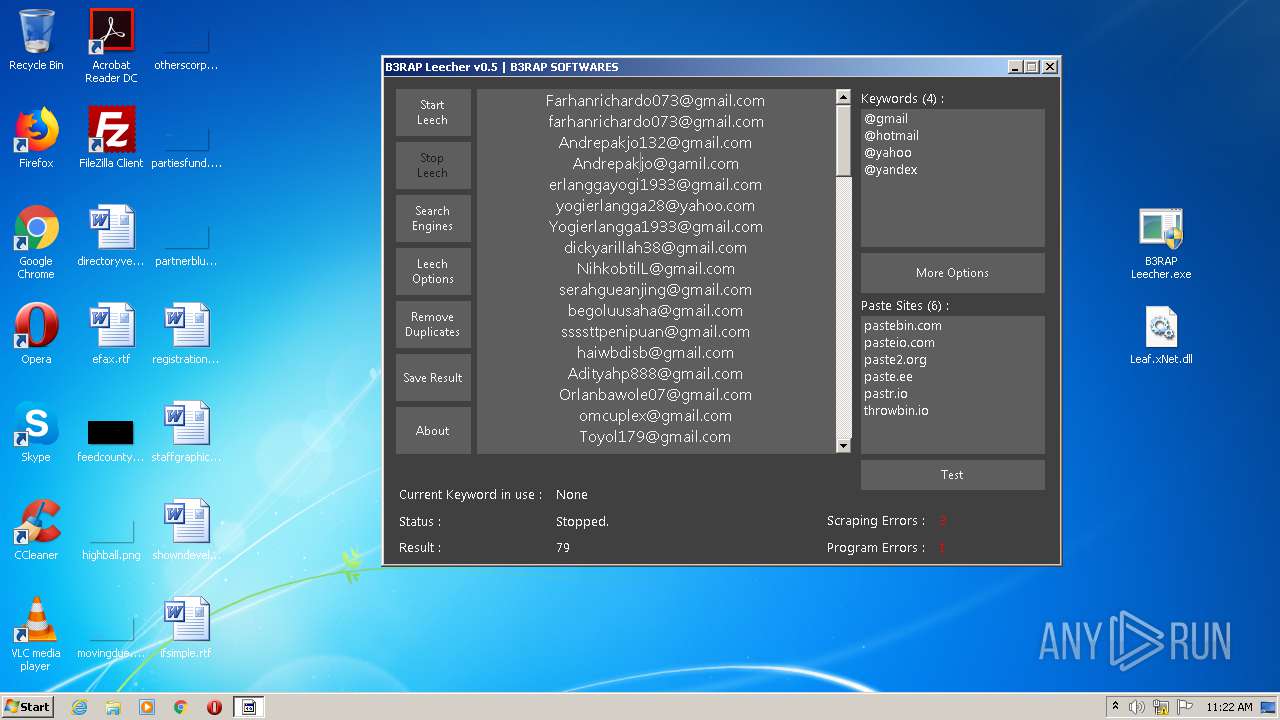
Manual execution by user
- B3RAP Leecher.exe (PID: 1564)
- B3RAP Leecher.exe (PID: 2580)
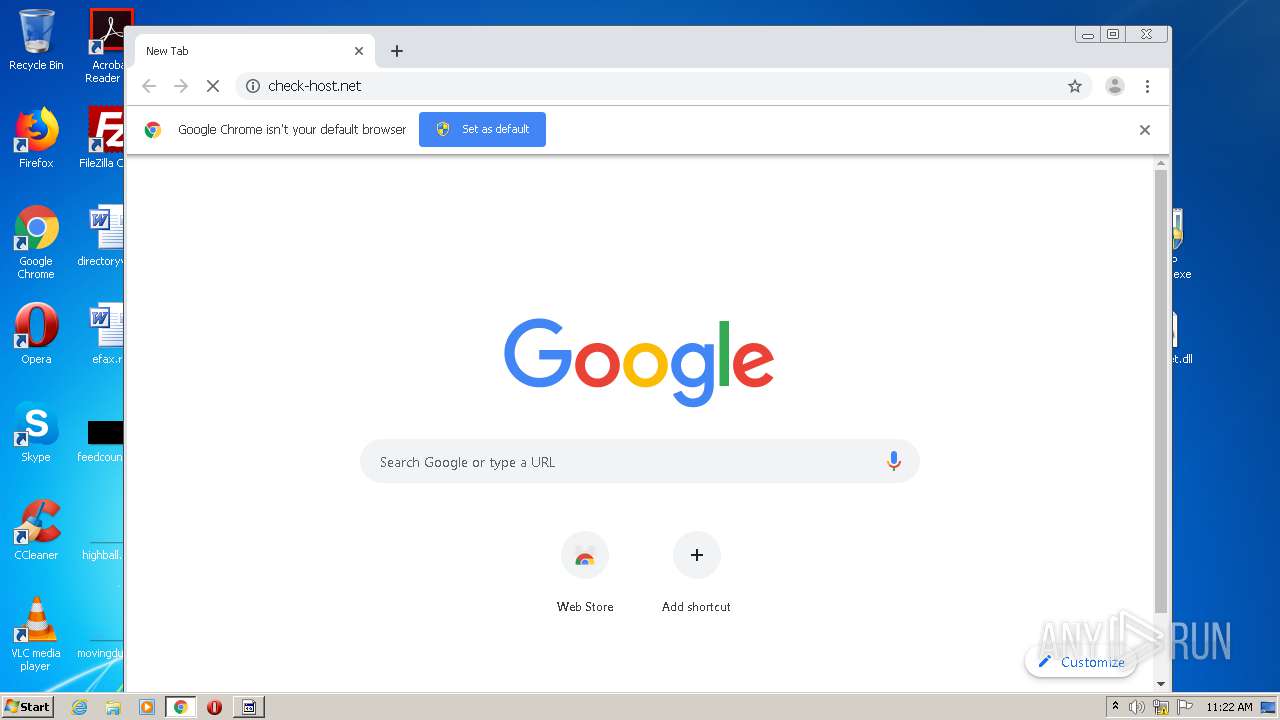
- chrome.exe (PID: 1200)
Reads settings of System Certificates
- B3RAP Leecher.exe (PID: 2580)
Reads the hosts file
- chrome.exe (PID: 1200)
- chrome.exe (PID: 3888)
Application launched itself
- chrome.exe (PID: 1200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:08:17 20:27:19 |
| ZipCRC: | 0x57585fa4 |
| ZipCompressedSize: | 2821778 |
| ZipUncompressedSize: | 7210496 |
| ZipFileName: | B3RAP Leecher.exe |
Total processes
71
Monitored processes
32
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,18430383831217336746,4802970433864857268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12698239041049071809 --mojo-platform-channel-handle=3420 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,18430383831217336746,4802970433864857268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13882022509400078044 --mojo-platform-channel-handle=3584 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,18430383831217336746,4802970433864857268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7456253276593308013 --mojo-platform-channel-handle=3592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,18430383831217336746,4802970433864857268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17350285291882316147 --mojo-platform-channel-handle=3160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,18430383831217336746,4802970433864857268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10628467791594246923 --mojo-platform-channel-handle=2772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,18430383831217336746,4802970433864857268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7037001560527417281 --mojo-platform-channel-handle=3784 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,18430383831217336746,4802970433864857268,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16482173269828549442 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,18430383831217336746,4802970433864857268,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4495182955548510930 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,18430383831217336746,4802970433864857268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17977626519884544783 --mojo-platform-channel-handle=3720 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
687
Read events
592
Write events
91
Delete events
4
Modification events
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\B3RAP Leecher.zip | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2580) B3RAP Leecher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2580) B3RAP Leecher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
11
Suspicious files
22
Text files
229
Unknown types
7
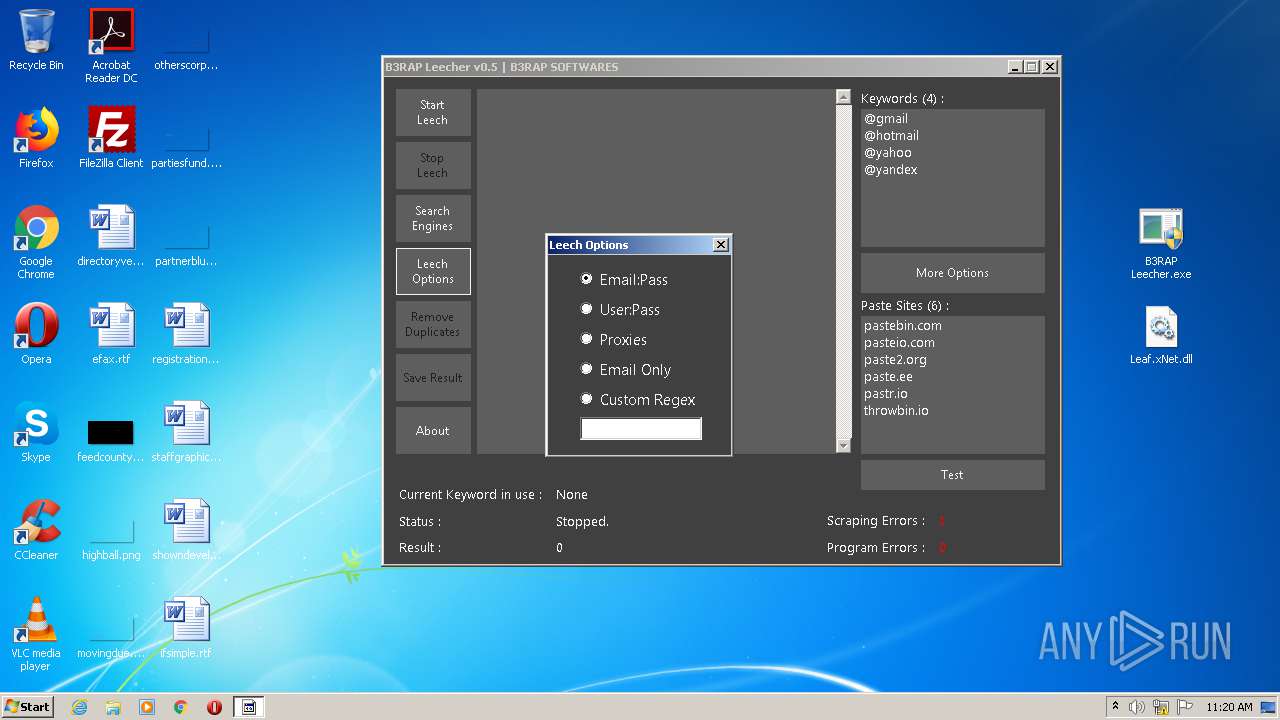
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | B3RAP Leecher.exe | C:\Users\admin\AppData\Local\B3RAP_Leecher\B3RAP_Leecher.exe_Url_megwer2x4it3dw4jglpvzn4ku3d3pcbo\1.0.0.0\ukqbqbj3.newcfg | — | |
MD5:— | SHA256:— | |||
| 2580 | B3RAP Leecher.exe | C:\Users\admin\AppData\Local\B3RAP_Leecher\B3RAP_Leecher.exe_Url_megwer2x4it3dw4jglpvzn4ku3d3pcbo\1.0.0.0\xt4ma1tr.newcfg | — | |
MD5:— | SHA256:— | |||
| 2580 | B3RAP Leecher.exe | C:\Users\admin\AppData\Local\B3RAP_Leecher\B3RAP_Leecher.exe_Url_megwer2x4it3dw4jglpvzn4ku3d3pcbo\1.0.0.0\osvszysg.newcfg | — | |
MD5:— | SHA256:— | |||
| 2580 | B3RAP Leecher.exe | C:\Users\admin\AppData\Local\B3RAP_Leecher\B3RAP_Leecher.exe_Url_megwer2x4it3dw4jglpvzn4ku3d3pcbo\1.0.0.0\1n1fcjmh.newcfg | — | |
MD5:— | SHA256:— | |||
| 2580 | B3RAP Leecher.exe | C:\Users\admin\AppData\Local\B3RAP_Leecher\B3RAP_Leecher.exe_Url_megwer2x4it3dw4jglpvzn4ku3d3pcbo\1.0.0.0\n0vpuerv.newcfg | — | |
MD5:— | SHA256:— | |||
| 2580 | B3RAP Leecher.exe | C:\Users\admin\AppData\Local\B3RAP_Leecher\B3RAP_Leecher.exe_Url_megwer2x4it3dw4jglpvzn4ku3d3pcbo\1.0.0.0\jqzn3b0t.newcfg | — | |
MD5:— | SHA256:— | |||
| 1200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC38483-4B0.pma | — | |
MD5:— | SHA256:— | |||
| 2668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2668.9477\B3RAP Leecher.exe | executable | |
MD5:— | SHA256:— | |||
| 2580 | B3RAP Leecher.exe | C:\Users\admin\AppData\Roaming\LeakManiaVPN\CONFIG\LeakMania-NL.ovpn | text | |
MD5:— | SHA256:— | |||
| 2580 | B3RAP Leecher.exe | C:\Users\admin\AppData\Local\B3RAP_Leecher\B3RAP_Leecher.exe_Url_megwer2x4it3dw4jglpvzn4ku3d3pcbo\1.0.0.0\user.config | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
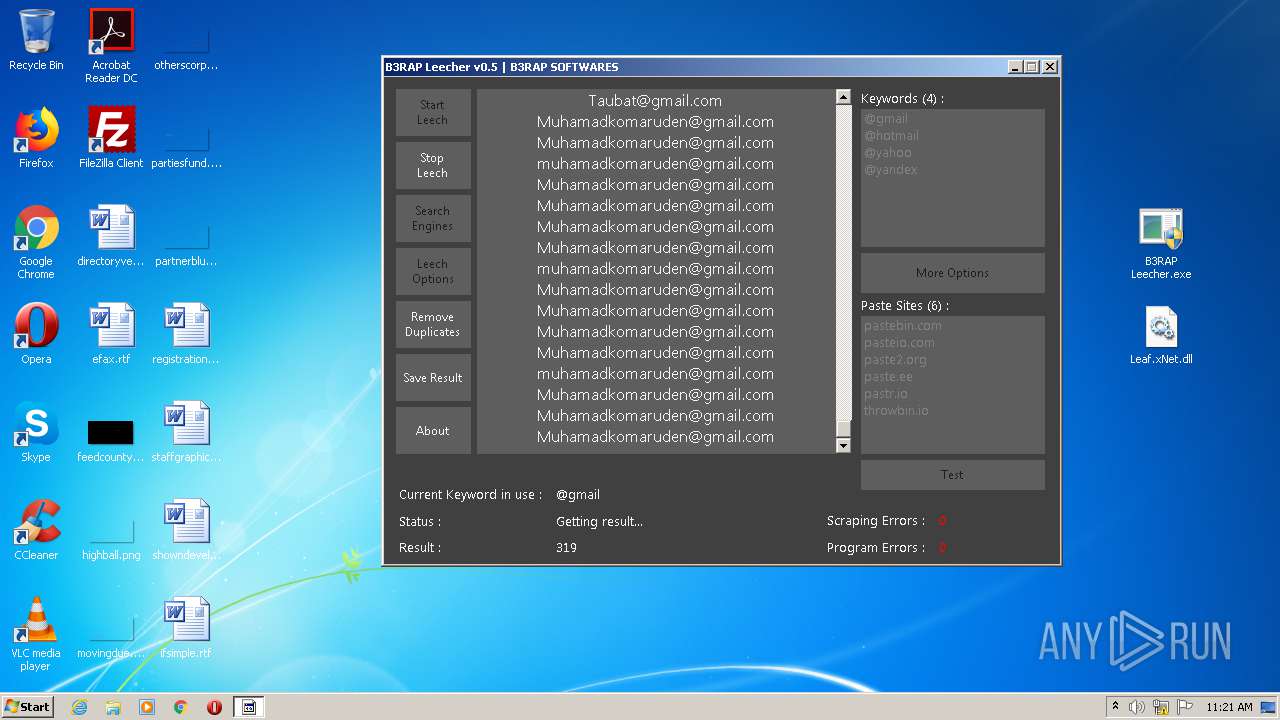
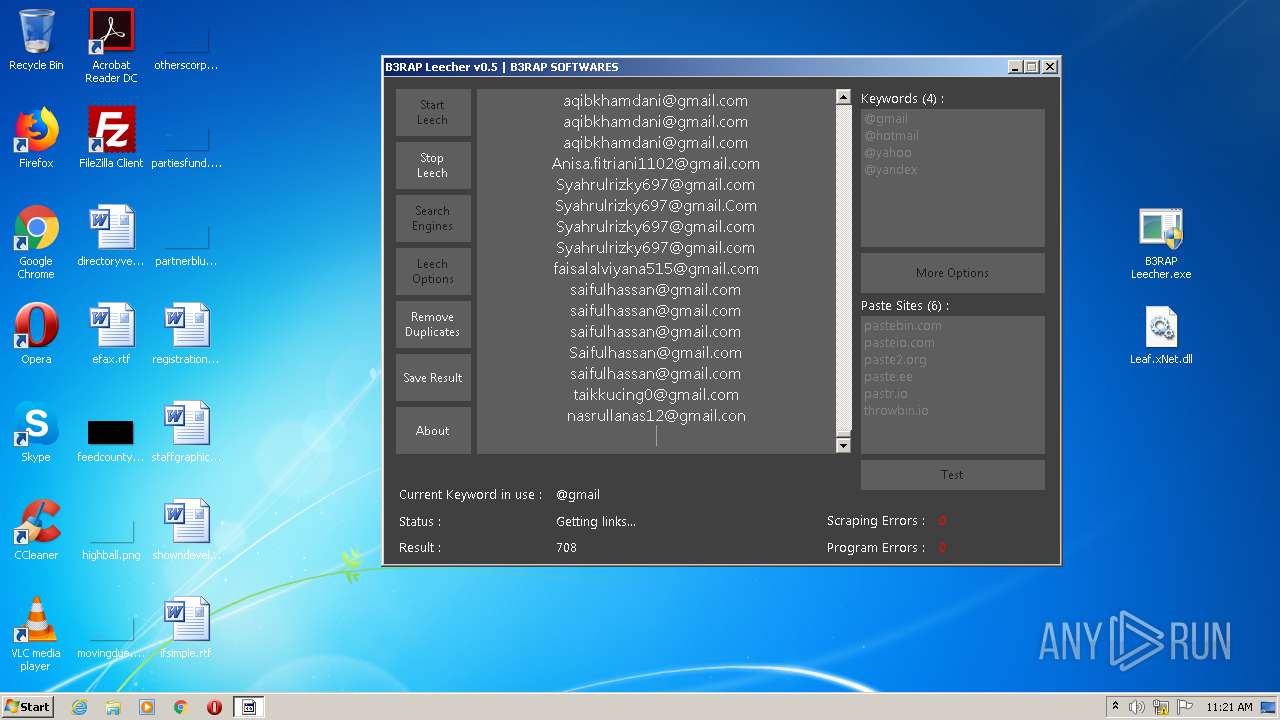
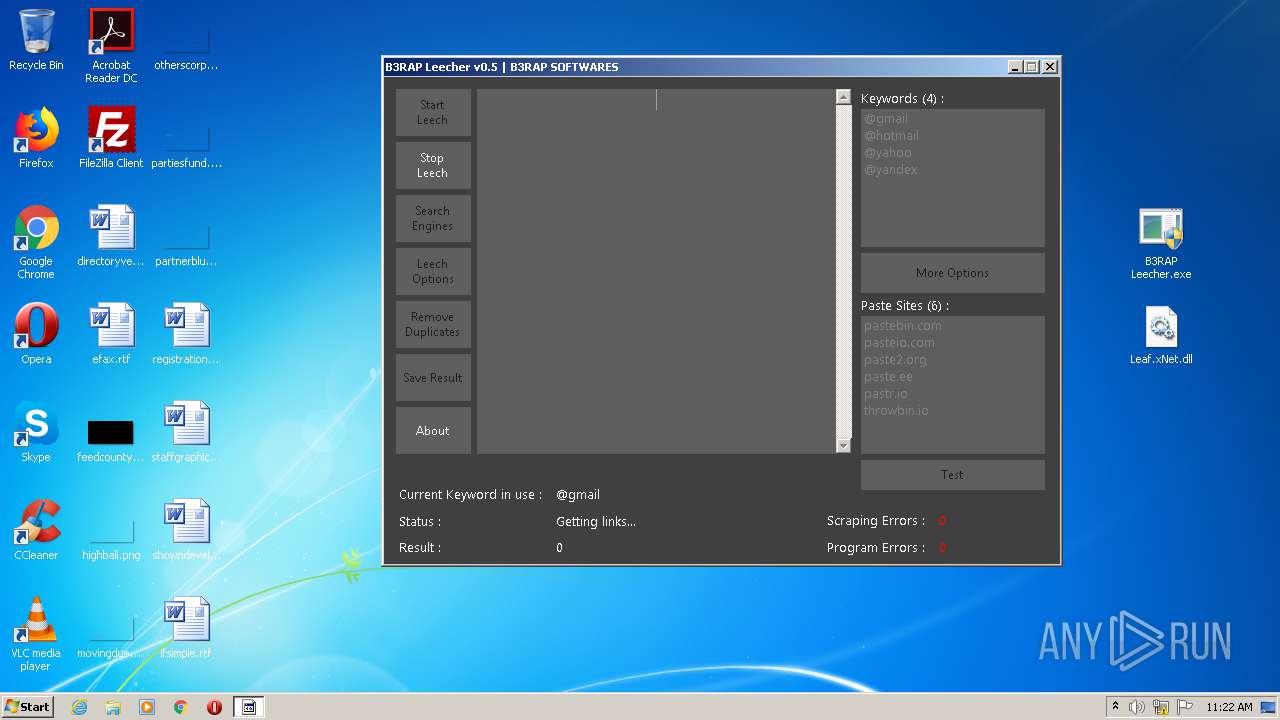
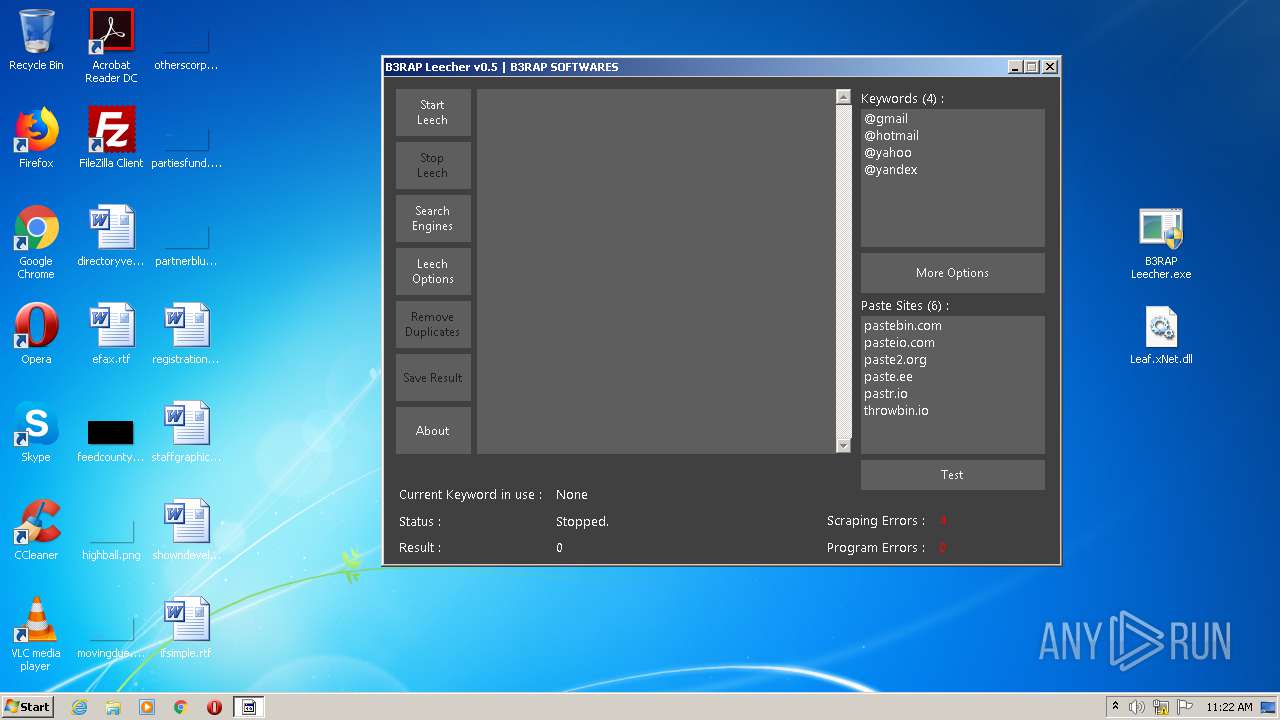
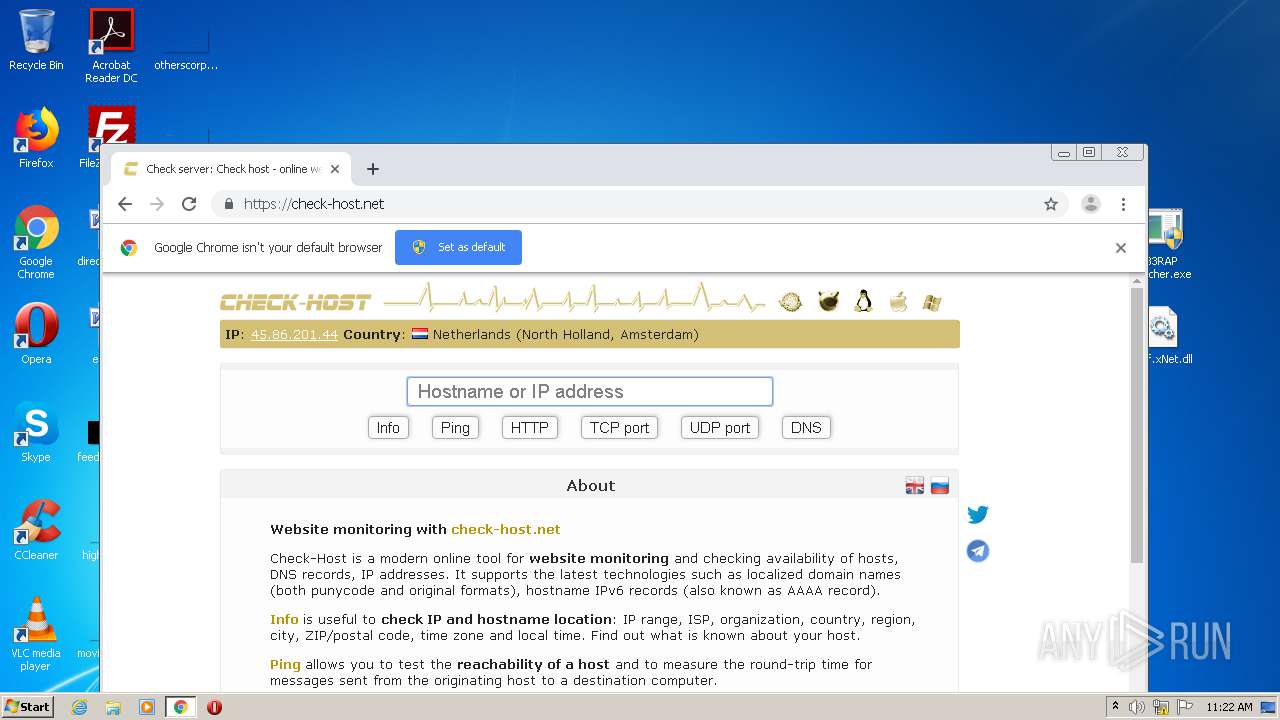
HTTP(S) requests
1
TCP/UDP connections
165
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
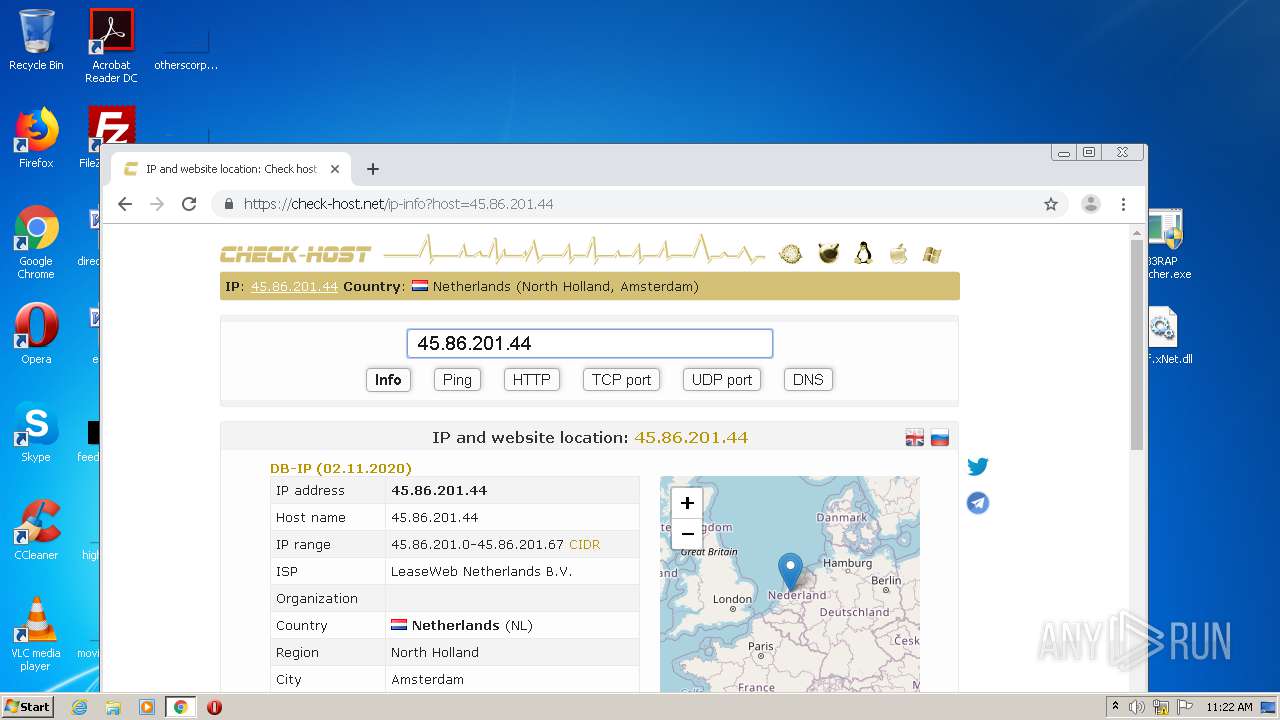
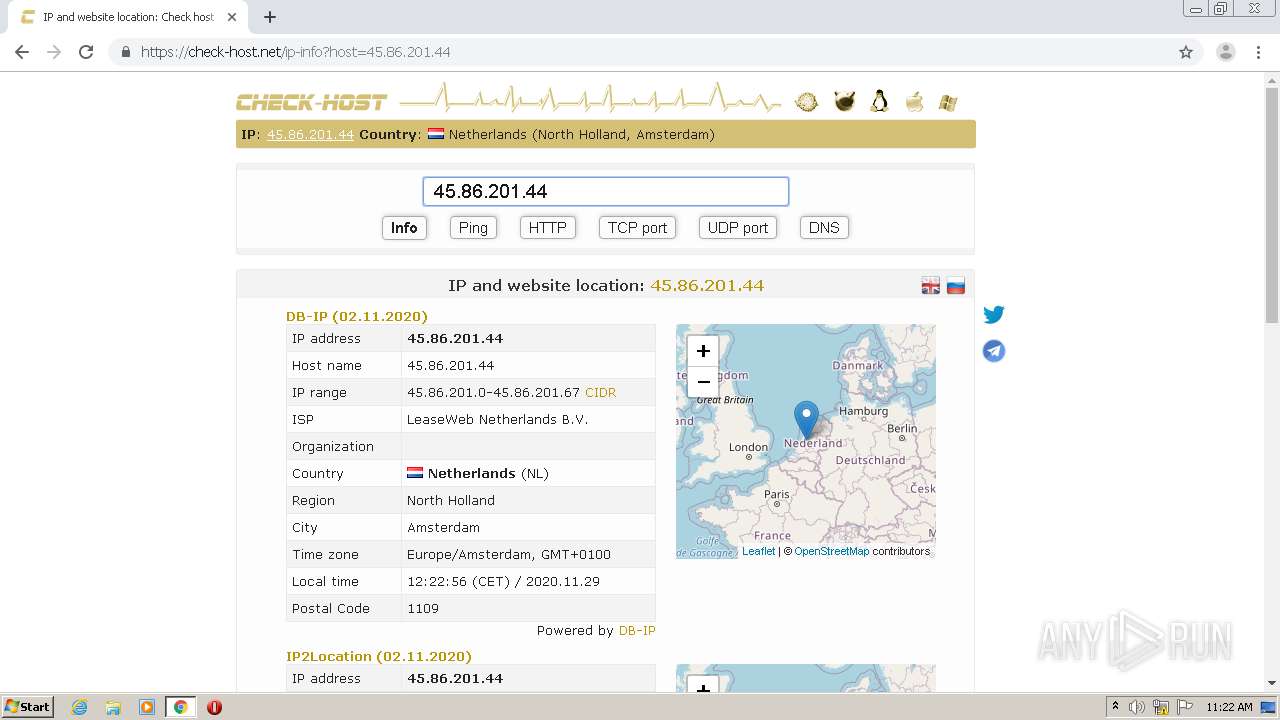
3888 | chrome.exe | GET | 301 | 172.67.165.117:80 | http://check-host.net/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
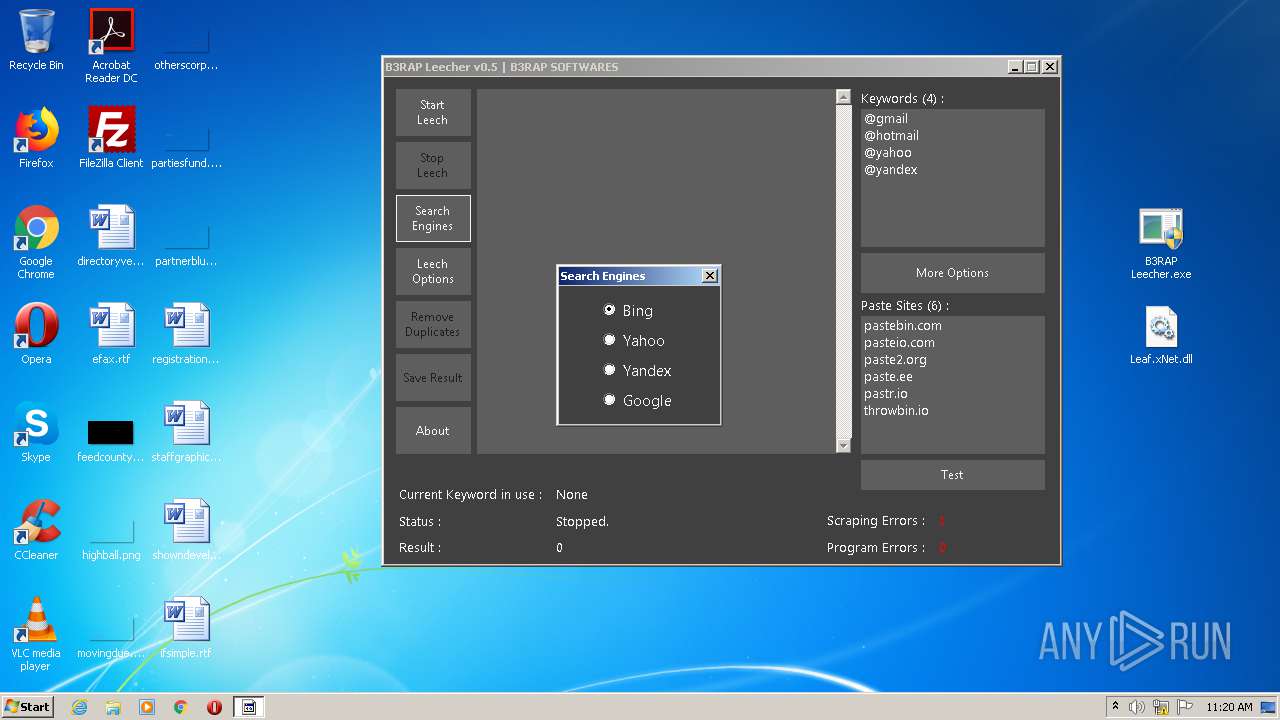
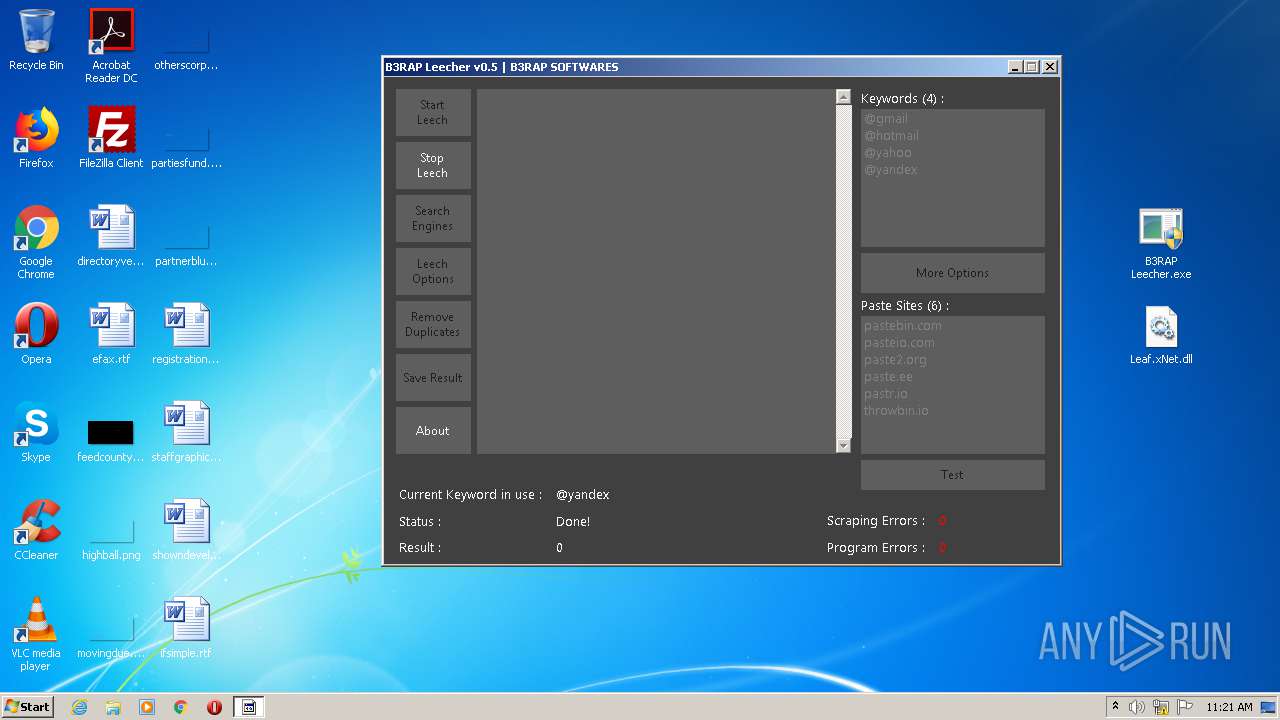
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
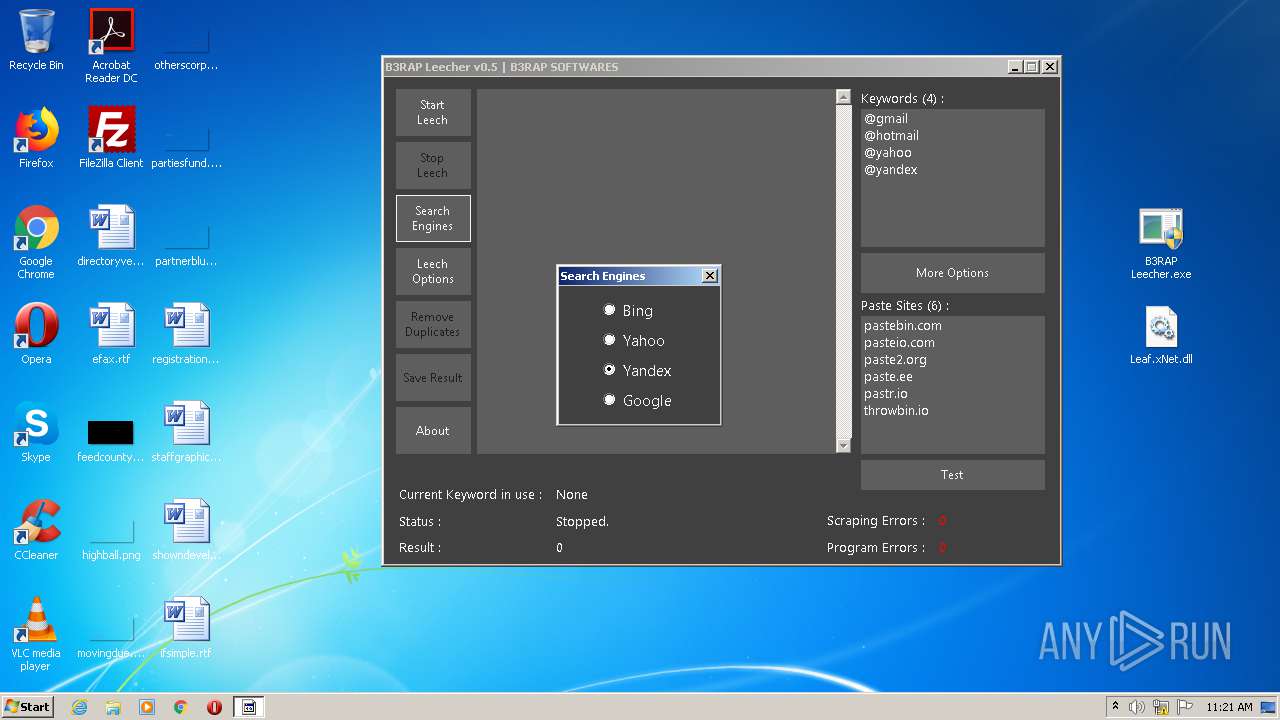
— | — | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
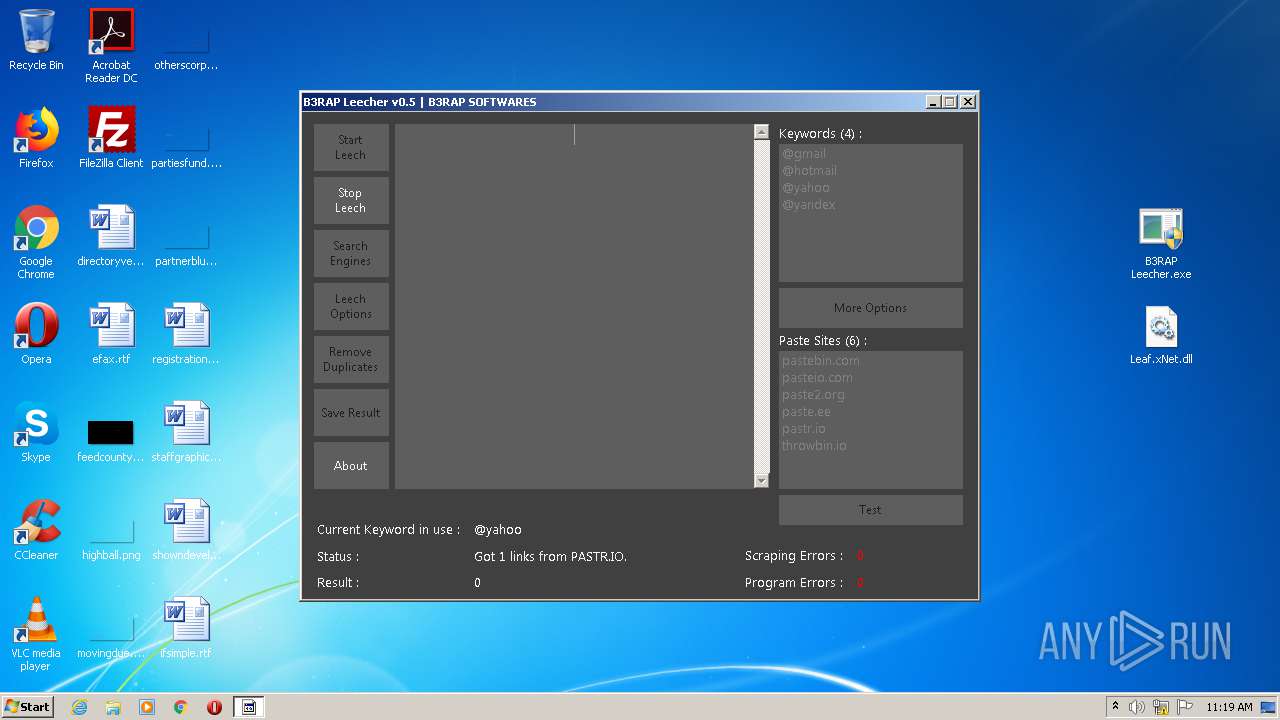
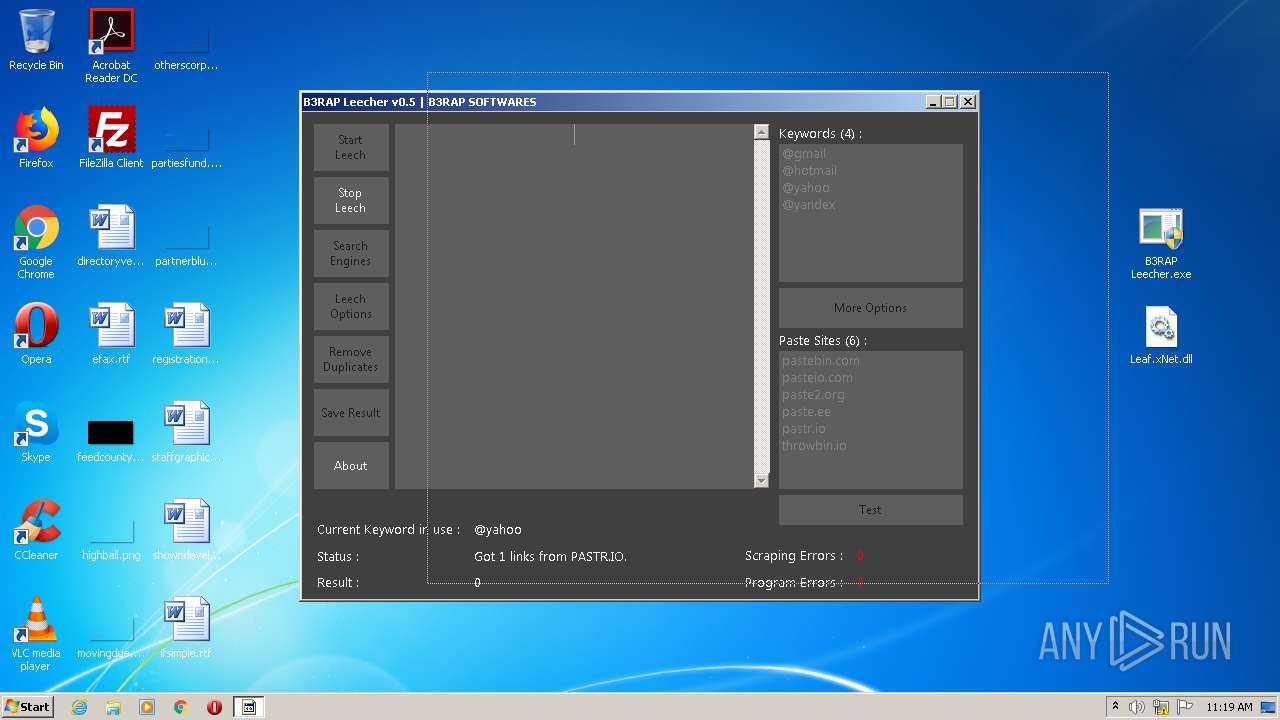
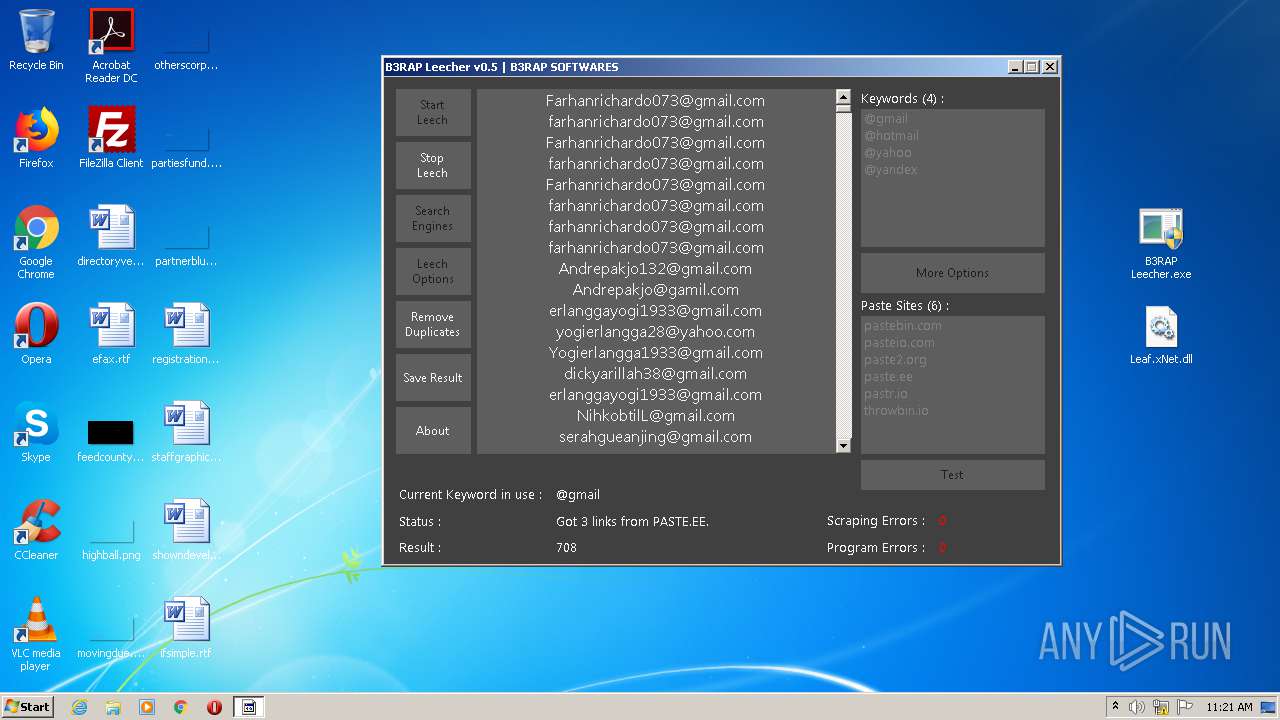
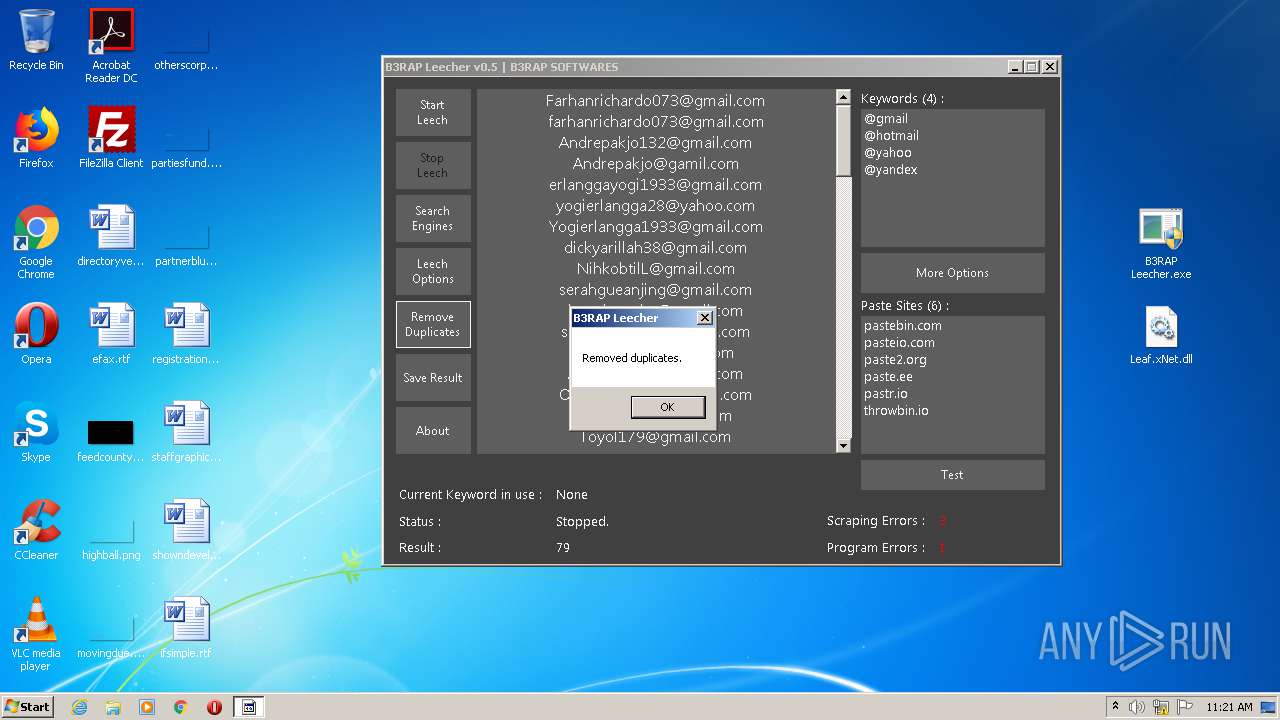
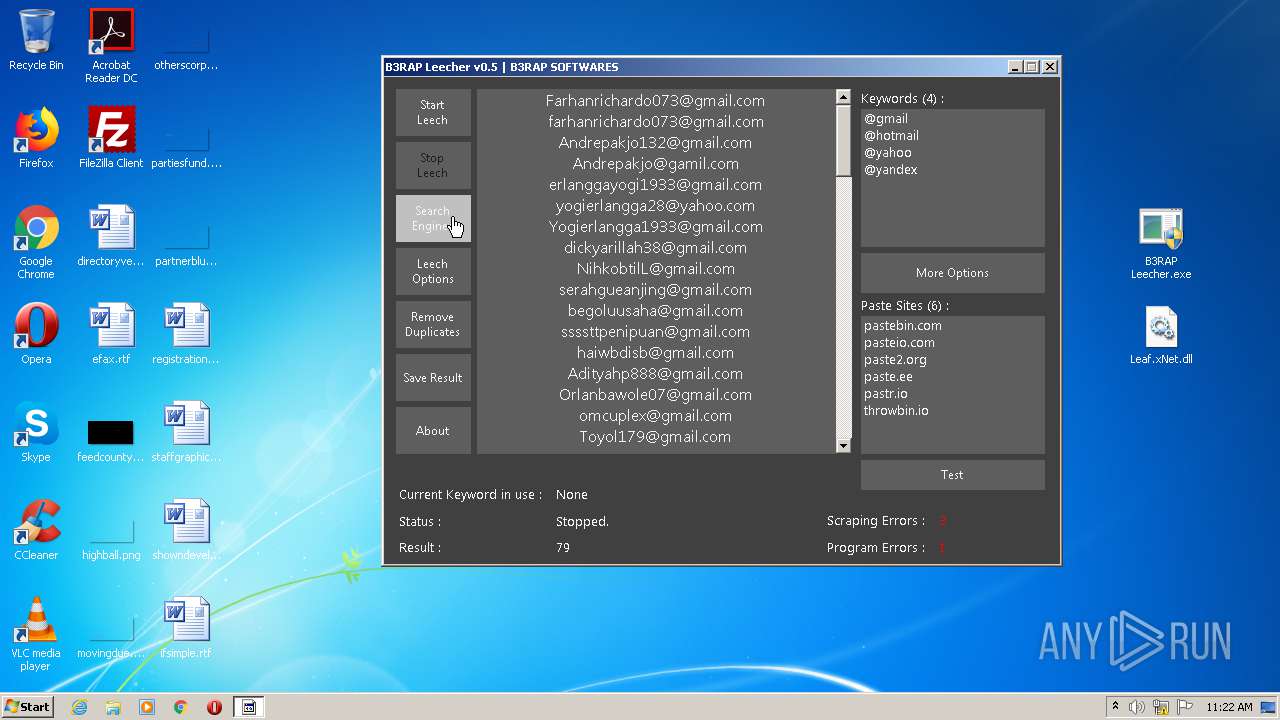
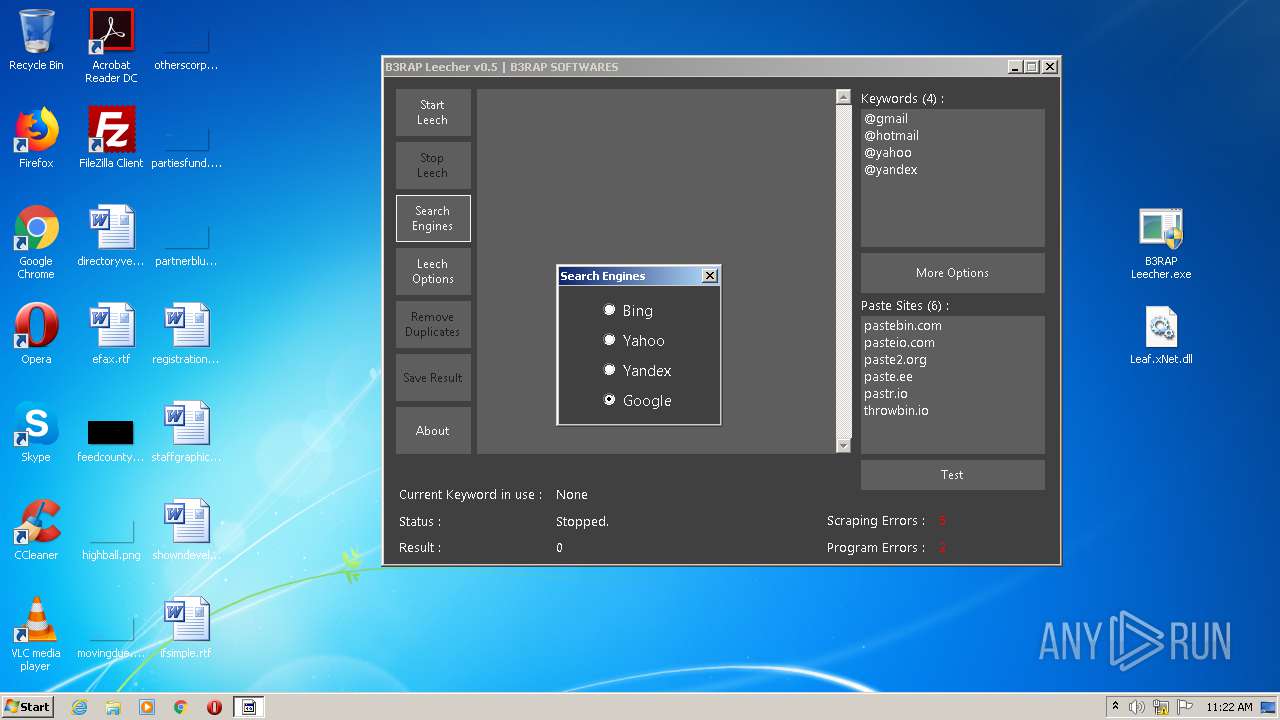
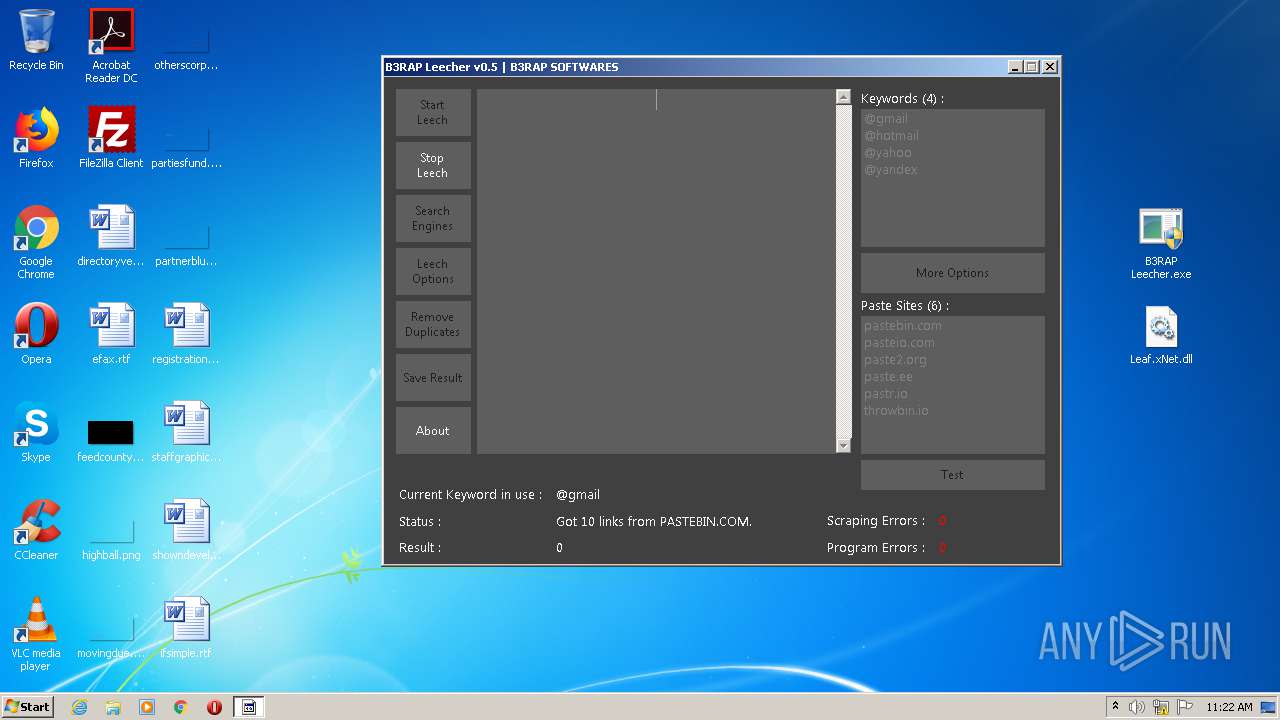
2580 | B3RAP Leecher.exe | 162.255.119.131:443 | pastr.io | Namecheap, Inc. | US | malicious |
2580 | B3RAP Leecher.exe | 104.23.99.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
2580 | B3RAP Leecher.exe | 5.255.255.88:443 | www.yandex.com | YANDEX LLC | RU | whitelisted |
2580 | B3RAP Leecher.exe | 104.27.178.65:443 | throwbin.io | Cloudflare Inc | US | shared |
— | — | 104.27.178.65:443 | throwbin.io | Cloudflare Inc | US | shared |
2580 | B3RAP Leecher.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2580 | B3RAP Leecher.exe | 172.67.164.22:443 | pasteio.com | — | US | unknown |
2580 | B3RAP Leecher.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
pastebin.com |
| malicious |
paste2.org |
| whitelisted |
paste.ee |
| malicious |
pastr.io |
| malicious |
www.yandex.com |
| whitelisted |
pasteio.com |
| malicious |
www.google.com |
| malicious |
throwbin.io |
| malicious |
clientservices.googleapis.com |
| whitelisted |