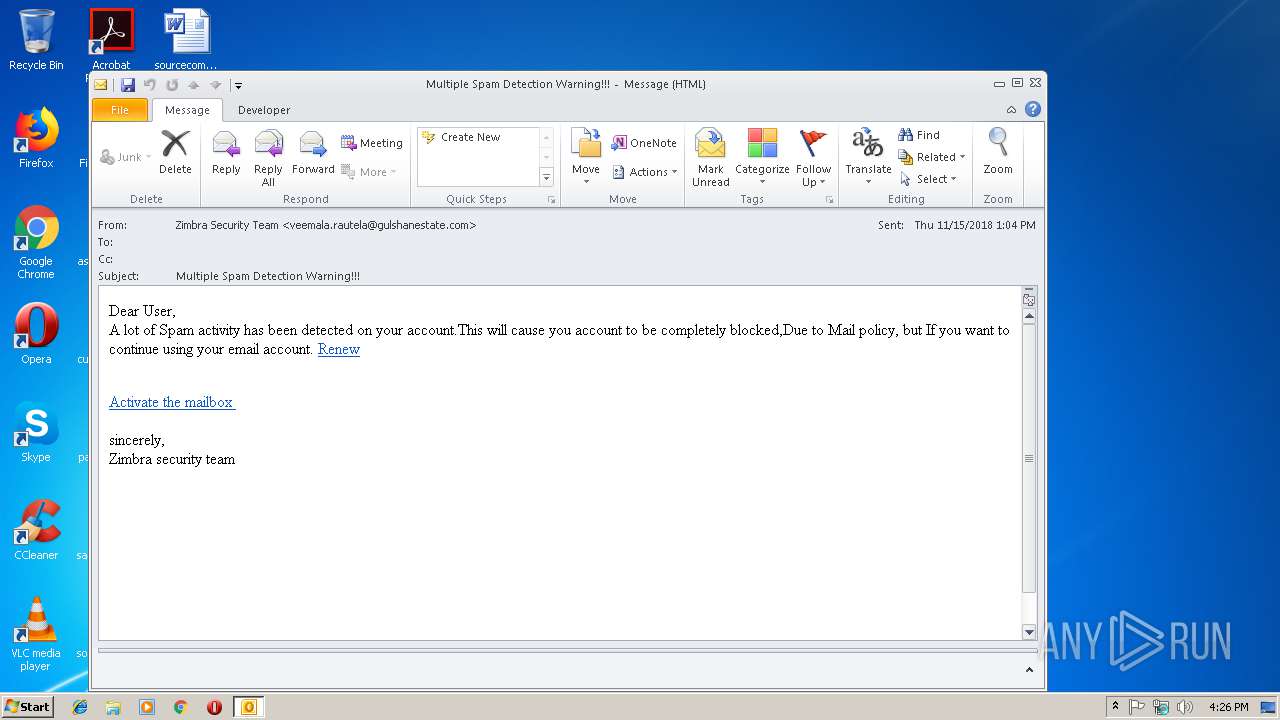
| File name: | Multiple Spam Detection Warning!!!.eml |
| Full analysis: | https://app.any.run/tasks/c0b18a9c-5e0e-43e8-a68e-9053055fcb18 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 16:26:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with CRLF line terminators |
| MD5: | 8EEF8512FE58DEEB30F157115996A05A |
| SHA1: | 56CDAFE8767B165ABE4E7D99F4FA962591FBE35F |
| SHA256: | 0C76F2AD803B4927C828B3B9DDC3A2DA0580498FEF4C9E7B874D706DF2F4D9F2 |
| SSDEEP: | 384:ZyczfhiFs/EgcOMIQ2eeHZkRiotykDeezYuZkRiotykAee1SswSMh4eHRBeebbGW:ZycEFs/cTOeeHKRHleezYuKRHKee1Szn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3076)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3076)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3076)
INFO
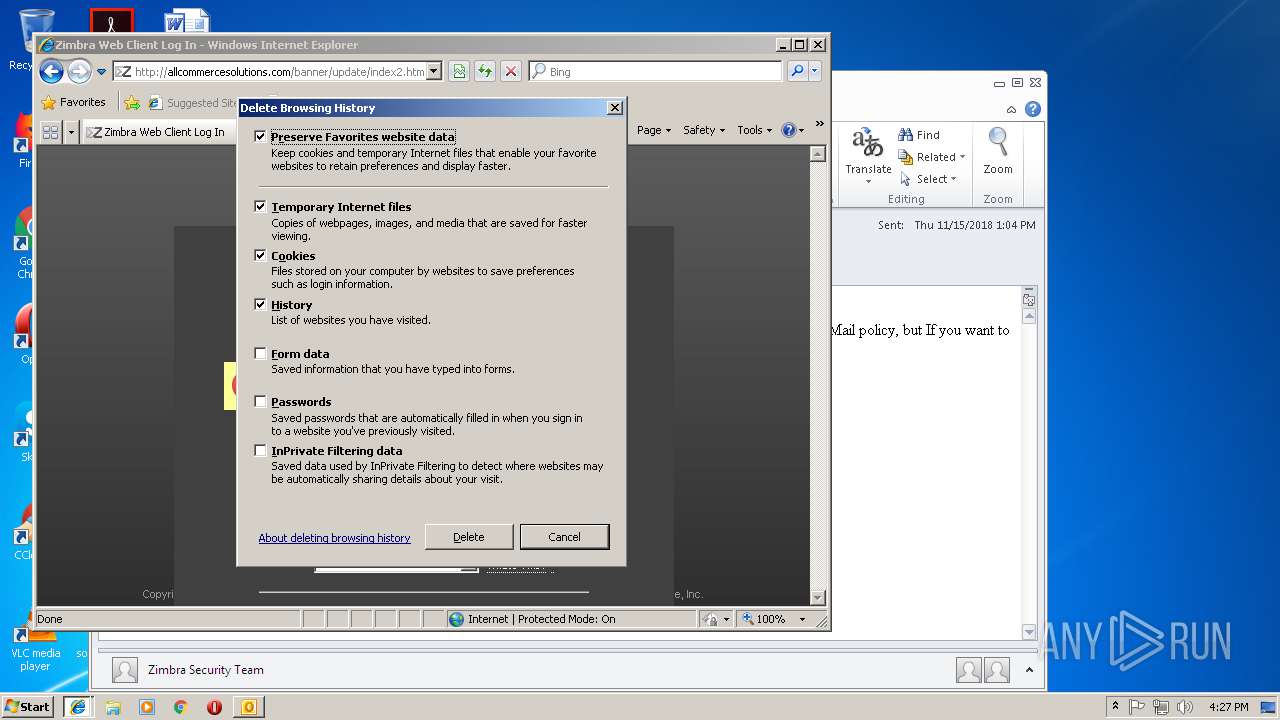
Changes internet zones settings
- iexplore.exe (PID: 3772)
Application launched itself
- iexplore.exe (PID: 3772)
Reads Internet Cache Settings
- iexplore.exe (PID: 4016)
- iexplore.exe (PID: 3772)
- iexplore.exe (PID: 2460)
Reads internet explorer settings
- iexplore.exe (PID: 4016)
- iexplore.exe (PID: 2460)
Creates files in the user directory
- iexplore.exe (PID: 4016)
- iexplore.exe (PID: 3772)
Reads settings of System Certificates
- iexplore.exe (PID: 3772)
Connects to unusual port
- iexplore.exe (PID: 3772)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 3) (100) |
|---|
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2460 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3772 CREDAT:6403 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3076 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Multiple Spam Detection Warning!!!.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
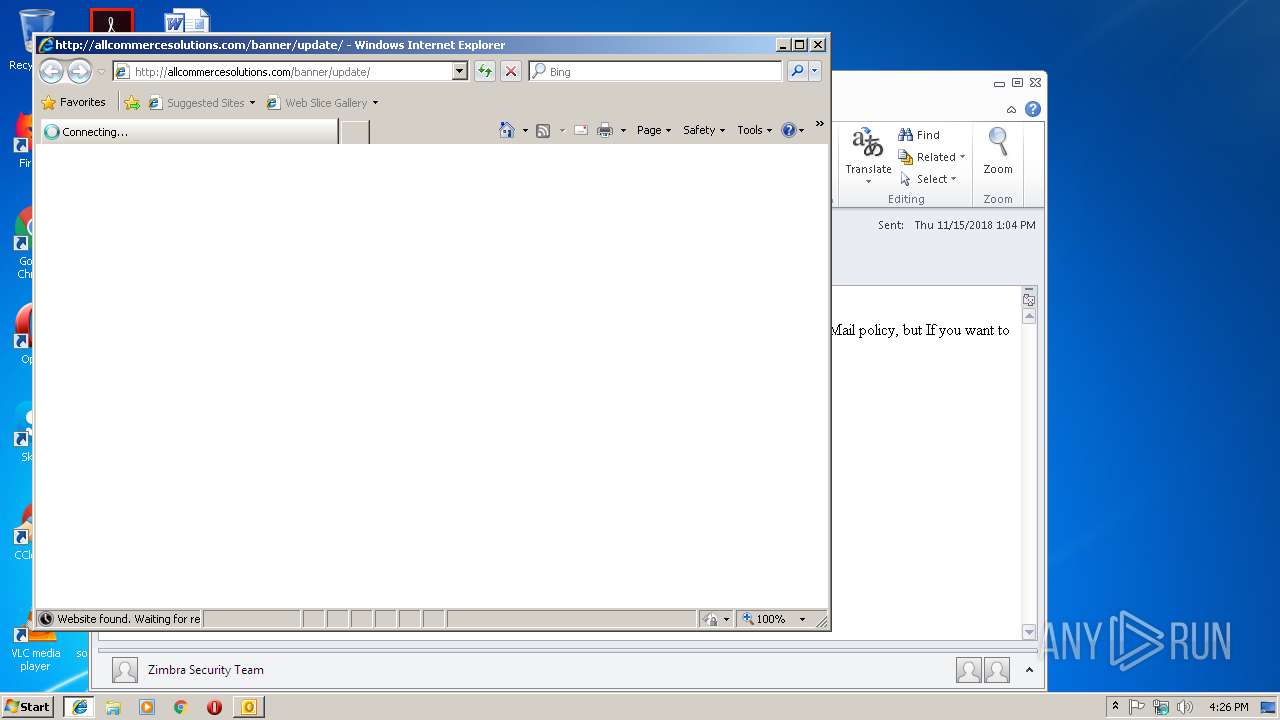
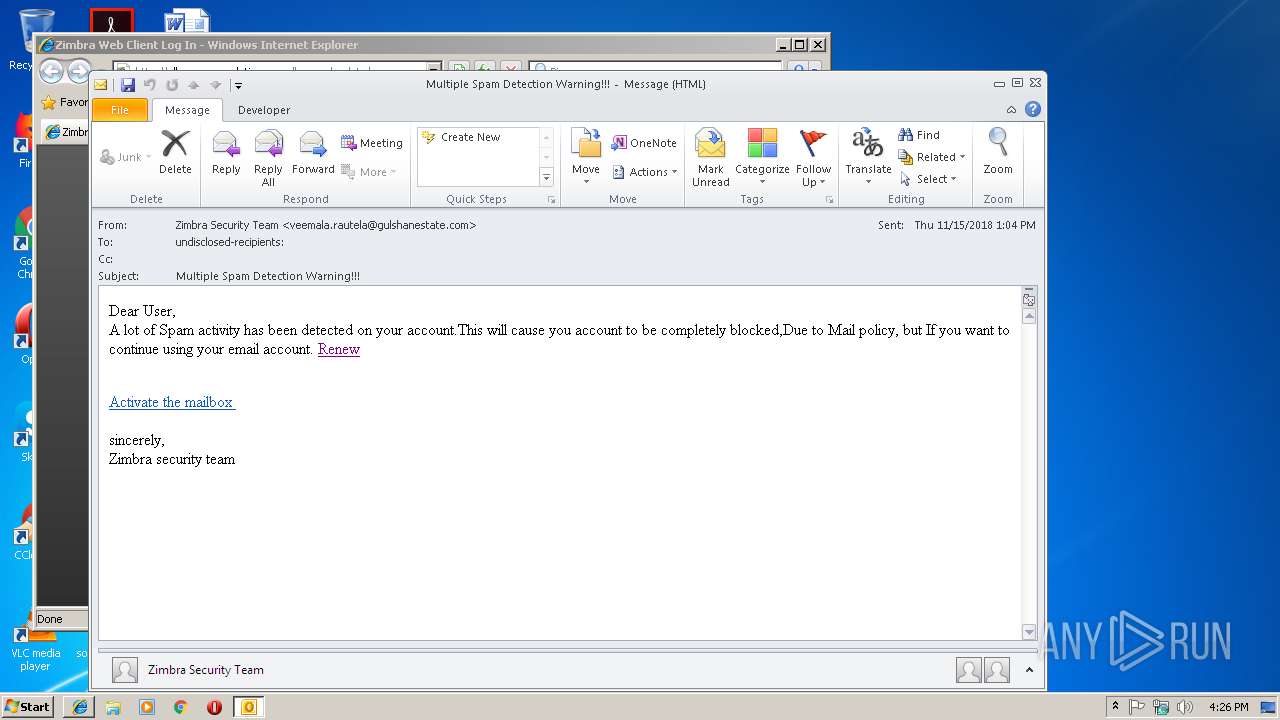
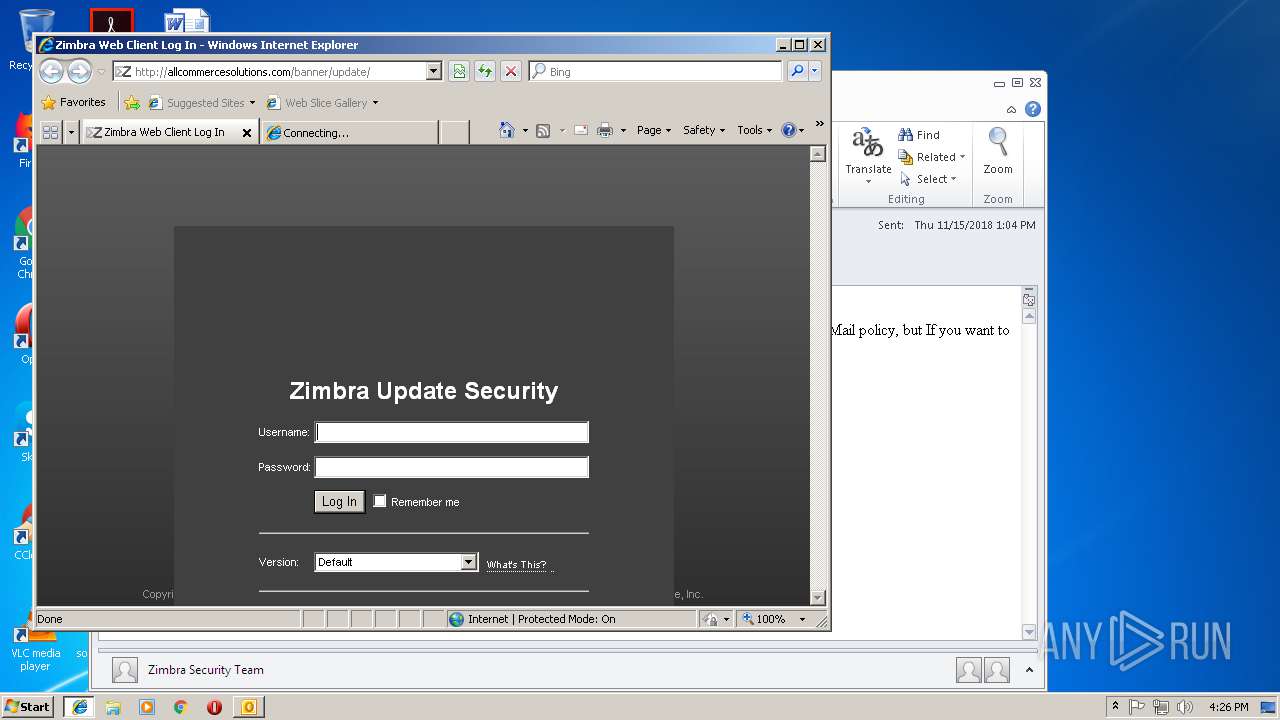
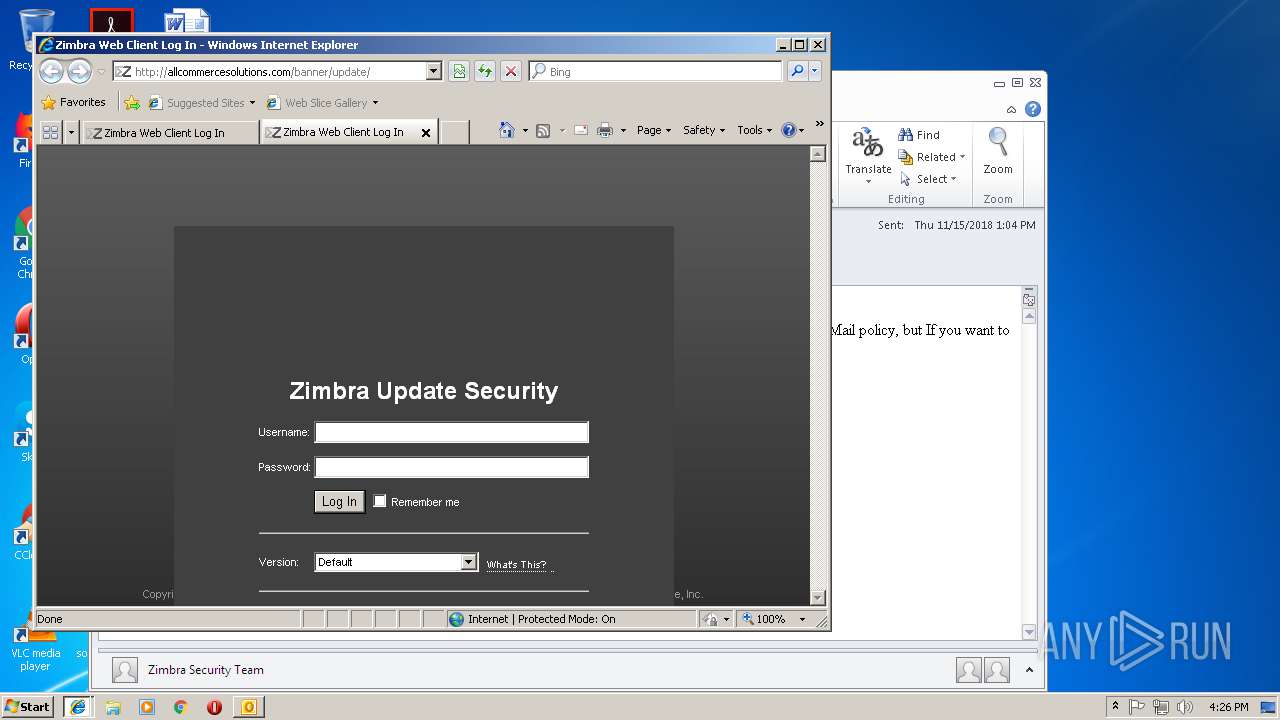
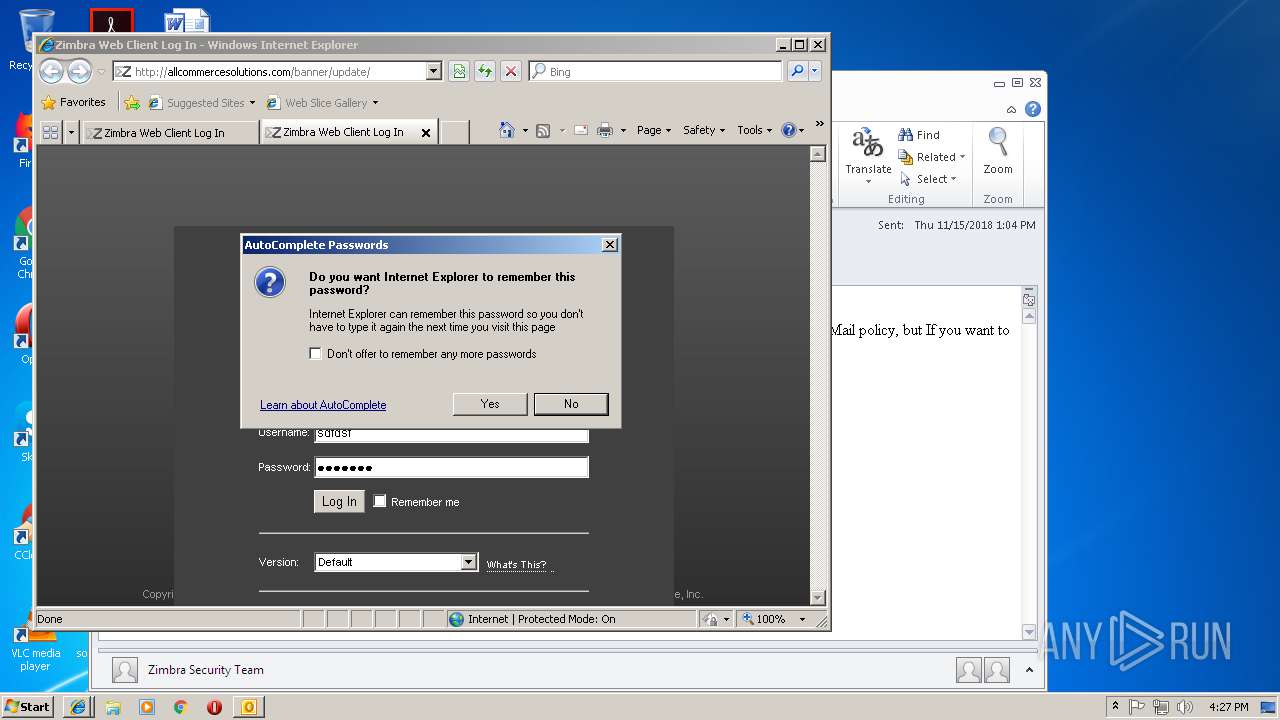
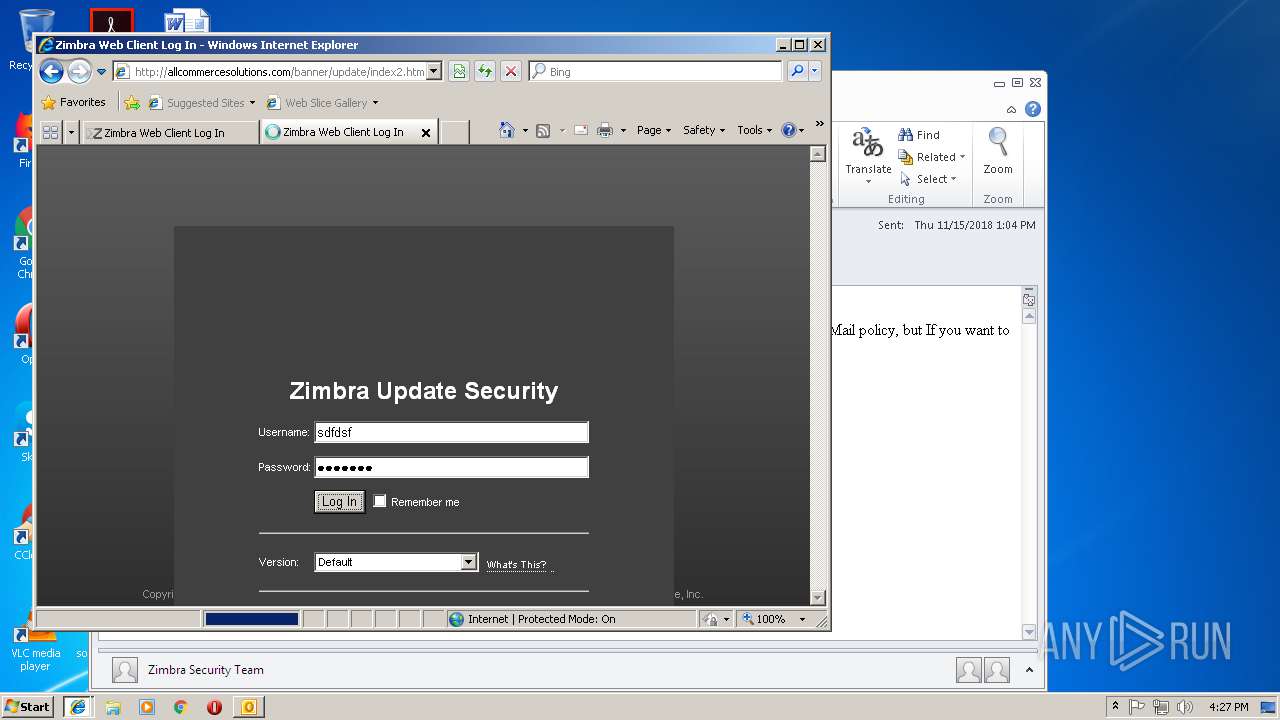
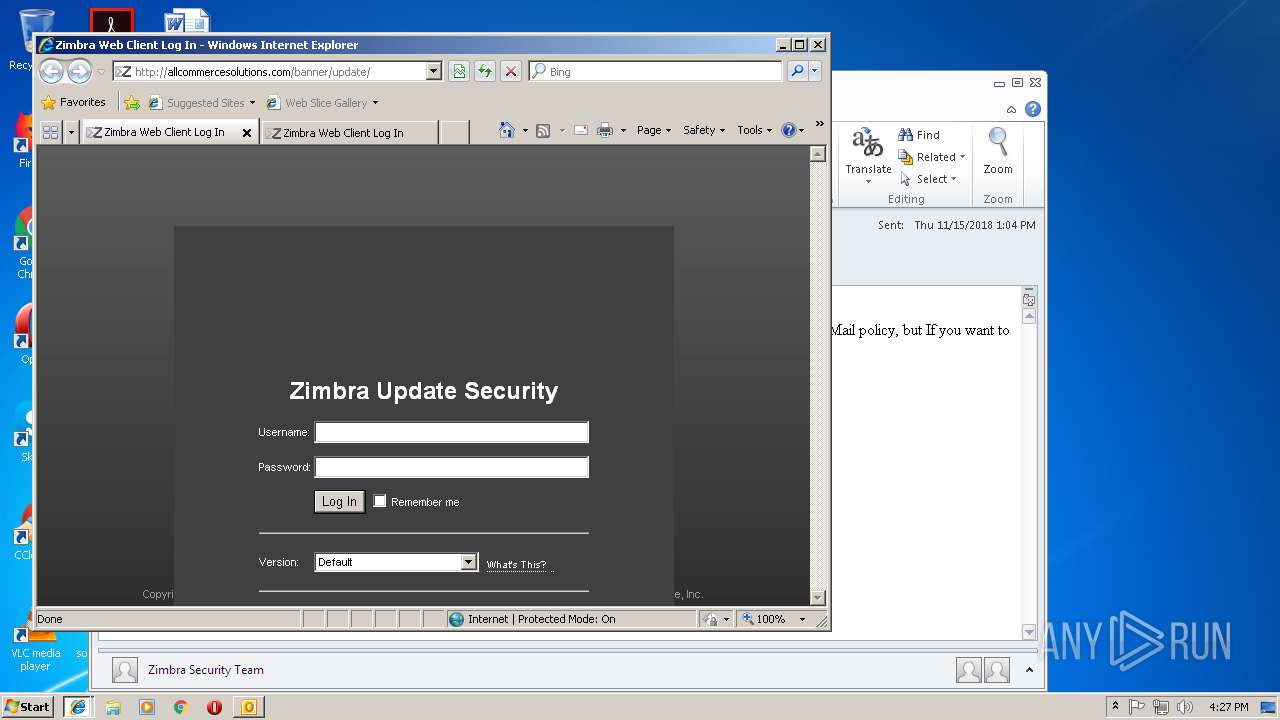
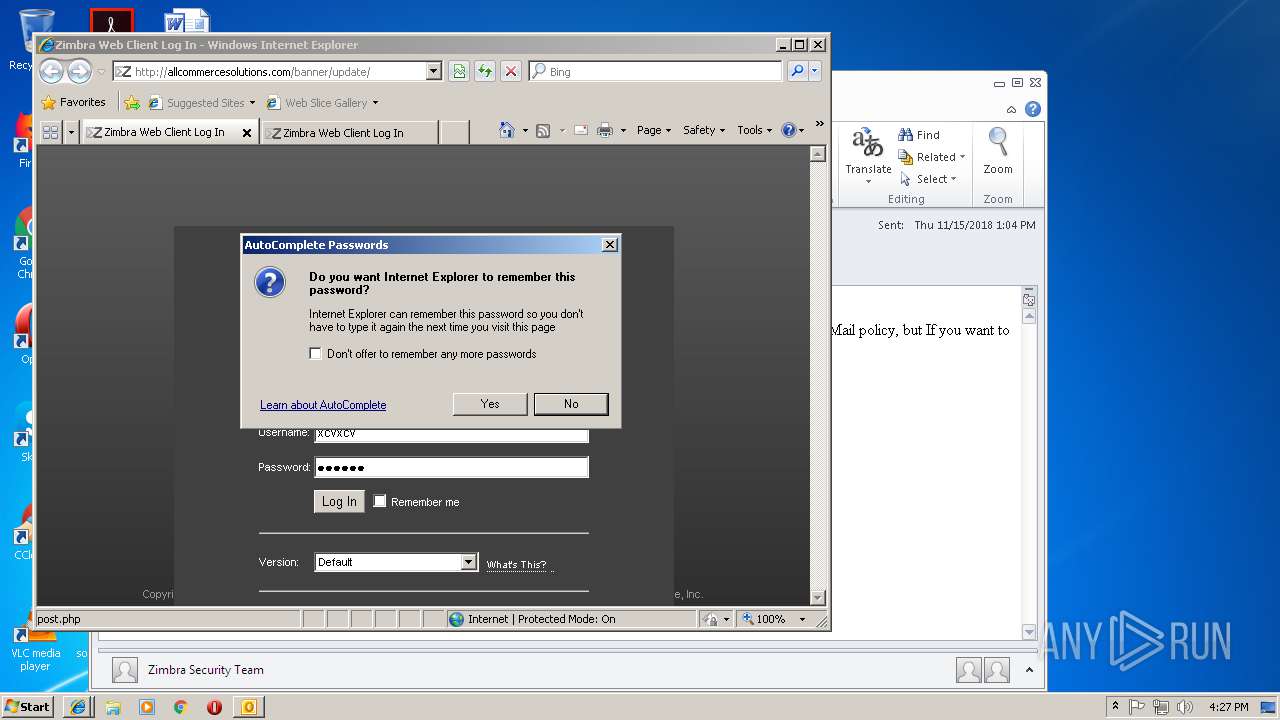
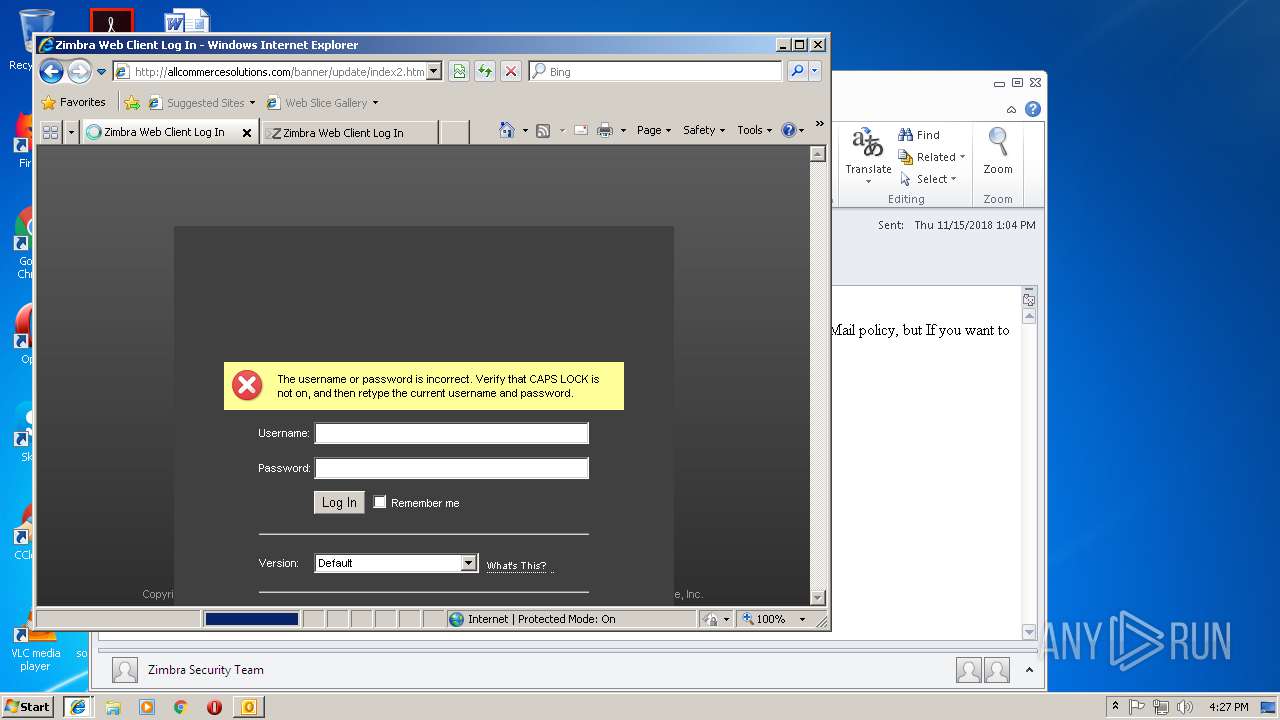
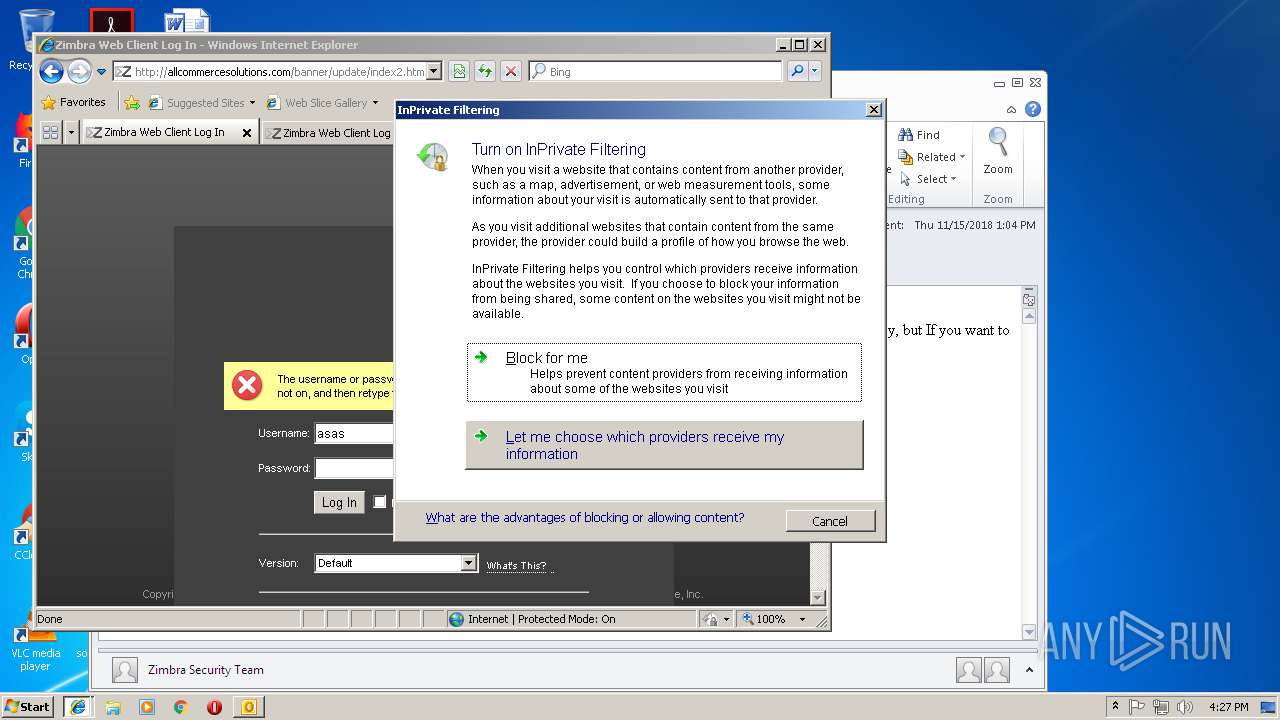
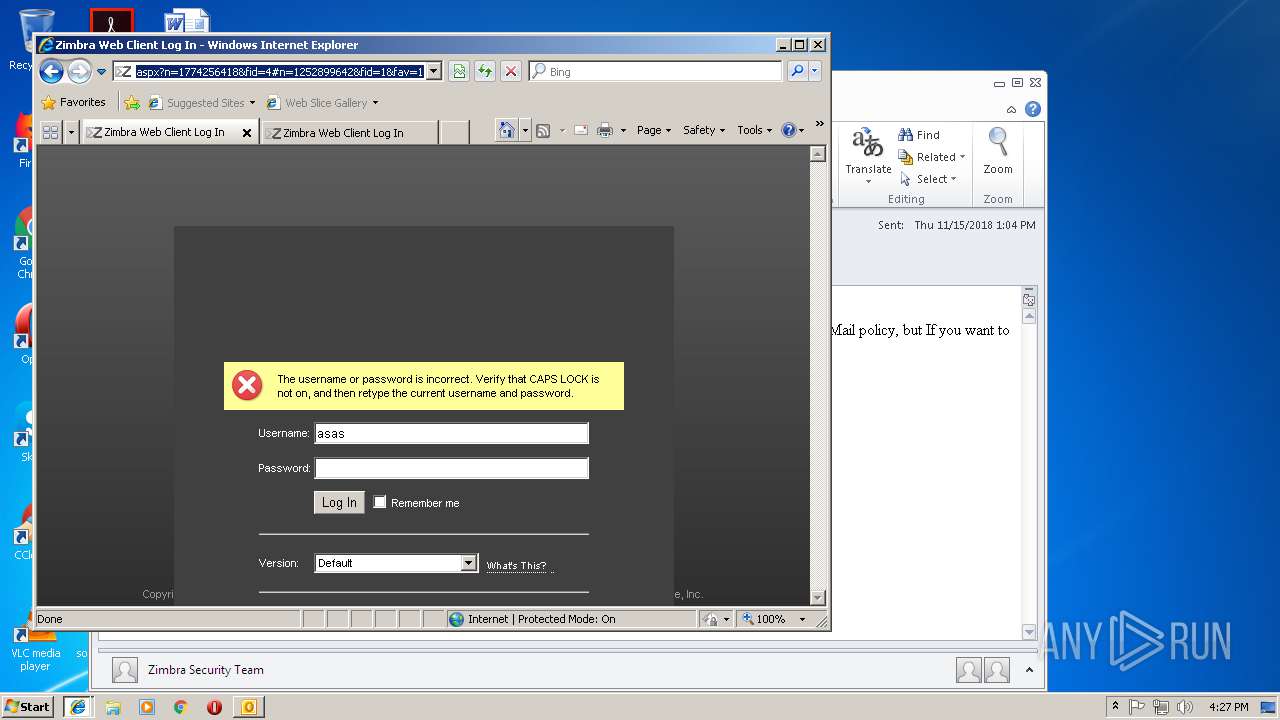
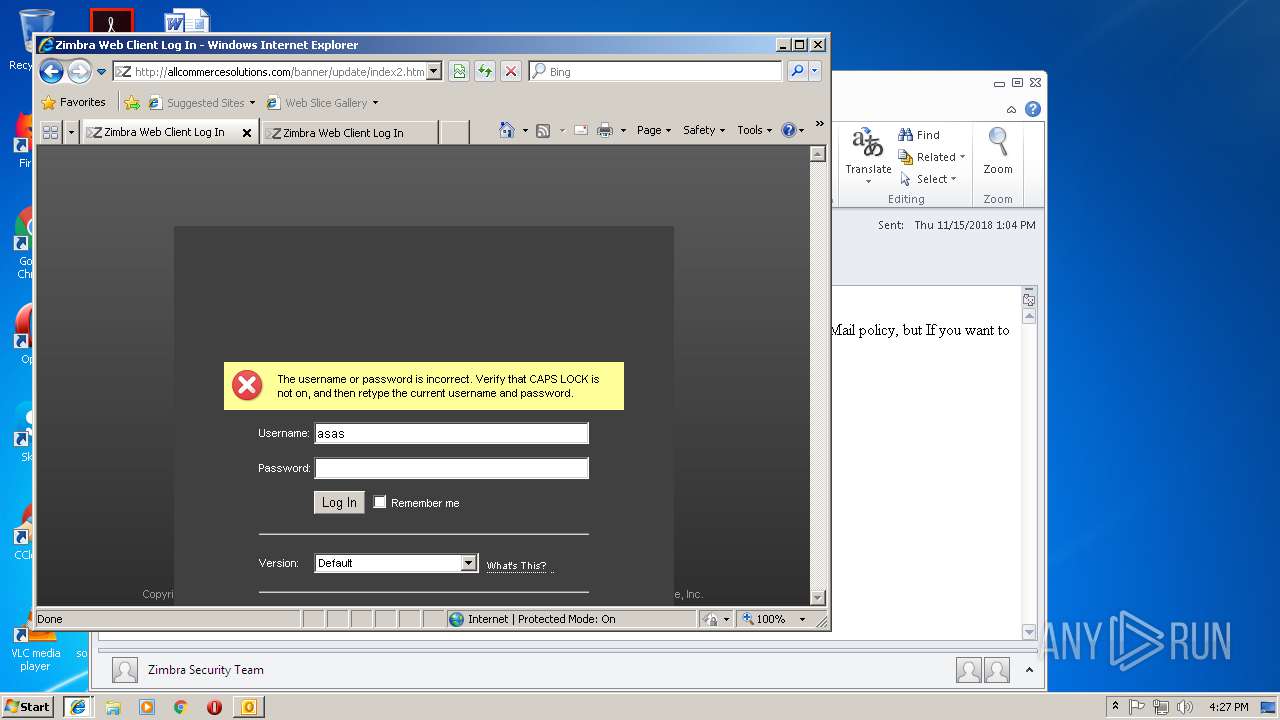
| 3772 | "C:\Program Files\Internet Explorer\iexplore.exe" http://allcommercesolutions.com/banner/update/ | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4016 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3772 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 918
Read events
1 418
Write events
478
Delete events
22
Modification events
| (PID) Process: | (3076) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3076) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3076) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | f7f81a39-5f63-5b42-9efd-1f13b5431005lt;< |
Value: 243C3C00040C0000010000000000000000000000 | |||
| (PID) Process: | (3076) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 040C00008A3675FEFF7CD40100000000 | |||
| (PID) Process: | (3076) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3076) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219778560 | |||
| (PID) Process: | (3076) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3076) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3076) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3076) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1299120149 | |||
Executable files
0
Suspicious files
4
Text files
34
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3076 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9424.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabB48C.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarB48D.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabB49E.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarB49F.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabB5E8.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarB5E9.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
22
DNS requests
6
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4016 | iexplore.exe | GET | — | 65.60.41.2:80 | http://allcommercesolutions.com/banner/update/index_files/common,login,zhtml.css | US | — | — | suspicious |
2460 | iexplore.exe | GET | 304 | 65.60.41.2:80 | http://allcommercesolutions.com/banner/update/ | US | — | — | suspicious |
2460 | iexplore.exe | GET | — | 65.60.41.2:80 | http://allcommercesolutions.com/banner/update/index_files/skin.css | US | — | — | suspicious |
2460 | iexplore.exe | GET | 304 | 65.60.41.2:80 | http://allcommercesolutions.com/banner/update/index_files/common,login,zhtml.css | US | — | — | suspicious |
2460 | iexplore.exe | GET | 304 | 65.60.41.2:80 | http://allcommercesolutions.com/banner/update/index_files/skin.css | US | — | — | suspicious |
4016 | iexplore.exe | GET | 200 | 65.60.41.2:80 | http://allcommercesolutions.com/banner/update/ | US | html | 10.4 Kb | suspicious |
4016 | iexplore.exe | GET | 200 | 65.60.41.2:80 | http://allcommercesolutions.com/banner/update/ | US | html | 10.4 Kb | suspicious |
4016 | iexplore.exe | GET | 200 | 65.60.41.2:80 | http://allcommercesolutions.com/banner/update/index_files/skin.css | US | text | 17.1 Kb | suspicious |
4016 | iexplore.exe | GET | 404 | 65.60.41.2:80 | http://allcommercesolutions.com/zimbra/skins/carbon/logos/LoginBanner.png | US | html | 358 b | suspicious |
4016 | iexplore.exe | GET | 404 | 65.60.41.2:80 | http://allcommercesolutions.com/banner/update/FILES/jquery-ui-1.9.2.custom.min.js?s=1399644532 | US | html | 366 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3076 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3772 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4016 | iexplore.exe | 65.60.41.2:80 | allcommercesolutions.com | SingleHop, Inc. | US | suspicious |
3772 | iexplore.exe | 93.157.128.196:444 | mailhs.highschool.cz | HelaPC s.r.o. | CZ | unknown |
2460 | iexplore.exe | 65.60.41.2:80 | allcommercesolutions.com | SingleHop, Inc. | US | suspicious |
3772 | iexplore.exe | 104.107.216.27:80 | www.download.windowsupdate.com | Akamai International B.V. | NL | whitelisted |
3772 | iexplore.exe | 192.206.5.81:80 | zimbra29.ocpwebserver.com | MegaVelocity Inc. | CA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
allcommercesolutions.com |
| suspicious |
www.bing.com |
| whitelisted |
mailhs.highschool.cz |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
zimbra29.ocpwebserver.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4016 | iexplore.exe | Potentially Bad Traffic | ET INFO Possible Phish - Saved Website Comment Observed |
4016 | iexplore.exe | Potentially Bad Traffic | ET INFO Possible Phish - Saved Website Comment Observed |
4 ETPRO signatures available at the full report