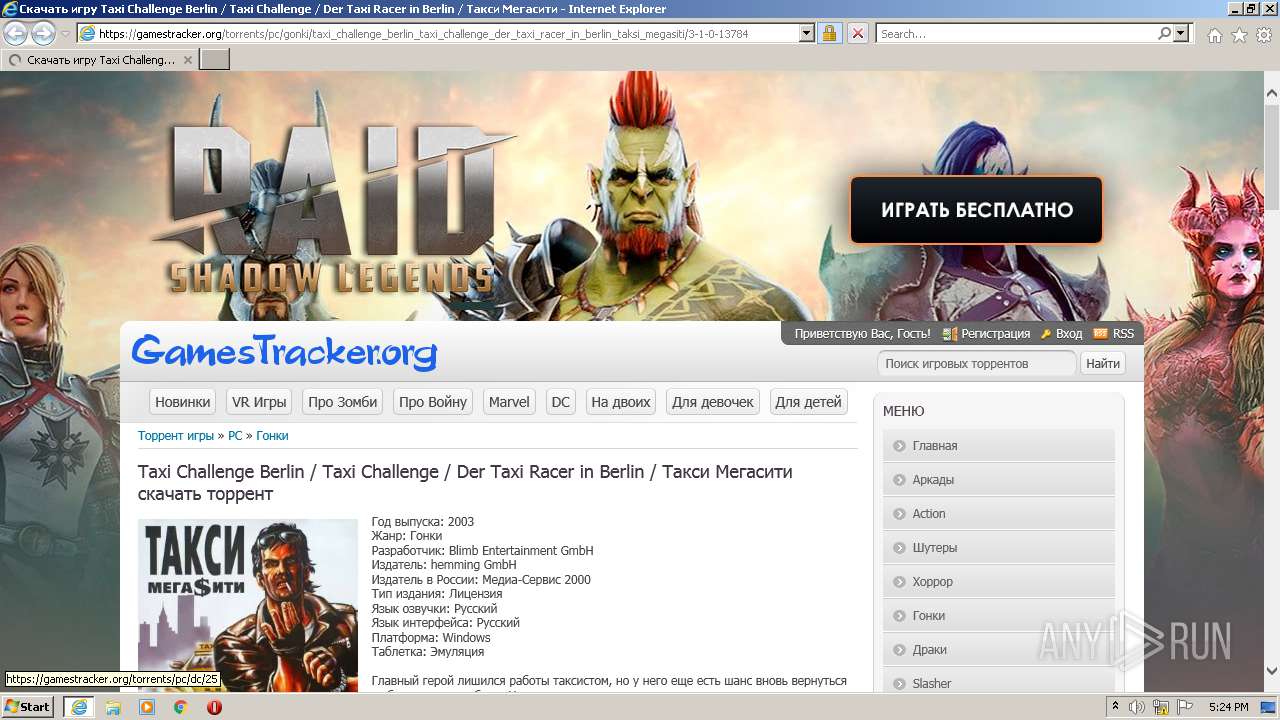
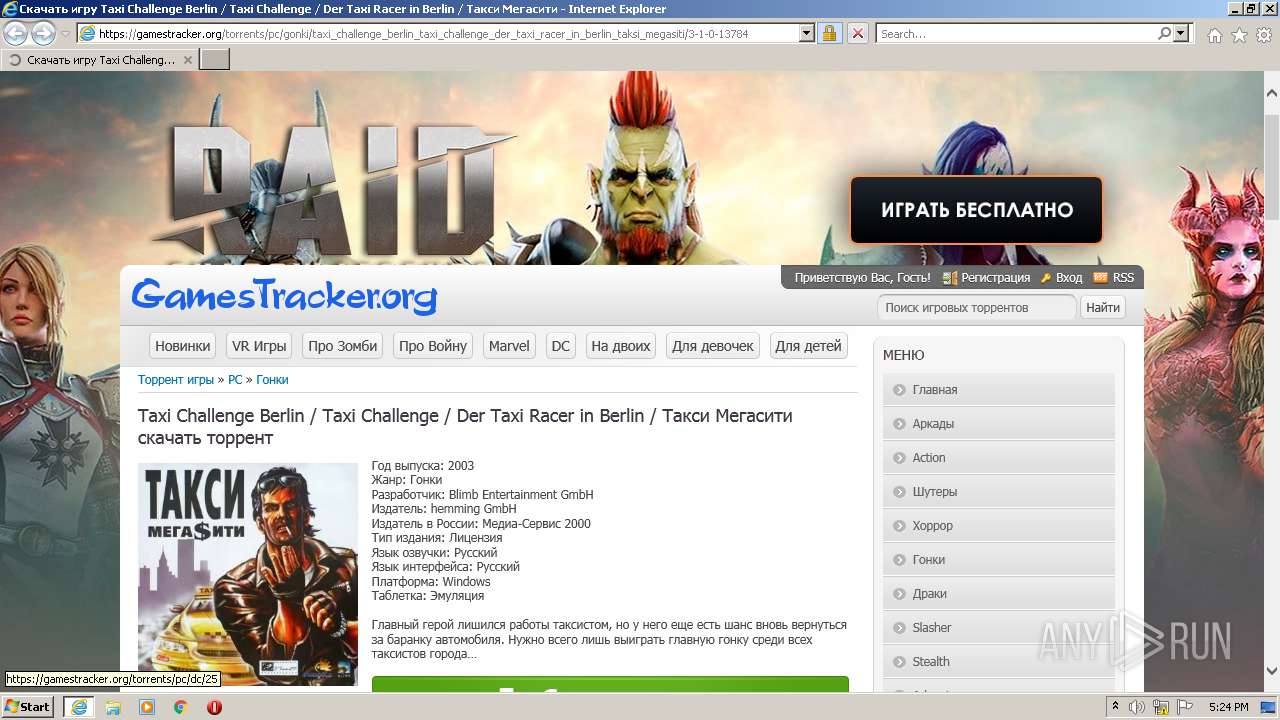
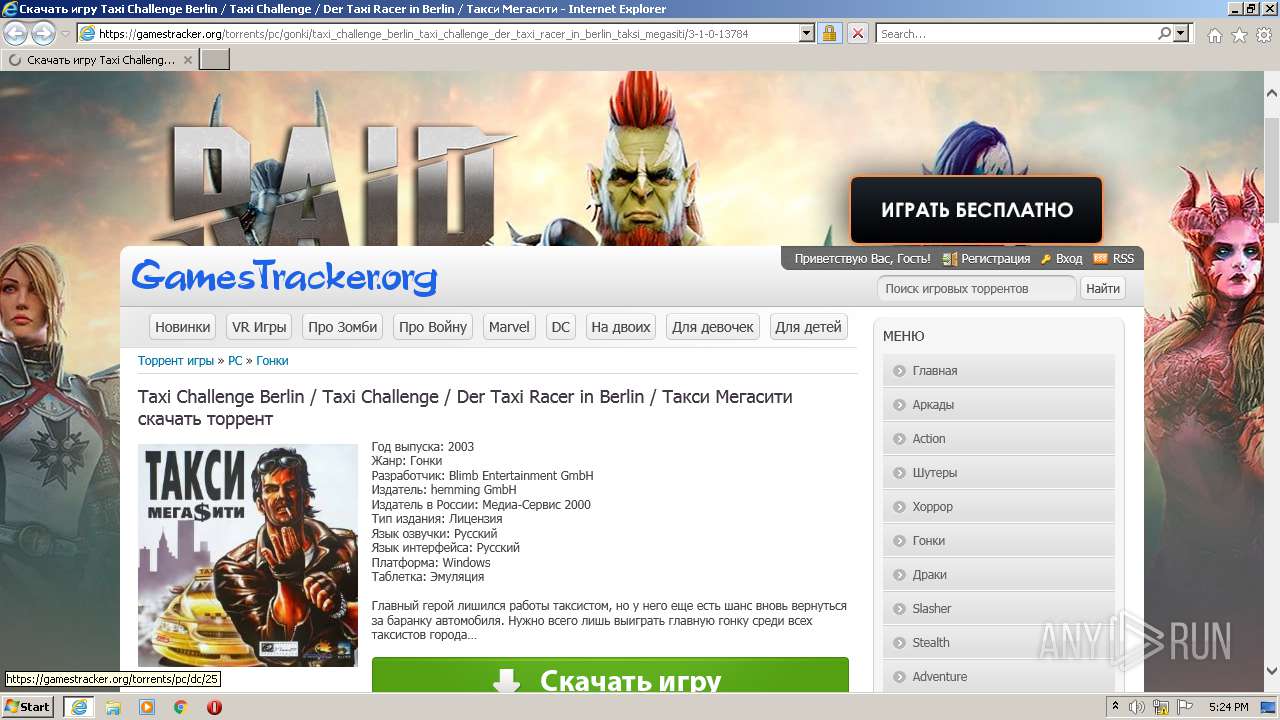
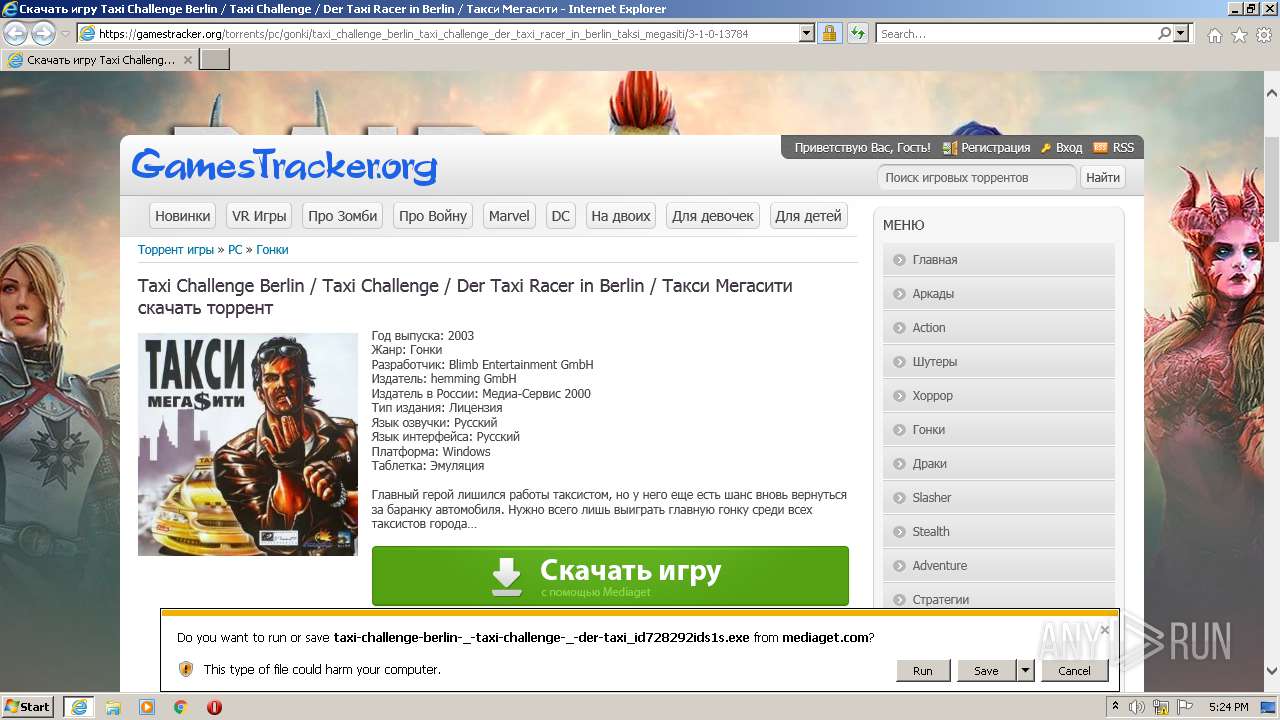
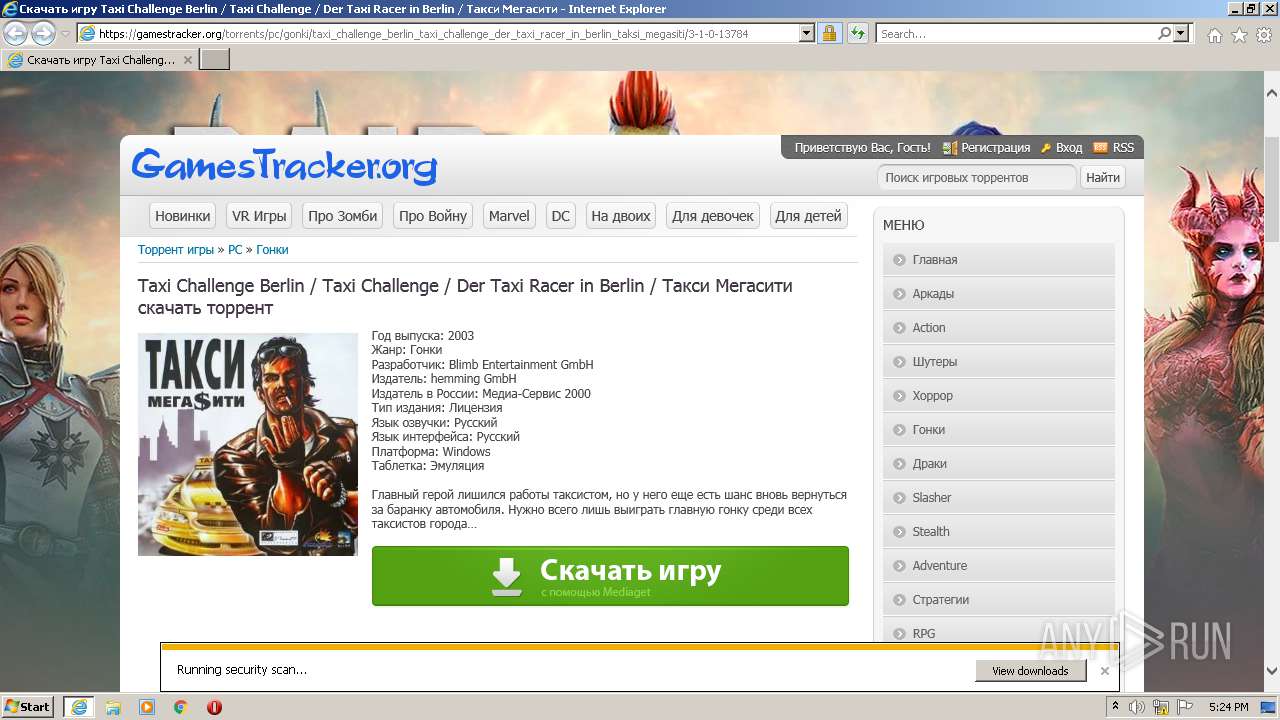
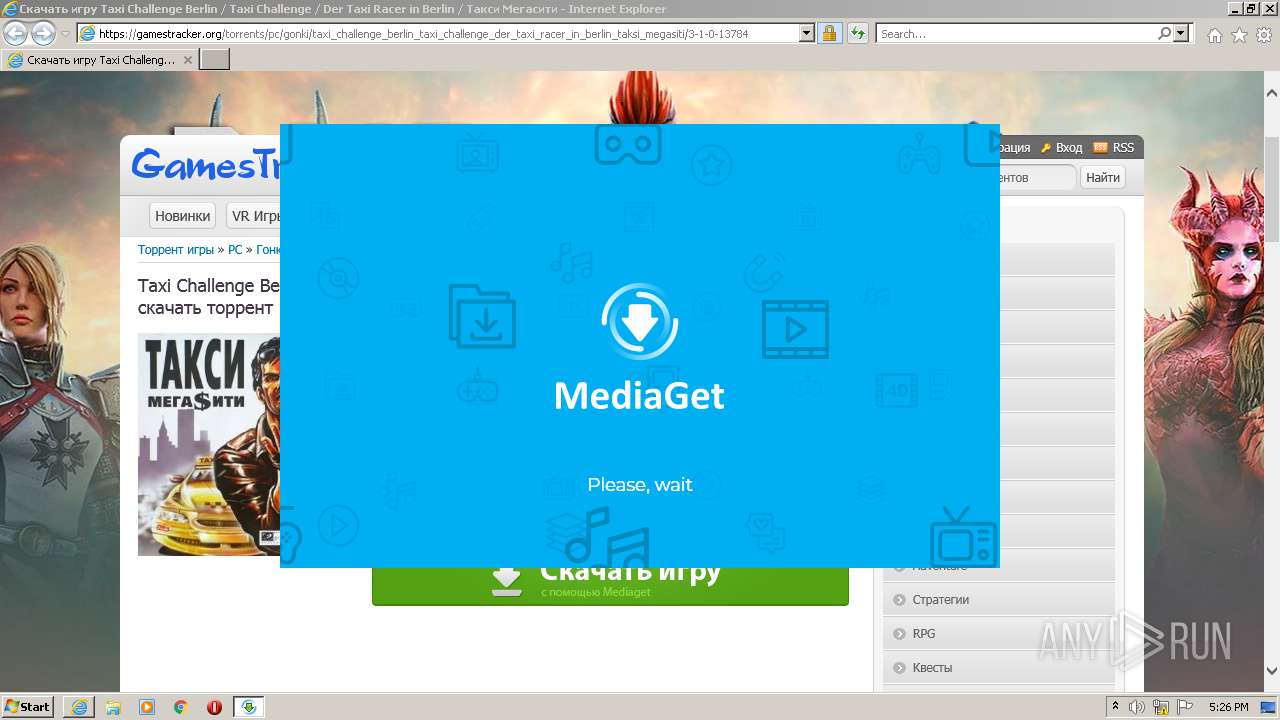
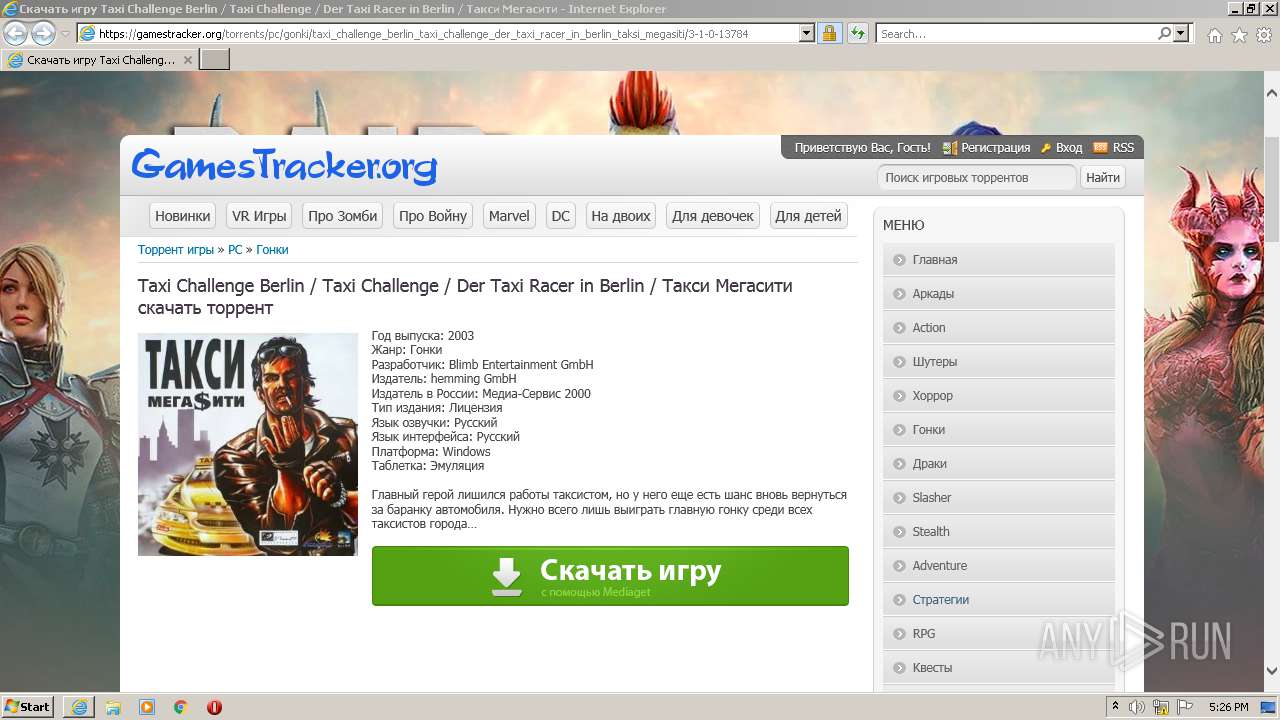
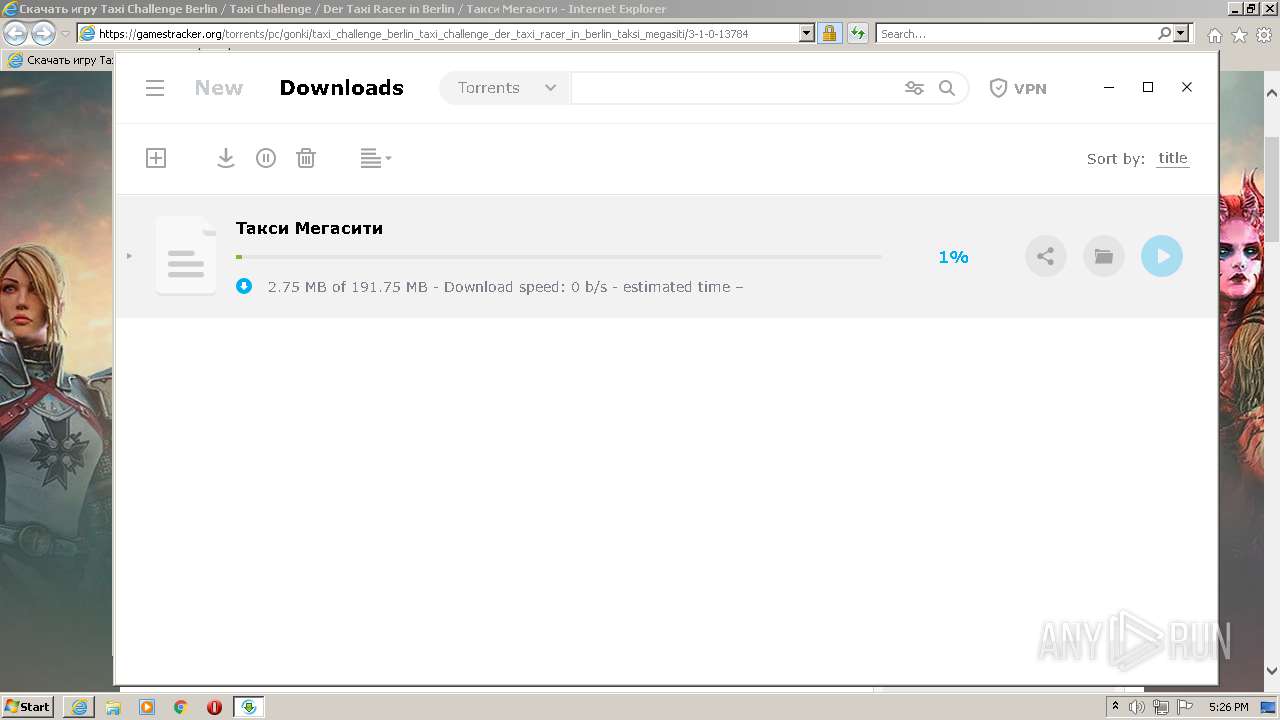
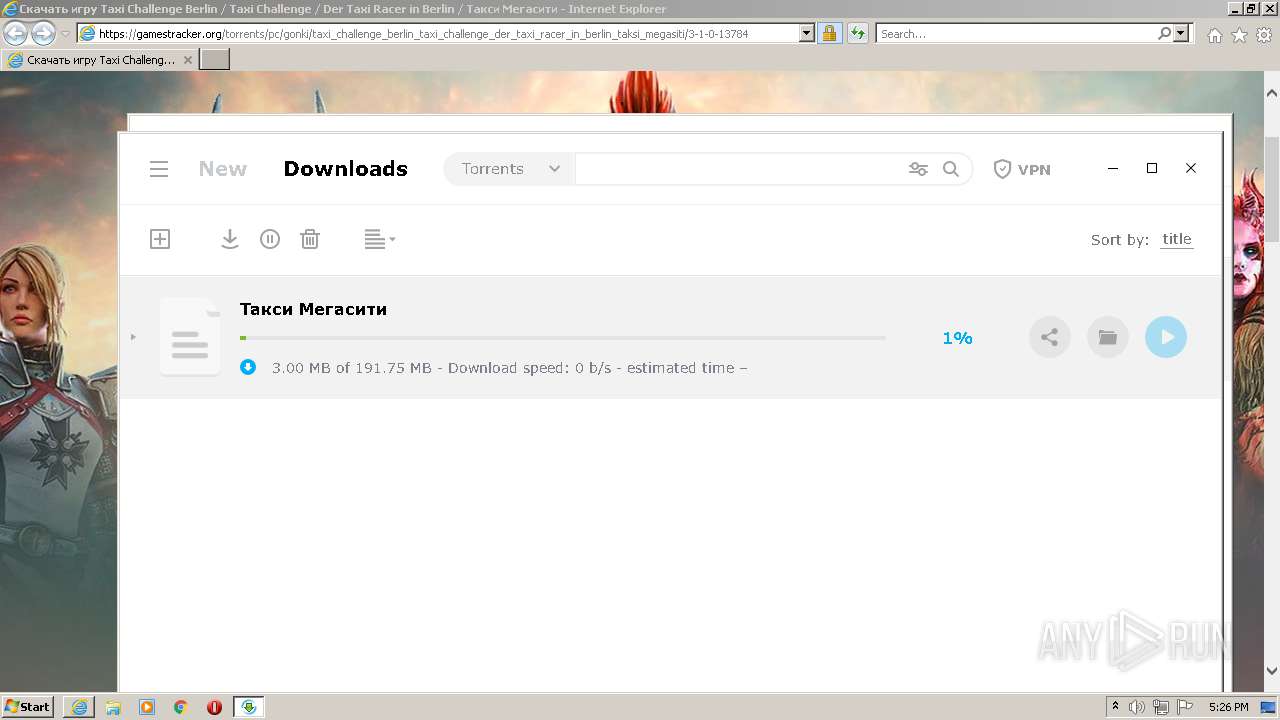
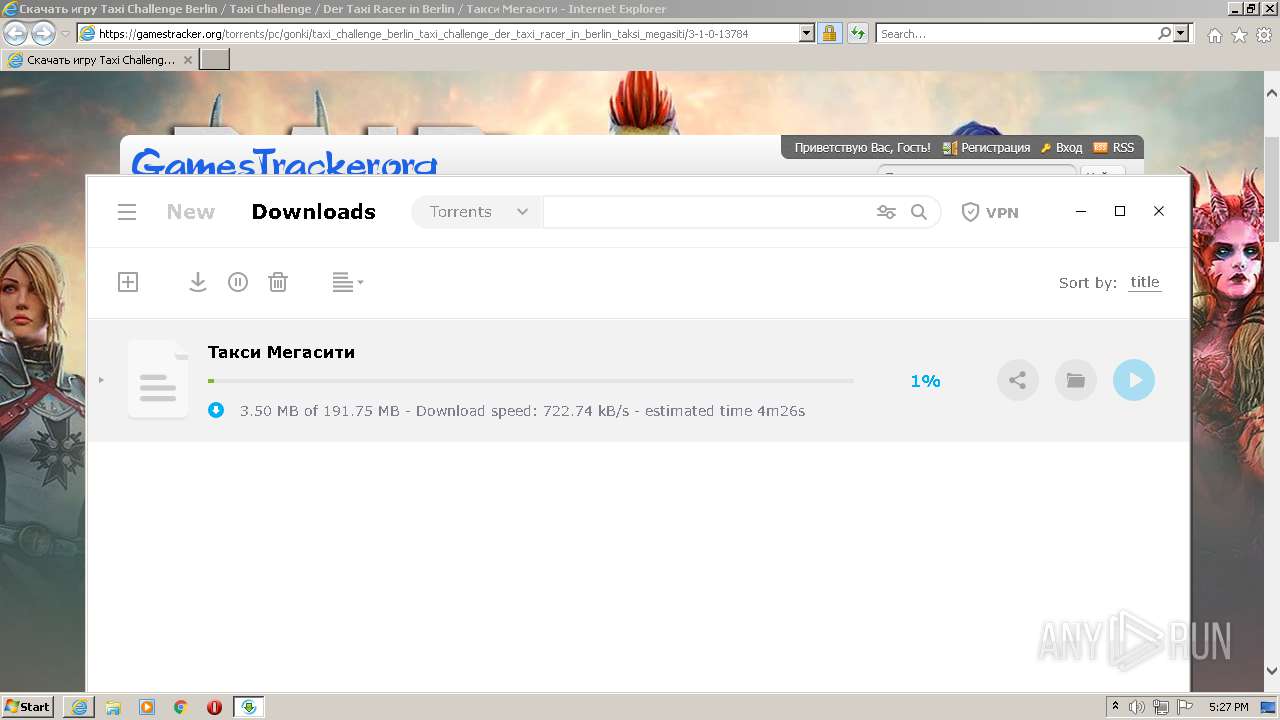
| URL: | https://gamestracker.org/torrents/pc/gonki/taxi_challenge_berlin_taxi_challenge_der_taxi_racer_in_berlin_taksi_megasiti/3-1-0-13784 |
| Full analysis: | https://app.any.run/tasks/67aeb53e-8eb8-4692-b8f2-ca3a3ab3c1da |
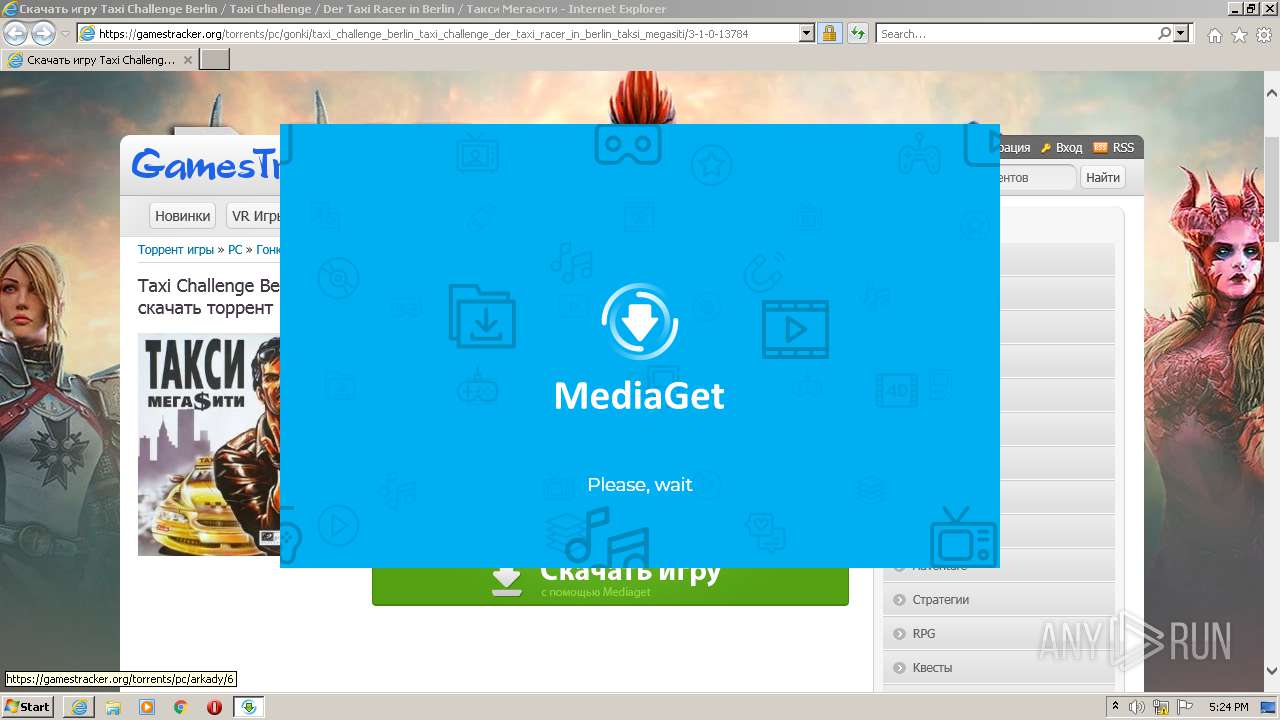
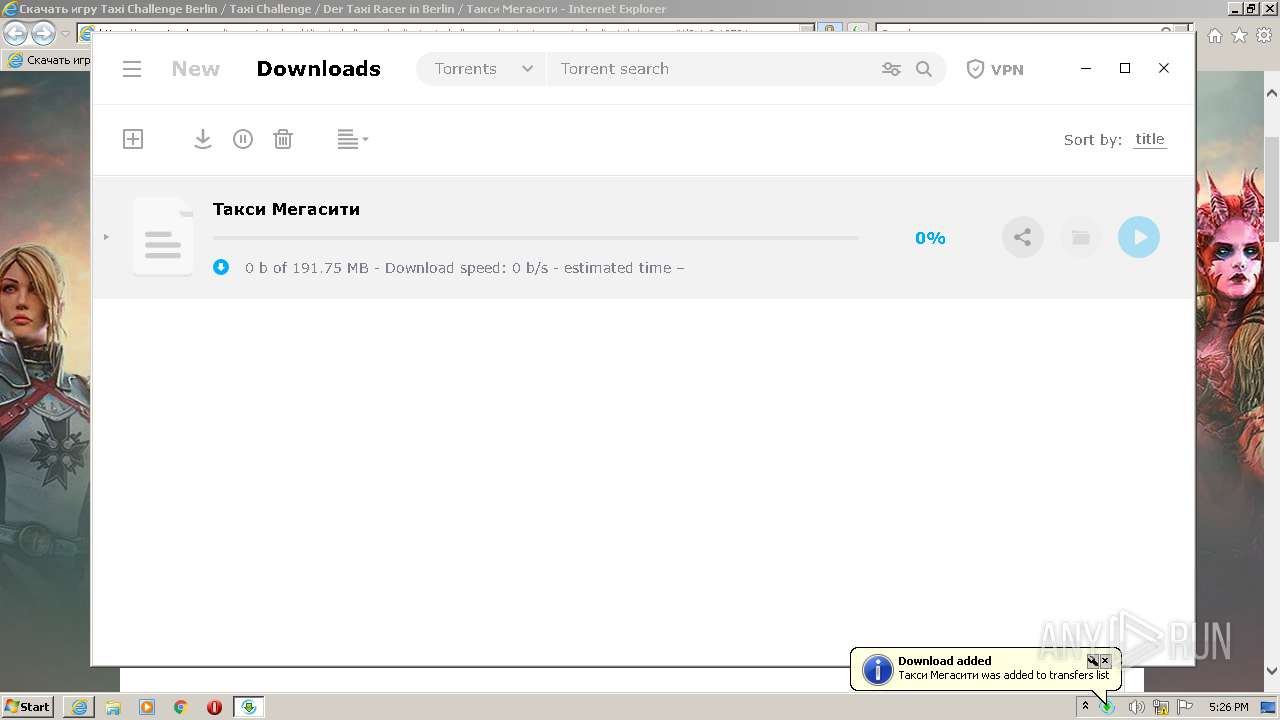
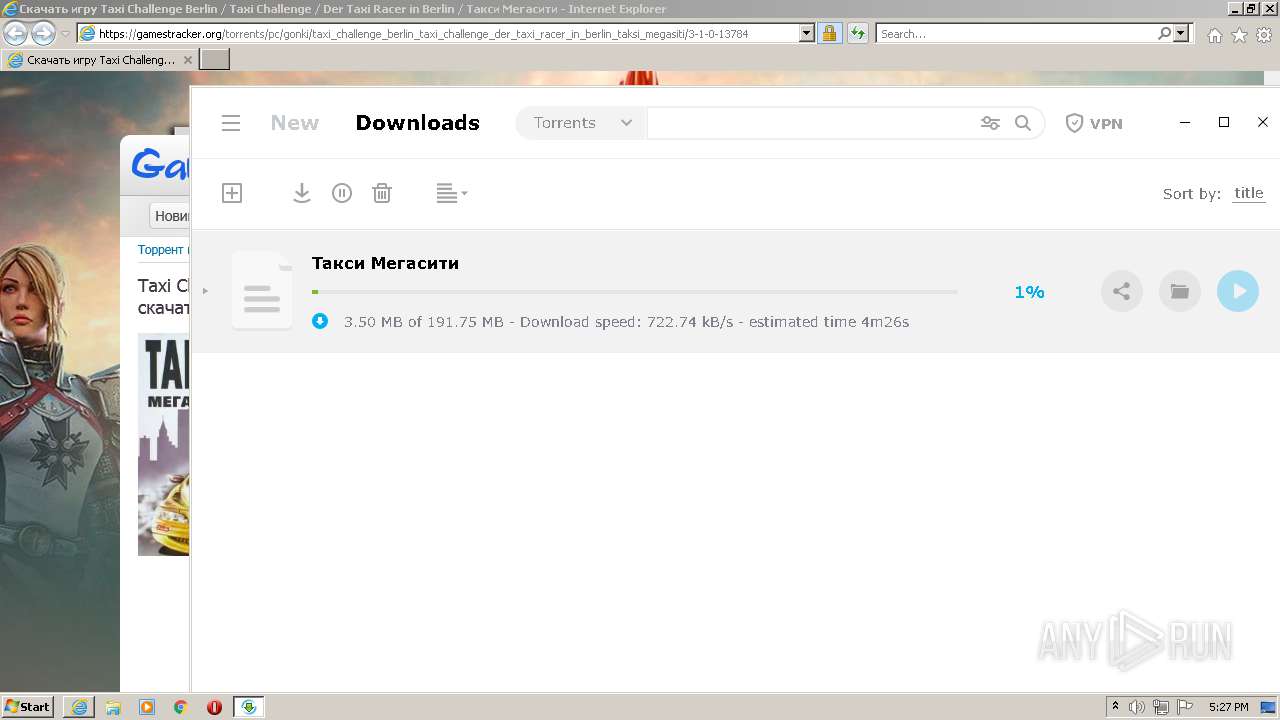
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2021, 16:23:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FDF1BE564F3772821E9D905CB61ADB8C |
| SHA1: | 4D086B4C7AE461008C7F2A48A17E01E3D7AA4929 |
| SHA256: | 0C6CC604C7784CE81ACBA69C8E5C8CEE8717D6B4B0A9BD8CE8E1DE5FBAEF8CAD |
| SSDEEP: | 3:N8lKE+SRMQlWKVGKCoK1tOO/KFCOO7qE9EHLsyIWO9tsQ:2V+SRHl9CB6O/KFdO2E9E1IBYQ |
MALICIOUS
Drops executable file immediately after starts
- msdt.exe (PID: 2256)
- soax.exe (PID: 2700)
- soax.tmp (PID: 312)
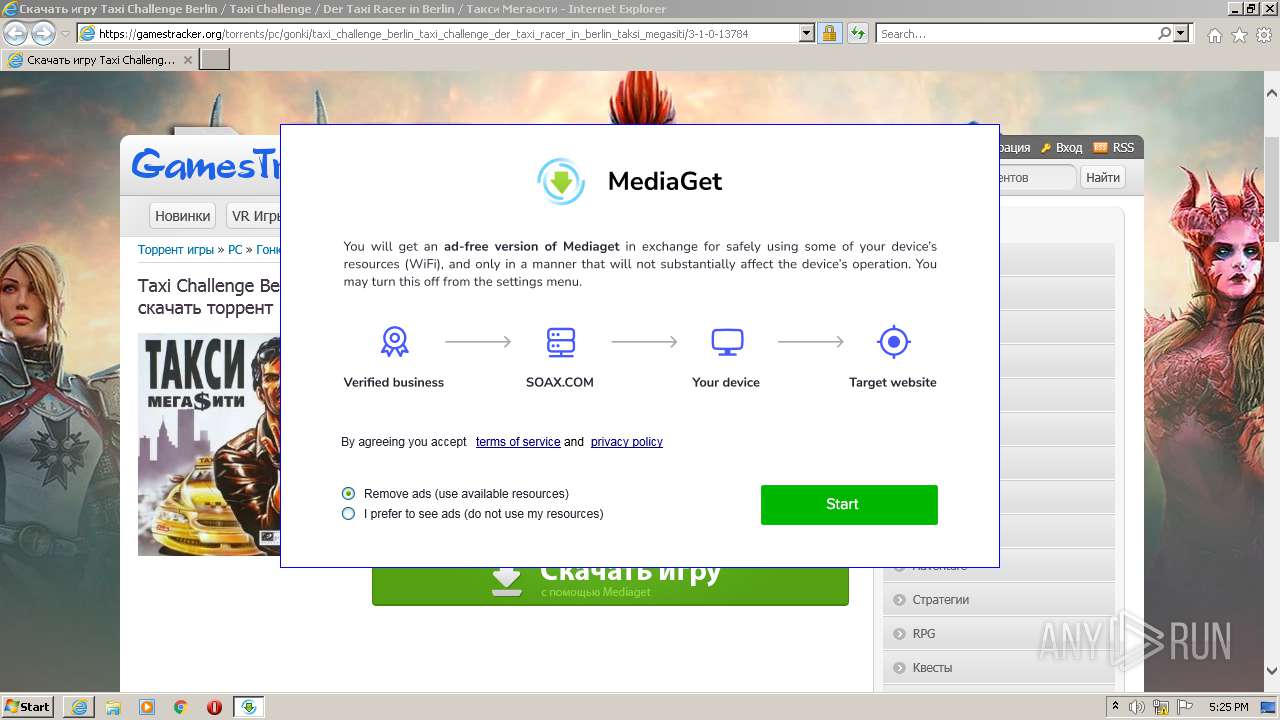
Actions looks like stealing of personal data
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
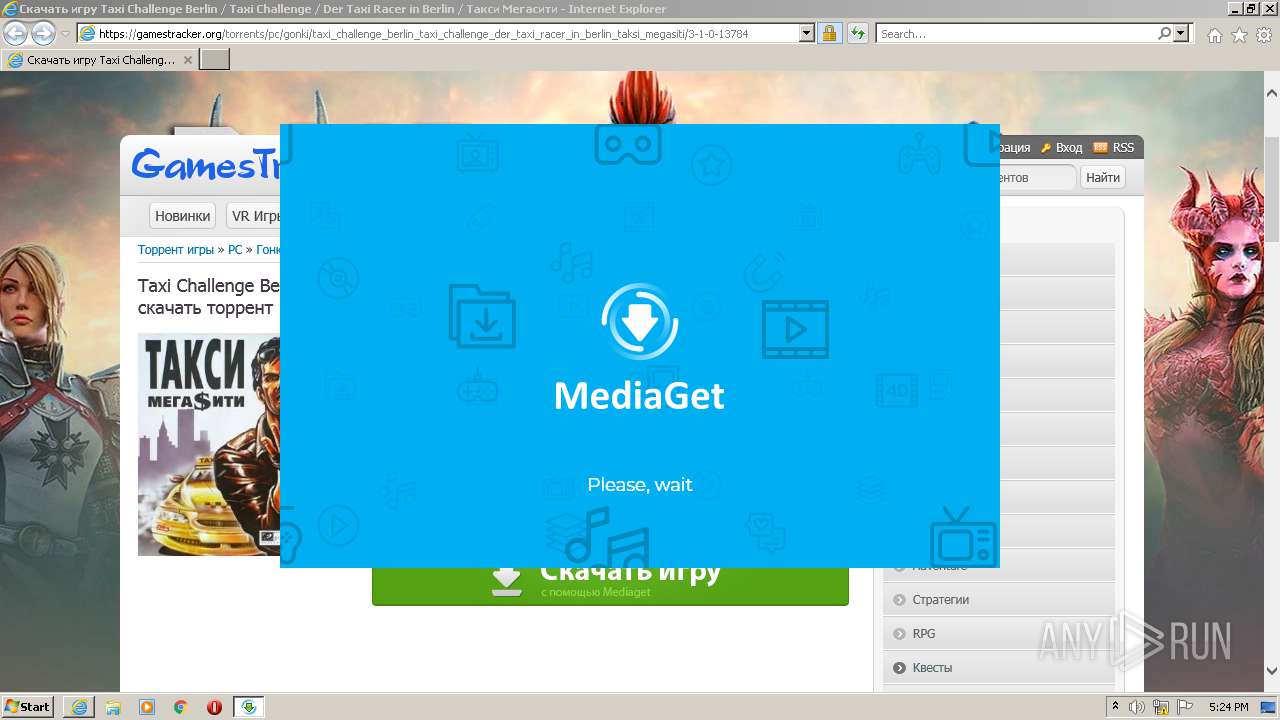
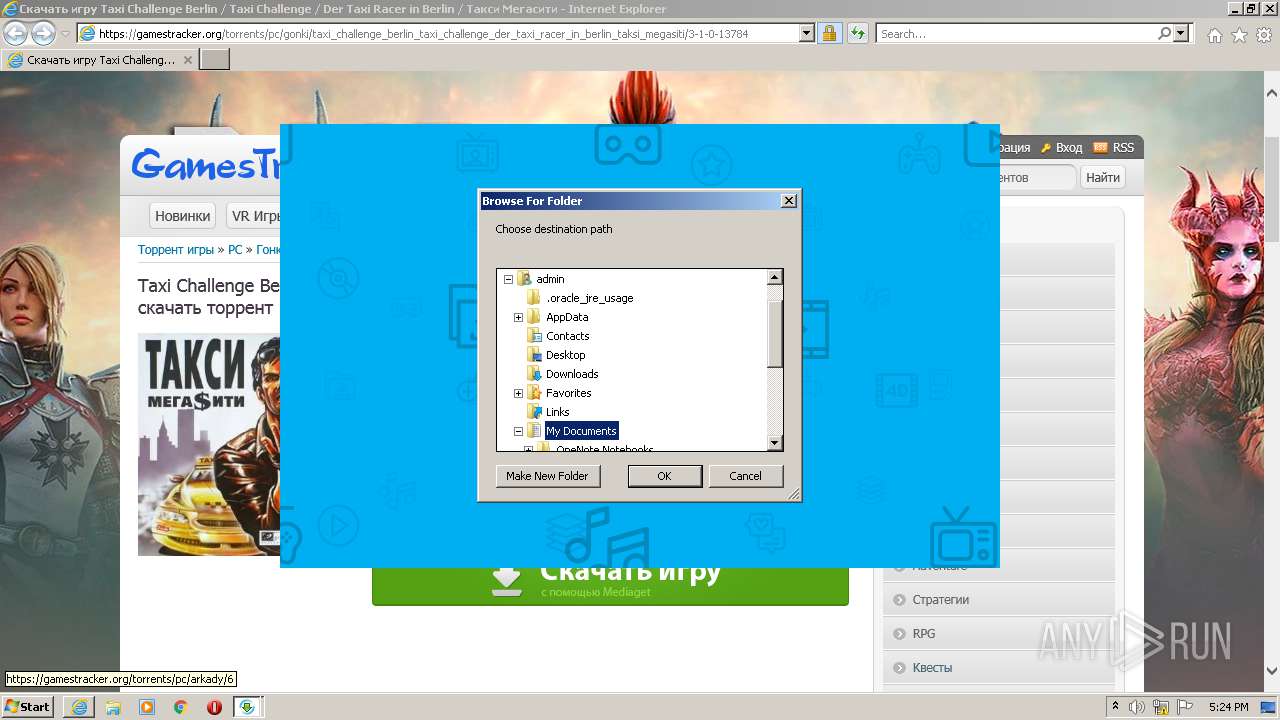
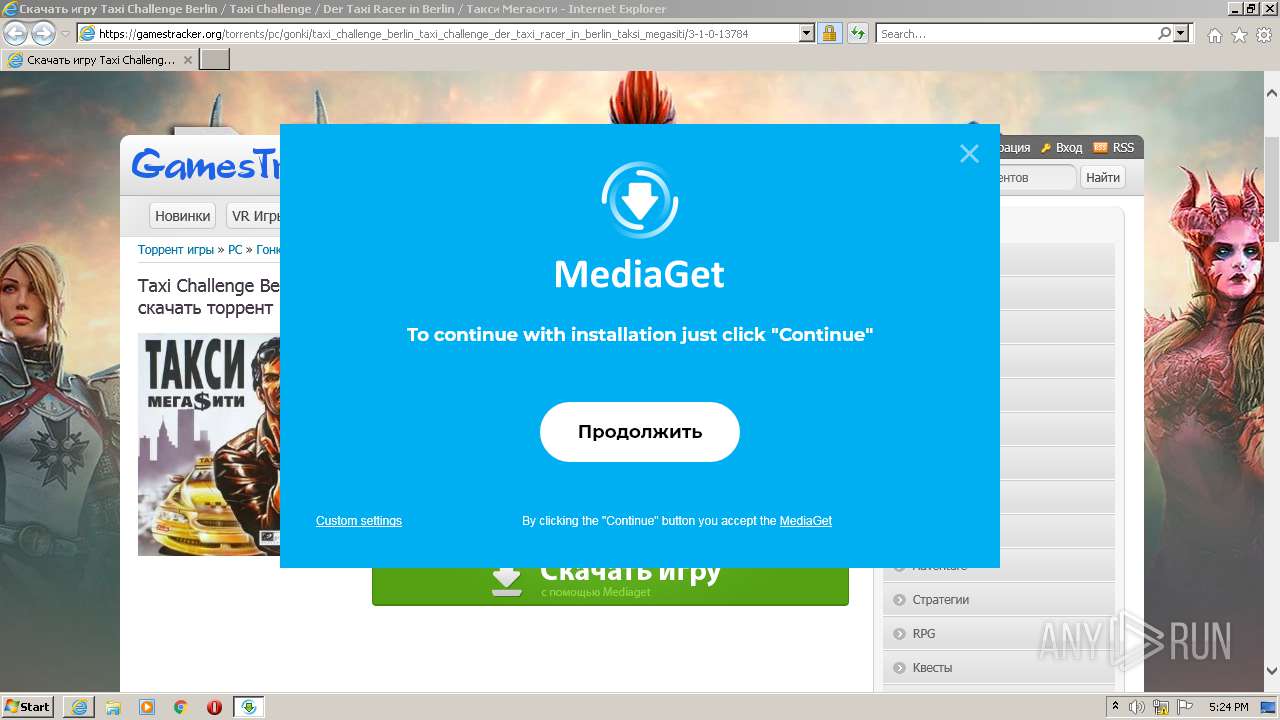
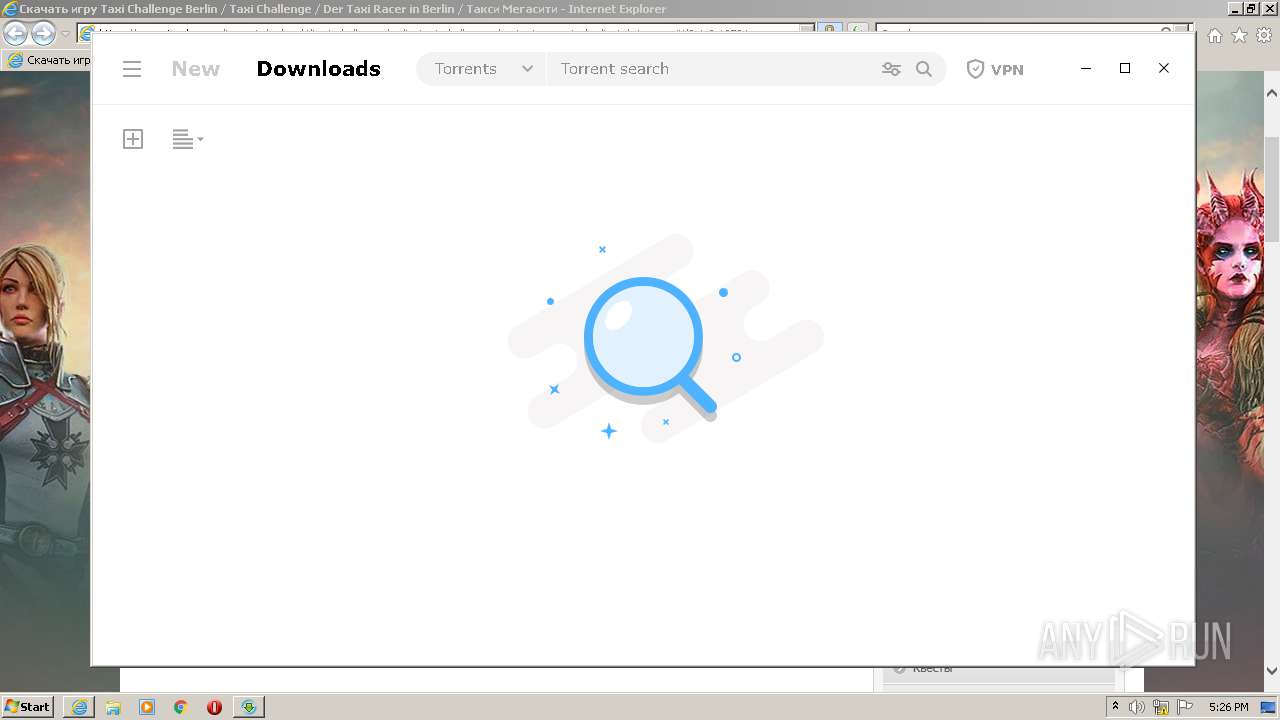
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 816)
- mediaget.exe (PID: 2744)
- mediaget_crashpad_handler.exe (PID: 3364)
- QtWebEngineProcess.exe (PID: 3160)
- QtWebEngineProcess.exe (PID: 3320)
- QtWebEngineProcess.exe (PID: 3144)
- soax-m.exe (PID: 576)
- QtWebEngineProcess.exe (PID: 3992)
Application was dropped or rewritten from another process
- MediaGet2.exe (PID: 3640)
- MediaGet2.exe (PID: 3940)
- mediaget.exe (PID: 2744)
- mediaget_crashpad_handler.exe (PID: 3364)
- QtWebEngineProcess.exe (PID: 3160)
- QtWebEngineProcess.exe (PID: 3144)
- QtWebEngineProcess.exe (PID: 3320)
- soax.exe (PID: 2700)
- soax-m.exe (PID: 576)
- QtWebEngineProcess.exe (PID: 3992)
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
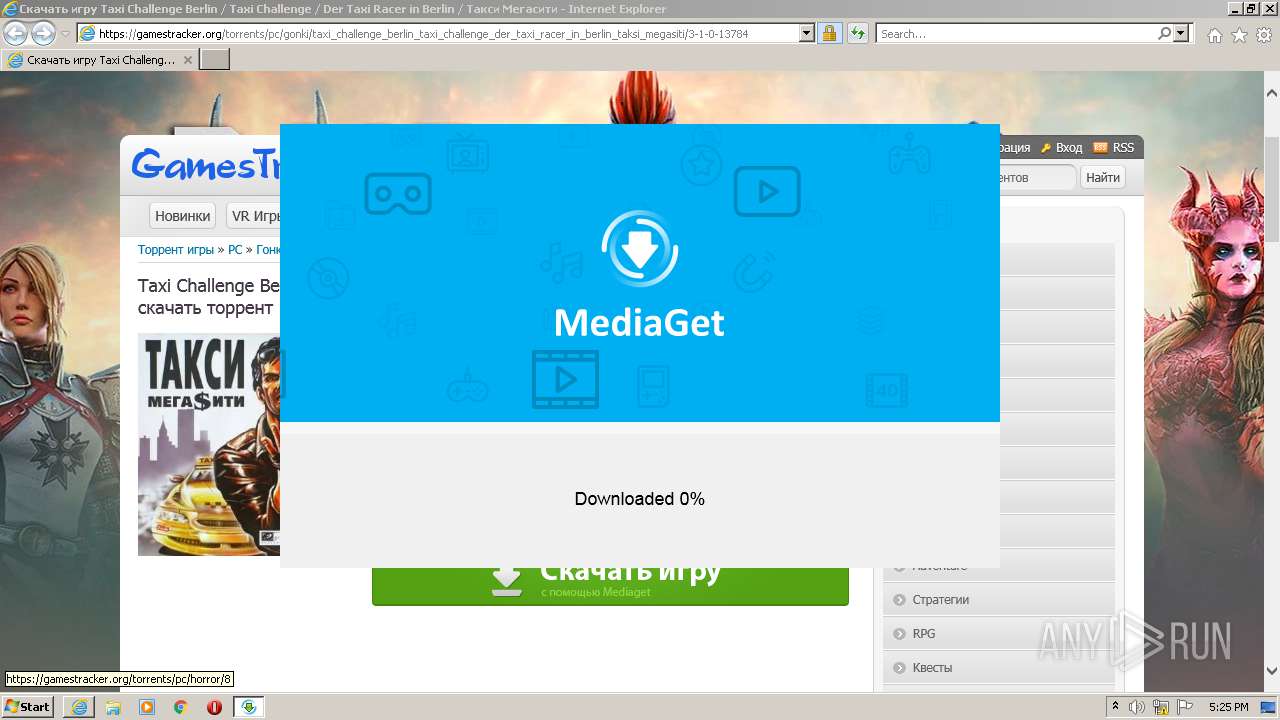
Changes the autorun value in the registry
- mediaget.exe (PID: 2744)
- soax.tmp (PID: 312)
SUSPICIOUS
Executable content was dropped or overwritten
- msdt.exe (PID: 2256)
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 1116)
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
- soax.exe (PID: 2700)
- soax.tmp (PID: 312)
- mediaget.exe (PID: 2744)
Drops a file with too old compile date
- msdt.exe (PID: 2256)
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3728)
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
Executed via COM
- sdiagnhost.exe (PID: 3496)
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 3496)
Drops a file with a compile date too recent
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 1116)
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
- soax.tmp (PID: 312)
Checks supported languages
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
- MediaGet2.exe (PID: 3940)
- mediaget.exe (PID: 2744)
- mediaget_crashpad_handler.exe (PID: 3364)
- QtWebEngineProcess.exe (PID: 3160)
- QtWebEngineProcess.exe (PID: 3320)
- QtWebEngineProcess.exe (PID: 3144)
- soax.exe (PID: 2700)
- soax.tmp (PID: 312)
- soax-m.exe (PID: 576)
- QtWebEngineProcess.exe (PID: 3992)
Drops a file that was compiled in debug mode
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
- soax.tmp (PID: 312)
- mediaget.exe (PID: 2744)
Reads internet explorer settings
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
Creates files in the user directory
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
Creates a software uninstall entry
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
Reads the computer name
- MediaGet2.exe (PID: 3940)
- mediaget.exe (PID: 2744)
- QtWebEngineProcess.exe (PID: 3160)
- soax.tmp (PID: 312)
- soax-m.exe (PID: 576)
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
Reads Environment values
- mediaget.exe (PID: 2744)
- soax-m.exe (PID: 576)
Changes default file association
- mediaget.exe (PID: 2744)
Reads Windows owner or organization settings
- soax.tmp (PID: 312)
Reads the Windows organization settings
- soax.tmp (PID: 312)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1116)
Checks supported languages
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 1116)
- msdt.exe (PID: 2256)
- sdiagnhost.exe (PID: 3496)
- ipconfig.exe (PID: 3912)
- ROUTE.EXE (PID: 2932)
- makecab.exe (PID: 2996)
- SearchProtocolHost.exe (PID: 816)
Reads the computer name
- iexplore.exe (PID: 1116)
- iexplore.exe (PID: 3728)
- msdt.exe (PID: 2256)
- sdiagnhost.exe (PID: 3496)
- ROUTE.EXE (PID: 2932)
- ipconfig.exe (PID: 3912)
- SearchProtocolHost.exe (PID: 816)
Reads settings of System Certificates
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 1116)
- msdt.exe (PID: 2256)
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
- mediaget.exe (PID: 2744)
- soax-m.exe (PID: 576)
- QtWebEngineProcess.exe (PID: 3160)
Application launched itself
- iexplore.exe (PID: 1116)
Reads internet explorer settings
- iexplore.exe (PID: 3728)
Checks Windows Trust Settings
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 1116)
- msdt.exe (PID: 2256)
- sdiagnhost.exe (PID: 3496)
Creates files in the user directory
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 1116)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1116)
Changes settings of System certificates
- iexplore.exe (PID: 1116)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1116)
Dropped object may contain Bitcoin addresses
- taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe (PID: 2832)
- iexplore.exe (PID: 1116)
- soax-m.exe (PID: 576)
Reads the hosts file
- mediaget.exe (PID: 2744)
- QtWebEngineProcess.exe (PID: 3160)
Application was dropped or rewritten from another process
- soax.tmp (PID: 312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
20
Malicious processes
9
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Users\admin\AppData\Local\Temp\is-DACTN.tmp\soax.tmp" /SL5="$A80260,2205570,121344,C:\Users\admin\AppData\Local\Temp\soax\soax.exe" /verysilent | C:\Users\admin\AppData\Local\Temp\is-DACTN.tmp\soax.tmp | soax.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 576 | "C:\Users\admin\AppData\Local\soax-m\soax-m.exe" | C:\Users\admin\AppData\Local\soax-m\soax-m.exe | soax.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 816 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://gamestracker.org/torrents/pc/gonki/taxi_challenge_berlin_taxi_challenge_der_taxi_racer_in_berlin_taksi_megasiti/3-1-0-13784" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2256 | -modal 131378 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDF846F.tmp -ep NetworkDiagnosticsWeb | C:\Windows\system32\msdt.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\AppData\Local\Temp\soax\soax.exe" /verysilent | C:\Users\admin\AppData\Local\Temp\soax\soax.exe | taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe | ||||||||||||
User: admin Company: soax Integrity Level: MEDIUM Description: soax Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2744 | "C:\Users\admin\MediaGet2\mediaget.exe" --installer | C:\Users\admin\MediaGet2\mediaget.exe | taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe | ||||||||||||
User: admin Company: MediaGet Integrity Level: MEDIUM Description: MediaGet torrent client Exit code: 0 Modules
| |||||||||||||||
| 2832 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\taxi-challenge-berlin-_-taxi-challenge-_-der-taxi_id728292ids1s.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0 Modules
| |||||||||||||||
| 2932 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\system32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2996 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\system32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft� Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
37 293
Read events
36 463
Write events
757
Delete events
73
Modification events
| (PID) Process: | (1116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 957324704 | |||
| (PID) Process: | (1116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30914876 | |||
| (PID) Process: | (1116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30914876 | |||
| (PID) Process: | (1116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
128
Suspicious files
81
Text files
488
Unknown types
67
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 1116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3F26ED5DE6B4E859CCCA6035ECB8D9CB | binary | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3F26ED5DE6B4E859CCCA6035ECB8D9CB | der | |
MD5:— | SHA256:— | |||
| 1116 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\NDF846F.tmp | binary | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 1116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
99
DNS requests
56
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3728 | iexplore.exe | GET | 200 | 67.27.157.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e3171d3491934918 | US | compressed | 59.7 Kb | whitelisted |
3728 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1116 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEHJqaUWUuUGuV9euEAx07js%3D | US | der | 312 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEQCTi7COYph7T3X5jLalBFyW | US | der | 728 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | US | der | 471 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEGXZ7A2inC5WpiqZeTr%2FCrM%3D | US | der | 471 b | whitelisted |
3728 | iexplore.exe | GET | 200 | 95.100.153.66:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEQDkBUeDDgxkUpdvejVJwN1I | unknown | der | 1.54 Kb | whitelisted |
3728 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CECosiqdXosrVzE6LrmbYt3c%3D | RU | der | 1.48 Kb | whitelisted |
3728 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1116 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3728 | iexplore.exe | 67.27.157.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1116 | iexplore.exe | 67.27.157.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3728 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1116 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
824 | svchost.exe | 193.109.247.75:443 | gamestracker.org | Filanco, ltd. | RU | suspicious |
1116 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1084 | svchost.exe | 67.27.157.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
— | — | 193.109.247.75:443 | gamestracker.org | Filanco, ltd. | RU | suspicious |
3728 | iexplore.exe | 193.109.246.75:443 | s75.ucoz.net | Filanco, ltd. | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gamestracker.org |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
s75.ucoz.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
824 | svchost.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
— | — | Potential Corporate Privacy Violation | ET P2P Vuze BT UDP Connection (5) |
Process | Message |
|---|---|
mediaget.exe | > __thiscall Application::Application(int &,char *[])
|
mediaget.exe | os version: "6.1.7601" __ os name: "Windows 7 Version 6.1 (Build 7601: SP 1)"
|
mediaget.exe | > int __thiscall Application::exec(void)
|
mediaget.exe | > __thiscall MediagetServerSettings::MediagetServerSettings(void)
|
mediaget.exe | INSTALL ID: "" _ OLD ID: ""
|
mediaget.exe | reseller - "" installId ""
|
mediaget.exe | > void __thiscall MediagetServerSettings::flushSettings(void)
|