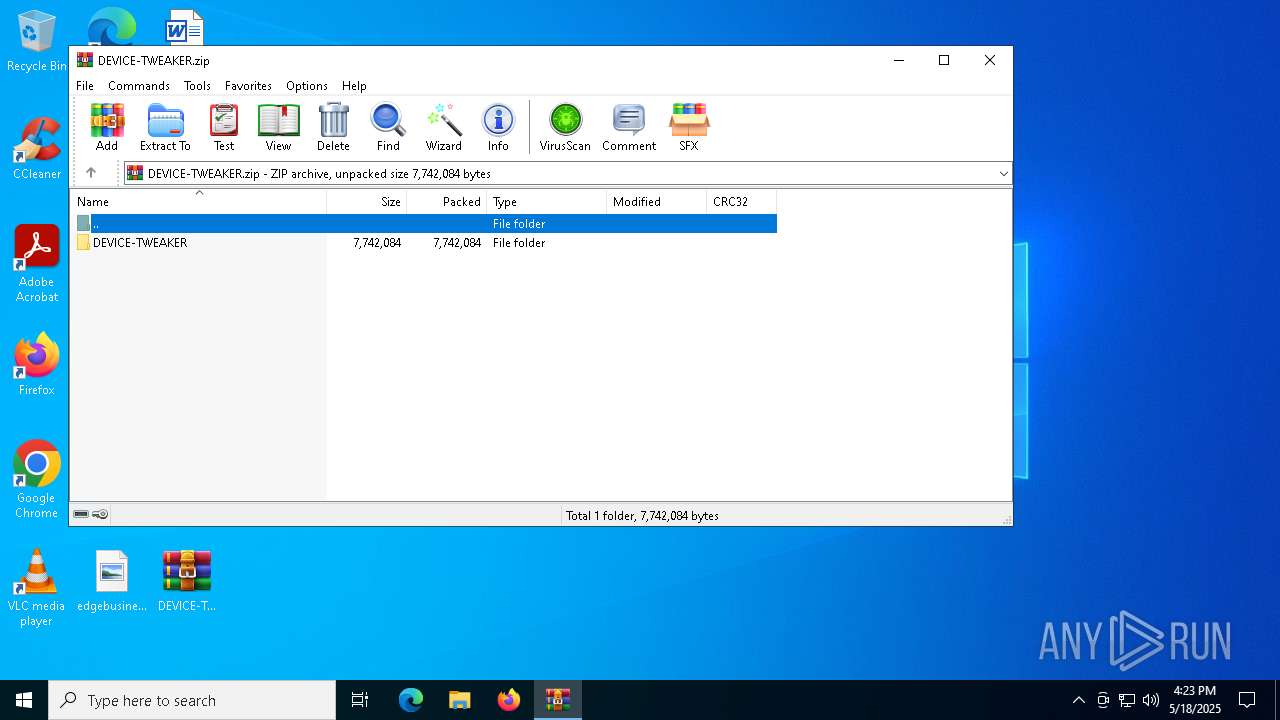
| File name: | DEVICE-TWEAKER.zip |
| Full analysis: | https://app.any.run/tasks/abef1197-f6c4-48f3-a6ec-975899ee0901 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 16:23:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | E614313872F99EDD049F0D8F297BBD80 |
| SHA1: | CC583DC1E8B5557DDB2537395CC76505F2572D93 |
| SHA256: | 0C571E491F21E5CABD5A8F18369275DB5159DEC2E34B9289C78A9ACC5BFD87F2 |
| SSDEEP: | 98304:zCDr9I6mZMz9hPJYkrcSPiiphGfjJ4Mo2qF5km+UnhWGrU7RuY9bljBWT6ogU0JT:G6GXnisQ9dOWlK/i |
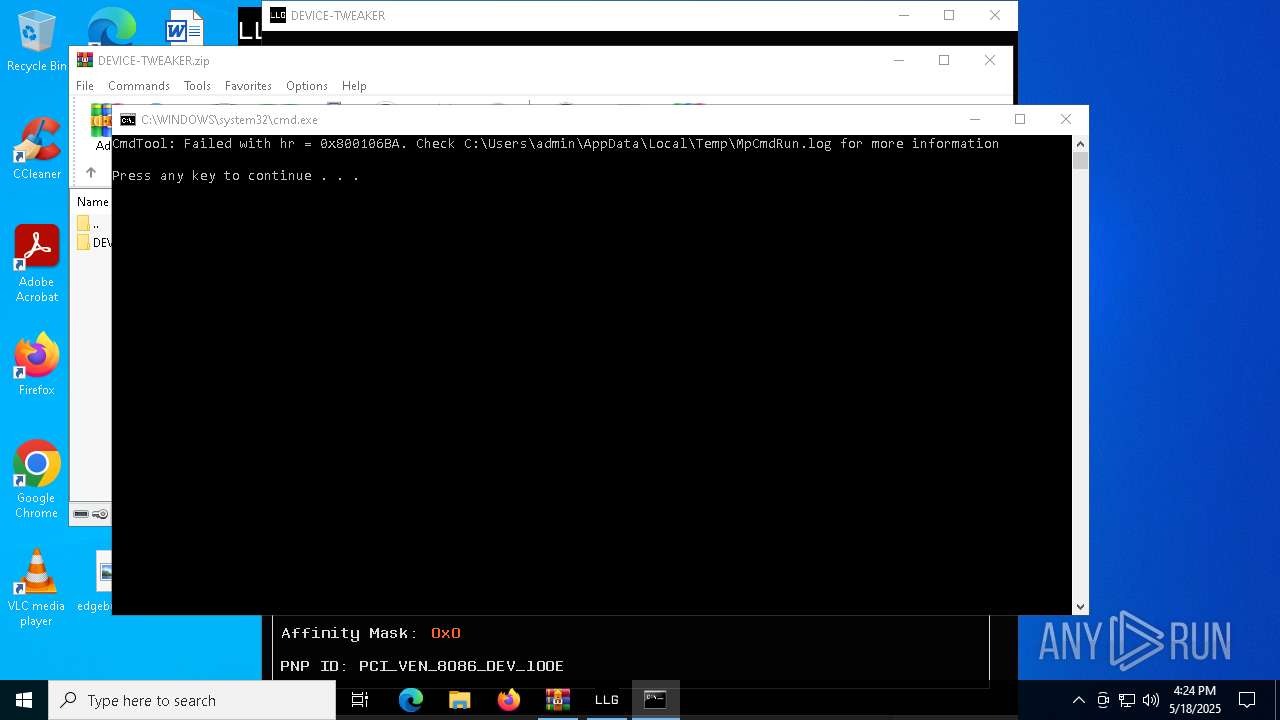
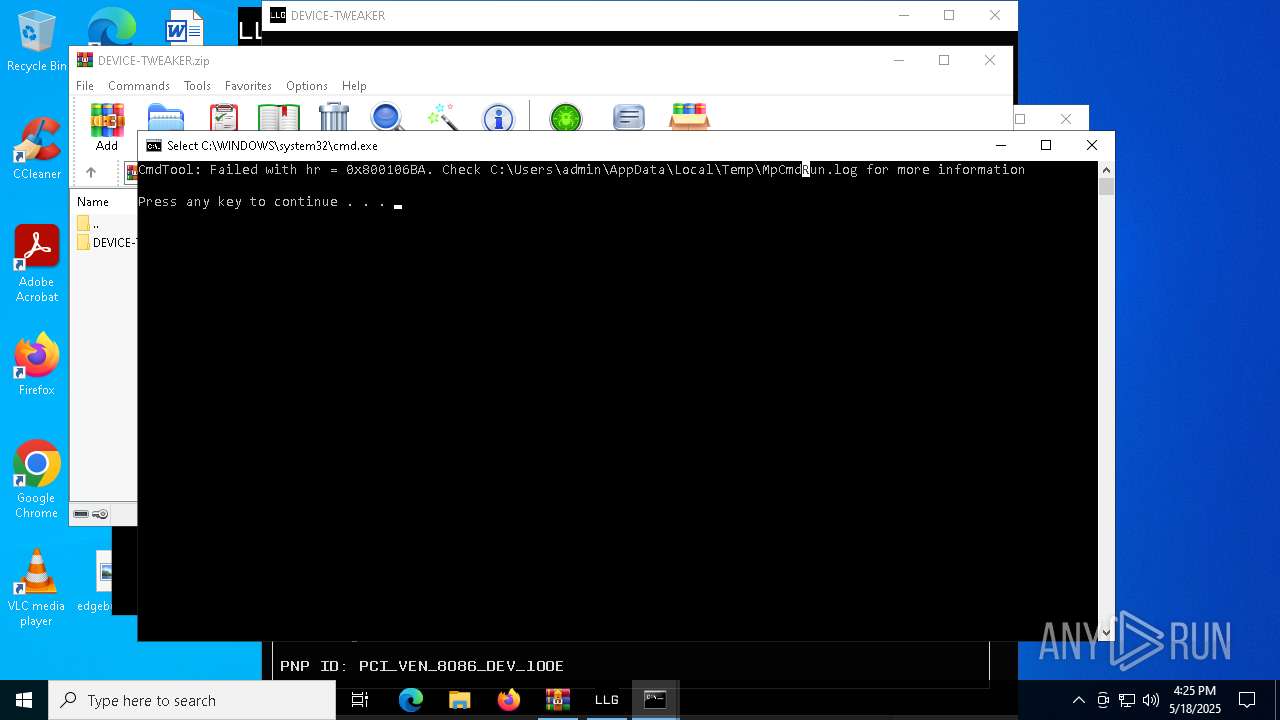
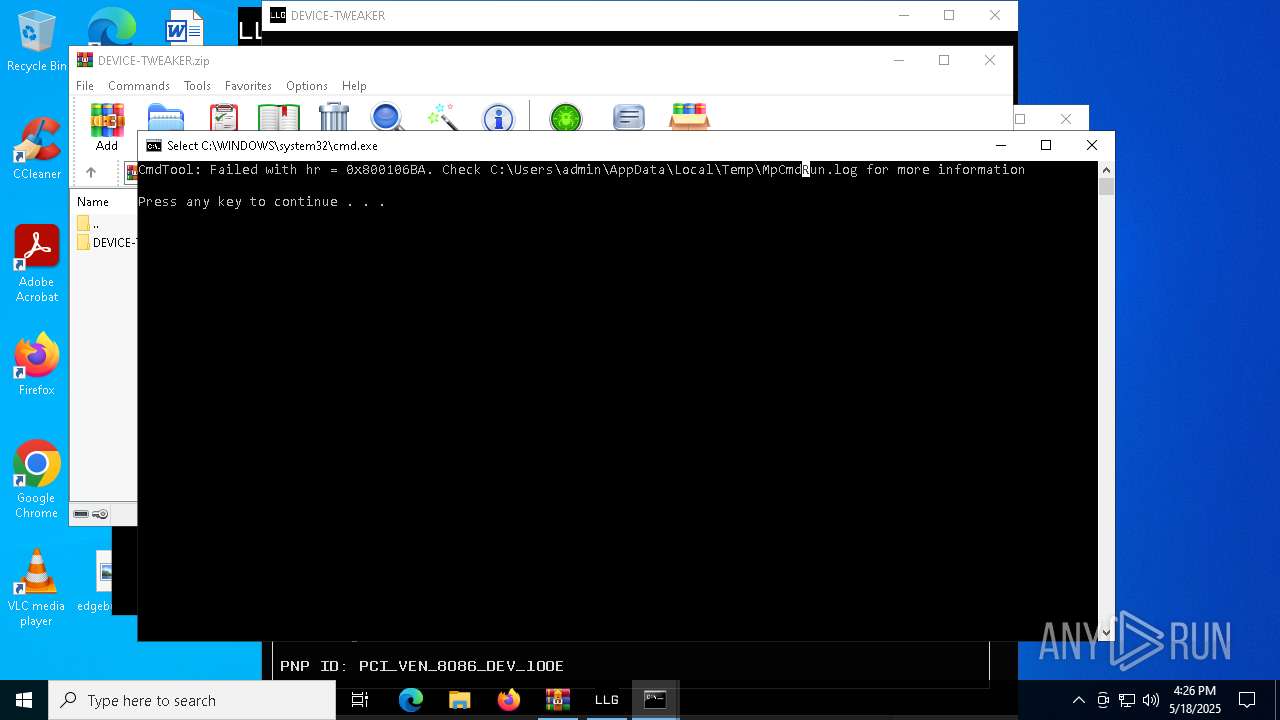
MALICIOUS
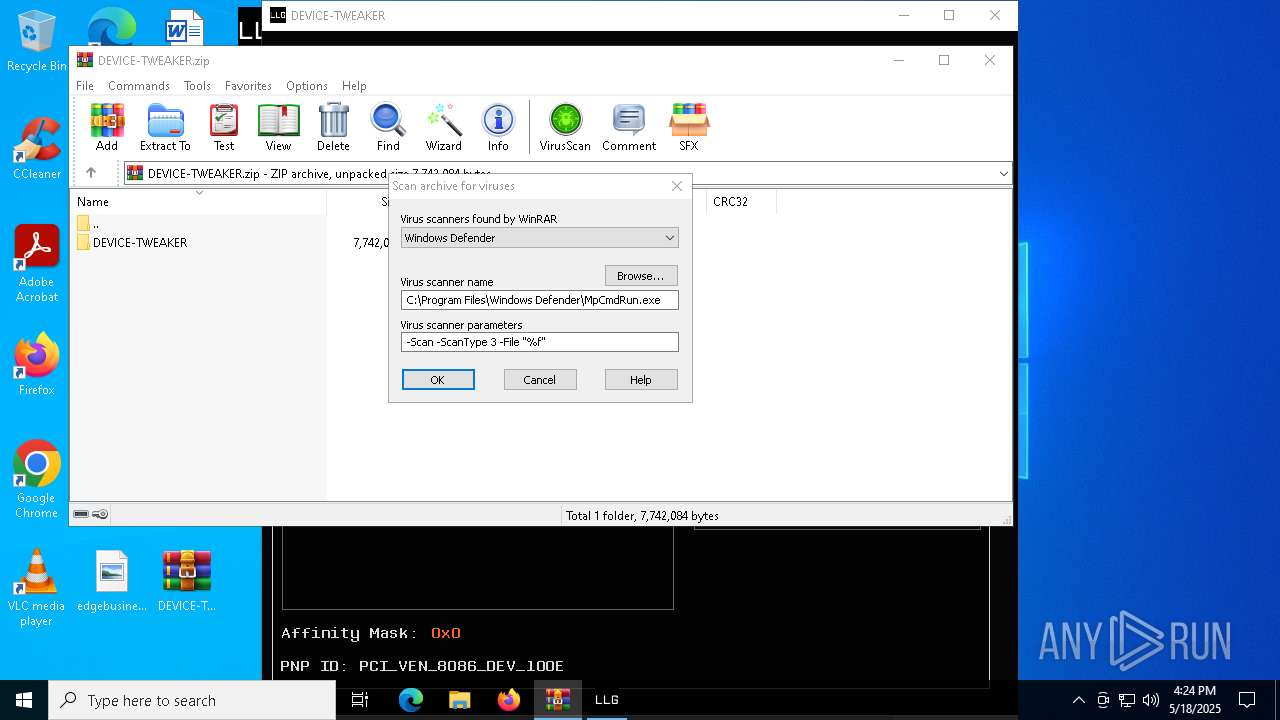
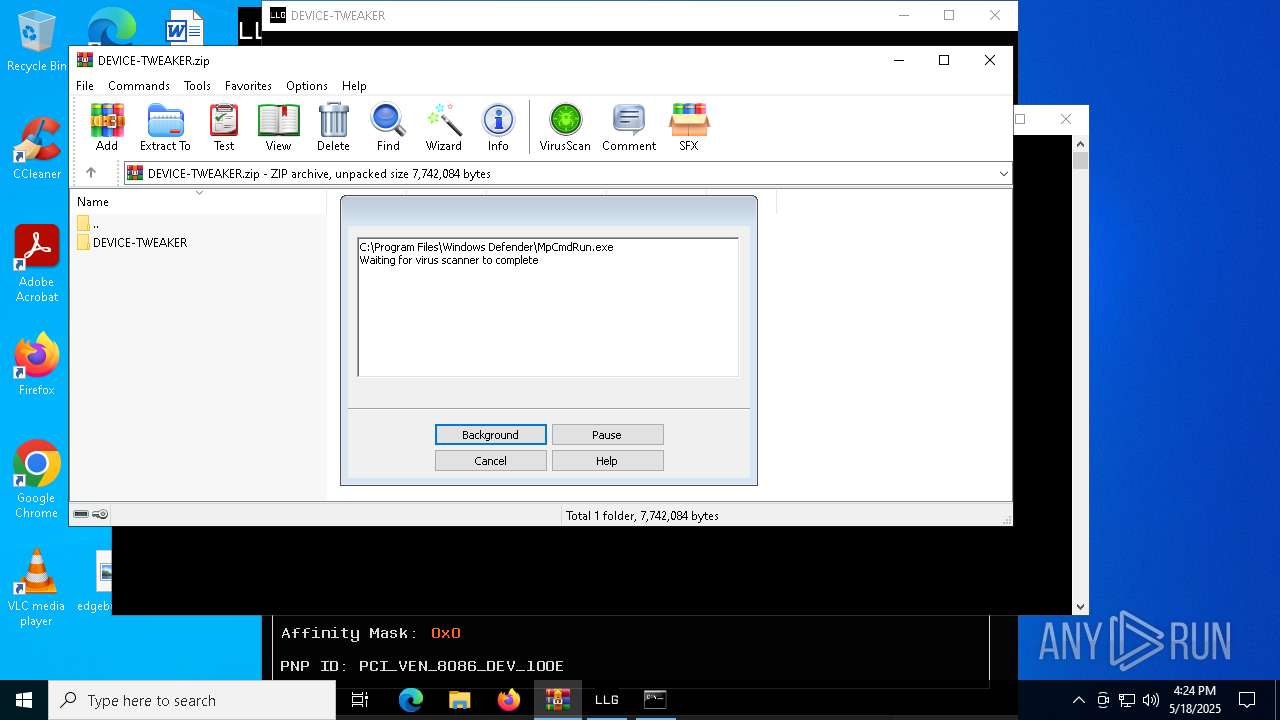
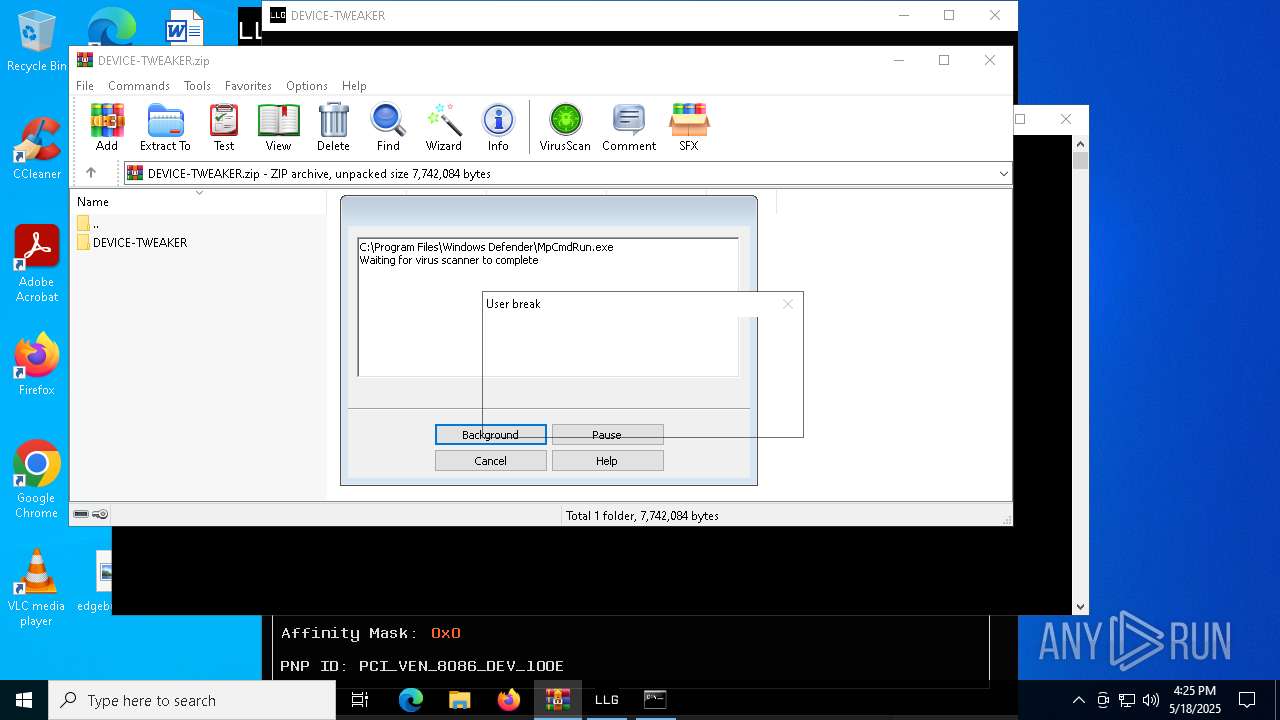
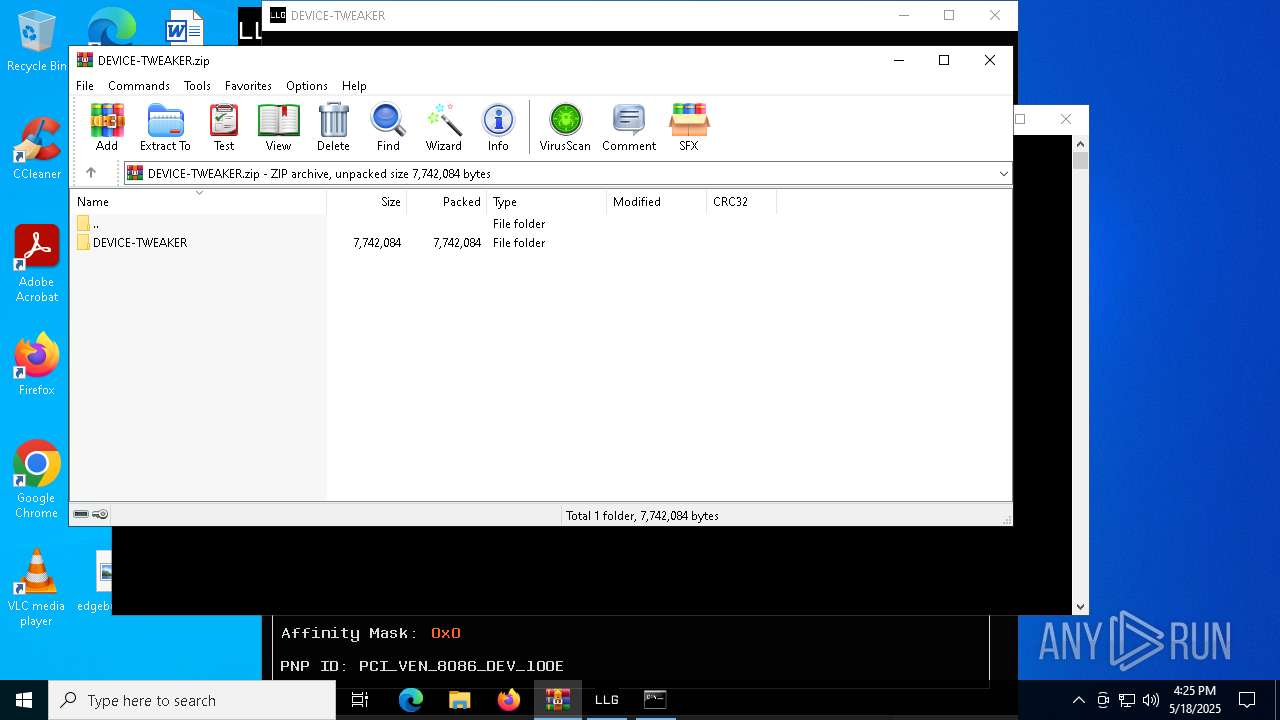
Generic archive extractor
- WinRAR.exe (PID: 7664)
SUSPICIOUS
Reads the BIOS version
- DEVICE-TWEAKER.exe (PID: 7876)
Gets information about processes (POWERSHELL)
- DEVICE-TWEAKER.exe (PID: 7876)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7664)
- DEVICE-TWEAKER.exe (PID: 7876)
Uses base64 encoding (POWERSHELL)
- DEVICE-TWEAKER.exe (PID: 7876)
Writes data into a file (POWERSHELL)
- DEVICE-TWEAKER.exe (PID: 7876)
Converts a specified value to an integer (POWERSHELL)
- DEVICE-TWEAKER.exe (PID: 7876)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 7664)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 7664)
INFO
Checks supported languages
- DEVICE-TWEAKER.exe (PID: 7876)
- MpCmdRun.exe (PID: 6516)
- MpCmdRun.exe (PID: 7572)
Manual execution by a user
- DEVICE-TWEAKER.exe (PID: 7876)
- DEVICE-TWEAKER.exe (PID: 7816)
- OpenWith.exe (PID: 7924)
- OpenWith.exe (PID: 7932)
Process checks whether UAC notifications are on
- DEVICE-TWEAKER.exe (PID: 7876)
Checks whether the specified file exists (POWERSHELL)
- DEVICE-TWEAKER.exe (PID: 7876)
Themida protector has been detected
- DEVICE-TWEAKER.exe (PID: 7876)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7664)
Reads the computer name
- DEVICE-TWEAKER.exe (PID: 7876)
- MpCmdRun.exe (PID: 6516)
- MpCmdRun.exe (PID: 7572)
Reads the machine GUID from the registry
- DEVICE-TWEAKER.exe (PID: 7876)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 7932)
- OpenWith.exe (PID: 7924)
Create files in a temporary directory
- DEVICE-TWEAKER.exe (PID: 7876)
- MpCmdRun.exe (PID: 6516)
Reads Environment values
- DEVICE-TWEAKER.exe (PID: 7876)
Reads the software policy settings
- DEVICE-TWEAKER.exe (PID: 7876)
- slui.exe (PID: 7212)
Checks if a key exists in the options dictionary (POWERSHELL)
- DEVICE-TWEAKER.exe (PID: 7876)
Checks proxy server information
- slui.exe (PID: 7212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | None |
| ZipModifyDate: | 2025:05:15 17:08:42 |
| ZipCRC: | 0x617d5801 |
| ZipCompressedSize: | 66 |
| ZipUncompressedSize: | 66 |
| ZipFileName: | DEVICE-TWEAKER/system_priorities.cfg |
Total processes
139
Monitored processes
12
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
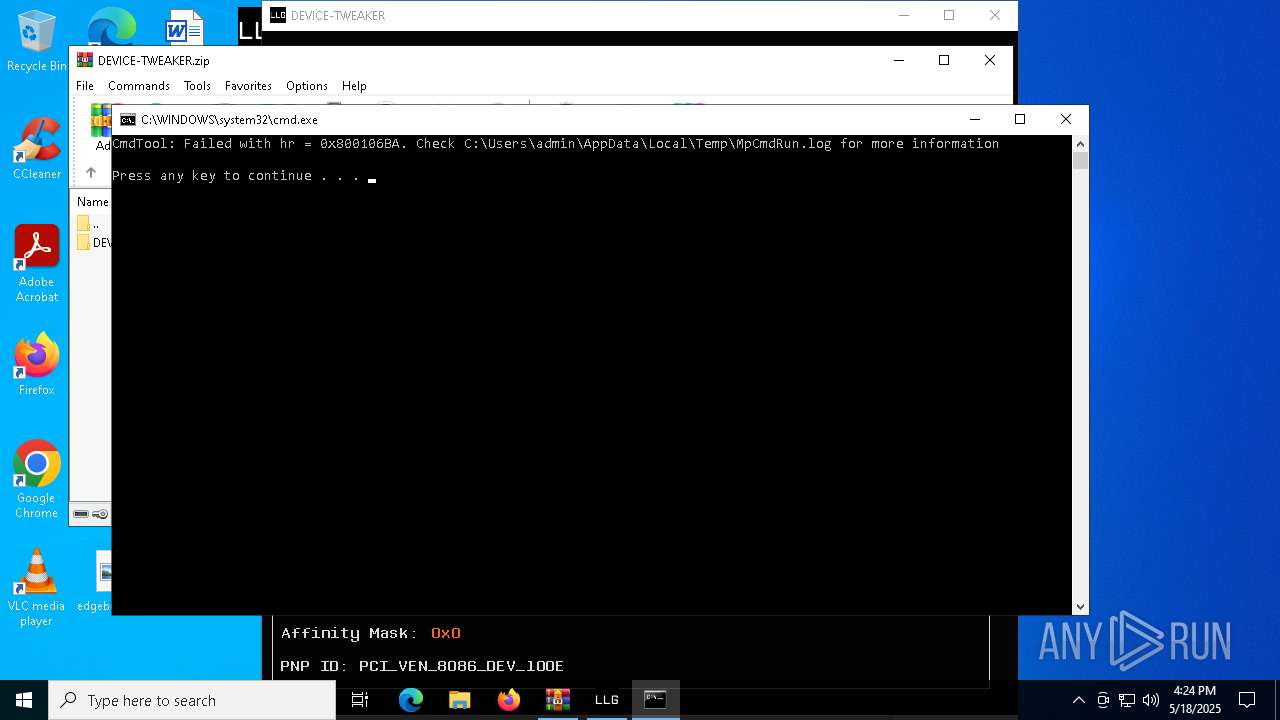
| 4380 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR7664.35052\Rar$Scan113290.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5528 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR7664.26735\Rar$Scan30179.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6032 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
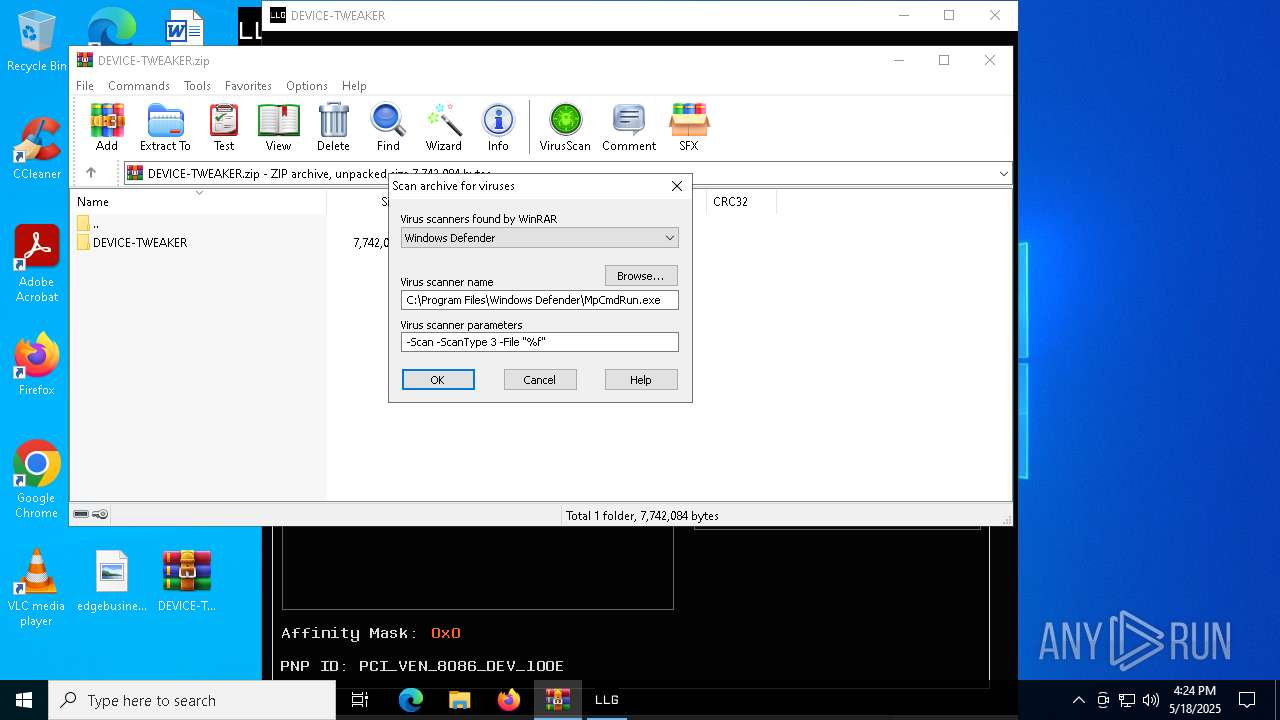
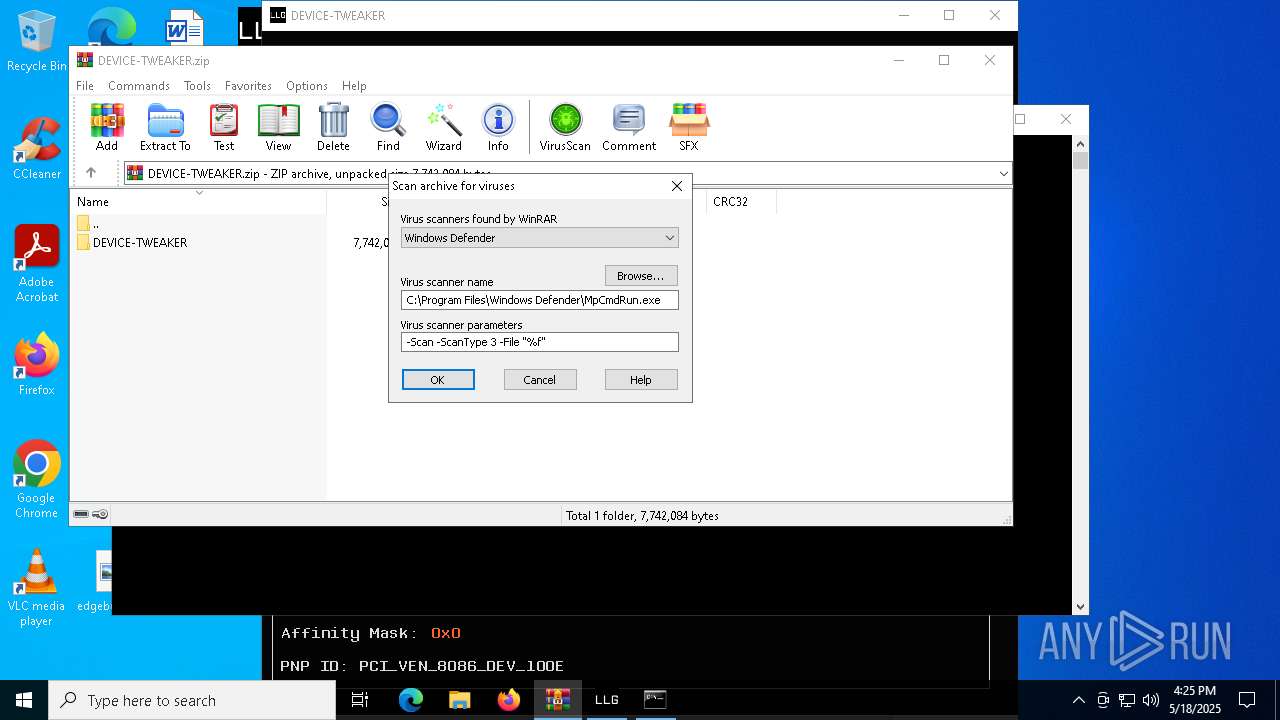
| 6516 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR7664.26735" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7212 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7572 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR7664.35052" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7664 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\DEVICE-TWEAKER.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
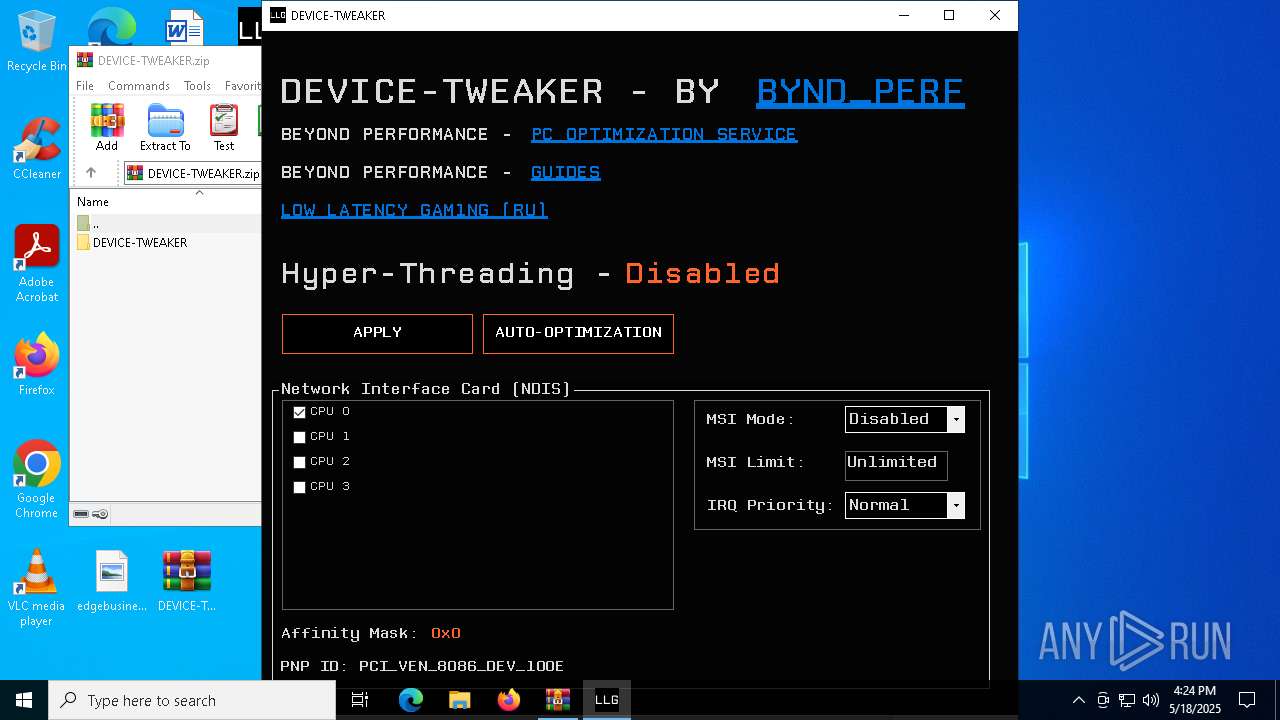
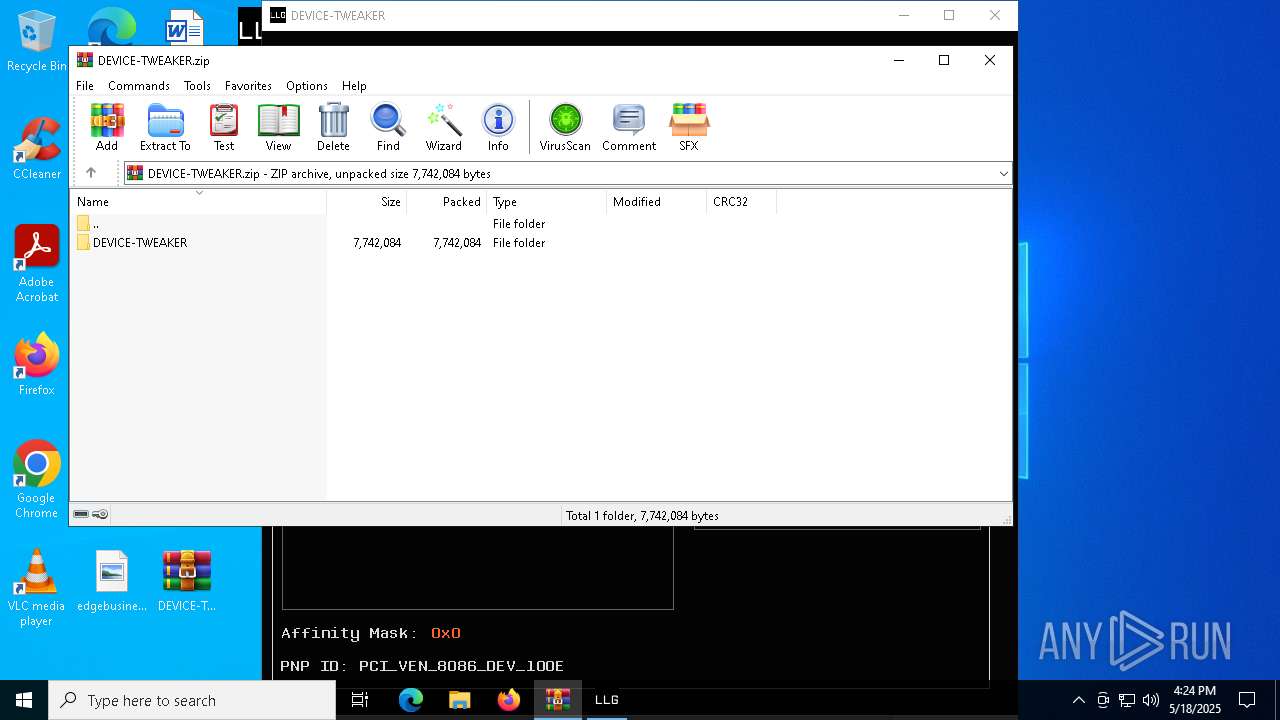
| 7816 | "C:\Users\admin\Desktop\DEVICE-TWEAKER.exe" | C:\Users\admin\Desktop\DEVICE-TWEAKER.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: BYND_PERF Exit code: 3221226540 Version: 1.4.8.8 Modules
| |||||||||||||||
| 7876 | "C:\Users\admin\Desktop\DEVICE-TWEAKER.exe" | C:\Users\admin\Desktop\DEVICE-TWEAKER.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: BYND_PERF Version: 1.4.8.8 Modules
| |||||||||||||||
Total events
16 126
Read events
16 115
Write events
11
Delete events
0
Modification events
| (PID) Process: | (7664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\DEVICE-TWEAKER.zip | |||
| (PID) Process: | (7664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
| (PID) Process: | (7664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
2
Suspicious files
3
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7664.26735\DEVICE-TWEAKER.zip\DEVICE-TWEAKER\system_priorities.cfg | text | |
MD5:6516274159E3BD60992C5B41C858E99E | SHA256:D6C3191F3C8A5E8E9566EF89FDD7DF7AA455D7F4897F2E40228F5B20D9BD23BA | |||
| 7664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7664.26735\DEVICE-TWEAKER.zip\DEVICE-TWEAKER\DEVICE-TWEAKER.exe | executable | |
MD5:5E915A7BAE95BEDB3A5C7C5AA1865C0B | SHA256:E652B9B466D84ADBDA644A87AEB36E087D2A1569B35D58DDDAE46C332A3FFF91 | |||
| 7664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7664.26735\DEVICE-TWEAKER.zip\DEVICE-TWEAKER\games_priorities.cfg | text | |
MD5:6516274159E3BD60992C5B41C858E99E | SHA256:D6C3191F3C8A5E8E9566EF89FDD7DF7AA455D7F4897F2E40228F5B20D9BD23BA | |||
| 6516 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | binary | |
MD5:828059FD31FFF8585FF7FF9185E99BF7 | SHA256:A0742649C3338922EAEA379AB54577C036E51A53A524F973E5A9B06BC3DC7D83 | |||
| 7664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7664.35052\DEVICE-TWEAKER.zip\DEVICE-TWEAKER\games_priorities.cfg | text | |
MD5:6516274159E3BD60992C5B41C858E99E | SHA256:D6C3191F3C8A5E8E9566EF89FDD7DF7AA455D7F4897F2E40228F5B20D9BD23BA | |||
| 7664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7664.35052\DEVICE-TWEAKER.zip\DEVICE-TWEAKER\system_priorities.cfg | text | |
MD5:6516274159E3BD60992C5B41C858E99E | SHA256:D6C3191F3C8A5E8E9566EF89FDD7DF7AA455D7F4897F2E40228F5B20D9BD23BA | |||
| 7664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7664.35052\Rar$Scan113290.bat | text | |
MD5:77B8C2CA321922B685F2D1279CE3D6F0 | SHA256:96D69D4895CE583215FA5191451DED6342F4943051B2A56DE4A1260C40A0B14B | |||
| 7876 | DEVICE-TWEAKER.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:2AF279E73EBE24F3A6E689A595D21DA6 | SHA256:744A9C29CC187A660EF373FE35642BAC63B4CF8A94D301D90307F3FB0775D35F | |||
| 7876 | DEVICE-TWEAKER.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1qdq2ydl.ghh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7664.35052\DEVICE-TWEAKER.zip\DEVICE-TWEAKER\DEVICE-TWEAKER.exe | executable | |
MD5:5E915A7BAE95BEDB3A5C7C5AA1865C0B | SHA256:E652B9B466D84ADBDA644A87AEB36E087D2A1569B35D58DDDAE46C332A3FFF91 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
50
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5216 | RUXIMICS.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5216 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6184 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
6184 | SIHClient.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
6184 | SIHClient.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
6184 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
6184 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
6184 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5216 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5216 | RUXIMICS.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |