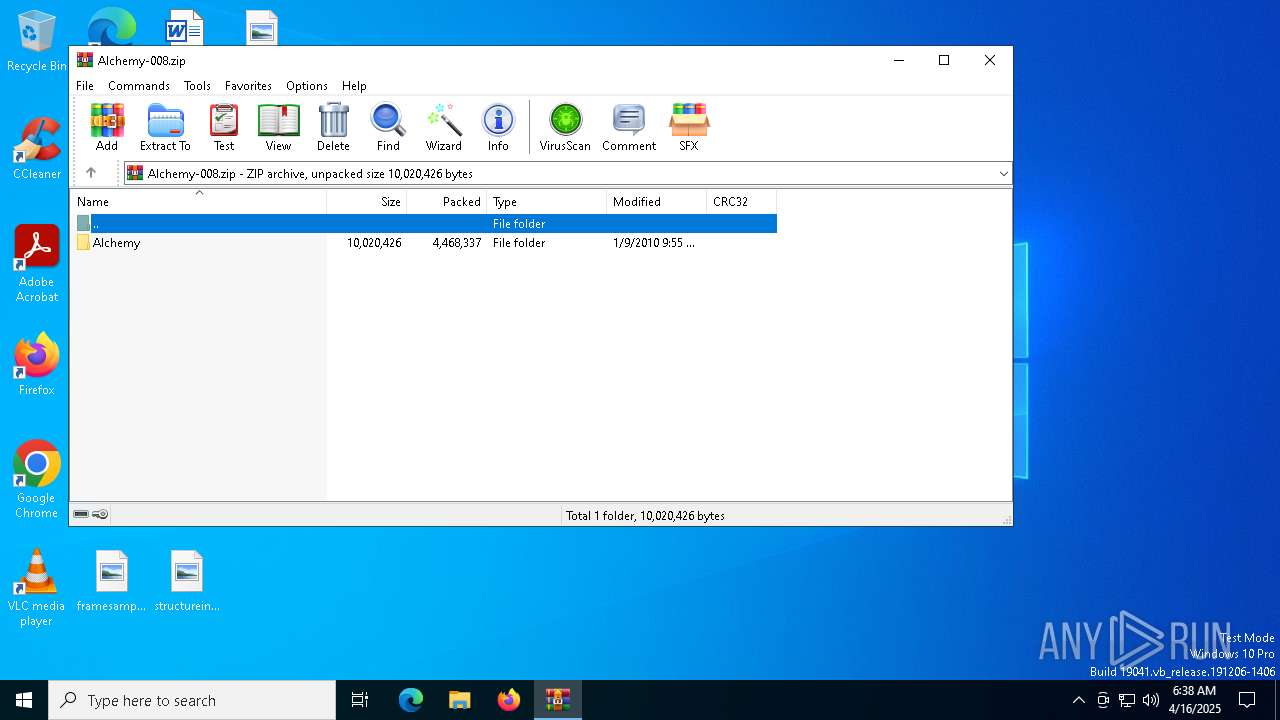
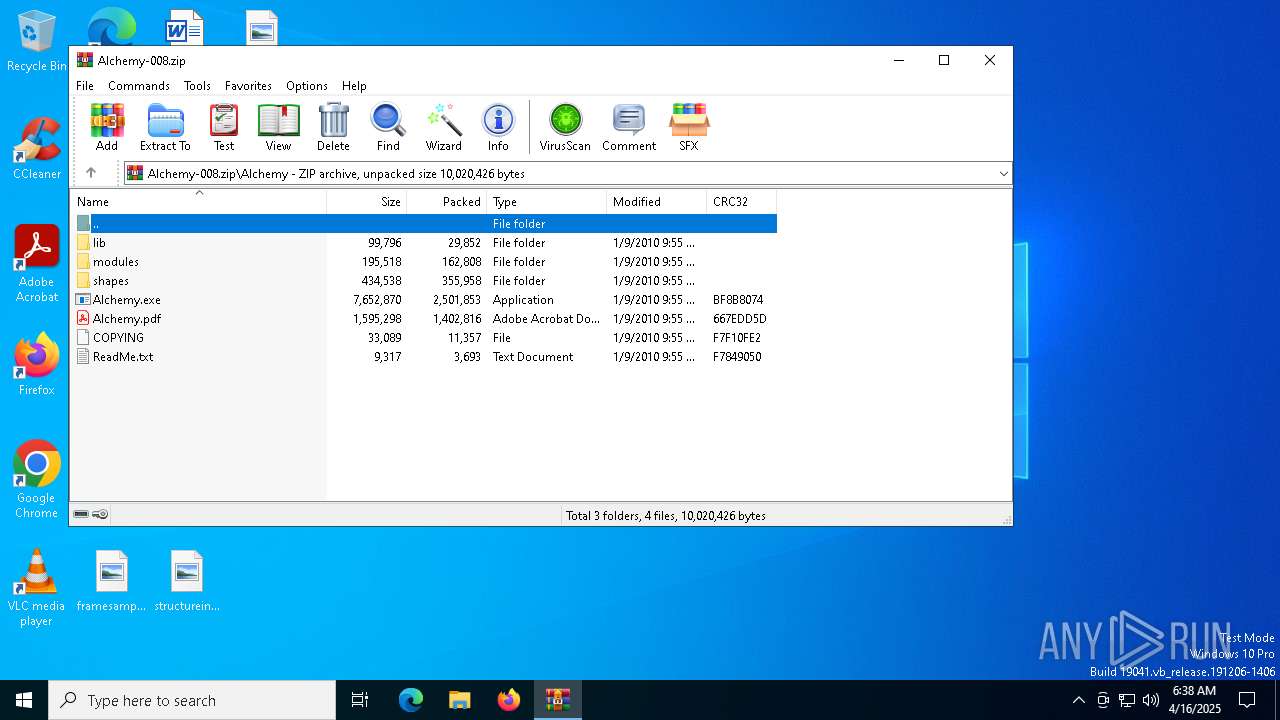
| File name: | Alchemy-008.zip |
| Full analysis: | https://app.any.run/tasks/2060e8e3-1012-410f-806e-6aabfa60393b |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2025, 06:38:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | EFA6A6CABE950355B03BC363DA971629 |
| SHA1: | 61D9556E3D46173F882F4832564014E5B1D2050A |
| SHA256: | 0C566D4898DAFDD86CE7E880FDC407105F7D5882073A85FBC36E3FB04994BA86 |
| SSDEEP: | 98304:waqzEqGLYf7mgzIsbrHqBfOaRljSvIGjuOOEMNX3XWYyD2eBi0b+Sh5rHSlH31bv:uSR3cvpSx |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks for Java to be installed
- Alchemy.exe (PID: 7996)
- javaw.exe (PID: 8016)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 5548)
Checks supported languages
- Alchemy.exe (PID: 7996)
- javaw.exe (PID: 8016)
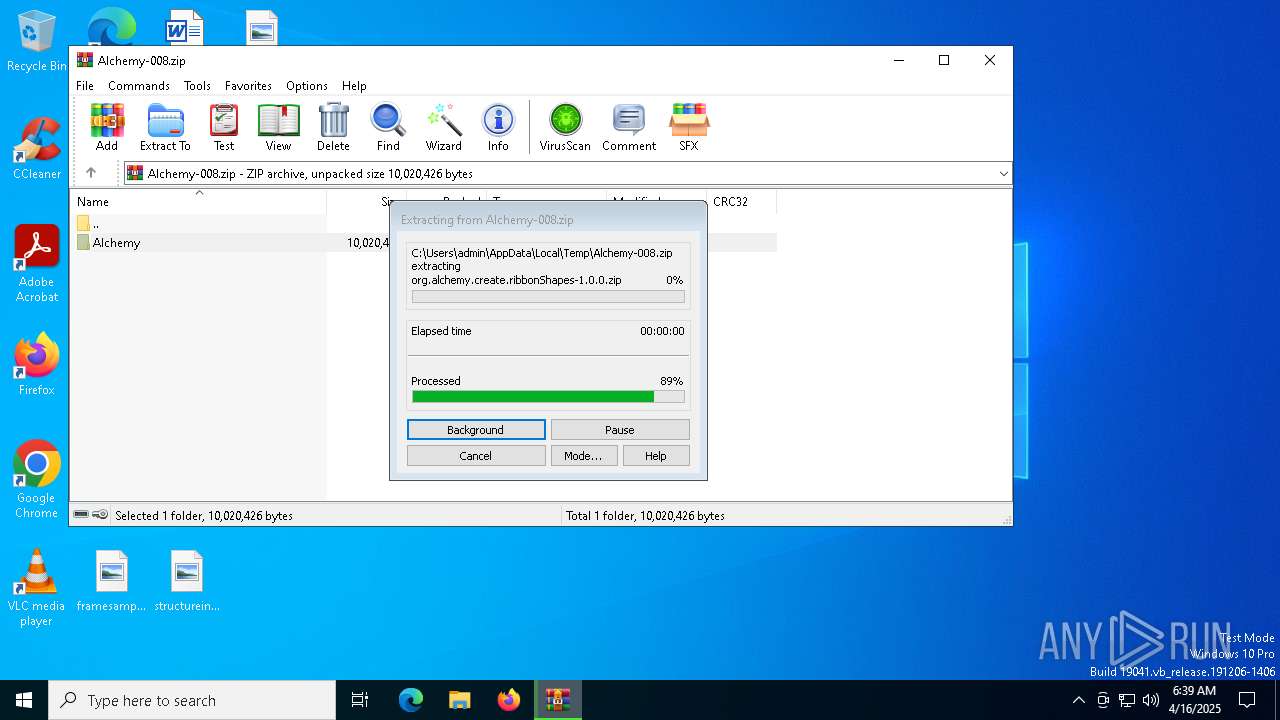
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5548)
Manual execution by a user
- Alchemy.exe (PID: 7996)
Creates files in the program directory
- javaw.exe (PID: 8016)
Create files in a temporary directory
- javaw.exe (PID: 8016)
Reads the computer name
- javaw.exe (PID: 8016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2010:01:09 09:55:46 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Alchemy/ |
Total processes
135
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5548 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Alchemy-008.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7256 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7288 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7836 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
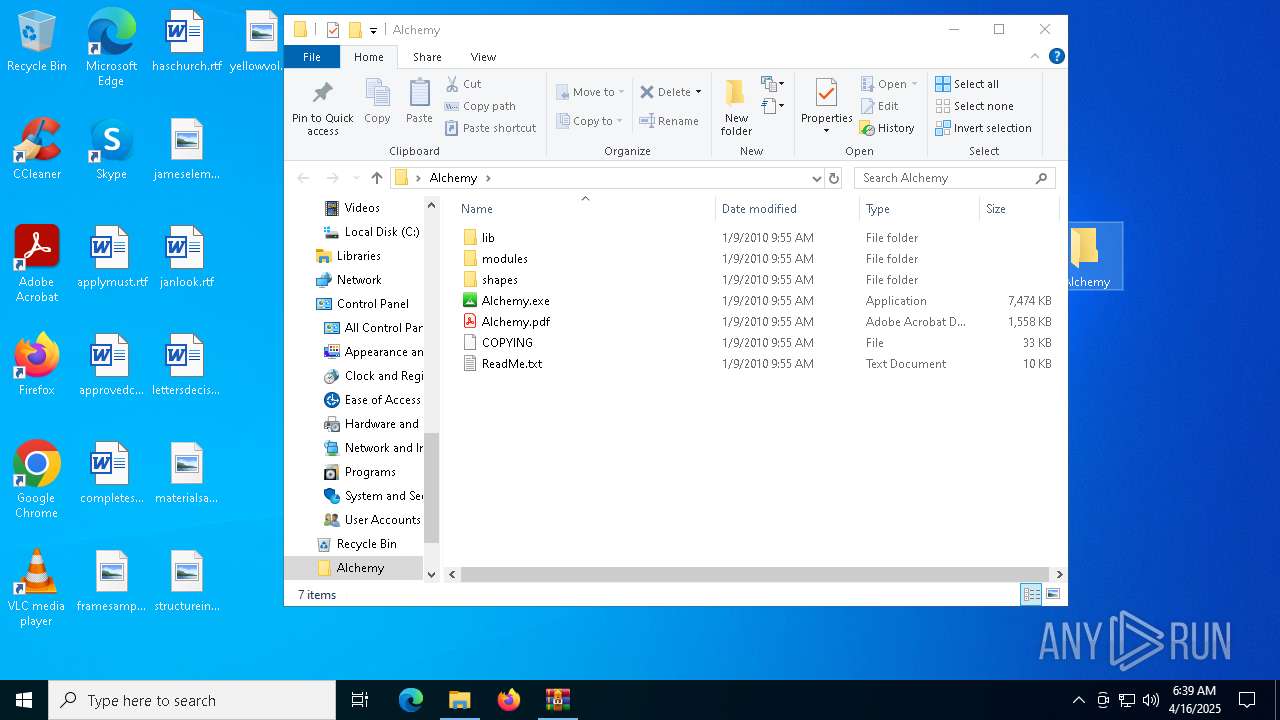
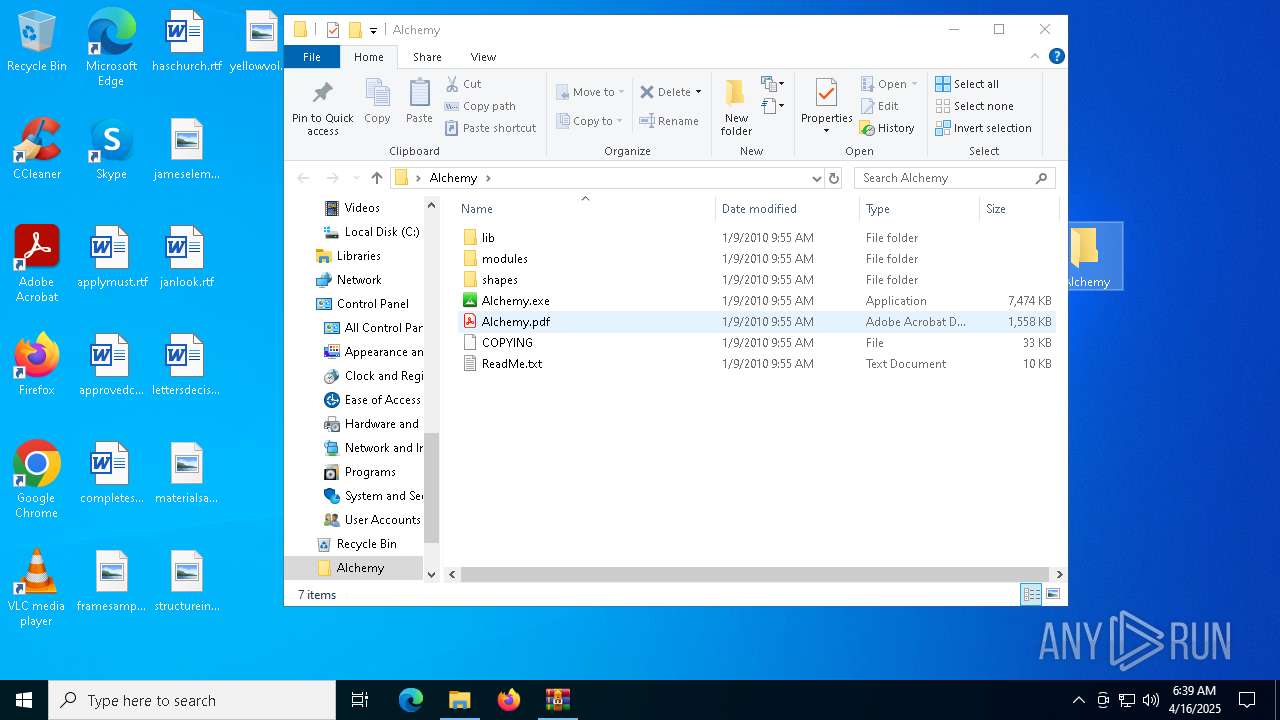
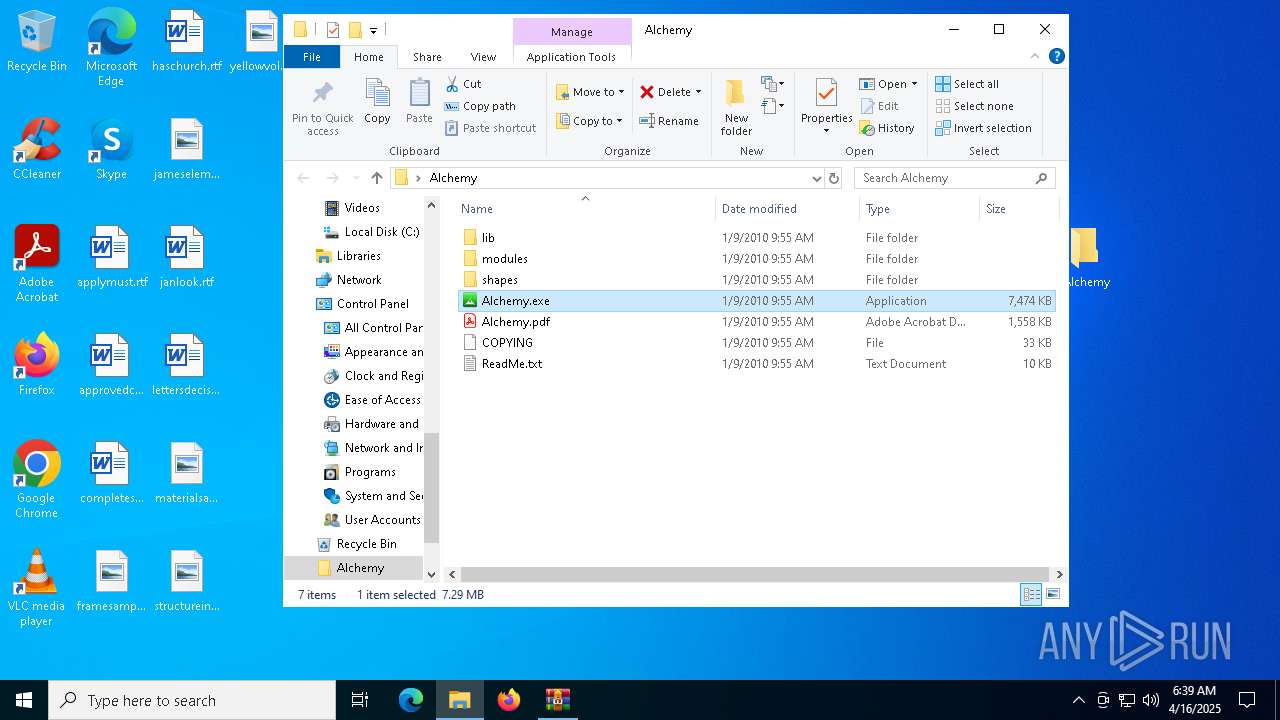
| 7996 | "C:\Users\admin\Desktop\Alchemy\Alchemy.exe" | C:\Users\admin\Desktop\Alchemy\Alchemy.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Alchemy is an open drawing project aimed at exploring how we can sketch, draw, and create on computers in new ways. Exit code: 0 Version: BETA 008 (0.0.8.1) Modules
| |||||||||||||||
| 8016 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -Xms128m -Xmx512m -Djava.library.path=lib -jar "C:\Users\admin\Desktop\Alchemy\Alchemy.exe" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | Alchemy.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Version: 8.0.2710.9 Modules
| |||||||||||||||
| 8112 | C:\WINDOWS\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 028
Read events
3 019
Write events
8
Delete events
1
Modification events
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Alchemy-008.zip | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8016) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\Prefs\jpen\provider |
| Operation: | delete value | Name: | /Native/Library/Loader.architecture |
Value: | |||
Executable files
3
Suspicious files
31
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5548.35021\Alchemy\modules\org.alchemy.affect.blindness-1.0.6.zip | compressed | |
MD5:182F6D88264A6835AC5CF4863C9B64E7 | SHA256:831C34A3E2C165FE3638B9B8CA7B801D52CAB9FC87E619DBA6FE97BB5DE4430E | |||
| 5548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5548.35021\Alchemy\modules\org.alchemy.affect.displace-1.0.5.zip | compressed | |
MD5:9C7192E22C909E7BA401D183BC759A78 | SHA256:AA3F4E142BC9ACE0FAD8FAAE754C72DC7E546E707E801BAFB9F11780E9B3D9B3 | |||
| 5548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5548.35021\Alchemy\modules\org.alchemy.affect.colorSwitcher-1.0.5.zip | compressed | |
MD5:4695805279CA831713B874B991D14BC9 | SHA256:BF0970C38BC1ABC6A39D04CF219D8DAD21031D7EF40C6FEA2E40F0B8802F0A09 | |||
| 5548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5548.35021\Alchemy\lib\jpen-2-2-64.dll | executable | |
MD5:7F7DDAB006FC5ADDCEEAC5E719E99AE2 | SHA256:4FED1F4CAE958DCC2DA883D22FD718453D87D44EED3B0F4C4E6E837FD01557C2 | |||
| 5548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5548.35021\Alchemy\lib\jpen-2-2.dll | executable | |
MD5:98E67A3486C3031B1B3F29B2C78656EF | SHA256:DCED1EA809FC89C025792A72F261711F202D7F1E8B206270A019F1D53CD0516A | |||
| 5548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5548.35021\Alchemy\modules\org.alchemy.affect.repeat-1.0.6.zip | compressed | |
MD5:121ABCDF913E57CF060FEFEAB1F48502 | SHA256:E86624F5D8A3DCD2BDF18B8596F180FAB75833B7071E2151951E1BA503F2B007 | |||
| 5548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5548.35021\Alchemy\modules\org.alchemy.affect.gradient-1.0.1.zip | compressed | |
MD5:DF0FC09C1F54BD7092A75E42B76B99CD | SHA256:338AE1A174D9B31A244BE60F2410575482A0878D083F7C575D107FE753D7ADDF | |||
| 5548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5548.35021\Alchemy\modules\org.alchemy.affect.limit-1.0.0.zip | compressed | |
MD5:DBA4DA0F0E8D97D36231611BE8D1865F | SHA256:6DA3A3F64185A73180C864B7F29B3C1B72C2DF320332699F19222A00F849C284 | |||
| 5548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5548.35021\Alchemy\modules\org.alchemy.affect.mirror-1.0.11.zip | compressed | |
MD5:9CBF82E91E2FD4B79887D1622B14AD9F | SHA256:C48DA470A2E71B1D7014CF65A5F540ED6E7D3620FE66C059FD252A3E9EEFE92F | |||
| 5548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5548.35021\Alchemy\modules\org.alchemy.affect.micExpand-1.0.7.zip | compressed | |
MD5:A636880EB58692F0835863B1BDAFC1F6 | SHA256:0B7EE732A5F6510F8FCF92AFEB2FC6DFA7F02F44A9F30FEE3F8A7287C78684D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7868 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7868 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7868 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7868 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |