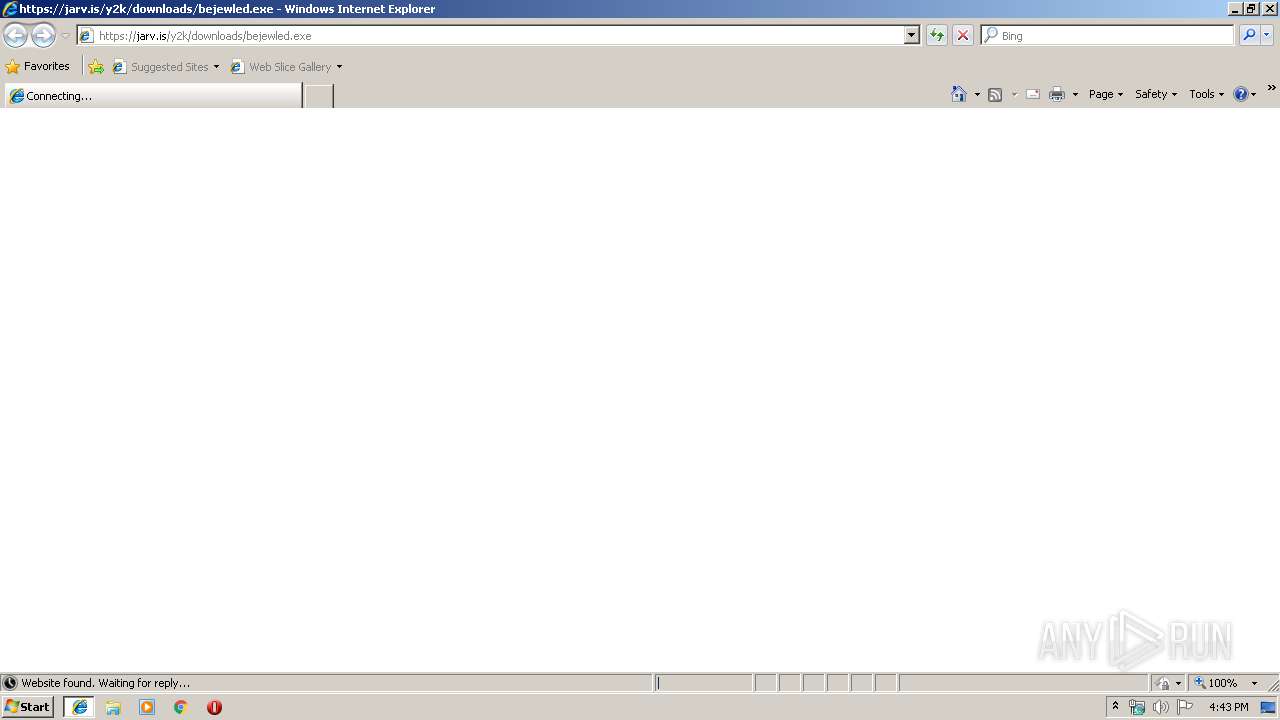
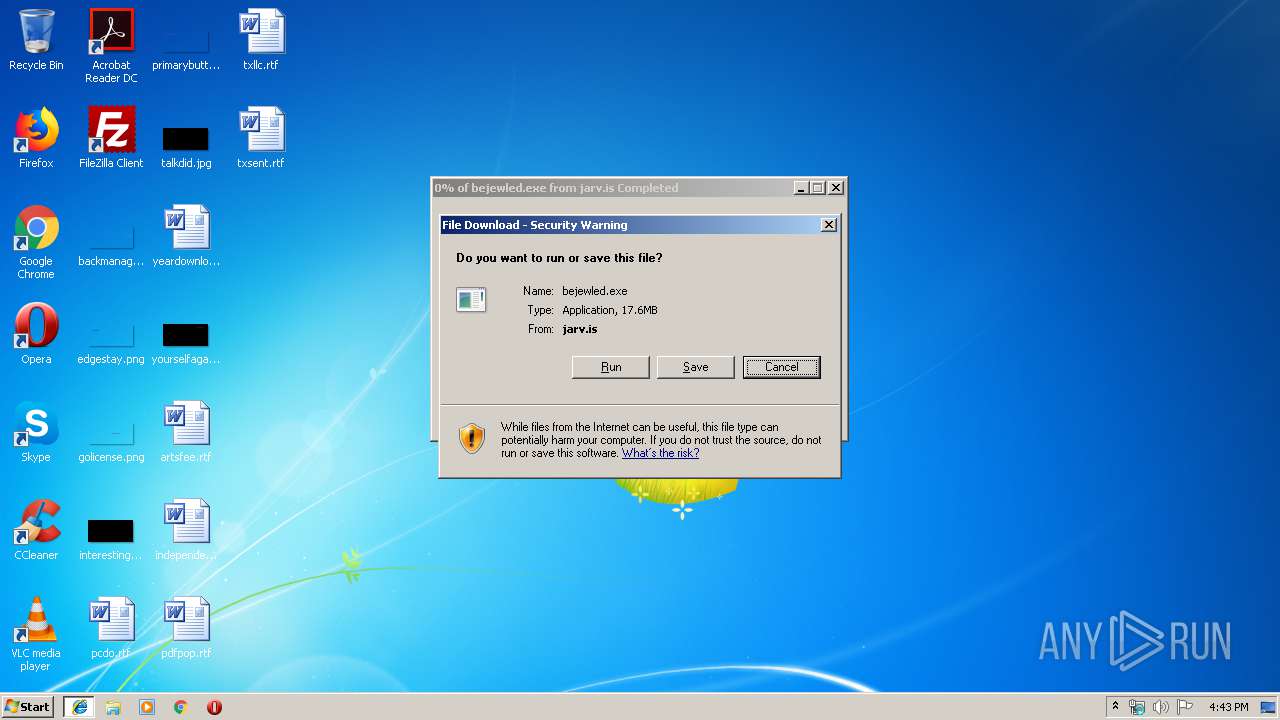
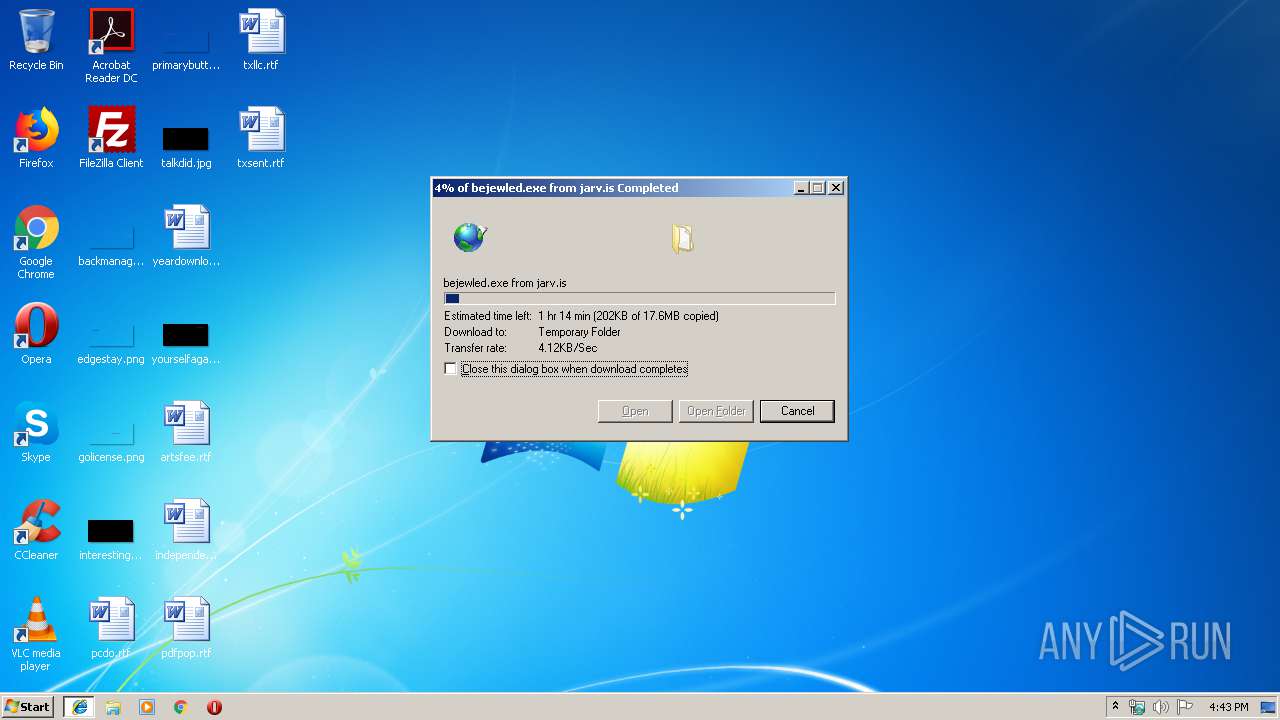
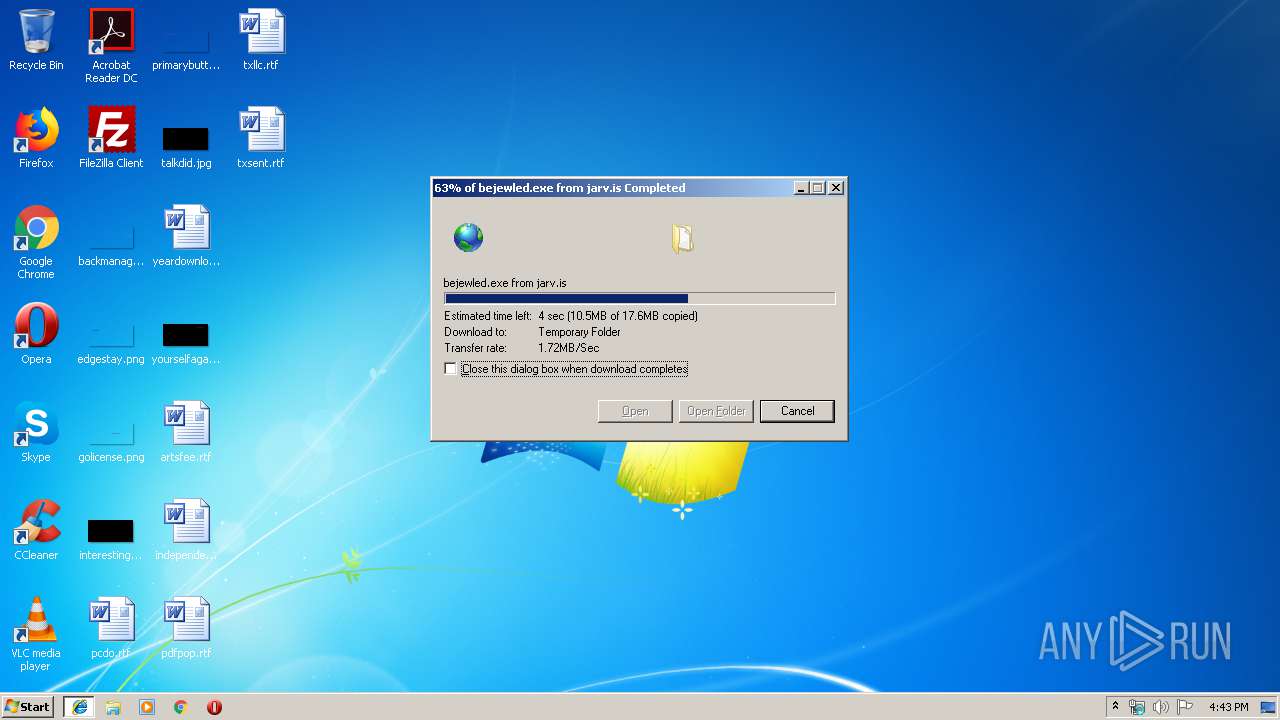
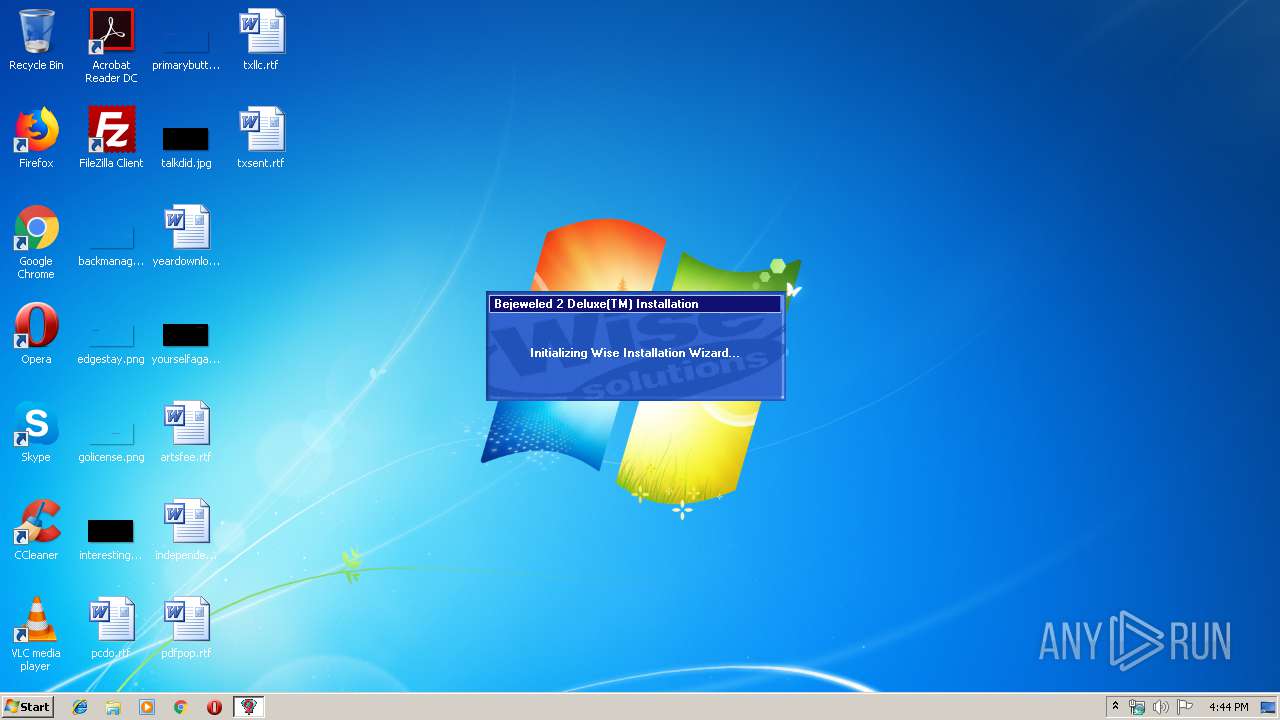
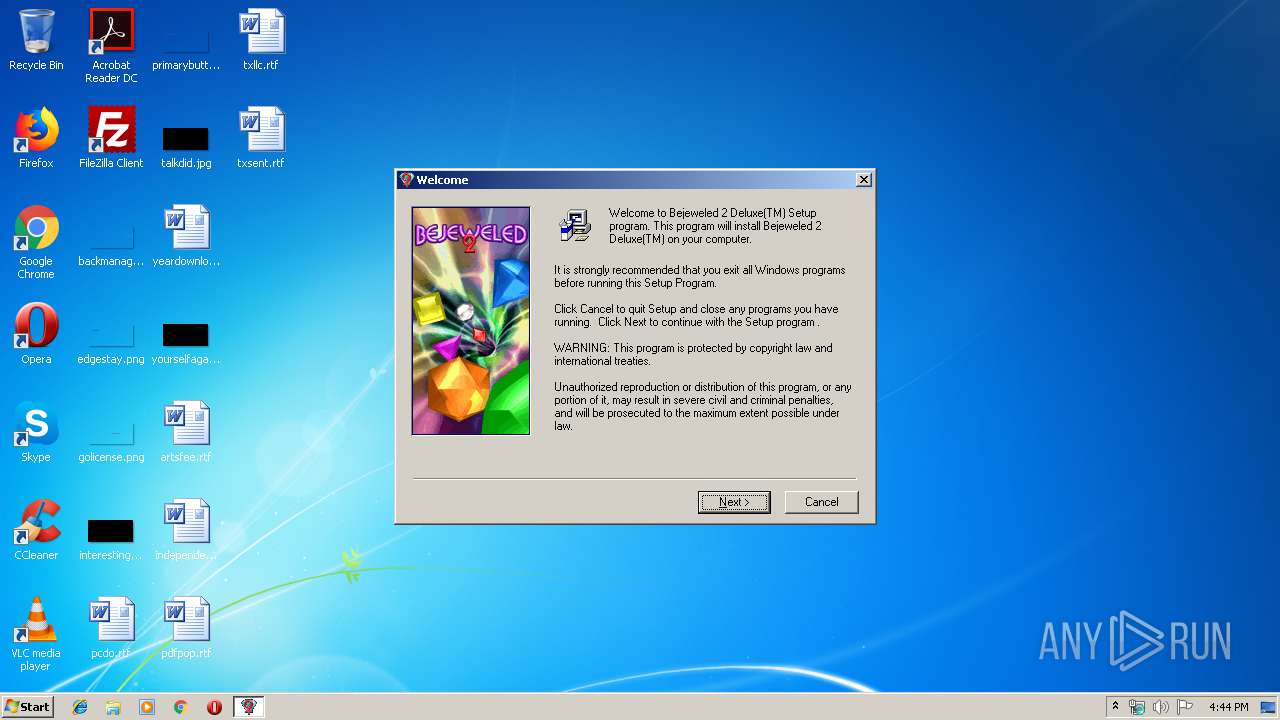
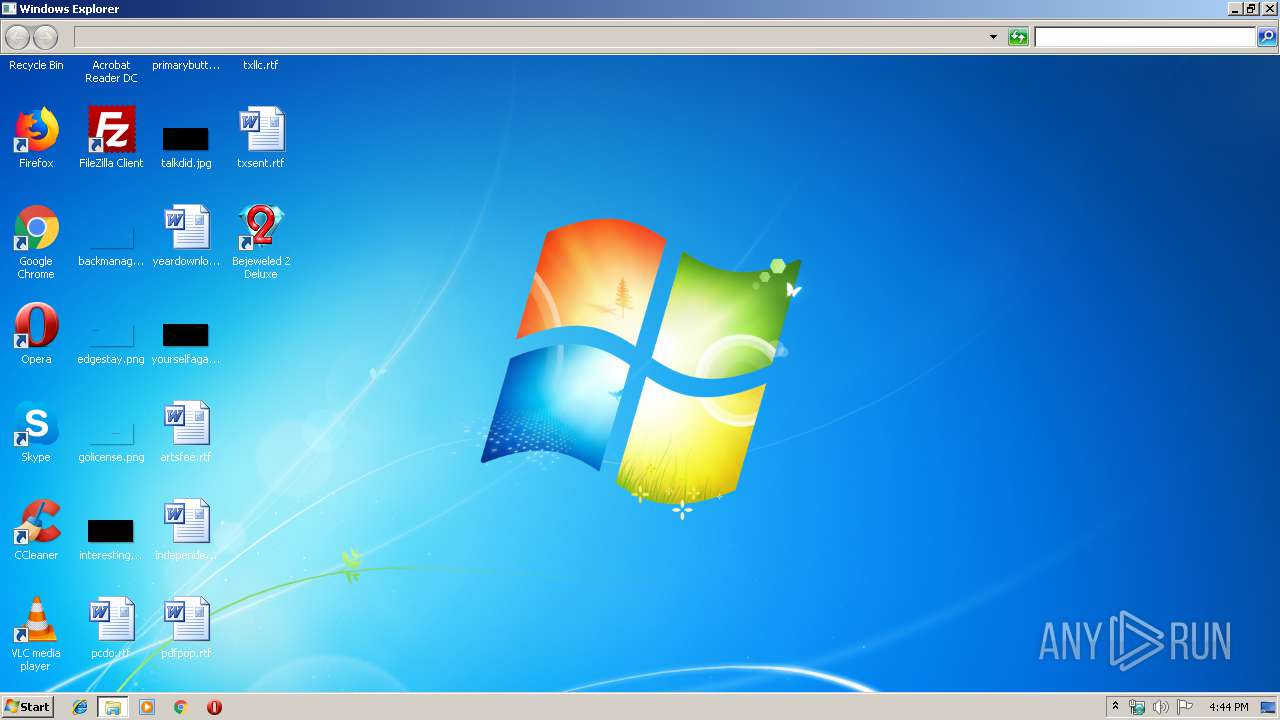
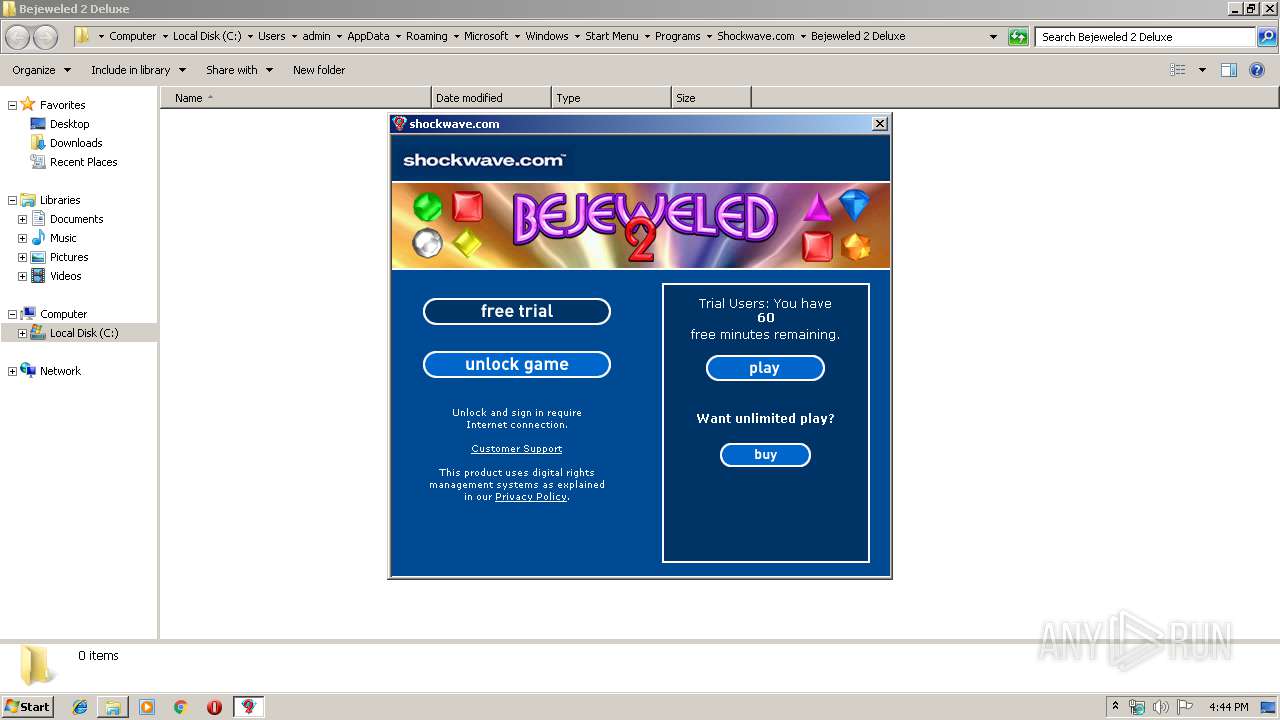
| URL: | https://jarv.is/y2k/downloads/bejewled.exe |
| Full analysis: | https://app.any.run/tasks/88bddd03-9c76-47c5-a5f9-3072009442e5 |
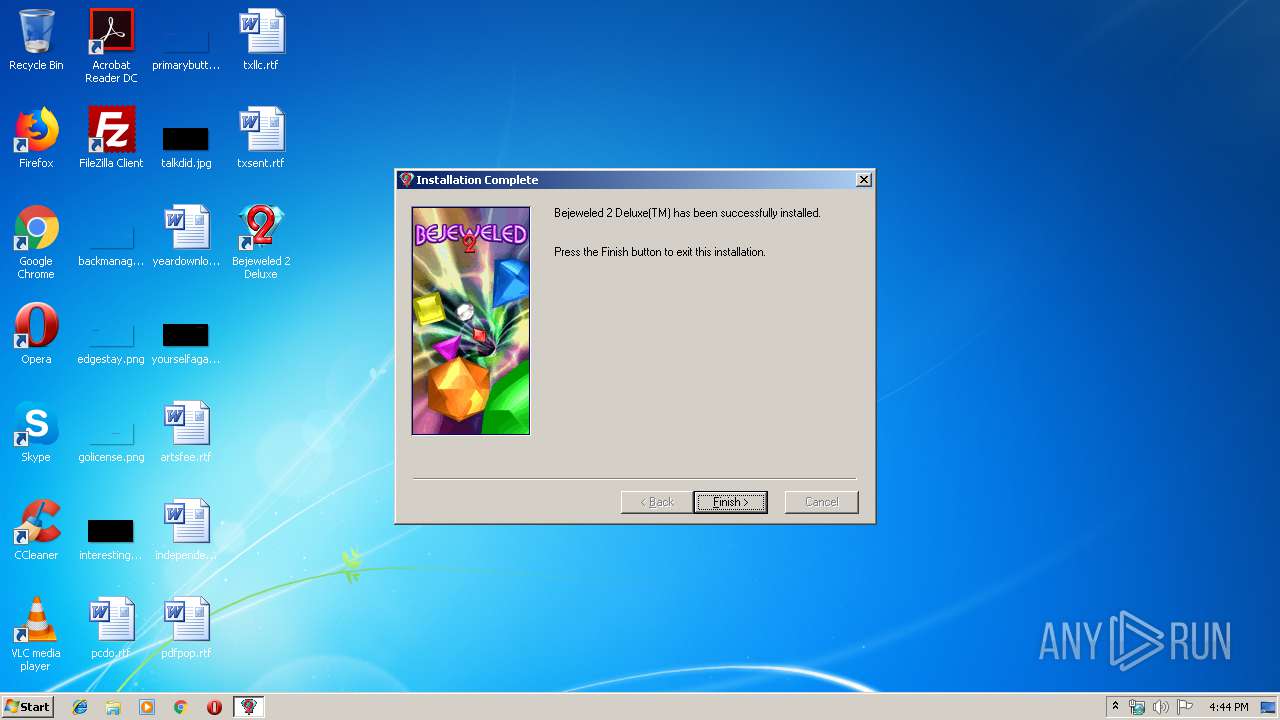
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 15:43:27 |
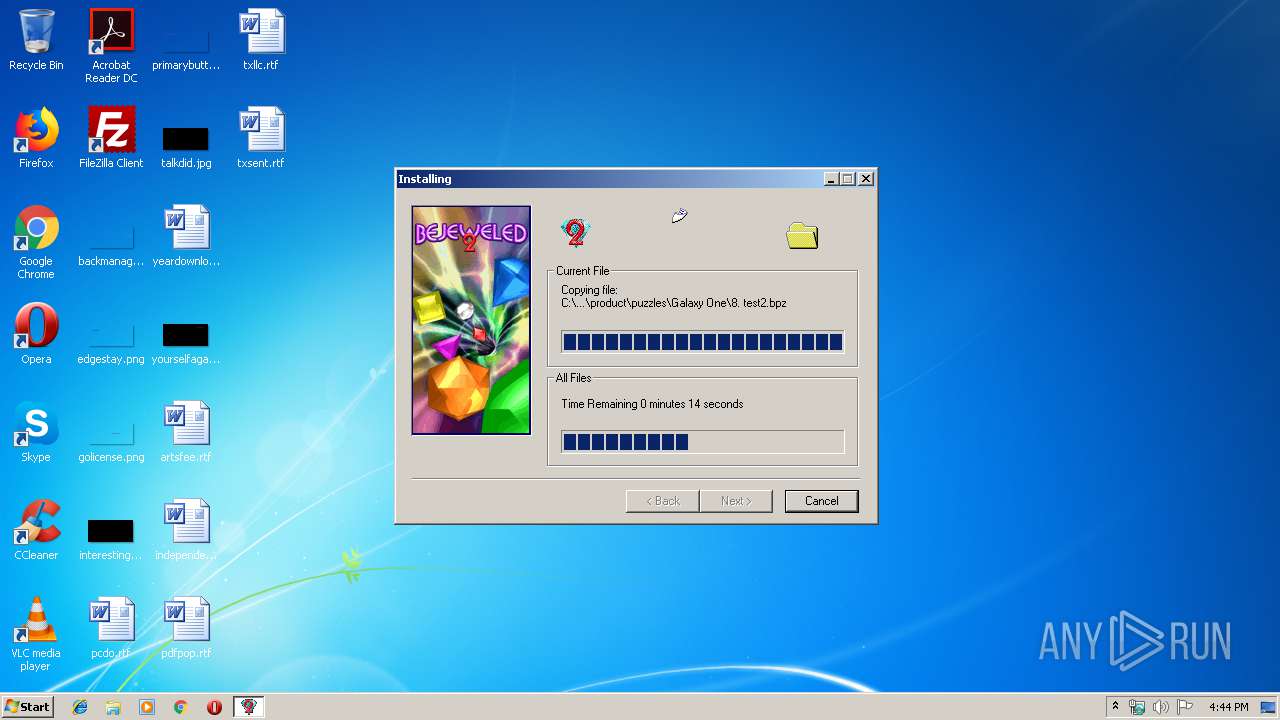
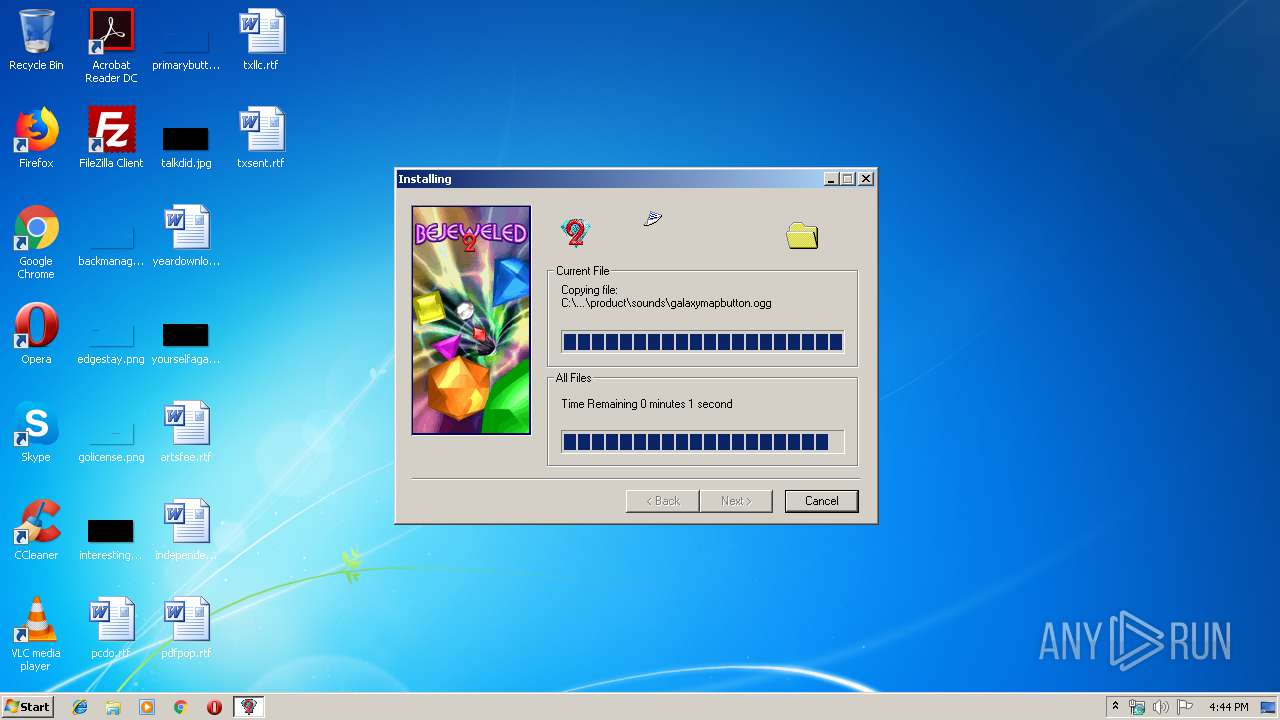
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 744203822118E4FB81C90DC0A95FA39F |
| SHA1: | 617A776A1EC30ECD7E8244438BBAA4AB4AD3027E |
| SHA256: | 0C53AA79AEF5078D5299F318B93B3B70CF572DCE0C7538D75757974DE4973400 |
| SSDEEP: | 3:N8k3eS94KKAL:28eSV3 |
MALICIOUS
Application was dropped or rewritten from another process
- GLB3254.tmp (PID: 3284)
- bejewled[1].exe (PID: 3864)
- bejewled[1].exe (PID: 2980)
- WinBej2.exe (PID: 2424)
- Bejeweled2Deluxe.exe (PID: 3880)
Loads dropped or rewritten executable
- svchost.exe (PID: 848)
- GLB3254.tmp (PID: 3284)
- explorer.exe (PID: 252)
- svchost.exe (PID: 816)
- WinBej2.exe (PID: 2424)
- Bejeweled2Deluxe.exe (PID: 3880)
Changes settings of System certificates
- WinBej2.exe (PID: 2424)
SUSPICIOUS
Starts Internet Explorer
- explorer.exe (PID: 252)
Executable content was dropped or overwritten
- bejewled[1].exe (PID: 3864)
- iexplore.exe (PID: 4000)
- iexplore.exe (PID: 3336)
- GLB3254.tmp (PID: 3284)
Starts application with an unusual extension
- bejewled[1].exe (PID: 3864)
Reads Internet Cache Settings
- explorer.exe (PID: 252)
Removes files from Windows directory
- GLB3254.tmp (PID: 3284)
Creates files in the Windows directory
- GLB3254.tmp (PID: 3284)
Creates a software uninstall entry
- GLB3254.tmp (PID: 3284)
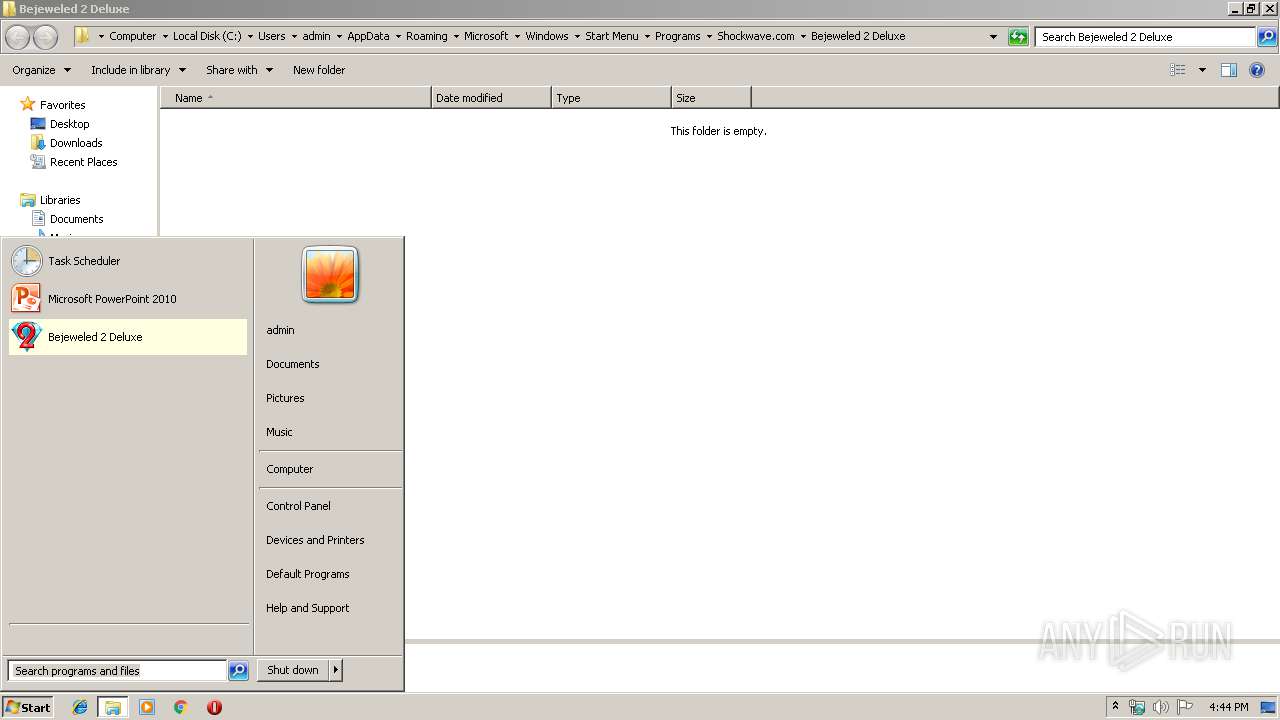
Creates COM task schedule object
- Bejeweled2Deluxe.exe (PID: 3880)
Executed via COM
- explorer.exe (PID: 2816)
Reads internet explorer settings
- Bejeweled2Deluxe.exe (PID: 3880)
Adds / modifies Windows certificates
- WinBej2.exe (PID: 2424)
Searches for installed software
- svchost.exe (PID: 816)
Creates files in the program directory
- WinBej2.exe (PID: 2424)
- GLB3254.tmp (PID: 3284)
INFO
Creates files in the user directory
- iexplore.exe (PID: 3336)
- iexplore.exe (PID: 4000)
Reads Internet Cache Settings
- iexplore.exe (PID: 4000)
- iexplore.exe (PID: 3336)
Changes internet zones settings
- iexplore.exe (PID: 3336)
Application launched itself
- iexplore.exe (PID: 3336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
12
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ctfmon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 816 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 848 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
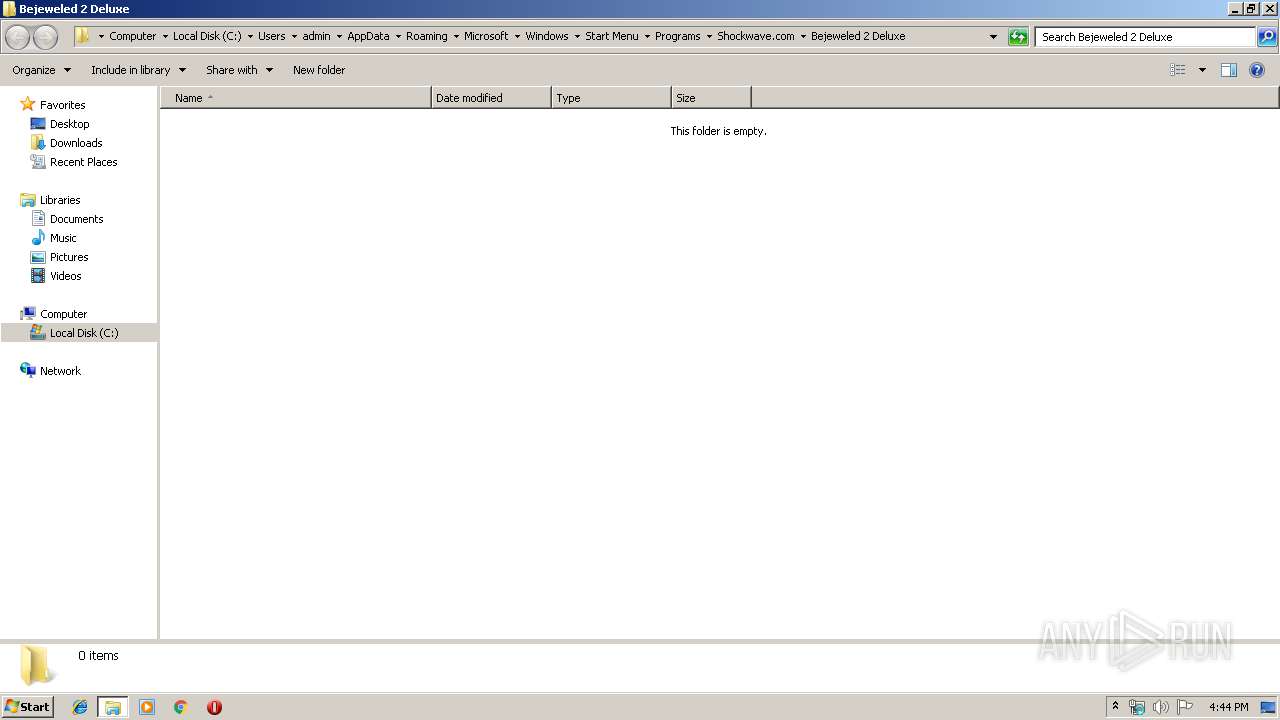
| 2424 | "C:\Program Files\Shockwave.com\Bejeweled 2 Deluxe\product\WinBej2.exe" | C:\Program Files\Shockwave.com\Bejeweled 2 Deluxe\product\WinBej2.exe | Bejeweled2Deluxe.exe | ||||||||||||
User: admin Company: PopCap.com Integrity Level: MEDIUM Description: Bejeweled2 Exit code: 0 Version: 0, 0, 0, 0 Modules
| |||||||||||||||
| 2816 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2980 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\bejewled[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\bejewled[1].exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3284 | C:\Users\admin\AppData\Local\Temp\GLB3254.tmp 4736 C:\Users\admin\AppData\Local\MICROS~1\Windows\TEMPOR~1\Content.IE5\I0488CJO\BEJEWL~1.EXE | C:\Users\admin\AppData\Local\Temp\GLB3254.tmp | bejewled[1].exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3336 | "C:\Program Files\Internet Explorer\iexplore.exe" https://jarv.is/y2k/downloads/bejewled.exe | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3656 | "C:\Windows\explorer.exe" C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Shockwave.com\Bejeweled 2 Deluxe | C:\Windows\explorer.exe | — | GLB3254.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3864 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\bejewled[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\bejewled[1].exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 903
Read events
2 669
Write events
225
Delete events
9
Modification events
| (PID) Process: | (848) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\CoDeviceInstallers |
| Operation: | write | Name: | AeFileID |
Value: 300030003000300037003900370065006500350033006600340039003700330062003400330035003900330032006300350037003300660030003400310033006100660064003500390037003700620061006600300065000000 | |||
| (PID) Process: | (848) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\CoDeviceInstallers |
| Operation: | write | Name: | AeProgramID |
Value: 300030003000300064006100330039006100330065006500350065003600620034006200300064003300320035003500620066006500660039003500360030003100380039003000610066006400380030003700300039000000 | |||
| (PID) Process: | (3336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {B5009CF3-7E3A-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3336) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
Executable files
11
Suspicious files
171
Text files
705
Unknown types
181
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3336 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3336 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3336 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7789350BE20A851A.TMP | — | |
MD5:— | SHA256:— | |||
| 848 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YMT4PLAZ\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3336 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\C5OJ9CF4\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3336 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFECF928C93A61D62A.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3336 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3336 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4000 | iexplore.exe | 104.31.67.47:443 | jarv.is | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jarv.is |
| unknown |
www.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WinBej2.exe | BuildNum: 1948
|
WinBej2.exe | BuildNum: 1948
|
WinBej2.exe | BuildDate: Wed Oct 27 16:01:07 2004
|
WinBej2.exe | Loading completed: 218 out of 218
|
WinBej2.exe | Resource Loading Time: 9
|