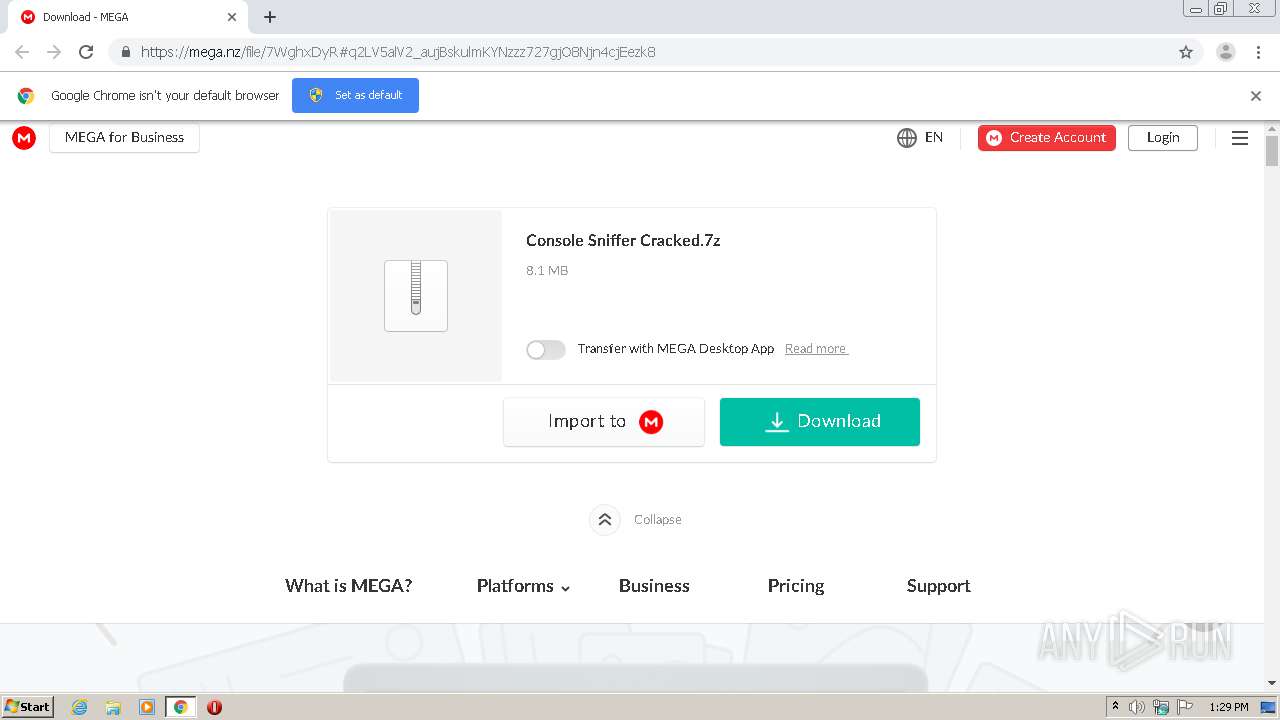
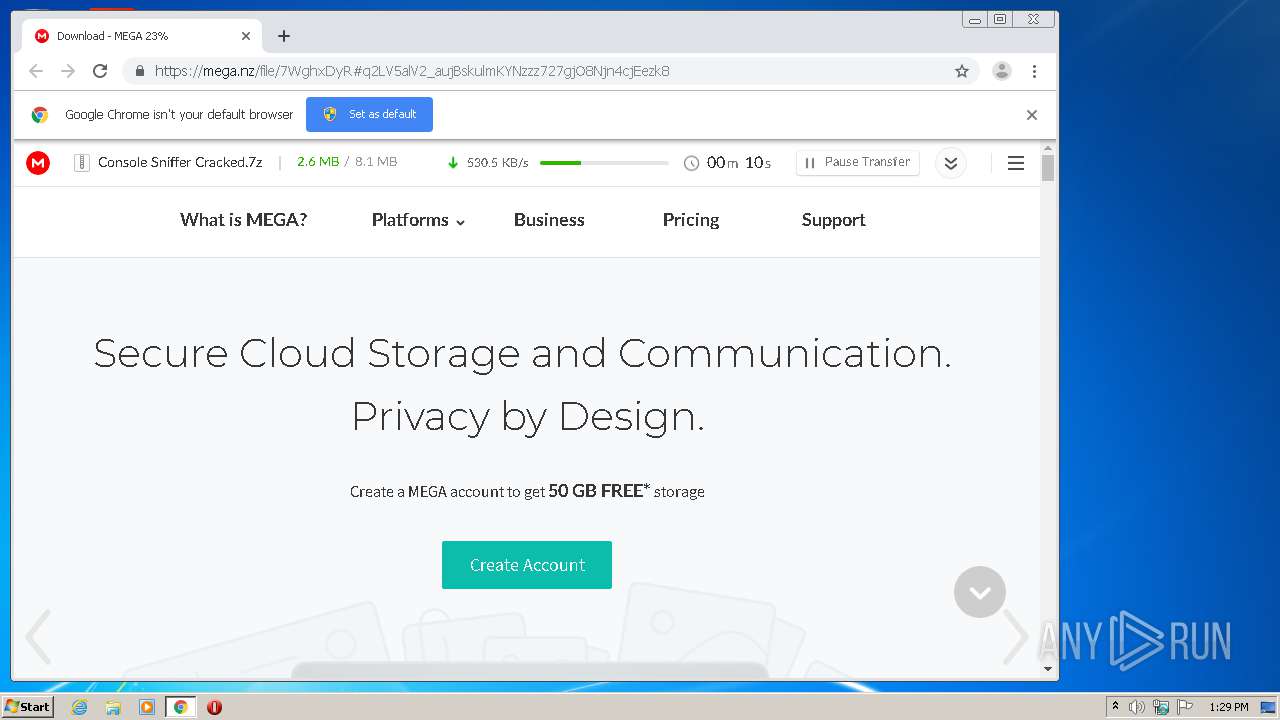
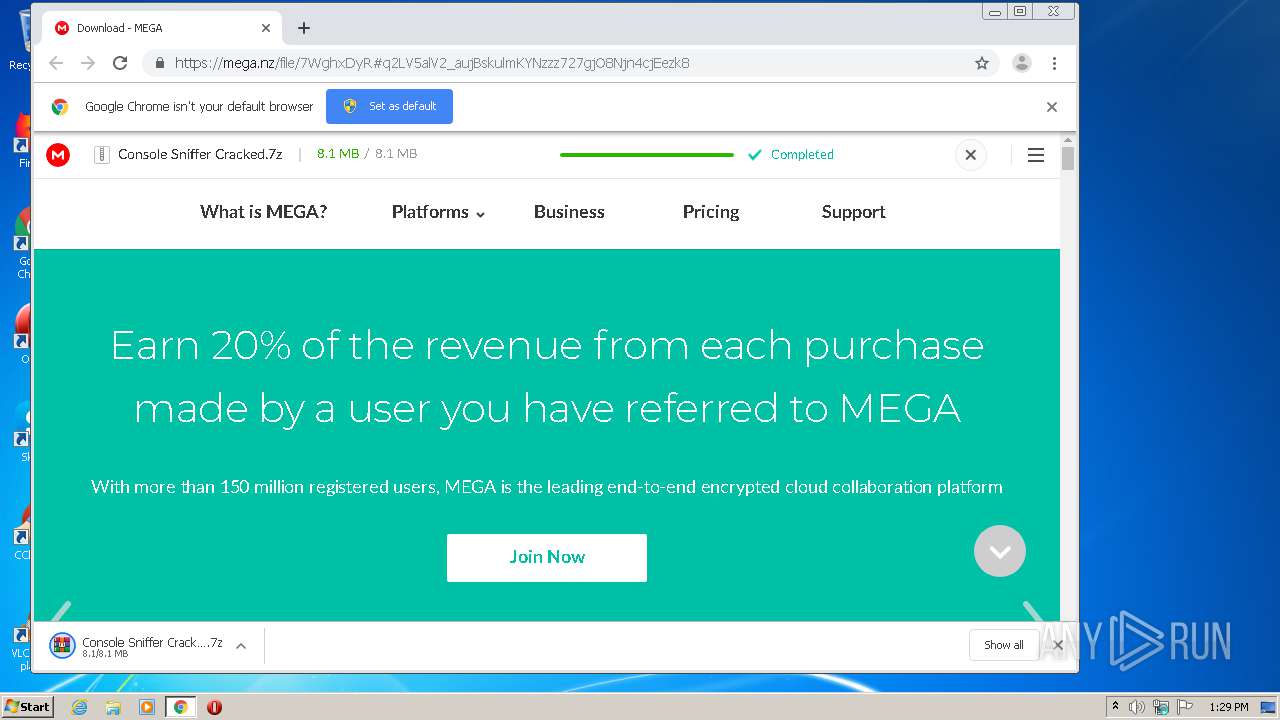
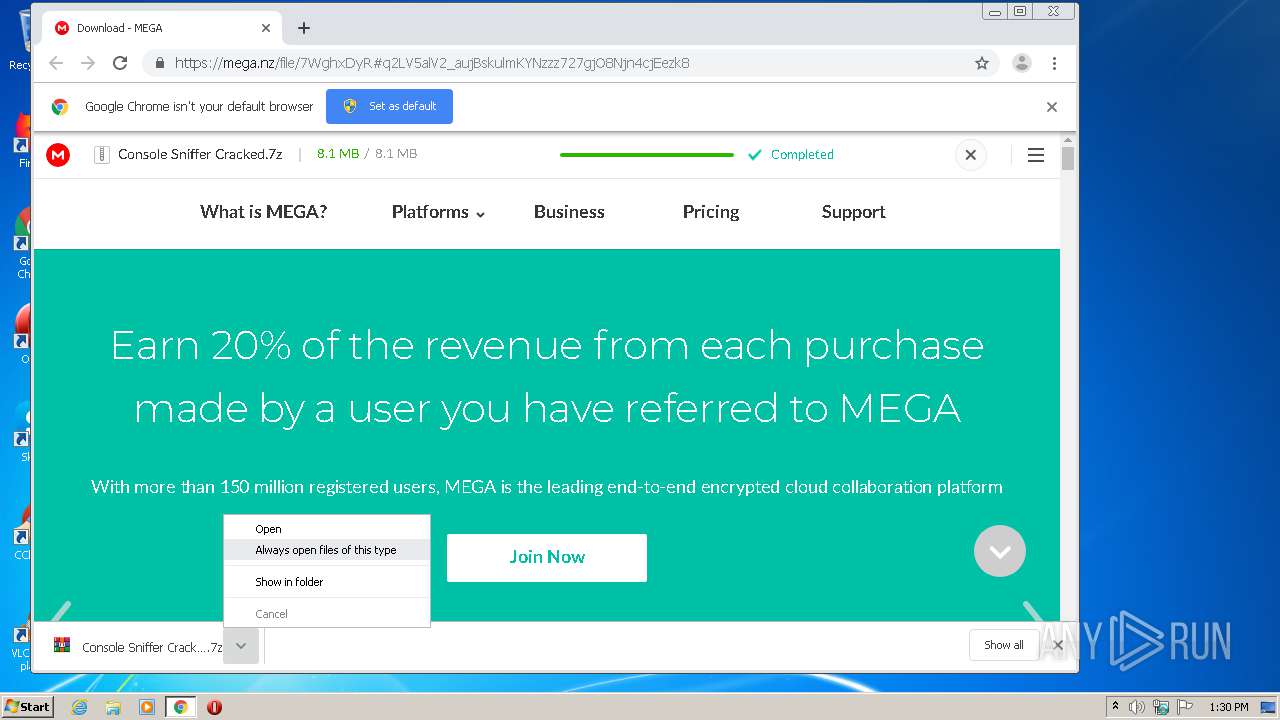
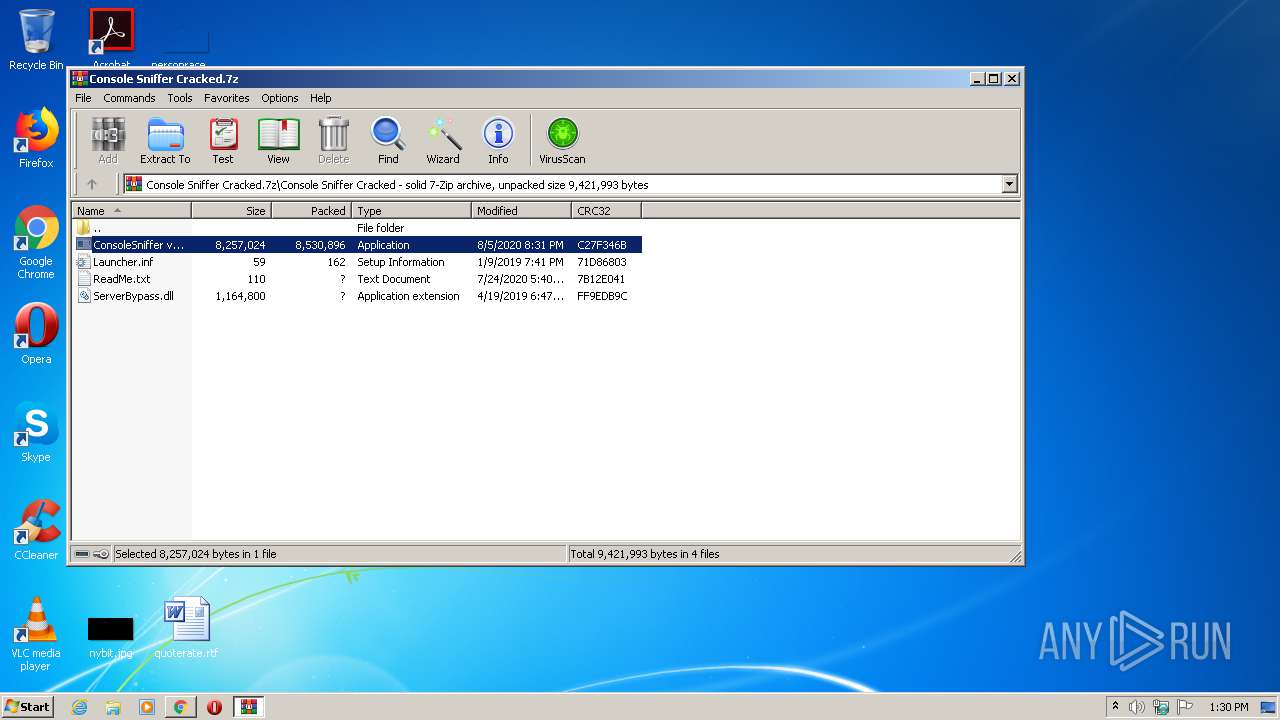
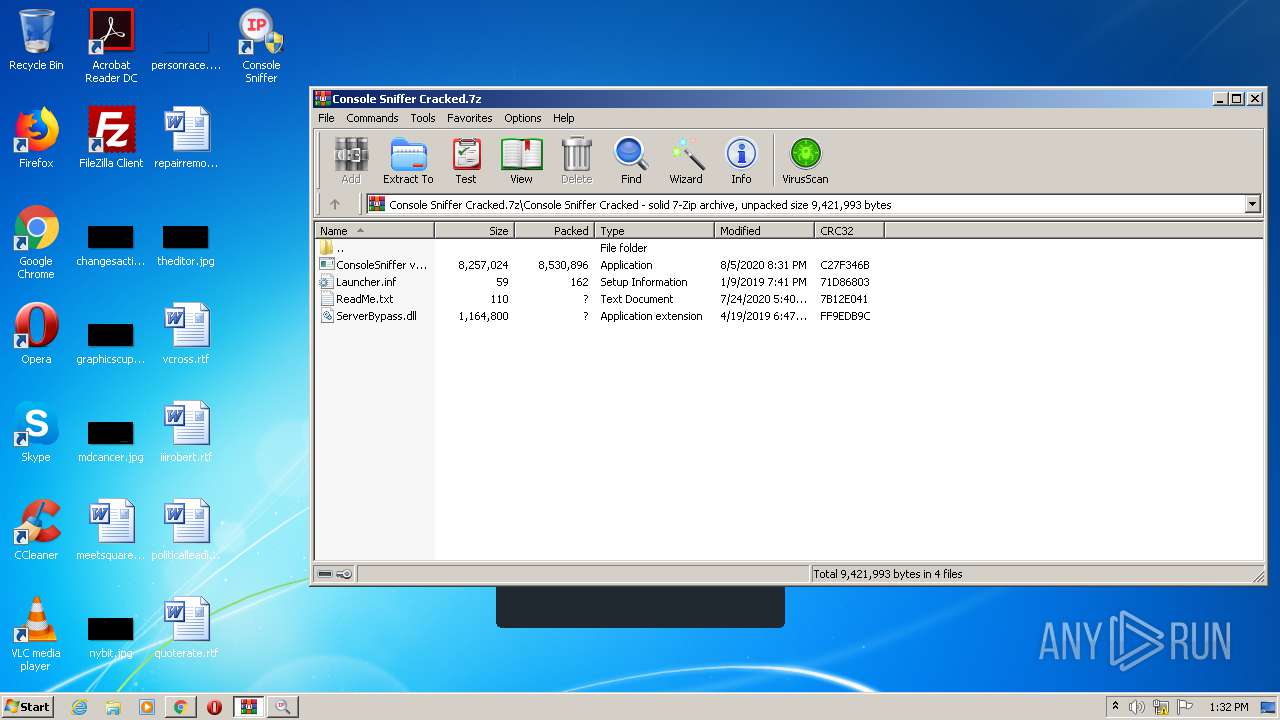
| URL: | https://mega.nz/file/7WghxDyR#q2LV5alV2_aujBskulmKYNzzz727gjO8Njn4cjEezk8 |
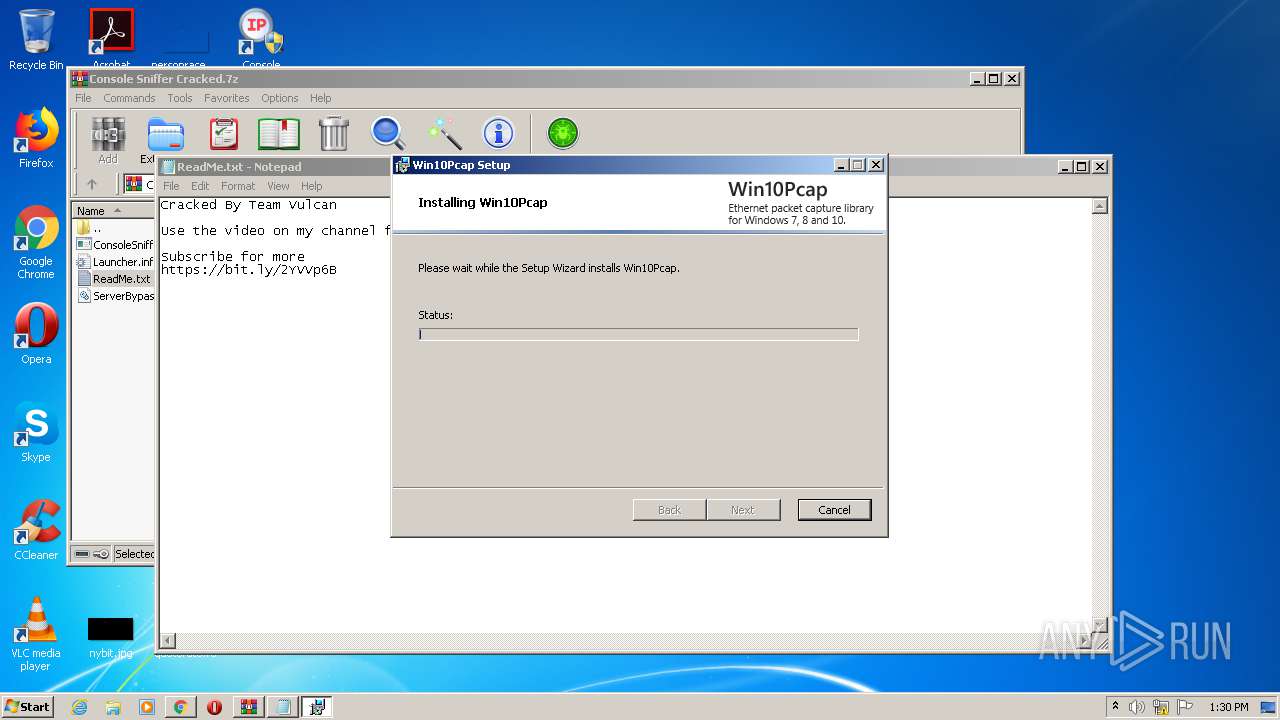
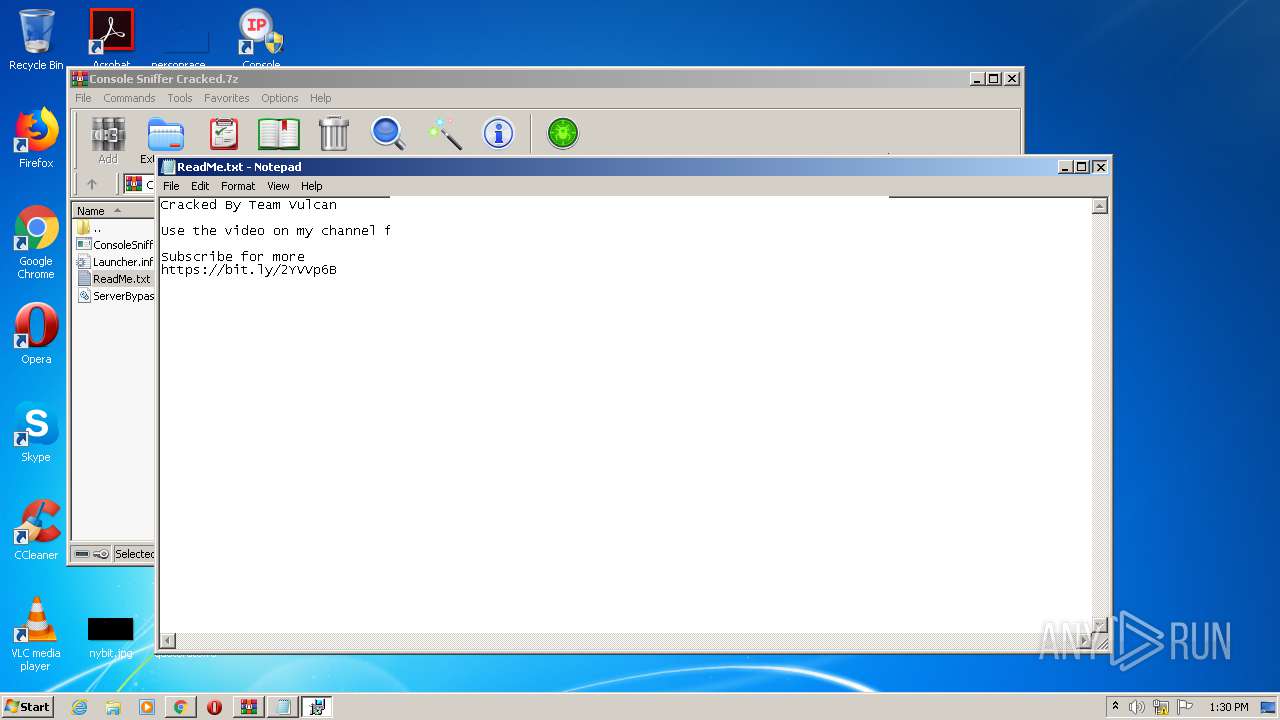
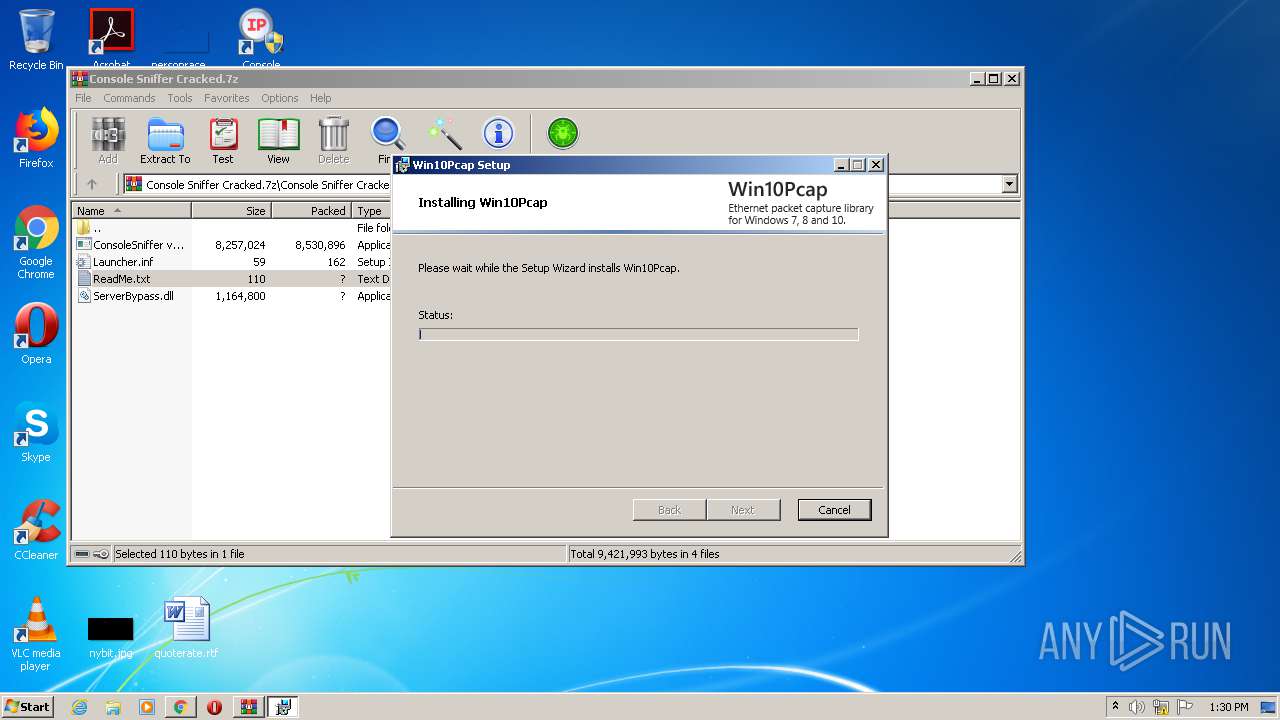
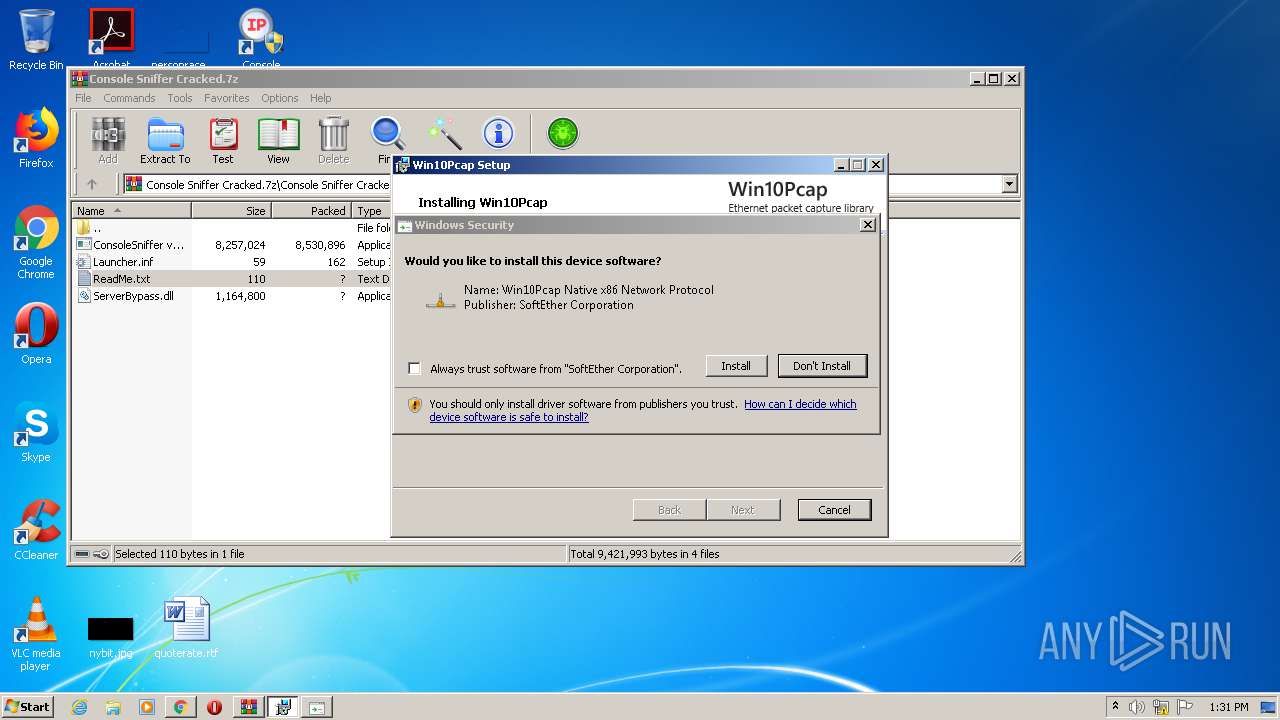
| Full analysis: | https://app.any.run/tasks/09588976-ca38-4a61-baeb-19784c18f7a8 |
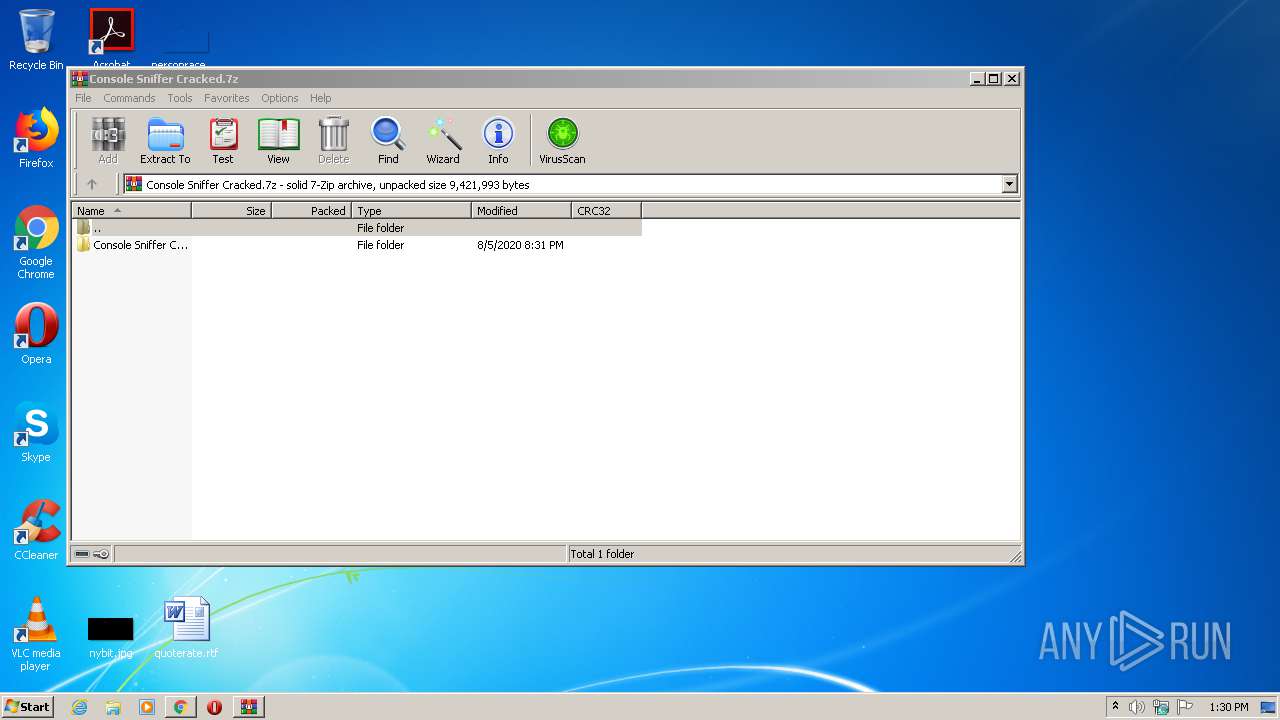
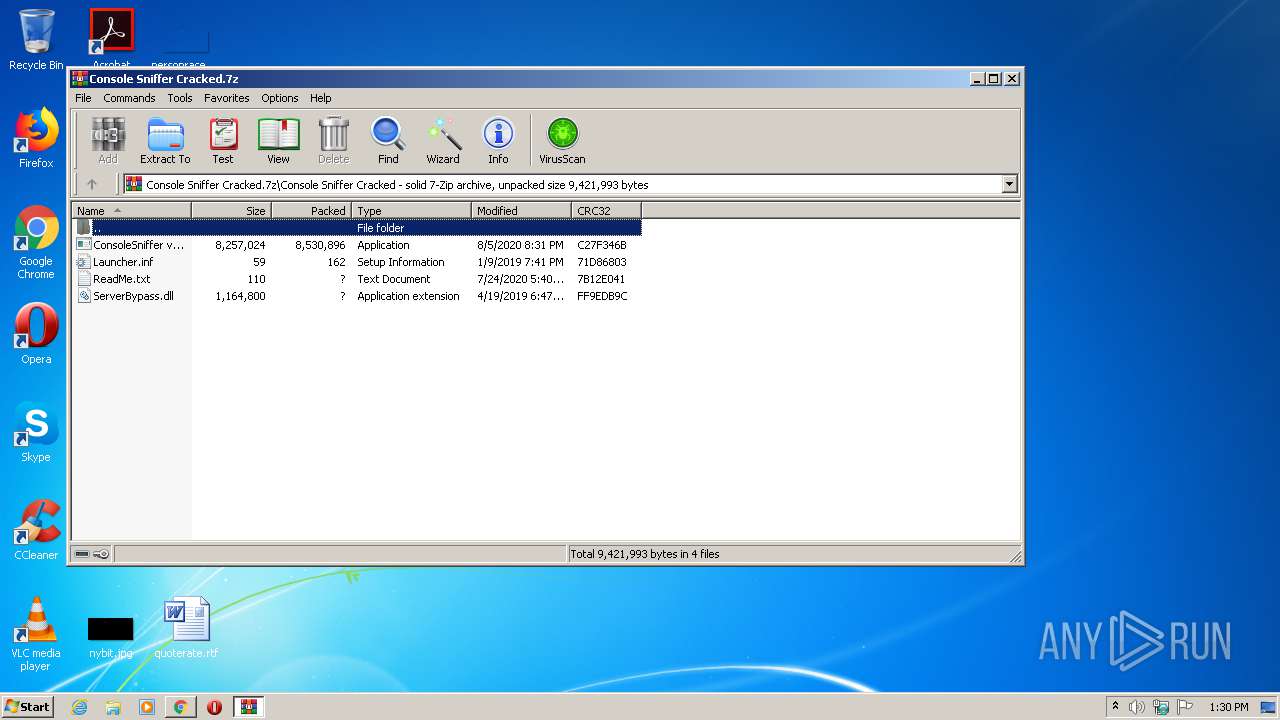
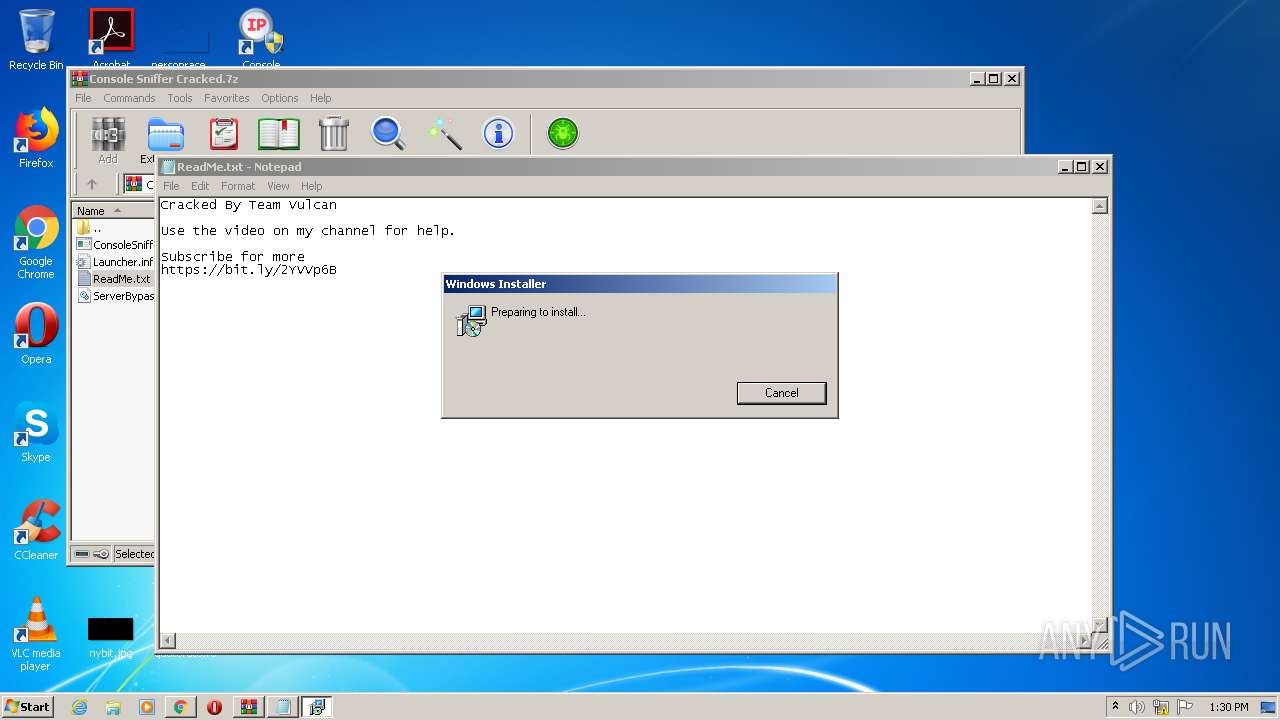
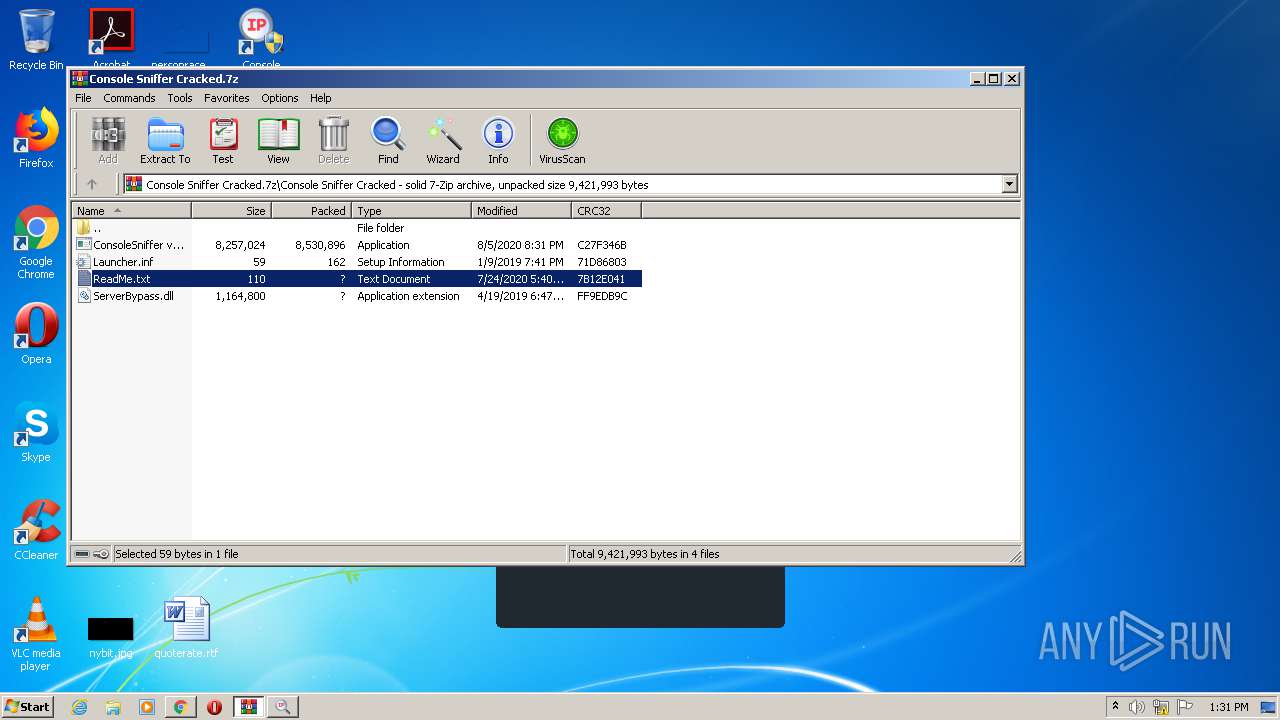
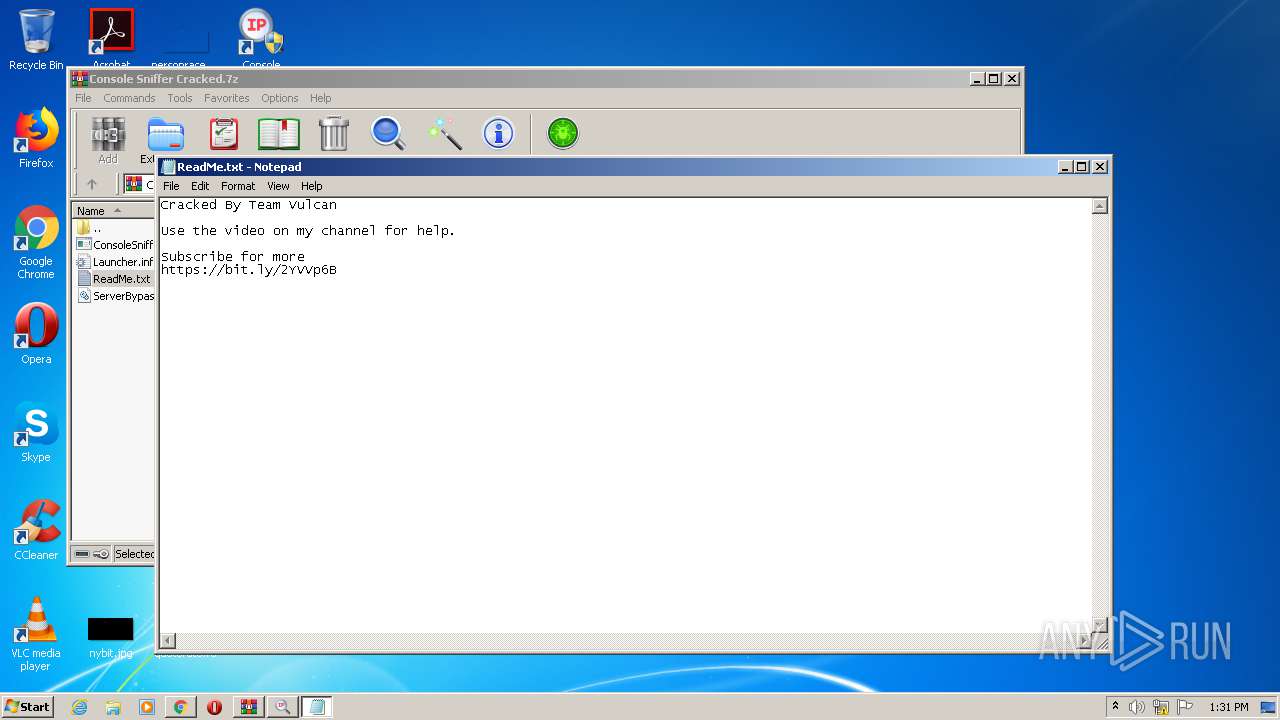
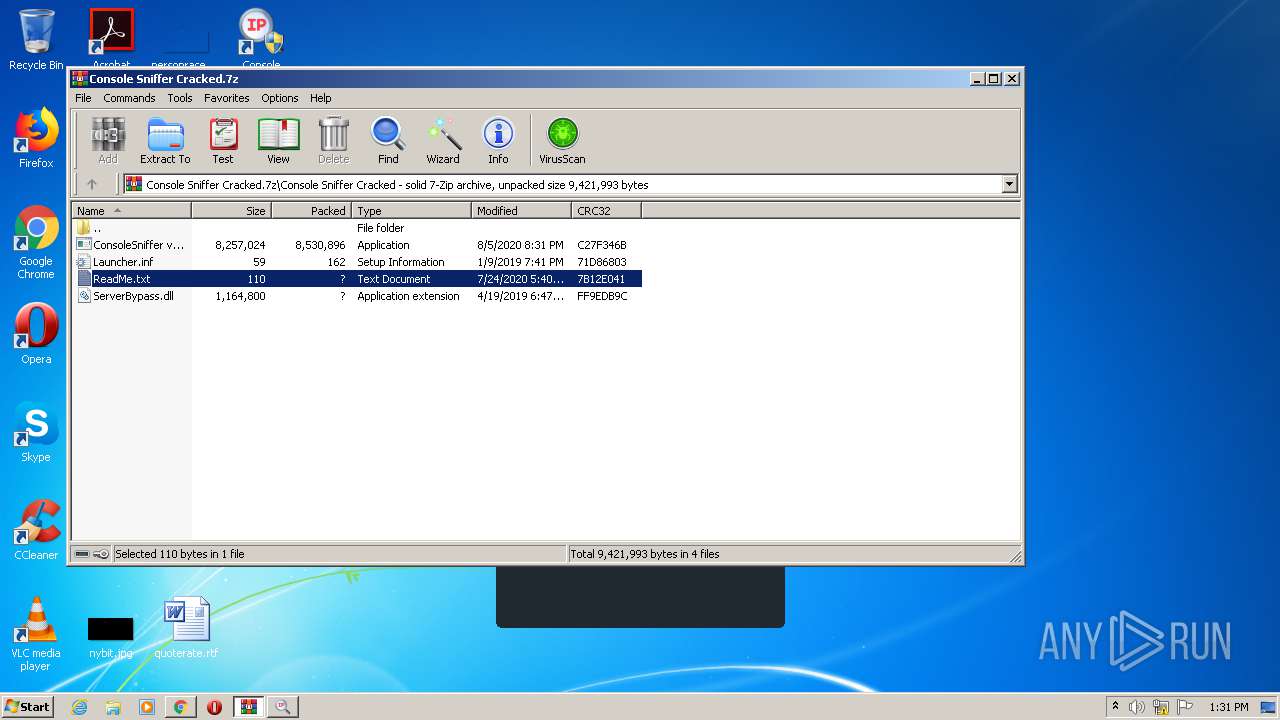
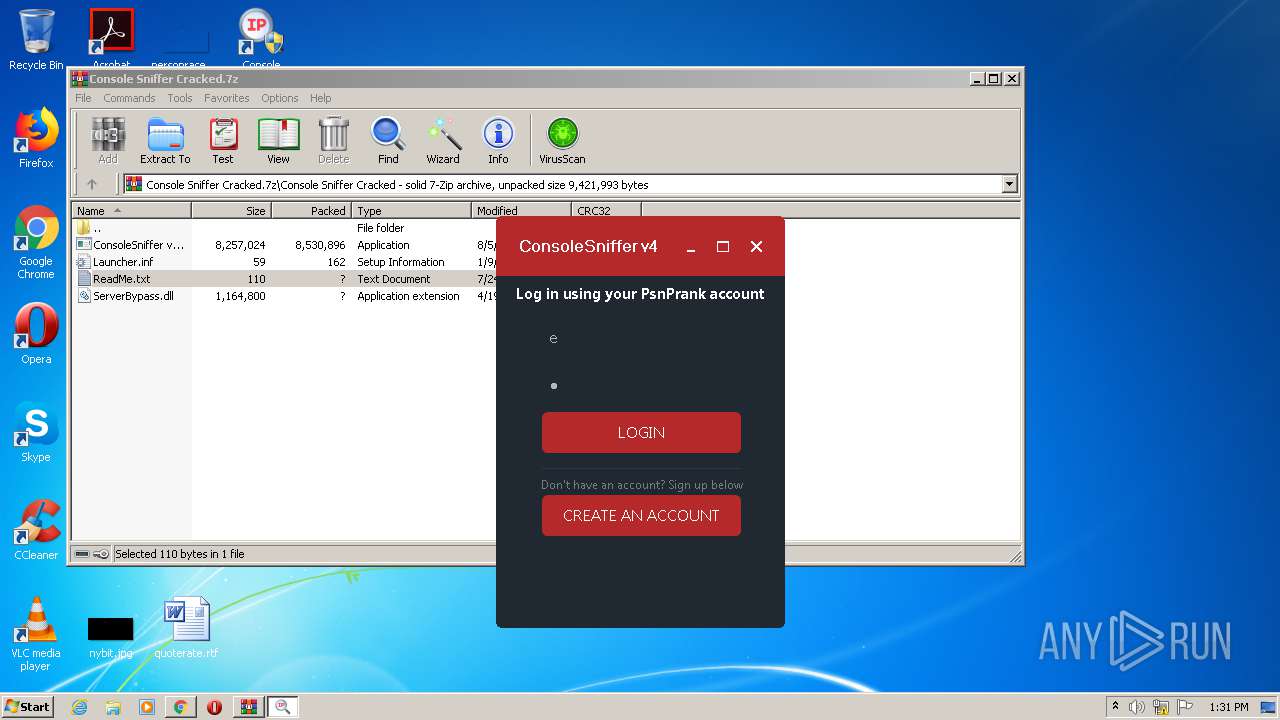
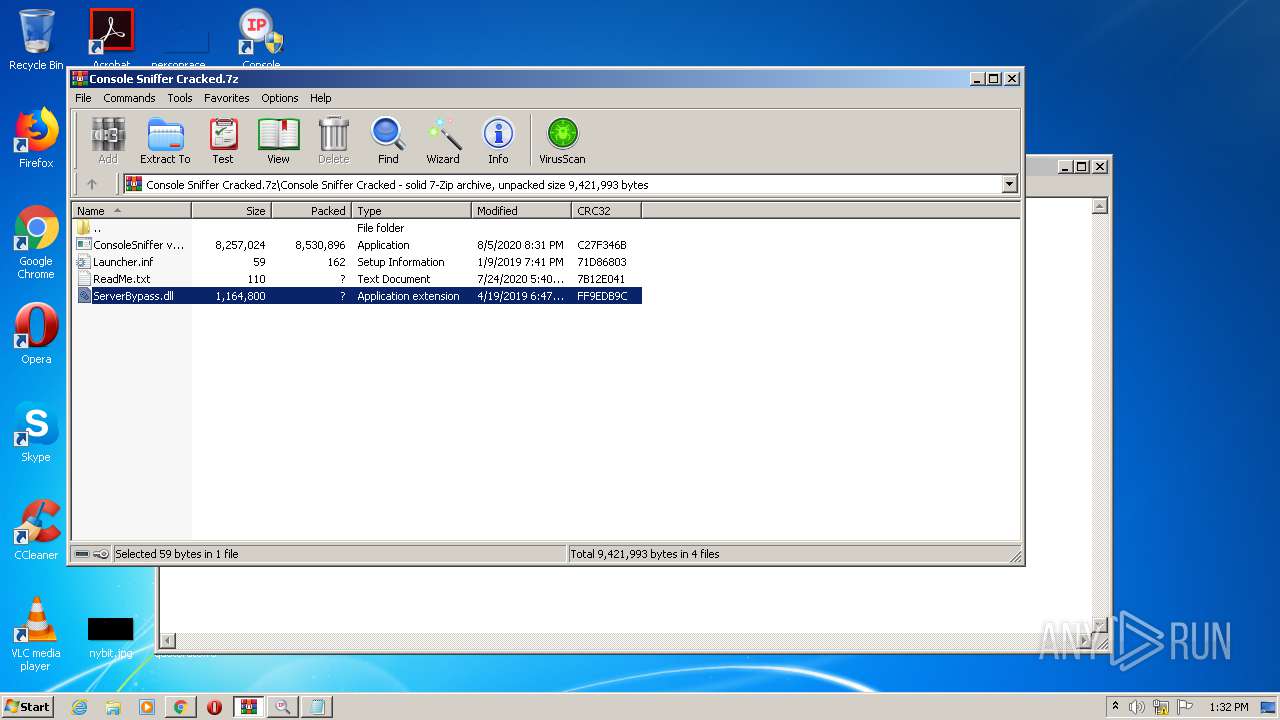
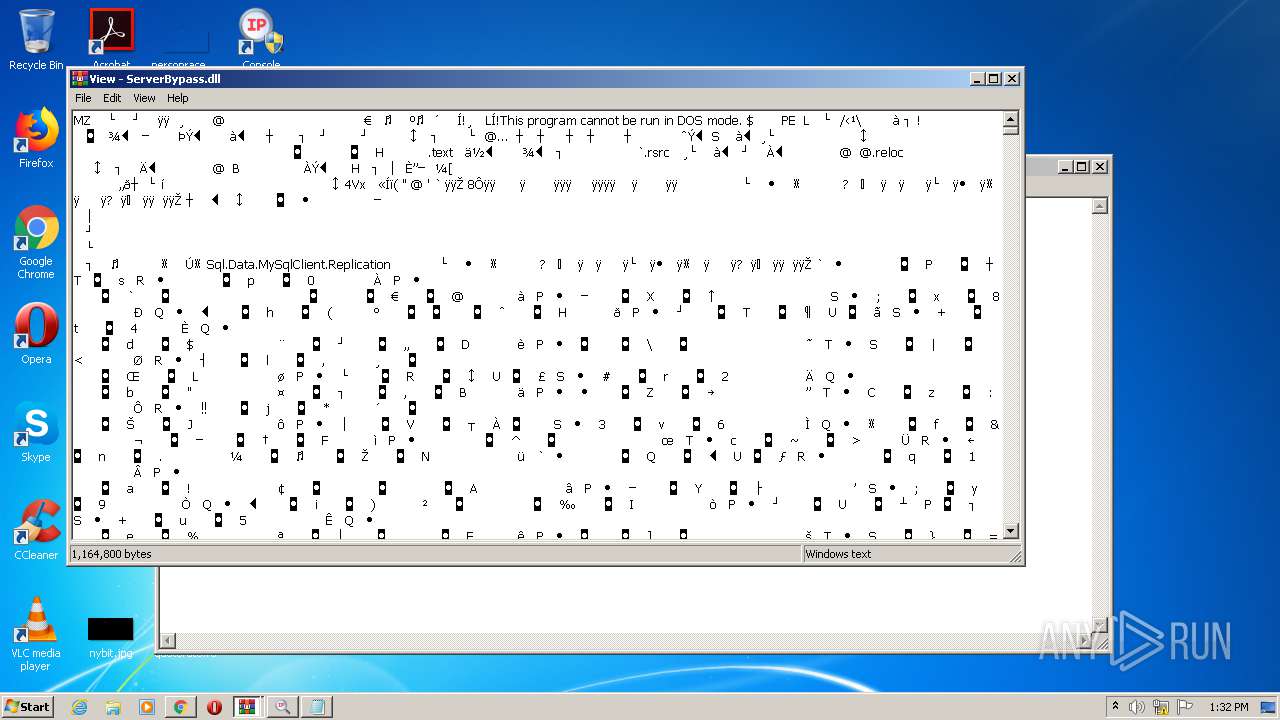
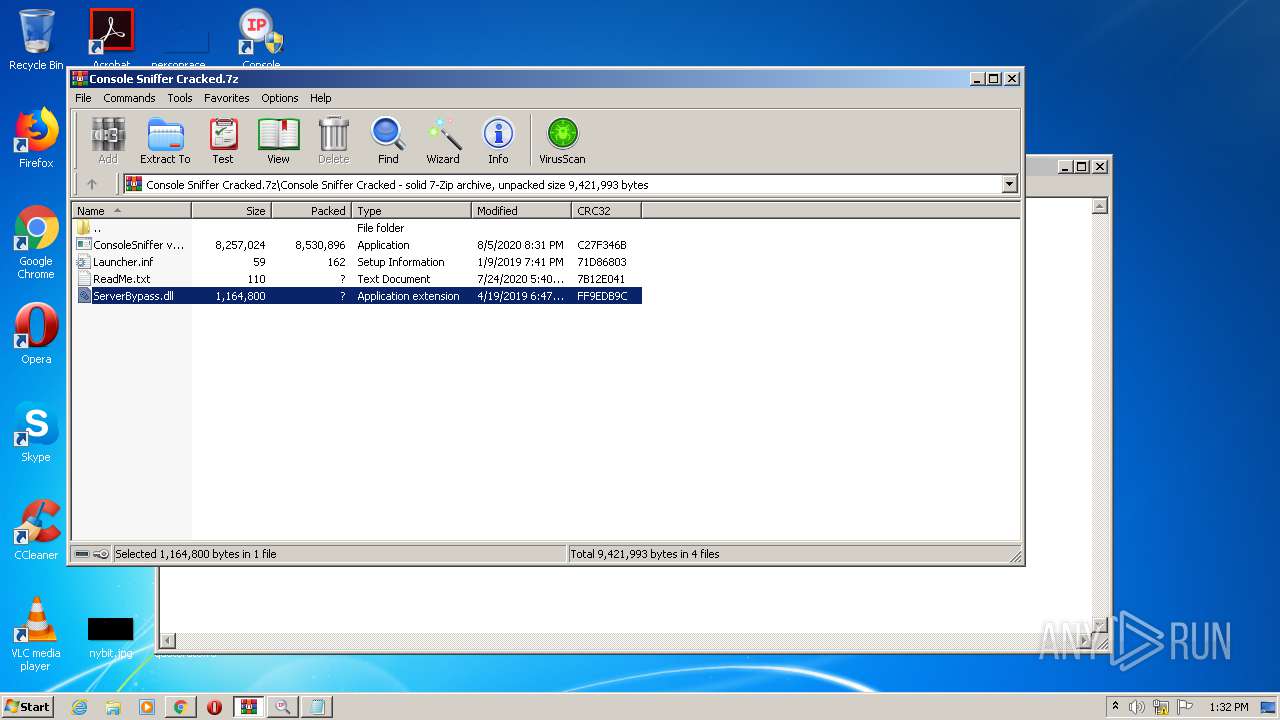
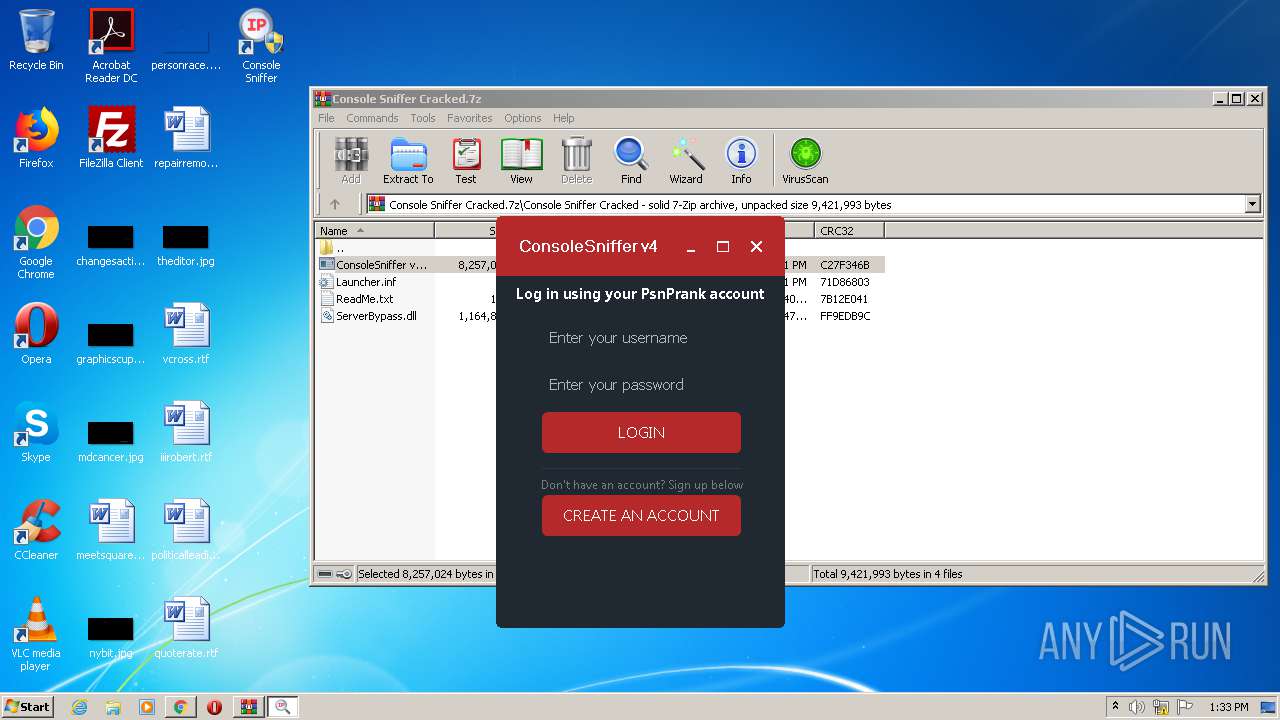
| Verdict: | Malicious activity |
| Analysis date: | September 06, 2020, 12:29:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
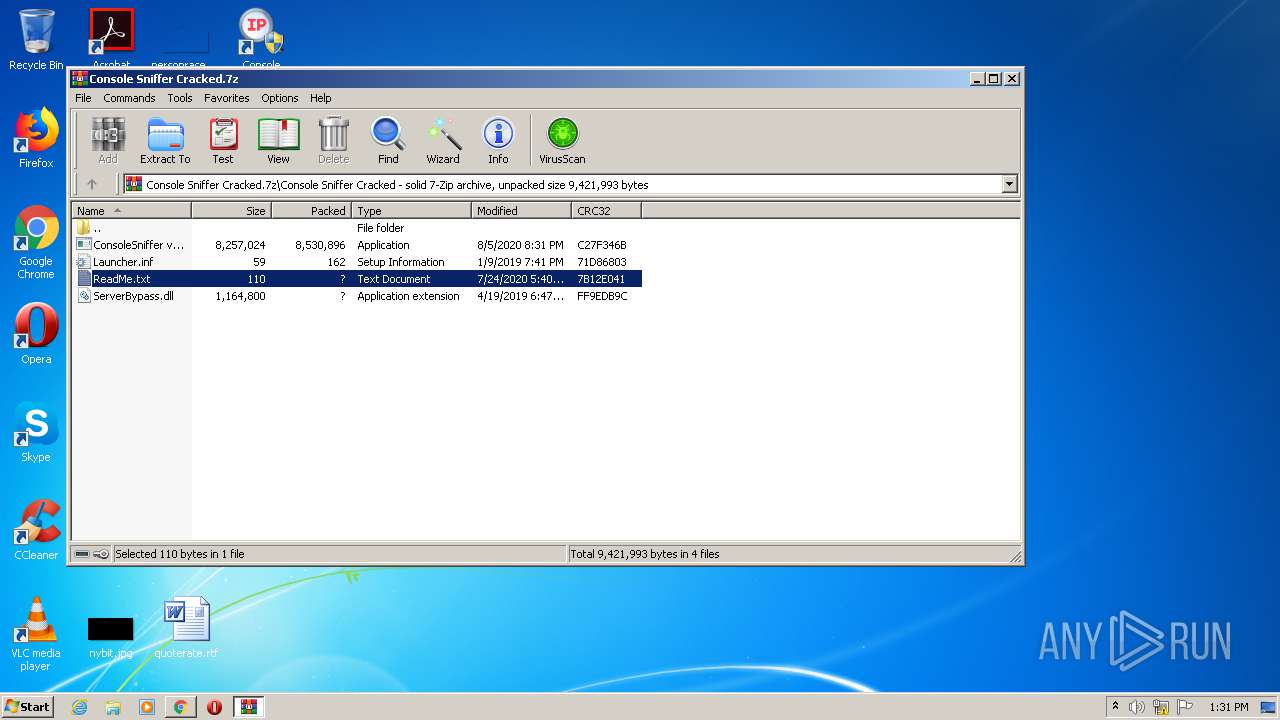
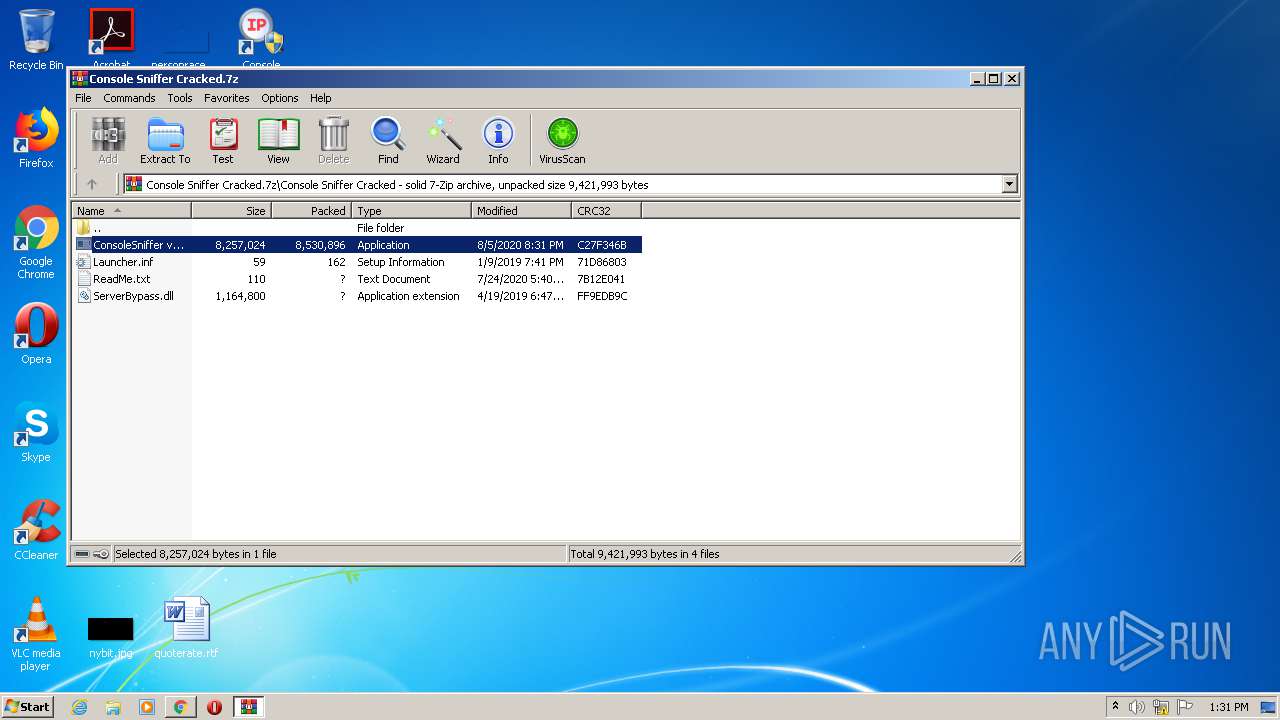
| MD5: | AFBBFB5317943005C3B477740EB20714 |
| SHA1: | A28166EE6EC1AFE63676F132041D34C65E9A7933 |
| SHA256: | 0C4D424E86DF4D2116C5DF11A6269ED3117CAFA7DD50DFAE30BC4491A49E696B |
| SSDEEP: | 3:N8X/iTyCPhc3LpzQgzX0H3npPoqn:2kGdvzX0H3npwq |
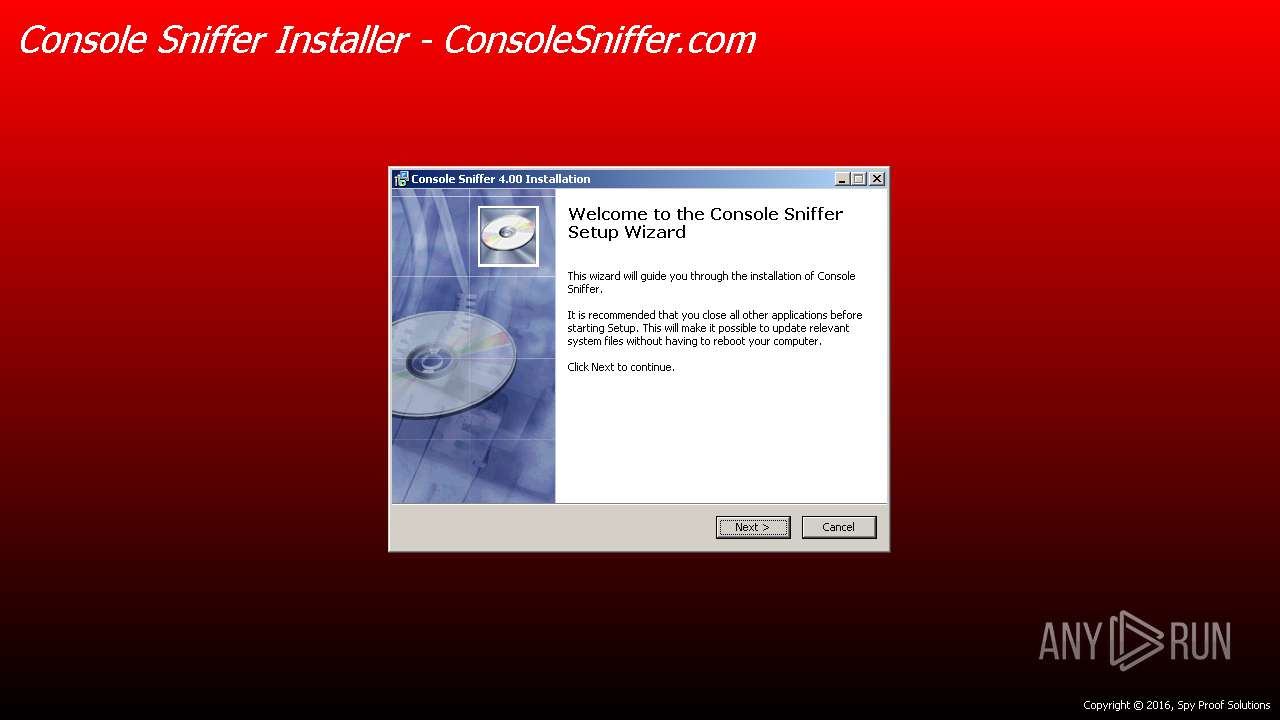
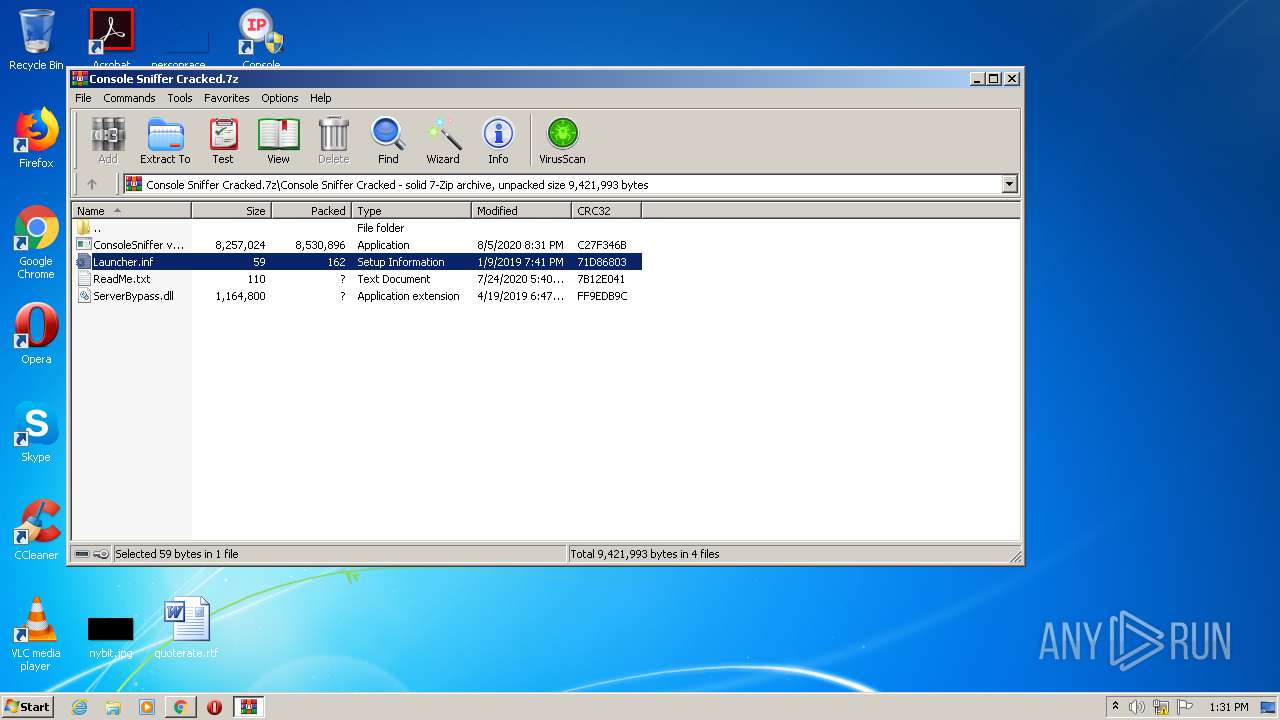
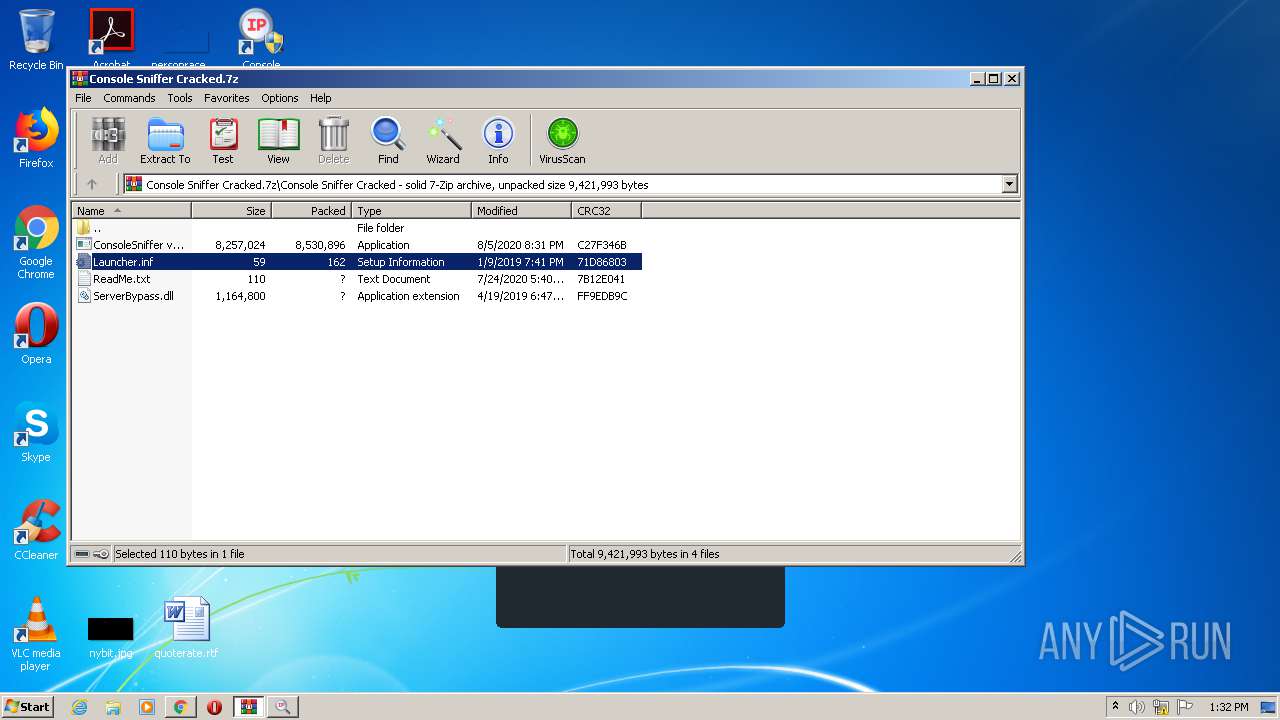
MALICIOUS
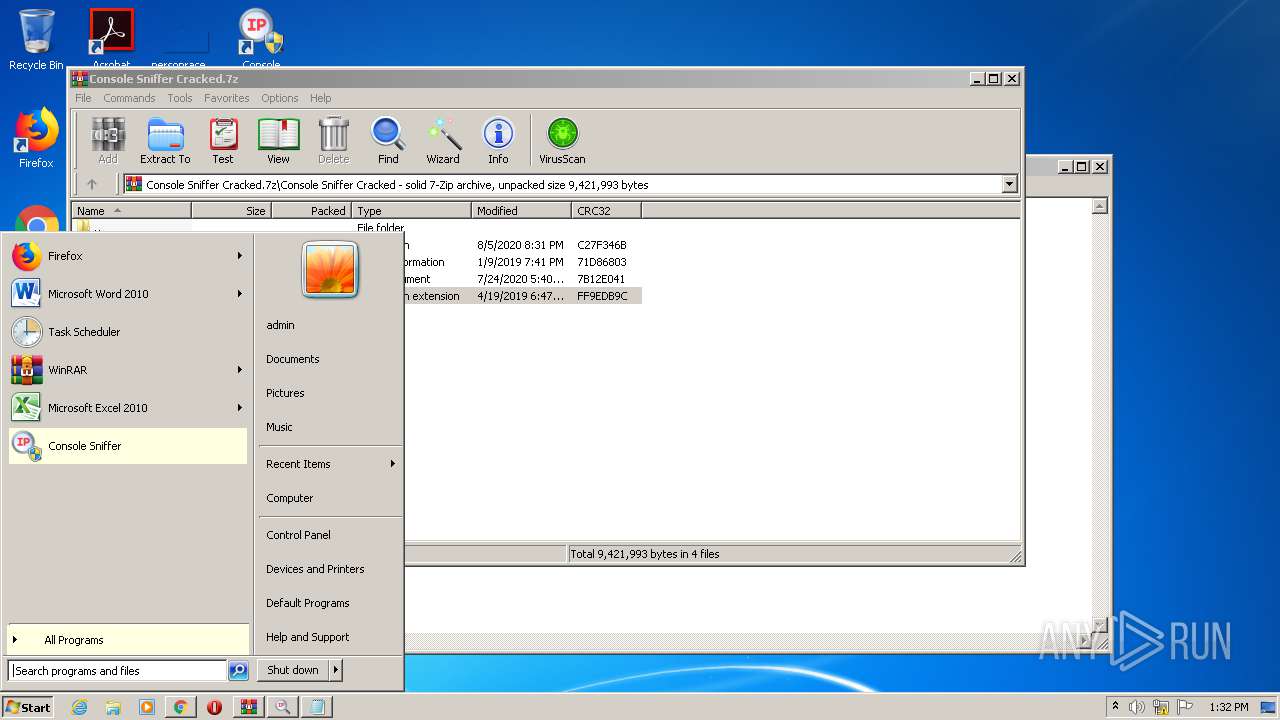
Writes to a start menu file
- ConsoleSniffer v4.1 installer.exe (PID: 2456)
- ConsoleSniffer v4.1 installer.exe (PID: 2484)
Application was dropped or rewritten from another process
- svhost.exe (PID: 1932)
- ConsoleSniffer v4.1 installer.exe (PID: 3796)
- ConsoleSniffer v4.1 installer.exe (PID: 2456)
- File.exe (PID: 292)
- vcredist_x86 - 2012 update 4.exe (PID: 2904)
- Launcher.exe (PID: 2152)
- vcredist_x86 - 2012 update 4.exe (PID: 316)
- Installer.exe (PID: 3164)
- File.exe (PID: 3820)
- ConsoleSniffer v4.1 installer.exe (PID: 2484)
- svhost.exe (PID: 692)
- ConsoleSniffer v4.1 installer.exe (PID: 3648)
- Launcher.exe (PID: 2136)
- Launcher.exe (PID: 2272)
- update.exe (PID: 3892)
- ConsoleSniffer.exe (PID: 3540)
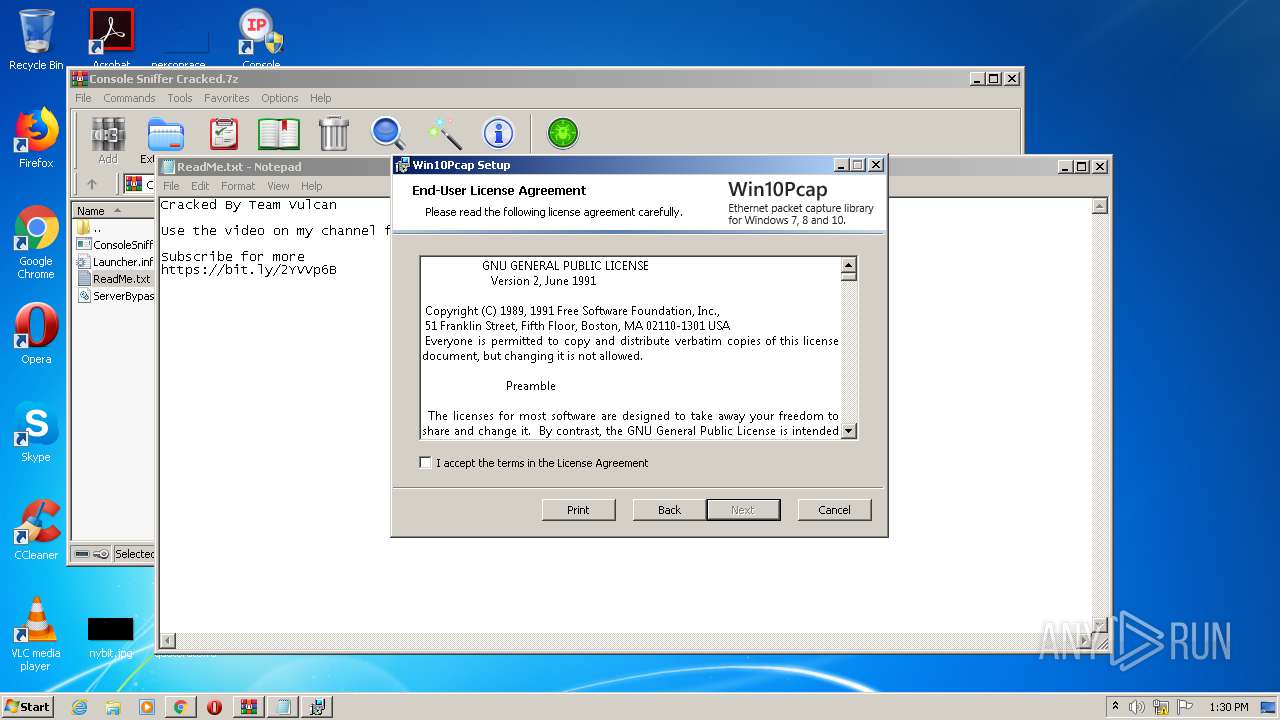
Changes settings of System certificates
- msiexec.exe (PID: 1800)
Changes the autorun value in the registry
- vcredist_x86 - 2012 update 4.exe (PID: 2904)
Loads dropped or rewritten executable
- Launcher.exe (PID: 2152)
- Launcher.exe (PID: 2272)
- update.exe (PID: 3892)
- ConsoleSniffer.exe (PID: 3540)
SUSPICIOUS
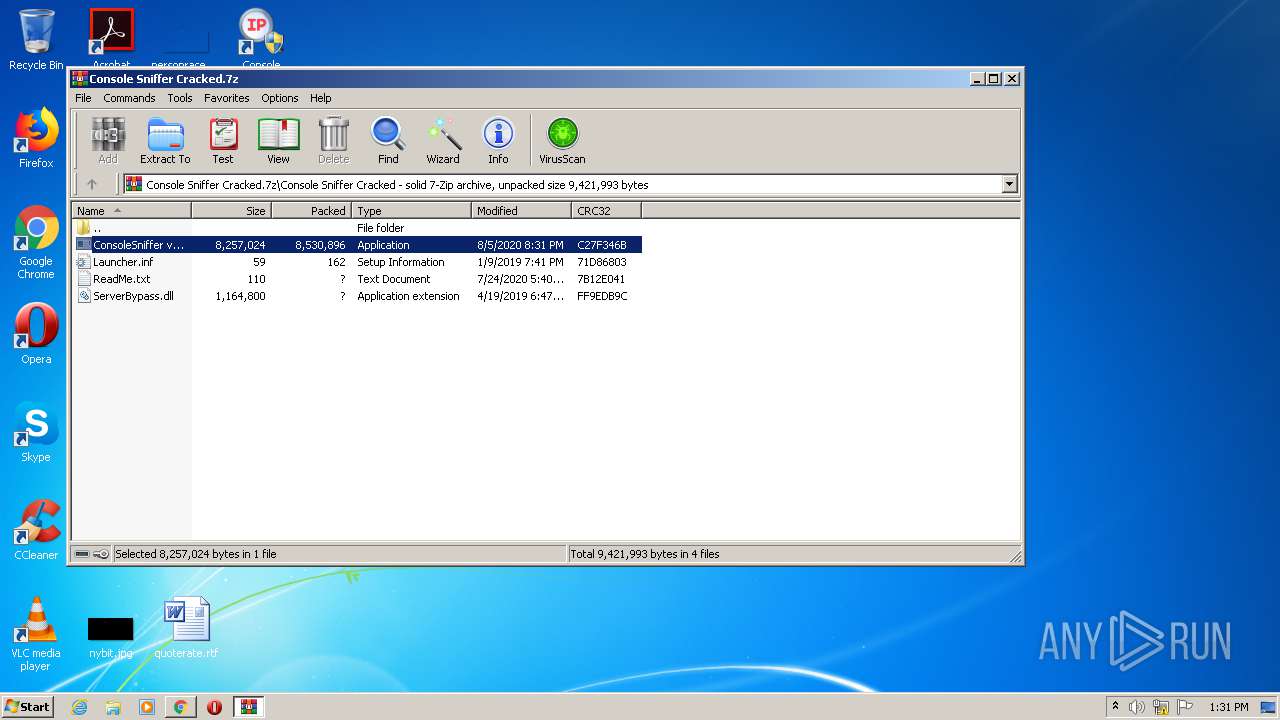
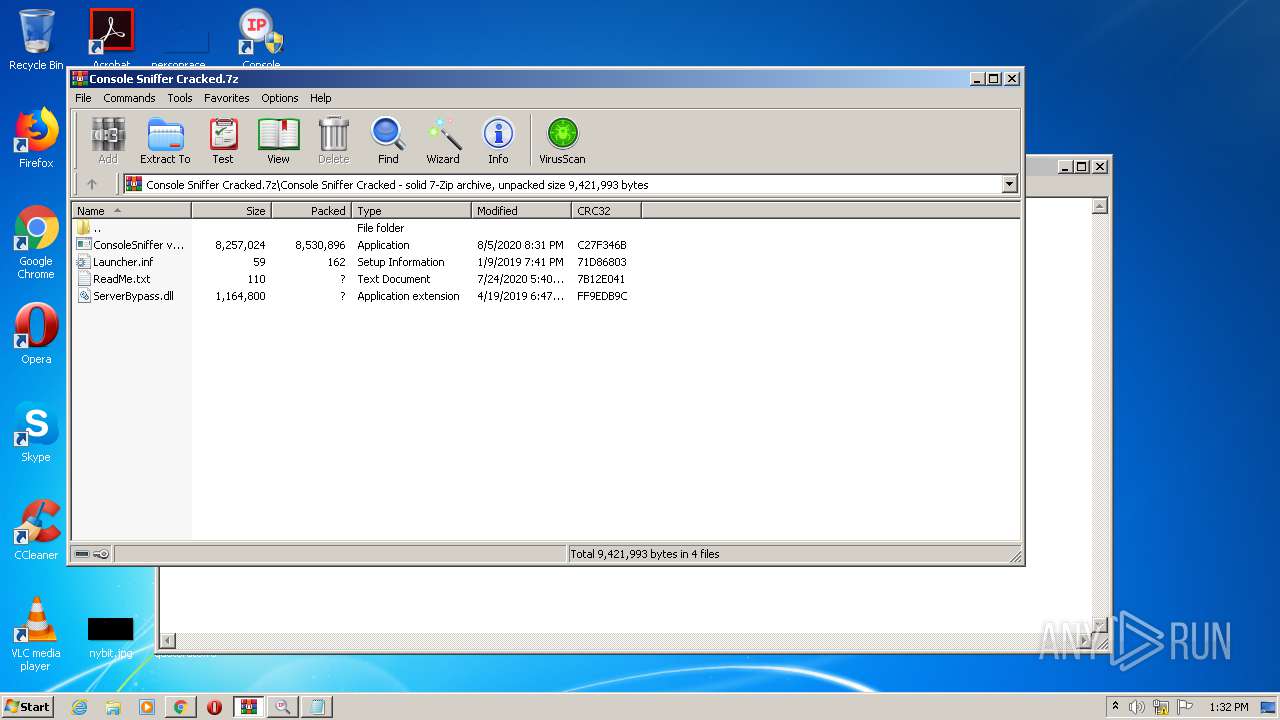
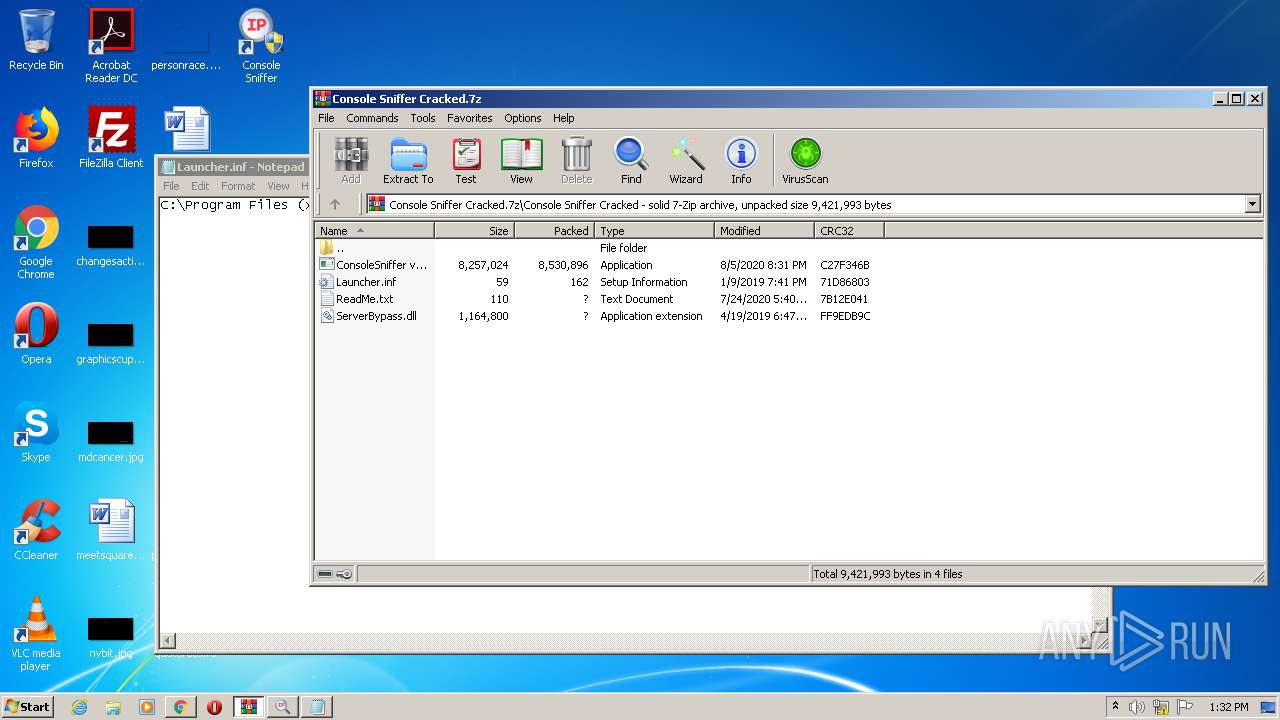
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3424)
- ConsoleSniffer v4.1 installer.exe (PID: 2456)
- File.exe (PID: 292)
- vcredist_x86 - 2012 update 4.exe (PID: 316)
- cmd.exe (PID: 296)
- vcredist_x86 - 2012 update 4.exe (PID: 2904)
- Installer.exe (PID: 3164)
- DrvInst.exe (PID: 1796)
- ConsoleSniffer v4.1 installer.exe (PID: 2484)
- cmd.exe (PID: 2360)
Starts CMD.EXE for commands execution
- ConsoleSniffer v4.1 installer.exe (PID: 2456)
- ConsoleSniffer v4.1 installer.exe (PID: 2484)
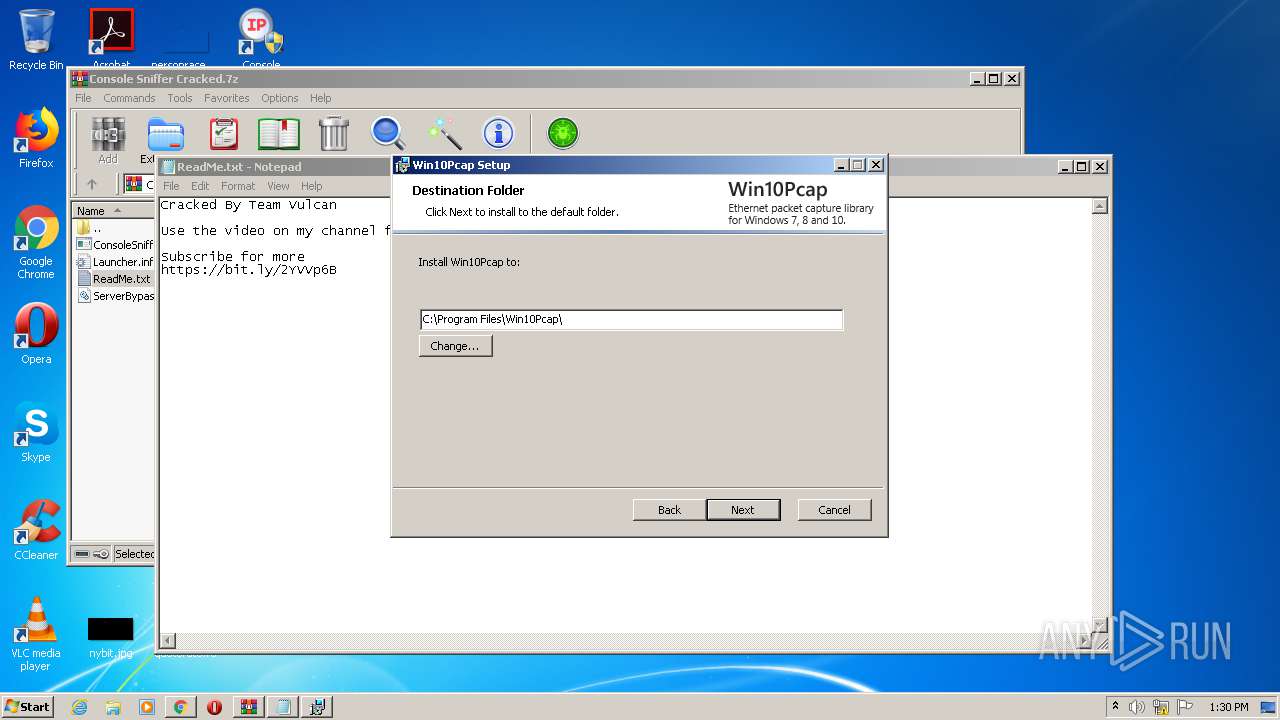
Creates files in the program directory
- File.exe (PID: 292)
- vcredist_x86 - 2012 update 4.exe (PID: 2904)
Application launched itself
- vcredist_x86 - 2012 update 4.exe (PID: 2904)
Creates a software uninstall entry
- File.exe (PID: 292)
- vcredist_x86 - 2012 update 4.exe (PID: 2904)
Creates files in the user directory
- File.exe (PID: 292)
- ConsoleSniffer v4.1 installer.exe (PID: 2456)
Searches for installed software
- vcredist_x86 - 2012 update 4.exe (PID: 316)
- vcredist_x86 - 2012 update 4.exe (PID: 2904)
Adds / modifies Windows certificates
- msiexec.exe (PID: 1800)
Executed via COM
- DrvInst.exe (PID: 1796)
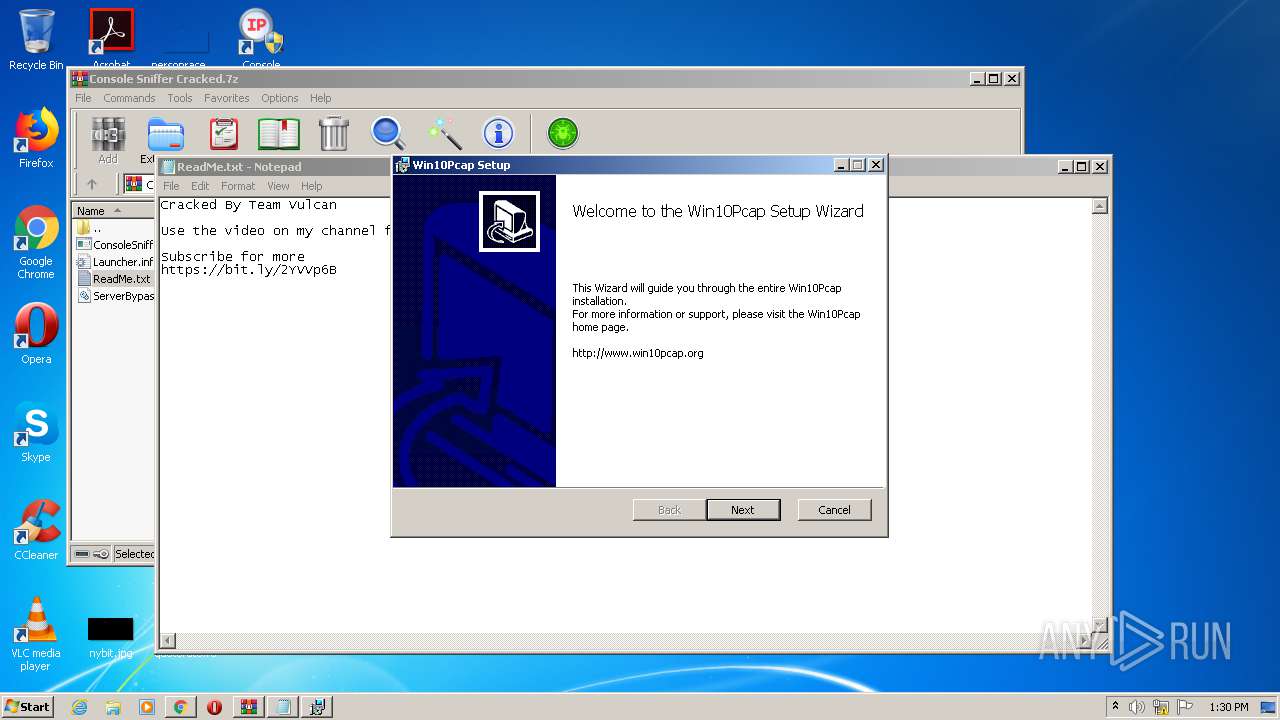
Starts Microsoft Installer
- Launcher.exe (PID: 2152)
Creates files in the Windows directory
- DrvInst.exe (PID: 1796)
- Installer.exe (PID: 3164)
Removes files from Windows directory
- DrvInst.exe (PID: 1796)
- Installer.exe (PID: 3164)
Creates files in the driver directory
- DrvInst.exe (PID: 1796)
- Installer.exe (PID: 3164)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 1796)
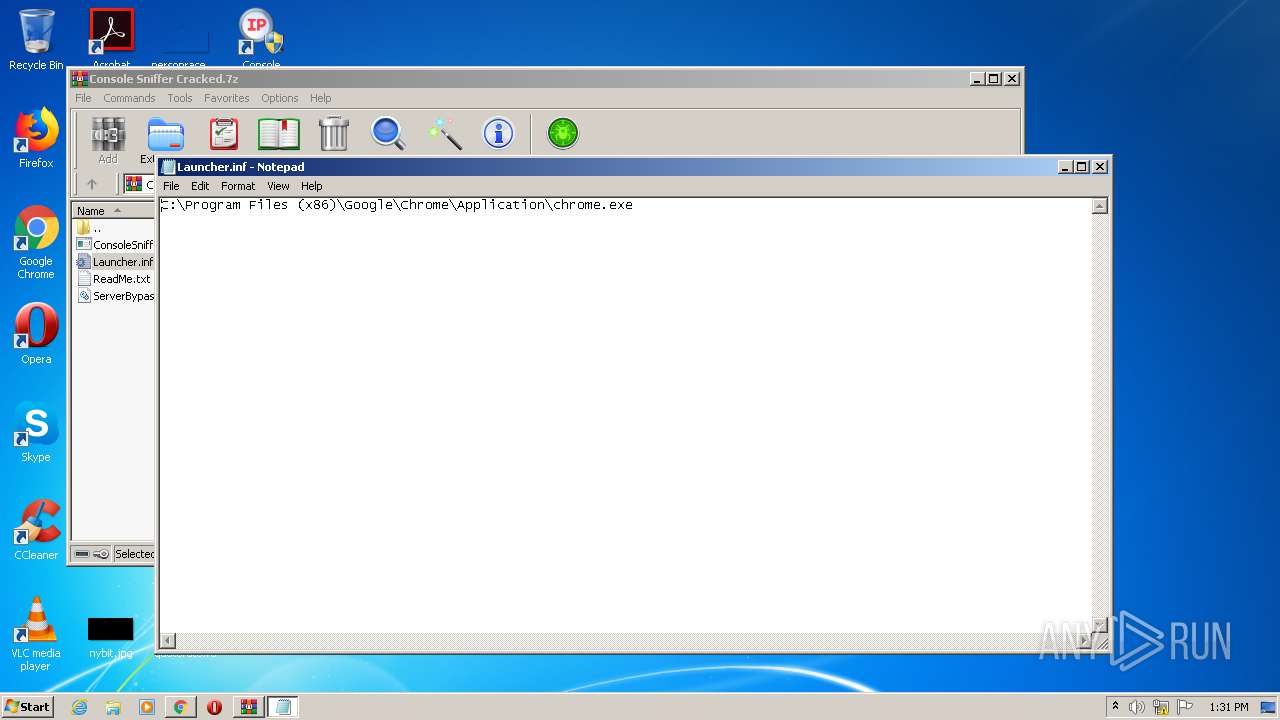
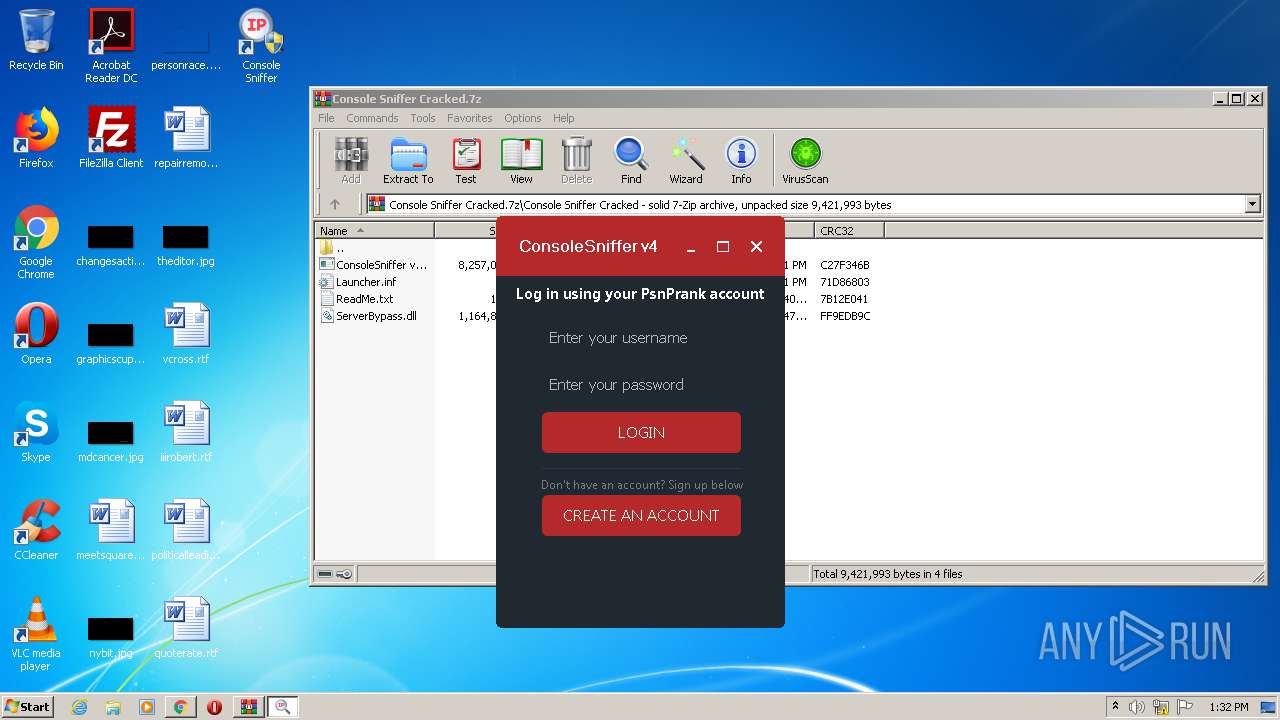
Starts Internet Explorer
- ConsoleSniffer.exe (PID: 3540)
INFO
Reads the hosts file
- chrome.exe (PID: 3900)
- chrome.exe (PID: 4044)
Reads settings of System Certificates
- chrome.exe (PID: 4044)
- iexplore.exe (PID: 3144)
Application launched itself
- chrome.exe (PID: 3900)
- iexplore.exe (PID: 3144)
Changes settings of System certificates
- DrvInst.exe (PID: 1796)
- iexplore.exe (PID: 3144)
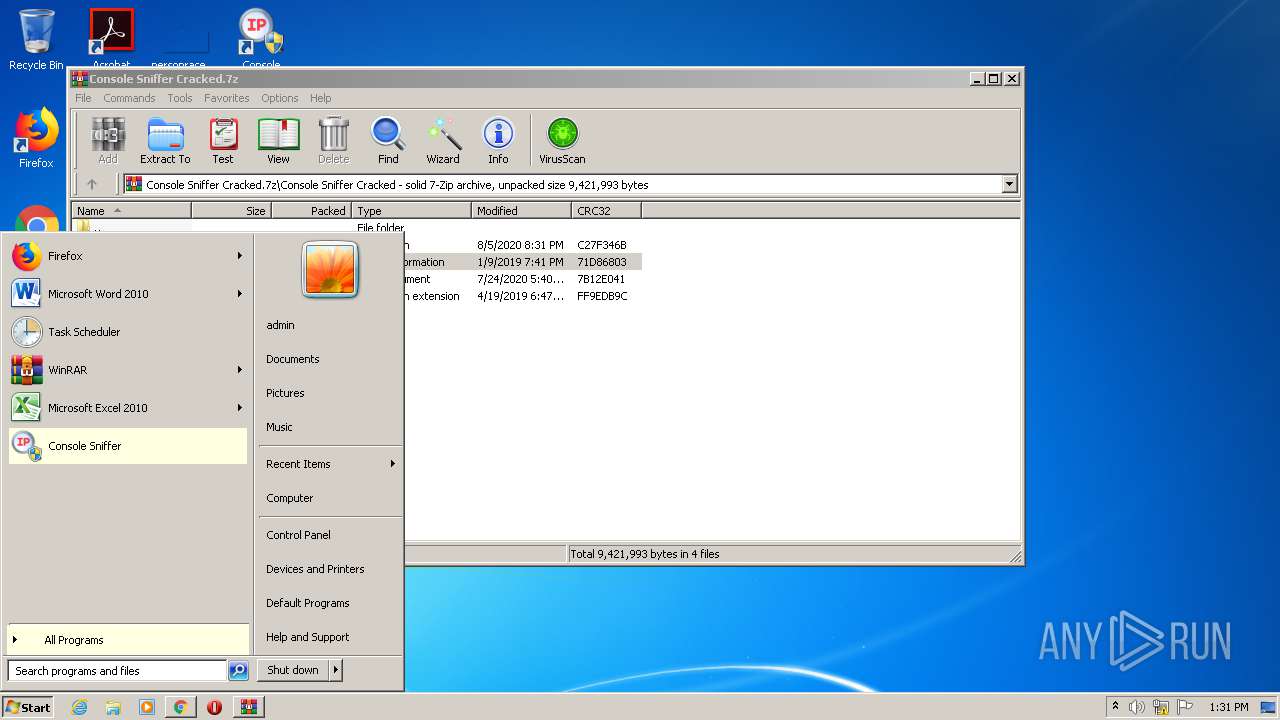
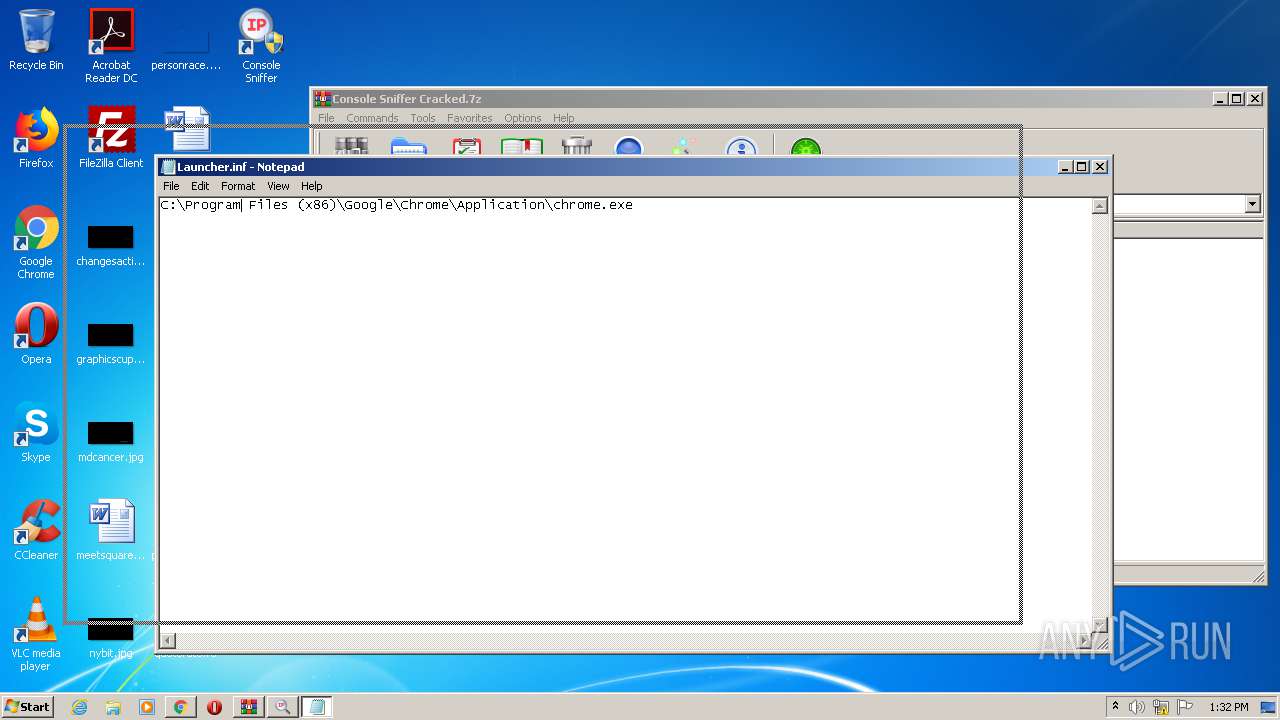
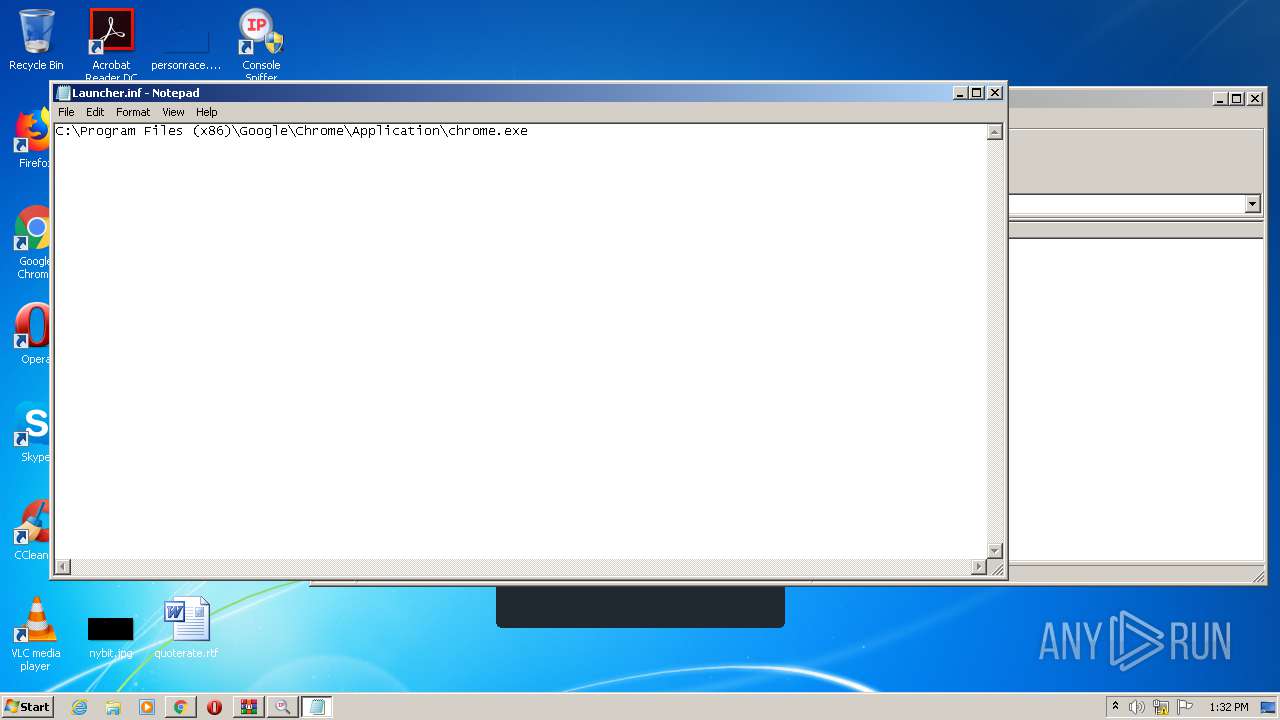
Manual execution by user
- Launcher.exe (PID: 2136)
- Launcher.exe (PID: 2272)
Reads Internet Cache Settings
- iexplore.exe (PID: 3144)
- iexplore.exe (PID: 2968)
Reads internet explorer settings
- iexplore.exe (PID: 2968)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3144)
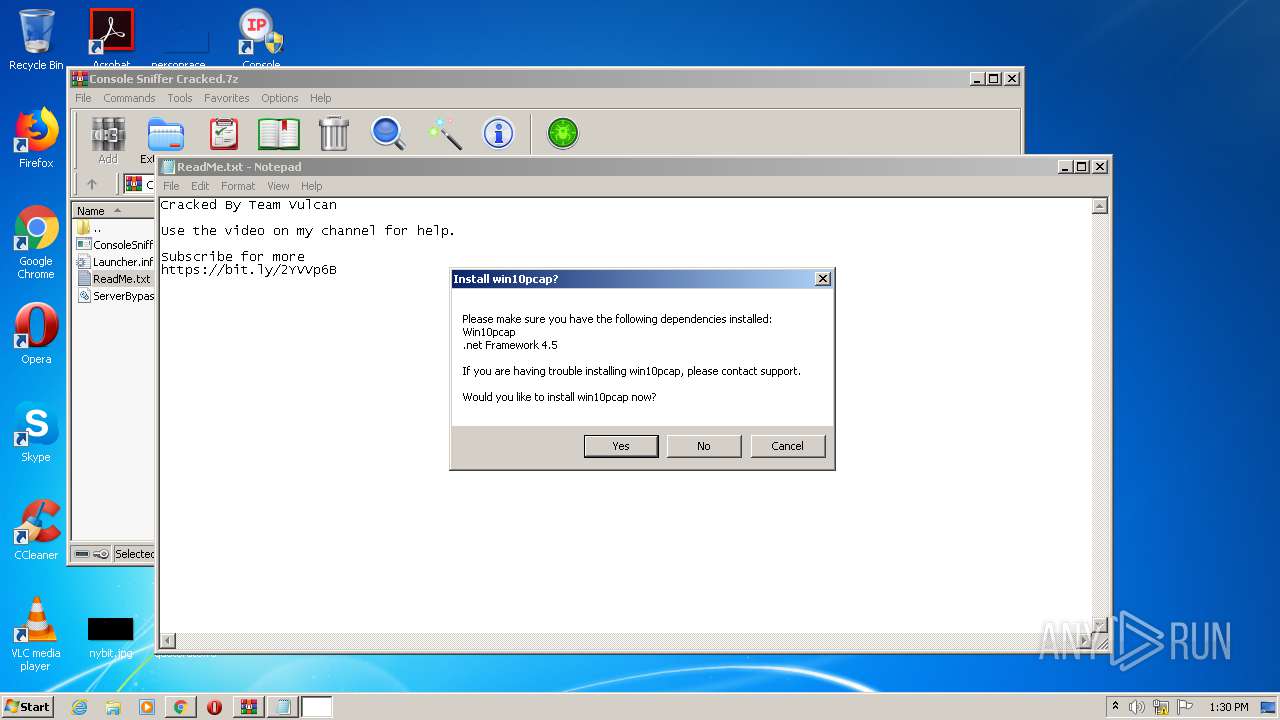
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2968)
Creates files in the user directory
- iexplore.exe (PID: 2968)
Changes internet zones settings
- iexplore.exe (PID: 3144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
106
Monitored processes
46
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Users\admin\AppData\Local\Temp\File.exe" | C:\Users\admin\AppData\Local\Temp\File.exe | ConsoleSniffer v4.1 installer.exe | ||||||||||||
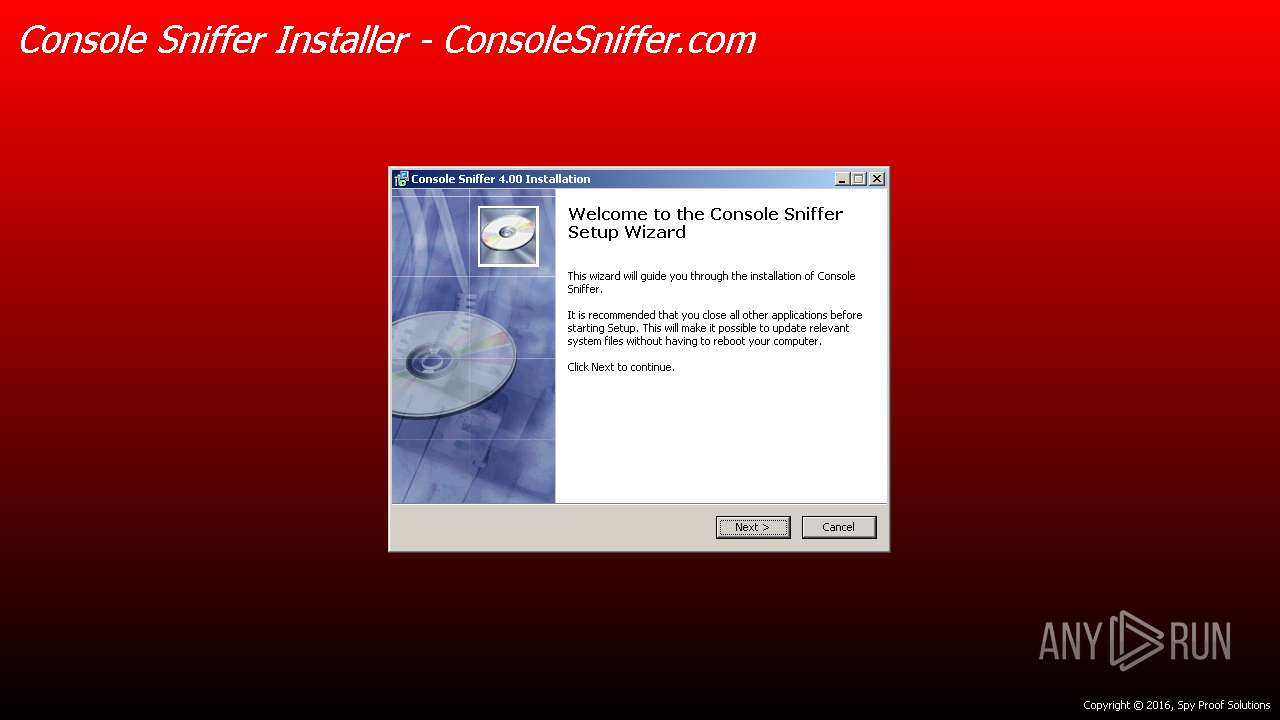
User: admin Company: Spy Proof Solutions Integrity Level: HIGH Description: Console Sniffer 4.00 Installation Exit code: 0 Version: 4.00 Modules
| |||||||||||||||
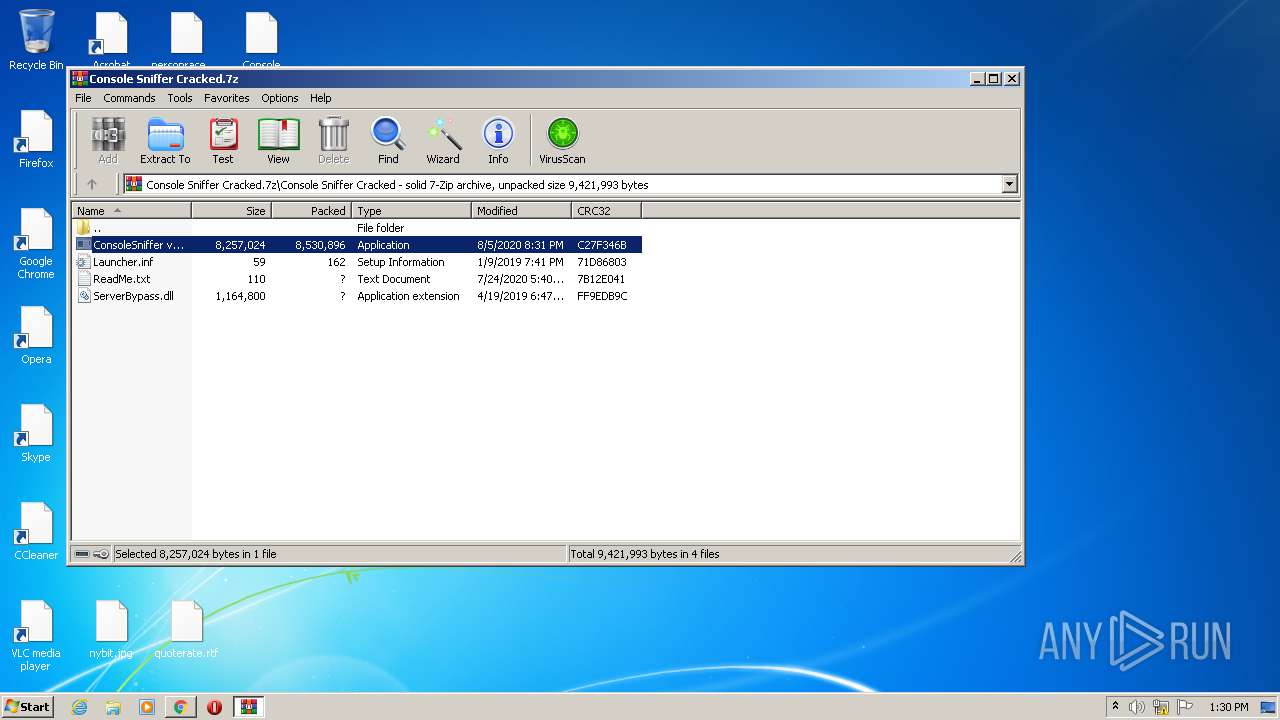
| 296 | "C:\Windows\System32\cmd.exe" /c copy "C:/Users/admin/AppData/Local/Temp/Rar$EXa3424.23866/Console Sniffer Cracked/ConsoleSniffer v4.1 installer.exe" "%temp%\FolderN\name.exe" /Y | C:\Windows\System32\cmd.exe | ConsoleSniffer v4.1 installer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
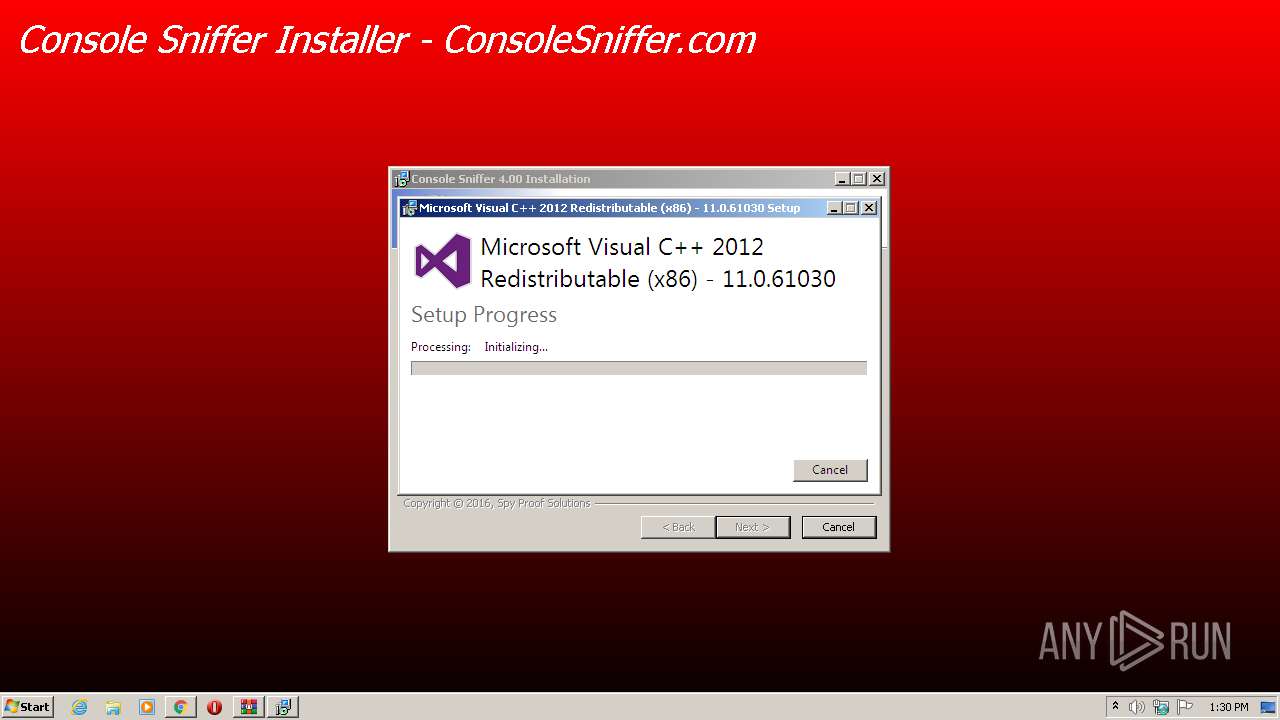
| 316 | "C:\Program Files\Spy Proof Solutions\Console Sniffer\vcredist_x86 - 2012 update 4.exe" /passive /norestart -burn.unelevated BurnPipe.{98E2A517-9975-477C-9939-68140B52737C} {5371BD5C-46B1-4EE9-B788-900A78D92F93} 2904 | C:\Program Files\Spy Proof Solutions\Console Sniffer\vcredist_x86 - 2012 update 4.exe | vcredist_x86 - 2012 update 4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 692 | "C:\Users\admin\AppData\Local\Temp\svhost.exe" | C:\Users\admin\AppData\Local\Temp\svhost.exe | — | ConsoleSniffer v4.1 installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
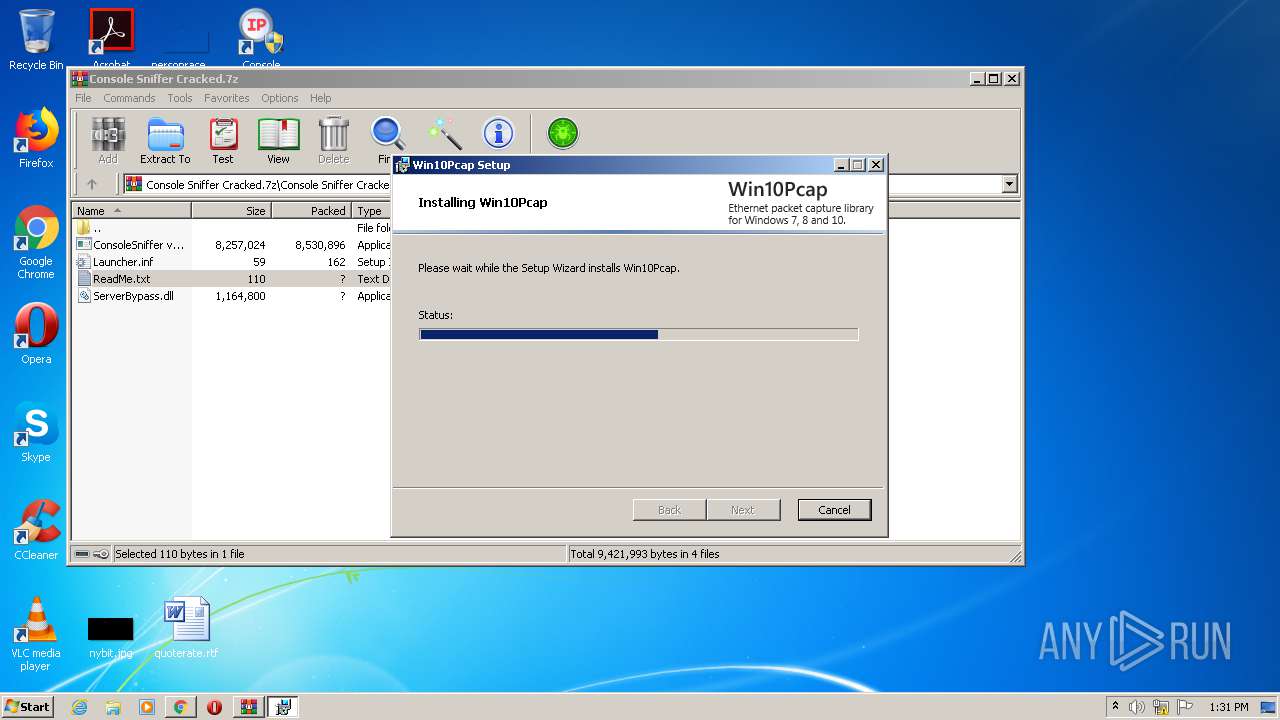
| 1796 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{6f06219d-0448-0c6b-76f8-033d8e14bb72}\Win10Pcap.inf" "0" "631592c13" "00000300" "WinSta0\Default" "000005BC" "208" "C:\Program Files\Win10Pcap\Win32\drivers\win78" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1800 | "C:\Windows\System32\msiexec.exe" /i "C:\Program Files\Spy Proof Solutions\Console Sniffer\Win10Pcap-v10.2-5002.msi" | C:\Windows\System32\msiexec.exe | — | Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,5107485057732982321,8816197908670736681,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9078115835192969461 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1888 | timeout /t 300 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1932 | "C:\Users\admin\AppData\Local\Temp\svhost.exe" | C:\Users\admin\AppData\Local\Temp\svhost.exe | ConsoleSniffer v4.1 installer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
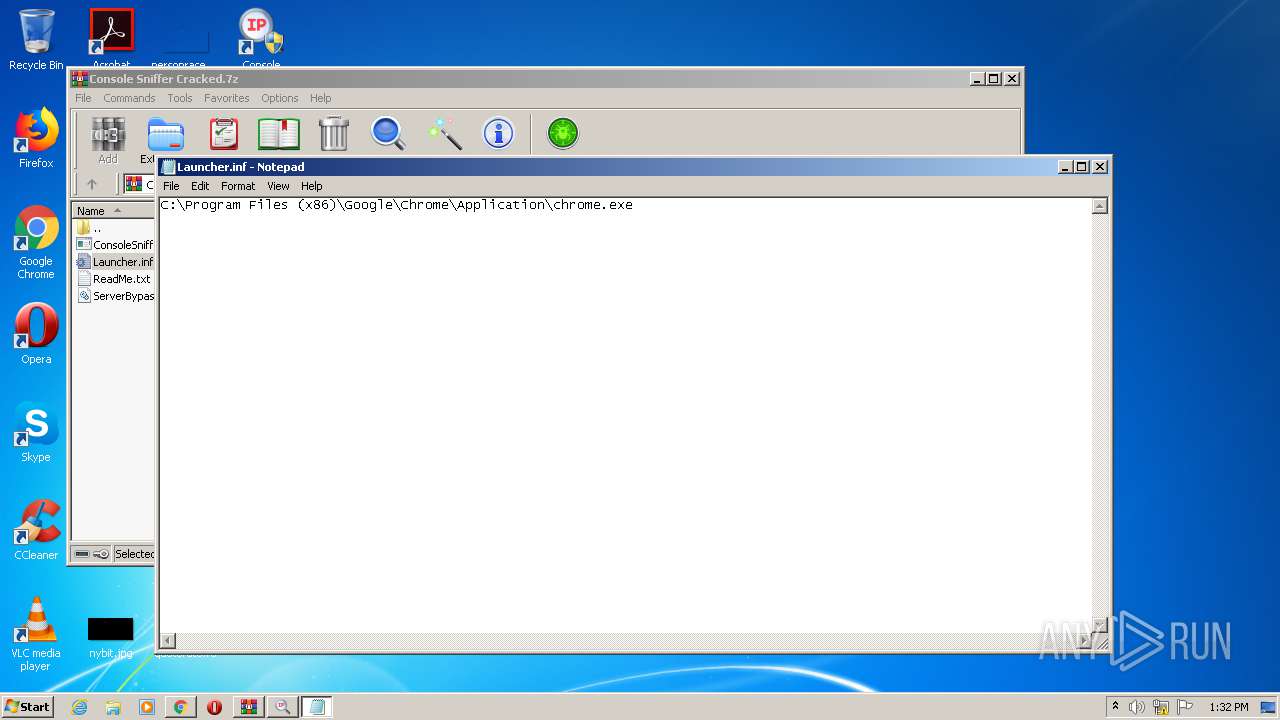
| 2136 | "C:\Program Files\Spy Proof Solutions\Console Sniffer\Launcher.exe" | C:\Program Files\Spy Proof Solutions\Console Sniffer\Launcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Launcher Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
4 302
Read events
3 836
Write events
450
Delete events
16
Modification events
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3900-13243868975574250 |
Value: 259 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
39
Suspicious files
124
Text files
259
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\16fa2e68-7155-4ce5-a134-ccef6a8df0eb.tmp | — | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RFe2660.TMP | — | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe25b4.TMP | text | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFe2640.TMP | text | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe27e6.TMP | — | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe25b4.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
78
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
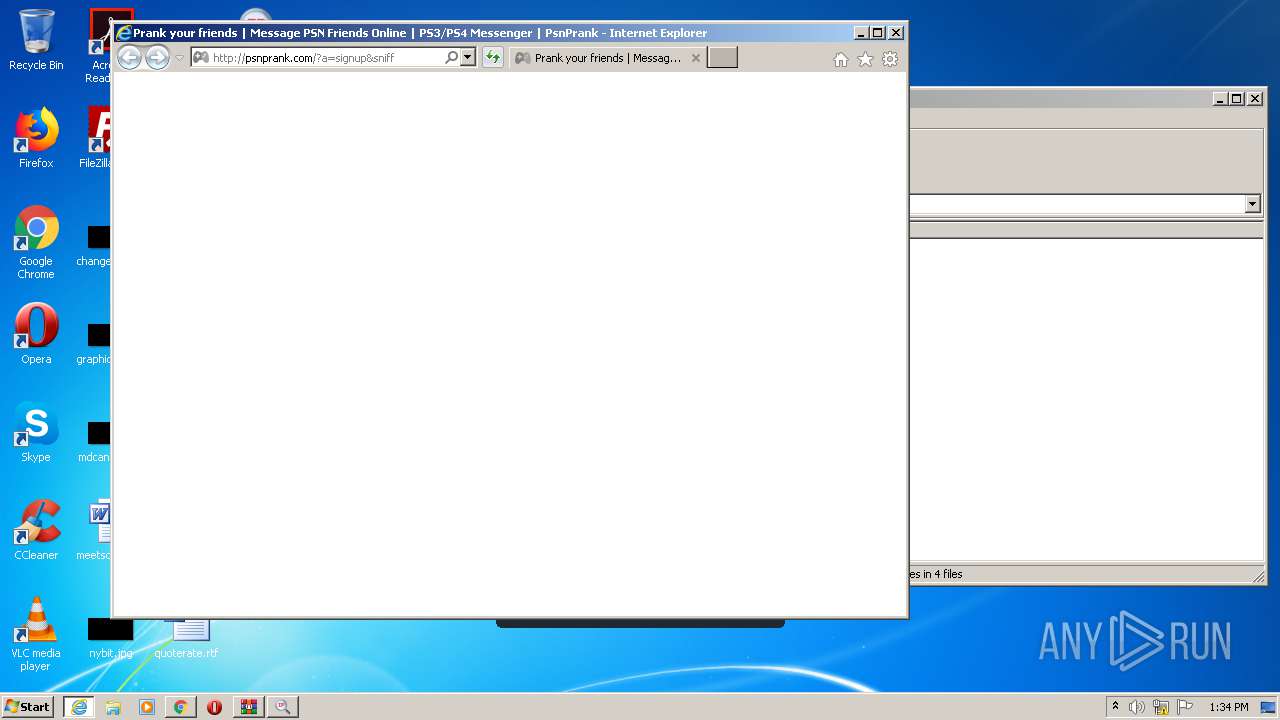
2968 | iexplore.exe | GET | — | 74.91.122.37:80 | http://psnprank.com/frontend/scripts/md5.js | US | — | — | suspicious |
2968 | iexplore.exe | GET | — | 74.91.122.37:80 | http://psnprank.com/frontend/styles/images/paypal-big.png | US | — | — | suspicious |
2968 | iexplore.exe | GET | — | 74.91.122.37:80 | http://psnprank.com/frontend/styles/madebyobamasu.css?madebyobamasu=334 | US | — | — | suspicious |
2968 | iexplore.exe | GET | — | 74.91.122.37:80 | http://psnprank.com/frontend/scripts/jquery.color.js | US | — | — | suspicious |
2968 | iexplore.exe | GET | — | 74.91.122.37:80 | http://psnprank.com/frontend/styles/images/btc-white.png | US | — | — | suspicious |
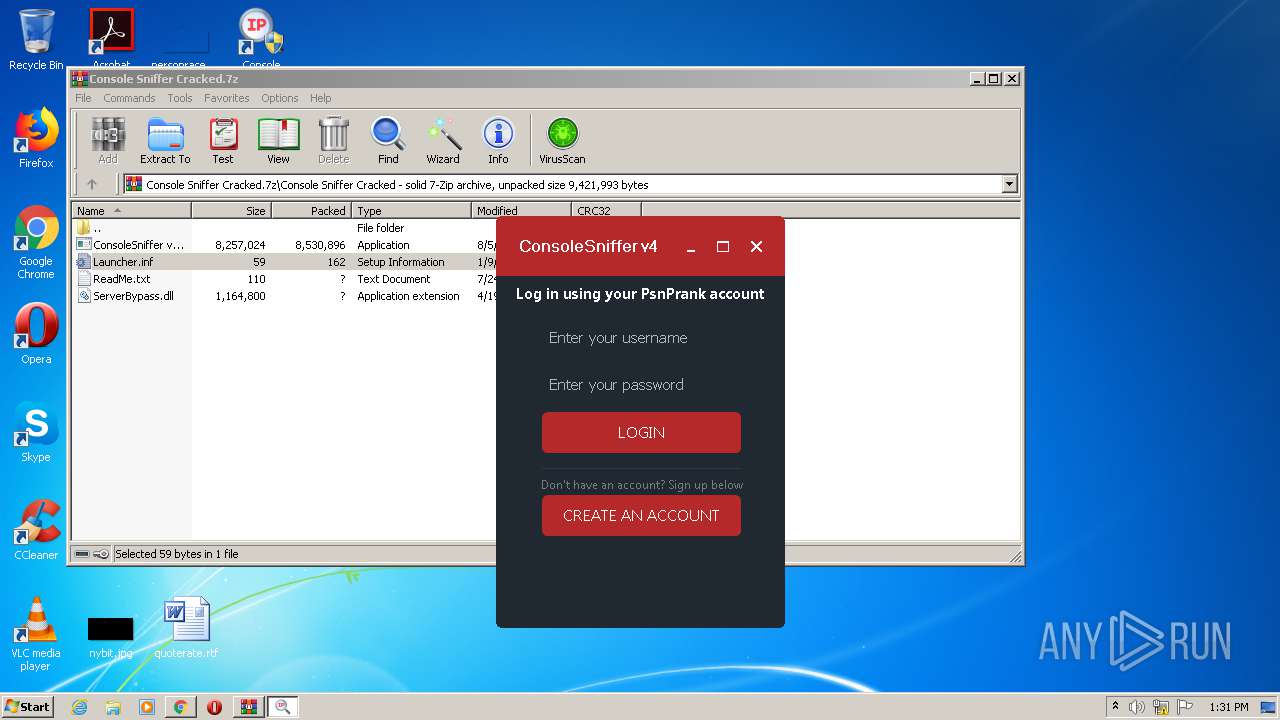
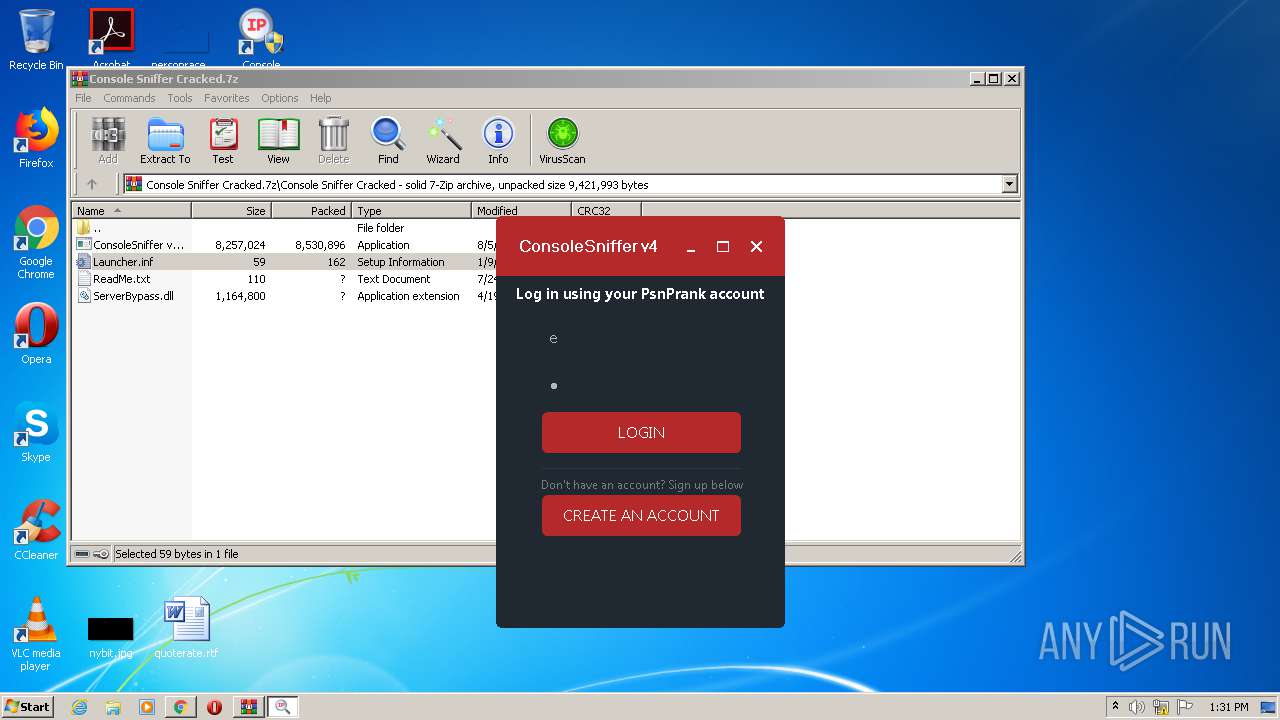
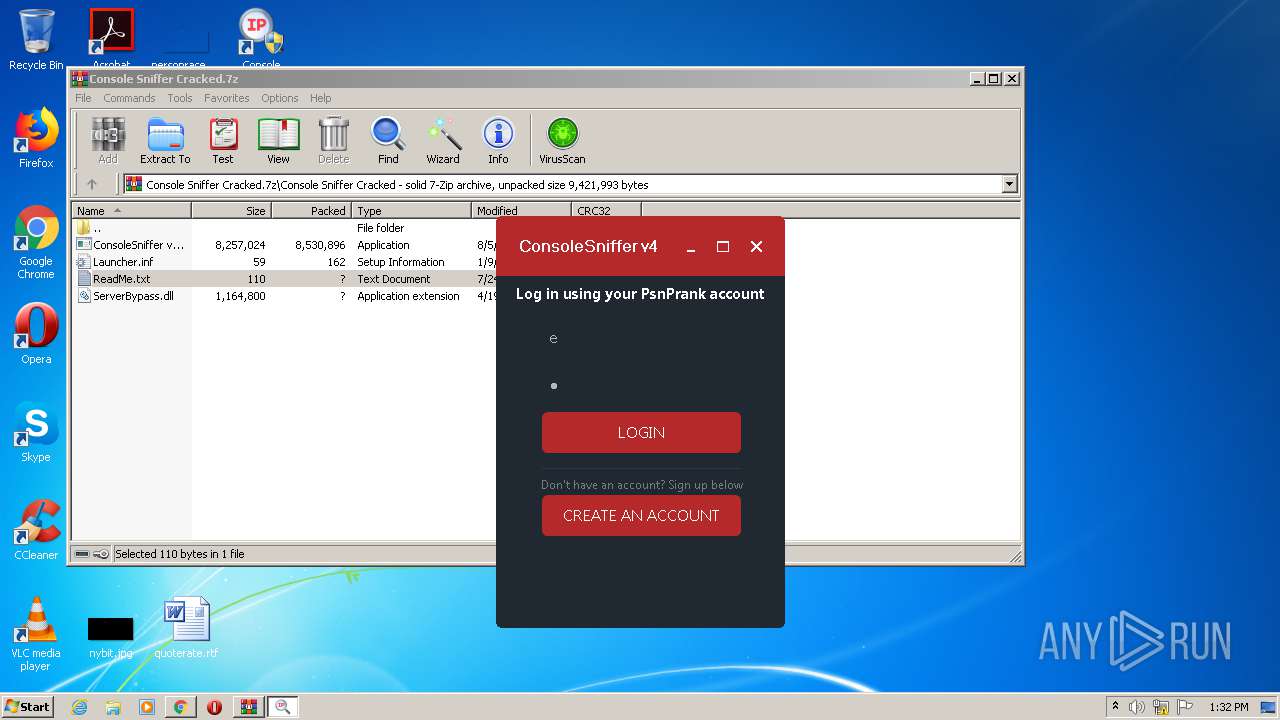
3540 | ConsoleSniffer.exe | GET | 200 | 74.91.122.37:80 | http://hub.psnprank.com/api/?a=sendmessage&user_triggered=true&user=e&pass=e&sniff&id=q0YqLKbiSegcb6Uz05HWWP%2F7qfULOhTK&k=WBcmHwq4UwkGcPdI6OTscOkcXi5tz0KKF86ynaet8qmeSxqa7ZcLG%2BqWhD34tJg48An6Qum0VN8%3D&version=4&ran=96933&license_email= | US | text | 41 b | unknown |
2968 | iexplore.exe | GET | 200 | 74.91.122.37:80 | http://psnprank.com/frontend/scripts/base64.js | US | text | 3.34 Kb | suspicious |
3540 | ConsoleSniffer.exe | GET | 200 | 74.91.122.37:80 | http://hub.psnprank.com/api/?a=sendmessage&user_triggered=true&user=e&pass=e&sniff&id=q0YqLKbiSegcb6Uz05HWWP%2F7qfULOhTK&k=WBcmHwq4UwkGcPdI6OTscOkcXi5tz0KKF86ynaet8qmeSxqa7ZcLG%2BqWhD34tJg48An6Qum0VN8%3D&version=4&ran=37085&license_email= | US | text | 41 b | unknown |
2968 | iexplore.exe | GET | 200 | 74.91.122.37:80 | http://psnprank.com/frontend/styles/images/loading.gif | US | image | 13.7 Kb | suspicious |
3540 | ConsoleSniffer.exe | GET | 200 | 74.91.122.37:80 | http://hub.psnprank.com/api/?a=sendmessage&user_triggered=true&user=Enter%20your%20username&pass=Enter%20your%20password&sniff&id=orE%2F7Xt1jV2CbeWnTHMYbHvvGAPNc0v%2F&k=tFoEMfDOZS5C6IrfUl4QfJy7tg6S0xZxng2oWp3NAaOMtP6aLzwV%2BvHNIDLG1wtX%2FlGZ%2FF0tywo%3D&version=4&ran=55744&license_email= | US | text | 41 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4044 | chrome.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
4044 | chrome.exe | 172.217.21.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
4044 | chrome.exe | 89.44.169.132:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | suspicious |
4044 | chrome.exe | 185.206.27.43:443 | gfs214n133.userstorage.mega.co.nz | — | — | unknown |
4044 | chrome.exe | 31.216.144.29:443 | gfs270n222.userstorage.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
1932 | svhost.exe | 77.247.127.140:6608 | — | — | — | malicious |
4044 | chrome.exe | 172.217.18.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2904 | vcredist_x86 - 2012 update 4.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
4044 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
4044 | chrome.exe | 31.216.147.133:443 | g.api.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mega.nz |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
gfs206n110.userstorage.mega.co.nz |
| suspicious |