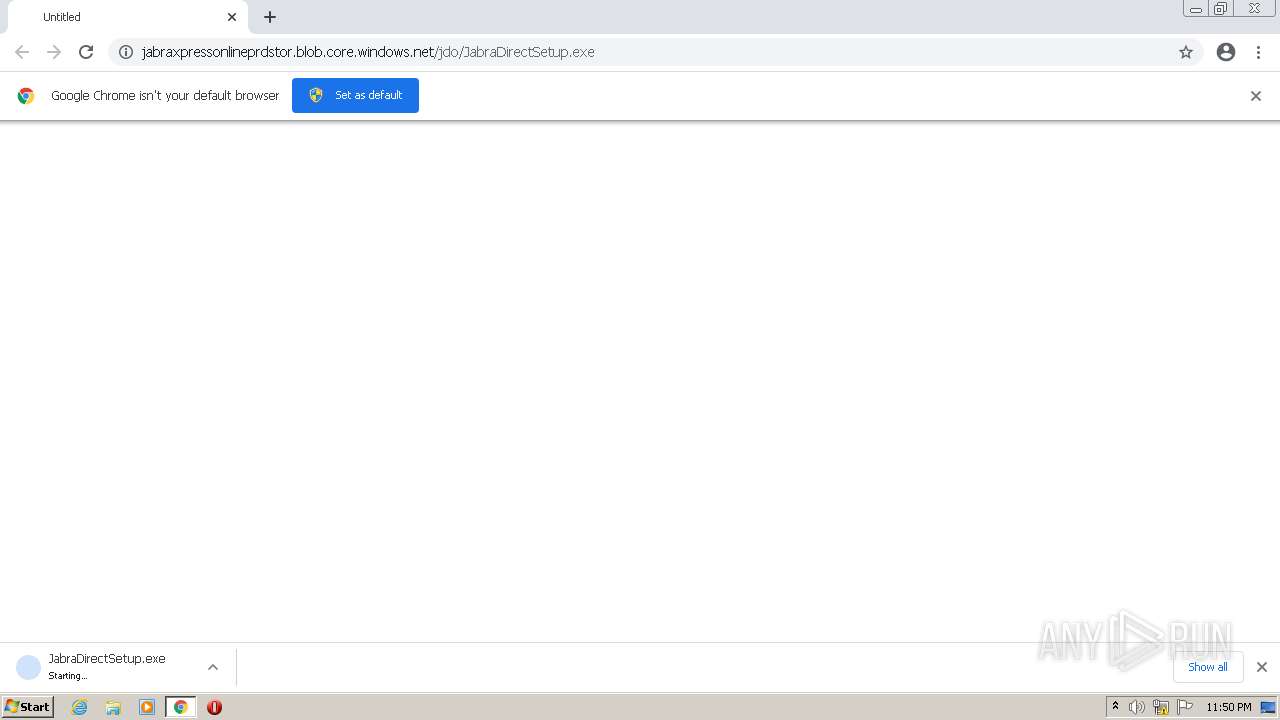
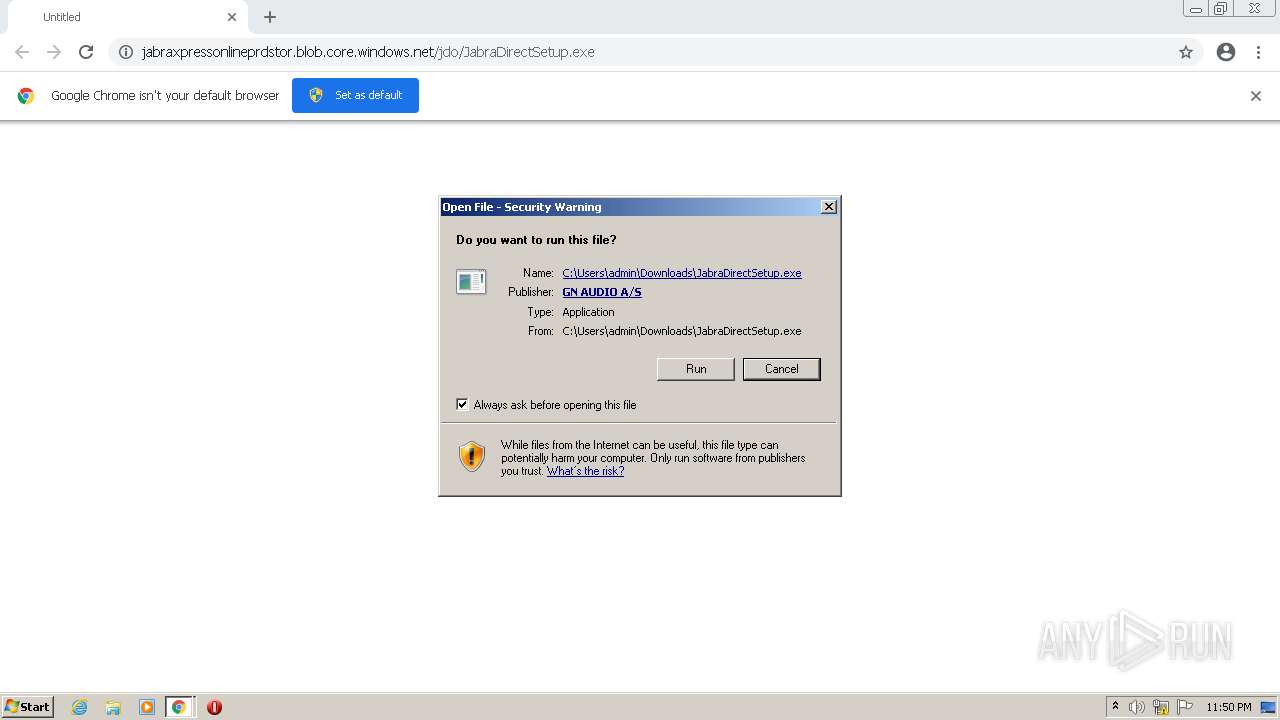
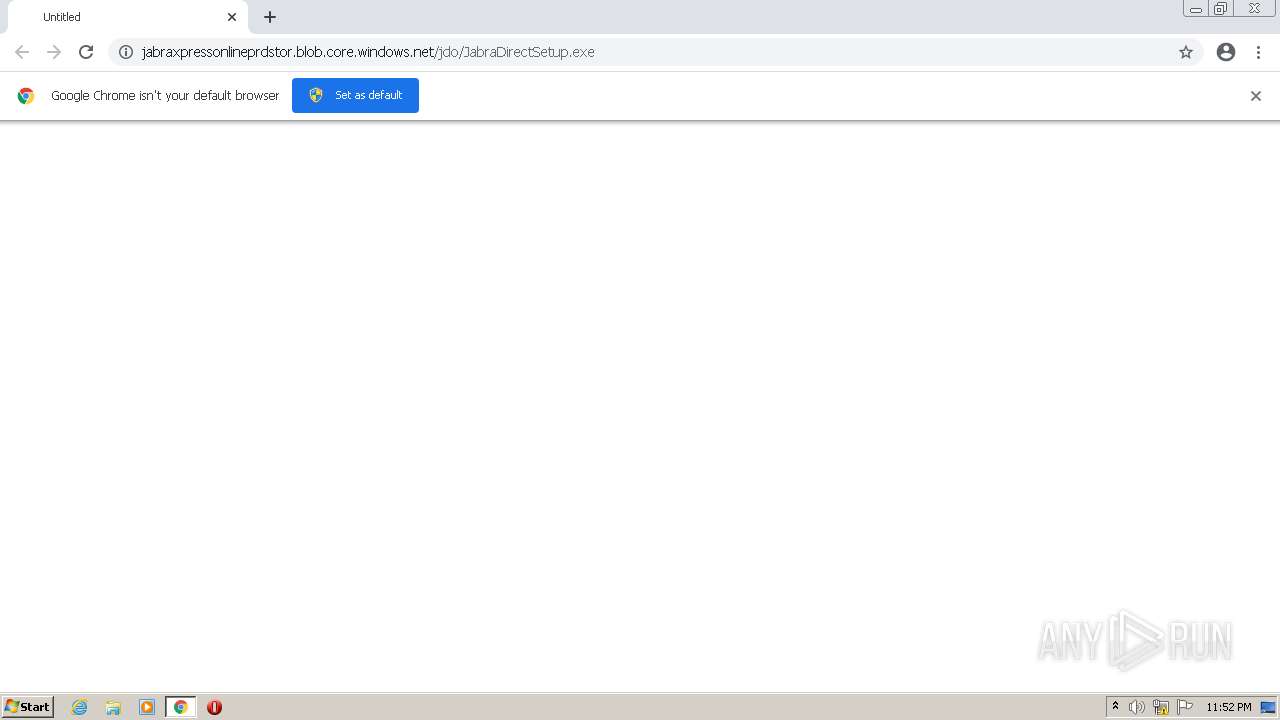
| URL: | https://jabraxpressonlineprdstor.blob.core.windows.net/jdo/JabraDirectSetup.exe |
| Full analysis: | https://app.any.run/tasks/35d50b18-0b6f-431c-96ee-449dc9106c9c |
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2022, 23:49:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C7D1B49DF76251725E73EAD3BEE4FE1E |
| SHA1: | 887D6C525434BA504459AF734EE0DC214A97903D |
| SHA256: | 0C487829A3AB9491DE1AF4A5260624E1115124980D957DF0FE07318D811AAA2B |
| SSDEEP: | 3:N80E9AyMmF4GwYWadA:2p9AfUWIA |
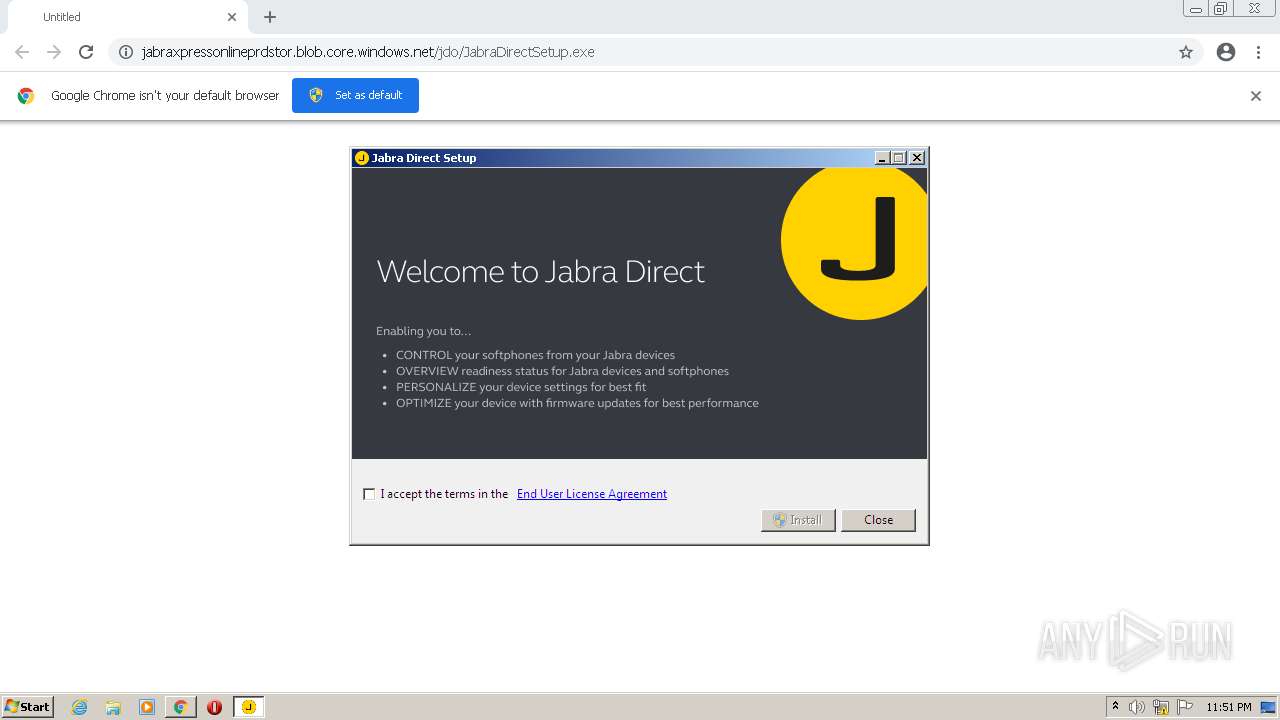
MALICIOUS
Drops executable file immediately after starts
- JabraDirectSetup.exe (PID: 3656)
- JabraDirectSetup.exe (PID: 3124)
- rundll32.exe (PID: 4092)
- MsiExec.exe (PID: 1056)
- chrome.exe (PID: 2164)
Loads dropped or rewritten executable
- JabraDirectSetup.exe (PID: 3656)
- msiexec.exe (PID: 2300)
- MsiExec.exe (PID: 1780)
- MsiExec.exe (PID: 3120)
- MsiExec.exe (PID: 3384)
- jabra-direct.exe (PID: 1088)
- jabra-direct.exe (PID: 3596)
- jabra-direct.exe (PID: 1108)
- jabra-direct.exe (PID: 2972)
- rundll32.exe (PID: 4092)
- jabra-direct.exe (PID: 116)
- jabra-direct.exe (PID: 3360)
Application was dropped or rewritten from another process
- JabraDirectSetup.exe (PID: 3656)
- JabraDirectSetup.exe (PID: 2232)
- JabraDirectSetup.exe (PID: 3124)
Changes the autorun value in the registry
- JabraDirectSetup.exe (PID: 2232)
- msiexec.exe (PID: 2300)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3036)
- JabraDirectSetup.exe (PID: 3656)
- JabraDirectSetup.exe (PID: 3124)
- JabraDirectSetup.exe (PID: 2232)
- msiexec.exe (PID: 2300)
- rundll32.exe (PID: 4092)
- MsiExec.exe (PID: 1056)
- jabra-direct.exe (PID: 1088)
- chrome.exe (PID: 2164)
Drops a file that was compiled in debug mode
- JabraDirectSetup.exe (PID: 3656)
- JabraDirectSetup.exe (PID: 3124)
- JabraDirectSetup.exe (PID: 2232)
- msiexec.exe (PID: 2300)
- rundll32.exe (PID: 4092)
- MsiExec.exe (PID: 1056)
- jabra-direct.exe (PID: 1088)
- chrome.exe (PID: 2164)
Searches for installed software
- JabraDirectSetup.exe (PID: 3656)
- JabraDirectSetup.exe (PID: 2232)
Starts itself from another location
- JabraDirectSetup.exe (PID: 3656)
Reads the computer name
- JabraDirectSetup.exe (PID: 3656)
- JabraDirectSetup.exe (PID: 2232)
- DrvInst.exe (PID: 2588)
- jabra-direct.exe (PID: 1088)
- jabra-direct.exe (PID: 1108)
- jabra-direct.exe (PID: 3596)
- jabra-direct.exe (PID: 116)
- powershell.exe (PID: 3516)
Checks supported languages
- JabraDirectSetup.exe (PID: 2232)
- JabraDirectSetup.exe (PID: 3124)
- JabraDirectSetup.exe (PID: 3656)
- DrvInst.exe (PID: 2588)
- jabra-direct.exe (PID: 1088)
- jabra-direct.exe (PID: 1108)
- jabra-direct.exe (PID: 3596)
- jabra-direct.exe (PID: 2972)
- jabra-direct.exe (PID: 116)
- powershell.exe (PID: 3516)
- jabra-direct.exe (PID: 3360)
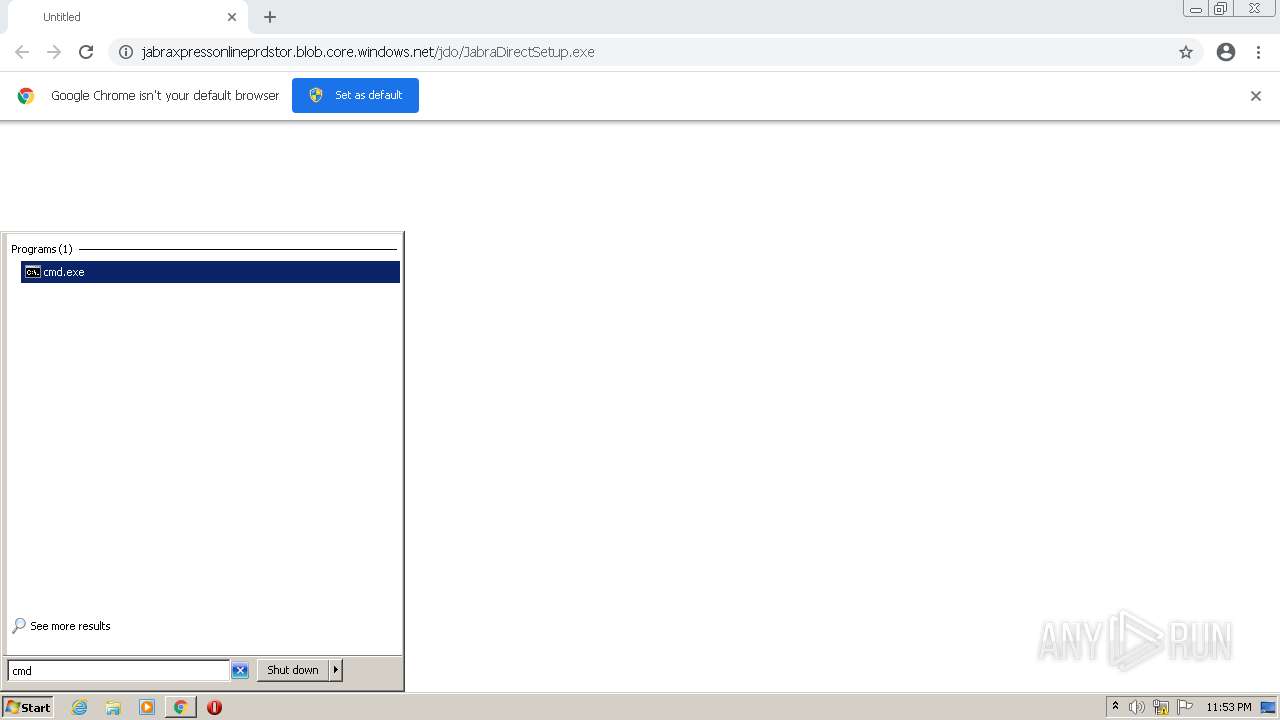
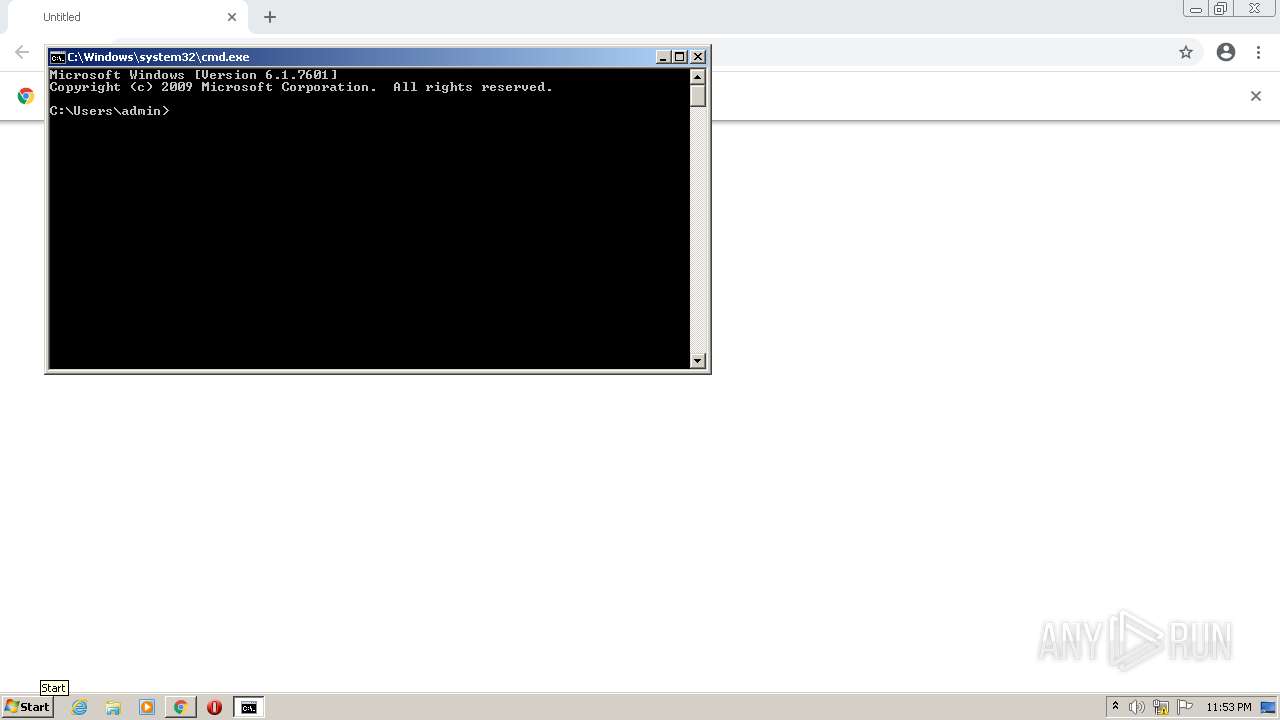
- cmd.exe (PID: 2256)
Executed as Windows Service
- msiexec.exe (PID: 2300)
- vssvc.exe (PID: 3076)
Creates a software uninstall entry
- JabraDirectSetup.exe (PID: 2232)
- msiexec.exe (PID: 2300)
Creates files in the program directory
- JabraDirectSetup.exe (PID: 2232)
- msiexec.exe (PID: 2300)
Reads Windows owner or organization settings
- msiexec.exe (PID: 2300)
Reads Environment values
- vssvc.exe (PID: 3076)
- netsh.exe (PID: 3708)
- netsh.exe (PID: 3240)
- jabra-direct.exe (PID: 1088)
Application launched itself
- msiexec.exe (PID: 2300)
- jabra-direct.exe (PID: 1088)
Uses TASKKILL.EXE to kill process
- MsiExec.exe (PID: 3384)
Creates a directory in Program Files
- msiexec.exe (PID: 2300)
Drops a file with too old compile date
- msiexec.exe (PID: 2300)
- MsiExec.exe (PID: 1056)
Creates files in the Windows directory
- msiexec.exe (PID: 2300)
- DrvInst.exe (PID: 2588)
Drops a file with a compile date too recent
- msiexec.exe (PID: 2300)
Uses NETSH.EXE for network configuration
- MsiExec.exe (PID: 3120)
Reads the Windows organization settings
- msiexec.exe (PID: 2300)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 2300)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 3120)
Removes files from Windows directory
- msiexec.exe (PID: 2300)
- DrvInst.exe (PID: 2588)
Executed via COM
- DrvInst.exe (PID: 2588)
Creates files in the driver directory
- DrvInst.exe (PID: 2588)
Creates files in the user directory
- jabra-direct.exe (PID: 1088)
- jabra-direct.exe (PID: 3596)
Executes PowerShell scripts
- jabra-direct.exe (PID: 1088)
Uses ICACLS.EXE to modify access control list
- jabra-direct.exe (PID: 1088)
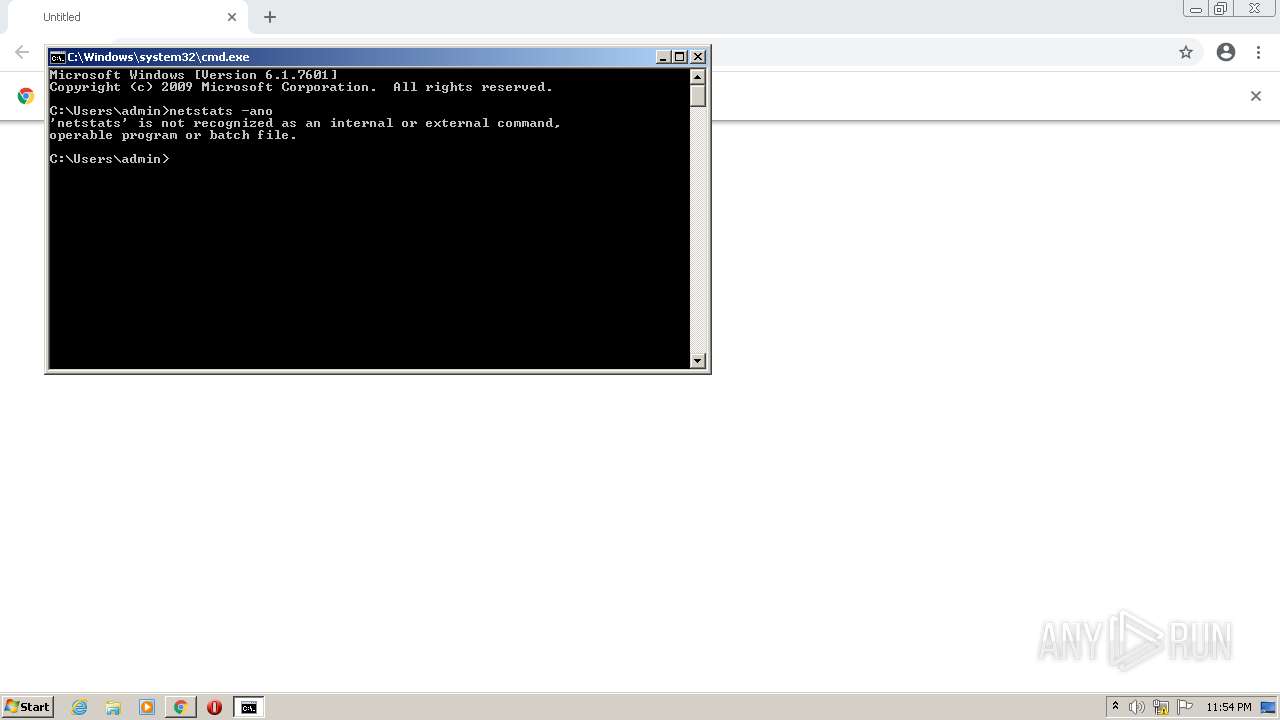
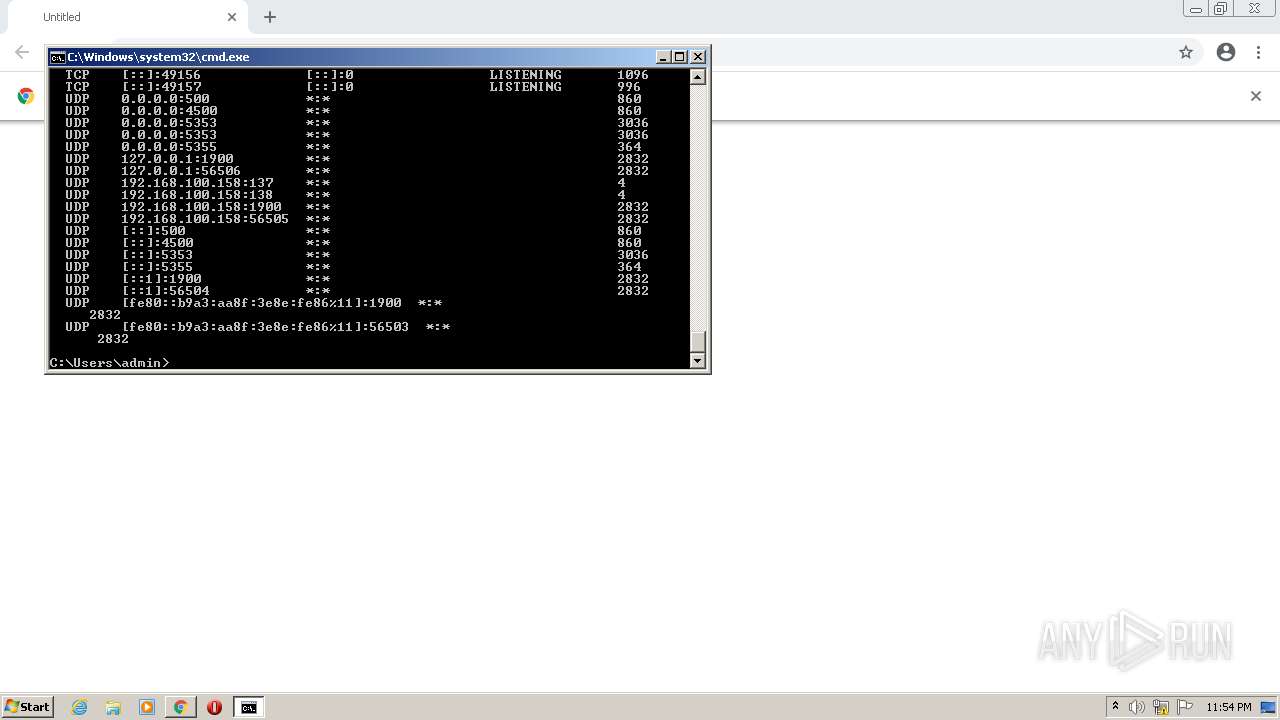
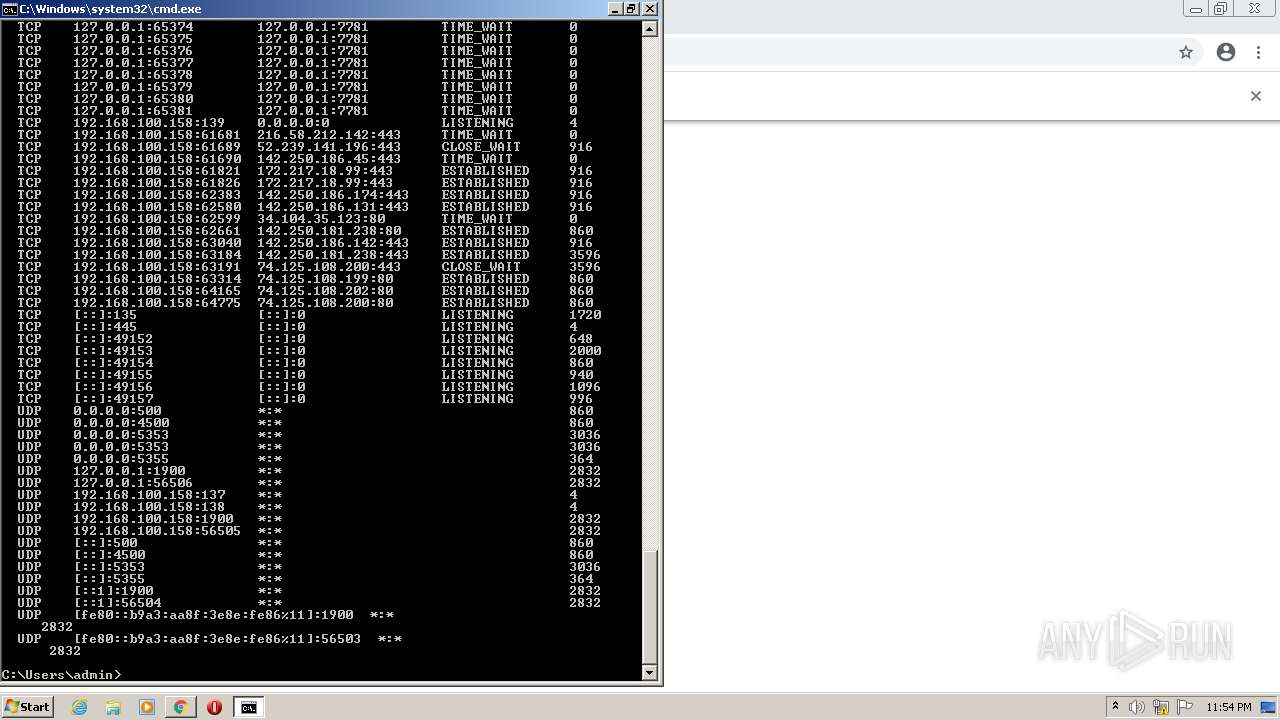
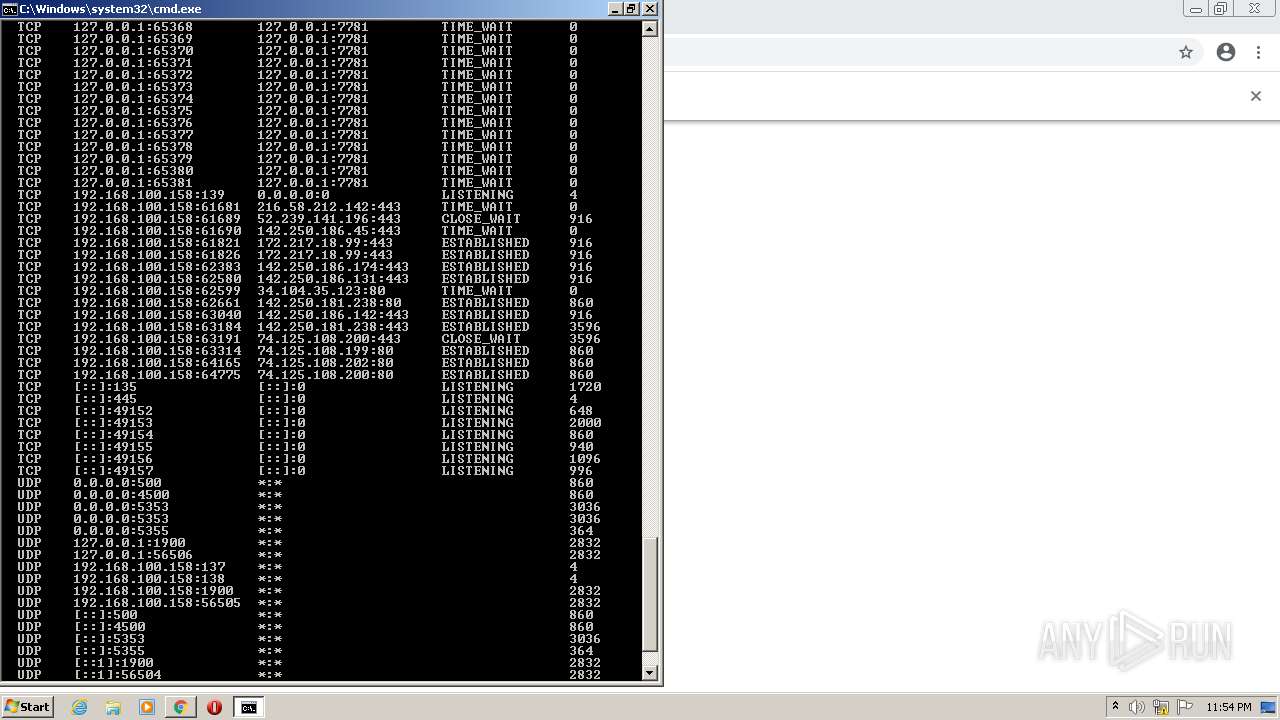
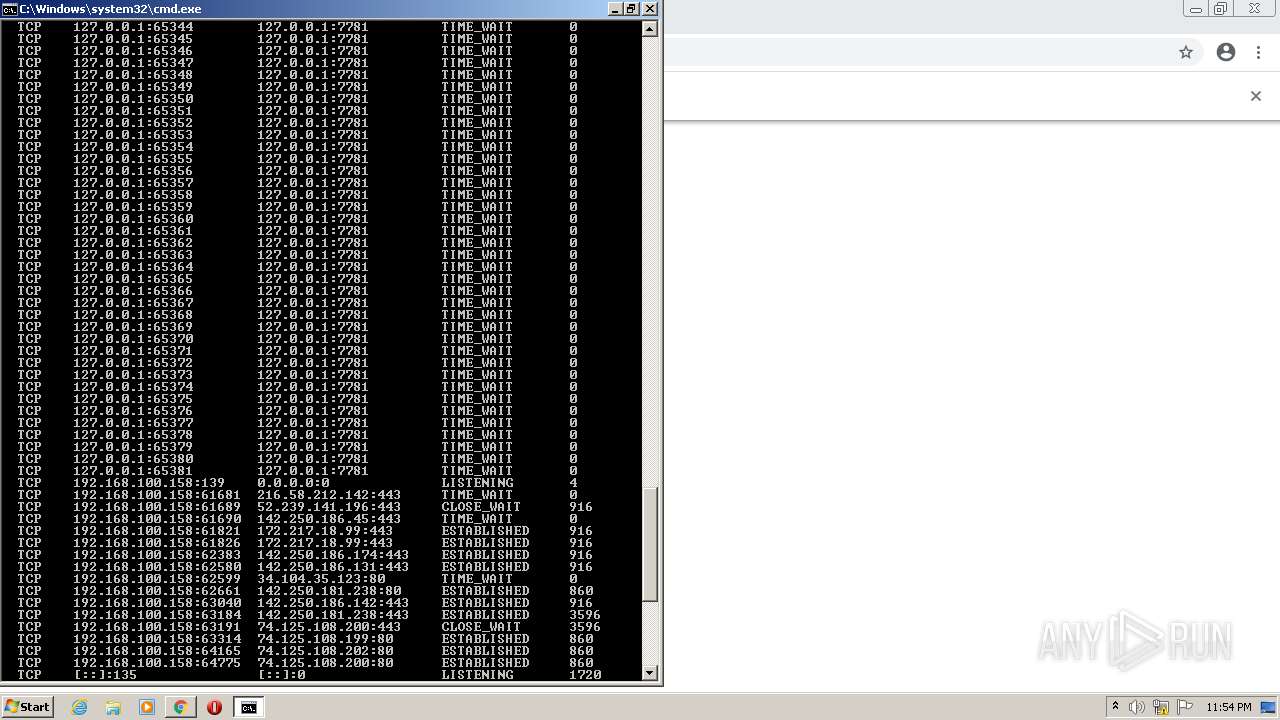
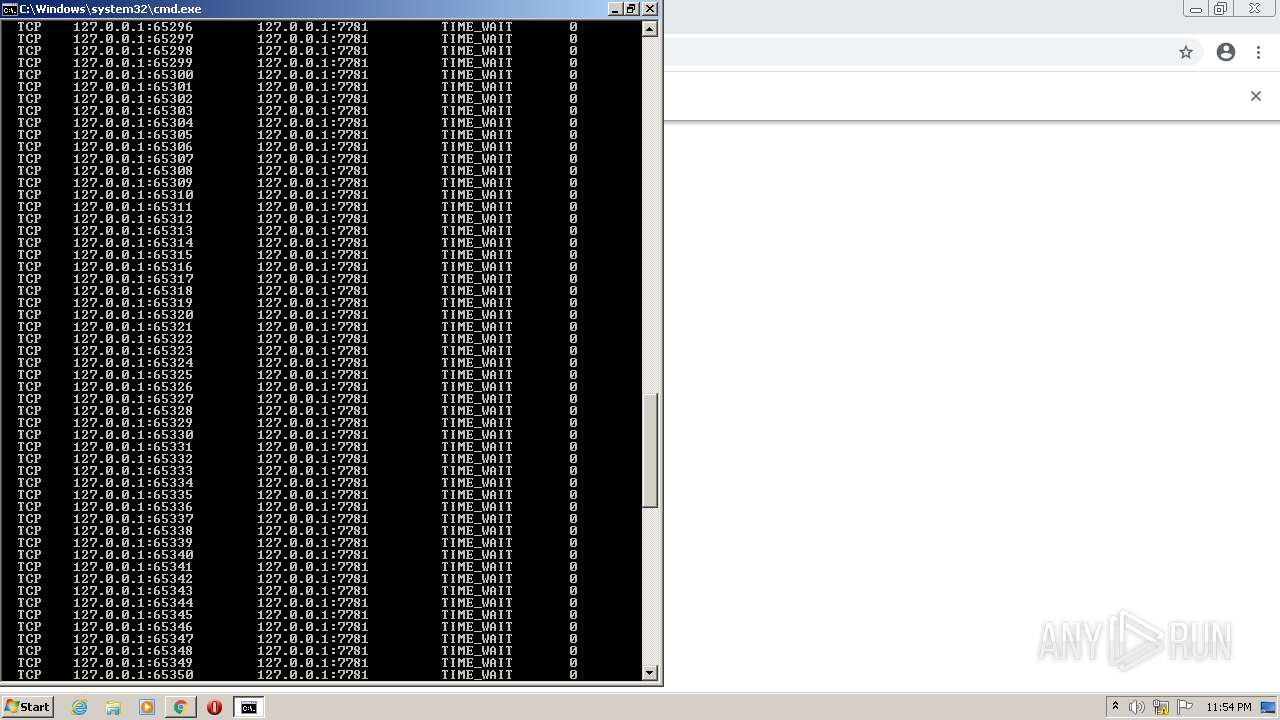
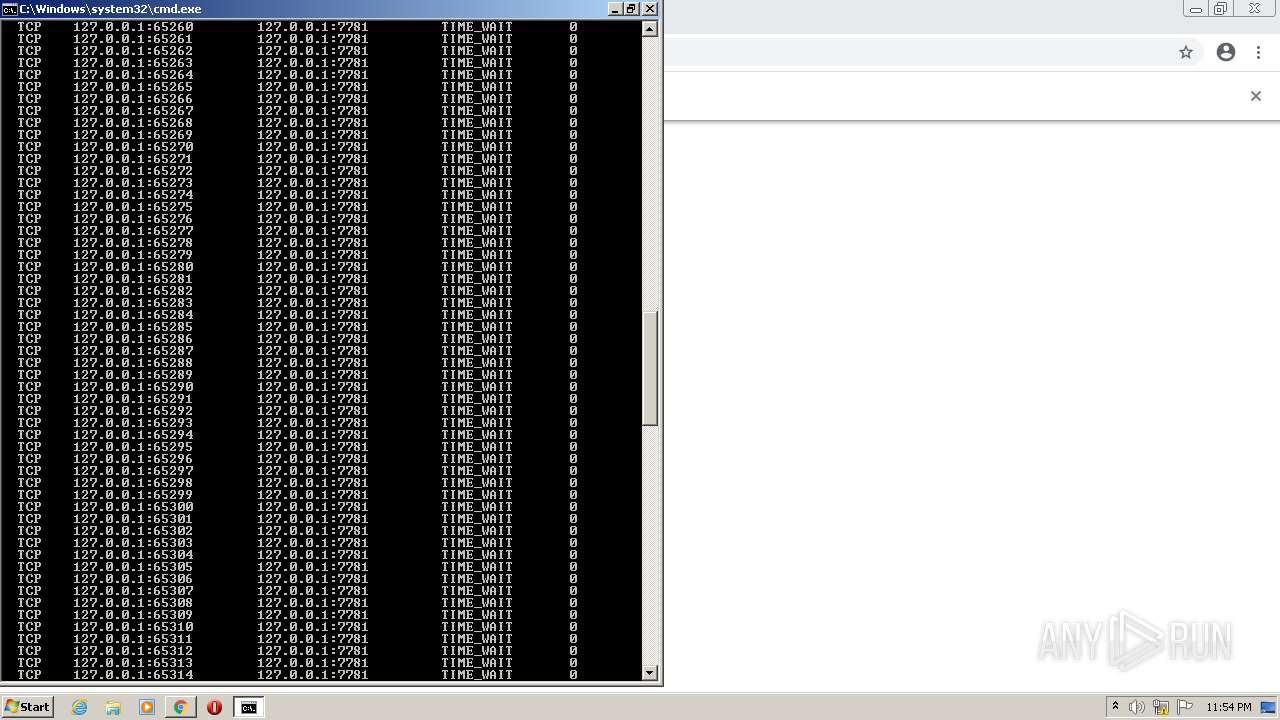
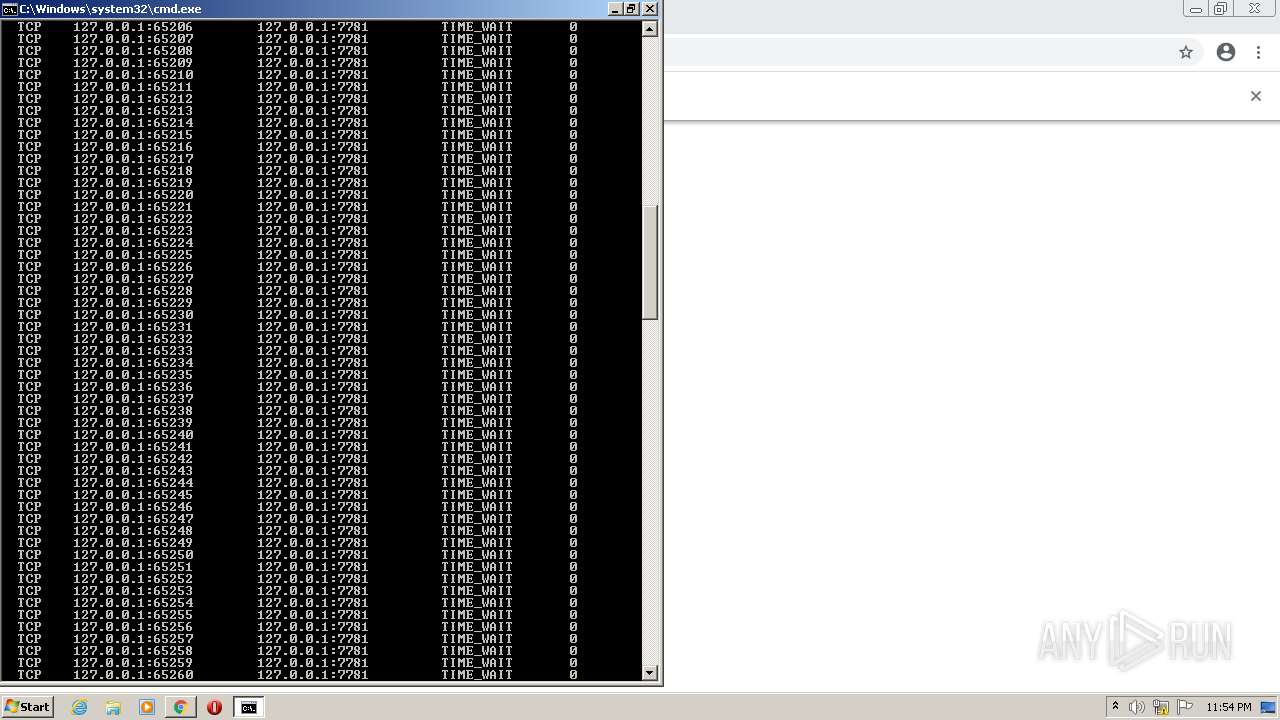
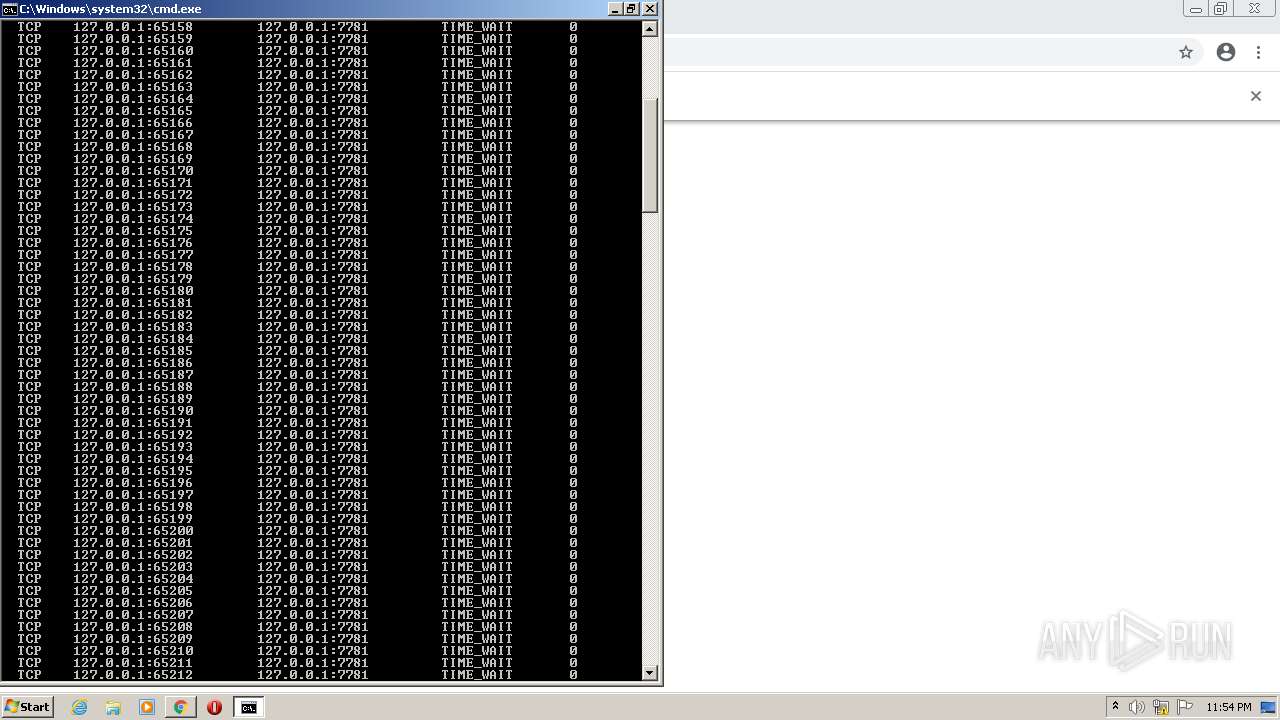
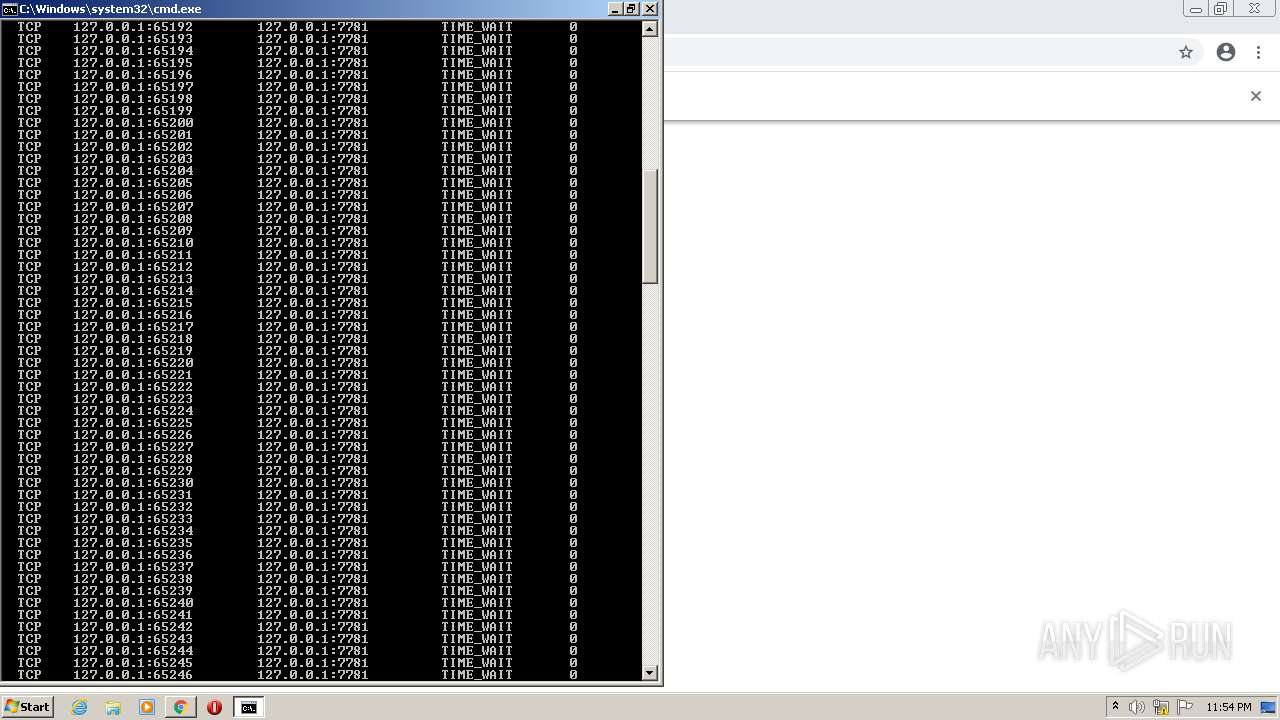
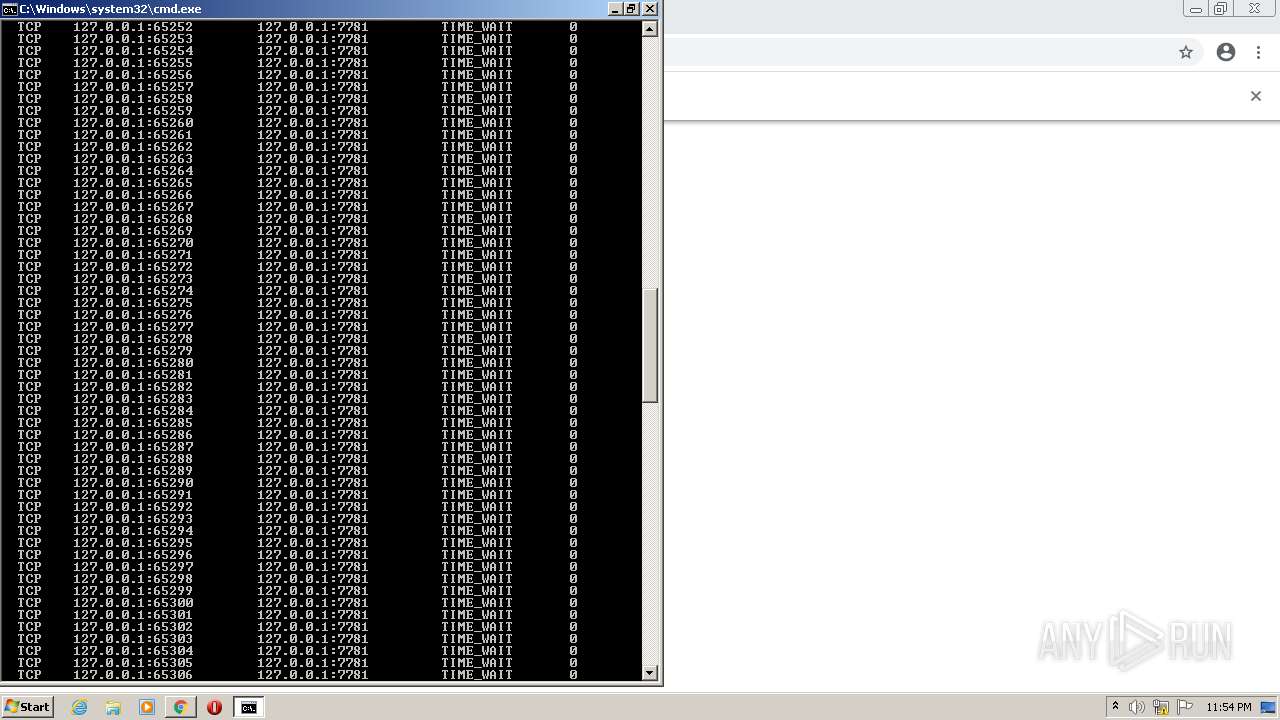
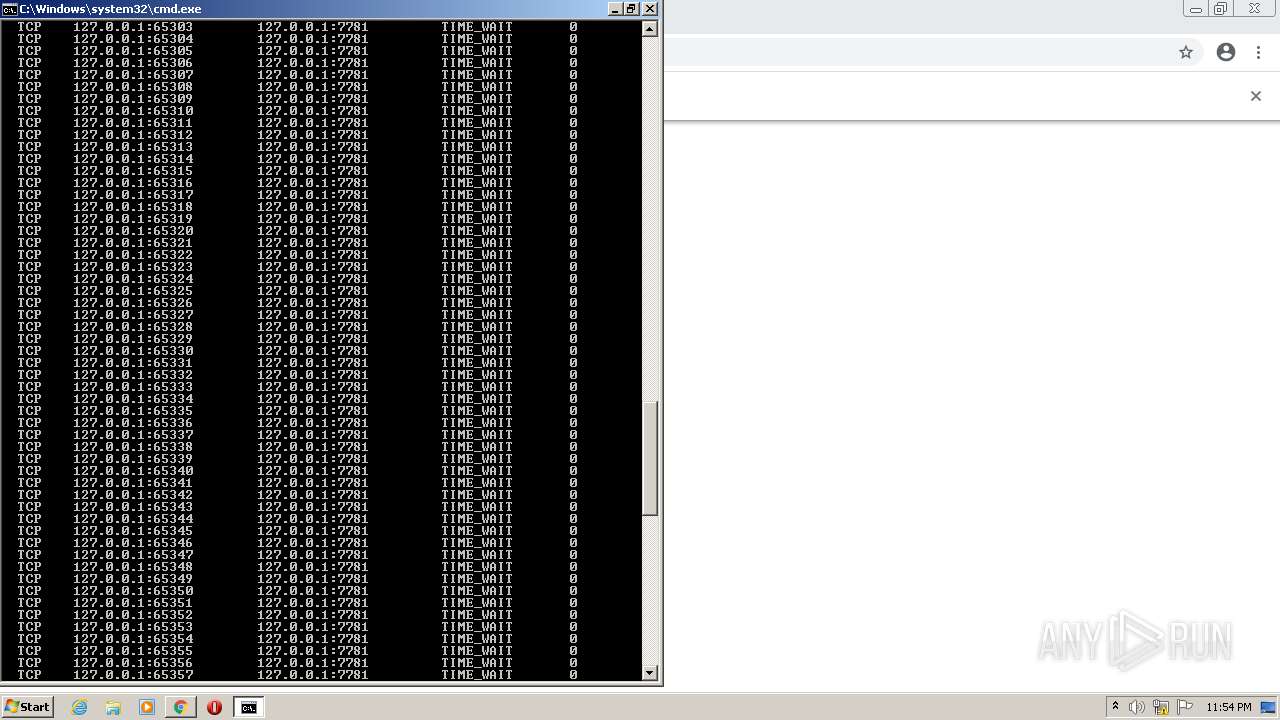
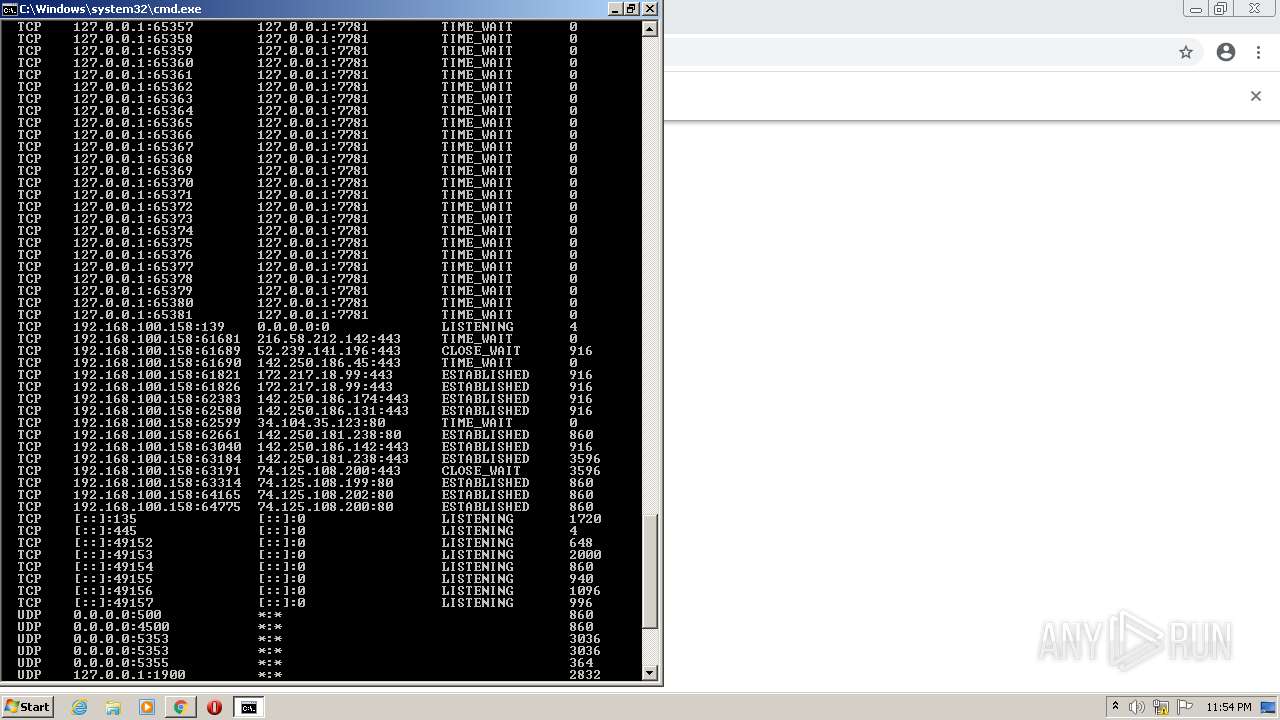
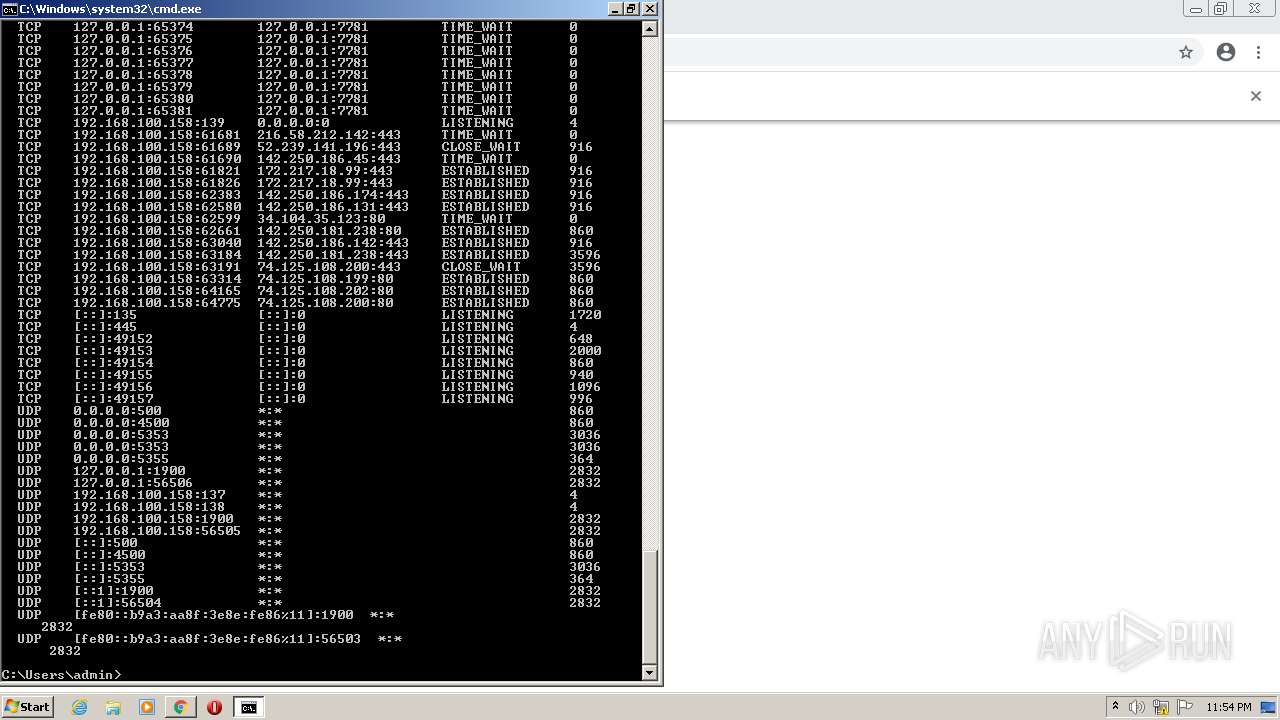
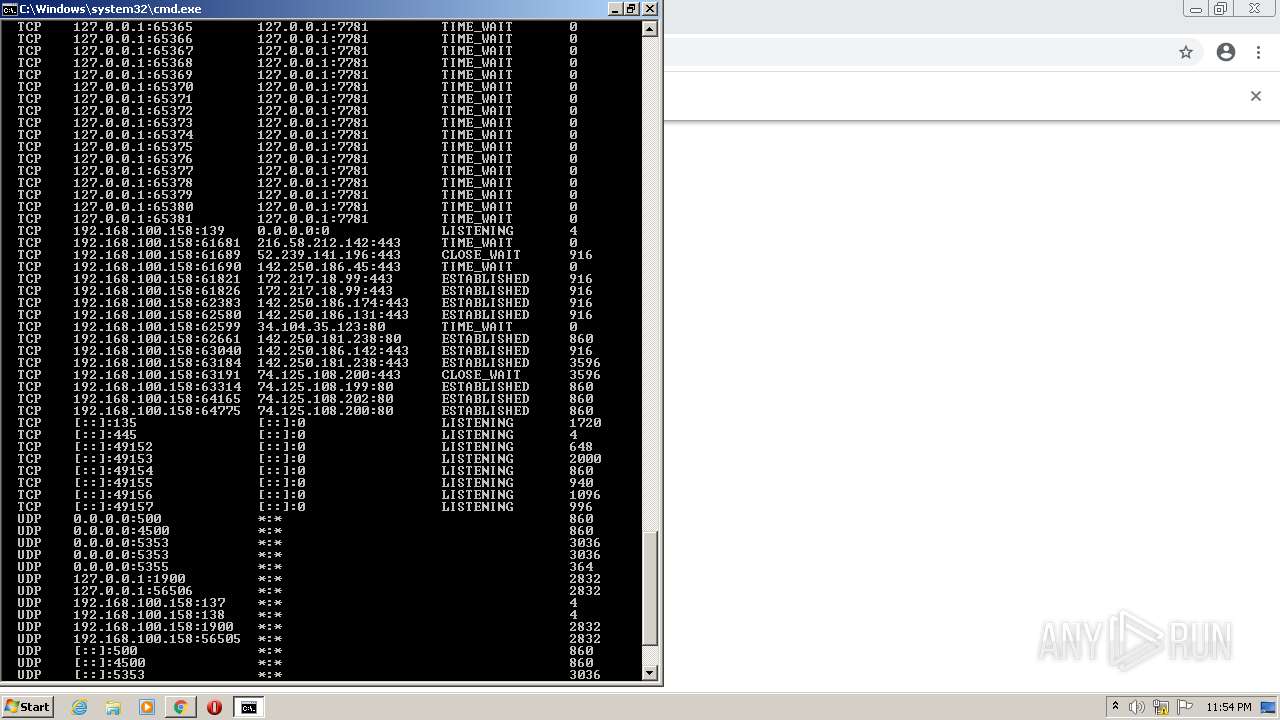
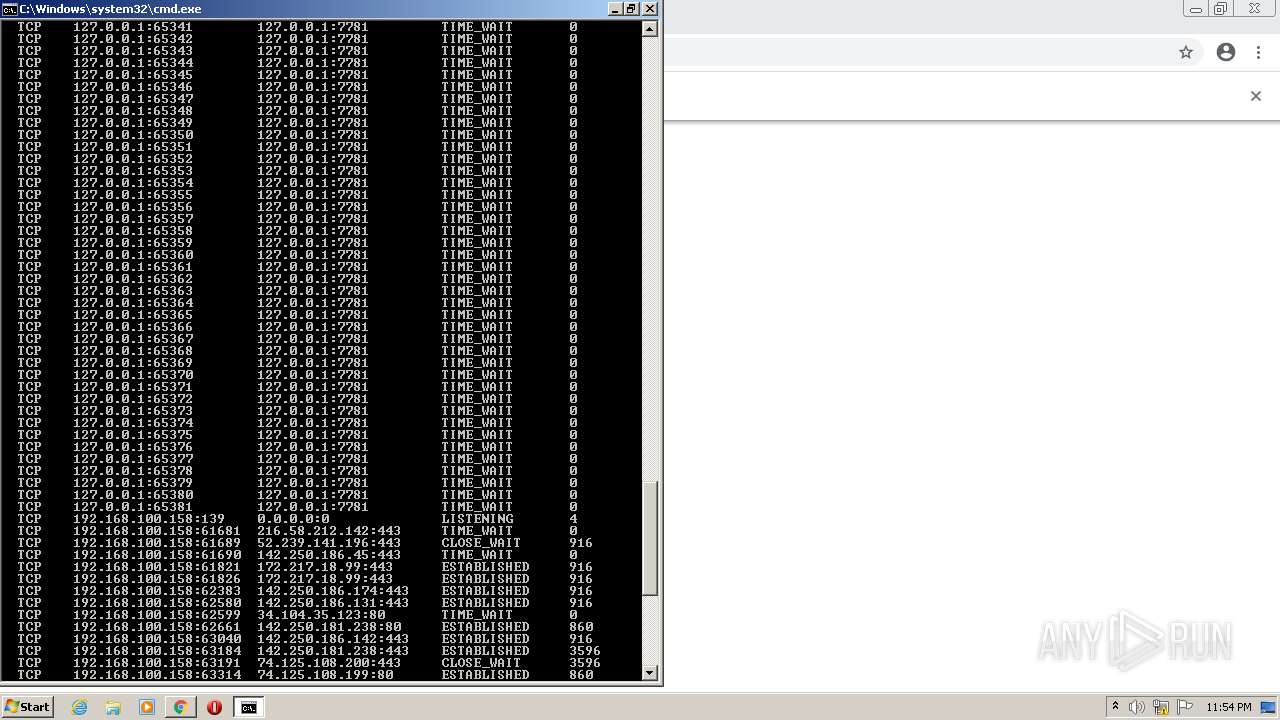
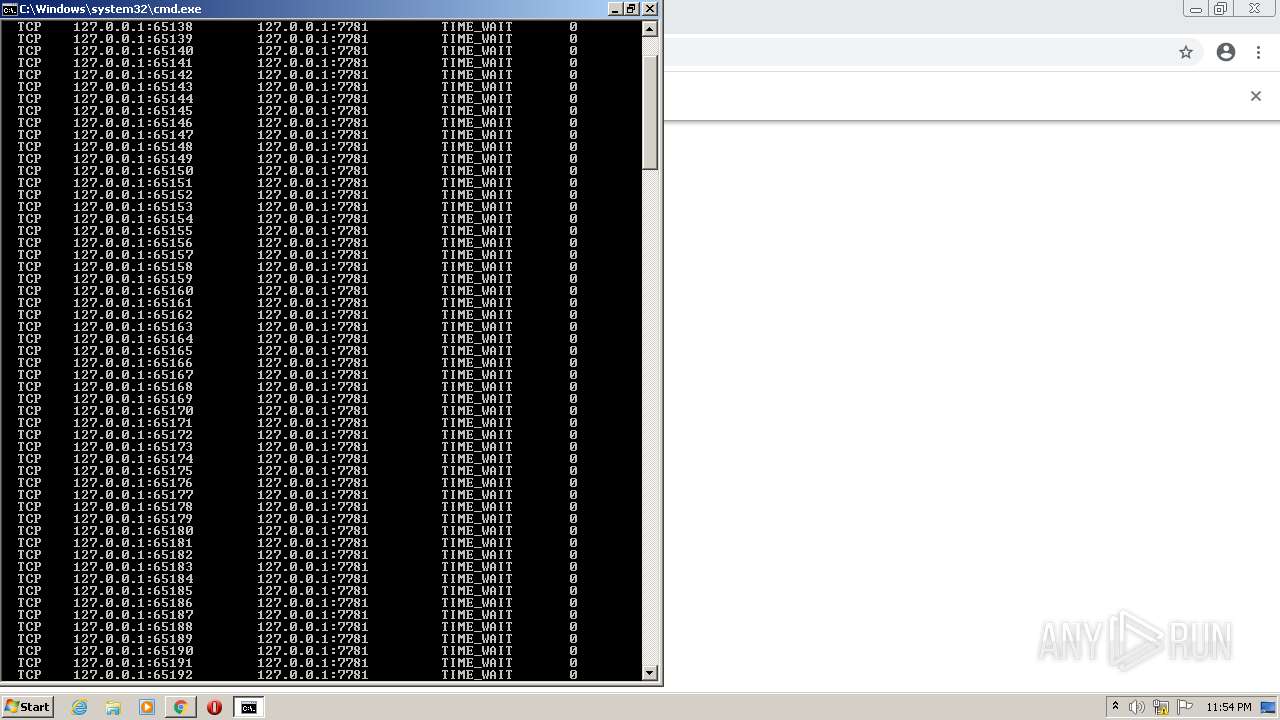
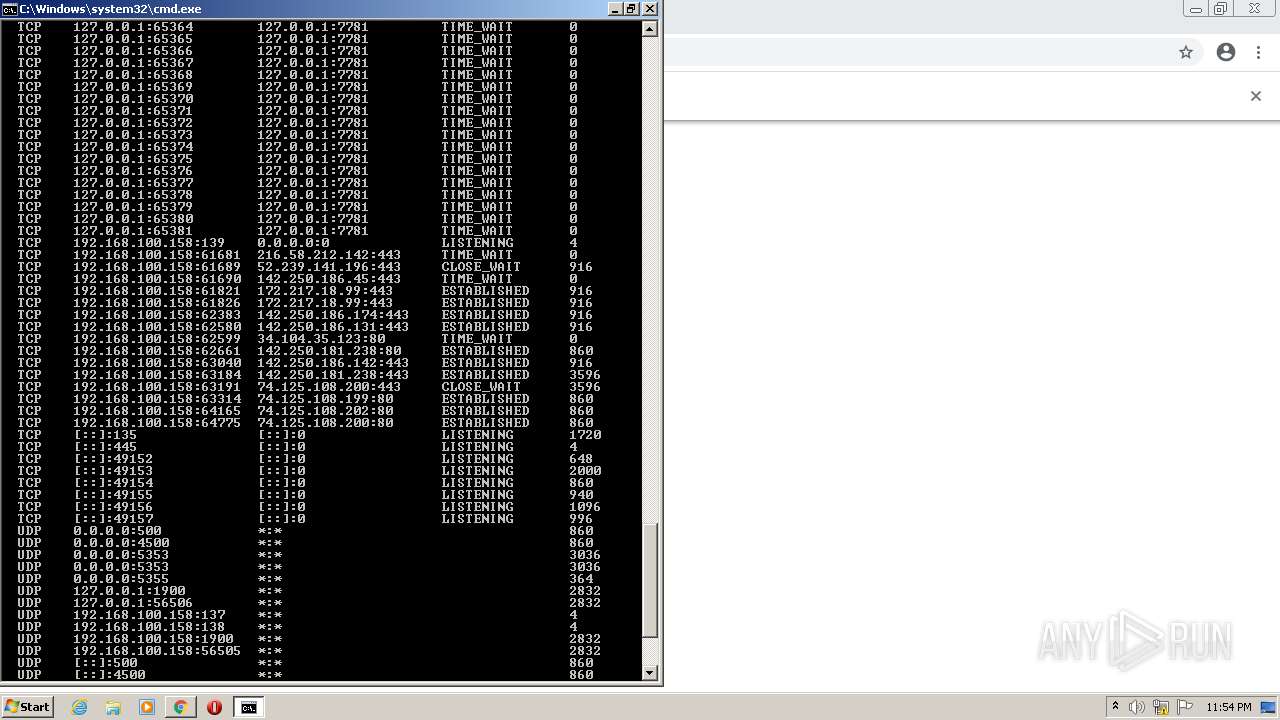
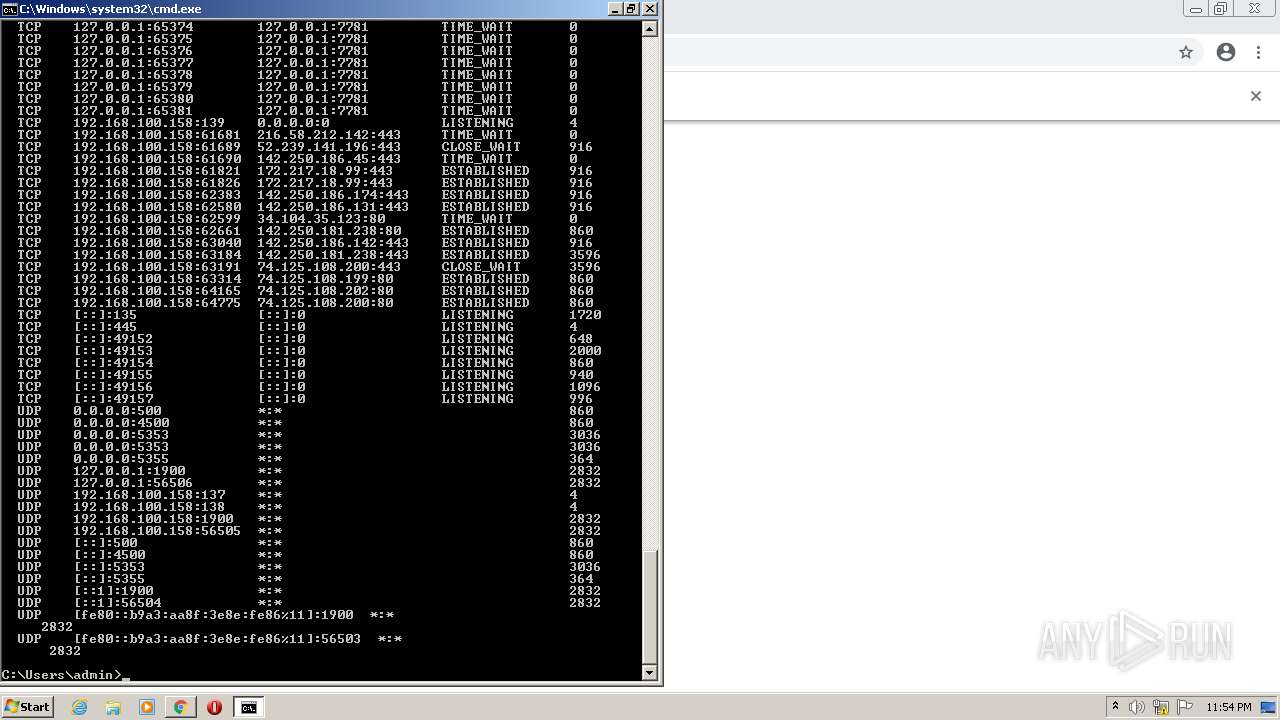
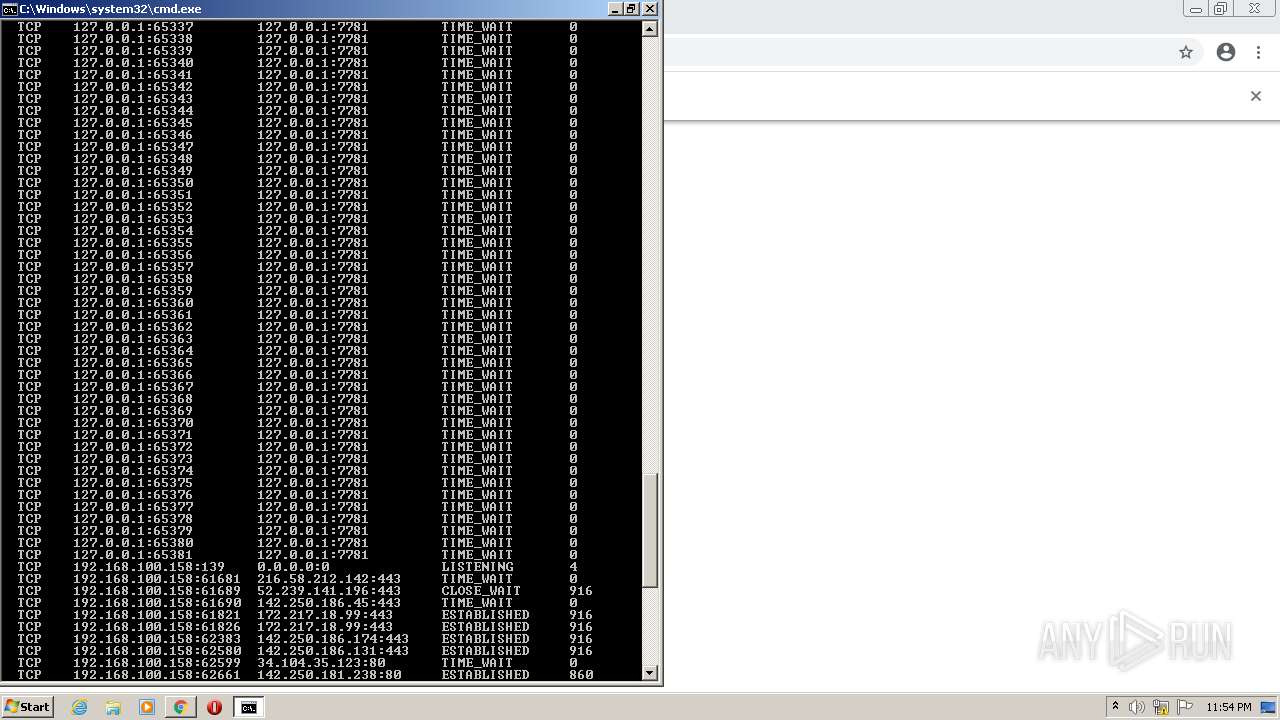
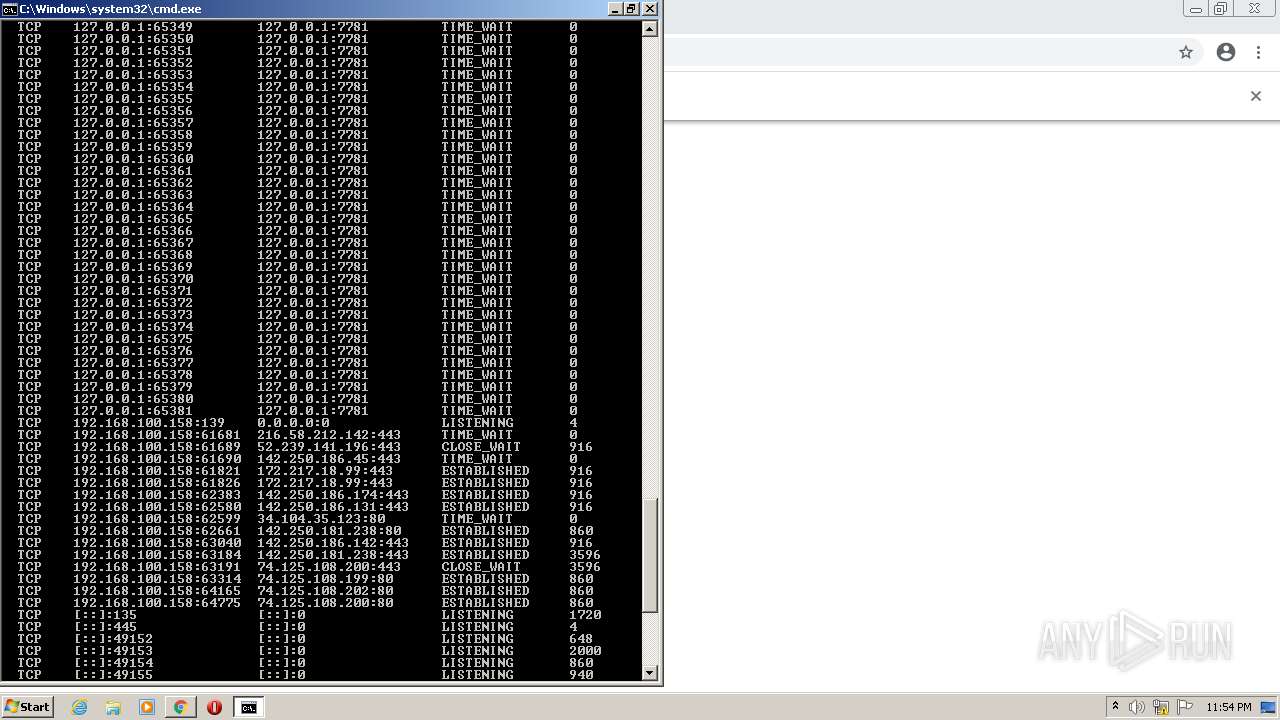
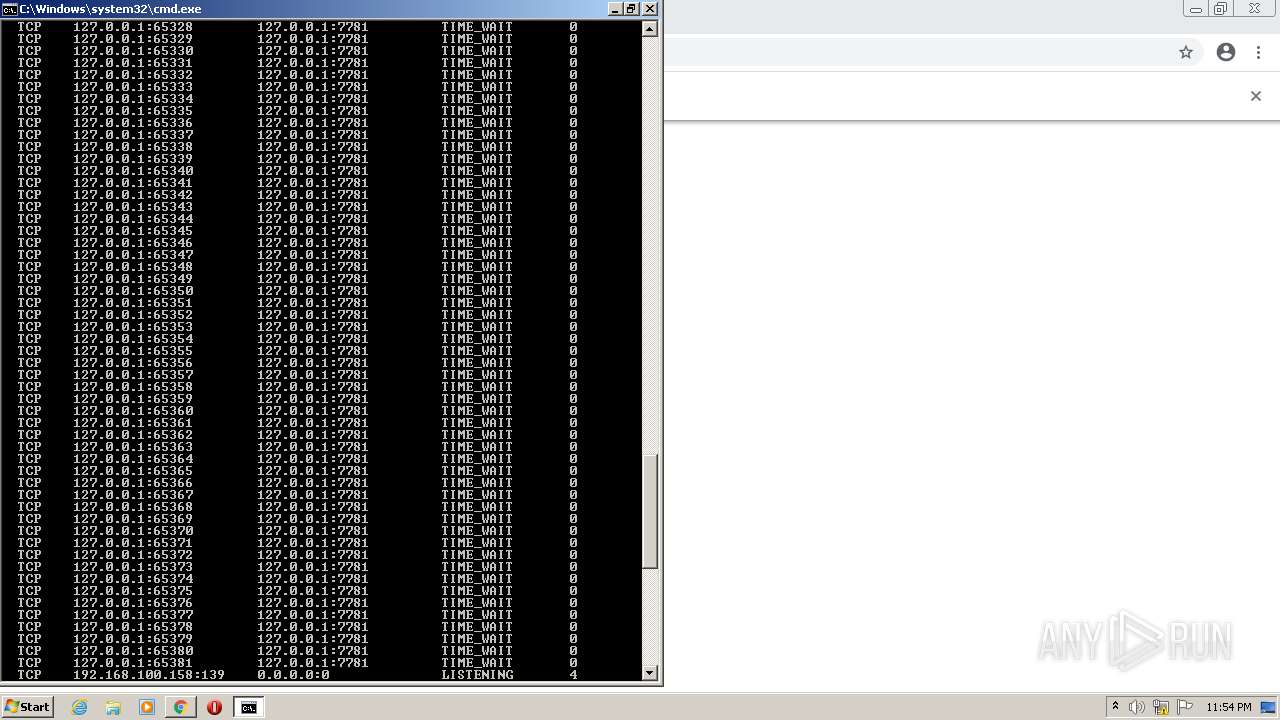
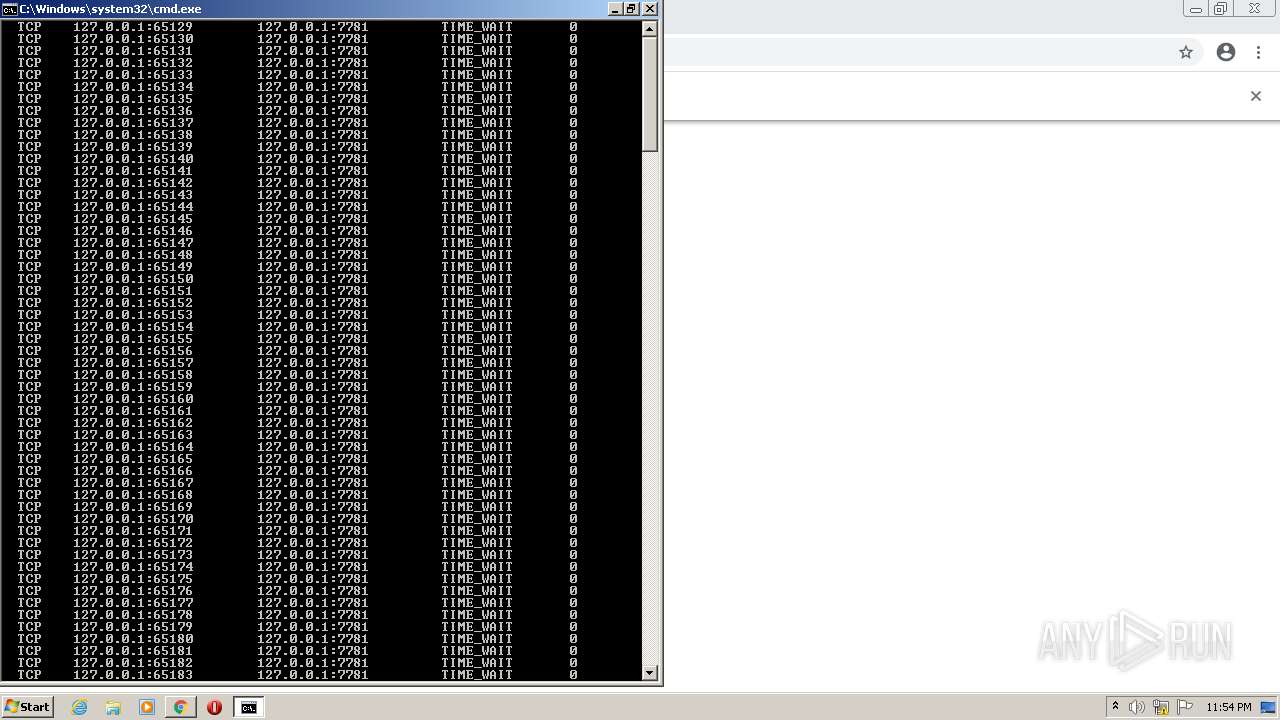
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 2256)
INFO
Checks supported languages
- chrome.exe (PID: 2484)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 2640)
- chrome.exe (PID: 1968)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 916)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 1948)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 1408)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 1888)
- chrome.exe (PID: 2560)
- msiexec.exe (PID: 2300)
- chrome.exe (PID: 3760)
- vssvc.exe (PID: 3076)
- taskkill.exe (PID: 3144)
- MsiExec.exe (PID: 3120)
- MsiExec.exe (PID: 3384)
- netsh.exe (PID: 3240)
- rundll32.exe (PID: 4092)
- netsh.exe (PID: 3708)
- MsiExec.exe (PID: 1056)
- MsiExec.exe (PID: 1780)
- chrome.exe (PID: 2448)
- icacls.exe (PID: 2212)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 924)
- NETSTAT.EXE (PID: 3156)
- chrome.exe (PID: 2808)
Reads the computer name
- chrome.exe (PID: 4068)
- chrome.exe (PID: 2640)
- chrome.exe (PID: 916)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 1888)
- chrome.exe (PID: 1948)
- vssvc.exe (PID: 3076)
- msiexec.exe (PID: 2300)
- MsiExec.exe (PID: 3384)
- taskkill.exe (PID: 3144)
- MsiExec.exe (PID: 3120)
- netsh.exe (PID: 3240)
- rundll32.exe (PID: 4092)
- netsh.exe (PID: 3708)
- MsiExec.exe (PID: 1780)
- MsiExec.exe (PID: 1056)
- icacls.exe (PID: 2212)
- NETSTAT.EXE (PID: 3156)
Reads the hosts file
- chrome.exe (PID: 3036)
- chrome.exe (PID: 916)
- jabra-direct.exe (PID: 1088)
- jabra-direct.exe (PID: 3596)
Reads settings of System Certificates
- chrome.exe (PID: 916)
- chrome.exe (PID: 3036)
- msiexec.exe (PID: 2300)
- DrvInst.exe (PID: 2588)
- jabra-direct.exe (PID: 3596)
Application launched itself
- chrome.exe (PID: 3036)
Checks Windows Trust Settings
- chrome.exe (PID: 3036)
- msiexec.exe (PID: 2300)
- DrvInst.exe (PID: 2588)
- powershell.exe (PID: 3516)
Reads the date of Windows installation
- chrome.exe (PID: 2560)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2300)
- JabraDirectSetup.exe (PID: 2232)
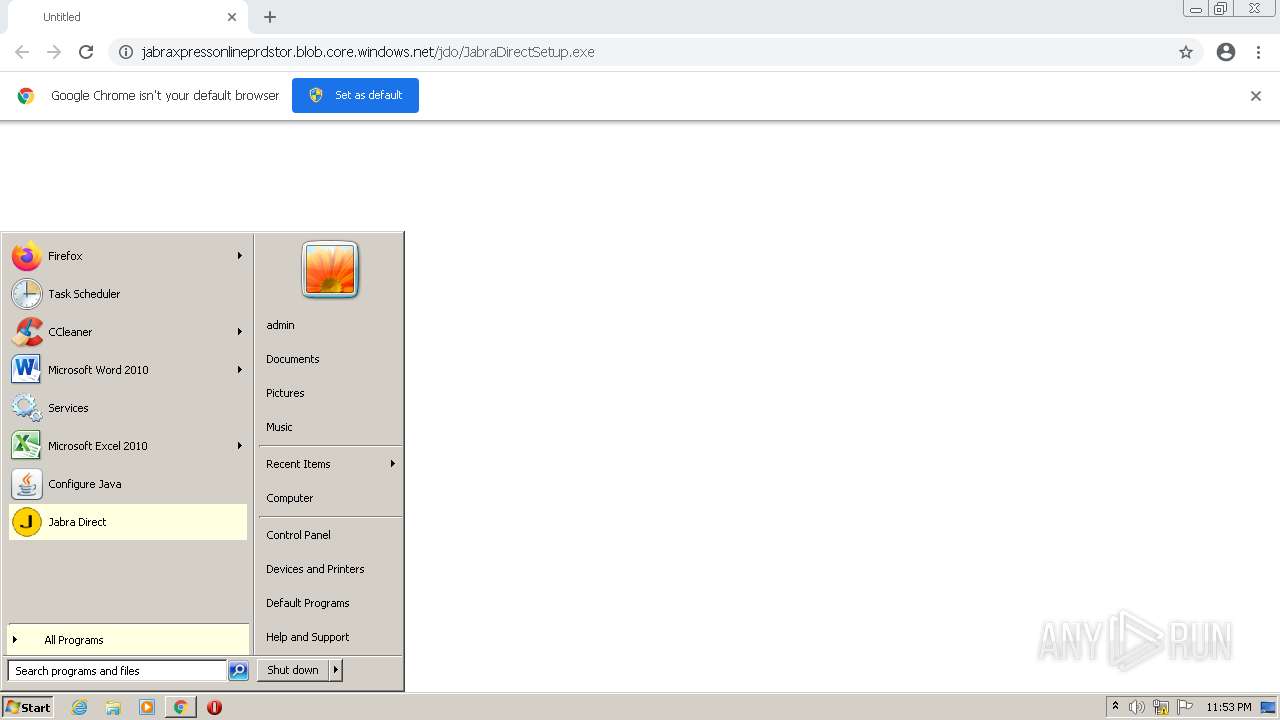
Manual execution by user
- cmd.exe (PID: 2256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
100
Monitored processes
51
Malicious processes
9
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Jabra\Direct4\jabra-direct.exe" --type=gpu-process --field-trial-handle=1032,16997019282031929038,3211119675869524772,131072 --enable-features=WebComponentsV0Enabled --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1040 /prefetch:2 | C:\Program Files\Jabra\Direct4\jabra-direct.exe | — | jabra-direct.exe | |||||||||||
User: admin Company: GN Audio A/S Integrity Level: LOW Description: Jabra Direct Exit code: 0 Version: 5.10.2 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1012,3019228300289885390,1538508468314575863,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1232 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1012,3019228300289885390,1538508468314575863,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3228 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1056 | C:\Windows\system32\MsiExec.exe -Embedding F8A7CF8E31151C4BC422B74470F0DCD0 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Jabra\Direct4\jabra-direct.exe" | C:\Program Files\Jabra\Direct4\jabra-direct.exe | JabraDirectSetup.exe | ||||||||||||
User: admin Company: GN Audio A/S Integrity Level: MEDIUM Description: Jabra Direct Exit code: 0 Version: 5.10.2 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Jabra\Direct4\jabra-direct.exe" --type=gpu-process --field-trial-handle=1032,16997019282031929038,3211119675869524772,131072 --enable-features=WebComponentsV0Enabled --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1040 /prefetch:2 | C:\Program Files\Jabra\Direct4\jabra-direct.exe | — | jabra-direct.exe | |||||||||||
User: admin Company: GN Audio A/S Integrity Level: LOW Description: Jabra Direct Exit code: 0 Version: 5.10.2 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1012,3019228300289885390,1538508468314575863,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3208 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1780 | C:\Windows\system32\MsiExec.exe -Embedding E0AD021BCEB781DCBAFCD01AC1435227 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1012,3019228300289885390,1538508468314575863,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1760 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1012,3019228300289885390,1538508468314575863,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
32 056
Read events
31 036
Write events
984
Delete events
36
Modification events
| (PID) Process: | (3036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3036) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
183
Suspicious files
145
Text files
168
Unknown types
85
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61D62EA7-BDC.pma | — | |
MD5:— | SHA256:— | |||
| 3504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9ebac67b-32e8-4562-9b35-0428282689c5.tmp | text | |
MD5:— | SHA256:— | |||
| 3036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF112da4.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF112f1b.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 3036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF113526.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 3036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\139f61a1-0073-4ca3-bd42-bf94d6cfcc16.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
29
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 200 | 74.125.108.201:80 | http://r4---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.45.13&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641426497&mv=m&mvi=4&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 74.125.108.201:80 | http://r4---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.45.13&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641426257&mv=m&mvi=4&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=yes | US | binary | 5.63 Kb | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 576 b | whitelisted |
860 | svchost.exe | GET | 206 | 74.125.108.201:80 | http://r4---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.45.13&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641426497&mv=m&mvi=4&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=yes | US | binary | 9.48 Kb | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 576 b | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 576 b | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 576 b | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 576 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
916 | chrome.exe | 216.58.212.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
916 | chrome.exe | 52.239.141.196:443 | jabraxpressonlineprdstor.blob.core.windows.net | Microsoft Corporation | NL | unknown |
916 | chrome.exe | 142.250.186.45:443 | accounts.google.com | Google Inc. | US | suspicious |
916 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
916 | chrome.exe | 142.250.186.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
916 | chrome.exe | 142.250.186.131:443 | update.googleapis.com | Google Inc. | US | whitelisted |
860 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
860 | svchost.exe | 74.125.108.201:80 | r4---sn-1gi7znek.gvt1.com | Google Inc. | US | whitelisted |
3596 | jabra-direct.exe | 52.178.79.163:443 | backend-xpress.jabra.com | Microsoft Corporation | NL | suspicious |
1088 | jabra-direct.exe | 52.169.64.244:443 | northeurope-0.in.applicationinsights.azure.com | Microsoft Corporation | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jabraxpressonlineprdstor.blob.core.windows.net |
| unknown |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r4---sn-1gi7znek.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |