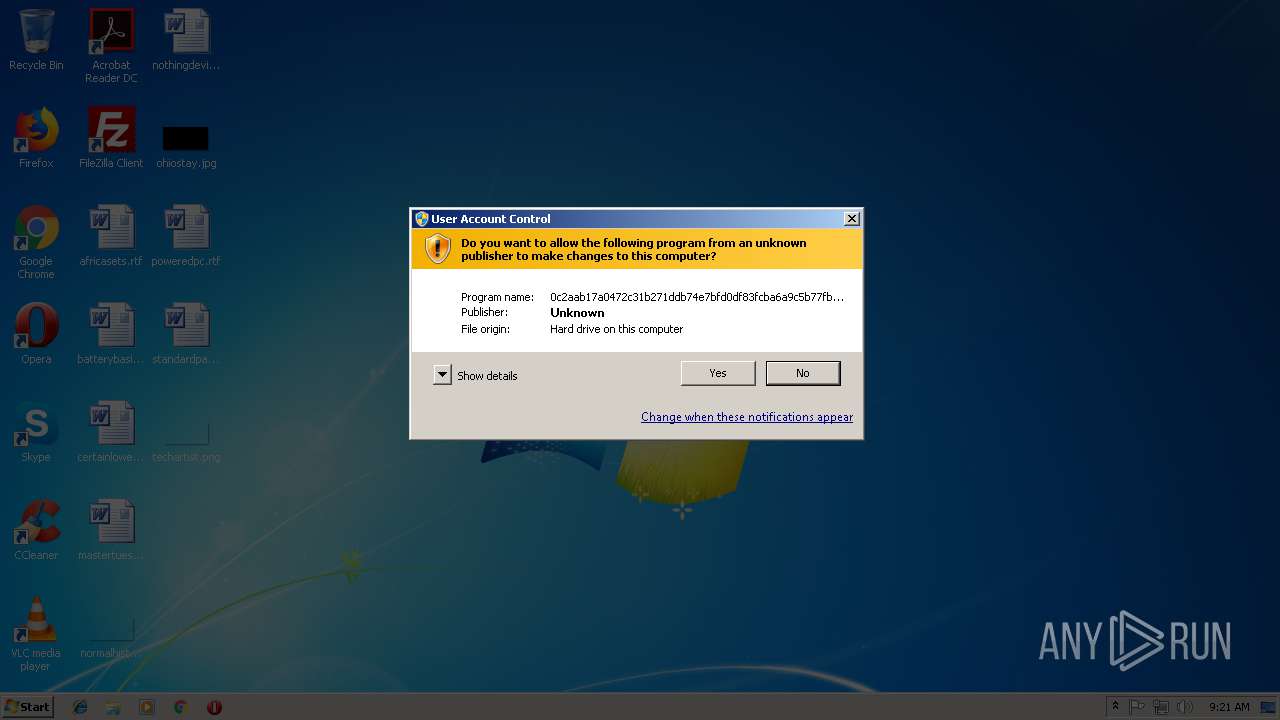
| File name: | 0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7 |
| Full analysis: | https://app.any.run/tasks/993f5671-79e4-461d-bb75-92324c5b0502 |
| Verdict: | Suspicious activity |
| Analysis date: | October 04, 2018, 08:21:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6BC52D3F6C47BFB7B84BF49A57A75B70 |
| SHA1: | 459756E91F0DE21E3B6662C785EA08F49F2ADE6D |
| SHA256: | 0C2AAB17A0472C31B271DDB74E7BFD0DF83FCBA6A9C5B77FB5F6B161BEC45EF7 |
| SSDEEP: | 12288:Fitl4SQlc4FMxapAyN7uJgPZ9yF/fwZaF8A8a:w1eLDpj5uJ6jyB7FD8a |
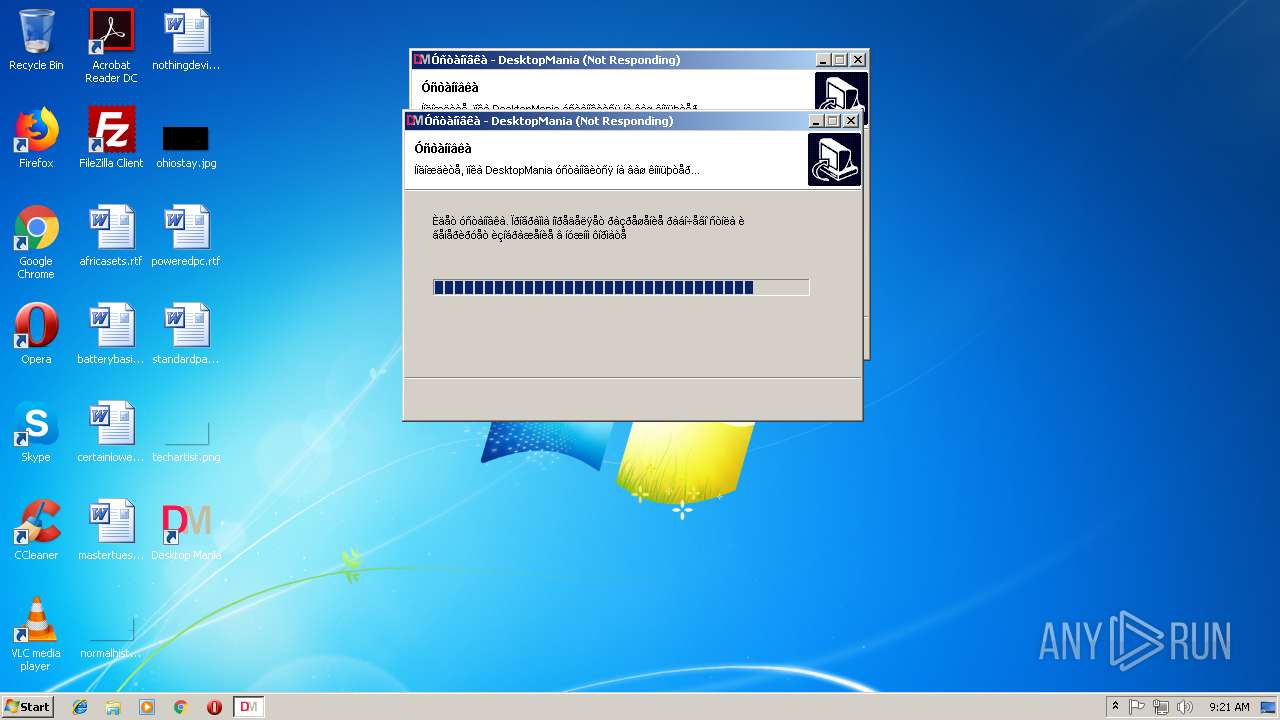
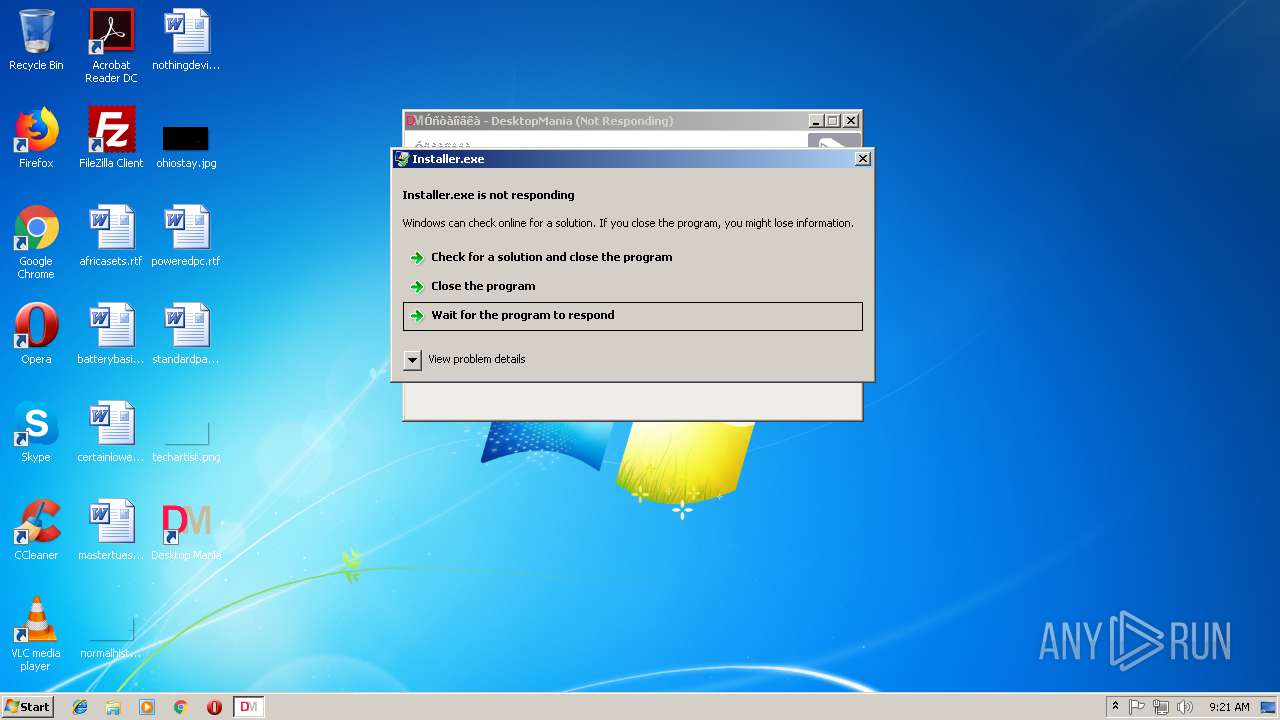
MALICIOUS
Loads dropped or rewritten executable
- Installer.exe (PID: 3704)
Application was dropped or rewritten from another process
- Installer.exe (PID: 3704)
Writes to a start menu file
- Installer.exe (PID: 3704)
SUSPICIOUS
Executable content was dropped or overwritten
- 0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe (PID: 3136)
- Installer.exe (PID: 3704)
Creates files in the program directory
- Installer.exe (PID: 3704)
Creates files in the user directory
- Installer.exe (PID: 3704)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:08:15 14:35:21+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 73728 |
| InitializedDataSize: | 22528 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x131f0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Aug-2014 12:35:21 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 15-Aug-2014 12:35:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00011718 | 0x00011800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51916 |
.itext | 0x00013000 | 0x00000740 | 0x00000800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.57827 |
.data | 0x00014000 | 0x0000108C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.98105 |
.bss | 0x00016000 | 0x00005BAC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001C000 | 0x00000A10 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.3781 |
.tls | 0x0001D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.reloc | 0x0001F000 | 0x000012DC | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.46473 |
.rsrc | 0x00021000 | 0x00002400 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.72749 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.17428 | 830 | UNKNOWN | UNKNOWN | RT_MANIFEST |
4091 | 2.8508 | 144 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.36848 | 196 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.38569 | 304 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.27129 | 964 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.35594 | 824 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.30151 | 604 | UNKNOWN | UNKNOWN | RT_STRING |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.11755 | 224 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.02322 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
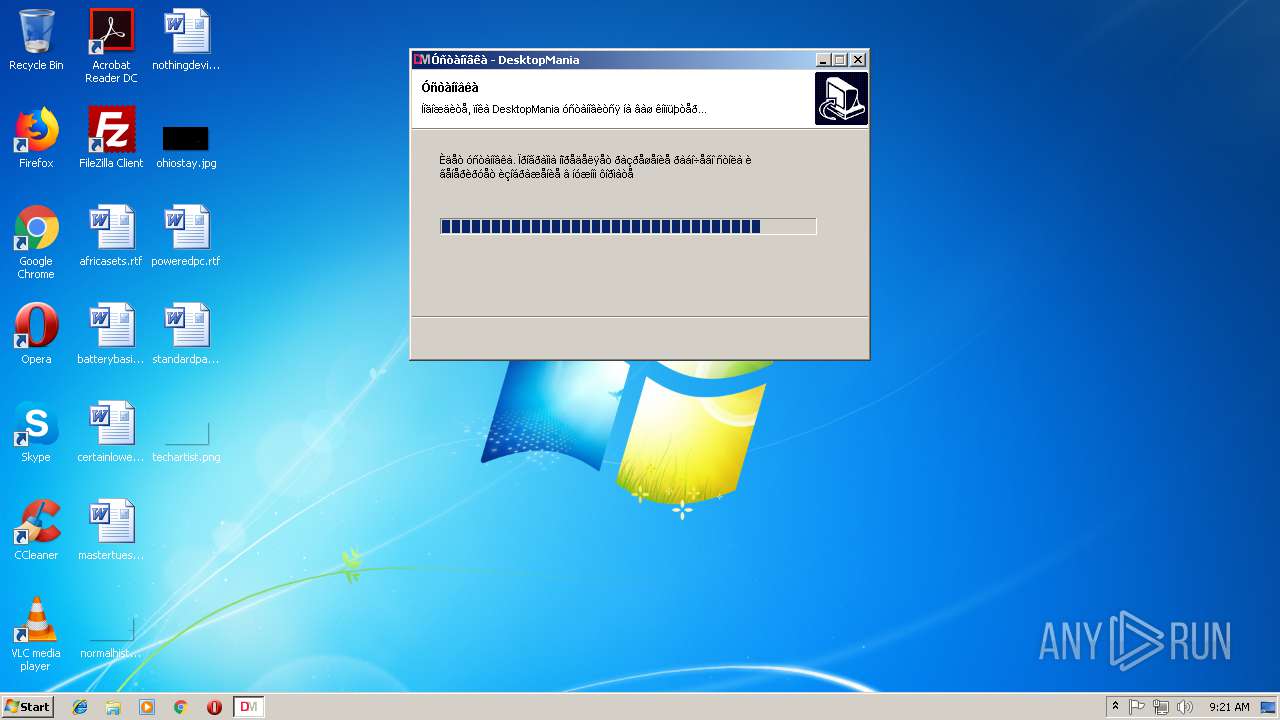
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 648 | "C:\Users\admin\Downloads\0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe" | C:\Users\admin\Downloads\0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3136 | "C:\Users\admin\Downloads\0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe" | C:\Users\admin\Downloads\0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3704 | "C:\Users\admin\AppData\Local\Temp\{AB402B18-26BD-4572-93A4-566D653AE521}\Installer.exe" -install | C:\Users\admin\AppData\Local\Temp\{AB402B18-26BD-4572-93A4-566D653AE521}\Installer.exe | 0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
519
Read events
493
Write events
26
Delete events
0
Modification events
| (PID) Process: | (3136) 0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3136) 0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3704) Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installer_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3704) Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installer_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3704) Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installer_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3704) Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installer_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3704) Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installer_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3704) Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installer_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3704) Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installer_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3704) Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installer_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
7
Suspicious files
1
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3136 | 0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe | C:\Users\admin\AppData\Local\Temp\{AB402B18-26BD-4572-93A4-566D653AE521}\YaLogo.jpg | image | |
MD5:— | SHA256:— | |||
| 3136 | 0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe | C:\Users\admin\AppData\Local\Temp\{AB402B18-26BD-4572-93A4-566D653AE521}\Shell.dll | executable | |
MD5:— | SHA256:— | |||
| 3136 | 0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe | C:\Users\admin\AppData\Local\Temp\{AB402B18-26BD-4572-93A4-566D653AE521}\preview.jpg | image | |
MD5:— | SHA256:— | |||
| 3136 | 0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe | C:\Users\admin\AppData\Local\Temp\{AB402B18-26BD-4572-93A4-566D653AE521}\Installer.exe | executable | |
MD5:— | SHA256:— | |||
| 3136 | 0c2aab17a0472c31b271ddb74e7bfd0df83fcba6a9c5b77fb5f6b161bec45ef7.exe | C:\Users\admin\AppData\Local\Temp\{AB402B18-26BD-4572-93A4-566D653AE521}\preview.dat | binary | |
MD5:— | SHA256:— | |||
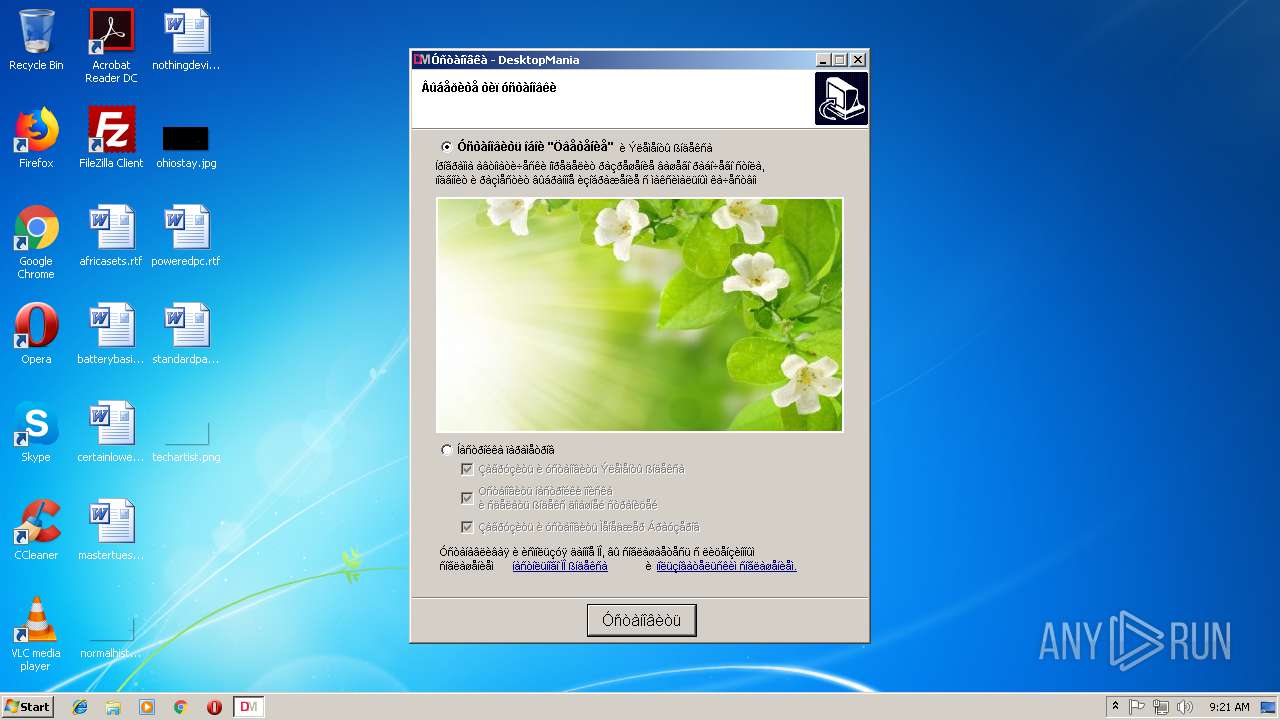
| 3704 | Installer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\DesktopMania\Desktop Mania.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3704 | Installer.exe | C:\Users\admin\Desktop\Desktop Mania.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3704 | Installer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\DesktopMania\Óäàëèòü (Uninstall).lnk | lnk | |
MD5:— | SHA256:— | |||
| 3704 | Installer.exe | C:\Program Files\DesktopMania\UnInstall.exe | executable | |
MD5:— | SHA256:— | |||
| 3704 | Installer.exe | C:\Program Files\DesktopMania\Shell.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3704 | Installer.exe | 144.76.25.173:80 | desktopmania.ru | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
desktopmania.ru |
| whitelisted |
dns.msftncsi.com |
| shared |