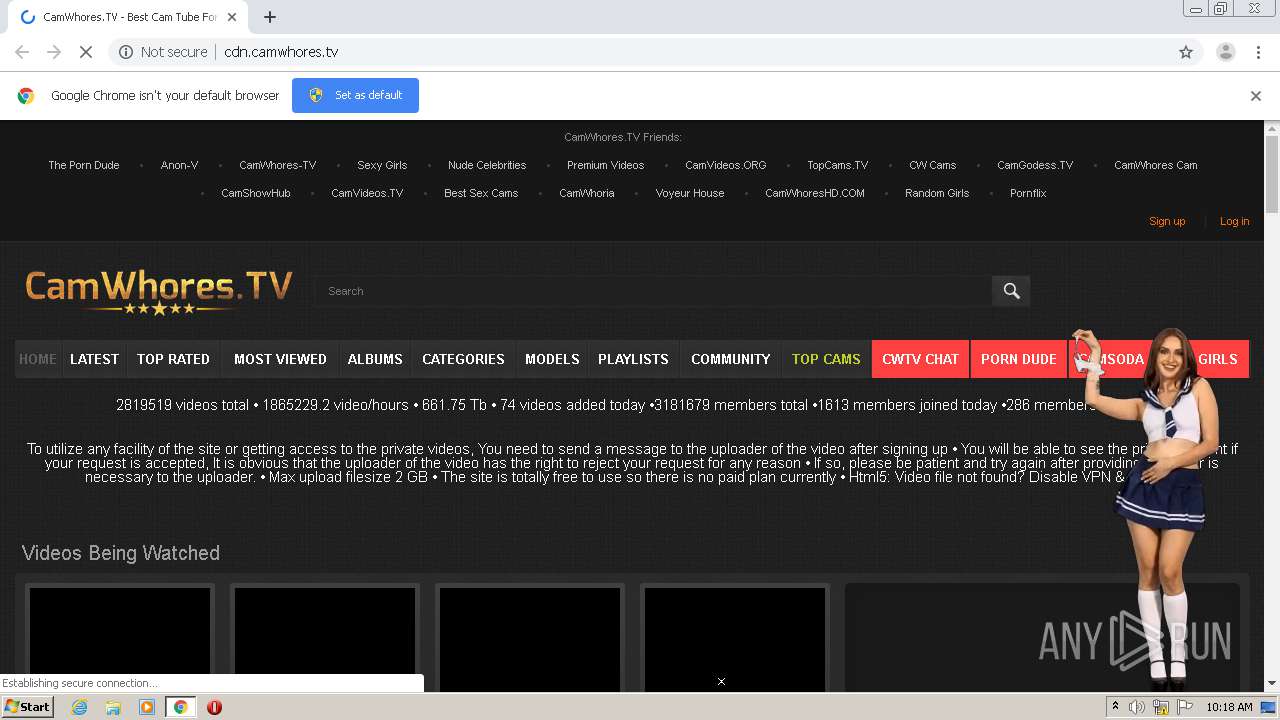
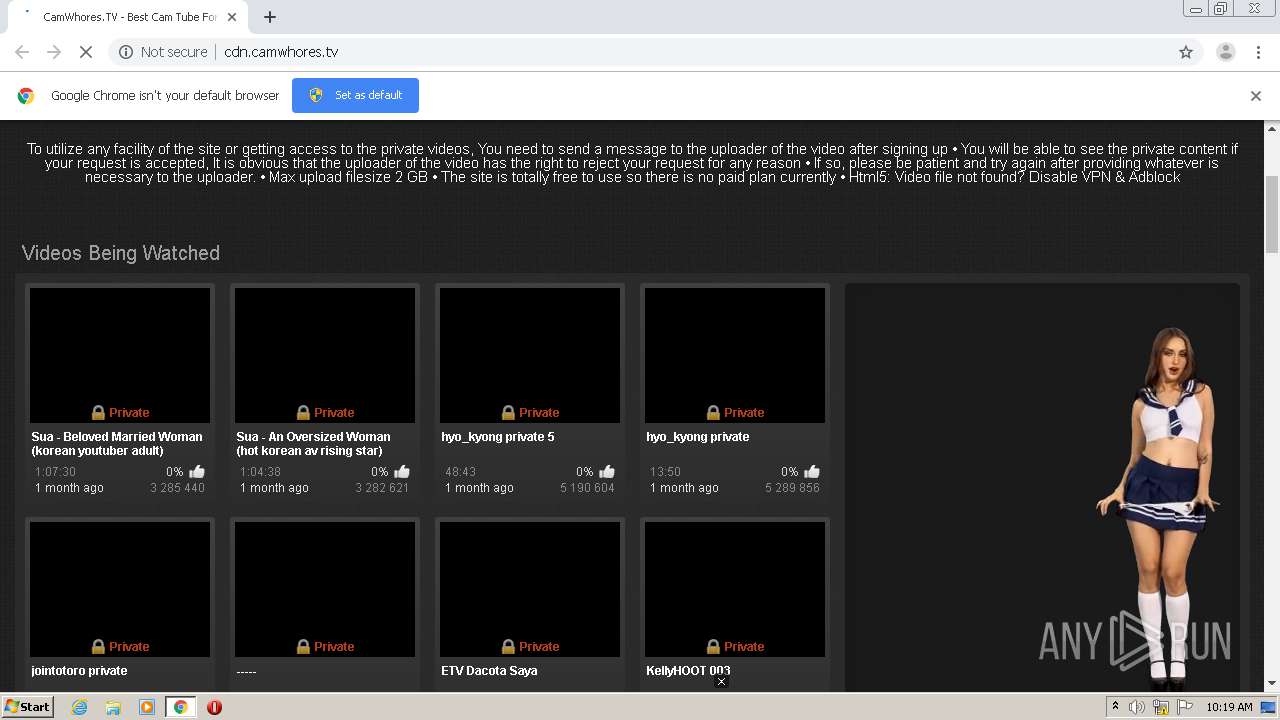
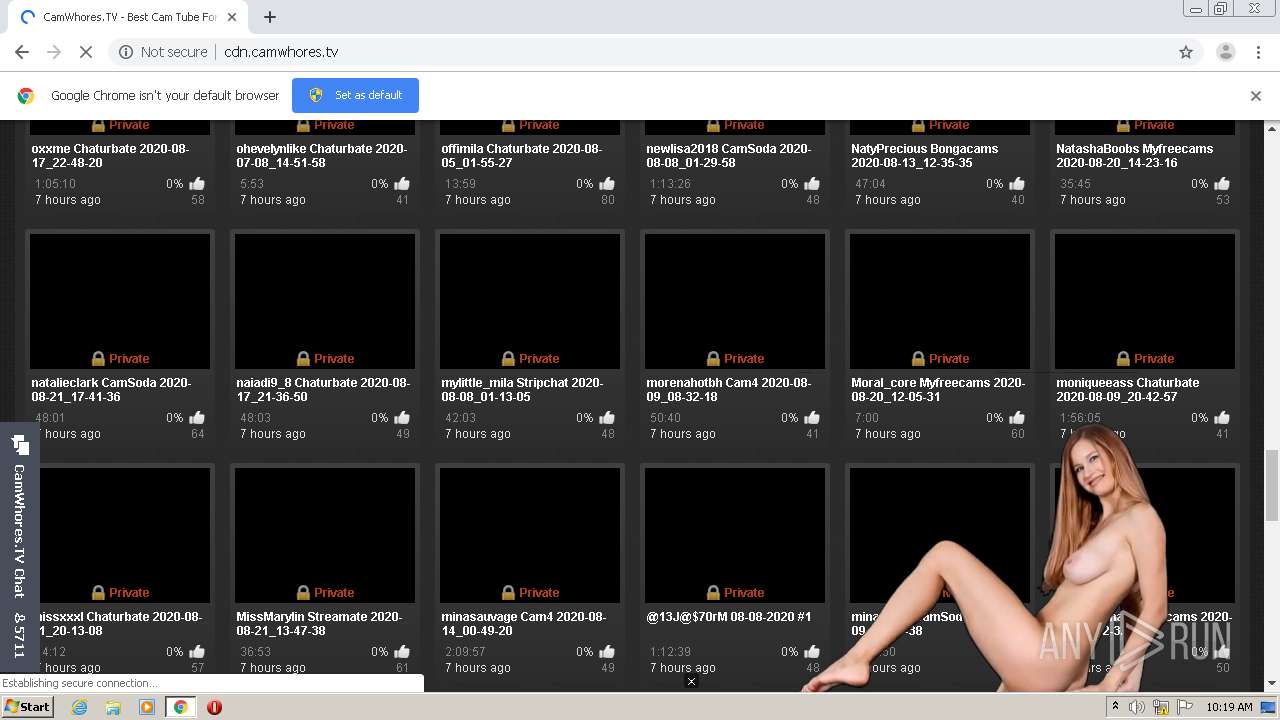
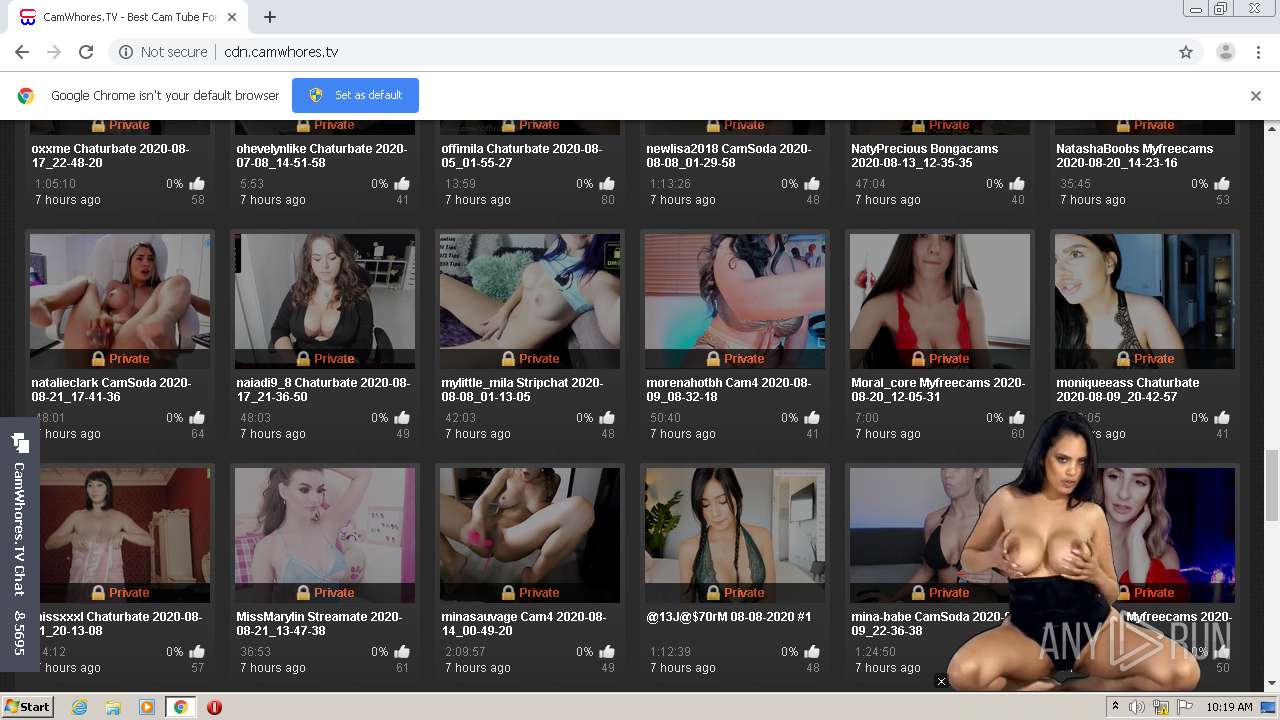
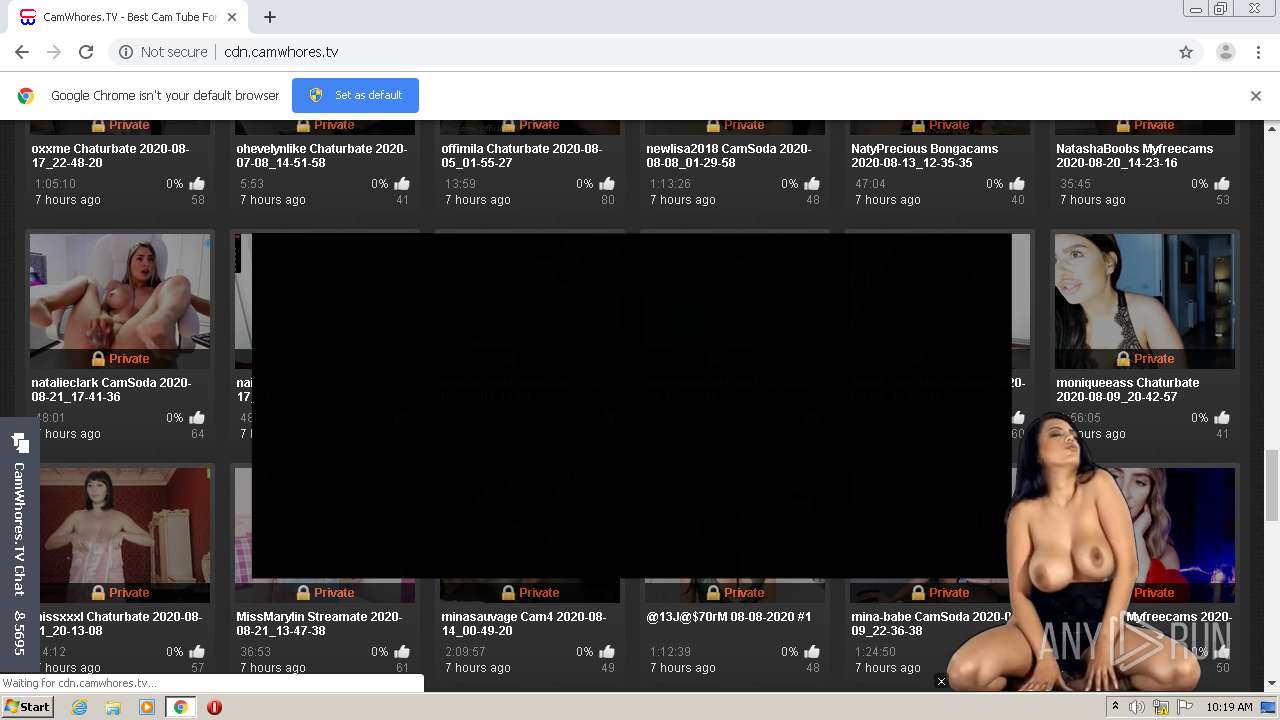
| URL: | http://cdn.camwhores.tv |
| Full analysis: | https://app.any.run/tasks/f1589cbb-9b1d-46b2-b676-ea9cafc4ef5f |
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2020, 09:18:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 62009CB2EFD675C5E813127A42D0D90D |
| SHA1: | AEE769D518D5147B4EB1B965F3703A36FACE5E97 |
| SHA256: | 0C23DD868F0A410114F36CDF8329A47B441536018E77A801E873C0E5C3506A77 |
| SSDEEP: | 3:N1KdBLXvNKXn1:CXXvYXn1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2936)
- chrome.exe (PID: 3544)
Reads settings of System Certificates
- chrome.exe (PID: 3544)
Application launched itself
- chrome.exe (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x7126a9d0,0x7126a9e0,0x7126a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,5655725912133638268,6791691020113198175,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14016723832857119670 --mojo-platform-channel-handle=1052 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5655725912133638268,6791691020113198175,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18197064159357641804 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5655725912133638268,6791691020113198175,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13771970588642098210 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5655725912133638268,6791691020113198175,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14493605758124475118 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5655725912133638268,6791691020113198175,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9913991630028882615 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5655725912133638268,6791691020113198175,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=820232986970687228 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5655725912133638268,6791691020113198175,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6087574677478334123 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5655725912133638268,6791691020113198175,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5903091768258073293 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,5655725912133638268,6791691020113198175,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6802761094608998131 --mojo-platform-channel-handle=3936 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
630
Read events
566
Write events
61
Delete events
3
Modification events
| (PID) Process: | (2936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3648) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2936-13242907129437750 |
Value: 259 | |||
| (PID) Process: | (2936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2936) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
70
Text files
83
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3ef7833a-dfe5-4613-8e2b-8ab52cc53499.tmp | — | |
MD5:— | SHA256:— | |||
| 2936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:142AFC7F980CB38310D0680F2E8907CF | SHA256:3D5E5DF95E28CF65C77882748077EC52706AF02F8D869E188B6D16F782F82F44 | |||
| 2936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
| 2936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe2640.TMP | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
| 2936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFe268f.TMP | text | |
MD5:142AFC7F980CB38310D0680F2E8907CF | SHA256:3D5E5DF95E28CF65C77882748077EC52706AF02F8D869E188B6D16F782F82F44 | |||
| 2936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe2892.TMP | — | |
MD5:— | SHA256:— | |||
| 2936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:AFDDC99E148FD40EED8086EE532B61C4 | SHA256:3F1C412561D08C113C1561C9D273FBA00DAB5481B4AC1428FCC91D9285BA7E1E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
85
TCP/UDP connections
103
DNS requests
73
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3544 | chrome.exe | GET | 200 | 89.248.174.159:80 | http://cdn.camwhores.tv/styles/all-responsive-metal.css?v=3.5.6 | SC | text | 18.3 Kb | whitelisted |
3544 | chrome.exe | GET | 200 | 89.248.174.159:80 | http://cdn.camwhores.tv/ | SC | html | 14.6 Kb | whitelisted |
3544 | chrome.exe | GET | 200 | 205.185.208.17:80 | http://s2.static.cfgr3.com/popin/latest/popin-min.js | US | text | 2.76 Kb | suspicious |
3544 | chrome.exe | GET | 200 | 89.248.174.159:80 | http://cdn.camwhores.tv/images/pattern.gif | SC | image | 1.68 Kb | whitelisted |
3544 | chrome.exe | GET | 200 | 89.248.174.159:80 | http://cdn.camwhores.tv/styles/jquery.fancybox-metal.css?v=5.3 | SC | text | 1.58 Kb | whitelisted |
3544 | chrome.exe | GET | 200 | 89.248.174.159:80 | http://cdn.camwhores.tv/js/main.min.js?v=5.3 | SC | text | 271 Kb | whitelisted |
3544 | chrome.exe | GET | 200 | 89.248.174.159:80 | http://cdn.camwhores.tv/t6e6d2454fa5.js | SC | text | 34.2 Kb | whitelisted |
3544 | chrome.exe | GET | 200 | 89.248.174.159:80 | http://cdn.camwhores.tv/images/logo.png | SC | image | 26.8 Kb | whitelisted |
3544 | chrome.exe | GET | 200 | 89.248.174.159:80 | http://cdn.camwhores.tv/images/btn-search.png | SC | image | 2.08 Kb | whitelisted |
3544 | chrome.exe | GET | 200 | 89.248.174.159:80 | http://cdn.camwhores.tv/images/ico-later.png | SC | image | 1.05 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3544 | chrome.exe | 172.64.172.25:443 | go.strpjmp.com | Cloudflare Inc | US | unknown |
3544 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3544 | chrome.exe | 89.248.174.159:80 | cdn.camwhores.tv | Quasi Networks LTD. | SC | unknown |
3544 | chrome.exe | 172.217.22.72:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3544 | chrome.exe | 172.67.71.107:443 | widgets.skyprivate.com | — | US | unknown |
3544 | chrome.exe | 151.101.2.133:80 | player.h-cdn.com | Fastly | US | malicious |
3544 | chrome.exe | 205.185.208.17:80 | s2.static.cfgr3.com | Highwinds Network Group, Inc. | US | suspicious |
3544 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
3544 | chrome.exe | 205.185.216.10:80 | static.selfpua.com | Highwinds Network Group, Inc. | US | whitelisted |
3544 | chrome.exe | 104.31.10.158:80 | www.chatbro.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.camwhores.tv |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
player.h-cdn.com |
| malicious |
s2.static.cfgr3.com |
| suspicious |
widgets.skyprivate.com |
| unknown |
static.selfpua.com |
| malicious |
www.google.com |
| malicious |
www.chatbro.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |