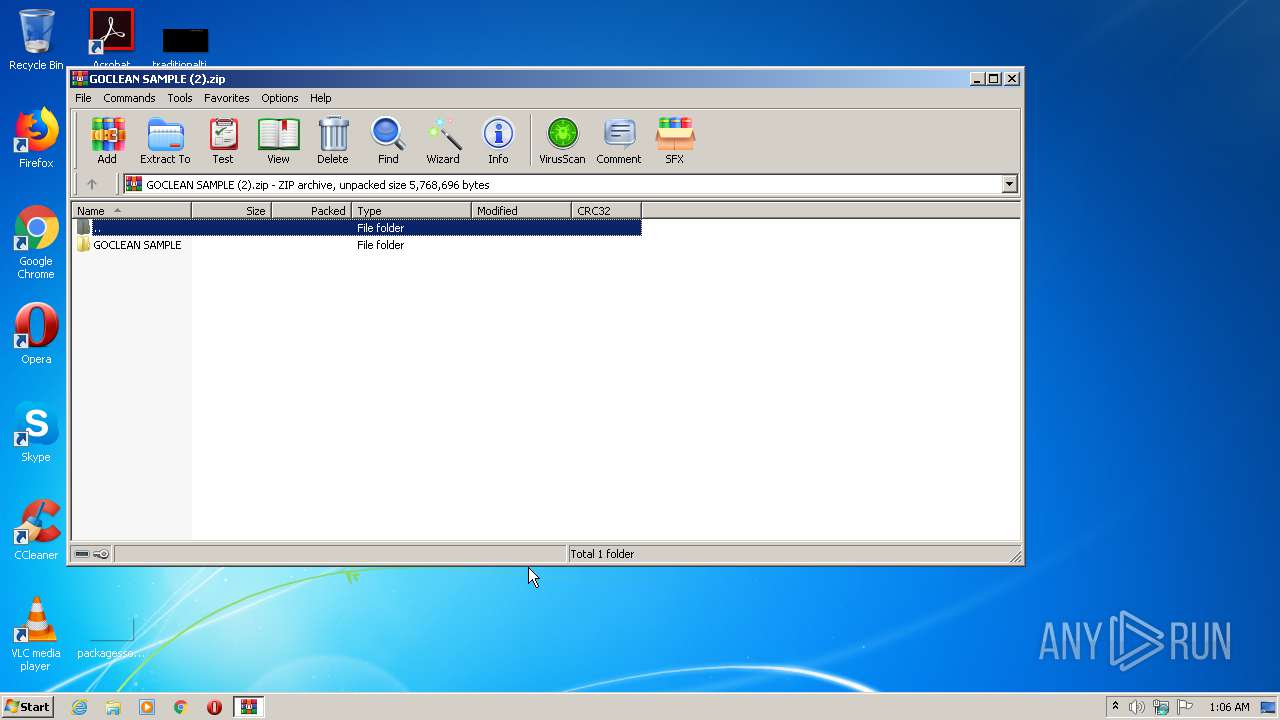
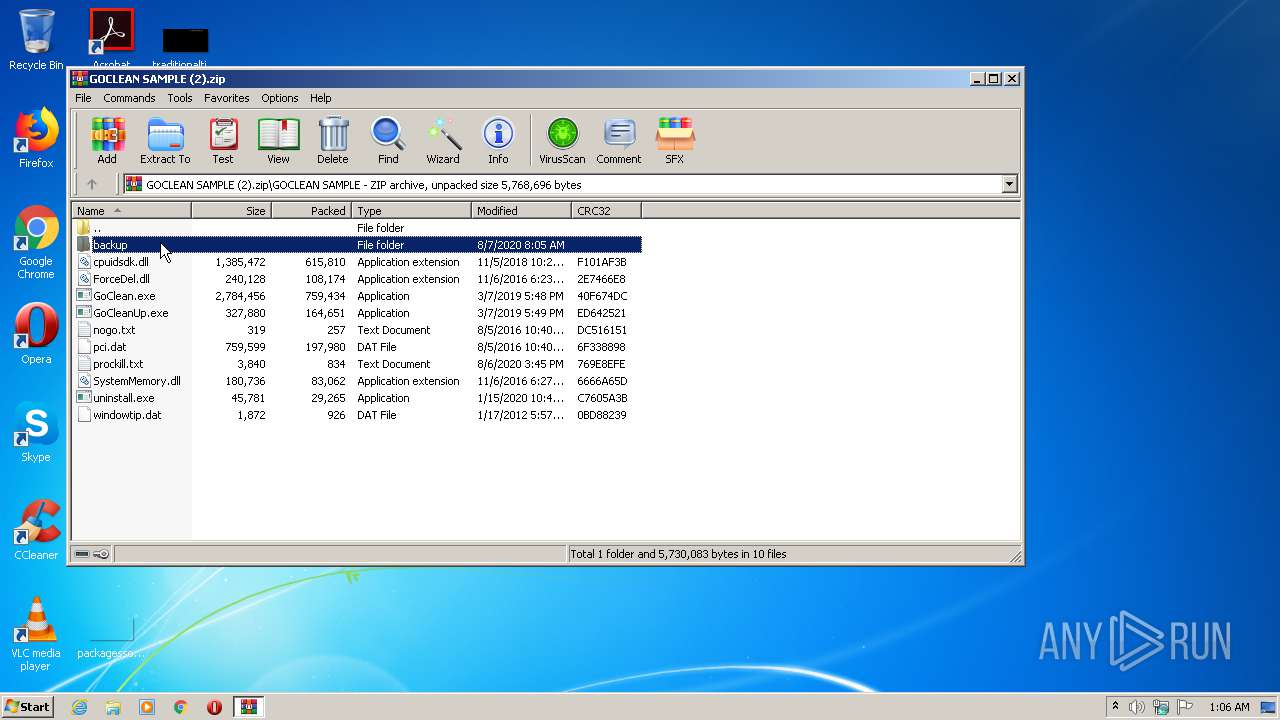
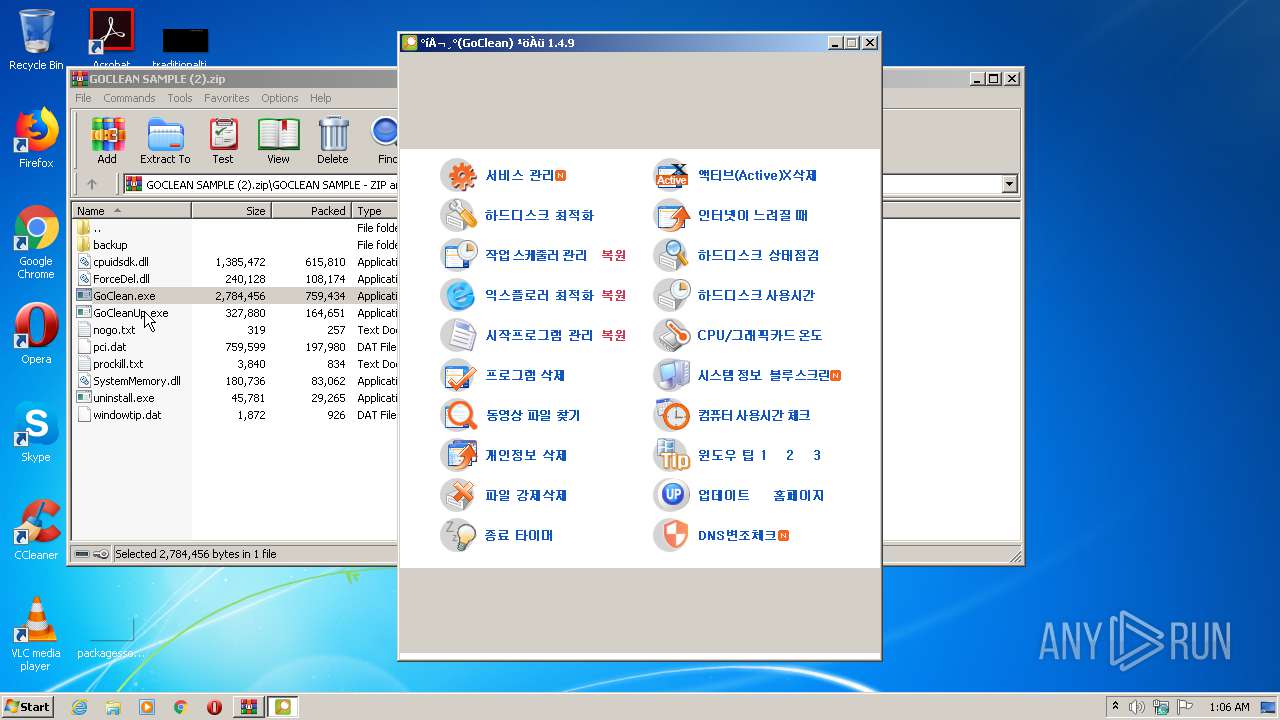
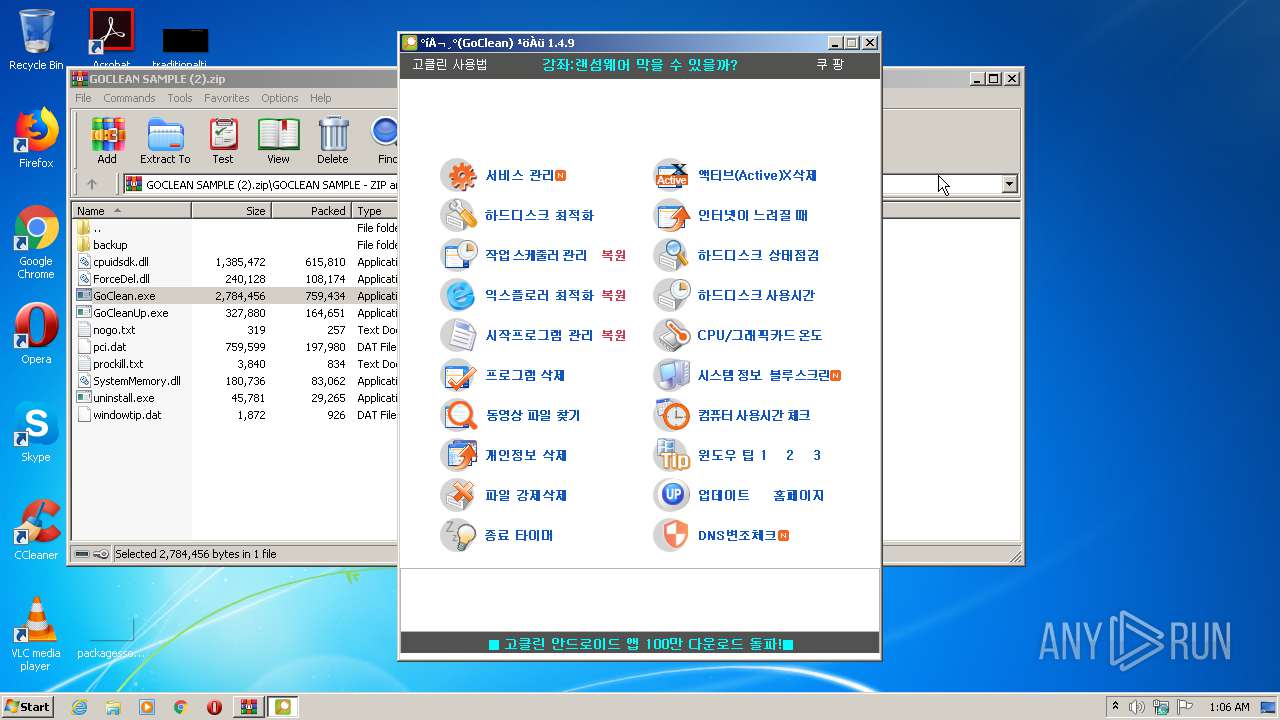
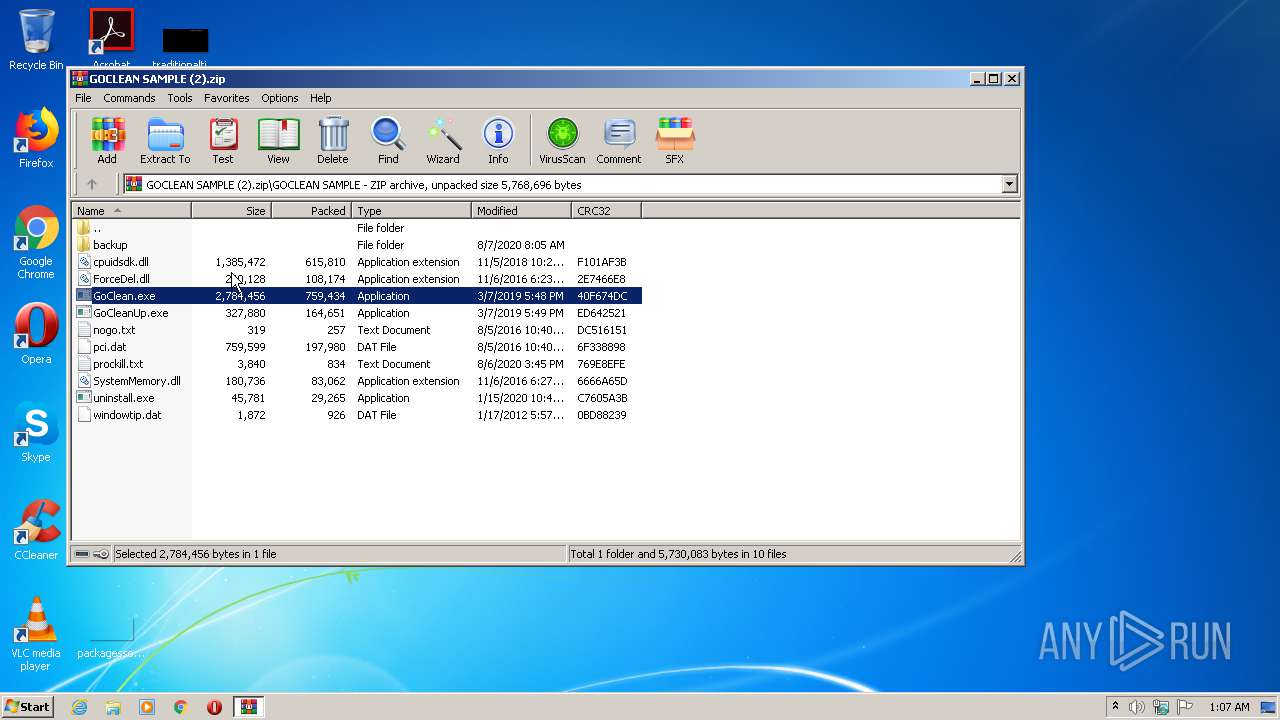
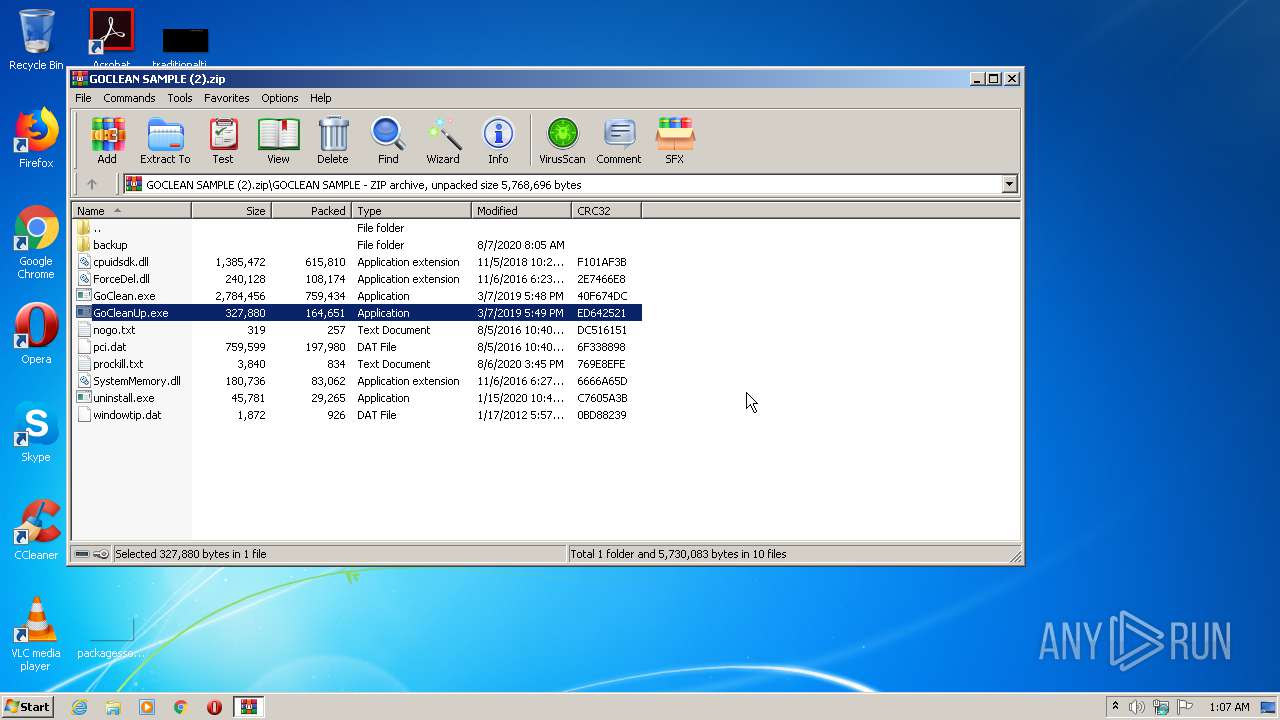
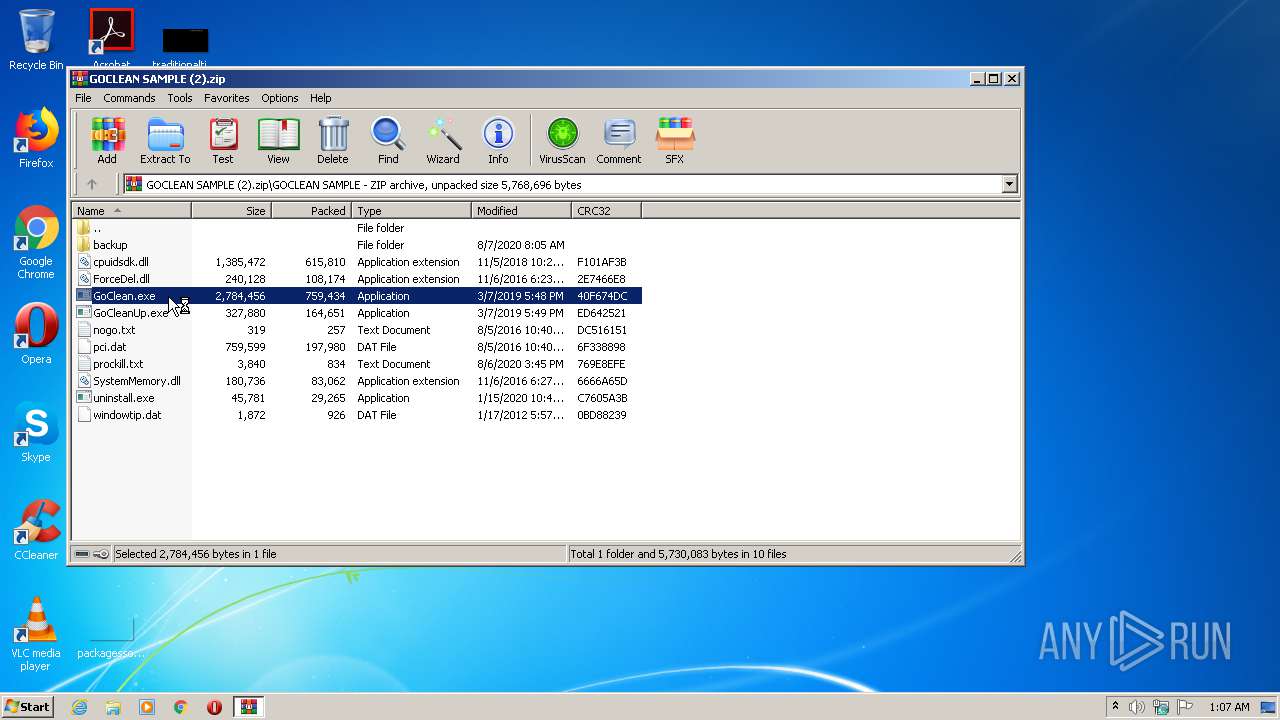
| File name: | GOCLEAN SAMPLE (2).zip |
| Full analysis: | https://app.any.run/tasks/a1159c65-2df1-49f9-886d-b15507528a1d |
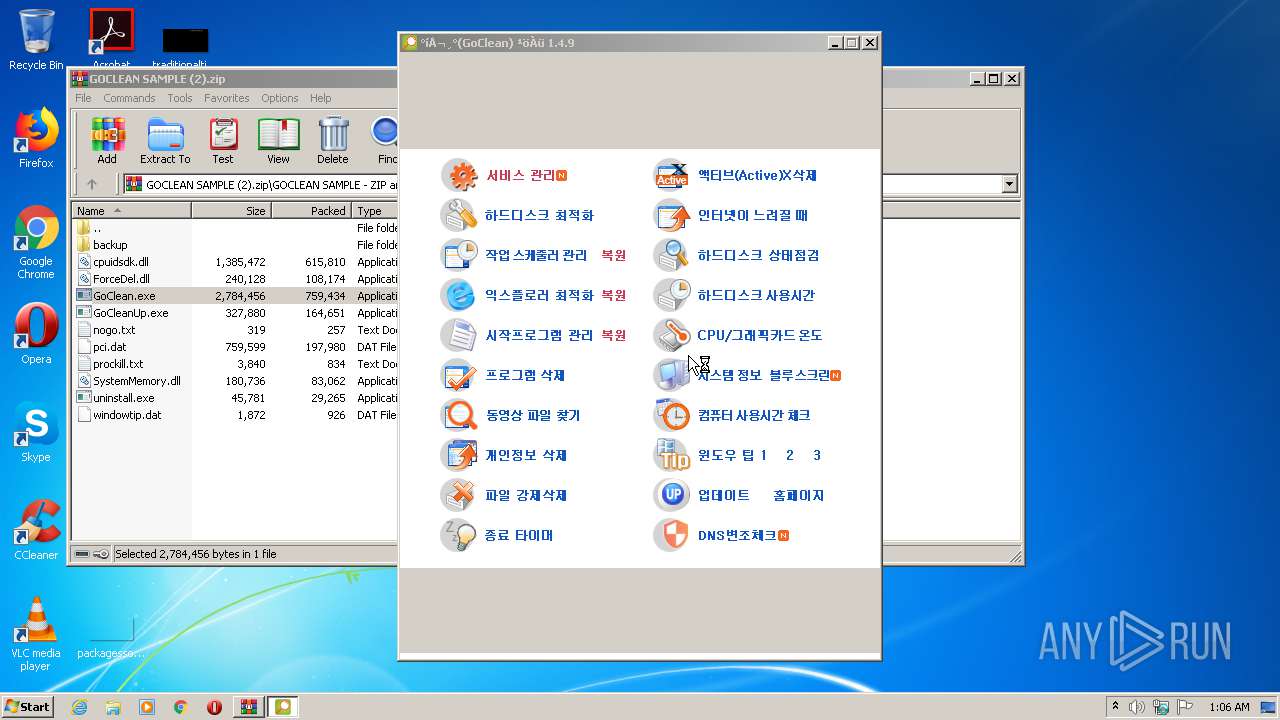
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2020, 00:06:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8ED2ECDAC7AEC5332B5A992EAE0B3D8F |
| SHA1: | F08E40531DB1DDB21DD224DBE59B5C8925C870FD |
| SHA256: | 0C215B7BE57AC955A45E630784C0E61E4FEDAA5FA87178ADD6CBEF1FBECE91FB |
| SSDEEP: | 49152:ZRQzi5i9hIpIBvg95YtmE1Xzul4yN6ke7l2pfnUYlOtX:vkjbIpIBvggtmGc4yNppZqX |
MALICIOUS
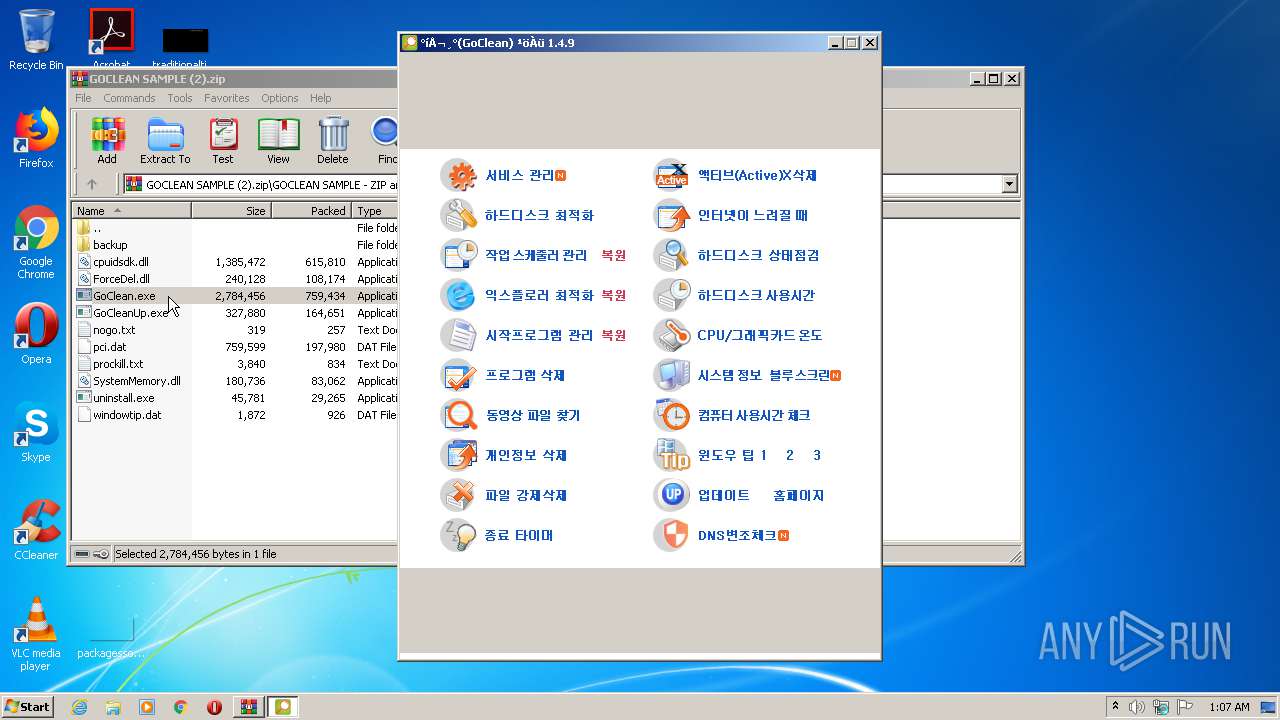
Application was dropped or rewritten from another process
- GoClean.exe (PID: 3900)
- GoClean.exe (PID: 3524)
- GoCleanUp.exe (PID: 2672)
- GoClean.exe (PID: 1728)
- GoCleanUp.exe (PID: 2956)
- GoClean.exe (PID: 1248)
Changes settings of System certificates
- GoClean.exe (PID: 3900)
SUSPICIOUS
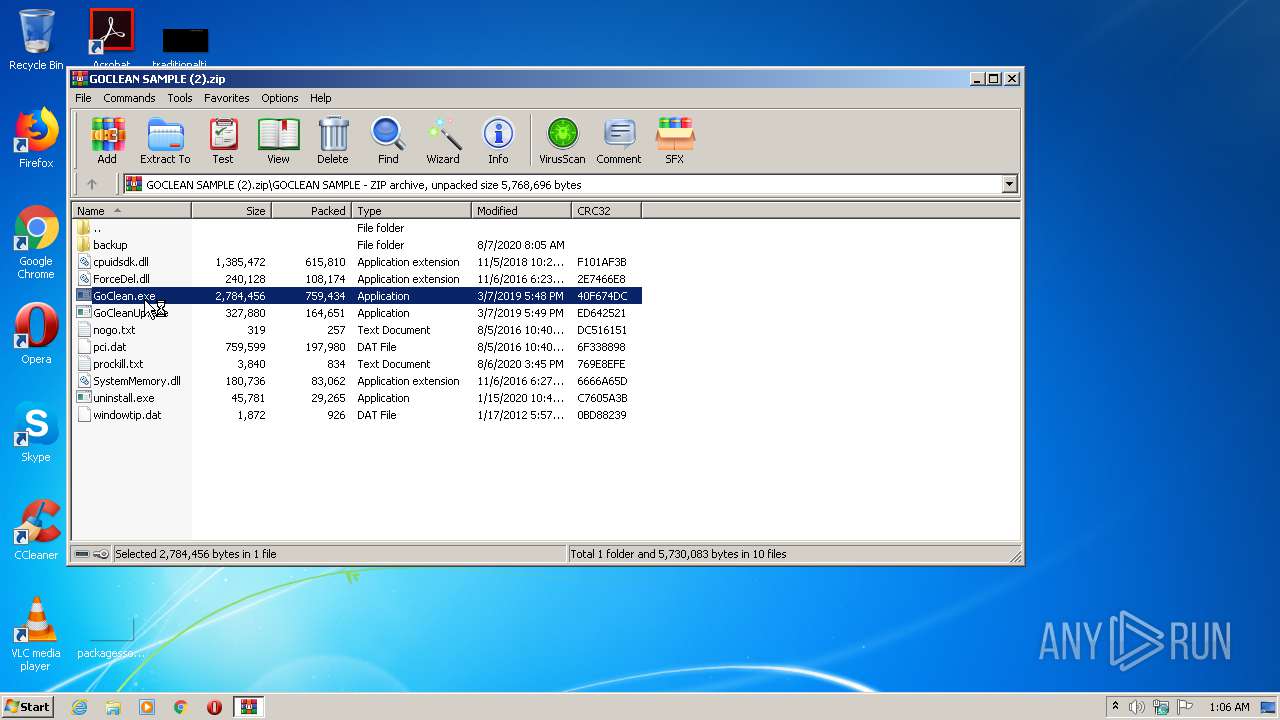
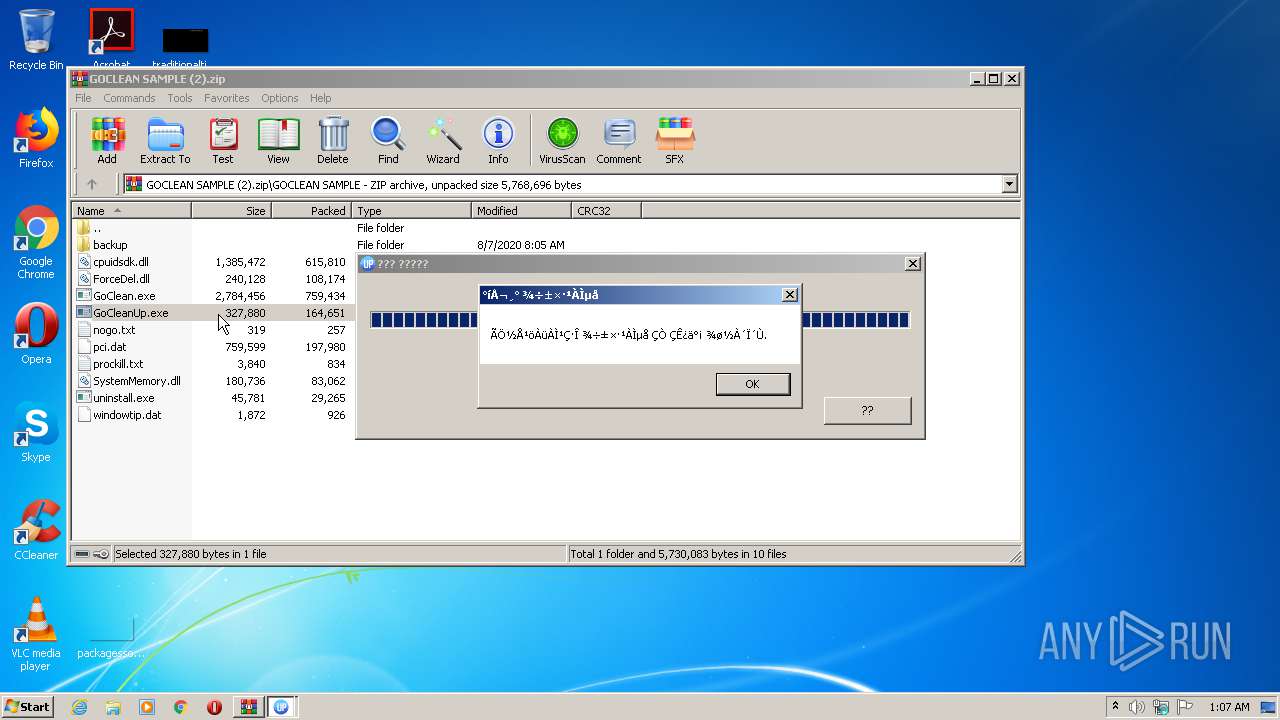
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2660)
Reads Internet Cache Settings
- GoClean.exe (PID: 3900)
- GoClean.exe (PID: 1728)
- GoCleanUp.exe (PID: 2672)
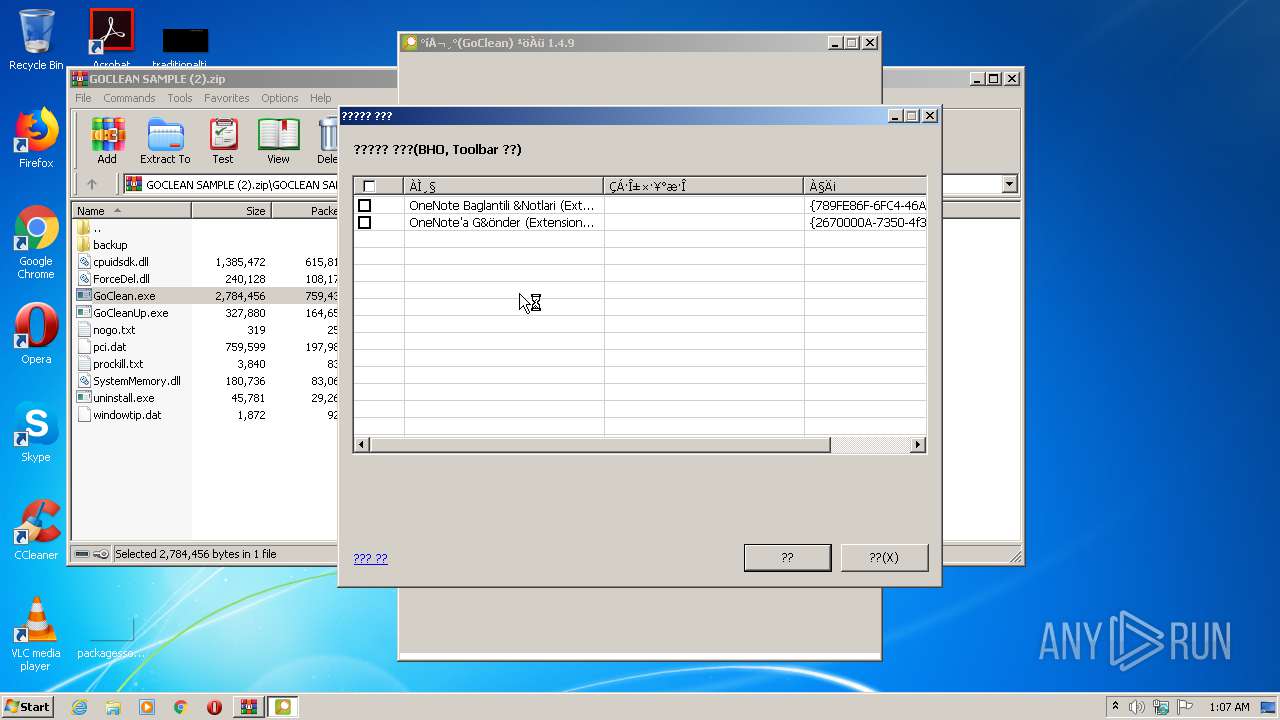
Reads internet explorer settings
- GoClean.exe (PID: 3900)
- GoClean.exe (PID: 1728)
Creates files in the user directory
- GoClean.exe (PID: 3900)
- GoClean.exe (PID: 1728)
Adds / modifies Windows certificates
- GoClean.exe (PID: 3900)
Starts Internet Explorer
- GoClean.exe (PID: 3900)
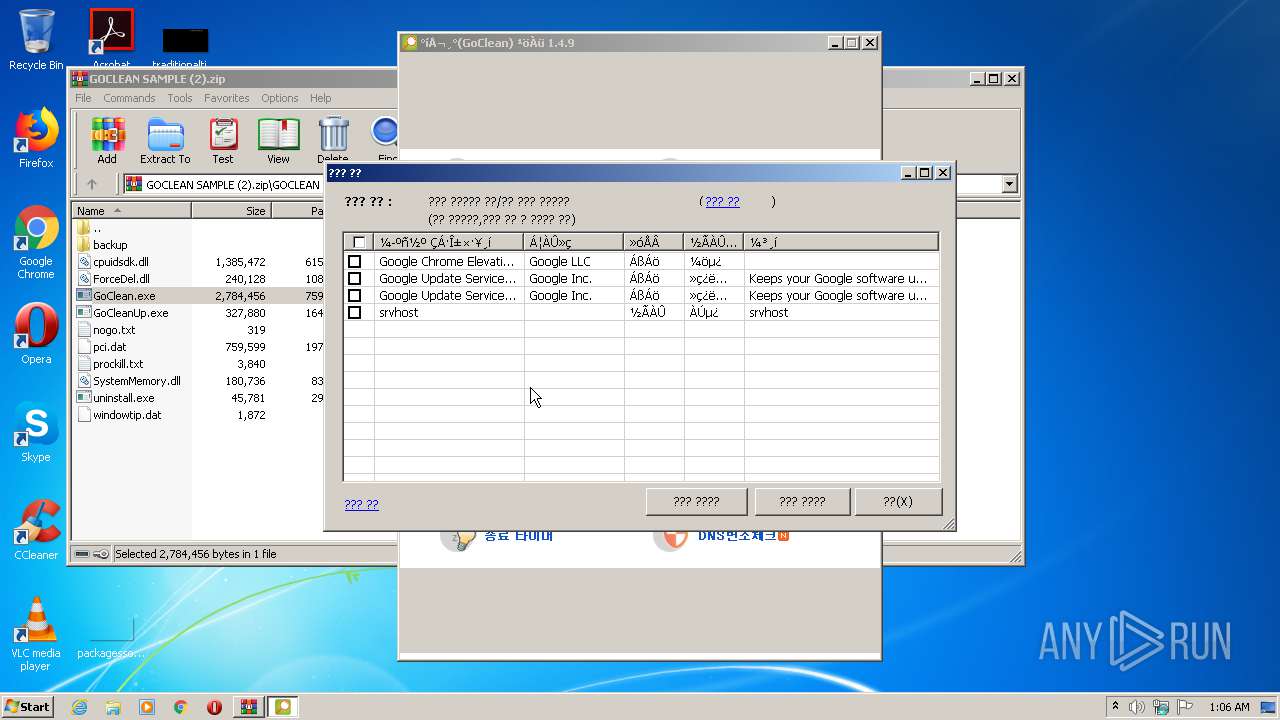
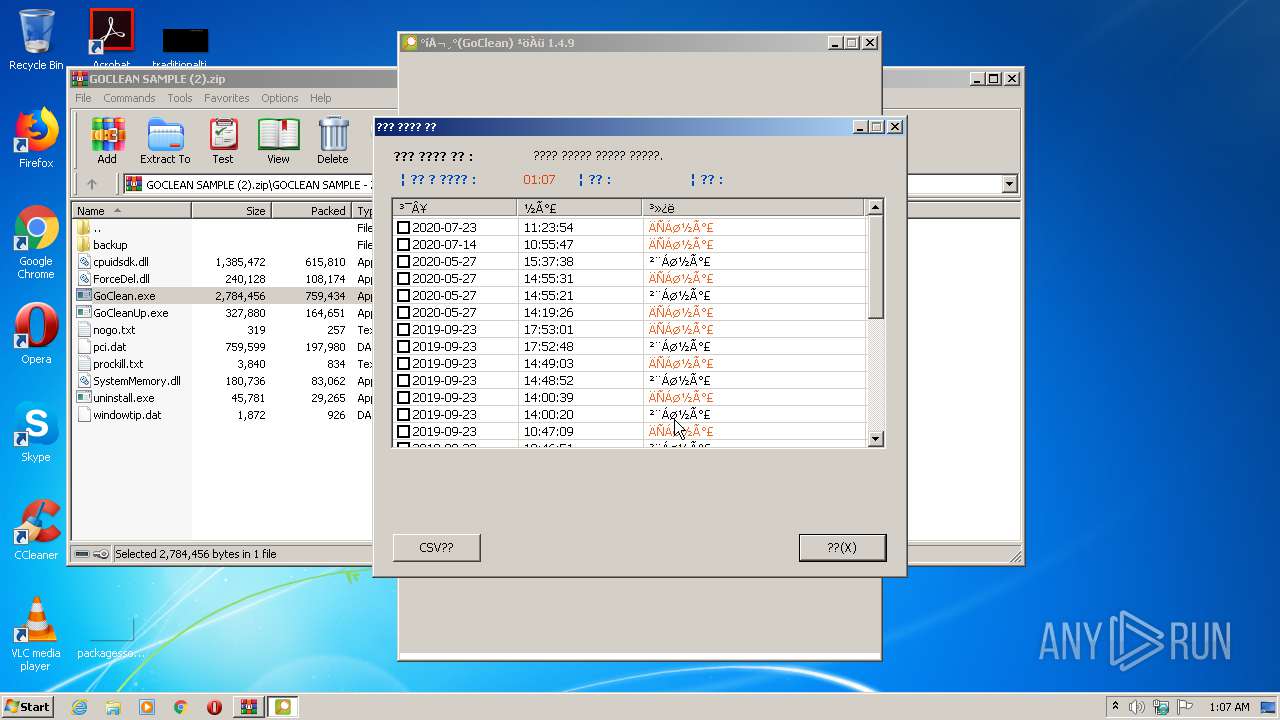
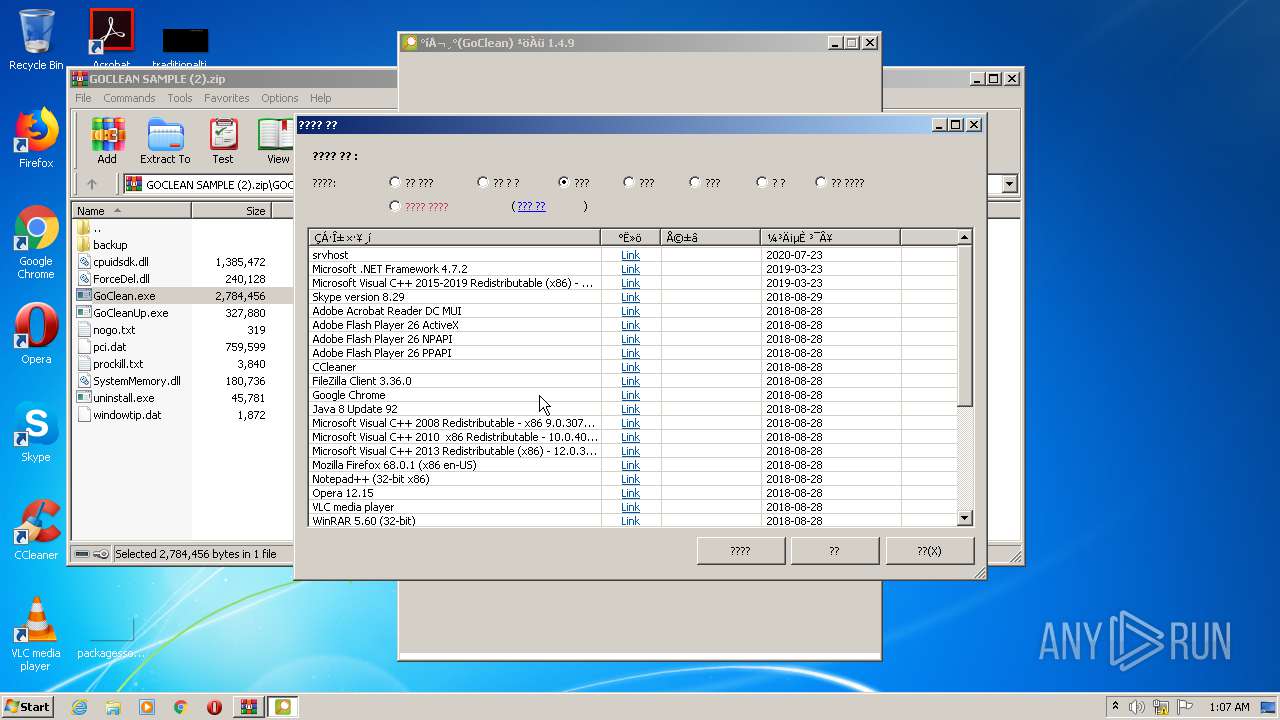
Searches for installed software
- GoClean.exe (PID: 1728)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 2972)
Changes internet zones settings
- iexplore.exe (PID: 3656)
Reads internet explorer settings
- iexplore.exe (PID: 2972)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3656)
Reads settings of System Certificates
- GoClean.exe (PID: 1728)
- iexplore.exe (PID: 3656)
Changes settings of System certificates
- iexplore.exe (PID: 3656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:08:07 08:05:03 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | GOCLEAN SAMPLE/backup/ |
Total processes
55
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1248 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.16417\GOCLEAN SAMPLE\GoClean.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.16417\GOCLEAN SAMPLE\GoClean.exe | — | WinRAR.exe | |||||||||||
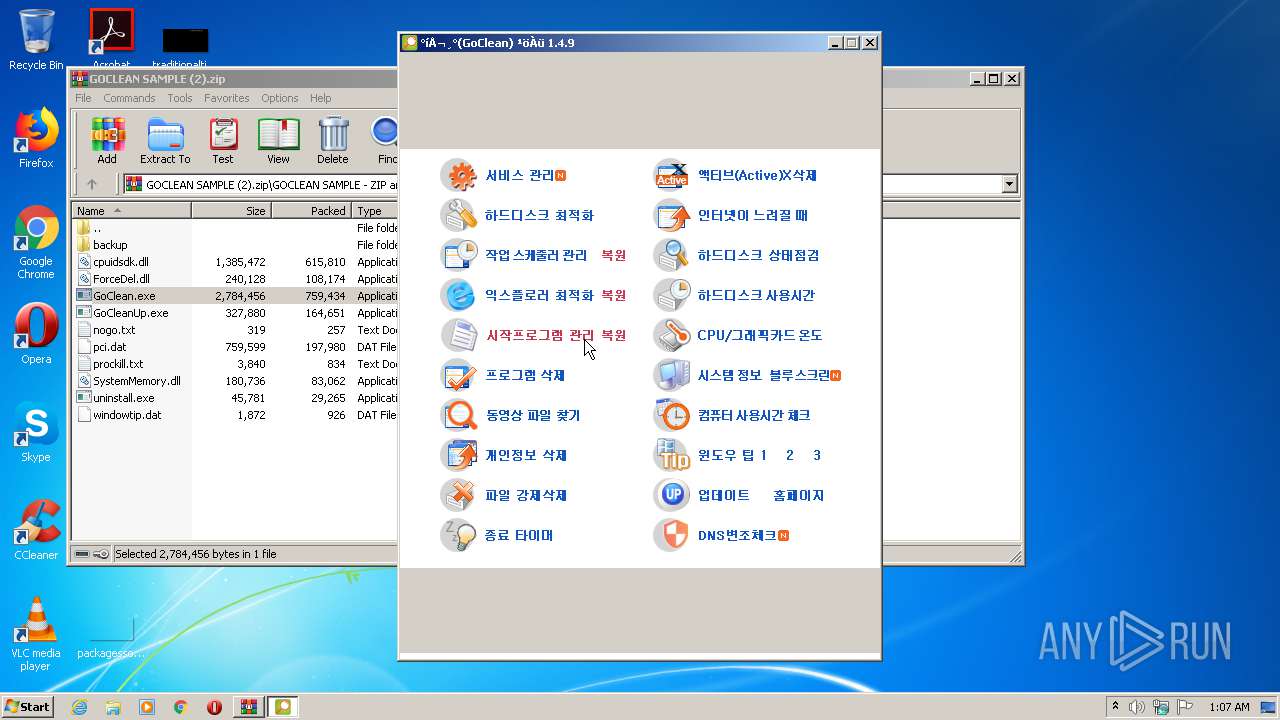
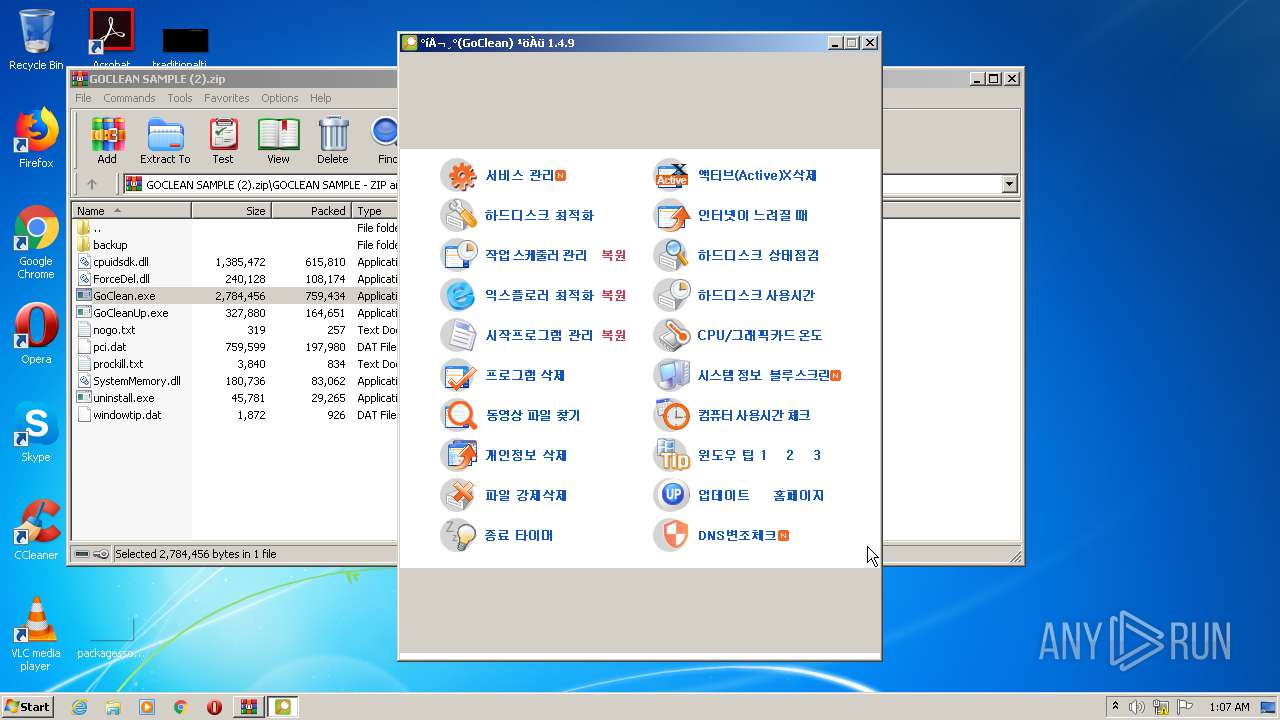
User: admin Company: 고클린 Integrity Level: MEDIUM Description: 고클린 Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1728 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.16417\GOCLEAN SAMPLE\GoClean.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.16417\GOCLEAN SAMPLE\GoClean.exe | WinRAR.exe | ||||||||||||
User: admin Company: 고클린 Integrity Level: HIGH Description: 고클린 Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\GOCLEAN SAMPLE (2).zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2672 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.14980\GOCLEAN SAMPLE\GoCleanUp.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.14980\GOCLEAN SAMPLE\GoCleanUp.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.14980\GOCLEAN SAMPLE\GoCleanUp.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.14980\GOCLEAN SAMPLE\GoCleanUp.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3656 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3524 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\GoClean.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\GoClean.exe | — | WinRAR.exe | |||||||||||
User: admin Company: 고클린 Integrity Level: MEDIUM Description: 고클린 Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3656 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.gobest.kr/goclean/goclean-ad-new.htm | C:\Program Files\Internet Explorer\iexplore.exe | GoClean.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3900 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\GoClean.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\GoClean.exe | WinRAR.exe | ||||||||||||
User: admin Company: 고클린 Integrity Level: HIGH Description: 고클린 Exit code: 2 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
1 787
Read events
1 629
Write events
153
Delete events
5
Modification events
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\134\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\134\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GOCLEAN SAMPLE (2).zip | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2660) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\134\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
18
Suspicious files
10
Text files
119
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\backup\task\HPLJCustParticipation | xml | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\backup\startprog\2020¦G08+·06+--15++35¦-15+-.reg | text | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\backup\task\OneDrive Standalone Update Task v2 | xml | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\backup\task\OneDrive Standalone Update Task-S-1-5-18 | xml | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\backup\startprog\2020¦G08+·06+--15++35¦-34+-.reg | text | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\backup\startprog\2020¦G08+·06+--15++33¦-59+-.reg | text | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\backup\task\OneDrive Standalone Update Task-S-1-5-21-1461305-839808047-932995037-236329 | xml | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\backup\task\RtHDVBg_Dolby | xml | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\backup\task\Query-OfficeDocuments | xml | |
MD5:— | SHA256:— | |||
| 2660 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2660.12924\GOCLEAN SAMPLE\backup\startprog\2020¦G08+·06+--15++34¦-57+-.reg | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
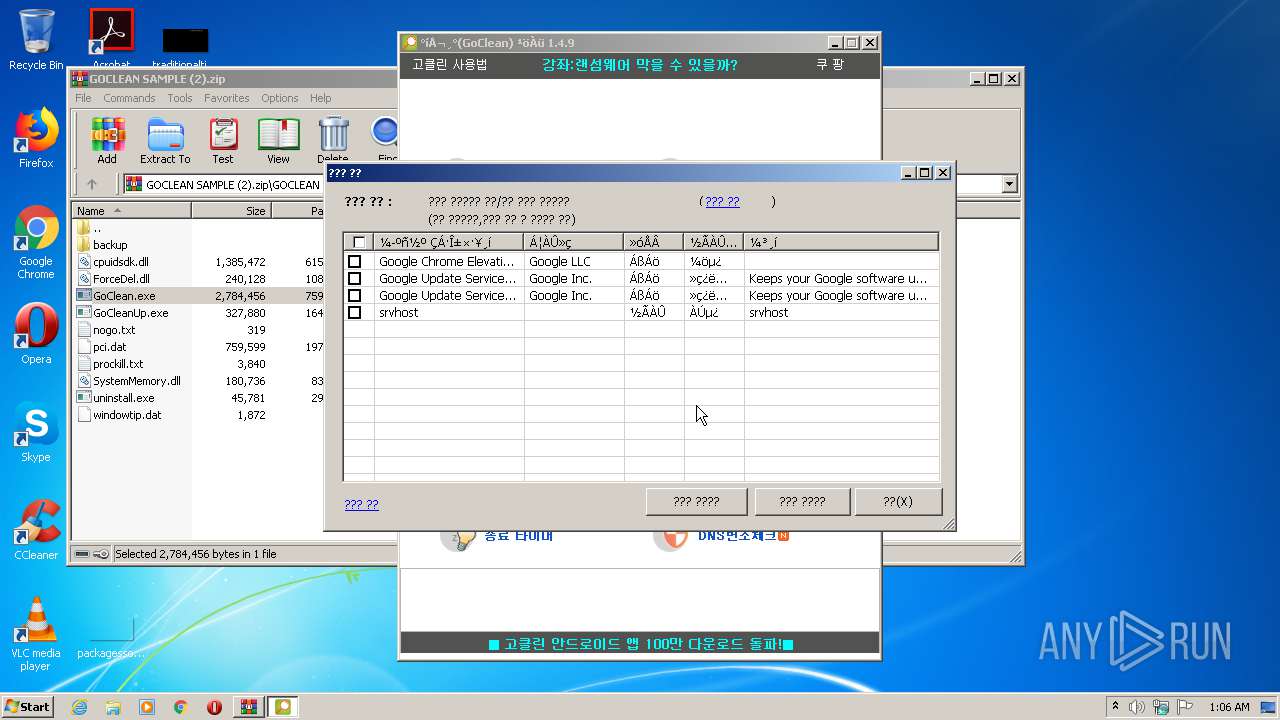
HTTP(S) requests
38
TCP/UDP connections
23
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3900 | GoClean.exe | GET | 200 | 143.204.201.66:80 | http://www.gobest.kr/adfile/ad-m-top-147.htm | US | html | 3.67 Kb | whitelisted |
3900 | GoClean.exe | GET | 200 | 143.204.201.66:80 | http://www.gobest.kr/adfile/top-2.htm | US | html | 1.15 Kb | whitelisted |
3900 | GoClean.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDM9j8%2B94pW6ggAAAAATZ8E | US | der | 472 b | whitelisted |
3900 | GoClean.exe | GET | 200 | 14.0.115.222:80 | http://img.mobon.net/Frtb/common/css/mobon_reset.css?201706292 | KR | text | 9.73 Kb | suspicious |
3900 | GoClean.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3900 | GoClean.exe | GET | 200 | 14.0.115.222:80 | http://img.mobon.net/Frtb/common/css/mobon_reset.css?201706292 | KR | text | 9.73 Kb | suspicious |
3900 | GoClean.exe | GET | 200 | 14.0.115.222:80 | http://img.mobon.net/js/mobonStorage.js | KR | text | 2.93 Kb | suspicious |
3900 | GoClean.exe | GET | 200 | 14.0.115.222:80 | http://img.mobon.net/Frtb/js/frame_default_script_S.js | KR | text | 24.2 Kb | suspicious |
3900 | GoClean.exe | GET | 200 | 14.0.115.222:80 | http://img.mobon.net/js/mobonStorage.js | KR | text | 9.73 Kb | suspicious |
3900 | GoClean.exe | GET | 200 | 14.0.115.222:80 | http://img.mobon.net/ad/imgfile//2020/YnVuMm1vYmlsZQ==/342fd19f-ab77-4ff3-b70b-89da6072c58003.jpg | KR | image | 126 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3900 | GoClean.exe | 143.204.201.66:80 | www.gobest.kr | — | US | suspicious |
3900 | GoClean.exe | 172.217.18.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3900 | GoClean.exe | 119.205.238.29:80 | www.mediacategory.com | Korea Telecom | KR | suspicious |
3900 | GoClean.exe | 14.0.115.222:80 | img.mobon.net | — | KR | suspicious |
3900 | GoClean.exe | 172.217.16.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2672 | GoCleanUp.exe | 143.204.201.66:80 | www.gobest.kr | — | US | suspicious |
2972 | iexplore.exe | 143.204.201.66:80 | www.gobest.kr | — | US | suspicious |
1728 | GoClean.exe | 172.217.18.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1728 | GoClean.exe | 143.204.201.66:80 | www.gobest.kr | — | US | suspicious |
1728 | GoClean.exe | 119.205.238.29:80 | www.mediacategory.com | Korea Telecom | KR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gobest.kr |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.mediacategory.com |
| suspicious |
ocsp.pki.goog |
| whitelisted |
img.mobon.net |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |