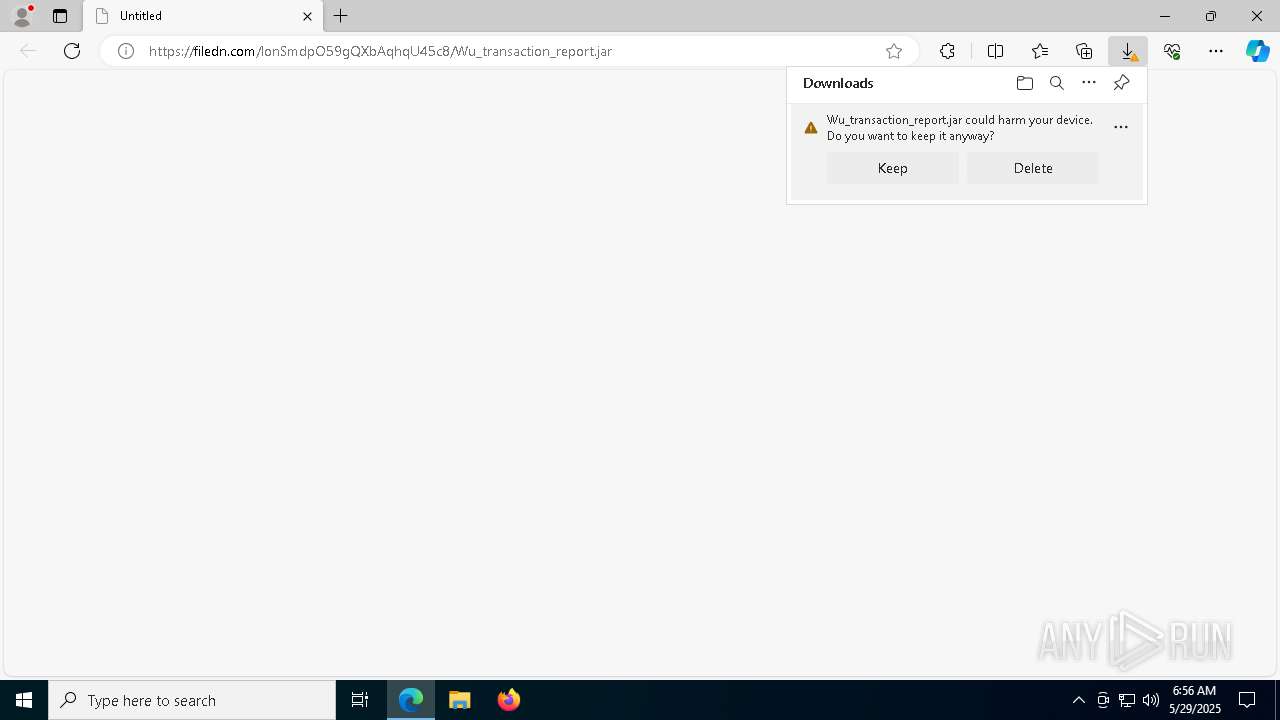
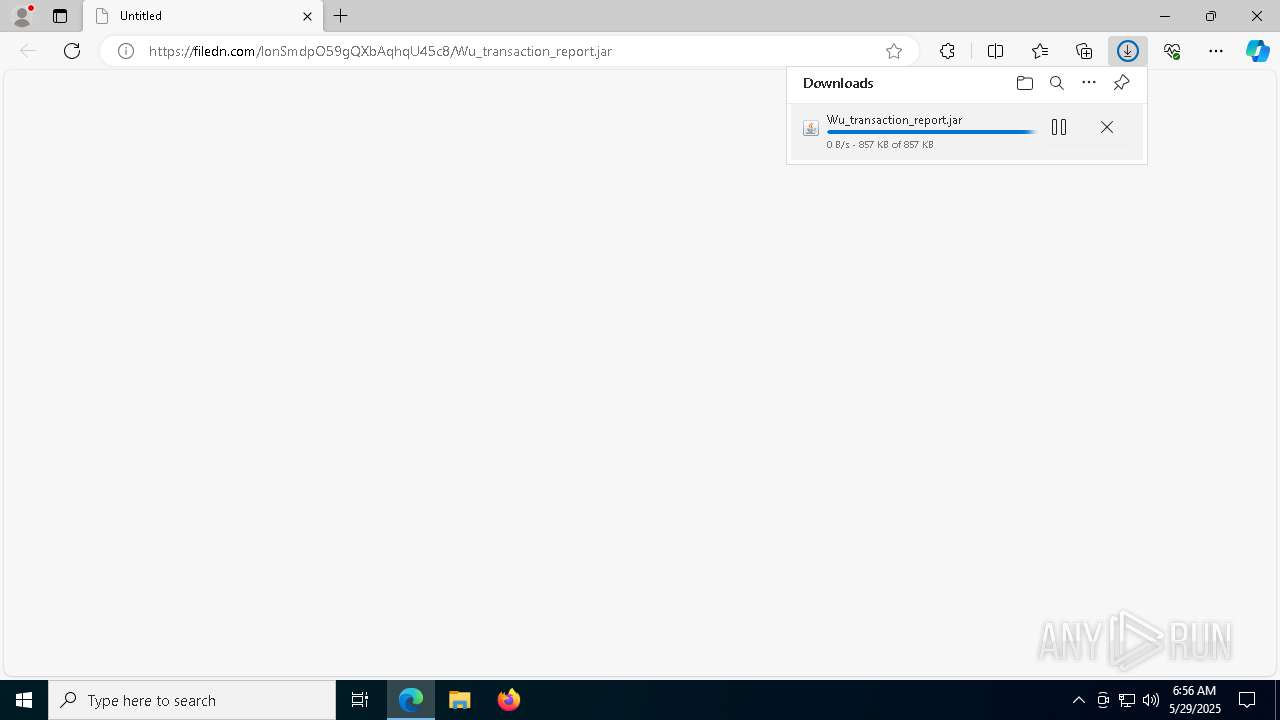
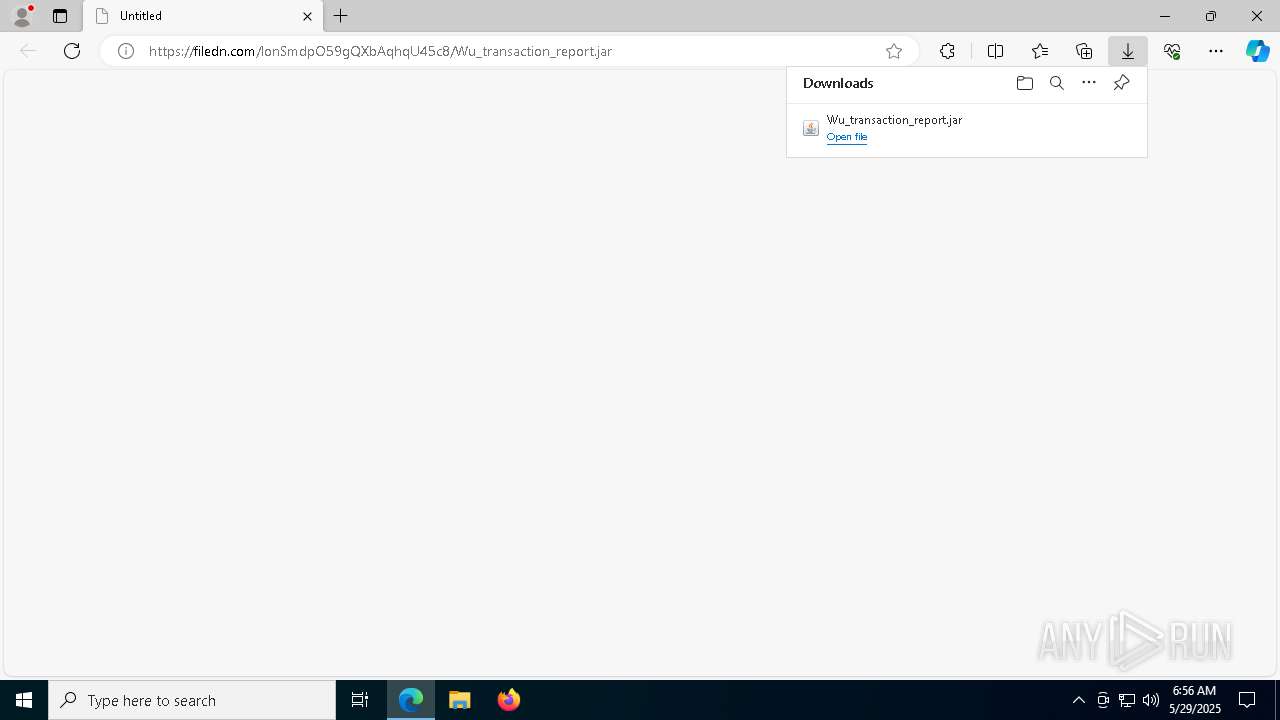
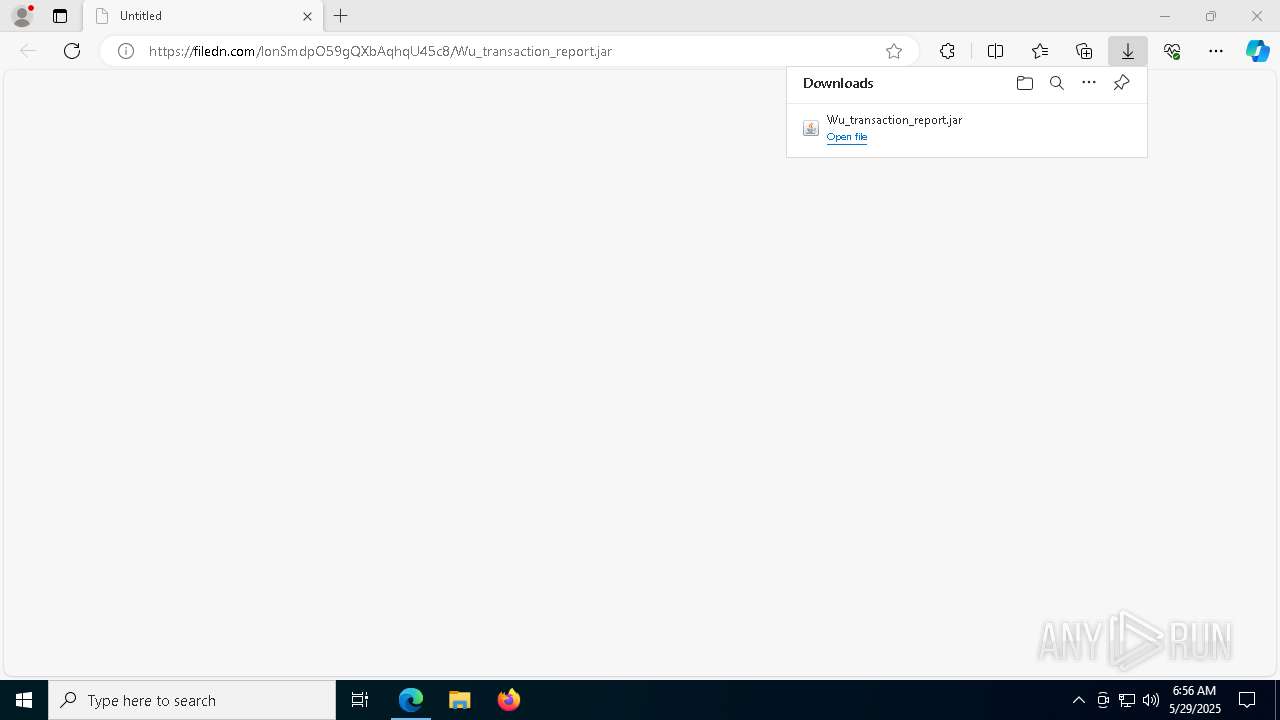
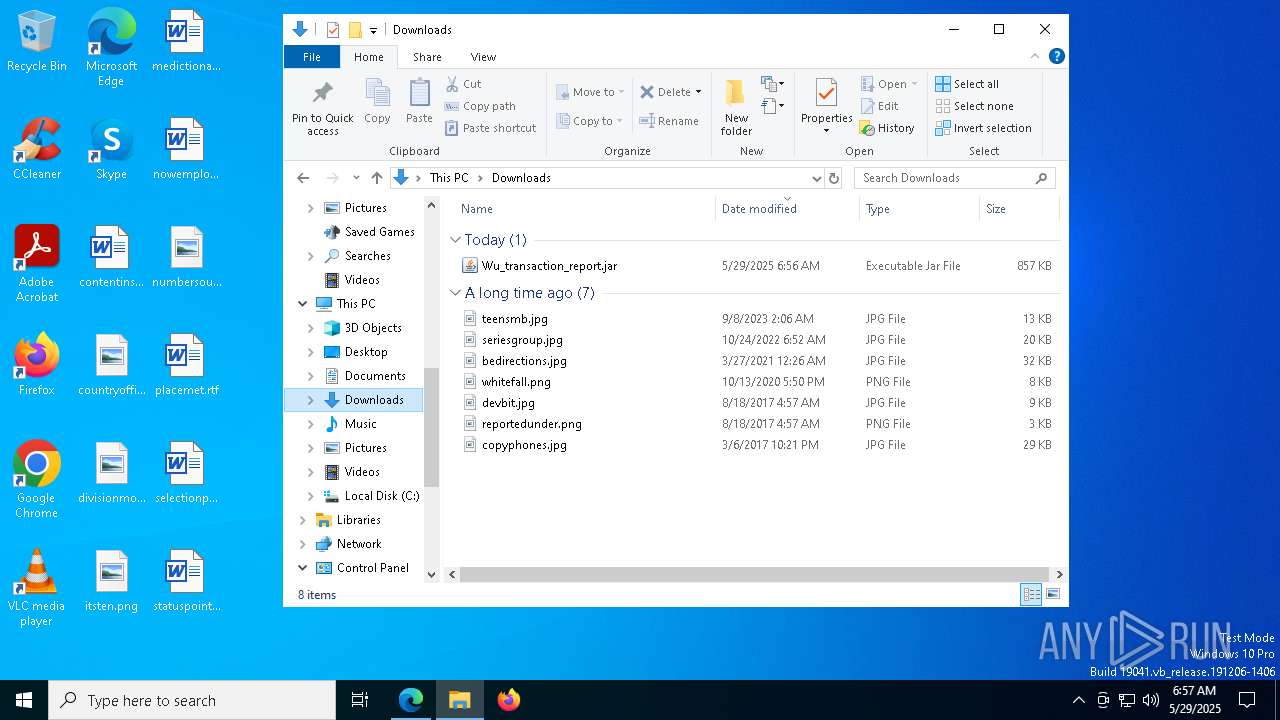
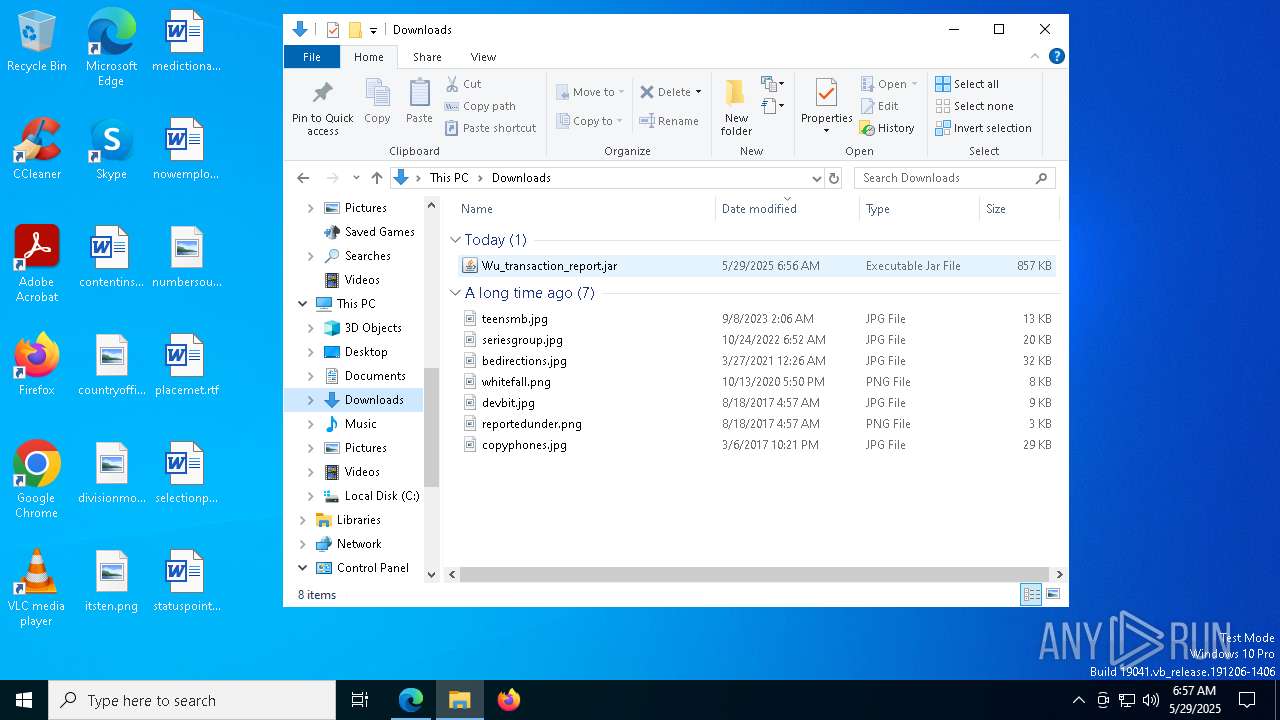
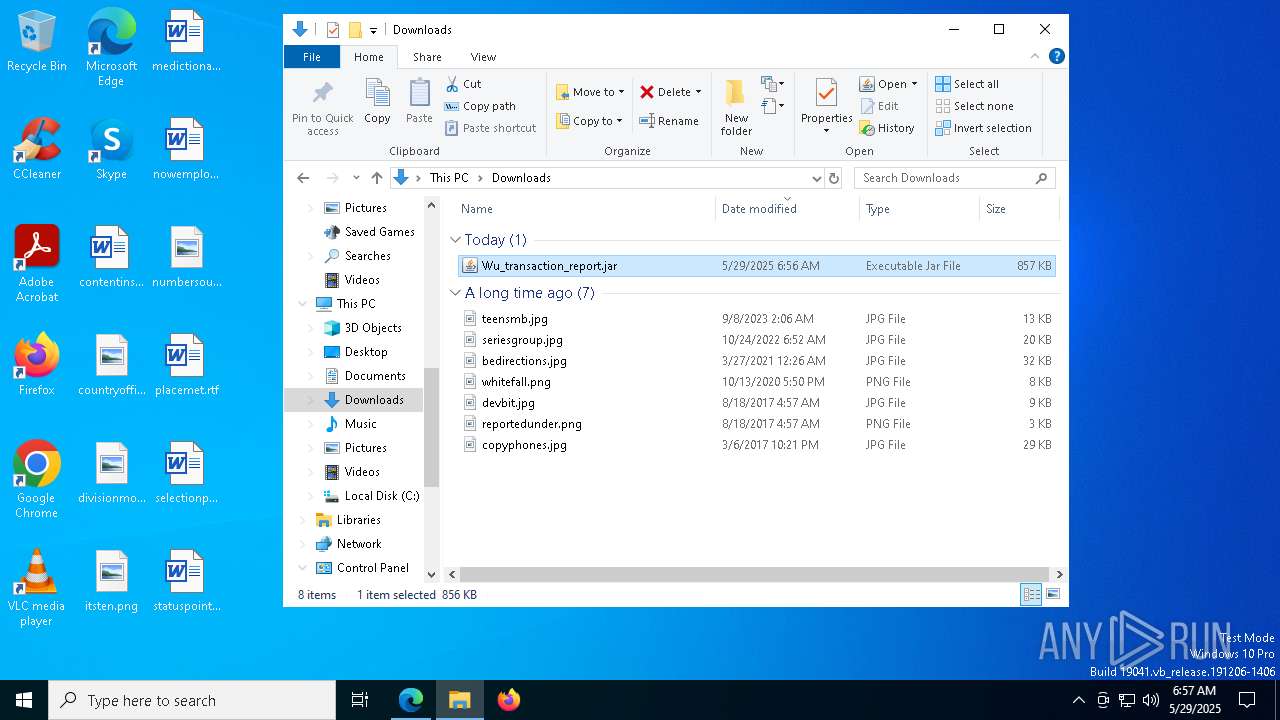
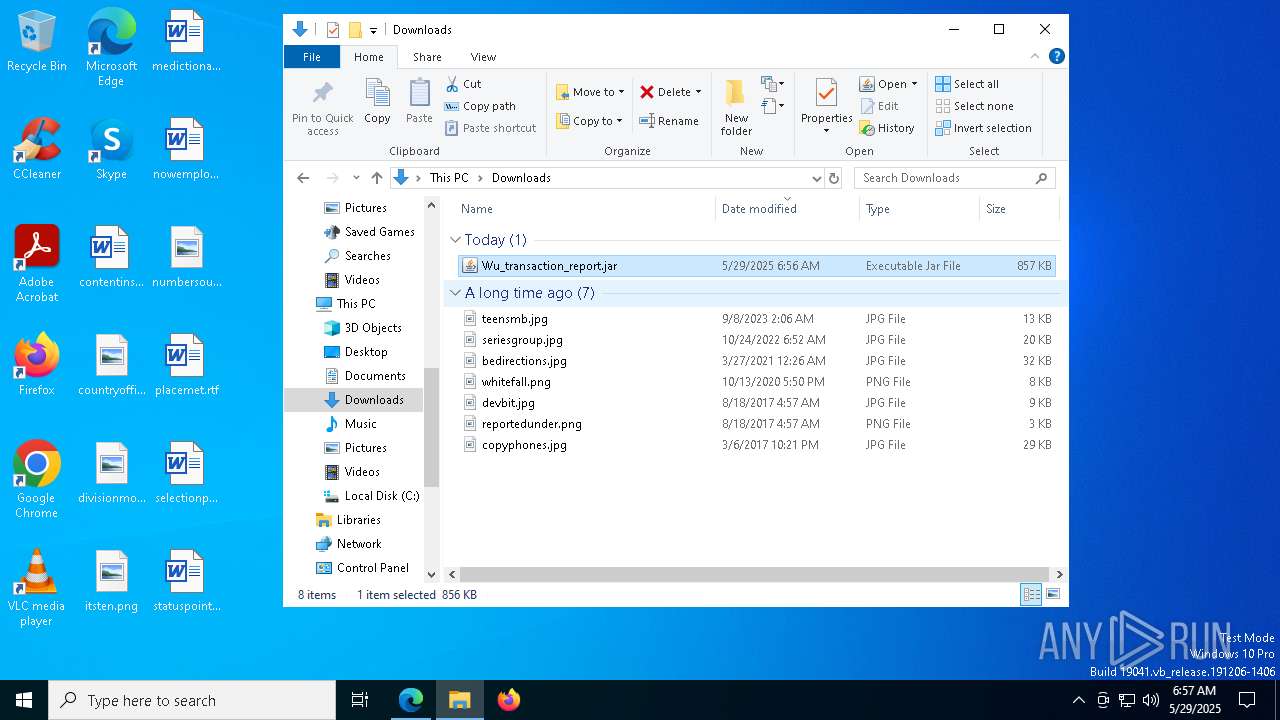
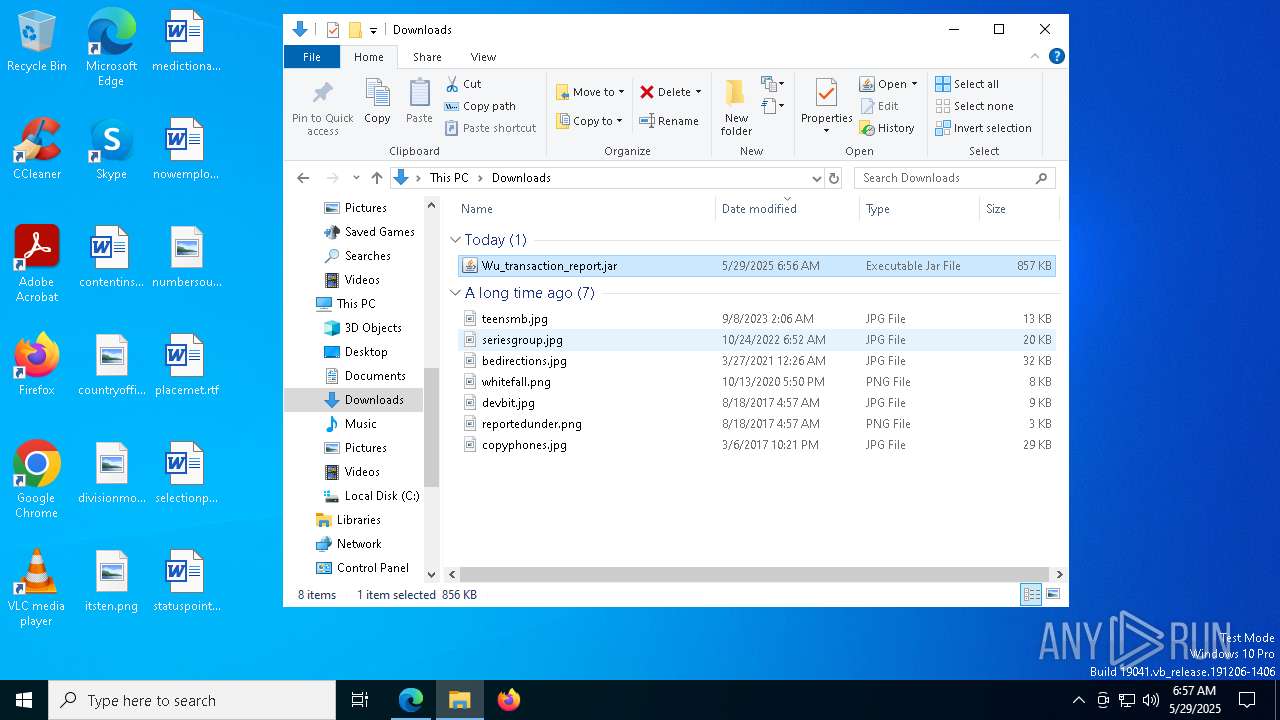
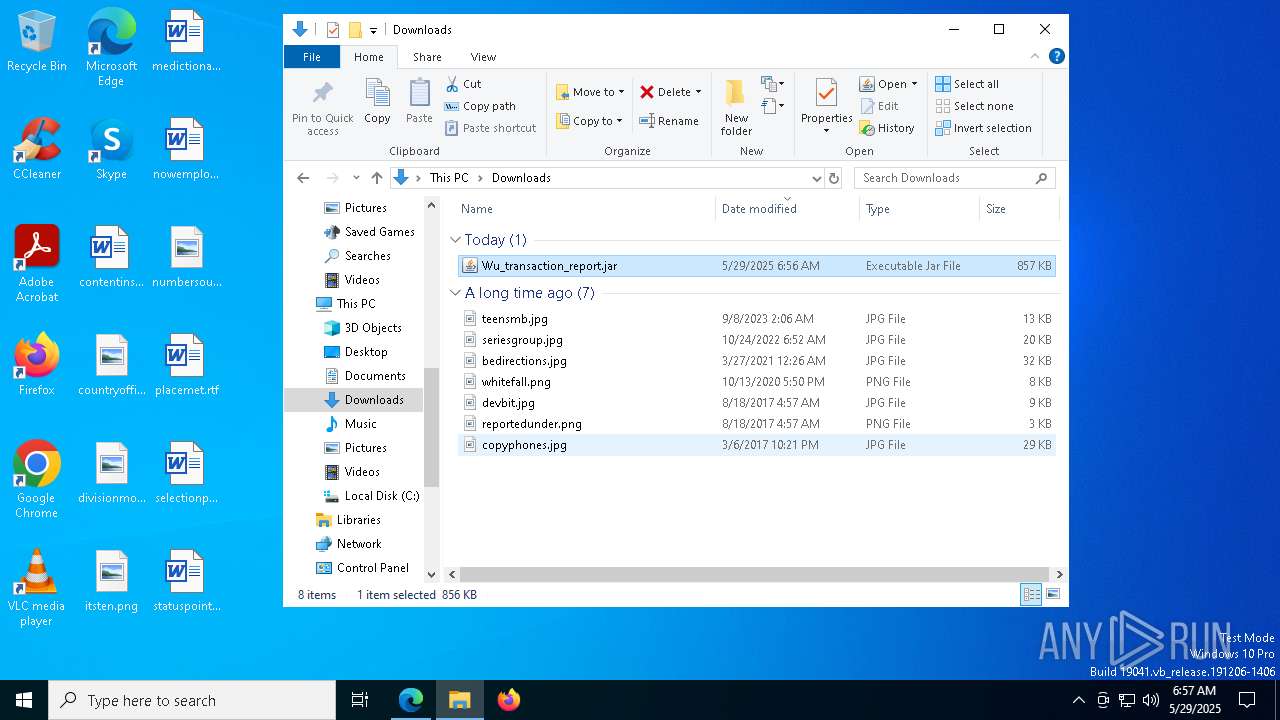
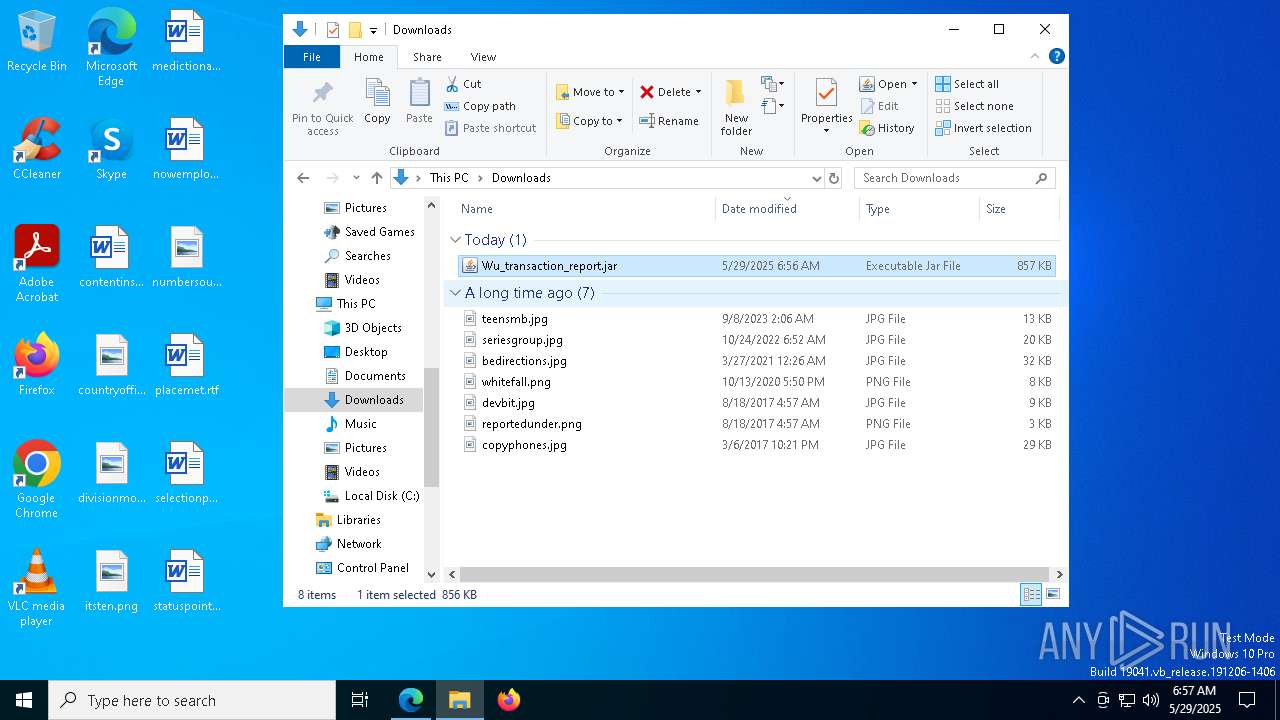
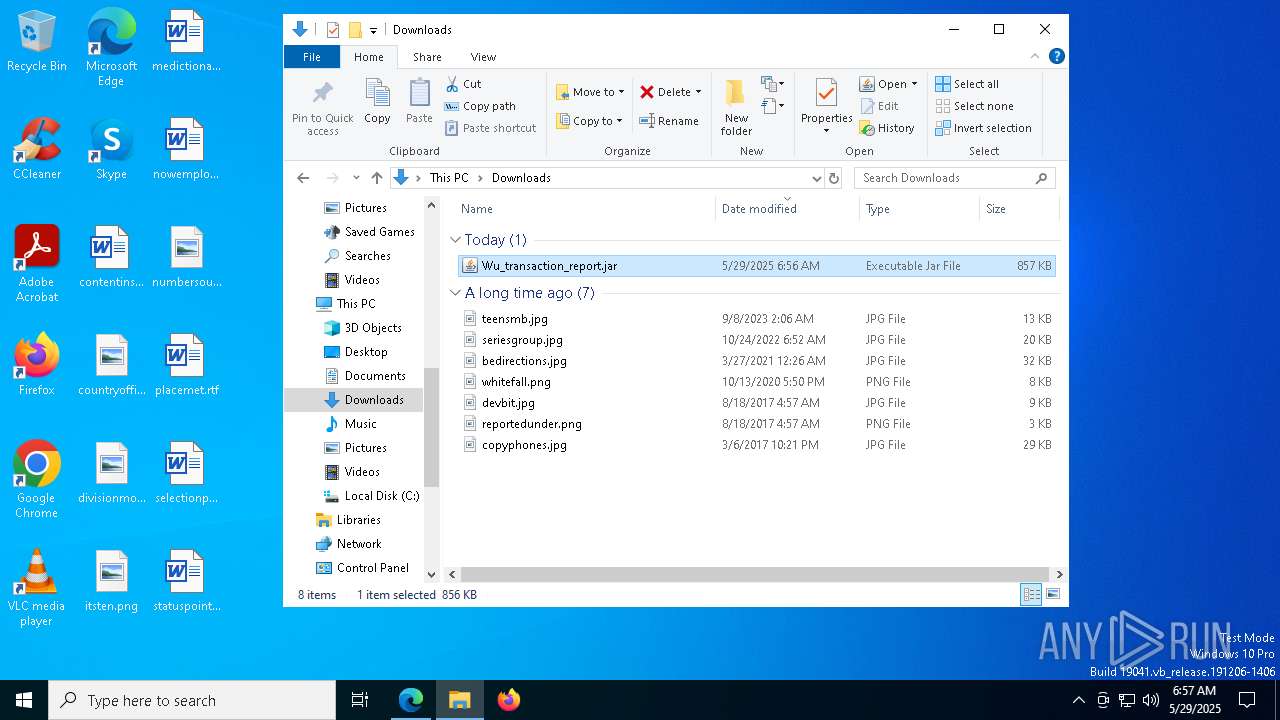
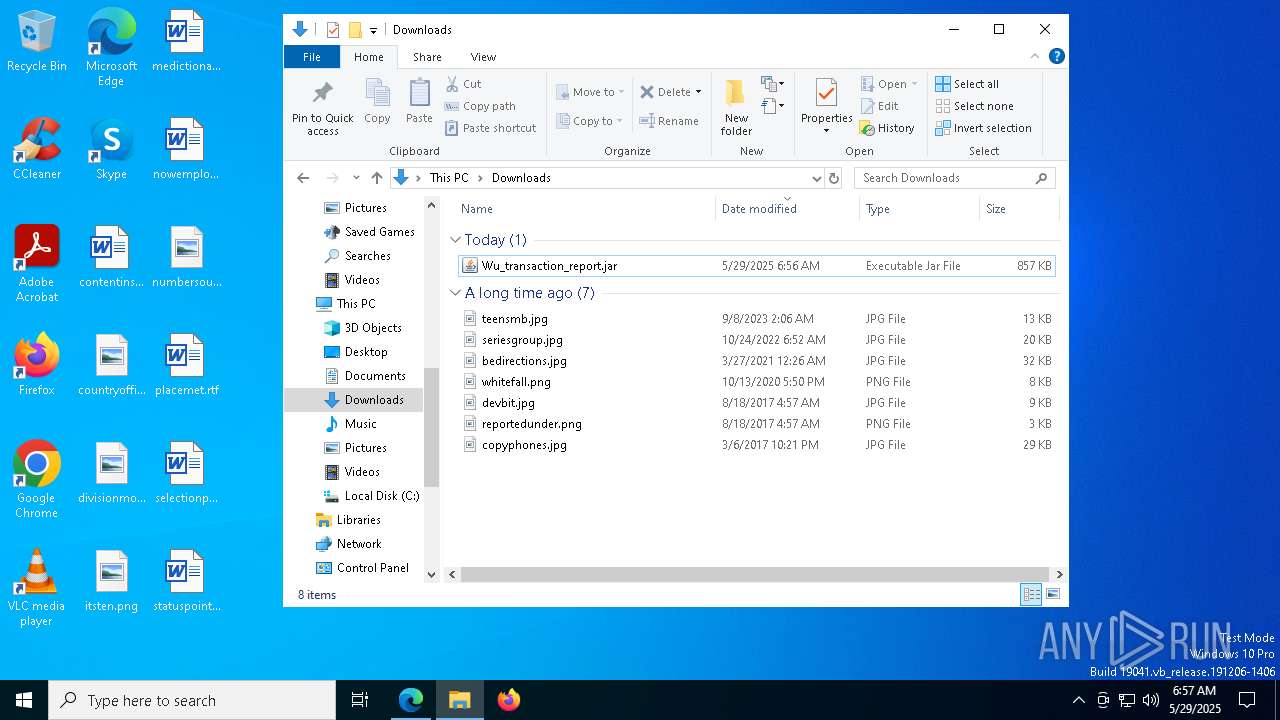
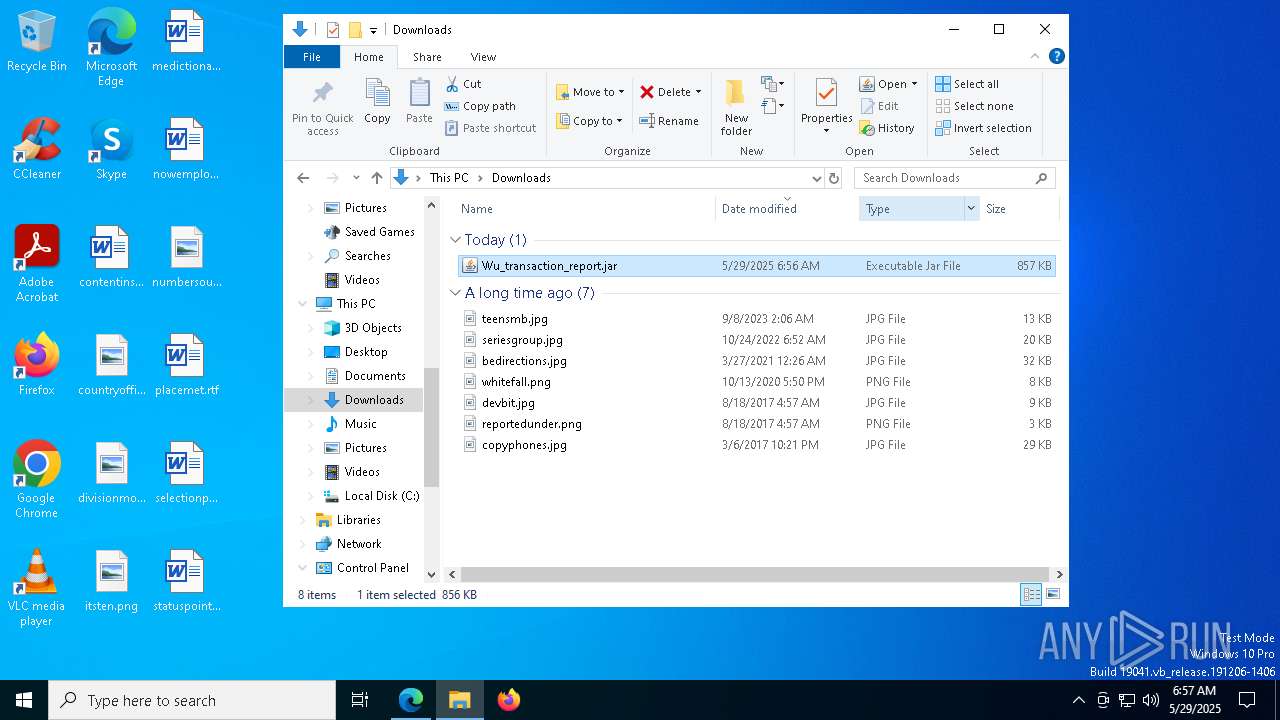
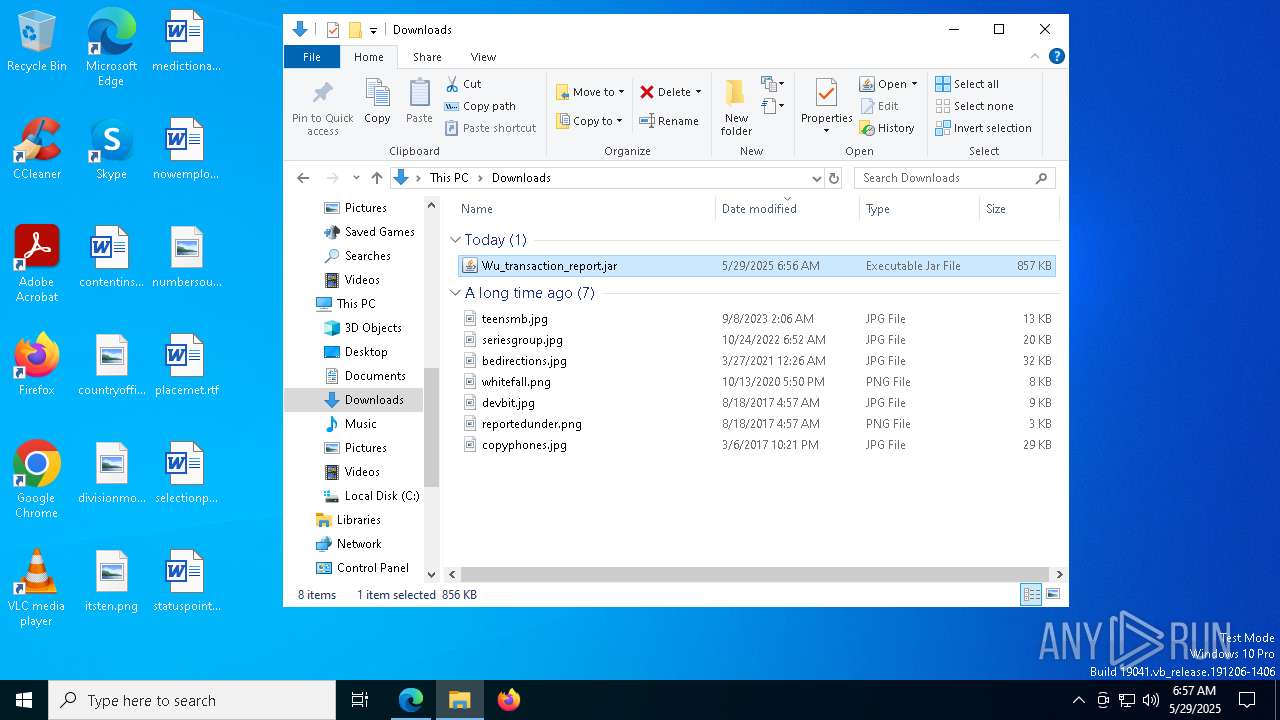
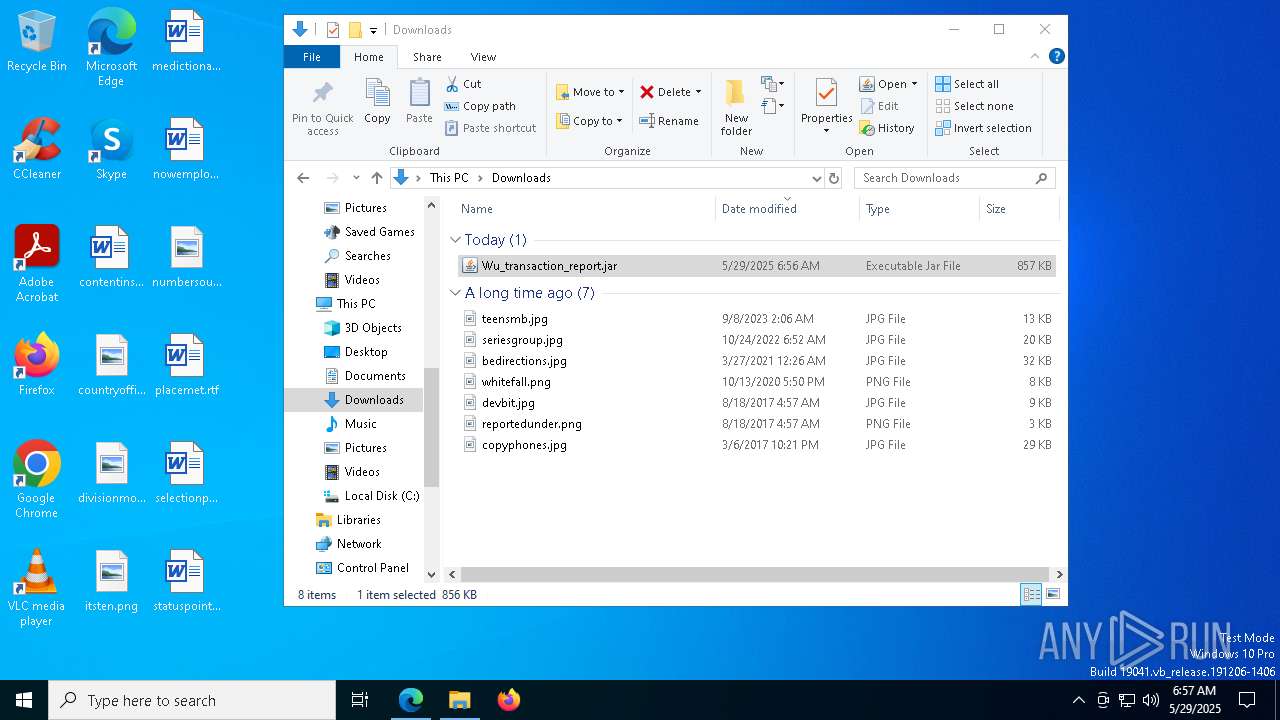
| URL: | https://filedn.com/lonSmdpO59gQXbAqhqU45c8/Wu_transaction_report.jar |
| Full analysis: | https://app.any.run/tasks/893d9220-0992-48ea-9132-27be4883c483 |
| Verdict: | Malicious activity |
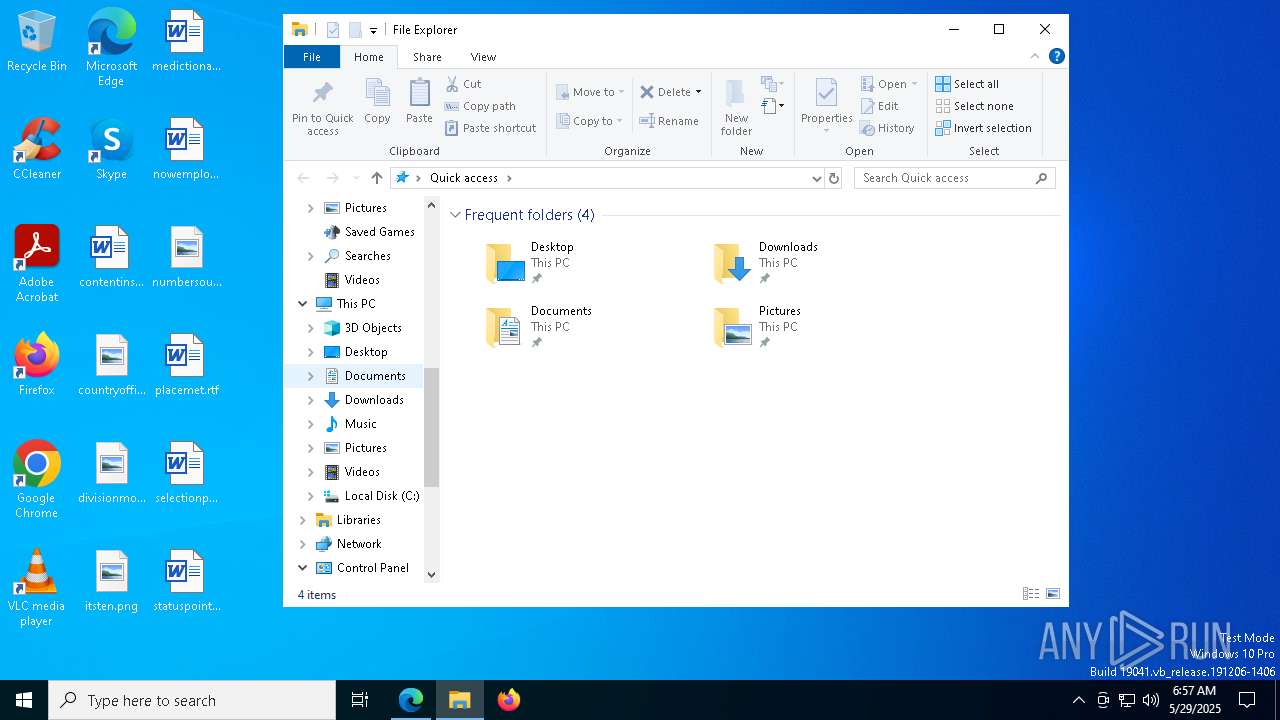
| Analysis date: | May 29, 2025, 06:56:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 608987ED255D442BB3C988F06E73A20A |
| SHA1: | A0F099D42725BA2414C6E79820C8315794F1AA99 |
| SHA256: | 0C1CC86D6A44A34017B1FE74E3C9B01B02E4AF9CE70583495A5637AD5C987389 |
| SSDEEP: | 3:N8pGTSKLZdUYGdrXEnGRMKOAeG:2oVLZdDGCnGyAx |
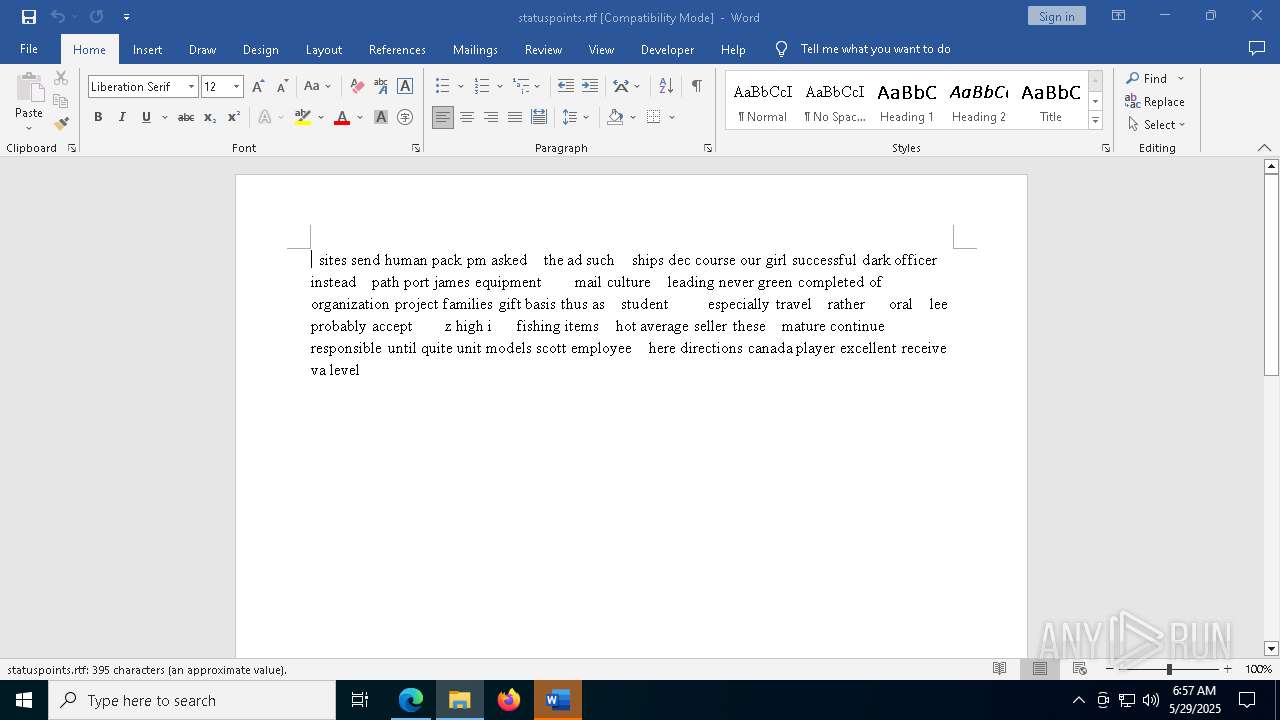
MALICIOUS
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 1348)
Gets %appdata% folder path (SCRIPT)
- wscript.exe (PID: 1348)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 1348)
Creates a new folder (SCRIPT)
- wscript.exe (PID: 1348)
Deletes a file (SCRIPT)
- wscript.exe (PID: 1348)
Create files in the Startup directory
- javaw.exe (PID: 6476)
SUSPICIOUS
The process executes JS scripts
- javaw.exe (PID: 6476)
- javaw.exe (PID: 6744)
- javaw.exe (PID: 3192)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 1348)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 1348)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 1348)
Uses WMIC.EXE to obtain computer system information
- java.exe (PID: 3868)
- java.exe (PID: 7752)
- java.exe (PID: 6992)
Accesses domain name via WMI (SCRIPT)
- WMIC.exe (PID: 5228)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 1348)
Connects to unusual port
- java.exe (PID: 6156)
- java.exe (PID: 4892)
- java.exe (PID: 1276)
- java.exe (PID: 456)
- java.exe (PID: 3884)
- java.exe (PID: 5352)
- java.exe (PID: 7300)
There is functionality for taking screenshot (YARA)
- java.exe (PID: 4892)
- java.exe (PID: 1276)
- java.exe (PID: 456)
- java.exe (PID: 3884)
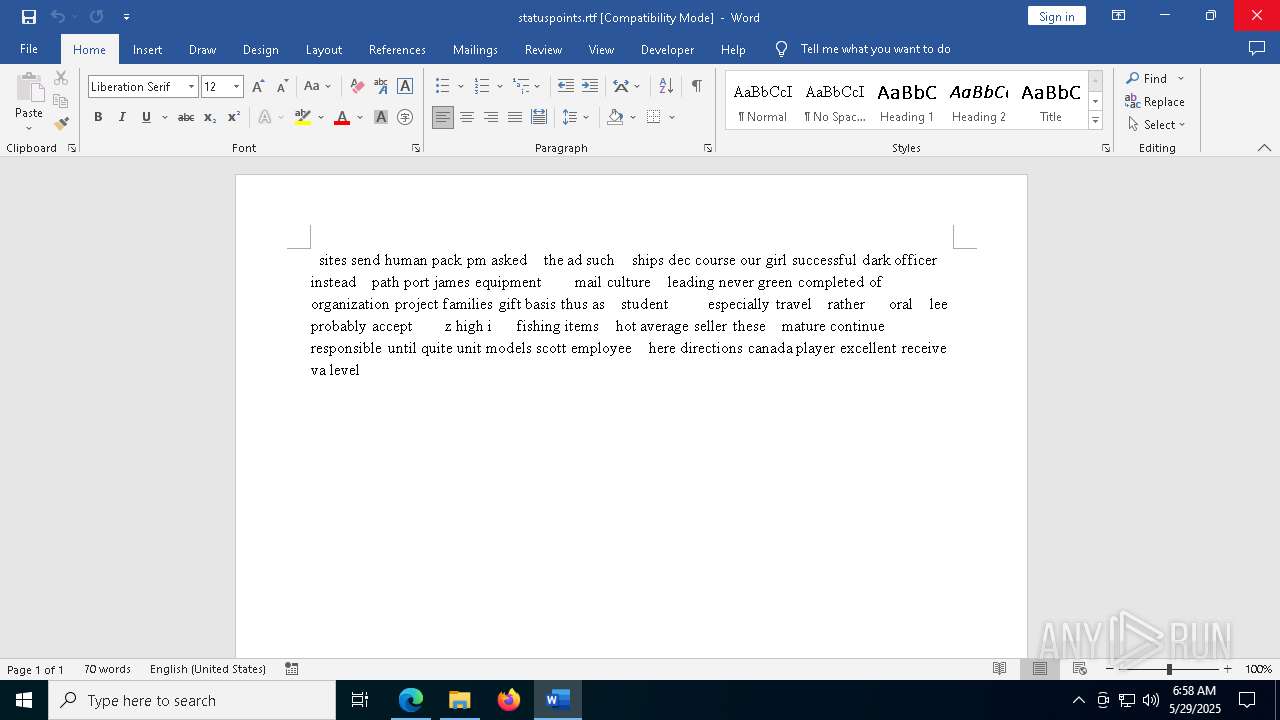
INFO
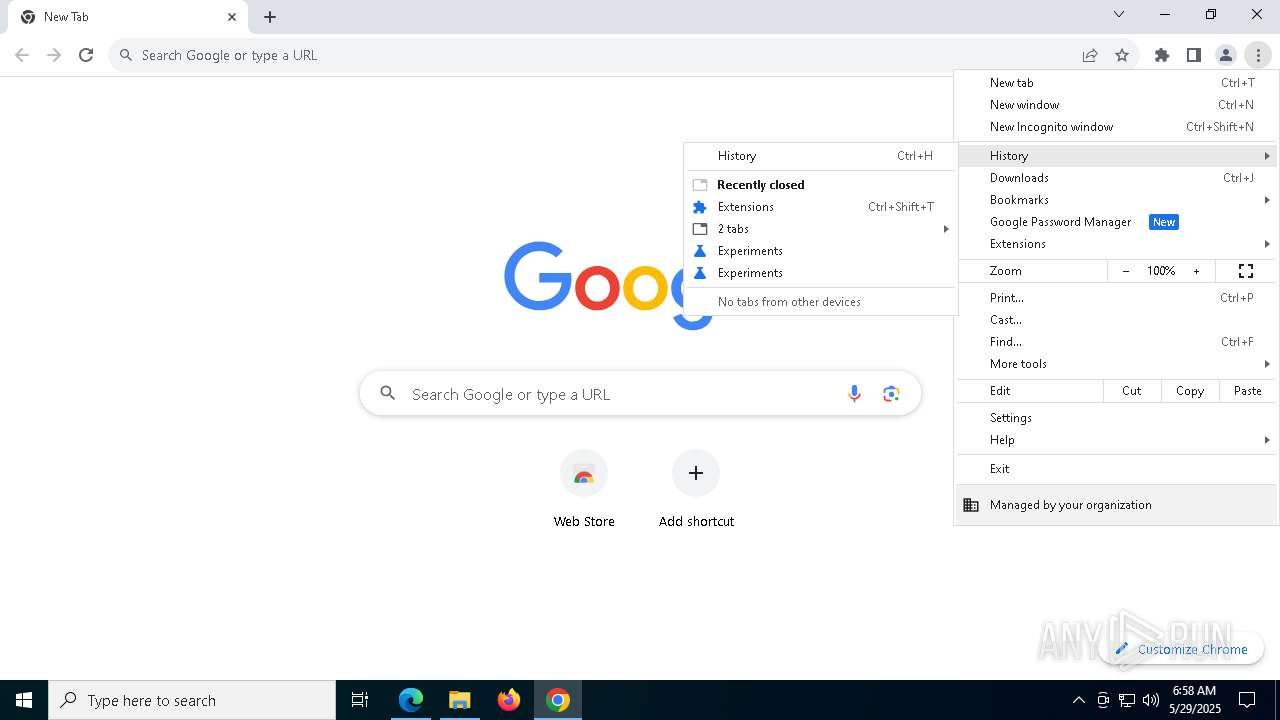
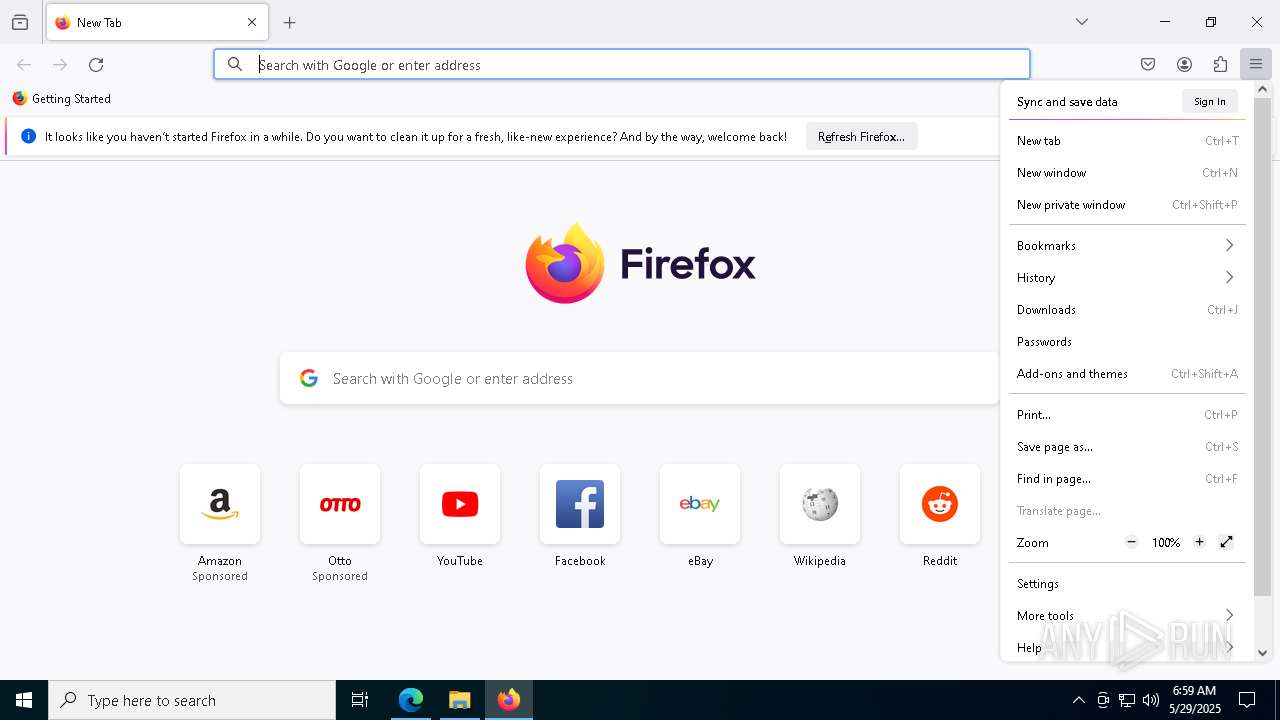
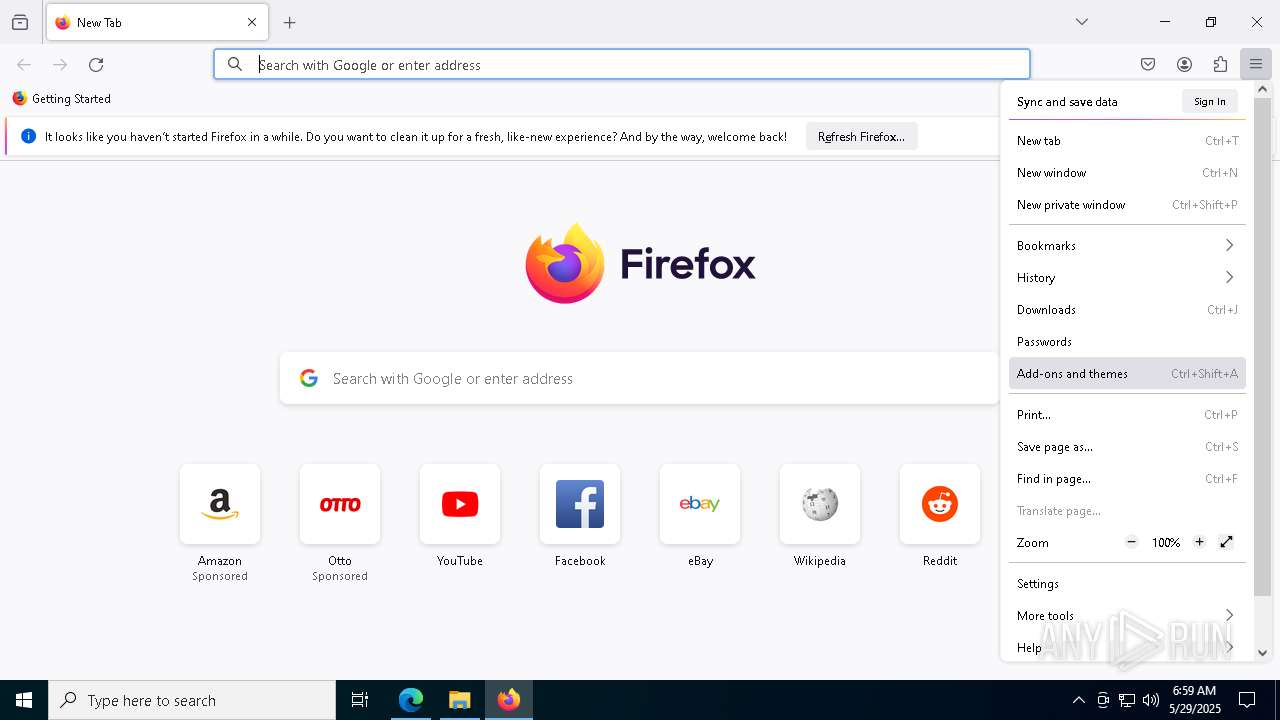
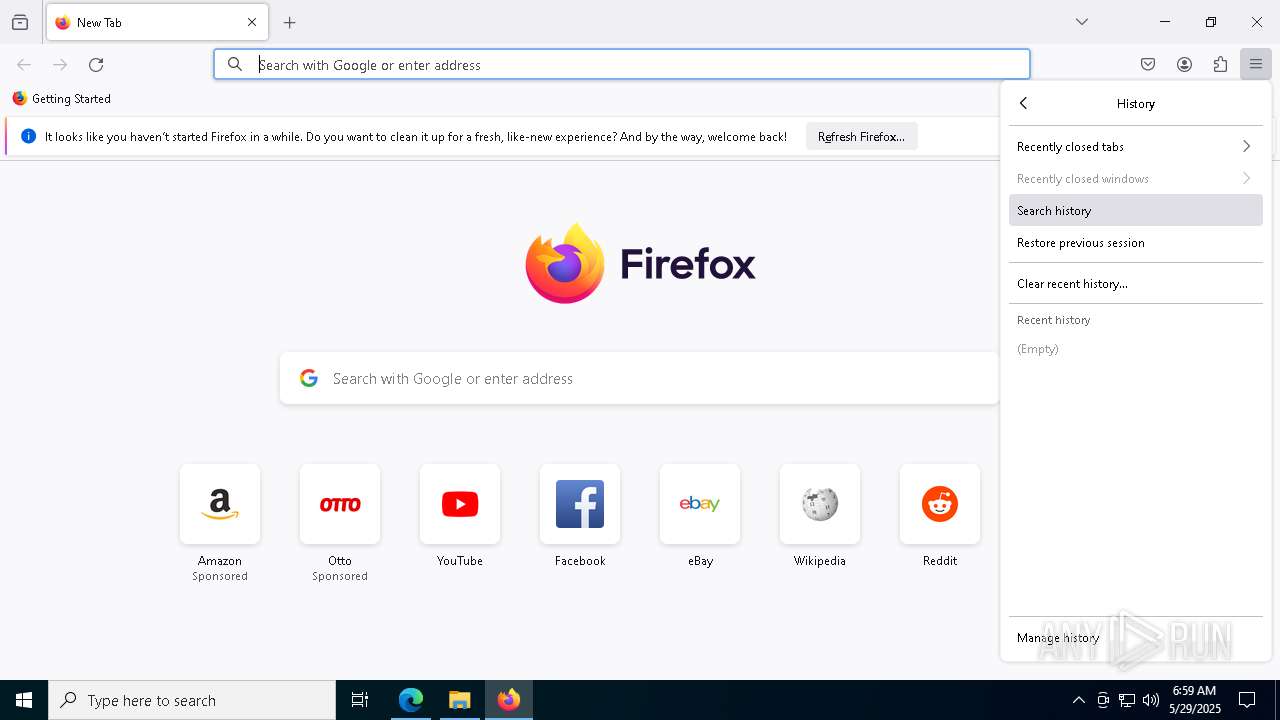
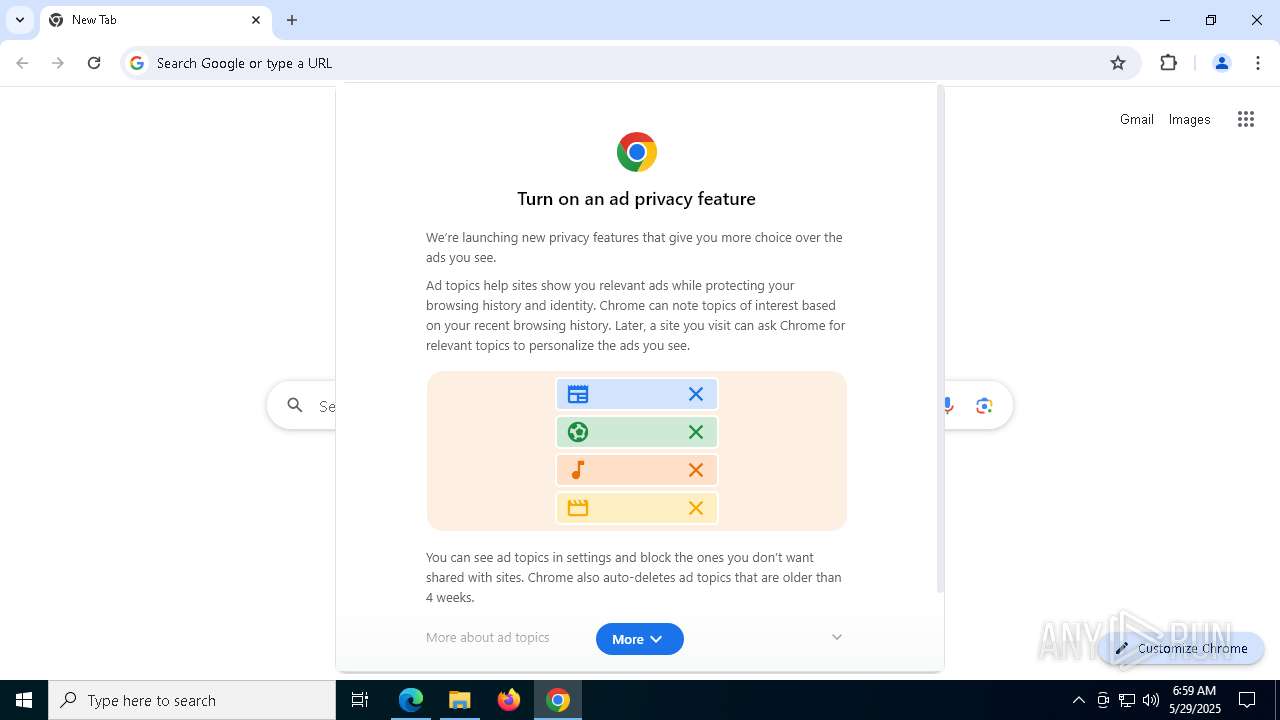
Application launched itself
- msedge.exe (PID: 5344)
- chrome.exe (PID: 8412)
- firefox.exe (PID: 8764)
- chrome.exe (PID: 8748)
- firefox.exe (PID: 8760)
Reads the computer name
- identity_helper.exe (PID: 7928)
- javaw.exe (PID: 6476)
- java.exe (PID: 3868)
- java.exe (PID: 1276)
- java.exe (PID: 6156)
- java.exe (PID: 4892)
Checks supported languages
- identity_helper.exe (PID: 7928)
- javaw.exe (PID: 6476)
- java.exe (PID: 3868)
- java.exe (PID: 4892)
- java.exe (PID: 1276)
- java.exe (PID: 6156)
Reads Environment values
- identity_helper.exe (PID: 7928)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 680)
- msedge.exe (PID: 5344)
Application based on Java
- javaw.exe (PID: 6476)
- javaw.exe (PID: 6744)
- javaw.exe (PID: 3192)
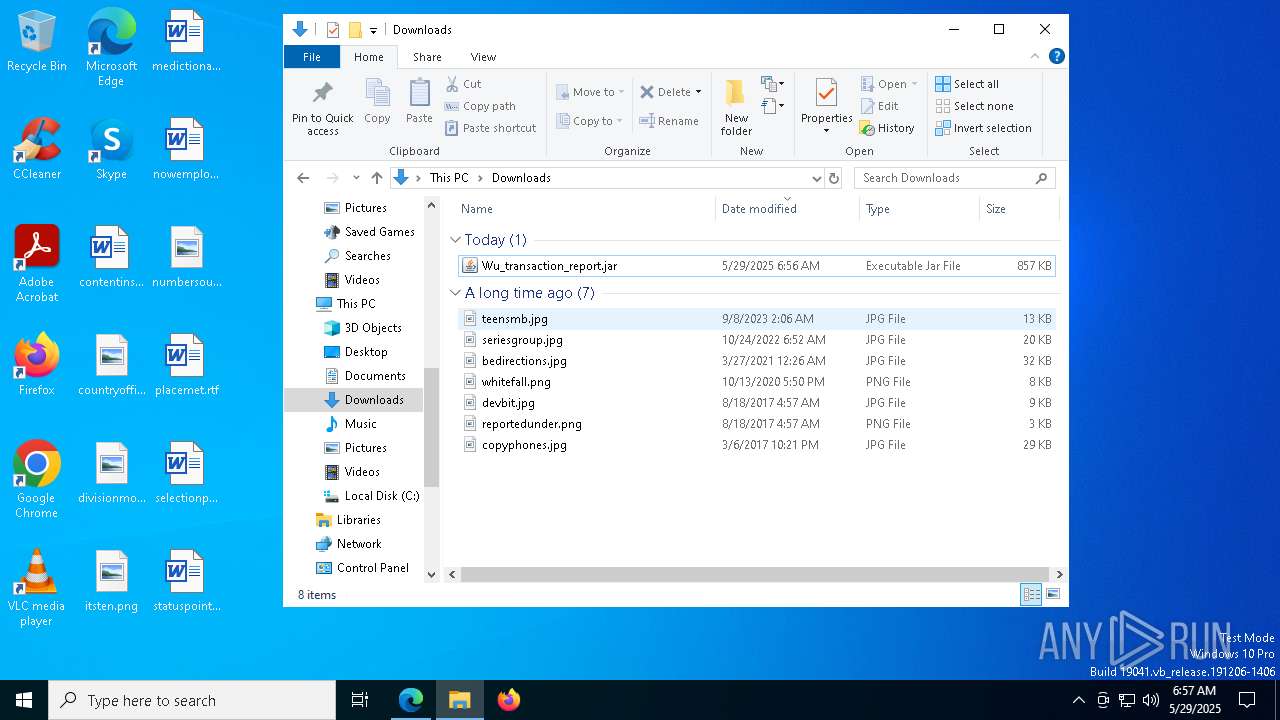
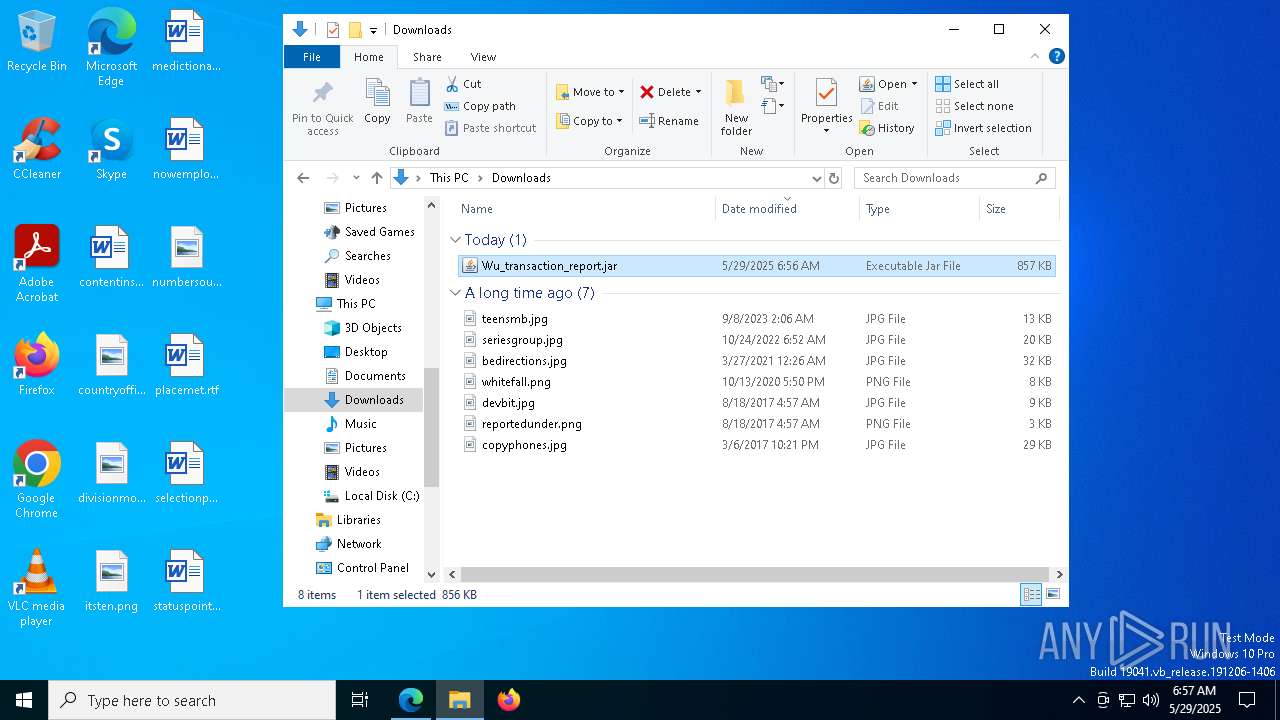
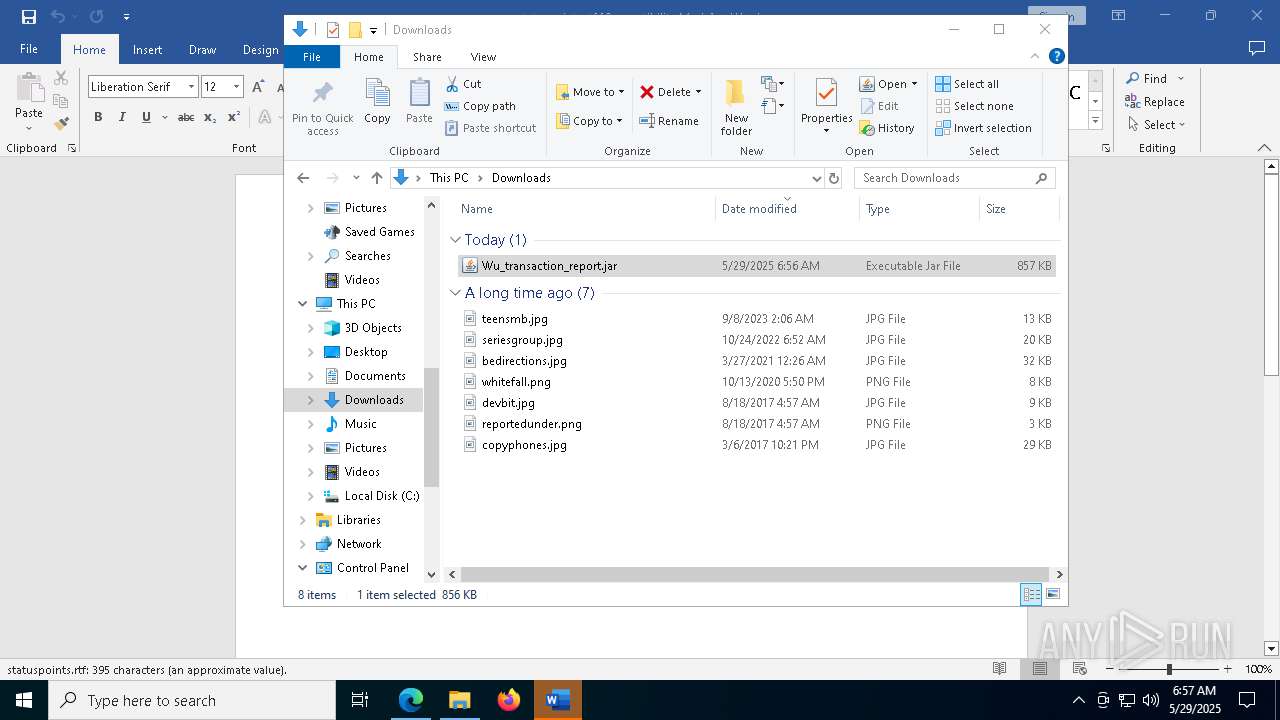
Launch of the file from Downloads directory
- msedge.exe (PID: 5344)
Creates files in the program directory
- javaw.exe (PID: 6476)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 680)
- WMIC.exe (PID: 5228)
Reads the machine GUID from the registry
- javaw.exe (PID: 6476)
Creates files or folders in the user directory
- javaw.exe (PID: 6476)
Create files in a temporary directory
- javaw.exe (PID: 6476)
- java.exe (PID: 3868)
- java.exe (PID: 1276)
- java.exe (PID: 4892)
- java.exe (PID: 6156)
Launch of the file from Startup directory
- javaw.exe (PID: 6476)
Manual execution by a user
- javaw.exe (PID: 6744)
- javaw.exe (PID: 3192)
- WINWORD.EXE (PID: 5084)
- chrome.exe (PID: 8412)
- msedge.exe (PID: 8992)
- firefox.exe (PID: 8764)
- chrome.exe (PID: 8748)
Executable content was dropped or overwritten
- msedge.exe (PID: 1560)
The sample compiled with english language support
- msedge.exe (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
294
Monitored processes
150
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=3368 --field-trial-handle=2164,i,10279400233696262731,17761275323909329782,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 456 | java -jar "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\olbb.jar" | C:\Program Files\Java\jre1.8.0_271\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Version: 8.0.2710.9 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5112 --field-trial-handle=2164,i,10279400233696262731,17761275323909329782,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6416 --field-trial-handle=2164,i,10279400233696262731,17761275323909329782,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 680 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4800 --field-trial-handle=2164,i,10279400233696262731,17761275323909329782,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
91 079
Read events
90 095
Write events
855
Delete events
129
Modification events
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F7628114D7942F00 | |||
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DDA48B14D7942F00 | |||
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {53FA9FA4-F032-497D-B1CC-23886EF33BA5} | |||
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FC3A9E51-6F92-4367-9E26-03B3F097E344} | |||
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 26F2BB14D7942F00 | |||
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
19
Suspicious files
1 248
Text files
278
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10a654.TMP | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10a663.TMP | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10a692.TMP | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10a6f0.TMP | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10a6f0.TMP | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
1 066
DNS requests
225
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5548 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748971709&P2=404&P3=2&P4=FZevrchYUnzAruYGj%2bC9SSthaxeNAplDtT6Vrt4ckbynzAPDel5qmp3zWsFrKwRDUe7EgzesG%2buXmxDul7ZO8Q%3d%3d | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5084 | WINWORD.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5548 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/877ae855-7794-49b4-bc7a-fd75aaeaddb7?P1=1749026200&P2=404&P3=2&P4=K3axD%2bOdrBvpkSr1KqelTVxYChbkPCDJR9%2fHmEq50PDWsXhA35kRYnKRgZJenI%2b%2b0uw9QulqAuZA%2bN9qqUB4fA%3d%3d | unknown | — | — | whitelisted |
5548 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/877ae855-7794-49b4-bc7a-fd75aaeaddb7?P1=1749026200&P2=404&P3=2&P4=K3axD%2bOdrBvpkSr1KqelTVxYChbkPCDJR9%2fHmEq50PDWsXhA35kRYnKRgZJenI%2b%2b0uw9QulqAuZA%2bN9qqUB4fA%3d%3d | unknown | — | — | whitelisted |
5548 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b649b6c2-4484-495a-96f2-2fd1ee2b66ca?P1=1748971719&P2=404&P3=2&P4=C9RxEsPRFMFiuCpJrSlHesiNMX3N9CMk3lFrrY%2bf%2f%2fWgm4c9r9ZMR5Rcv%2fKGHuUlvgi5ovPCD5XK%2bZHpHh7%2fjA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1284 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5344 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7224 | msedge.exe | 23.109.93.100:443 | filedn.com | SERVERS-COM | NL | malicious |
7224 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7224 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
filedn.com |
| malicious |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
7224 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7224 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7224 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7224 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7224 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7224 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7224 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |